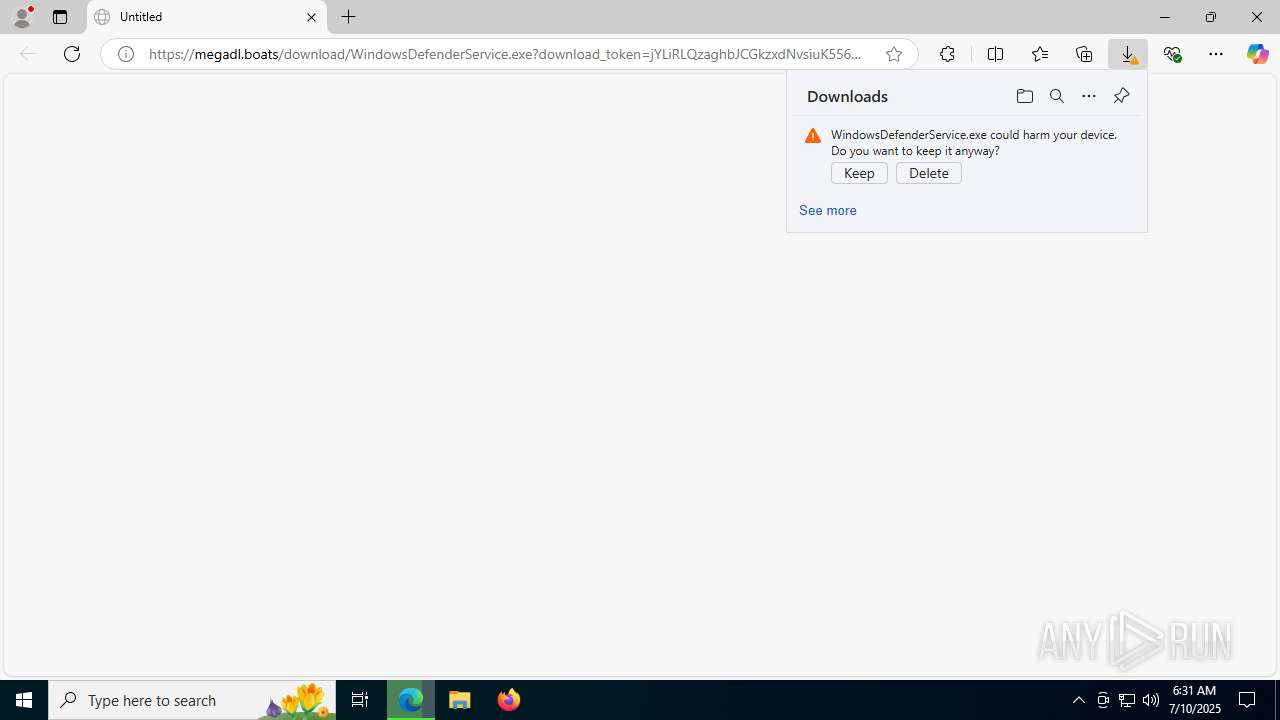
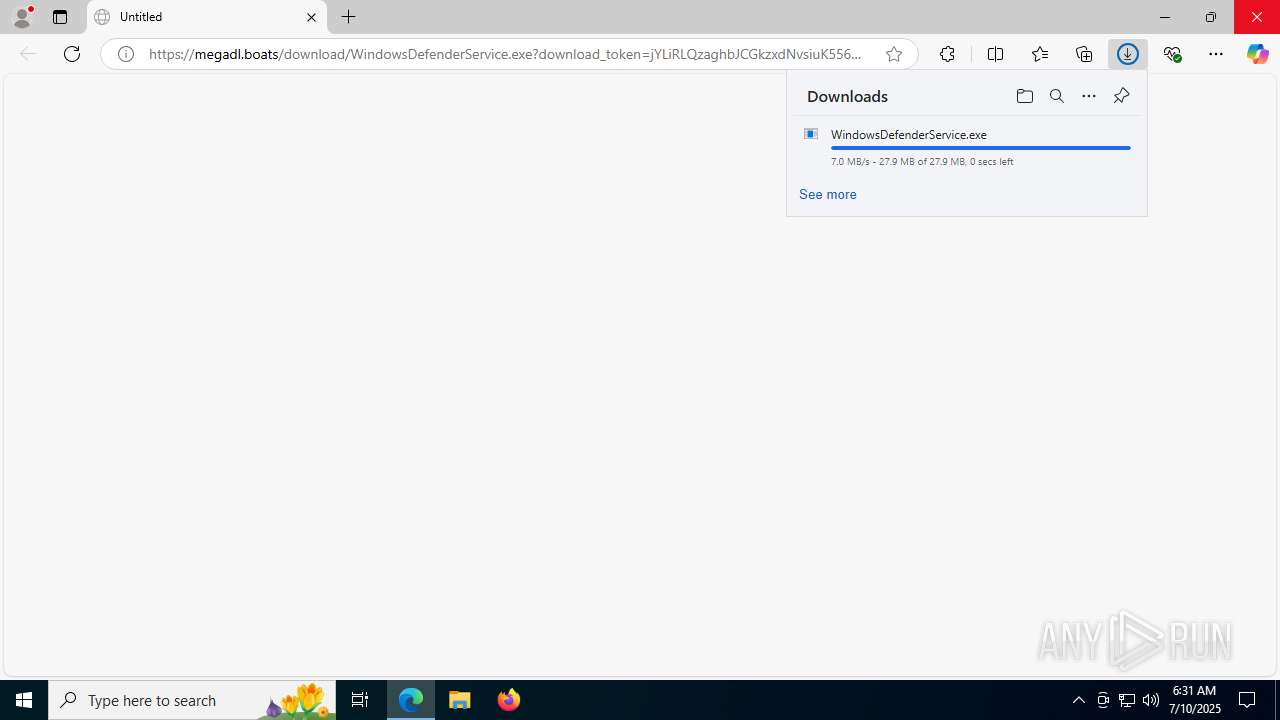
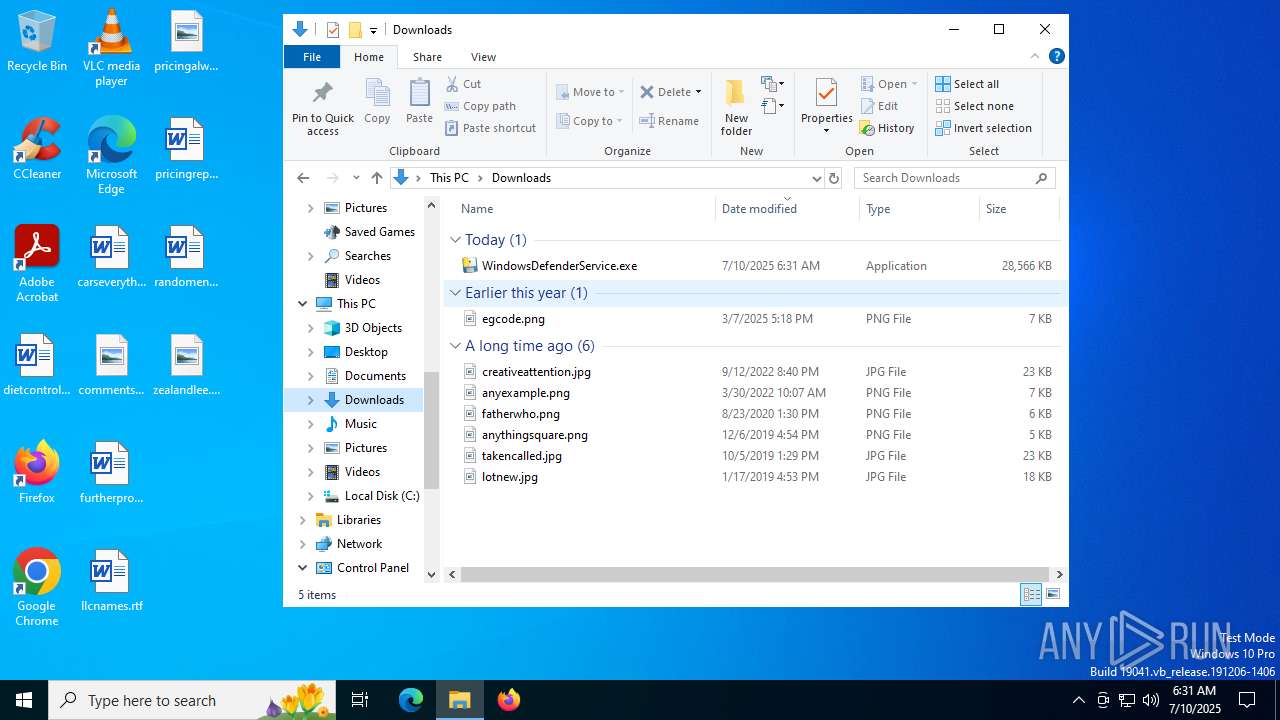
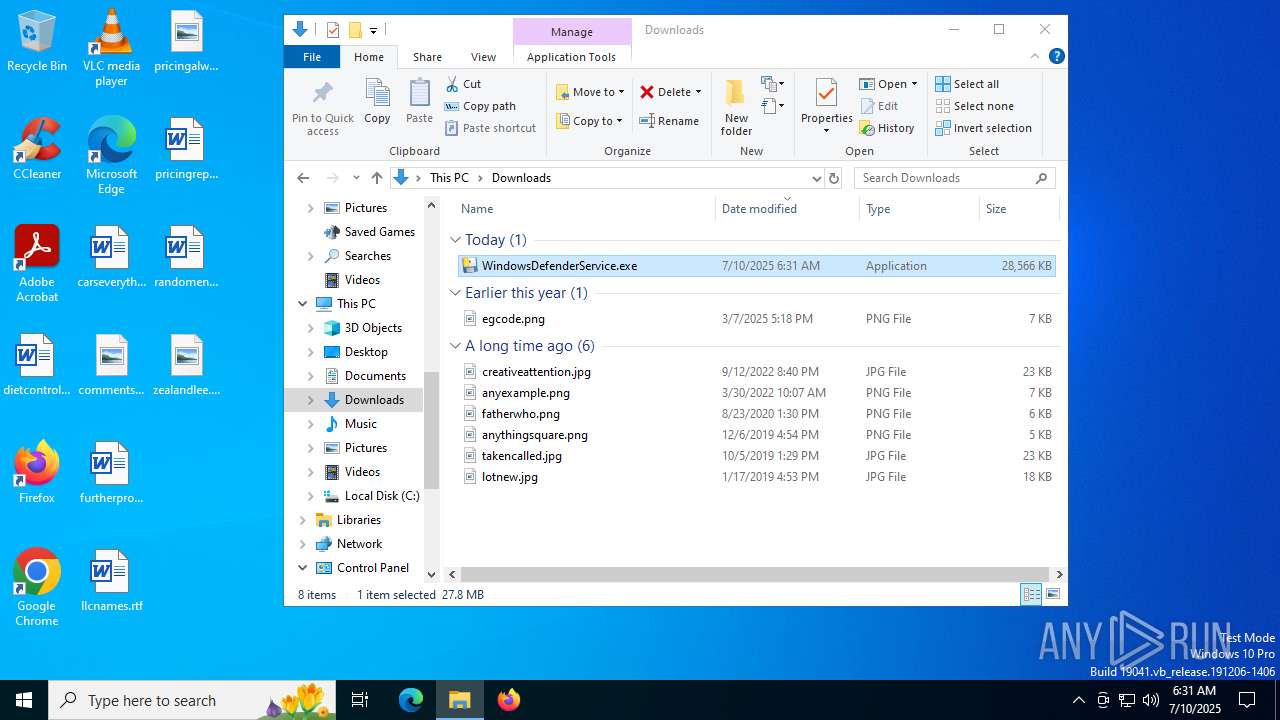
| URL: | https://megadl.boats/download/WindowsDefenderService.exe?download_token=jYLiRLQzaghbJCGkzxdNvsiuK556pjwaOT8bcJRHl3ckJYbljSLTgnyJhFis7V3ul6hUEQRU7JSqZVM3VAEFn1Z4XY1tAo5Uq9wjzOIii3GdPbbvSAN1ffuKnAurehhJYMnpVbI0nk5bzdvYIo56pjwaFn4sj56pjwa90e2APdfG4IeVOxLbArSaH9Ehk4BhHkTuALJ8kmYJEvnDNYjIJkPVxXZI8hMMFPlEO3pYBYfUzbxlVzWHRWqQeQp89hy4 |
| Full analysis: | https://app.any.run/tasks/8ef14e83-a64e-48ea-8307-a4cefc5b236f |
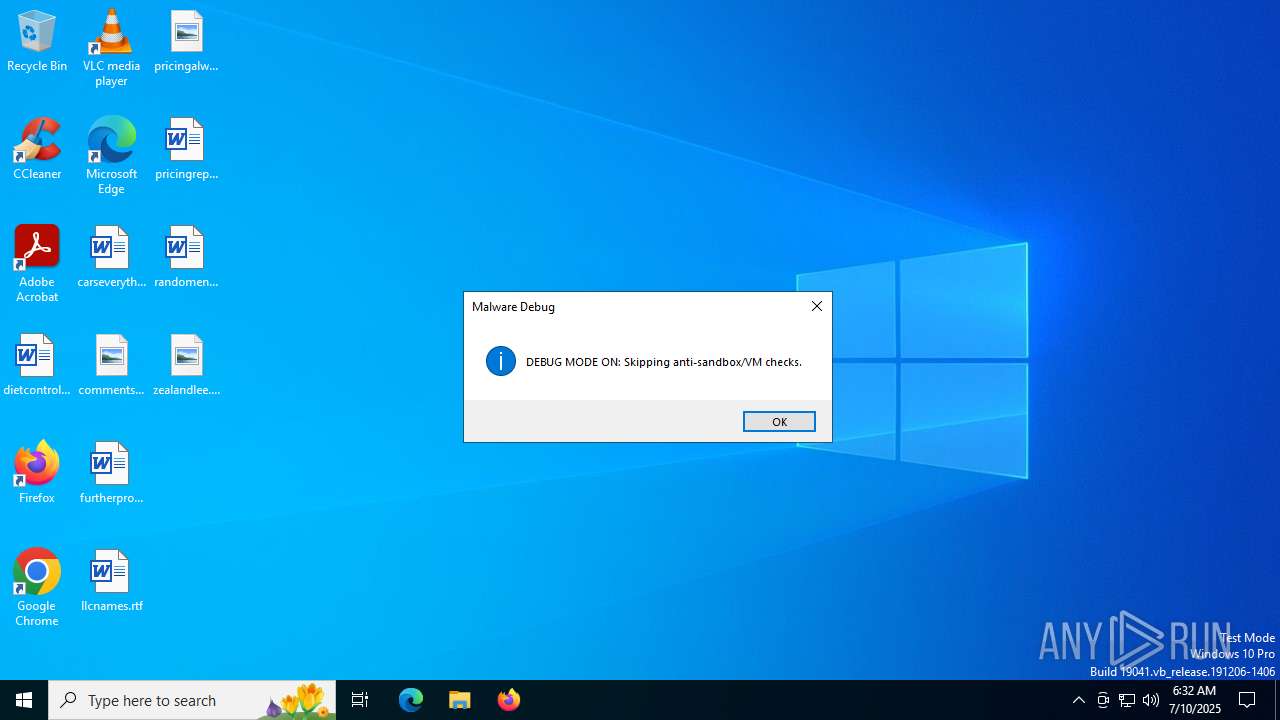
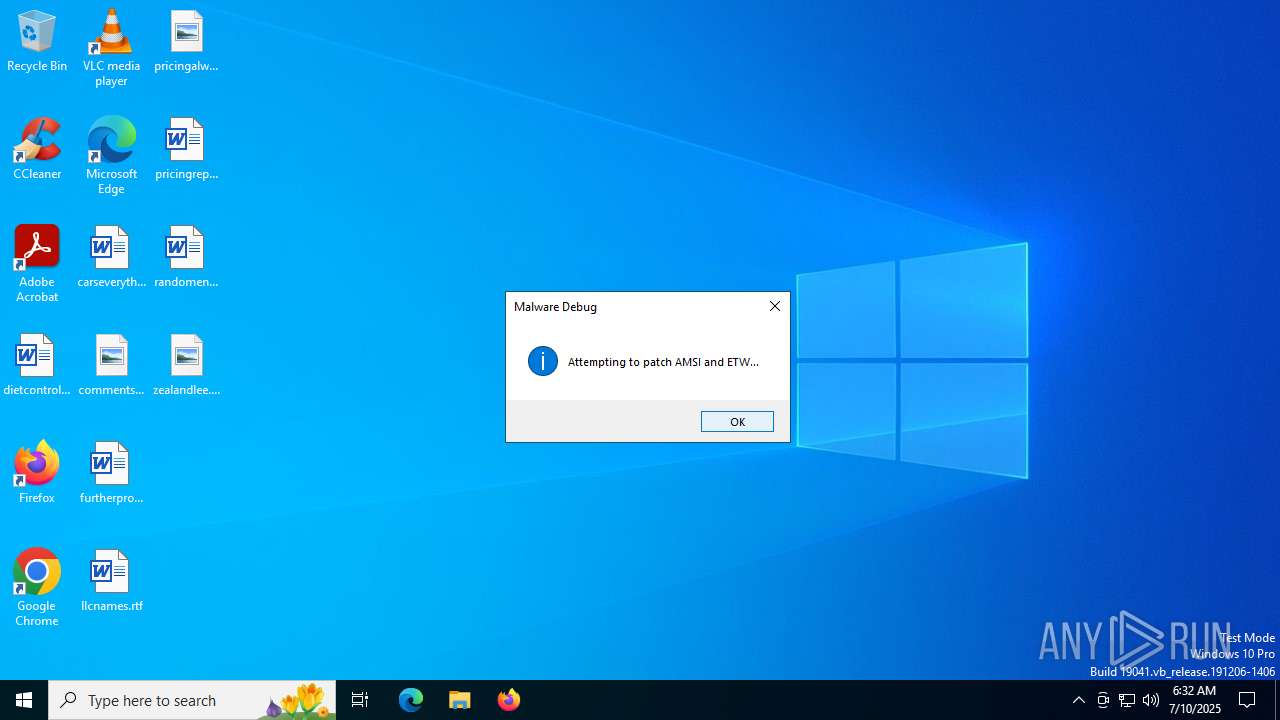
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2025, 06:31:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 61547A410C711247708030A726E665FD |
| SHA1: | B1C997461EA4F0025627F8B7674511873E7F478A |
| SHA256: | 7C1BF01D096EE6E05B2A435132C96DA27DB0C7B09E5305BE38BFF503E0B08956 |
| SSDEEP: | 6:2VFKLBJrnpJ/BM3ANPaqXyVI290MIhQNdH8geEmEUkDIsW1789JCwfda+:2VuhJ/xFaqiV05GIEmE9EWp8+ |
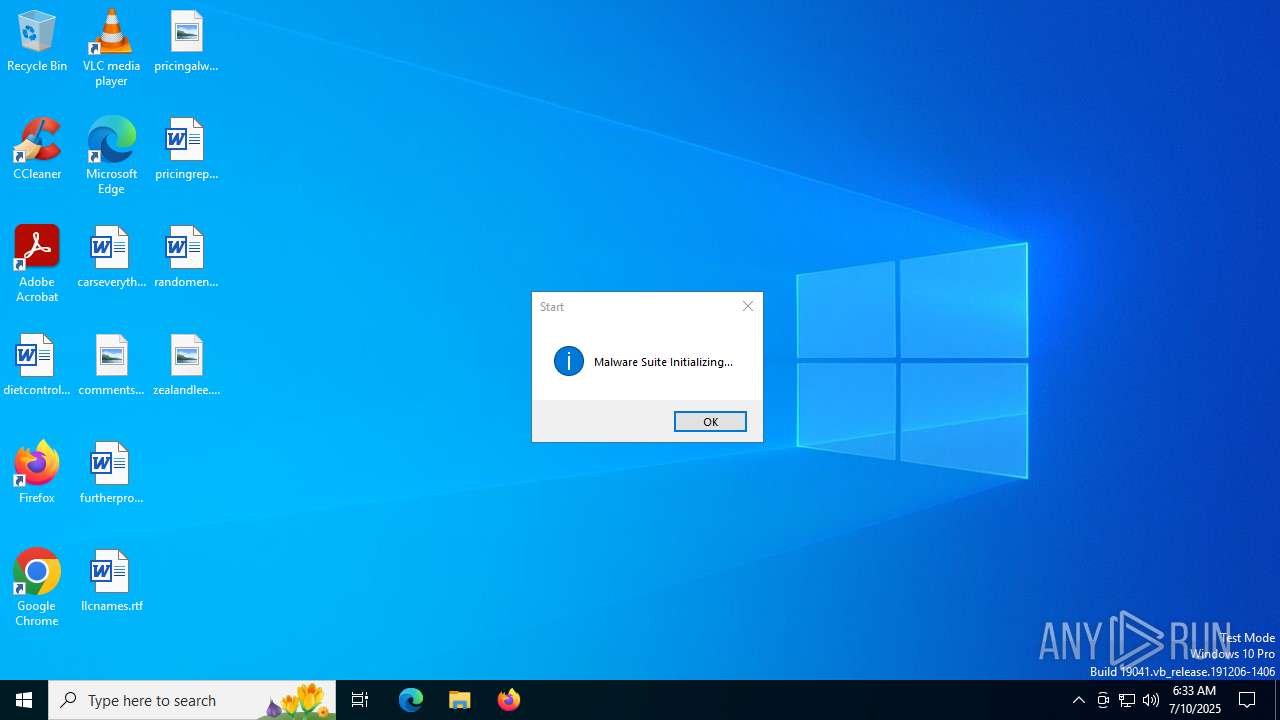
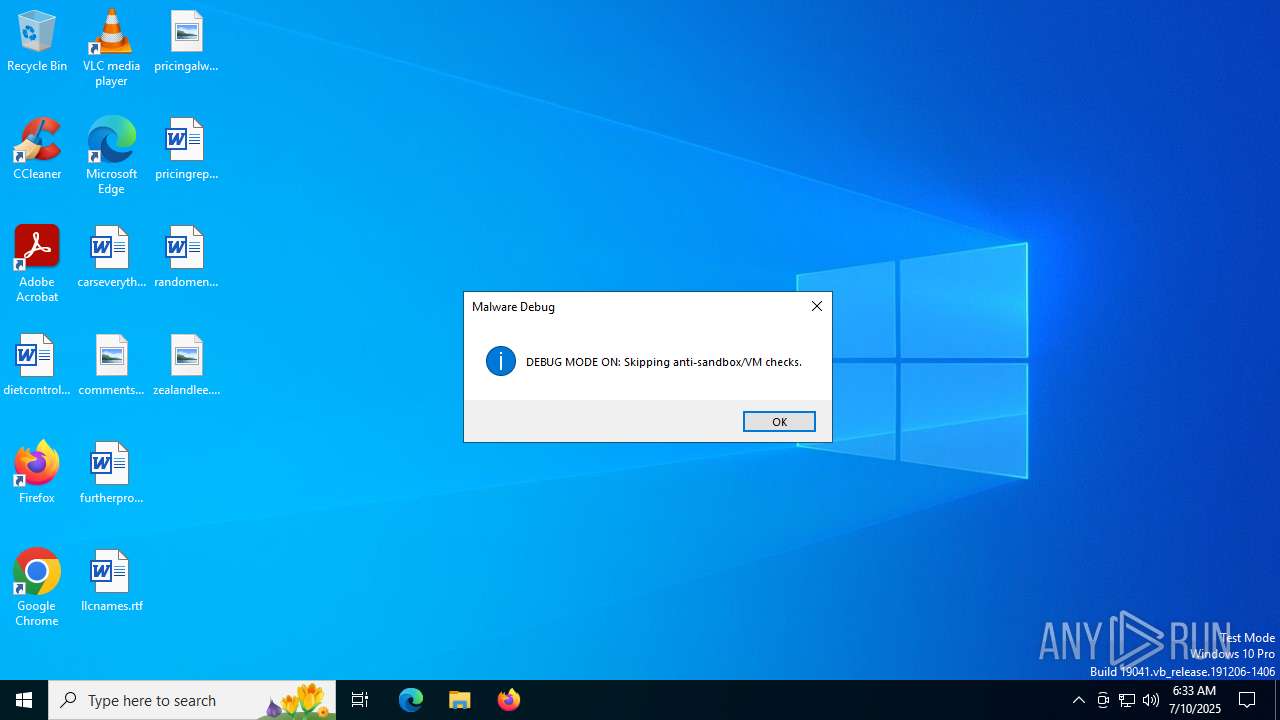
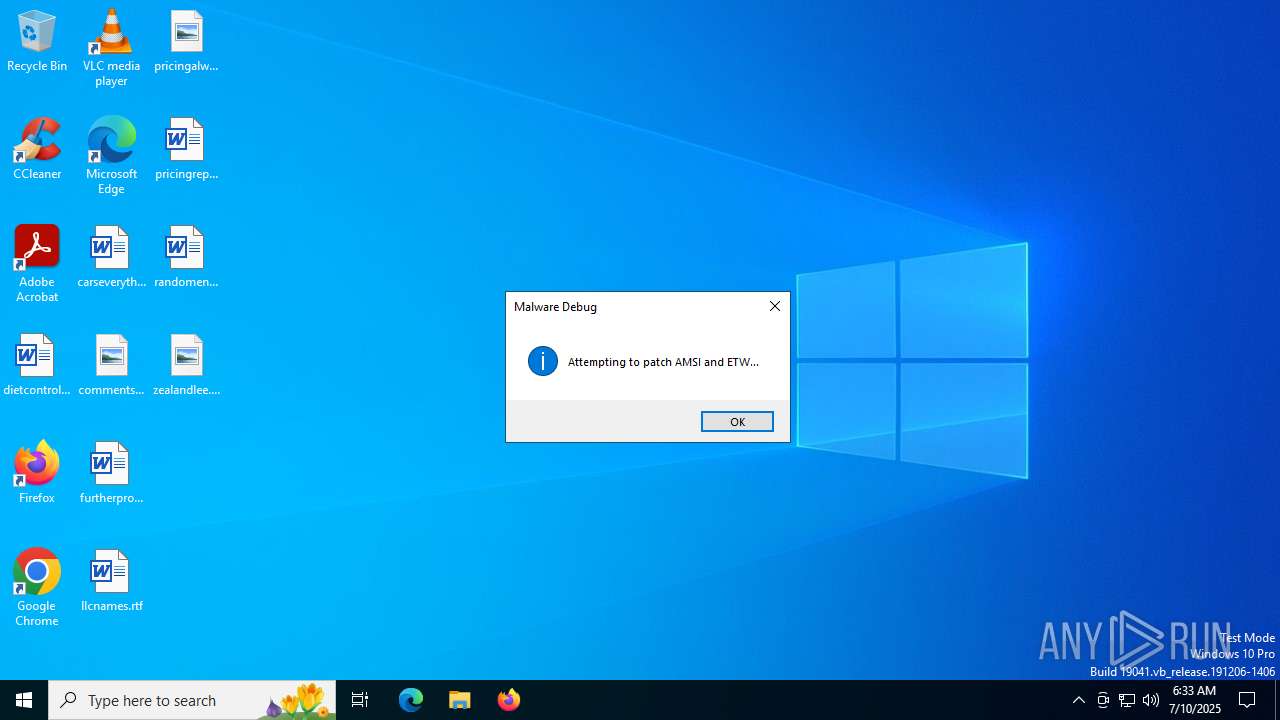
MALICIOUS
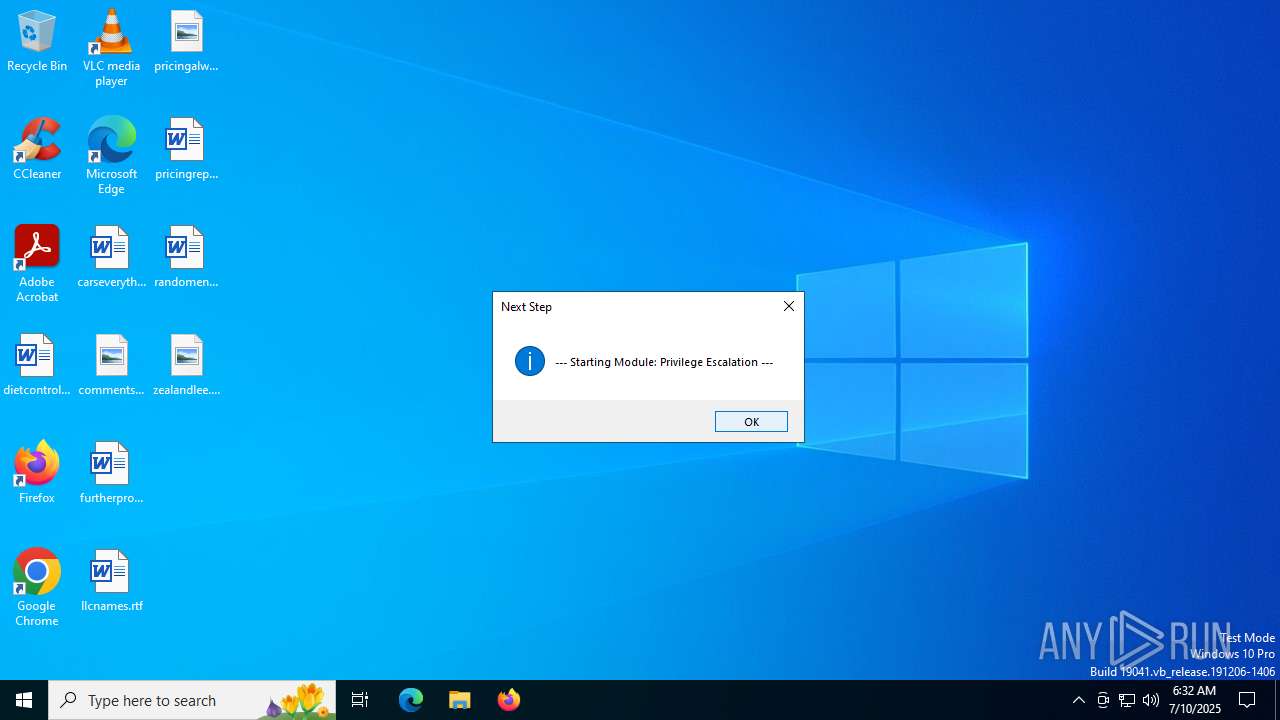
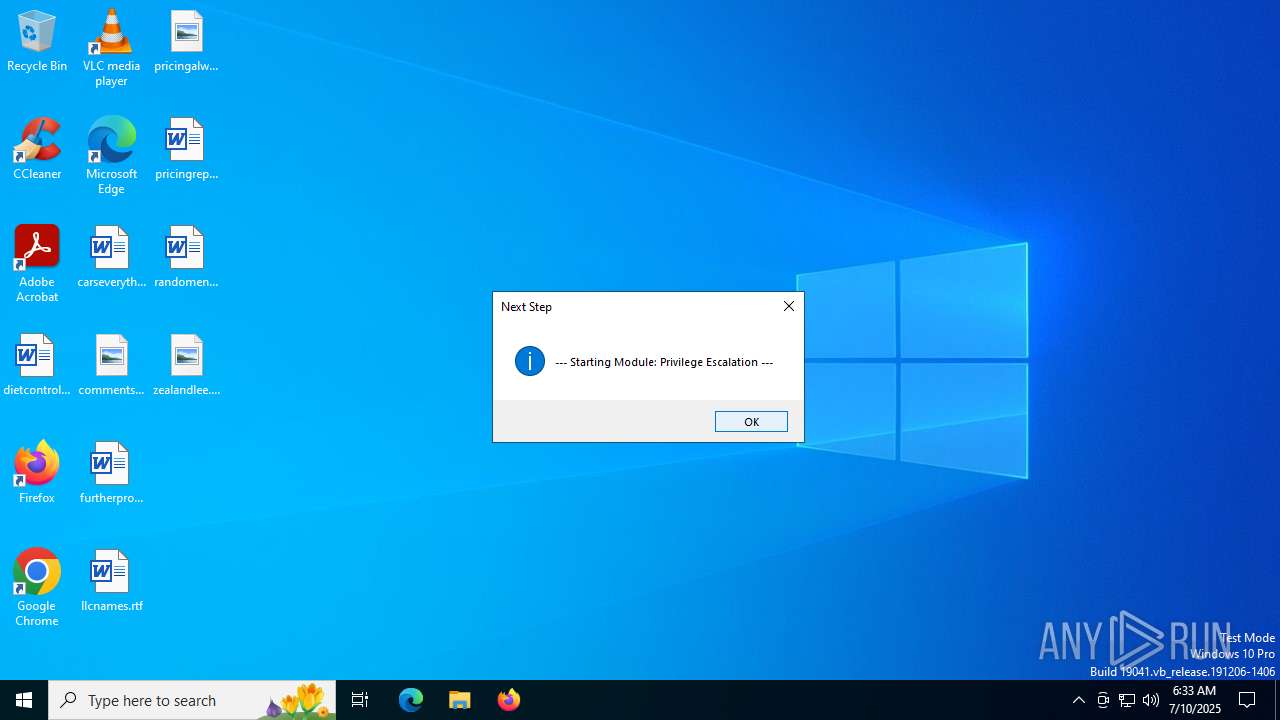
Bypass User Account Control (Modify registry)
- WindowsDefenderService.exe (PID: 2380)
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 7812)
SUSPICIOUS
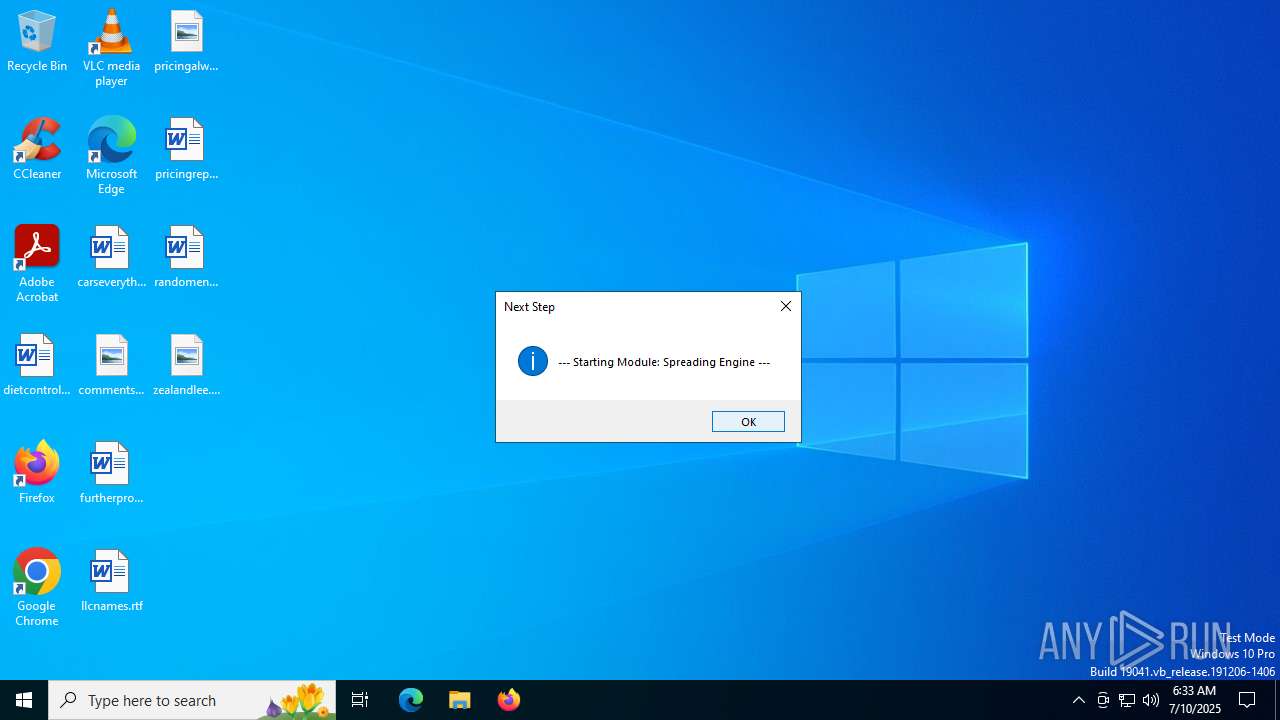
Process drops legitimate windows executable
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
- WindowsUpdateSvc.exe (PID: 8812)
Executable content was dropped or overwritten
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
- WindowsDefenderService.exe (PID: 7908)
- WindowsUpdateSvc.exe (PID: 8812)
The process drops C-runtime libraries
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
- WindowsUpdateSvc.exe (PID: 8812)
Process drops python dynamic module
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
- WindowsUpdateSvc.exe (PID: 8812)
Application launched itself
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
Loads Python modules
- WindowsDefenderService.exe (PID: 2380)
- WindowsDefenderService.exe (PID: 7908)
There is functionality for taking screenshot (YARA)
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 7908)
- WindowsDefenderService.exe (PID: 2040)
Reads the date of Windows installation
- WindowsDefenderService.exe (PID: 2380)
Starts CMD.EXE for commands execution
- WindowsDefenderService.exe (PID: 2380)
- WindowsDefenderService.exe (PID: 7908)
