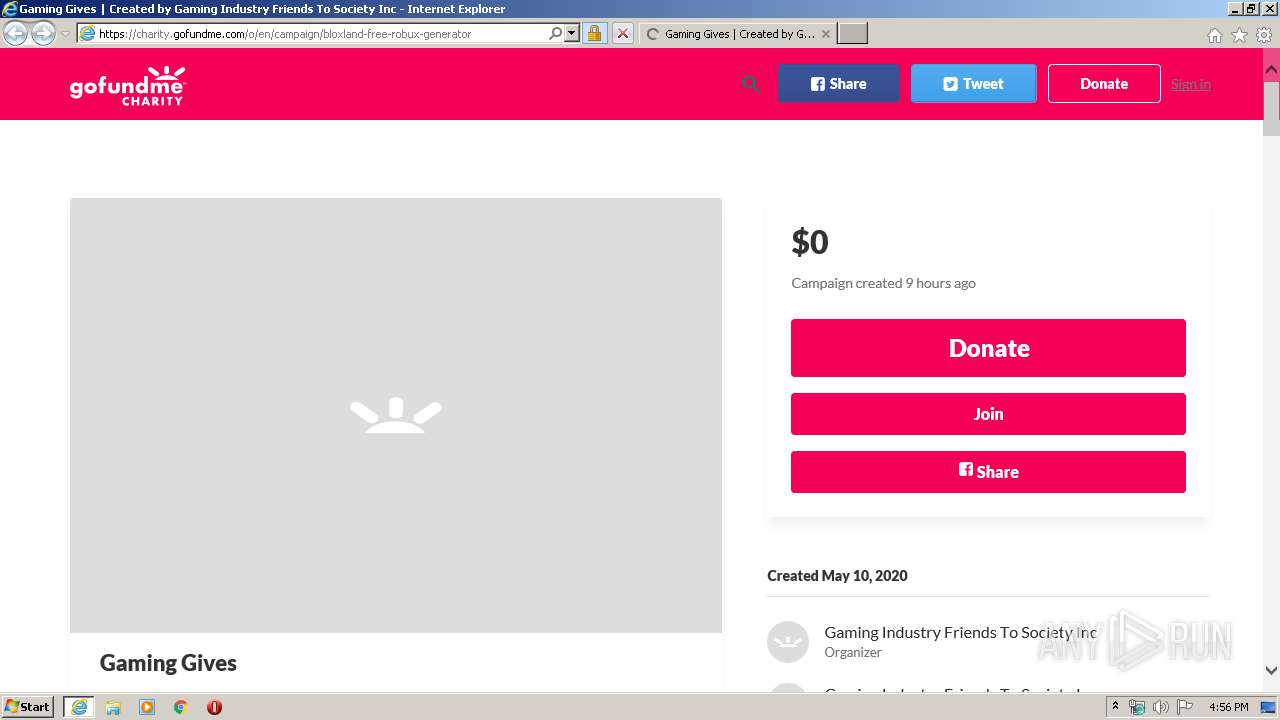
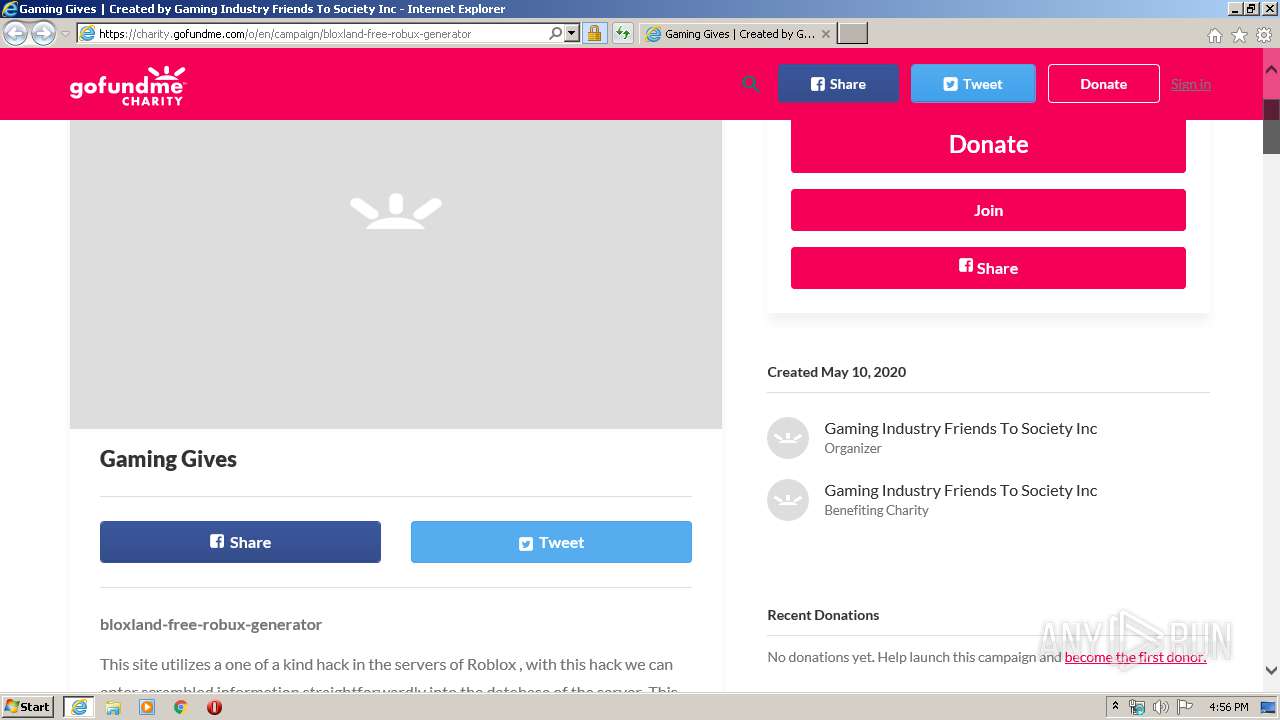
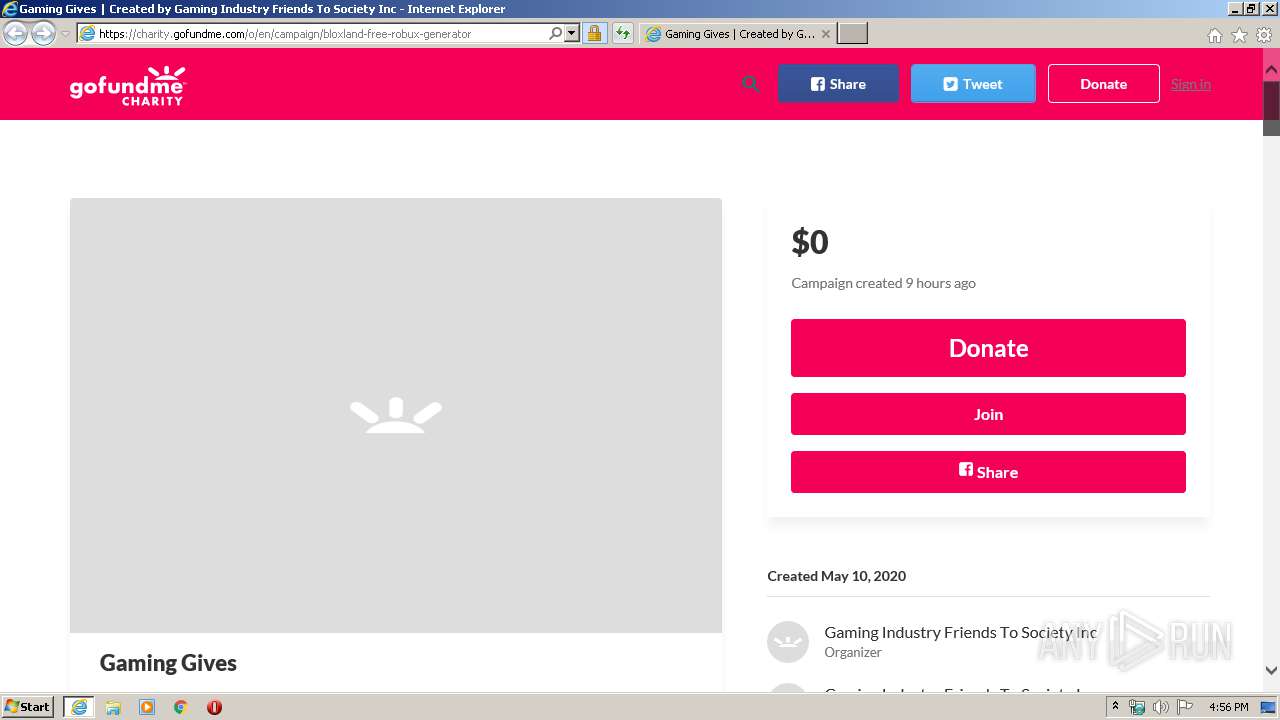
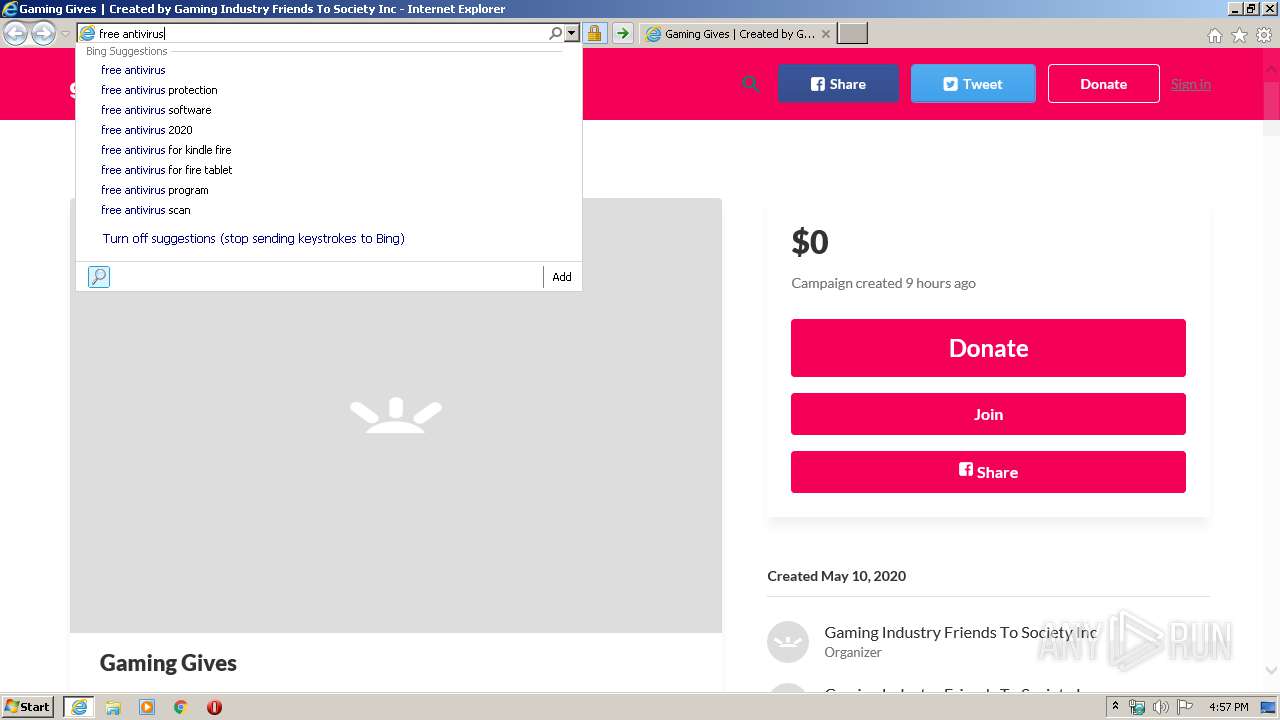
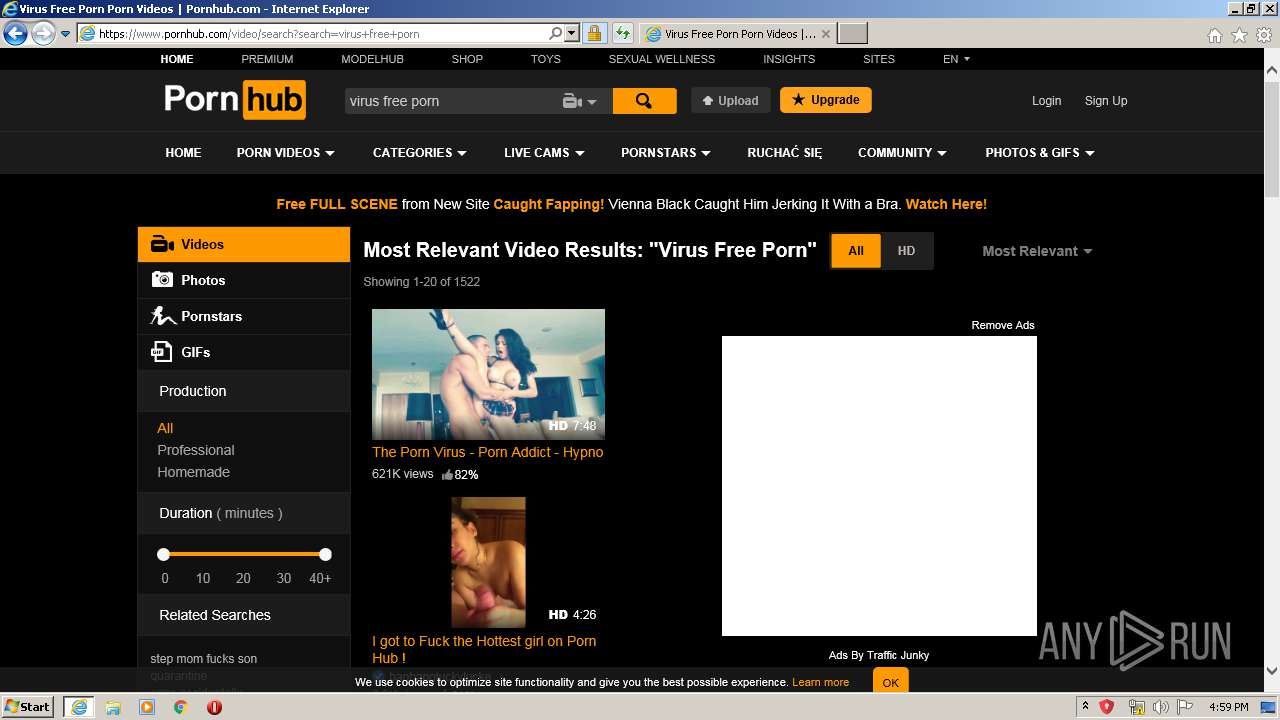
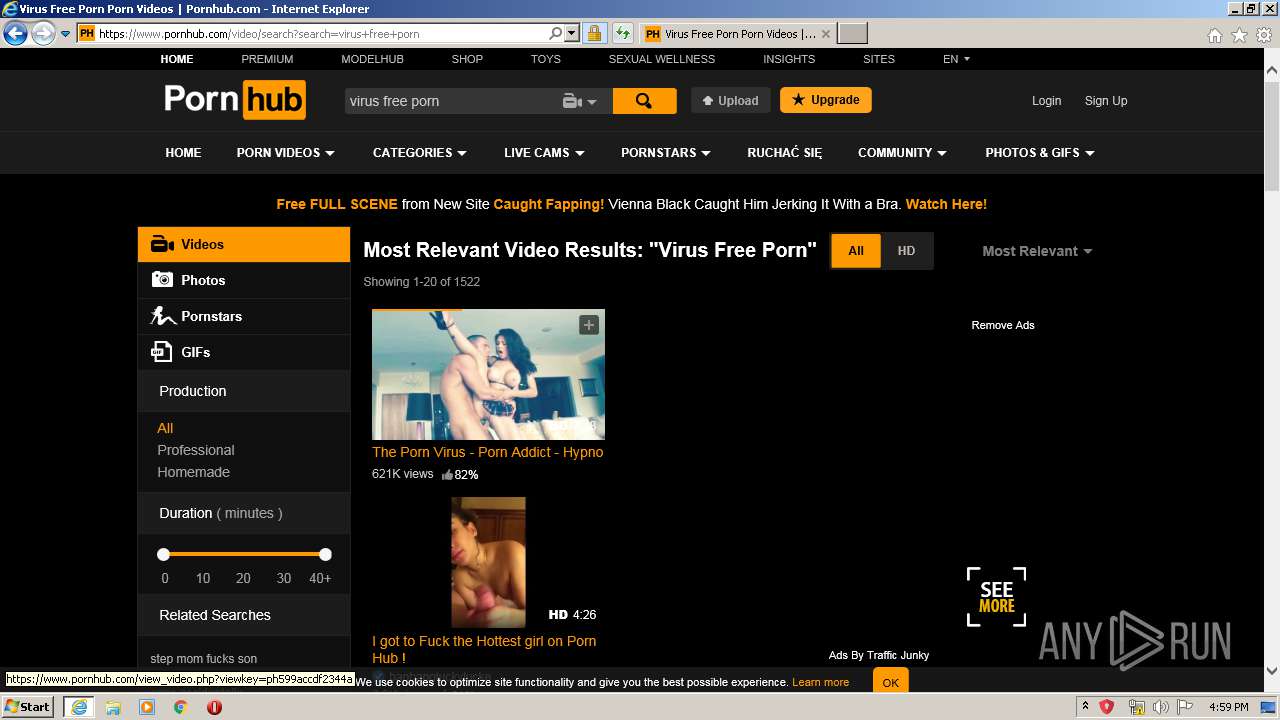
| URL: | https://charity.gofundme.com/o/en/campaign/bloxland-free-robux-generator |
| Full analysis: | https://app.any.run/tasks/2f32417f-6293-4f25-9059-034e7a534f74 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2020, 15:56:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E23C55B039BA8A4BC46609BADA100E4A |
| SHA1: | 905A355F16BB5F6D17C4EB7AE2543761FF2D0E92 |
| SHA256: | 7C119B802E0E7B90EA60BB218B7A0C87F206AB44DAA989C8645471B4231D78E0 |
| SSDEEP: | 3:N8QzH919Ld6vKTtHgTPX3:2Q791X6vKTtHA3 |
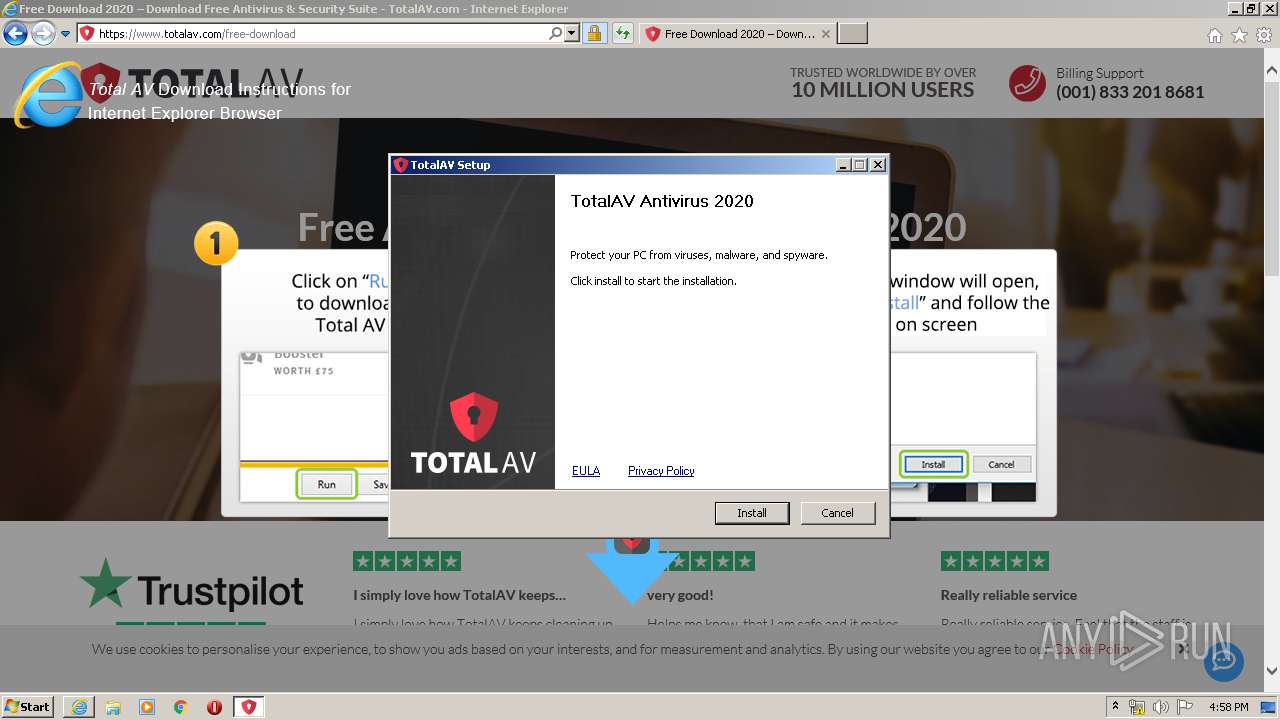
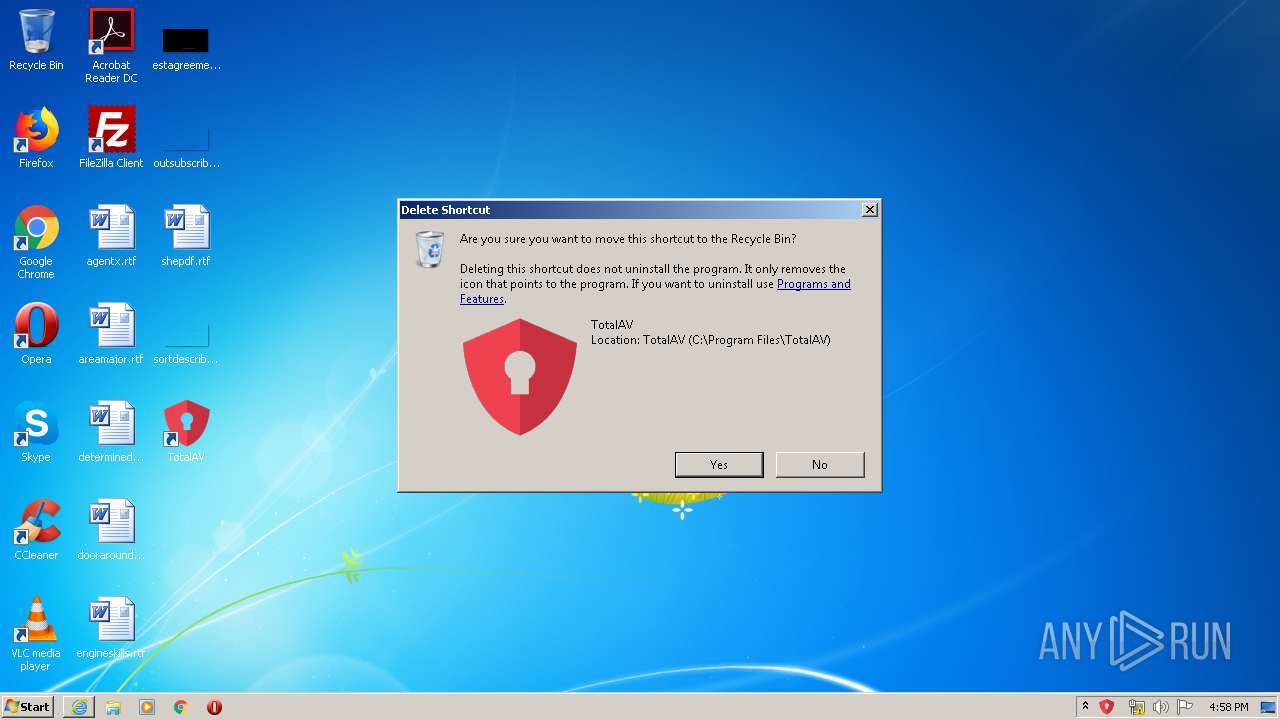
MALICIOUS
Application was dropped or rewritten from another process
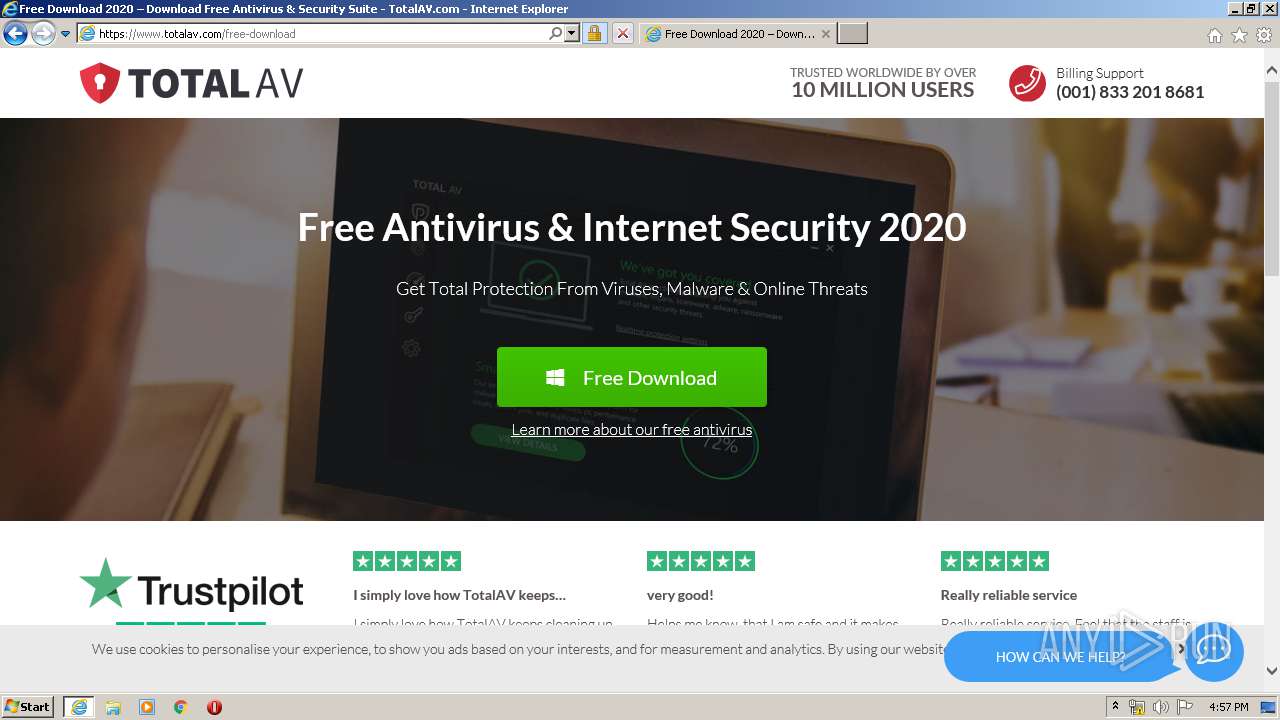
- TotalAV_Setup.exe (PID: 3816)
- TotalAV_Setup.exe (PID: 2880)
- nsCE97.tmp (PID: 2140)
- nsD0AC.tmp (PID: 3120)
- nsD252.tmp (PID: 4080)
- nsD4E4.tmp (PID: 3192)
- nsD61D.tmp (PID: 3220)
- nsE2FF.tmp (PID: 4060)
- SecurityService.exe (PID: 2364)
- subinacl.exe (PID: 3012)
- subinacl.exe (PID: 2504)
- TotalAV.exe (PID: 2116)
- SecurityService.exe (PID: 880)
- TotalAV.exe (PID: 2688)
Loads dropped or rewritten executable
- TotalAV_Setup.exe (PID: 3816)
- TotalAV.exe (PID: 2116)
- SecurityService.exe (PID: 880)
Changes settings of System certificates
- SecurityService.exe (PID: 880)
- TotalAV.exe (PID: 2116)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 856)
Starts application with an unusual extension
- TotalAV_Setup.exe (PID: 3816)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2744)
- TotalAV_Setup.exe (PID: 3816)
- SecurityService.exe (PID: 880)
Uses TASKKILL.EXE to kill process
- nsCE97.tmp (PID: 2140)
- nsD0AC.tmp (PID: 3120)
- nsD252.tmp (PID: 4080)
- nsD4E4.tmp (PID: 3192)
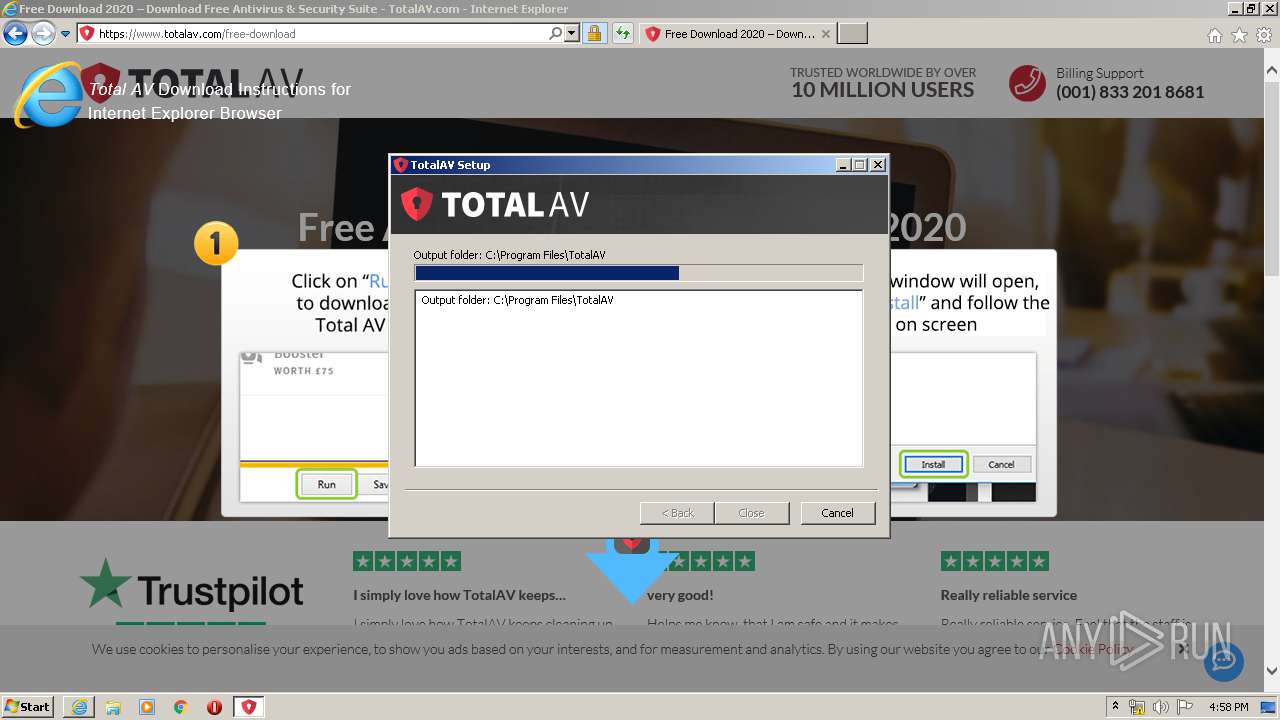
Creates files in the program directory
- TotalAV_Setup.exe (PID: 3816)
- SecurityService.exe (PID: 2364)
- TotalAV.exe (PID: 2116)
- SecurityService.exe (PID: 880)
Creates a software uninstall entry
- TotalAV_Setup.exe (PID: 3816)
Reads Environment values
- SecurityService.exe (PID: 2364)
- TotalAV.exe (PID: 2116)
- SecurityService.exe (PID: 880)
- TotalAV.exe (PID: 2688)
Executed as Windows Service
- SecurityService.exe (PID: 880)
Creates files in the user directory
- TotalAV.exe (PID: 2116)
Creates files in the Windows directory
- SecurityService.exe (PID: 880)
Adds / modifies Windows certificates
- SecurityService.exe (PID: 880)
- TotalAV.exe (PID: 2116)
Removes files from Windows directory
- SecurityService.exe (PID: 880)
Modifies the open verb of a shell class
- SecurityService.exe (PID: 880)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 3568)
Changes internet zones settings
- iexplore.exe (PID: 2744)
Creates files in the user directory
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 3988)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 856)
- iexplore.exe (PID: 3568)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3988)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 3988)
Reads internet explorer settings
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 3568)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2744)
Reads settings of System Certificates
- iexplore.exe (PID: 2744)
- TotalAV.exe (PID: 2116)
- SecurityService.exe (PID: 880)
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 3568)
Application launched itself
- iexplore.exe (PID: 2744)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2744)
Changes settings of System certificates
- iexplore.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
22
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 880 | "C:\Program Files\TotalAV\SecurityService.exe" | C:\Program Files\TotalAV\SecurityService.exe | services.exe | ||||||||||||
User: SYSTEM Company: TotalAV Integrity Level: SYSTEM Description: TotalAV Ultimate Antivirus Service Exit code: 0 Version: 5.5.83.0 Modules
| |||||||||||||||
| 1296 | "taskkill" /f /T /IM "avupdate.exe" | C:\Windows\system32\taskkill.exe | — | nsD0AC.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | "taskkill" /f /T /IM "Update.Win.exe" | C:\Windows\system32\taskkill.exe | — | nsD252.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
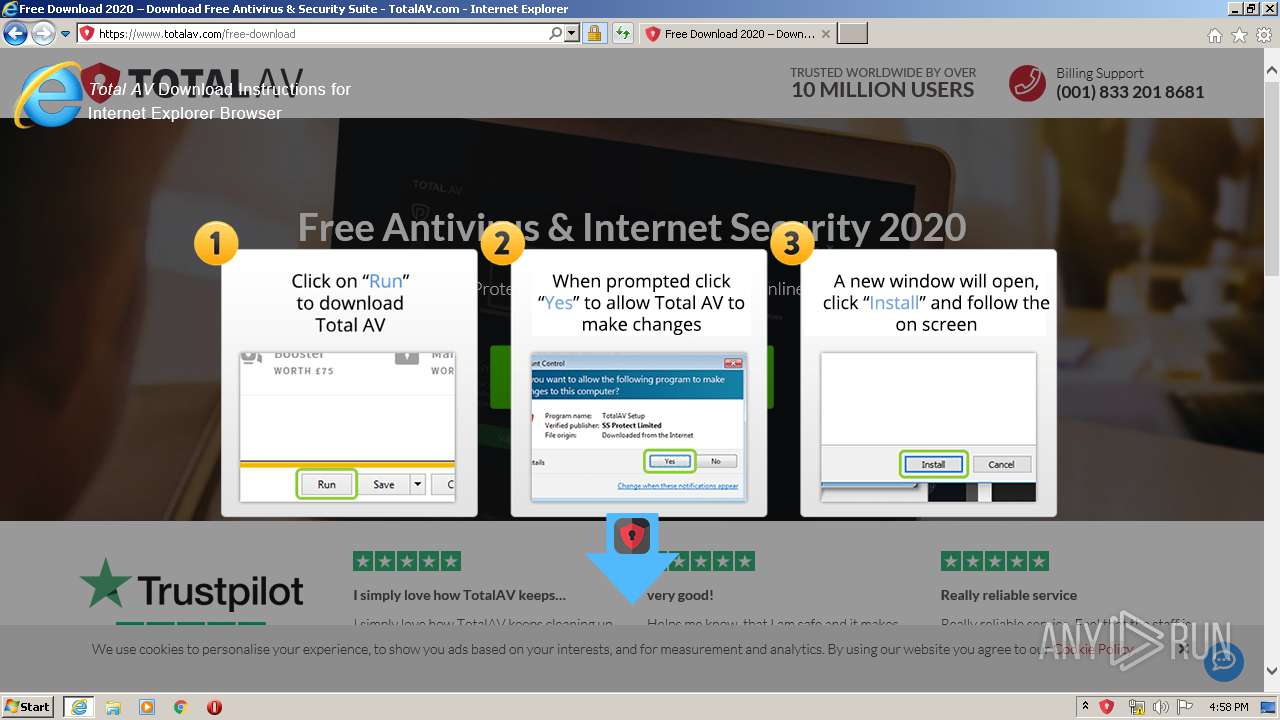
| 2116 | "C:\Program Files\TotalAV\TotalAV.exe" --installed | C:\Program Files\TotalAV\TotalAV.exe | TotalAV_Setup.exe | ||||||||||||
User: admin Company: TotalAV Integrity Level: HIGH Description: TotalAV Ultimate Antivirus User Interface Exit code: 0 Version: 5.5.83.0 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\nssC724.tmp\nsCE97.tmp" "taskkill" /F /FI "WINDOWTITLE eq TotalAV" | C:\Users\admin\AppData\Local\Temp\nssC724.tmp\nsCE97.tmp | — | TotalAV_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\TotalAV\SecurityService.exe" "--install" | C:\Program Files\TotalAV\SecurityService.exe | — | nsE2FF.tmp | |||||||||||
User: admin Company: TotalAV Integrity Level: HIGH Description: TotalAV Ultimate Antivirus Service Exit code: 0 Version: 5.5.83.0 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\TotalAV\bins\subinacl.exe" /SERVICE "SecurityServiceMonitor" /GRANT=everyone=T | C:\Program Files\TotalAV\bins\subinacl.exe | — | SecurityService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: SubInAcl Exit code: 0 Version: 5.2.3790.1180 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\TotalAV\TotalAV.exe" --startup | C:\Program Files\TotalAV\TotalAV.exe | — | SecurityService.exe | |||||||||||
User: admin Company: TotalAV Integrity Level: MEDIUM Description: TotalAV Ultimate Antivirus User Interface Exit code: 0 Version: 5.5.83.0 Modules
| |||||||||||||||
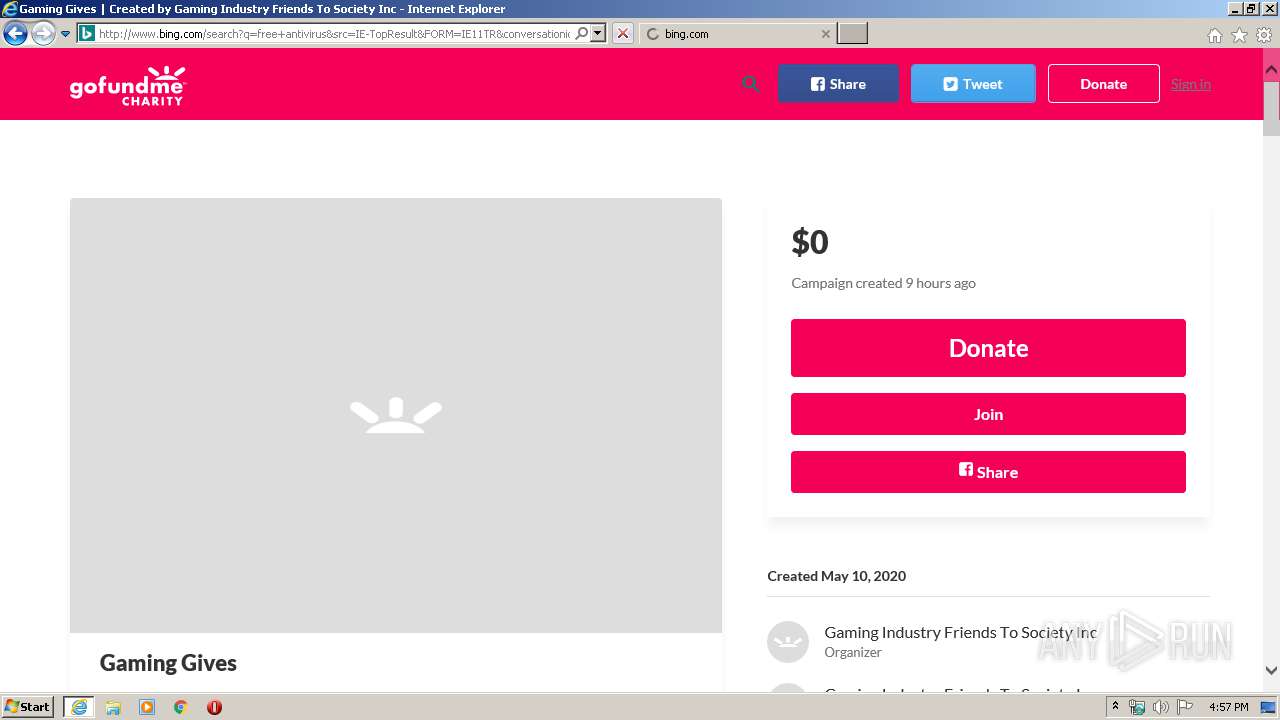
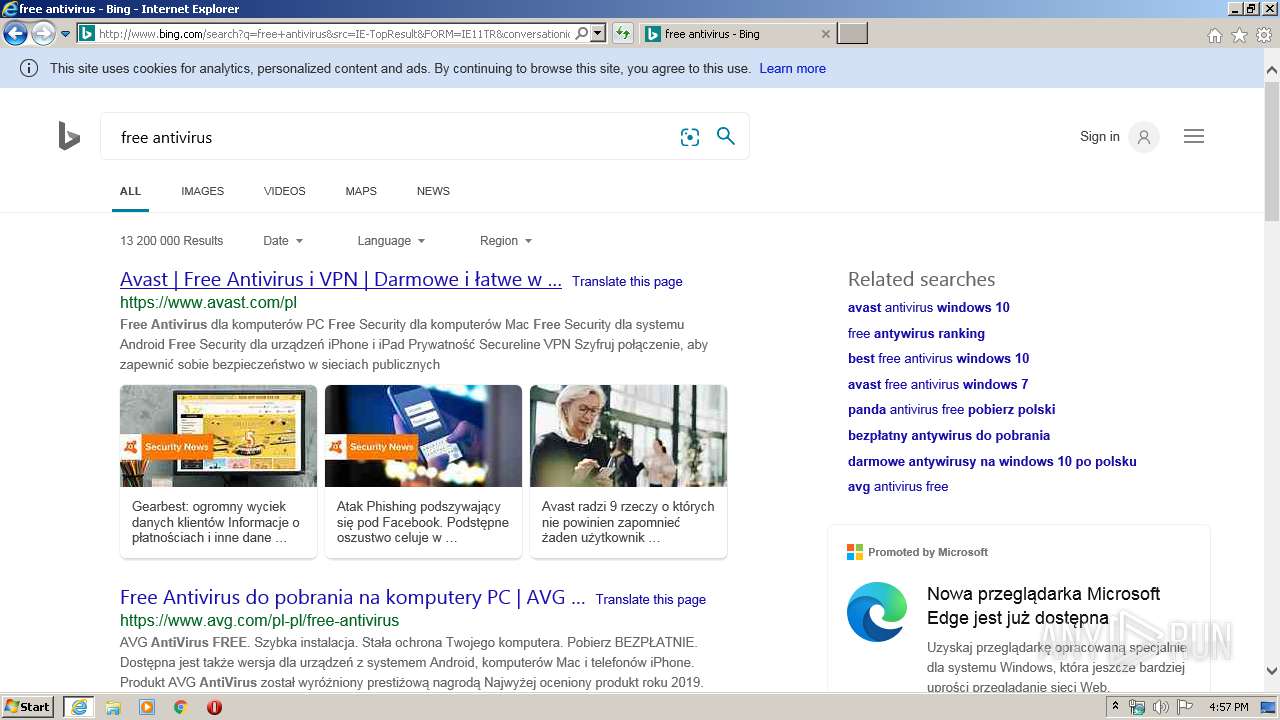
| 2744 | "C:\Program Files\Internet Explorer\iexplore.exe" https://charity.gofundme.com/o/en/campaign/bloxland-free-robux-generator | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 261
Read events
2 770
Write events
3 768
Delete events
1 723
Modification events
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2849925000 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30811875 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
161
Suspicious files
264
Text files
575
Unknown types
196
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7916.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7917.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\OG3W43KP.txt | — | |
MD5:— | SHA256:— | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:1A47E518796015B2D2F290BAAC828632 | SHA256:8CB574C9CBE86FF824ABFF002794FC739140969CBFBBD3DD4AA9FCD5B2A5DCA4 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:EEB5B38981FE9E2F71BBCE542563331C | SHA256:DE7088855D6A1CF830B3C87CA5A1158AEFF9EF56D7040835A7DDF22B79E8C4CA | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:DAE0CF39DCEDA7E19D844ABDE6EED7C3 | SHA256:787D0919586E590BF617C326DE2E6617BD21DA39F6C3FB85E7D54ED628B5E5BD | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:D464DAB830D7D79D06886BA993C7D872 | SHA256:4F0429B0F9A21E3641D1E017FE0EF29CB897C0C89A01091AAC79F5E13597AD97 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3E76C743A83DA5F33812D485498E8C61_1B3F54E2934B358C32CD6E46DE41A3D2 | binary | |
MD5:0DD64880694E420CD614445C181BDE20 | SHA256:D3FF756A926BFA2B7316E3661D383C449DDF09290AC52159A1BC623527C7251E | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\CSUUX83Y.txt | text | |
MD5:75A3FDD8B273DFAB55F0A624A377D9C8 | SHA256:60742904F59408D13AAFA9E38B3034DCCD9B17307585456EE53CB369770E3CDC | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:BBECA3D3B9E8488BCDA68D00714AA1BB | SHA256:1C355B2B6605DDE347F1AB29111CF0C6374489E317D4C1592923CB92F3329835 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
377
TCP/UDP connections
353
DNS requests
119
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3988 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCB%2BSLuPwIVdw%3D%3D | US | der | 1.74 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3988 | iexplore.exe | 52.1.183.139:443 | charity.gofundme.com | Amazon.com, Inc. | US | unknown |
3988 | iexplore.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3988 | iexplore.exe | 143.204.202.97:443 | uploads.crowdrise.com | — | US | malicious |
3988 | iexplore.exe | 192.124.249.23:80 | — | Sucuri | US | suspicious |
3988 | iexplore.exe | 104.16.132.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3988 | iexplore.exe | 151.101.2.109:443 | cdn.polyfill.io | Fastly | US | suspicious |
3988 | iexplore.exe | 104.16.87.20:443 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
3988 | iexplore.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3988 | iexplore.exe | 143.204.202.115:443 | assets-charity.gofundme.com | — | US | suspicious |
3988 | iexplore.exe | 172.217.16.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
charity.gofundme.com |
| unknown |
ocsp.godaddy.com |
| whitelisted |
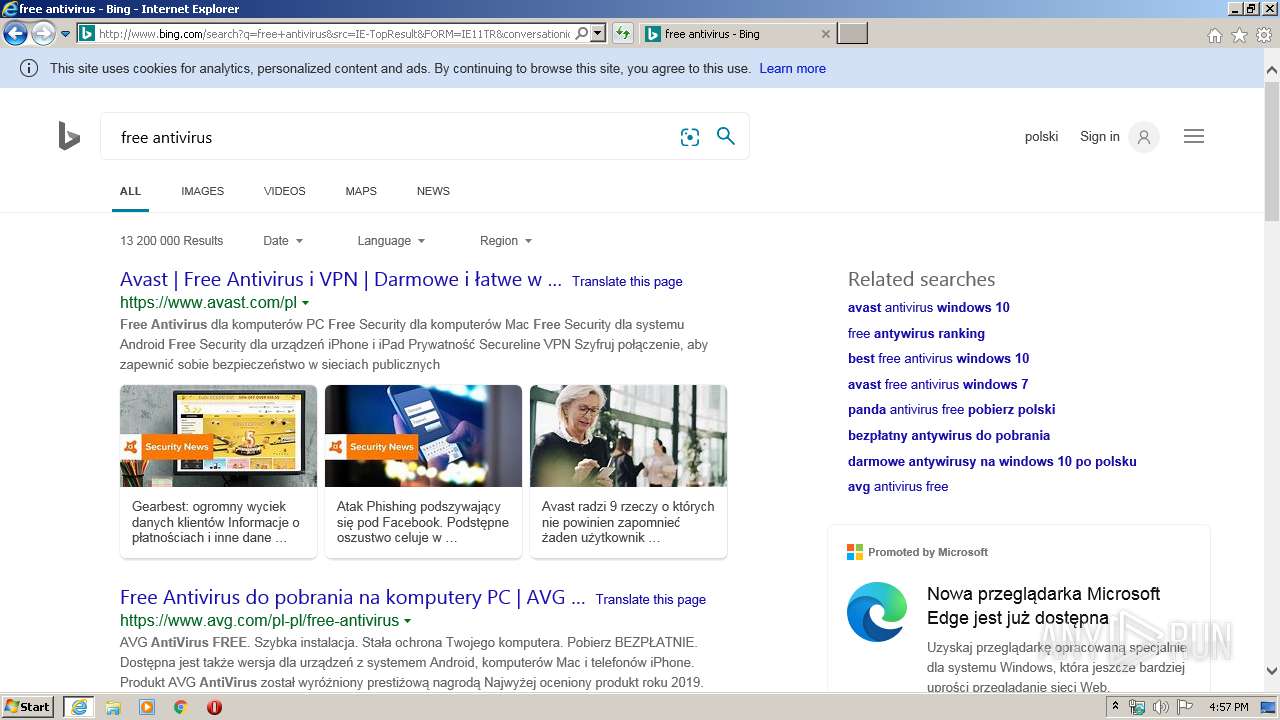
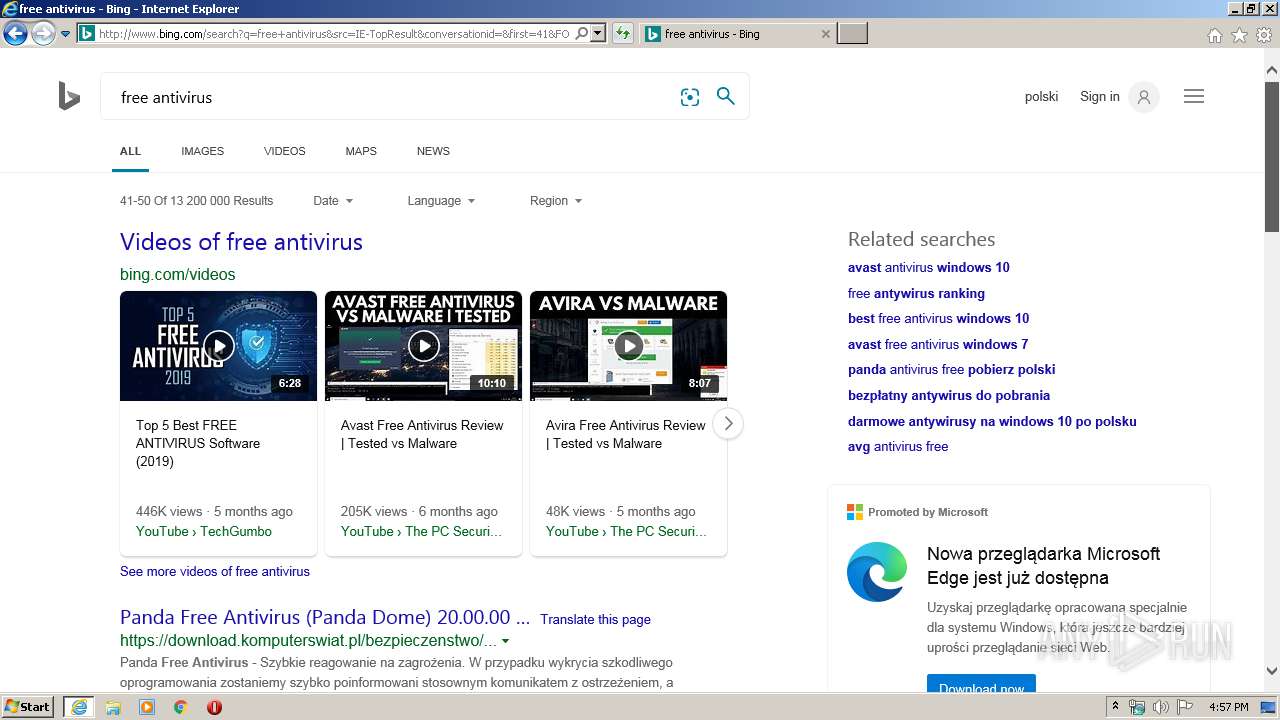
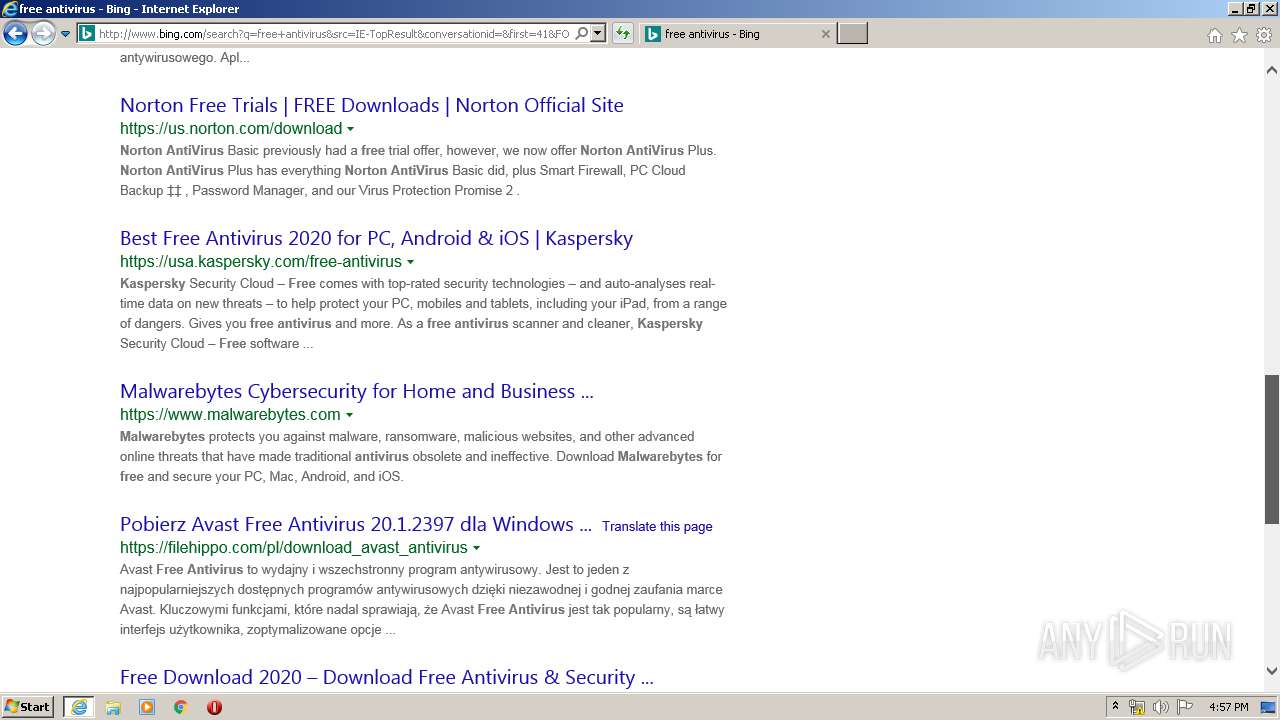
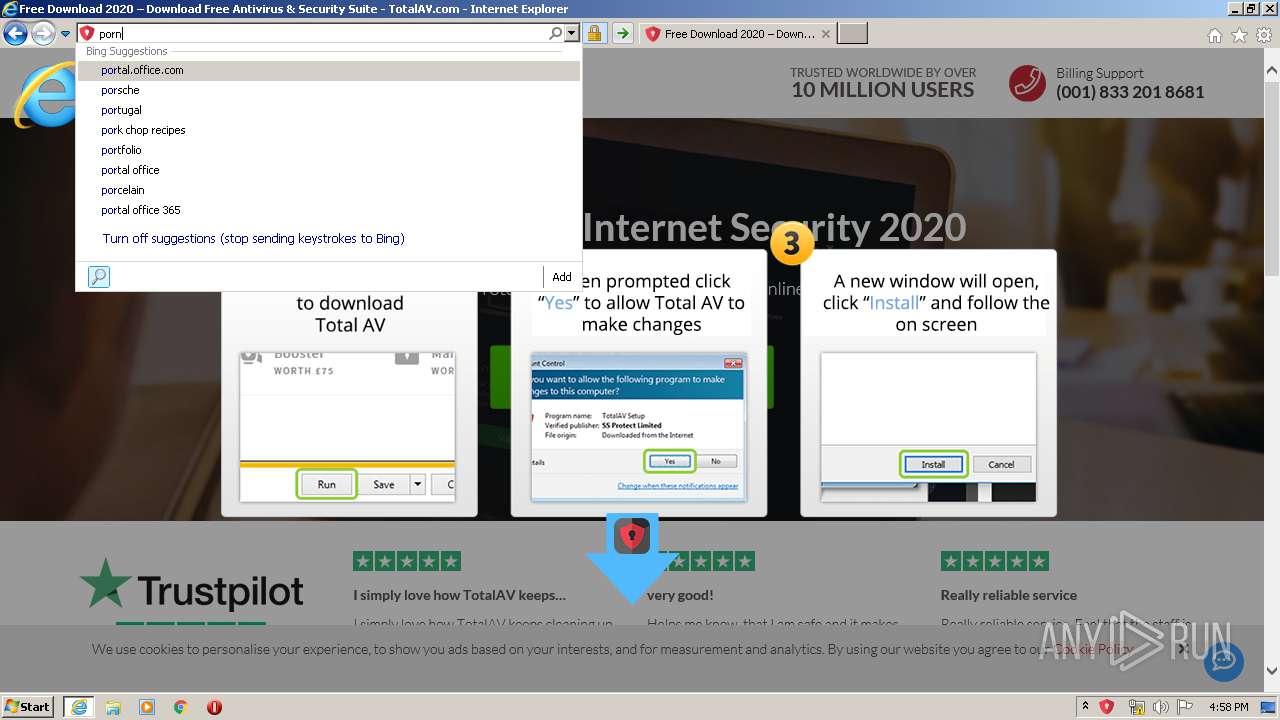
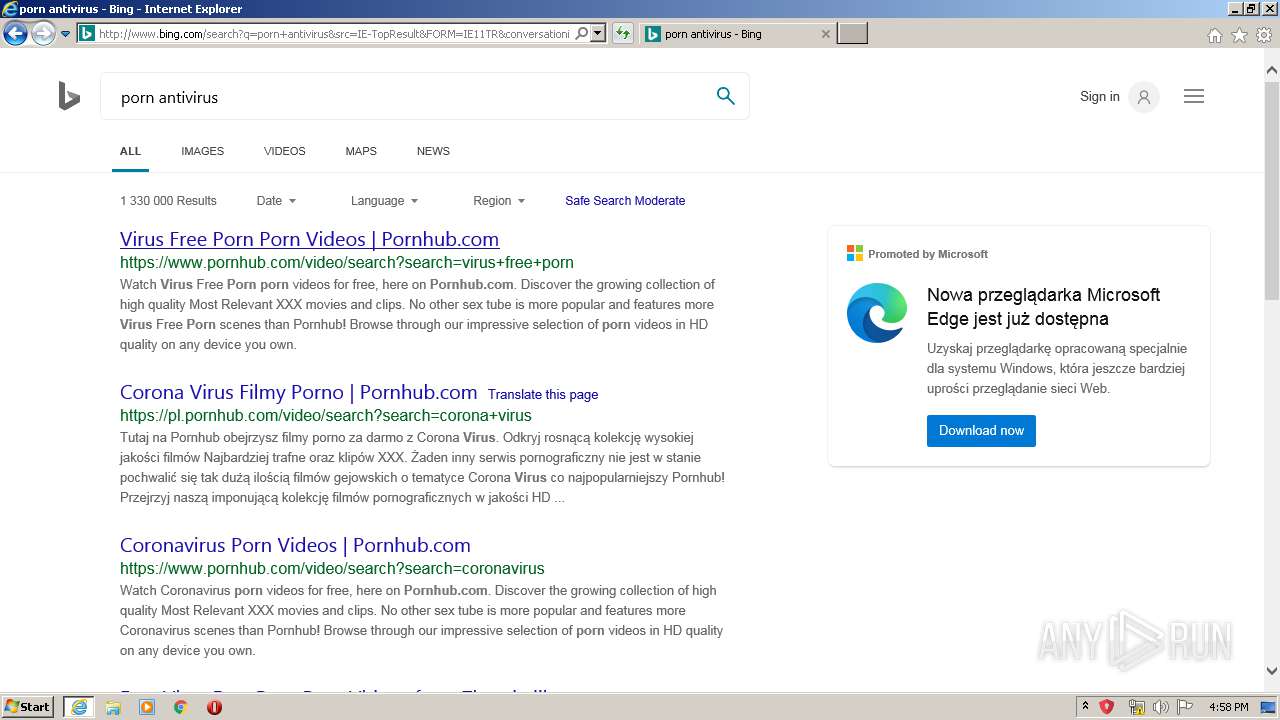
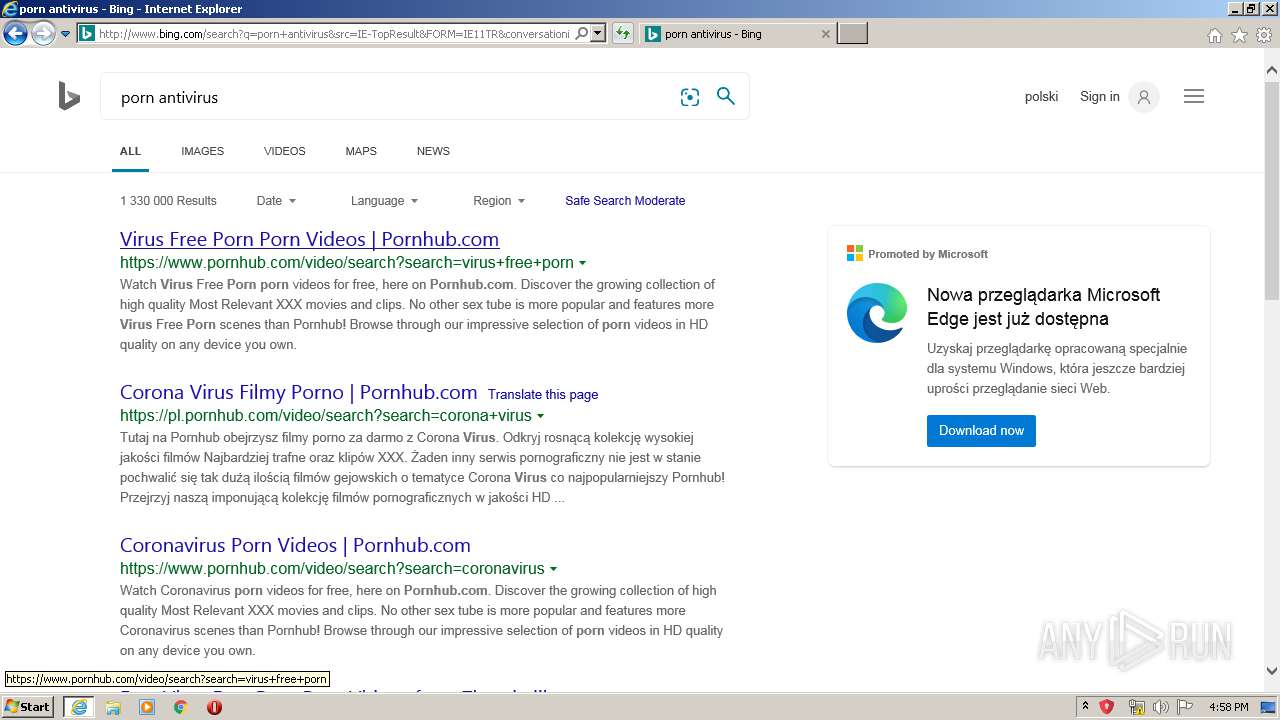
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
uploads.crowdrise.com |
| malicious |
cdn.jsdelivr.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.polyfill.io |
| whitelisted |
assets-charity.gofundme.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3988 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |