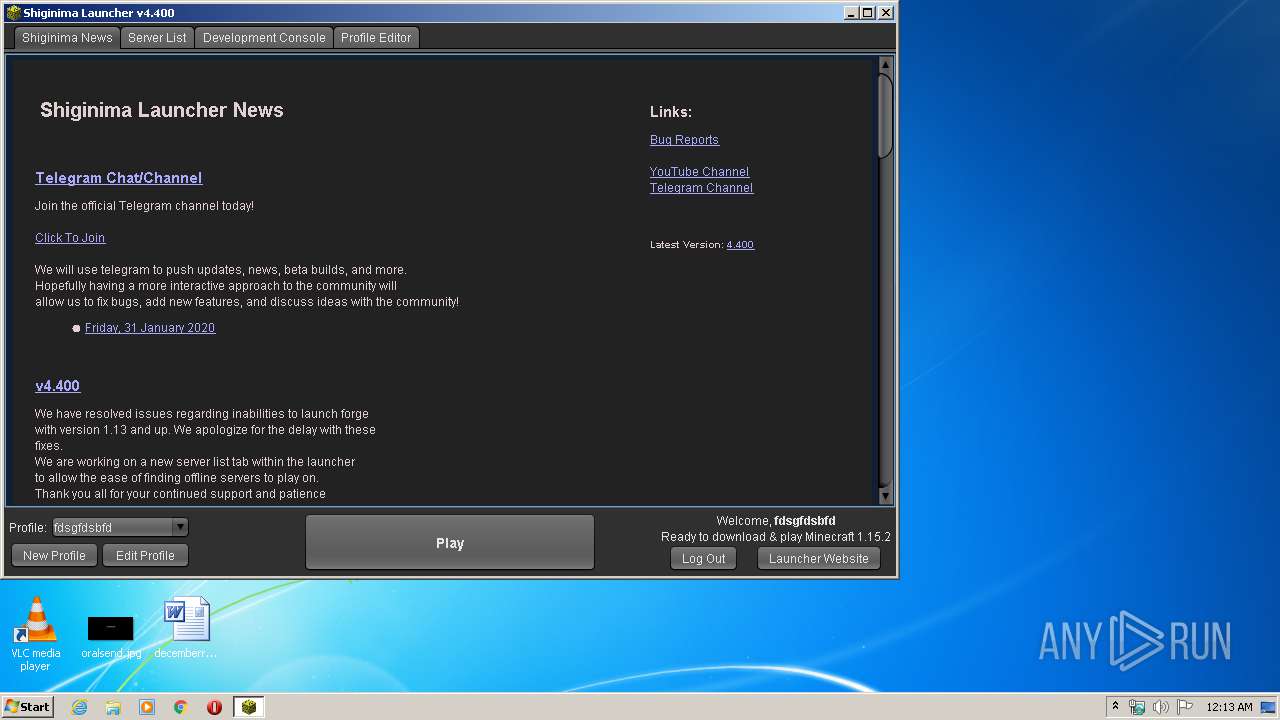
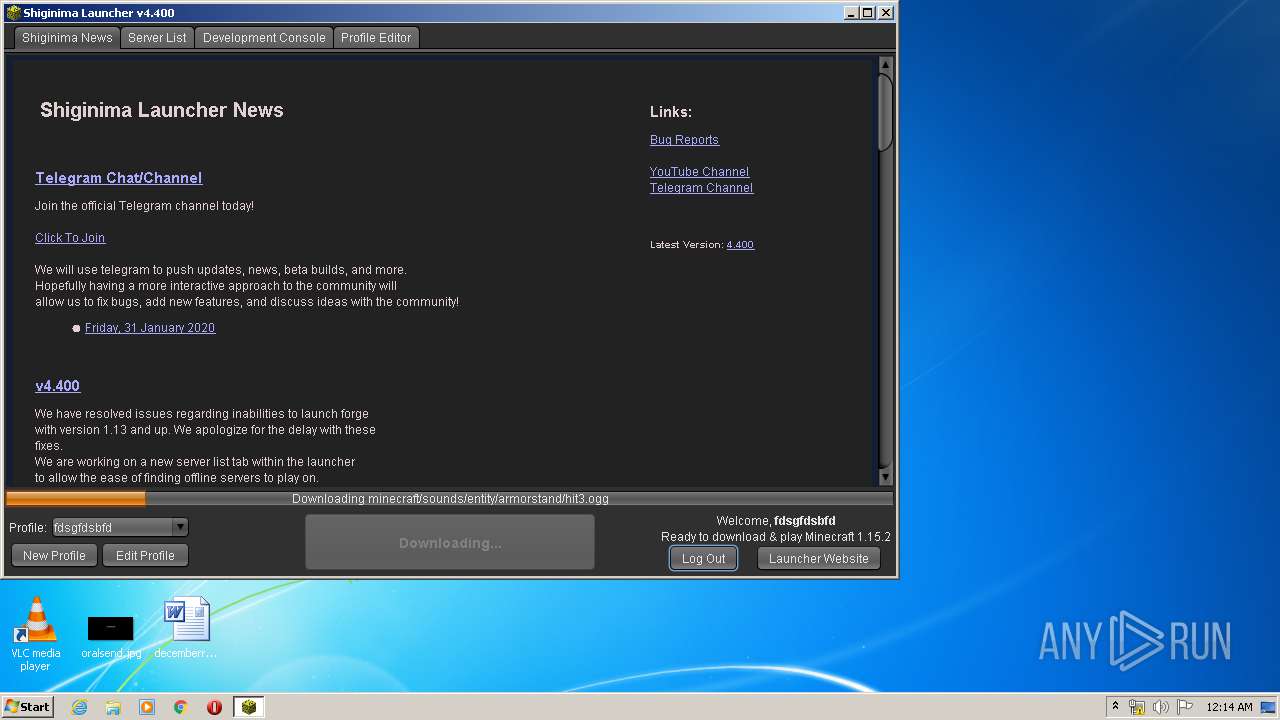
| File name: | Shiginima Launcher SE v4400.exe |
| Full analysis: | https://app.any.run/tasks/18ba1e7a-8d2b-4cf7-b763-93c668caef77 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2020, 00:12:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | C3DB052DA531710367FAF5E011475715 |
| SHA1: | 46F599E4E1ECE582006739DEBE0A522925A9CD13 |
| SHA256: | 7C6220B046553F9C95B8098FF83BFC6B7828093650BECBC1B44E3D7819D7EFD1 |
| SSDEEP: | 98304:qpTJ89MMbcZsgsDlilods/txVGHTJKsTnEFnAzvDfBzXEYNsJ5Ono:aTm9MMbcFililB0HdRTnEFnAzlEQsJ5H |
MALICIOUS
No malicious indicators.SUSPICIOUS
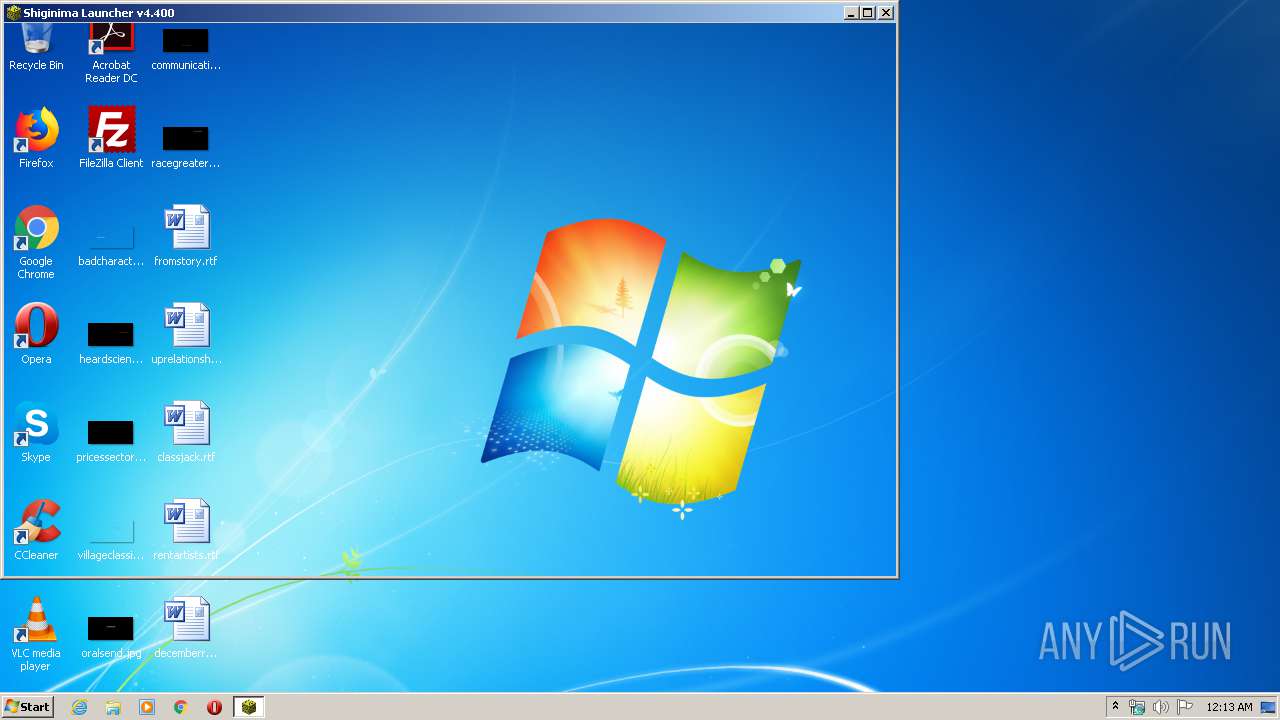
Executes JAVA applets
- Shiginima Launcher SE v4400.exe (PID: 3164)
Creates files in the user directory
- javaw.exe (PID: 312)
INFO
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:01 01:14:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 19968 |
| InitializedDataSize: | 23040 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.0.0 |
| ProductVersionNumber: | 4.4.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
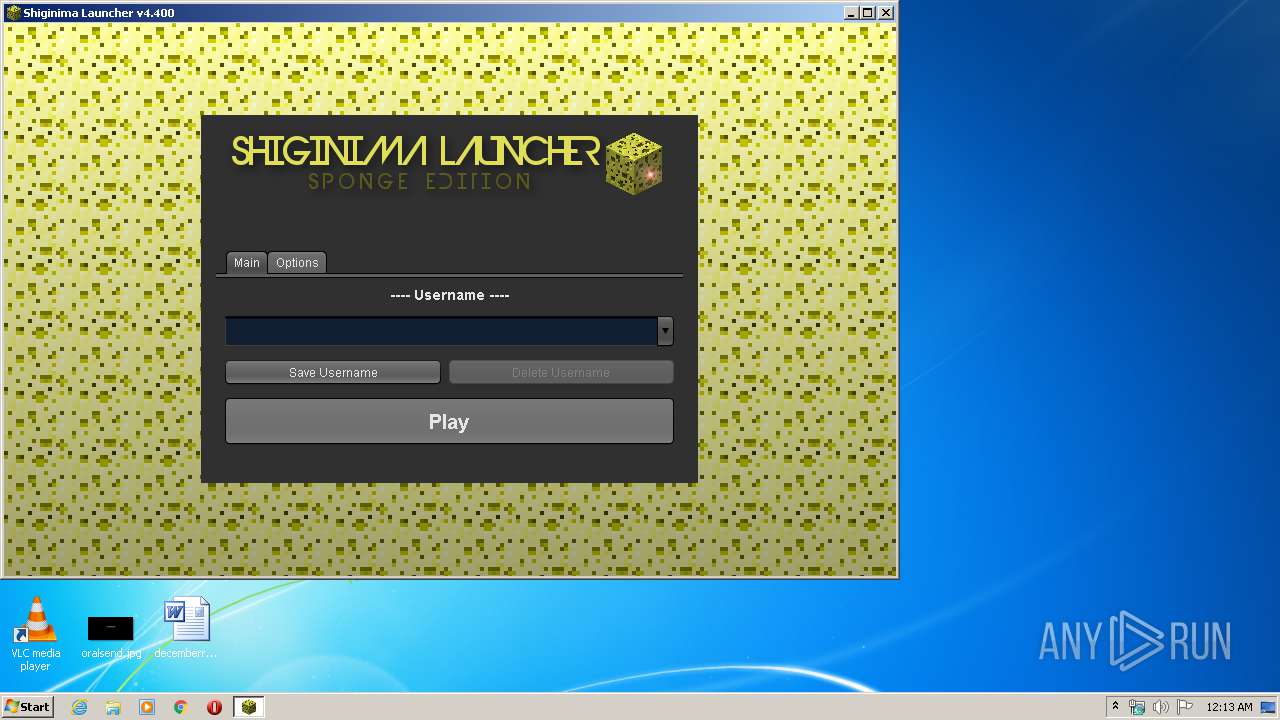
| CompanyName: | Shiginima |
| FileDescription: | Shiginima Launcher SE v4.400 |
| FileVersion: | 4.4 |
| InternalName: | Shiginima Salad |
| LegalCopyright: | Shiginima, Mojang |
| LegalTrademarks: | - |
| OriginalFileName: | Shiginima Launcher SE v4.400.exe |
| ProductName: | Shiginima Launcher SE v4.300 |
| ProductVersion: | Shiginima Launcher SE v4.400 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2020 00:14:31 |
| Detected languages: |
|
| CompanyName: | Shiginima |
| FileDescription: | Shiginima Launcher SE v4.400 |
| FileVersion: | 4.400 |
| InternalName: | Shiginima Salad |
| LegalCopyright: | Shiginima, Mojang |
| LegalTrademarks: | - |
| OriginalFilename: | Shiginima Launcher SE v4.400.exe |
| ProductName: | Shiginima Launcher SE v4.300 |
| ProductVersion: | Shiginima Launcher SE v4.400 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Feb-2020 00:14:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004CE0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03278 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000680 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x000043D4 | 0x00004400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.85731 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30486 | 892 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 5.74619 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
11 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
15 | 3.17512 | 17 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 3.91327 | 25 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
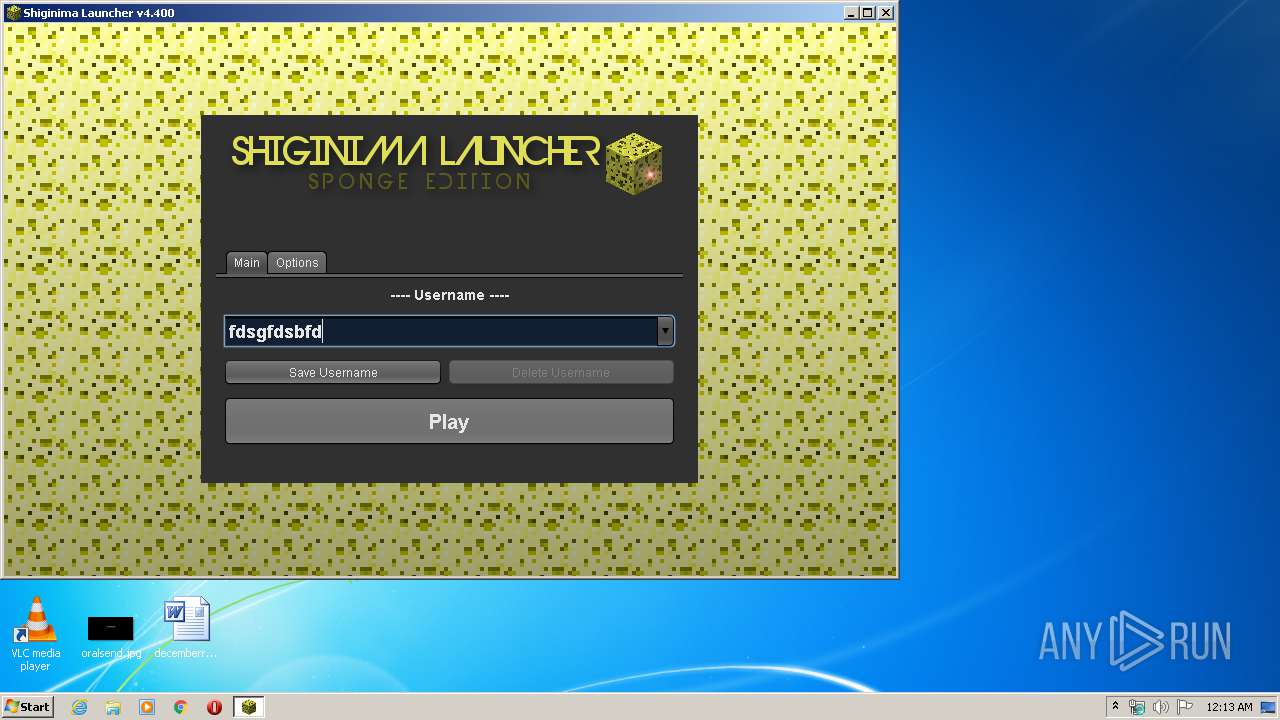
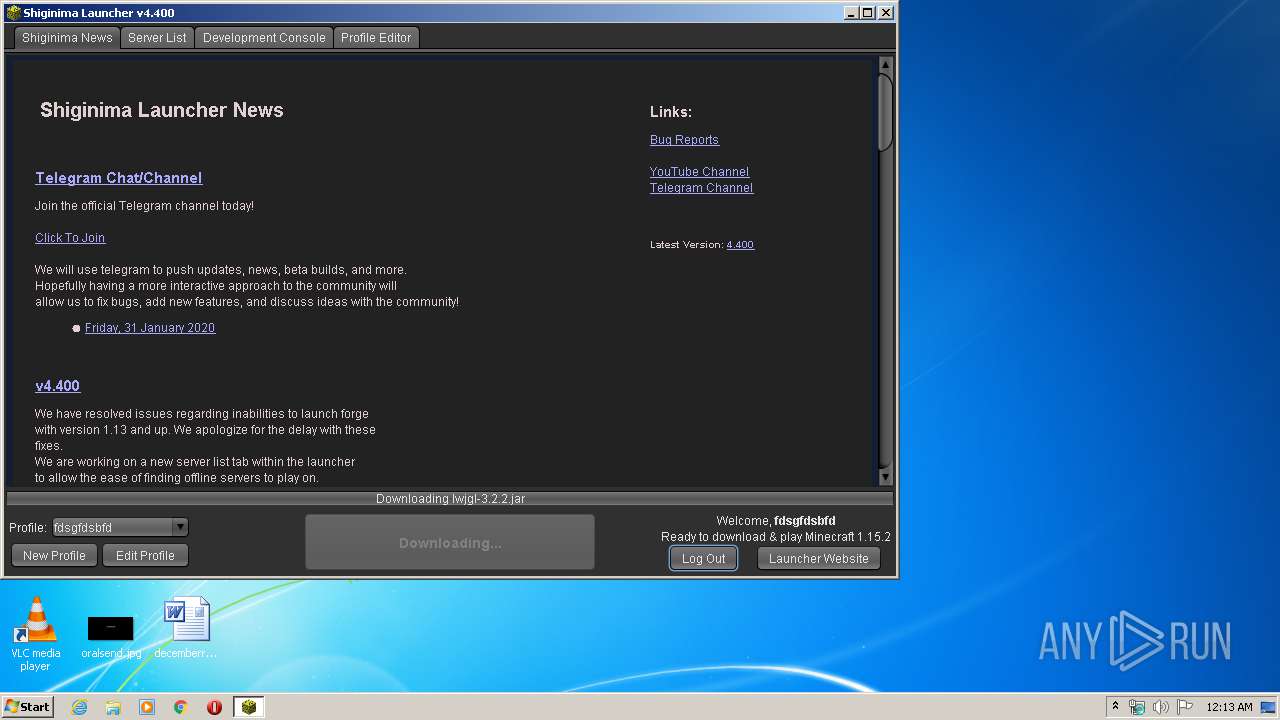
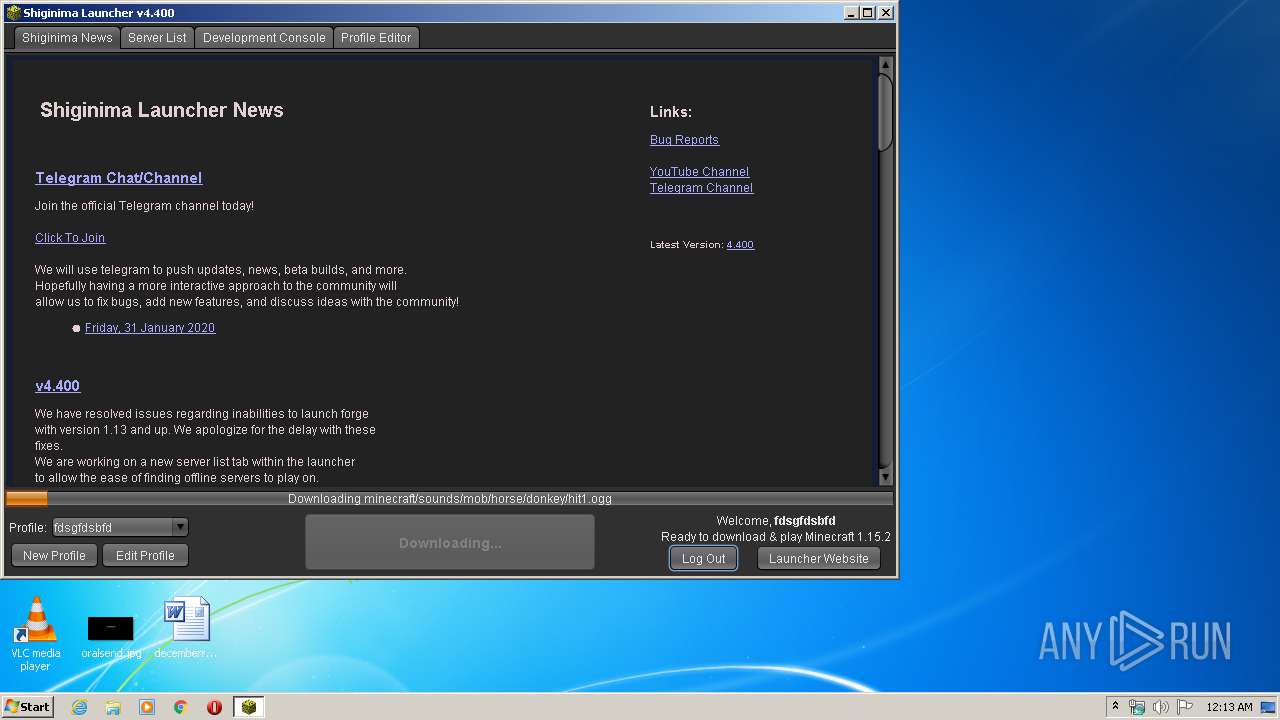
| 312 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -classpath "C:\Users\admin\AppData\Local\Temp\Shiginima Launcher SE v4400.exe" net.mc.main.Main | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | Shiginima Launcher SE v4400.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\Temp\Shiginima Launcher SE v4400.exe" | C:\Users\admin\AppData\Local\Temp\Shiginima Launcher SE v4400.exe | — | explorer.exe | |||||||||||
User: admin Company: Shiginima Integrity Level: MEDIUM Description: Shiginima Launcher SE v4.400 Exit code: 0 Version: 4.400 Modules
| |||||||||||||||
Total events
24
Read events
23
Write events
1
Delete events
0
Modification events
| (PID) Process: | (312) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
19
Suspicious files
20
Text files
75
Unknown types
410
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 312 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio1146435374705117685.tmp | — | |
MD5:— | SHA256:— | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2618946821925287108.tmp | — | |
MD5:— | SHA256:— | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5807882313009010627.tmp | — | |
MD5:— | SHA256:— | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2379188705527609196.tmp | — | |
MD5:— | SHA256:— | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | text | |
MD5:7D5BDA4AA6291BE4D542C4BB4F0FAA28 | SHA256:9E06DADB059B2A9739F5D16FA6E6FBDD7007205DAA1CEABDCE5BB12B27D12027 | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\versions\1.15.2\1.15.2.json | text | |
MD5:DFFCA39F645161B920143664E69CAB9F | SHA256:F54C64A8F870D8D00168F16388D55D9C37991DEDE806D85B6F781C81F5D61263 | |||
| 312 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:3A00E4B8FD4AE522E2C61C81A8F204A6 | SHA256:99B025562E3D7FBCE930325B97CEF4AAD5A696F9D97E151E2880DE78C4F8EE9B | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\shig.inima | text | |
MD5:571CC0288E3F5DB4C85AE85DCD1C64CE | SHA256:36ED29282E1D008064F2C06952EDDABDF7C73B58E2BC5215A497AC4541BE6553 | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\patchy\1.1\patchy-1.1.jar | compressed | |
MD5:D7DFCF04D1DA01D966D3CA806CA8C22F | SHA256:41764C3F297E0B6CEB802D47E5A3179A8B81BB824063773673C240860E5F5D72 | |||
| 312 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\assets\indexes\1.15.json | text | |
MD5:B87D613CC6B28A57399263A919C2C35A | SHA256:7ADF13AE92F2F8F843EC765CC8065516057B703224128FF0C569A89B0755C26E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
562
TCP/UDP connections
38
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | javaw.exe | HEAD | 200 | 198.252.102.62:80 | http://teamshiginima.com/version.php | US | — | — | whitelisted |
312 | javaw.exe | GET | 200 | 198.252.102.62:80 | http://teamshiginima.com/version.php | US | text | 533 b | whitelisted |
312 | javaw.exe | GET | 301 | 198.252.102.62:80 | http://teamshiginima.com/launch.png | US | html | 706 b | whitelisted |
312 | javaw.exe | GET | 200 | 198.252.102.62:80 | http://news.teamshiginima.com/ | US | html | 27.9 Kb | malicious |
312 | javaw.exe | GET | 301 | 198.252.102.62:80 | http://teamshiginima.com/launch.png | US | html | 706 b | whitelisted |
312 | javaw.exe | GET | 200 | 198.252.102.62:80 | http://servers.teamshiginima.com/ | US | html | 1.65 Kb | malicious |
312 | javaw.exe | GET | 200 | 198.252.102.62:80 | http://servers.teamshiginima.com/placeholder.png | US | image | 643 b | malicious |
312 | javaw.exe | GET | 200 | 198.252.102.62:80 | http://servers.teamshiginima.com/placeholder.png | US | image | 643 b | malicious |
312 | javaw.exe | GET | 200 | 198.252.102.62:80 | http://servers.teamshiginima.com/placeholder.png | US | image | 643 b | malicious |
312 | javaw.exe | GET | 200 | 99.86.3.8:80 | http://resources.download.minecraft.net/f4/f4cbd2c2eedb8fd4889e9671a4fc0ddb53171119 | US | ogg | 15.5 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
312 | javaw.exe | 99.86.1.139:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
312 | javaw.exe | 198.252.102.62:80 | teamshiginima.com | SoftLayer Technologies Inc. | US | suspicious |
312 | javaw.exe | 99.86.4.83:443 | libraries.minecraft.net | AT&T Services, Inc. | US | suspicious |
312 | javaw.exe | 143.204.212.134:443 | launcher.mojang.com | — | US | unknown |
312 | javaw.exe | 99.86.3.8:80 | resources.download.minecraft.net | AT&T Services, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teamshiginima.com |
| whitelisted |
servers.teamshiginima.com |
| malicious |
news.teamshiginima.com |
| malicious |
launchermeta.mojang.com |
| whitelisted |
libraries.minecraft.net |
| shared |
launcher.mojang.com |
| whitelisted |
resources.download.minecraft.net |
| shared |