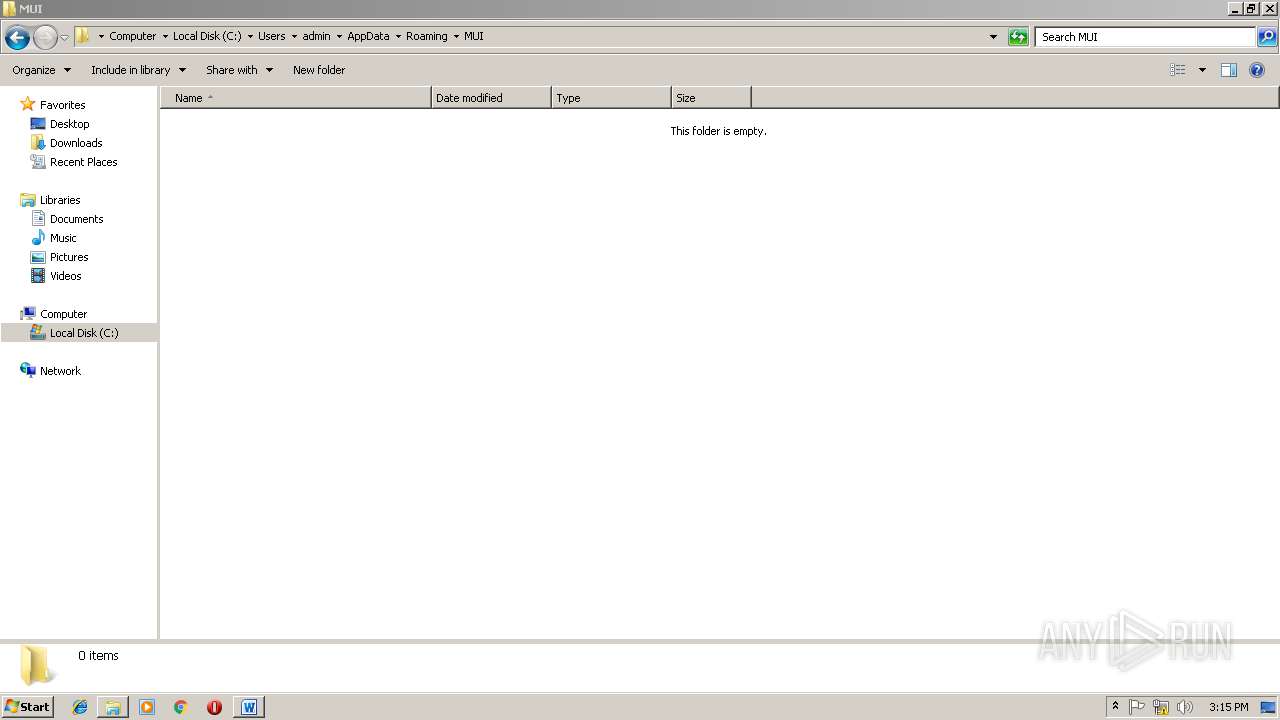
| File name: | 7c50f42fc4df44918d5b200b3ede38be5342286a08c6acc30e01d4b74b2014a5 |
| Full analysis: | https://app.any.run/tasks/9522ceb7-3b4b-40db-9ab3-112f4a379549 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 15:13:01 |
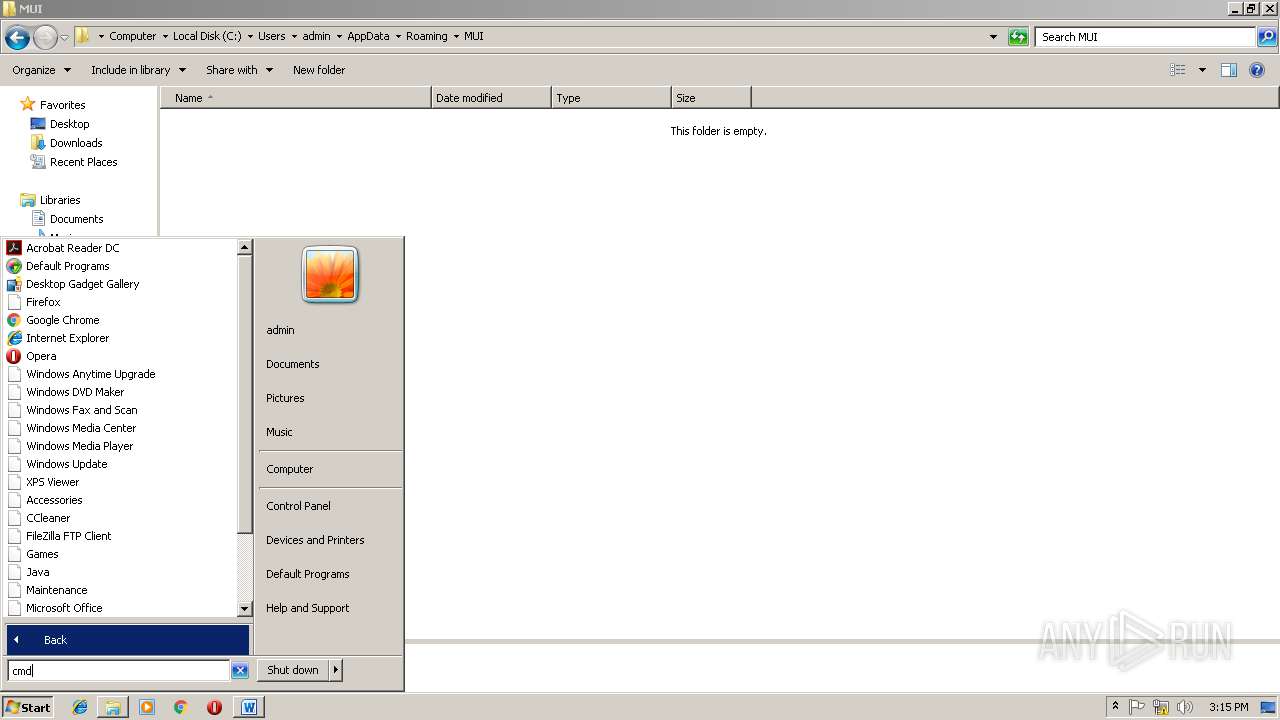
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
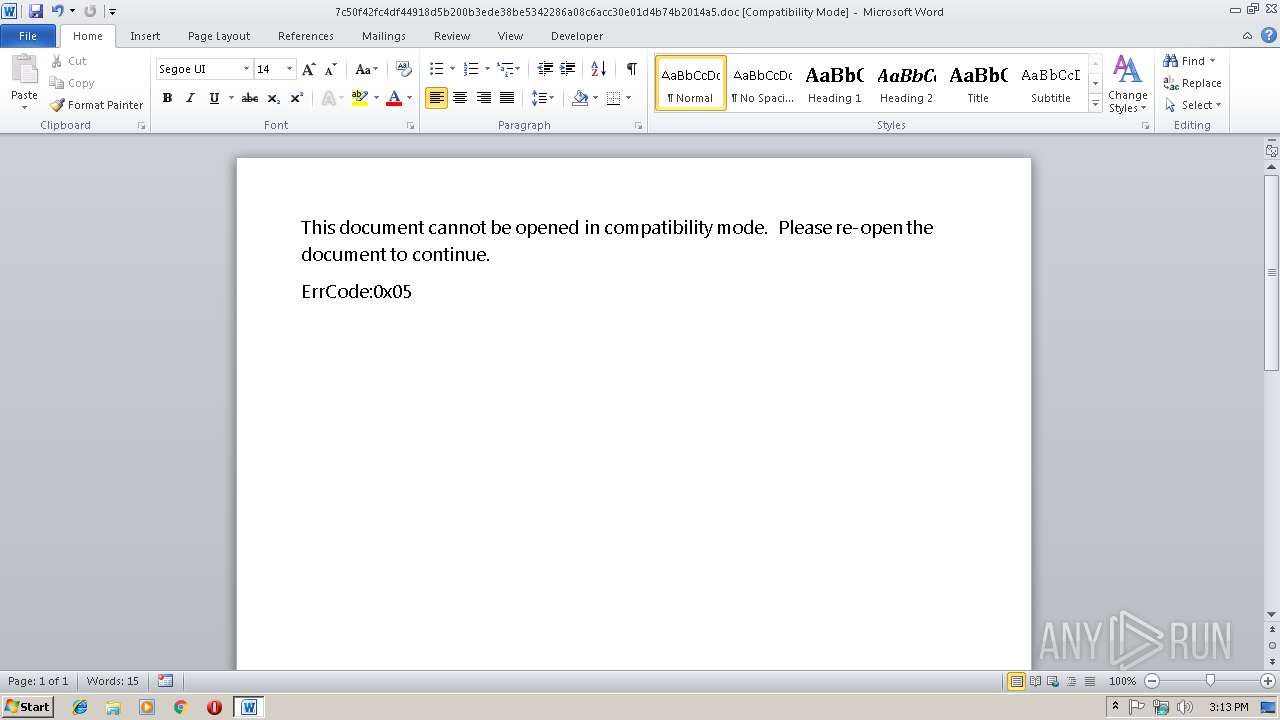
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 936, Author: John, Template: Normal.dotm, Last Saved By: Windows , Revision Number: 131, Name of Creating Application: Microsoft Office Word, Total Editing Time: 13:00, Create Time/Date: Sun Nov 25 17:35:00 