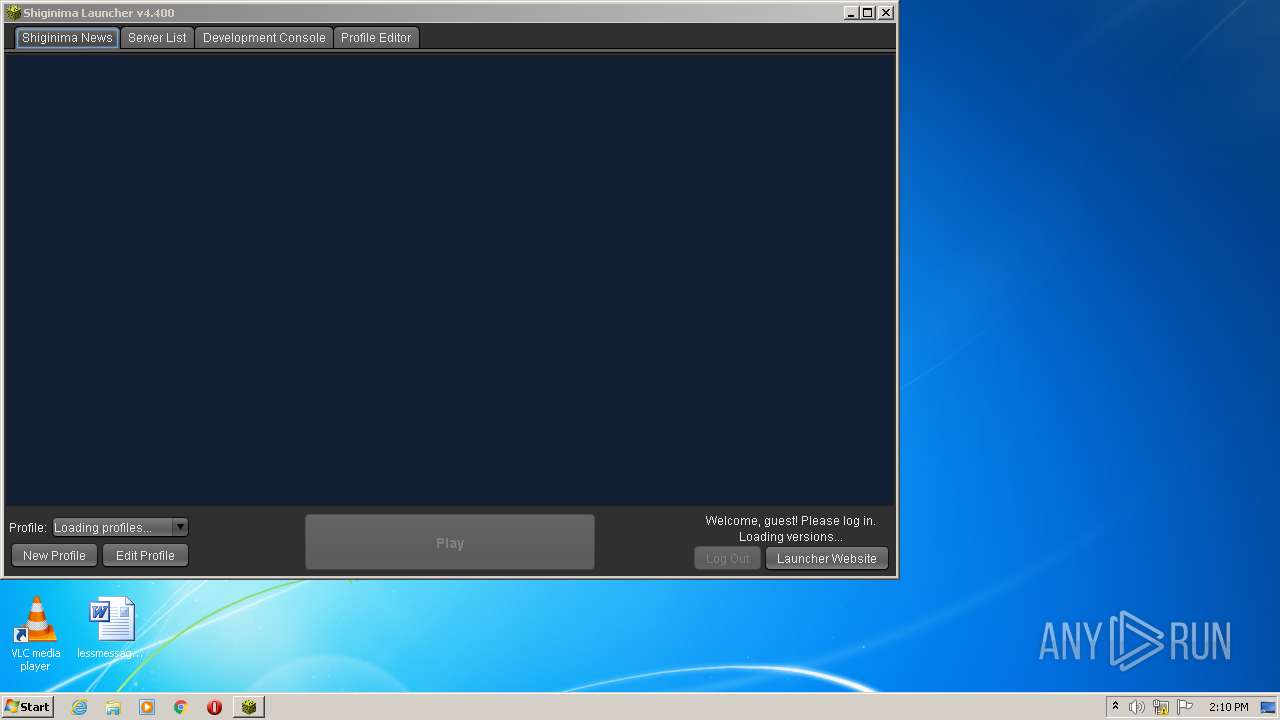
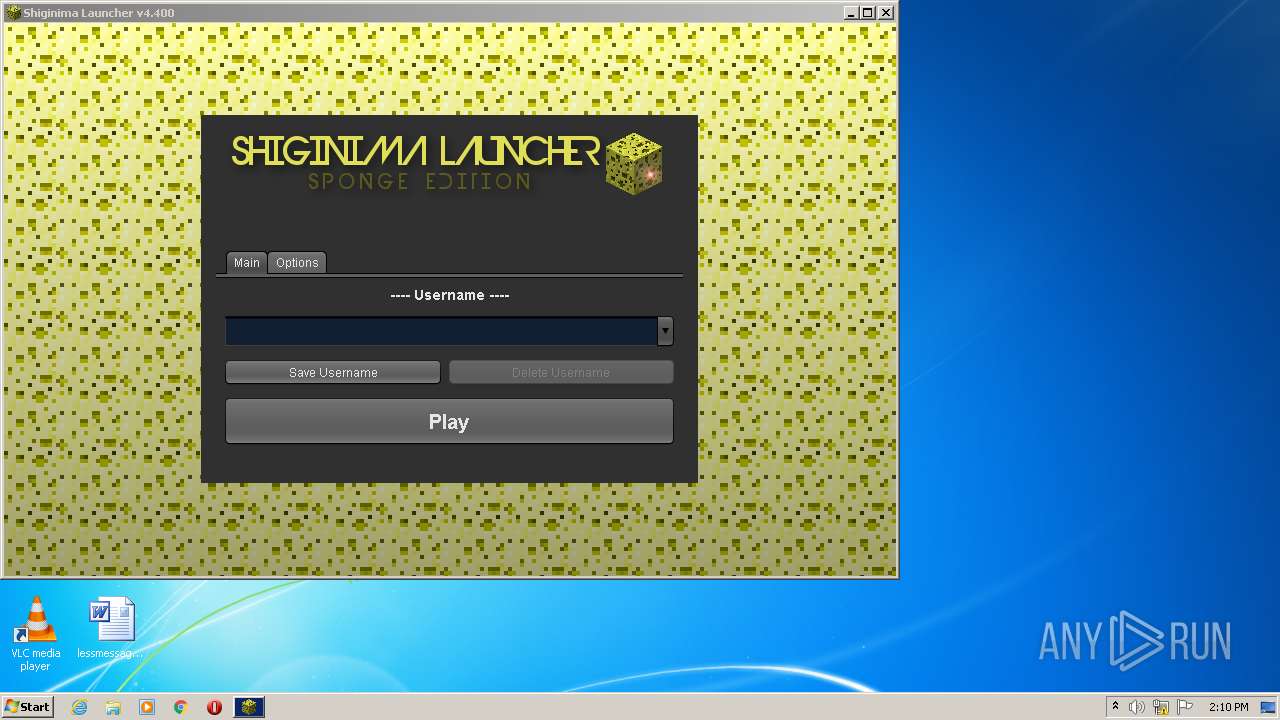
| File name: | shiginima-launcher-se-v4400.exe |
| Full analysis: | https://app.any.run/tasks/8e8f4a81-e1b7-4e4b-8e07-be68c8af8107 |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2022, 14:09:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | C3DB052DA531710367FAF5E011475715 |
| SHA1: | 46F599E4E1ECE582006739DEBE0A522925A9CD13 |
| SHA256: | 7C6220B046553F9C95B8098FF83BFC6B7828093650BECBC1B44E3D7819D7EFD1 |
| SSDEEP: | 98304:qpTJ89MMbcZsgsDlilods/txVGHTJKsTnEFnAzvDfBzXEYNsJ5Ono:aTm9MMbcFililB0HdRTnEFnAzlEQsJ5H |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes JAVA applets
- shiginima-launcher-se-v4400.exe (PID: 712)
Checks supported languages
- shiginima-launcher-se-v4400.exe (PID: 712)
- javaw.exe (PID: 148)
Check for Java to be installed
- shiginima-launcher-se-v4400.exe (PID: 712)
Creates files in the program directory
- javaw.exe (PID: 148)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 148)
Reads the computer name
- javaw.exe (PID: 148)
Creates files in the user directory
- javaw.exe (PID: 148)
INFO
Reads the computer name
- icacls.exe (PID: 3368)
Checks supported languages
- icacls.exe (PID: 3368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
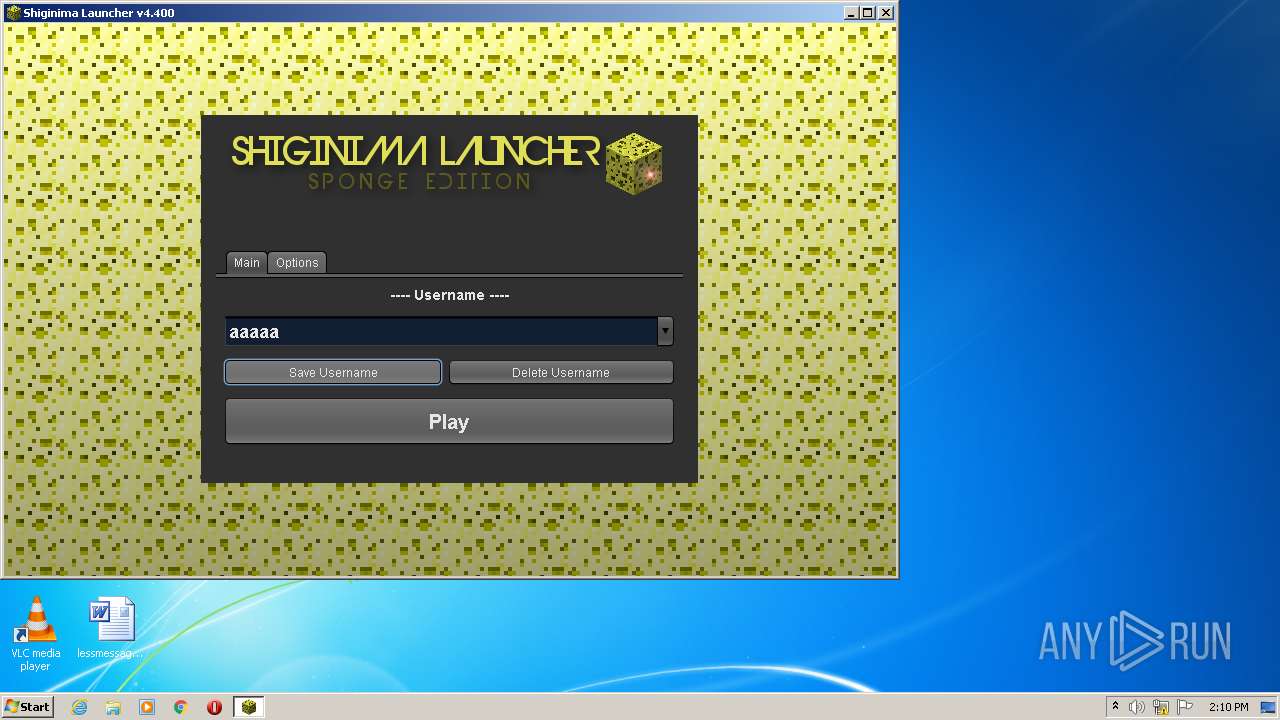
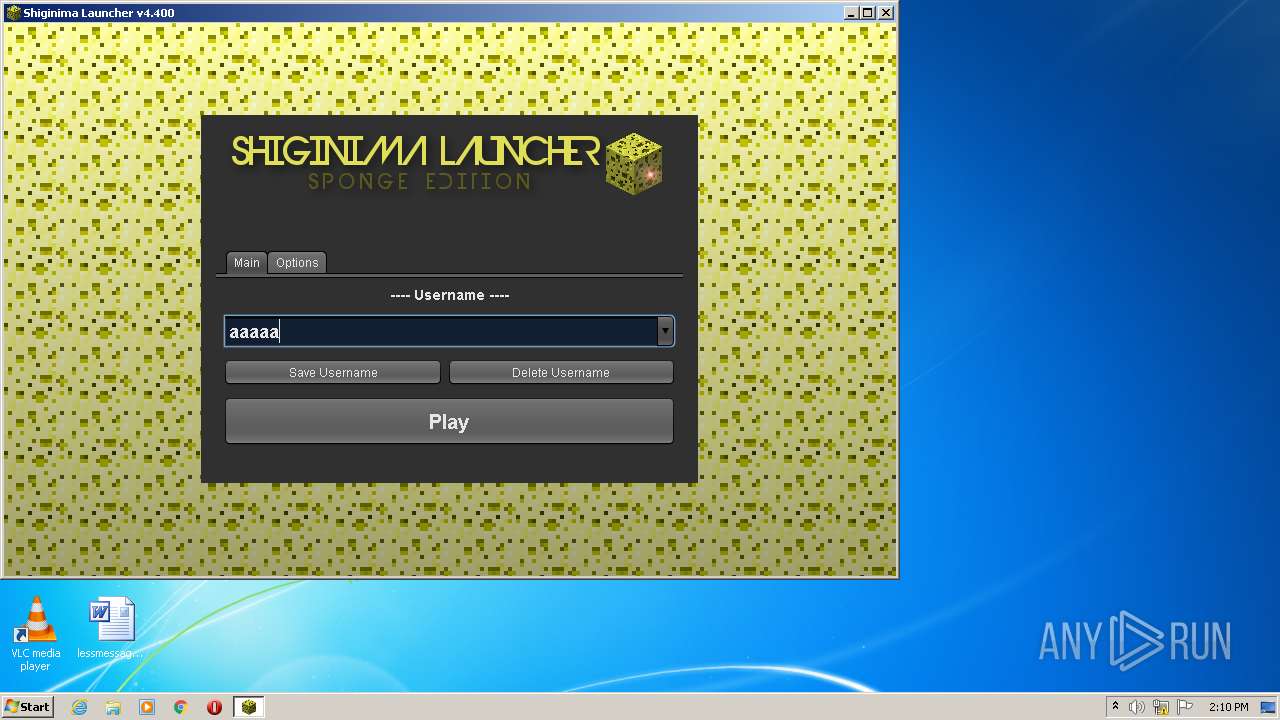
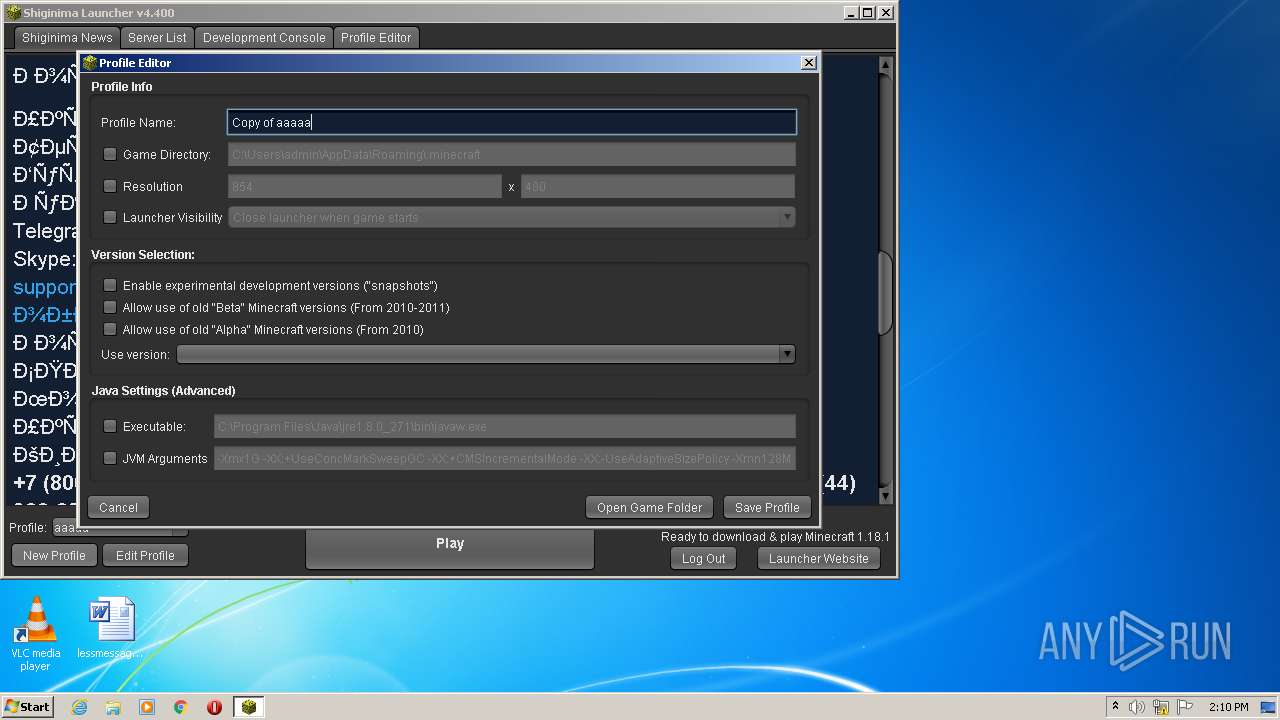
| ProductVersion: | Shiginima Launcher SE v4.400 |
|---|---|
| ProductName: | Shiginima Launcher SE v4.300 |
| OriginalFileName: | Shiginima Launcher SE v4.400.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Shiginima, Mojang |
| InternalName: | Shiginima Salad |
| FileVersion: | 4.4 |
| FileDescription: | Shiginima Launcher SE v4.400 |
| CompanyName: | Shiginima |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 4.4.0.0 |
| FileVersionNumber: | 4.4.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1290 |
| UninitializedDataSize: | 36864 |
| InitializedDataSize: | 23040 |
| CodeSize: | 19968 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2020:02:01 01:14:31+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2020 00:14:31 |
| Detected languages: |
|
| CompanyName: | Shiginima |
| FileDescription: | Shiginima Launcher SE v4.400 |
| FileVersion: | 4.400 |
| InternalName: | Shiginima Salad |
| LegalCopyright: | Shiginima, Mojang |
| LegalTrademarks: | - |
| OriginalFilename: | Shiginima Launcher SE v4.400.exe |
| ProductName: | Shiginima Launcher SE v4.300 |
| ProductVersion: | Shiginima Launcher SE v4.400 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Feb-2020 00:14:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004CE0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03278 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000680 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x000043D4 | 0x00004400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.85731 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30486 | 892 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 5.74619 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
11 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
15 | 3.17512 | 17 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 3.91327 | 25 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
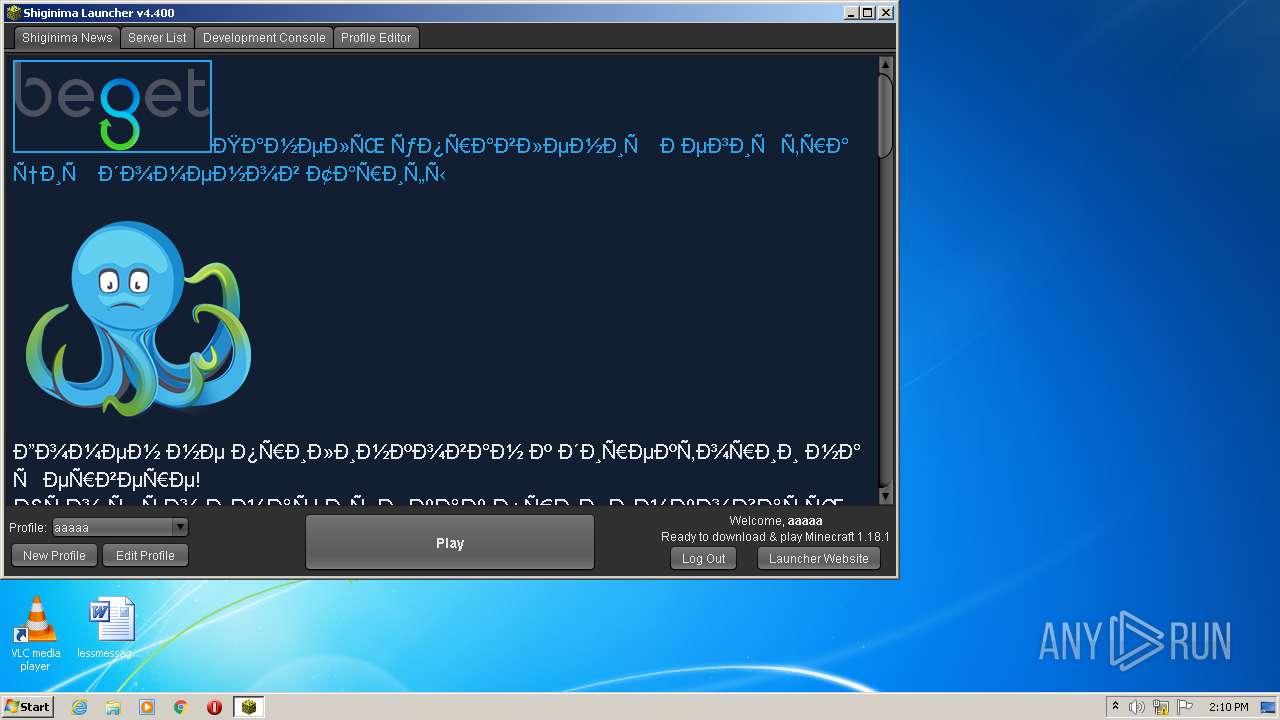
| 148 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -classpath "C:\Users\admin\Downloads\shiginima-launcher-se-v4400.exe" net.mc.main.Main | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | shiginima-launcher-se-v4400.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 712 | "C:\Users\admin\Downloads\shiginima-launcher-se-v4400.exe" | C:\Users\admin\Downloads\shiginima-launcher-se-v4400.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Shiginima Integrity Level: MEDIUM Description: Shiginima Launcher SE v4.400 Exit code: 0 Version: 4.400 Modules
| |||||||||||||||
| 3368 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
745
Read events
744
Write events
1
Delete events
0
Modification events
| (PID) Process: | (148) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 148 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 148 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | text | |
MD5:— | SHA256:— | |||
| 148 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2391575837343433531.tmp | image | |
MD5:ECCE36EEF6A0792DFAE8A539F4ADE63D | SHA256:5EA73AC7D95F47B036D8FD70E60994FA33C19BA43FCC6A491F96292E05B01331 | |||
| 148 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5714703495899534750.tmp | image | |
MD5:B8A61355127D82D931BC39EFB10FB9B6 | SHA256:8A3DA25EC37F06992149890C67D1868D05D1DB8DC693B99FECF19FC94807C828 | |||
| 148 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8255989050419372839.tmp | image | |
MD5:D2FC27C31904067D5E9C765700CD5292 | SHA256:3E46FF5095EB7E0E7DDB78AD26D673D0F791A89D8741346F44EC706AE94CAE9F | |||
| 148 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio6577702269064823687.tmp | image | |
MD5:D2FC27C31904067D5E9C765700CD5292 | SHA256:3E46FF5095EB7E0E7DDB78AD26D673D0F791A89D8741346F44EC706AE94CAE9F | |||
| 148 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\shig.inima | text | |
MD5:571CC0288E3F5DB4C85AE85DCD1C64CE | SHA256:36ED29282E1D008064F2C06952EDDABDF7C73B58E2BC5215A497AC4541BE6553 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
16
DNS requests
9
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
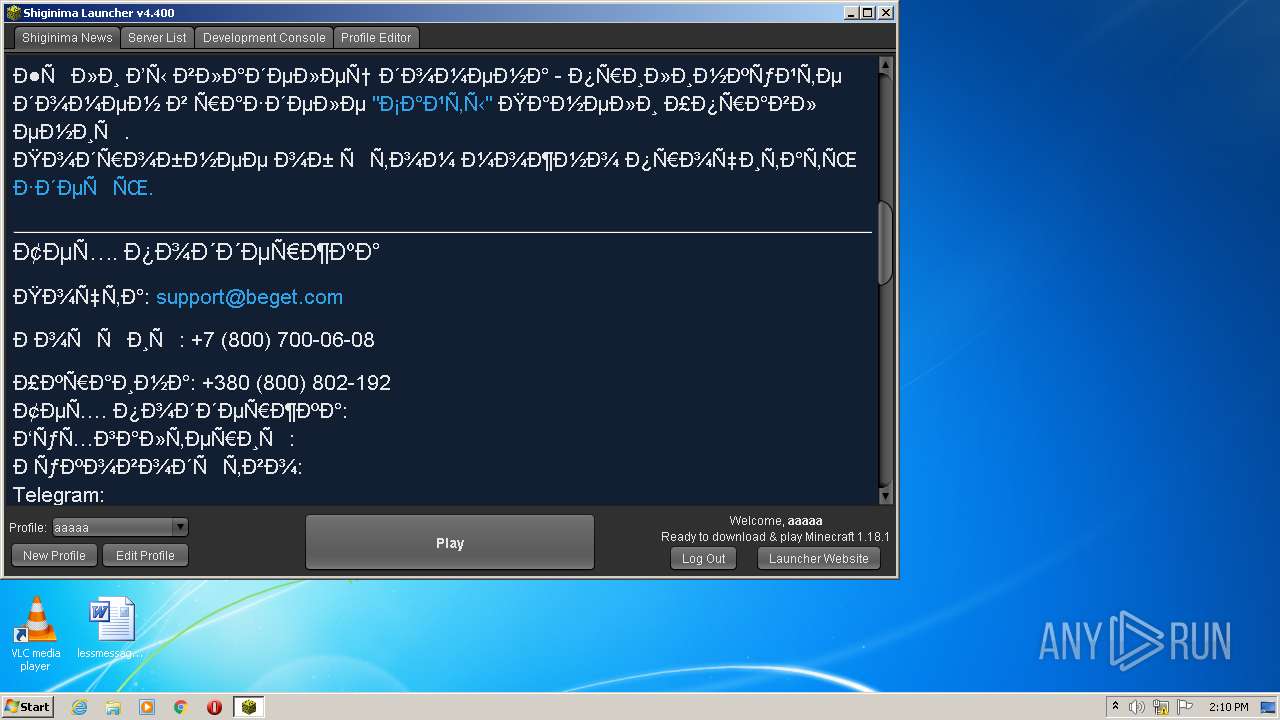
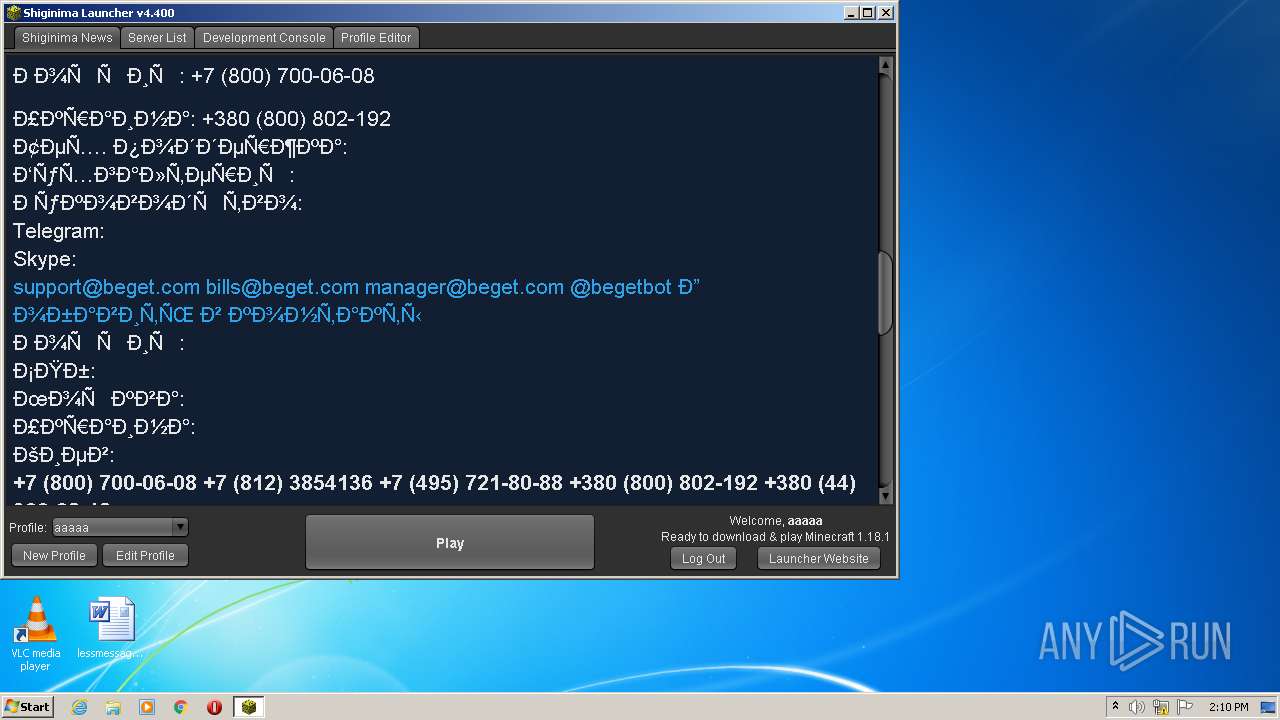
148 | javaw.exe | GET | 200 | 87.236.16.22:80 | http://servers.teamshiginima.com/ | RU | html | 35.1 Kb | malicious |
148 | javaw.exe | GET | 200 | 87.236.16.22:80 | http://news.teamshiginima.com/ | RU | html | 35.1 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
148 | javaw.exe | 87.236.16.22:80 | teamshiginima.com | Beget Ltd | RU | malicious |
— | — | 87.236.16.22:80 | teamshiginima.com | Beget Ltd | RU | malicious |
148 | javaw.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
148 | javaw.exe | 18.66.247.17:443 | launchermeta.mojang.com | Massachusetts Institute of Technology | US | unknown |
148 | javaw.exe | 216.58.214.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 188.114.97.7:443 | use.fontawesome.com | Cloudflare Inc | US | malicious |
148 | javaw.exe | 188.114.97.7:443 | use.fontawesome.com | Cloudflare Inc | US | malicious |
148 | javaw.exe | 5.101.158.81:443 | cp.beget.com | Beget Ltd | RU | suspicious |
— | — | 5.101.158.81:443 | cp.beget.com | Beget Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teamshiginima.com |
| whitelisted |
shigmeahyea.us.to |
| suspicious |
servers.teamshiginima.com |
| malicious |
news.teamshiginima.com |
| malicious |
launchermeta.mojang.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
cp.beget.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
148 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
148 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |