| File name: | kernel32.dll |
| Full analysis: | https://app.any.run/tasks/7933c6d9-71e8-4d0c-a753-8183f7bedb02 |
| Verdict: | No threats detected |
| Analysis date: | March 15, 2018, 03:54:55 |
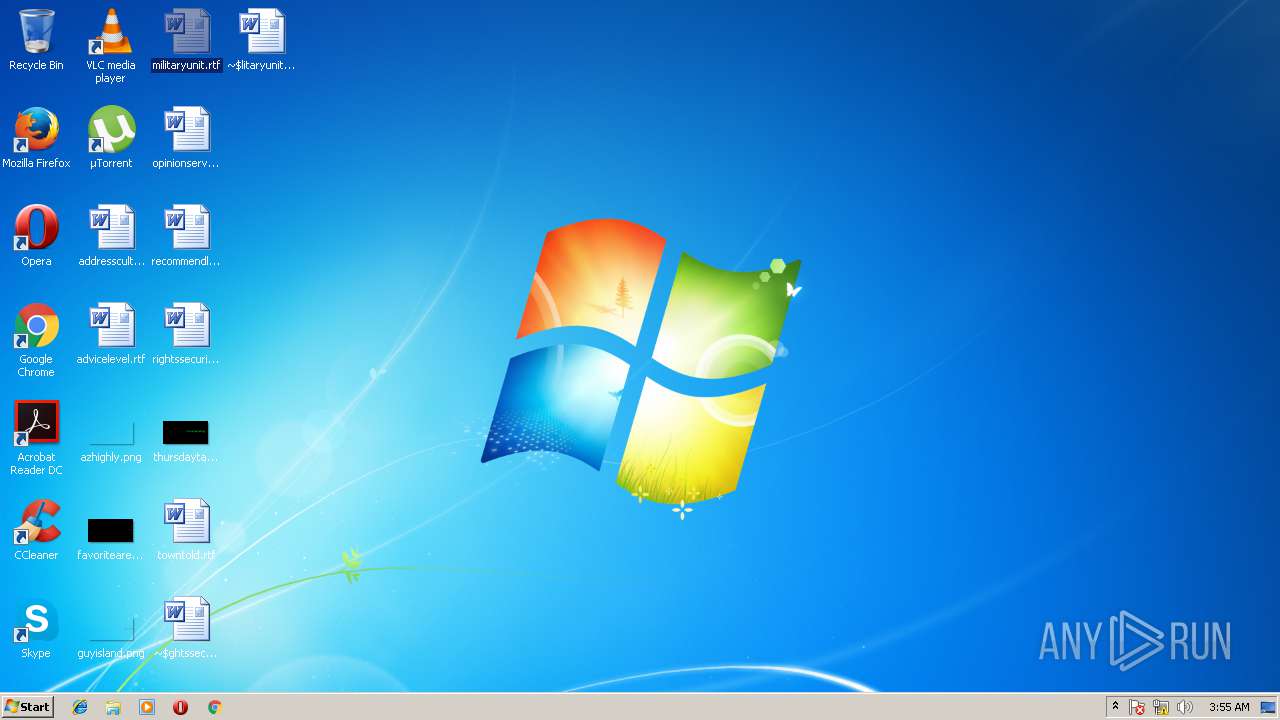
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (console) x86-64, for MS Windows |
| MD5: | 222A8E8EA615529B5025DE5782830AF1 |
| SHA1: | A2E3E202914E94402462F2DB2ECD6EEDCCCA0B8C |
| SHA256: | 7C76BB7AEC3C51164A49041E8A710C3C291BA1D30BAE07D126434A52A80D99E1 |
| SSDEEP: | 12288:+W0ban3HUgpTeJNOwSgwUv2hGmNsTFdr3EqsWaFL2cDfguXrsvA/Sa8VVrgs:TknNO6w/hGmNsb3XsWg2y1rsvA/Sa8zB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- WINWORD.EXE (PID: 2168)
- WINWORD.EXE (PID: 2616)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2168)
- WINWORD.EXE (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 1976:06:22 07:45:20+01:00 |
| PEType: | PE32+ |
| LinkerVersion: | 14.1 |
| CodeSize: | 463360 |
| InitializedDataSize: | 226304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12070 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.16299.15 |
| ProductVersionNumber: | 10.0.16299.15 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows NT BASE API Client DLL |
| FileVersion: | 10.0.16299.15 (WinBuild.160101.0800) |
| InternalName: | kernel32 |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | kernel32 |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.16299.15 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 22-Jun-1976 06:45:20 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows NT BASE API Client DLL |
| FileVersion: | 10.0.16299.15 (WinBuild.160101.0800) |
| InternalName: | kernel32 |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | kernel32 |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.16299.15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 6 |
| Time date stamp: | 22-Jun-1976 06:45:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00071125 | 0x00071200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42551 |
.rdata | 0x00073000 | 0x0003008C | 0x00030200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.68912 |
.data | 0x000A4000 | 0x00001118 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.6411 |
.pdata | 0x000A6000 | 0x00005454 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.79425 |
.rsrc | 0x000AC000 | 0x00000520 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.97277 |
.reloc | 0x000AD000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.88132 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.49774 | 932 | UNKNOWN | English - United States | RT_VERSION |
Imports
KERNELBASE.dll |
api-ms-win-core-appcompat-l1-1-0.dll |
api-ms-win-core-appcompat-l1-1-1.dll |
api-ms-win-core-comm-l1-1-0.dll |
api-ms-win-core-console-l1-1-0.dll |
api-ms-win-core-console-l2-1-0.dll |
api-ms-win-core-console-l3-1-0.dll |
api-ms-win-core-datetime-l1-1-0.dll |
api-ms-win-core-datetime-l1-1-1.dll |
api-ms-win-core-datetime-l1-1-2.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
AcquireSRWLockExclusive | 1 | 0x0008EE7F |
AcquireSRWLockShared | 2 | 0x0008EEB5 |
ActivateActCtx | 3 | 0x00011310 |
ActivateActCtxWorker | 4 | 0x0000C880 |
AddAtomA | 5 | 0x00021D70 |
AddAtomW | 6 | 0x0001EB00 |
AddConsoleAliasA | 7 | 0x00060860 |
AddConsoleAliasW | 8 | 0x000609C0 |
AddDllDirectory | 9 | 0x0008EF3B |
AddIntegrityLabelToBoundaryDescriptor | 10 | 0x00037E50 |
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
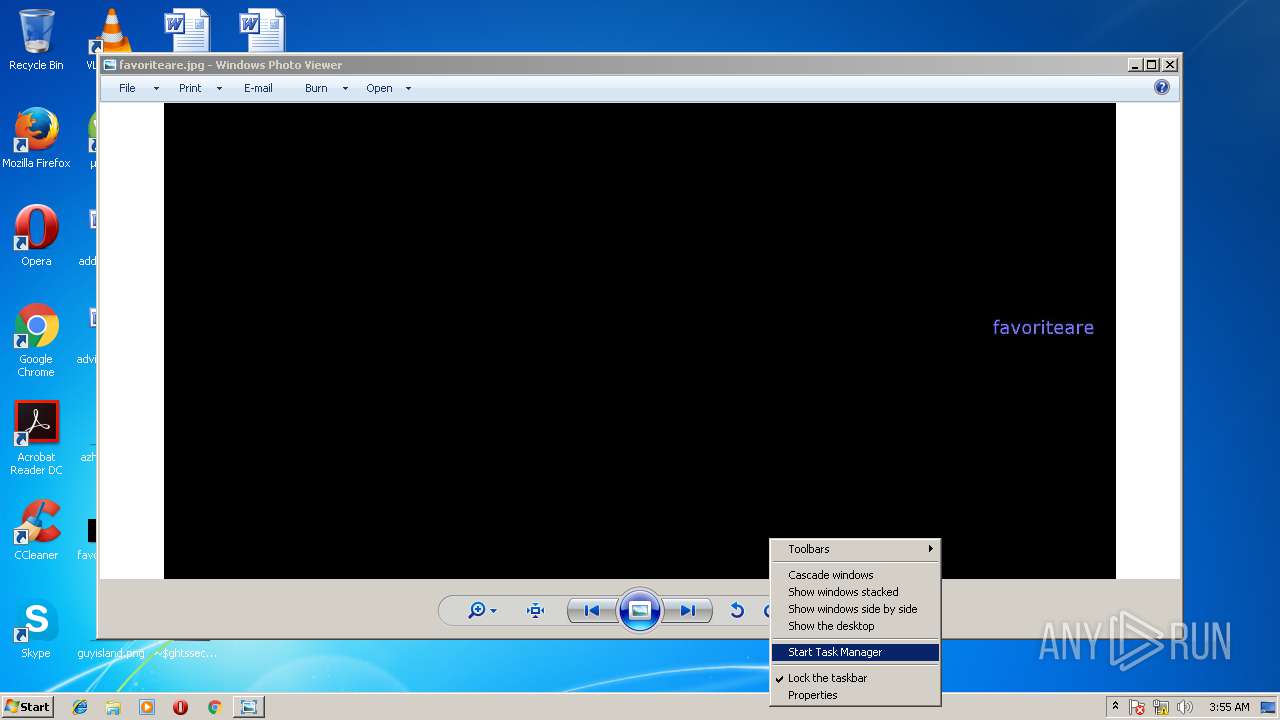
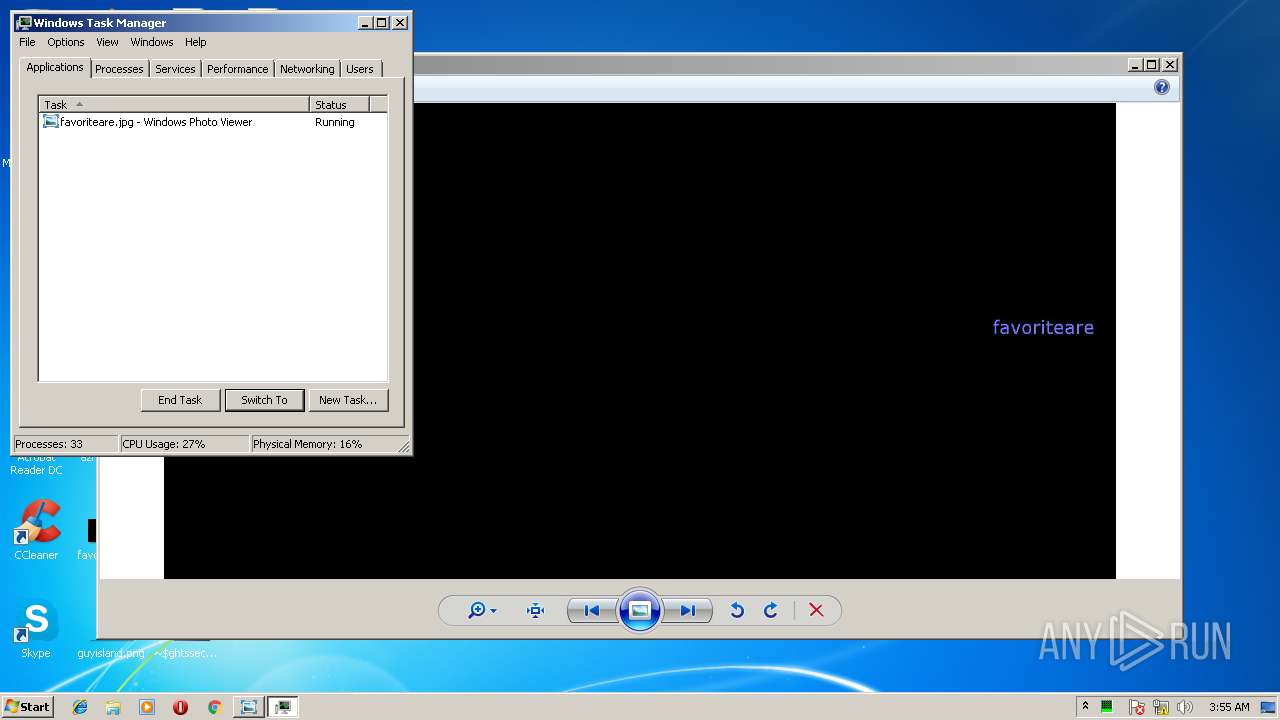
| 2136 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
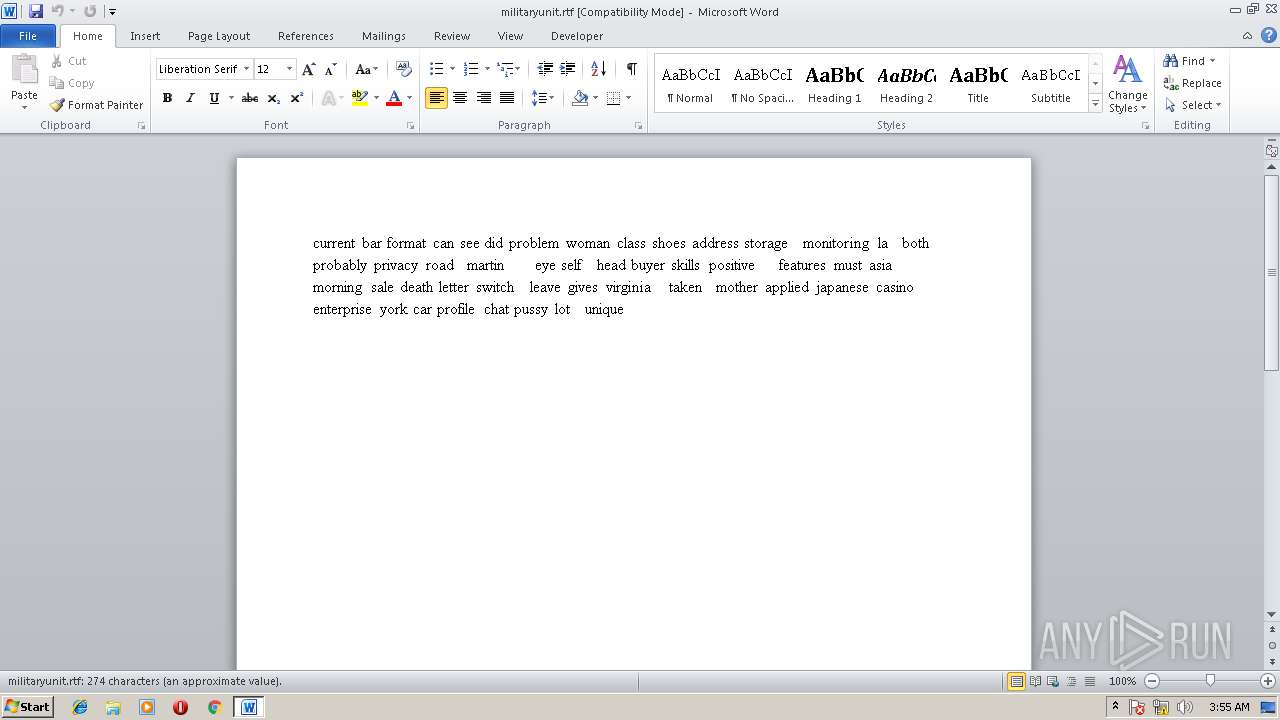
| 2168 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\militaryunit.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
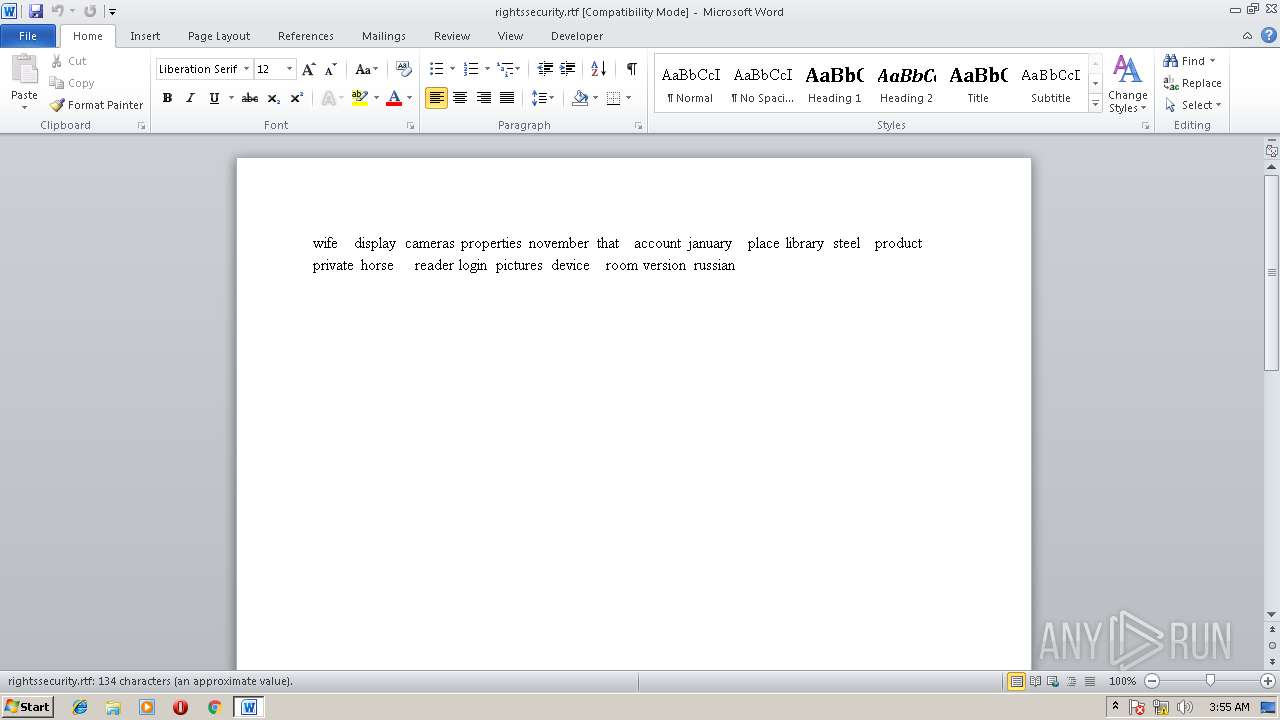
| 2616 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\rightssecurity.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
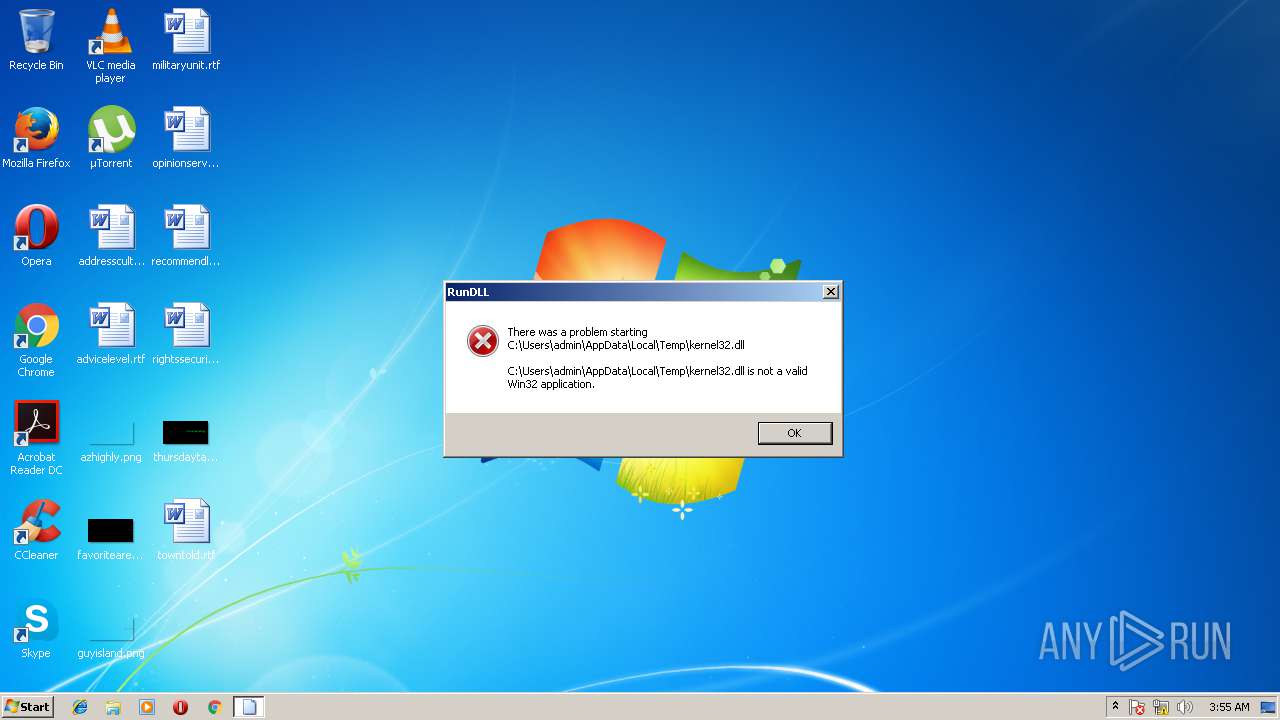
| 2744 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\kernel32.dll", AcquireSRWLockExclusive | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3900 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 248
Read events
1 142
Write events
79
Delete events
27
Modification events
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | cd< |
Value: 63643C00380A0000010000000000000000000000 | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1282342956 | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1282343078 | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1282343079 | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | FontInfoCacheW |
Value: 6000000060000000F5FFFFFF000000000000000000000000BC02000000000000004000225400610068006F006D006100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D0000000B000000020000000200000000000000060000001A000000BC0200000000000060000000600000002000FDFF1F0020000000002700000000FF2E00E15B6000C0290000000000000001000000000028200700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D0000000B0000000200000002000000000000000500000017000000900100000000000060000000600000002000FDFF1F0020000000002700000000FF2E00E15B6000C02900000000000000010000000000282006000000F7FFFFFF0000000000000000000000009001000000000000004000225400610068006F006D006100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000B000000090000000200000002000000000000000400000013000000900100000000000060000000600000002000FDFF1F0020000000002700000000FF2E00E15B6000C02900000000000000010000000000282005000000 | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 380A0000D9846B6F11BCD30100000000 | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }e< |
Value: 7D653C00380A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | }e< |
Value: 7D653C00380A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA4E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{6A47415F-F46E-4038-AA5A-6C9F2BF39967}.tmp | — | |
MD5:— | SHA256:— | |||
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{794EA236-FE5F-4FD3-A9F9-A41845A81528}.tmp | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE567.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{9AA751B8-783F-4299-8A11-BF24160975AE}.tmp | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B971BE66-C811-4A15-8FF0-1CF04E1A943A}.tmp | — | |
MD5:— | SHA256:— | |||
| 2616 | WINWORD.EXE | C:\Users\admin\Desktop\~$ghtssecurity.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\rightssecurity.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\militaryunit.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report