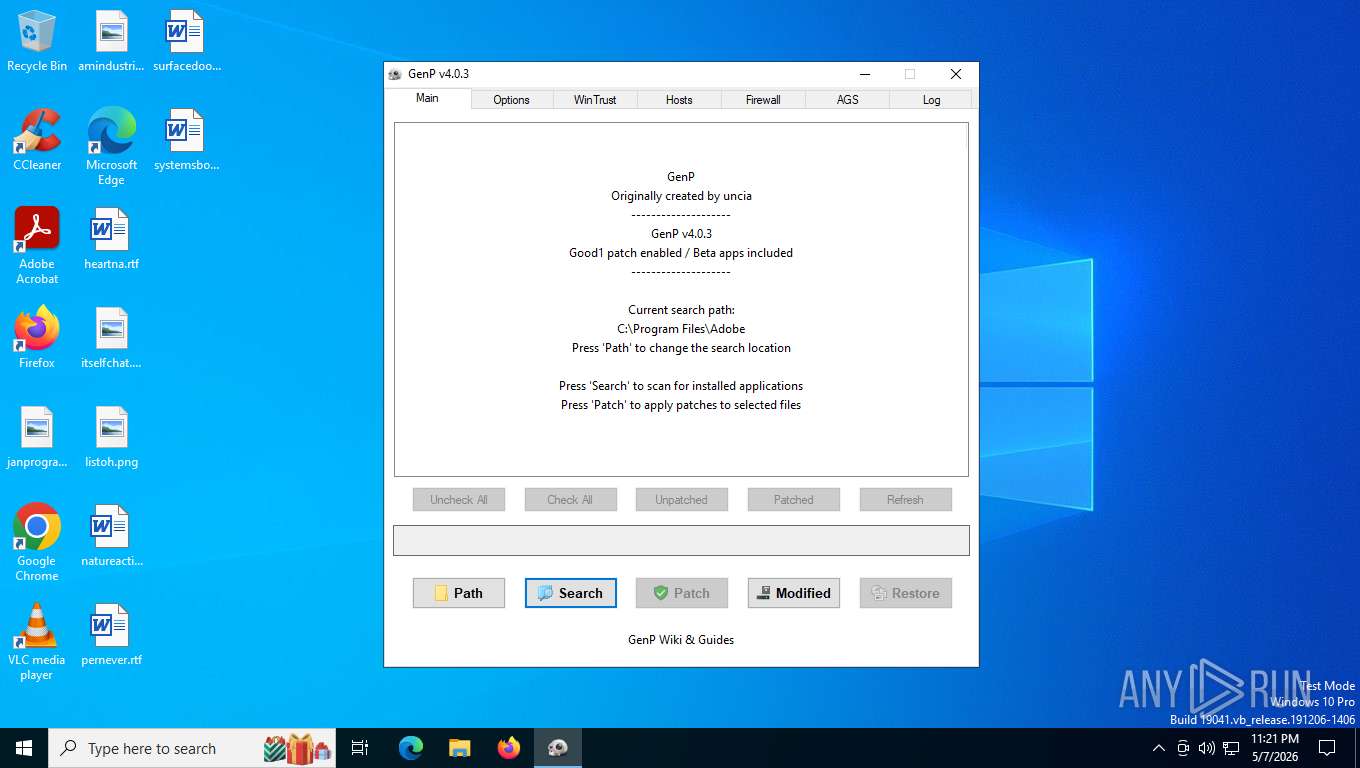
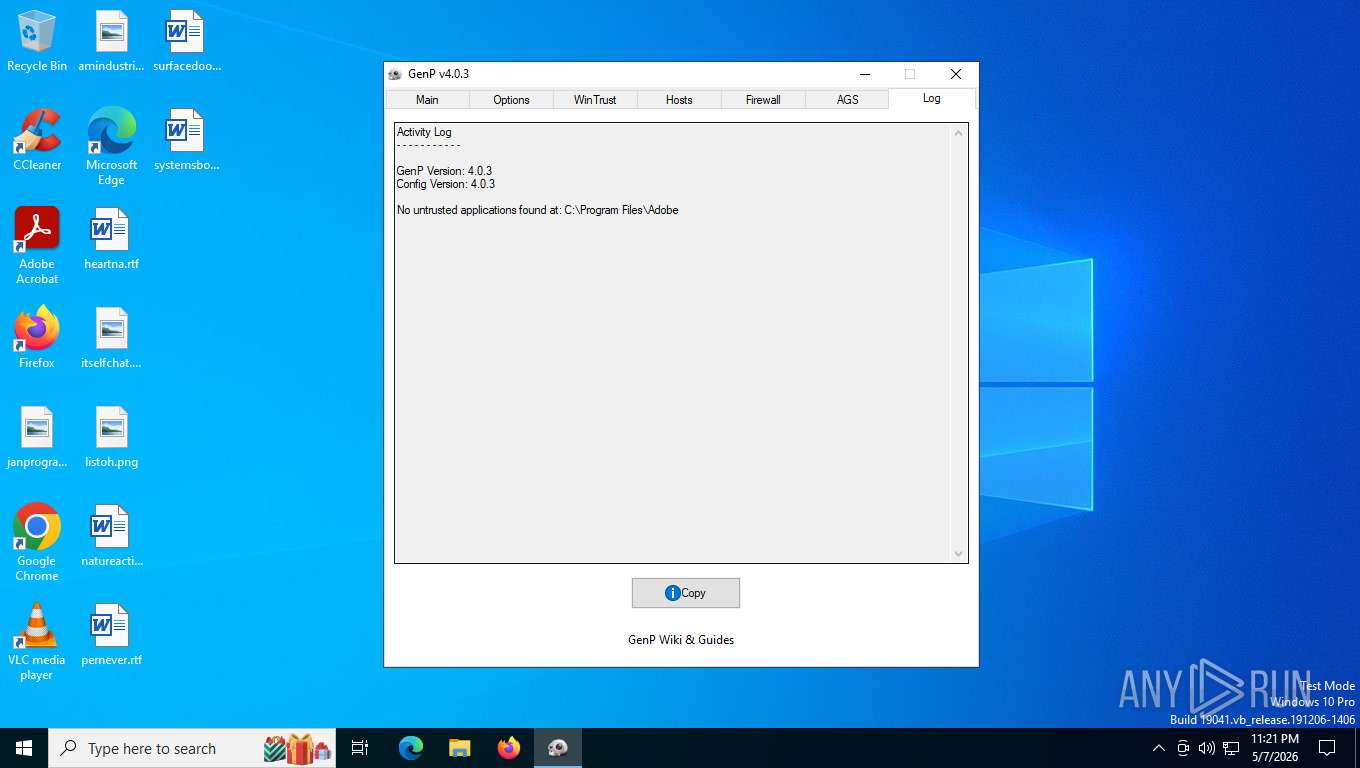
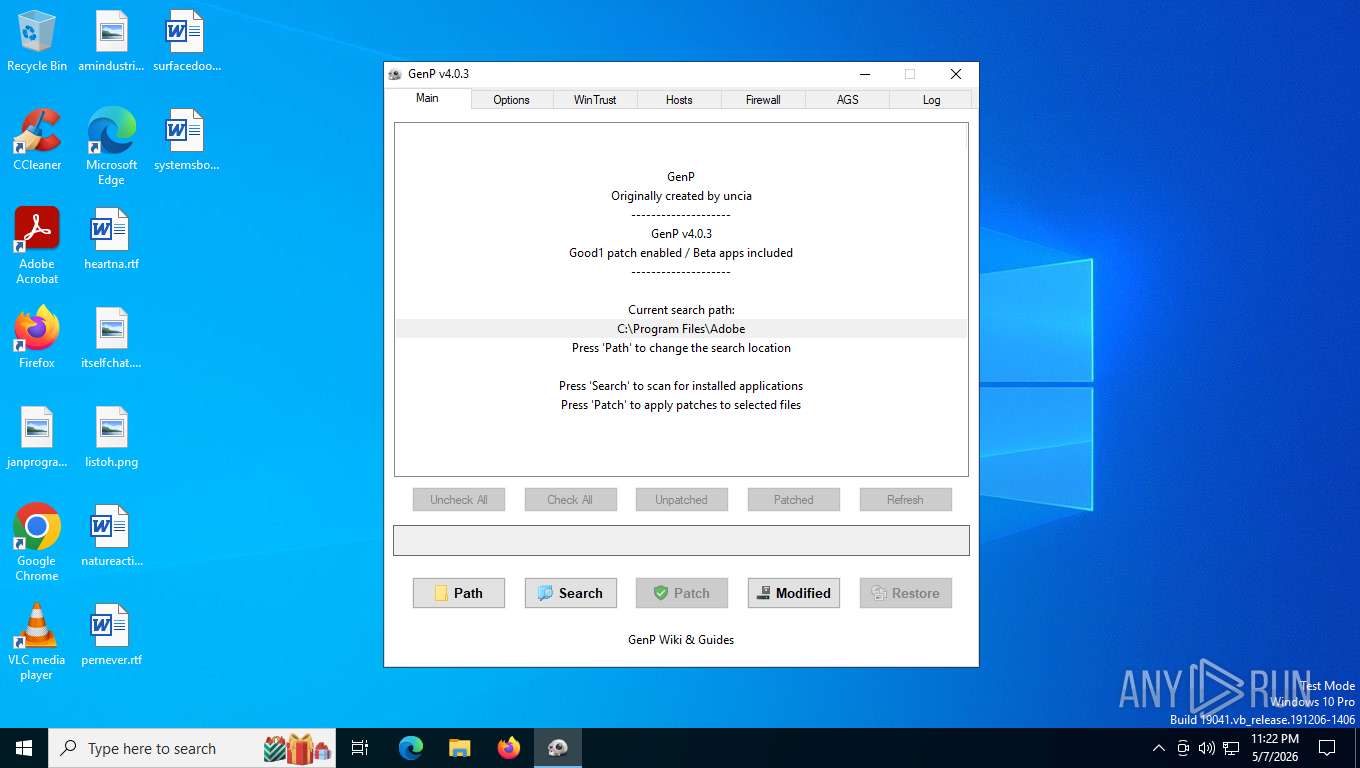
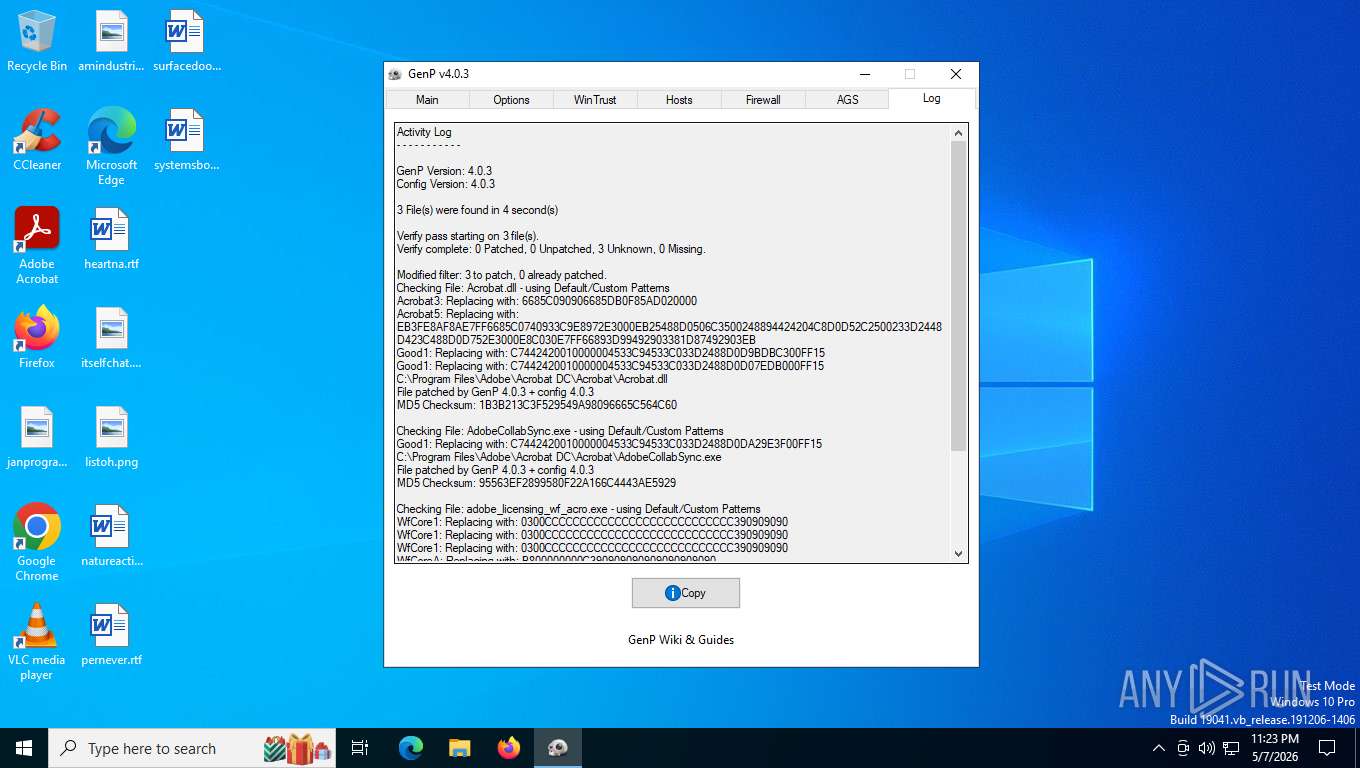
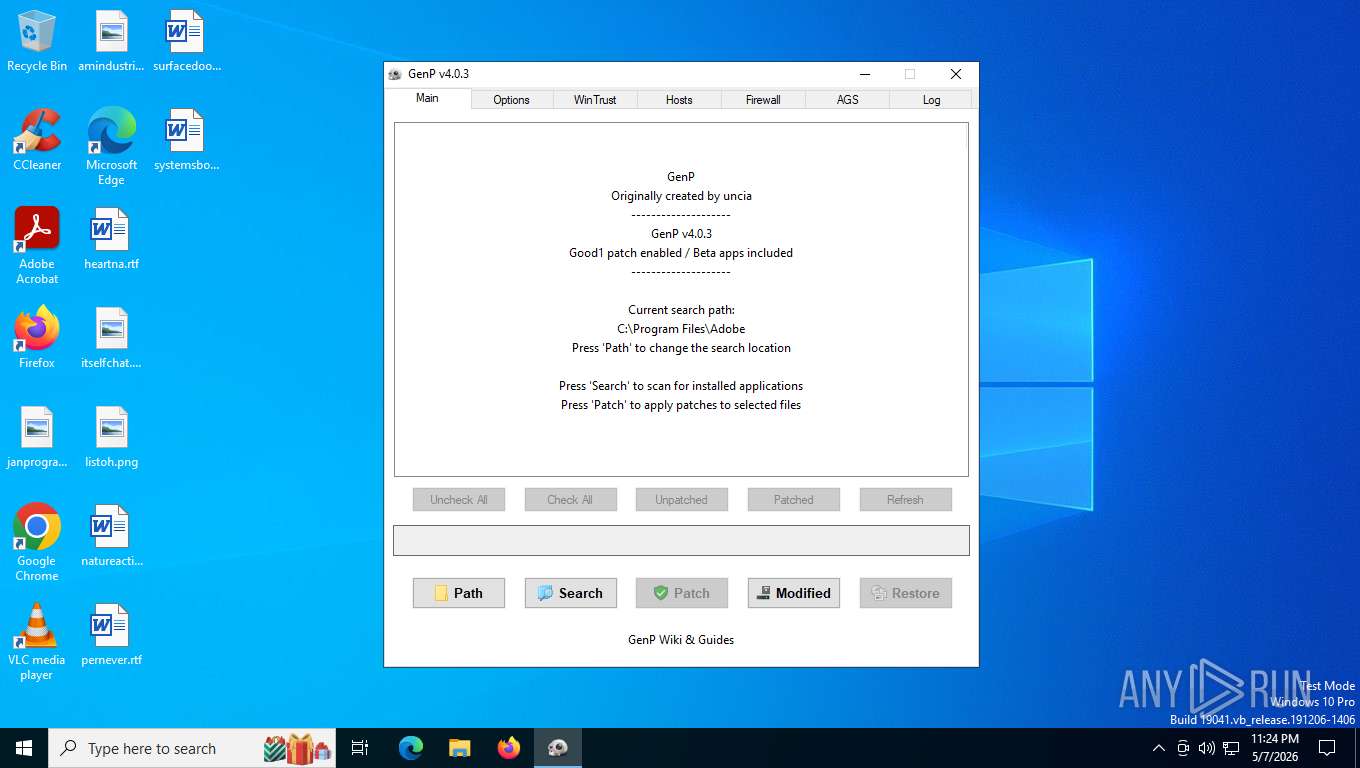
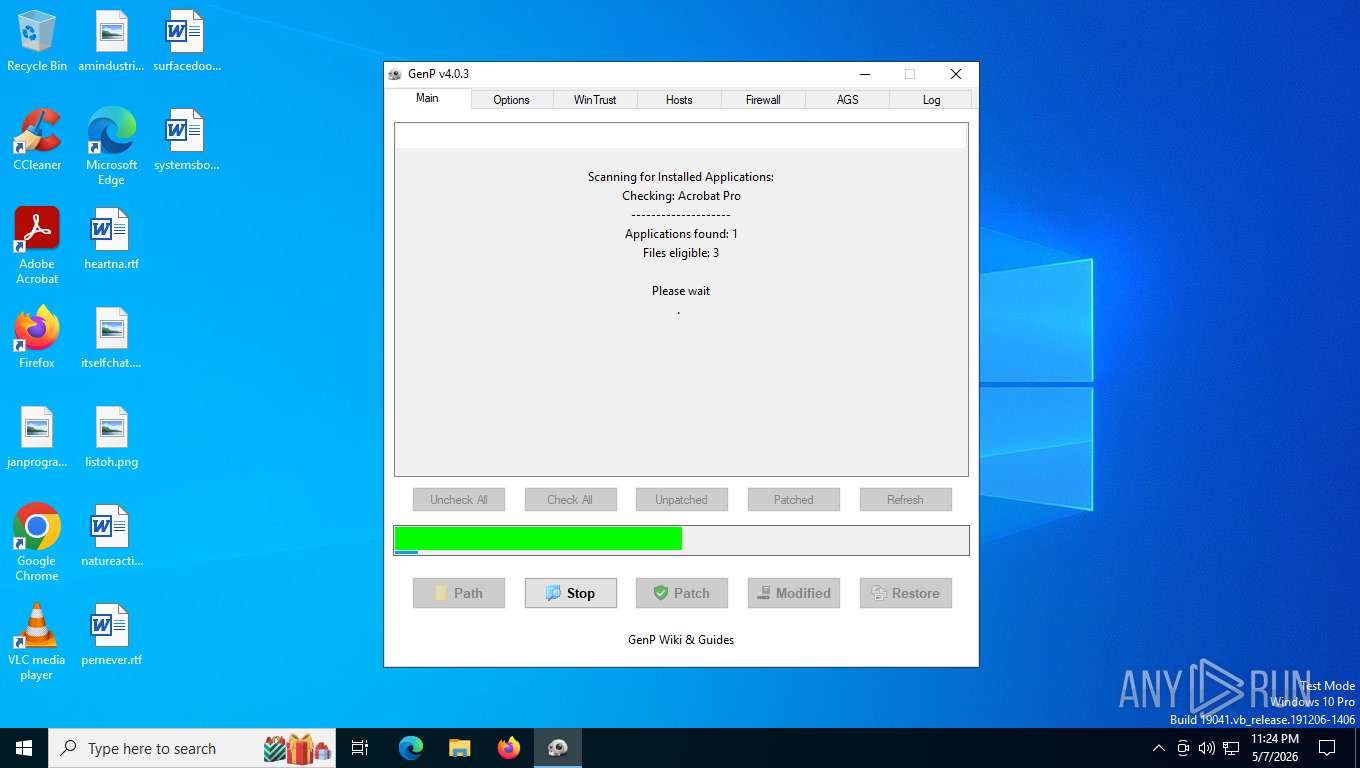
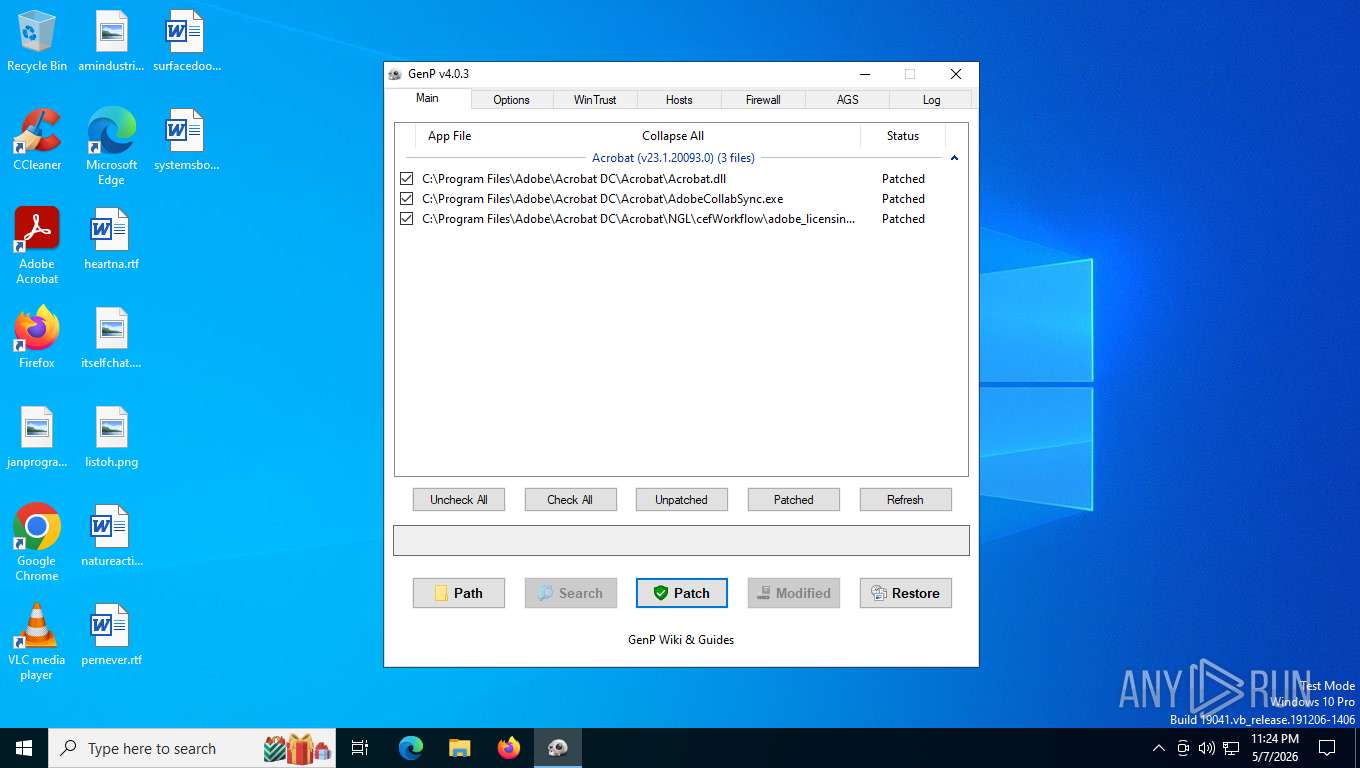
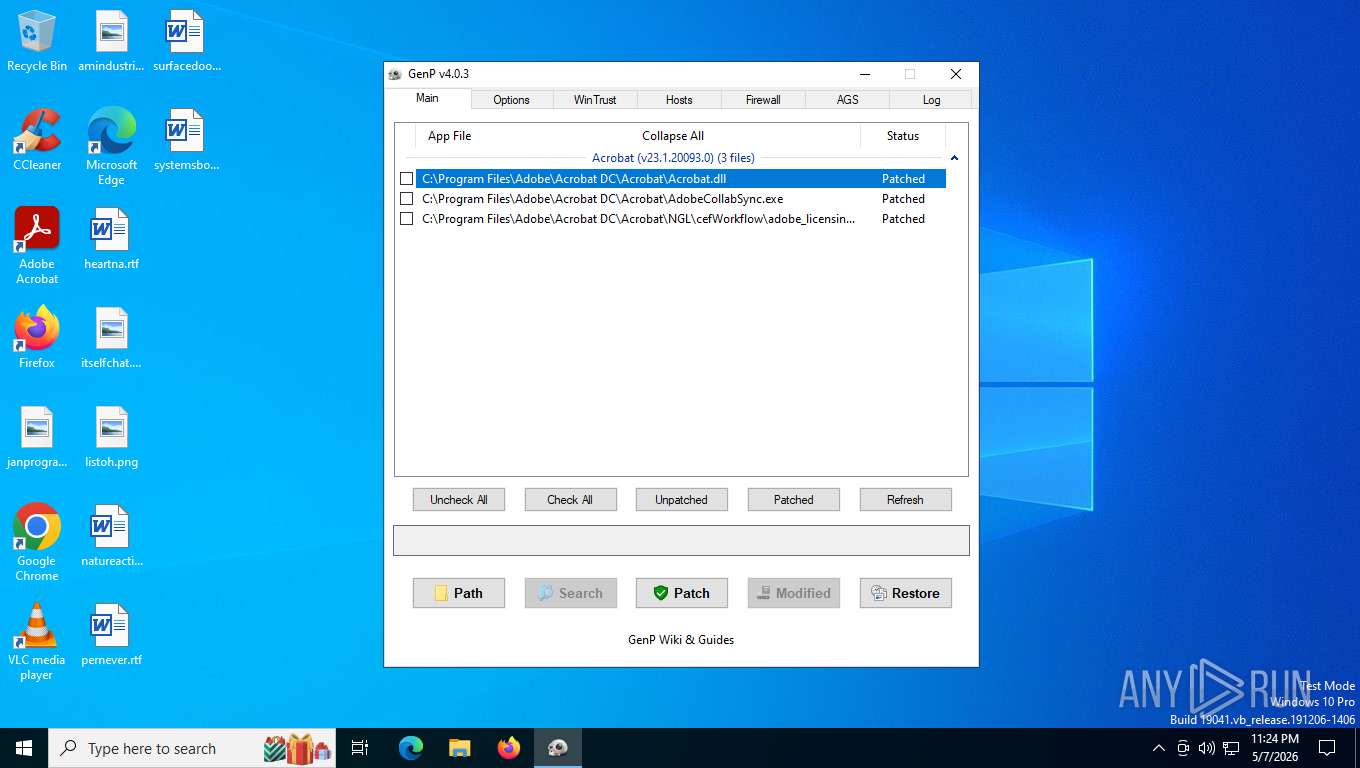
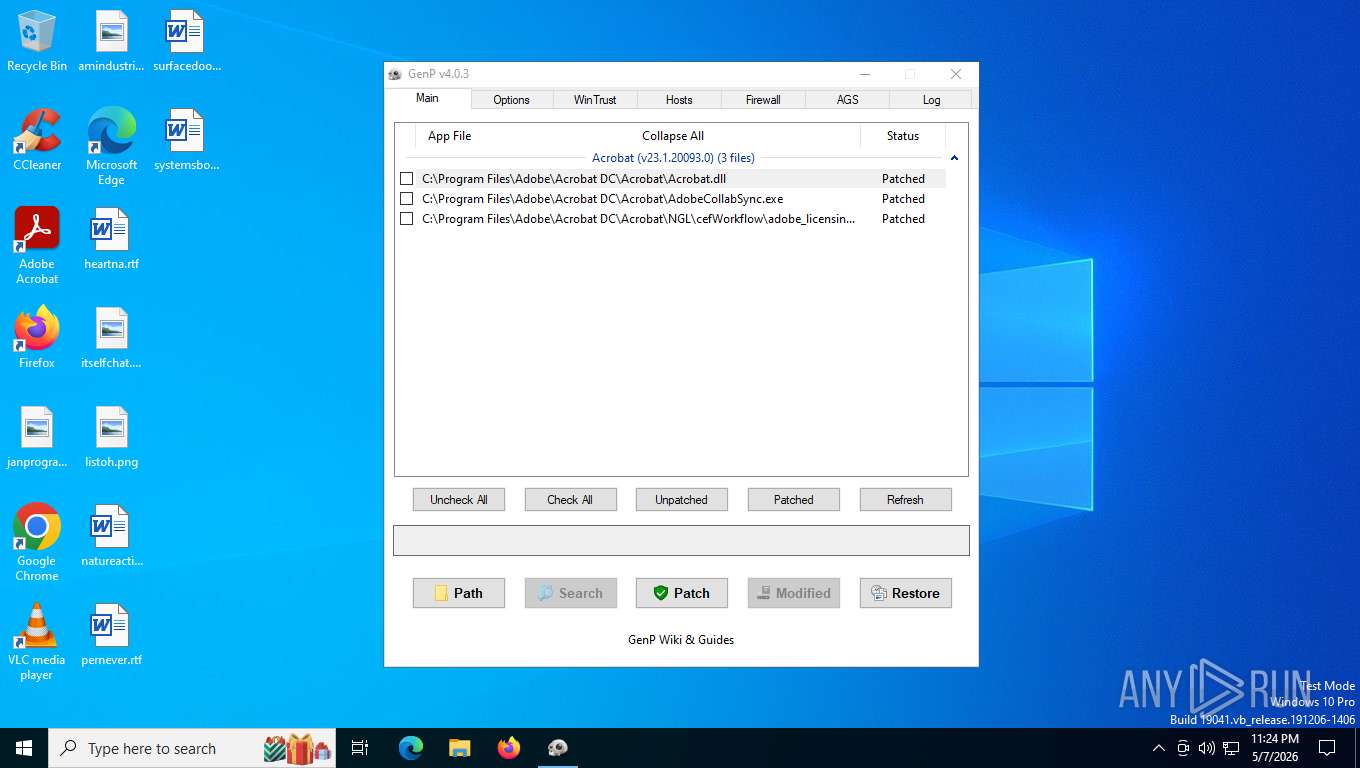
| File name: | GenP-v4.0.3.exe |
| Full analysis: | https://app.any.run/tasks/4e105e46-113f-4e15-8d0c-1aec274cfda5 |
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2026, 03:21:00 |
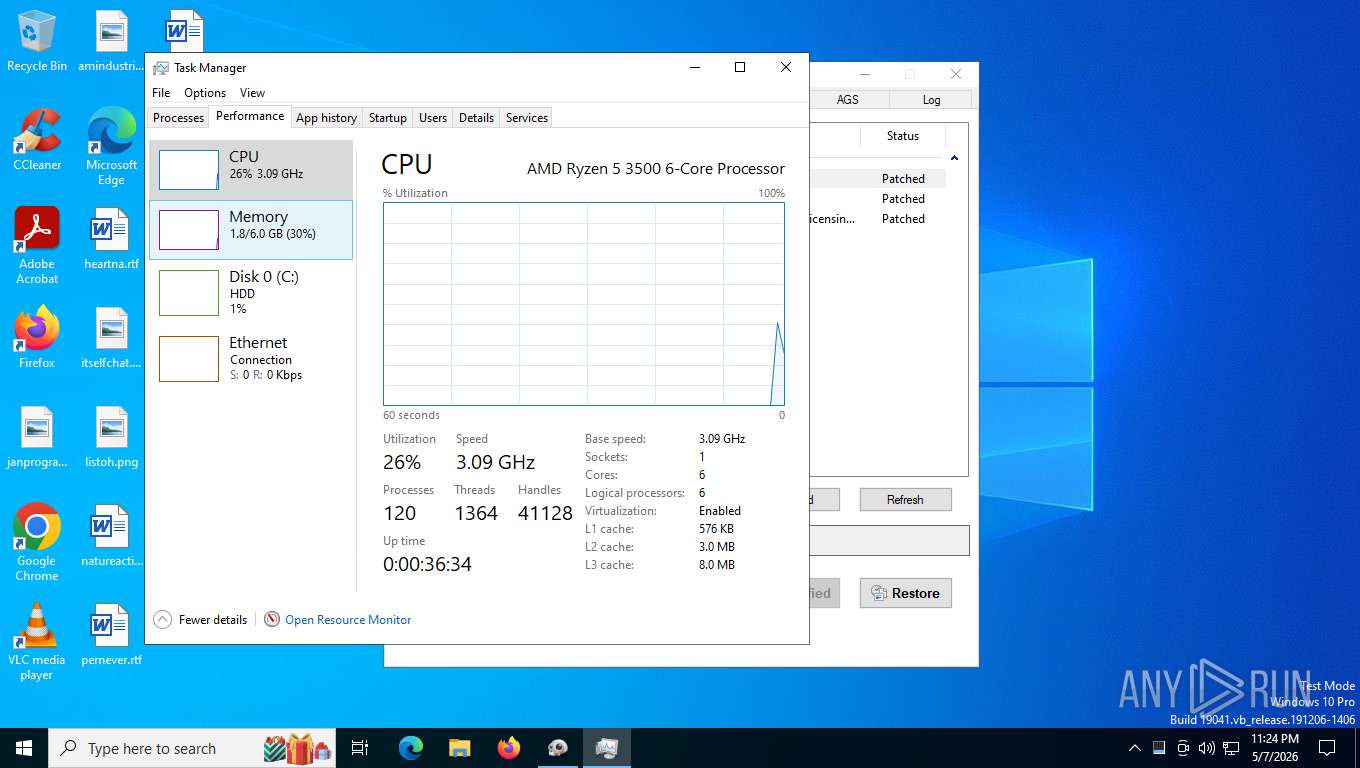
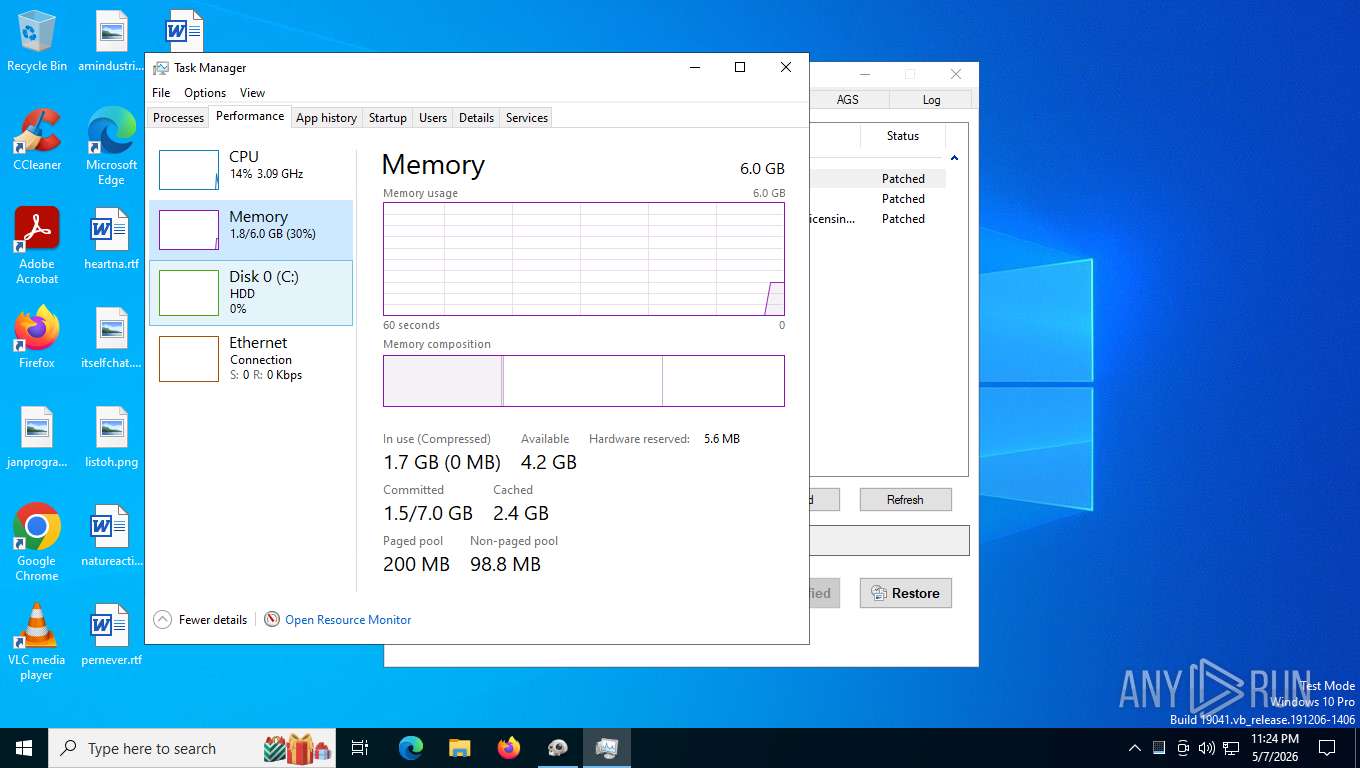
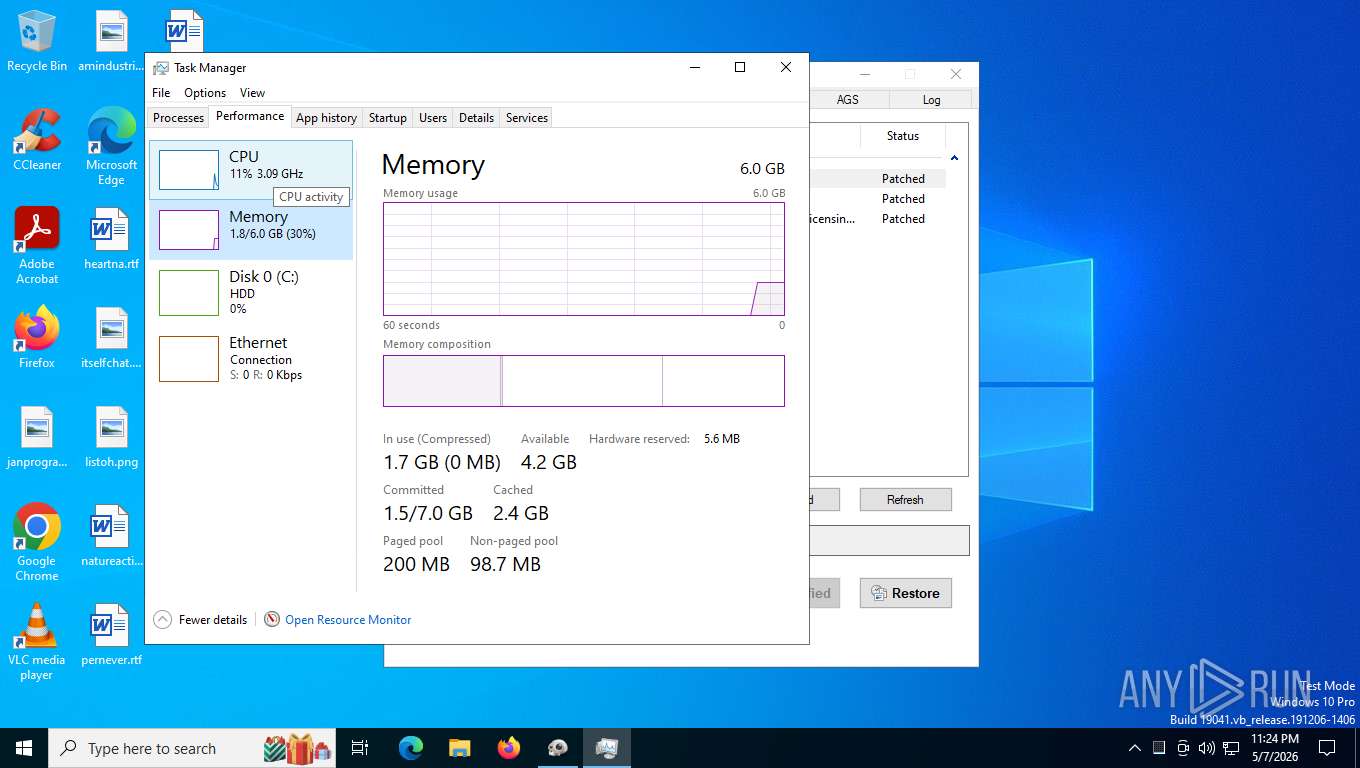
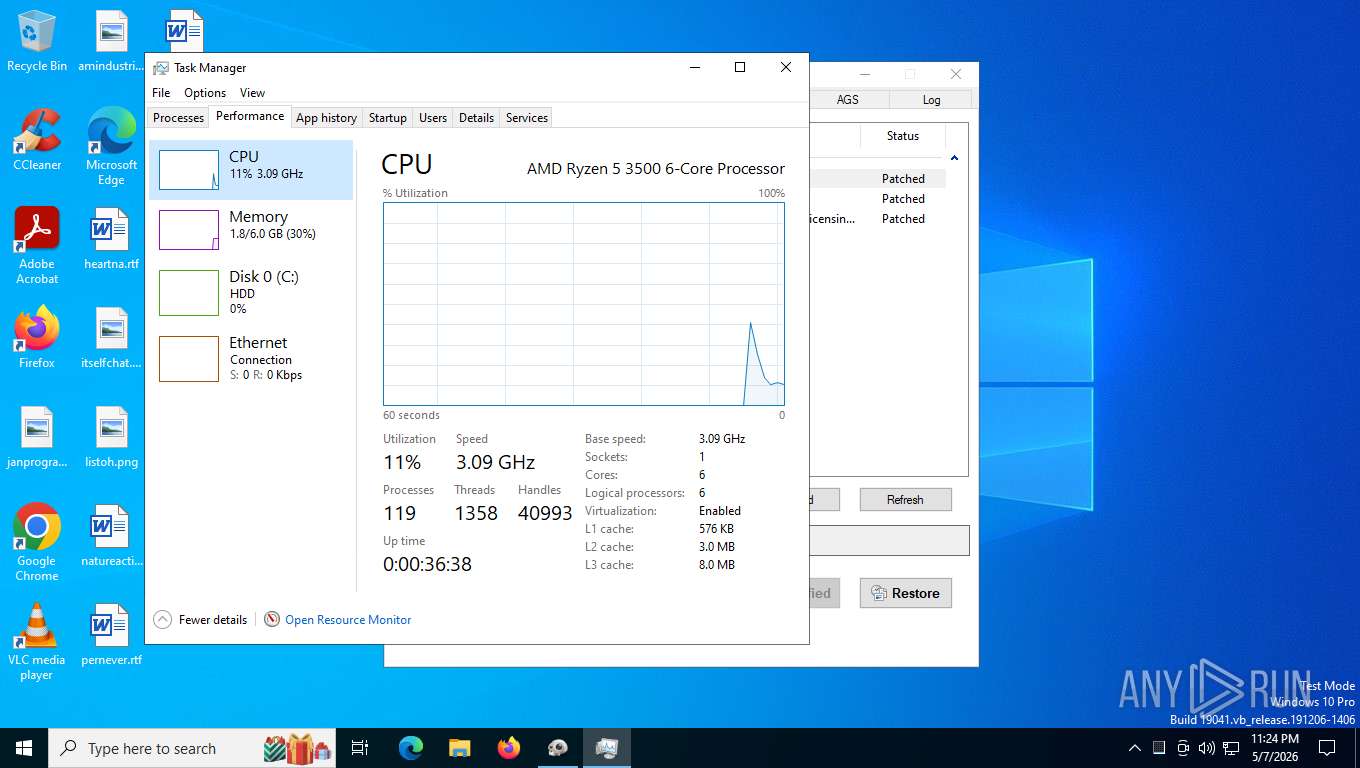
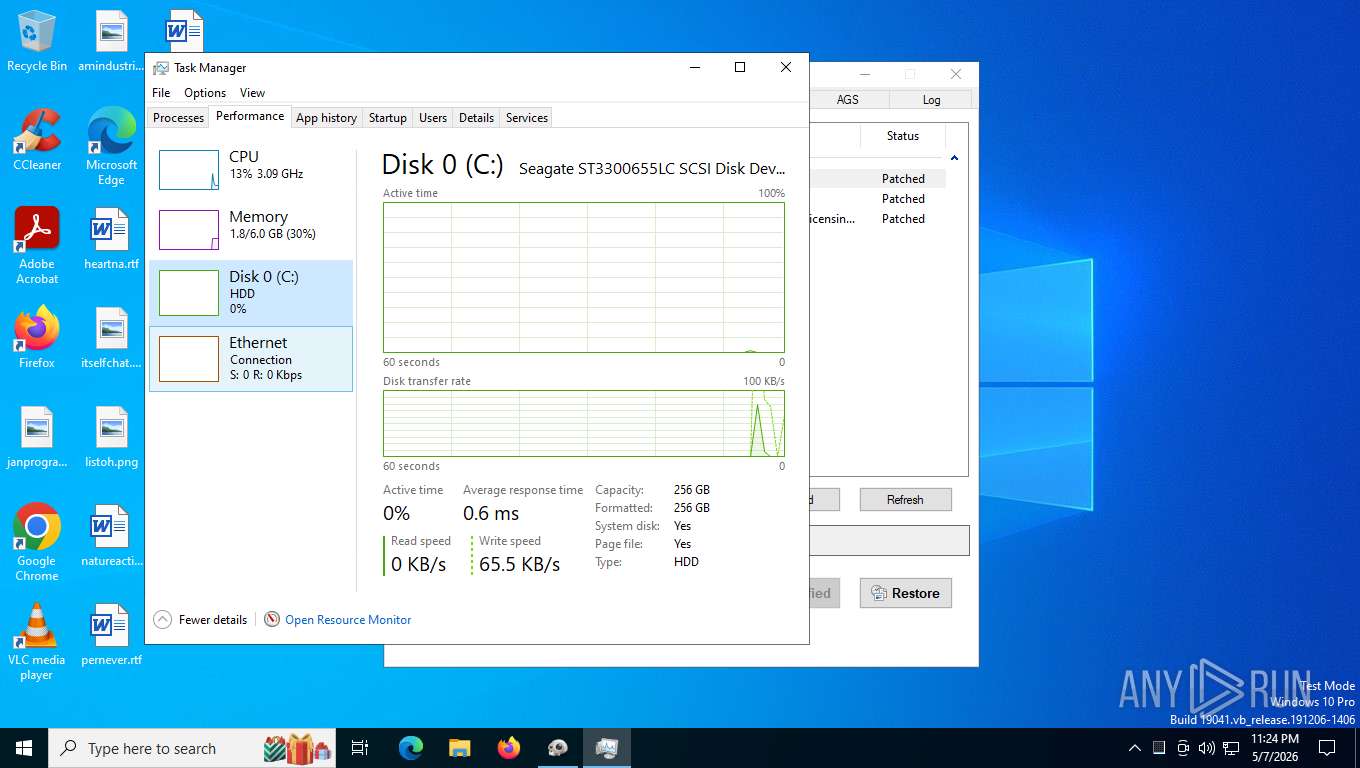
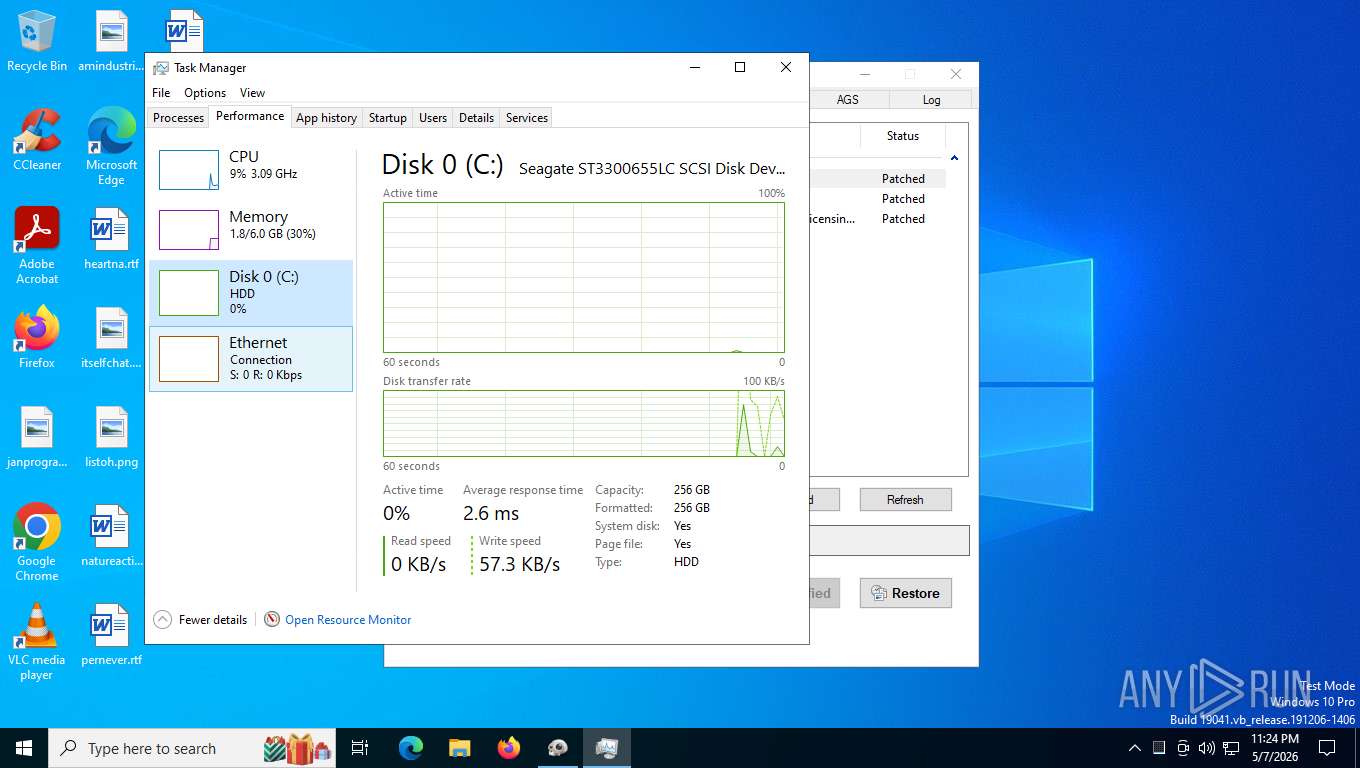
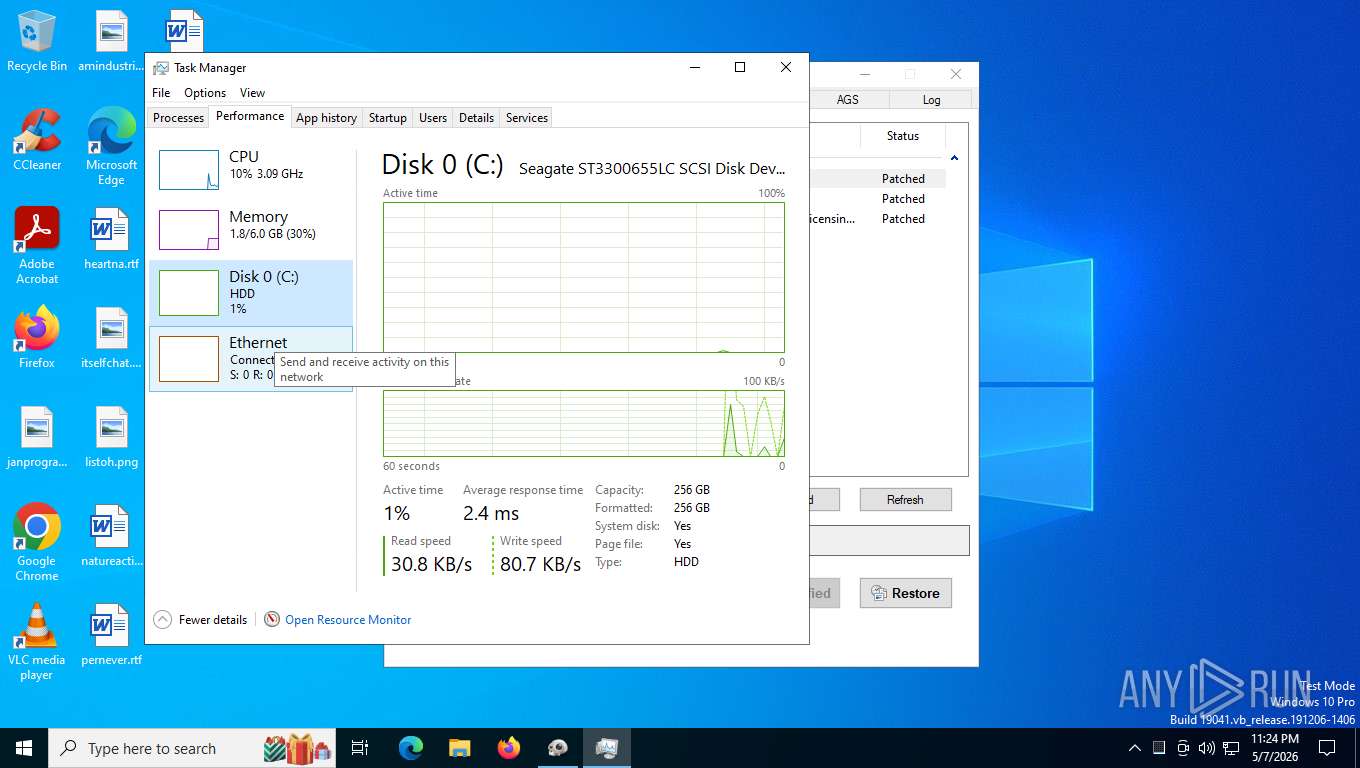
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | EB3059819B1DA02C7B2862E69F70152D |
| SHA1: | 7E30445EBD26A89CD84C1B6BBFA9809B5C5FAC0C |
| SHA256: | 7C43816908DED0439B3E230410B0DE9A20E3E16959F8F5804A8CF40C20F58FEE |
| SSDEEP: | 98304:CEng3KEZdwoB6imokHlR5JJcnJrZOKYYCTOQLvYq8y68hsmah+qi2Zv10AOR:CK |
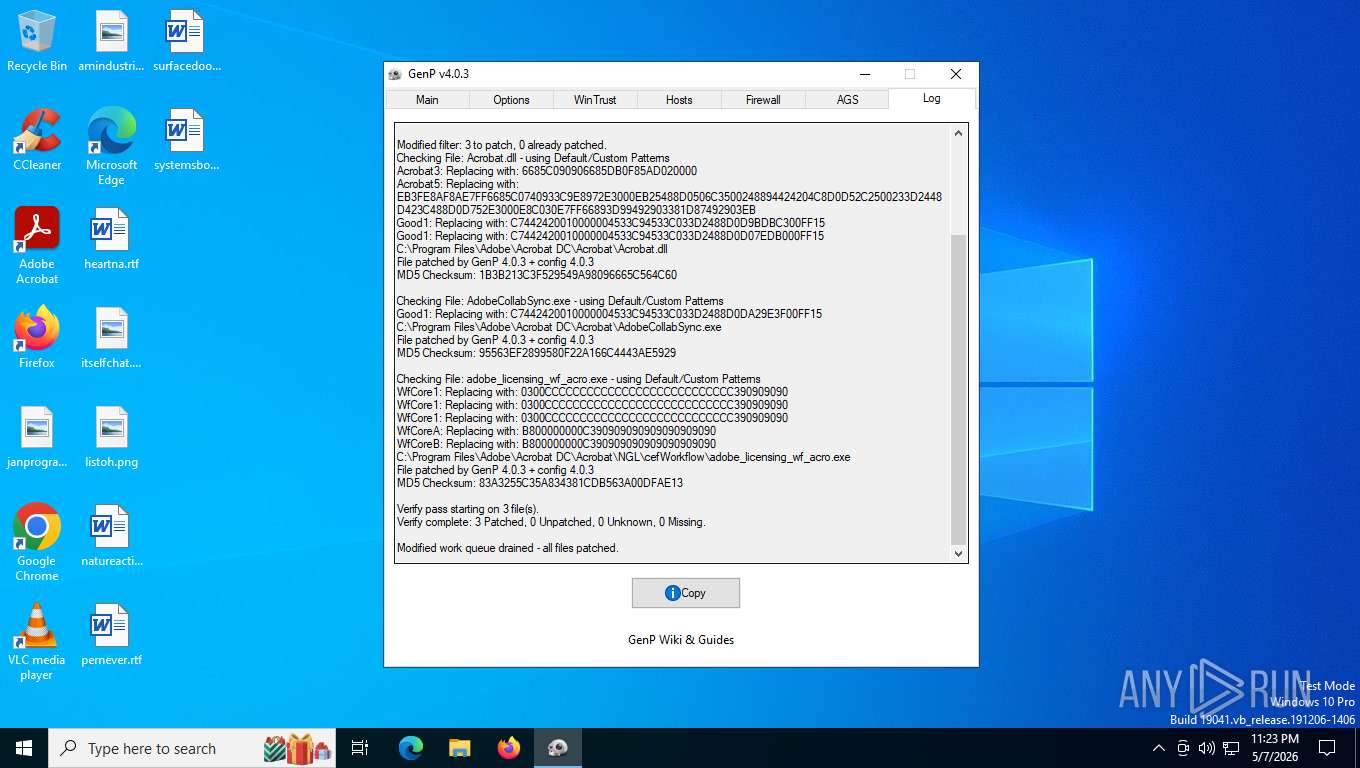
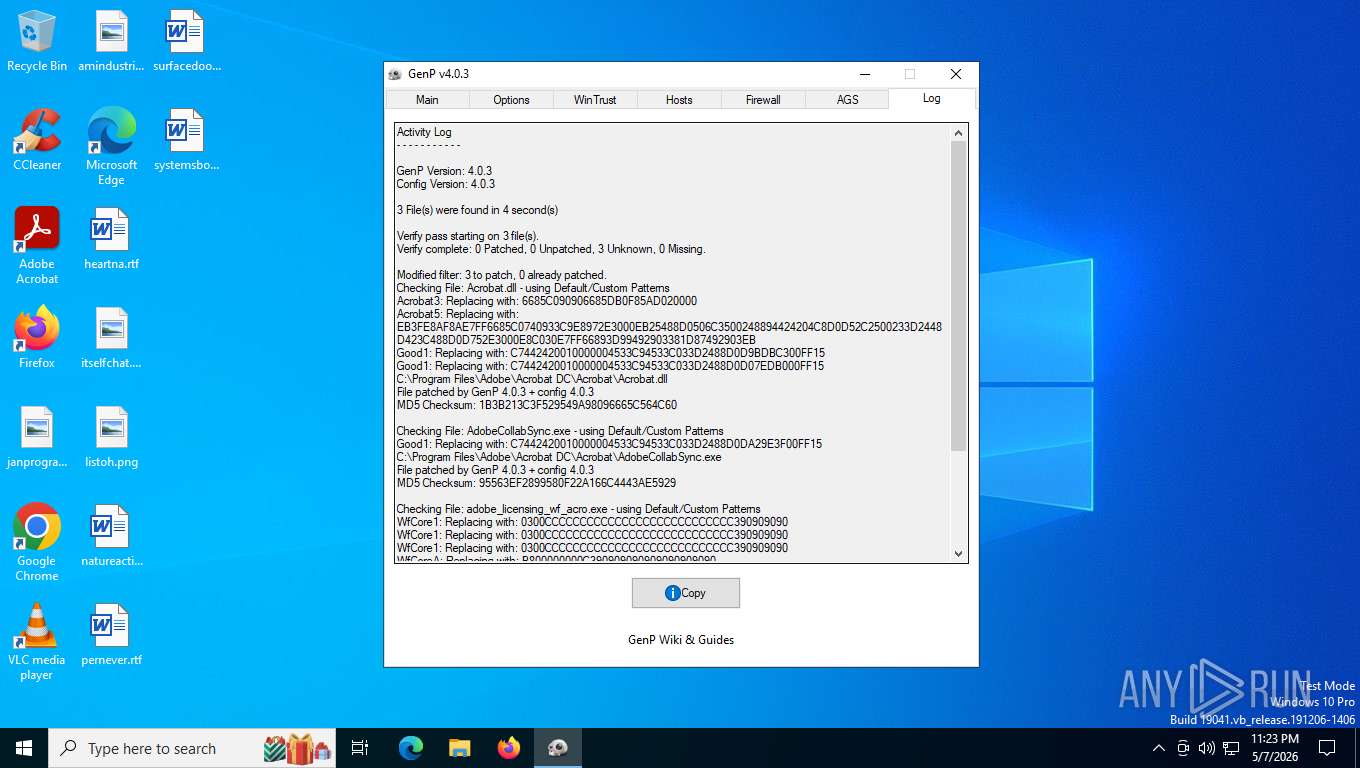
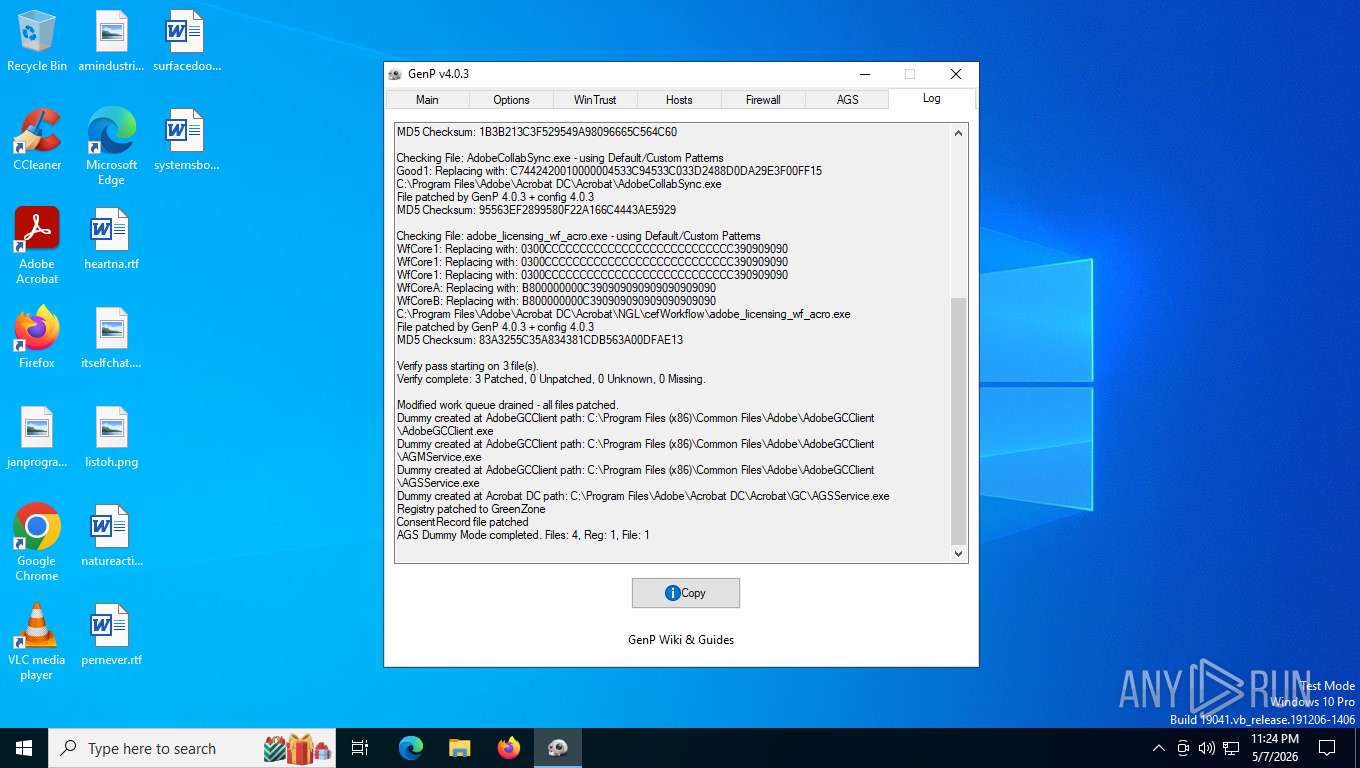
MALICIOUS
No malicious indicators.SUSPICIOUS
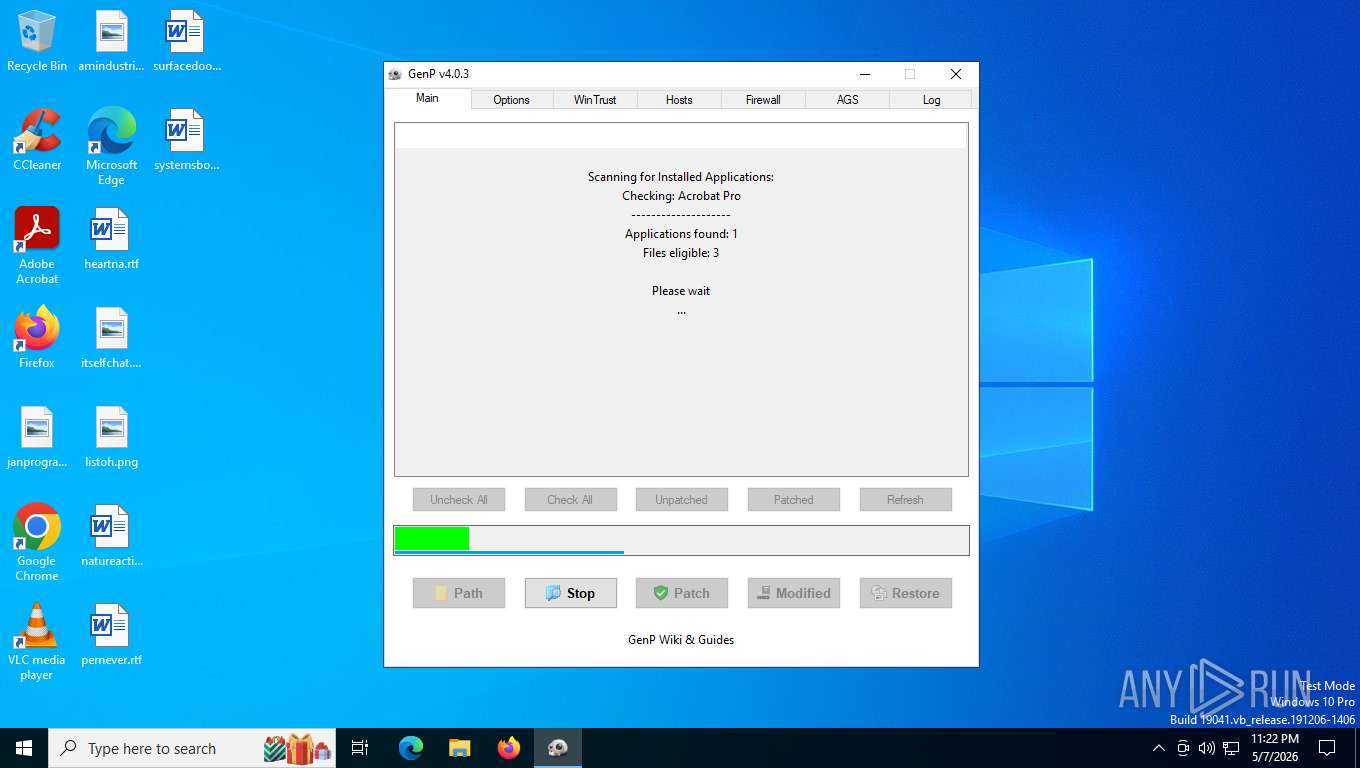
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7972)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 6444)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7972)
- cmd.exe (PID: 8516)
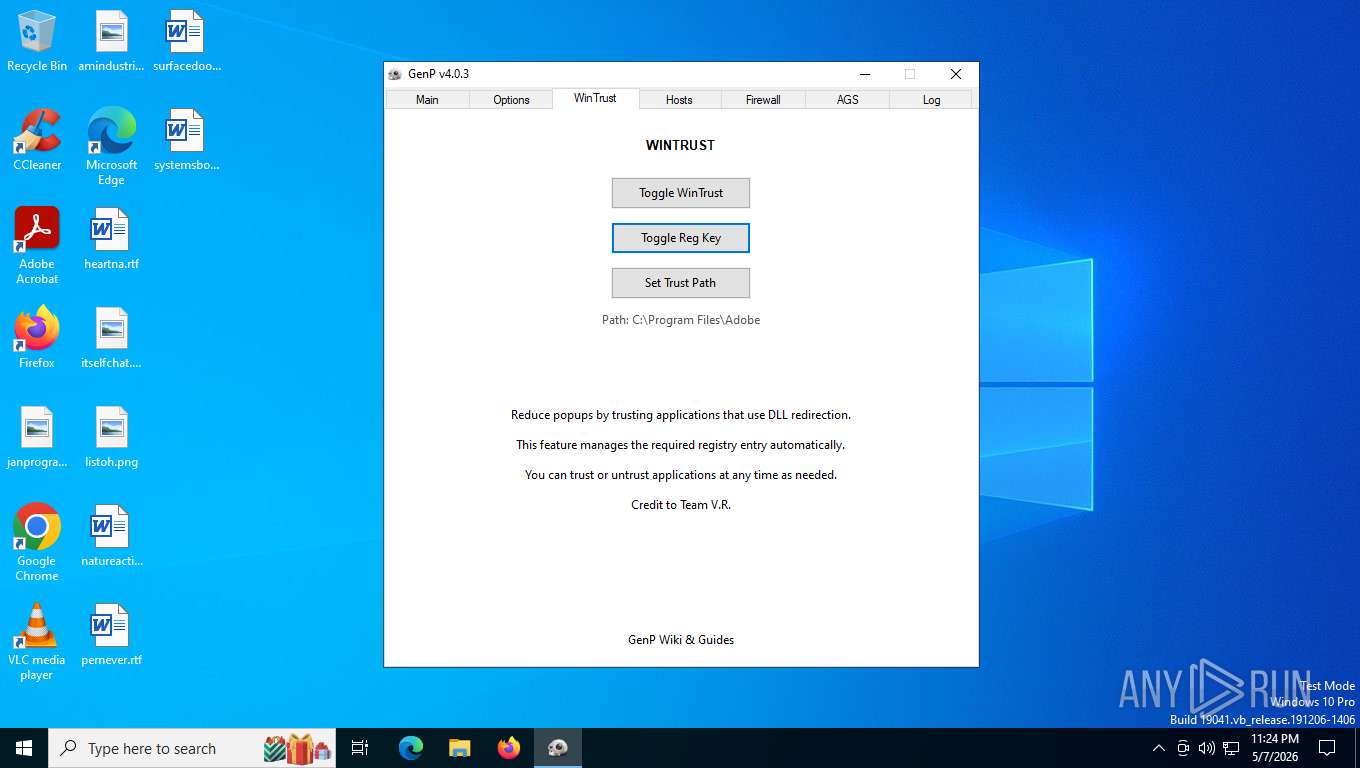
Creates files in the driver directory
- GenP-v4.0.3.exe (PID: 6980)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 6444)
Potential Corporate Privacy Violation
- GenP-v4.0.3.exe (PID: 6980)
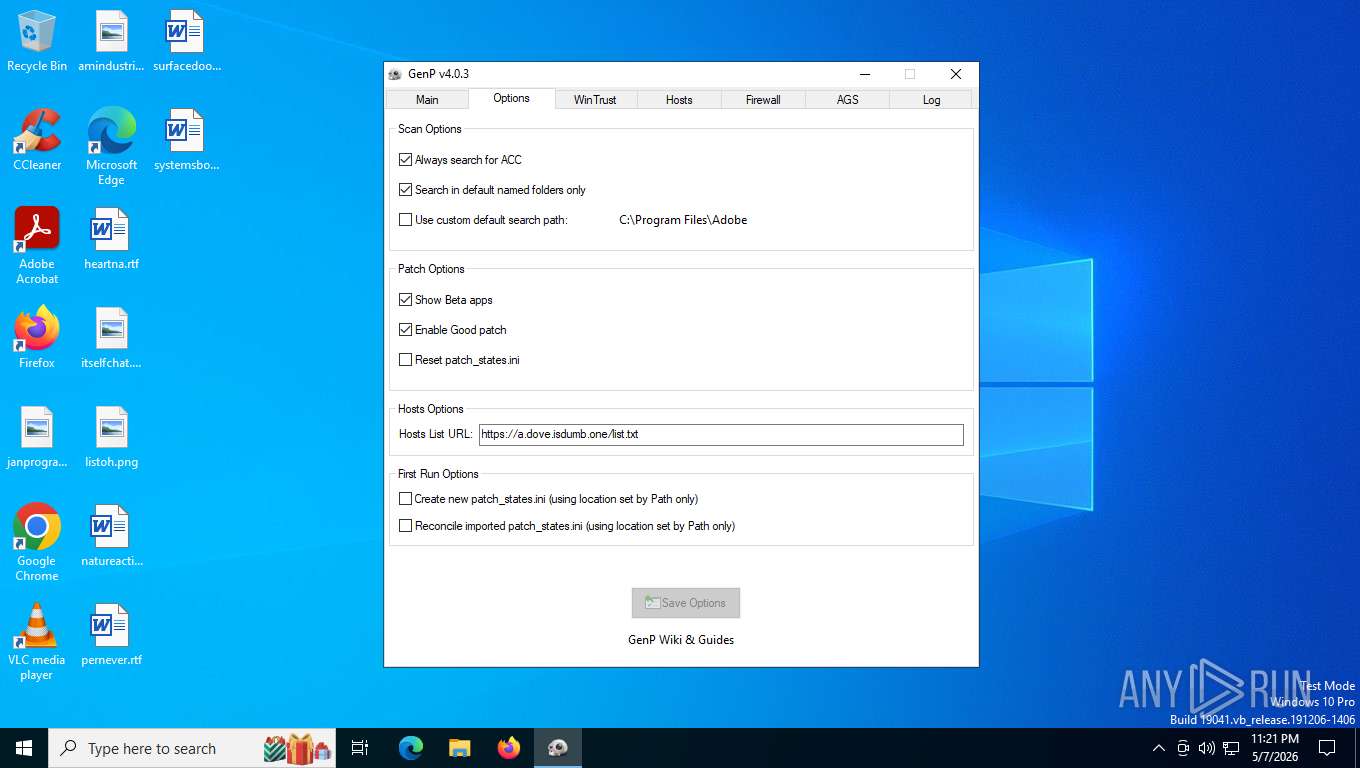
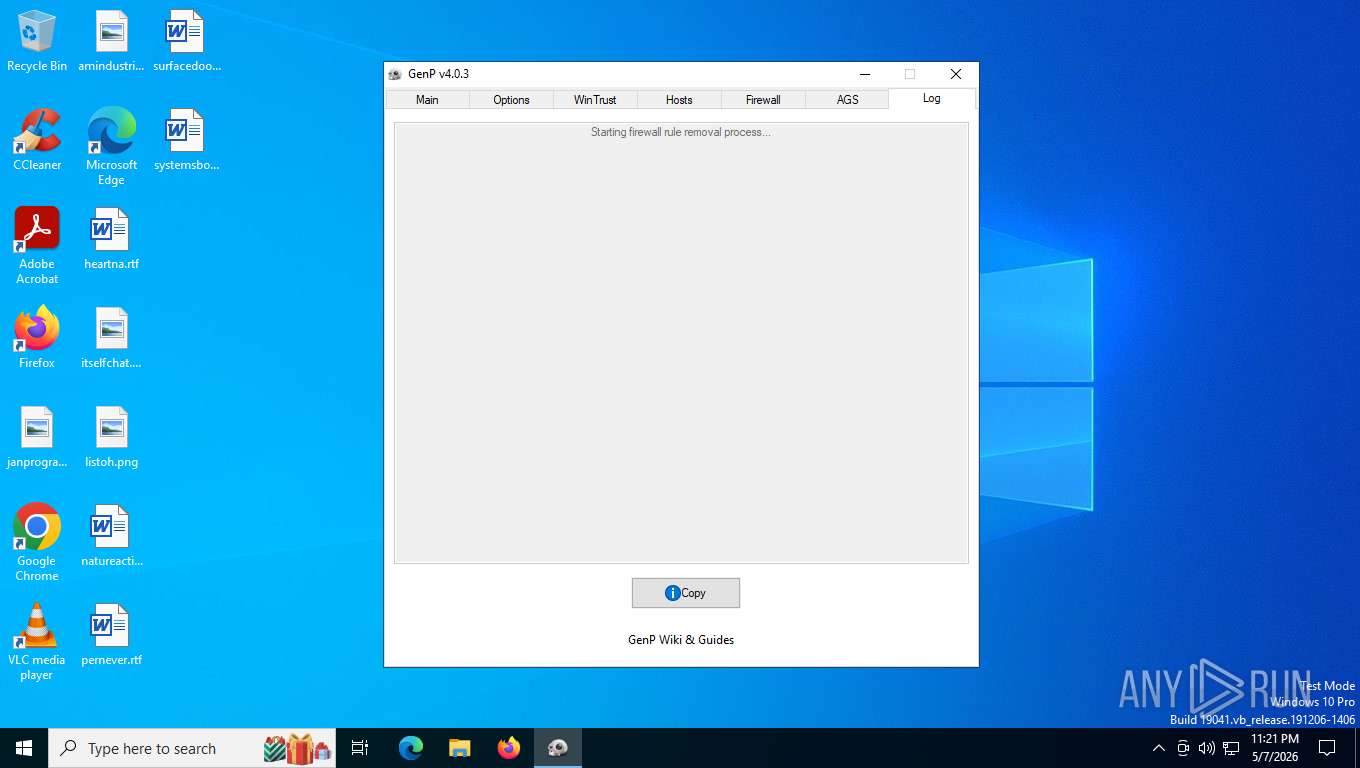
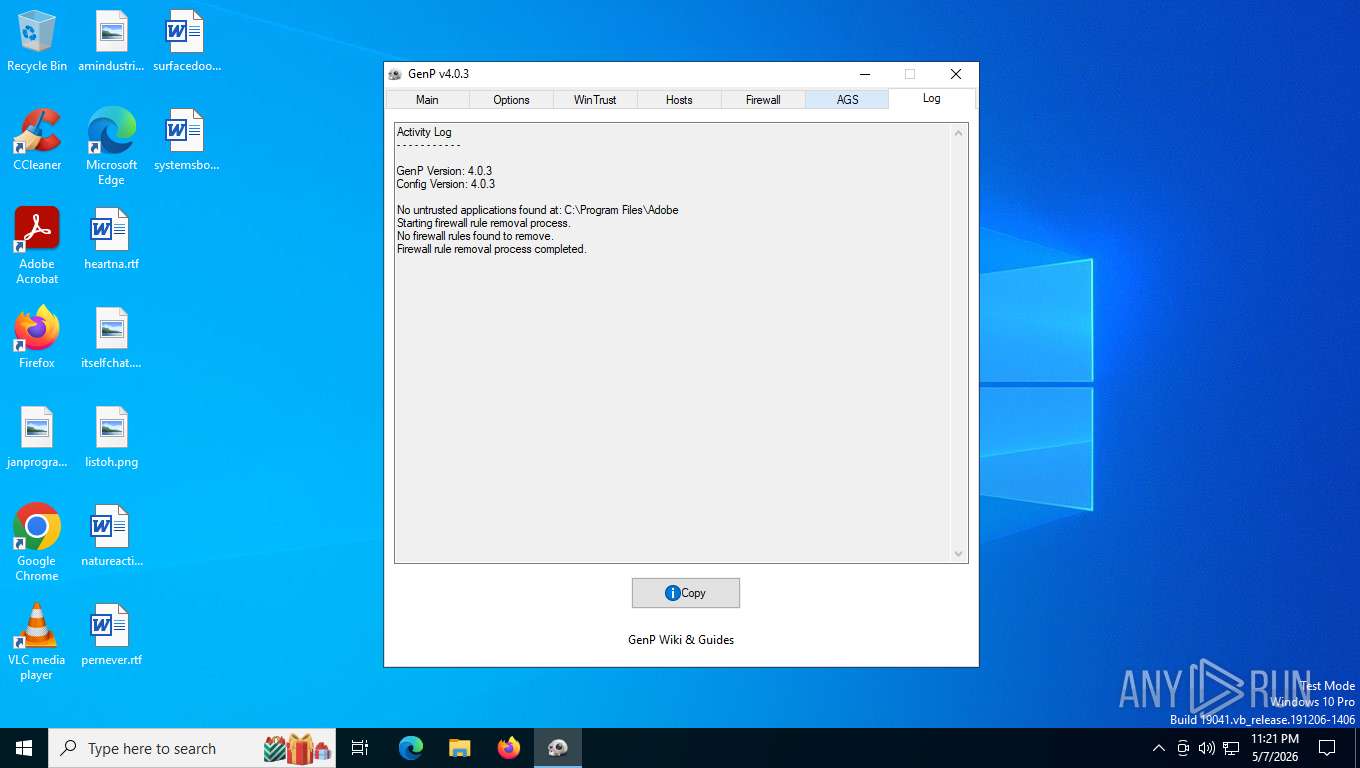
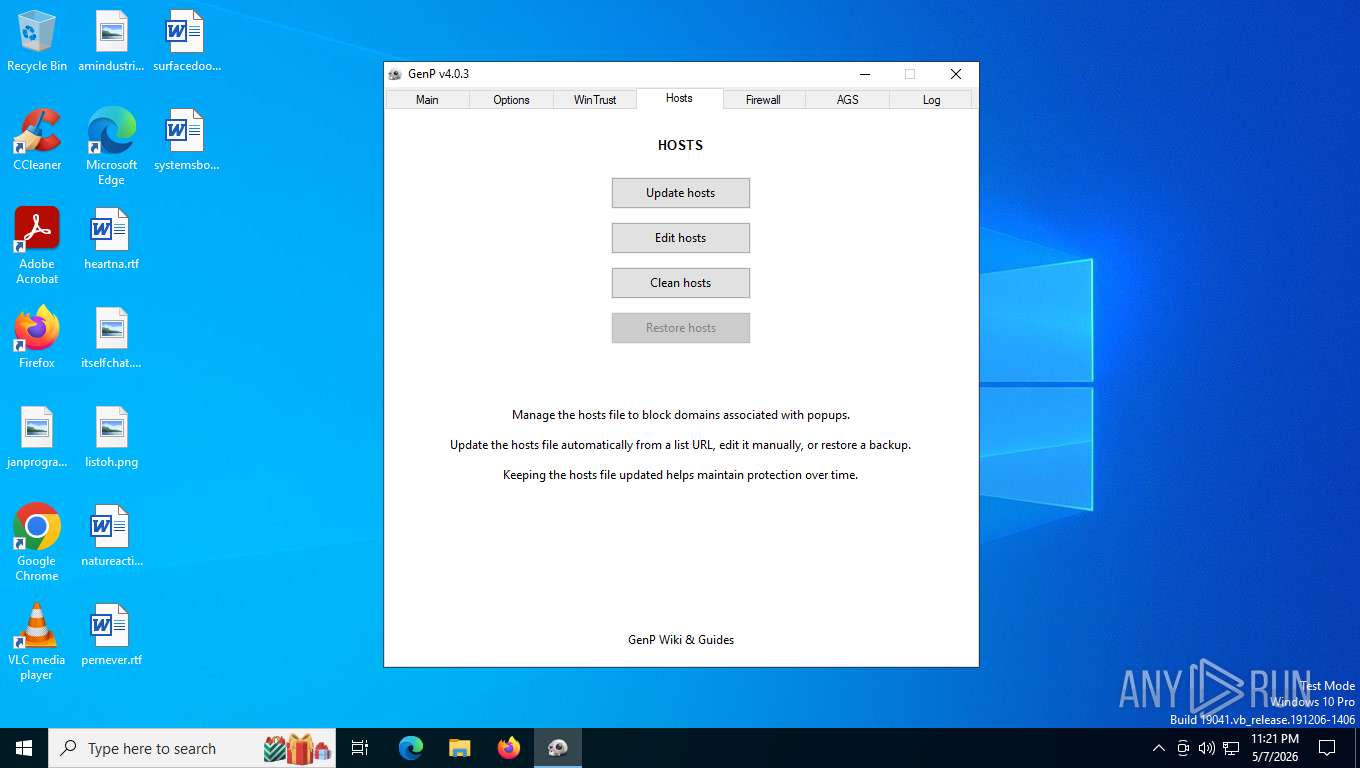
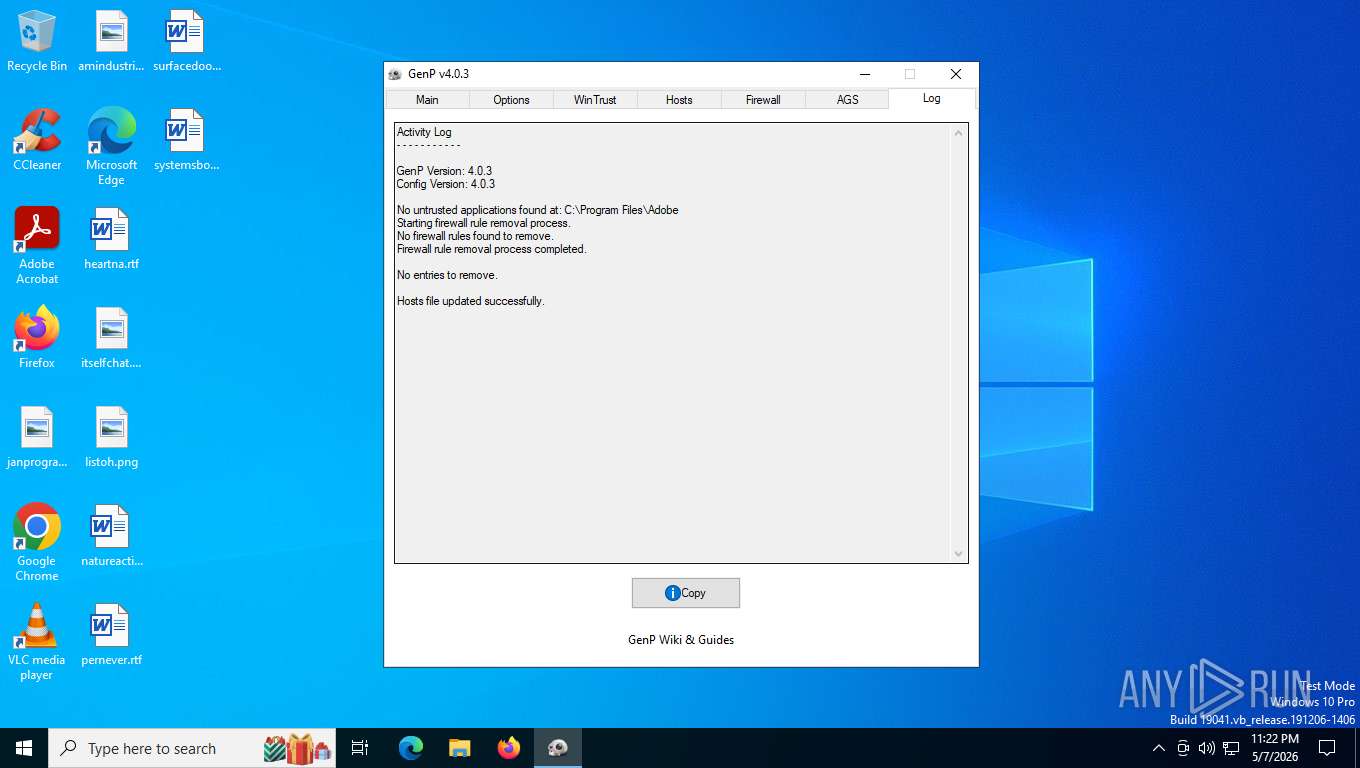
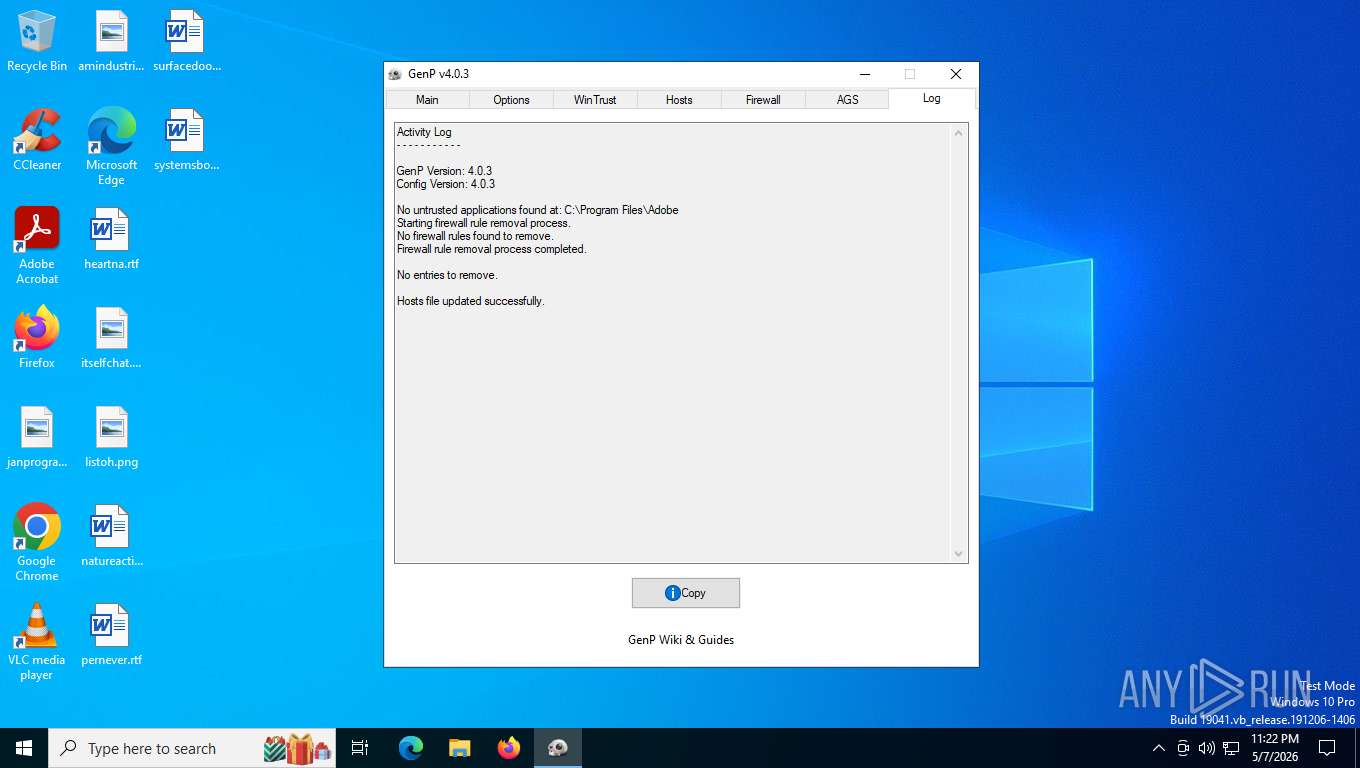
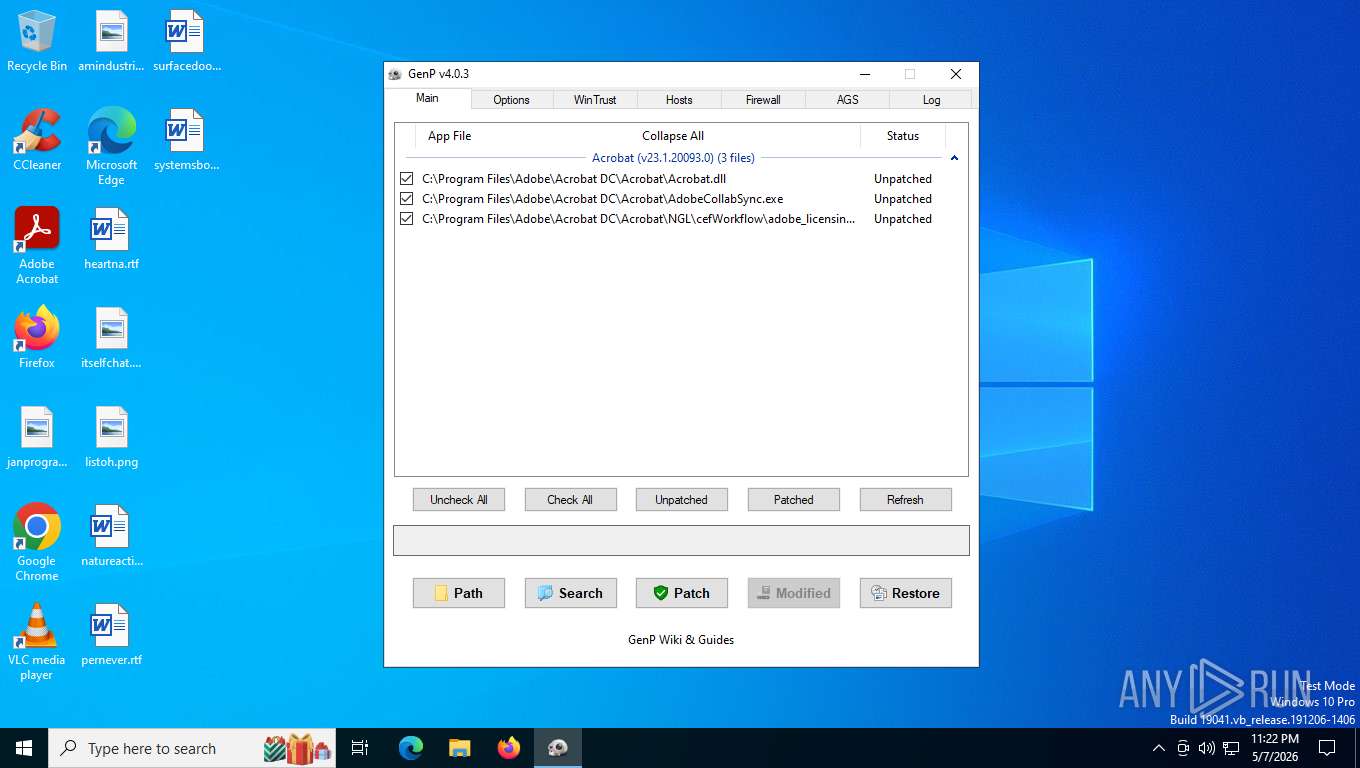
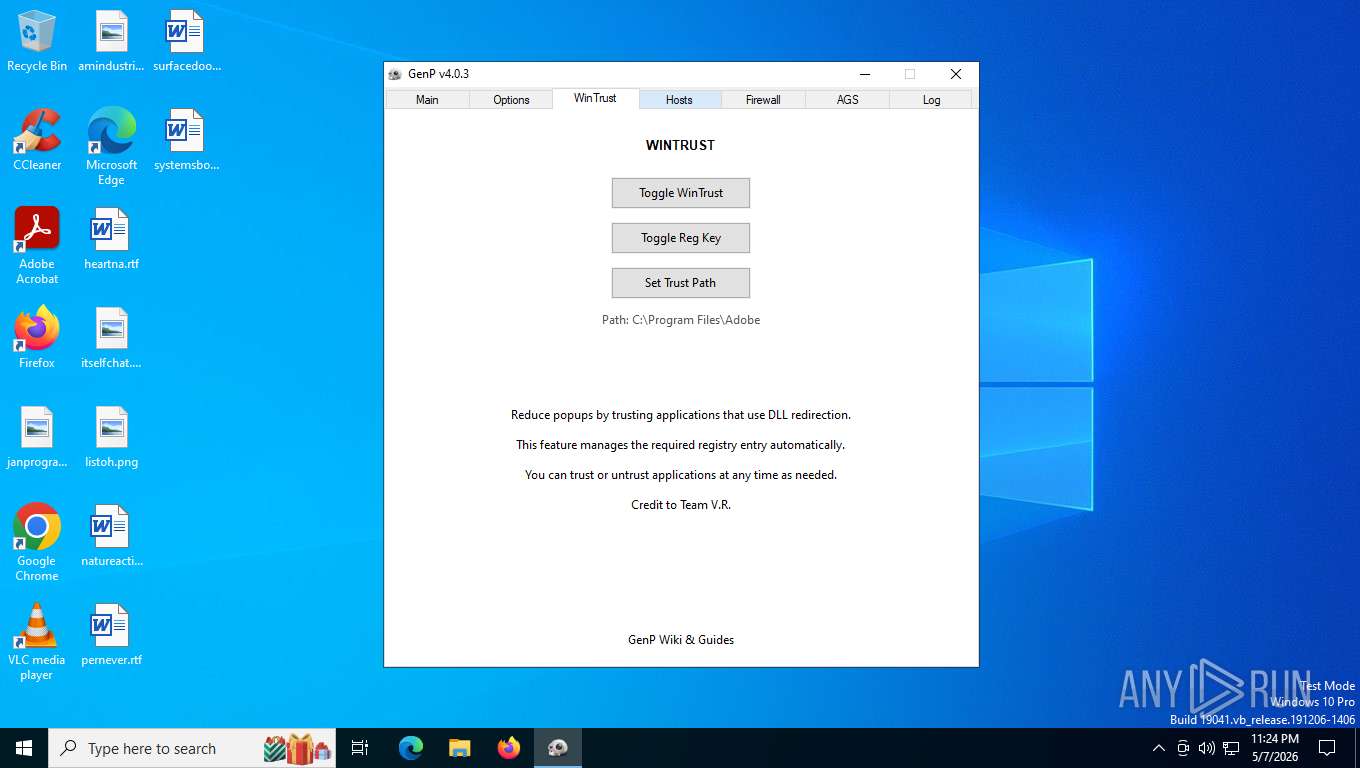
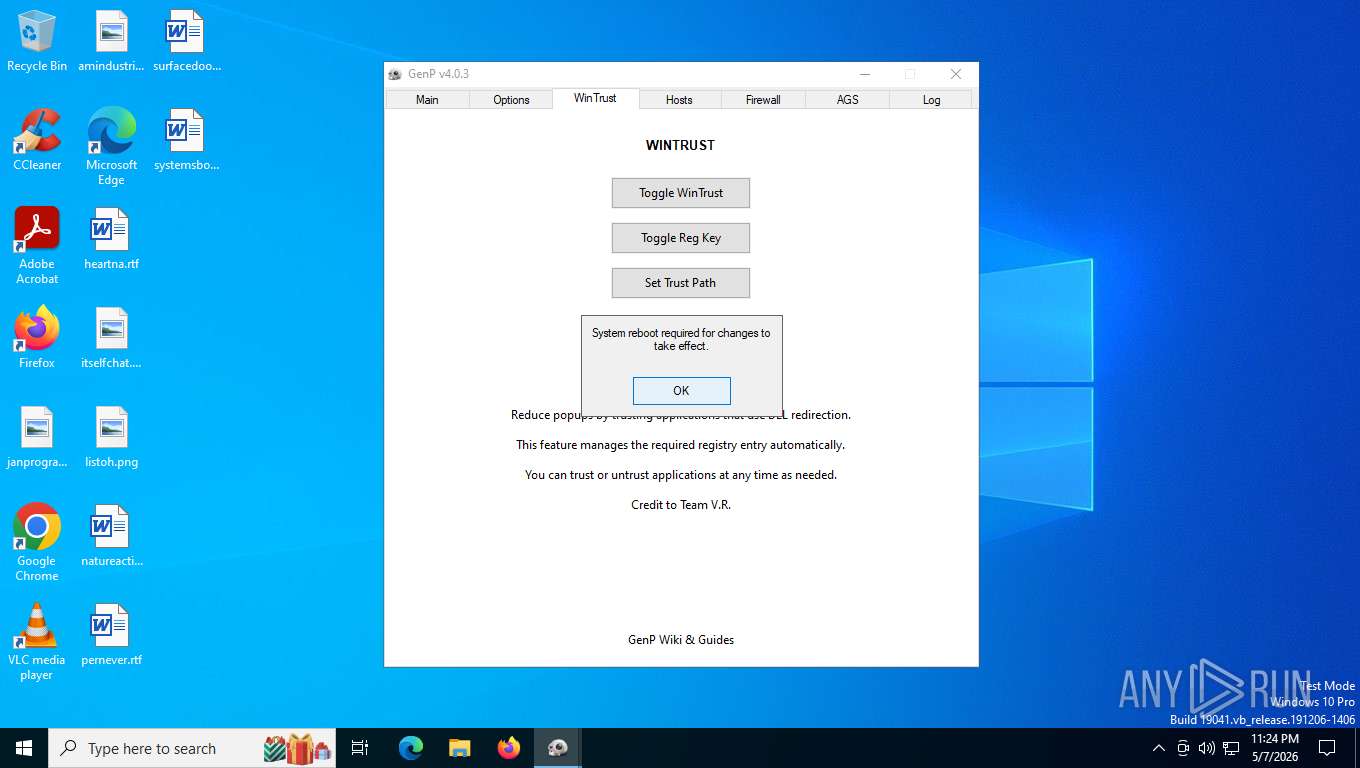
Modifies hosts file to alter network resolution
- GenP-v4.0.3.exe (PID: 6980)
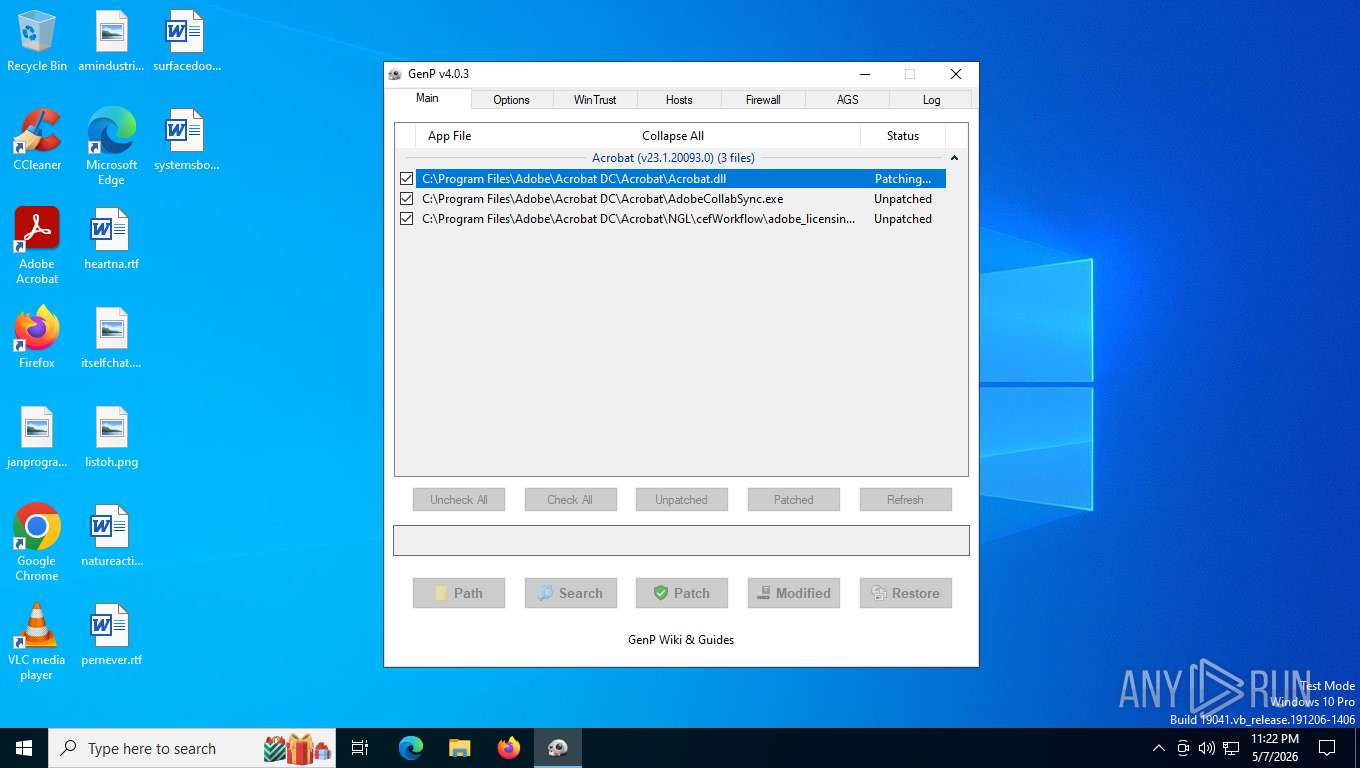
Uses TASKKILL.EXE to kill process
- GenP-v4.0.3.exe (PID: 6980)
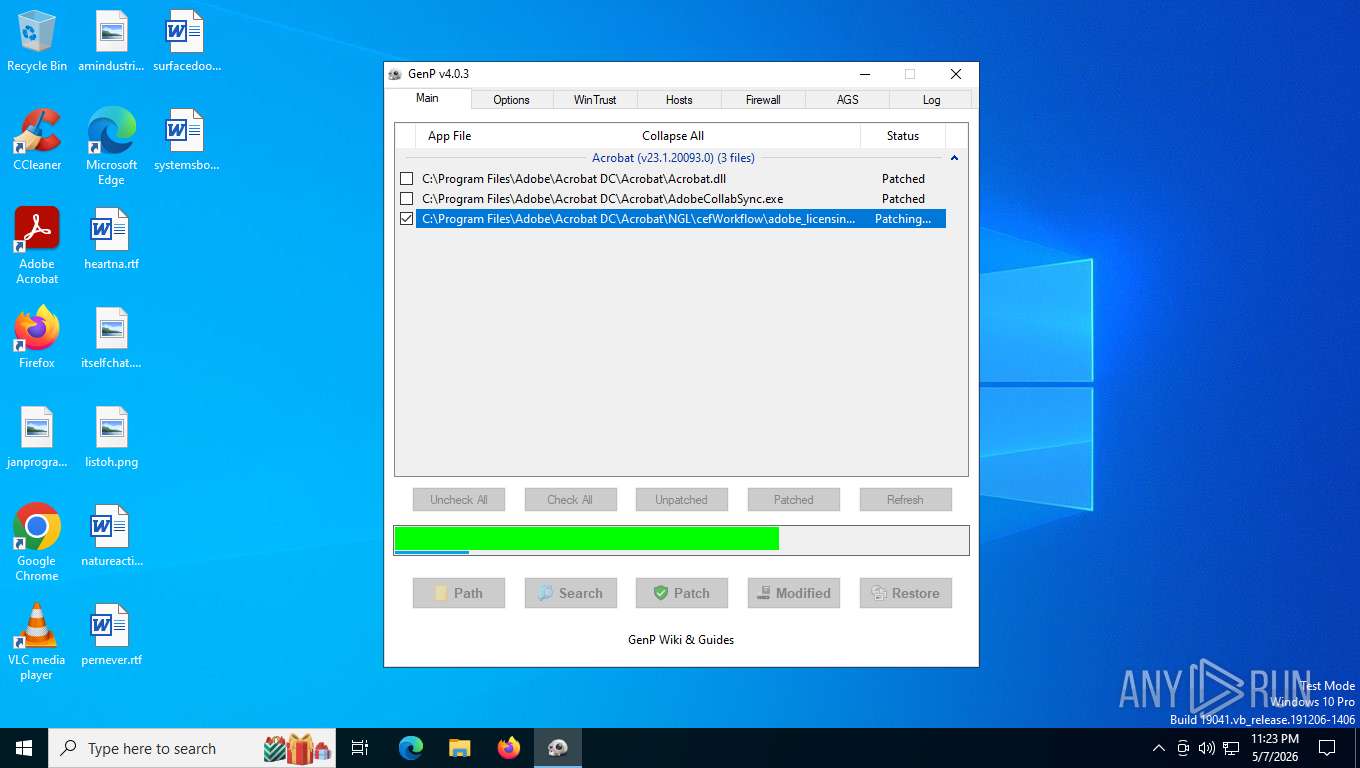
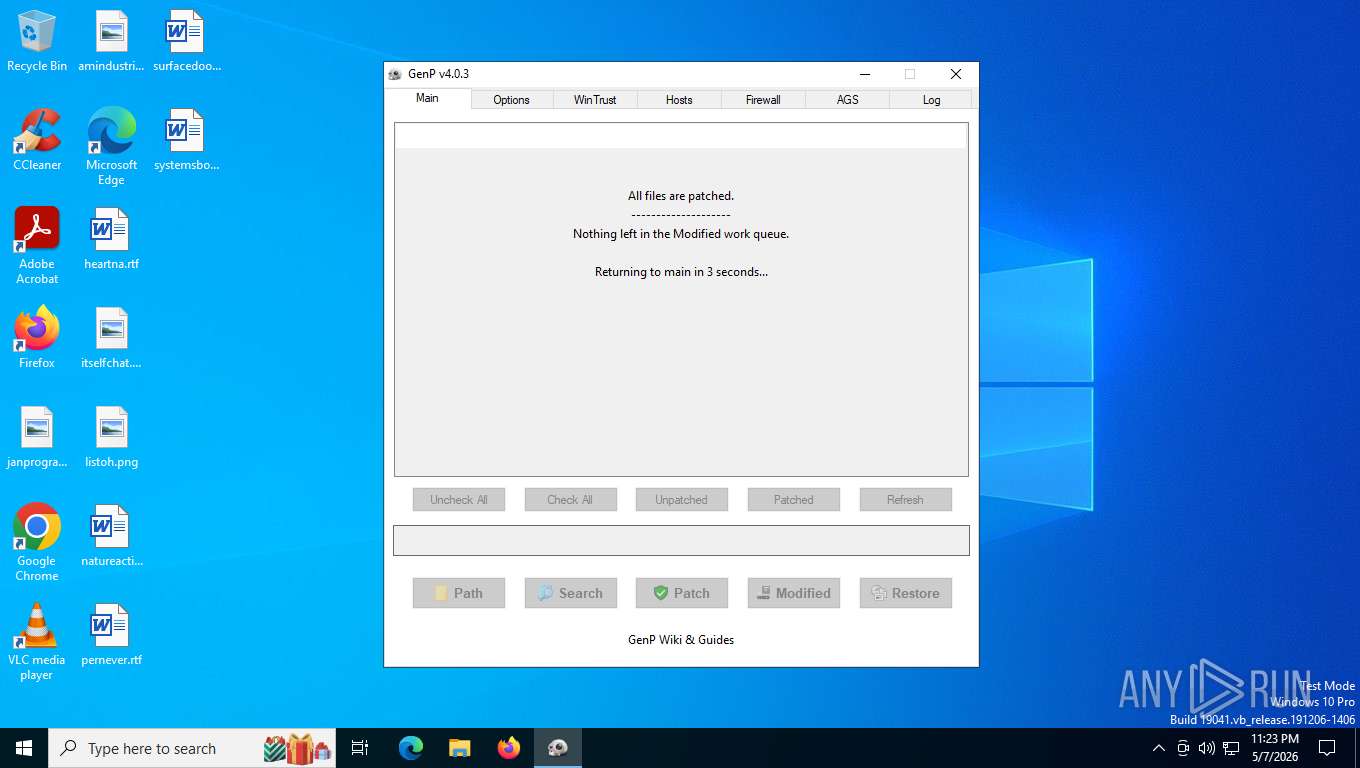
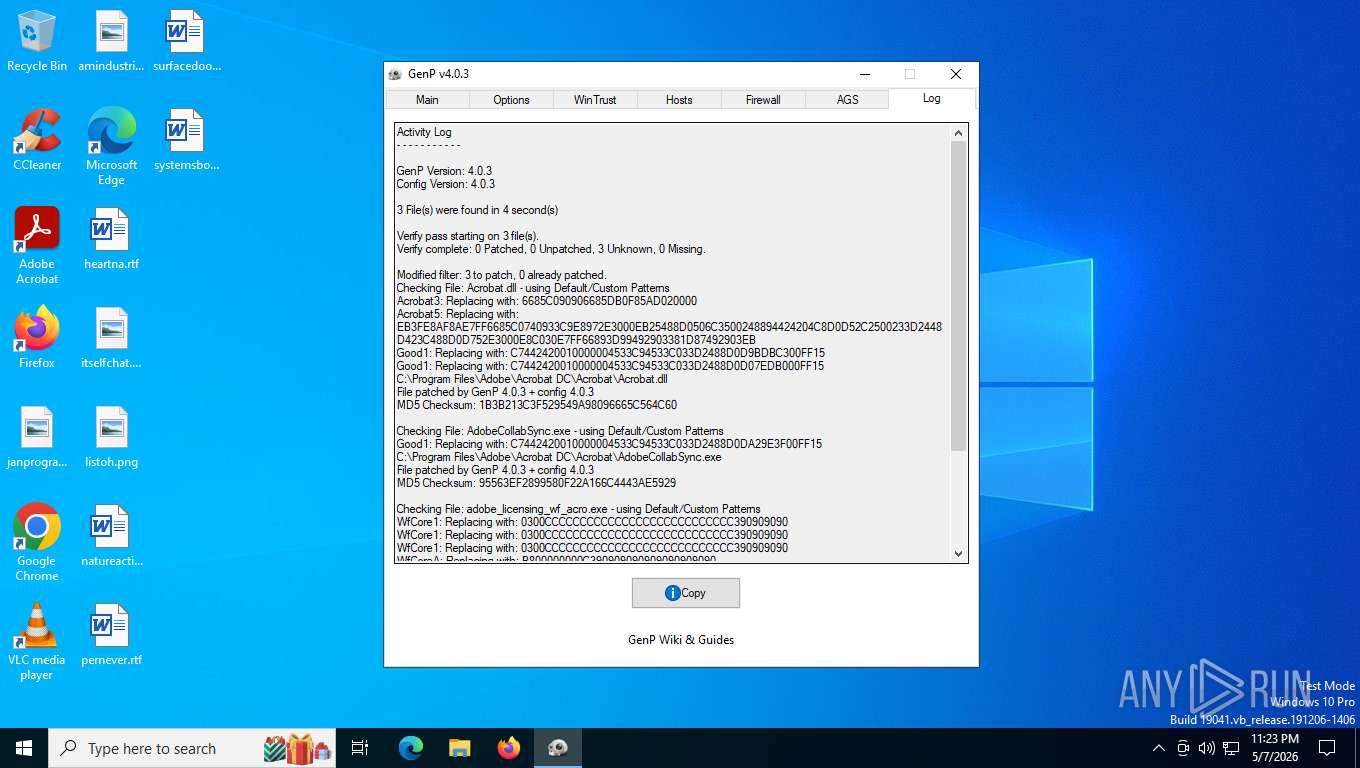
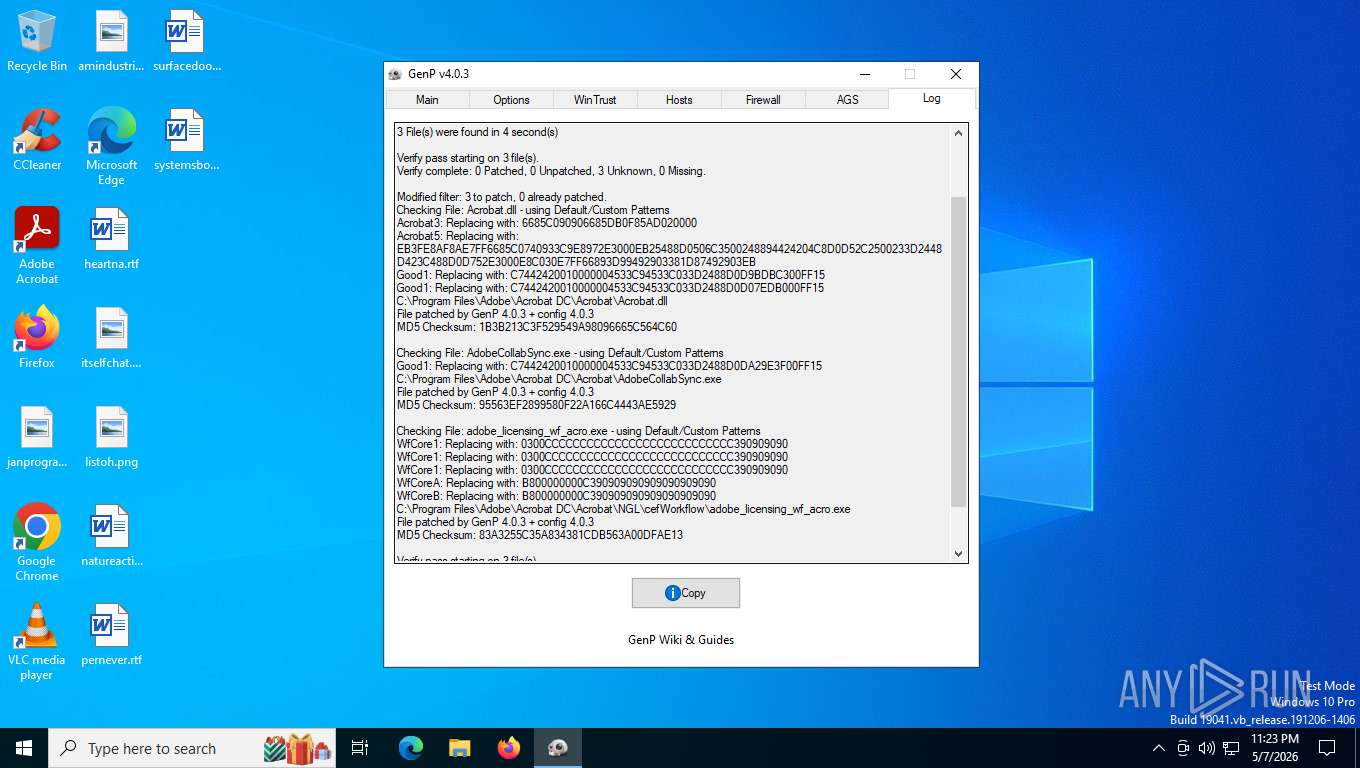
Executable content was dropped or overwritten
- GenP-v4.0.3.exe (PID: 6980)
Windows service management via SC.EXE
- sc.exe (PID: 2900)
- sc.exe (PID: 4688)
Service autostart disabling
- sc.exe (PID: 4688)
- sc.exe (PID: 2900)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4420)
INFO
Checks supported languages
- GenP-v4.0.3.exe (PID: 6980)
- identity_helper.exe (PID: 7320)
The sample compiled with english language support
- GenP-v4.0.3.exe (PID: 6980)
Reads the computer name
- GenP-v4.0.3.exe (PID: 6980)
- identity_helper.exe (PID: 7320)
Reads mouse settings
- GenP-v4.0.3.exe (PID: 6980)
There is functionality for taking screenshot (YARA)
- GenP-v4.0.3.exe (PID: 6980)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2424)
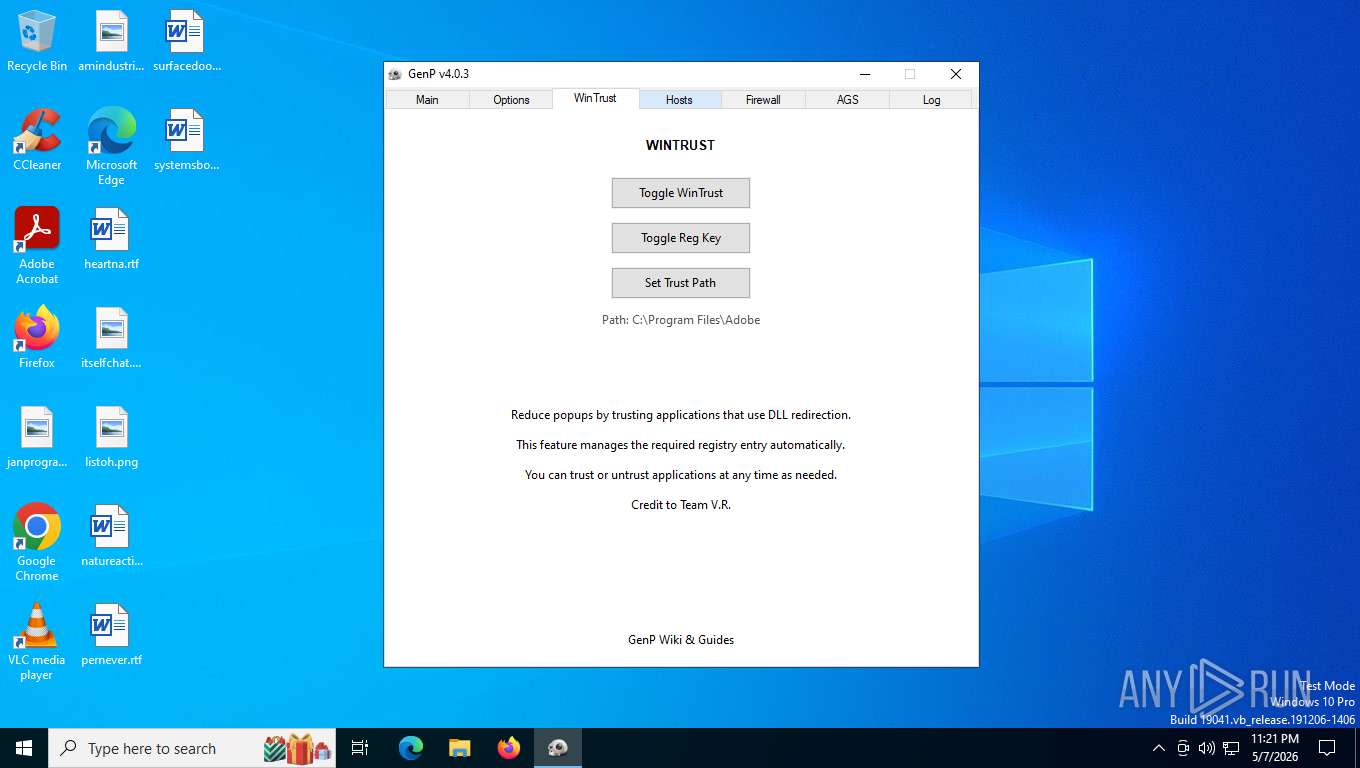
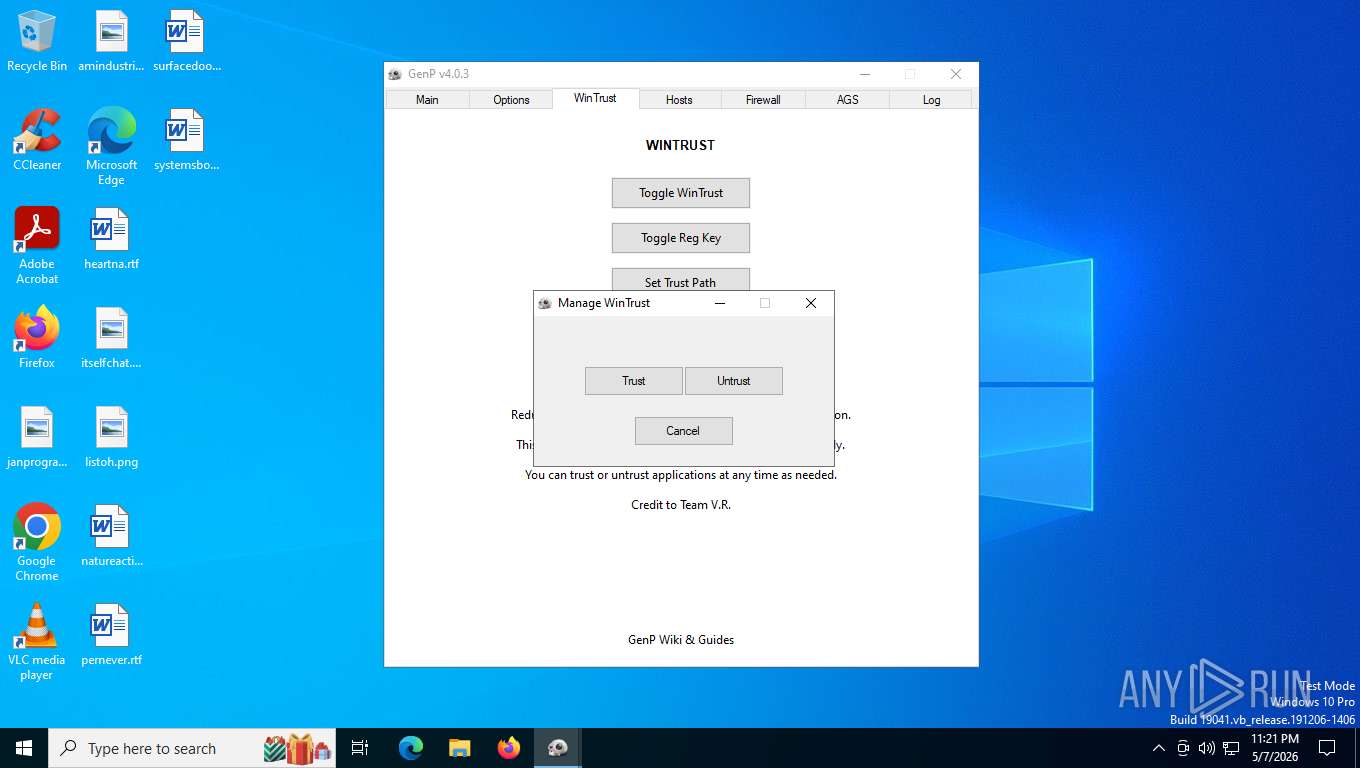
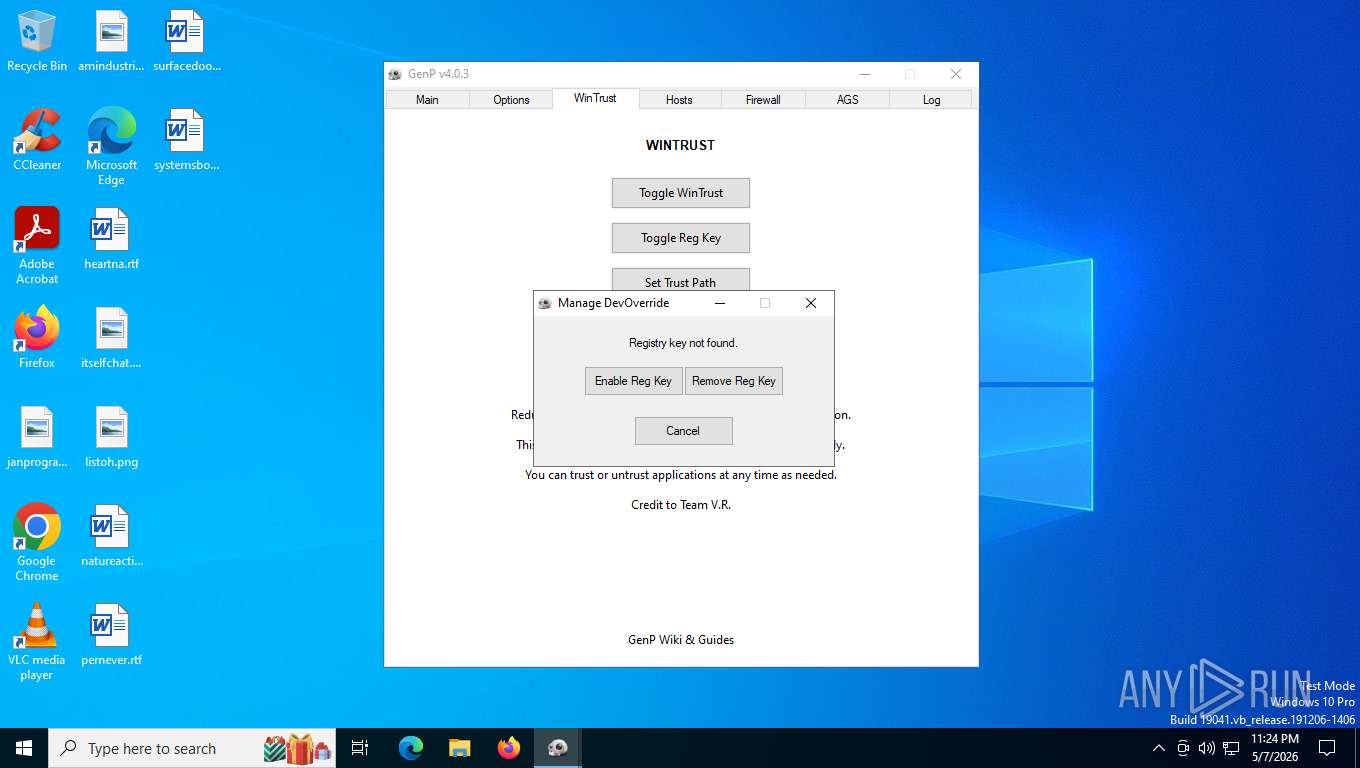
The process uses AutoIt
- GenP-v4.0.3.exe (PID: 6980)
Create files in a temporary directory
- GenP-v4.0.3.exe (PID: 6980)
Reads the machine GUID from the registry
- GenP-v4.0.3.exe (PID: 6980)
Reads security settings of Internet Explorer
- GenP-v4.0.3.exe (PID: 6980)
- Taskmgr.exe (PID: 4364)
Creates files or folders in the user directory
- GenP-v4.0.3.exe (PID: 6980)
Application launched itself
- Acrobat.exe (PID: 2896)
- AcroCEF.exe (PID: 7340)
- msedge.exe (PID: 5612)
Reads Environment values
- identity_helper.exe (PID: 7320)
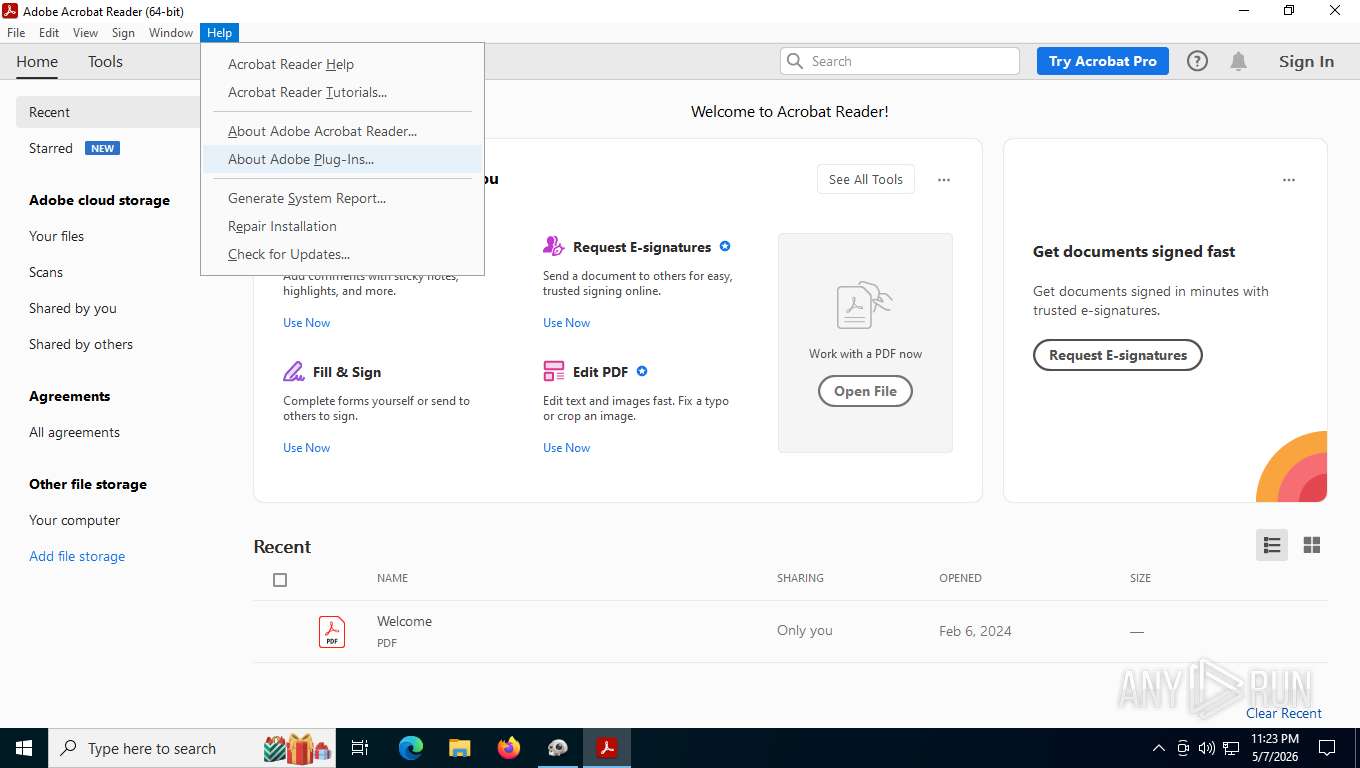
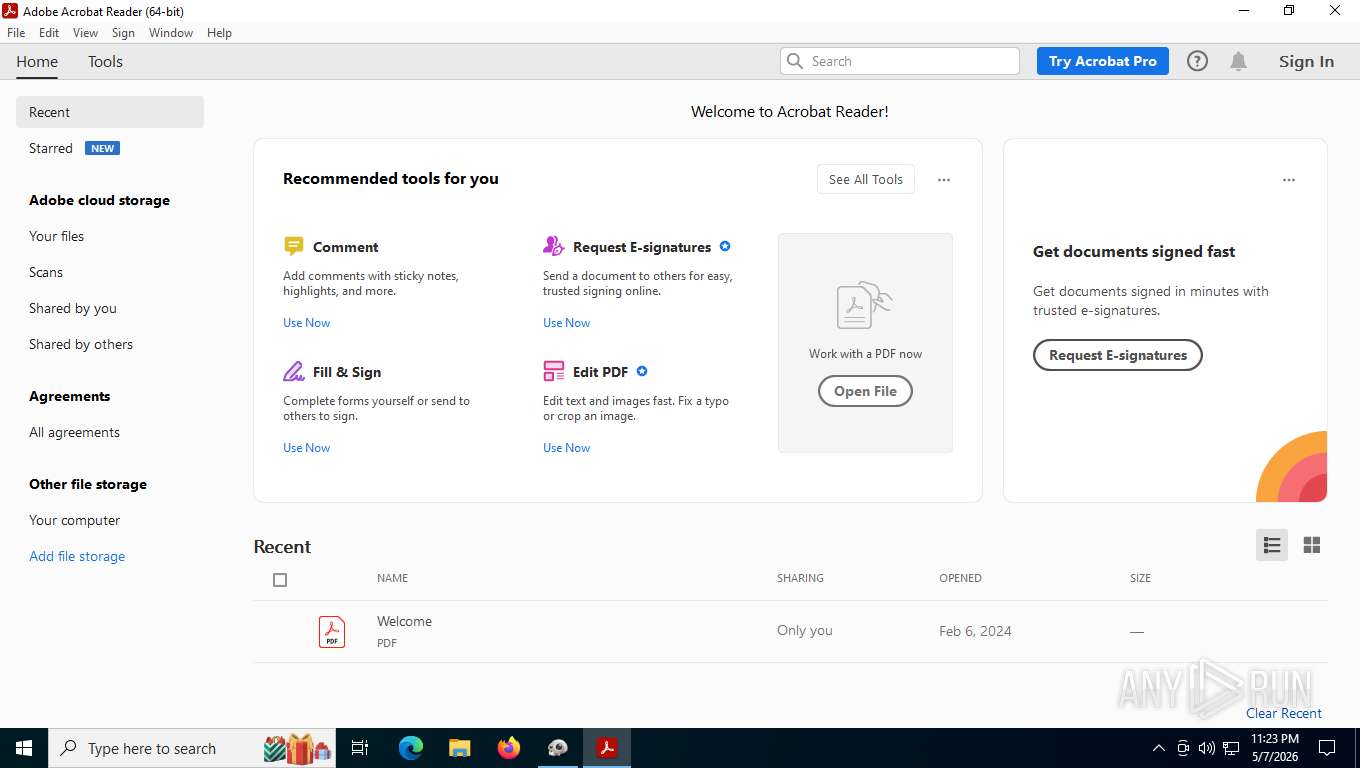
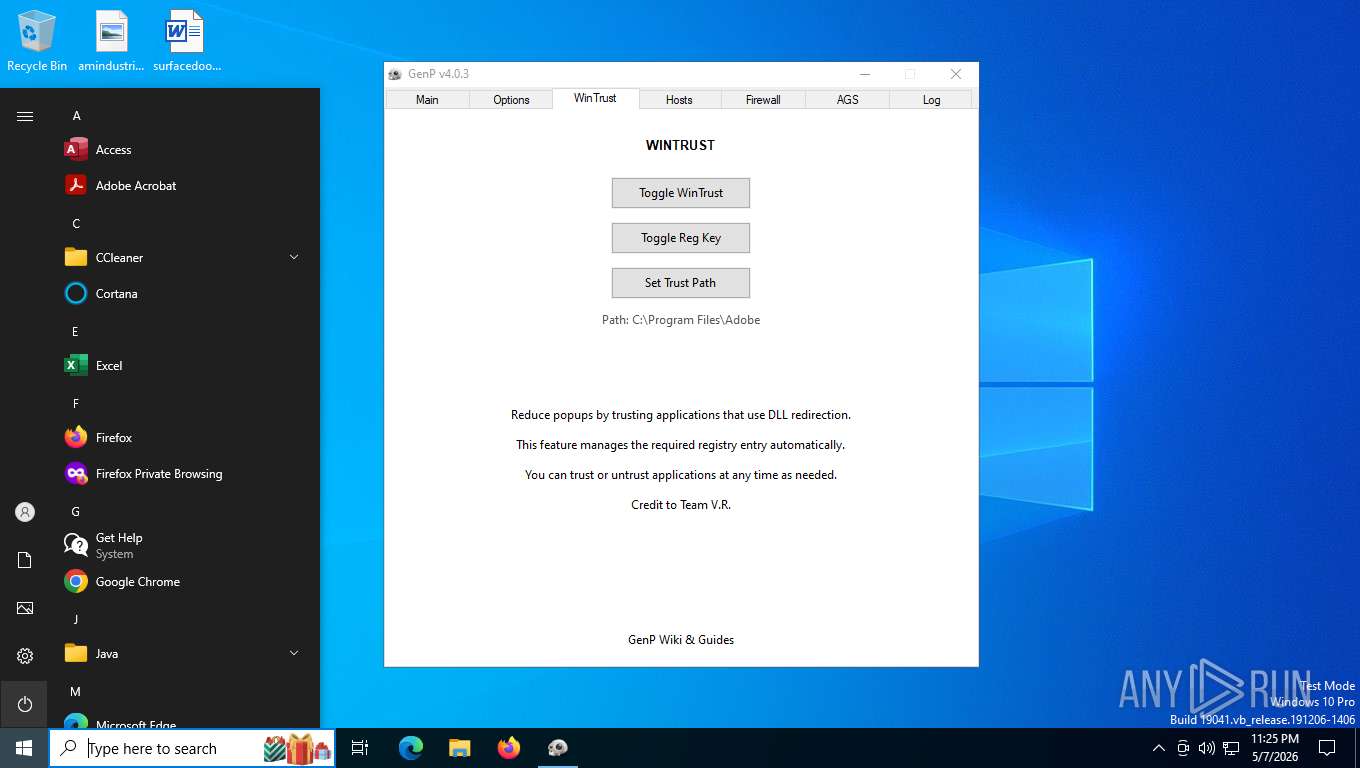
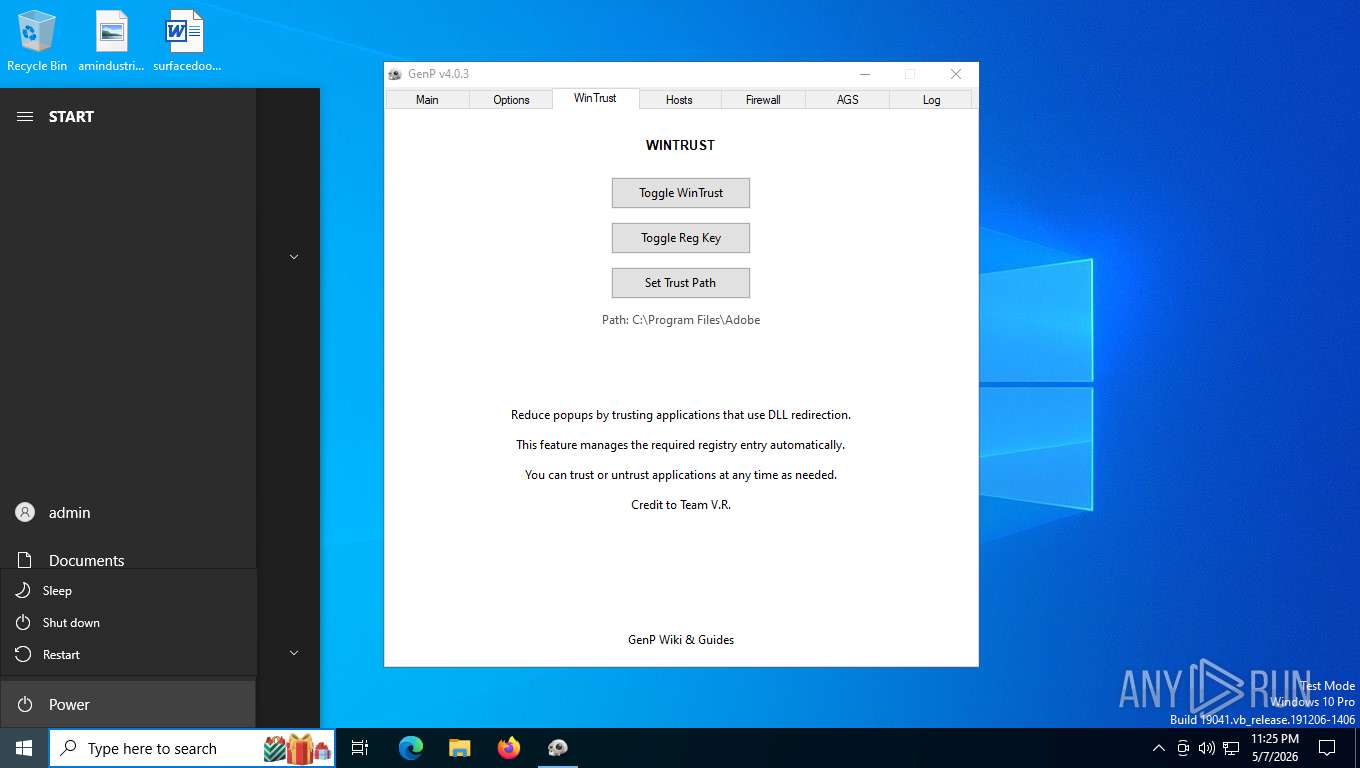
Manual execution by a user
- Acrobat.exe (PID: 2896)
- Taskmgr.exe (PID: 492)
- Taskmgr.exe (PID: 4364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2026:05:05 08:22:30+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 757760 |
| InitializedDataSize: | 1425408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x24218 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.3.0 |
| ProductVersionNumber: | 4.0.3.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 4.0.3 |
| Comments: | GenP |
| FileDescription: | GenP |
| ProductName: | GenP |
| ProductVersion: | 4.0.3 |
| CompanyName: | GenP |
| LegalCopyright: | GenP 2026 |
| LegalTradeMarks: | GenP 2026 |
| ID: | GenP-5/5/2026-8:22:30 AM |
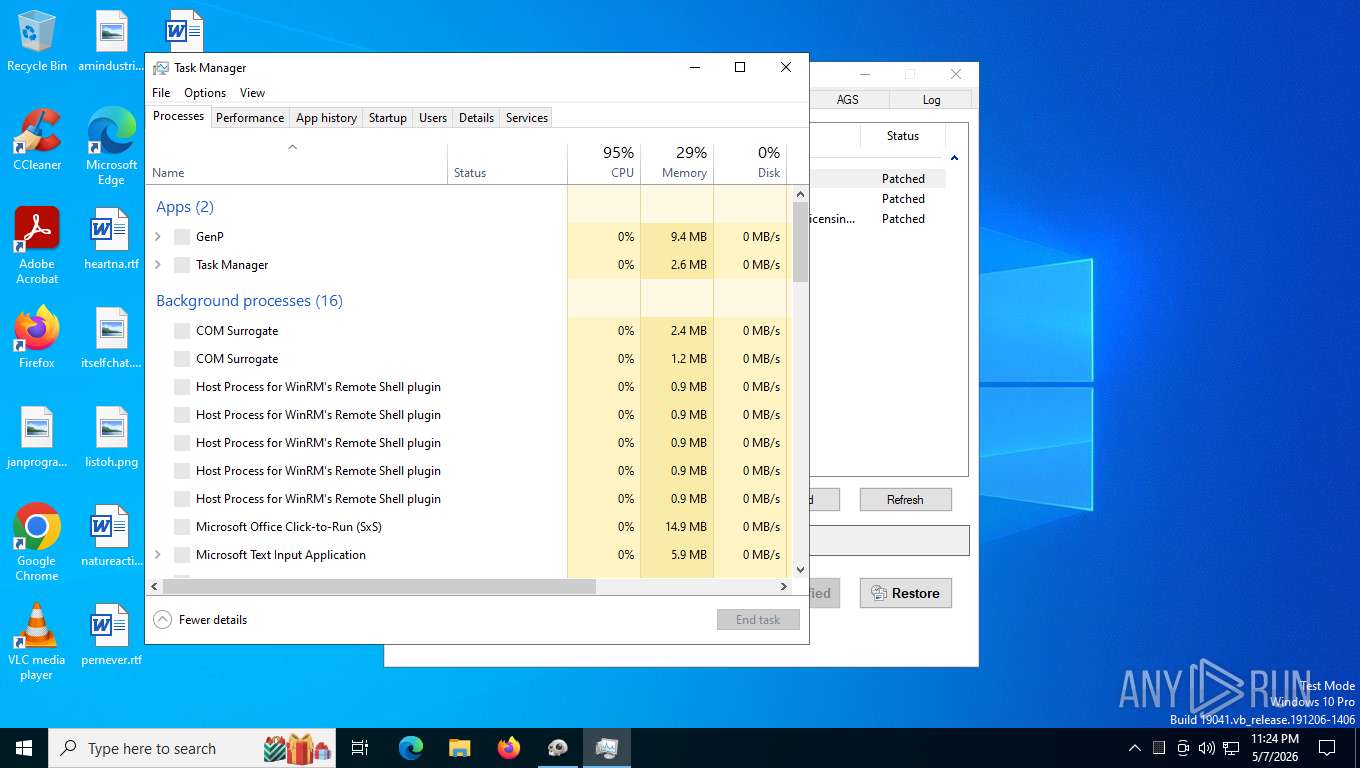
Total processes
320
Monitored processes
52
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 492 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2904 --field-trial-handle=1364,i,13390911756880566117,320235774671914576,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 936 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | TASKKILL /F /T /IM "adobe_licensing_wf_acro.exe" | C:\Windows\System32\taskkill.exe | — | GenP-v4.0.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2656 --field-trial-handle=1364,i,13390911756880566117,320235774671914576,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2424 | powershell.exe -Command "Get-NetFirewallRule -Direction Outbound | Where-Object { $_.DisplayName -like 'Adobe-Block*' } | Select-Object -Property DisplayName" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4328,i,13892232702319952382,15575993474447846918,262144 --variations-seed-version --mojo-platform-channel-handle=4336 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
36 475
Read events
36 332
Write events
134
Delete events
9
Modification events
| (PID) Process: | (6980) GenP-v4.0.3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6980) GenP-v4.0.3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6980) GenP-v4.0.3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2896) Acrobat.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | write | Name: | DisplayName |
Value: Adobe Acrobat Reader Protected Mode | |||
| (PID) Process: | (7104) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (7104) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\DLLInjection |
| Operation: | write | Name: | bBlockDLLInjection |
Value: 0 | |||
| (PID) Process: | (7104) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\SessionManagement |
| Operation: | write | Name: | bNormalExit |
Value: 0 | |||
| (PID) Process: | (7104) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\SessionManagement\cWindowsCurrent\cWin0 |
| Operation: | write | Name: | iTabCount |
Value: 0 | |||
| (PID) Process: | (7104) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\SessionManagement\cWindowsCurrent |
| Operation: | write | Name: | iWinCount |
Value: 1 | |||
| (PID) Process: | (7104) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVGeneral |
| Operation: | write | Name: | uLastAppLaunchTimeStamp |
Value: 94142456 | |||
Executable files
11
Suspicious files
325
Text files
284
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6980 | GenP-v4.0.3.exe | C:\Users\admin\AppData\Local\Temp\aut5457.tmp | binary | |
MD5:3034BFB6F82F96FD684AF5BED9485388 | SHA256:FD87D883976C2711F29AE2FE8A41D199DDEDC22E8977A32B304153A3ECB1AA84 | |||
| 6980 | GenP-v4.0.3.exe | C:\Users\admin\Downloads\config.ini | text | |
MD5:B6706ECCA9E5349ED1EB3E330CC762DE | SHA256:0C499BF43FCA5620168C7E2FC52B8BDA0CBA8F0AAFF1148459B326B517C011BC | |||
| 6980 | GenP-v4.0.3.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 6980 | GenP-v4.0.3.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 5920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jcgrhrsu.rka.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_g1piblph.b4b.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1p1bdgvh.4q4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zshs1snl.vr0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6980 | GenP-v4.0.3.exe | C:\Windows\System32\drivers\etc\hosts.bak | text | |
MD5:C40F0E533A52F202035621D27E732F5A | SHA256:408442168118E82FAF7D419AA4F0D8FA04F45A5E6D0E7065A9CDC723782C5AE3 | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ydtfu4ri.cok.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
353
TCP/UDP connections
158
DNS requests
135
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
2248 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
2248 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
2248 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
2248 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/FlightSettings/FSService?ProcessorClockSpeed=3094&IsRetailOS=1&OEMManufacturerName=DELL&FlightingPolicyValue=3&EnablePreviewBuilds=4294967295&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&ManagePreviewBuilds=3&BranchReadinessLevelSource=0&AttrDataVer=186&ProcessorCores=6&BranchReadinessLevelRaw=16&TotalPhysicalRAM=6144&TPMVersion=0&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&DeviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&App=FSS&AppVer=10.0&SmartActiveHoursState=1&ActiveHoursStart=20&SecureBootCapable=0&ActiveHoursEnd=13&DeviceFamily=Windows.Desktop | US | text | 87.3 Kb | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.160.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
2248 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 407 b | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.160.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.160.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
876 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7240 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
876 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
876 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
876 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
876 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6980 | GenP-v4.0.3.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |