| URL: | https://ddec1-0-en-ctp.trendmicro.com/wis/clicktime/v1/query?url=http%3a%2f%2fapp.campaignresources.motorolasolutions.com%2fe%2fer%3futm%5fcampaign%3dNA%5fQ219%5fCOM%5fDC%5fMUL%5fMS%5fWHITE%5fPAPER%5fEDM%5fTOP%5f100%5fTRBO%5fCUSTOMERS%26utm%5fmedium%3demail%26utm%5fsource%3dEloqua%26utm%5fcontent%3d5223%26s%3d1013191099%26lid%3d7764%26elqTrackId%3d9e5fbddd6b164967808e1d051d02004a%26elq%3df53d83d1ef6a4fc0bd778416684b8fd9%26elqaid%3d5223%26elqat%3d1&umid=a8abb4b4-89d6-416f-abbc-88883fb1eb3a&auth=65a620fa4b6e2edf0405a6ed61dc7465231096cd-e1a6662c8bd1b2fe29336e55c08daef8659b4658 |
| Full analysis: | https://app.any.run/tasks/71355f8e-5ea5-4445-9cab-236e91289f98 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 17:23:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CED11938B13EA5FA8B7618B75B189956 |
| SHA1: | F0C9A860B69CC534A6F9FA12AFED9BAFA75C767C |
| SHA256: | 7C19C2025F262C082BA53A8FC0C3D11D223CE7A159FBFF3AB97BC7A87009D5D3 |
| SSDEEP: | 12:2K9nDKMAWCOA2PB6h1j9+wqF1TEQyy2RGS/5VNDLaPho9YZS/j4zMl:28DKv3n97CTEj0QzaPho9Ye4O |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2568)
INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2568)
Application launched itself
- chrome.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3036797349715419885 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9928802584132751611 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10429705357730472136 --mojo-platform-channel-handle=2060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15855725898260618097 --mojo-platform-channel-handle=3868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=14112015671608954953 --mojo-platform-channel-handle=2492 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f2da9d0,0x6f2da9e0,0x6f2da9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5618711729565788869 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8699095878204951537 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2647212974985672907,2068481879732910935,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5157594110296855919 --mojo-platform-channel-handle=4040 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3416 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
599
Read events
527
Write events
68
Delete events
4
Modification events
| (PID) Process: | (2352) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2568-13210190596904375 |
Value: 259 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
113
Text files
157
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\82ea858b-e10e-4914-a5f0-92f2d1cae76c.tmp | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF36e7aa.TMP | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
93
DNS requests
72
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3764 | chrome.exe | GET | 204 | 18.196.248.131:80 | http://pm.w55c.net/ping_match.gif?st=TEALIUM&rurl=https%3A%2F%2Fdatacloud.tealiumiq.com%2Fvdata%2Fi.gif%3FdataxuId%3D_wfivefivec_%26tealium_vid%3D016c8c022b6600098e5eb33e0a9e03066005305e007e8%26tealium_account%3Dmotorola%26tealium_profile%3Dmain%26tealium_cookie_sync%3Dtrue | DE | — | — | shared |
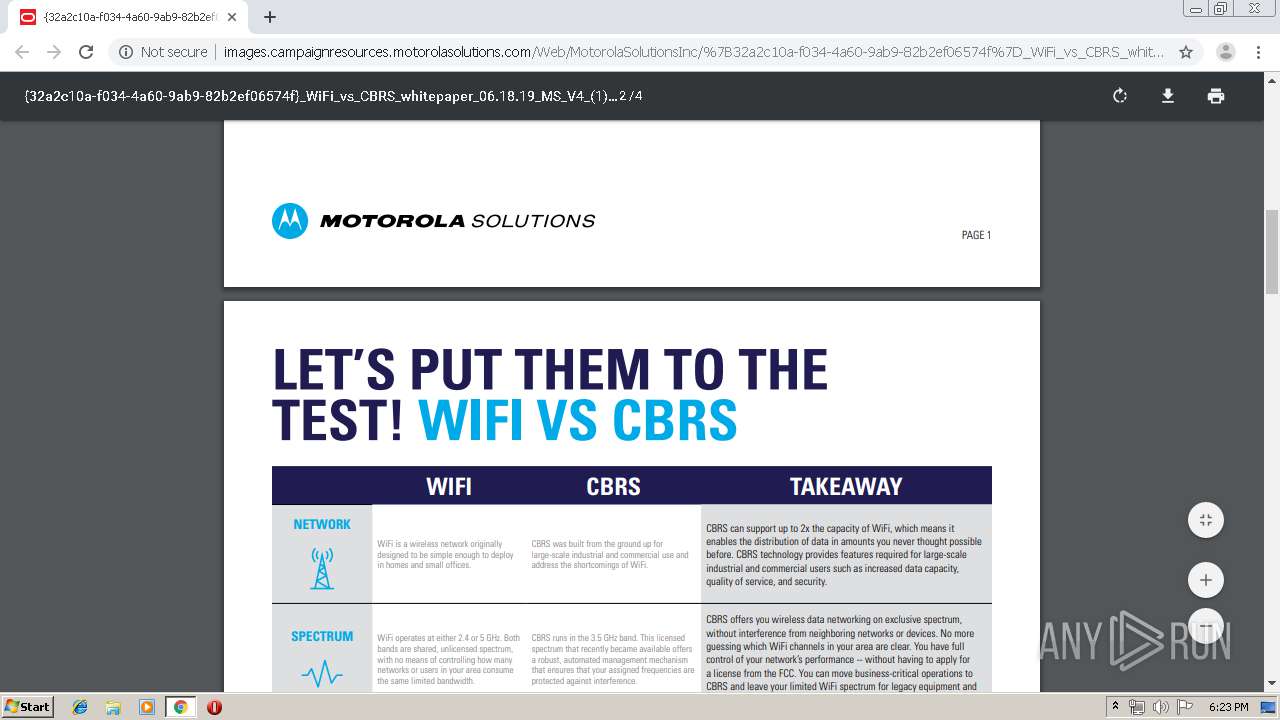
3764 | chrome.exe | GET | 200 | 2.16.186.49:80 | http://images.campaignresources.motorolasolutions.com/Web/MotorolaSolutionsInc/%7B32a2c10a-f034-4a60-9ab9-82b2ef06574f%7D_WiFi_vs_CBRS_whitepaper_06.18.19_MS_V4_(1).pdf?utm_campaign=NA_Q219_COM_DC_MUL_MS_WHITE_PAPER_EDM_TOP_100_TRBO_CUSTOMERS&utm_medium=email&utm_source=Eloqua&utm_content=5223 | unknown | pdf | 146 Kb | malicious |
3764 | chrome.exe | GET | 302 | 142.0.160.54:80 | http://app.campaignresources.motorolasolutions.com/e/er?utm_campaign=NA_Q219_COM_DC_MUL_MS_WHITE_PAPER_EDM_TOP_100_TRBO_CUSTOMERS&utm_medium=email&utm_source=Eloqua&utm_content=5223&s=1013191099&lid=7764&elqTrackId=9e5fbddd6b164967808e1d051d02004a&elq=f53d83d1ef6a4fc0bd778416684b8fd9&elqaid=5223&elqat=1 | US | html | 419 b | suspicious |
3764 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
3764 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.6 Kb | whitelisted |
3764 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
3764 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
3764 | chrome.exe | GET | 200 | 2.16.186.49:80 | http://images.campaignresources.motorolasolutions.com/favicon.ico | unknown | image | 9.90 Kb | malicious |
3764 | chrome.exe | GET | 200 | 52.85.182.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3764 | chrome.exe | GET | 200 | 52.85.182.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 34.217.225.182:443 | ddec1-0-en-ctp.trendmicro.com | Amazon.com, Inc. | US | unknown |
3764 | chrome.exe | 142.0.160.54:80 | app.campaignresources.motorolasolutions.com | Oracle Corporation | US | suspicious |
3764 | chrome.exe | 2.16.186.49:80 | images.campaignresources.motorolasolutions.com | Akamai International B.V. | — | whitelisted |
3764 | chrome.exe | 172.217.23.138:443 | www.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 74.125.4.216:80 | r2---sn-aigzrney.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ddec1-0-en-ctp.trendmicro.com |
| whitelisted |
accounts.google.com |
| shared |
app.campaignresources.motorolasolutions.com |
| suspicious |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
images.campaignresources.motorolasolutions.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |