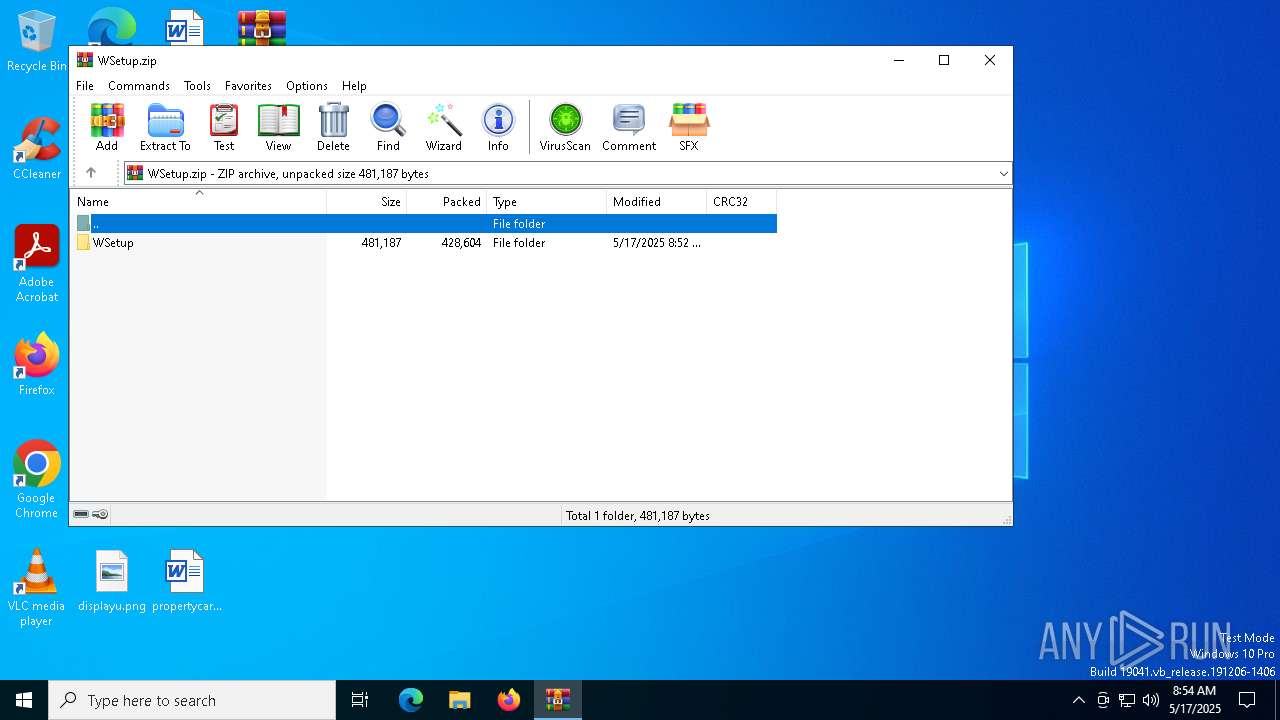
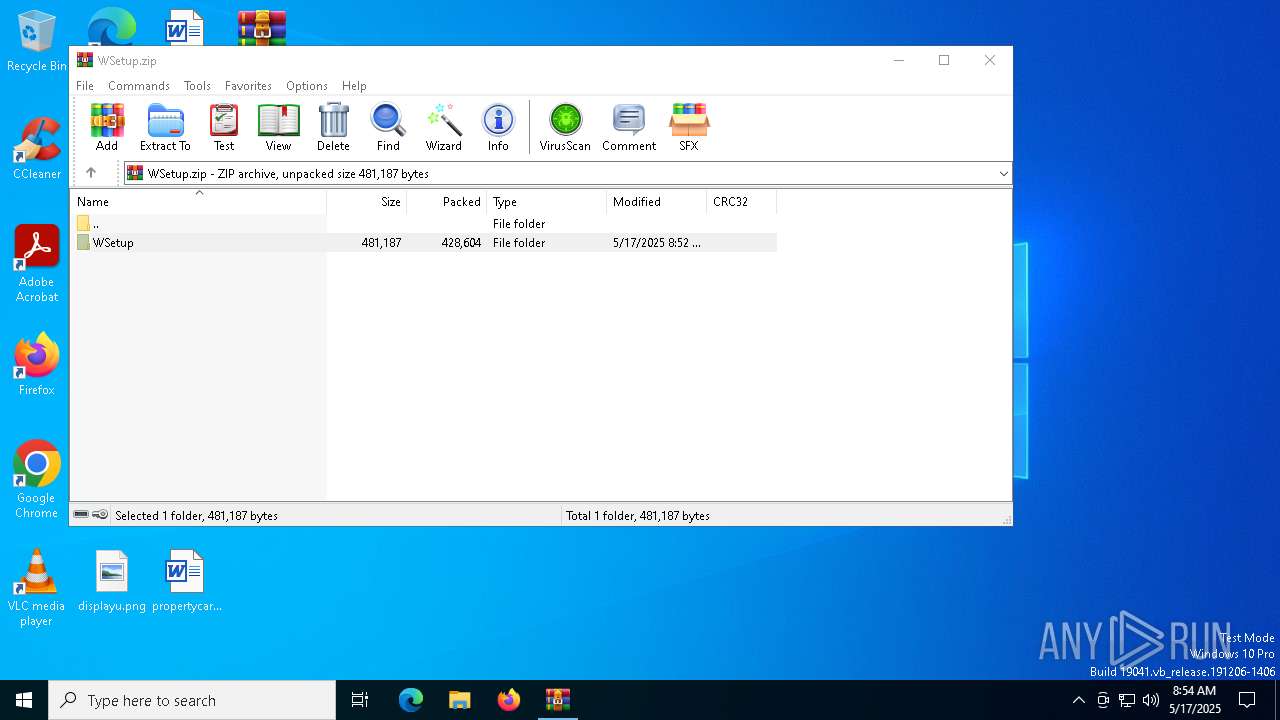
| File name: | WSetup.zip |
| Full analysis: | https://app.any.run/tasks/decc9abc-a44c-4fa8-a43c-784168575f1a |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 08:54:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 9E63F456E6C4372163F9136A73E1FA3D |
| SHA1: | D8FB7778EA4303FDB45714A6B9C7CA674444606E |
| SHA256: | 7C0ED6BCFD13FF1BE1C5BF7699017DA663DFC667FD68FB1175163D6A05E687B8 |
| SSDEEP: | 12288:06hmHdF4TltT258ndIIZ8anbHseniZKvlfeegZS7CX1fXYITLdstM:06hmHdFcltTK8ndIIWazseniZKtfeegH |
MALICIOUS
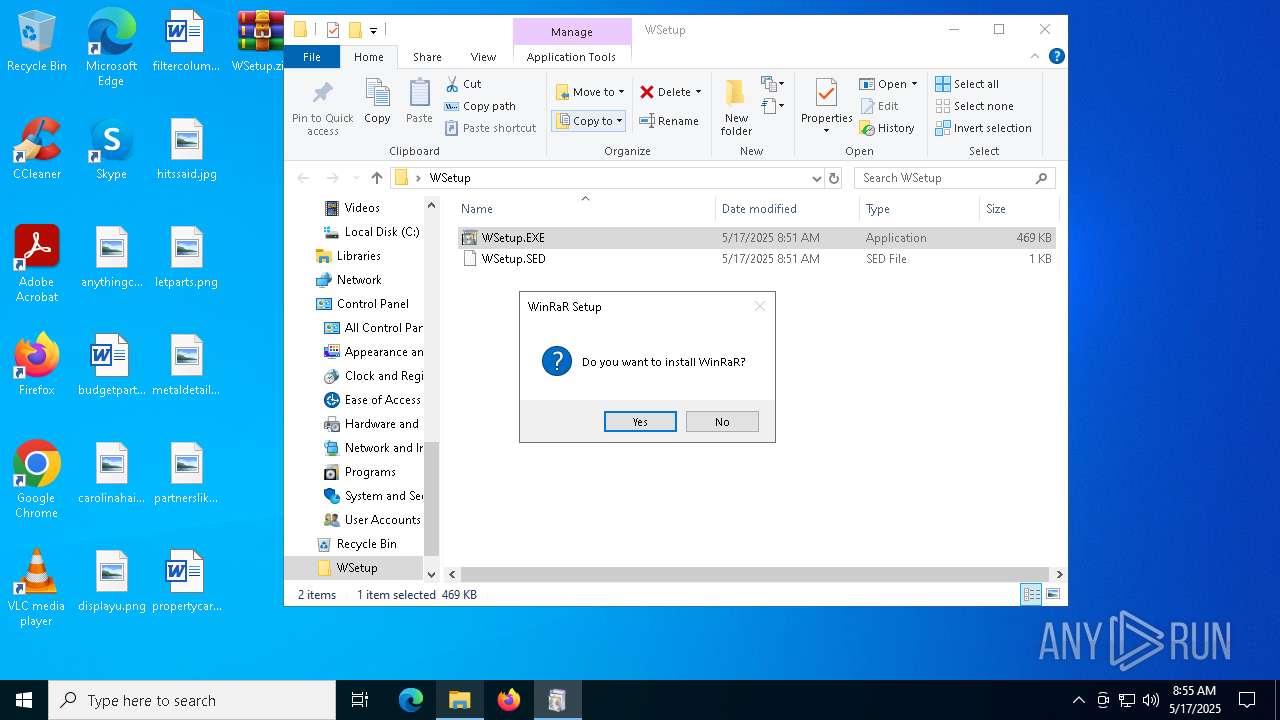
Generic archive extractor
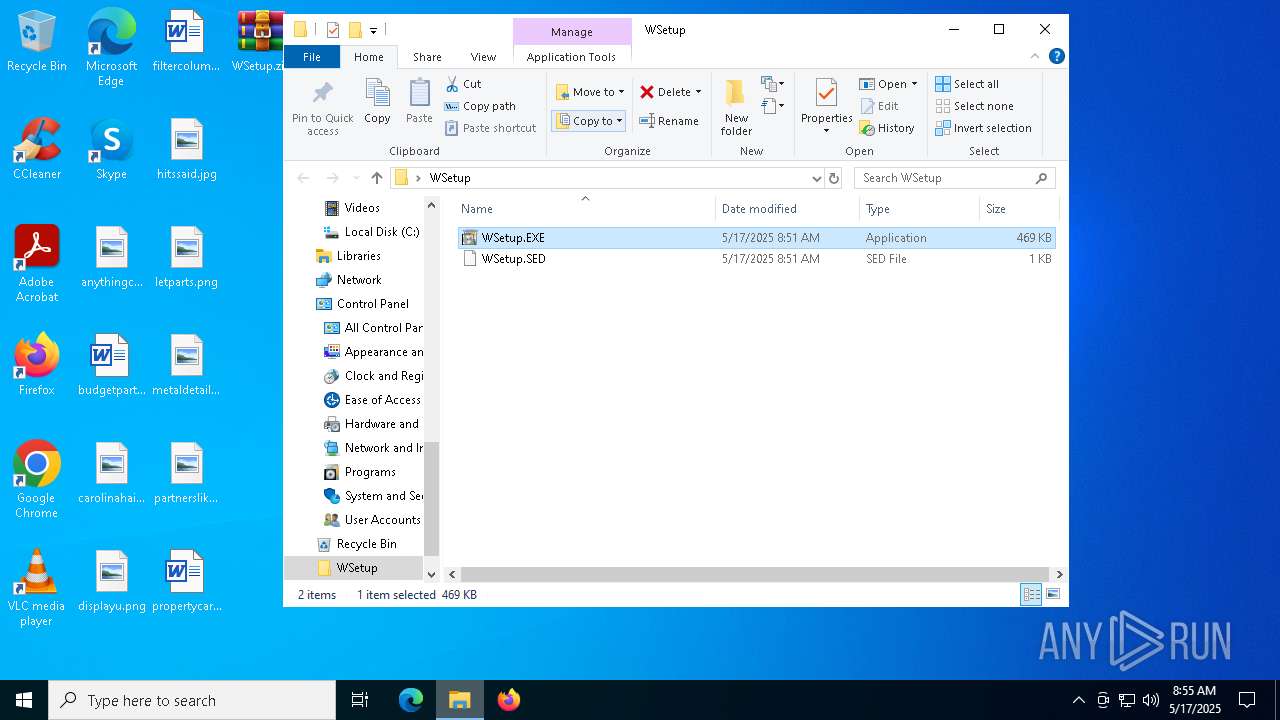
- WinRAR.exe (PID: 7332)
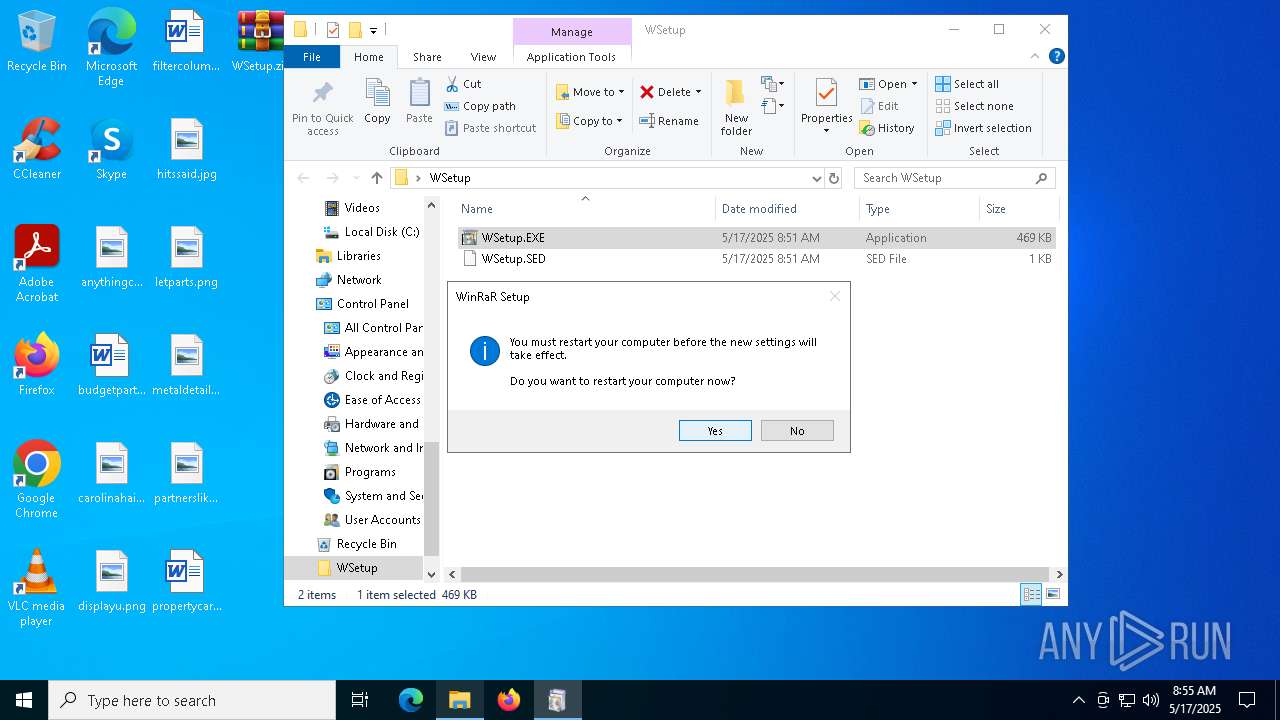
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5608)
Changes the autorun value in the registry
- WSetup.EXE (PID: 6972)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 7332)
Starts a Microsoft application from unusual location
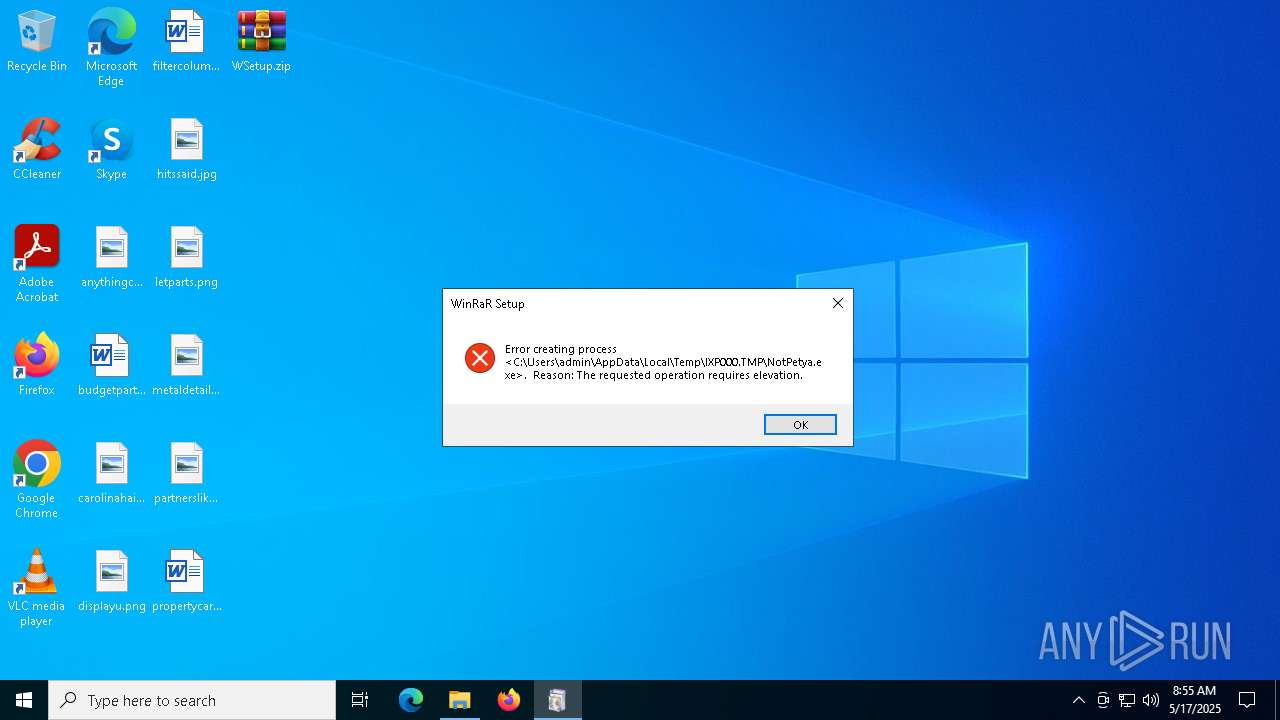
- WSetup.EXE (PID: 3768)
- WSetup.EXE (PID: 6972)
Executable content was dropped or overwritten
- WSetup.EXE (PID: 3768)
- WSetup.EXE (PID: 6972)
- NotPetya.exe (PID: 2244)
- rundll32.exe (PID: 5332)
Reads security settings of Internet Explorer
- NotPetya.exe (PID: 2244)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 5332)
Starts application with an unusual extension
- rundll32.exe (PID: 5332)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7332)
The sample compiled with english language support
- WinRAR.exe (PID: 7332)
- rundll32.exe (PID: 5332)
Checks supported languages
- WSetup.EXE (PID: 3768)
- D975.tmp (PID: 2600)
- WSetup.EXE (PID: 6972)
- NotPetya.exe (PID: 2244)
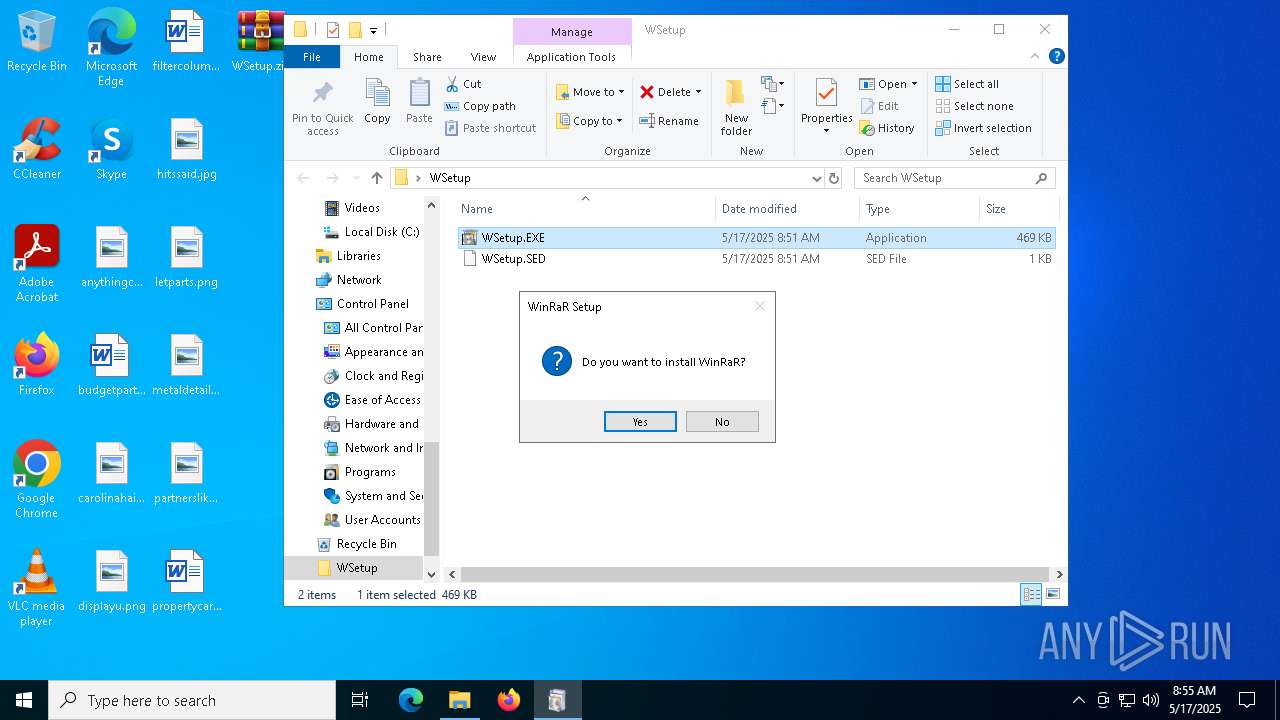
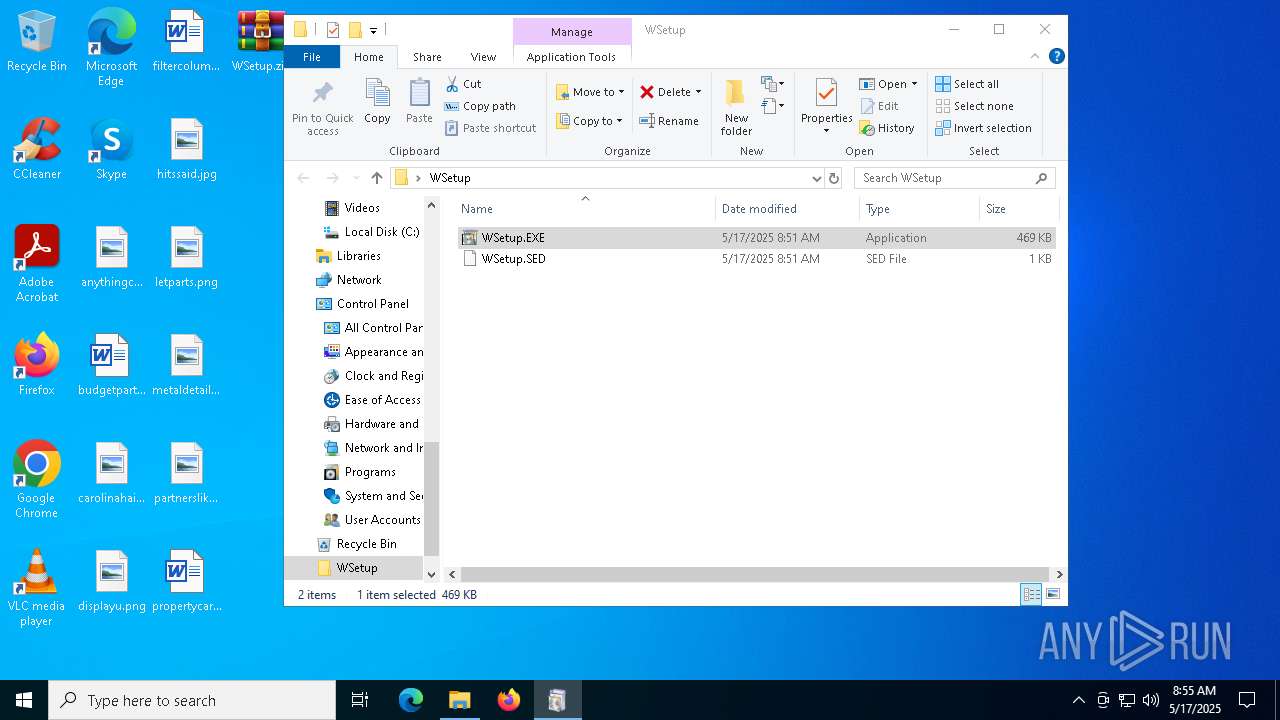
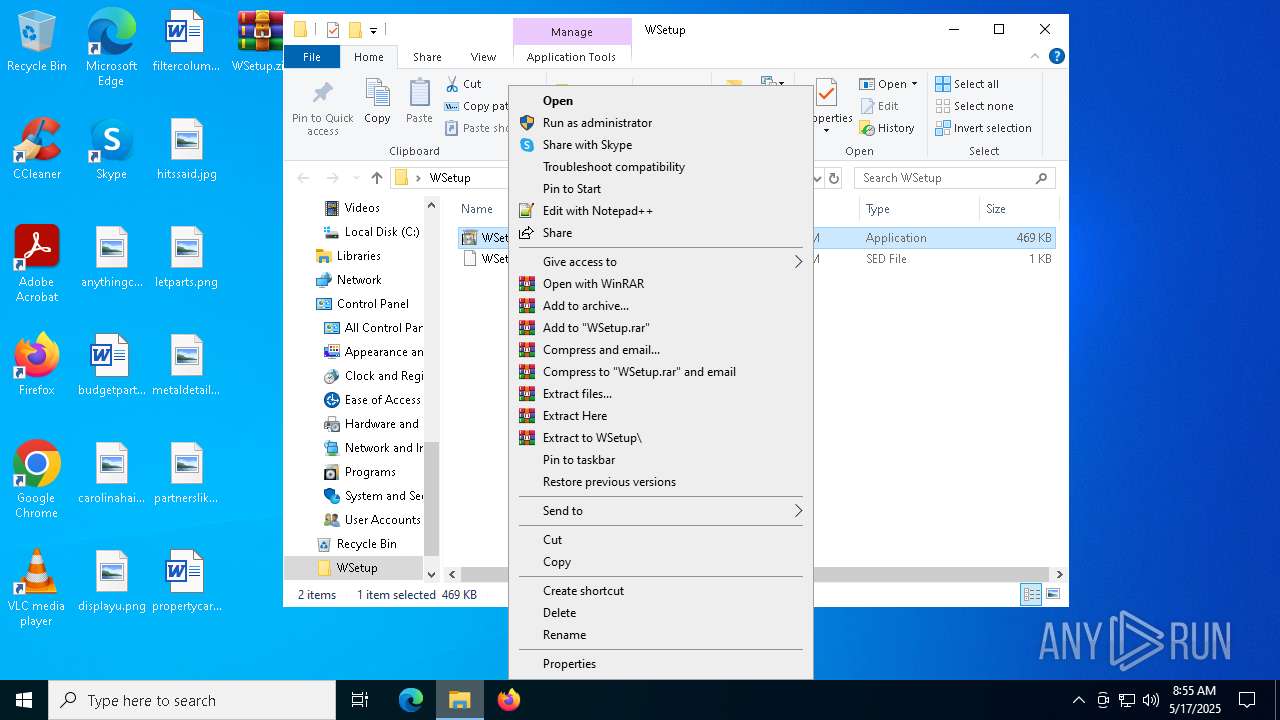
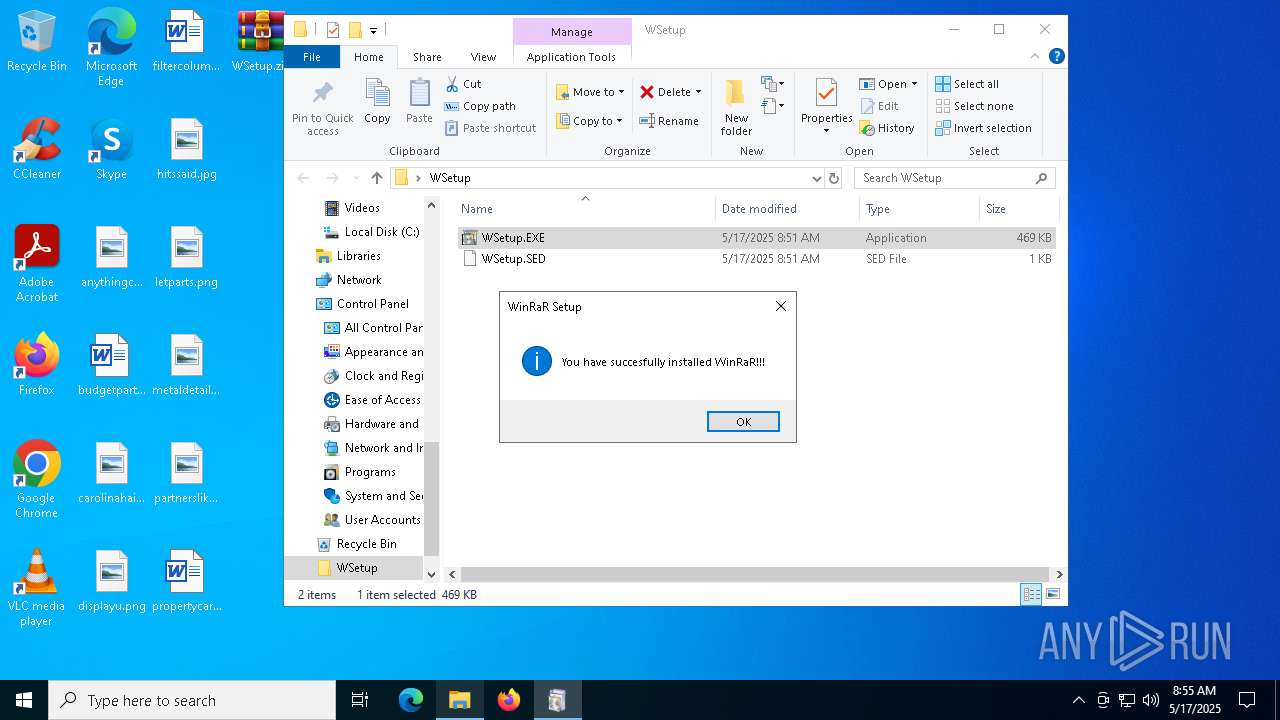
Manual execution by a user
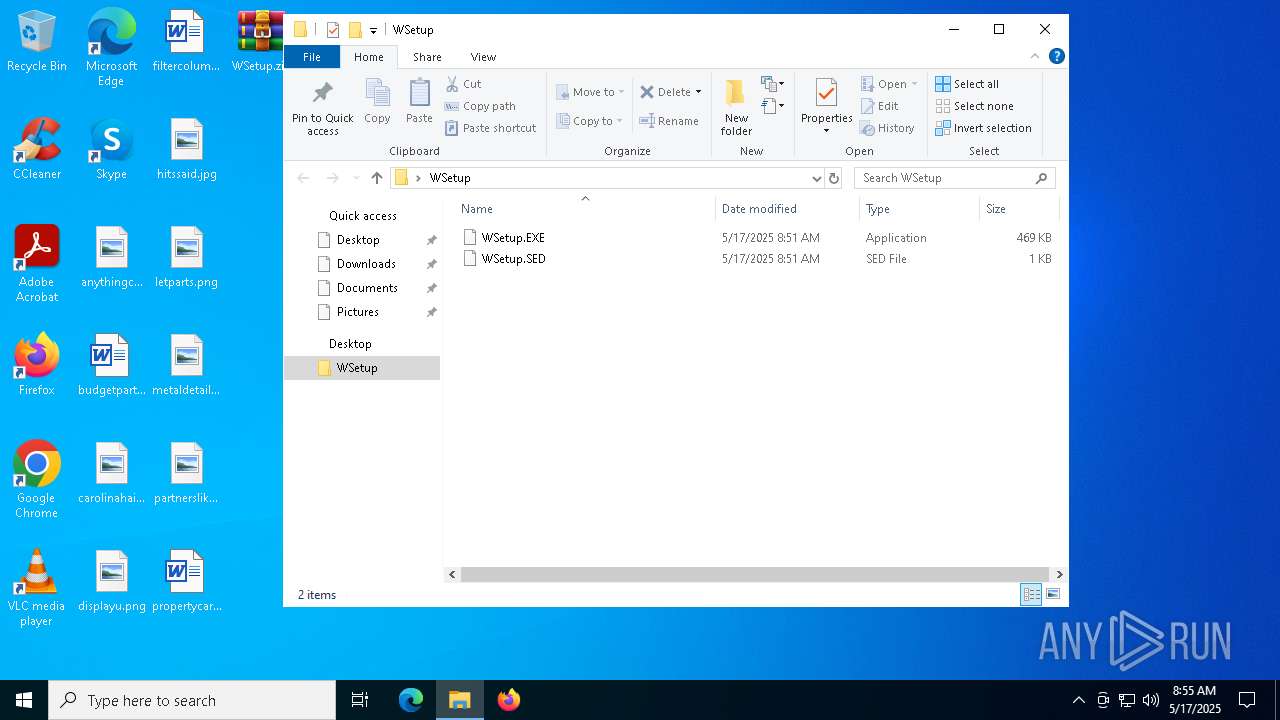
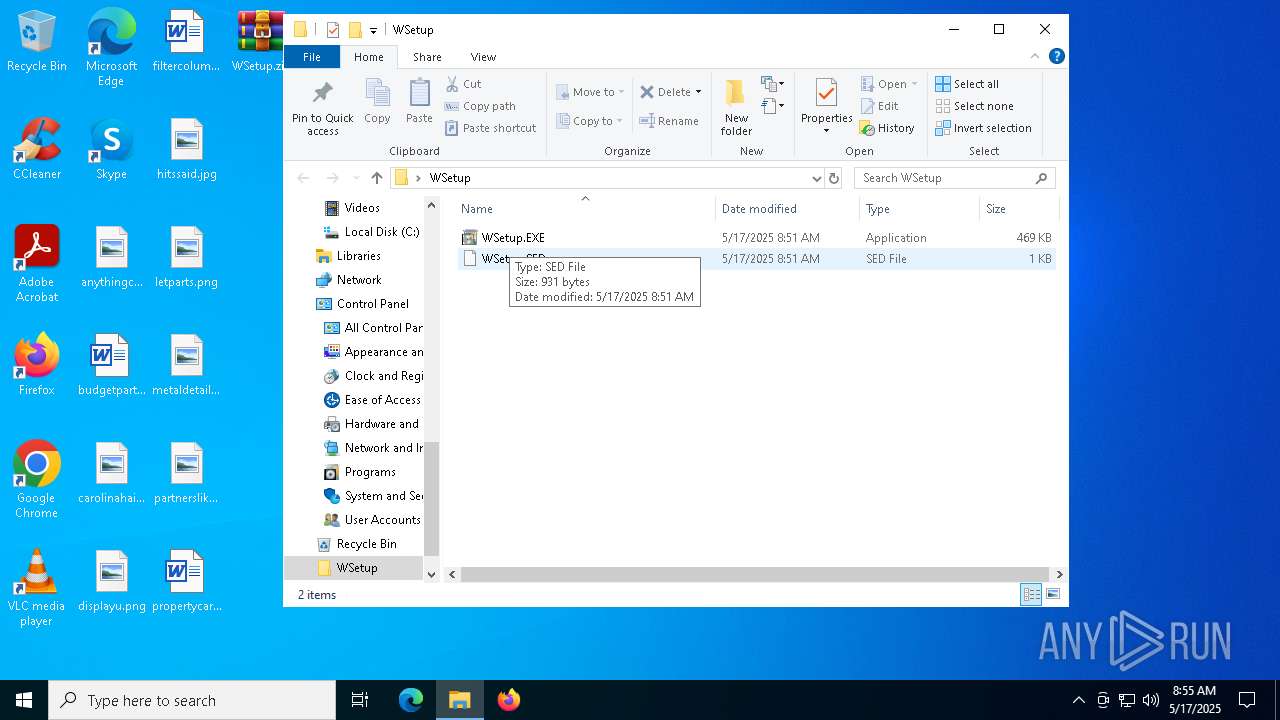
- WSetup.EXE (PID: 3768)
- WSetup.EXE (PID: 6972)
Create files in a temporary directory
- WSetup.EXE (PID: 3768)
- WSetup.EXE (PID: 6972)
- rundll32.exe (PID: 5332)
Reads the computer name
- WSetup.EXE (PID: 3768)
- NotPetya.exe (PID: 2244)
- WSetup.EXE (PID: 6972)
Reads the software policy settings
- slui.exe (PID: 7492)
Process checks computer location settings
- NotPetya.exe (PID: 2244)
Checks proxy server information
- rundll32.exe (PID: 5332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:17 01:52:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | WSetup/ |
Total processes
145
Monitored processes
15
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2088 | schtasks /Create /SC once /TN "" /TR "C:\WINDOWS\system32\shutdown.exe /r /f" /ST 09:58 | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NotPetya.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NotPetya.exe | WSetup.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 42 Modules
| |||||||||||||||
| 2600 | "C:\Users\admin\AppData\Local\Temp\D975.tmp" \\.\pipe\{18FD92F5-6907-44CA-8905-0069243B13A8} | C:\Users\admin\AppData\Local\Temp\D975.tmp | — | rundll32.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3768 | "C:\Users\admin\Desktop\WSetup\WSetup.EXE" | C:\Users\admin\Desktop\WSetup\WSetup.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 2147943140 Version: 11.00.10240.16384 (th1.150709-1700) Modules
| |||||||||||||||
| 4336 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | D975.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | "C:\Windows\System32\rundll32.exe" C:\WINDOWS\perfc.dat #1 | C:\Windows\SysWOW64\rundll32.exe | NotPetya.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5344 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5608 | /c schtasks /Create /SC once /TN "" /TR "C:\WINDOWS\system32\shutdown.exe /r /f" /ST 09:58 | C:\Windows\SysWOW64\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 681
Read events
2 661
Write events
19
Delete events
1
Modification events
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\WSetup.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
7
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5332 | rundll32.exe | \Device\HarddiskVolume2 | — | |
MD5:— | SHA256:— | |||
| 5332 | rundll32.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 7332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7332.39752\WSetup\WSetup.EXE | executable | |
MD5:199BE15EEDB1E0EDB81722AC865360B3 | SHA256:CDF22A0240DEED7C1FDCDEE2D552CA192764D6635C24B5A6B195E24A5A0F9BB0 | |||
| 5332 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\D975.tmp | executable | |
MD5:7E37AB34ECDCC3E77E24522DDFD4852D | SHA256:02EF73BD2458627ED7B397EC26EE2DE2E92C71A0E7588F78734761D8EDBDCD9F | |||
| 3768 | WSetup.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NotPetya.exe | executable | |
MD5:5B7E6E352BACC93F7B80BC968B6EA493 | SHA256:63545FA195488FF51955F09833332B9660D18F8AFB16BDF579134661962E548A | |||
| 5332 | rundll32.exe | C:\Windows\dllhost.dat | executable | |
MD5:AEEE996FD3484F28E5CD85FE26B6BDCD | SHA256:F8DBABDFA03068130C277CE49C60E35C029FF29D9E3C74C362521F3FB02670D5 | |||
| 7332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7332.39752\WSetup\WSetup.SED | text | |
MD5:81790C1BE1601BEFA01889E0DBF999D3 | SHA256:667C2AE1375983BBB68A0BC560FB1C9059ECD1FFA8465C9A68617E5437958EBE | |||
| 6972 | WSetup.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NotPetya.exe | executable | |
MD5:5B7E6E352BACC93F7B80BC968B6EA493 | SHA256:63545FA195488FF51955F09833332B9660D18F8AFB16BDF579134661962E548A | |||
| 2244 | NotPetya.exe | C:\Windows\perfc.dat | executable | |
MD5:71B6A493388E7D0B40C83CE903BC6B04 | SHA256:027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
53
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8056 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8056 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |