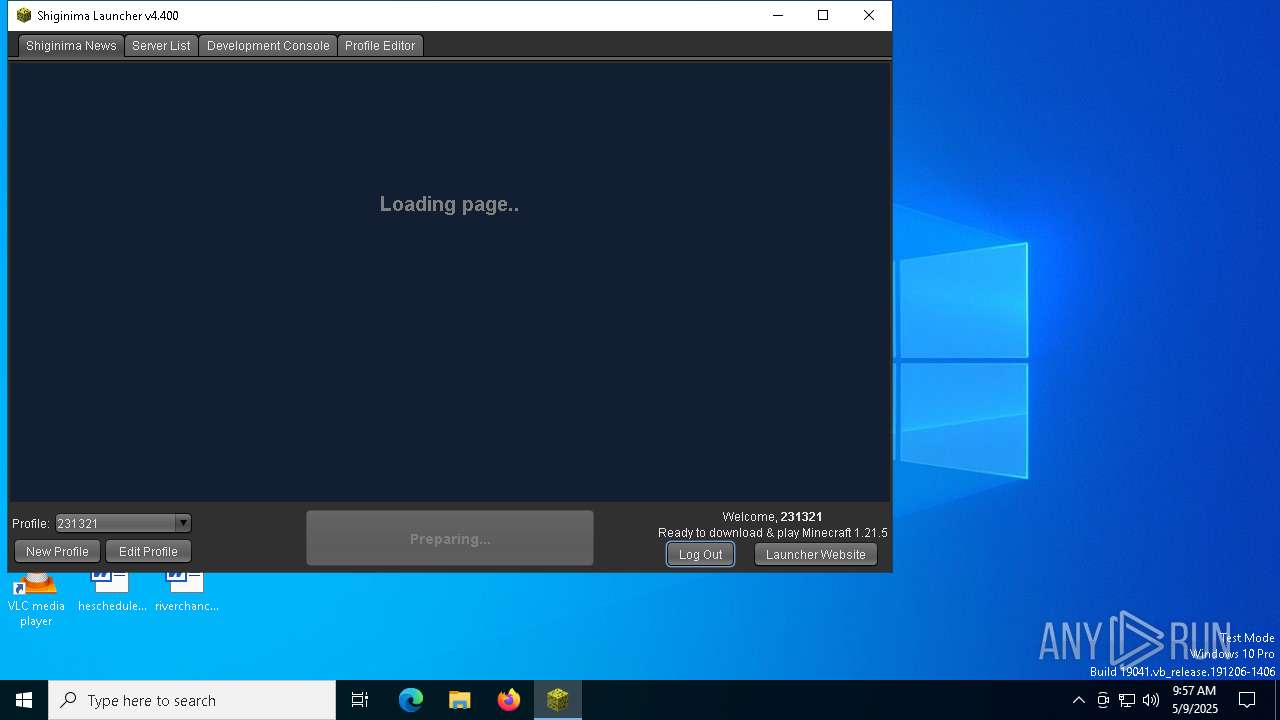
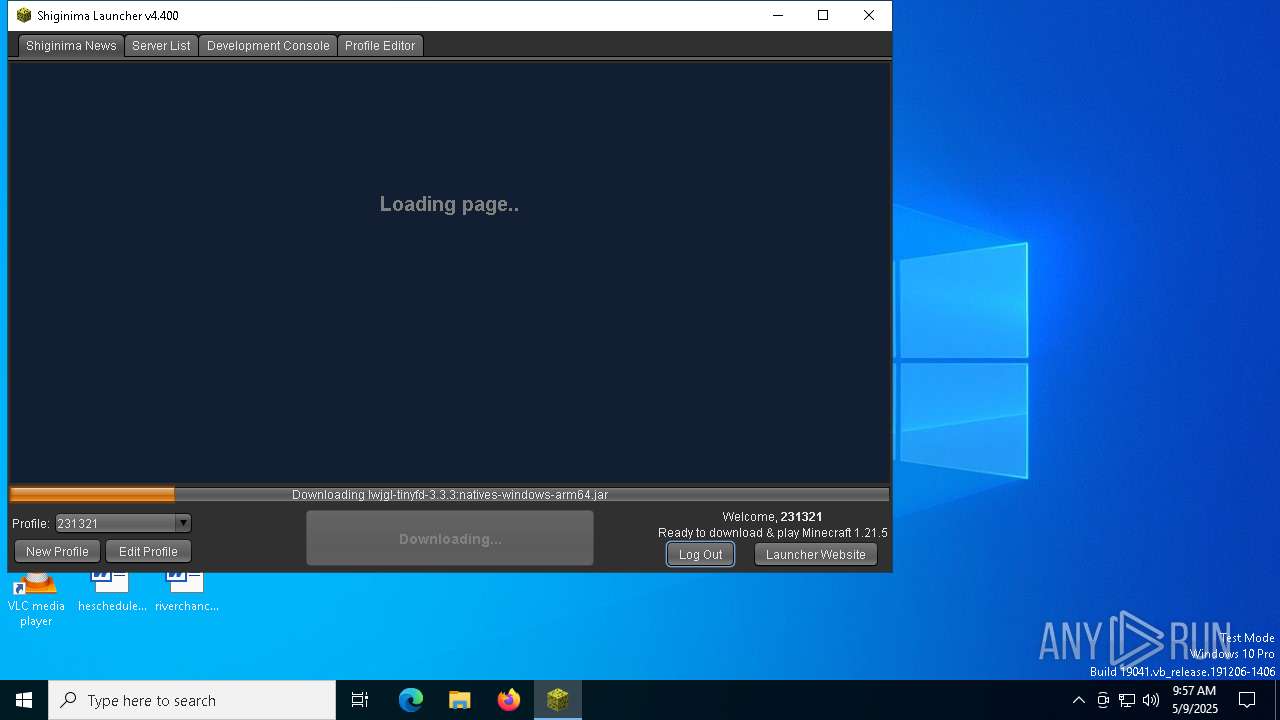
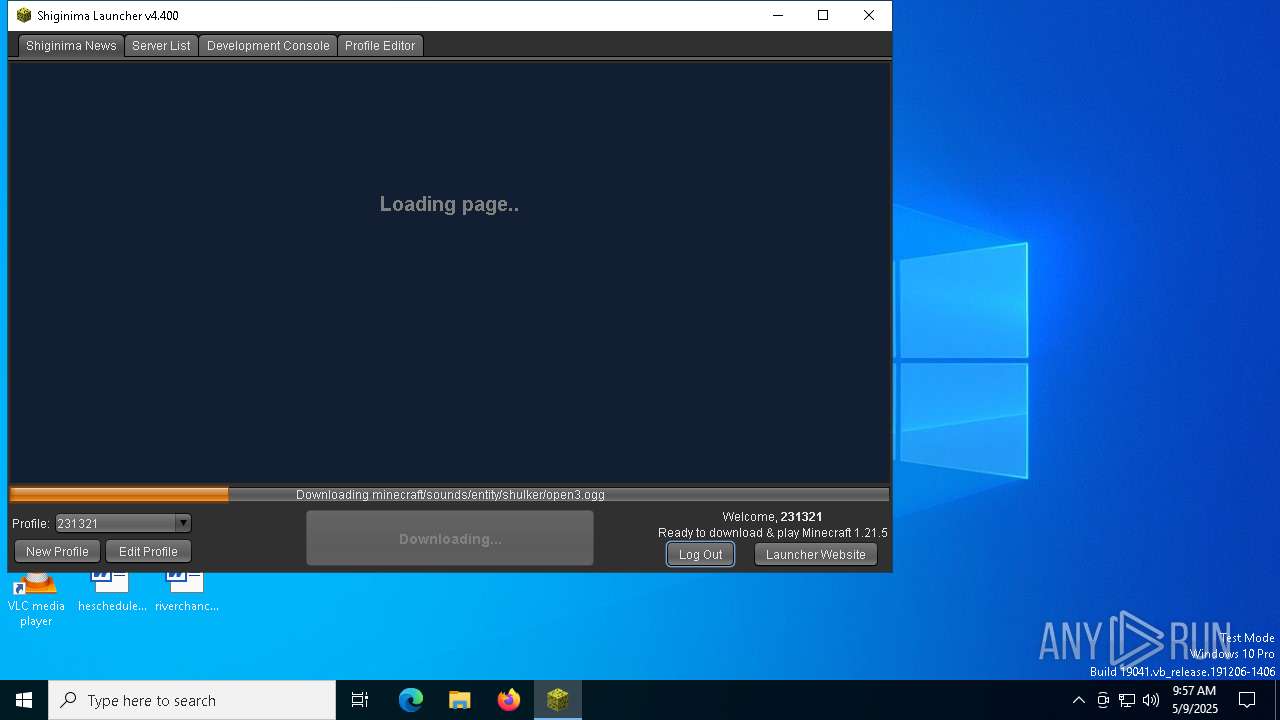
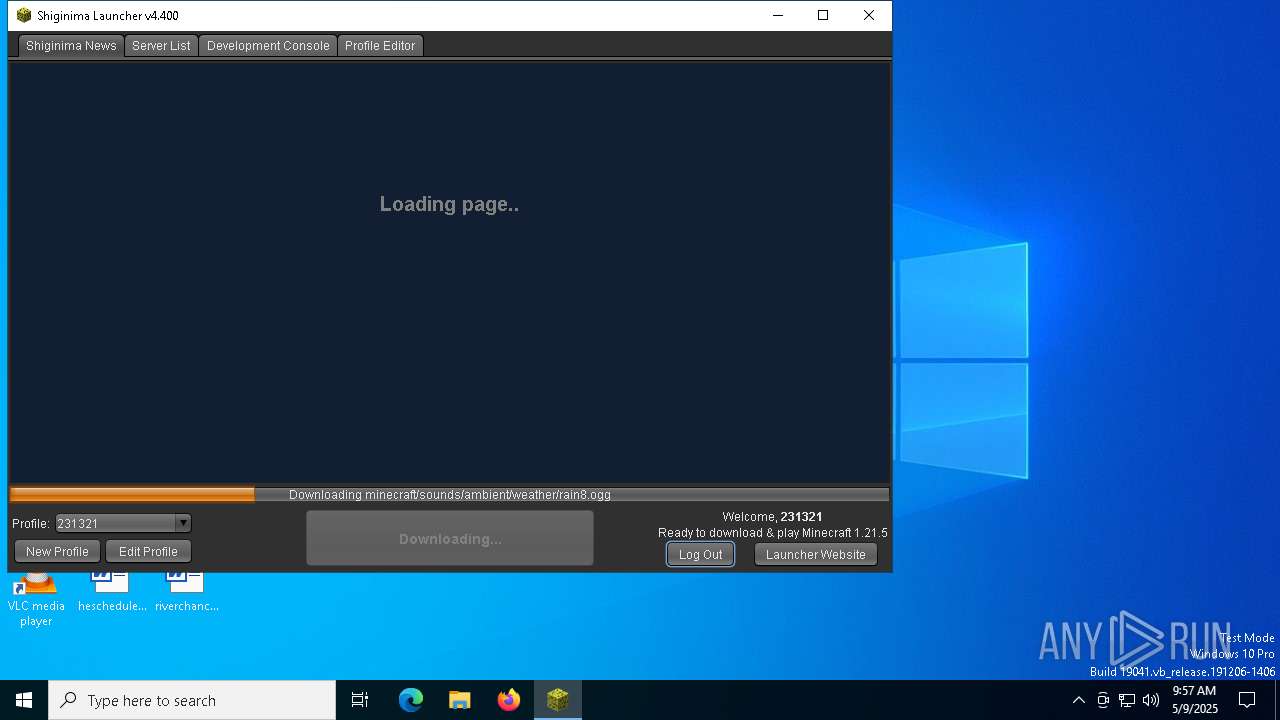
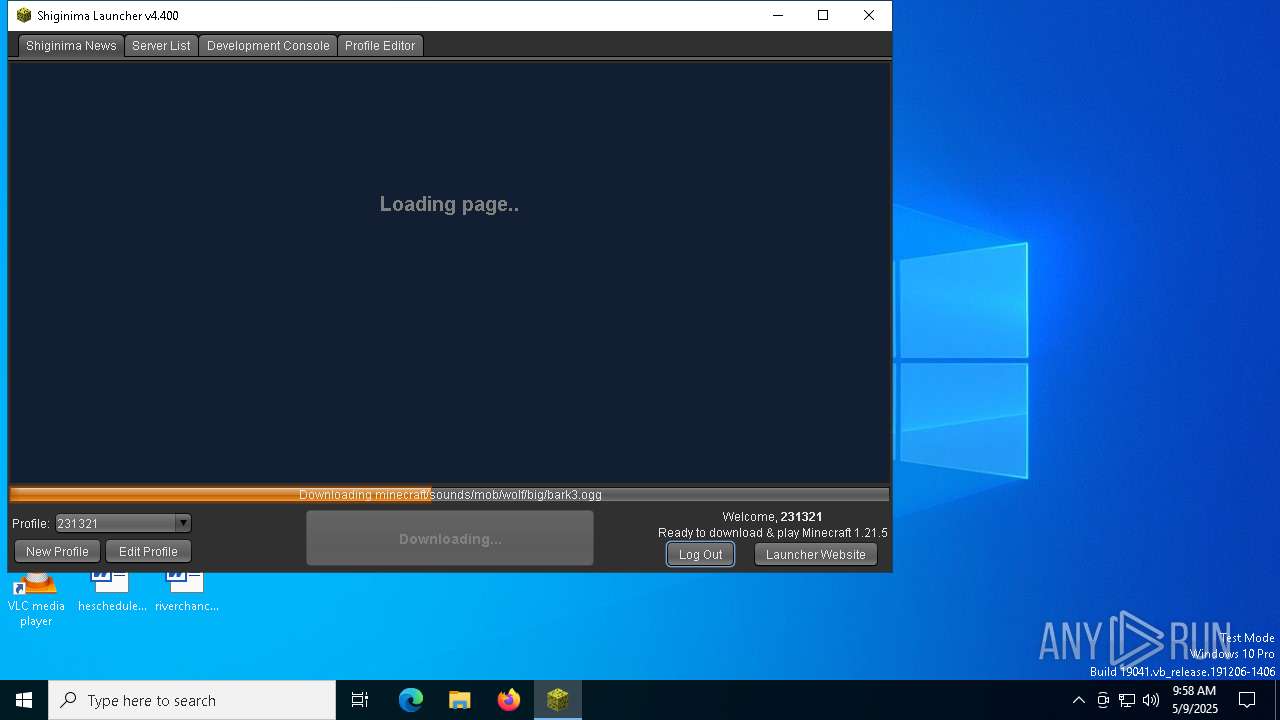
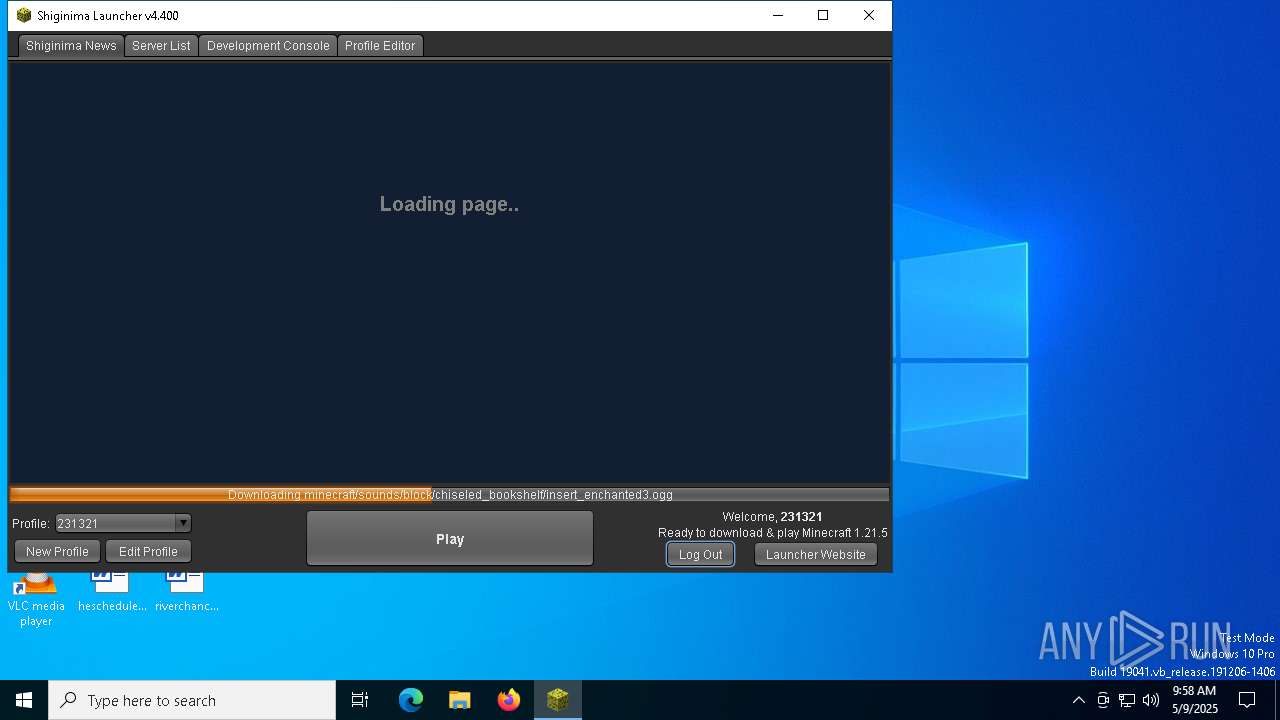
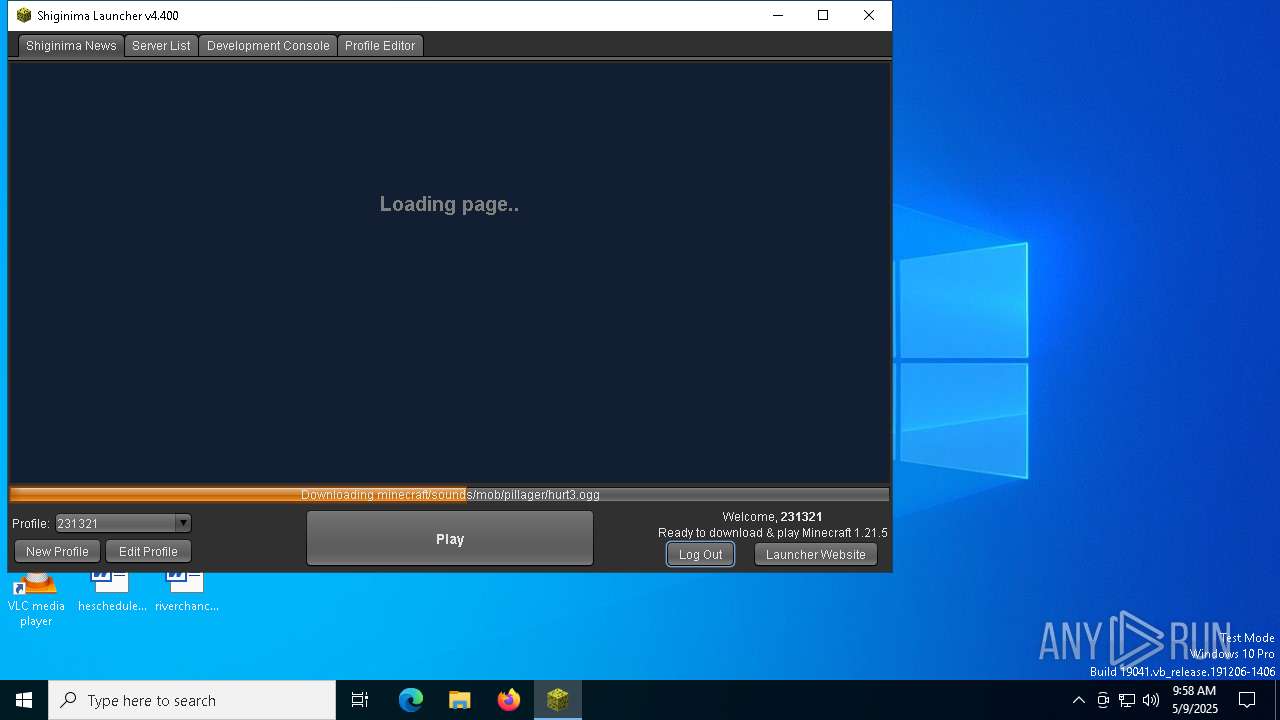
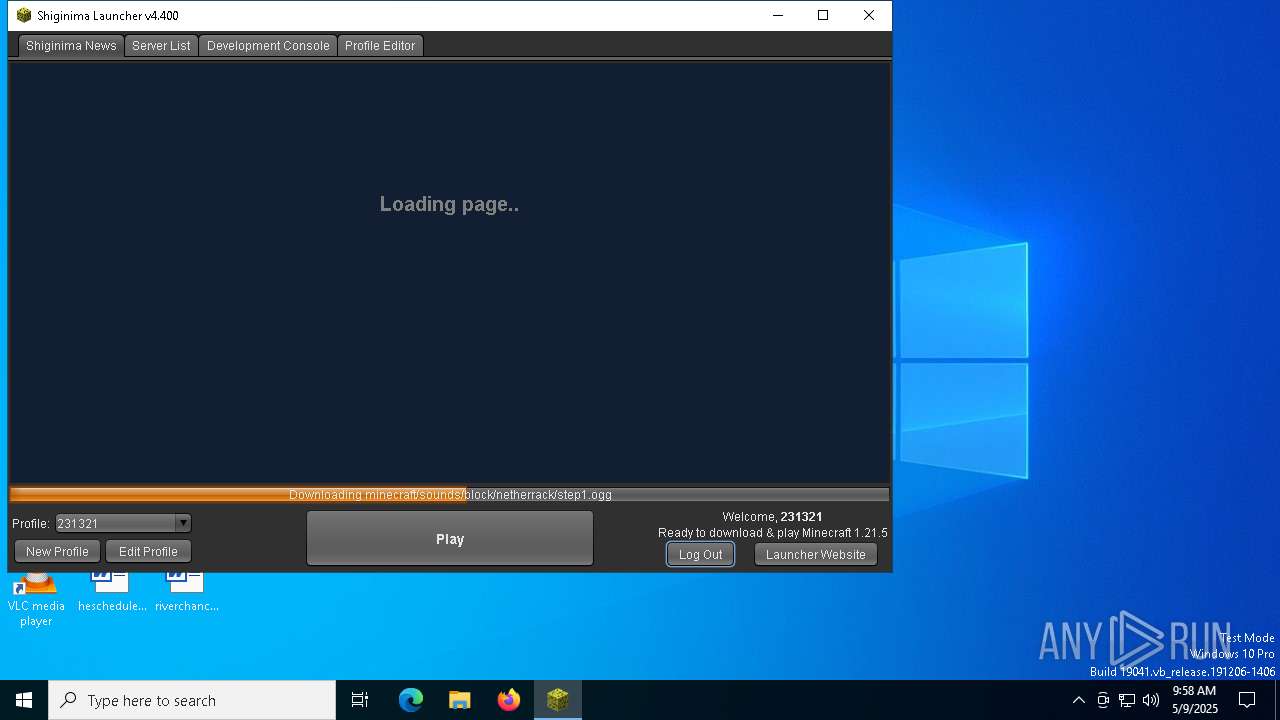
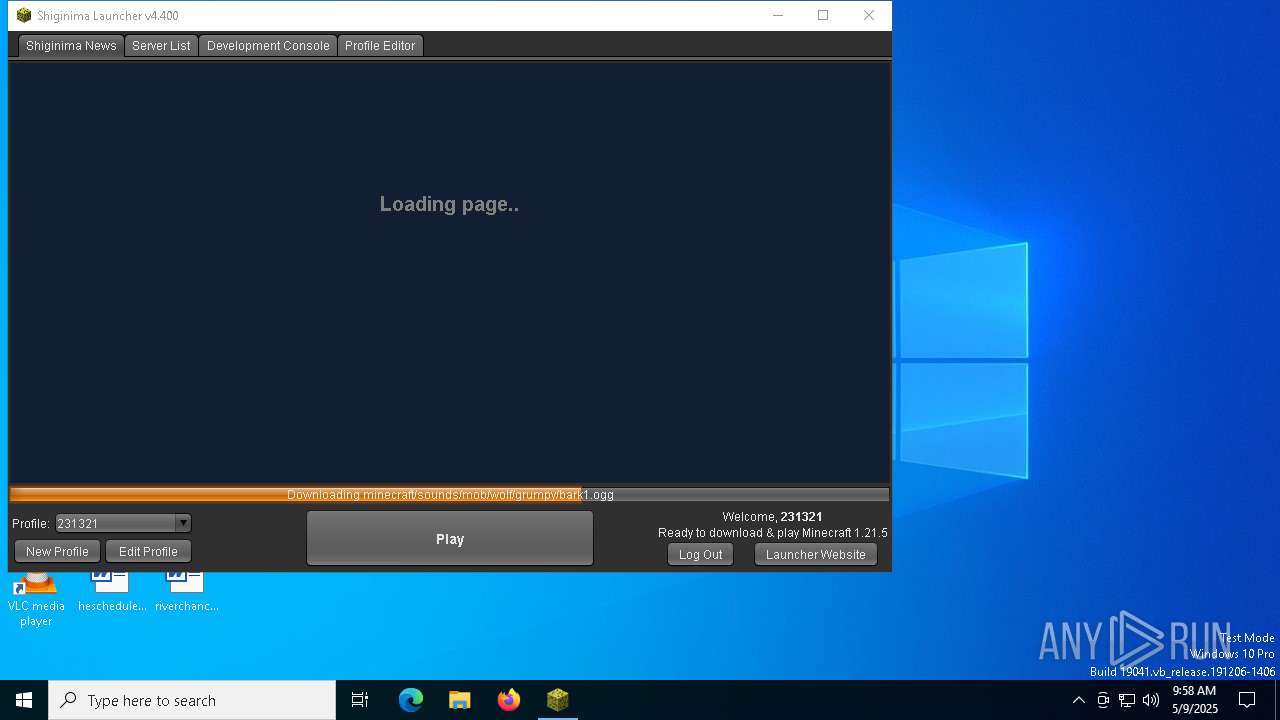
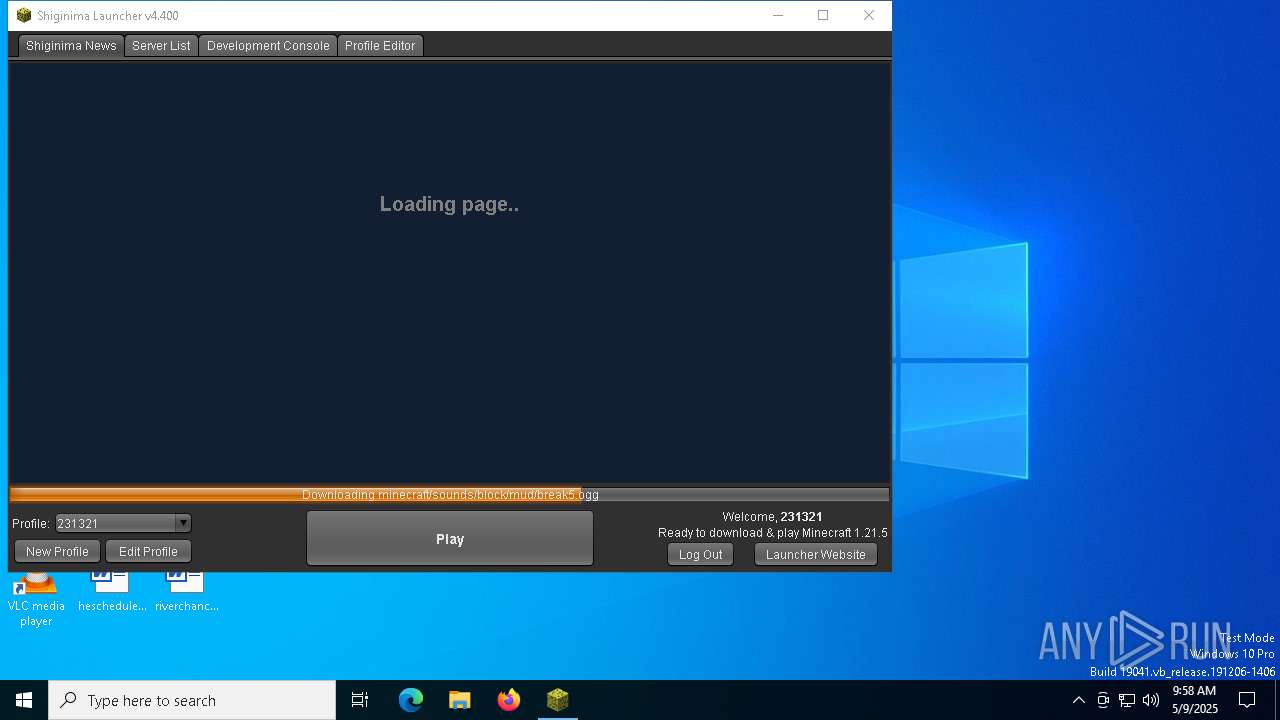
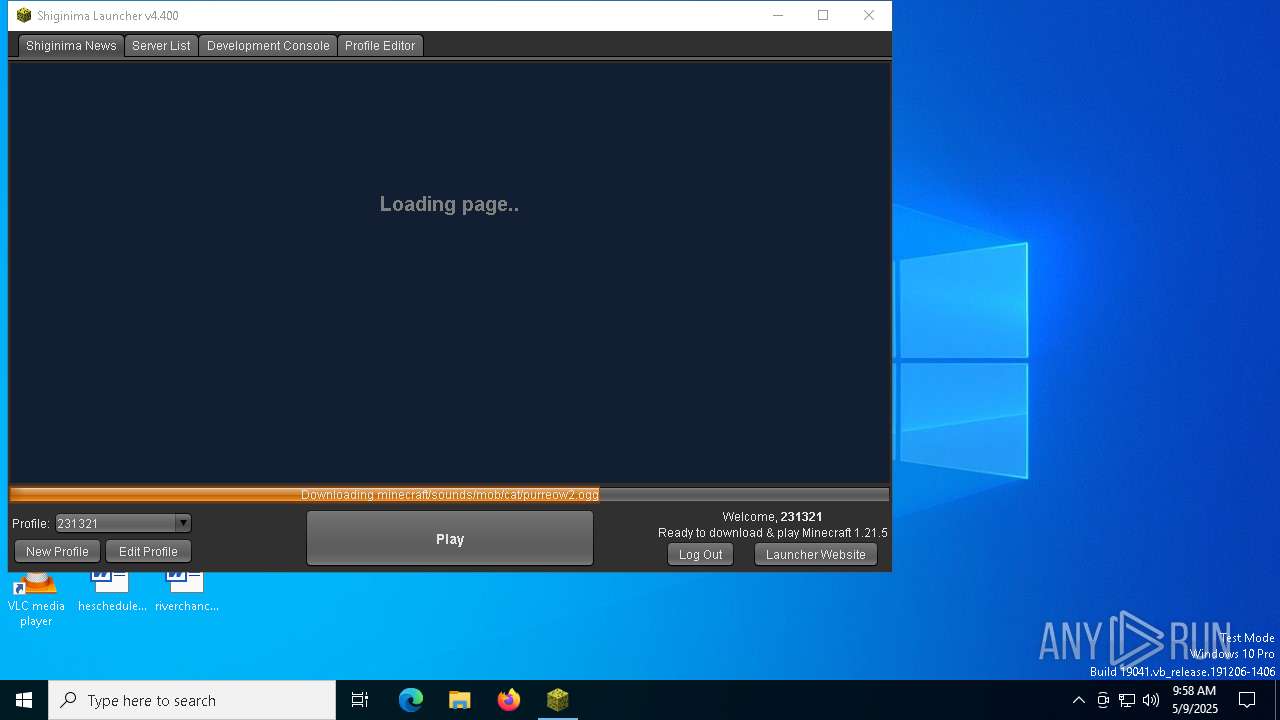
| File name: | Shiginima Launcher SE v4400.exe |
| Full analysis: | https://app.any.run/tasks/7ae2900d-3965-4741-a6f8-5269bf2b6d31 |
| Verdict: | Malicious activity |
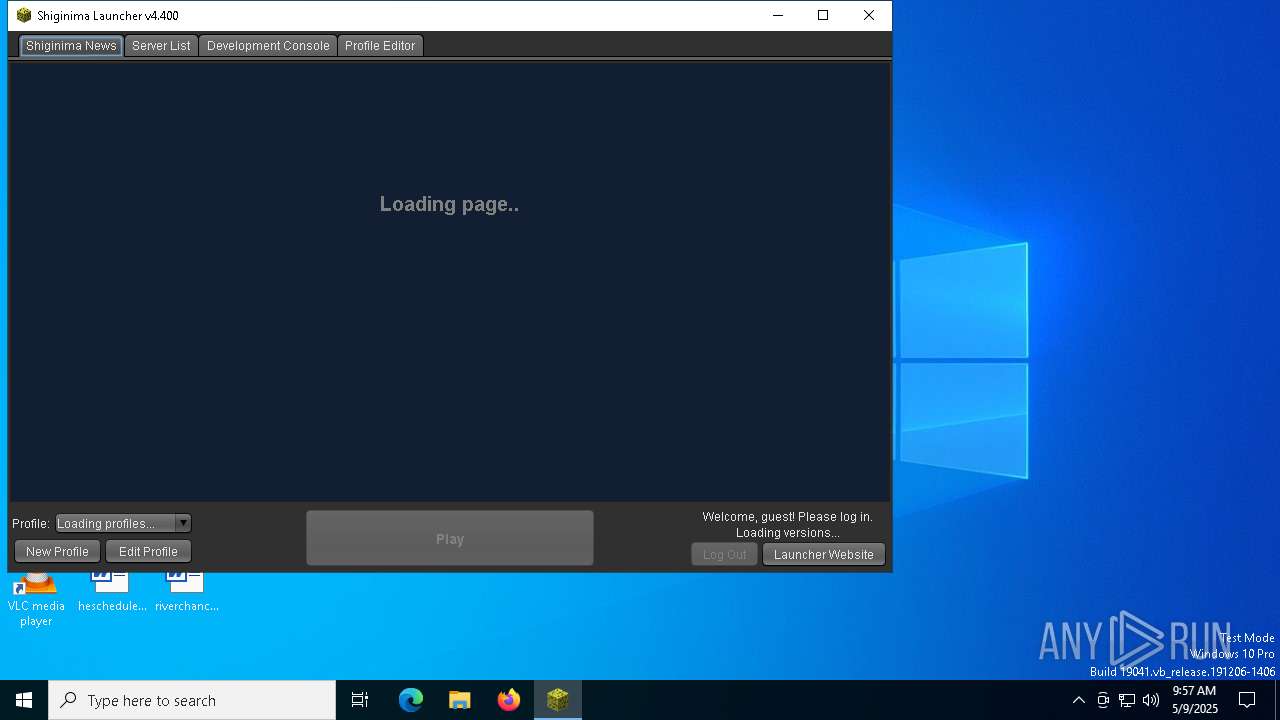
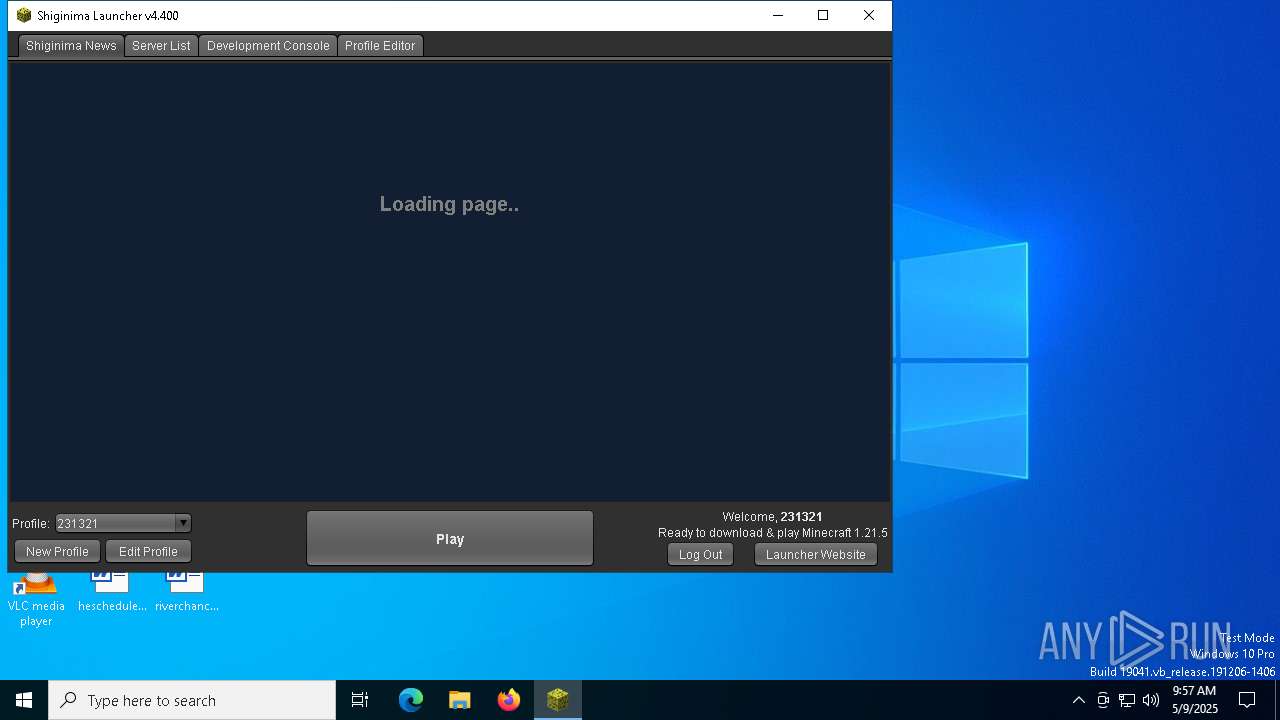
| Analysis date: | May 09, 2025, 09:57:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive, with extra data prepended |
| MD5: | C3DB052DA531710367FAF5E011475715 |
| SHA1: | 46F599E4E1ECE582006739DEBE0A522925A9CD13 |
| SHA256: | 7C6220B046553F9C95B8098FF83BFC6B7828093650BECBC1B44E3D7819D7EFD1 |
| SSDEEP: | 98304:+5uOC8VJzxZUhyU48rlEu1qq7eq3fI2odeXyQrtr3B+nTxUU22jlko089H8DykSB:SS+cCmPxNyb |
MALICIOUS
No malicious indicators.SUSPICIOUS
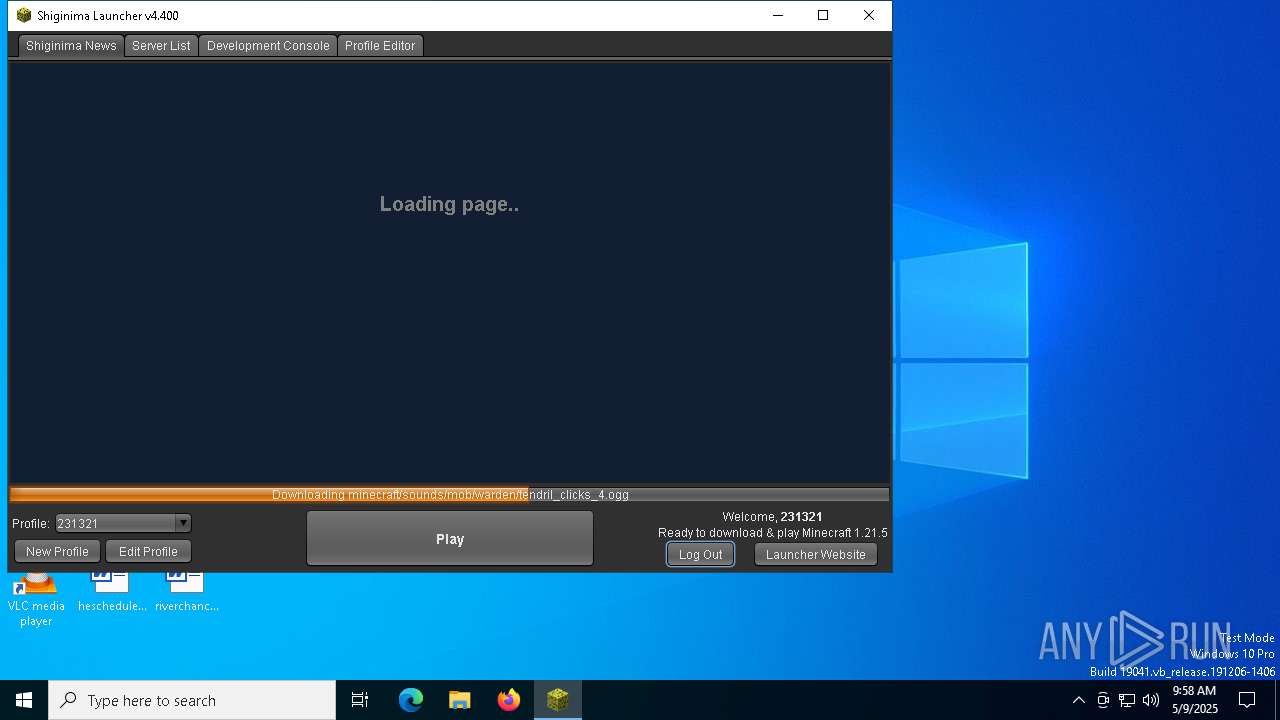
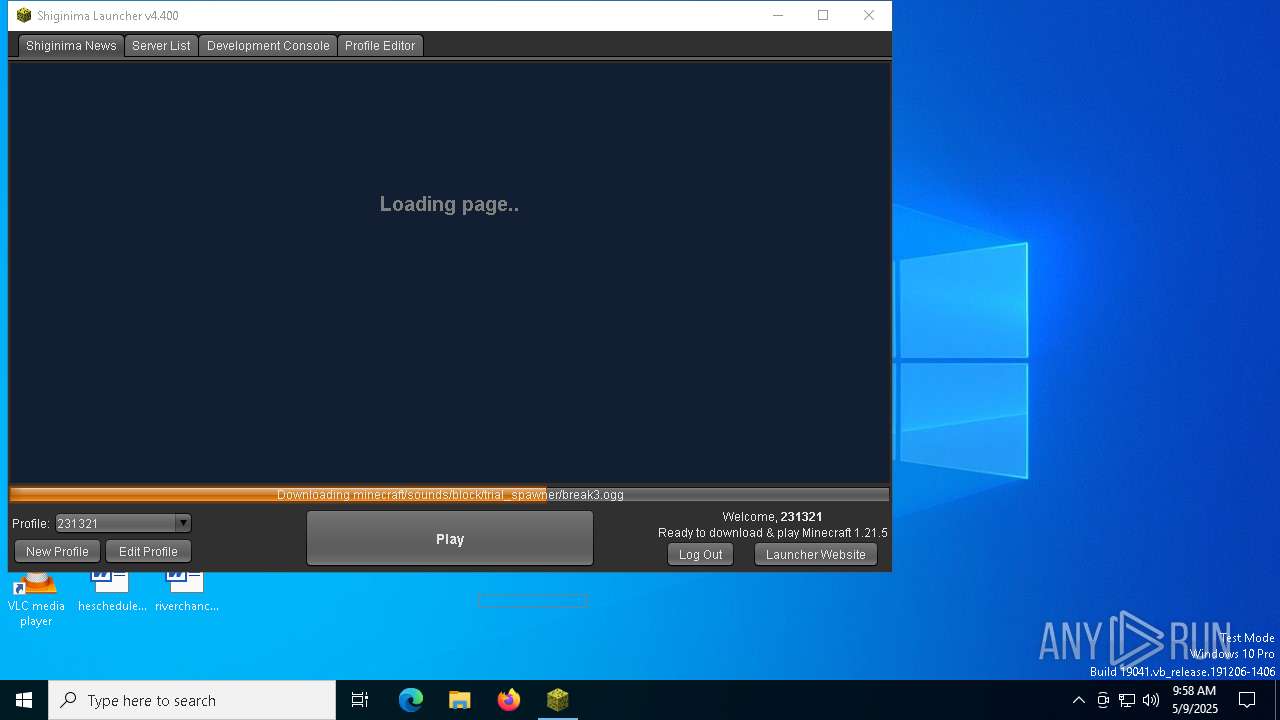
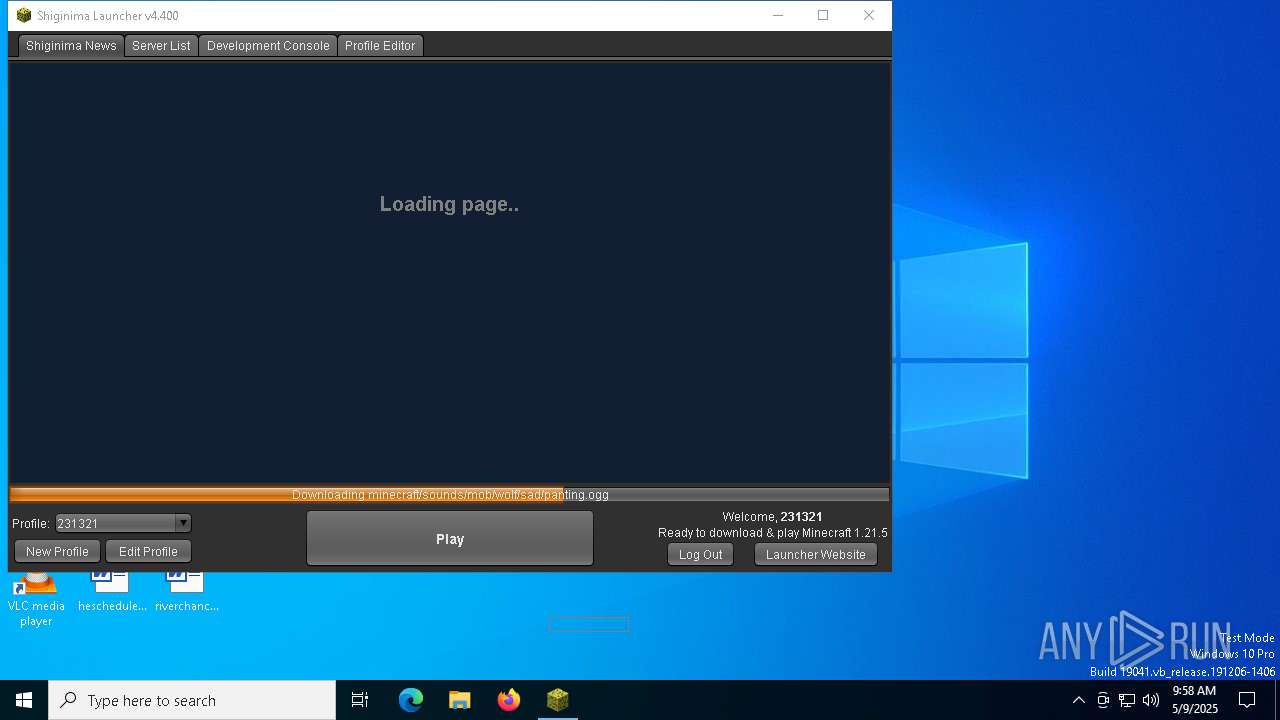
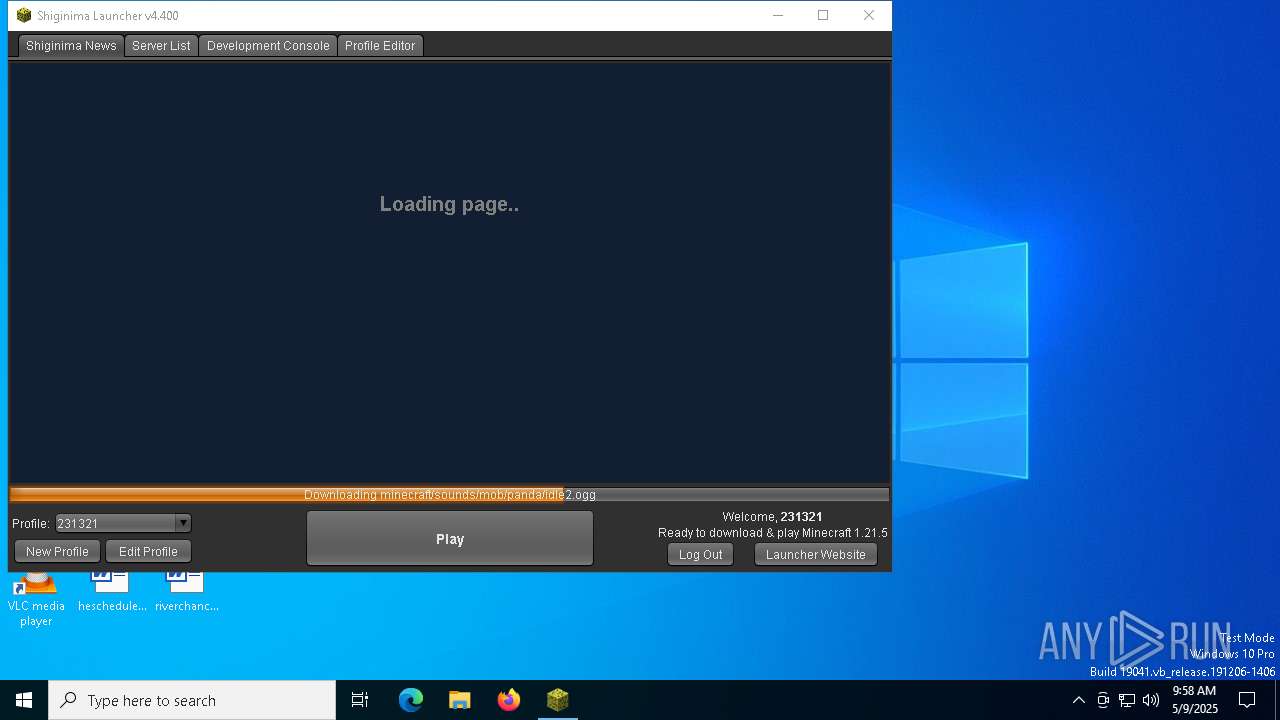
There is functionality for taking screenshot (YARA)
- javaw.exe (PID: 7288)
Checks for Java to be installed
- Shiginima Launcher SE v4400.exe (PID: 7272)
INFO
The sample compiled with english language support
- Shiginima Launcher SE v4400.exe (PID: 7272)
Create files in a temporary directory
- javaw.exe (PID: 7288)
Checks supported languages
- javaw.exe (PID: 7288)
- Shiginima Launcher SE v4400.exe (PID: 7272)
Creates files in the program directory
- javaw.exe (PID: 7288)
Reads the computer name
- javaw.exe (PID: 7288)
Creates files or folders in the user directory
- javaw.exe (PID: 7288)
Reads the machine GUID from the registry
- javaw.exe (PID: 7288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:01 00:14:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 19968 |
| InitializedDataSize: | 23040 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.0.0 |
| ProductVersionNumber: | 4.4.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
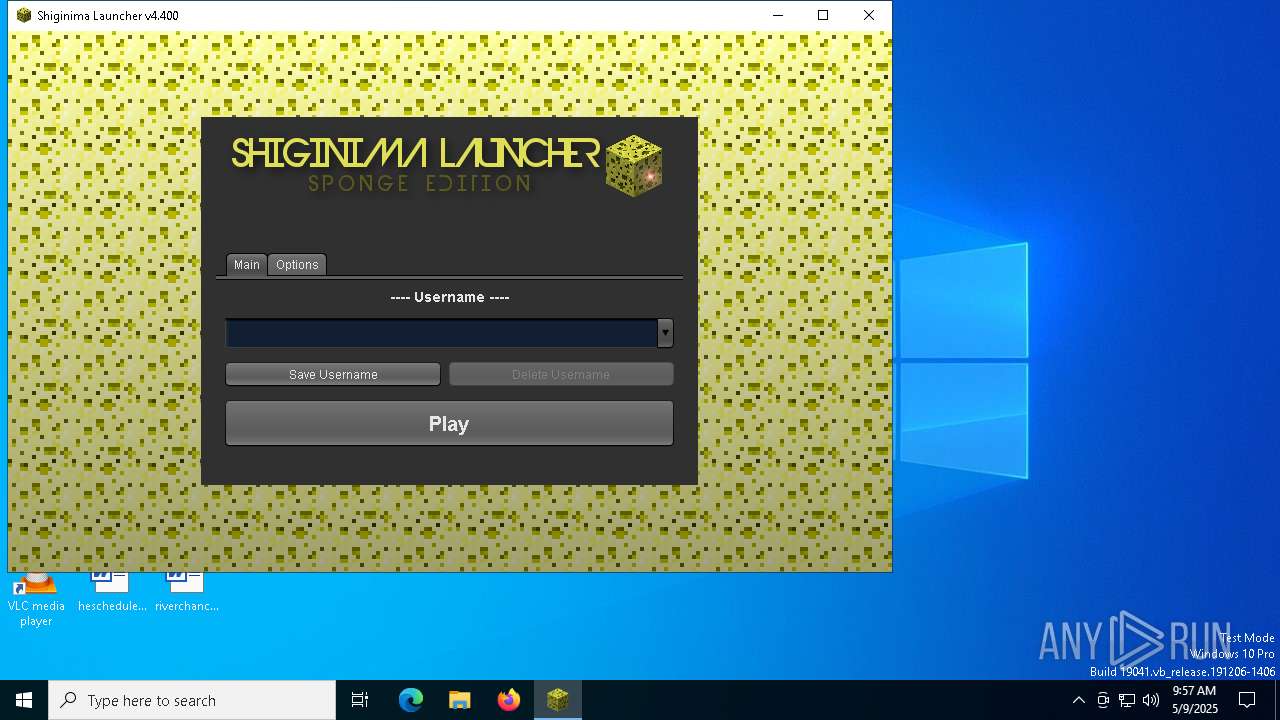
| CompanyName: | Shiginima |
| FileDescription: | Shiginima Launcher SE v4.400 |
| FileVersion: | 4.4 |
| InternalName: | Shiginima Salad |
| LegalCopyright: | Shiginima, Mojang |
| LegalTrademarks: | - |
| OriginalFileName: | Shiginima Launcher SE v4.400.exe |
| ProductName: | Shiginima Launcher SE v4.300 |
| ProductVersion: | Shiginima Launcher SE v4.400 |
Total processes
133
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7272 | "C:\Users\admin\AppData\Local\Temp\Shiginima Launcher SE v4400.exe" | C:\Users\admin\AppData\Local\Temp\Shiginima Launcher SE v4400.exe | — | explorer.exe | |||||||||||
User: admin Company: Shiginima Integrity Level: MEDIUM Description: Shiginima Launcher SE v4.400 Exit code: 0 Version: 4.400 Modules
| |||||||||||||||
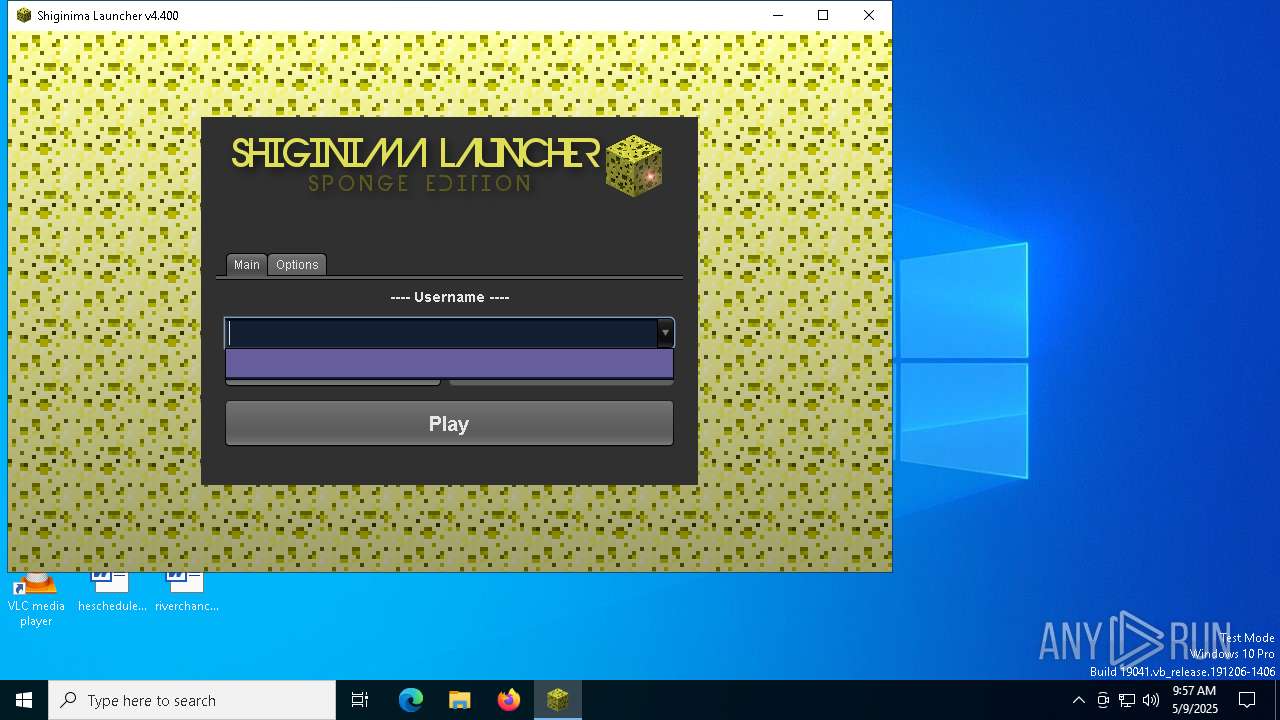
| 7288 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -classpath "C:\Users\admin\AppData\Local\Temp\Shiginima Launcher SE v4400.exe" net.mc.main.Main | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | Shiginima Launcher SE v4400.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 7376 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7496 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7528 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 510
Read events
4 510
Write events
0
Delete events
0
Modification events
Executable files
44
Suspicious files
20
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7288 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\shig.inima | text | |
MD5:571CC0288E3F5DB4C85AE85DCD1C64CE | SHA256:36ED29282E1D008064F2C06952EDDABDF7C73B58E2BC5215A497AC4541BE6553 | |||
| 7288 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:5DA99B092D64094B91A92E0721CF0E06 | SHA256:D6ED8F9F06E5490D09B8D79E8CF7C63F7B592FCCA5BC3DFCF594287F7C2B6AD7 | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2217768178745051918.tmp | image | |
MD5:D2FC27C31904067D5E9C765700CD5292 | SHA256:3E46FF5095EB7E0E7DDB78AD26D673D0F791A89D8741346F44EC706AE94CAE9F | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | binary | |
MD5:18E269C549AA007A8FD7925D87B4CD79 | SHA256:8DF48652D34DB126A444AF8961EED047D9E76AE3BC590741BFAE7C444E02900E | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio558058592100803931.tmp | image | |
MD5:D2FC27C31904067D5E9C765700CD5292 | SHA256:3E46FF5095EB7E0E7DDB78AD26D673D0F791A89D8741346F44EC706AE94CAE9F | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\io\netty\netty-resolver\4.1.118.Final\netty-resolver-4.1.118.Final.jar | java | |
MD5:FD965F84DC2A07042388339237691B35 | SHA256:FD569A57B3C50FF2AA878B946738389D806EB029781DC6DCD259087EC71D6F1F | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio7235072287427215363.tmp | image | |
MD5:B8A61355127D82D931BC39EFB10FB9B6 | SHA256:8A3DA25EC37F06992149890C67D1868D05D1DB8DC693B99FECF19FC94807C828 | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\brigadier\1.3.10\brigadier-1.3.10.jar | compressed | |
MD5:A755B426EB7942BB74B46A95B02F1DE4 | SHA256:C8EE4136E474AC7723CA2B432EC8D1A2BC88EF7D1EC57C314BA9E33CDC83DD75 | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-codec\commons-codec\1.17.1\commons-codec-1.17.1.jar | java | |
MD5:7B3438AB4C6D91E0066D410947E43F3E | SHA256:F9F6CB103F2DDC3C99A9D80ADA2AE7BF0685111FD6BFFCCB72033D1DA4E6FF23 | |||
| 7288 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\blocklist\1.0.10\blocklist-1.0.10.jar | compressed | |
MD5:FC1420E3182DD32B4DF9933F810EBEBB | SHA256:830BFD639C8DB49236BBD8E45D3A2B8C96C56FF654A10118654958A6235D4C44 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2 231
TCP/UDP connections
2 326
DNS requests
22
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7288 | javaw.exe | HEAD | — | 69.16.230.165:80 | http://teamshiginima.com/version.php | unknown | — | — | whitelisted |
7288 | javaw.exe | GET | — | 69.16.230.165:80 | http://news.teamshiginima.com/ | unknown | — | — | whitelisted |
7288 | javaw.exe | HEAD | — | 69.16.230.165:80 | http://teamshiginima.com/version.php | unknown | — | — | whitelisted |
7288 | javaw.exe | GET | — | 69.16.230.165:80 | http://servers.teamshiginima.com/ | unknown | — | — | whitelisted |
7288 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/26/269587652f4143877ba240bba36fadd3fccbe603 | unknown | — | — | whitelisted |
7288 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/86/8669668f3aa42ca007e5ae6dd78e0c96d2c5fcd4 | unknown | — | — | whitelisted |
7288 | javaw.exe | GET | — | 69.16.230.165:80 | http://servers.teamshiginima.com/ | unknown | — | — | whitelisted |
7288 | javaw.exe | GET | — | 69.16.230.165:80 | http://news.teamshiginima.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7288 | javaw.exe | 69.16.230.165:80 | teamshiginima.com | LIQUIDWEB | US | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
teamshiginima.com |
| whitelisted |
shigmeahyea.us.to |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
servers.teamshiginima.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7288 | javaw.exe | Potentially Bad Traffic | ET INFO Vulnerable Java Version 1.8.x Detected |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
7288 | javaw.exe | Potentially Bad Traffic | ET INFO Vulnerable Java Version 1.8.x Detected |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.us .to Domain |