Reads security settings of Internet Explorer
- WindowsDefenderService.exe (PID: 2380)
Changes default file association
- WindowsDefenderService.exe (PID: 2380)
Uses WMIC.EXE to obtain system information
- WindowsDefenderService.exe (PID: 7908)
Connects to SSH
- WindowsDefenderService.exe (PID: 7908)
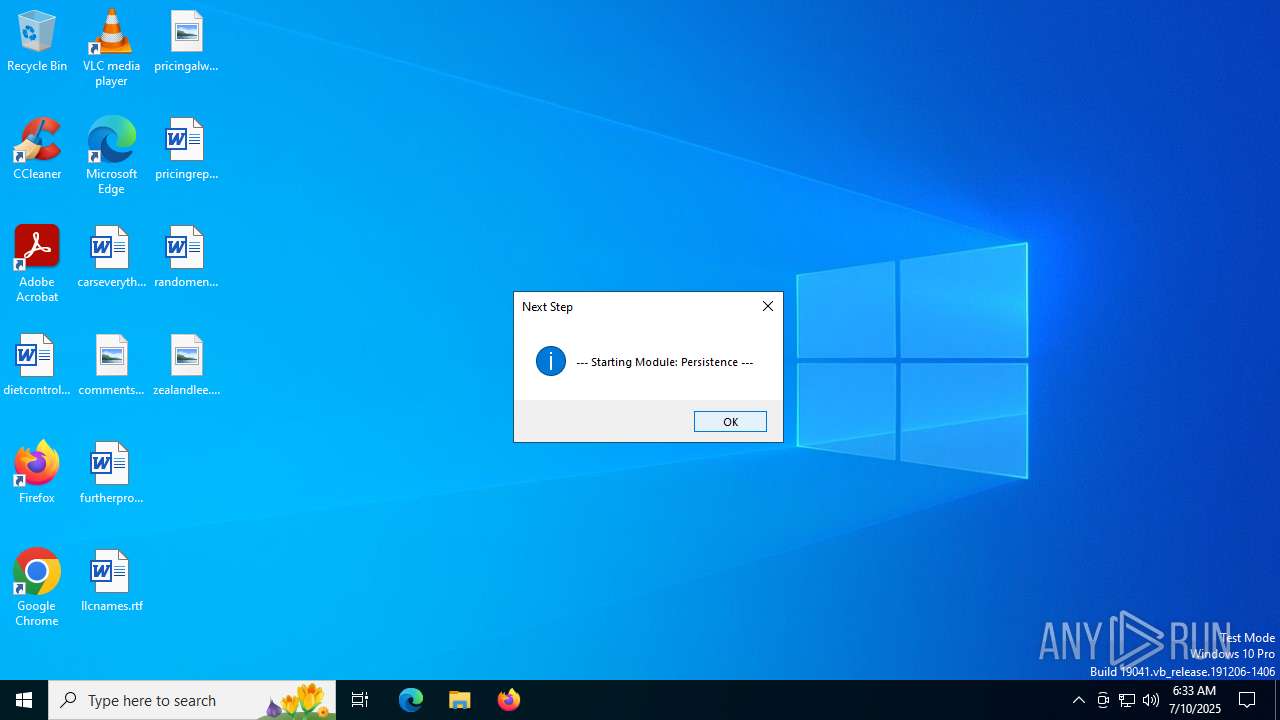
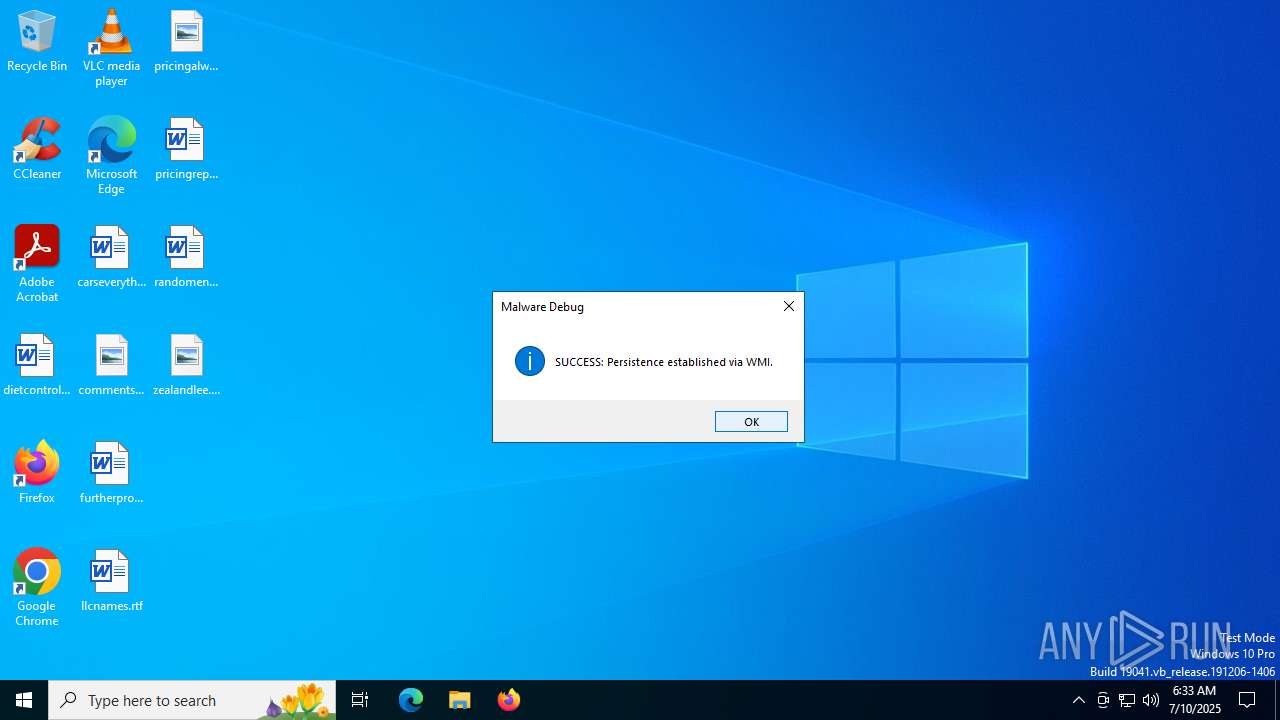
Uses WMIC.EXE for persistence
- WindowsDefenderService.exe (PID: 7908)
Uses NETSH.EXE to obtain data on the network
- WindowsDefenderService.exe (PID: 7908)
PROCDUMP has been detected
- pd64.exe (PID: 8592)
- pd64.exe (PID: 8592)
Executes as Windows Service
- WmiApSrv.exe (PID: 4888)
Executed via WMI
- WindowsUpdateSvc.exe (PID: 8812)
The executable file from the user directory is run by the CMD process
- pd64.exe (PID: 8592)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 3756)
- msedge.exe (PID: 6004)
Reads the computer name
- identity_helper.exe (PID: 7652)
- identity_helper.exe (PID: 7836)
- WindowsDefenderService.exe (PID: 2380)
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
- WindowsDefenderService.exe (PID: 7908)
- pd64.exe (PID: 8592)
- WindowsUpdateSvc.exe (PID: 8812)
Application launched itself
- msedge.exe (PID: 3756)
- msedge.exe (PID: 8016)
Reads Environment values
- identity_helper.exe (PID: 7652)
- identity_helper.exe (PID: 7836)
- pd64.exe (PID: 8592)
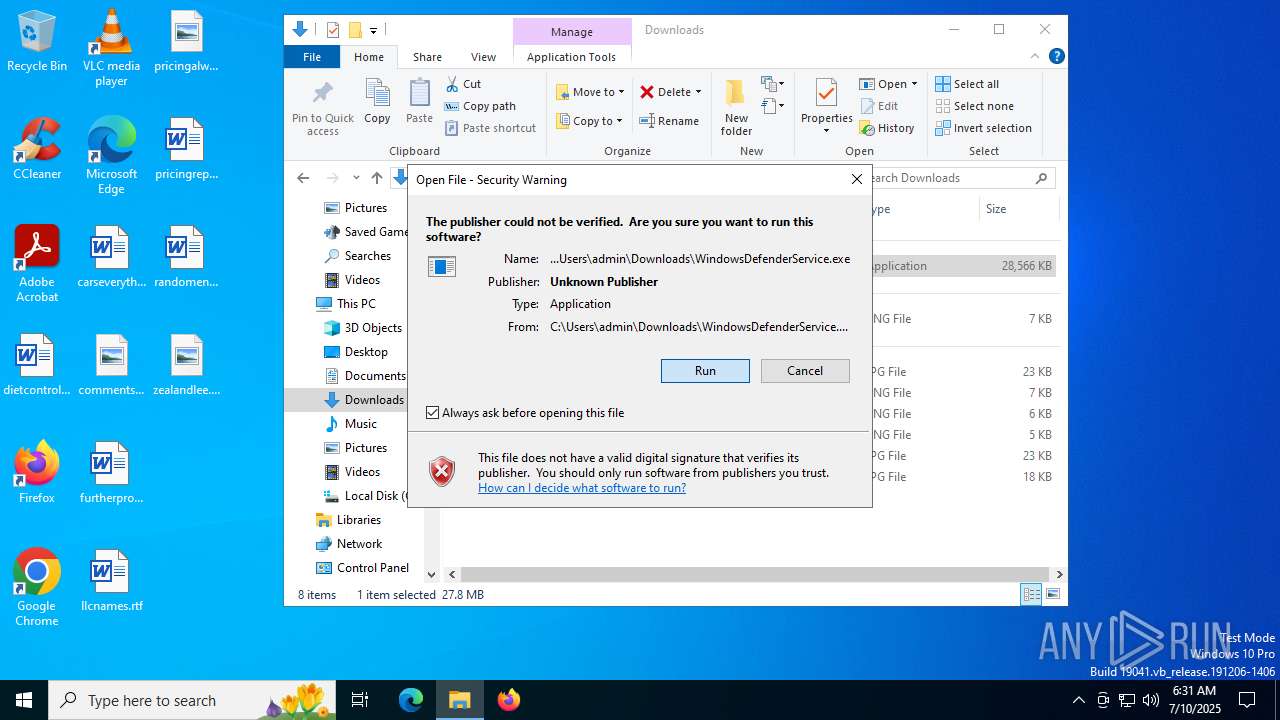
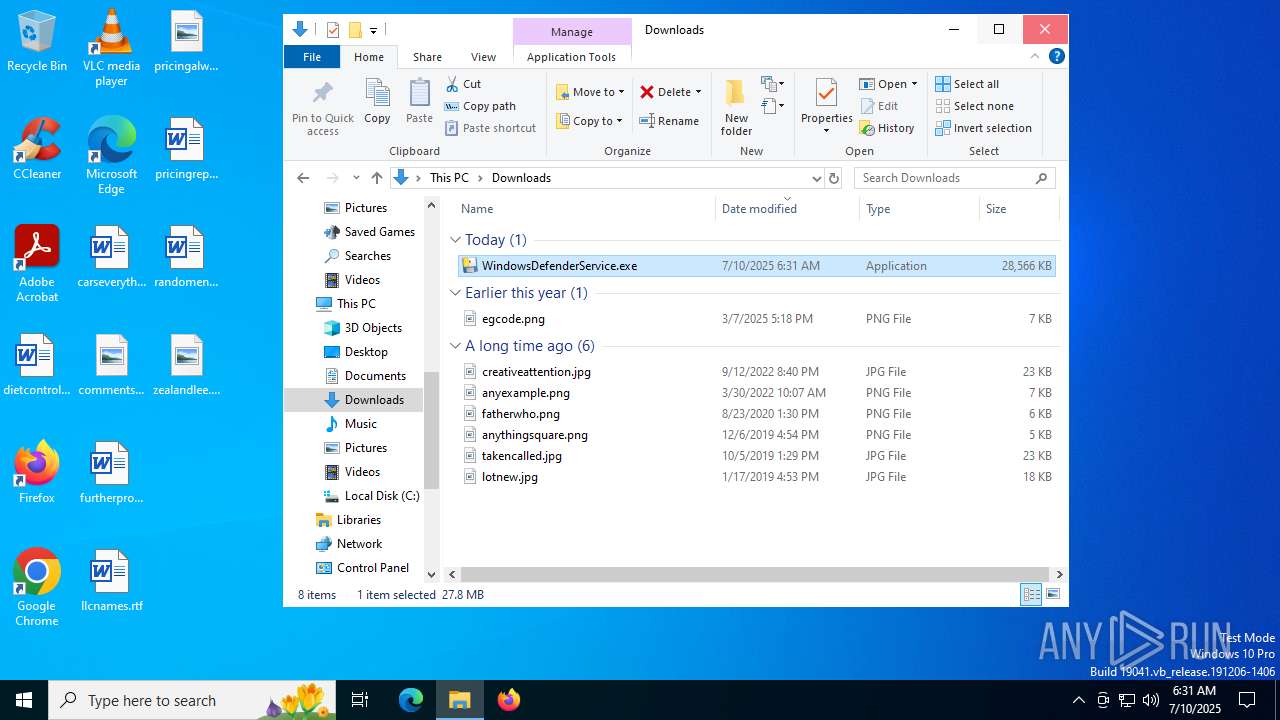
Manual execution by a user
- WindowsDefenderService.exe (PID: 3940)
Checks supported languages
- identity_helper.exe (PID: 7652)
- identity_helper.exe (PID: 7836)
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2380)
- WindowsDefenderService.exe (PID: 7908)
- pd64.exe (PID: 8592)
- WindowsUpdateSvc.exe (PID: 8812)
- WindowsDefenderService.exe (PID: 2040)
PyInstaller has been detected (YARA)
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
- WindowsDefenderService.exe (PID: 7908)
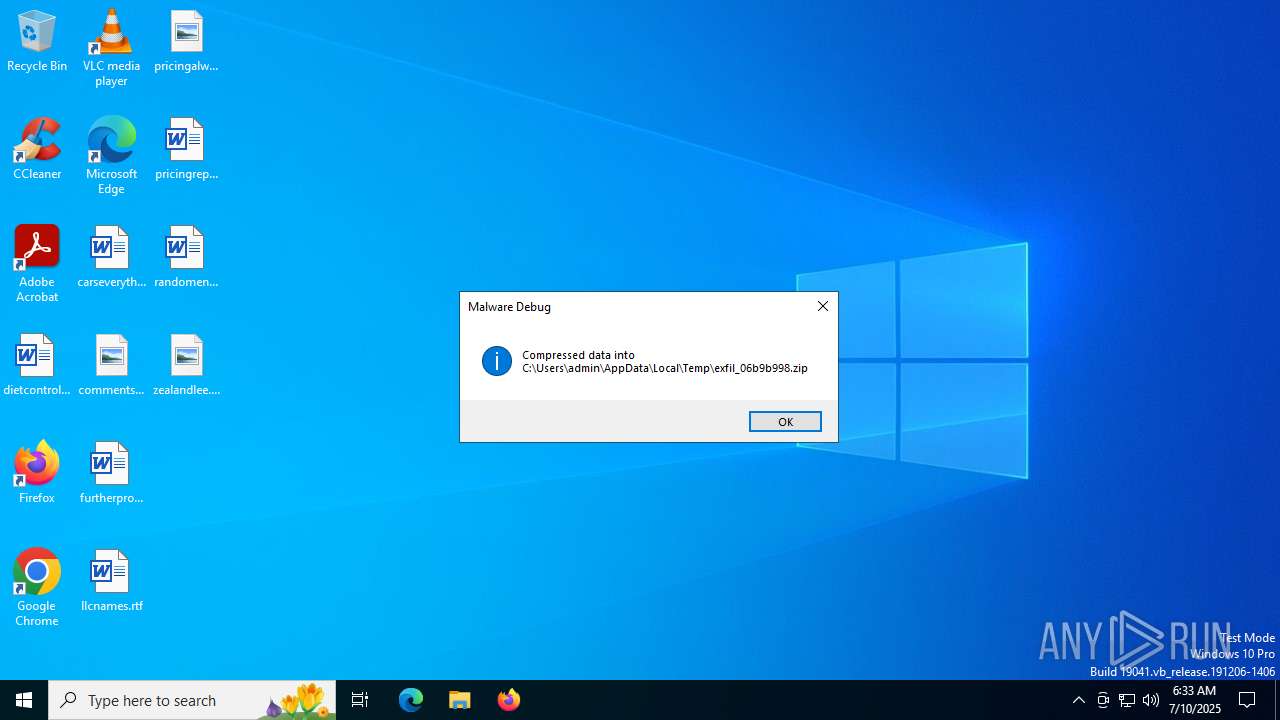
Create files in a temporary directory
- WindowsDefenderService.exe (PID: 3940)
- WindowsDefenderService.exe (PID: 2040)
- WindowsDefenderService.exe (PID: 7908)
- pd64.exe (PID: 8592)
Reads the machine GUID from the registry
- WindowsDefenderService.exe (PID: 2380)
- WindowsDefenderService.exe (PID: 7908)
Checks operating system version
- WindowsDefenderService.exe (PID: 2380)
- WindowsDefenderService.exe (PID: 7908)
Reads security settings of Internet Explorer
- fodhelper.exe (PID: 7812)
- WMIC.exe (PID: 5724)
- WMIC.exe (PID: 7868)
- WMIC.exe (PID: 2216)
The sample compiled with english language support
- WindowsDefenderService.exe (PID: 3940)
- WindowsUpdateSvc.exe (PID: 8812)
- WindowsDefenderService.exe (PID: 7908)
- WindowsDefenderService.exe (PID: 2040)
Checks proxy server information
- slui.exe (PID: 7160)
- WindowsDefenderService.exe (PID: 7908)
Reads the software policy settings
- slui.exe (PID: 7160)
Creates files or folders in the user directory
- WindowsDefenderService.exe (PID: 7908)
Application based on Rust
- WindowsDefenderService.exe (PID: 7908)
Process checks computer location settings
- WindowsDefenderService.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
64
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2672,i,12947687903796681699,1928074895353616352,262144 --variations-seed-version --mojo-platform-channel-handle=2688 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2444,i,10550879543571762150,15475944464382773737,262144 --variations-seed-version --mojo-platform-channel-handle=2436 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=4600,i,10550879543571762150,15475944464382773737,262144 --variations-seed-version --mojo-platform-channel-handle=5248 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1036 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4620,i,12947687903796681699,1928074895353616352,262144 --variations-seed-version --mojo-platform-channel-handle=5124 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\Downloads\WindowsDefenderService.exe" | C:\Users\admin\Downloads\WindowsDefenderService.exe | — | fodhelper.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5356,i,10550879543571762150,15475944464382773737,262144 --variations-seed-version --mojo-platform-channel-handle=5384 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2192 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4676,i,12947687903796681699,1928074895353616352,262144 --variations-seed-version --mojo-platform-channel-handle=4832 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2216 | wmic /namespace:"\\root\subscription" PATH __FilterToConsumerBinding CREATE Filter='__EventFilter.Name="SysUpdaterFilter"', Consumer='CommandLineEventConsumer.Name="SysUpdaterConsumer"' | C:\Windows\System32\wbem\WMIC.exe | — | WindowsDefenderService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5028,i,12947687903796681699,1928074895353616352,262144 --variations-seed-version --mojo-platform-channel-handle=4876 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
12 255
Read events
12 195
Write events
56
Delete events
4
Modification events
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31191396 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
342
Suspicious files
351
Text files
2 442
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17615a.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17615a.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176188.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176198.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176198.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176198.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
72
DNS requests
70
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7512 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752471285&P2=404&P3=2&P4=Gc9Vk4nsTOqsFlx3zrBjFnhWtUXpZWE2hv6k2or10TBiYECcQ9dwmsIZZBtAJB8WhUOpGRGTPnxPyF9XYyDFYQ%3d%3d | unknown | — | — | whitelisted |
6344 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7916 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7916 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7512 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752471285&P2=404&P3=2&P4=Gc9Vk4nsTOqsFlx3zrBjFnhWtUXpZWE2hv6k2or10TBiYECcQ9dwmsIZZBtAJB8WhUOpGRGTPnxPyF9XYyDFYQ%3d%3d | unknown | — | — | whitelisted |
7512 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752471285&P2=404&P3=2&P4=dCg2%2bzcCUmlemy9hWxNPU9pxrR%2bQCMr8zWNrdXHenx1iiL1%2f9o%2bDjMR%2fzzWqrGeEWq0F9zTwVtvX7lHPrP7OJg%3d%3d | unknown | — | — | whitelisted |
7512 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752471285&P2=404&P3=2&P4=dCg2%2bzcCUmlemy9hWxNPU9pxrR%2bQCMr8zWNrdXHenx1iiL1%2f9o%2bDjMR%2fzzWqrGeEWq0F9zTwVtvX7lHPrP7OJg%3d%3d | unknown | — | — | whitelisted |
7512 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1752471285&P2=404&P3=2&P4=Ih%2bYttbWsM3yl%2baYuyZh51LAF6BQVx6Blz210aekmTQjUxYyQeI1EqEJQ42QSxiSinrk0XFZ3%2bynVP93086I4w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1328 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6004 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6004 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6004 | msedge.exe | 104.21.9.143:443 | megadl.boats | CLOUDFLARENET | — | unknown |
6004 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6004 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
megadl.boats |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
2200 | svchost.exe | Misc activity | ET INFO DNS Query for Webhook/HTTP Request Inspection Service (webhook .site) |
7908 | WindowsDefenderService.exe | Misc activity | ET INFO Webhook/HTTP Request Inspection Service Domain (webhook .site in TLS SNI) |