| File name: | track-trace.exe |
| Full analysis: | https://app.any.run/tasks/e27077b9-c6d9-4e35-a493-539703f7e3df |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2018, 11:40:11 |
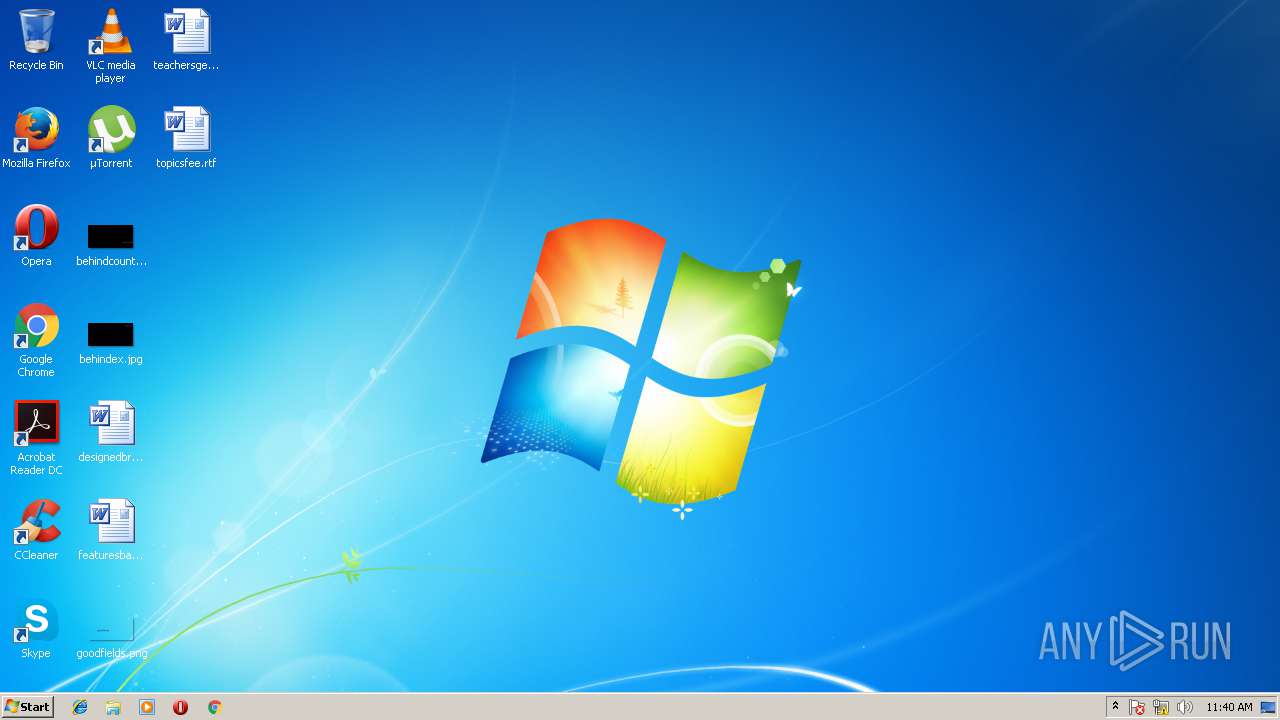
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 593EDF2034F05BBAA5B6EE1A2BD4C0BC |
| SHA1: | 8C9C5B3A220286A02A8253DF7369BB376AE9A134 |
| SHA256: | 7C771E4E478677F6B57E68FB261D369E38ABC5D0C65506A6330AB66EEA08C355 |
| SSDEEP: | 6144:Axz3hsjqGH6PtB1Lti1RRbBwSY2lc7kicx4NxHS5lNOh:uSjpHmtHLORRbBwvQipHSch |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- firefox.exe (PID: 3048)
- track-trace.exe (PID: 348)
Starts itself from another location
- track-trace.exe (PID: 348)
Reads CPU info
- firefox.exe (PID: 3048)
Starts CMD.EXE for commands execution
- track-trace.exe (PID: 348)
Application launched itself
- firefox.exe (PID: 3048)
INFO
Dropped object may contain URL's
- track-trace.exe (PID: 348)
- firefox.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:15 20:07:29+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 117248 |
| InitializedDataSize: | 260096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11741 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.9.2 |
| ProductVersionNumber: | 3.5.9.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| PrivateBuild: | 3.5.9.2 |
| FileDescription: | Nuts Snot Synchronized |
| LegalCopyright: | Copyright © 2016 All rights reserved. COMPELSON Labs |
| FileVersion: | 3.5.9.2 |
| LegalTrademarks: | Copyright © 2016 All rights reserved. COMPELSON Labs |
| CompanyName: | COMPELSON Labs |
| Comments: | Nuts Snot Synchronized |
| OriginalFileName: | Achievable.exe |
| ProductName: | Achievable |
| ProductVersion: | 3.5.9.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jan-2018 19:07:29 |
| Detected languages: |
|
| PrivateBuild: | 3.5.9.2 |
| FileDescription: | Nuts Snot Synchronized |
| LegalCopyright: | Copyright © 2016 All rights reserved. COMPELSON Labs |
| FileVersion: | 3.5.9.2 |
| LegalTrademarks: | Copyright © 2016 All rights reserved. COMPELSON Labs |
| CompanyName: | COMPELSON Labs |
| Comments: | Nuts Snot Synchronized |
| OriginalFilename: | Achievable.exe |
| ProductName: | Achievable |
| ProductVersion: | 3.5.9.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 15-Jan-2018 19:07:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001C709 | 0x0001C800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55986 |
.text1 | 0x0001E000 | 0x00000060 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 1.19814 |
.rdata | 0x0001F000 | 0x0000A748 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.06059 |
.data | 0x0002A000 | 0x00004064 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.09405 |
.trace | 0x0002F000 | 0x000007E0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.6781 |
_RDATA | 0x00030000 | 0x00000540 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57501 |
.rsrc | 0x00031000 | 0x00032568 | 0x00032600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.73346 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15573 | 1041 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.08252 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.57879 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.50209 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.94597 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.86191 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
226 | 6.70504 | 68304 | Latin 1 / Western European | English - United States | RCDATA |
880 | 4.2186 | 972 | Latin 1 / Western European | English - United States | RT_STRING |
2048 | 1.47851 | 296 | Latin 1 / Western European | English - United States | RT_BITMAP |
3065 | 4.52668 | 2812 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
CRYPT32.dll |
DCIMAN32.dll |
GDI32.dll |
GLU32.dll |
IMM32.dll |
KERNEL32.dll |
OLEAUT32.dll |
OPENGL32.dll |
RPCRT4.dll |
Total processes
37
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Users\admin\Downloads\track-trace.exe" | C:\Users\admin\Downloads\track-trace.exe | explorer.exe | ||||||||||||
User: admin Company: COMPELSON Labs Integrity Level: MEDIUM Description: Nuts Snot Synchronized Exit code: 0 Version: 3.5.9.2 Modules
| |||||||||||||||
| 2328 | "C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\dht_feed.exe" | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\dht_feed.exe | — | track-trace.exe | |||||||||||
User: admin Company: COMPELSON Labs Integrity Level: MEDIUM Description: Nuts Snot Synchronized Exit code: 0 Version: 3.5.9.2 Modules
| |||||||||||||||
| 2880 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\upd19ee55a1.bat" | C:\Windows\system32\cmd.exe | — | track-trace.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3048.0.393488434\400384663" -childID 1 -isForBrowser -intPrefs 5:50|6:-1|28:1000|33:20|34:10|43:128|44:10000|49:0|51:400|52:1|53:0|54:0|59:0|60:120|61:120|91:2|92:1|106:5000|117:0|119:0|130:10000|142:-1|147:128|148:10000|149:0|155:24|156:32768|158:0|159:0|167:5|171:1048576|172:100|173:5000|175:600|177:1|186:1|190:0|200:60000| -boolPrefs 1:0|2:0|4:0|26:1|27:1|30:0|35:1|36:0|37:0|38:0|41:1|42:1|45:0|46:0|47:0|48:0|50:0|55:1|56:1|57:0|58:1|62:1|63:1|64:0|65:1|66:1|67:0|68:1|71:0|72:0|75:1|76:1|80:1|81:1|82:1|83:0|85:0|86:0|87:1|88:0|93:1|94:0|100:0|105:0|108:1|109:1|112:1|114:1|118:0|121:1|124:1|125:1|131:0|132:0|133:1|135:0|141:0|143:1|144:0|145:1|146:0|153:0|154:0|157:1|160:0|162:1|164:1|165:0|170:0|174:1|179:0|180:0|181:0|182:1|183:0|184:0|185:1|188:0|192:0|193:0|194:1|195:1|196:0|197:1|198:1|199:1|201:0|202:0|204:0|212:1|213:1|214:0|215:0|216:0| -stringPrefs "3:7;release|134:3;1.0|151:332; ¼½¾ǃː̷̸։֊׃״؉؊٪۔܁܂܃܄ᅟᅠ᜵ ‐’․‧ ‹›⁁⁄⁒ ⅓⅔⅕⅖⅗⅘⅙⅚⅛⅜⅝⅞⅟∕∶⎮╱⧶⧸⫻⫽⿰⿱⿲⿳⿴⿵⿶⿷⿸⿹⿺⿻ 。〔〕〳゠ㅤ㈝㈞㎮㎯㏆㏟꞉︔︕︿﹝﹞./。ᅠ�|152:8;moderate|187:38;{f65cf664-d1ea-459b-aa87-8a0f4bc9ab90}|" -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" 3048 "\\.\pipe\gecko-crash-server-pipe.3048" tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 55.0.3 Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 55.0.3 Modules
| |||||||||||||||
Total events
643
Read events
641
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3048) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3048) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B000000090000000000000000000000000000000400000000000000108E82C8479FD301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A8640B0000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
Executable files
2
Suspicious files
67
Text files
14
Unknown types
67
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\storage\permanent\moz-safe-about+home\.metadata-tmp | — | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\storage\permanent\moz-safe-about+home\.metadata-v2-tmp | — | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\storage\permanent\moz-safe-about+home\idb\818200132aebmoouht.sqlite-journal | — | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\storage\permanent\moz-safe-about+home\idb\818200132aebmoouht.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\hggh073w.default\directoryLinks.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\compatibility.ini | ini | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\storage\permanent\moz-safe-about+home\.metadata-v2 | binary | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\hggh073w.default\cache2\entries\CD0AFE67BA14362B1E4B7C47AAE4A275BFF93C71 | der | |
MD5:— | SHA256:— | |||
| 3048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\hggh073w.default\storage\permanent\moz-safe-about+home\.metadata | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
27
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
— | — | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
— | — | POST | 200 | 172.217.18.14:80 | http://clients1.google.com/ocsp | US | der | 463 b | whitelisted |
— | — | POST | 200 | 172.217.18.14:80 | http://clients1.google.com/ocsp | US | der | 463 b | whitelisted |
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
— | — | POST | 200 | 172.217.18.14:80 | http://clients1.google.com/ocsp | US | der | 463 b | whitelisted |
— | — | POST | 200 | 172.217.18.14:80 | http://clients1.google.com/ocsp | US | der | 463 b | whitelisted |
— | — | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 54.148.143.136:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
— | — | 52.24.184.189:443 | normandy.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
— | — | 52.209.235.142:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
— | — | 34.208.7.8:443 | aus5.mozilla.org | Amazon.com, Inc. | US | whitelisted |
— | — | 13.33.47.190:443 | snippets.cdn.mozilla.net | — | US | unknown |
— | — | 34.211.20.200:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
— | — | 52.84.213.80:443 | tiles-cloudfront.cdn.mozilla.net | — | US | unknown |
— | — | 172.217.16.174:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
normandy.cdn.mozilla.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
normandy-cdn-elb-prod-787321160.us-west-2.elb.amazonaws.com |
| shared |
a1089.d.akamai.net |
| whitelisted |
locprod1-elb-eu-west-1.prod.mozaws.net |
| whitelisted |