2018, Last Saved Time/Date: Mon Nov 26 09:05:00 2018, Number of Pages: 1, Number of Words: 4, Number of Characters: 25, Security: 0 |
| MD5: | 862EC29AC552C70D70A6A85AC29AE38F |
| SHA1: | 05DDF9A9D057915AA2D88A7A1AB036F0395D2EFE |
| SHA256: | 7C50F42FC4DF44918D5B200B3EDE38BE5342286A08C6ACC30E01D4B74B2014A5 |
| SSDEEP: | 1536:nafUoVZy0S0ivJKC1j+oJ+mlZoh1PlbO8C7eGzjDSmPzLGtAPoWrpO:nafzVZy0SNMPQ+b1PlPuTvRJVO |
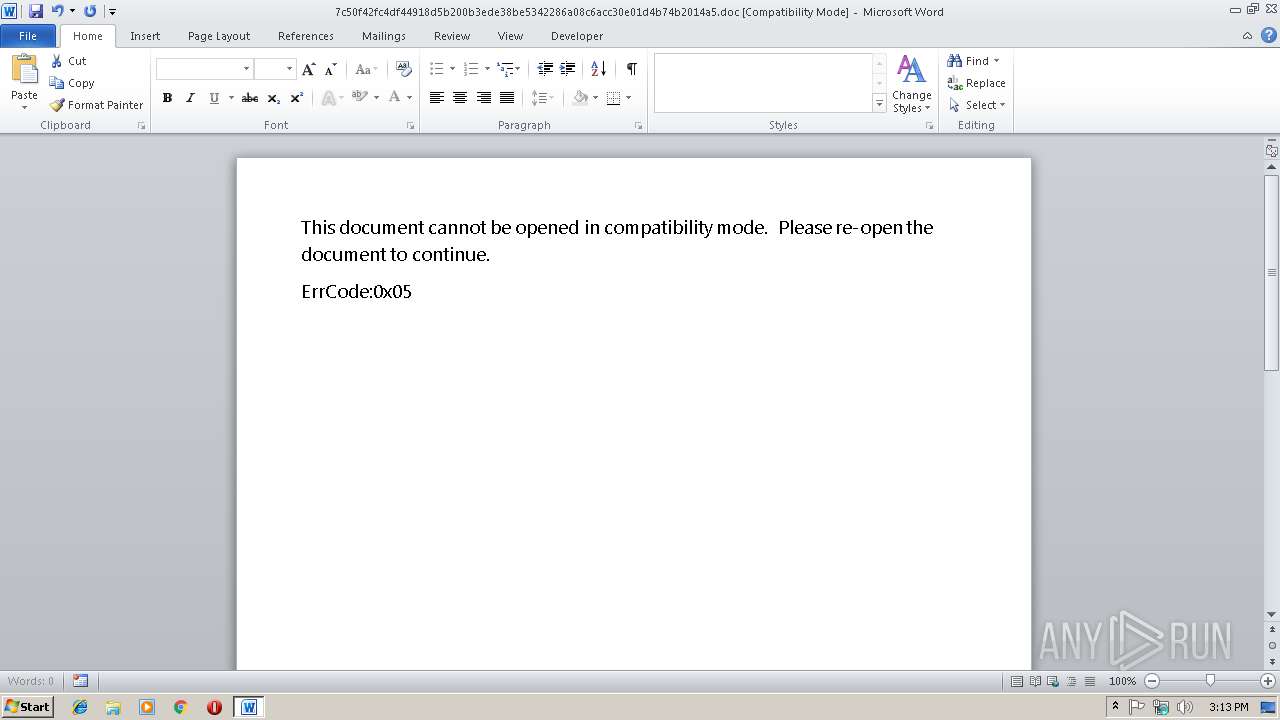
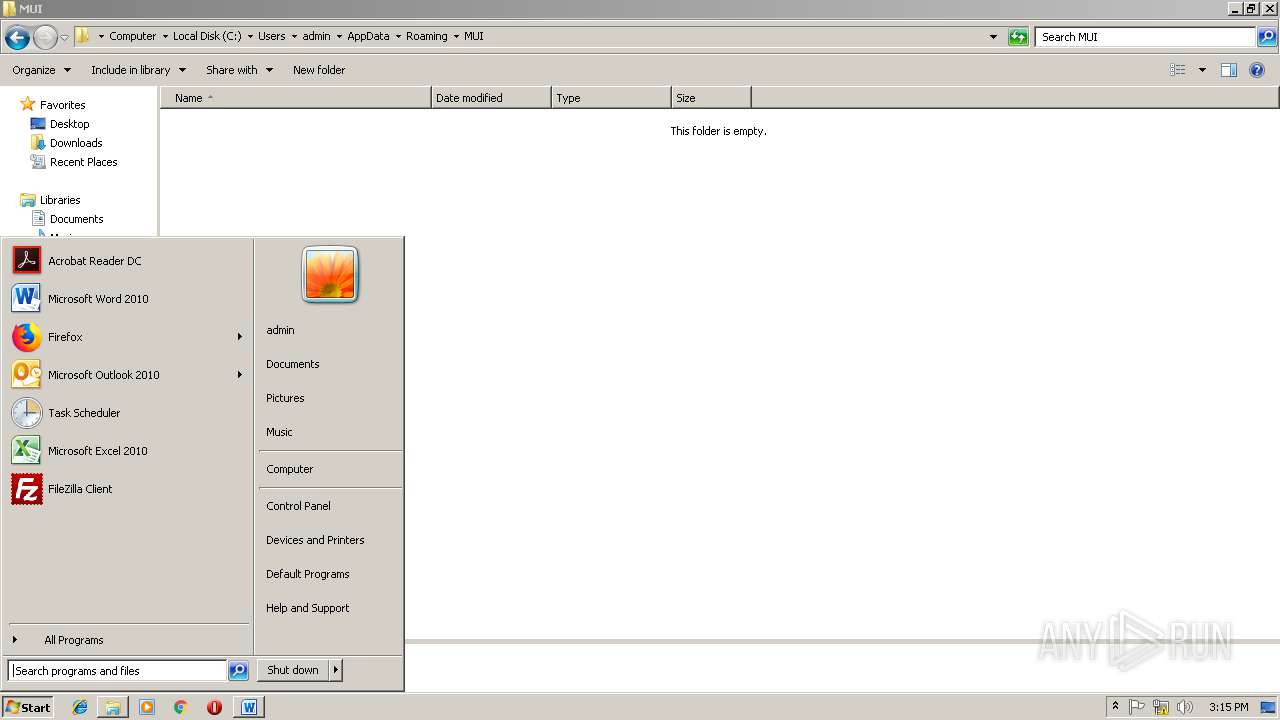
MALICIOUS
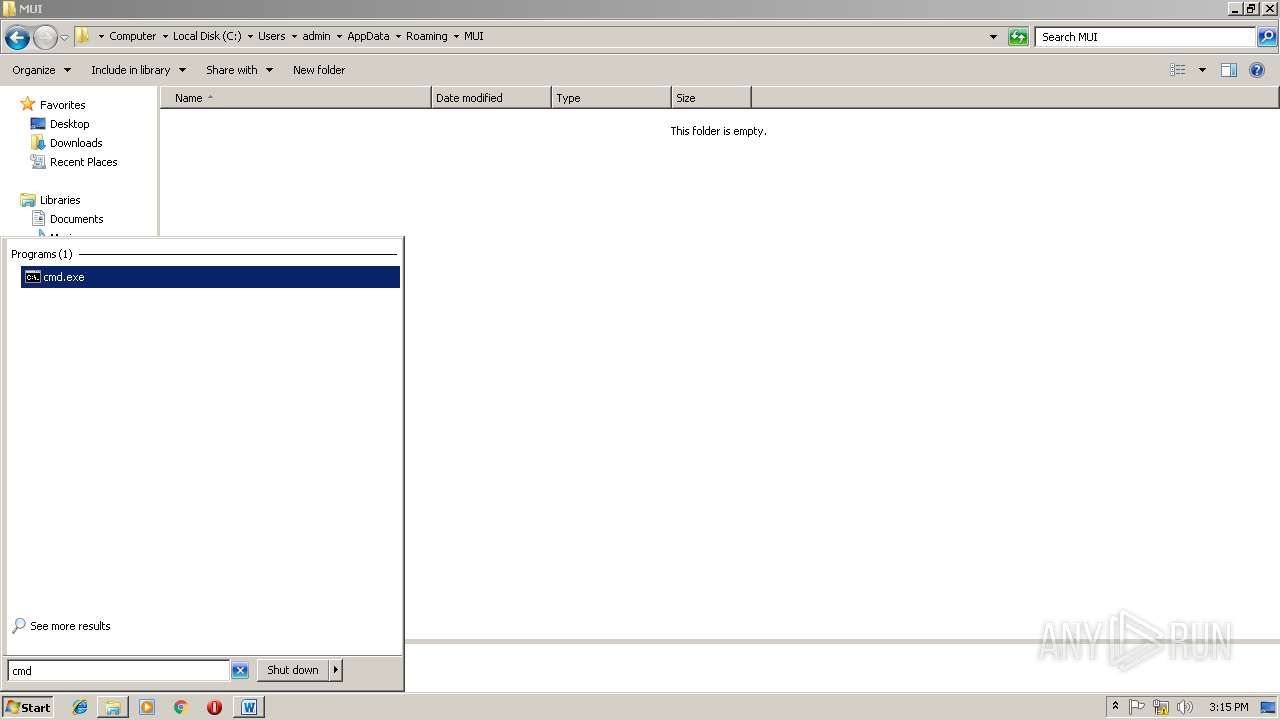
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2868)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2748)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2748)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3316)
SUSPICIOUS
No suspicious indicators.INFO
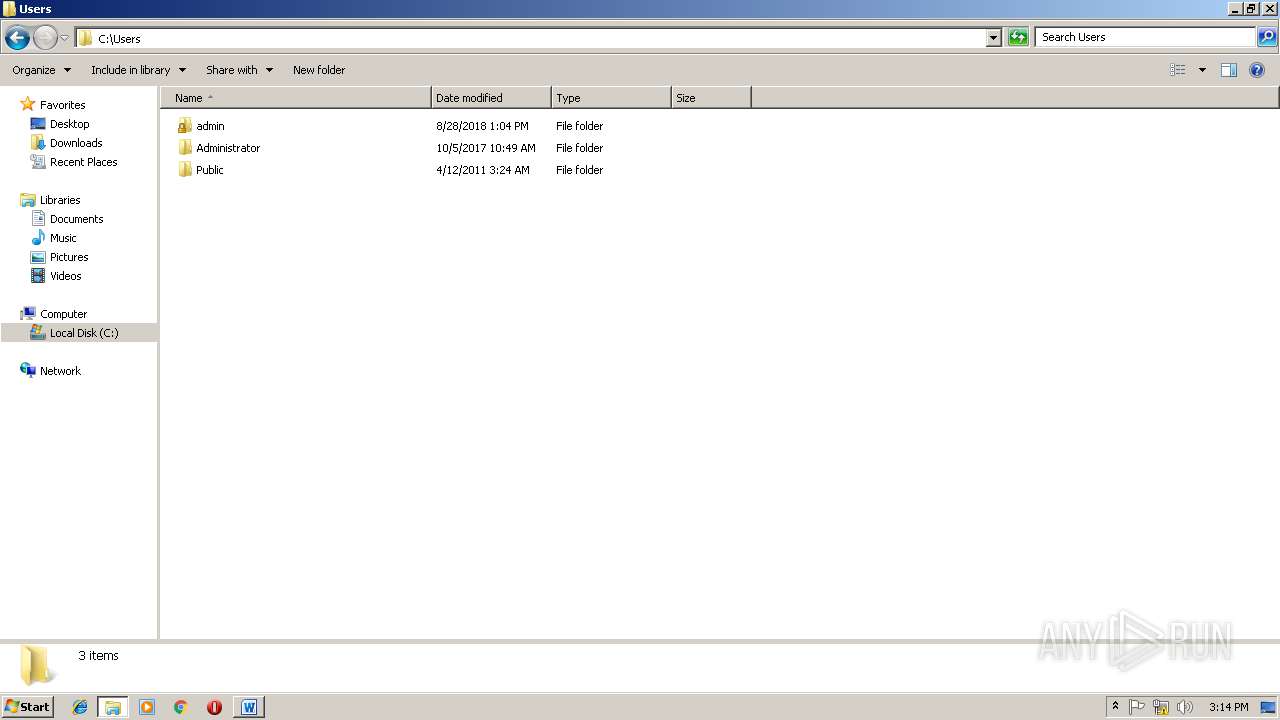
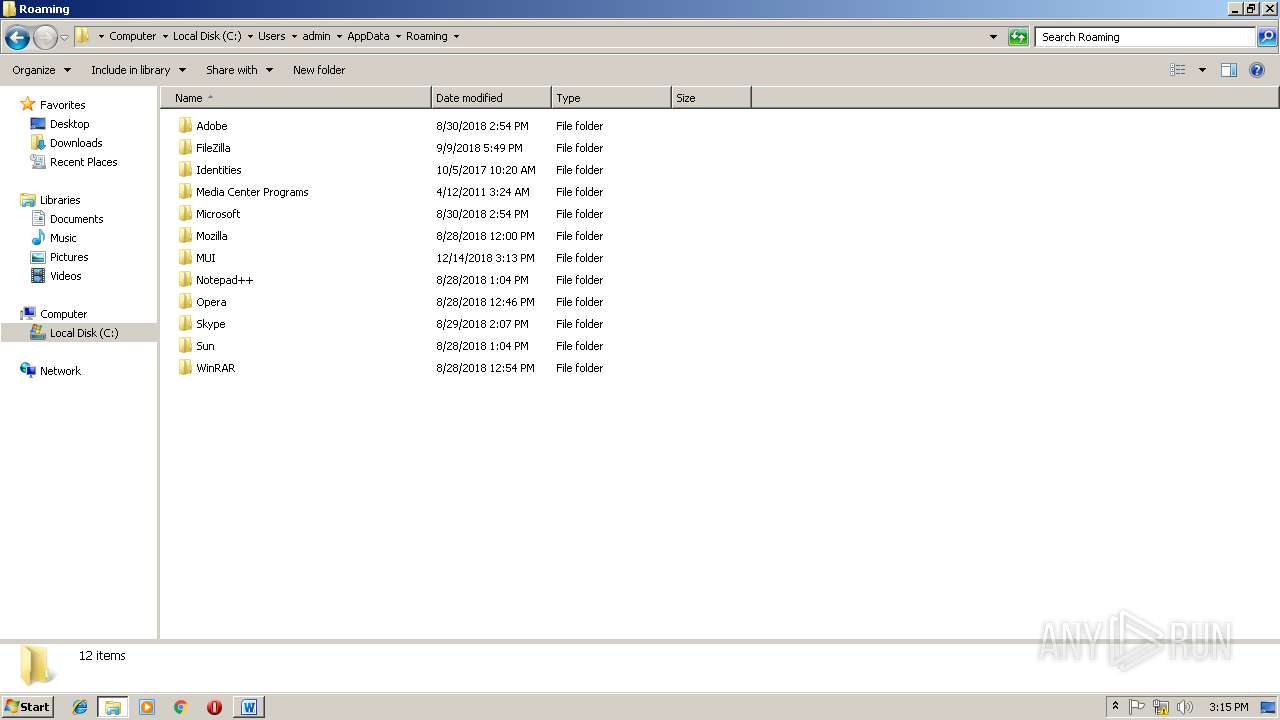
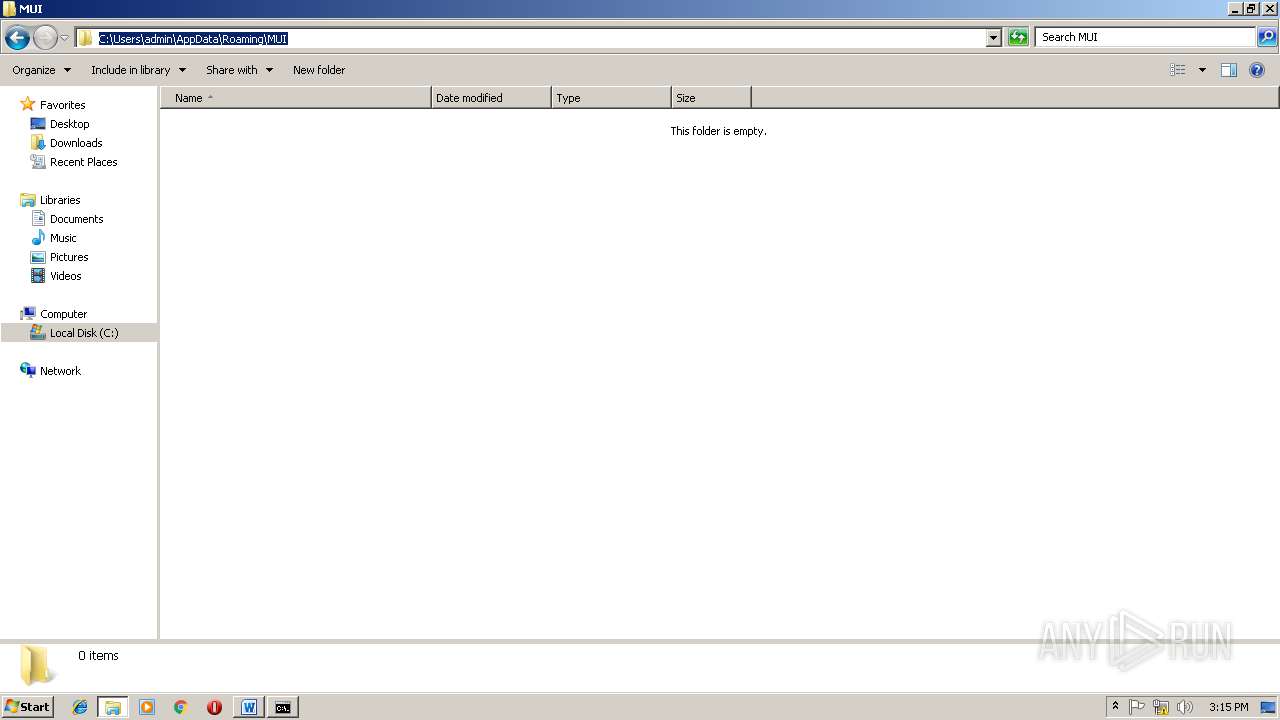
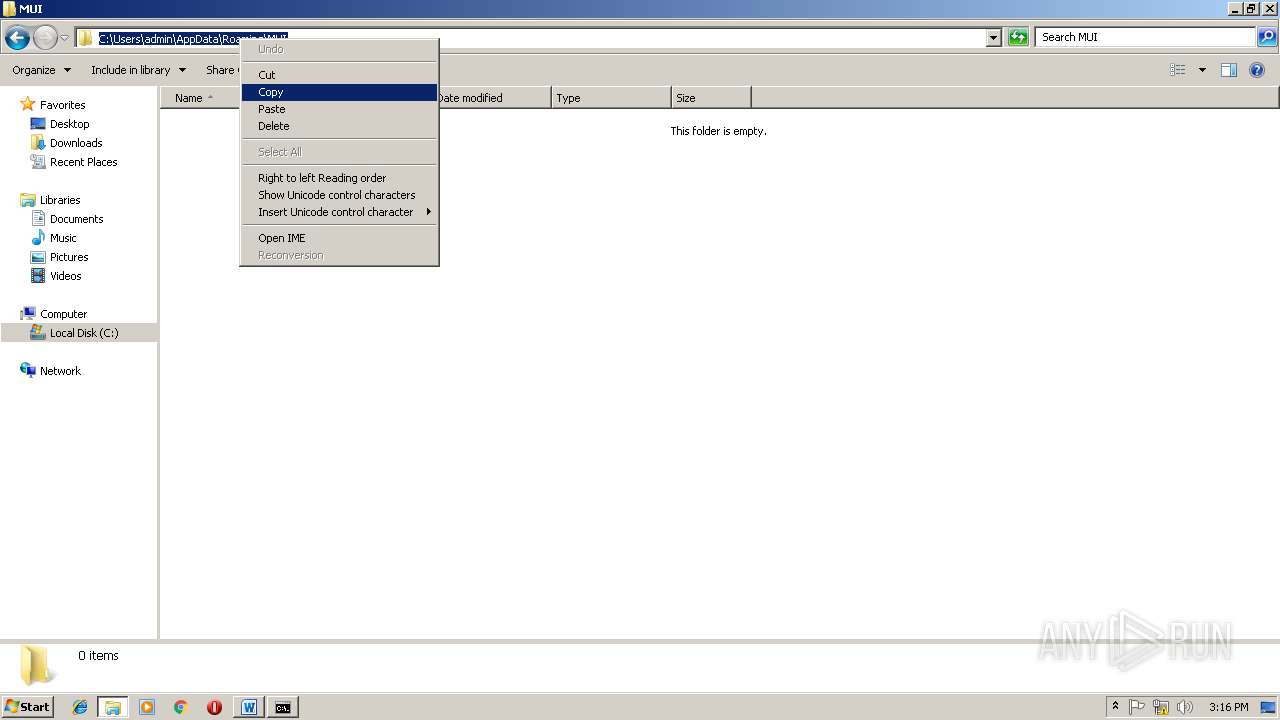
Creates files in the user directory
- WINWORD.EXE (PID: 2748)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | John |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Windows ?û? |
| RevisionNumber: | 131 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 13.0 minutes |
| CreateDate: | 2018:11:25 17:35:00 |
| ModifyDate: | 2018:11:26 09:05:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 25 |
| Security: | None |
| CodePage: | Windows Simplified Chinese (PRC, Singapore) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 28 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 28 |
| CompObjUserType: | Microsoft Word 97-2003 ?ĵ? |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2748 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\7c50f42fc4df44918d5b200b3ede38be5342286a08c6acc30e01d4b74b2014a5.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
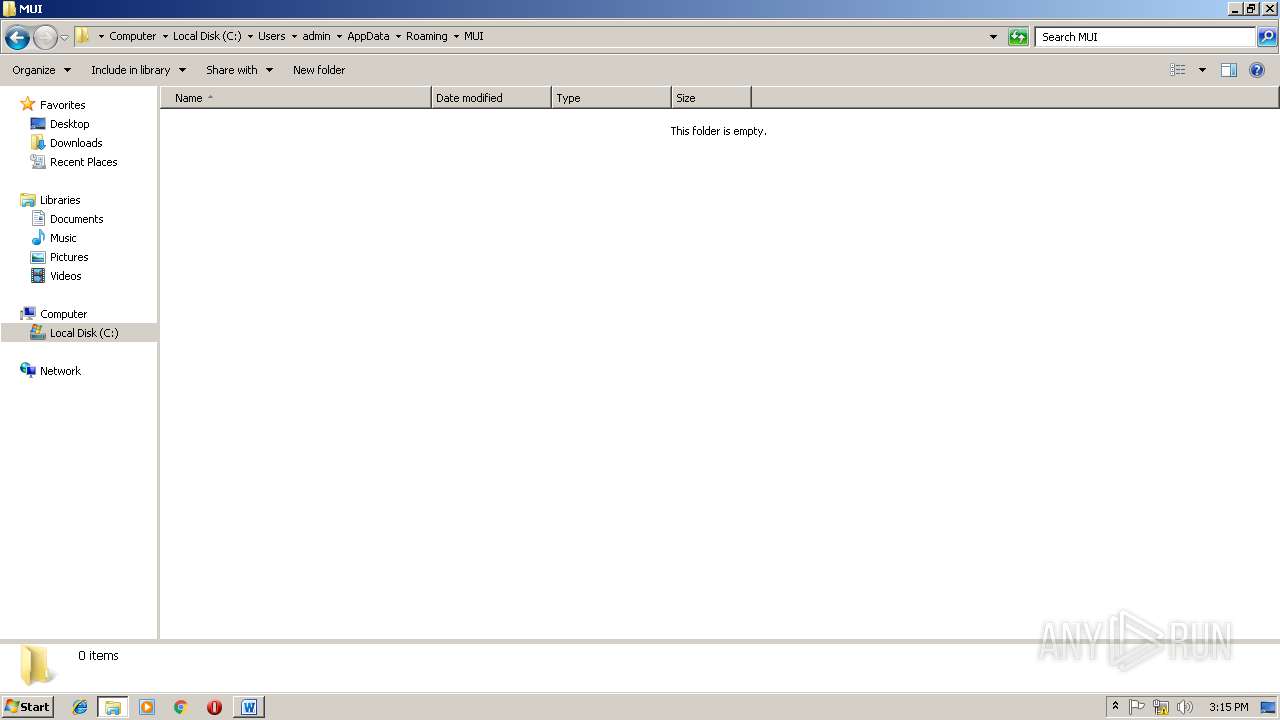
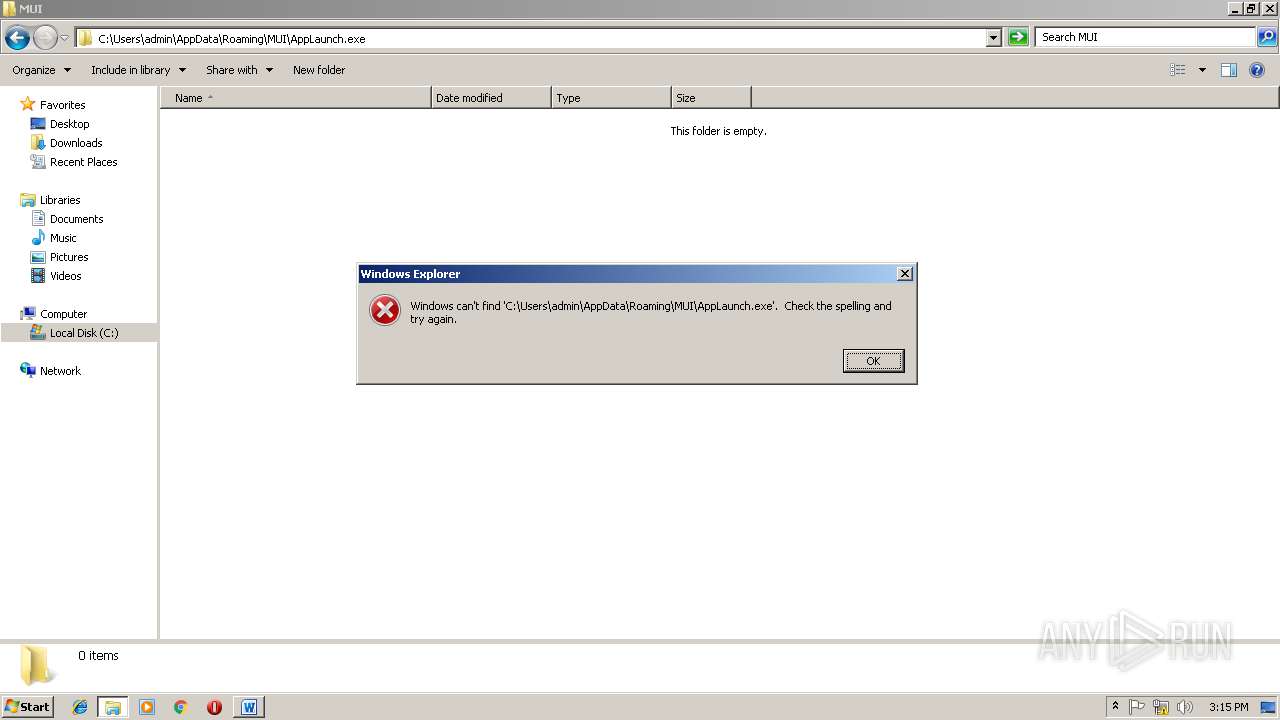
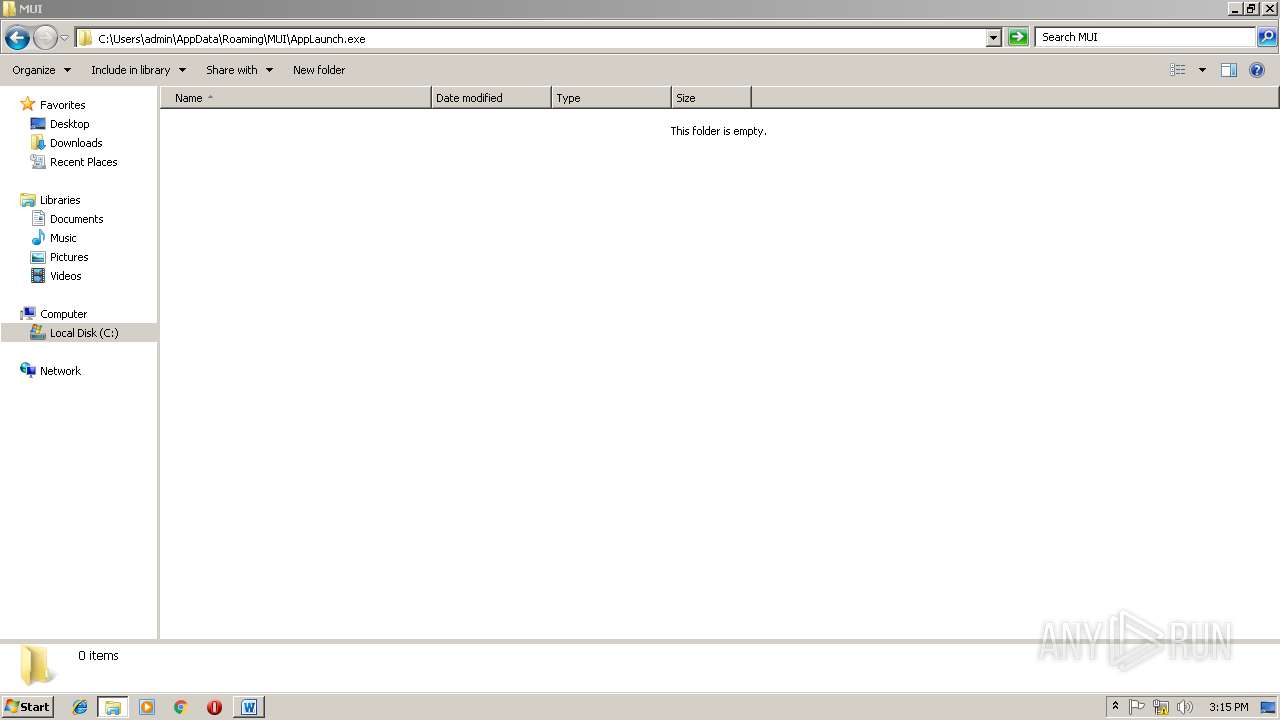
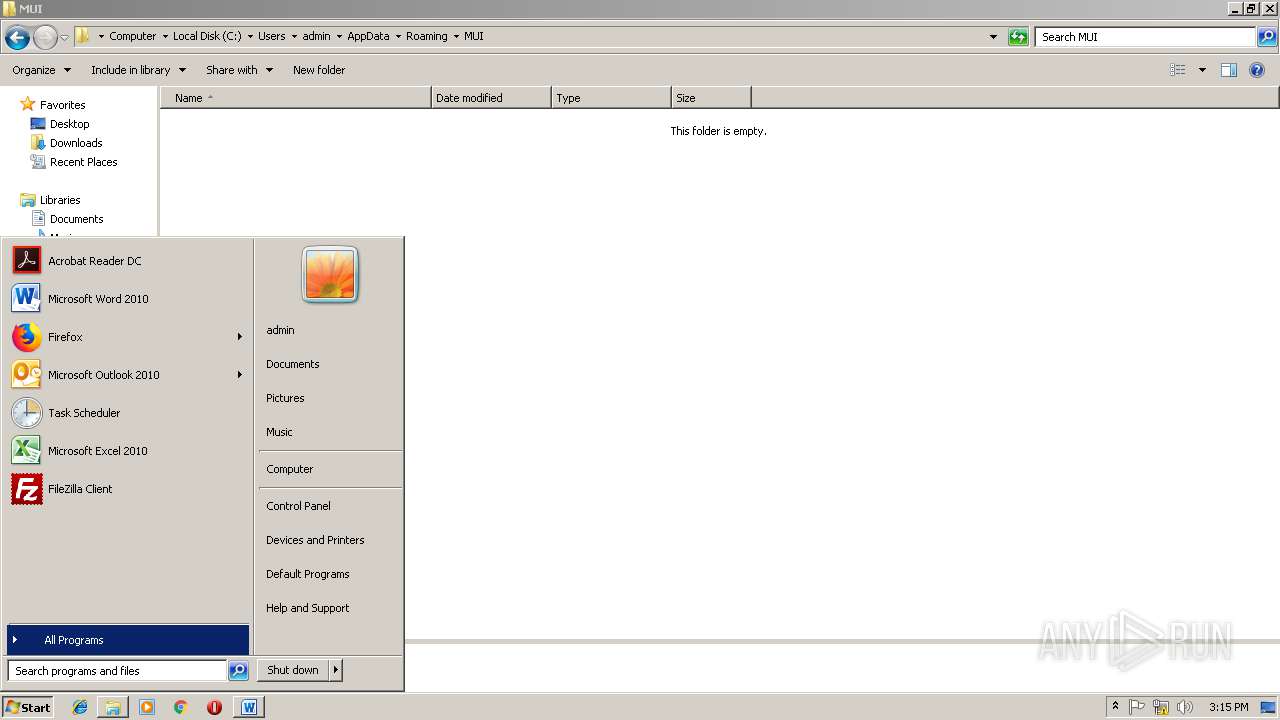
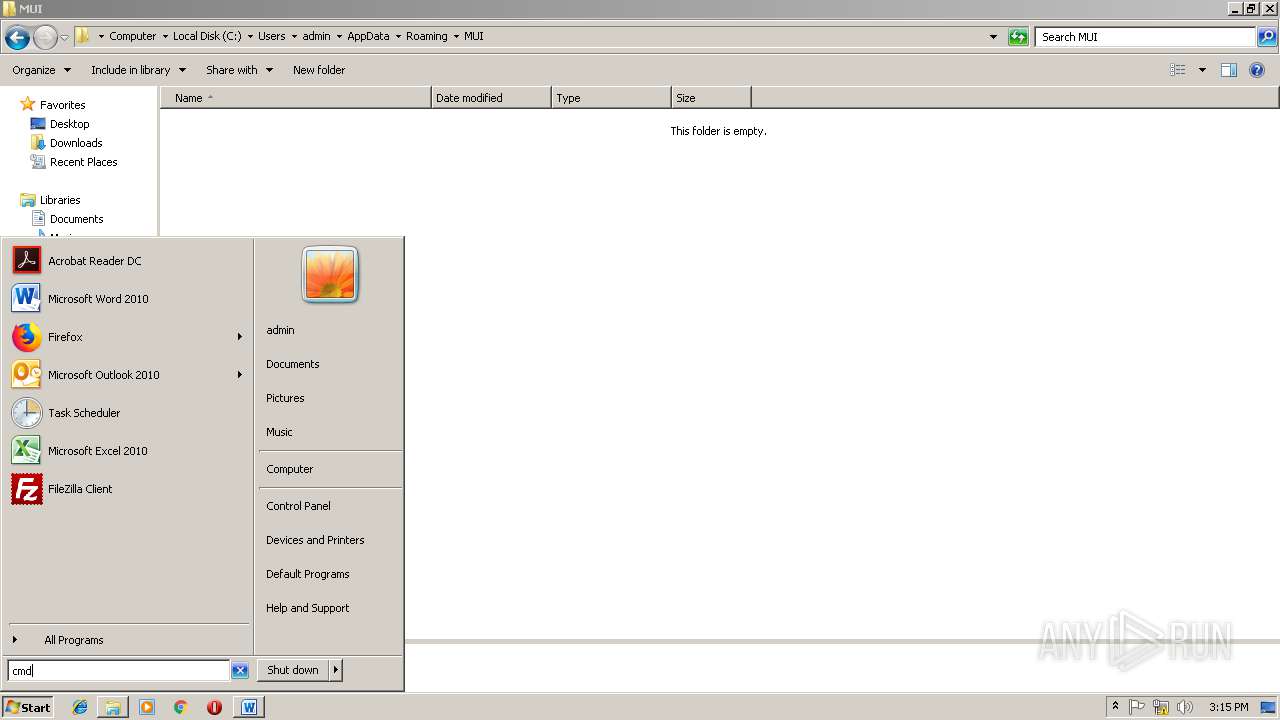
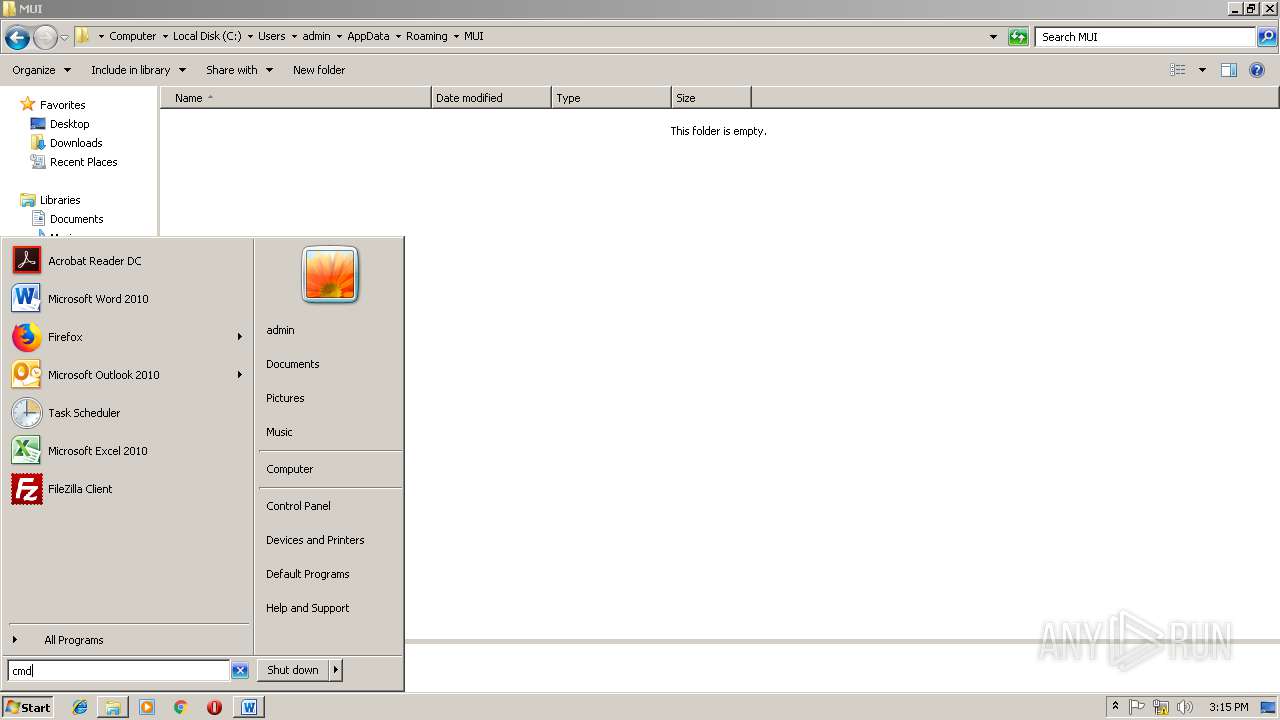
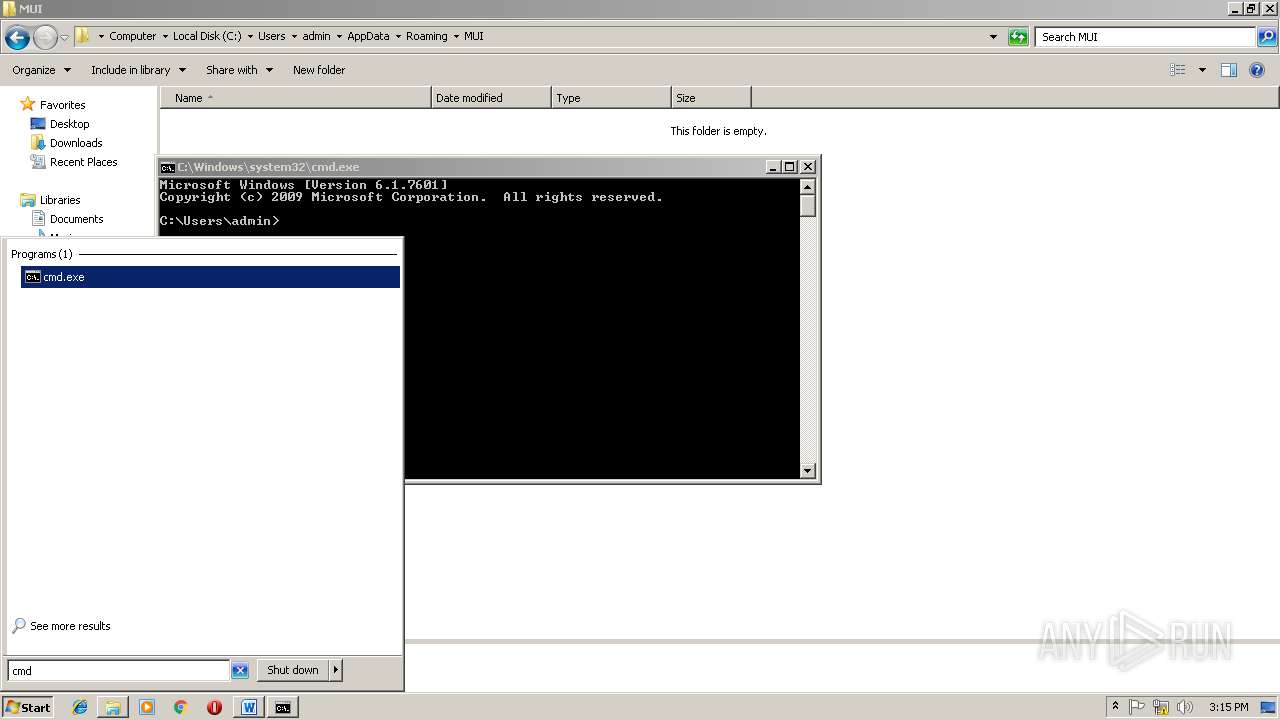
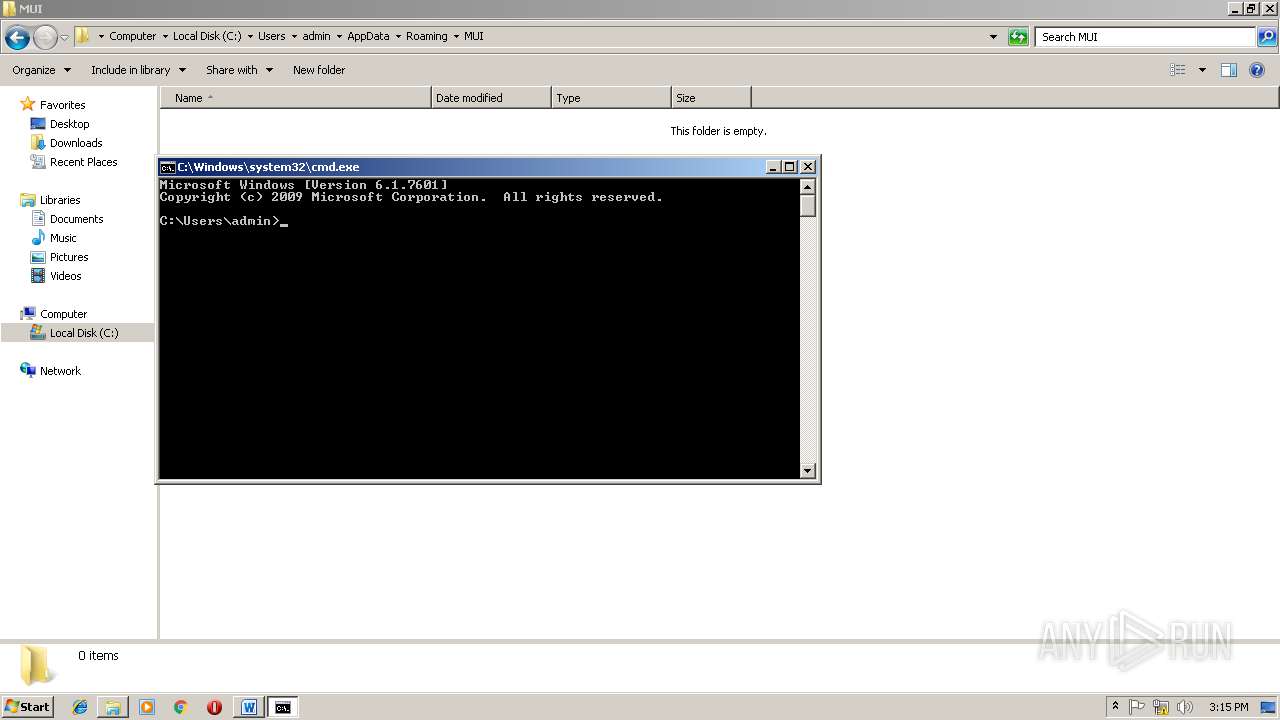
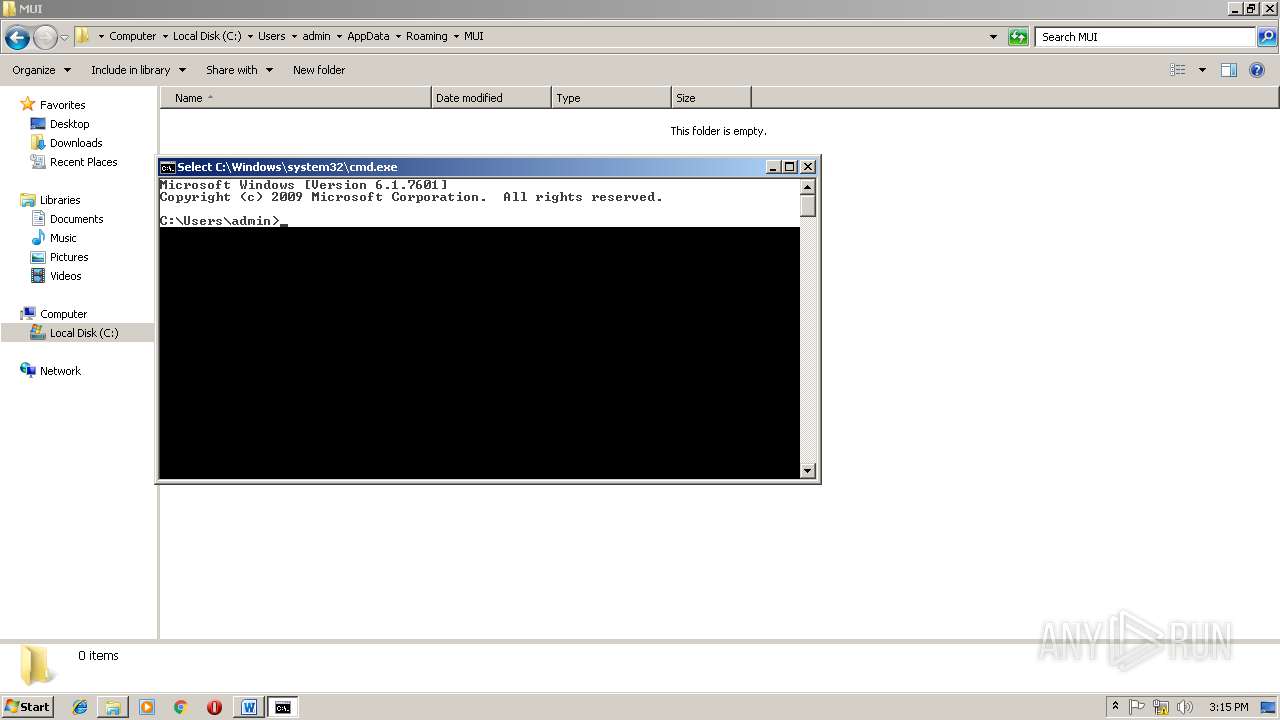
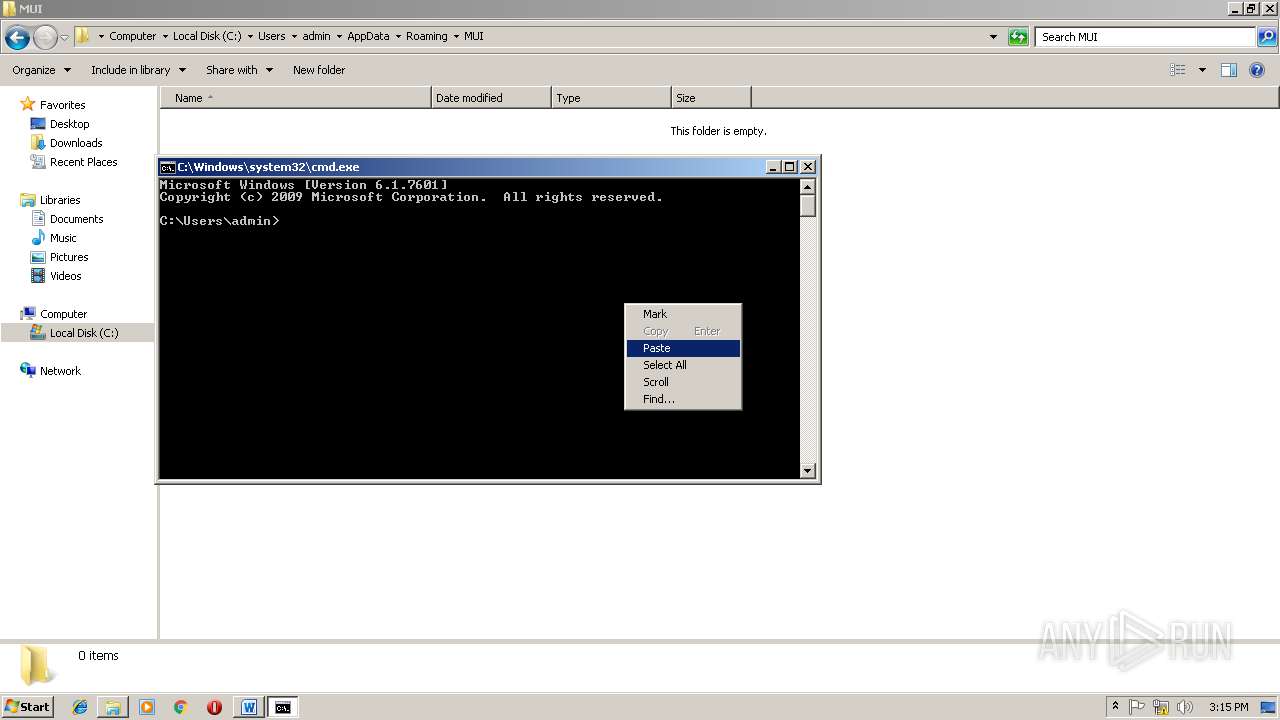
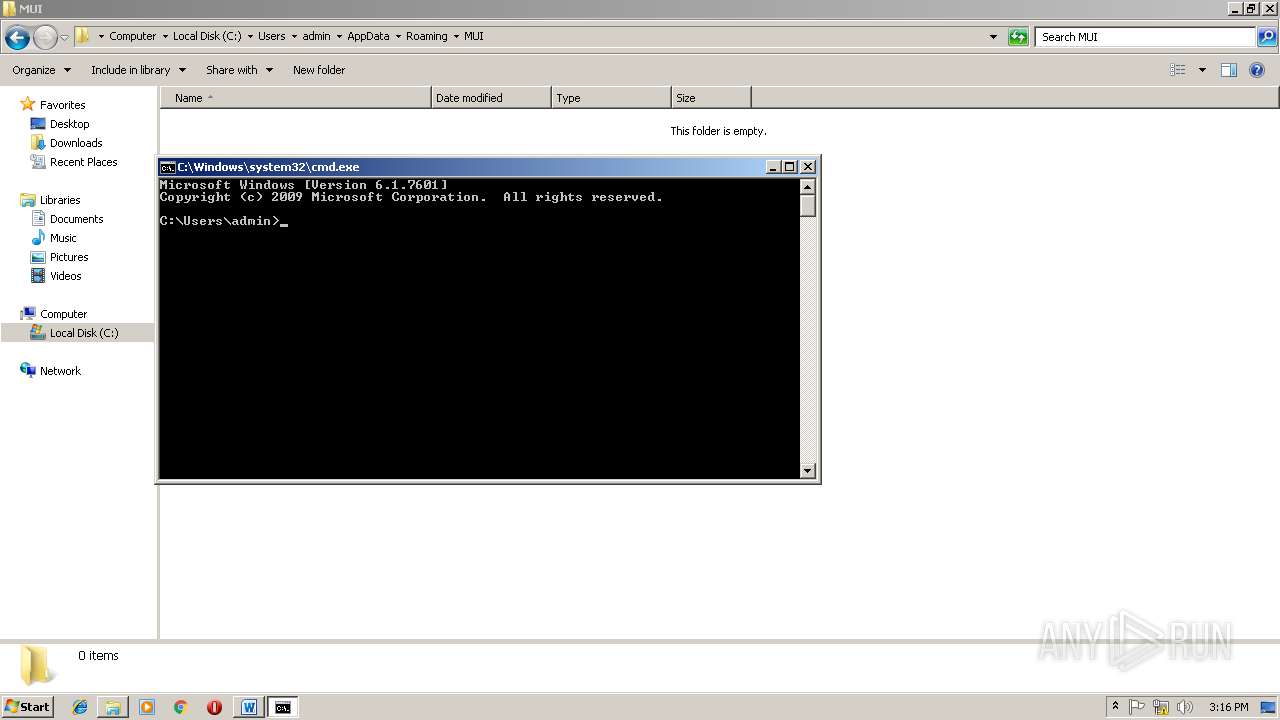
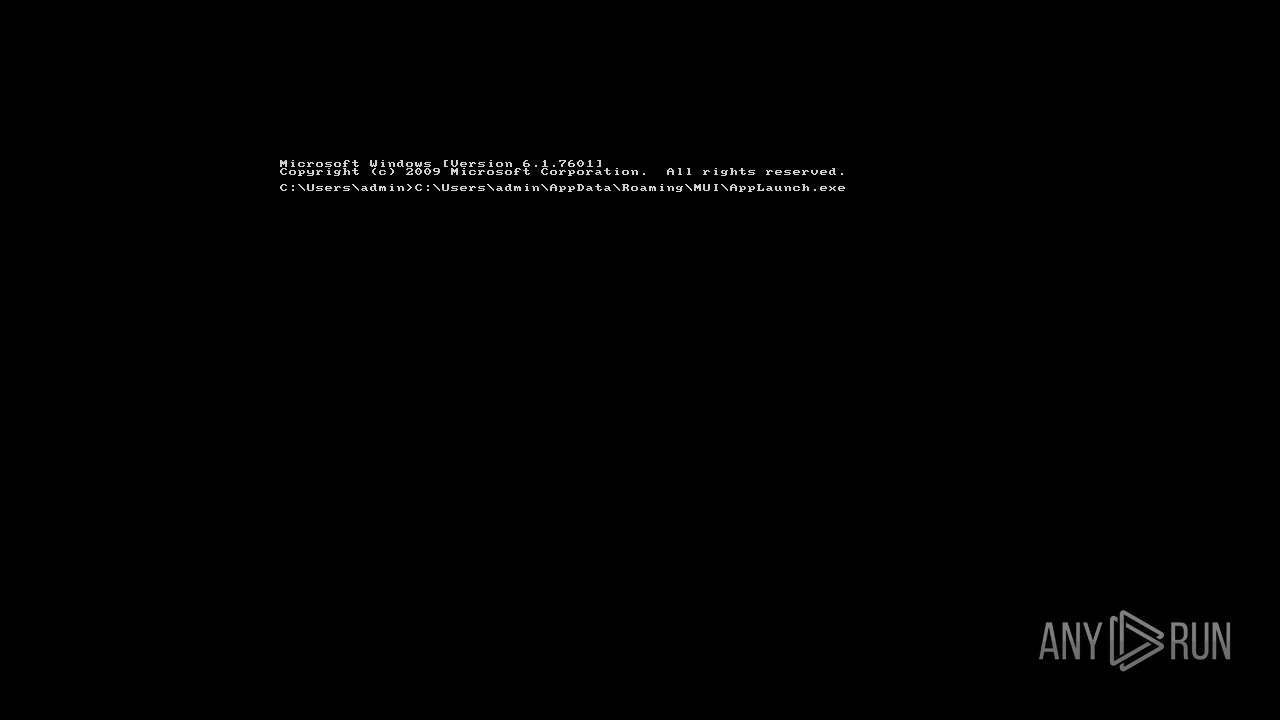
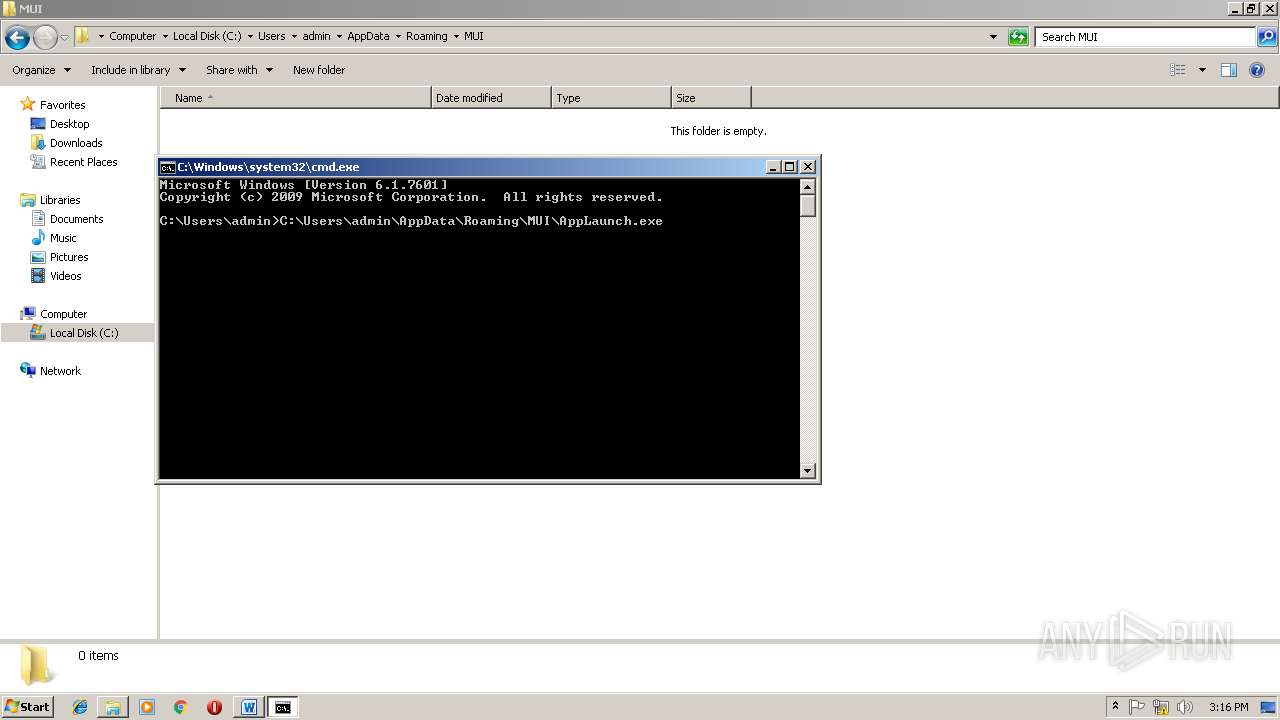
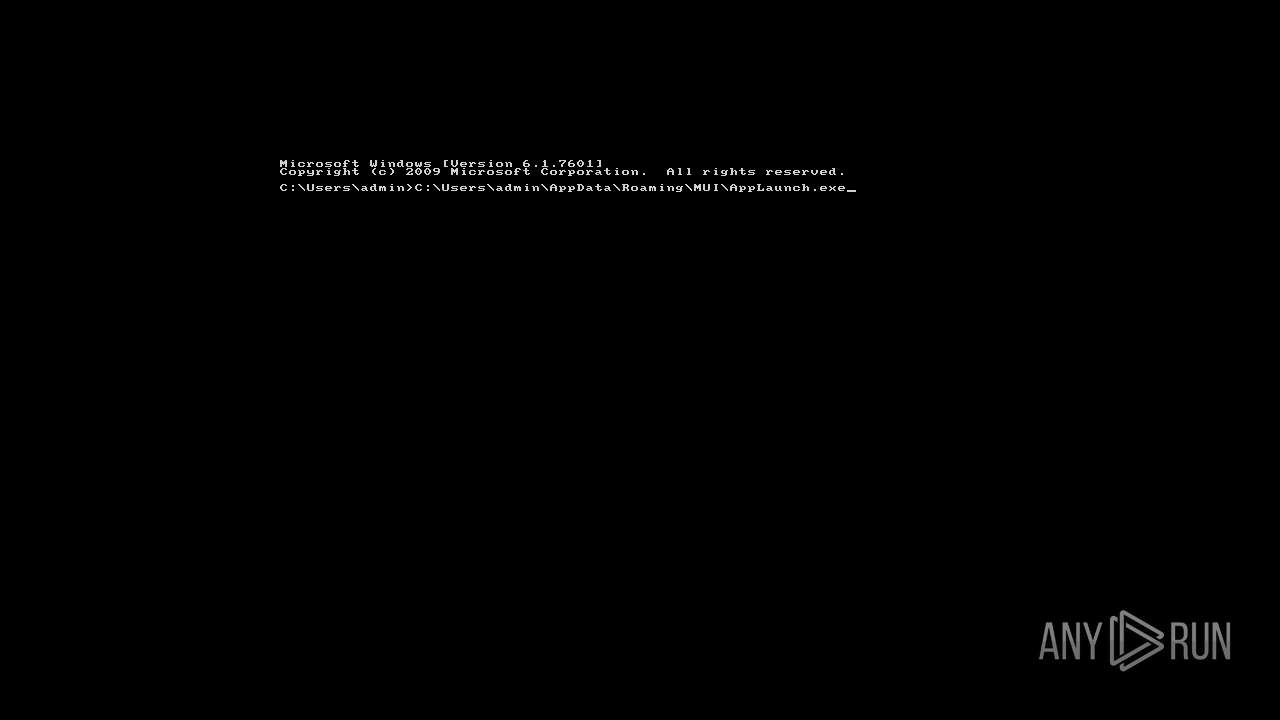
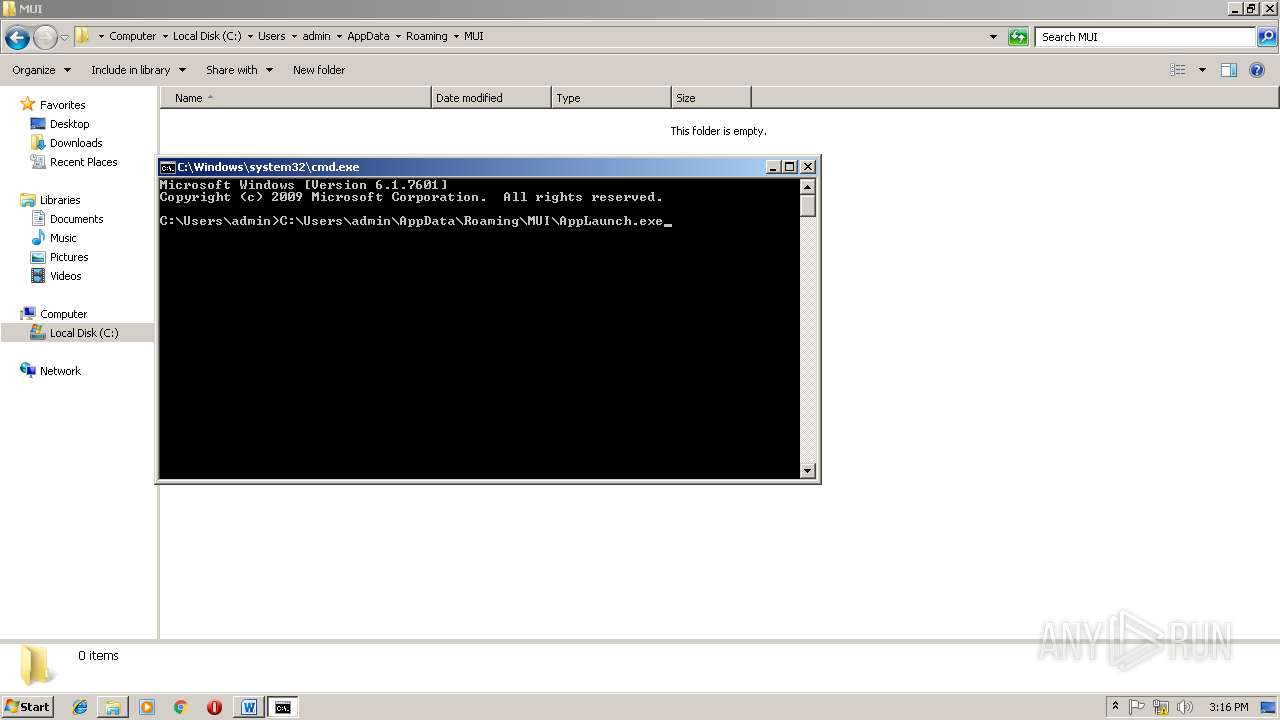
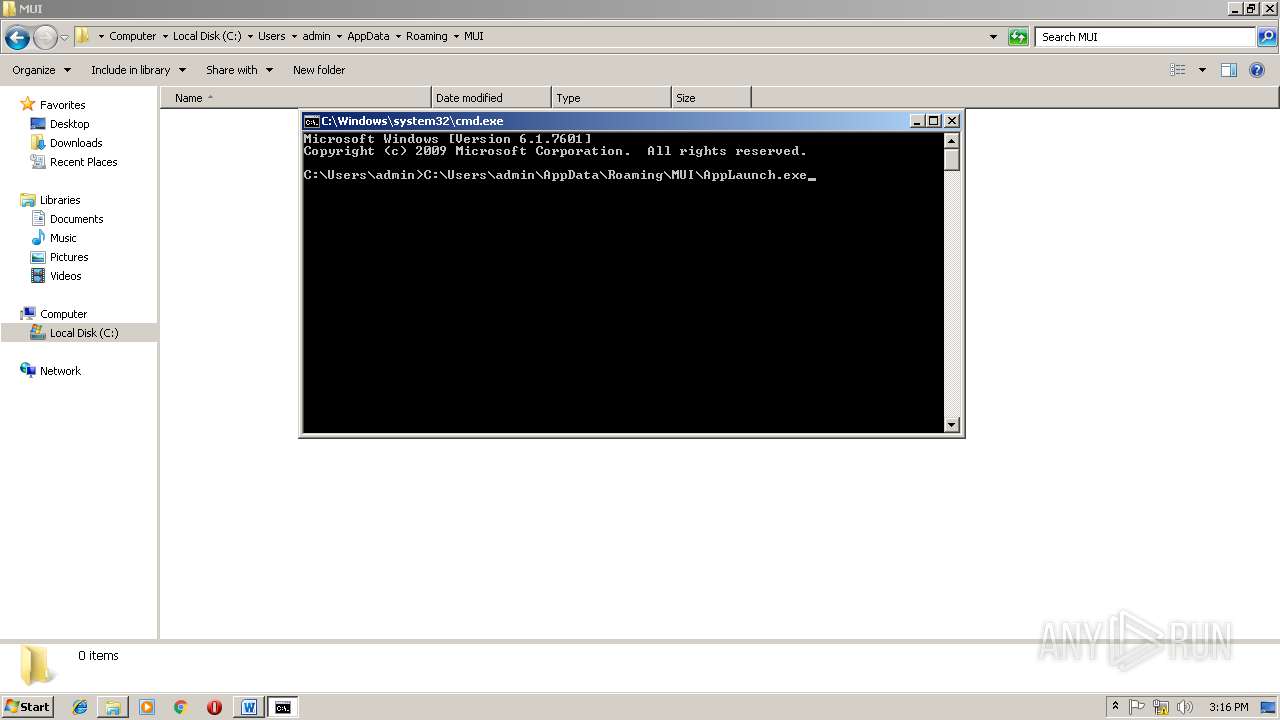
| 2868 | "C:\Windows\System32\cmd.exe" /c schtasks /create /tn AppLaunch /tr C:\Users\admin\AppData\Roaming\Mui\AppLaunch.exe /sc DAILY /f /RI 10 /du 24:00 /st 00:01 | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
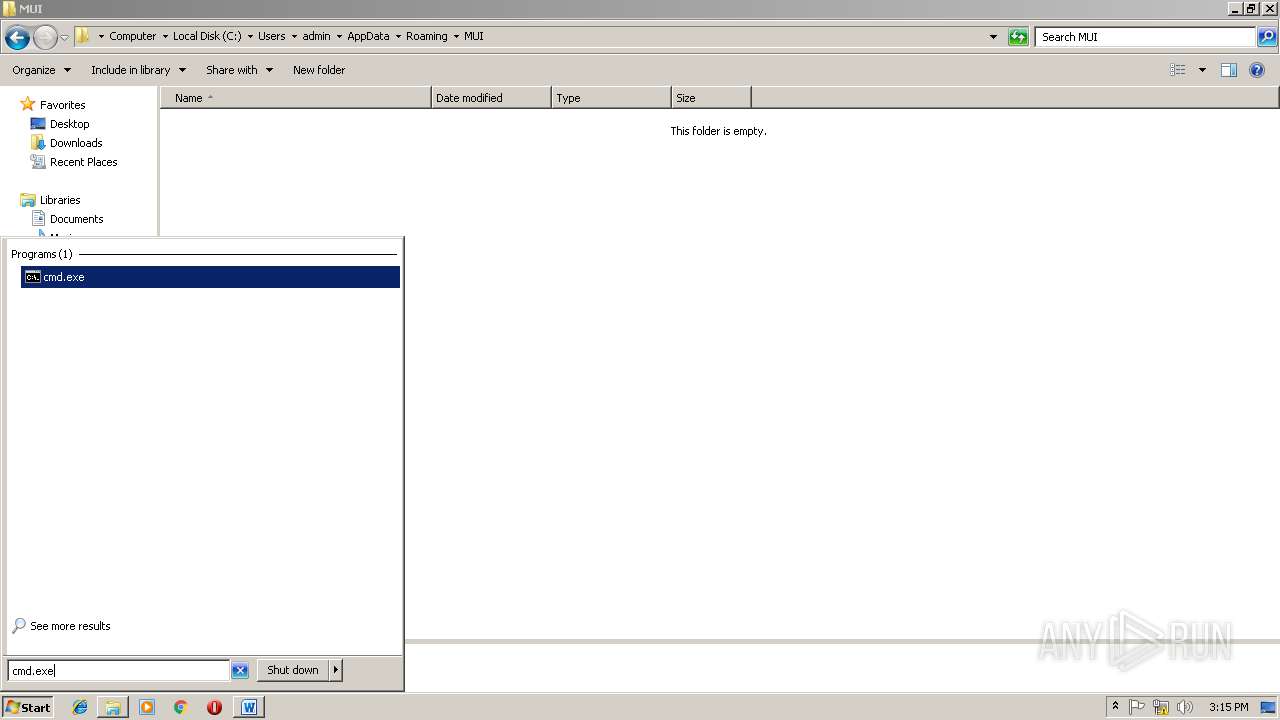
| 3316 | schtasks /create /tn AppLaunch /tr C:\Users\admin\AppData\Roaming\Mui\AppLaunch.exe /sc DAILY /f /RI 10 /du 24:00 /st 00:01 | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3712 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4024 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 235
Read events
882
Write events
346
Delete events
7
Modification events
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -9/ |
Value: 2D392F00BC0A0000010000000000000000000000 | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301151765 | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301151884 | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301151885 | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: BC0A0000286CFB87BF93D40100000000 | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f:/ |
Value: 663A2F00BC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | f:/ |
Value: 663A2F00BC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2748) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR592D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDF45F785D4078D70.TMP | — | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFEEB607C7219A3BFB.TMP | — | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF517E16D40B1FB30A.TMP | — | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRL0001.tmp | document | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\7c50f42fc4df44918d5b200b3ede38be5342286a08c6acc30e01d4b74b2014a5.doc | document | |
MD5:— | SHA256:— | |||
| 2748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$50f42fc4df44918d5b200b3ede38be5342286a08c6acc30e01d4b74b2014a5.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | WINWORD.EXE | 188.93.126.191:443 | www.idealnidom.com | Mainstream doo | RS | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.idealnidom.com |
| suspicious |