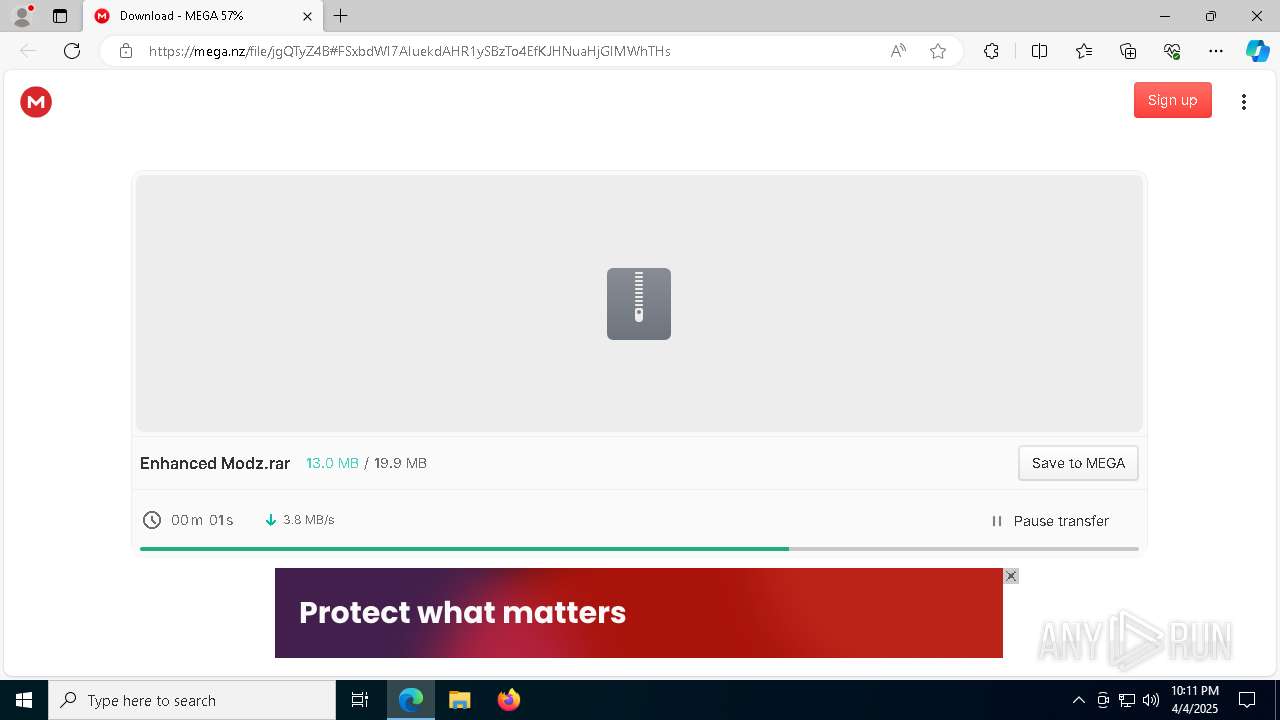
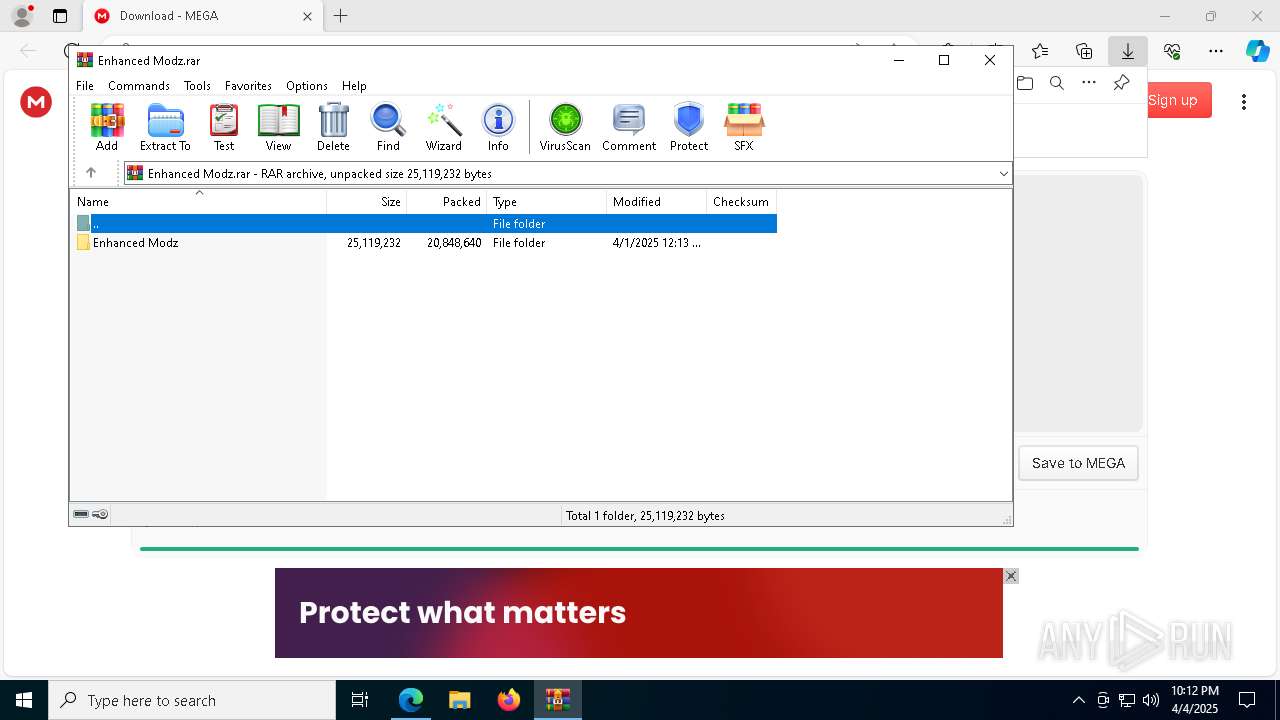
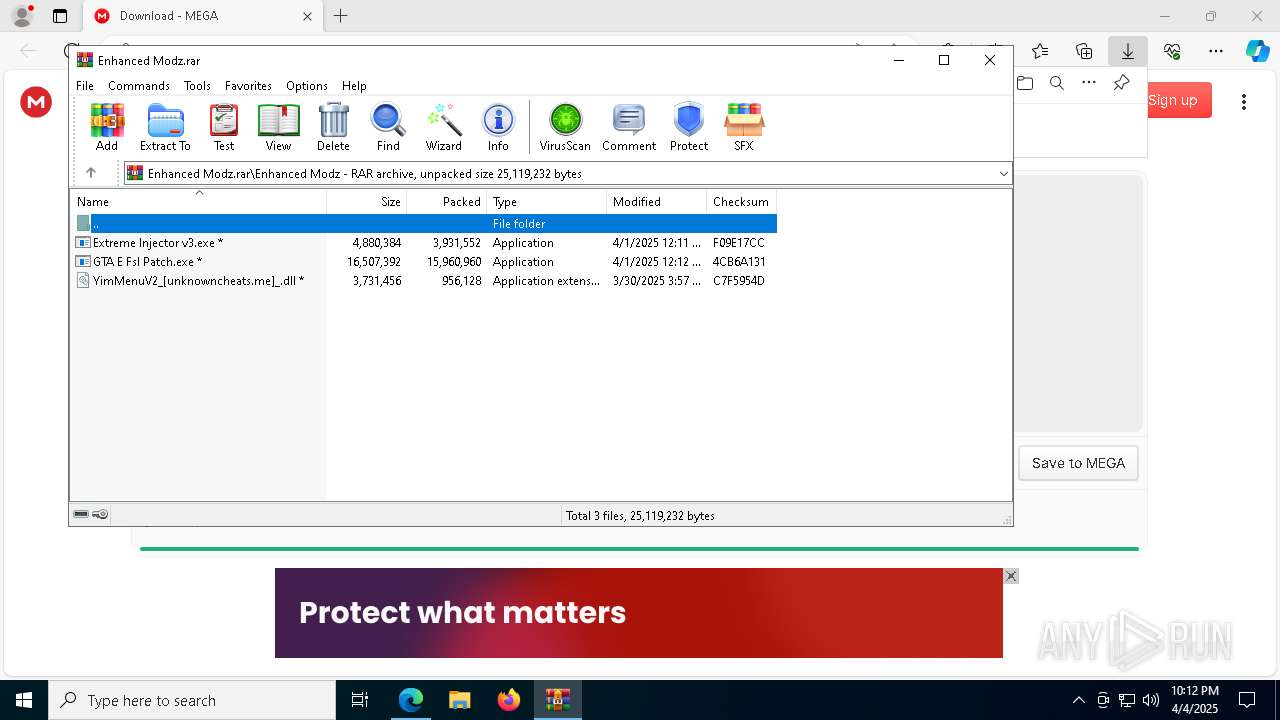
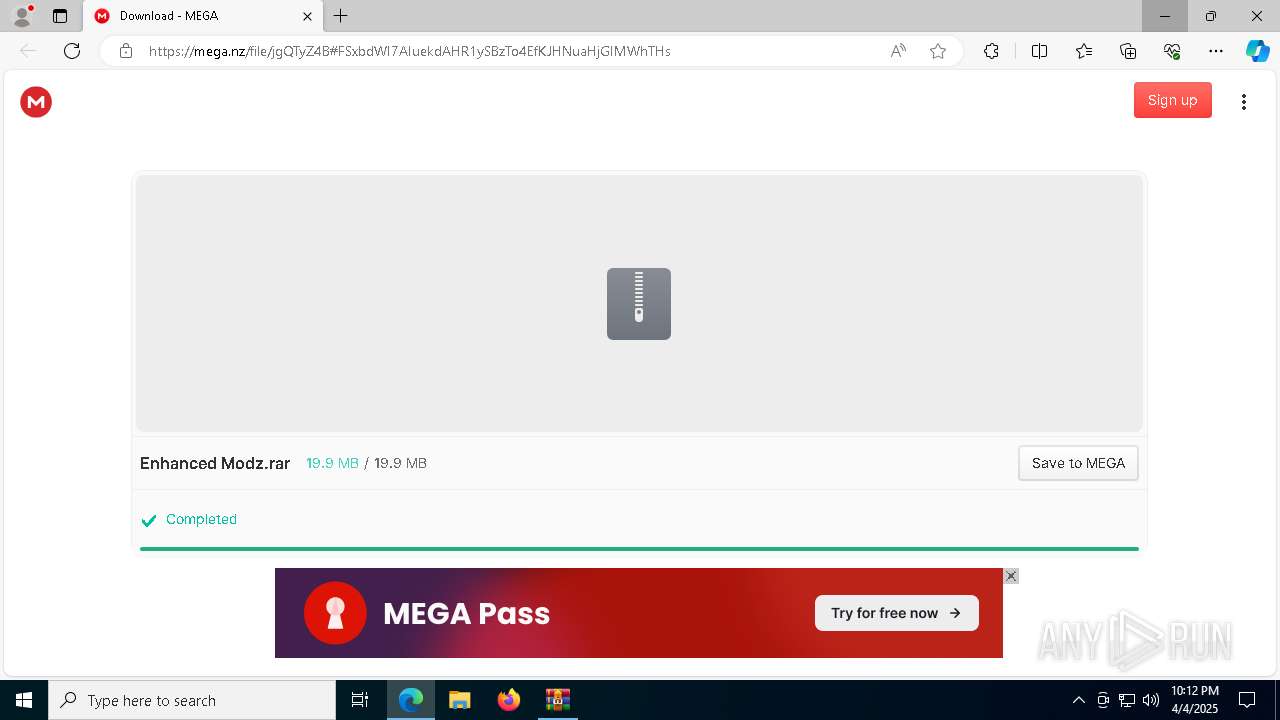
| URL: | https://mega.nz/file/jgQTyZ4B#FSxbdWI7AIuekdAHR1ySBzTo4EfKJHNuaHjGIMWhTHs |
| Full analysis: | https://app.any.run/tasks/f16447bf-14c6-4562-a223-489f88b516ff |
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2025, 22:11:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D7383BD06058656D7D981344B653B692 |
| SHA1: | 052FCBEF08779F101424DDD427424C081EA1F54B |
| SHA256: | 7C591520023C7464AA4D005AA9F2E4EA2694D59CFAAE094DC2FDE1D47B23E0B7 |
| SSDEEP: | 3:N8X/irBDyIZek/MGDorzRW:2BIMk/1+w |
MALICIOUS
Changes Windows Defender settings
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 684)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 2616)
Adds extension to the Windows Defender exclusion list
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
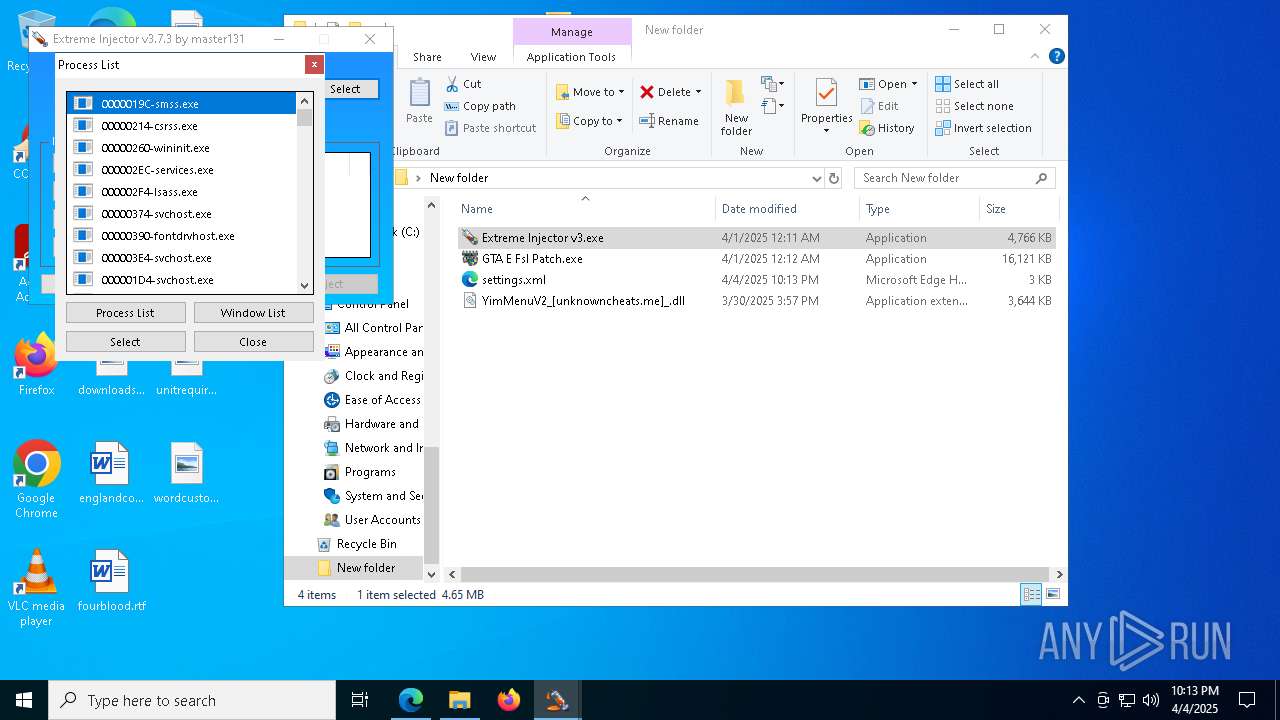
Application was injected by another process
- svchost.exe (PID: 468)
- svchost.exe (PID: 1252)
- svchost.exe (PID: 1260)
- svchost.exe (PID: 1352)
- svchost.exe (PID: 1288)
- svchost.exe (PID: 1784)
- svchost.exe (PID: 1232)
- svchost.exe (PID: 1416)
- svchost.exe (PID: 1552)
- svchost.exe (PID: 1444)
- svchost.exe (PID: 1652)
- svchost.exe (PID: 1792)
- svchost.exe (PID: 1524)
- svchost.exe (PID: 1772)
- svchost.exe (PID: 1988)
- svchost.exe (PID: 2172)
- svchost.exe (PID: 1044)
- lsass.exe (PID: 756)
- svchost.exe (PID: 1892)
- svchost.exe (PID: 1904)
- svchost.exe (PID: 2448)
- svchost.exe (PID: 2584)
- svchost.exe (PID: 2196)
- svchost.exe (PID: 2544)
- svchost.exe (PID: 2396)
- svchost.exe (PID: 2536)
- svchost.exe (PID: 2292)
- spoolsv.exe (PID: 2732)
- svchost.exe (PID: 2776)
- svchost.exe (PID: 2880)
- svchost.exe (PID: 3084)
- dasHost.exe (PID: 3012)
- svchost.exe (PID: 2932)
- svchost.exe (PID: 2920)
- svchost.exe (PID: 2068)
- svchost.exe (PID: 1980)
- svchost.exe (PID: 3104)
- svchost.exe (PID: 3232)
- svchost.exe (PID: 3196)
- svchost.exe (PID: 3184)
- OfficeClickToRun.exe (PID: 3112)
- svchost.exe (PID: 3216)
- svchost.exe (PID: 4292)
- svchost.exe (PID: 4312)
- svchost.exe (PID: 3284)
- svchost.exe (PID: 3860)
- svchost.exe (PID: 2624)
- svchost.exe (PID: 3812)
- svchost.exe (PID: 3564)
- svchost.exe (PID: 860)
- svchost.exe (PID: 1572)
- svchost.exe (PID: 4508)
- svchost.exe (PID: 2112)
- dllhost.exe (PID: 5880)
- svchost.exe (PID: 2996)
- svchost.exe (PID: 6024)
- svchost.exe (PID: 1684)
- MoUsoCoreWorker.exe (PID: 5496)
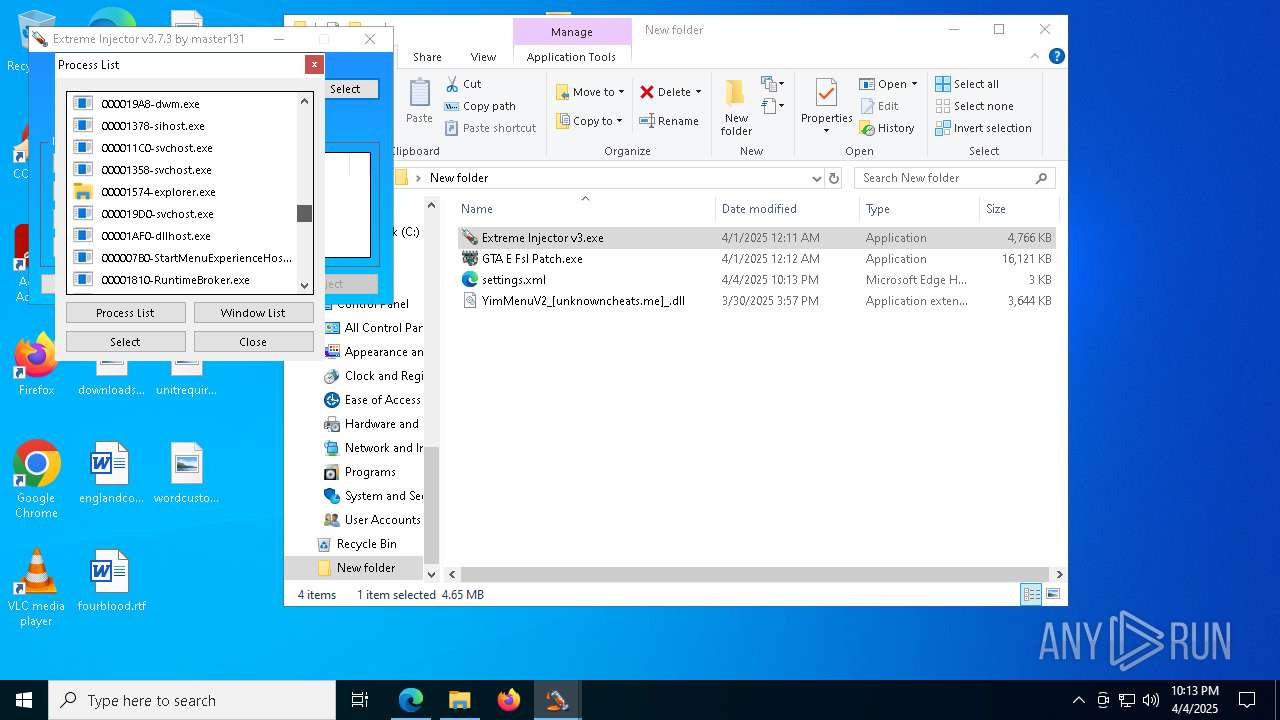
- winlogon.exe (PID: 6648)
- sihost.exe (PID: 4984)
- dwm.exe (PID: 6568)
- uhssvc.exe (PID: 648)
- RuntimeBroker.exe (PID: 6160)
- RuntimeBroker.exe (PID: 1036)
- RuntimeBroker.exe (PID: 5368)
- ApplicationFrameHost.exe (PID: 6952)
- ctfmon.exe (PID: 956)
- UserOOBEBroker.exe (PID: 1248)
- svchost.exe (PID: 4916)
- dllhost.exe (PID: 6176)
- svchost.exe (PID: 6544)
- svchost.exe (PID: 4348)
- dllhost.exe (PID: 6896)
- svchost.exe (PID: 6608)
- svchost.exe (PID: 4952)
- explorer.exe (PID: 5492)
- svchost.exe (PID: 4544)
- svchost.exe (PID: 4336)
- WmiPrvSE.exe (PID: 5156)
- svchost.exe (PID: 7152)
- WmiPrvSE.exe (PID: 3024)
- svchost.exe (PID: 4844)
- svchost.exe (PID: 2560)
- audiodg.exe (PID: 6168)
- svchost.exe (PID: 4684)
- svchost.exe (PID: 6180)
- svchost.exe (PID: 4692)
- consent.exe (PID: 8116)
- consent.exe (PID: 472)
- taskhostw.exe (PID: 2040)
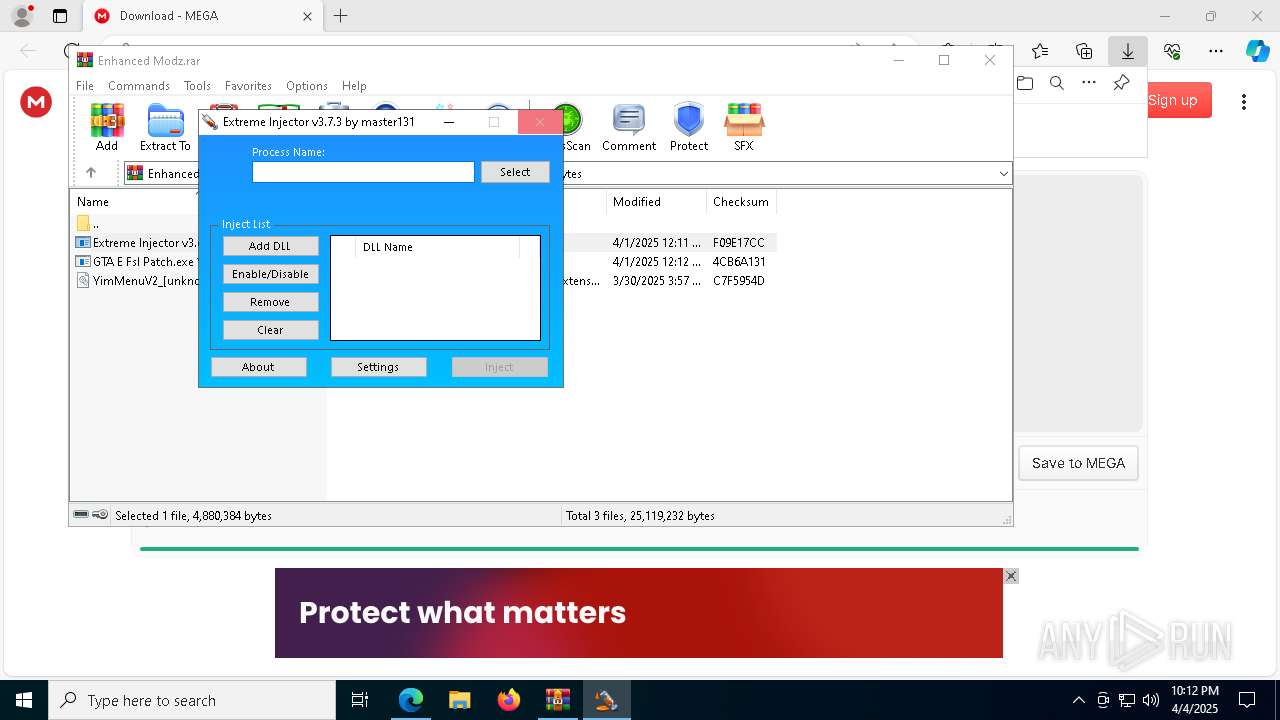
Runs injected code in another process
- dialer.exe (PID: 8060)
- dialer.exe (PID: 6644)
- dialer.exe (PID: 3028)
- dialer.exe (PID: 6668)
Vulnerable driver has been detected
- ofmvnvzjtyqd.exe (PID: 5112)
- ofmvnvzjtyqd.exe (PID: 7324)
SUSPICIOUS
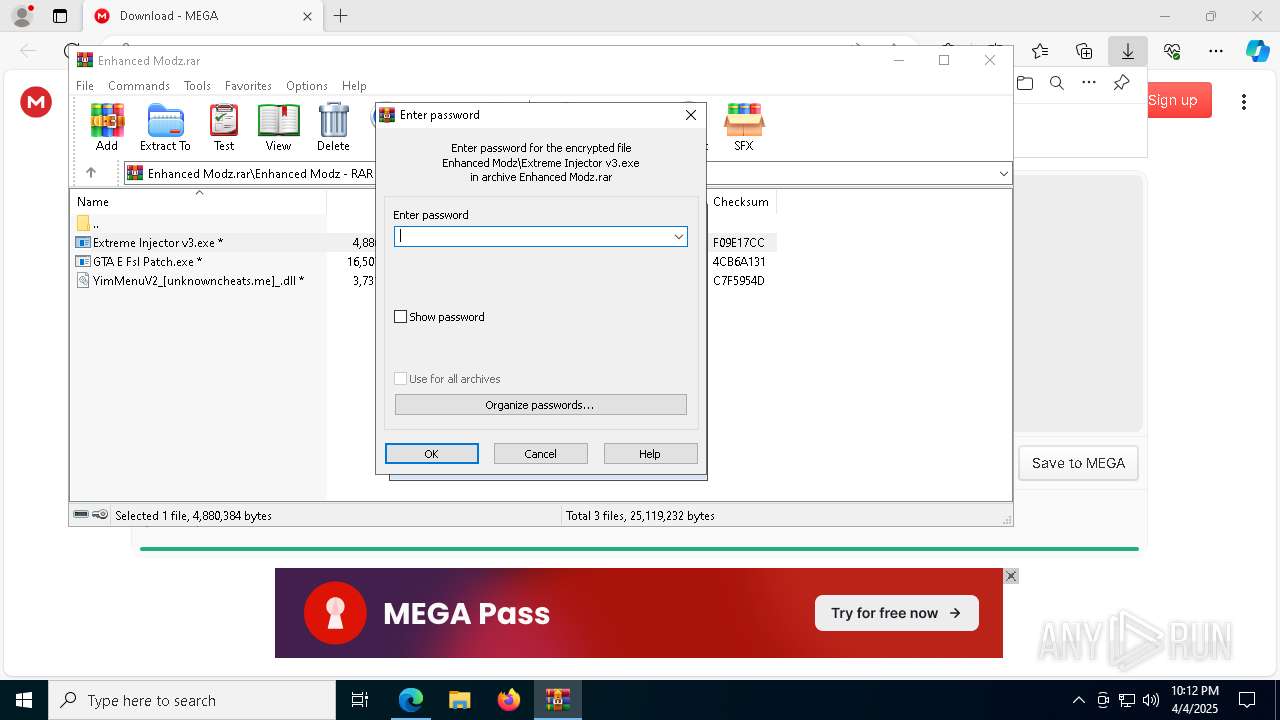
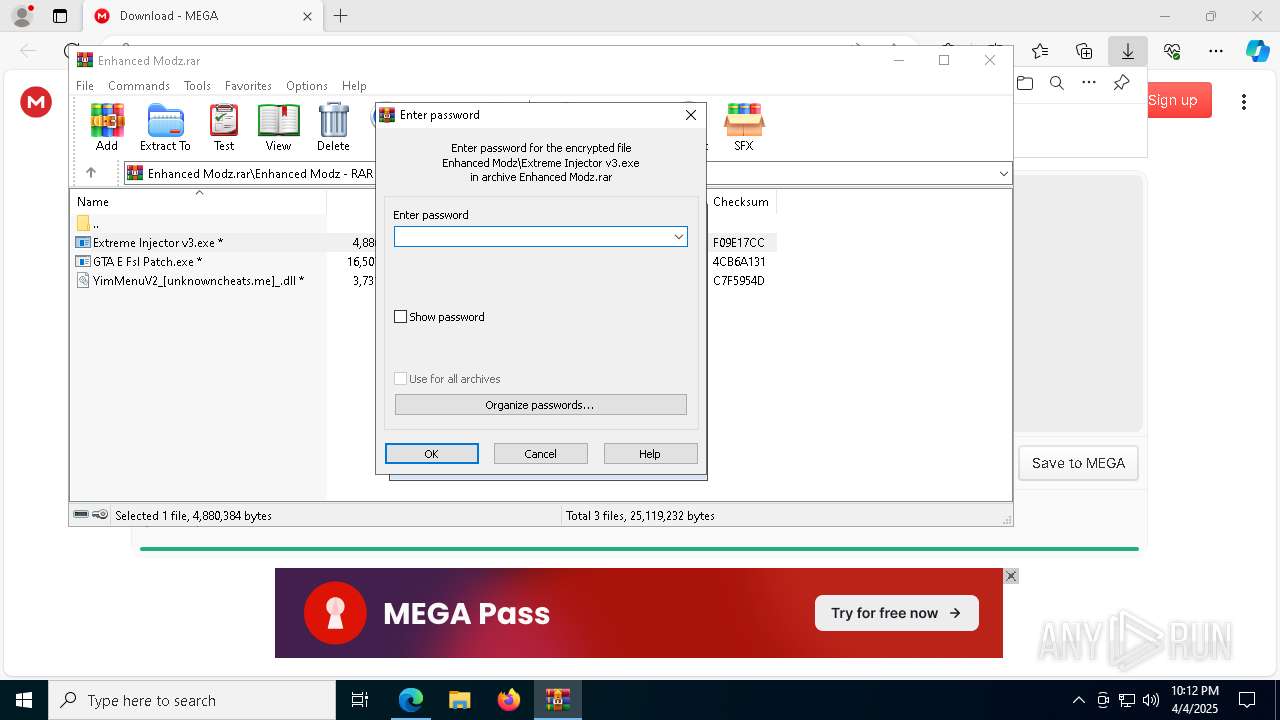
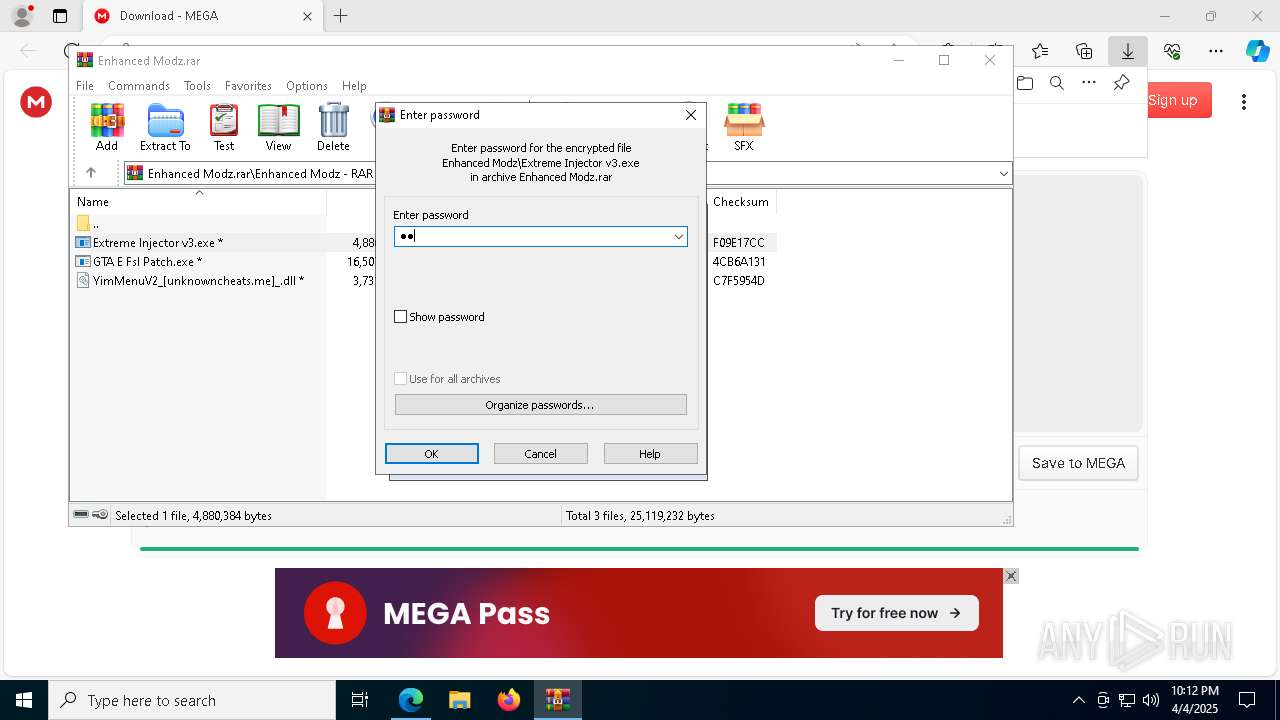
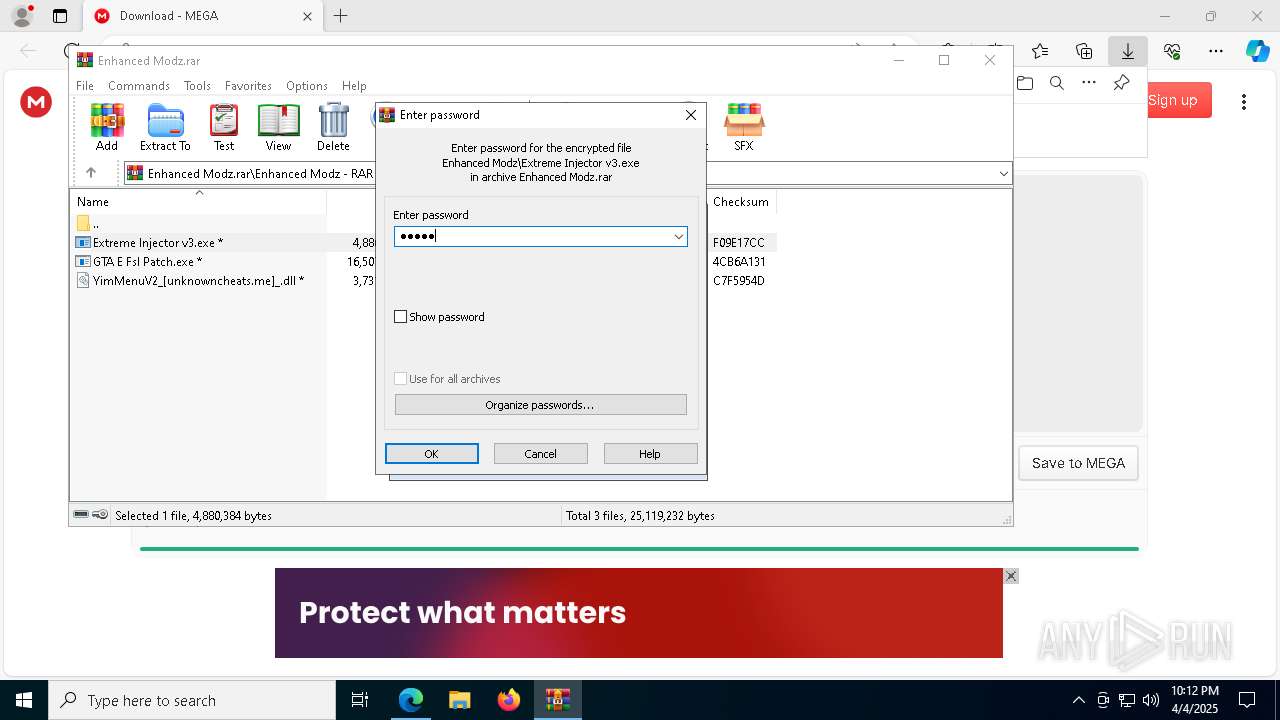
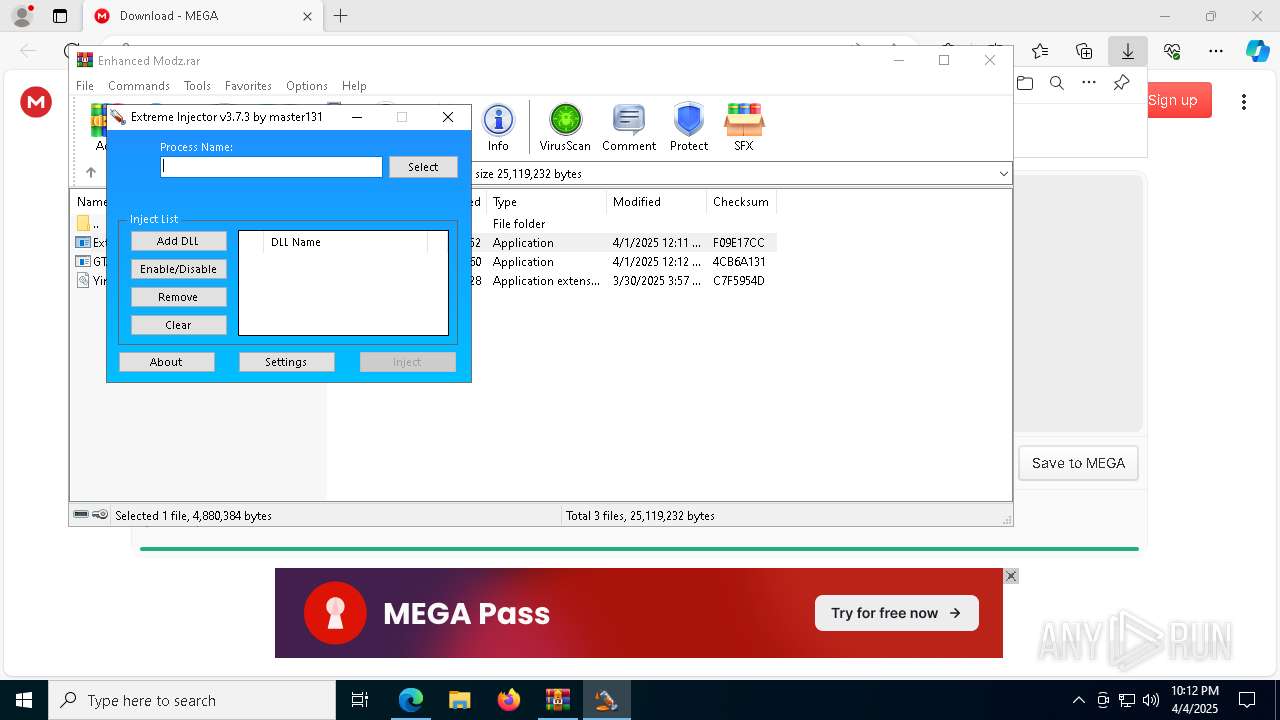
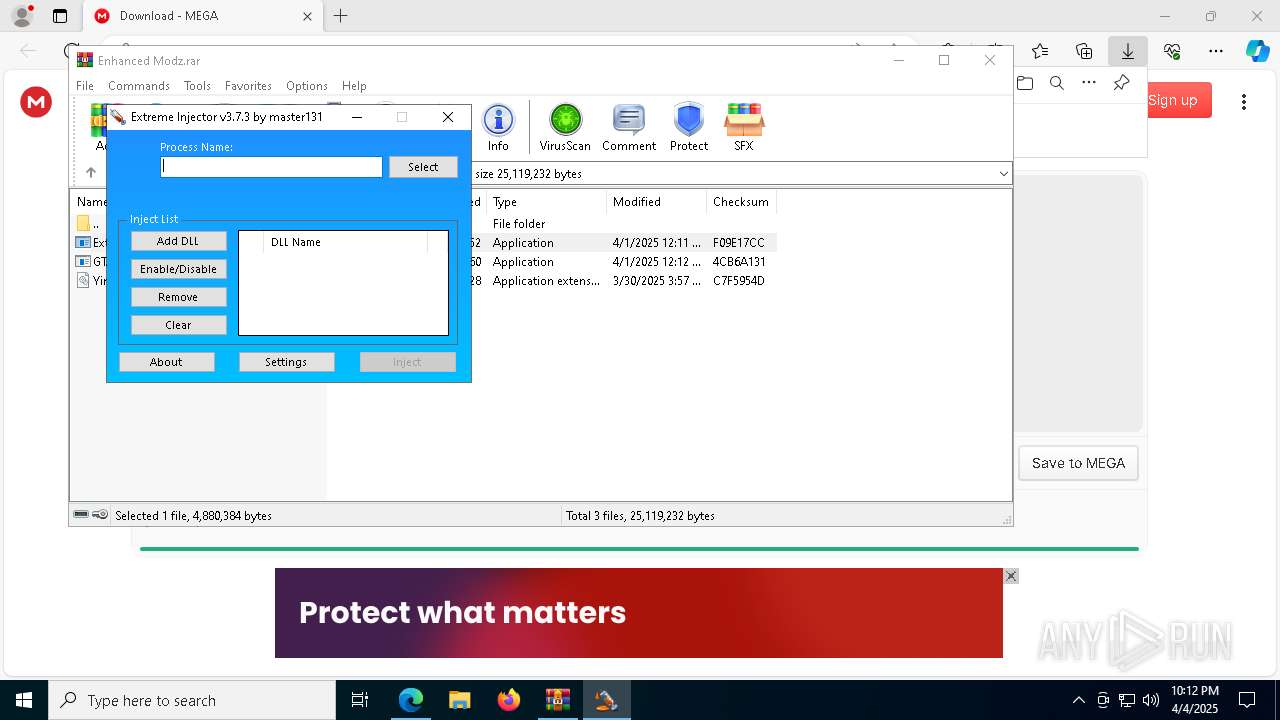
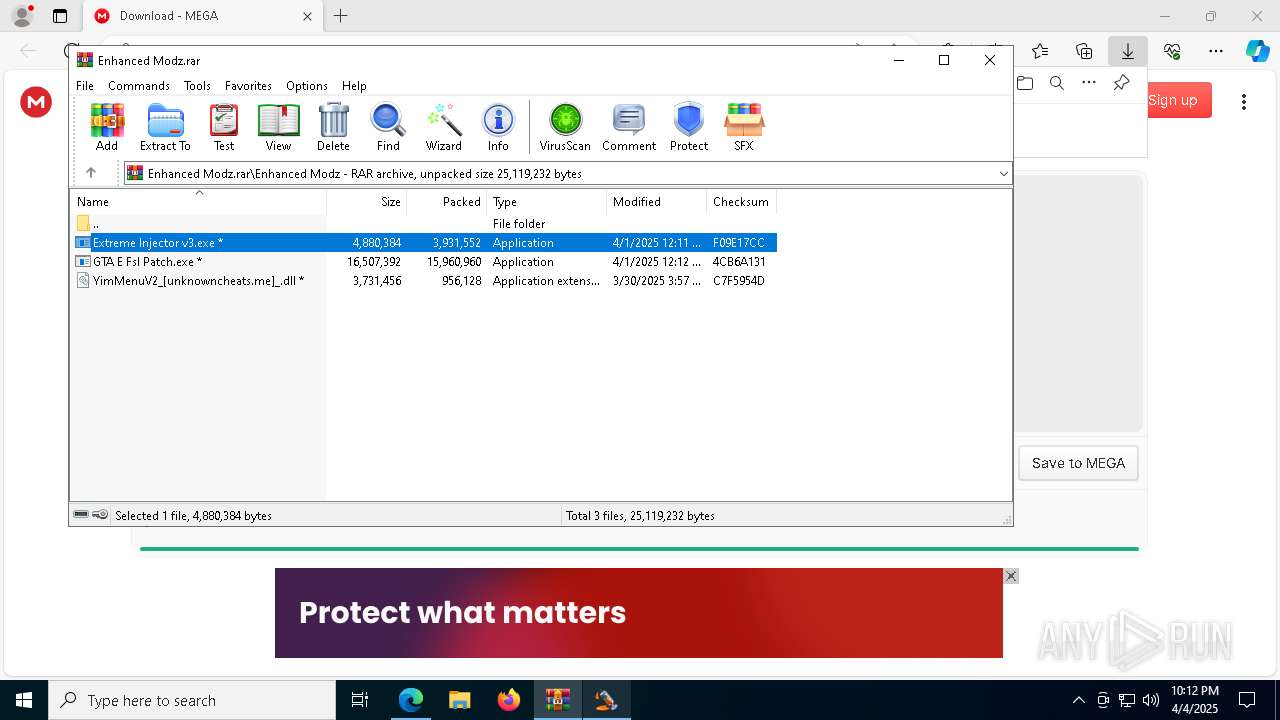
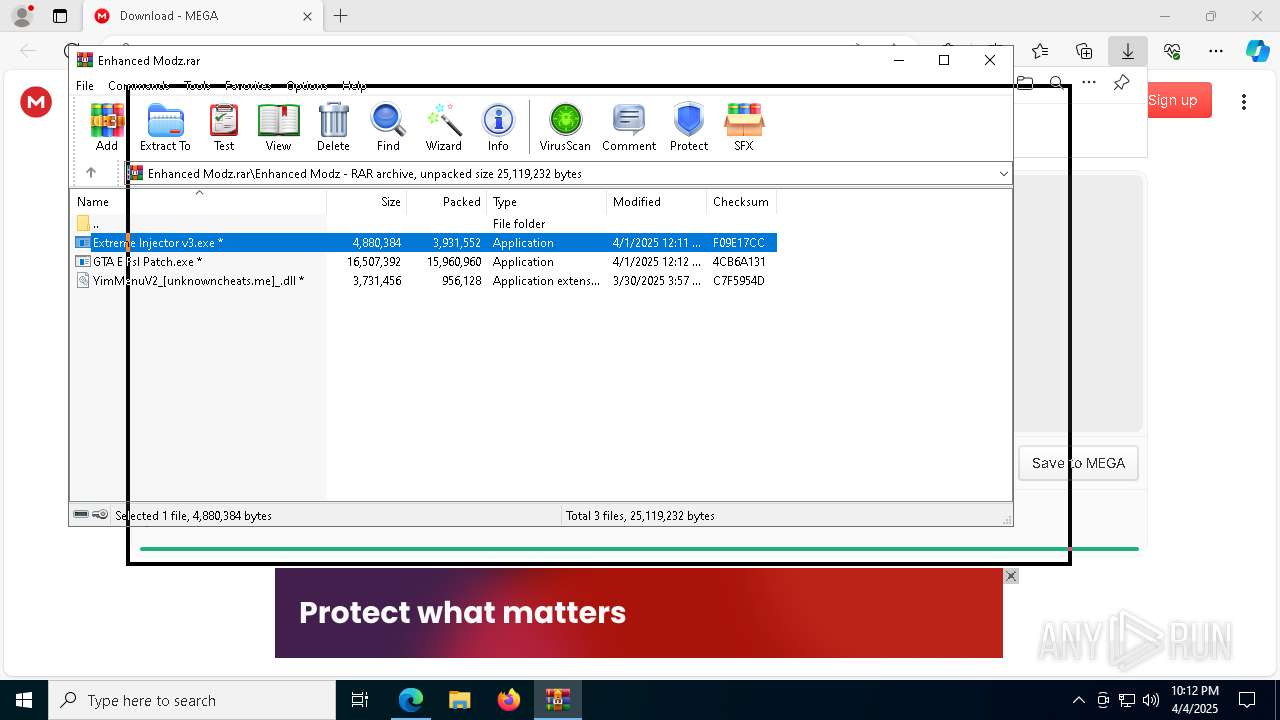
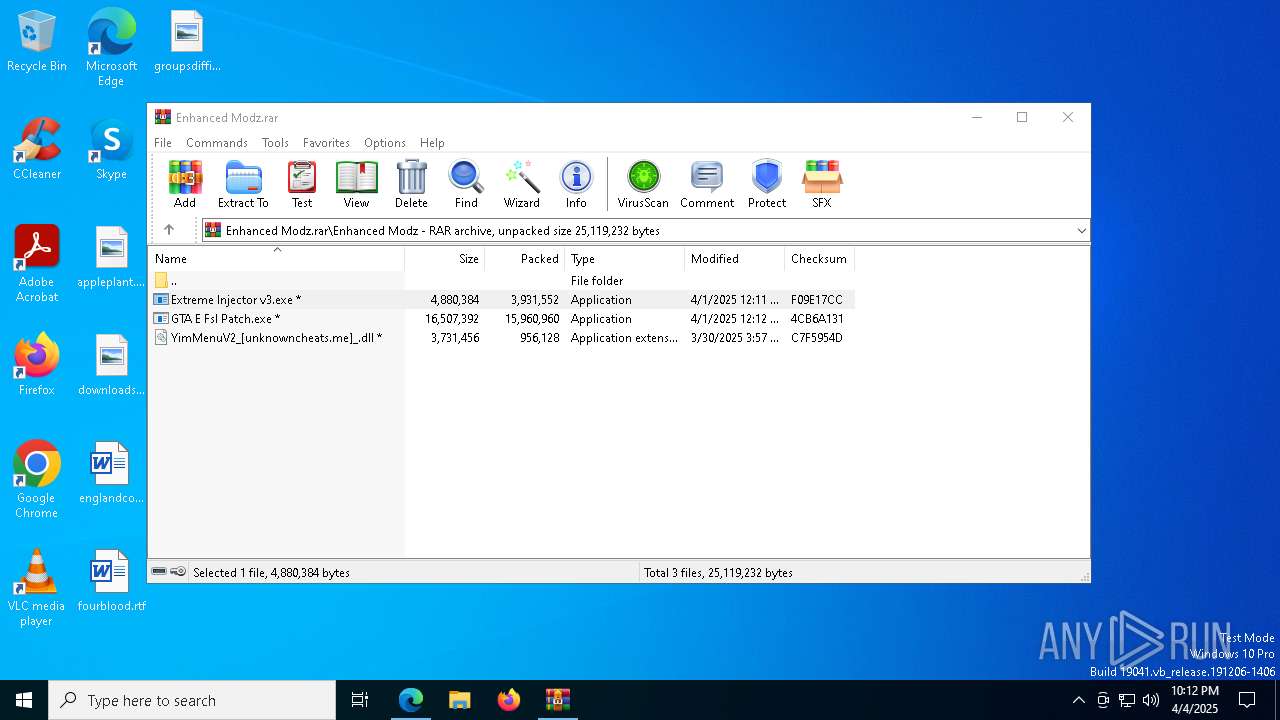
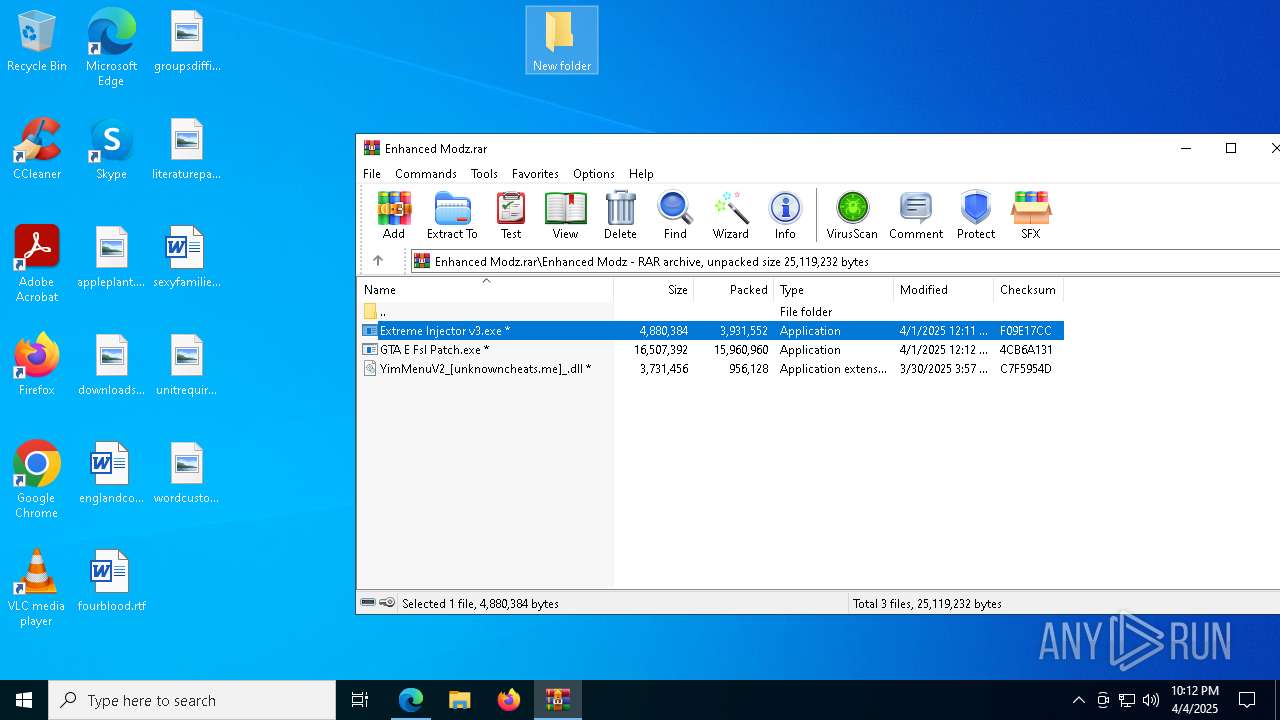
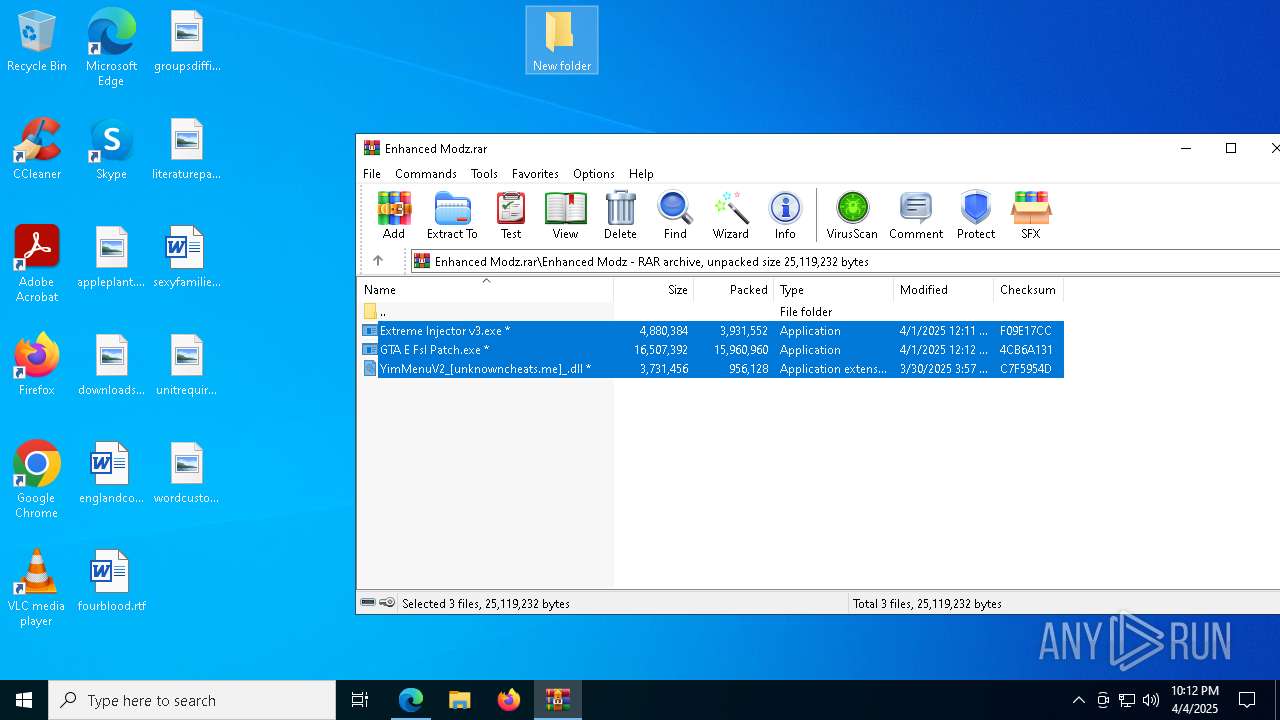
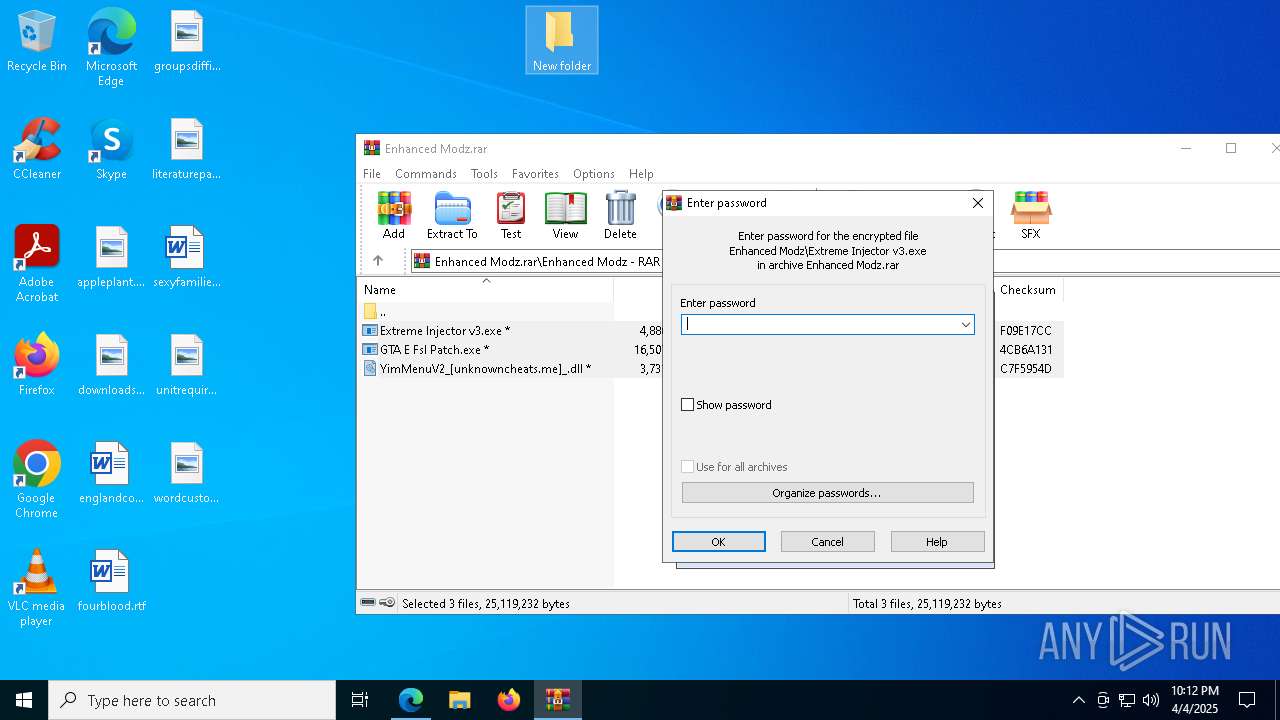
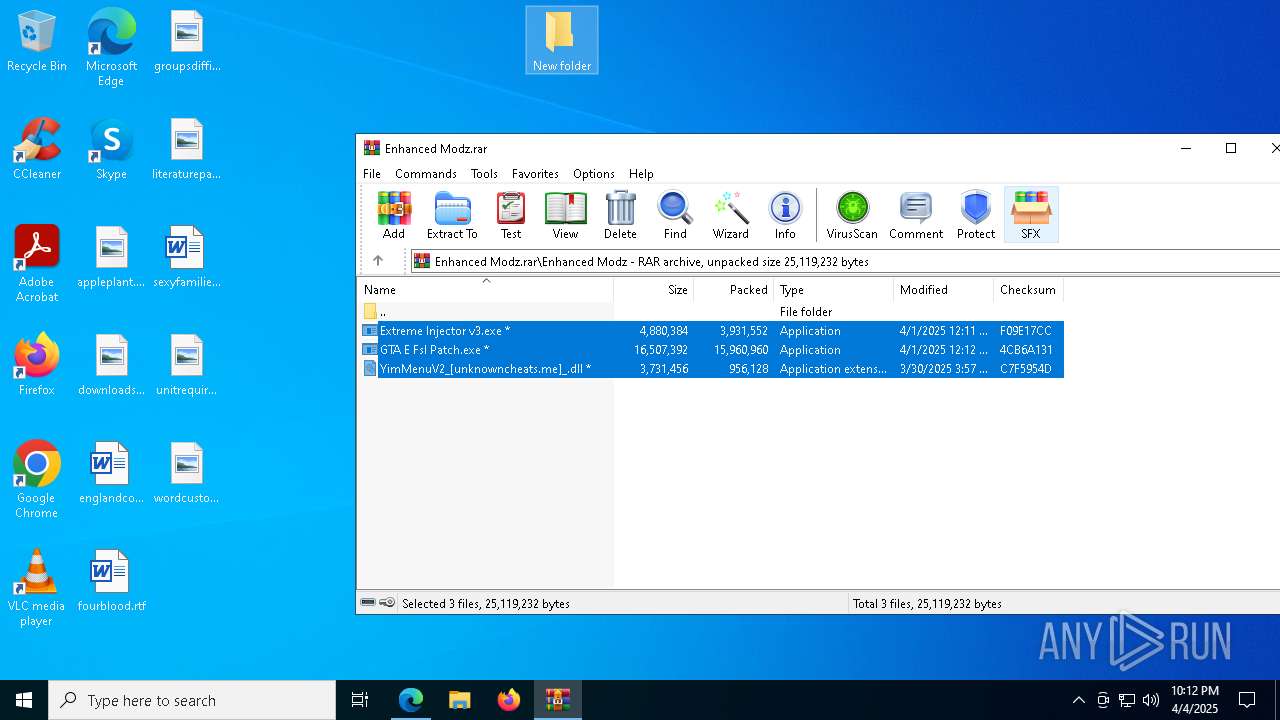
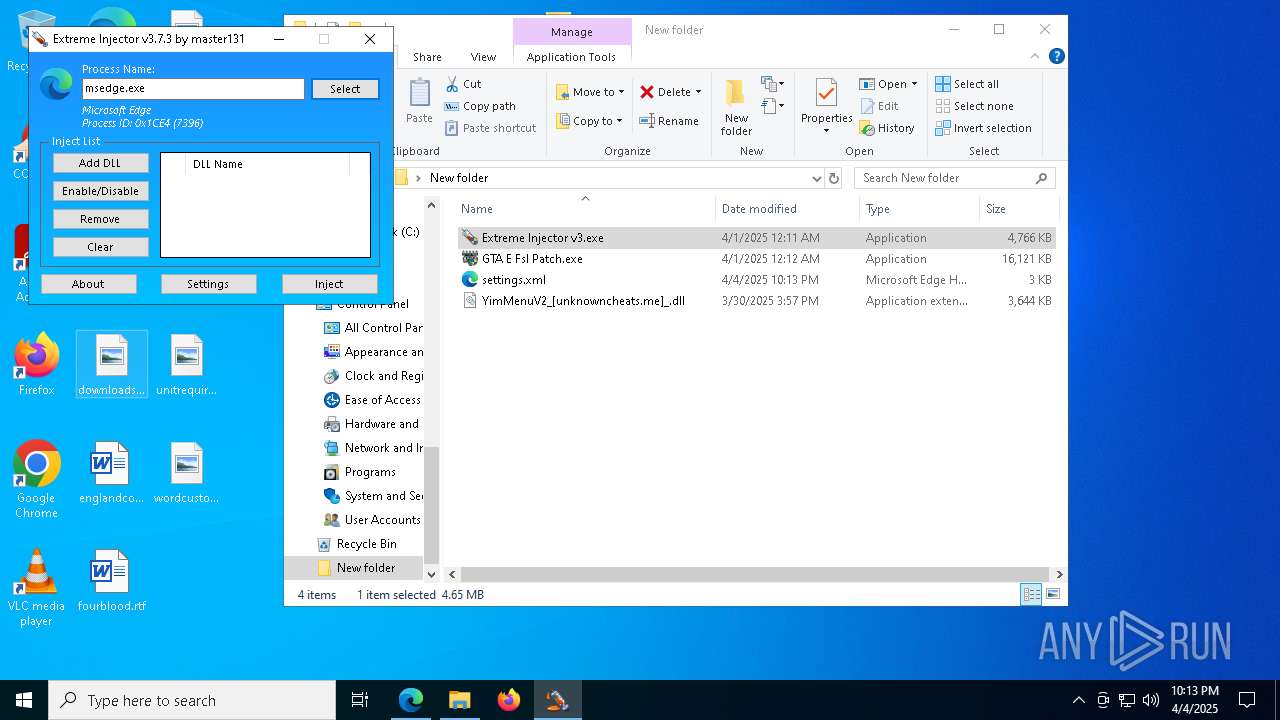
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6576)
- Extreme Injector v3.exe (PID: 4728)
- Extreme Injector v3.exe (PID: 7304)
- Extreme Injector v3.exe (PID: 4608)
- GTA E Fsl Patch.exe (PID: 5988)
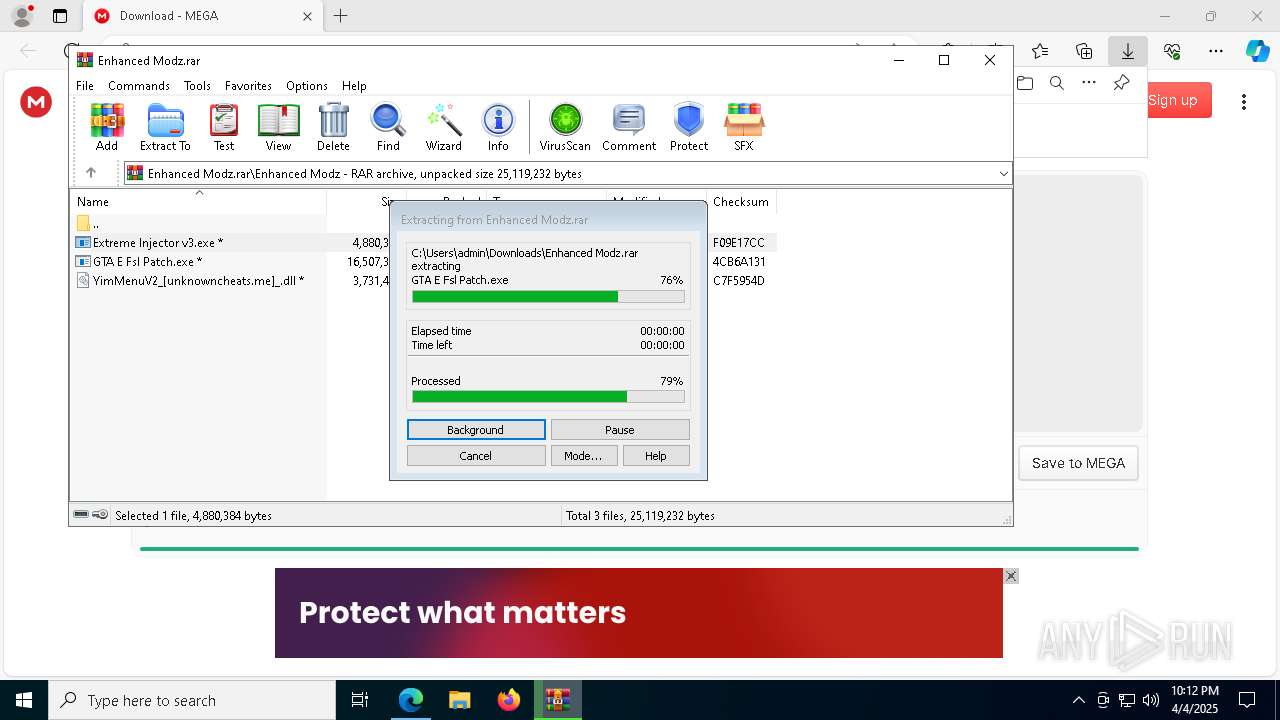
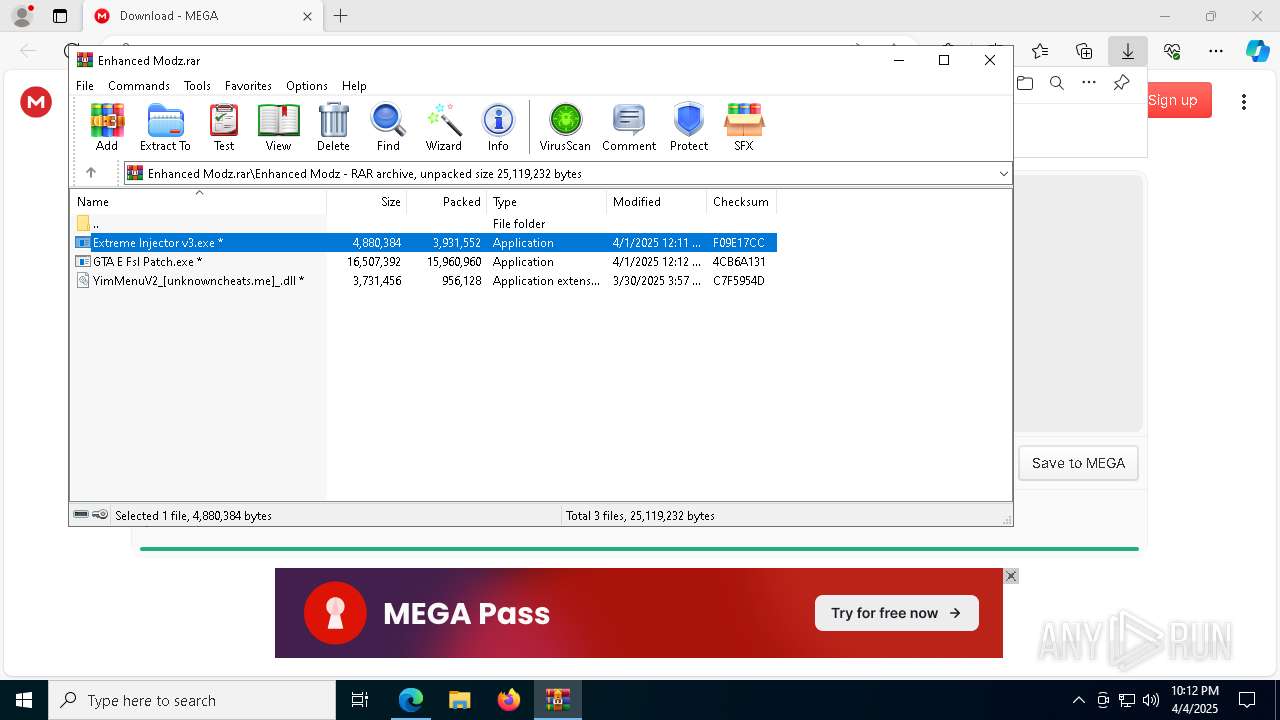
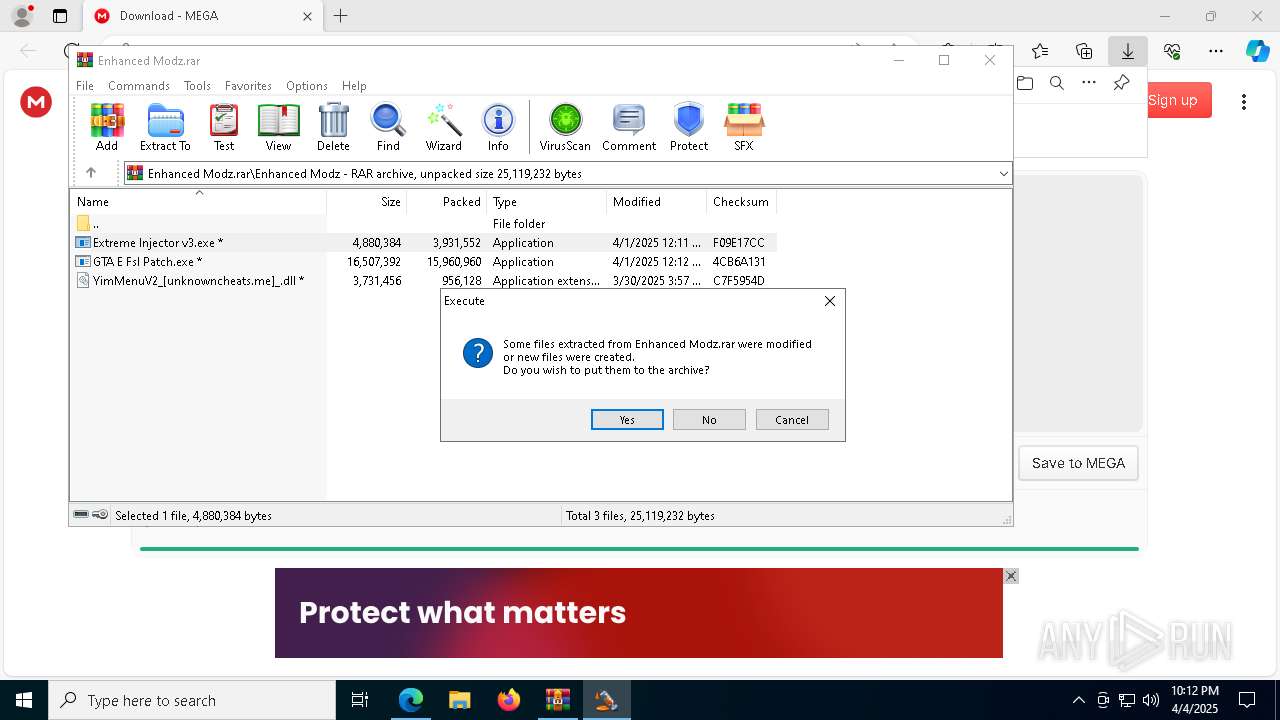
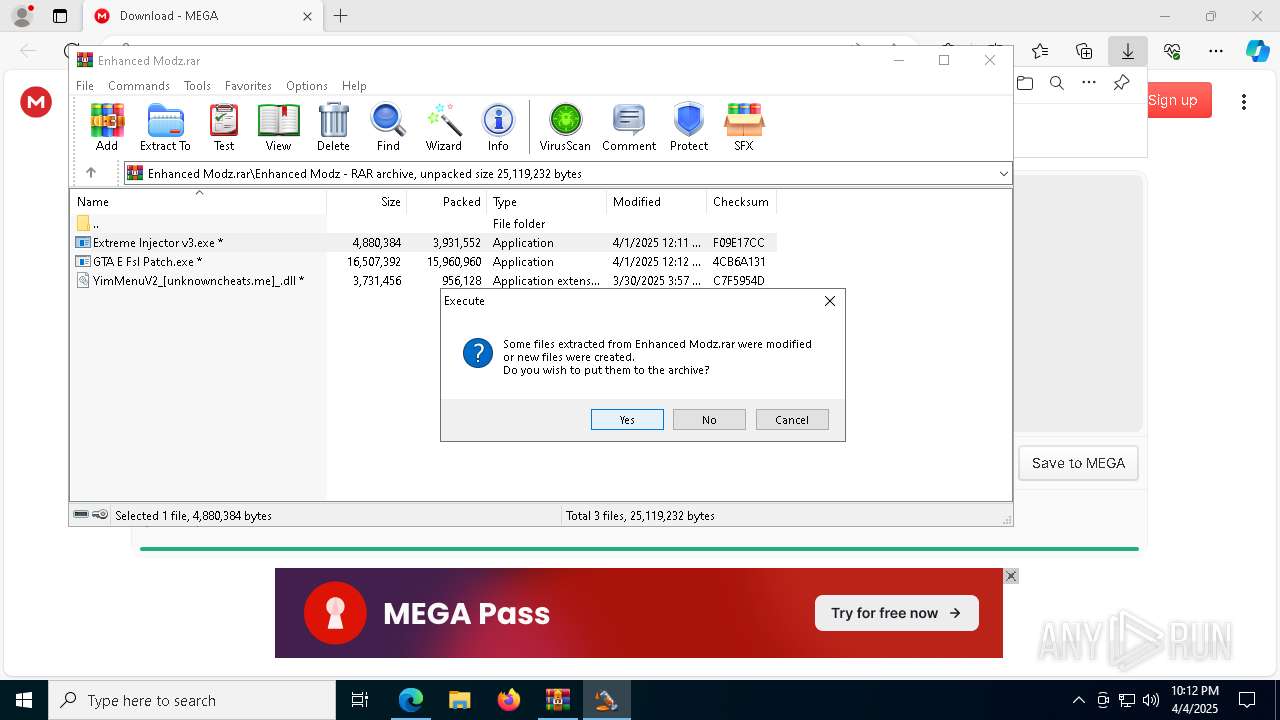
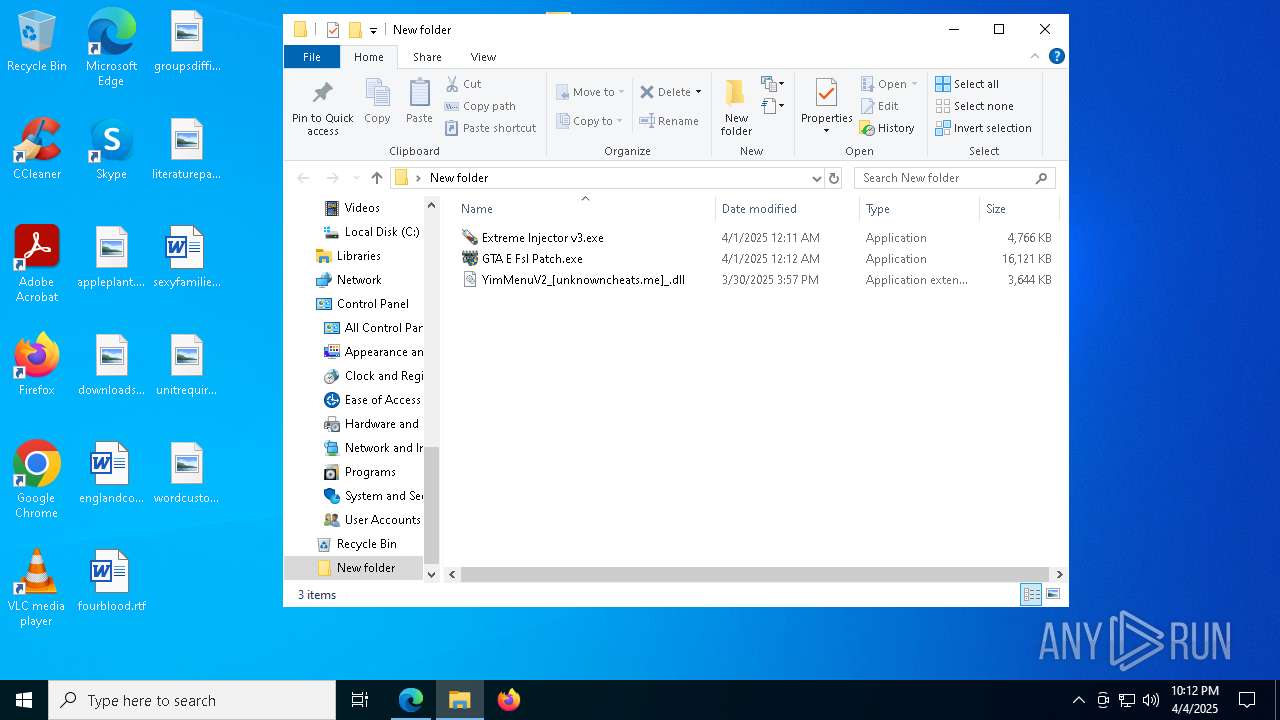
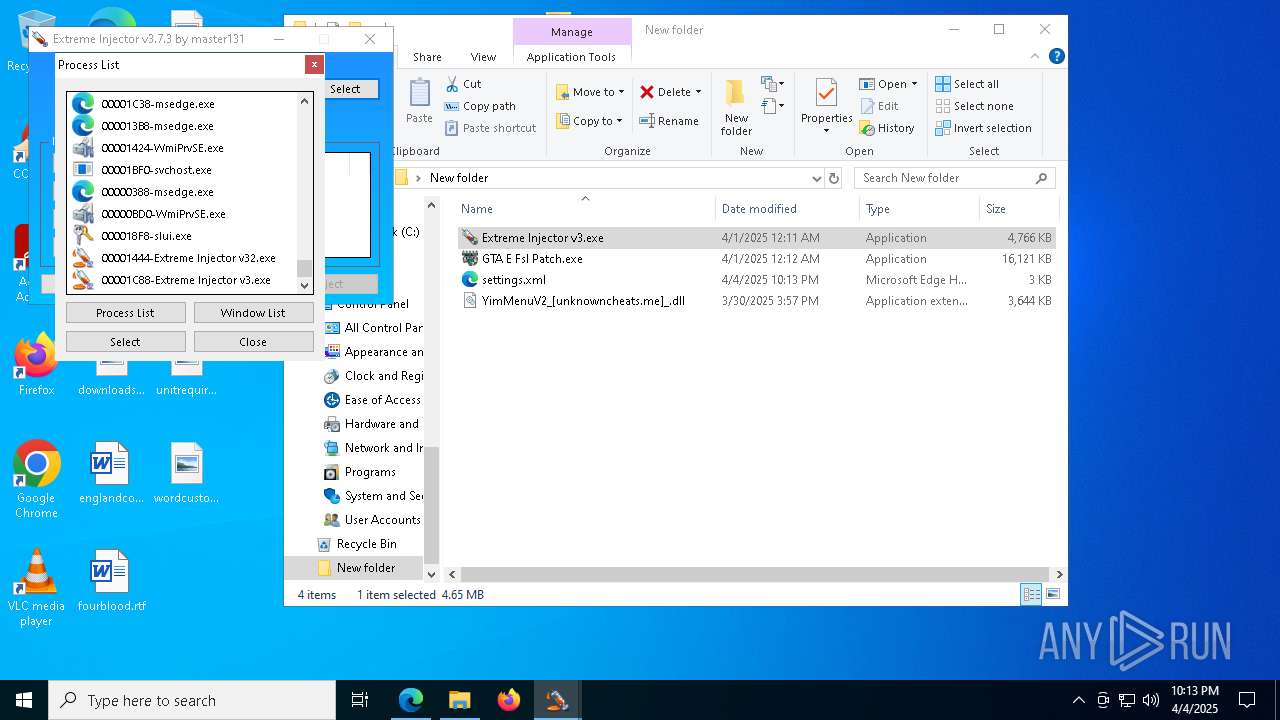
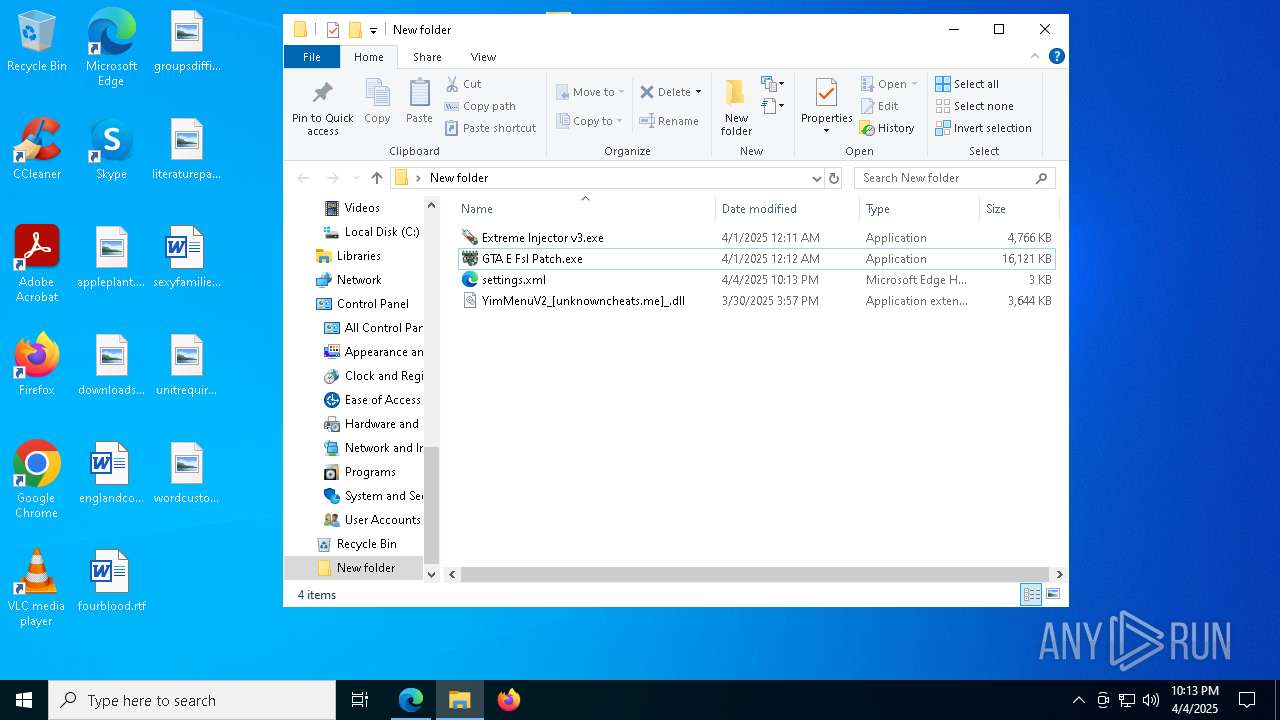
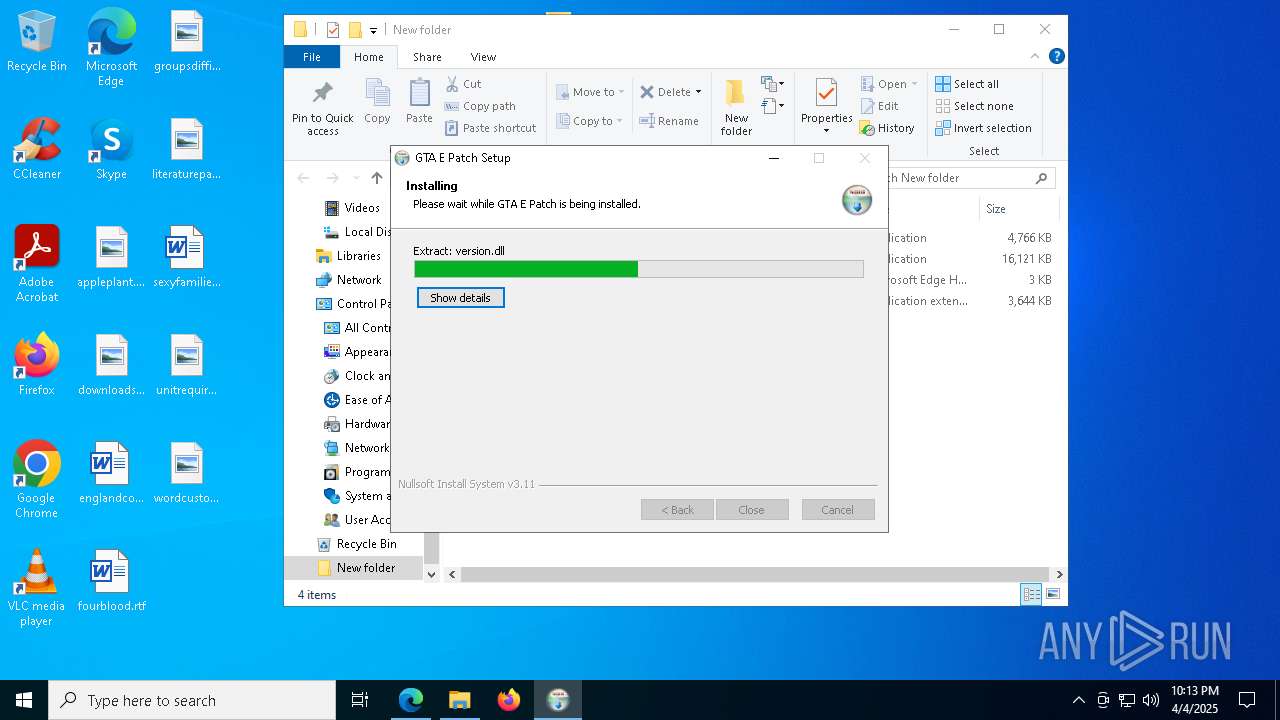
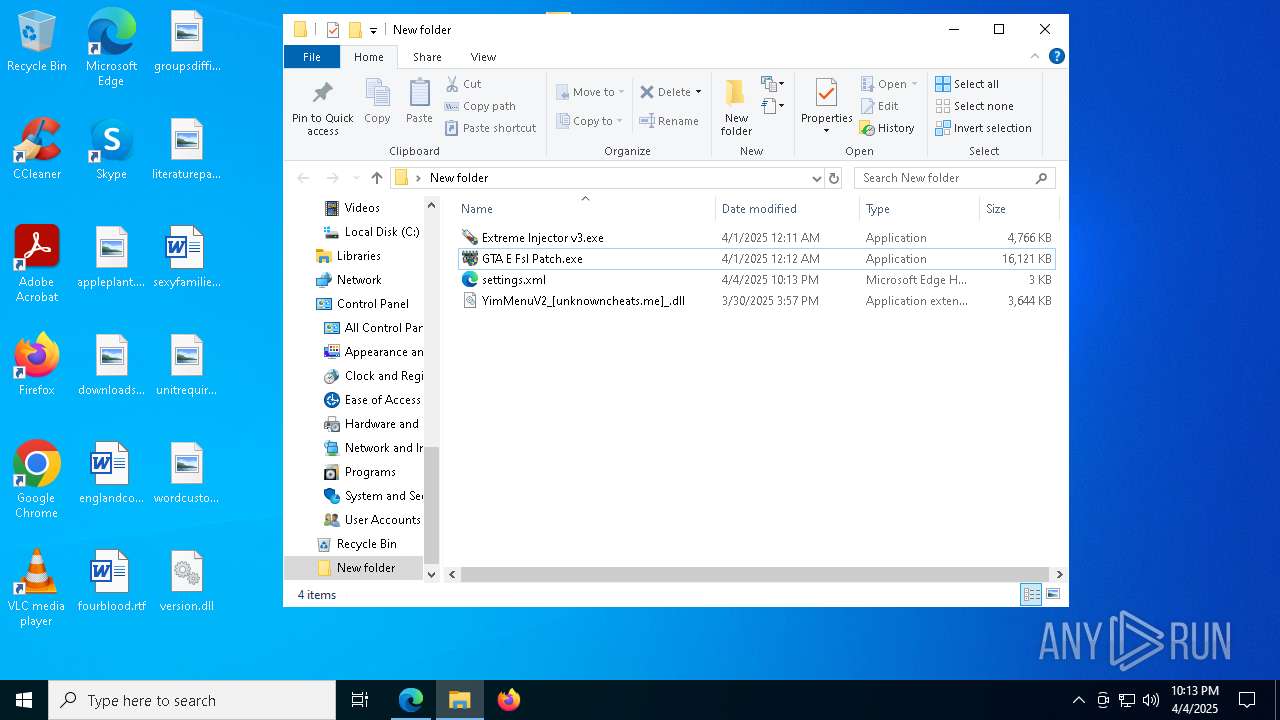
Executable content was dropped or overwritten
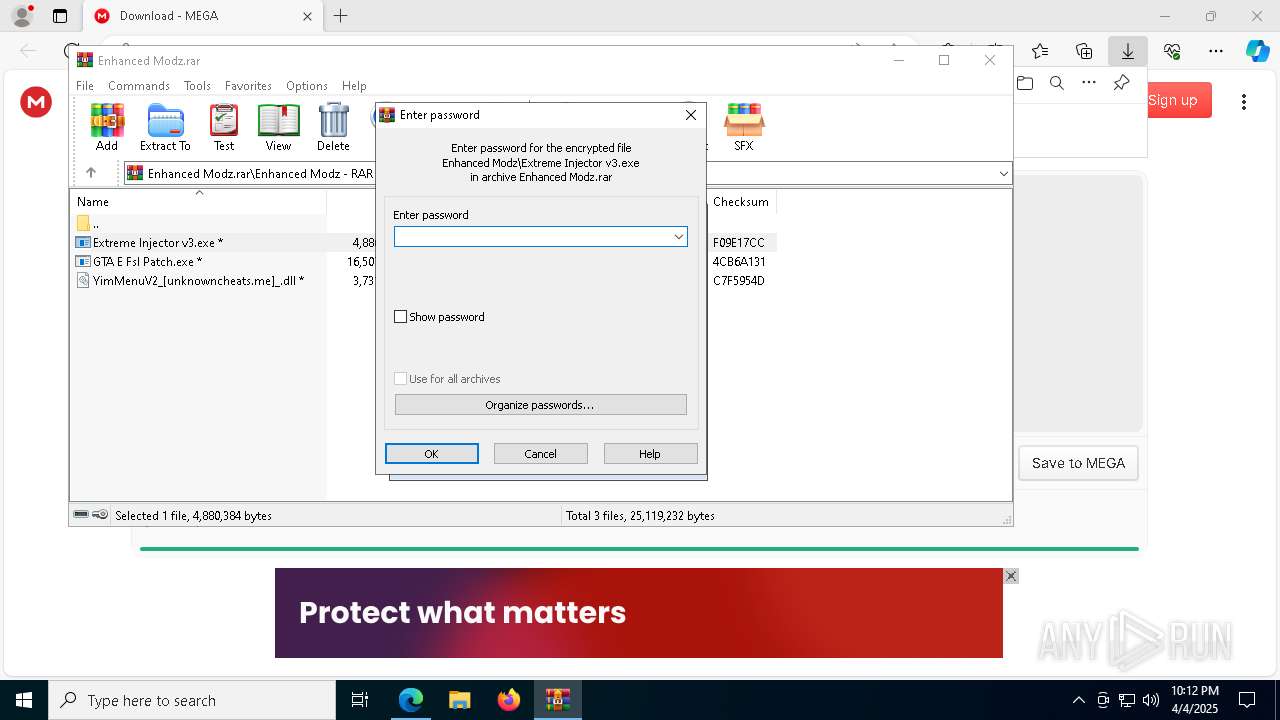
- Extreme Injector v3.exe (PID: 4728)
- Extreme Injector v32.exe (PID: 2092)
- svchost.exe (PID: 2996)
- explorer.exe (PID: 5492)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- GTA E Fsl Patch.exe (PID: 5988)
- ofmvnvzjtyqd.exe (PID: 7324)
- GTA E Fsl Patch.exe (PID: 6940)
Script adds exclusion extension to Windows Defender
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
Adds/modifies Windows certificates
- lsass.exe (PID: 756)
Script adds exclusion path to Windows Defender
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
Manipulates environment variables
- powershell.exe (PID: 6972)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 5044)
- powershell.exe (PID: 8108)
Starts POWERSHELL.EXE for commands execution
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
Starts CMD.EXE for commands execution
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
Uses powercfg.exe to modify the power settings
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
Stops a currently running service
- sc.exe (PID: 6660)
- sc.exe (PID: 6044)
- sc.exe (PID: 1628)
- sc.exe (PID: 4380)
- sc.exe (PID: 7500)
- sc.exe (PID: 6828)
- sc.exe (PID: 7212)
- sc.exe (PID: 6564)
- sc.exe (PID: 5588)
- sc.exe (PID: 4976)
- sc.exe (PID: 7212)
- sc.exe (PID: 6044)
- sc.exe (PID: 5408)
- sc.exe (PID: 1064)
- sc.exe (PID: 4100)
- sc.exe (PID: 4376)
- sc.exe (PID: 1096)
- sc.exe (PID: 7284)
- sc.exe (PID: 5980)
- sc.exe (PID: 7312)
- sc.exe (PID: 5280)
- sc.exe (PID: 4224)
Process uninstalls Windows update
- wusa.exe (PID: 6136)
- wusa.exe (PID: 2092)
- wusa.exe (PID: 6300)
- wusa.exe (PID: 5176)
Starts SC.EXE for service management
- Extreme Injector v32.exe (PID: 2092)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- ofmvnvzjtyqd.exe (PID: 7324)
Windows service management via SC.EXE
- sc.exe (PID: 2568)
- sc.exe (PID: 1096)
- sc.exe (PID: 928)
Creates a new Windows service
- sc.exe (PID: 2236)
Executes as Windows Service
- ofmvnvzjtyqd.exe (PID: 5112)
- ofmvnvzjtyqd.exe (PID: 7324)
Drops a system driver (possible attempt to evade defenses)
- ofmvnvzjtyqd.exe (PID: 5112)
- ofmvnvzjtyqd.exe (PID: 7324)
Connects to unusual port
- dialer.exe (PID: 2268)
INFO
Creates files in the program directory
- MoUsoCoreWorker.exe (PID: 5496)
- Extreme Injector v32.exe (PID: 2092)
Creates files or folders in the user directory
- lsass.exe (PID: 756)
- Extreme Injector v3.exe (PID: 4728)
- explorer.exe (PID: 5492)
Reads the computer name
- identity_helper.exe (PID: 3020)
- Extreme Injector v3.exe (PID: 4728)
- Extreme Injector v3.exe (PID: 8152)
- Extreme Injector v3.exe (PID: 7304)
- Extreme Injector v3.exe (PID: 4608)
- GTA E Fsl Patch.exe (PID: 5988)
- GTA E Fsl Patch.exe (PID: 6940)
Reads security settings of Internet Explorer
- svchost.exe (PID: 2536)
- explorer.exe (PID: 5492)
Checks supported languages
- identity_helper.exe (PID: 3020)
- Extreme Injector v3.exe (PID: 4728)
- Extreme Injector v32.exe (PID: 2092)
- Extreme Injector v3.exe (PID: 8152)
- uhssvc.exe (PID: 648)
- ofmvnvzjtyqd.exe (PID: 5112)
- Extreme Injector v32.exe (PID: 5188)
- Extreme Injector v3.exe (PID: 7304)
- Extreme Injector v3.exe (PID: 4608)
- ofmvnvzjtyqd.exe (PID: 7324)
- GTA E Fsl Patch.exe (PID: 5988)
- Extreme Injector v32.exe (PID: 8152)
- GTA E Fsl Patch.exe (PID: 6940)
Reads the software policy settings
- lsass.exe (PID: 756)
- Extreme Injector v3.exe (PID: 8152)
- slui.exe (PID: 6456)
- Extreme Injector v3.exe (PID: 7304)
- consent.exe (PID: 8116)
- consent.exe (PID: 472)
- slui.exe (PID: 6392)
Reads Environment values
- identity_helper.exe (PID: 3020)
- Extreme Injector v3.exe (PID: 8152)
- Extreme Injector v3.exe (PID: 7304)
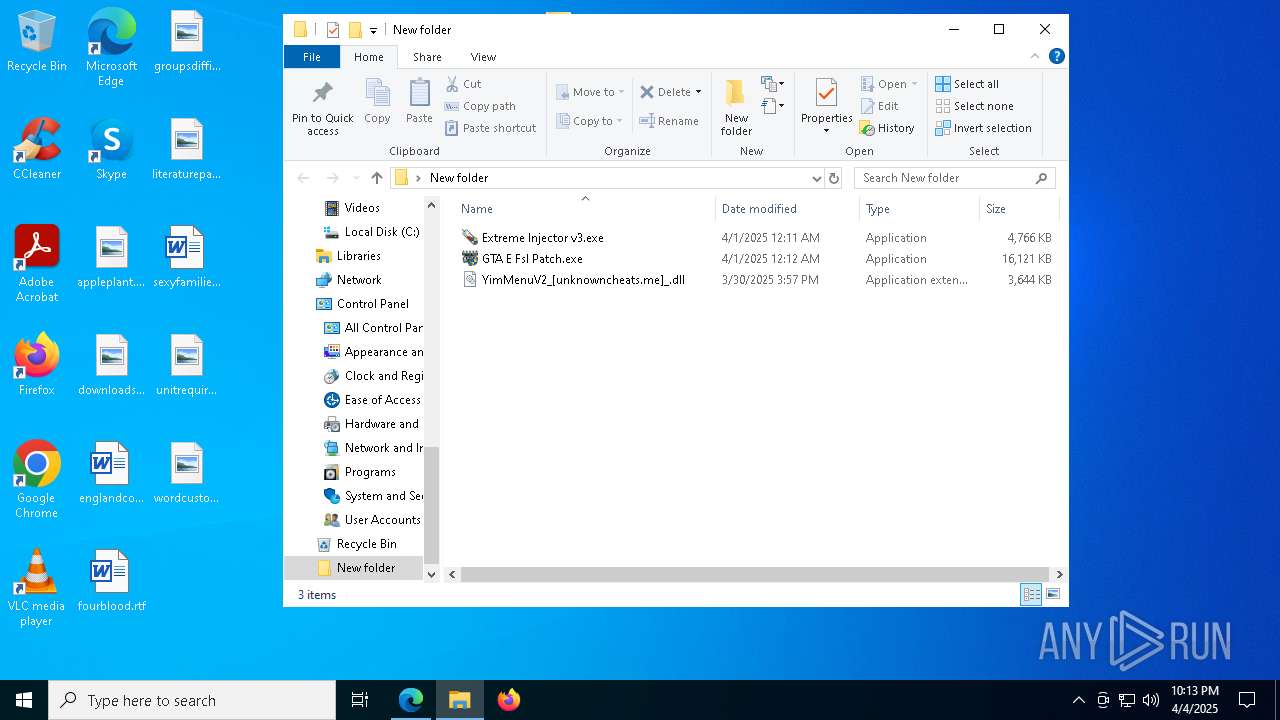
Autorun file from Downloads
- msedge.exe (PID: 6148)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7396)
- OfficeClickToRun.exe (PID: 3112)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6576)
Reads the time zone
- WmiPrvSE.exe (PID: 5156)
- MoUsoCoreWorker.exe (PID: 5496)
- svchost.exe (PID: 2396)
Process checks computer location settings
- Extreme Injector v3.exe (PID: 4728)
- Extreme Injector v3.exe (PID: 4608)
- GTA E Fsl Patch.exe (PID: 5988)
Create files in a temporary directory
- Extreme Injector v3.exe (PID: 8152)
- Extreme Injector v3.exe (PID: 4728)
- svchost.exe (PID: 4692)
- Extreme Injector v3.exe (PID: 4608)
- GTA E Fsl Patch.exe (PID: 5988)
Checks proxy server information
- Extreme Injector v3.exe (PID: 8152)
- Extreme Injector v3.exe (PID: 7304)
- slui.exe (PID: 6392)
Reads the machine GUID from the registry
- Extreme Injector v3.exe (PID: 8152)
- Extreme Injector v3.exe (PID: 7304)
Disables trace logs
- Extreme Injector v3.exe (PID: 8152)
- Extreme Injector v3.exe (PID: 7304)
The sample compiled with english language support
- WinRAR.exe (PID: 6576)
- svchost.exe (PID: 2996)
- explorer.exe (PID: 5492)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6972)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 5044)
- powershell.exe (PID: 8108)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6972)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 5044)
- powershell.exe (PID: 8108)
Application launched itself
- msedge.exe (PID: 7396)
The sample compiled with japanese language support
- ofmvnvzjtyqd.exe (PID: 5112)
- ofmvnvzjtyqd.exe (PID: 7324)
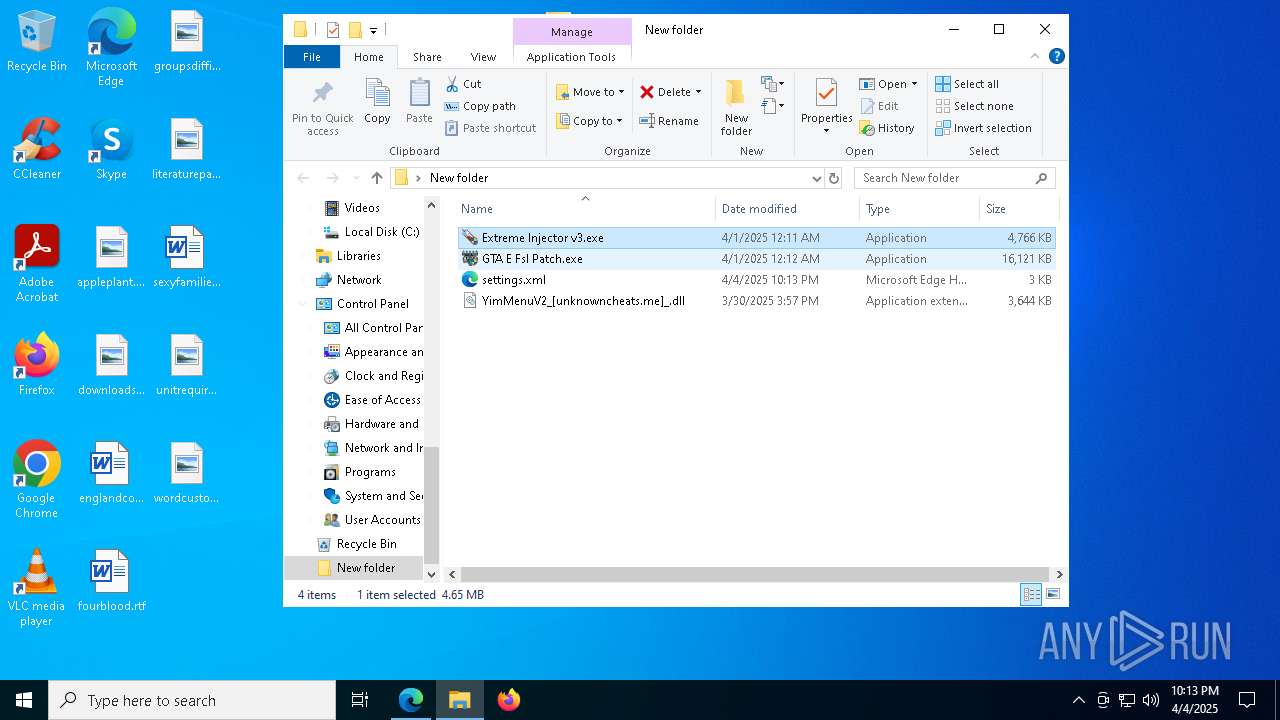
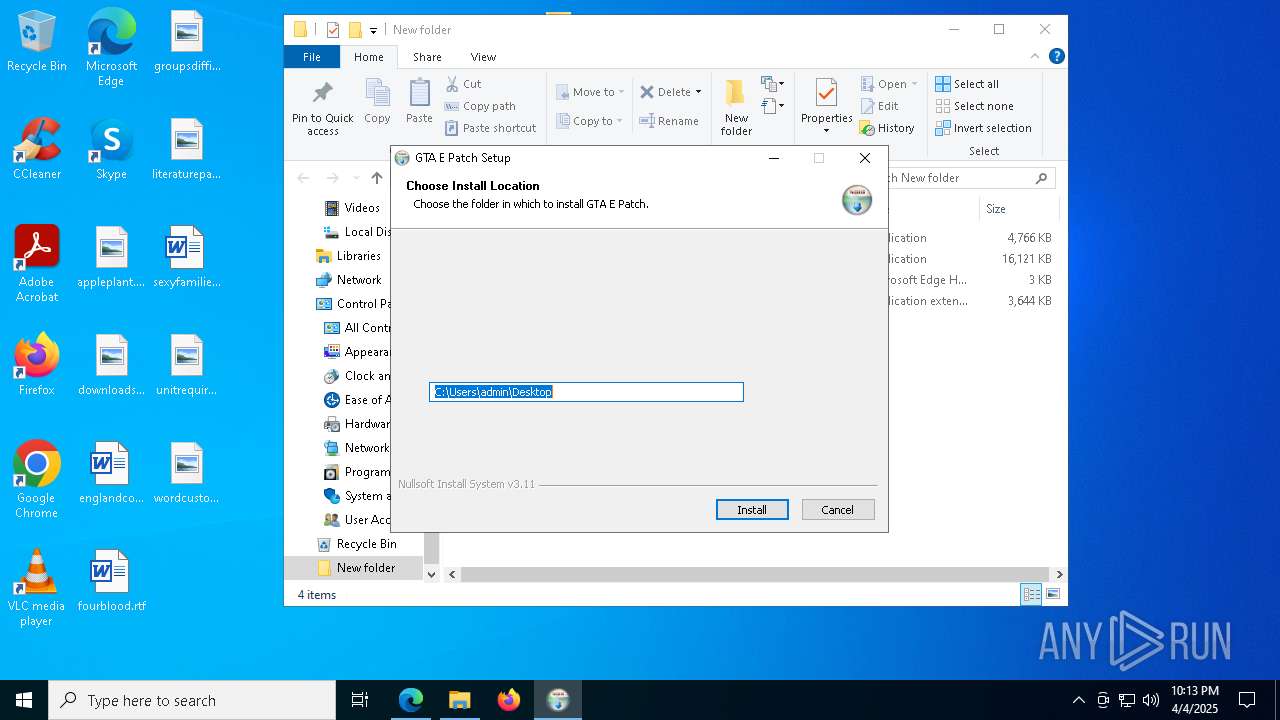
Manual execution by a user
- Extreme Injector v3.exe (PID: 776)
- Extreme Injector v3.exe (PID: 4608)
- GTA E Fsl Patch.exe (PID: 1628)
- GTA E Fsl Patch.exe (PID: 5988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
318
Monitored processes
272
Malicious processes
104
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | Extreme Injector v32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 468 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | consent.exe 4916 444 0000021B57621D70 | C:\Windows\System32\consent.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7956 --field-trial-handle=2416,i,16615261550615635135,13559014759043353983,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Microsoft Update Health Tools\uhssvc.exe" | C:\Program Files\Microsoft Update Health Tools\uhssvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Update Health Service Version: 10.0.19041.3626 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\system32\cmd.exe /c wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\cmd.exe | — | ofmvnvzjtyqd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | ofmvnvzjtyqd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
86 539
Read events
85 478
Write events
766
Delete events
295
Modification events
| (PID) Process: | (5496) MoUsoCoreWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsUpdate\Orchestrator |
| Operation: | delete value | Name: | EnhancedShutdownEnabled |
Value: | |||
| (PID) Process: | (5496) MoUsoCoreWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsUpdate\Orchestrator |
| Operation: | write | Name: | ShutdownFlyoutOptions |
Value: 0 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:000000000003024E |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000030264 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (7396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2112) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Orchestrator |
| Operation: | write | Name: | Preshutdown |
Value: 0 | |||
| (PID) Process: | (1260) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\UpdateOrchestrator |
| Operation: | write | Name: | SD |
Value: 0100049C5C000000680000000000000014000000020048000300000000001400FF011F0001010000000000051200000000001400A900120001010000000000051300000000001800A900120001020000000000052000000020020000010100000000000512000000010100000000000512000000 | |||
Executable files
39
Suspicious files
419
Text files
93
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b49c.TMP | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b46d.TMP | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b4cb.TMP | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b49c.TMP | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b4cb.TMP | — | |
MD5:— | SHA256:— | |||
| 7396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
169
DNS requests
86
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5544 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1744039857&P2=404&P3=2&P4=bURG4WfTsc6k7SlFtLDIenAP08cdWdluUiIUpazygFOwF7FkFYom64qU1Xy2QurPSg2f2f24v7cwLmYuU4Qc9A%3d%3d | unknown | — | — | whitelisted |
5544 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1744039857&P2=404&P3=2&P4=bURG4WfTsc6k7SlFtLDIenAP08cdWdluUiIUpazygFOwF7FkFYom64qU1Xy2QurPSg2f2f24v7cwLmYuU4Qc9A%3d%3d | unknown | — | — | whitelisted |
4692 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1744039857&P2=404&P3=2&P4=bURG4WfTsc6k7SlFtLDIenAP08cdWdluUiIUpazygFOwF7FkFYom64qU1Xy2QurPSg2f2f24v7cwLmYuU4Qc9A%3d%3d | unknown | — | — | whitelisted |
4692 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1744096095&P2=404&P3=2&P4=nZHTLroDspk2vryi5DJQHut%2fm7v9UpltYJYMM%2fbd83ZpdmRddH6yRVEybPG%2fyiNVhywDaYa3QVJy8MXmxKpmBw%3d%3d | unknown | — | — | whitelisted |
7680 | msedge.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1744039857&P2=404&P3=2&P4=bURG4WfTsc6k7SlFtLDIenAP08cdWdluUiIUpazygFOwF7FkFYom64qU1Xy2QurPSg2f2f24v7cwLmYuU4Qc9A%3d%3d | unknown | — | — | whitelisted |
4692 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1744096095&P2=404&P3=2&P4=nZHTLroDspk2vryi5DJQHut%2fm7v9UpltYJYMM%2fbd83ZpdmRddH6yRVEybPG%2fyiNVhywDaYa3QVJy8MXmxKpmBw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7396 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7680 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7680 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7680 | msedge.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
7680 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
mega.nz |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7680 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7680 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |