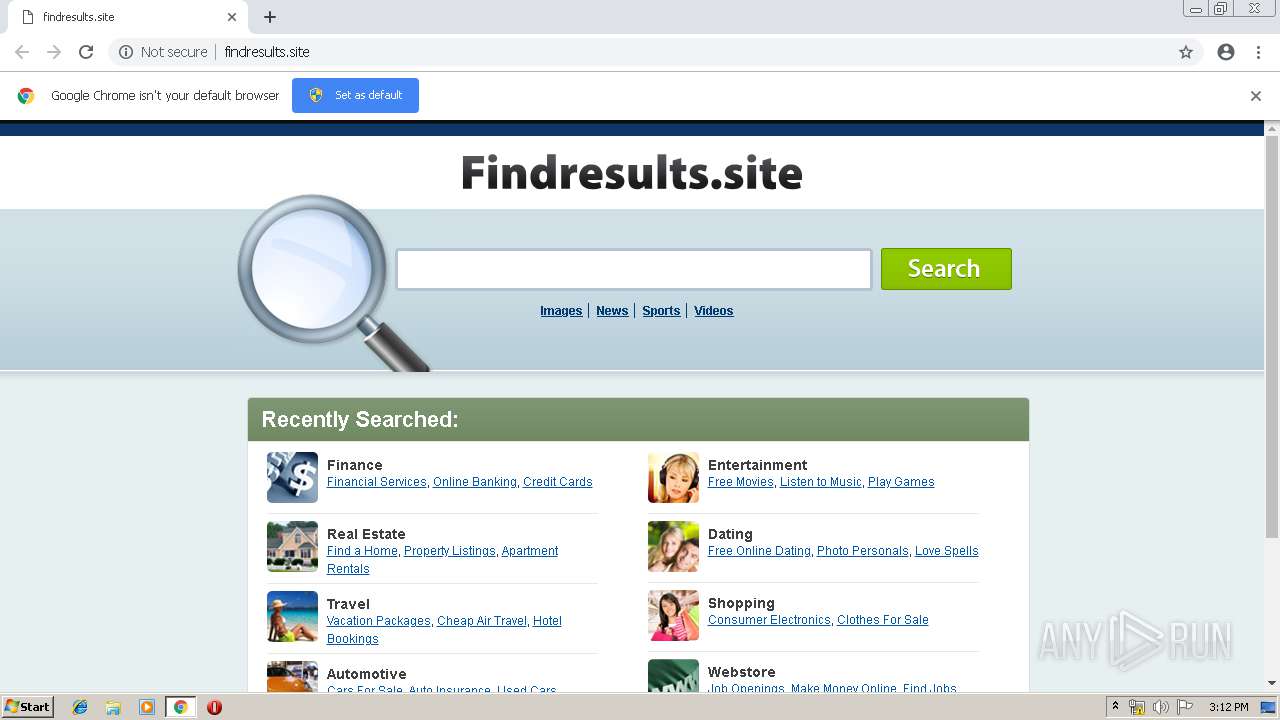
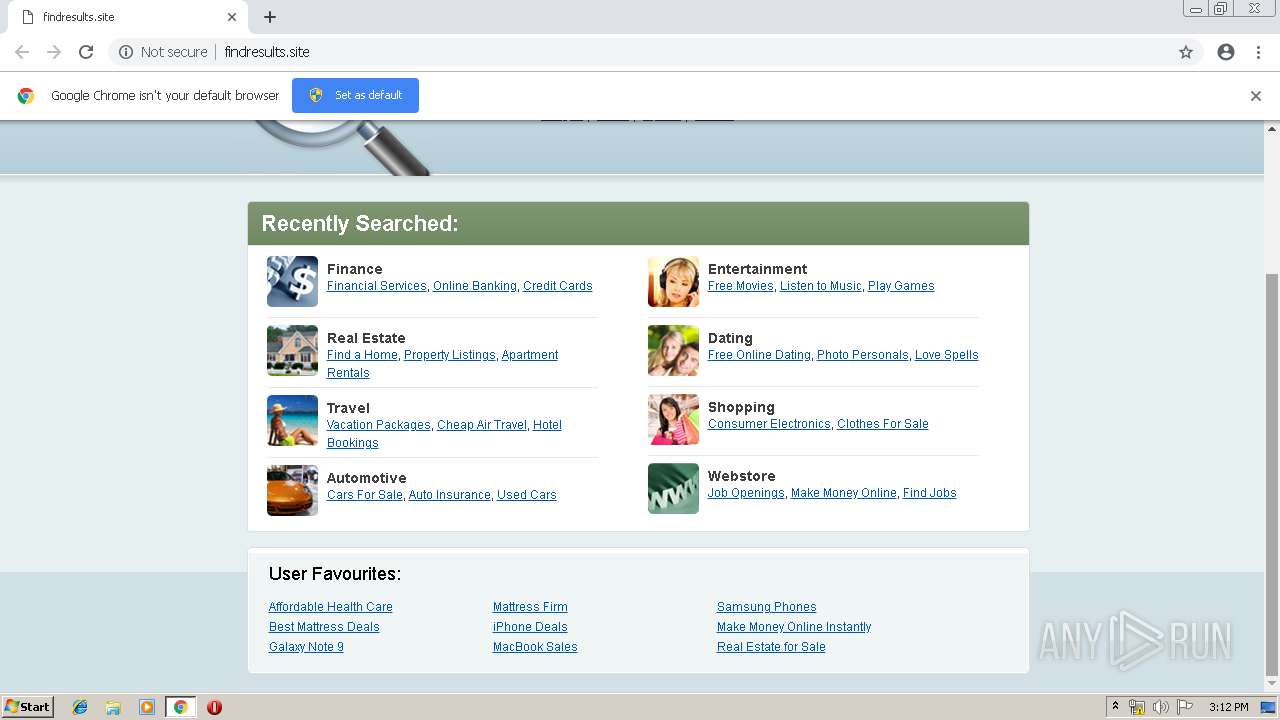
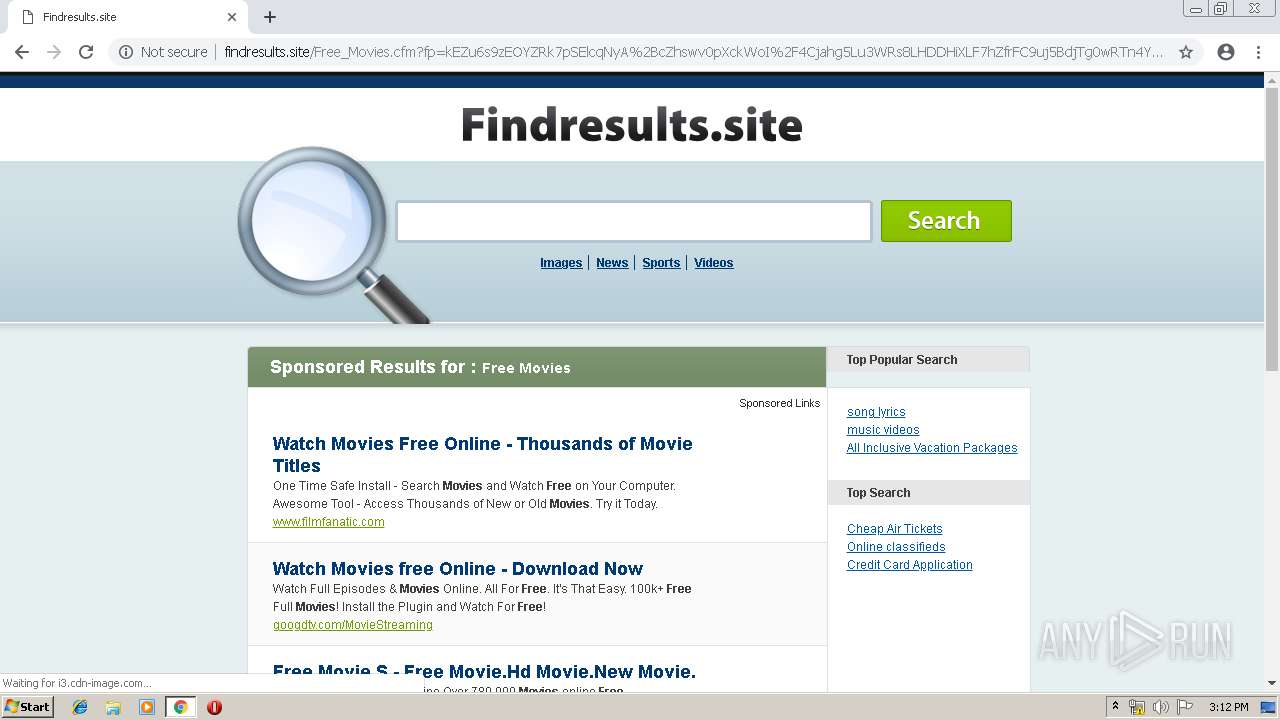
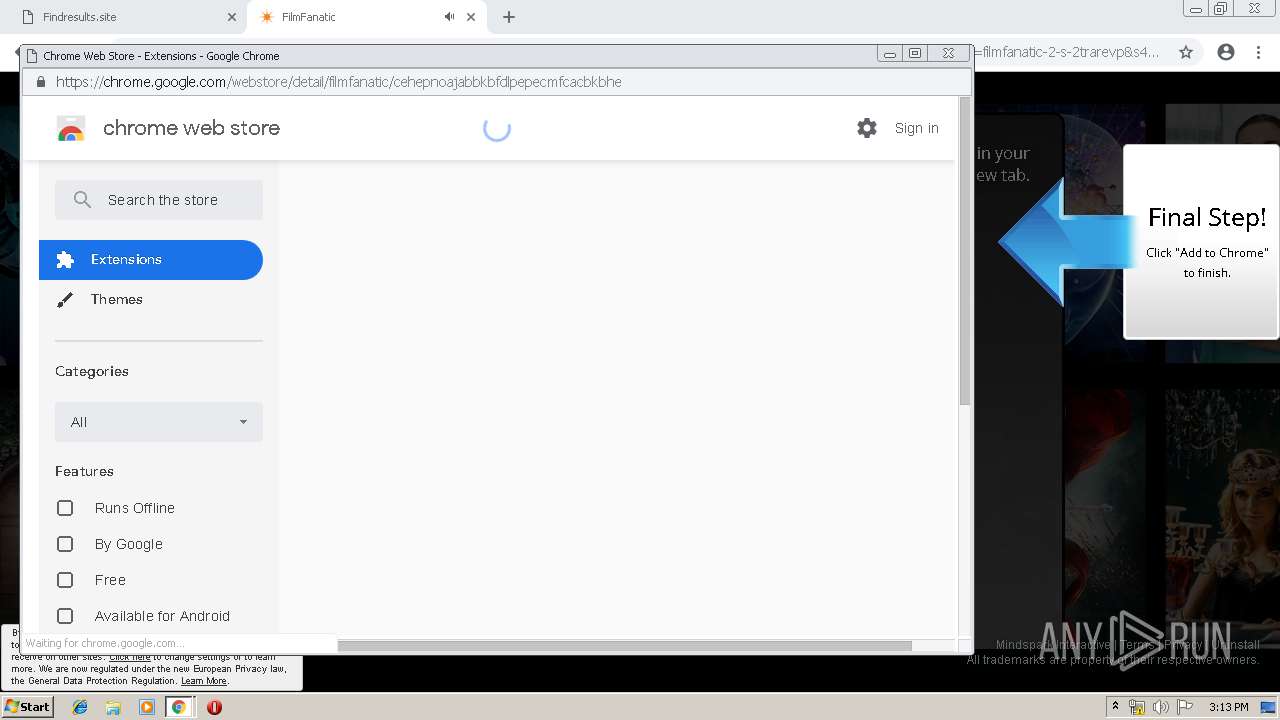
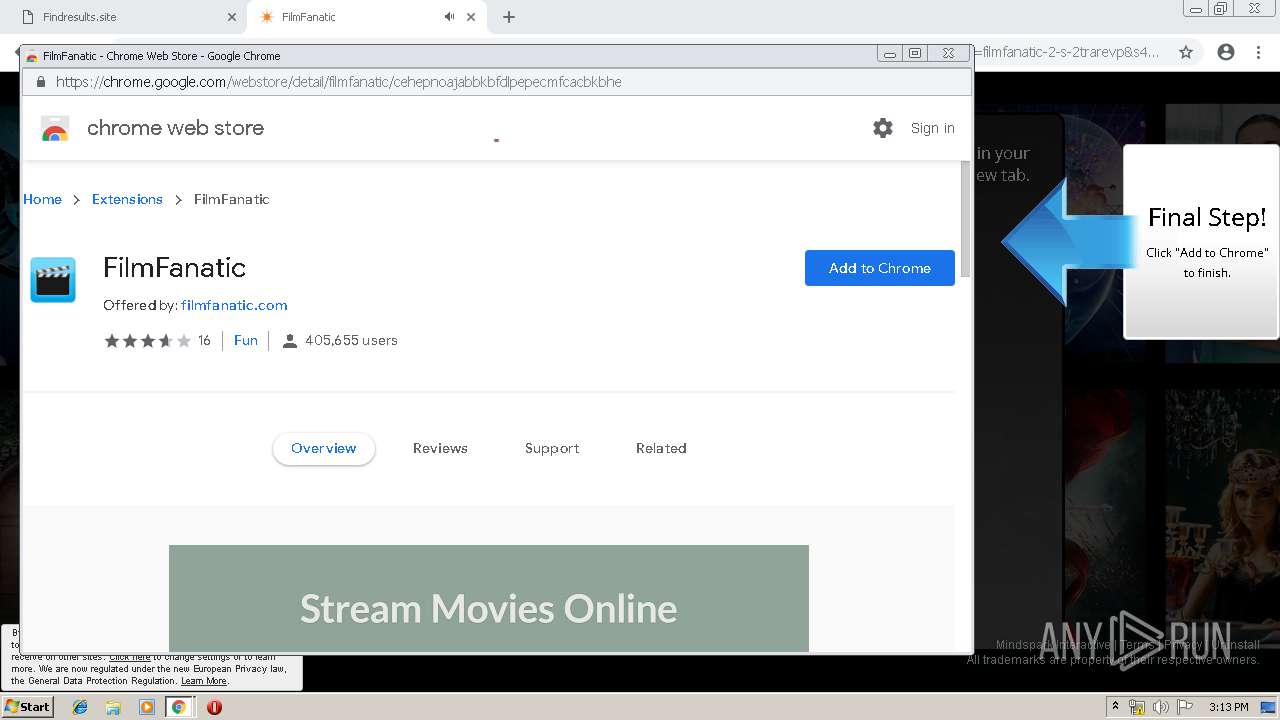
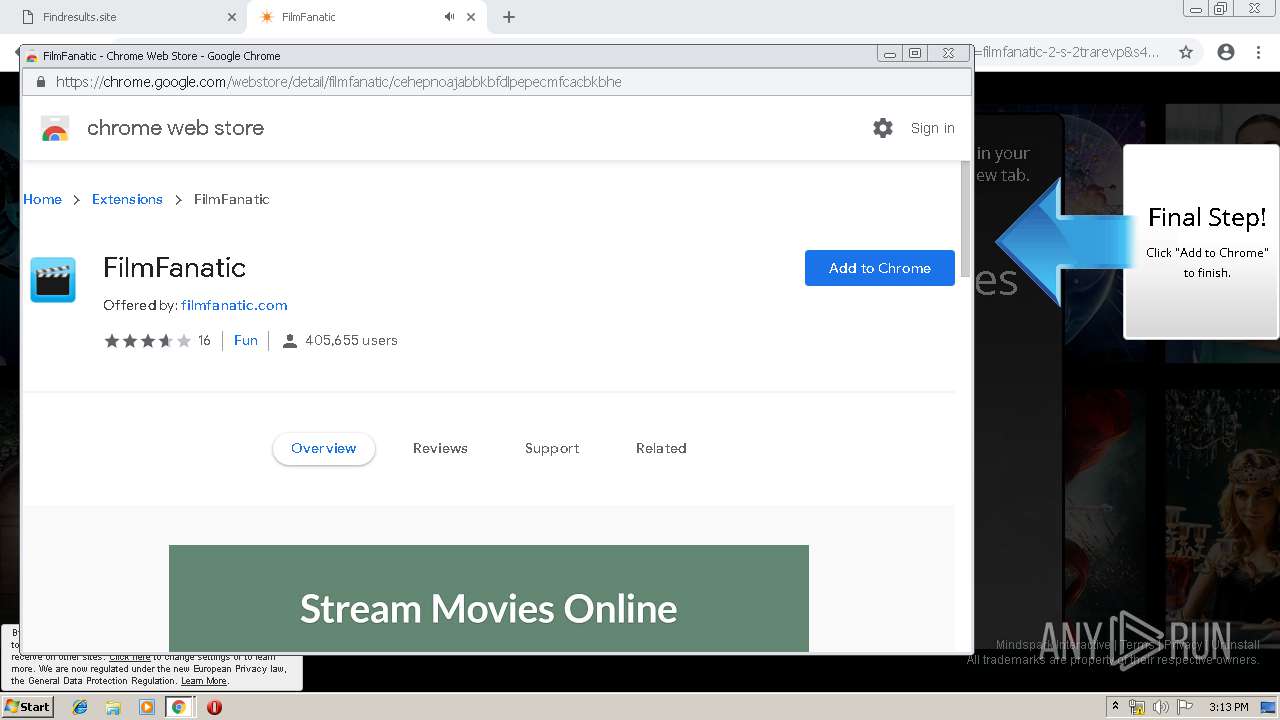
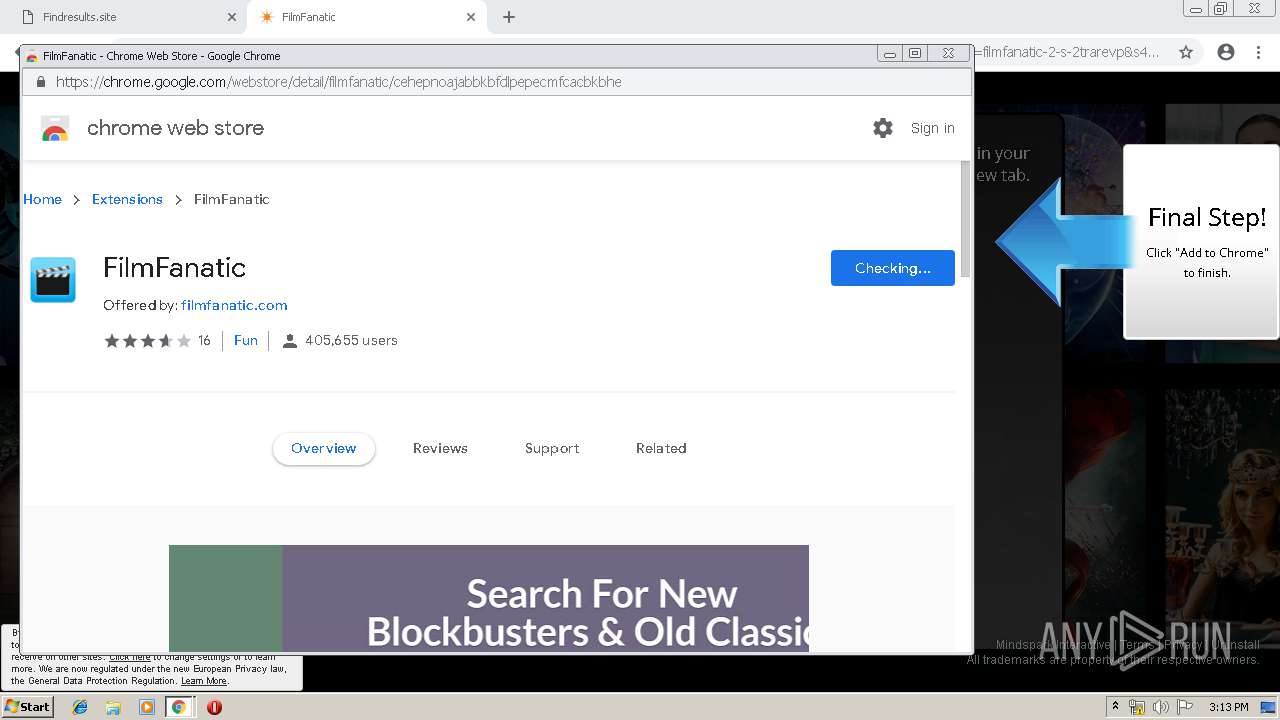
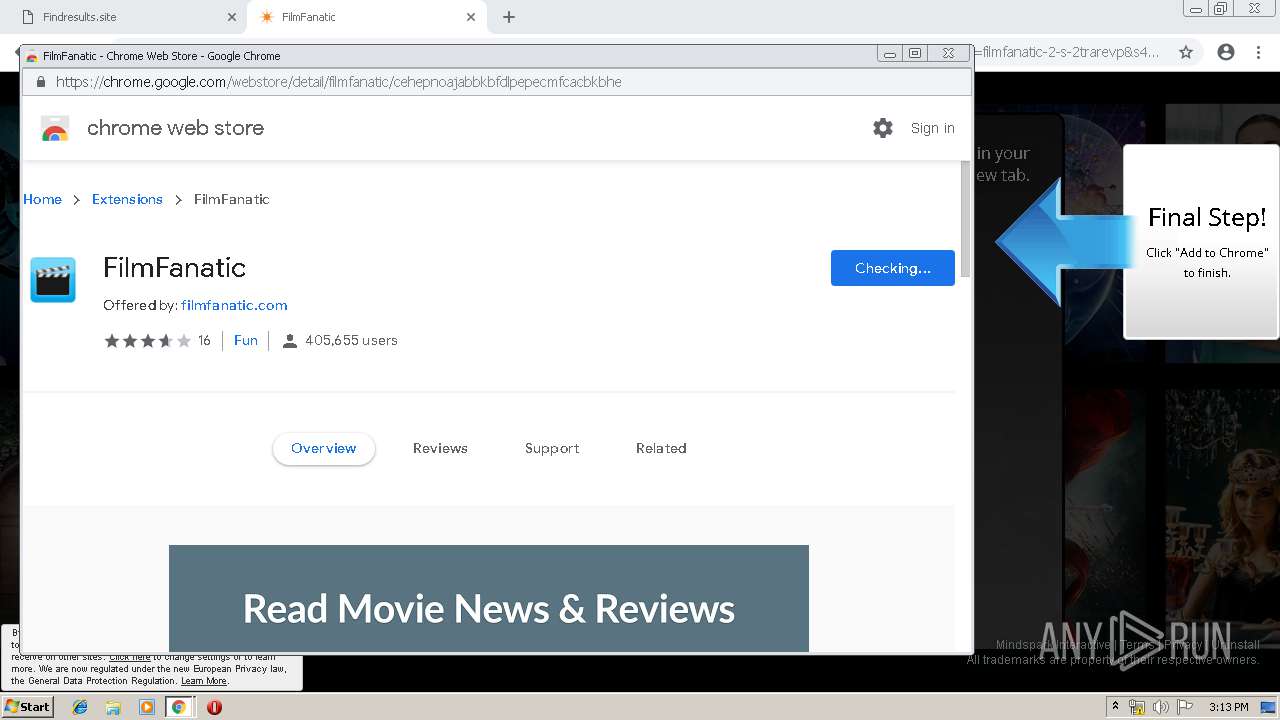
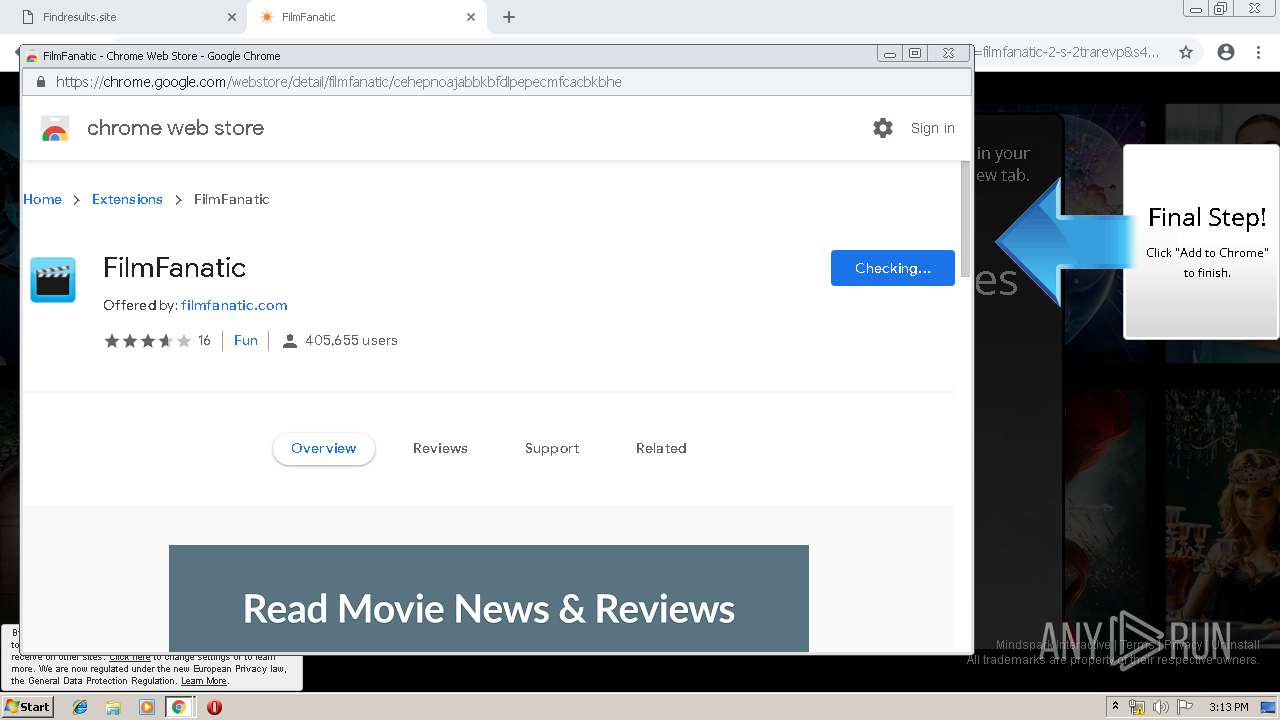
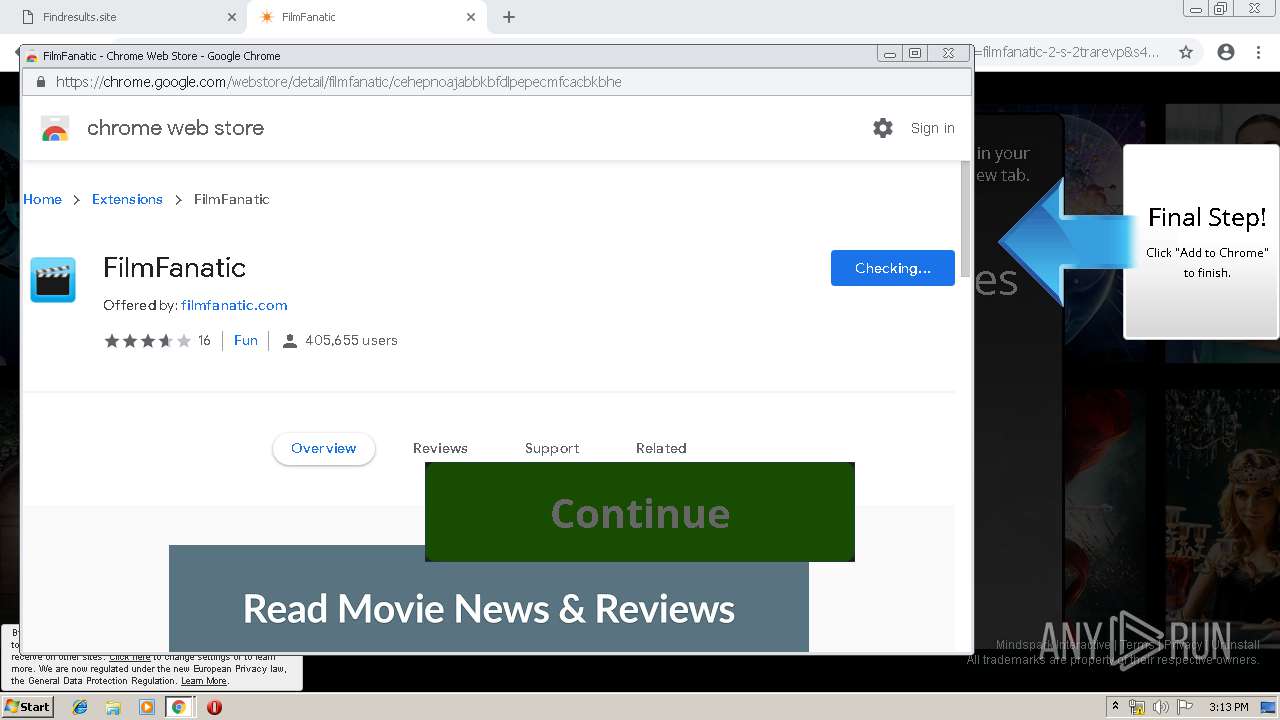
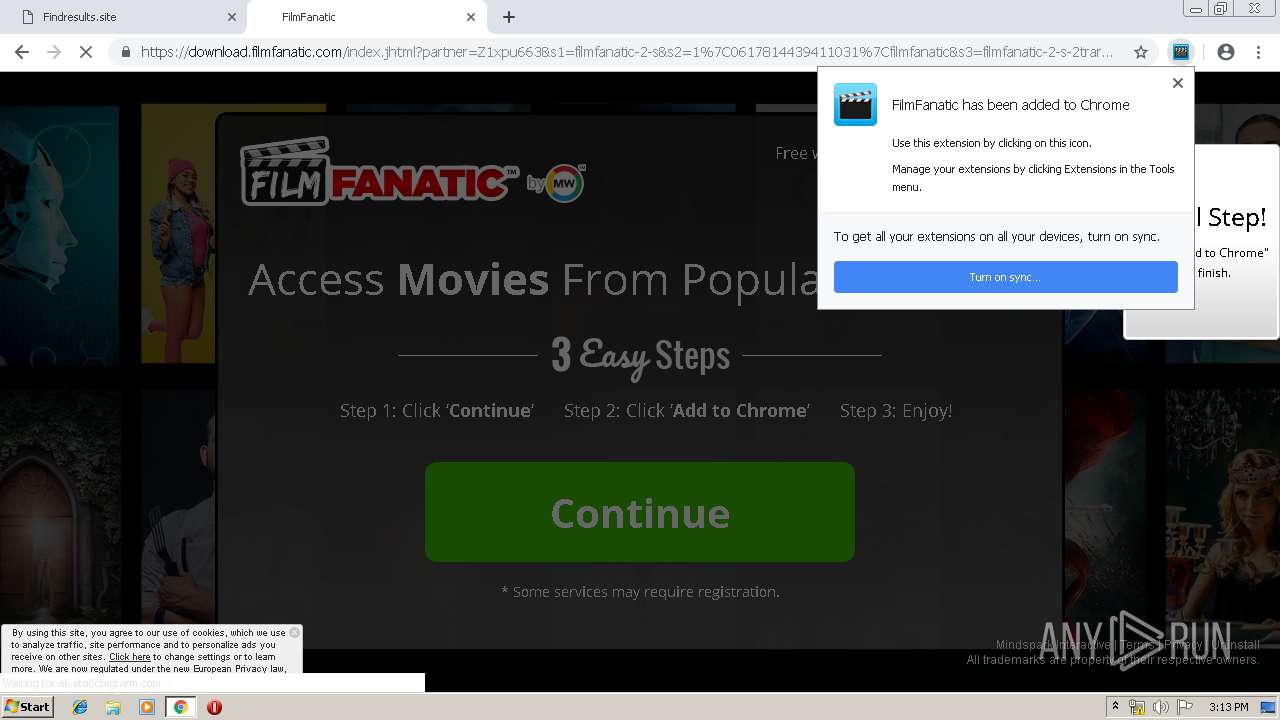
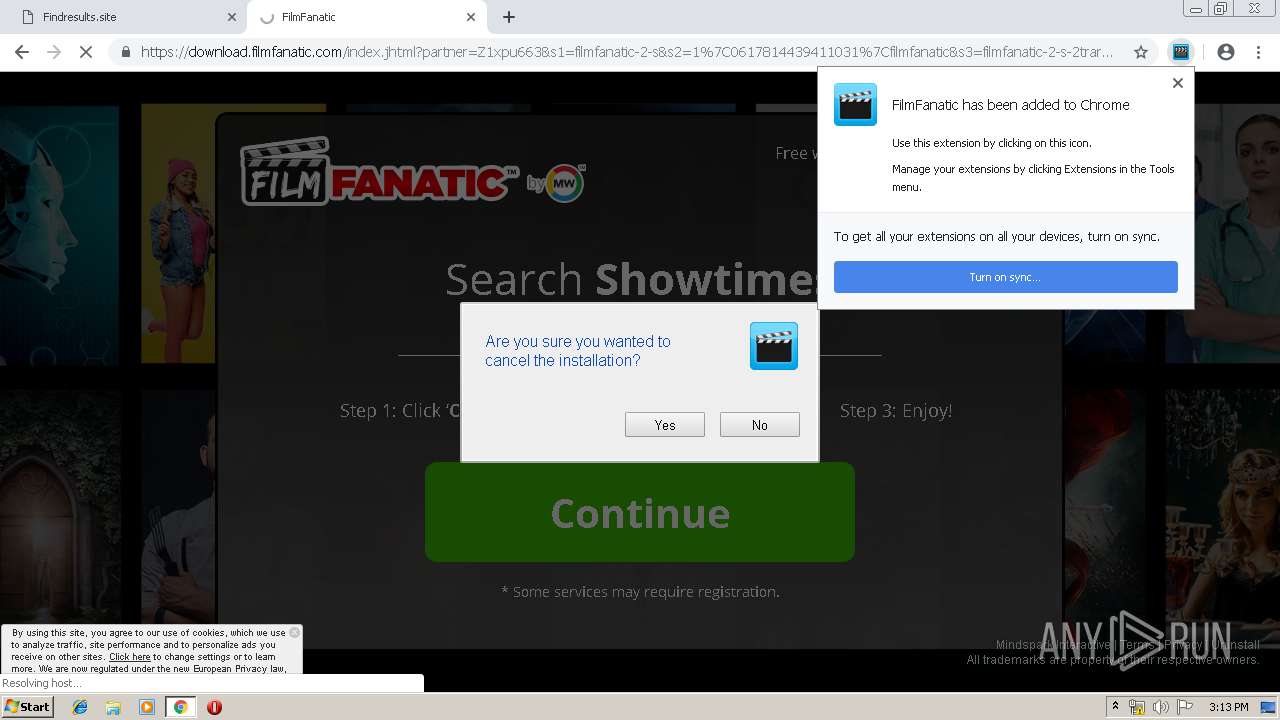
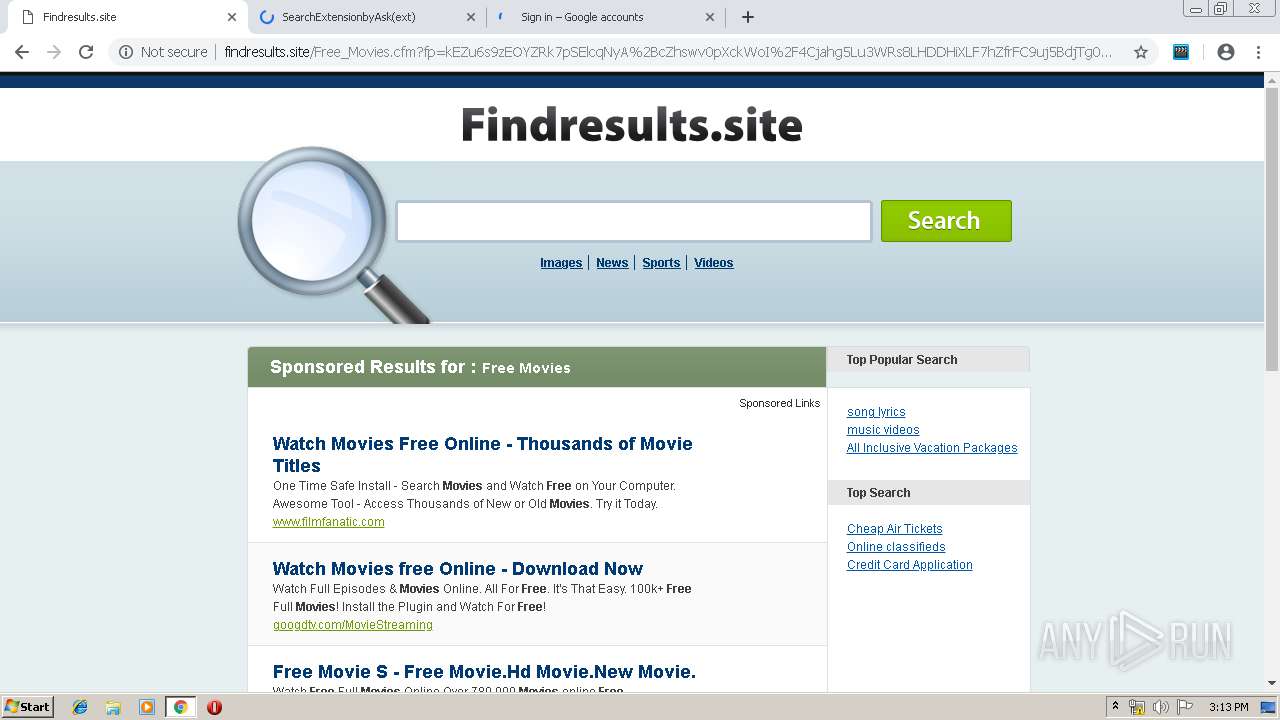
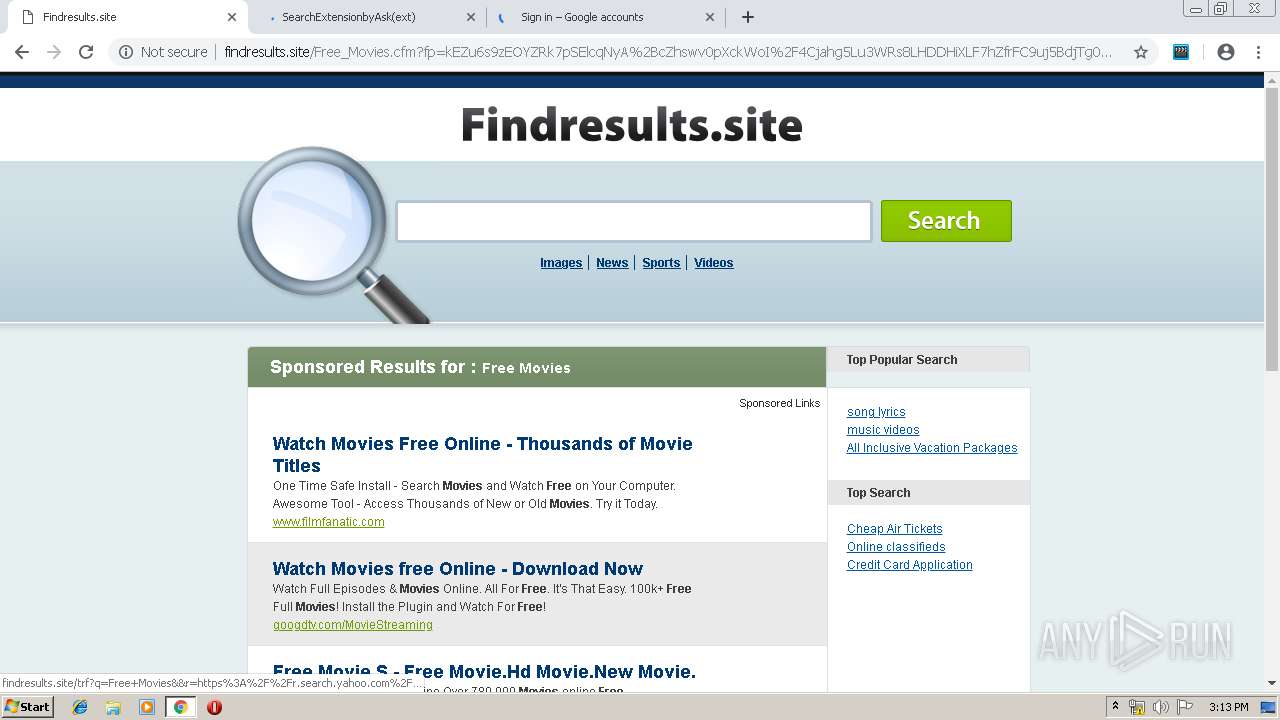
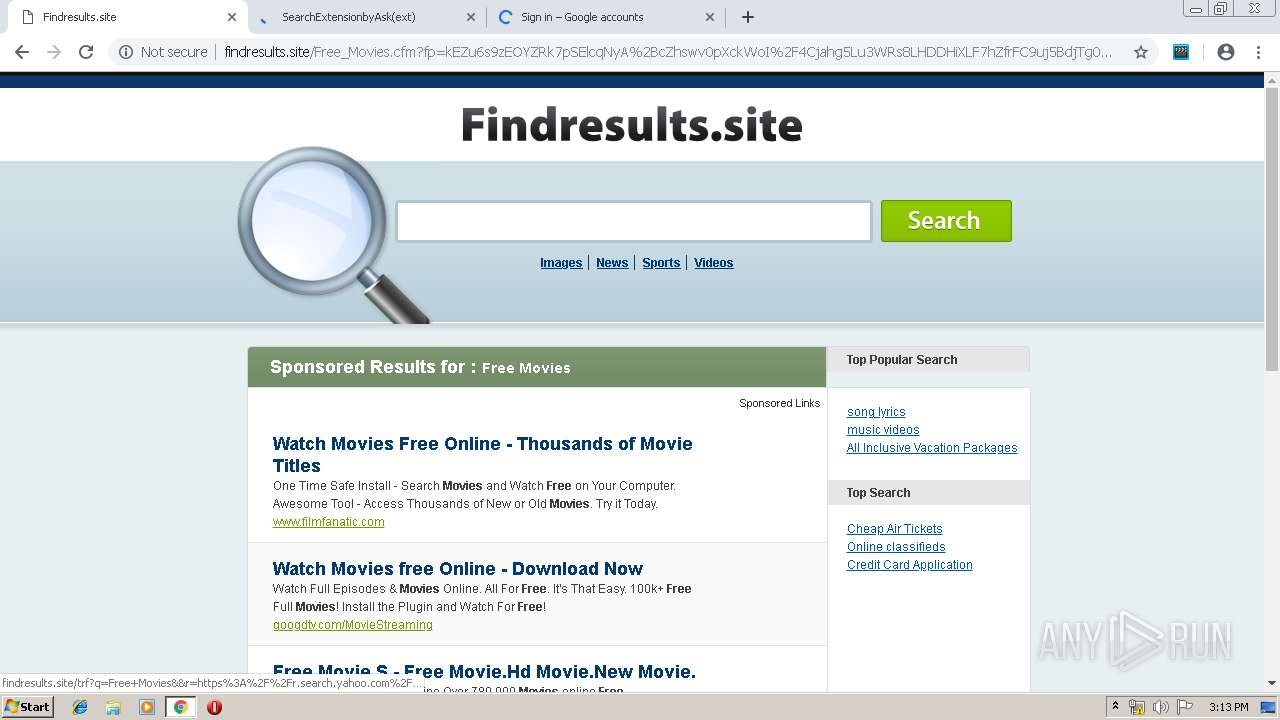
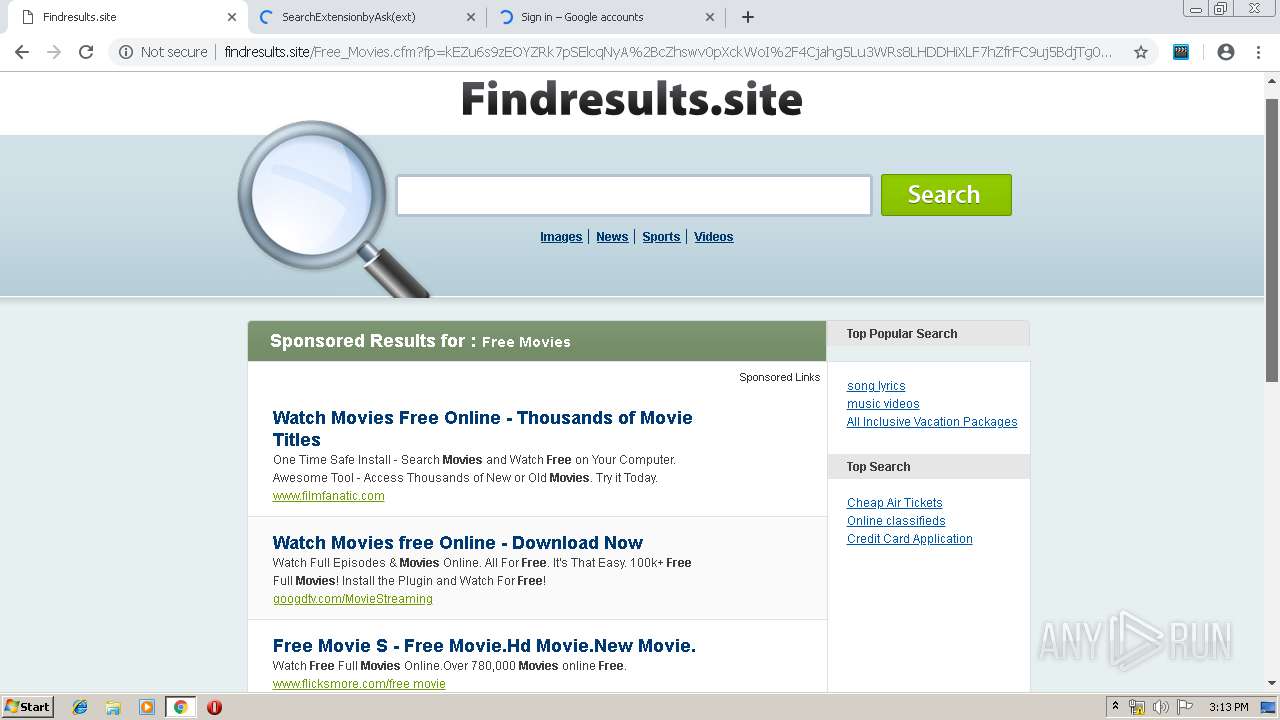
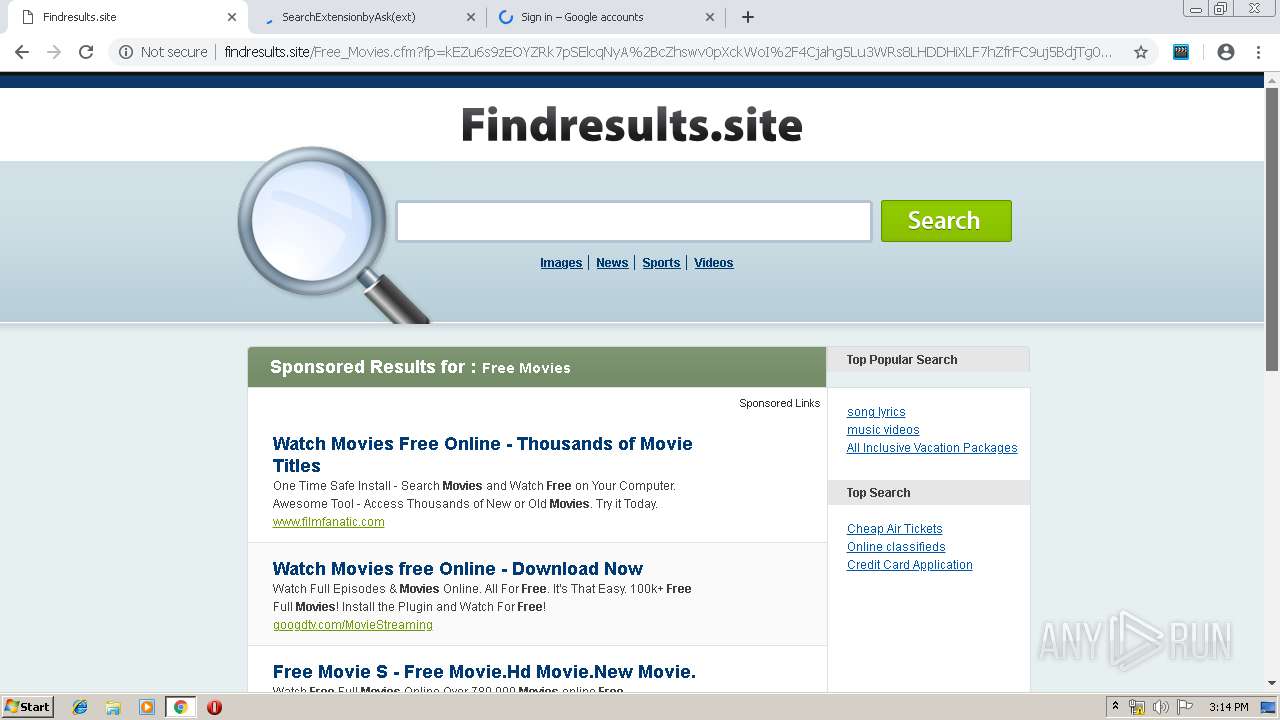
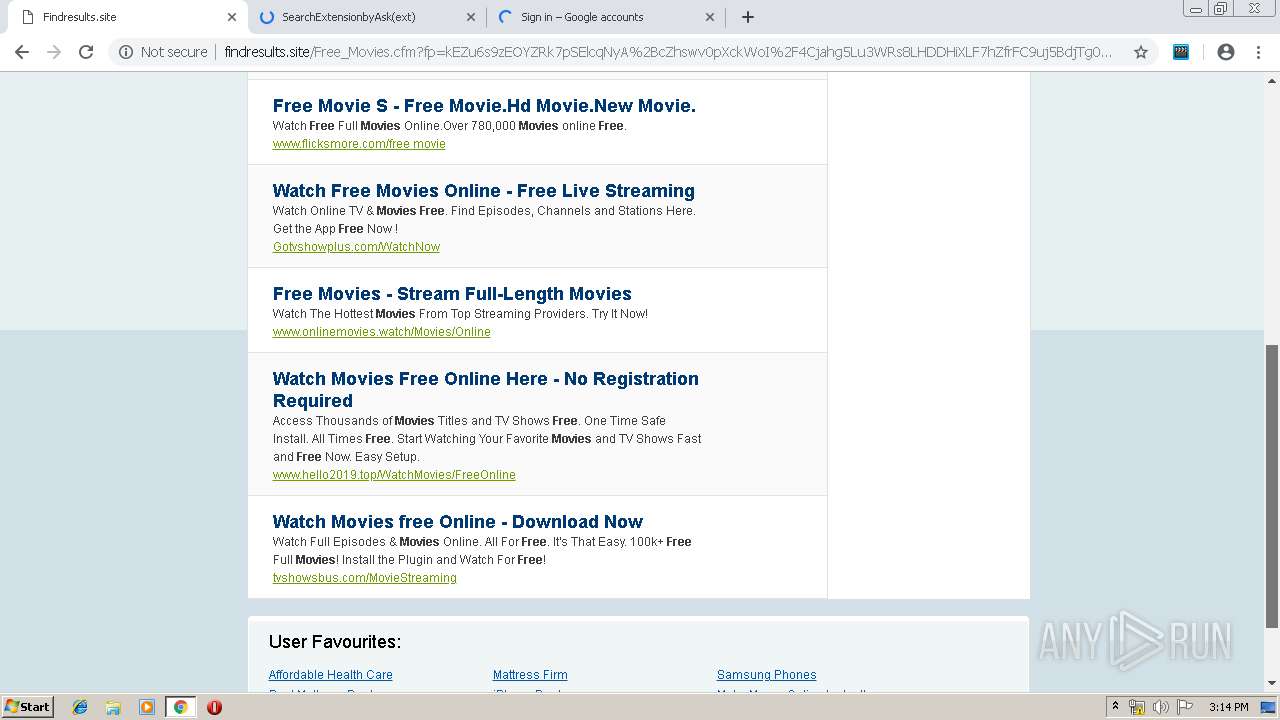
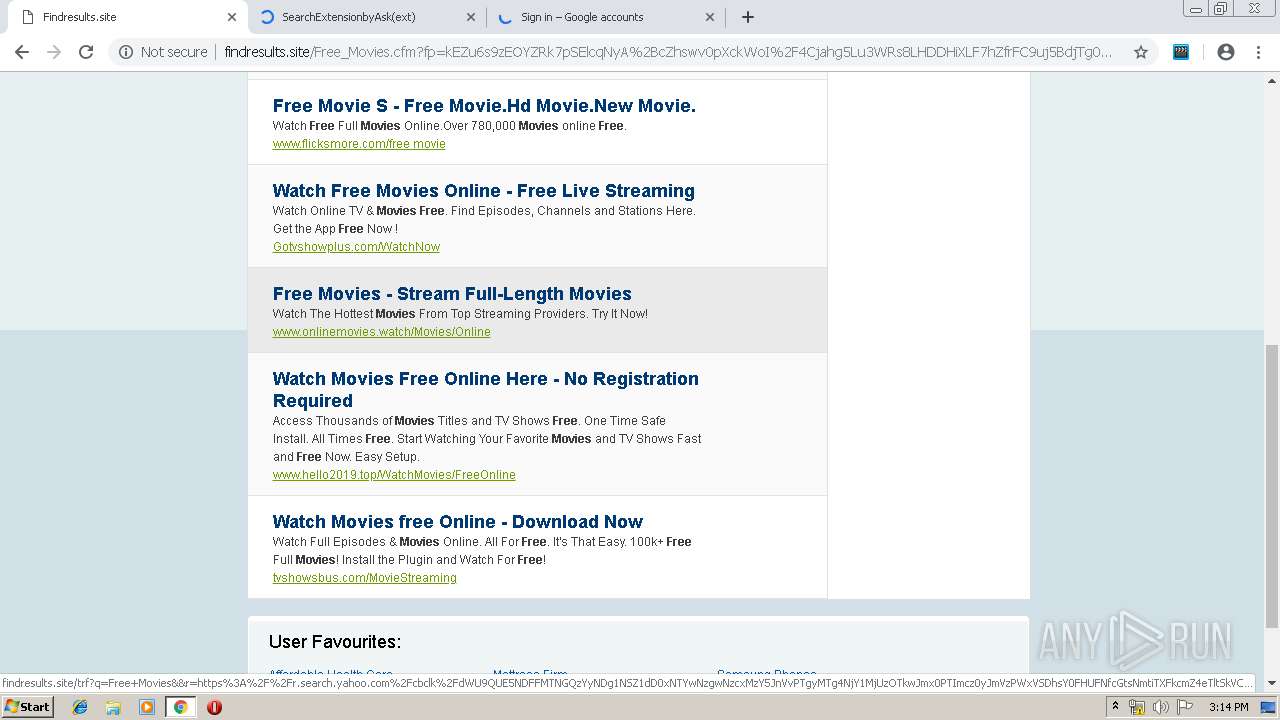
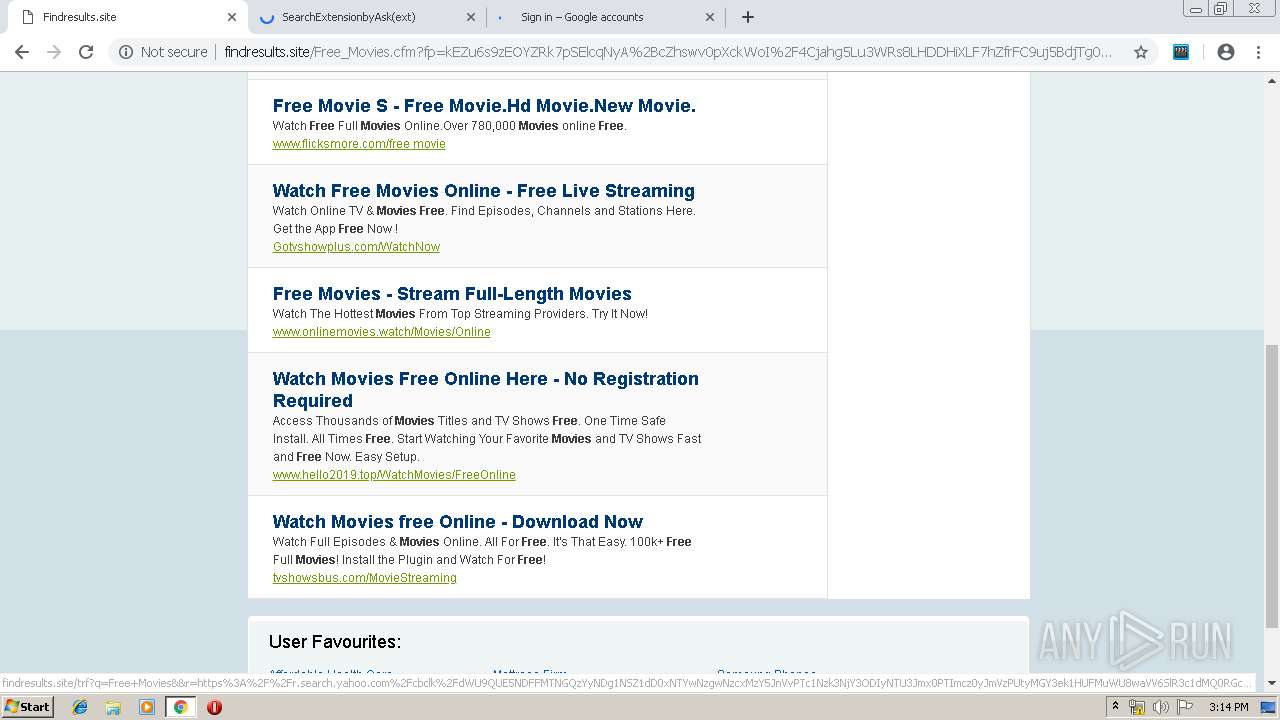
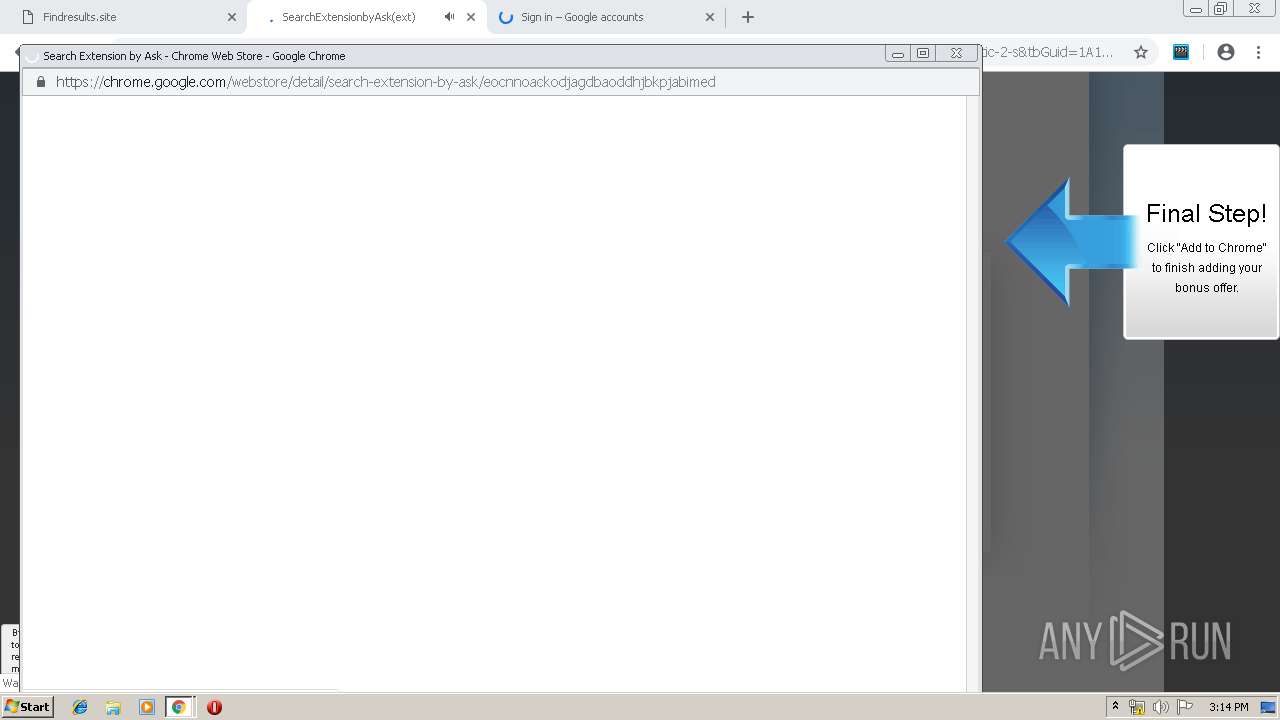
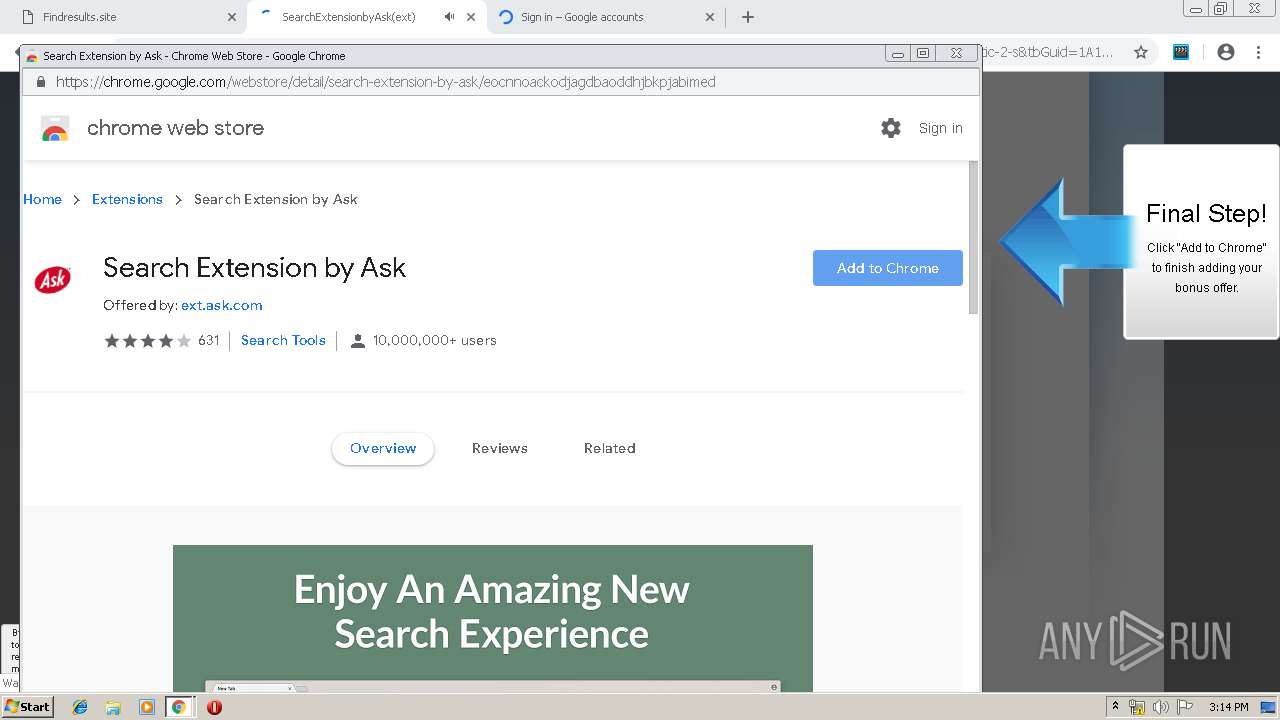
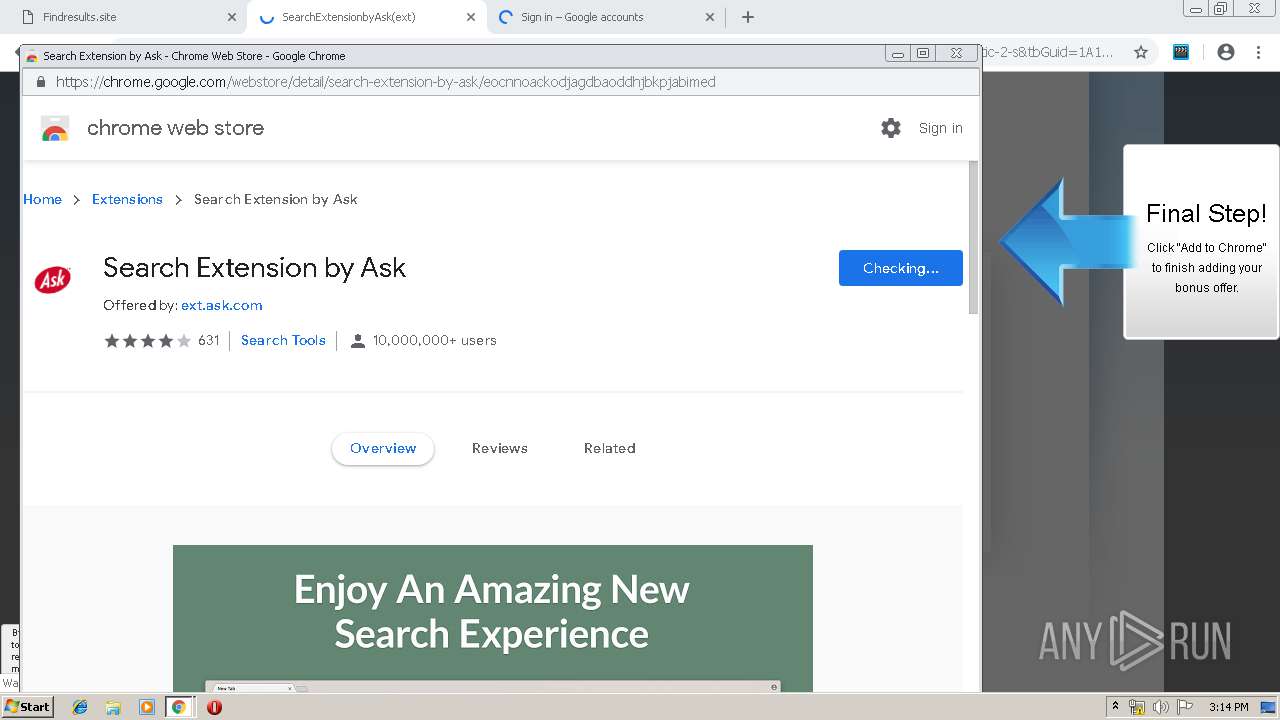
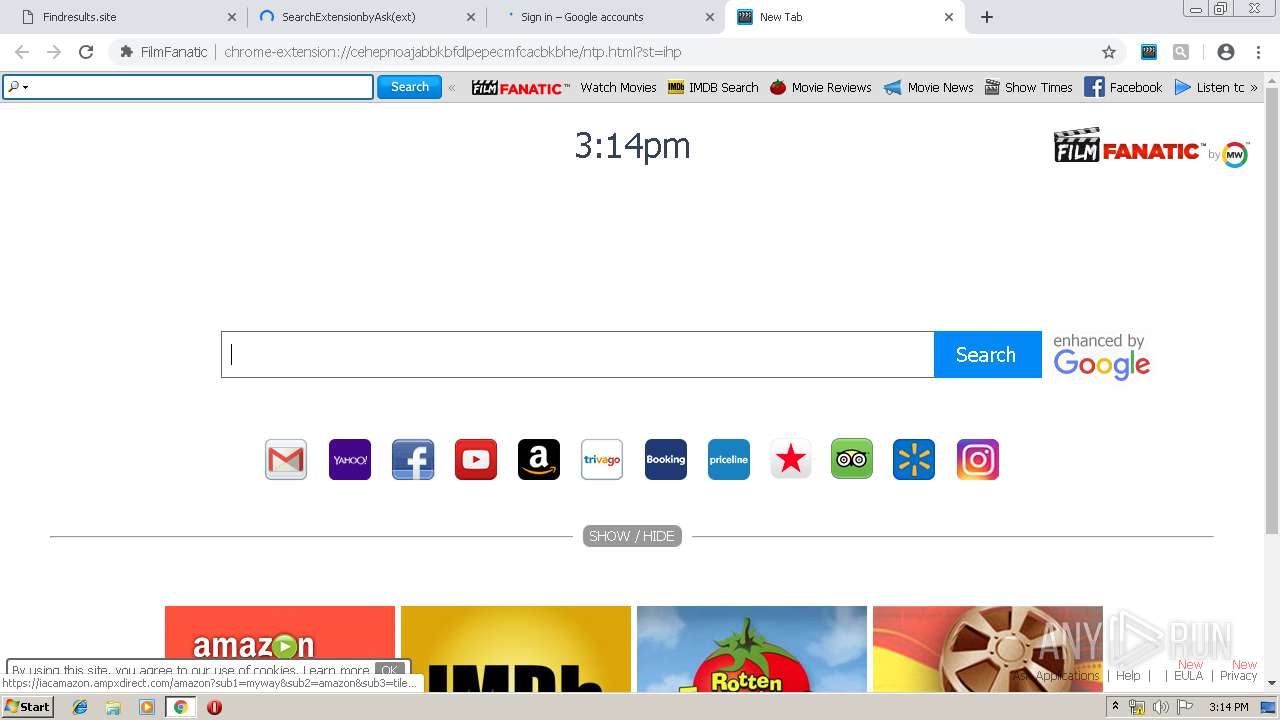
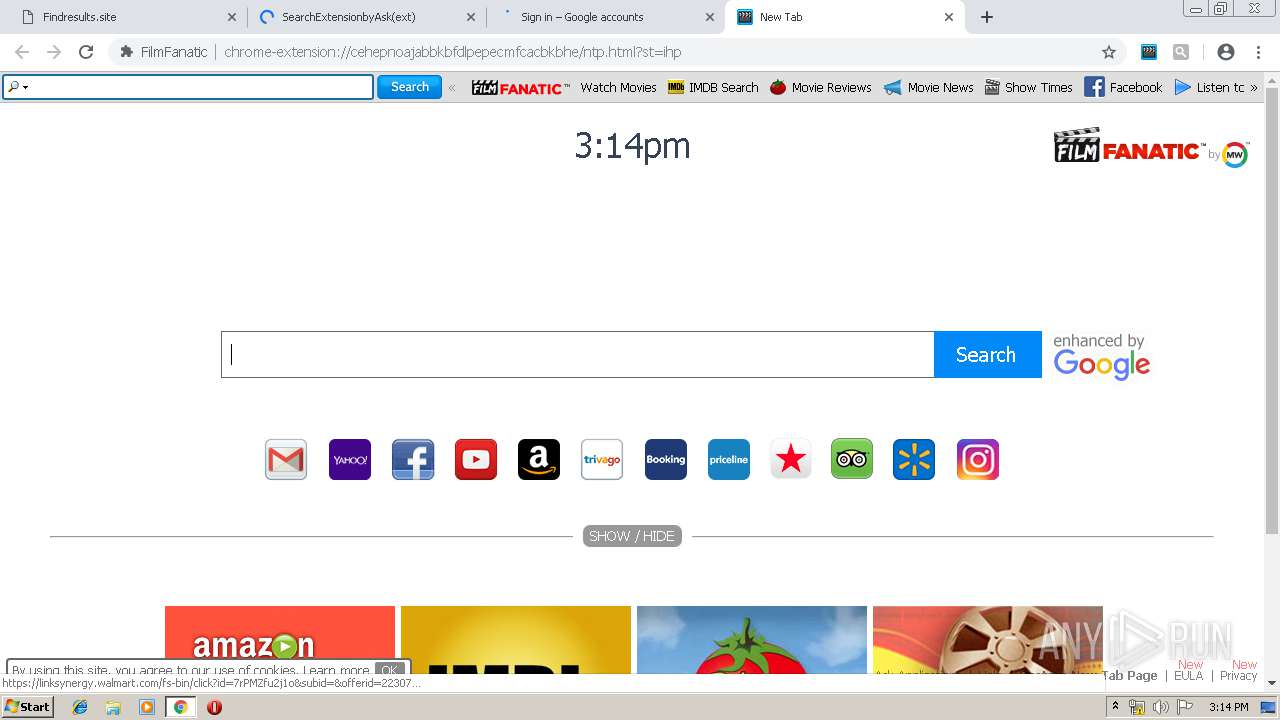
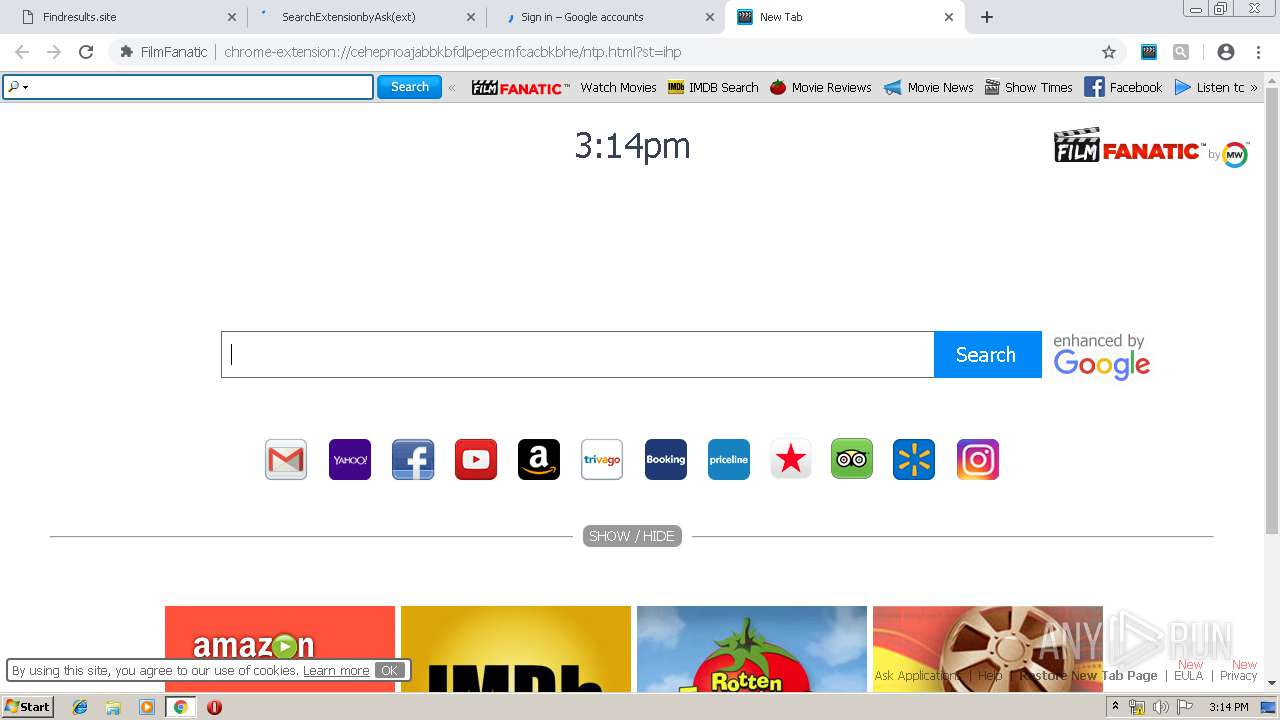
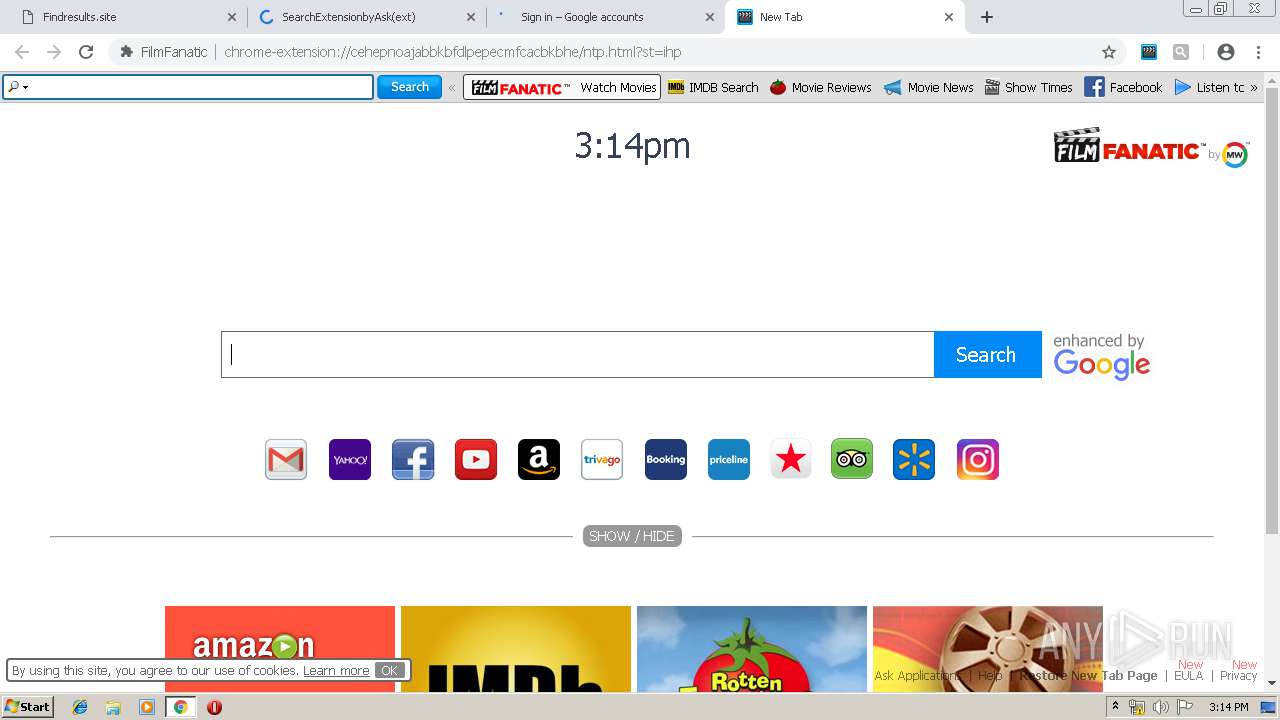
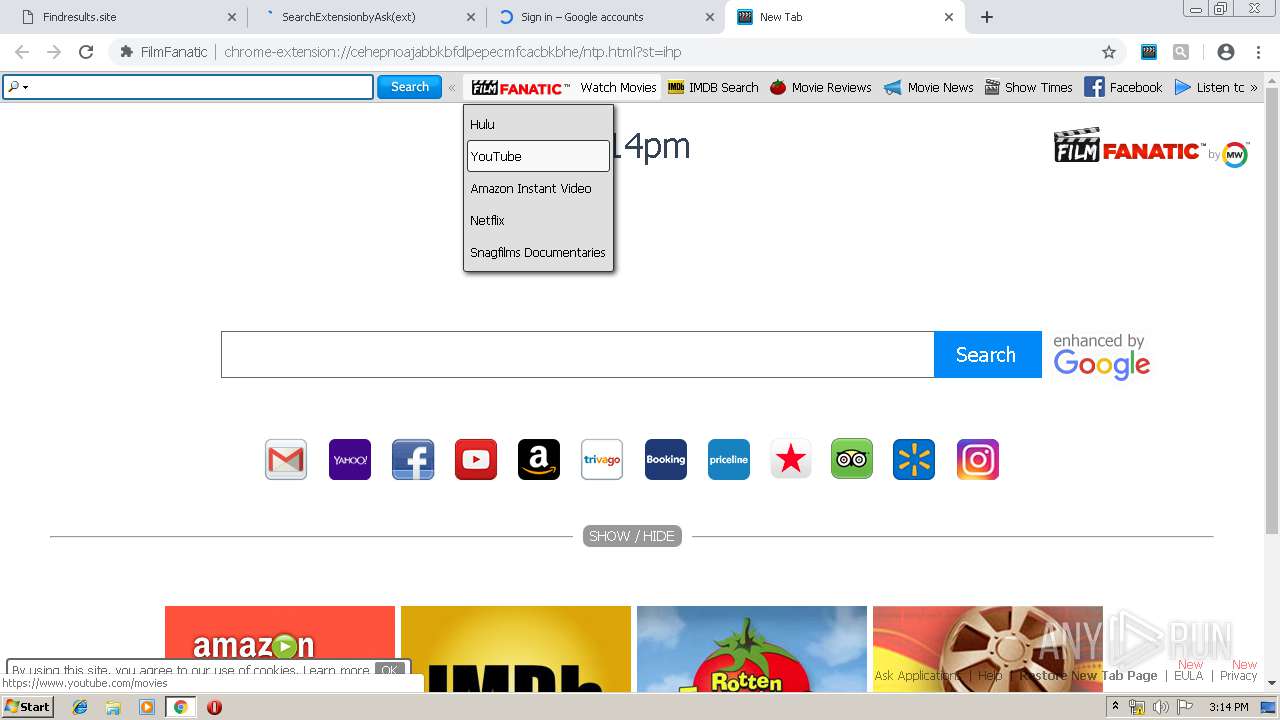
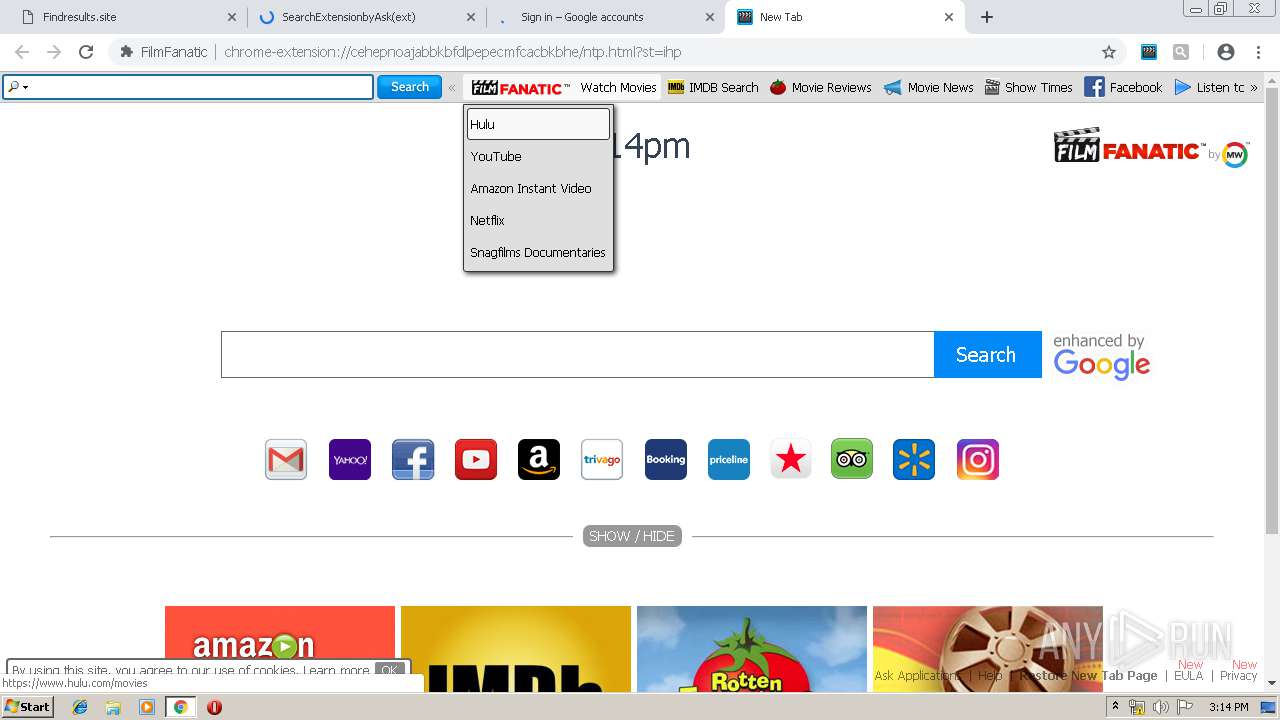
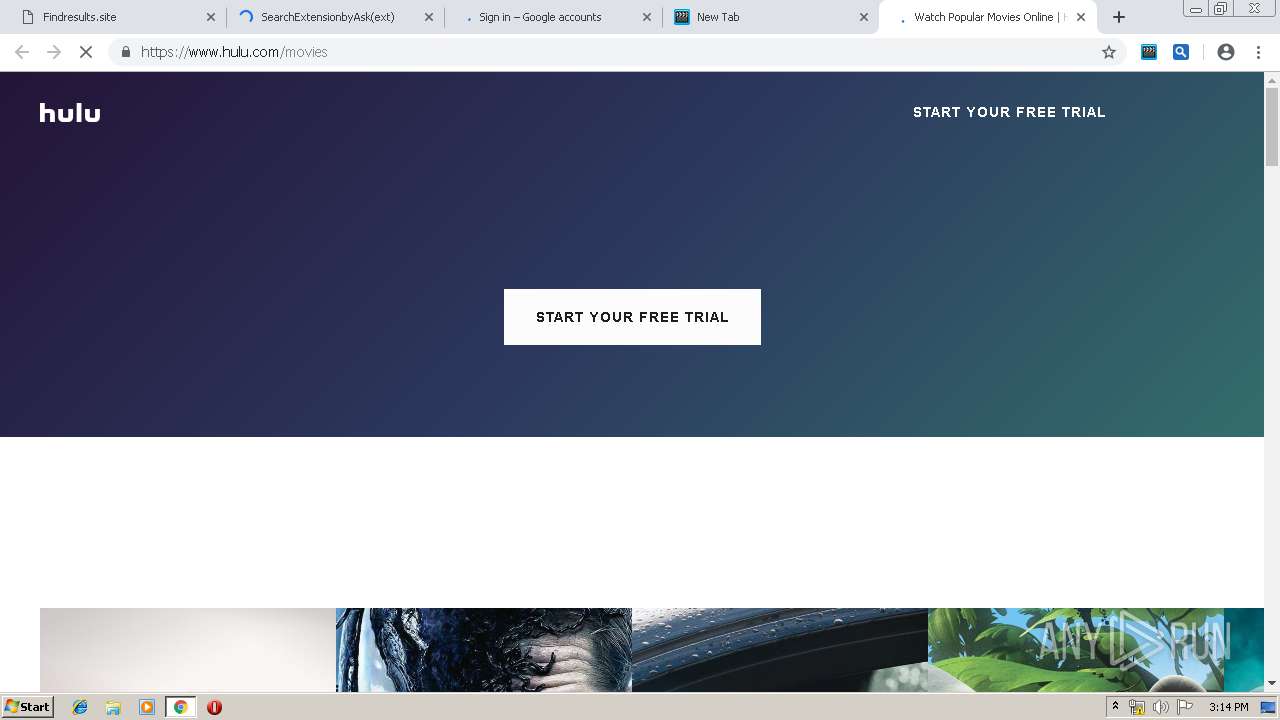
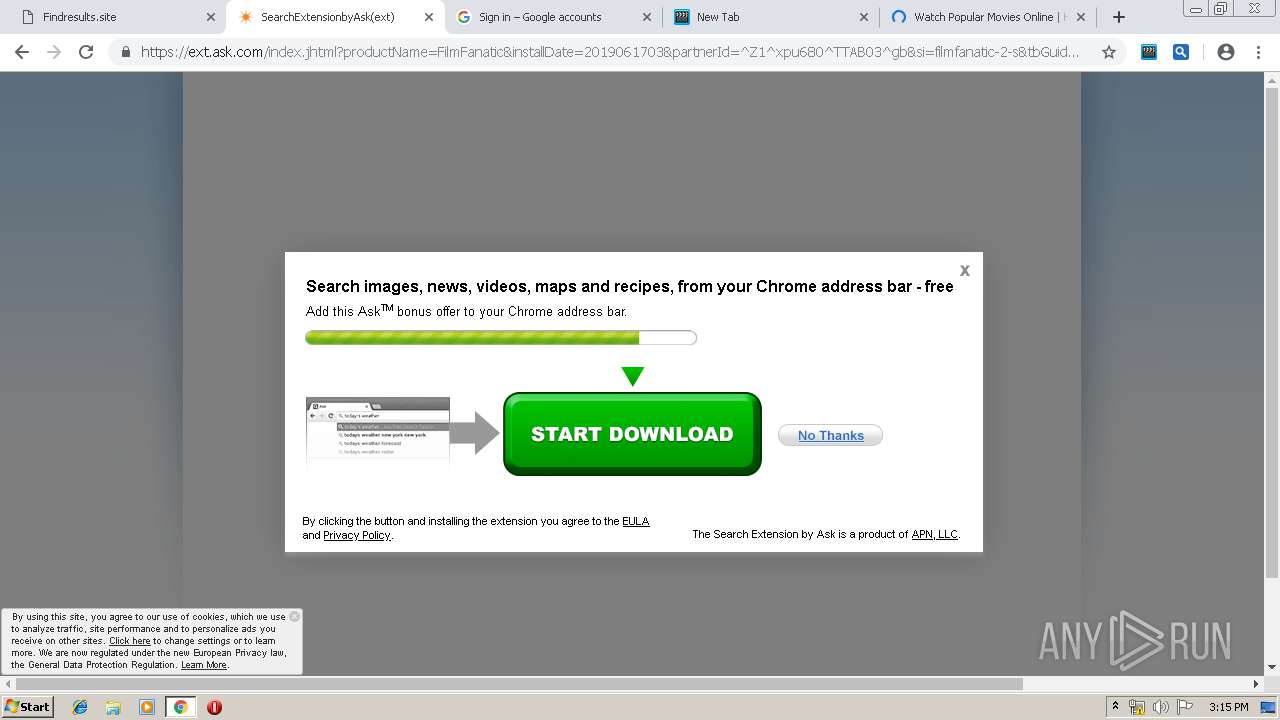
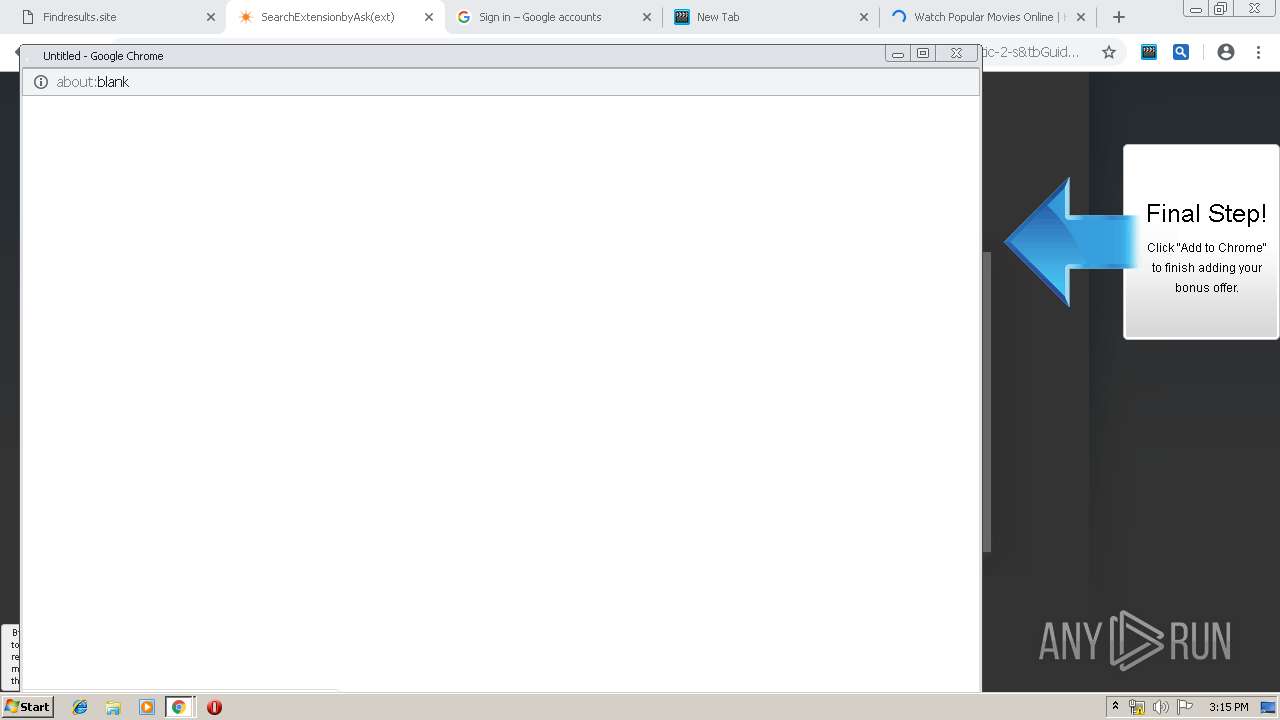
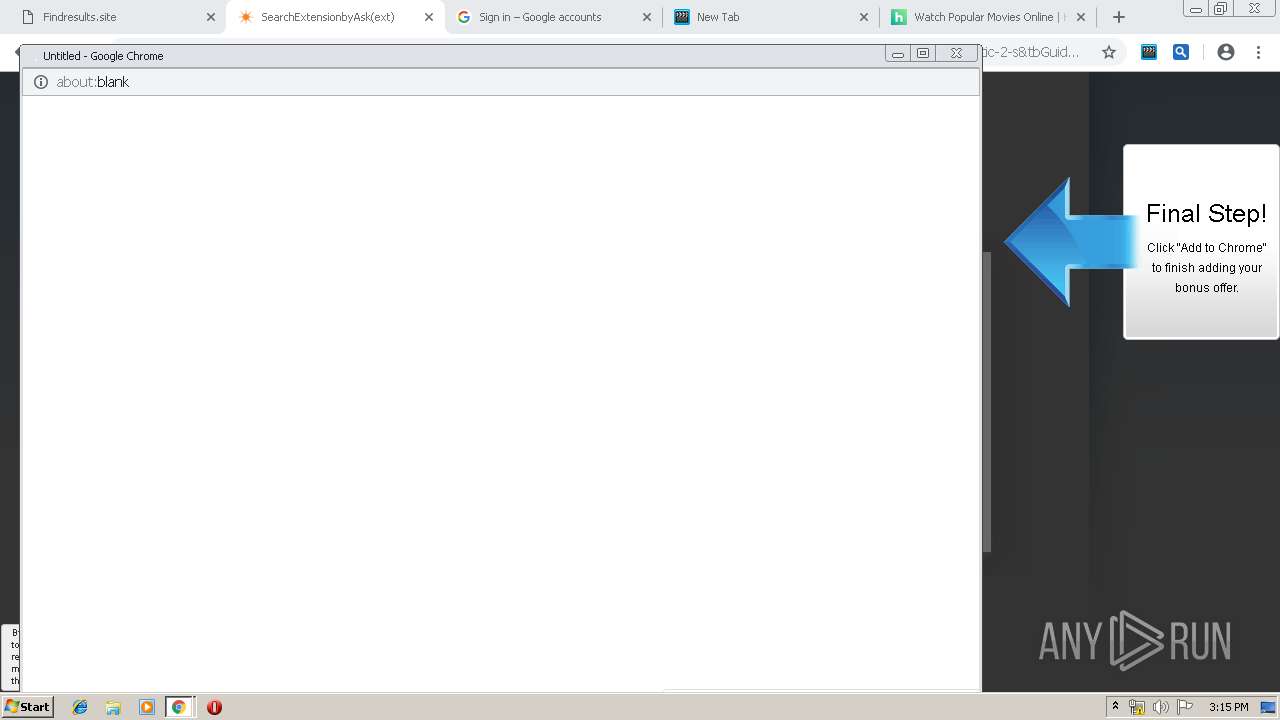
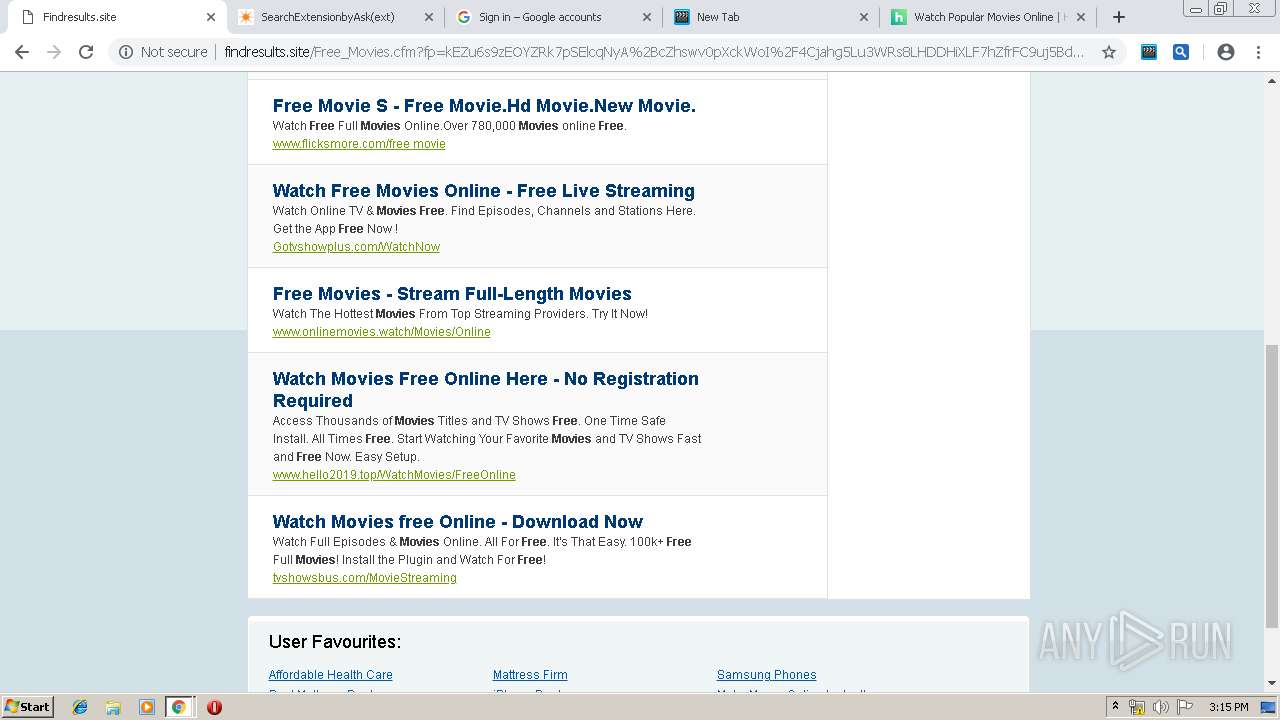
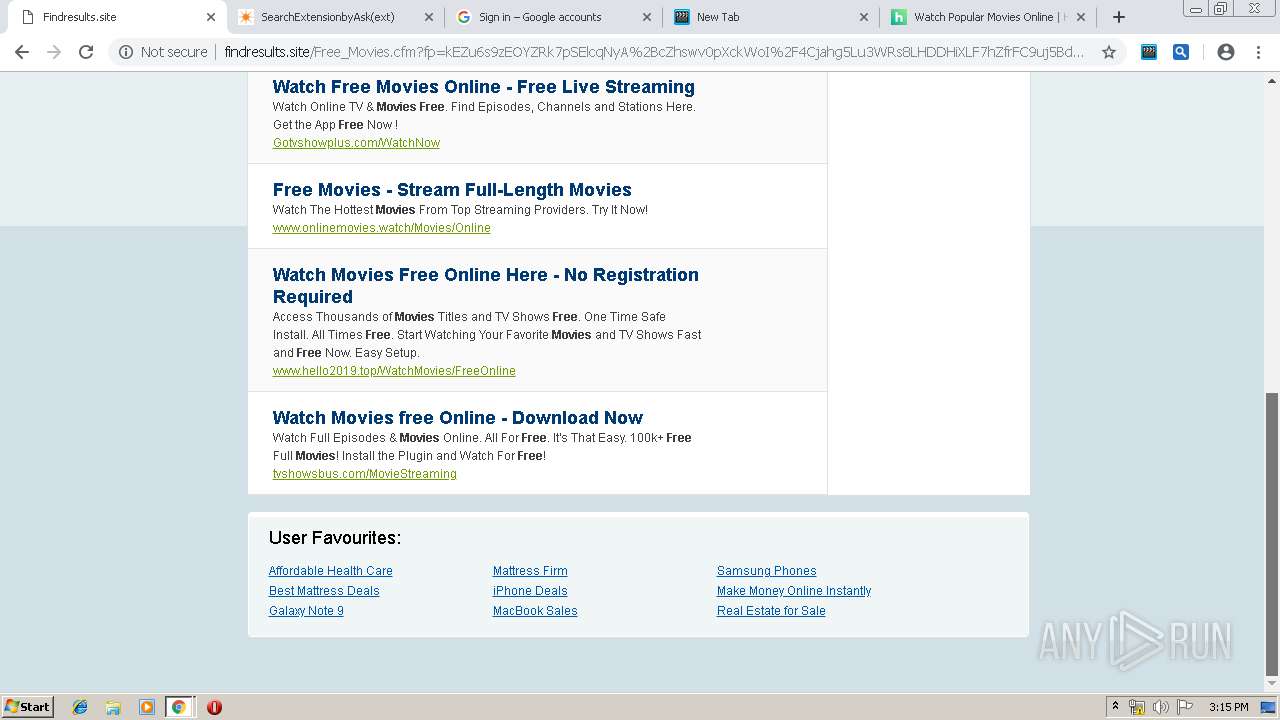
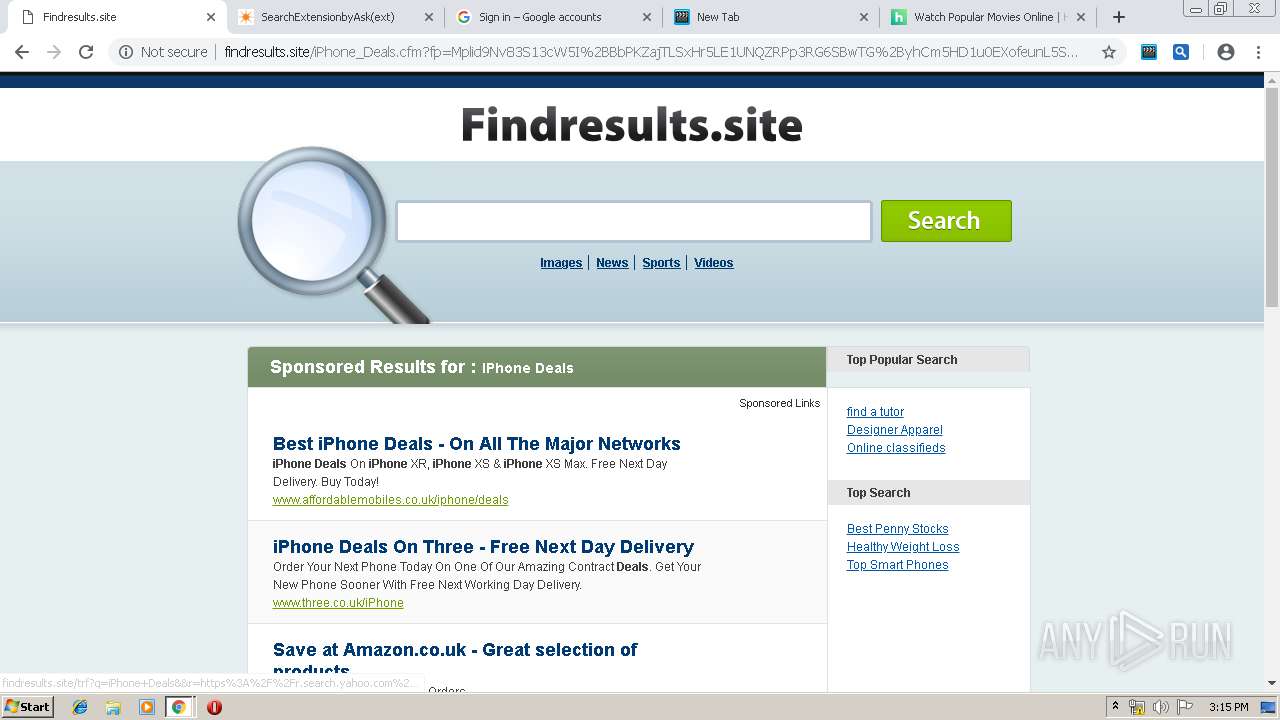
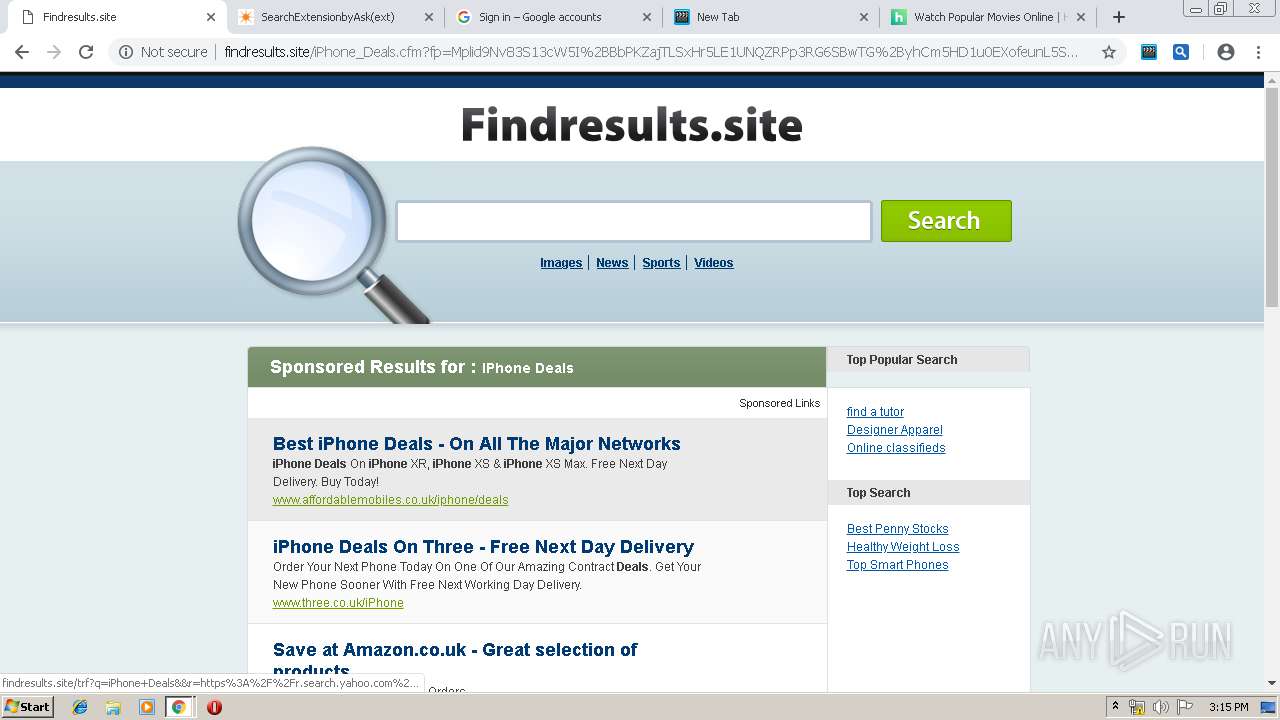
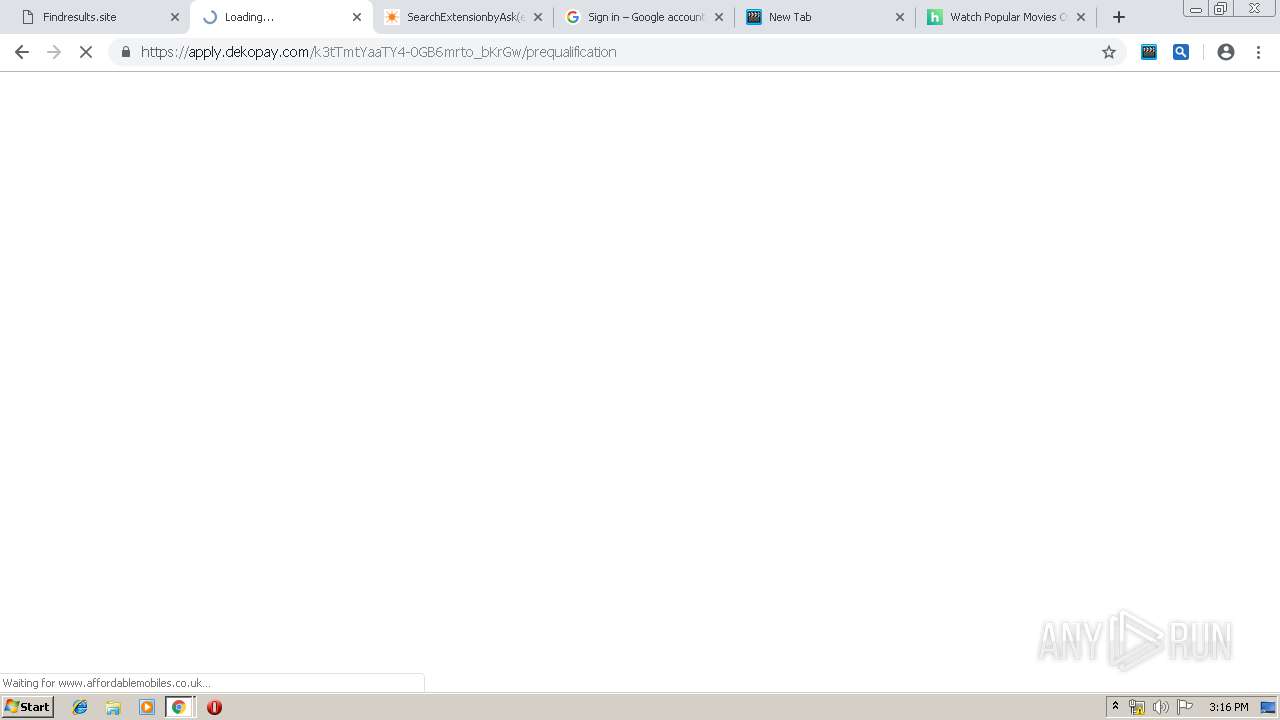
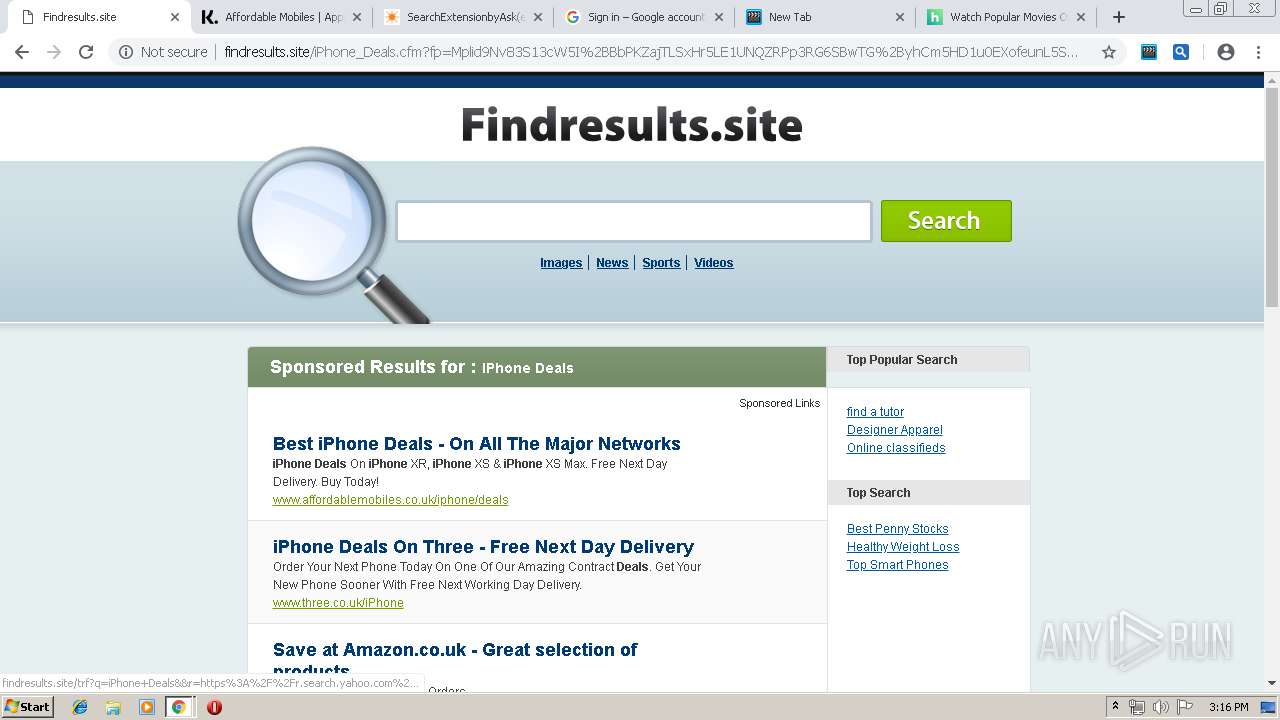
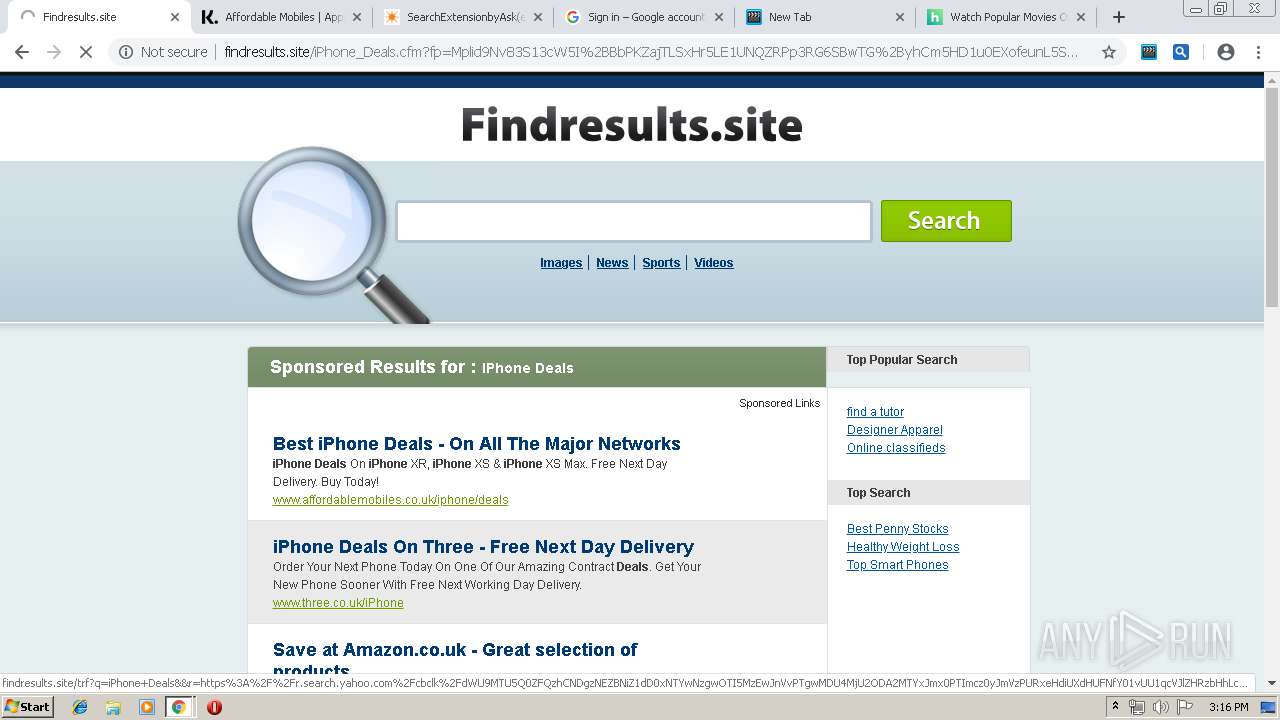
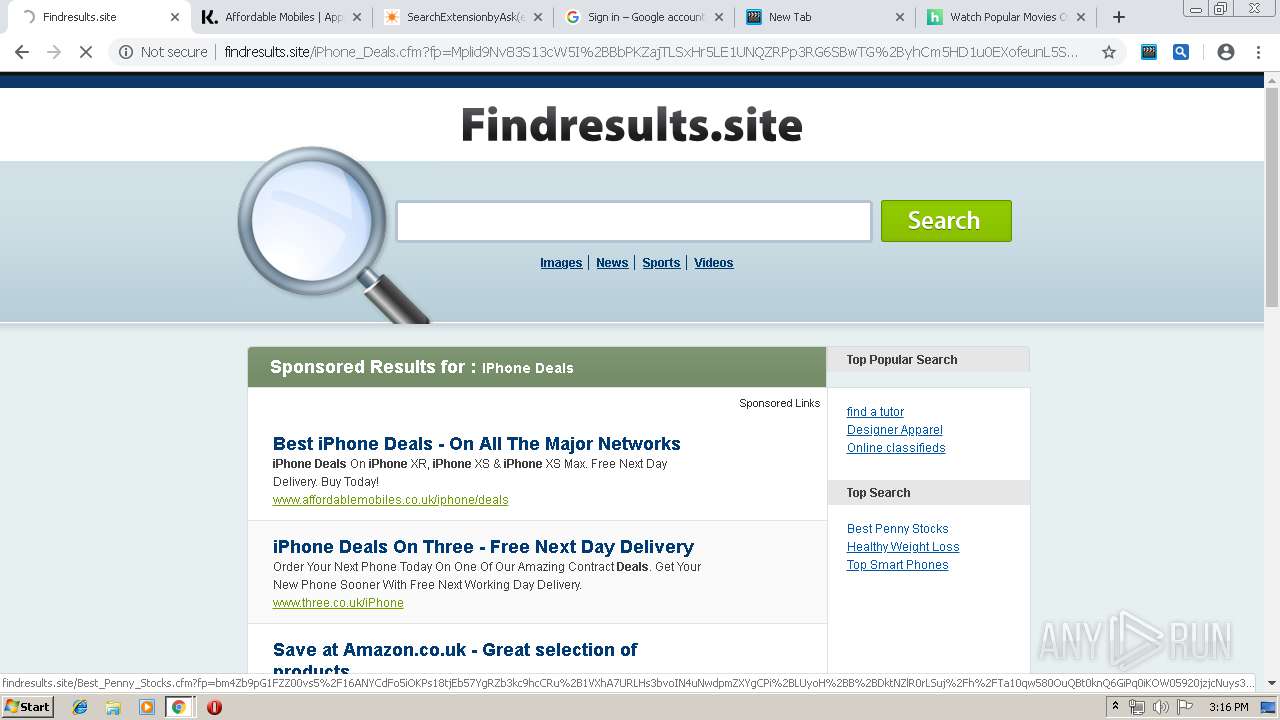
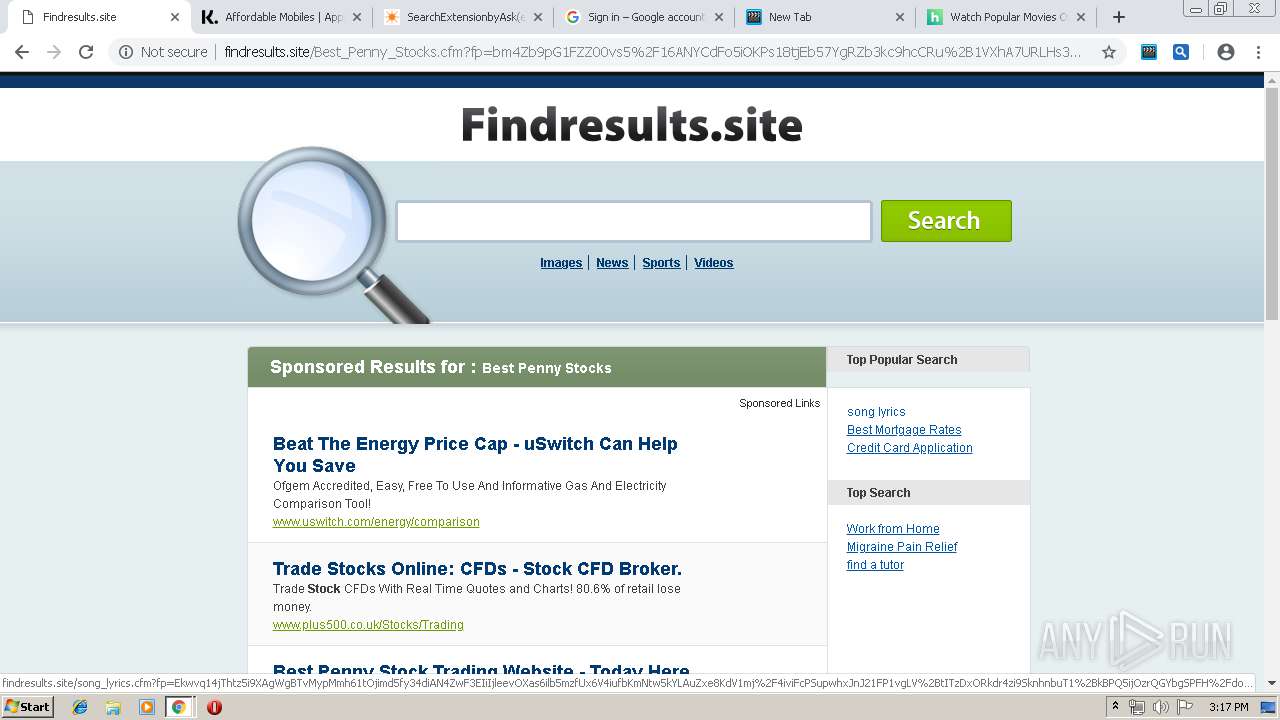
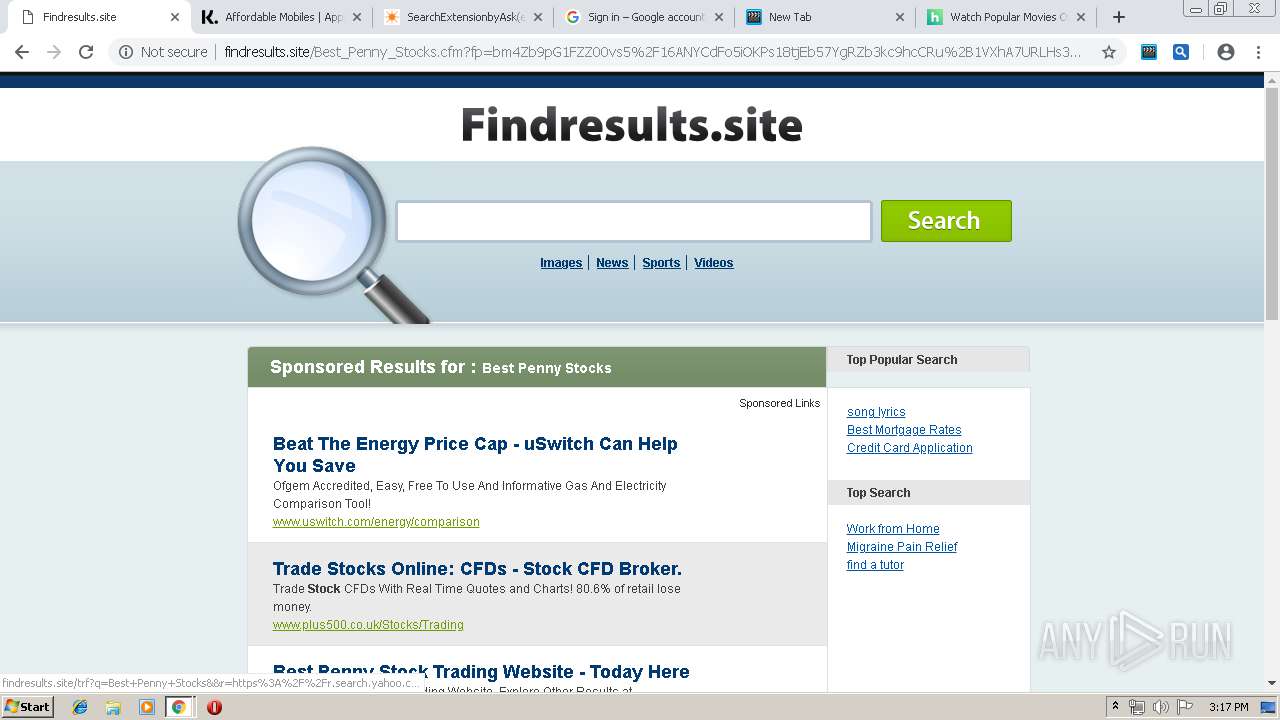
| URL: | http://findresults.site/ |
| Full analysis: | https://app.any.run/tasks/b4395ff0-bb24-4d2a-ac06-4fa71d1e8852 |
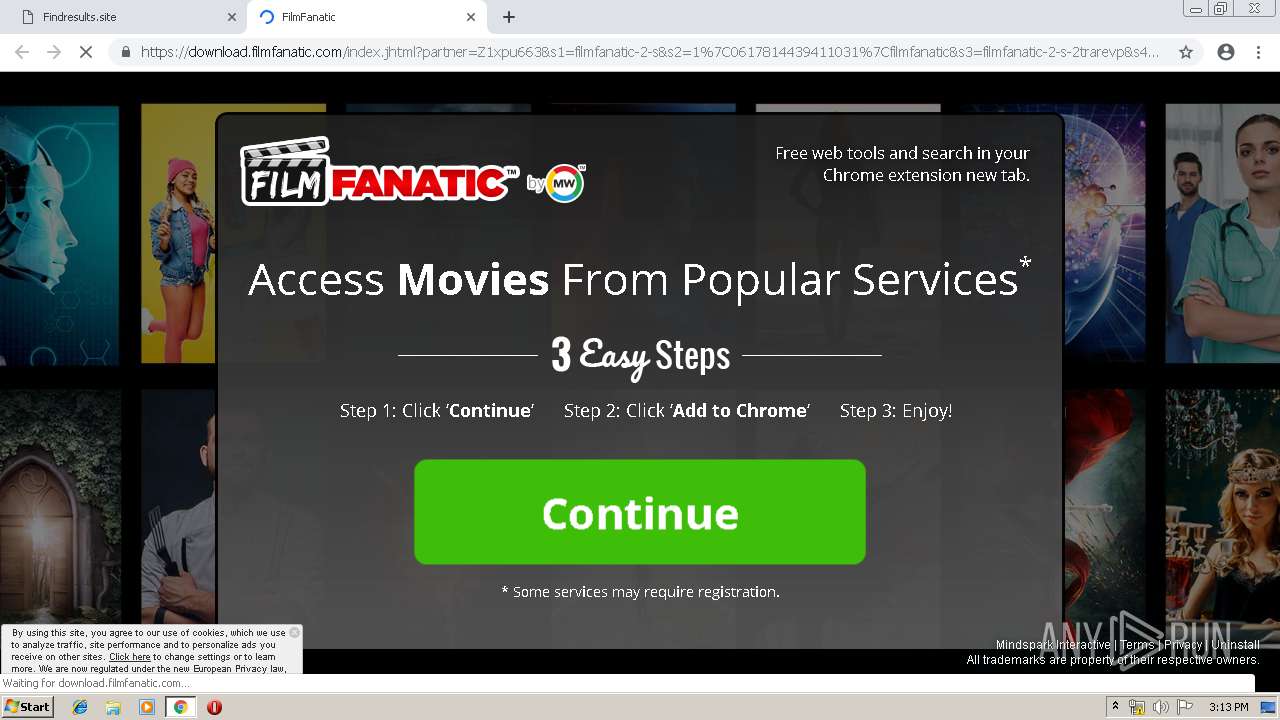
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2019, 14:11:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1A8F43C29F828FAAE57B3FC4A983FA81 |
| SHA1: | ECD4F183FE602AEC350901CB8E49EEBFCF500B70 |
| SHA256: | 7C07345F2D2E423B4A64B7713736AA307BA05F10DA1B9DC3C925E4B20AD50257 |
| SSDEEP: | 3:N1KYaXAWTOKn:CYaQWTOKn |
MALICIOUS
No malicious indicators.SUSPICIOUS
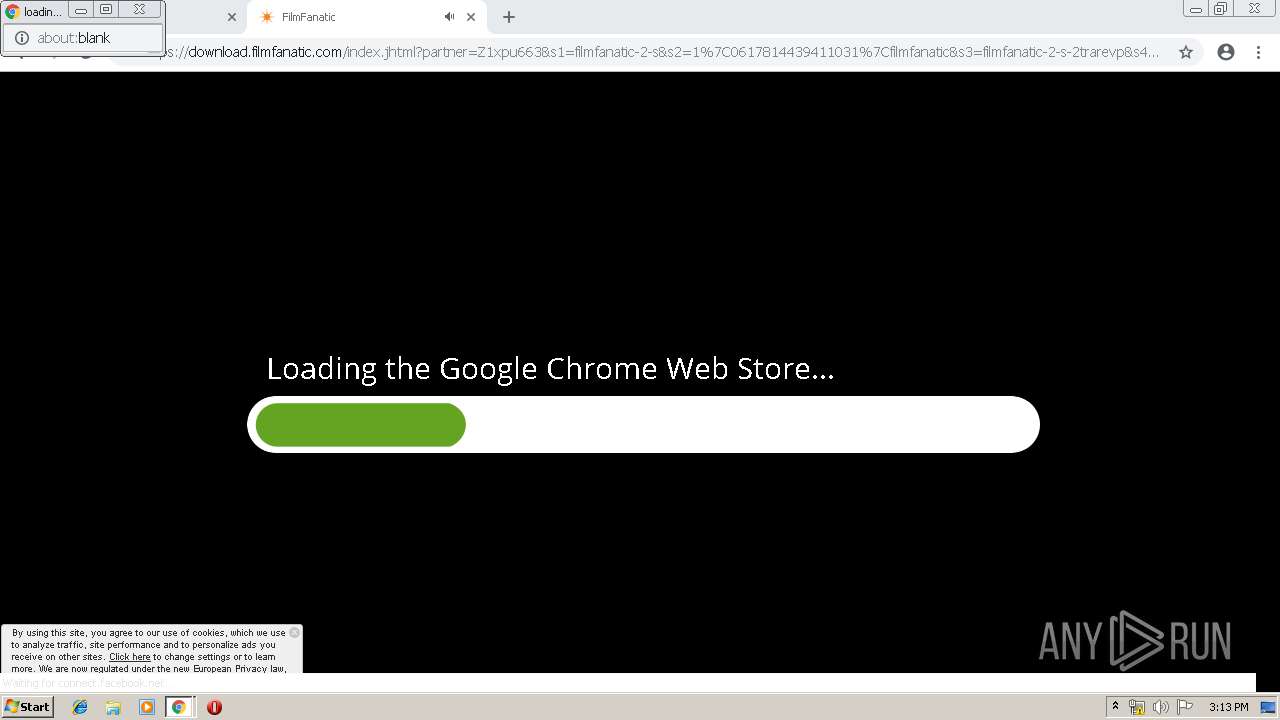
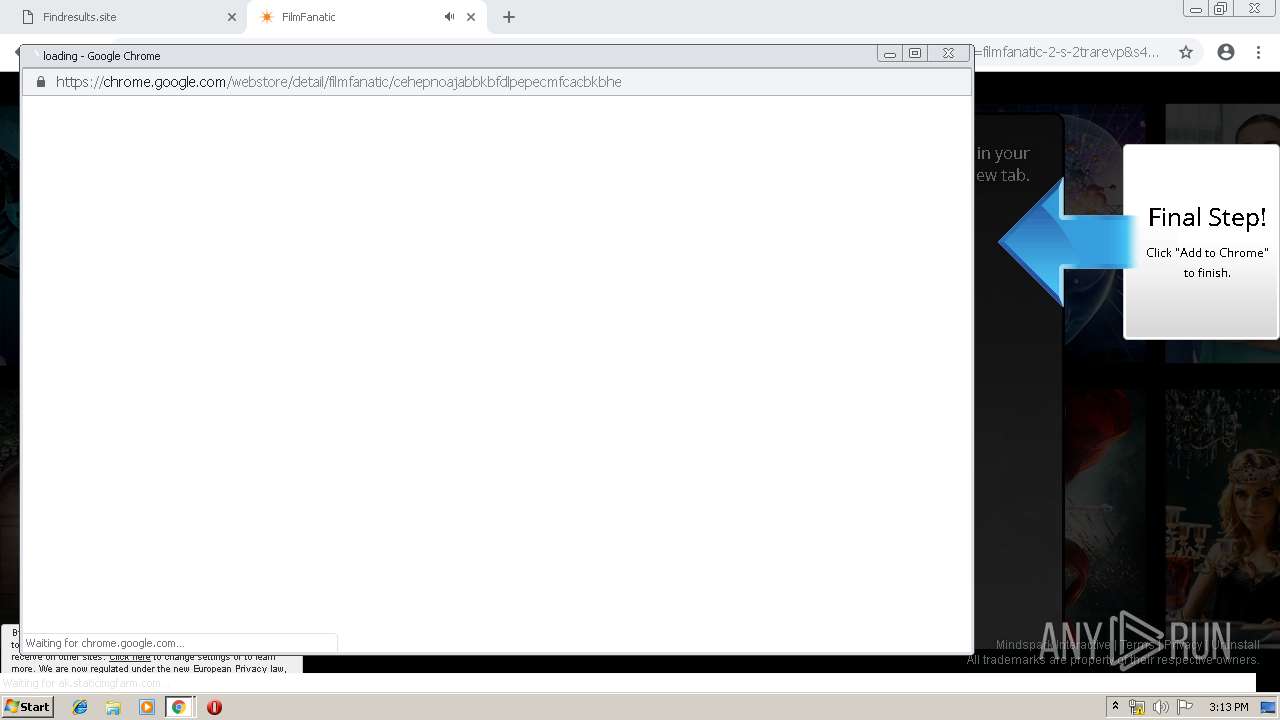
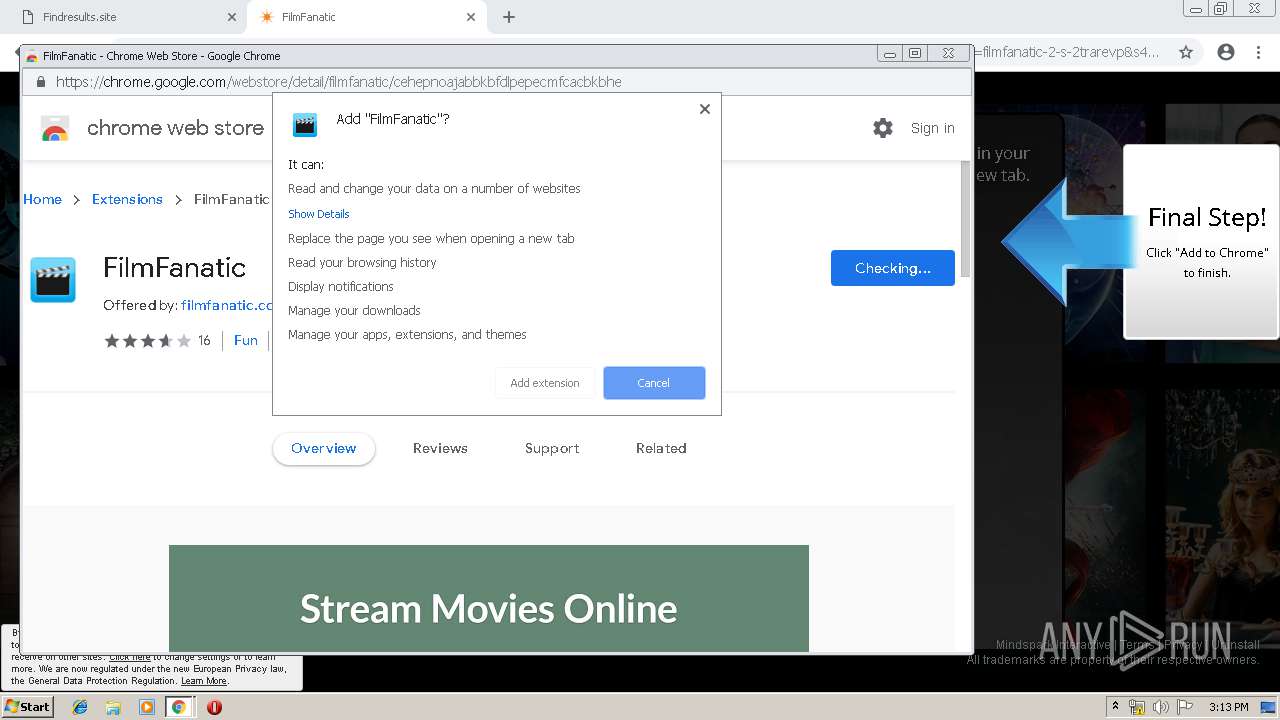
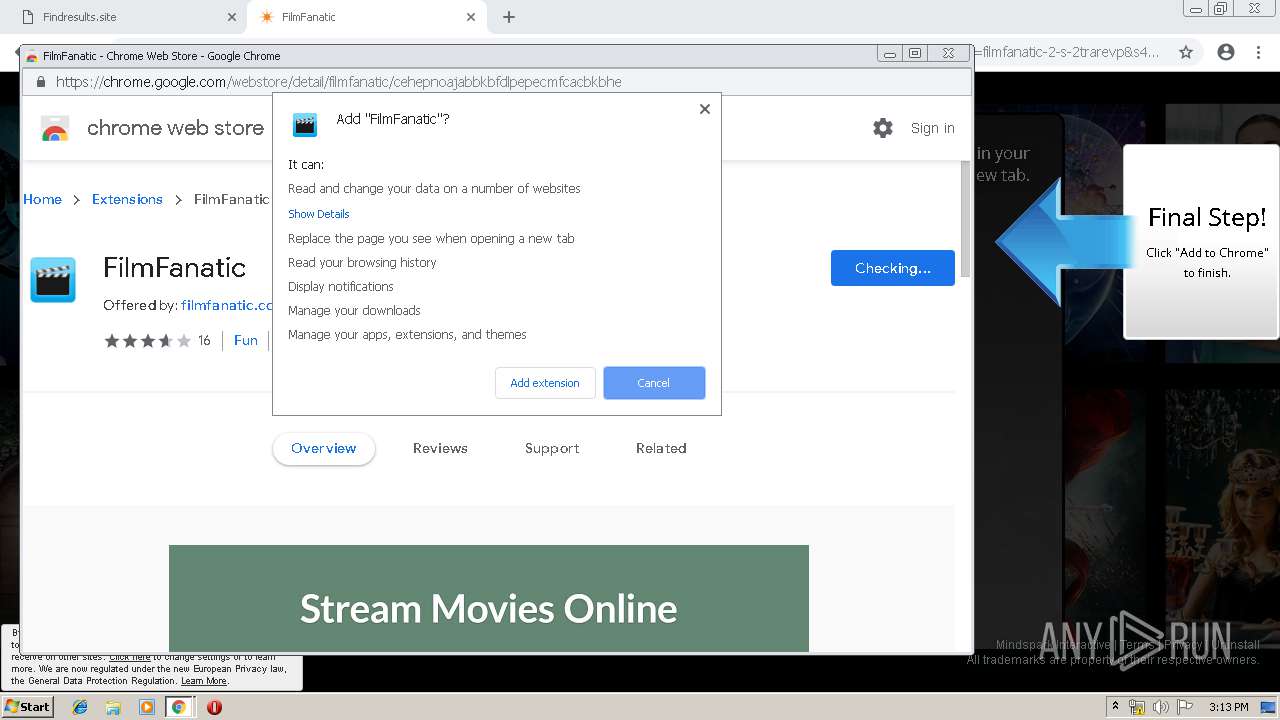
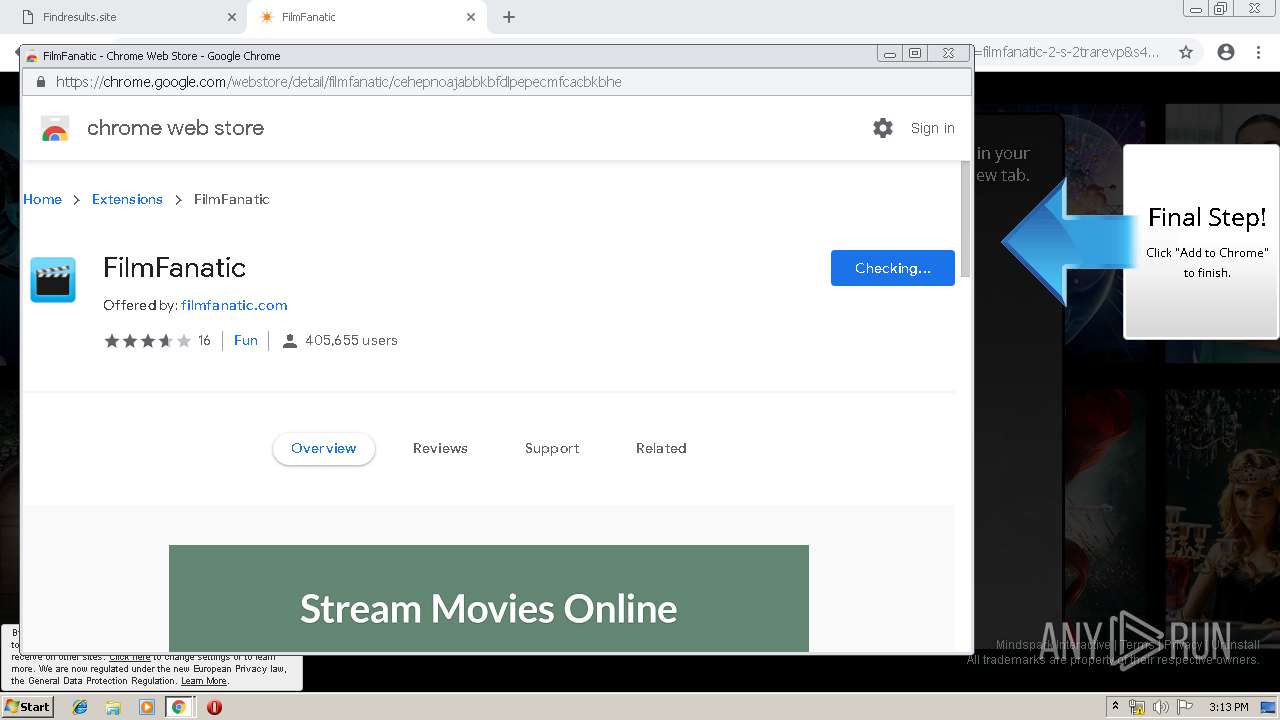
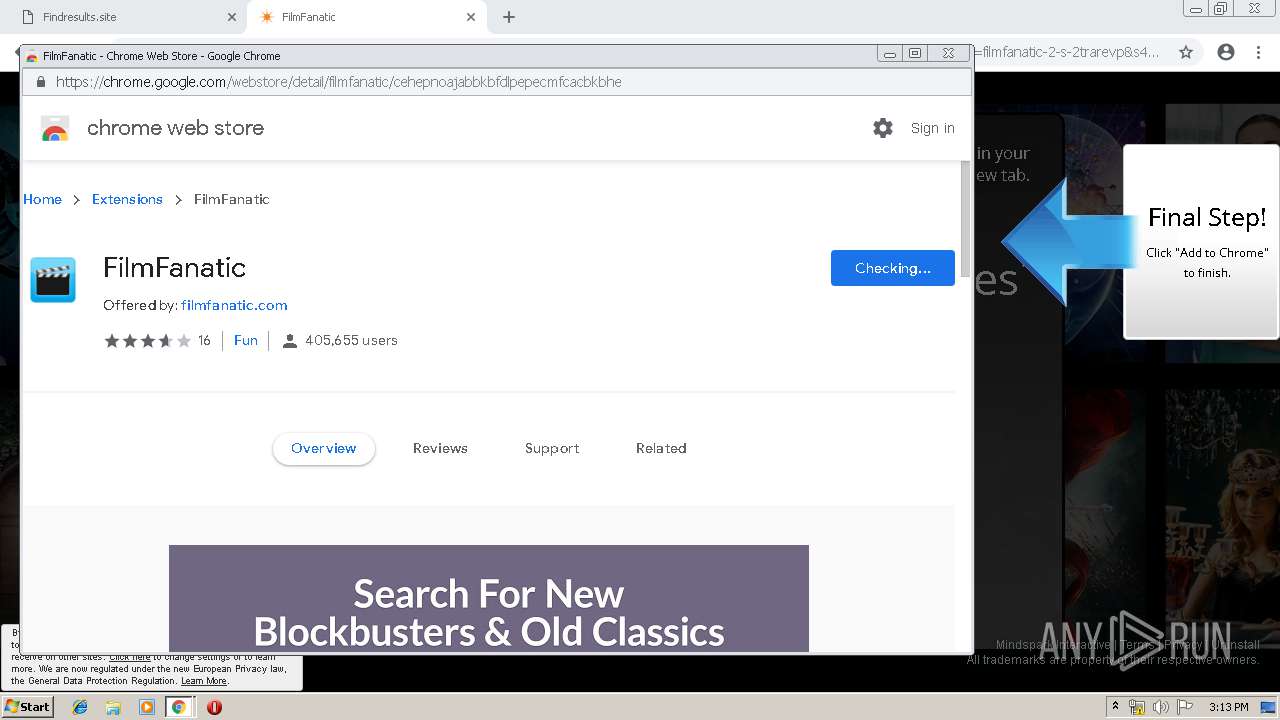
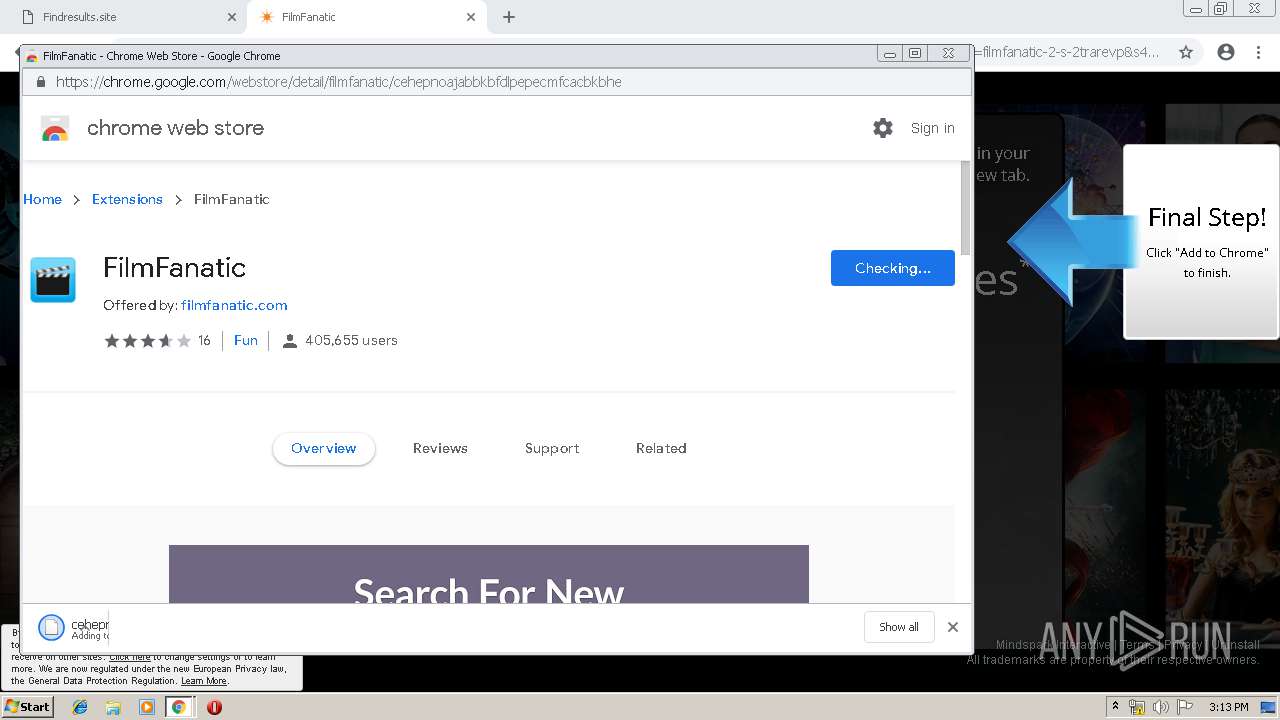
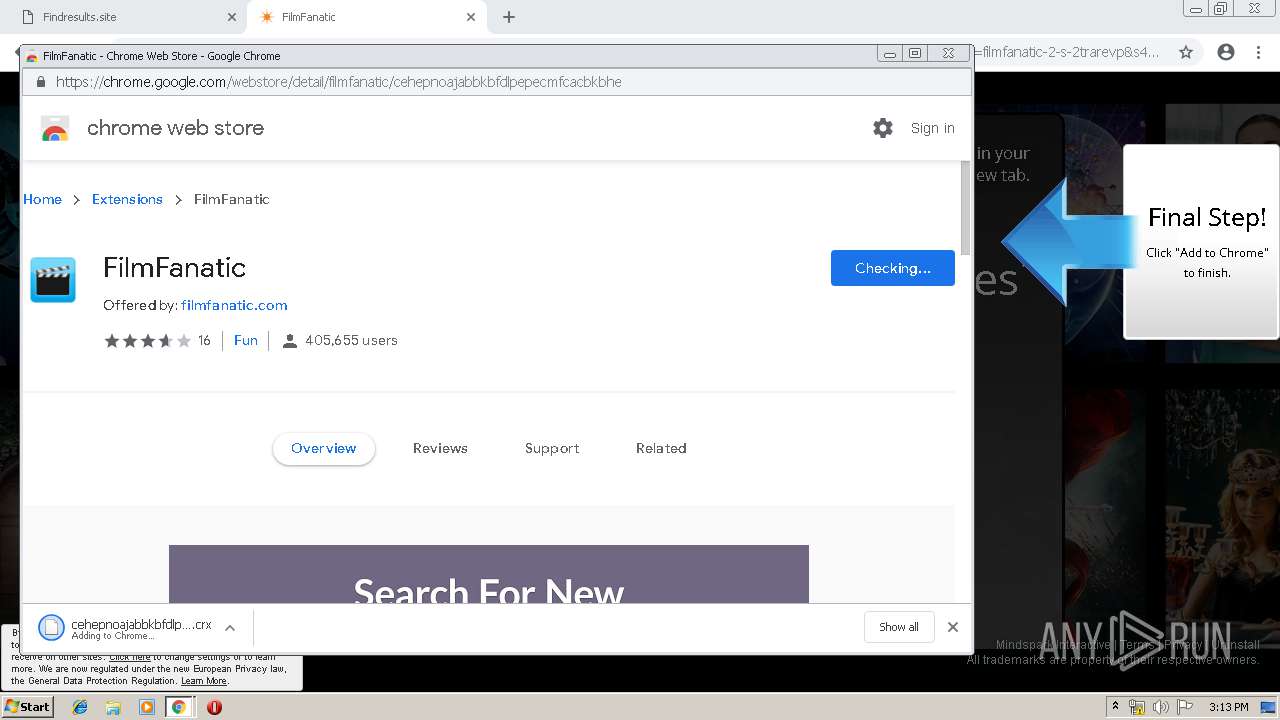
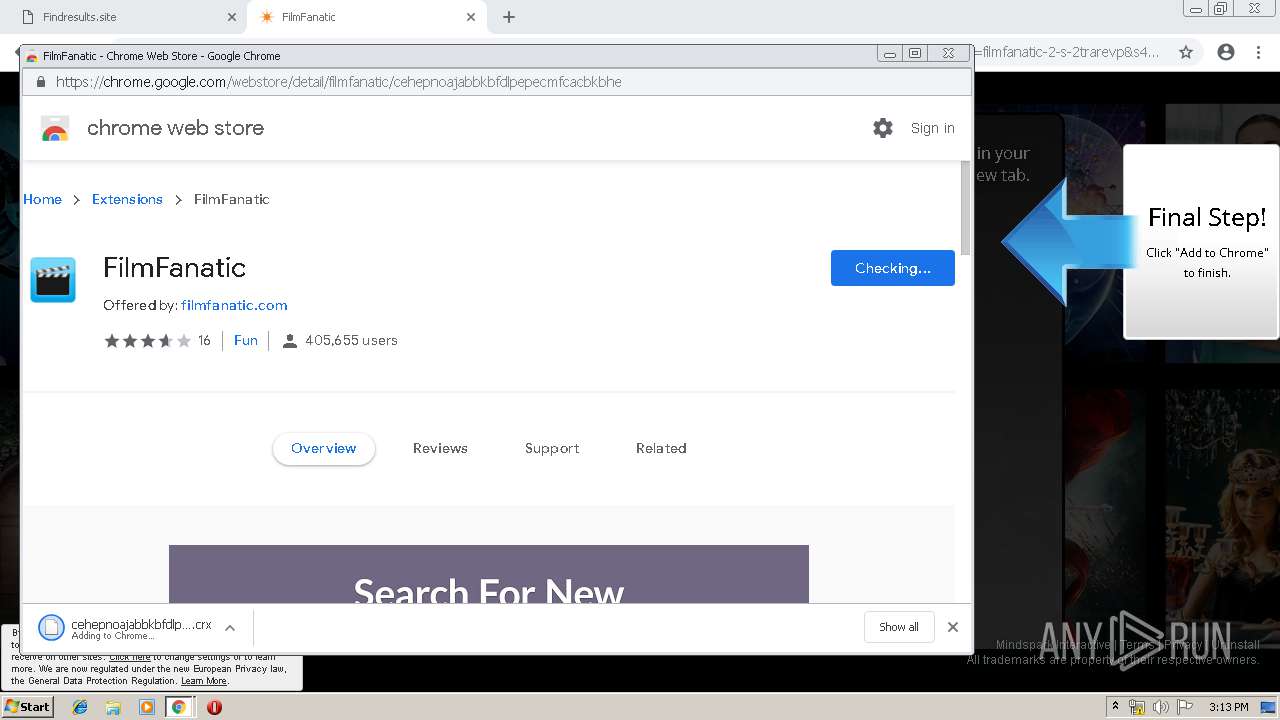
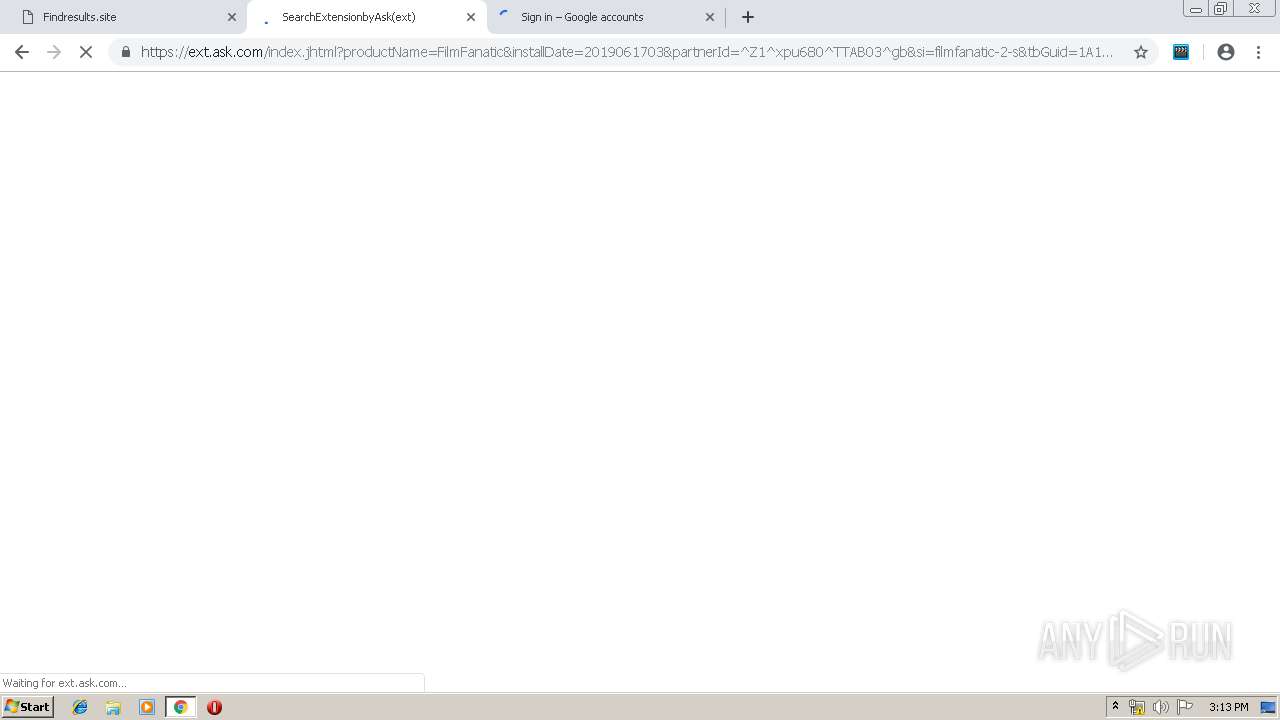
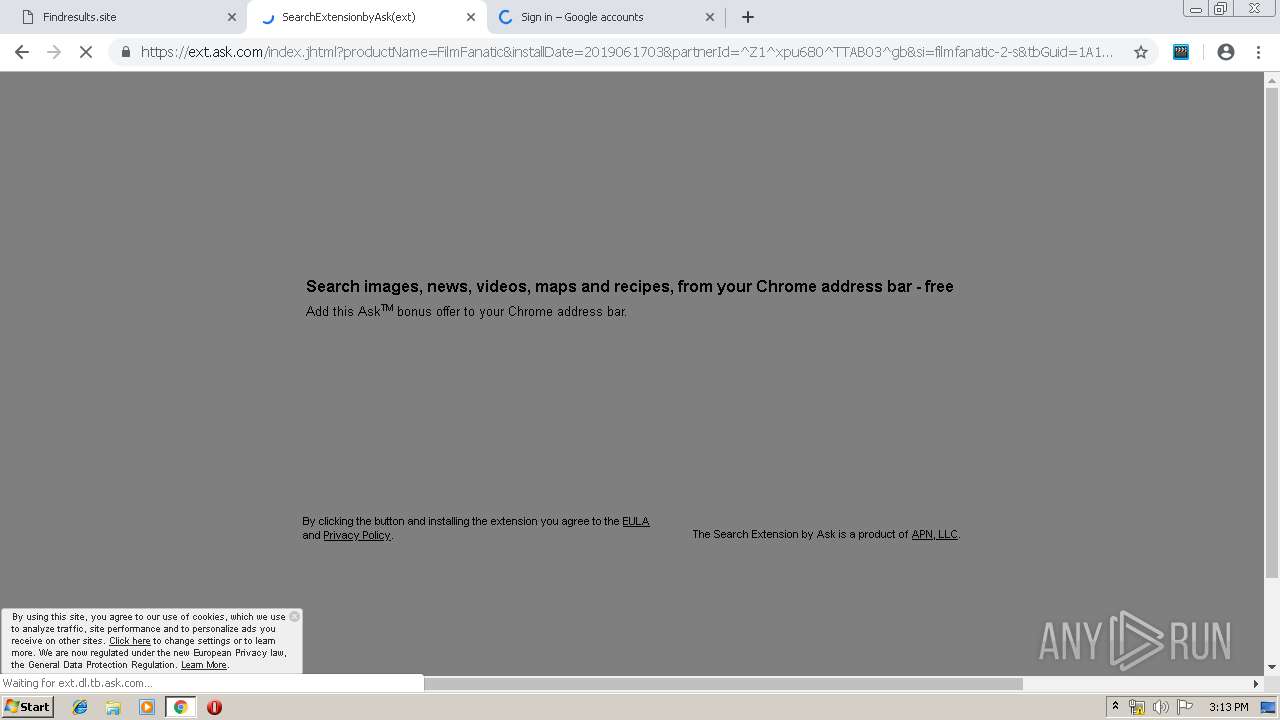
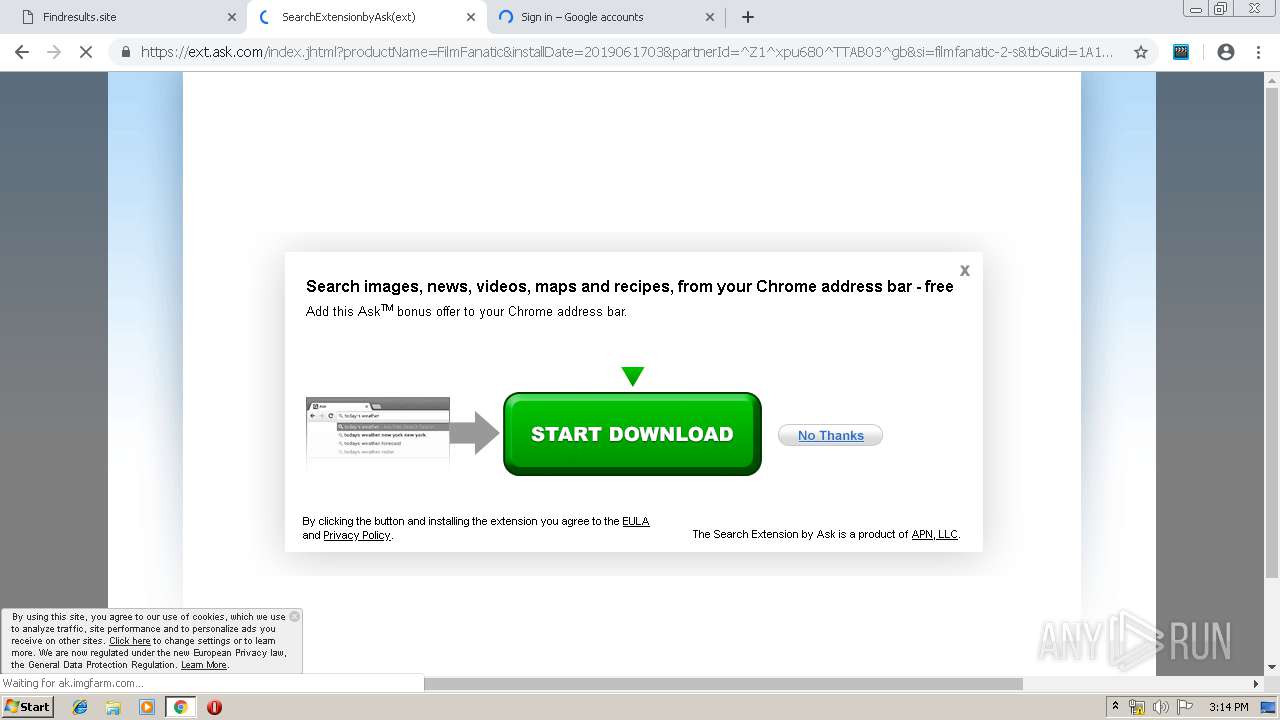
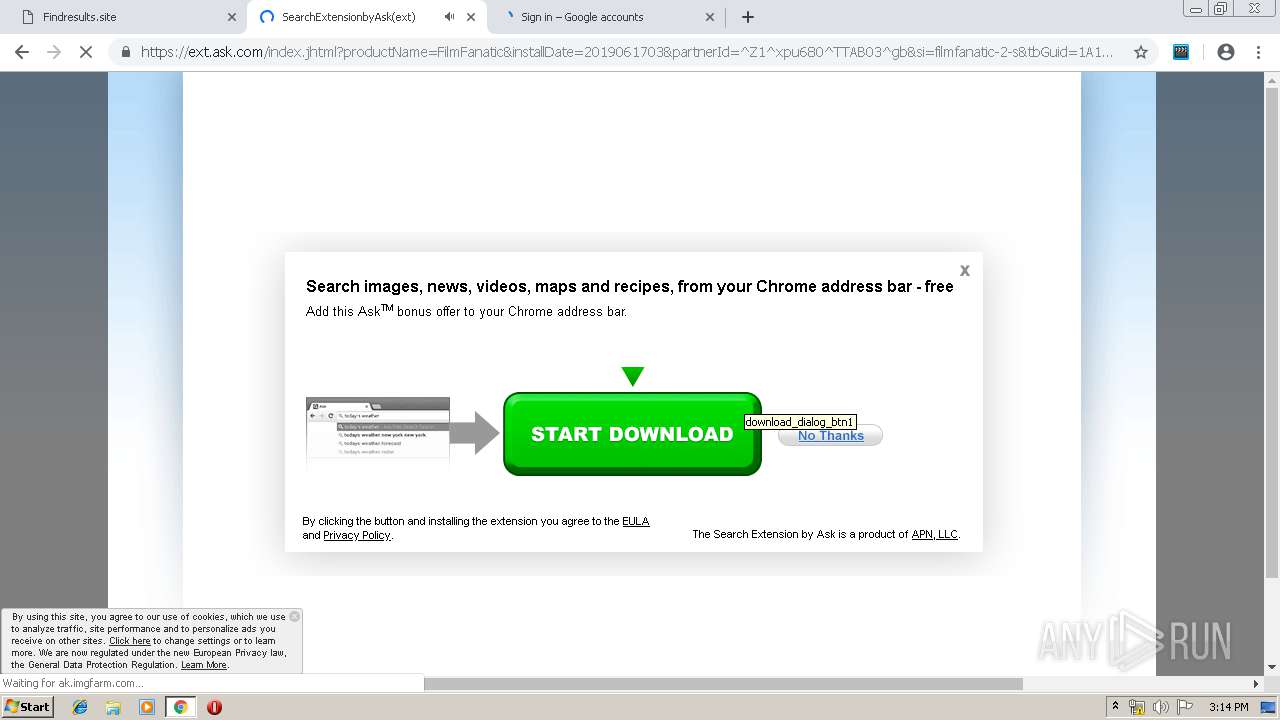
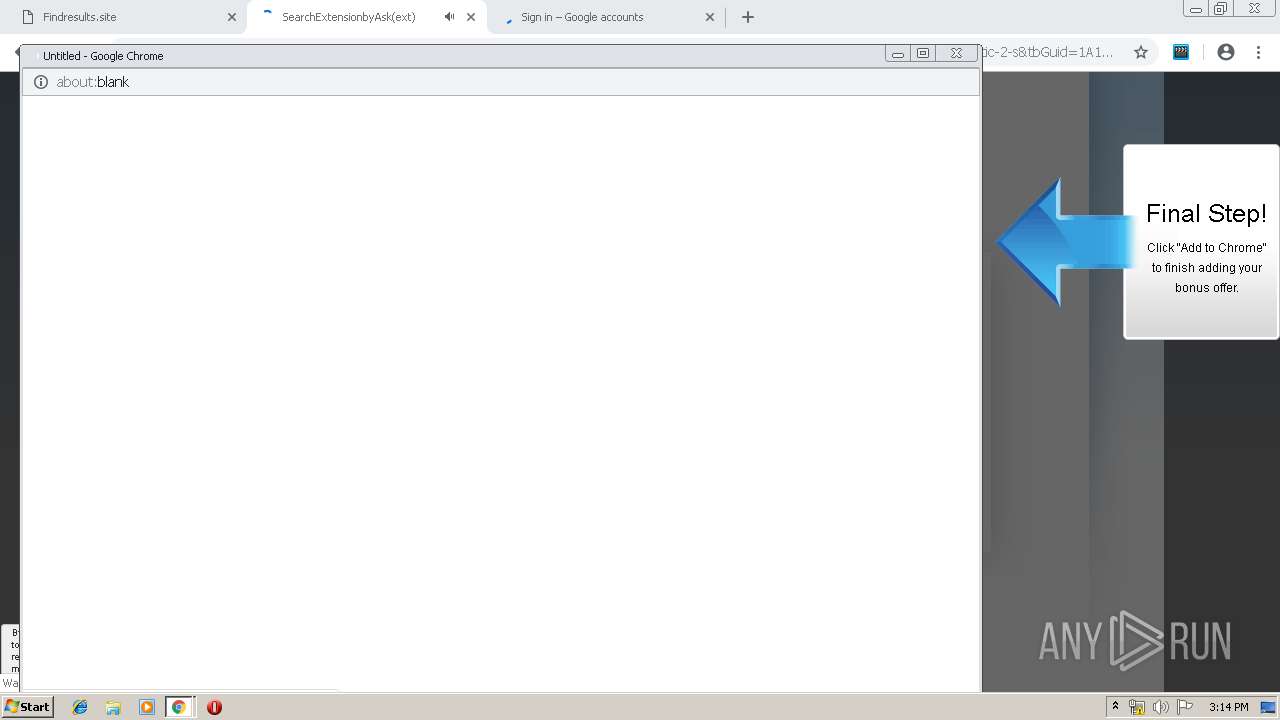
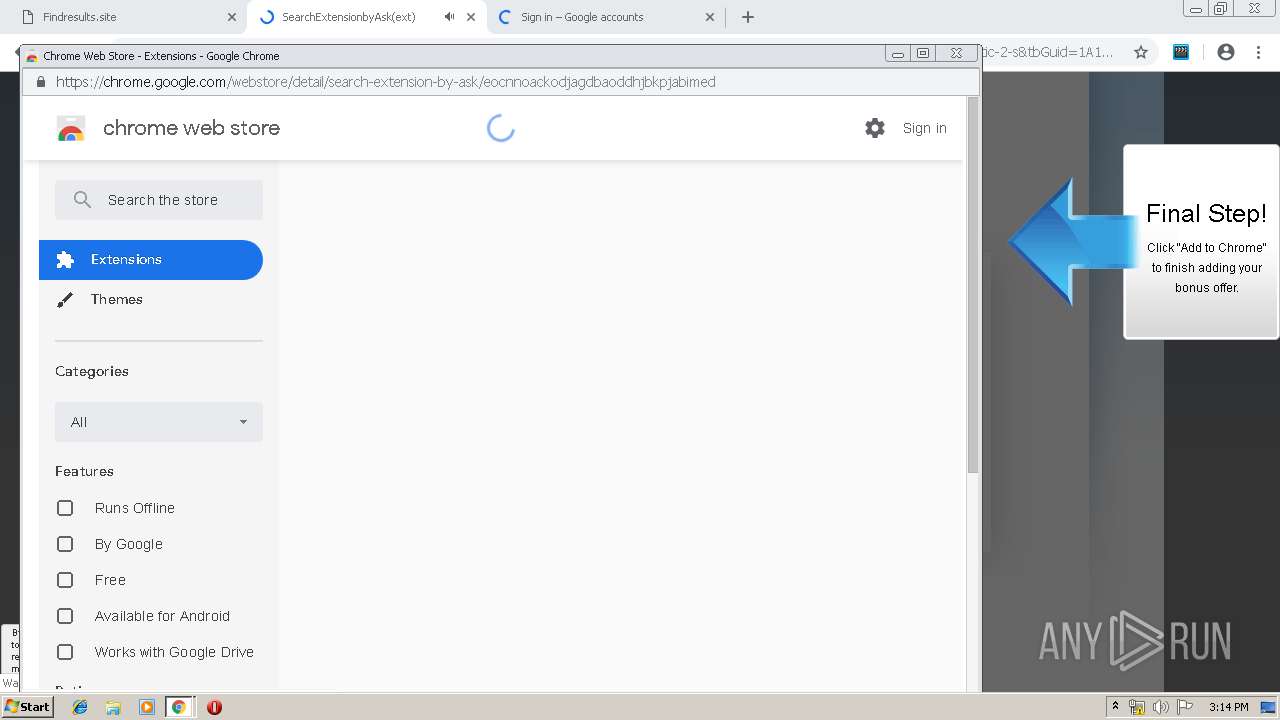
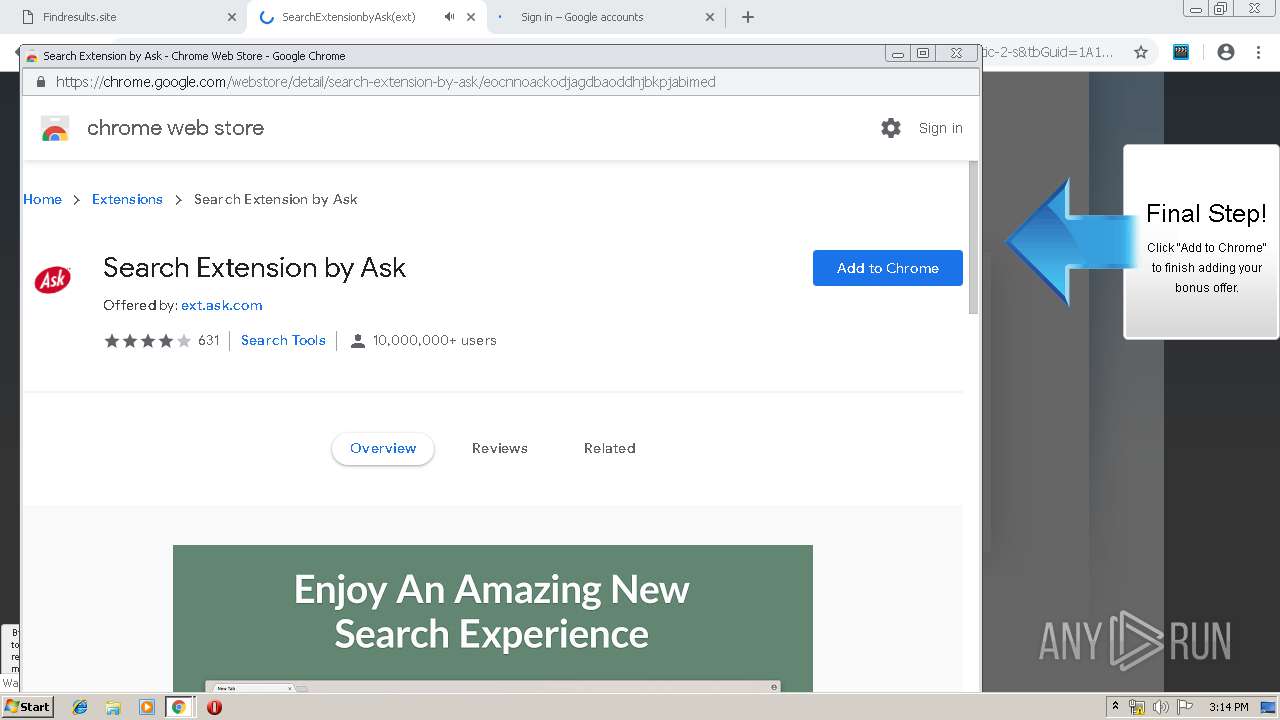
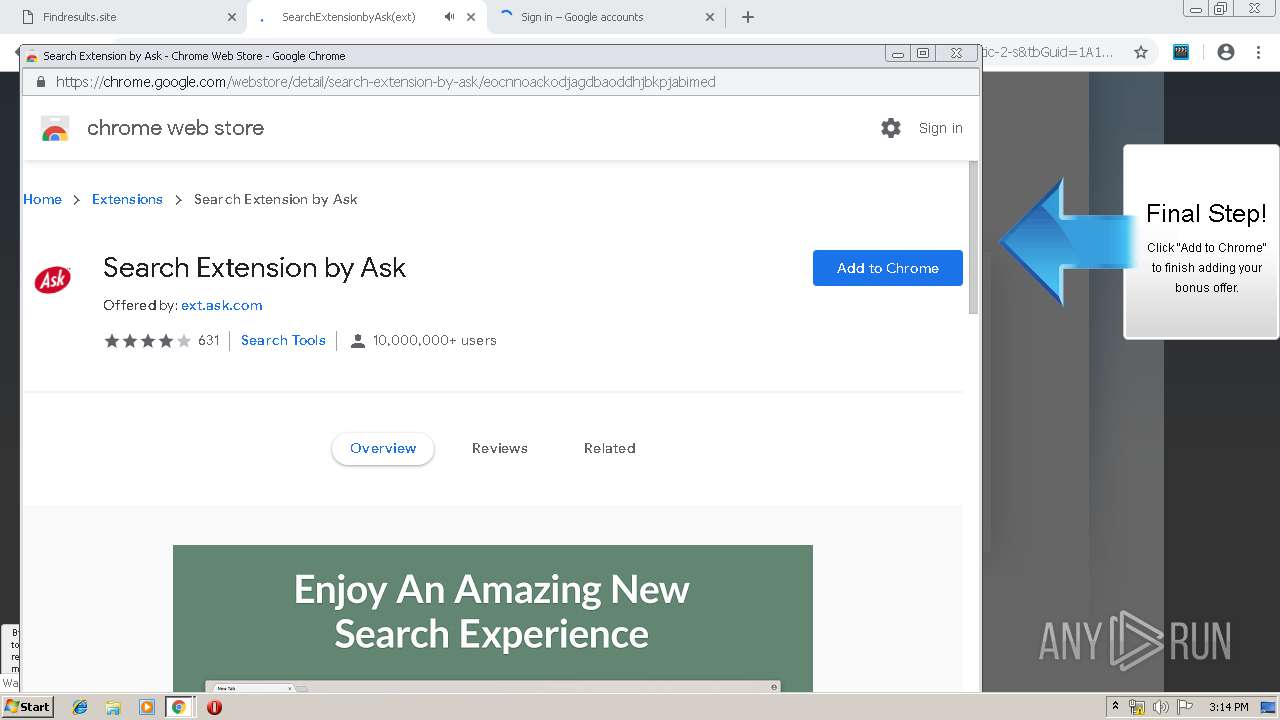
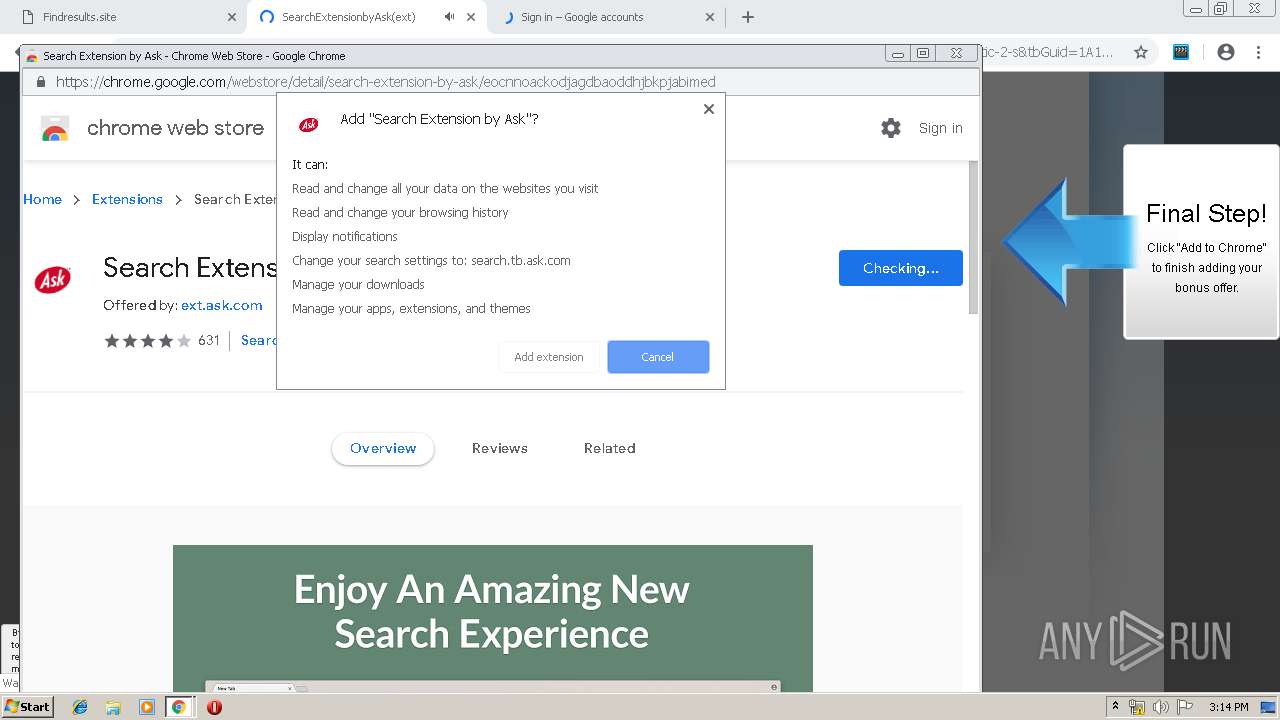
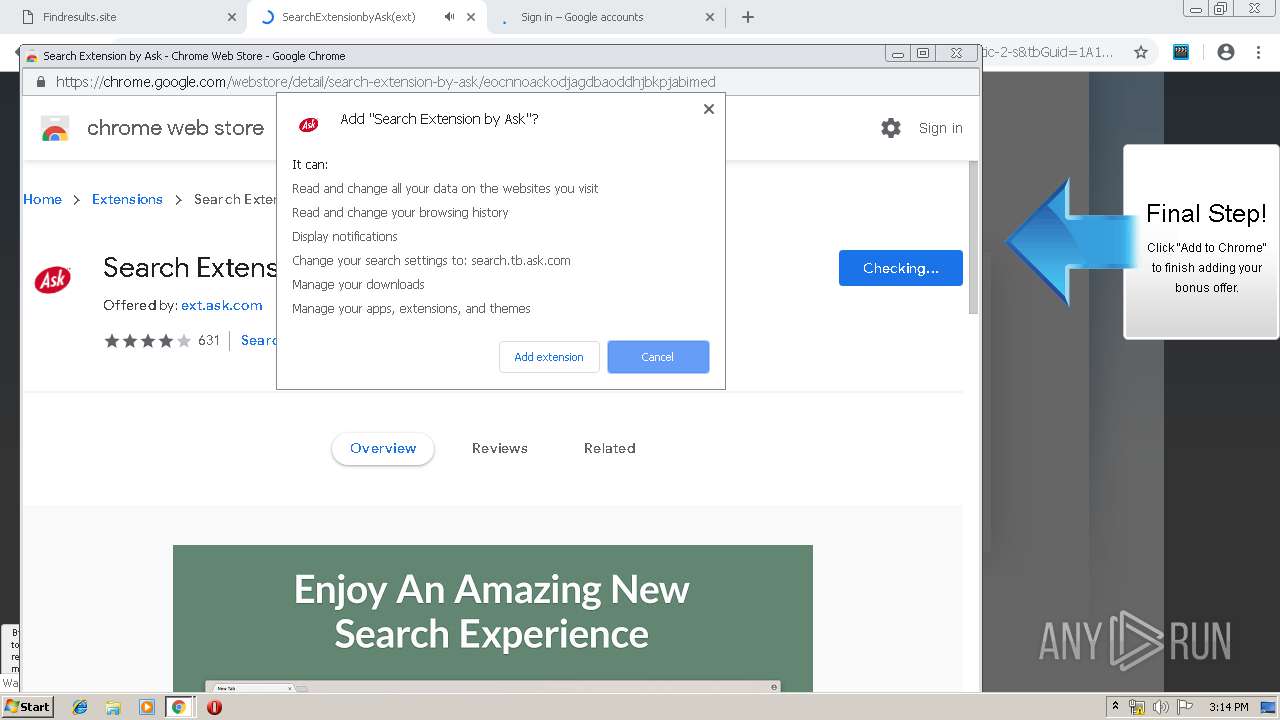
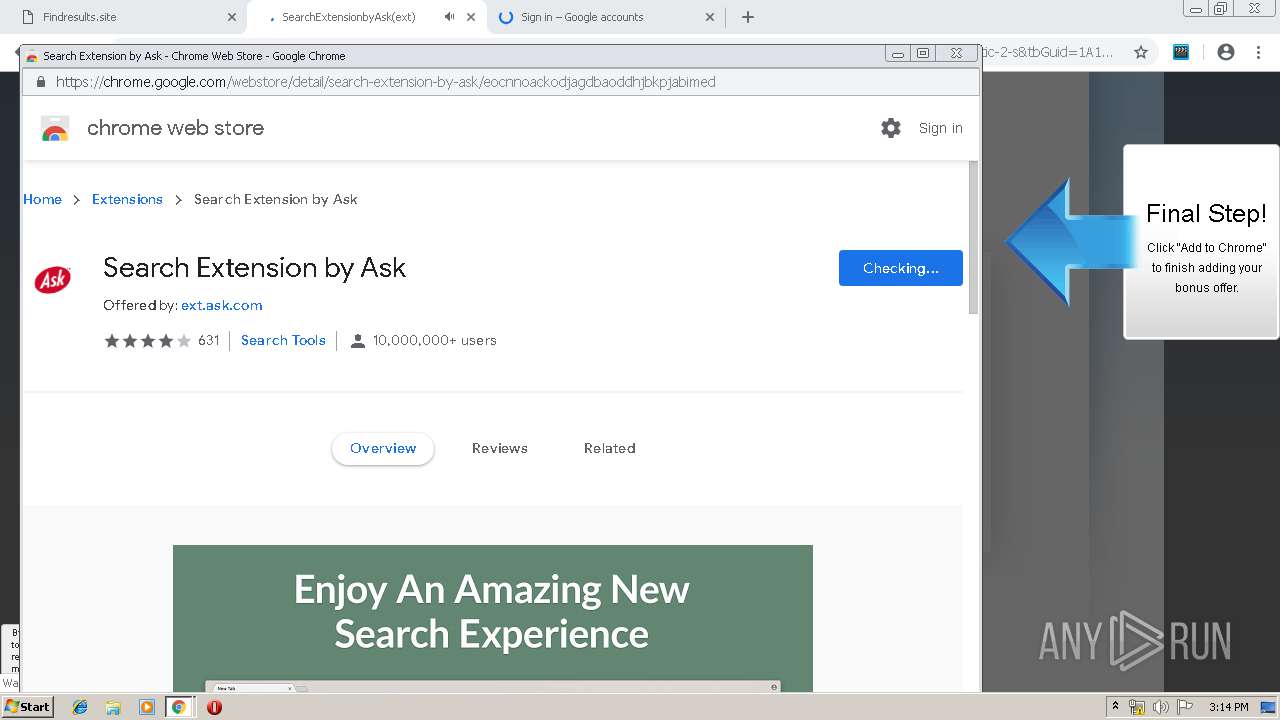
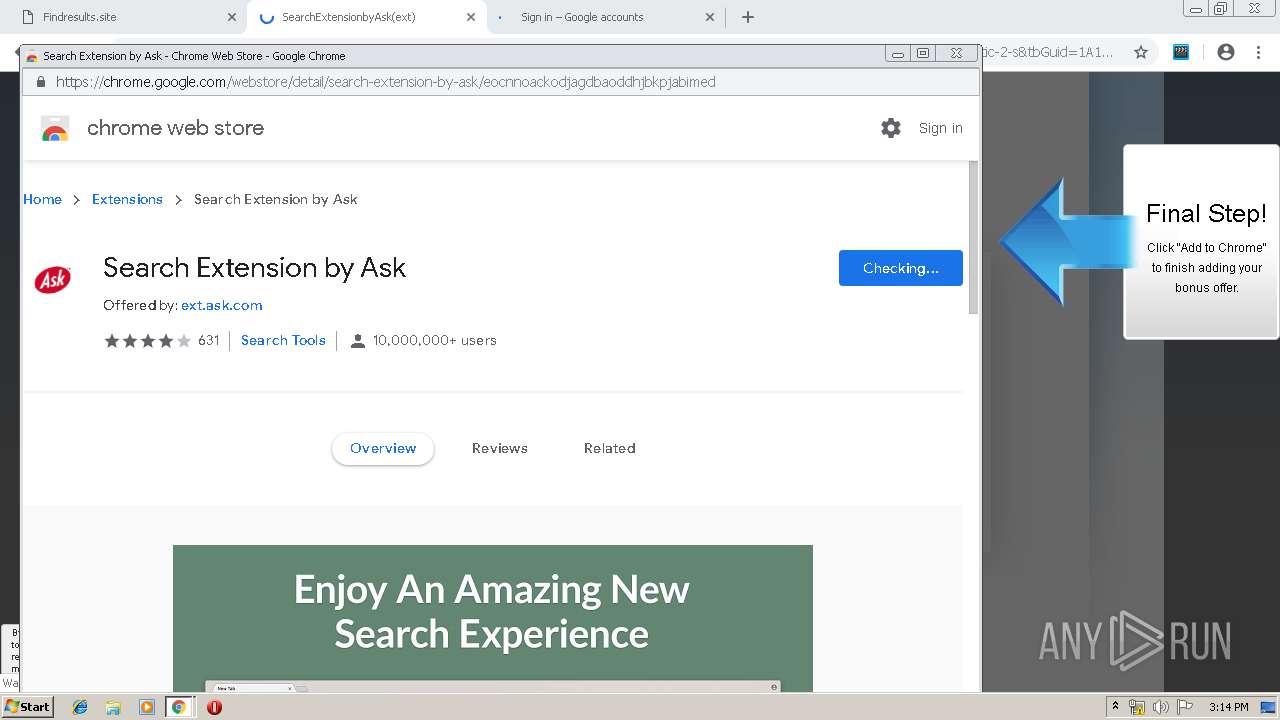
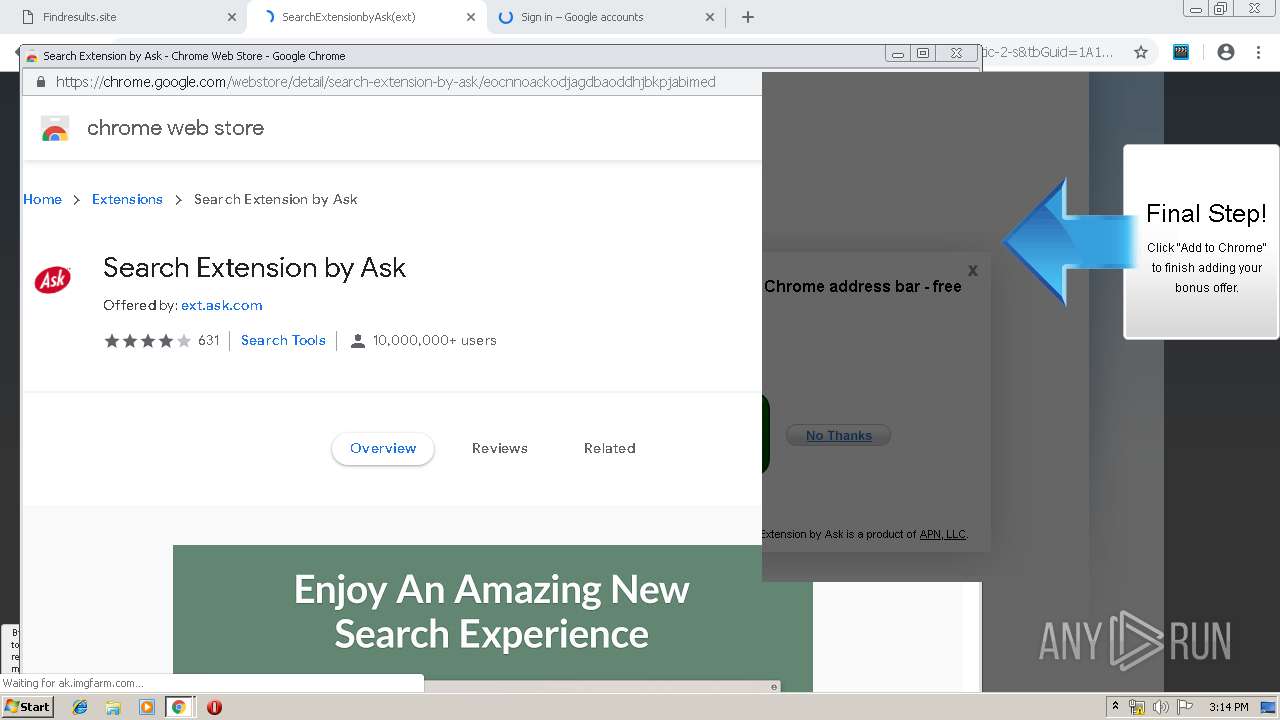
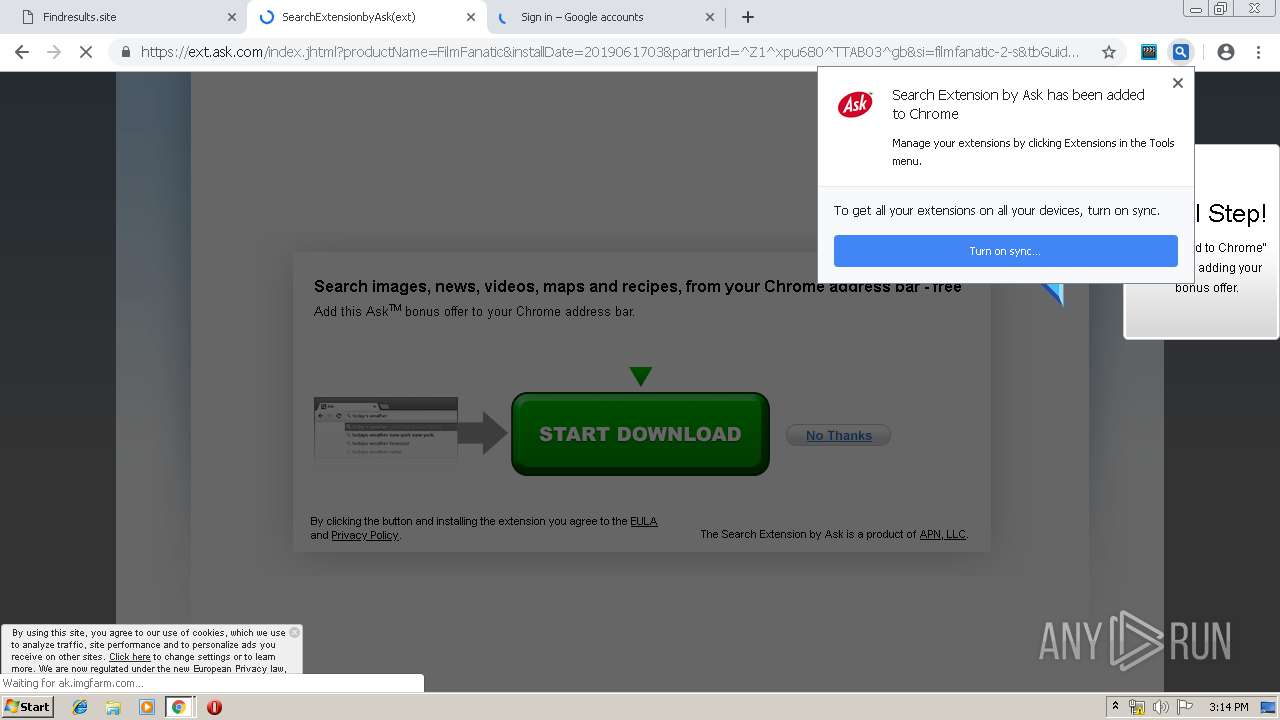
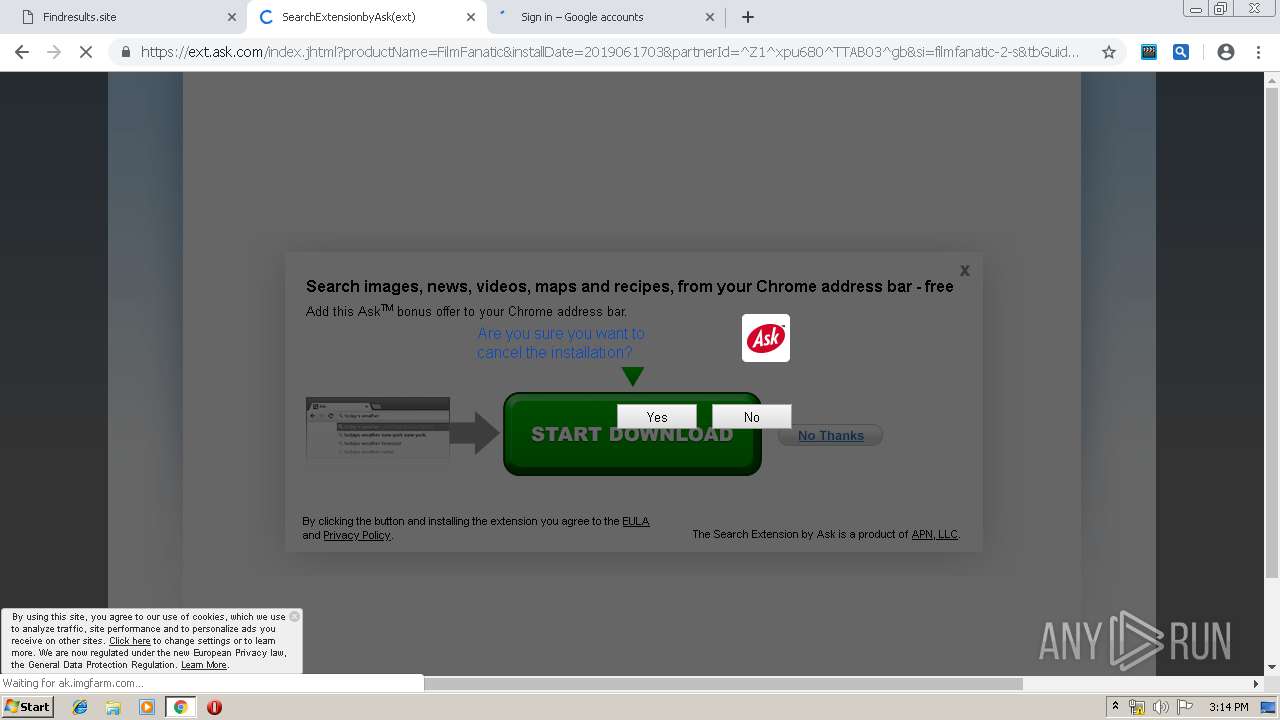
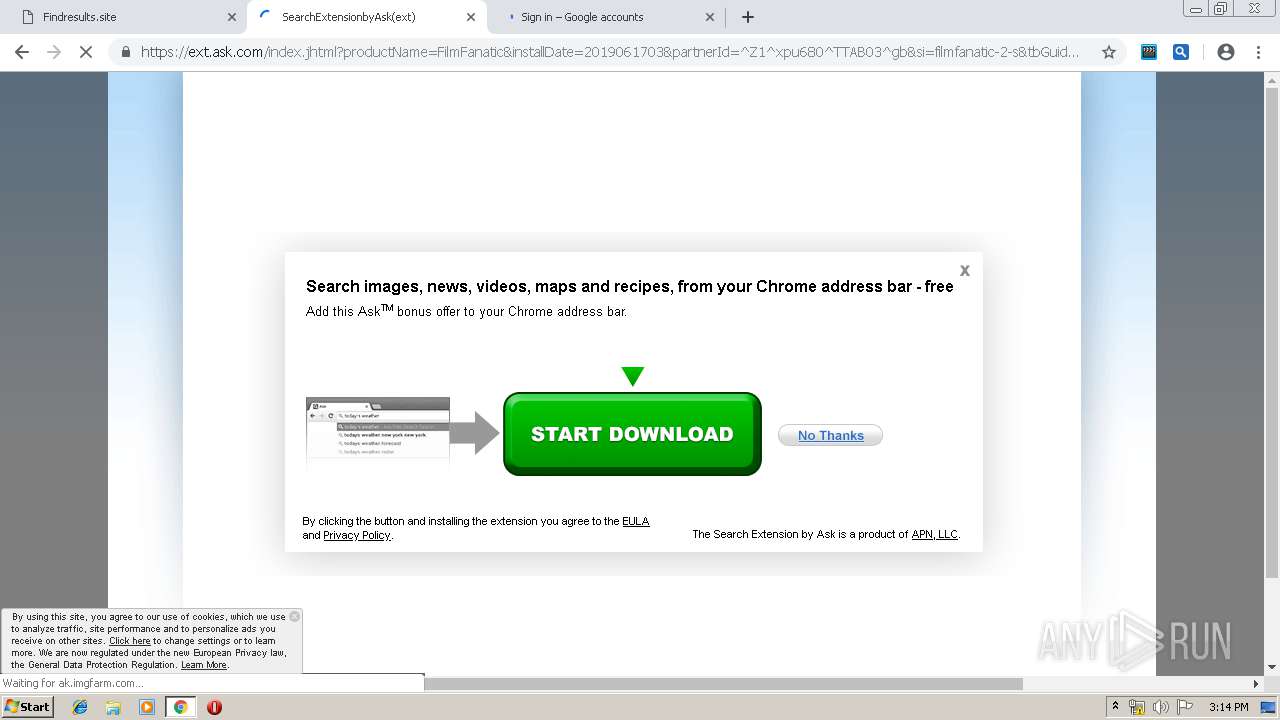
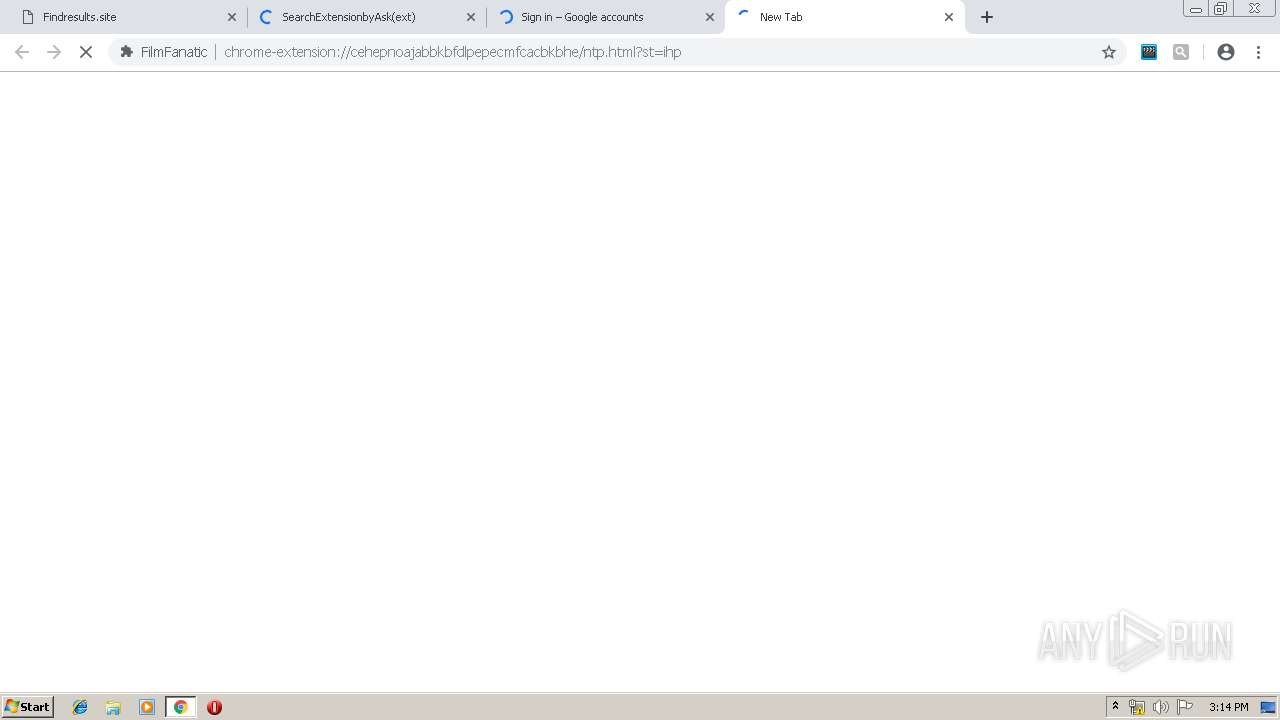
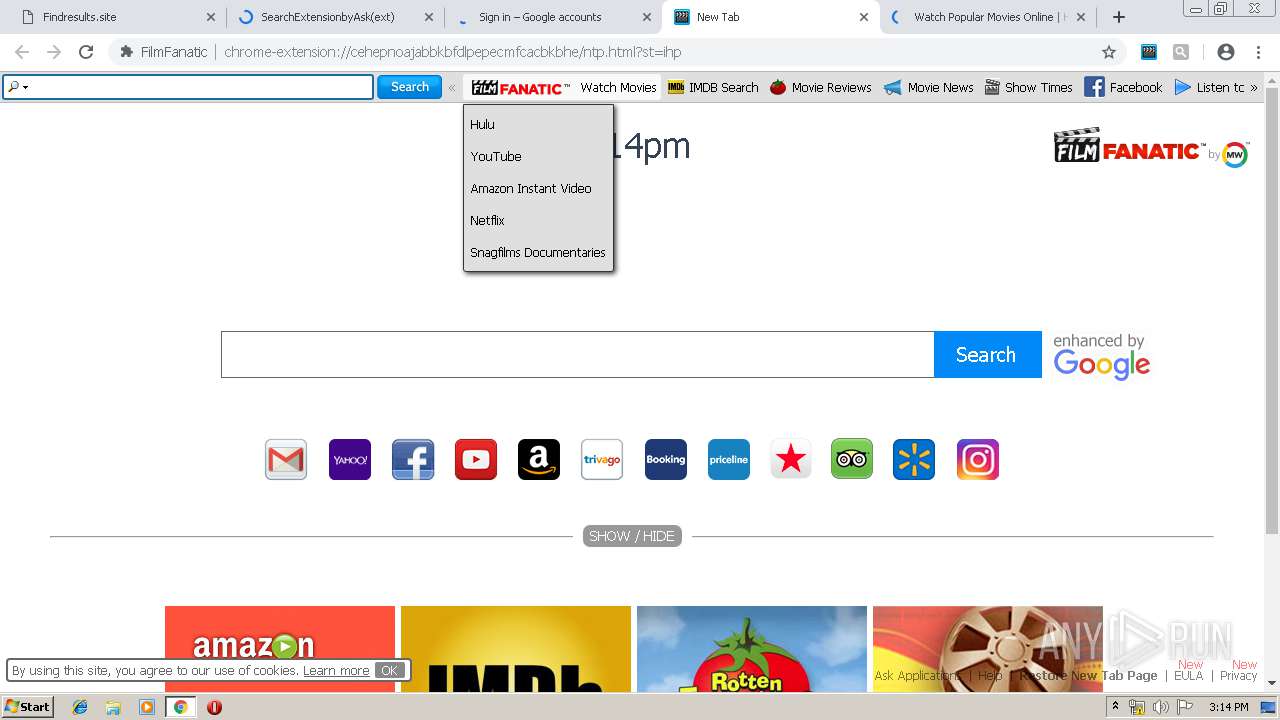
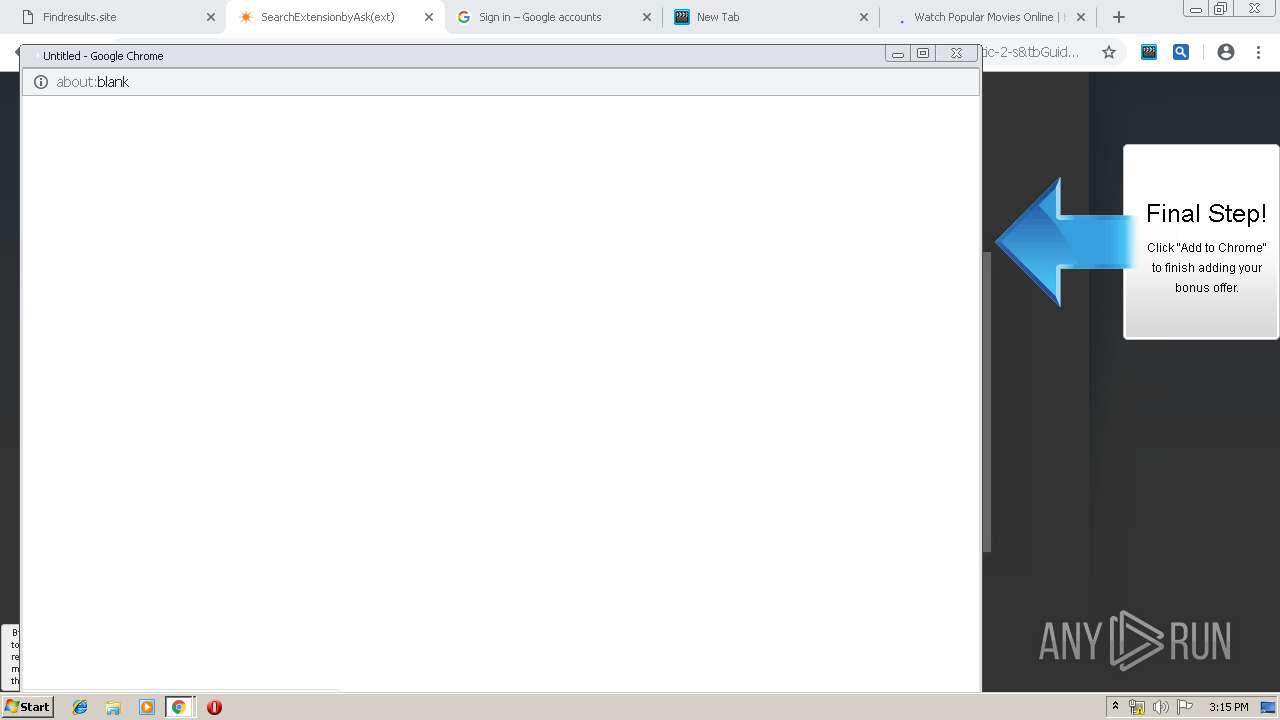
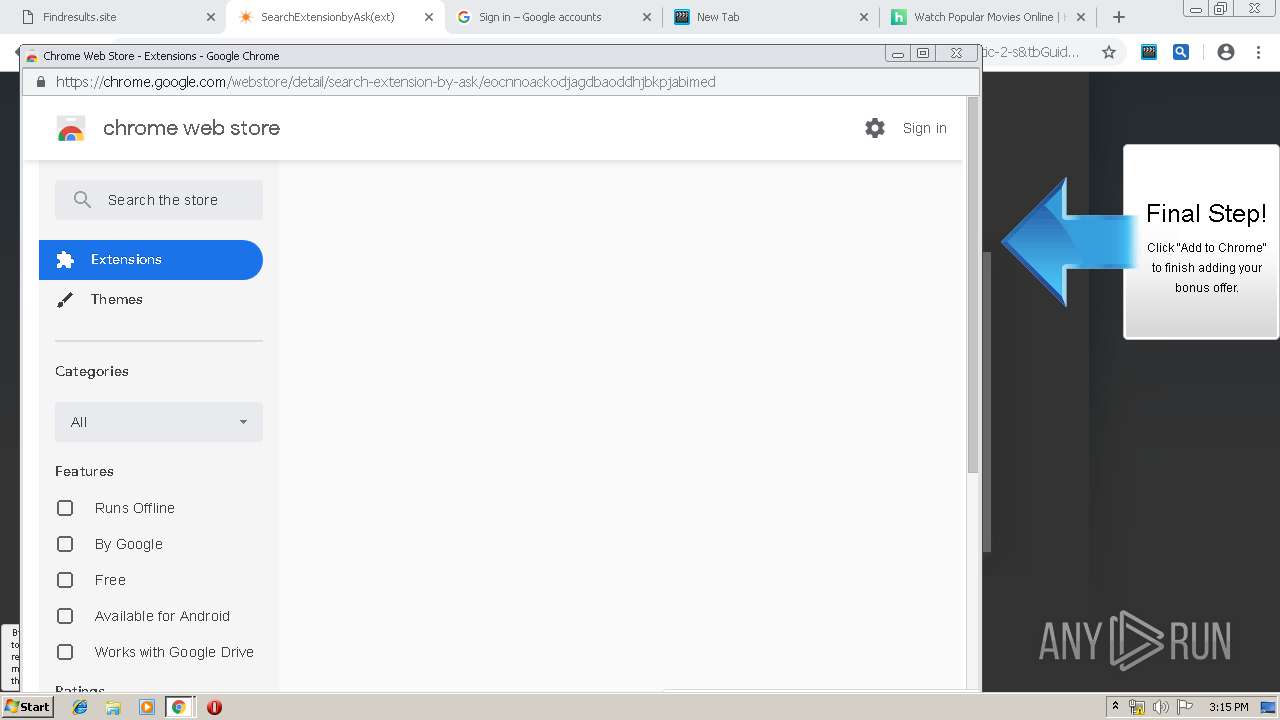
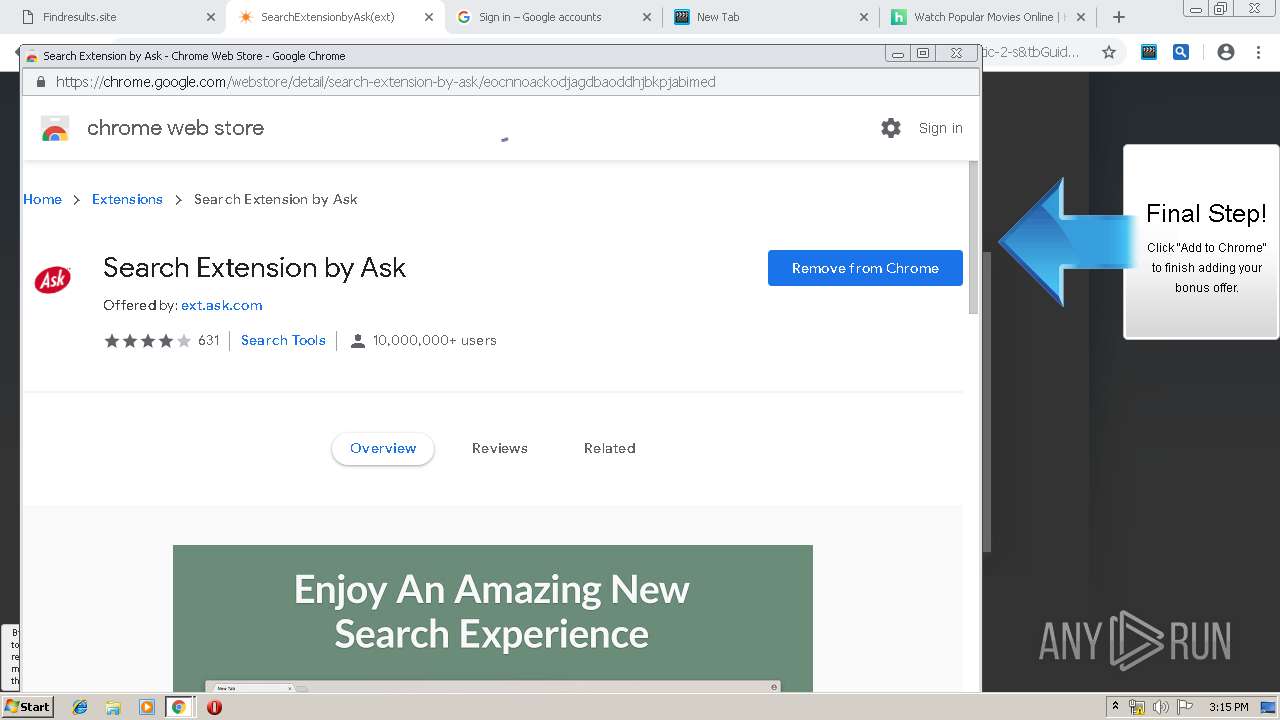
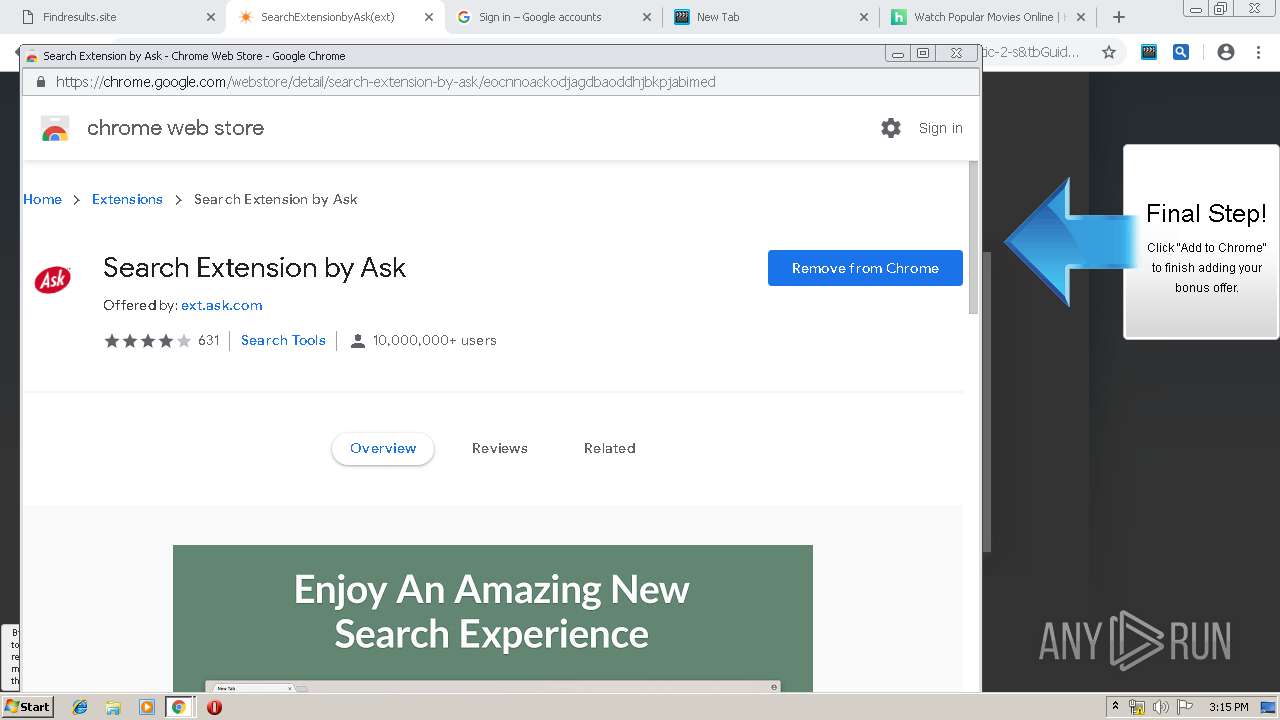
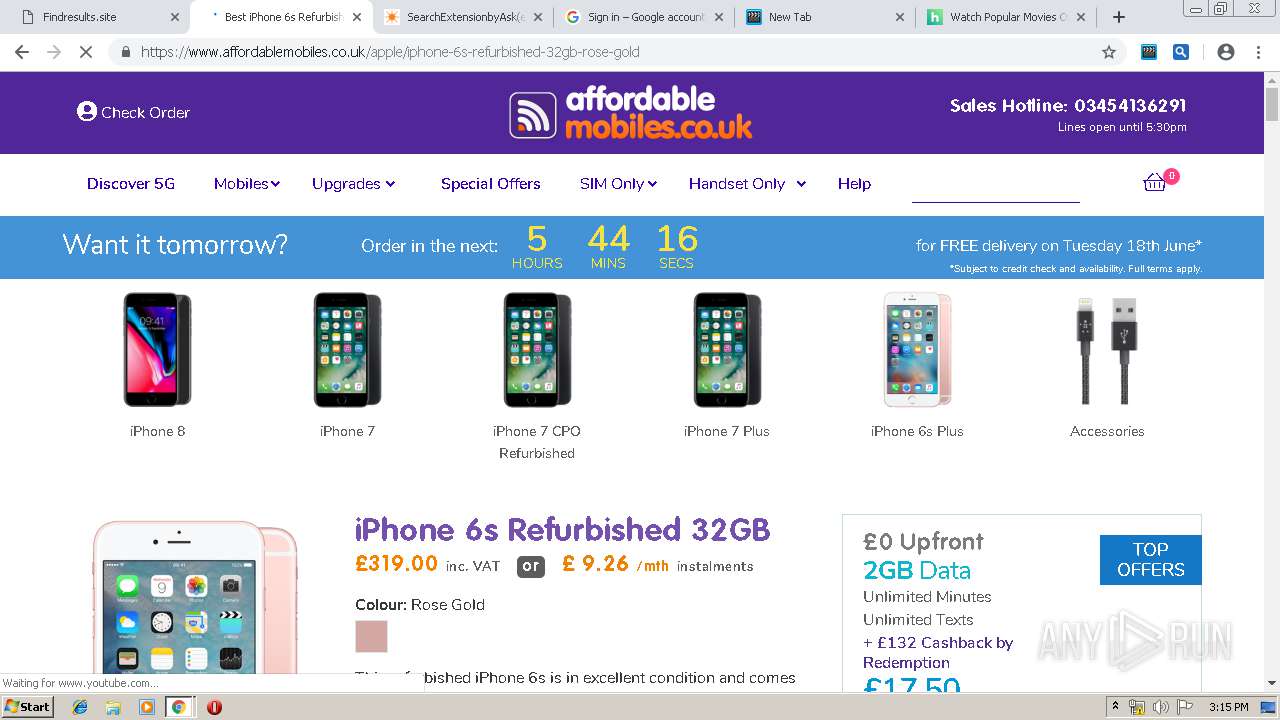
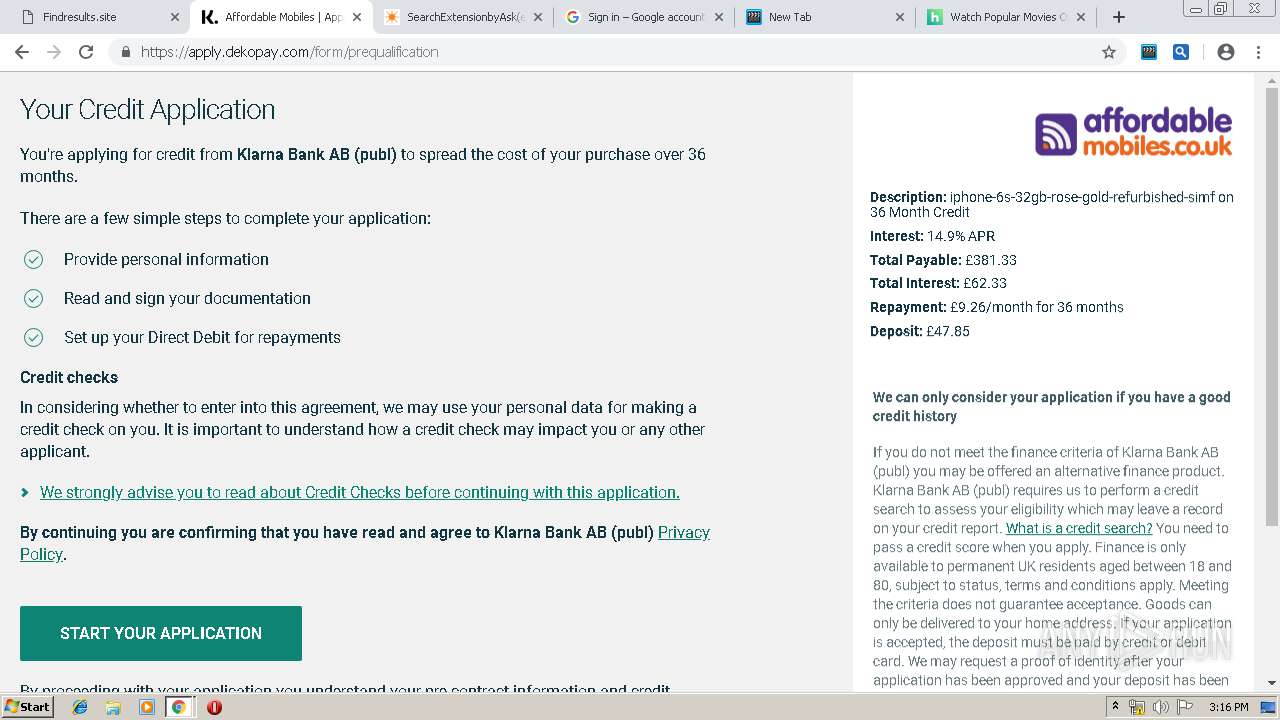
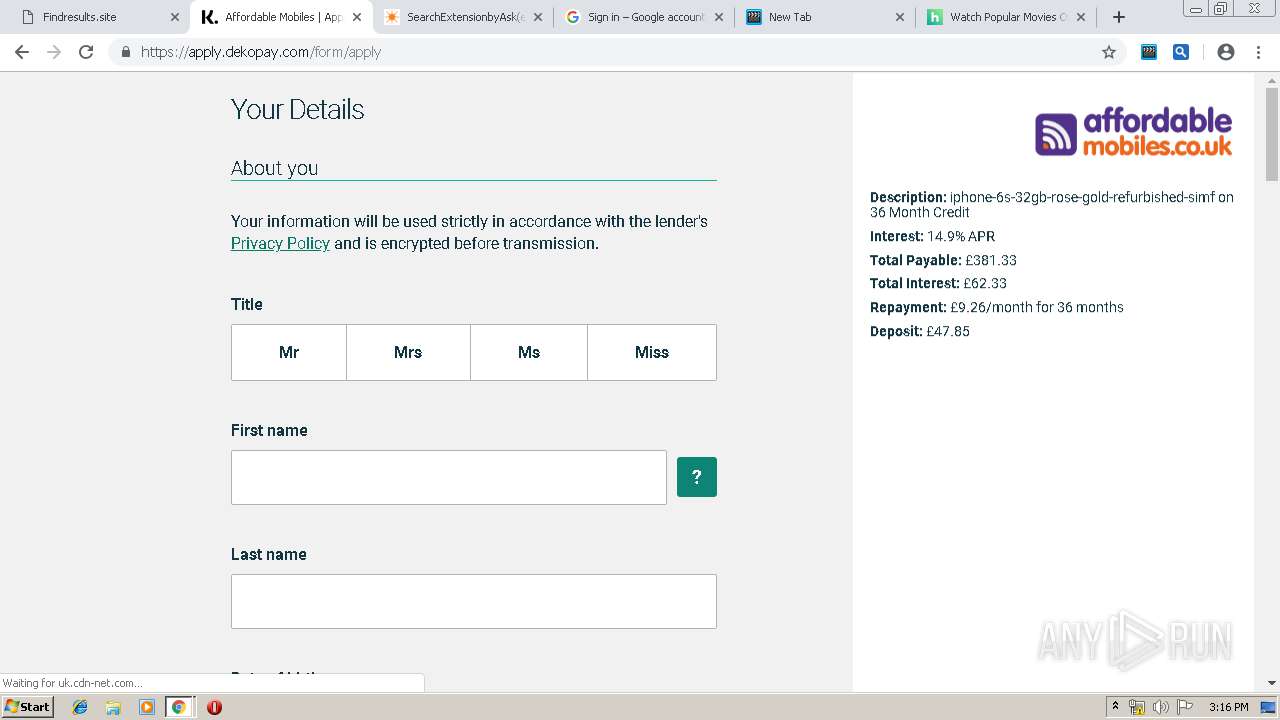
Modifies files in Chrome extension folder
- chrome.exe (PID: 3532)
INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3532)
Application launched itself
- chrome.exe (PID: 3532)
Reads Internet Cache Settings
- chrome.exe (PID: 3532)
Changes settings of System certificates
- chrome.exe (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
62
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13457796305356285652 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13457796305356285652 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2569580304973924430 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2569580304973924430 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8929878169114395622 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8929878169114395622 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3951898115158110506 --mojo-platform-channel-handle=964 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11062343942252121670 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11062343942252121670 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5483260175091067934 --mojo-platform-channel-handle=6092 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11320597946389636233 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11320597946389636233 --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2674182081768425023 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2674182081768425023 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3332 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --service-pipe-token=927289249614774528 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=927289249614774528 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
851
Read events
681
Write events
163
Delete events
7
Modification events
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3532-13205254338378500 |
Value: 259 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3532-13205254338378500 |
Value: 259 | |||
Executable files
0
Suspicious files
278
Text files
540
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF11ef9d.TMP | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fc044668-13a2-42a0-b405-135c09cd9d5f.tmp | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
233
DNS requests
138
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3532 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i4.cdn-image.com/__media__/images/4641_1.jpg | unknown | image | 1.61 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/pics/747/Myriad_Pro_900.font.js | unknown | text | 117 Kb | whitelisted |
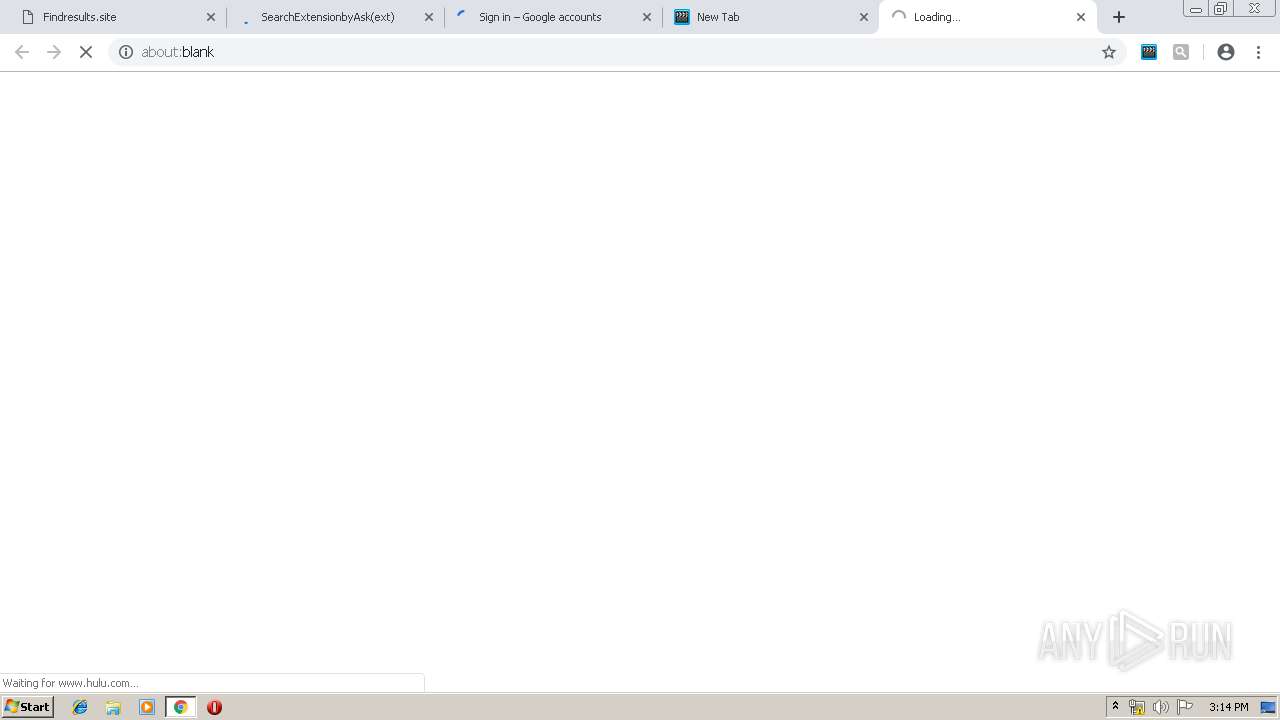
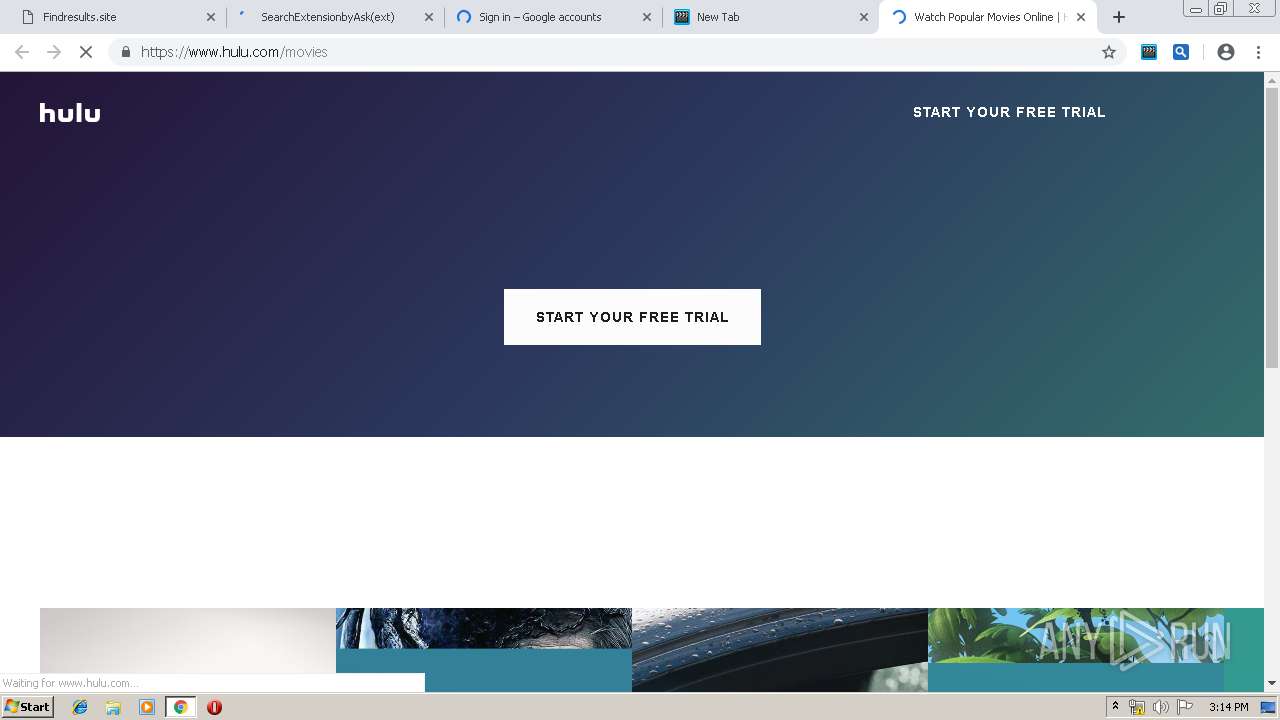
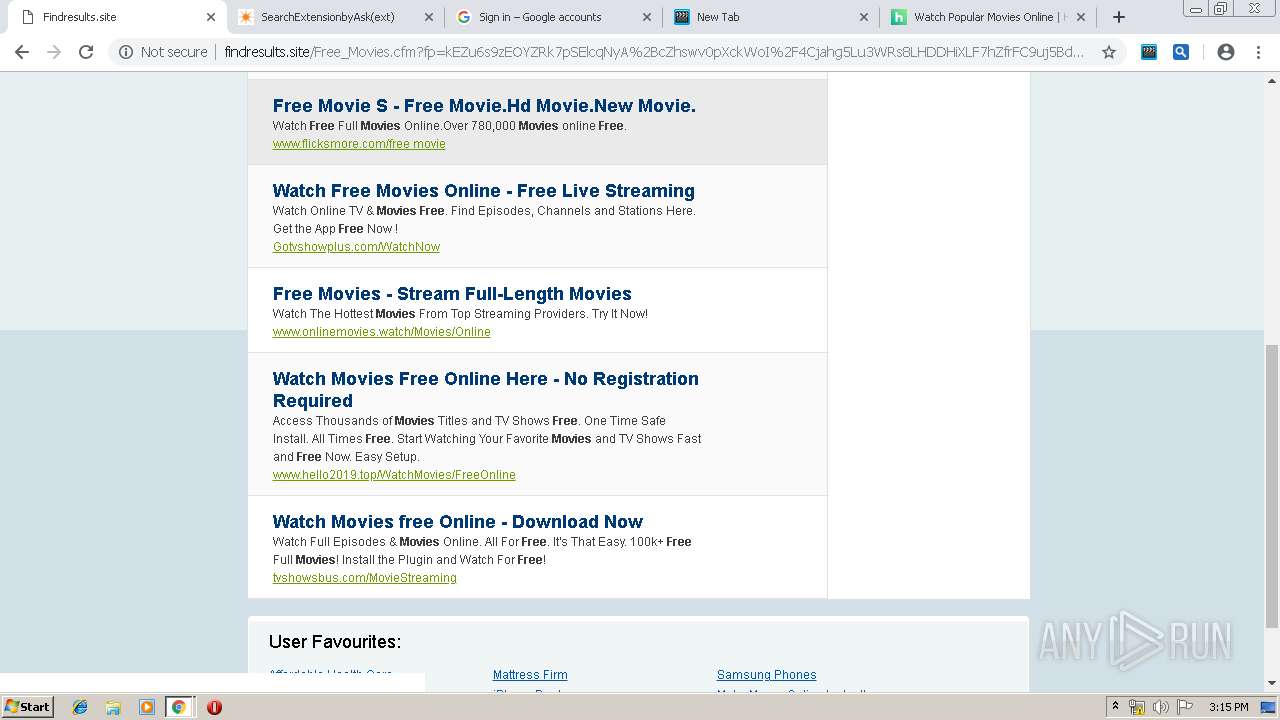
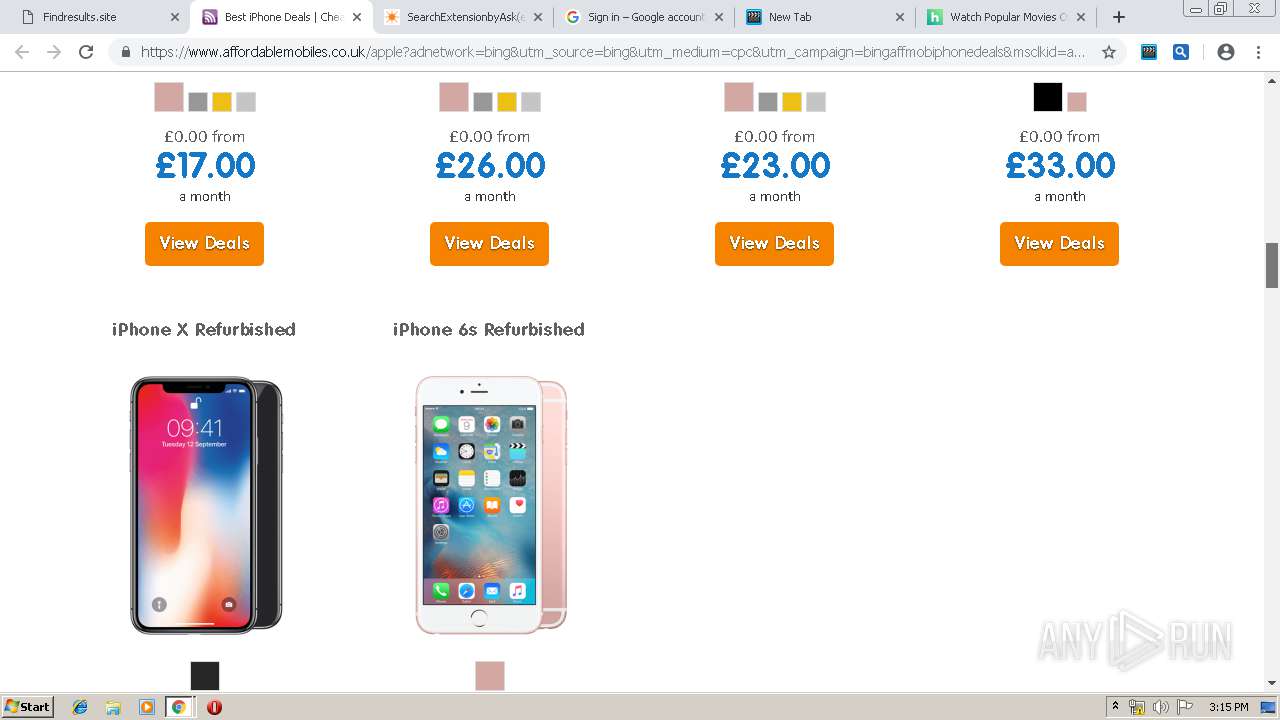
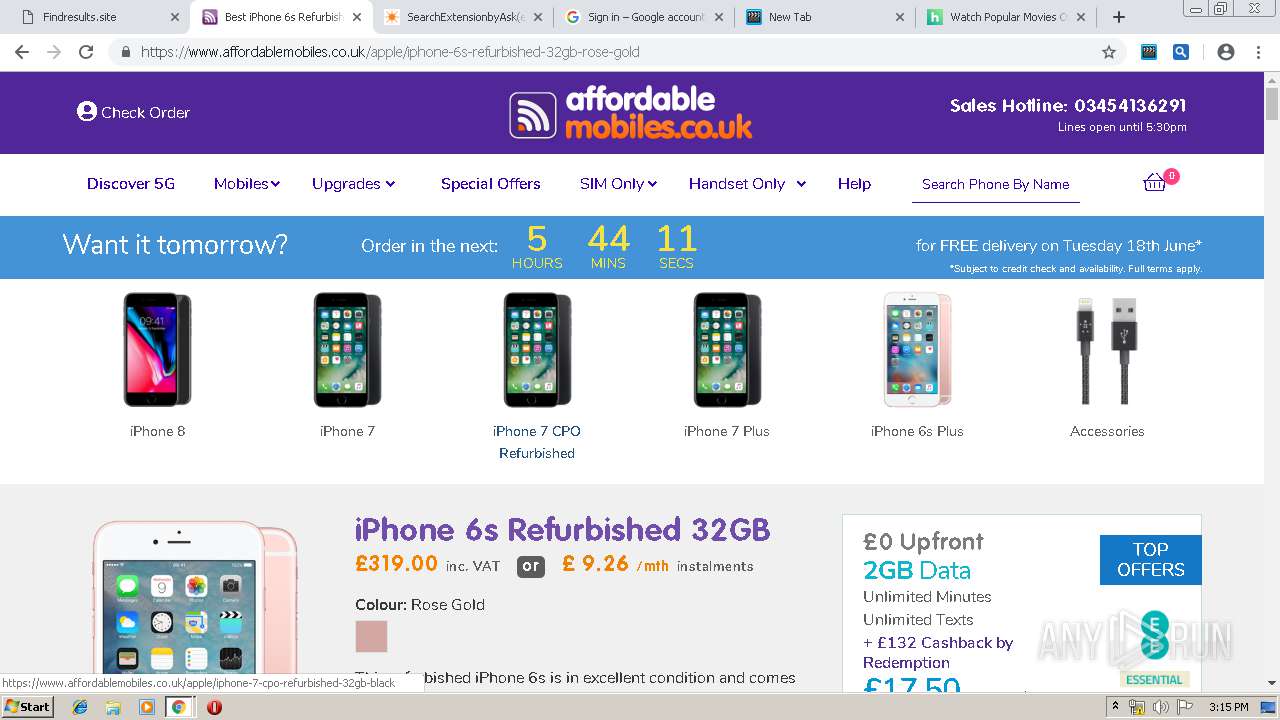
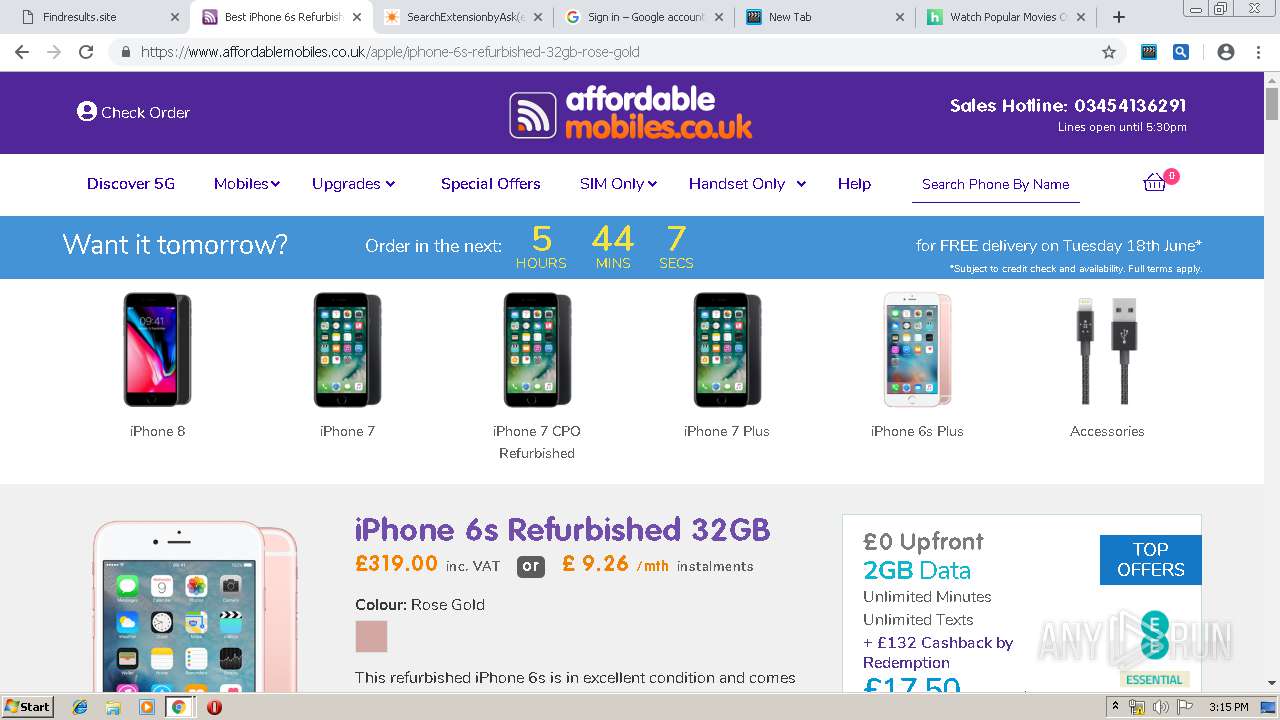
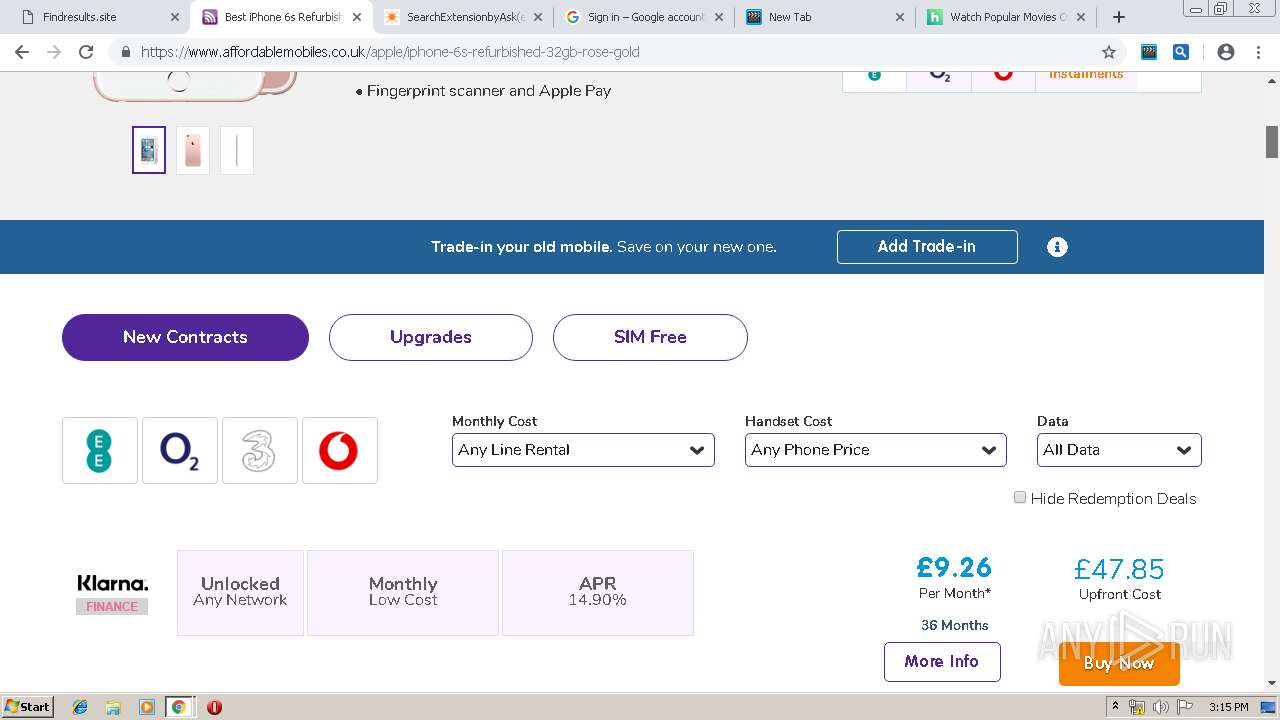
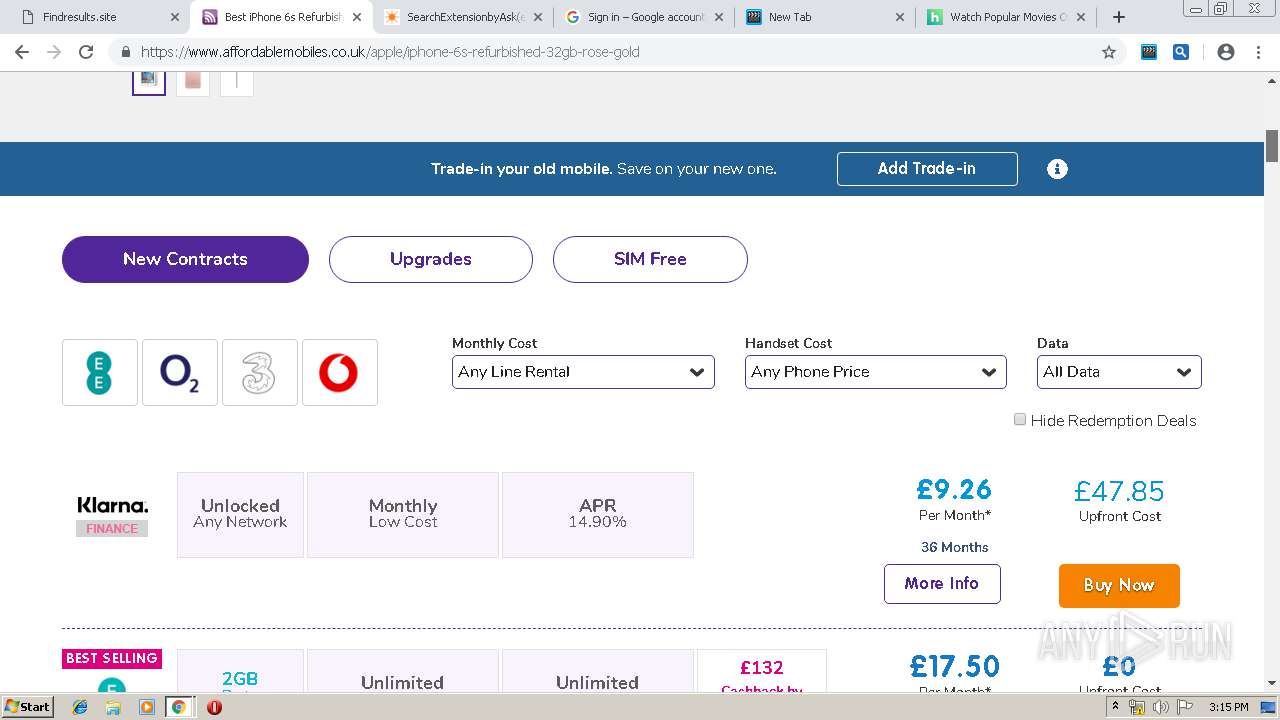
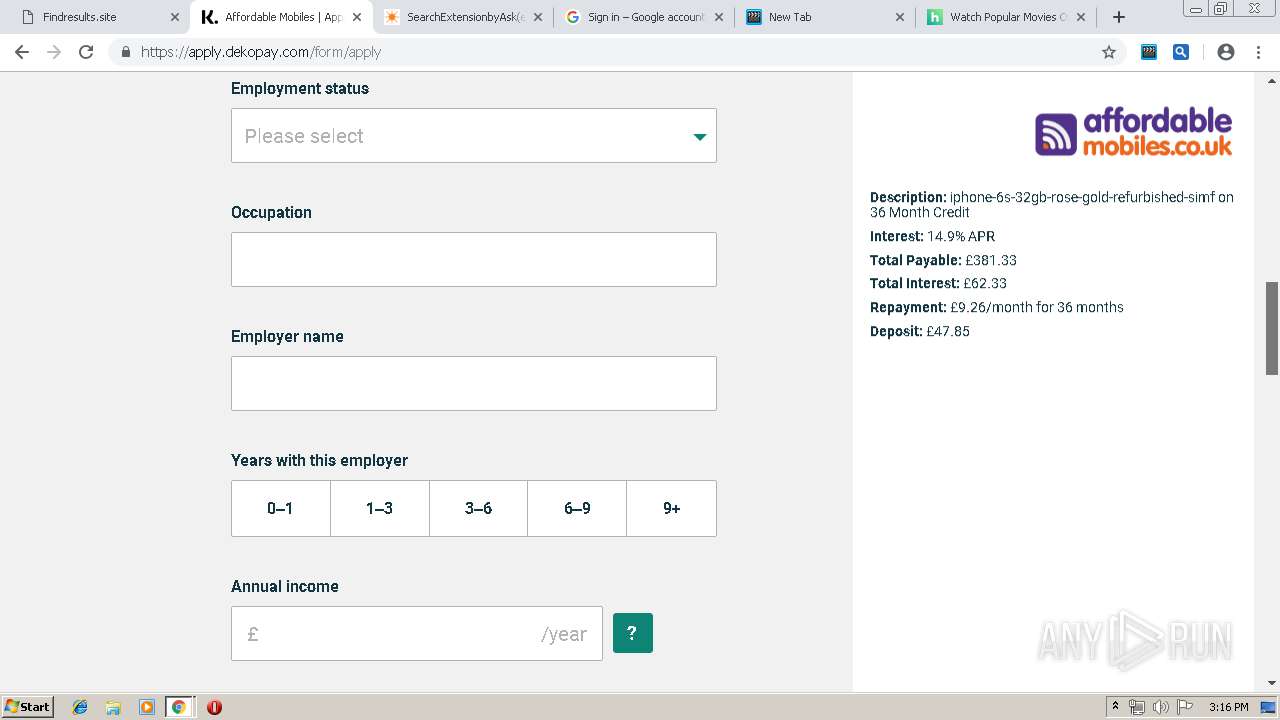
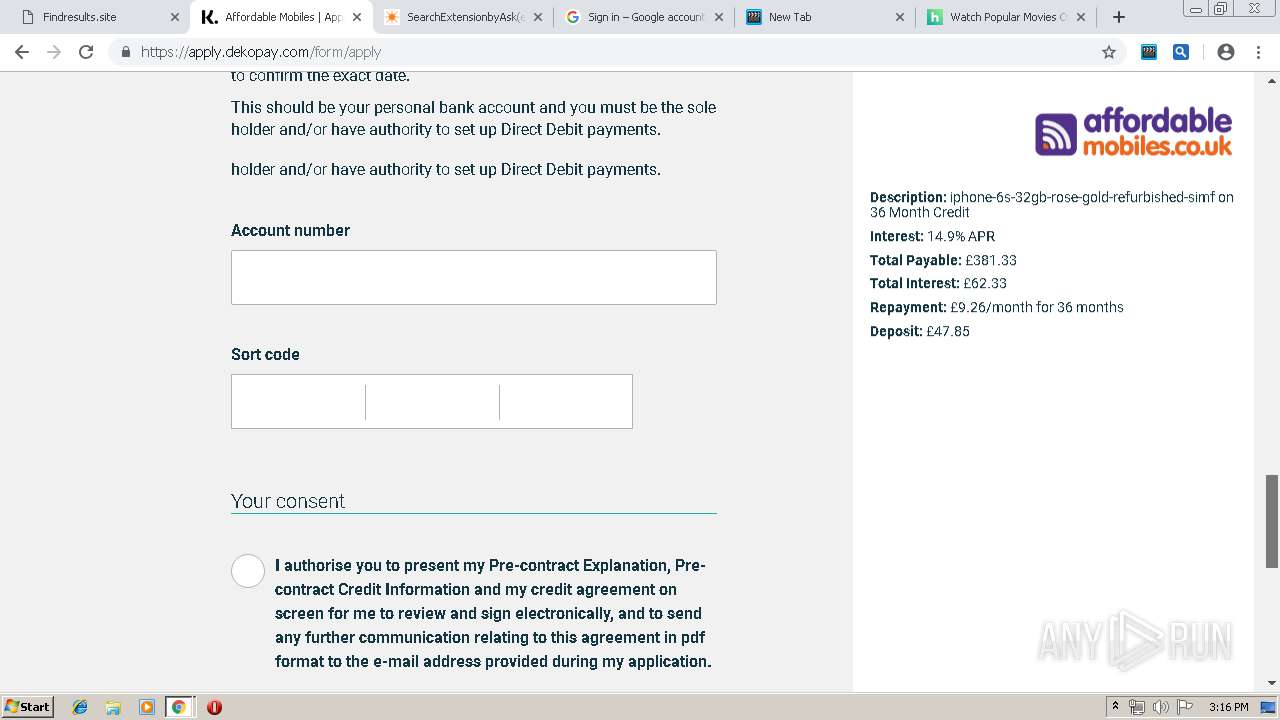
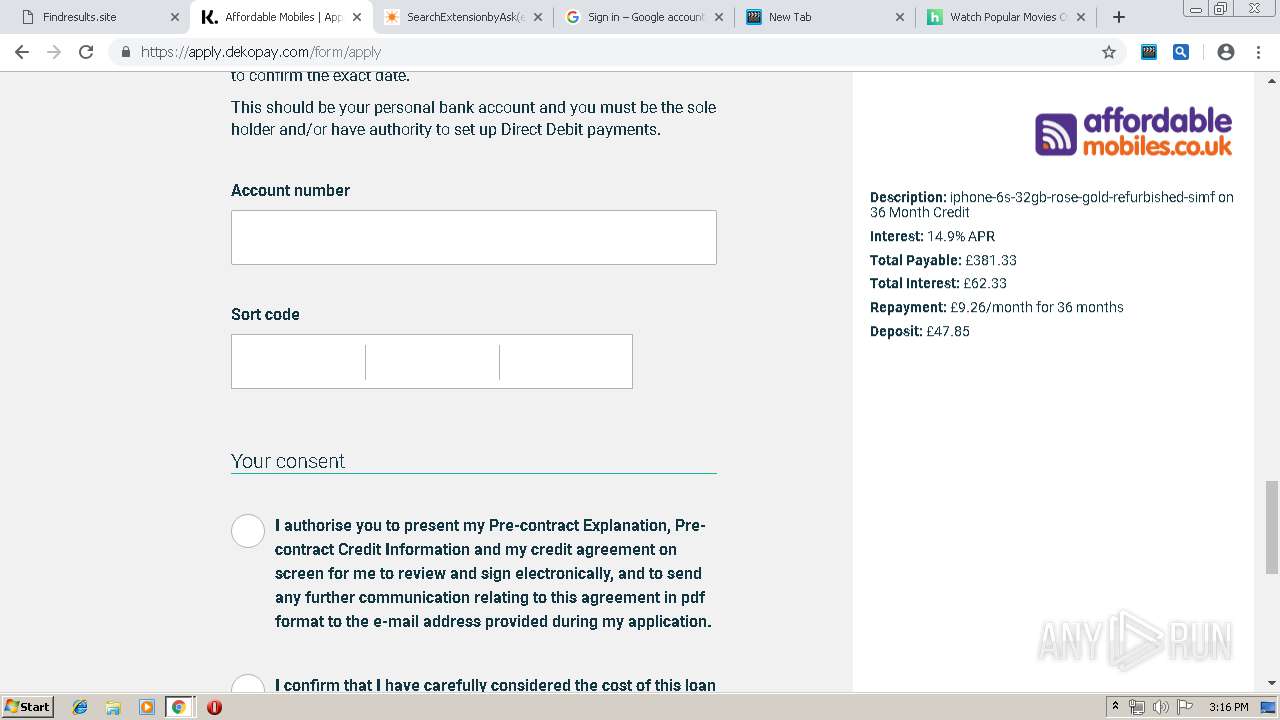
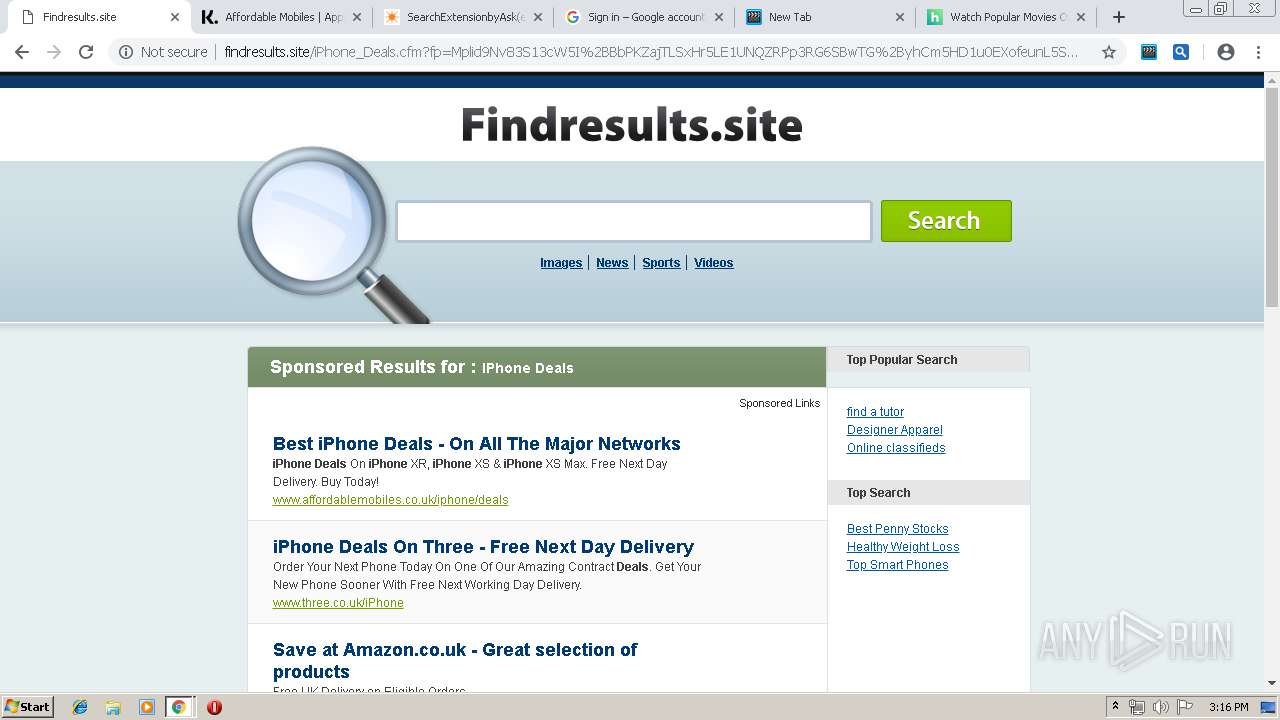
3532 | chrome.exe | GET | 200 | 208.91.196.175:80 | http://findresults.site/?fp=d6ZybVc6Nt7si%2BxAGnfWgcpHAf9SDZTnDzxaBW0MYOf%2BbMcGvtYS0HtwOOcbtLptJR30KTWTJSXDBZBMnre1IDNx0a4MAh5vYUoS6A%2BfMcZRK6dWDyZAiTj9F2dSJE97hQaWqjrWtOjS%2FPZraIs7XT4fCYuS0wrsC%2B2T6Sdjdig%3D&prvtof=Kw%2FpcFc7iO%2FkHlaJ93uhs0Zsyz3hgRlUEKr3HN1CsOY%3D&poru=oAfz3Pm34Mhcuv5i6YMmufUj7C7hlEzjU0C6meympUUerpgsFGAXWTIGbqSmixA%2B& | VG | html | 8.86 Kb | malicious |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/images/4640_2.jpg | unknown | image | 1.87 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i1.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i1.cdn-image.com/__media__/pics/747/search.gif | unknown | image | 2.42 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i2.cdn-image.com/__media__/images/4639_3.jpg | unknown | image | 1.75 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i2.cdn-image.com/__media__/images/4637_5.jpg | unknown | image | 1.93 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/images/4634_8.jpg | unknown | image | 1.33 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/images/4638_4.jpg | unknown | image | 1.80 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
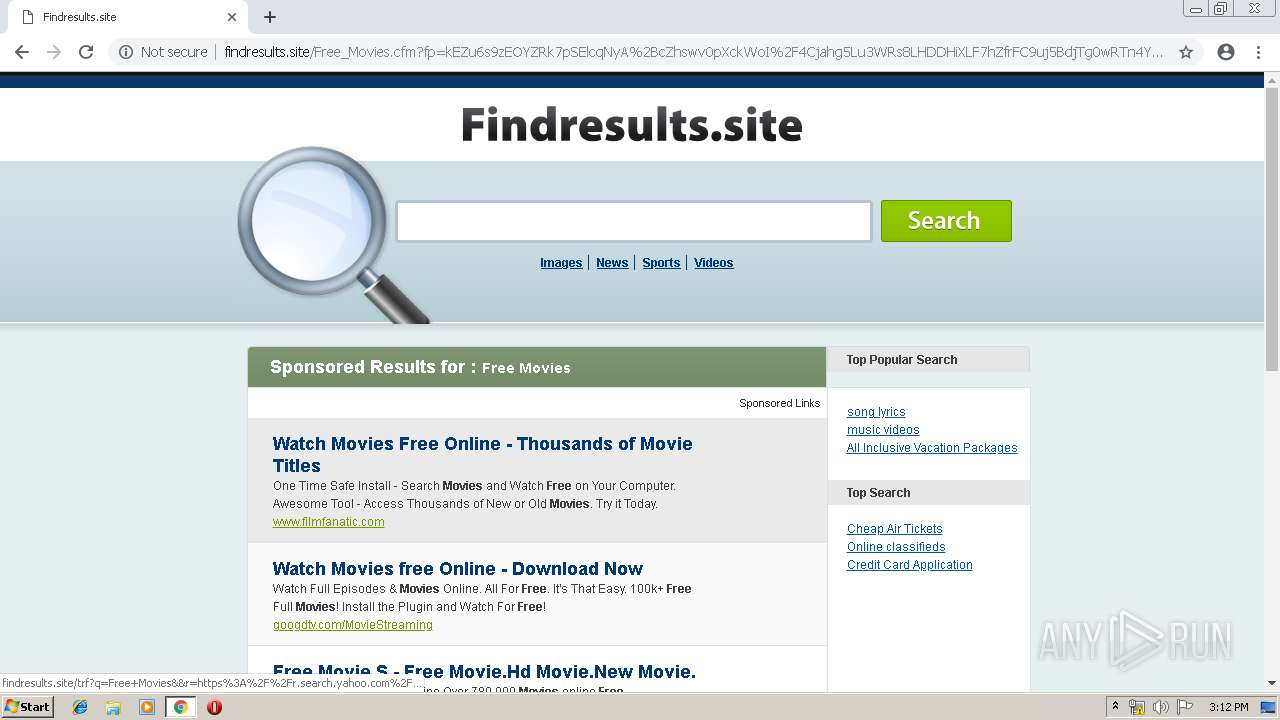
3532 | chrome.exe | 212.82.100.137:443 | r.search.yahoo.com | Yahoo! UK Services Limited | CH | shared |
3532 | chrome.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3532 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 208.91.196.175:80 | findresults.site | Confluence Networks Inc | VG | suspicious |
3532 | chrome.exe | 2.16.186.106:80 | i1.cdn-image.com | Akamai International B.V. | — | whitelisted |
3532 | chrome.exe | 2.16.186.64:80 | i1.cdn-image.com | Akamai International B.V. | — | whitelisted |
3532 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.23.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
findresults.site |
| malicious |
accounts.google.com |
| shared |
i1.cdn-image.com |
| whitelisted |
i3.cdn-image.com |
| whitelisted |
i4.cdn-image.com |
| whitelisted |
i2.cdn-image.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.findresults.site |
| malicious |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3532 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |