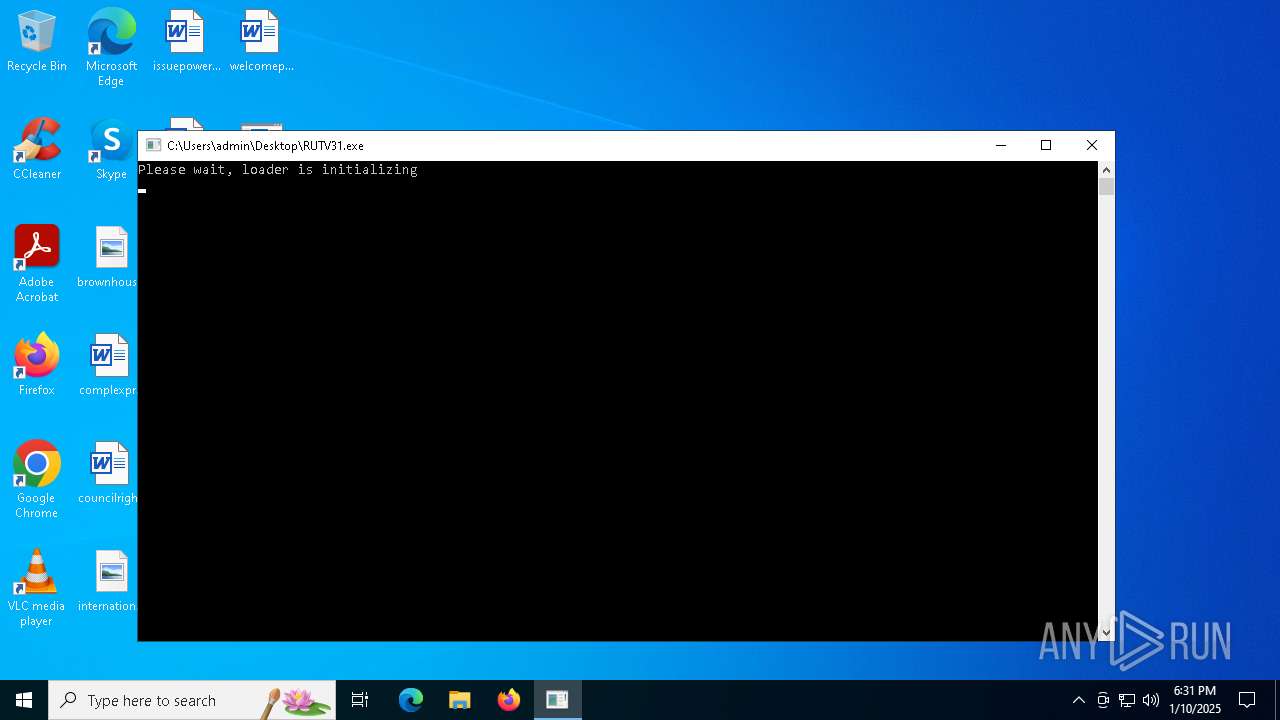
| File name: | RUTV31.exe |
| Full analysis: | https://app.any.run/tasks/2c328587-4bf3-4869-9f38-729ef53e8d99 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 18:30:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 13 sections |
| MD5: | 7321895DDA0016F090D1BE2061AE0614 |
| SHA1: | F3286858C7B60A05119697299B2BFFB8276E7B0C |
| SHA256: | 7C3E6C8115C0D2EAB7786C2A0BF4AB38698BAF3F0302A2B5C9C515ABC090553E |
| SSDEEP: | 98304:/Rl0Q/ksgId0XGf5smu/+eMl2gDbsoDPbKHZU0efByrDu0DClODBFZPytuKRToCC:GLkEO/npt0DJguVG7NC79SvrPuKu0AIK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- RUTV31.exe (PID: 5640)
- ldrupd.bin (PID: 1476)
- RUTV31.exe (PID: 3832)
Searches for installed software
- RUTV31.exe (PID: 5640)
- RUTV31.exe (PID: 3832)
Reads the Windows owner or organization settings
- RUTV31.exe (PID: 5640)
- RUTV31.exe (PID: 3832)
Executable content was dropped or overwritten
- RUTV31.exe (PID: 5640)
- ldrupd.bin (PID: 1476)
Starts application with an unusual extension
- RUTV31.exe (PID: 5640)
Starts CMD.EXE for commands execution
- RUTV31.exe (PID: 5640)
- RUTV31.exe (PID: 3832)
Reads security settings of Internet Explorer
- ldrupd.bin (PID: 1476)
Reads the BIOS version
- RUTV31.exe (PID: 3832)
Connects to unusual port
- RUTV31.exe (PID: 3832)
INFO
Reads product name
- RUTV31.exe (PID: 5640)
- RUTV31.exe (PID: 3832)
Reads Windows Product ID
- RUTV31.exe (PID: 5640)
- RUTV31.exe (PID: 3832)
Creates files or folders in the user directory
- RUTV31.exe (PID: 5640)
Reads Environment values
- RUTV31.exe (PID: 5640)
- RUTV31.exe (PID: 3832)
Checks supported languages
- ldrupd.bin (PID: 1476)
- RUTV31.exe (PID: 3832)
The process uses the downloaded file
- ldrupd.bin (PID: 1476)
Process checks computer location settings
- ldrupd.bin (PID: 1476)
Reads the computer name
- ldrupd.bin (PID: 1476)
- RUTV31.exe (PID: 3832)
Process checks whether UAC notifications are on
- RUTV31.exe (PID: 3832)
Reads the machine GUID from the registry
- RUTV31.exe (PID: 3832)
Themida protector has been detected
- RUTV31.exe (PID: 3832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:07 13:29:48+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.37 |
| CodeSize: | 1041408 |
| InitializedDataSize: | 413696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1557058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
125
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1476 | "C:\Users\admin\AppData\Local\ldrupd.bin" | C:\Users\admin\AppData\Local\ldrupd.bin | RUTV31.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\Desktop\RUTV31.exe" | C:\Users\admin\Desktop\RUTV31.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3612 | "C:\WINDOWS\SysWOW64\cmd.exe" | C:\Windows\SysWOW64\cmd.exe | — | RUTV31.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3724 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RUTV31.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3832 | "C:\Users\admin\Desktop\RUTV31.exe" | C:\Users\admin\Desktop\RUTV31.exe | ldrupd.bin | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 4540 | "C:\WINDOWS\SysWOW64\cmd.exe" | C:\Windows\SysWOW64\cmd.exe | — | RUTV31.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5112 | "C:\WINDOWS\SysWOW64\cmd.exe" | C:\Windows\SysWOW64\cmd.exe | — | RUTV31.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5640 | "C:\Users\admin\Desktop\RUTV31.exe" | C:\Users\admin\Desktop\RUTV31.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5968 | "C:\WINDOWS\SysWOW64\cmd.exe" | C:\Windows\SysWOW64\cmd.exe | — | RUTV31.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
966
Read events
966
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | ldrupd.bin | C:\Users\admin\Desktop\RUTV31.exe | executable | |
MD5:3F8F9BED19560F1FB171FD9B9688A1F7 | SHA256:3E608F5AEF7AFD382FA63B70D969A88B51330012E7678EF17057BF9F9B7934C1 | |||
| 5640 | RUTV31.exe | C:\Users\admin\AppData\Local\ldrupd.bin | executable | |
MD5:A24978A6B77E2CD99823E24C6EB4D055 | SHA256:80AC94C086EB6E52BC3BBEBD86E0795F6CB7476153AF0C767B9AE4B7E9931140 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
25
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1380 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1380 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1380 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1380 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1380 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 51.222.31.217:3333 | — | OVH SAS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |