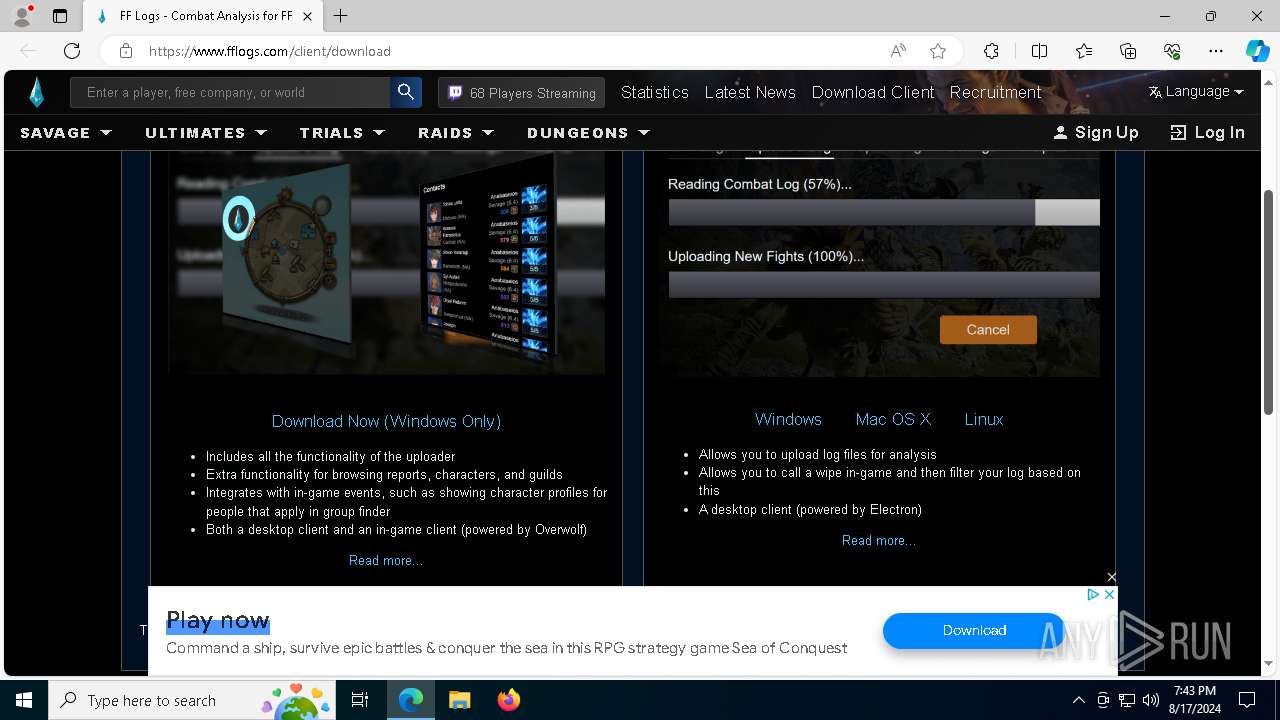
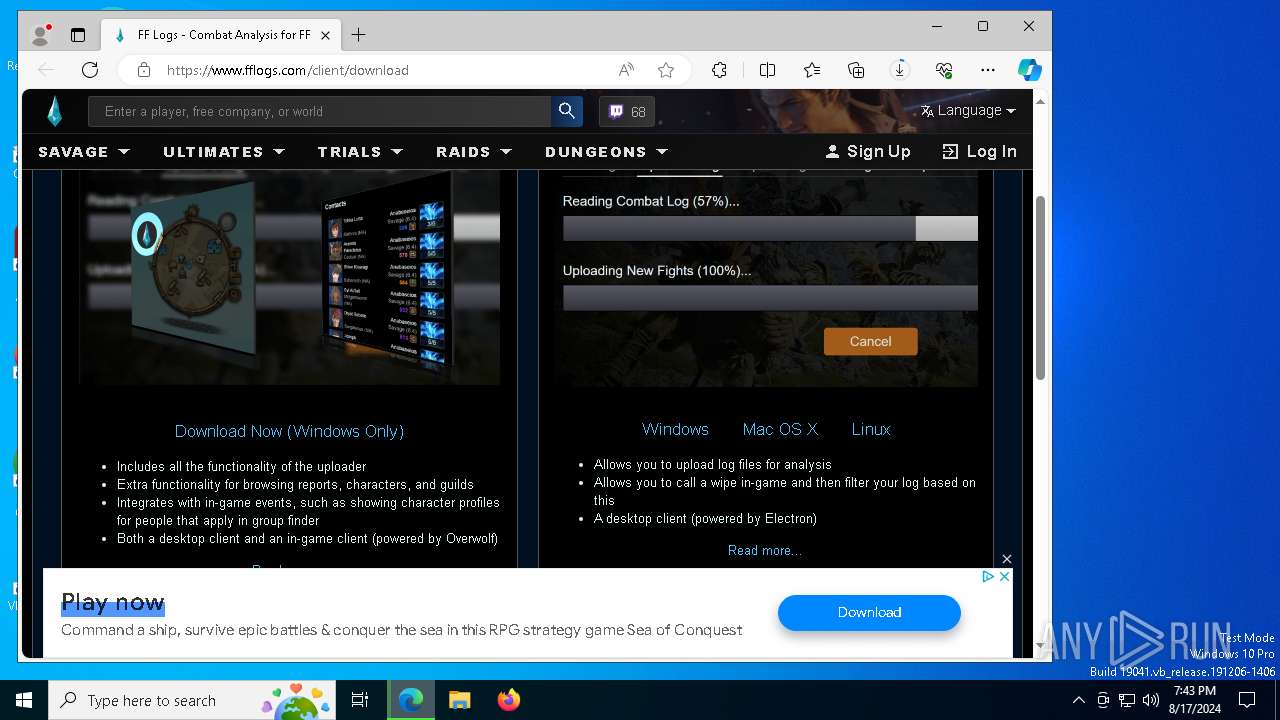
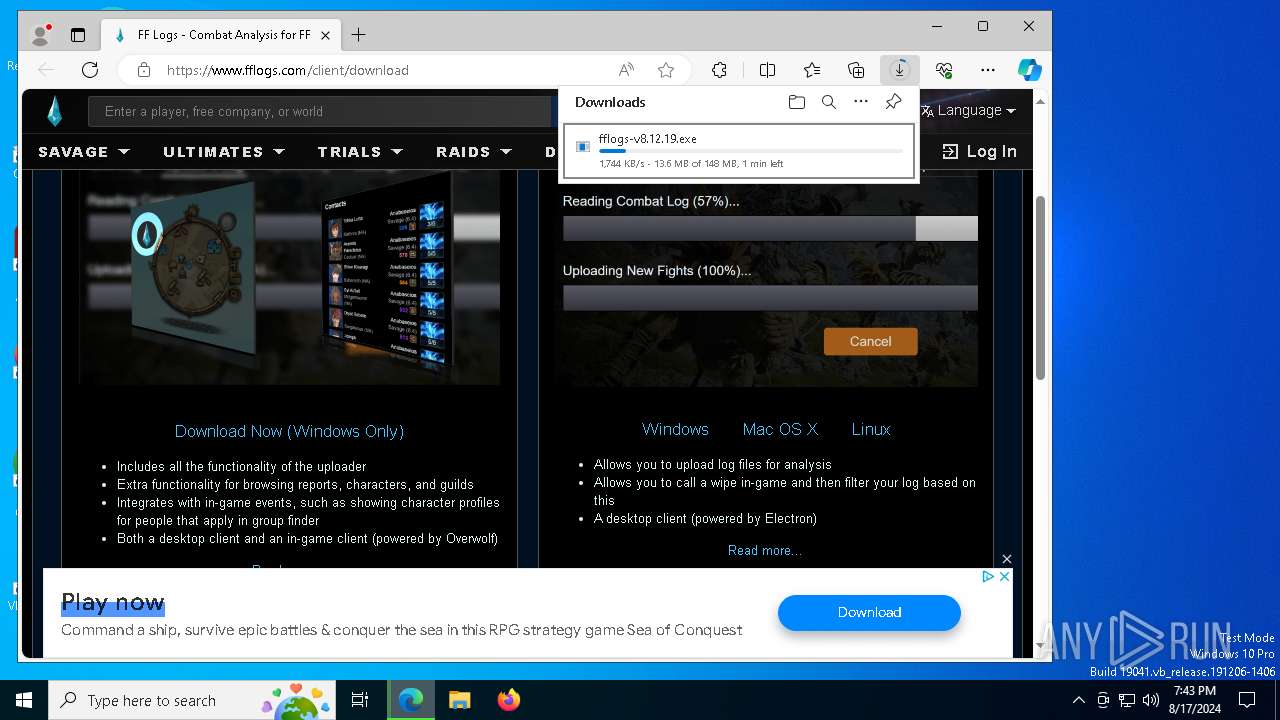
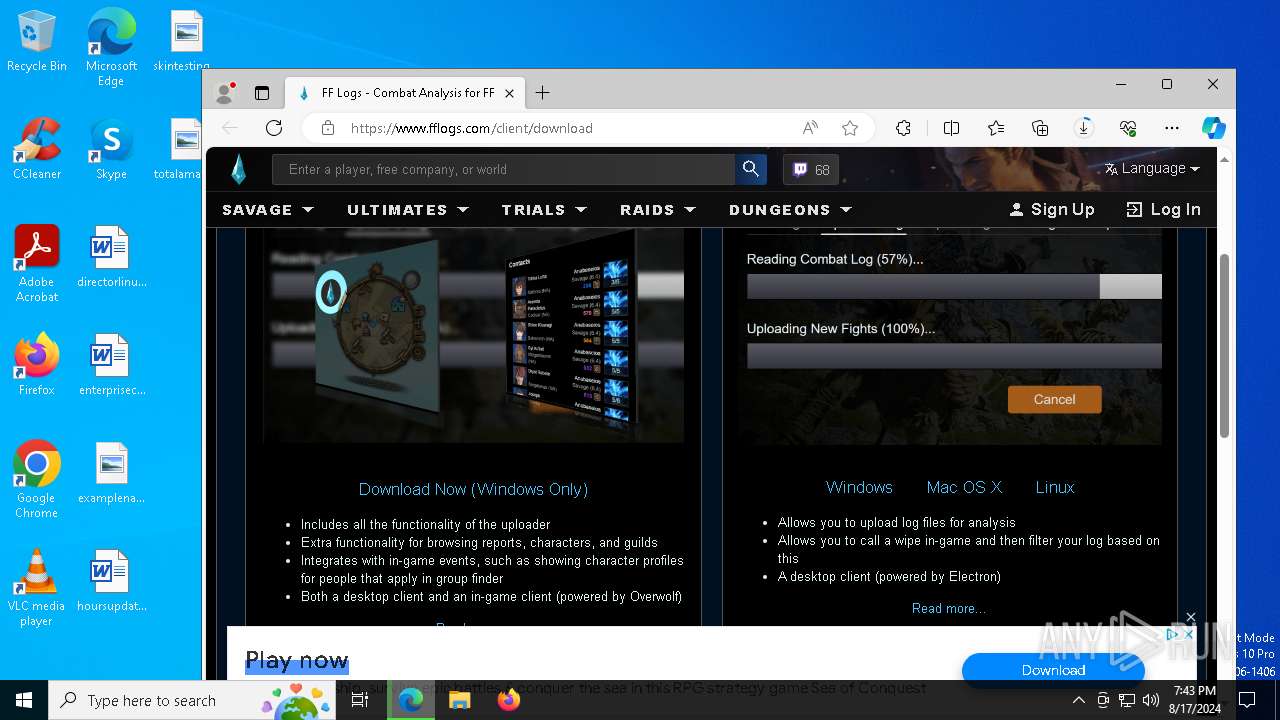
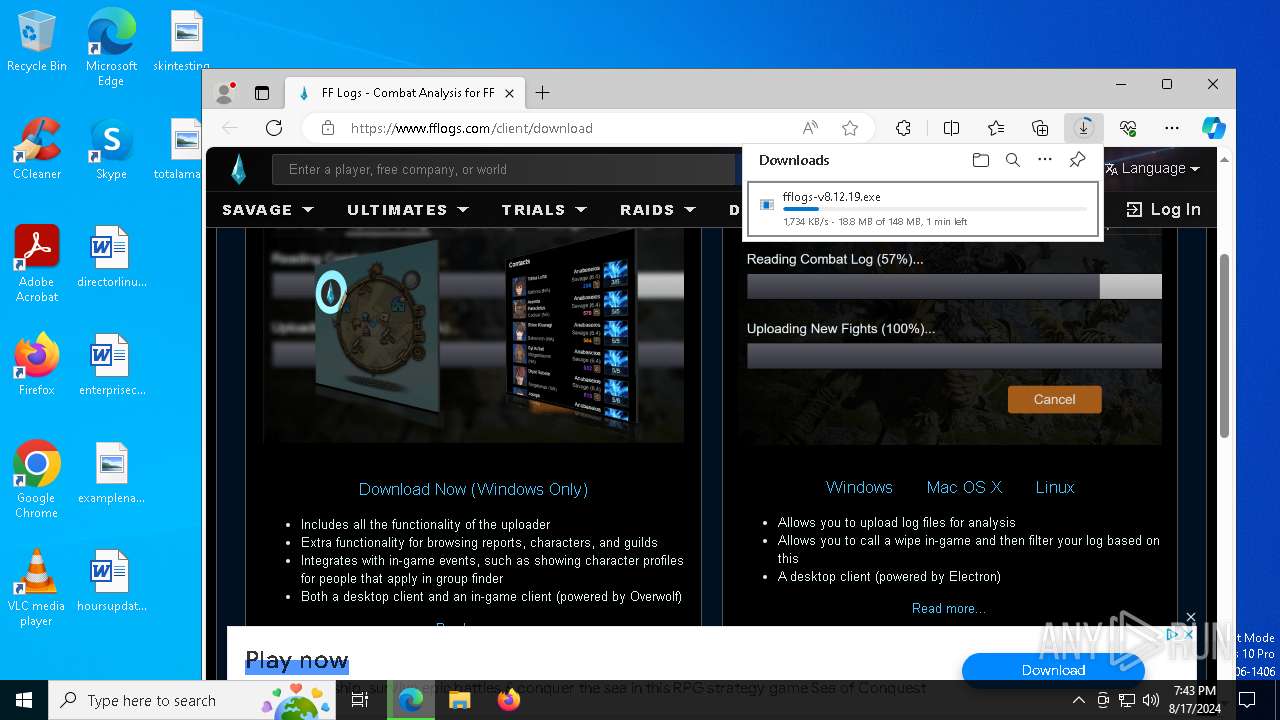
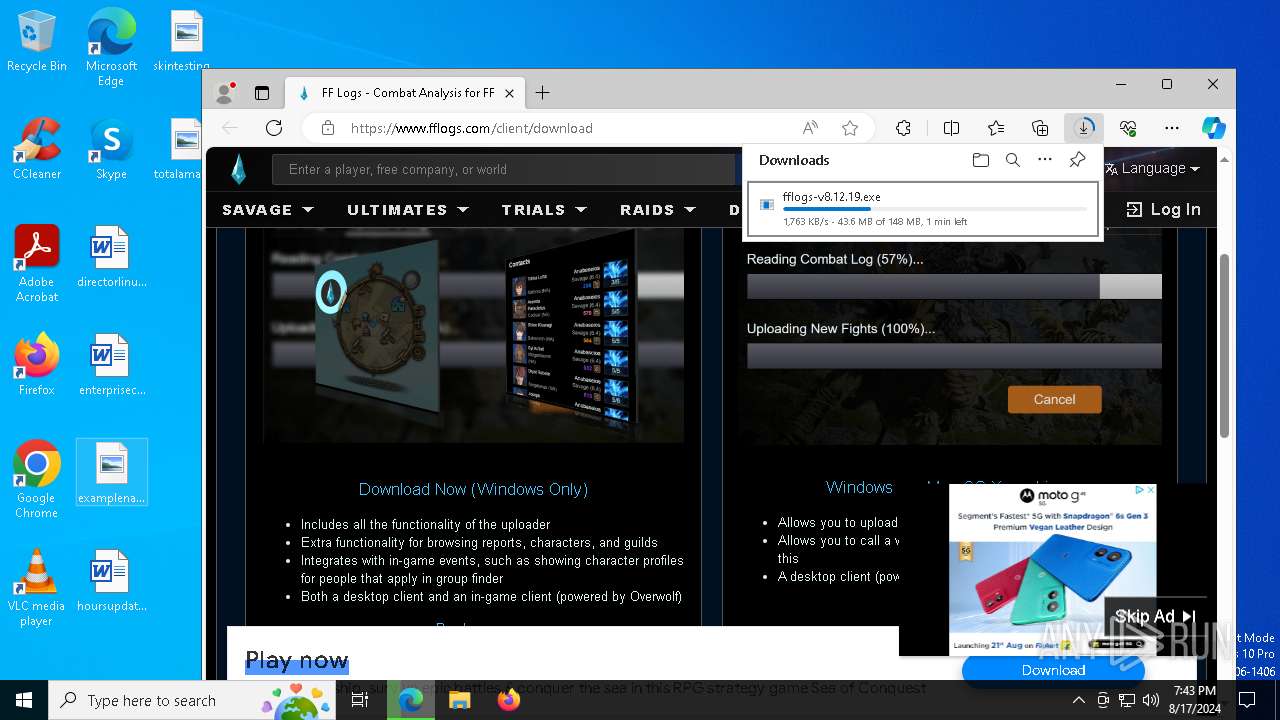
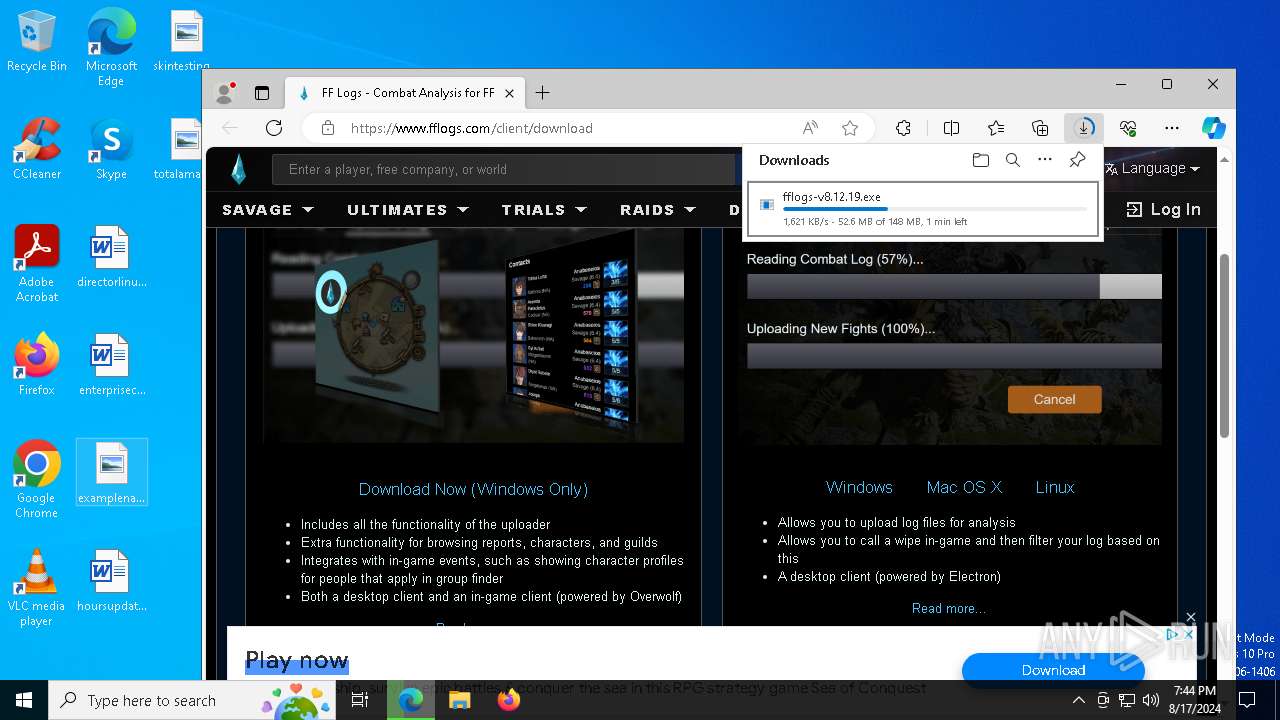
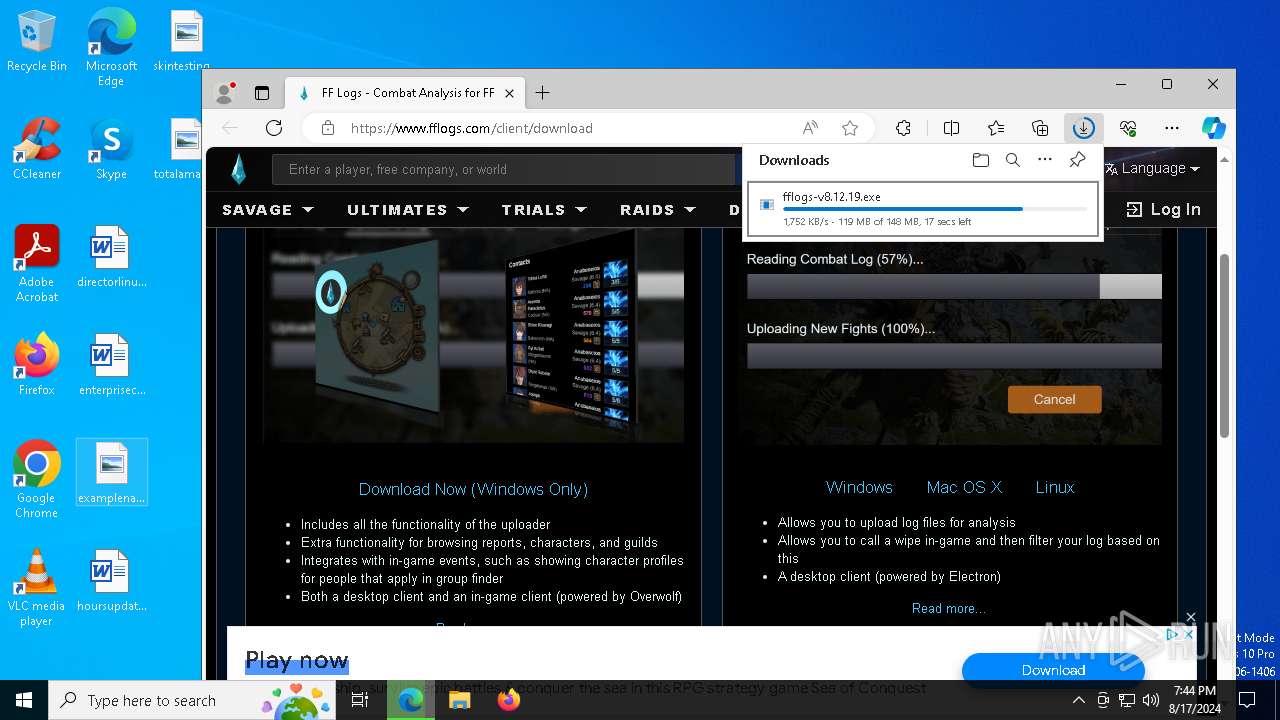
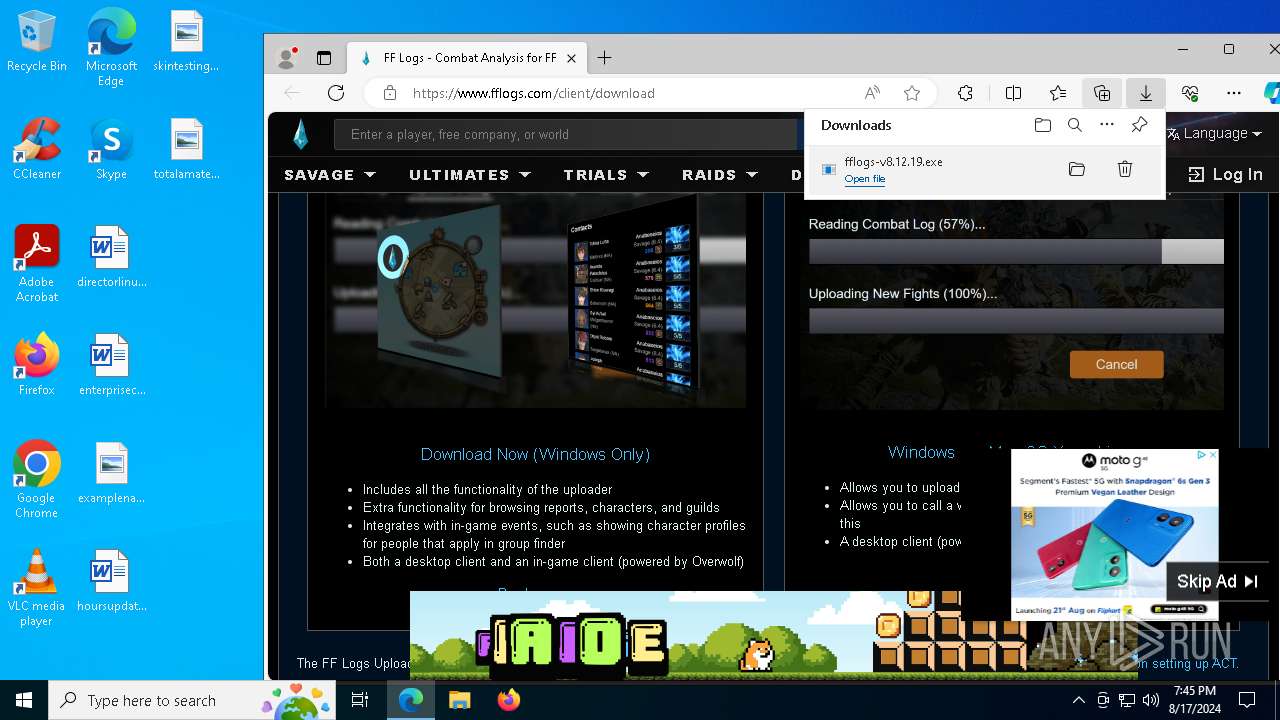
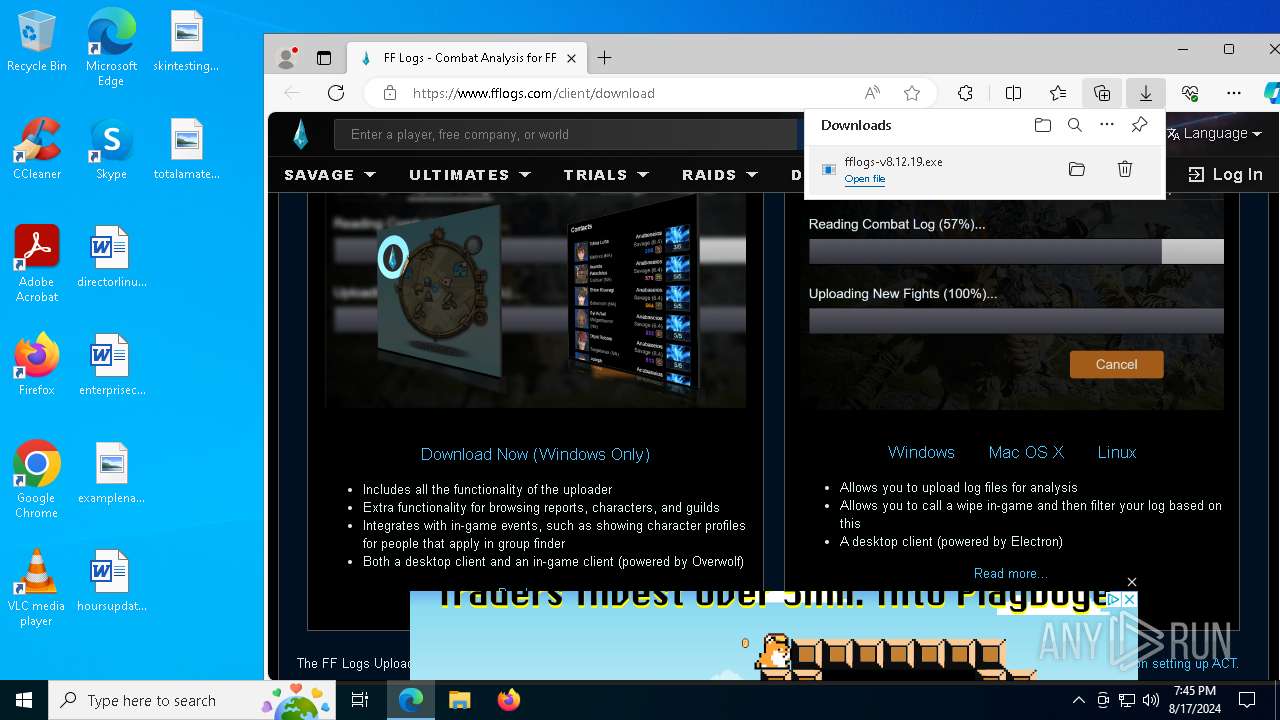
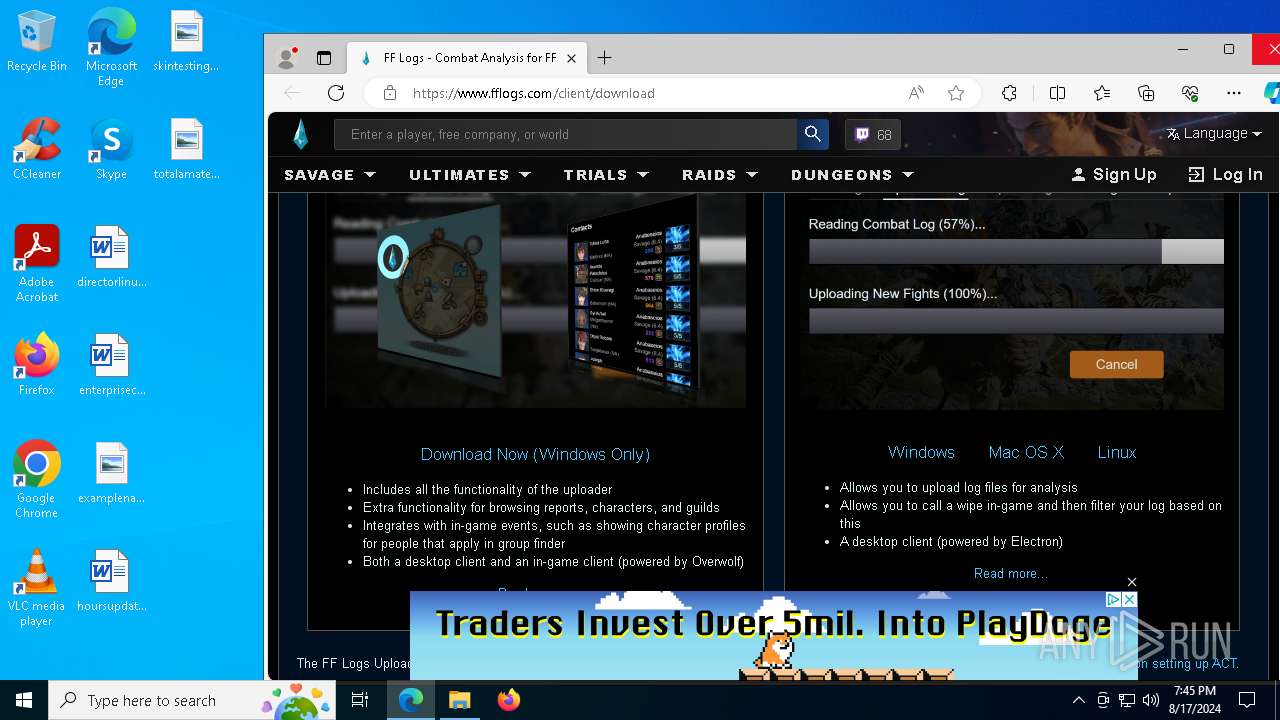
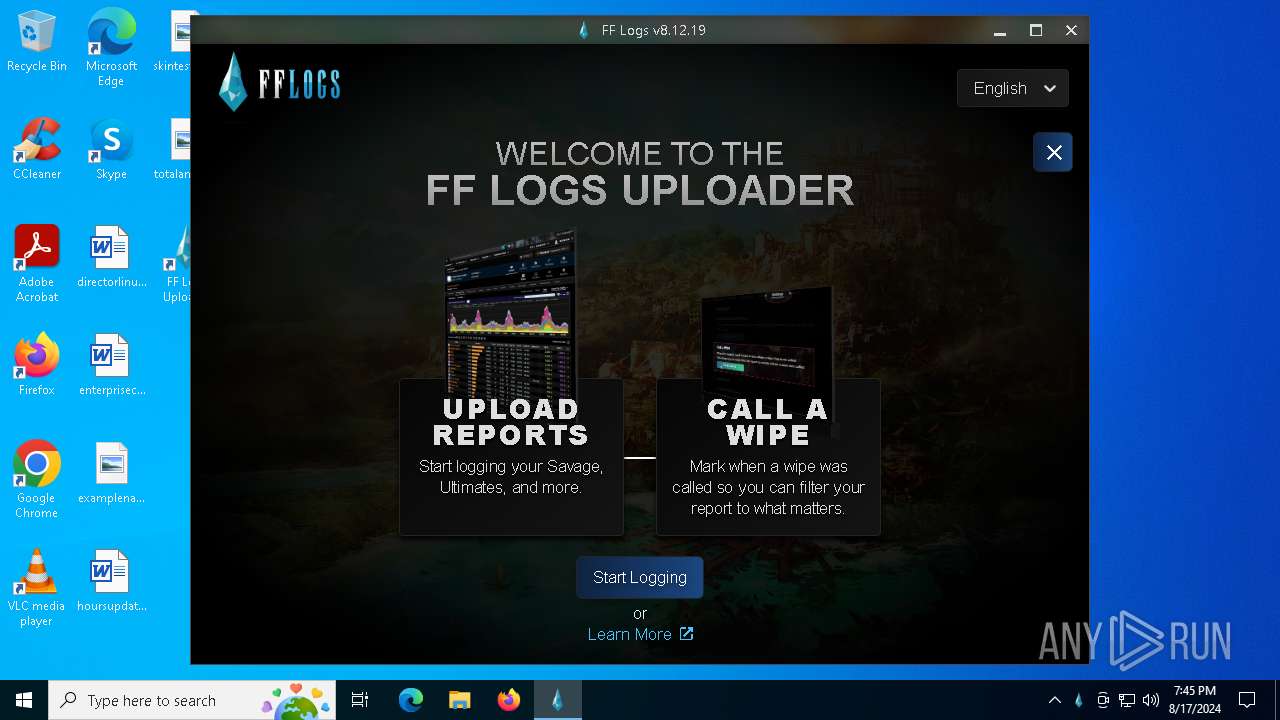
| URL: | https://www.fflogs.com/client/download |
| Full analysis: | https://app.any.run/tasks/d9427902-2f46-4deb-9e0b-18ec0b6ea855 |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2024, 19:43:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | E0B80D8A2A51A75A85A6AA2B3D0806B2 |
| SHA1: | A0ACCAC18B27F82A77EC57860C60A35E04F6769C |
| SHA256: | 7C02EDA40E48CC689DE44D39BEF13A43BA0410494DC7582525112DEB5645E211 |
| SSDEEP: | 3:N8DSLfECMGK2JMuwz:2OLVJMZz |
MALICIOUS
Changes powershell execution policy (Bypass)
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 6396)
Bypass execution policy to execute commands
- powershell.exe (PID: 6236)
- powershell.exe (PID: 2876)
- powershell.exe (PID: 8004)
Changes the autorun value in the registry
- FF Logs Uploader.exe (PID: 5248)
SUSPICIOUS
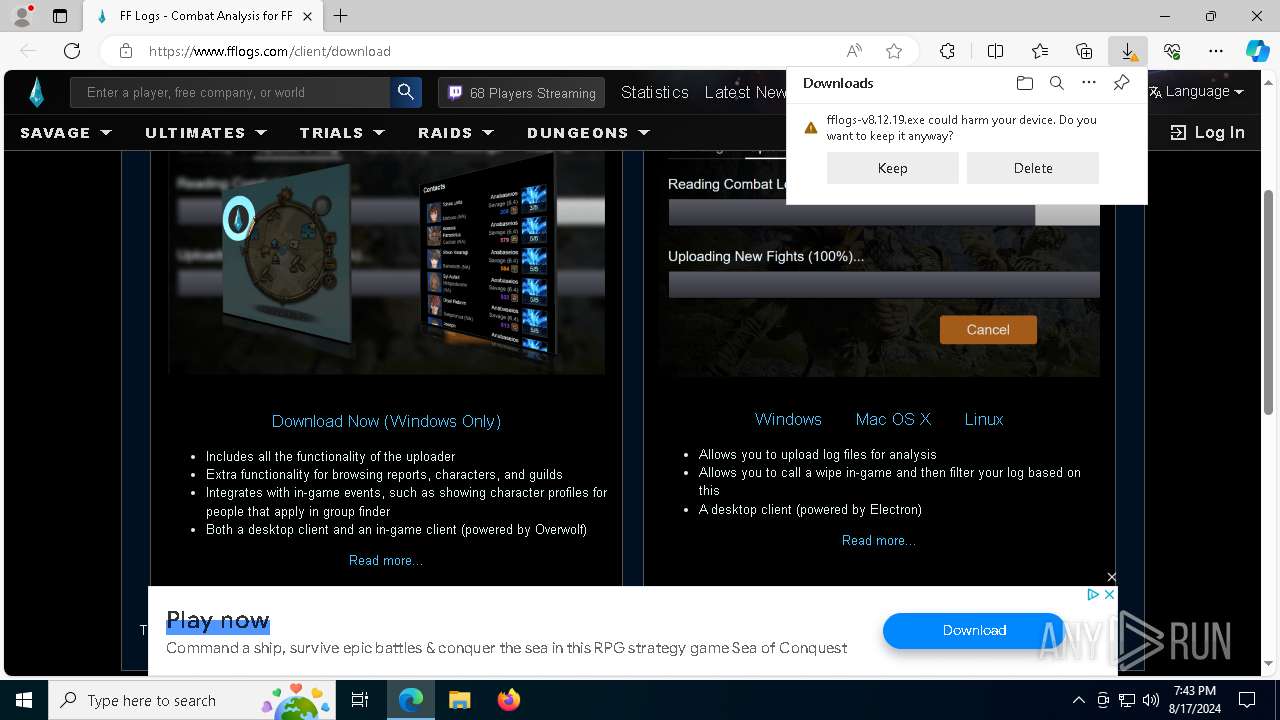
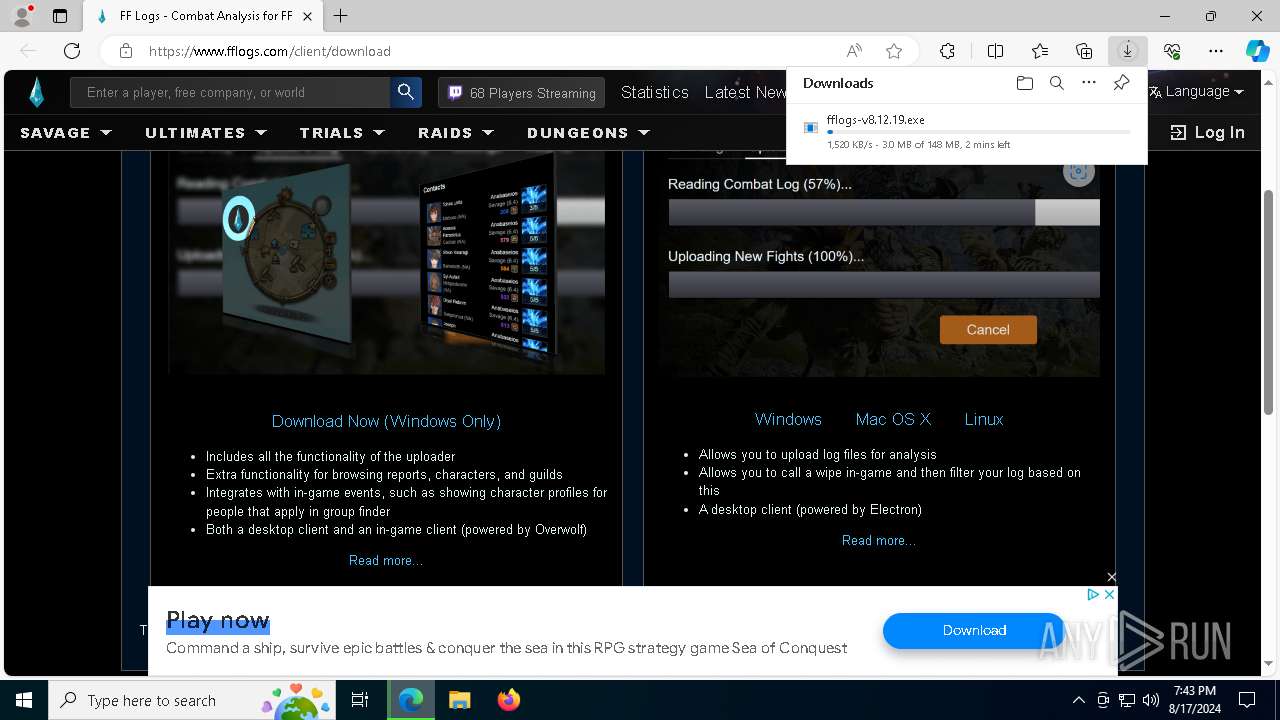
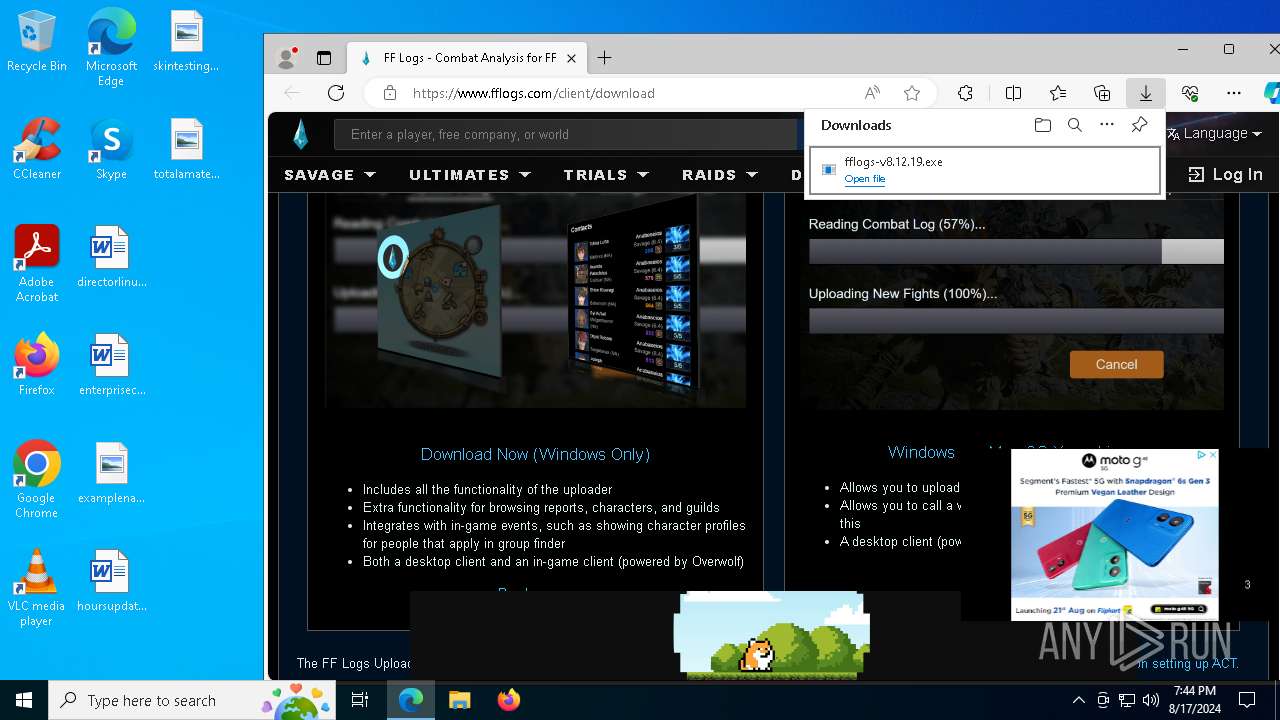
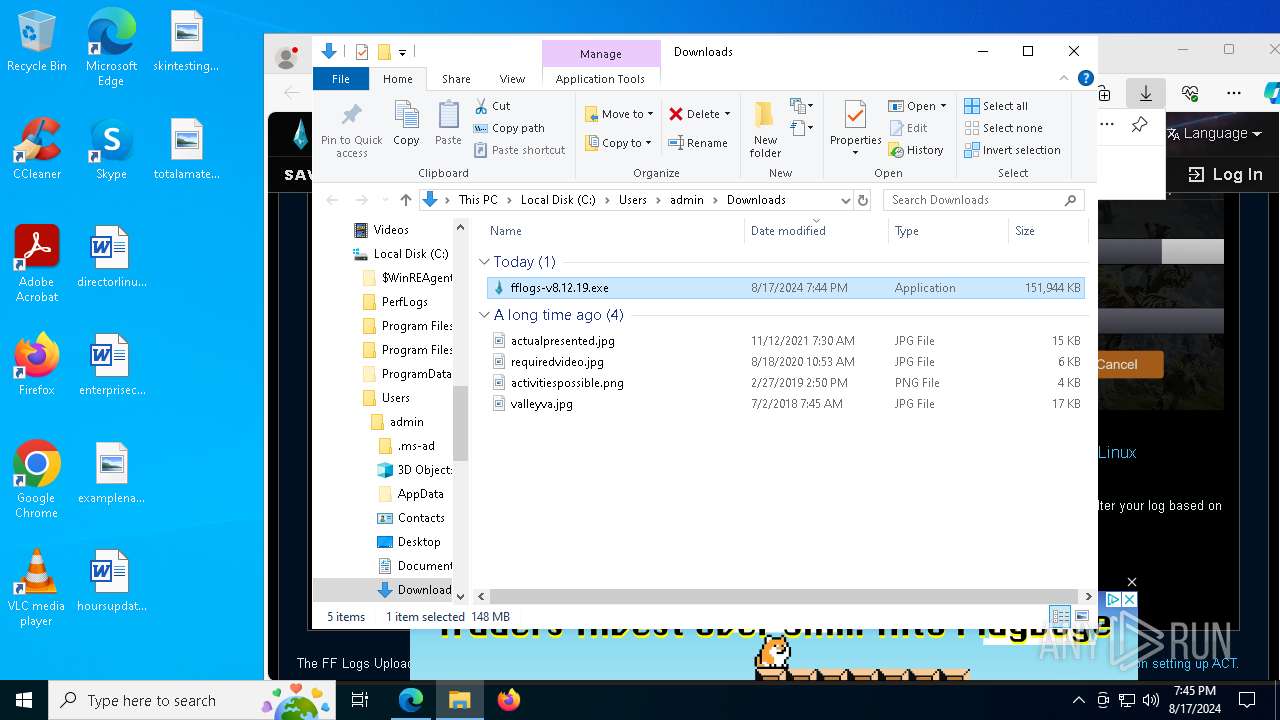
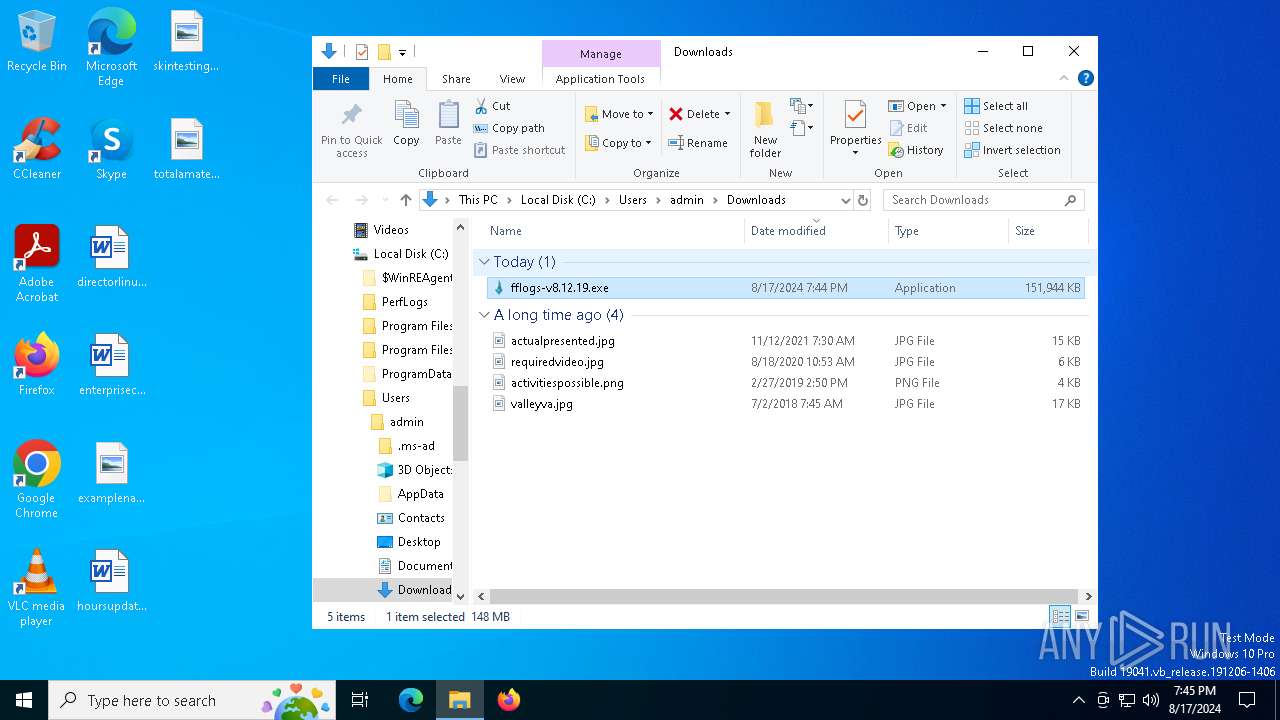
Drops the executable file immediately after the start
- fflogs-v8.12.19.exe (PID: 5152)
- fflogs-v8.12.19.exe (PID: 7288)
- csc.exe (PID: 6916)
The process creates files with name similar to system file names
- fflogs-v8.12.19.exe (PID: 5152)
- fflogs-v8.12.19.exe (PID: 7288)
Executable content was dropped or overwritten
- fflogs-v8.12.19.exe (PID: 5152)
- fflogs-v8.12.19.exe (PID: 7288)
- csc.exe (PID: 6916)
Executes application which crashes
- fflogs-v8.12.19.exe (PID: 5152)
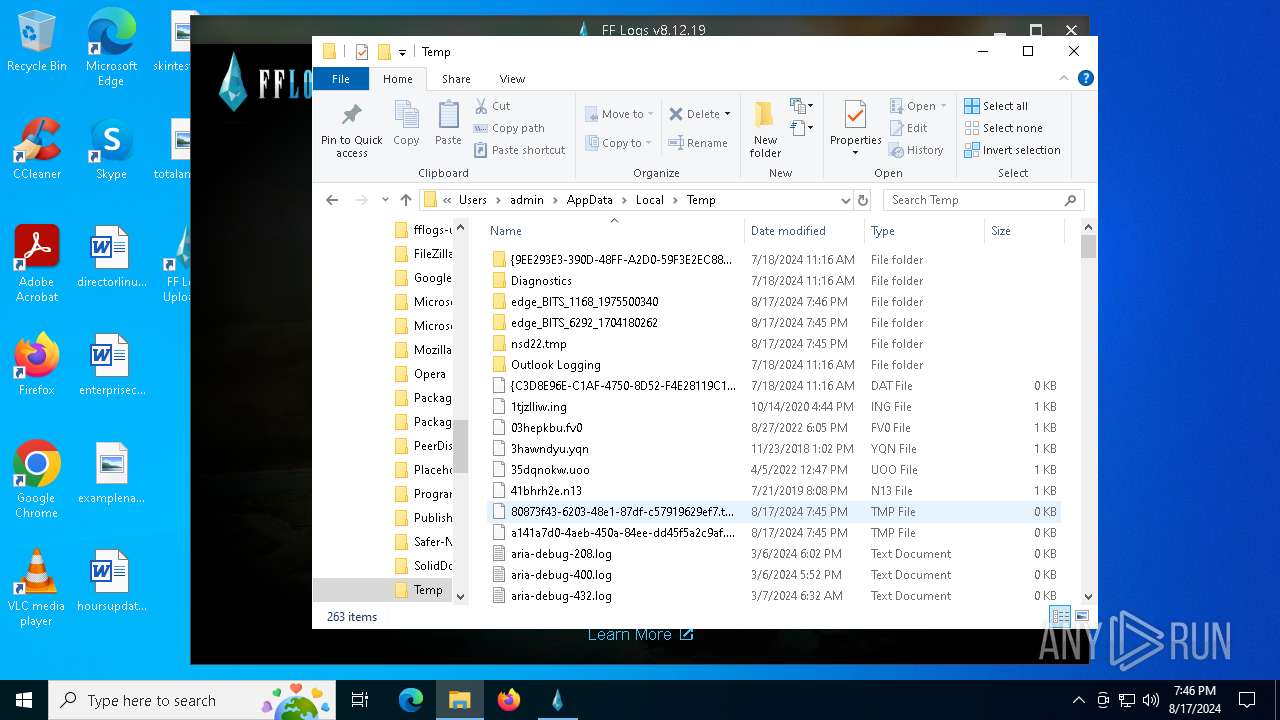
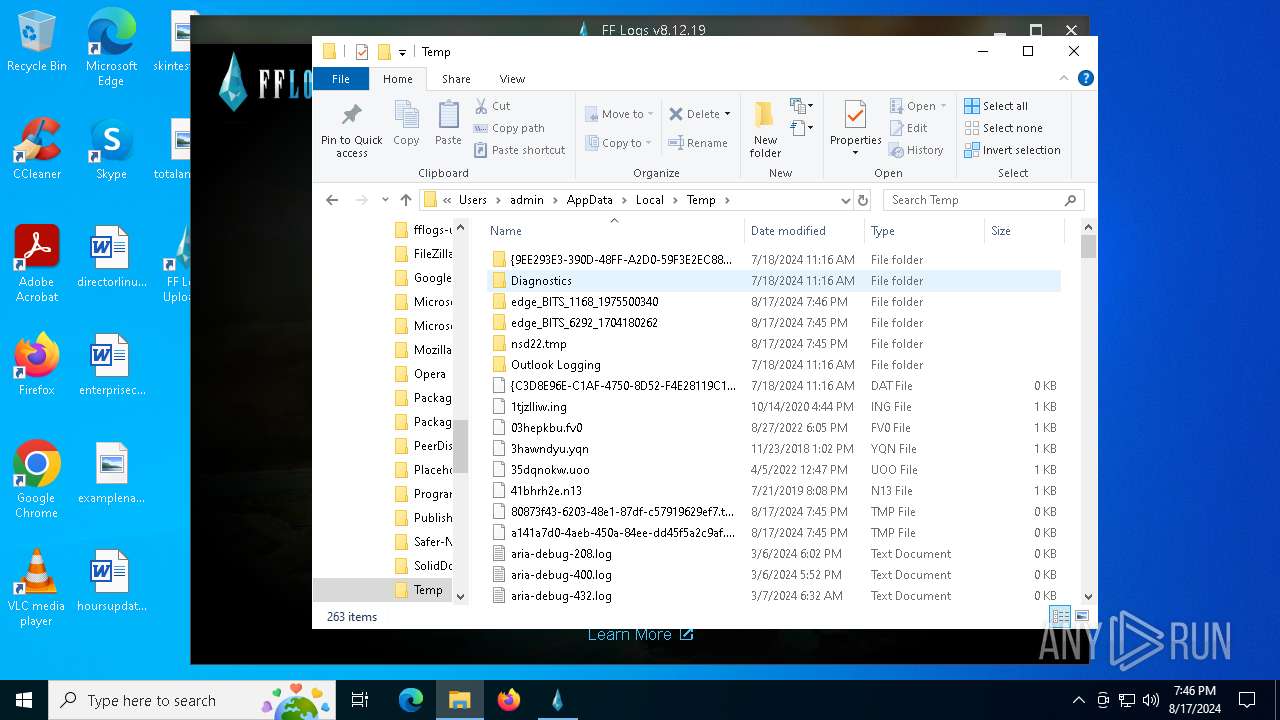
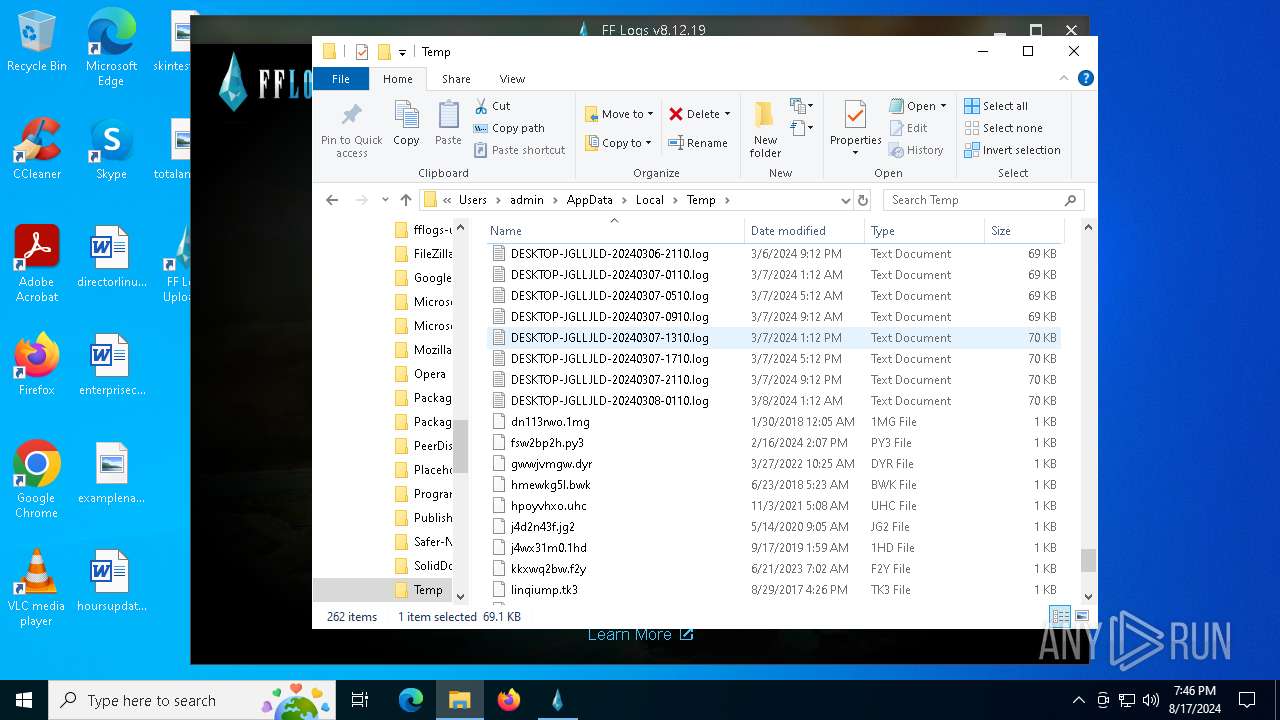
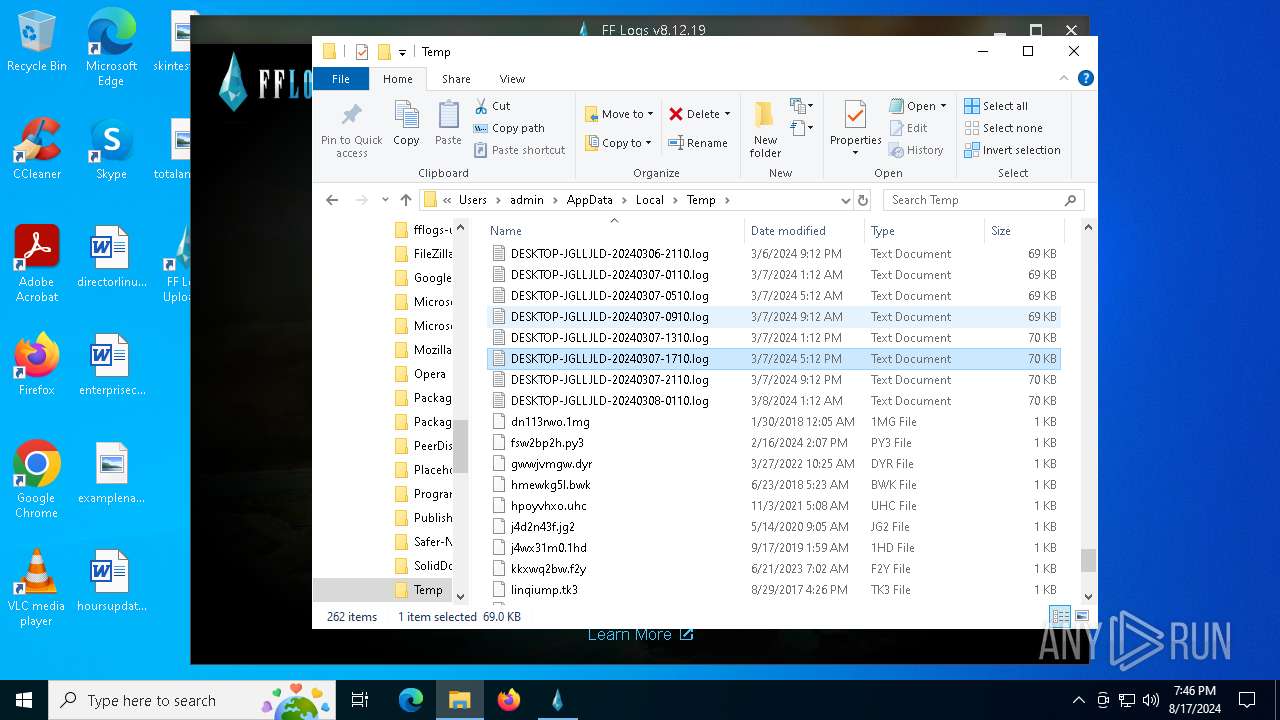
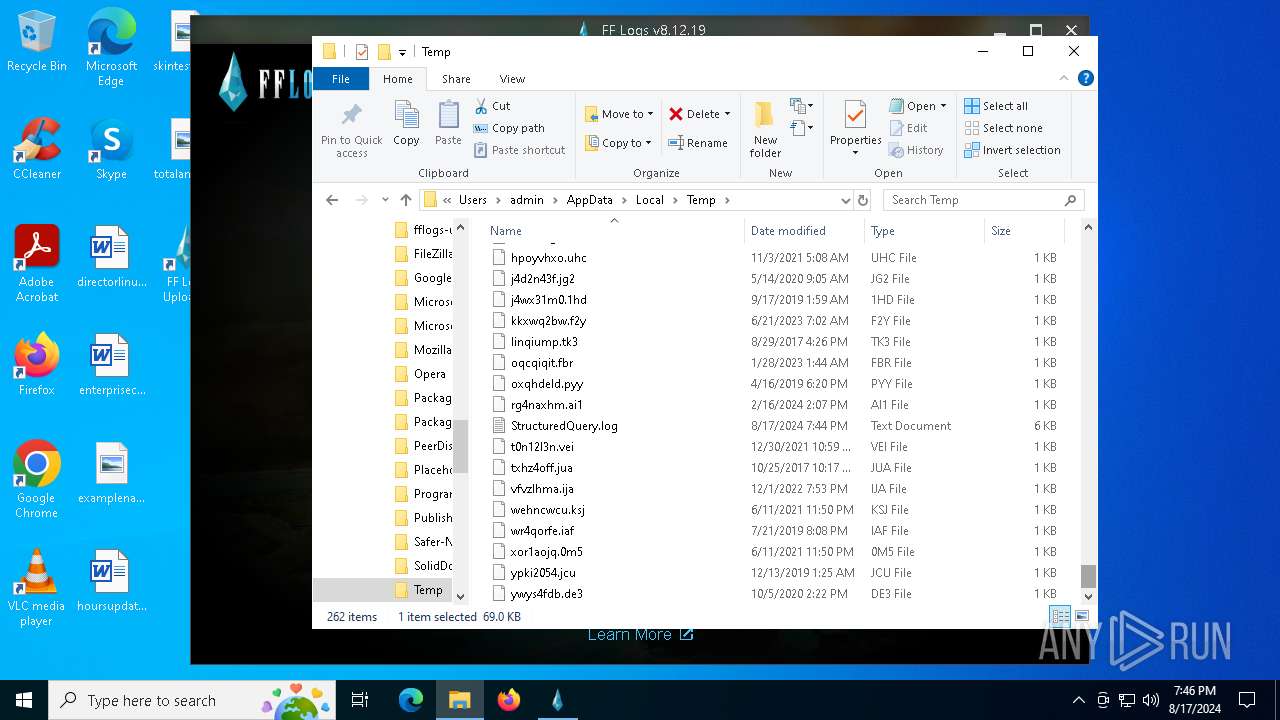
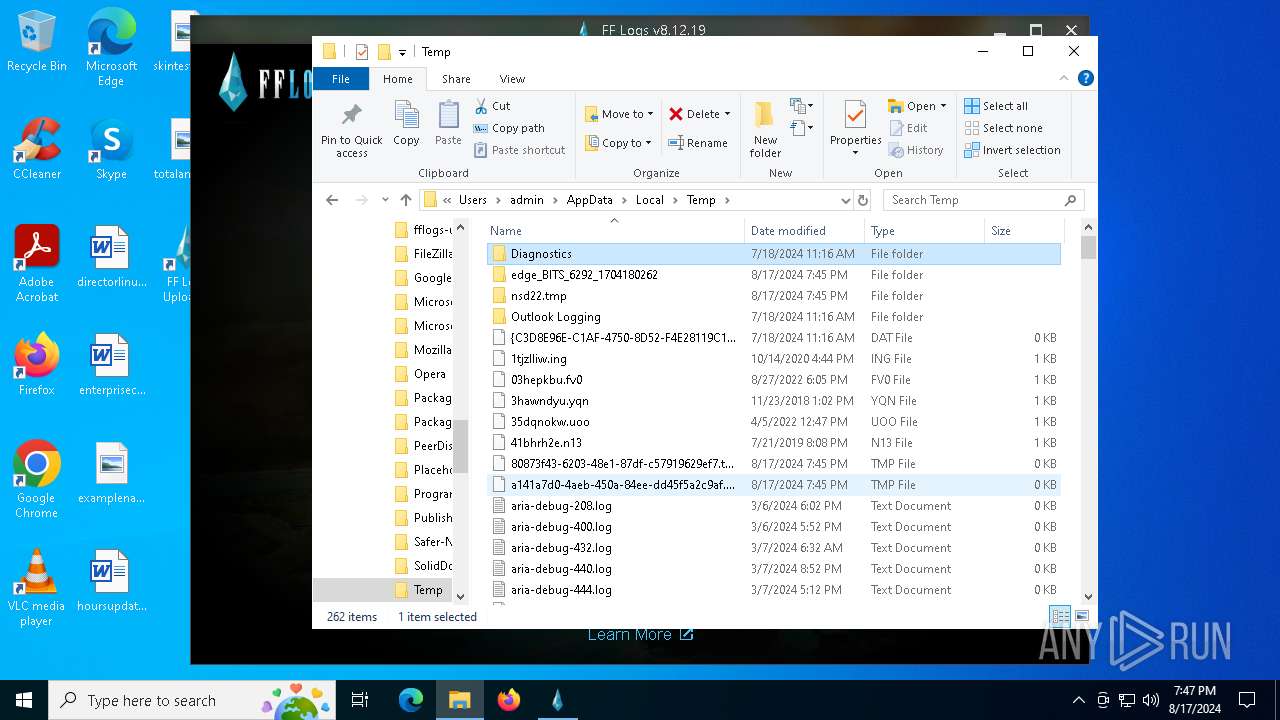
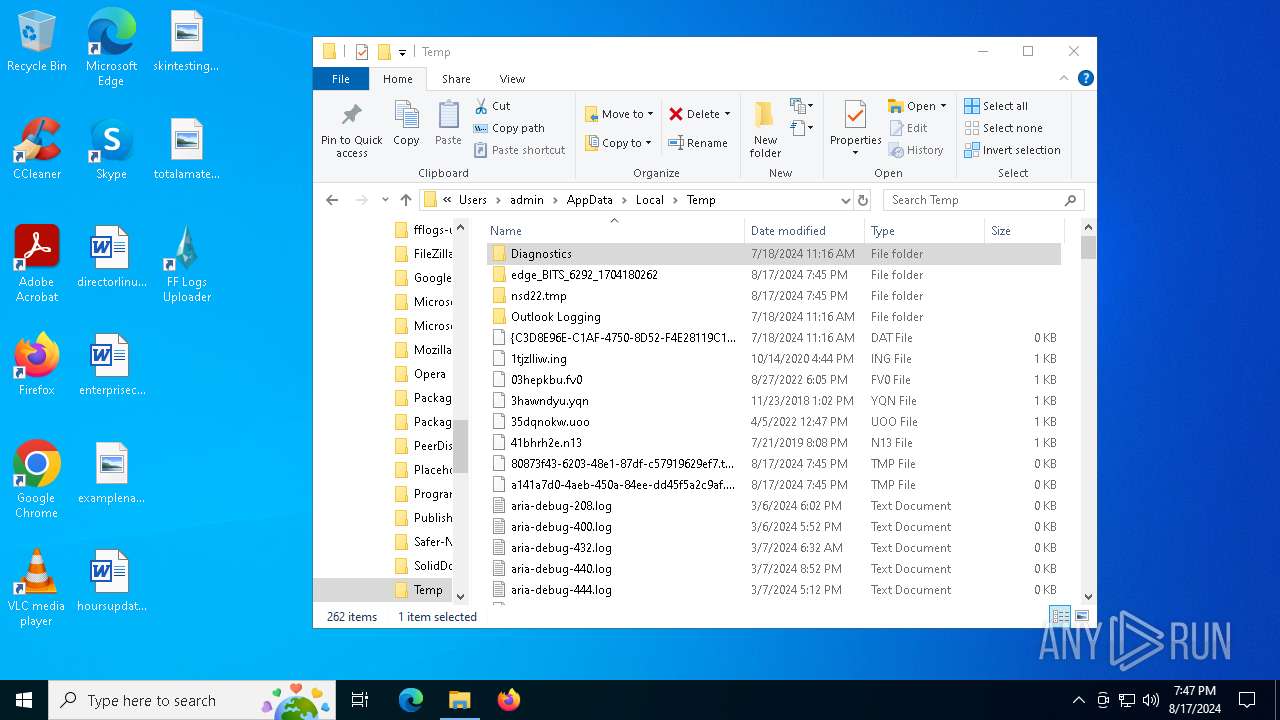
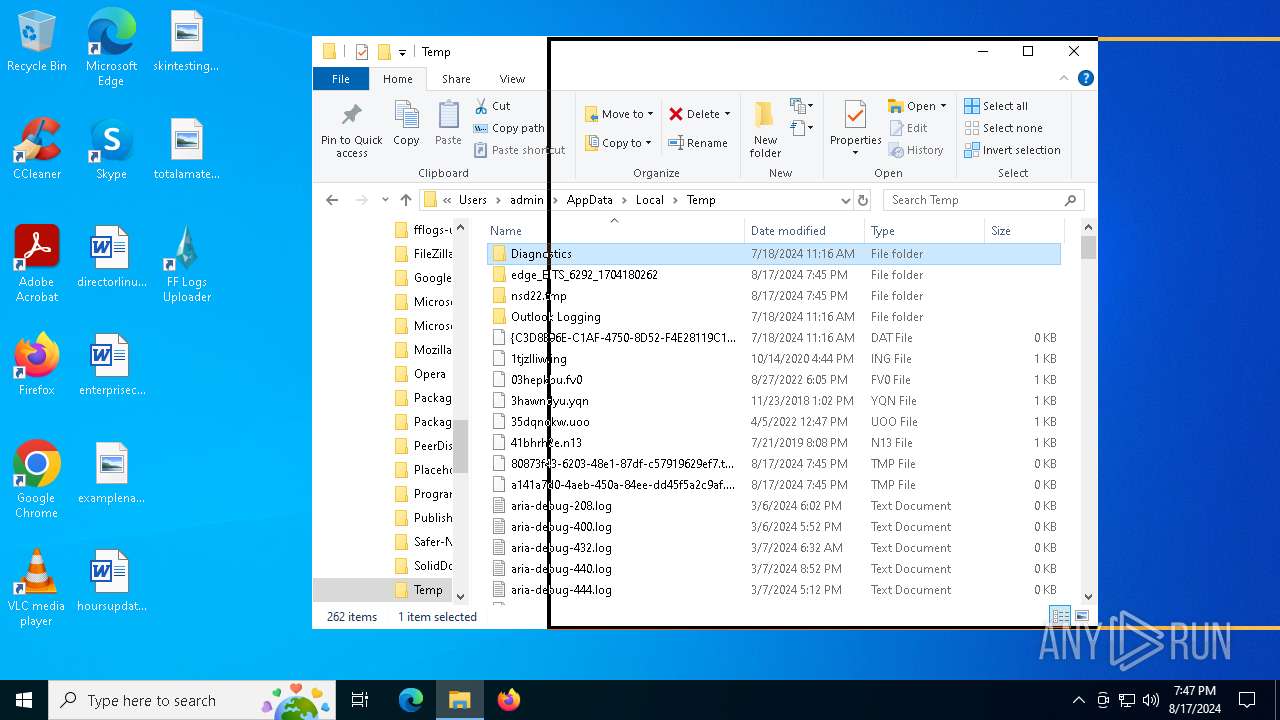
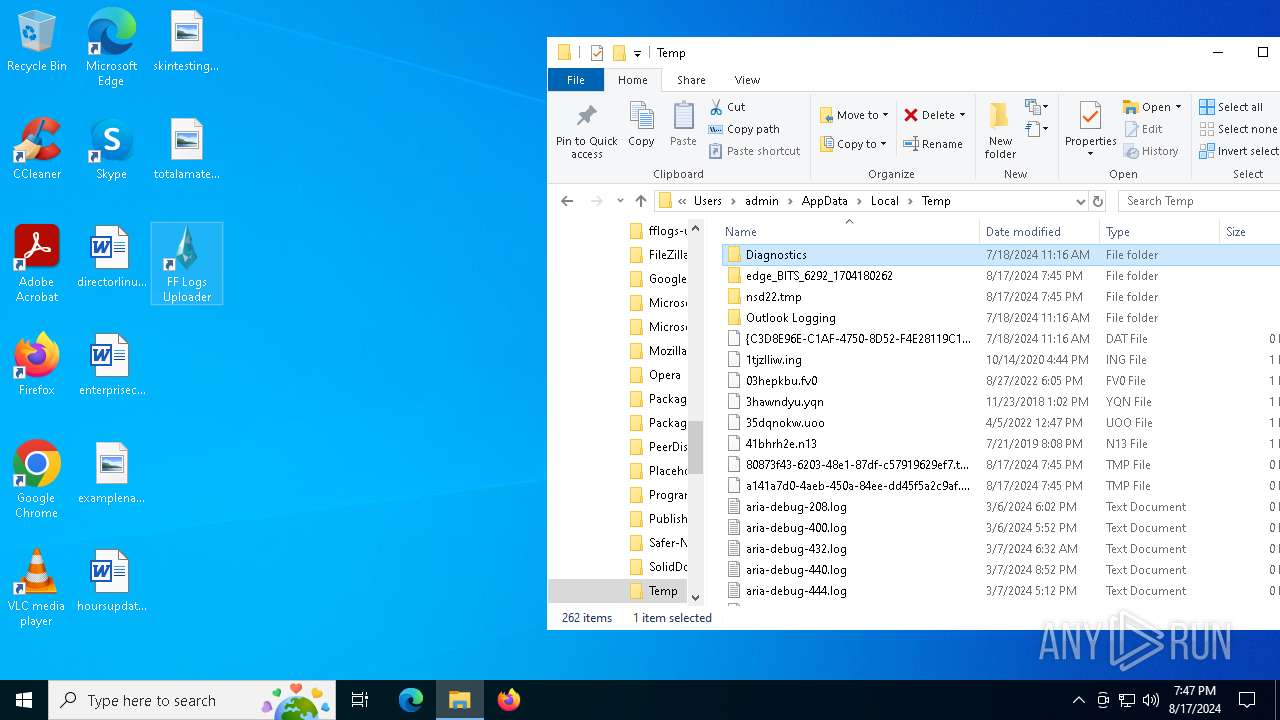
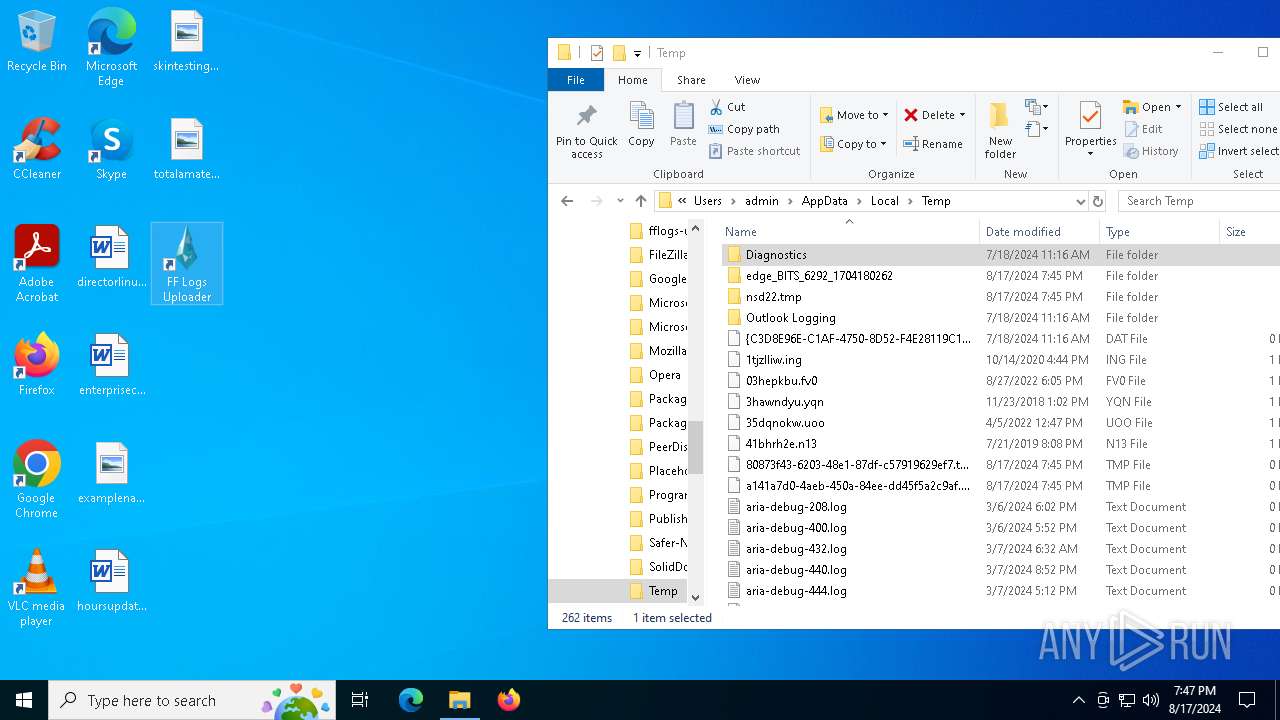
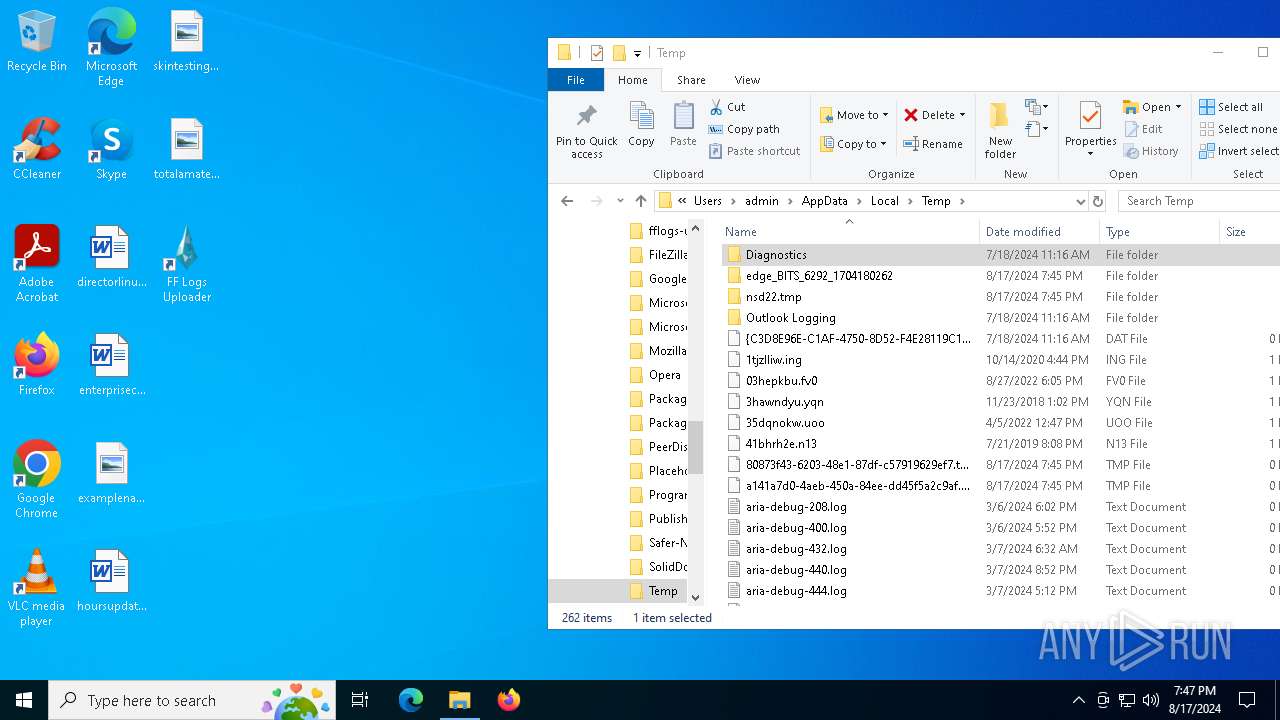
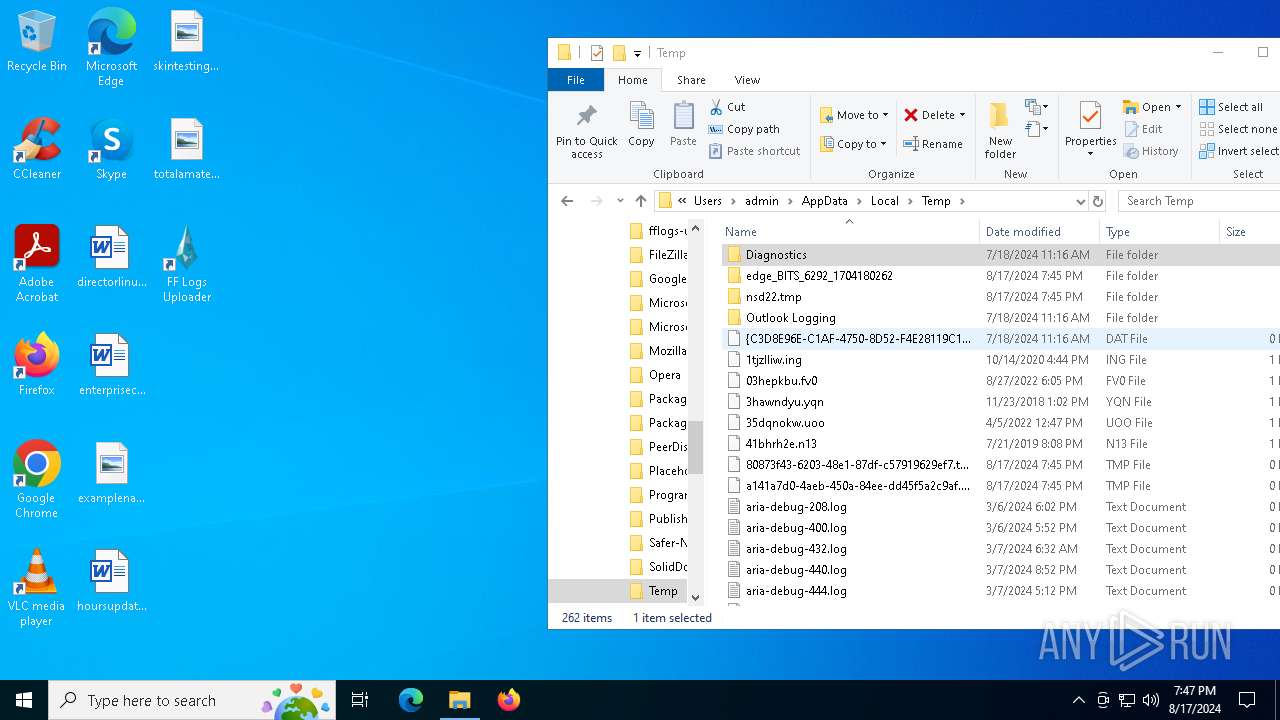
Malware-specific behavior (creating "System.dll" in Temp)
- fflogs-v8.12.19.exe (PID: 7288)
Starts CMD.EXE for commands execution
- fflogs-v8.12.19.exe (PID: 7288)
Get information on the list of running processes
- fflogs-v8.12.19.exe (PID: 7288)
- cmd.exe (PID: 3076)
Application launched itself
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 6396)
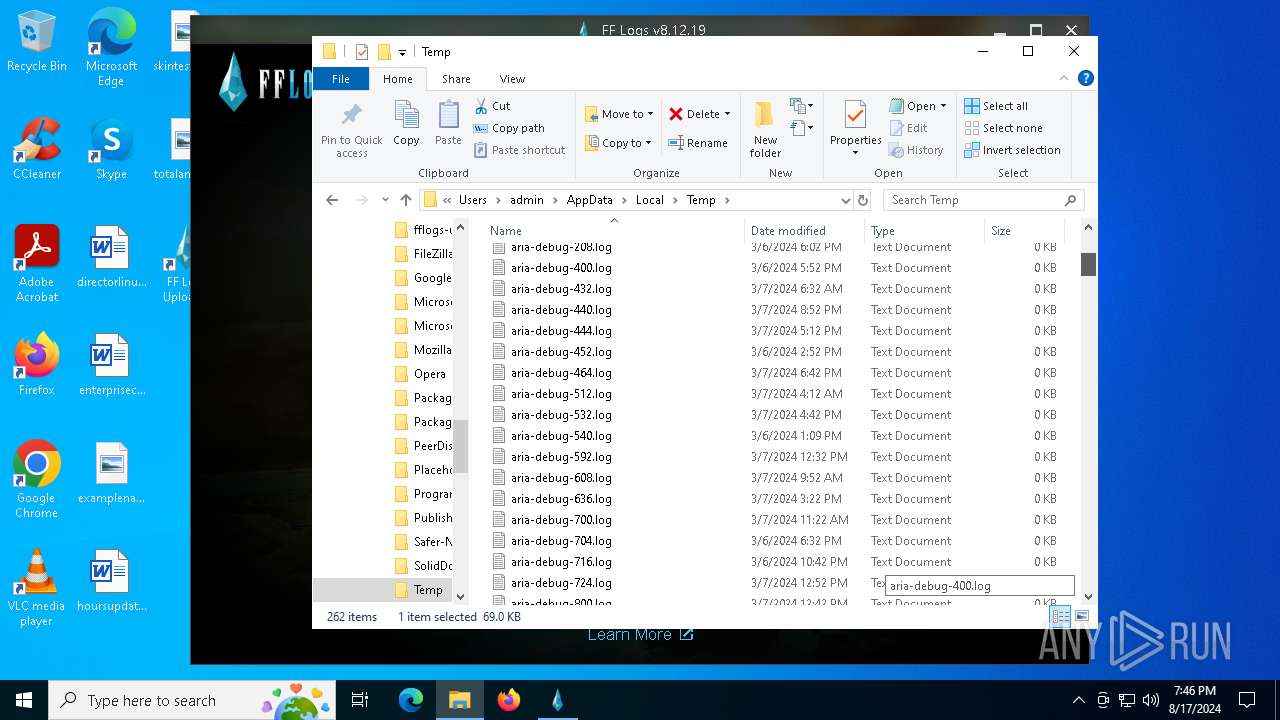
Drops 7-zip archiver for unpacking
- fflogs-v8.12.19.exe (PID: 7288)
Process drops legitimate windows executable
- fflogs-v8.12.19.exe (PID: 7288)
Reads security settings of Internet Explorer
- fflogs-v8.12.19.exe (PID: 7288)
Creates a software uninstall entry
- fflogs-v8.12.19.exe (PID: 7288)
Starts POWERSHELL.EXE for commands execution
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 6396)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6236)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 6292)
Application launched itself
- msedge.exe (PID: 6292)
- msedge.exe (PID: 1168)
Reads Environment values
- identity_helper.exe (PID: 8584)
- identity_helper.exe (PID: 8728)
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2648)
- FF Logs Uploader.exe (PID: 8152)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 6396)
The process uses the downloaded file
- msedge.exe (PID: 8992)
- msedge.exe (PID: 6292)
- fflogs-v8.12.19.exe (PID: 7288)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6292)
- msedge.exe (PID: 1168)
Checks supported languages
- identity_helper.exe (PID: 8584)
- fflogs-v8.12.19.exe (PID: 5152)
- identity_helper.exe (PID: 8728)
- fflogs-v8.12.19.exe (PID: 7288)
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 7824)
- FF Logs Uploader.exe (PID: 8688)
- FF Logs Uploader.exe (PID: 2648)
- FF Logs Uploader.exe (PID: 7636)
- TextInputHost.exe (PID: 6652)
- FF Logs Uploader.exe (PID: 8152)
- csc.exe (PID: 6916)
- cvtres.exe (PID: 6880)
- FF Logs Uploader.exe (PID: 5588)
- FF Logs Uploader.exe (PID: 3660)
- FF Logs Uploader.exe (PID: 9200)
- FF Logs Uploader.exe (PID: 7300)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 2336)
- FF Logs Uploader.exe (PID: 6396)
- FF Logs Uploader.exe (PID: 2804)
- FF Logs Uploader.exe (PID: 7260)
- FF Logs Uploader.exe (PID: 8336)
- FF Logs Uploader.exe (PID: 6148)
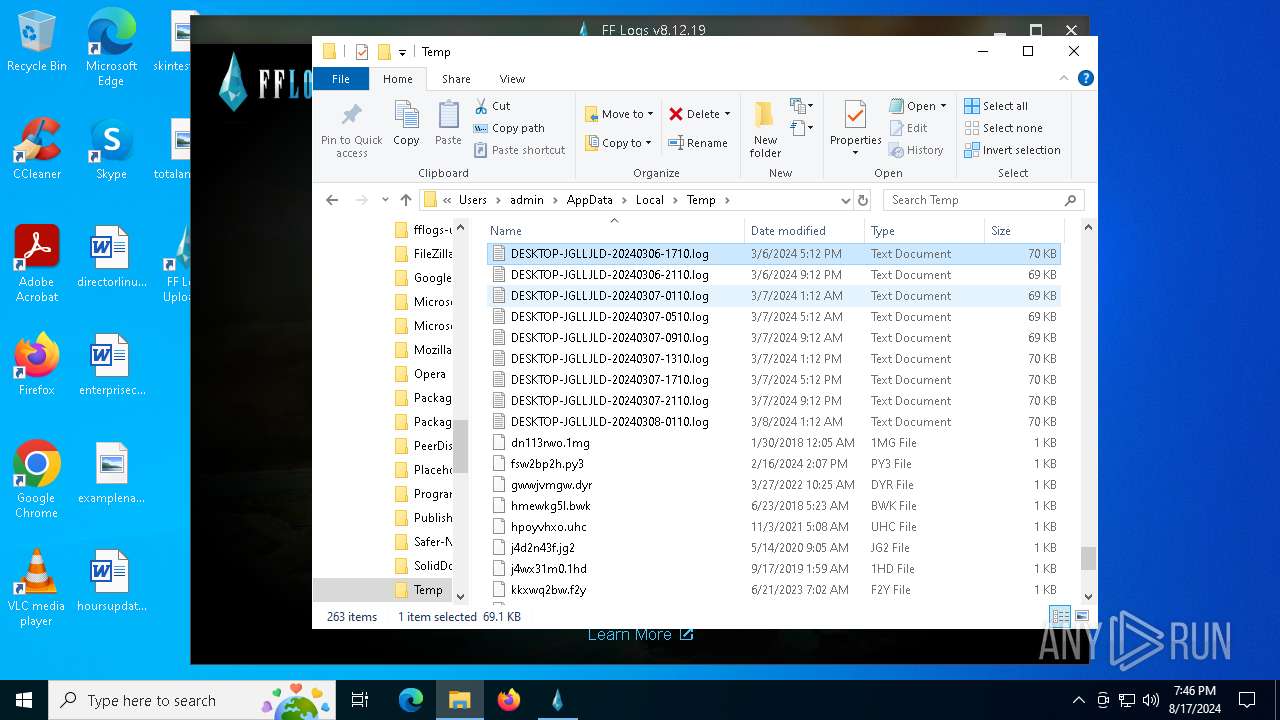
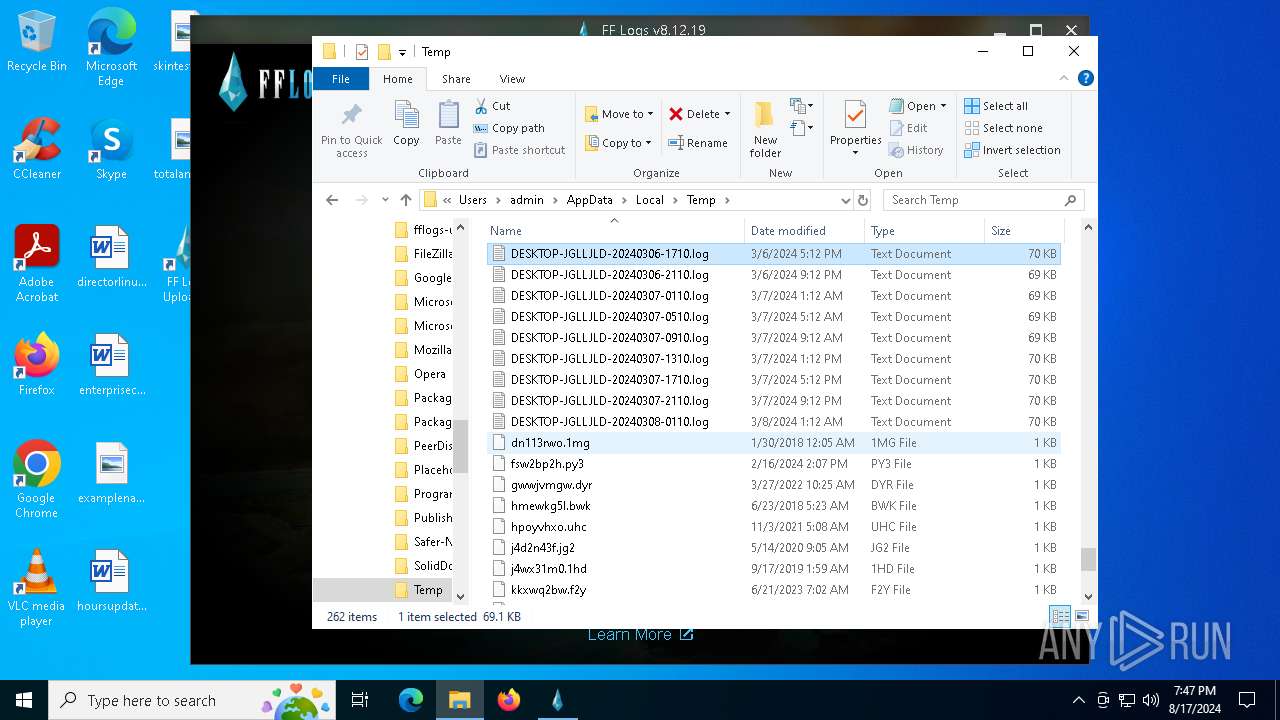
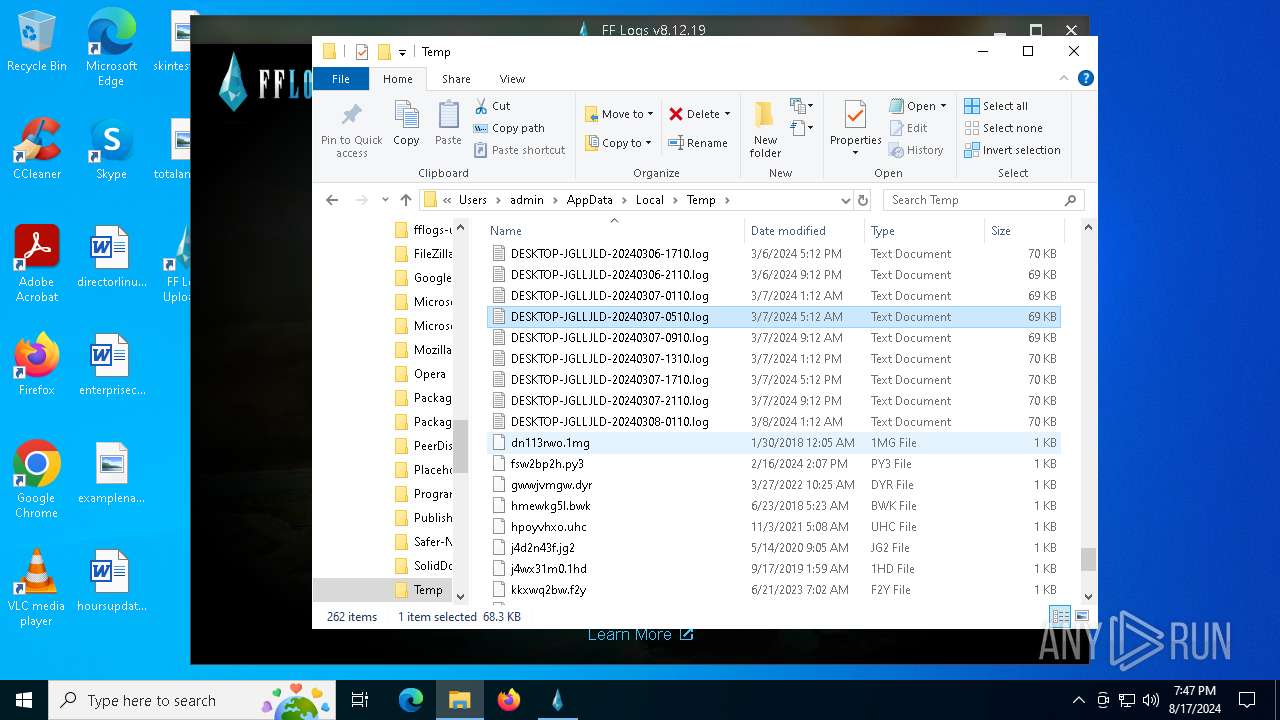
Reads the computer name
- identity_helper.exe (PID: 8584)
- fflogs-v8.12.19.exe (PID: 7288)
- identity_helper.exe (PID: 8728)
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 8688)
- FF Logs Uploader.exe (PID: 7636)
- TextInputHost.exe (PID: 6652)
- FF Logs Uploader.exe (PID: 3660)
- FF Logs Uploader.exe (PID: 9200)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 2336)
- FF Logs Uploader.exe (PID: 6396)
- FF Logs Uploader.exe (PID: 7260)
- FF Logs Uploader.exe (PID: 8336)
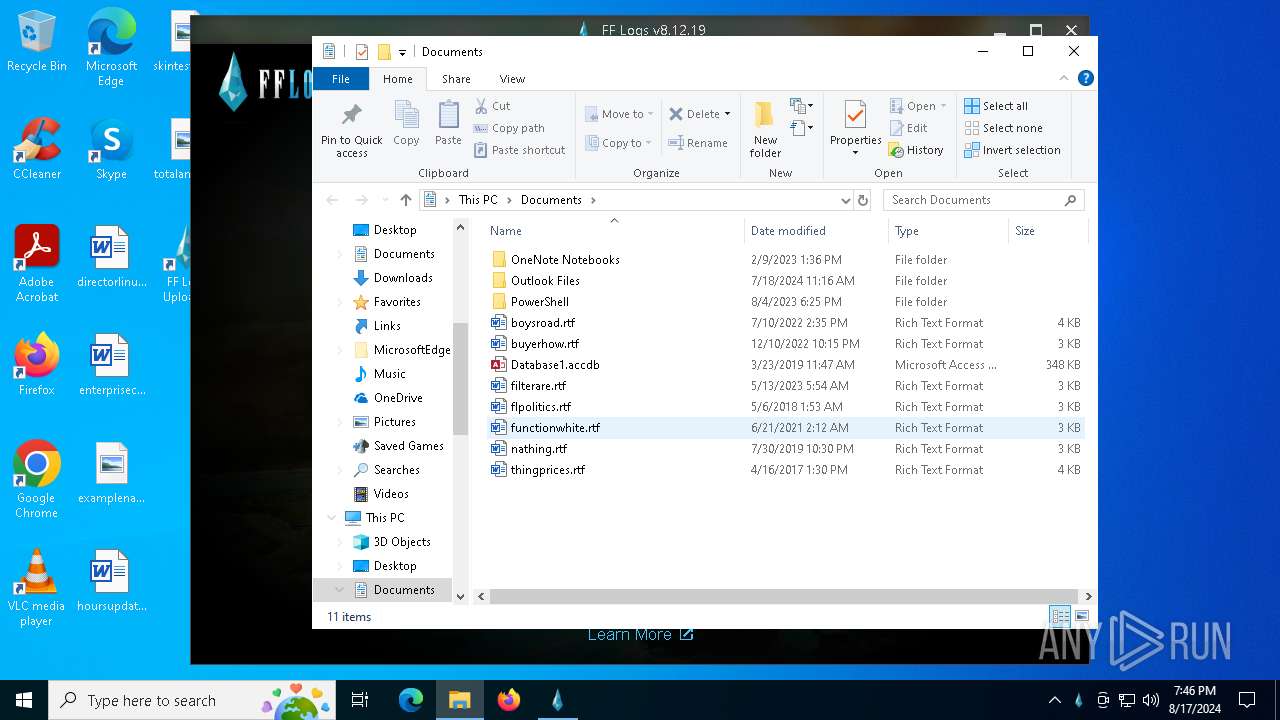
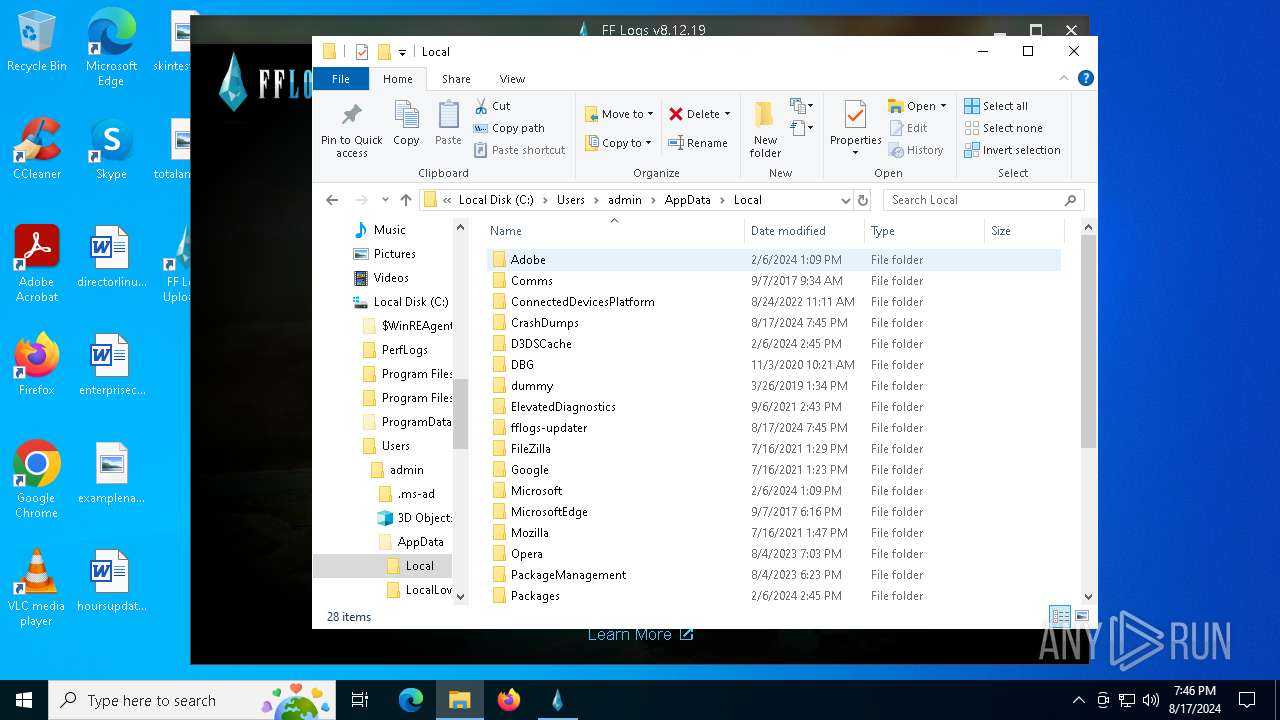
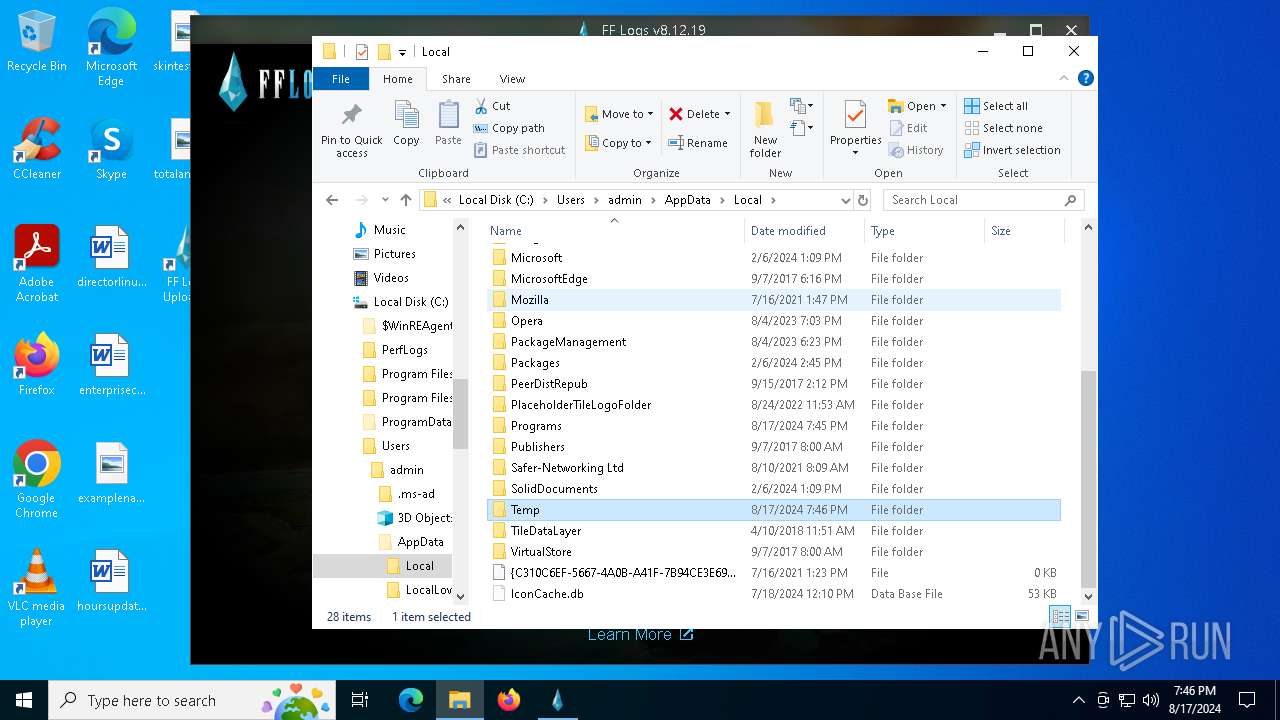
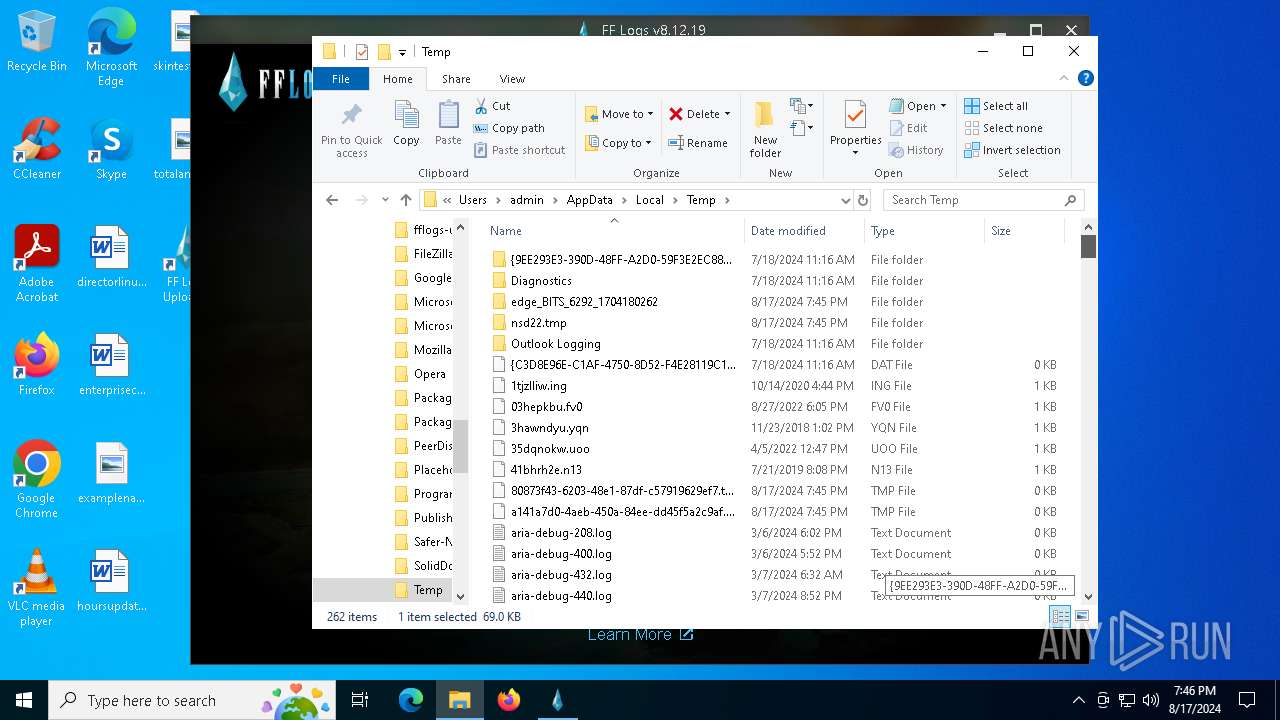
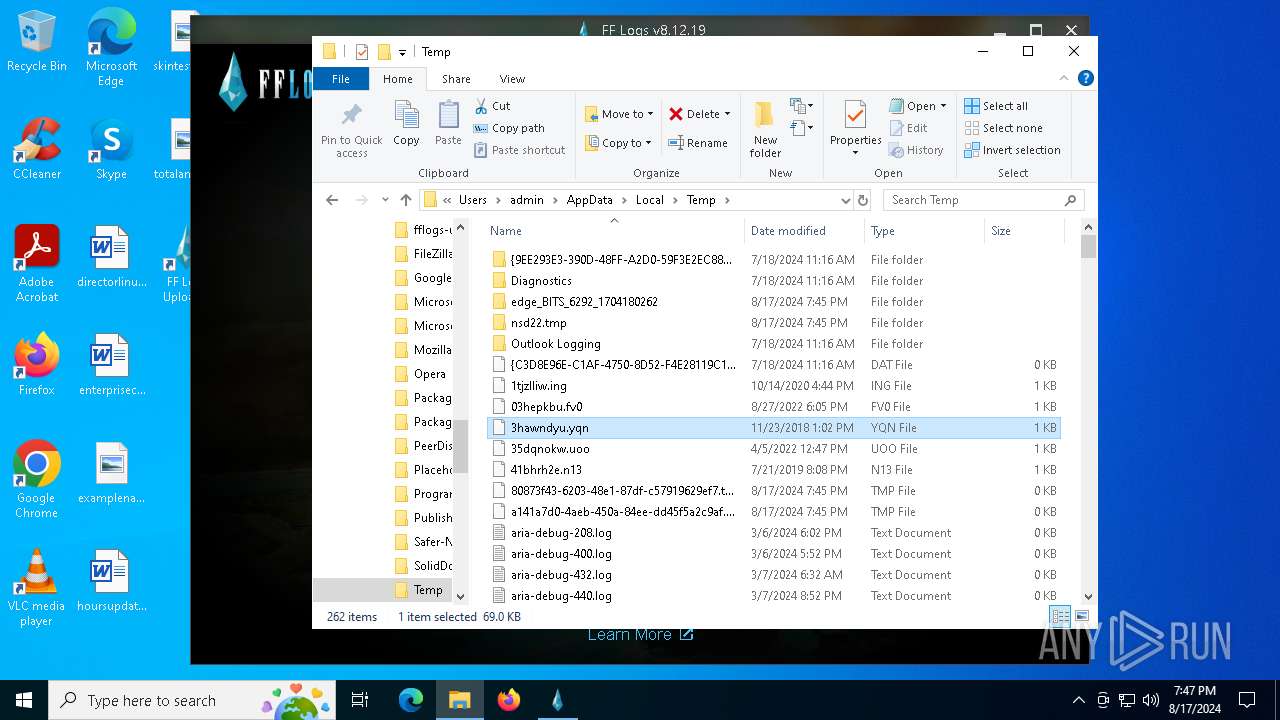
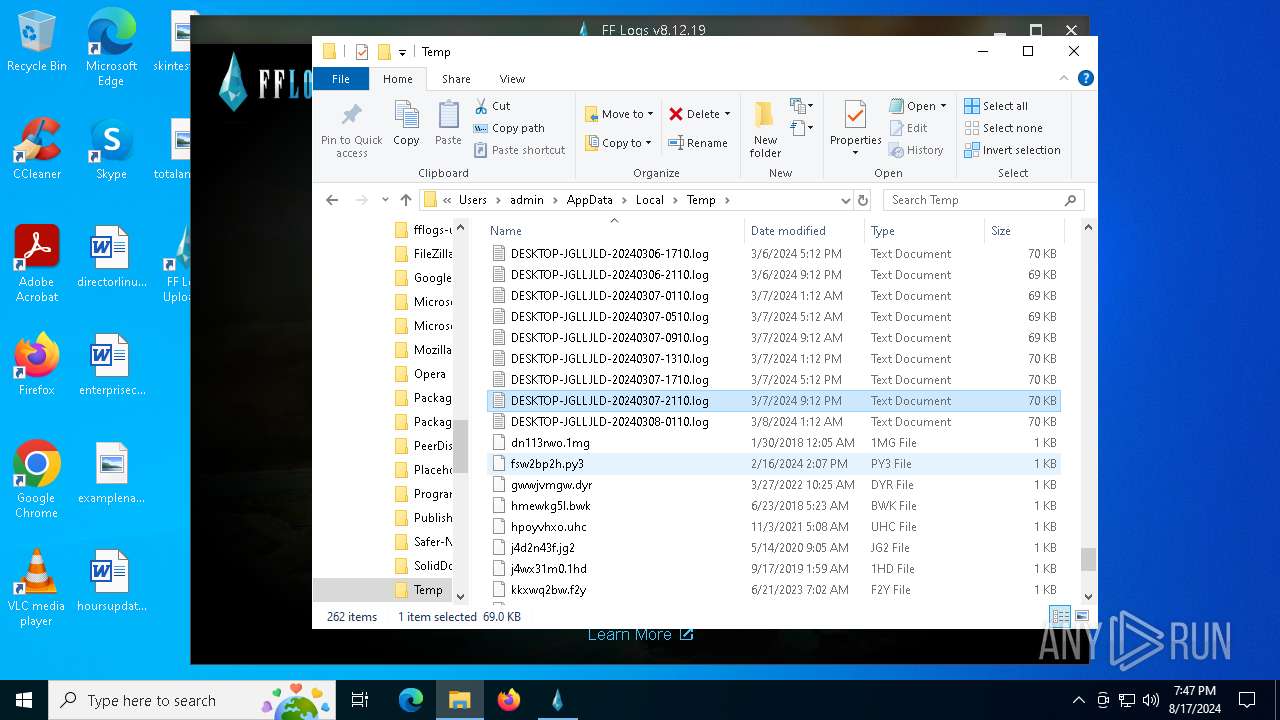
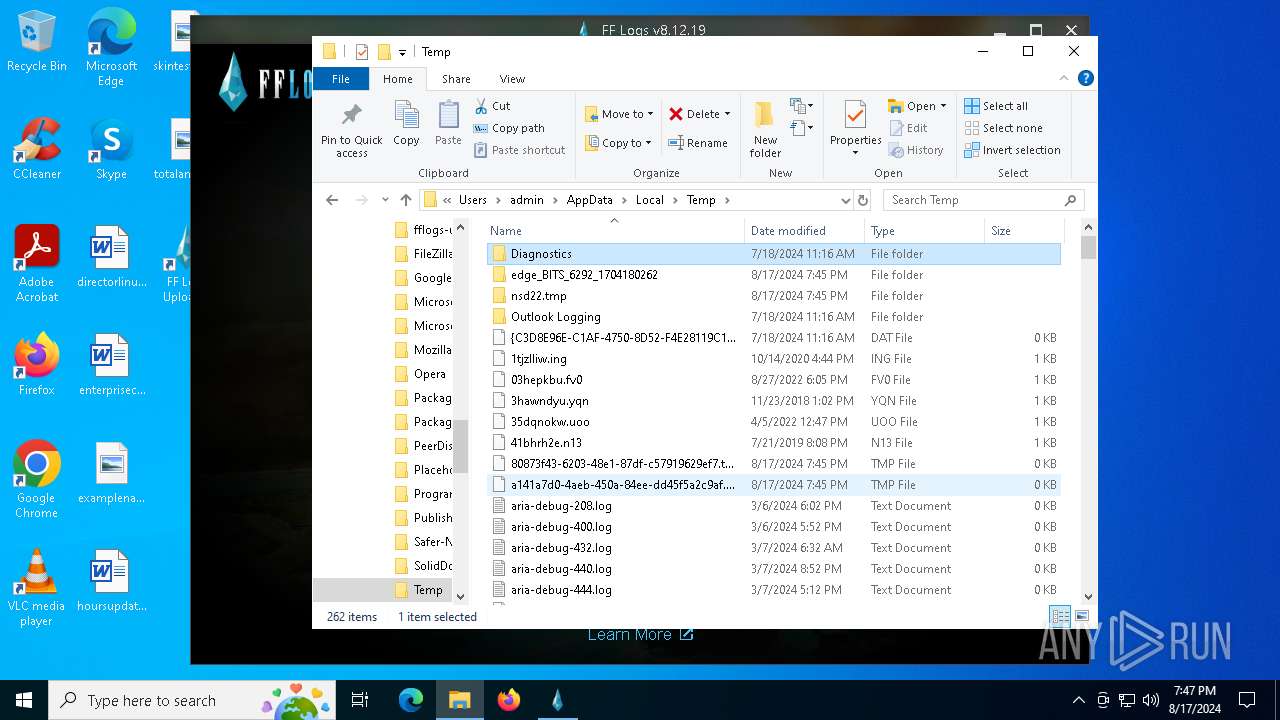
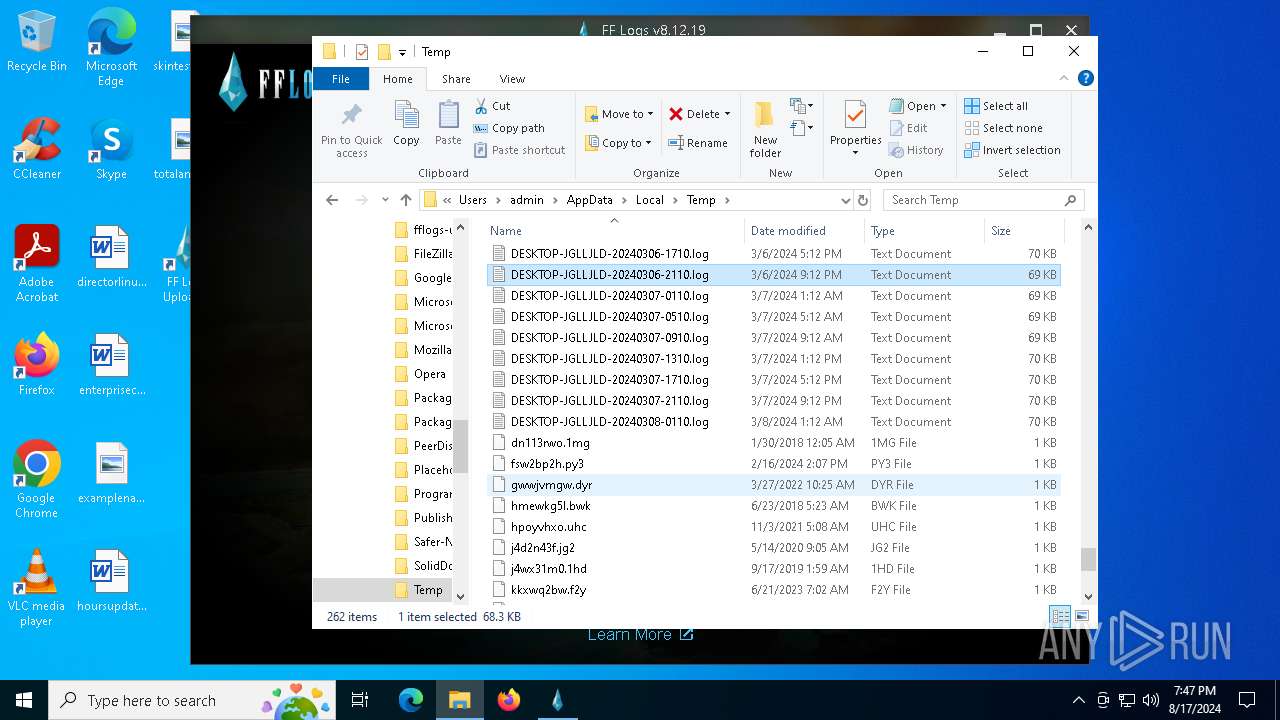
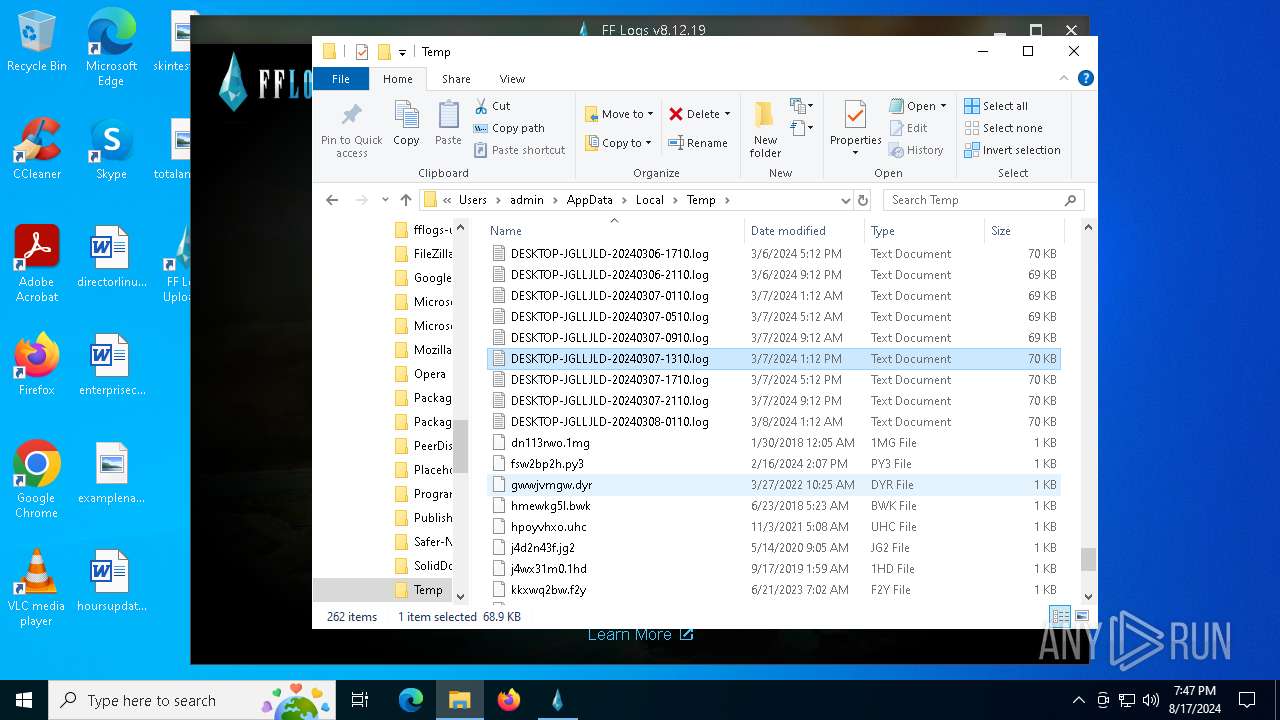
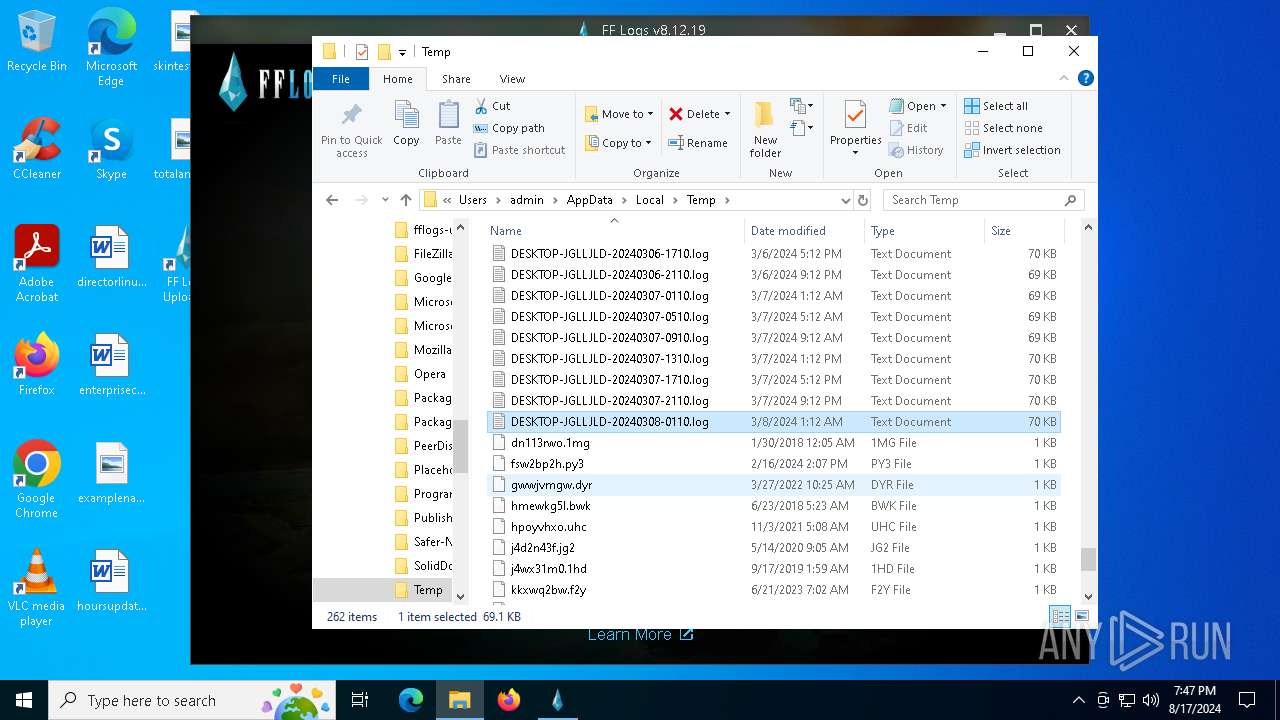
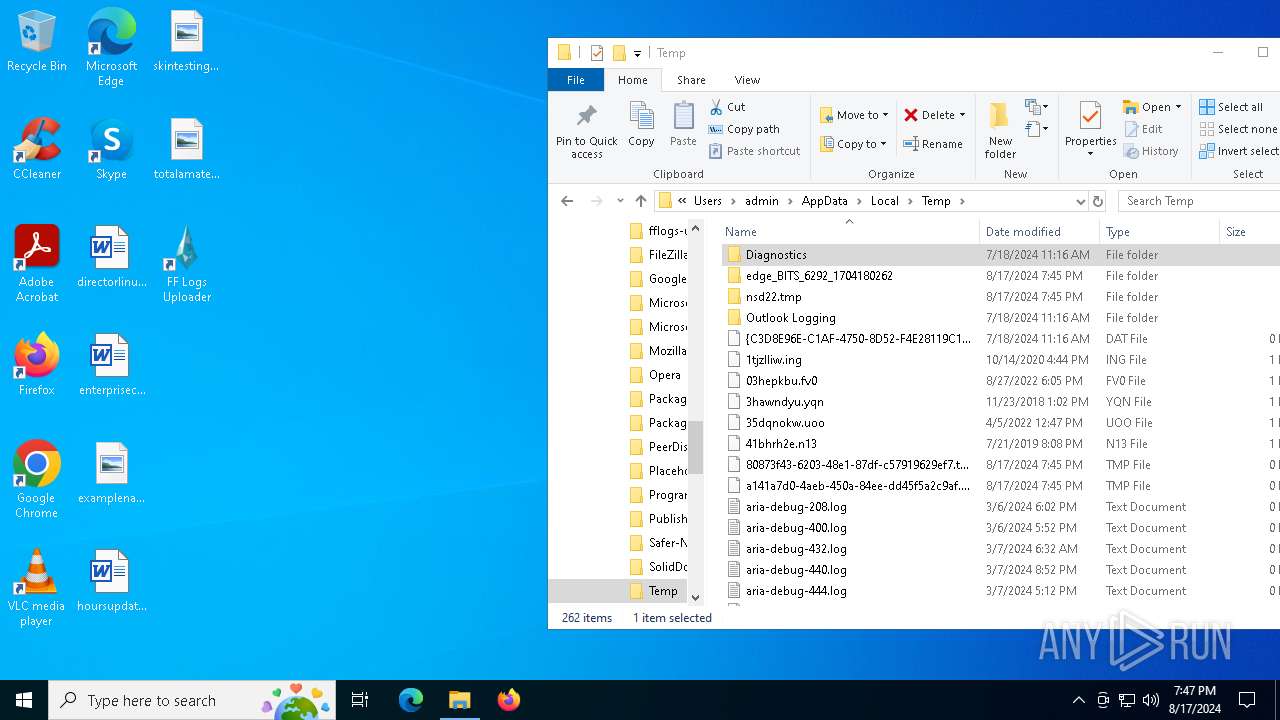
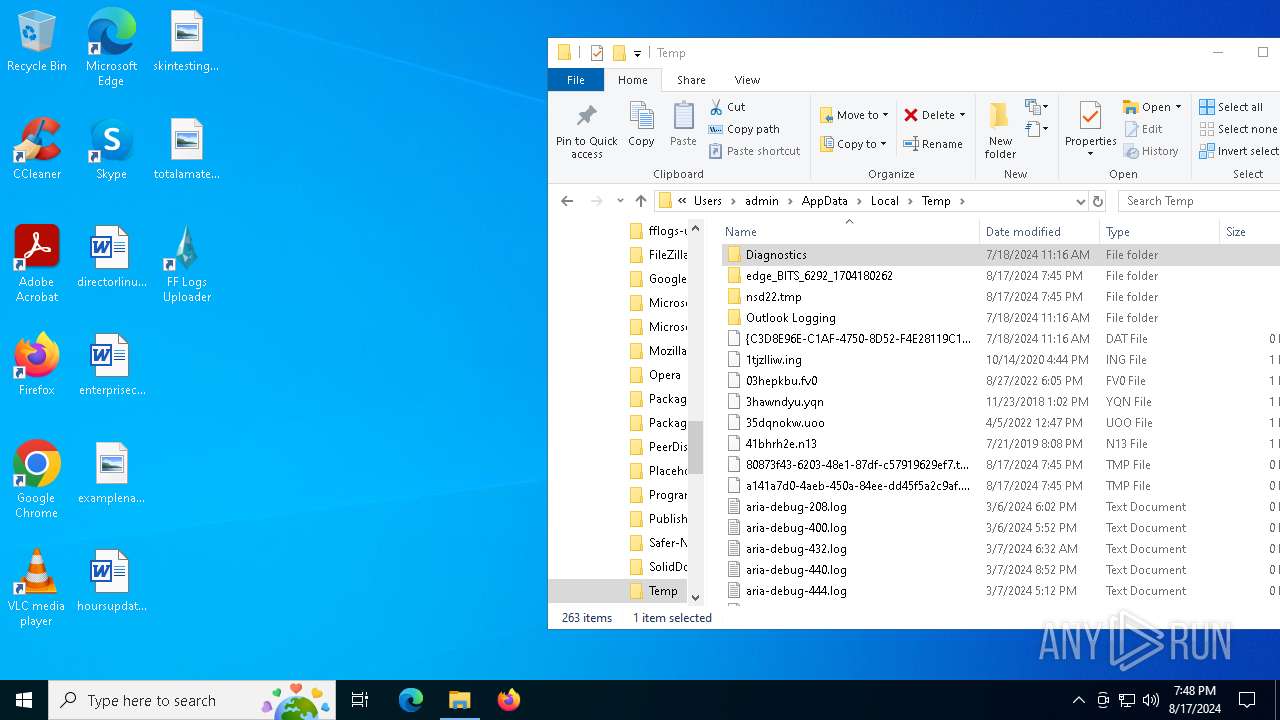
Create files in a temporary directory
- fflogs-v8.12.19.exe (PID: 5152)
- fflogs-v8.12.19.exe (PID: 7288)
- FF Logs Uploader.exe (PID: 5248)
- csc.exe (PID: 6916)
- cvtres.exe (PID: 6880)
Reads the software policy settings
- WerFault.exe (PID: 7152)
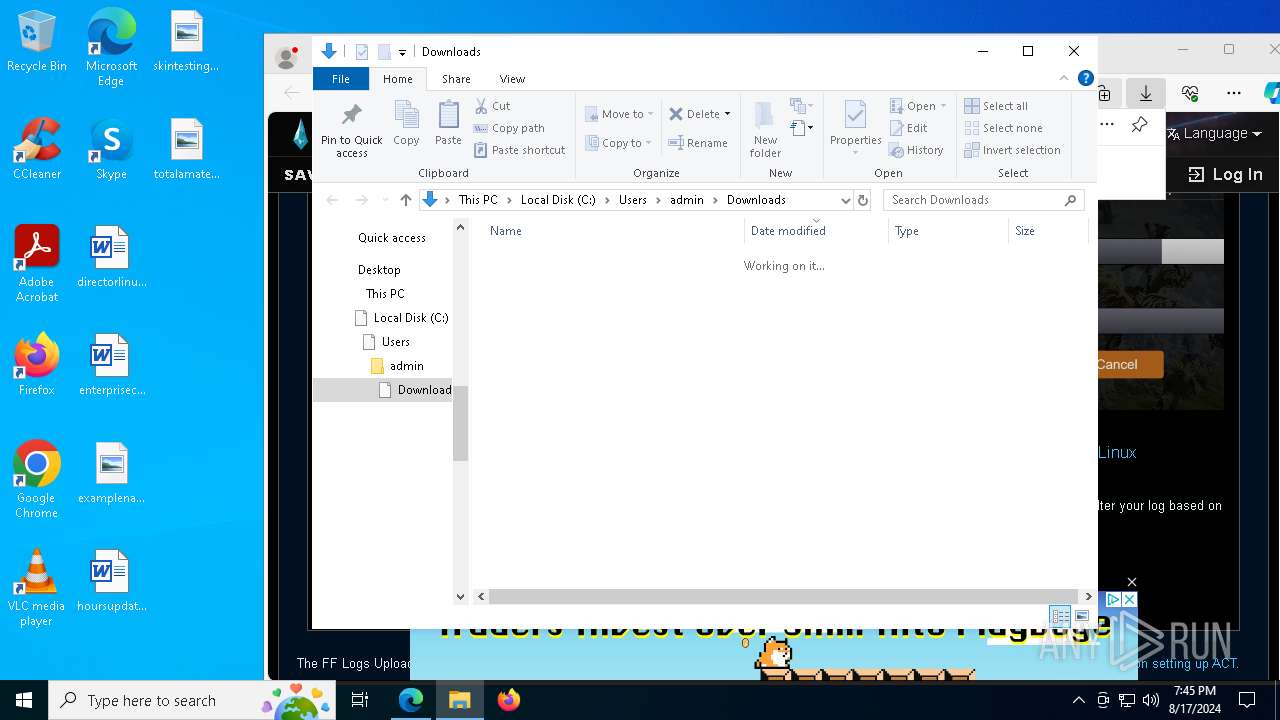
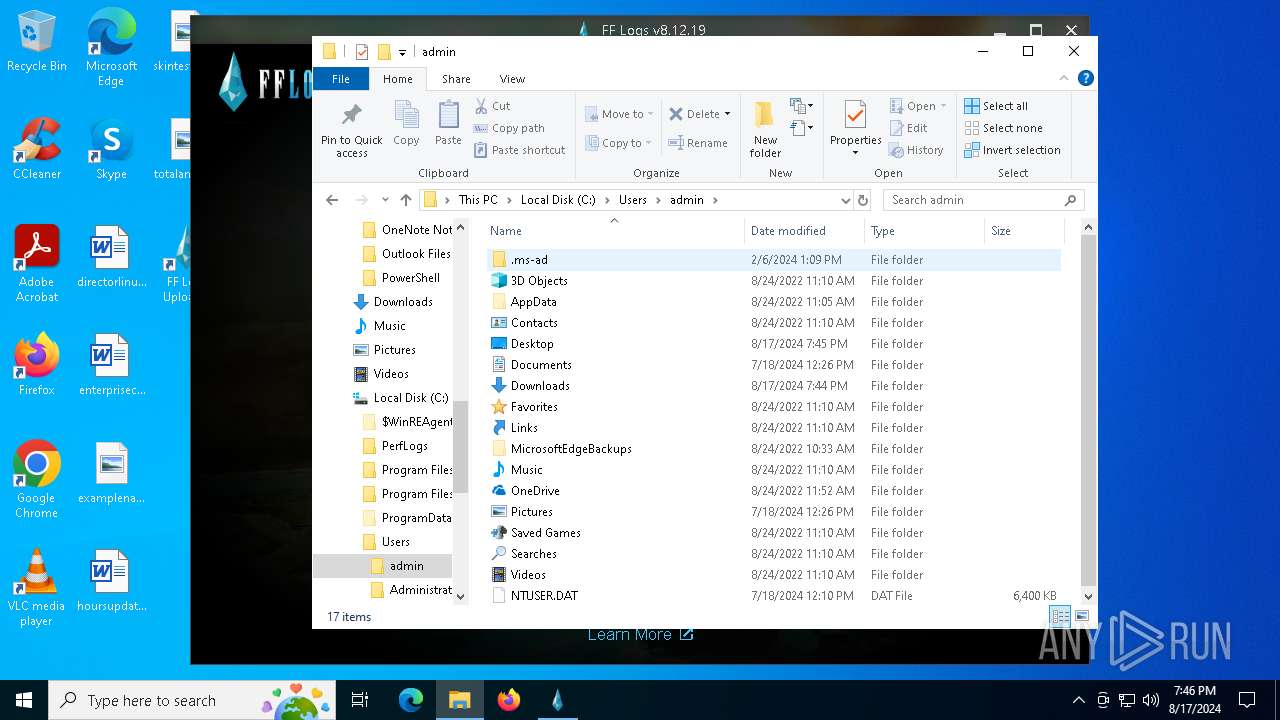
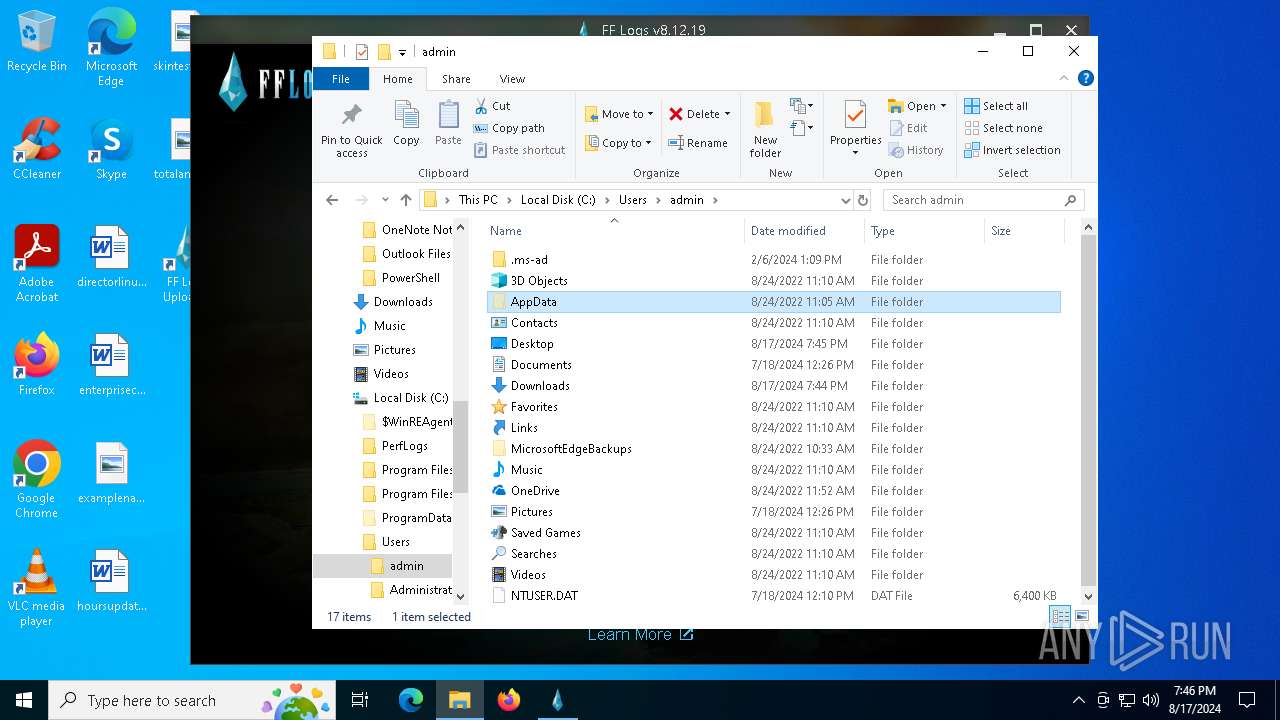
Creates files or folders in the user directory
- WerFault.exe (PID: 7152)
- FF Logs Uploader.exe (PID: 7824)
- FF Logs Uploader.exe (PID: 5248)
- fflogs-v8.12.19.exe (PID: 7288)
- FF Logs Uploader.exe (PID: 7636)
- FF Logs Uploader.exe (PID: 5588)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 9200)
- FF Logs Uploader.exe (PID: 2336)
- FF Logs Uploader.exe (PID: 2804)
- FF Logs Uploader.exe (PID: 6396)
- FF Logs Uploader.exe (PID: 8336)
Checks proxy server information
- WerFault.exe (PID: 7152)
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 6396)
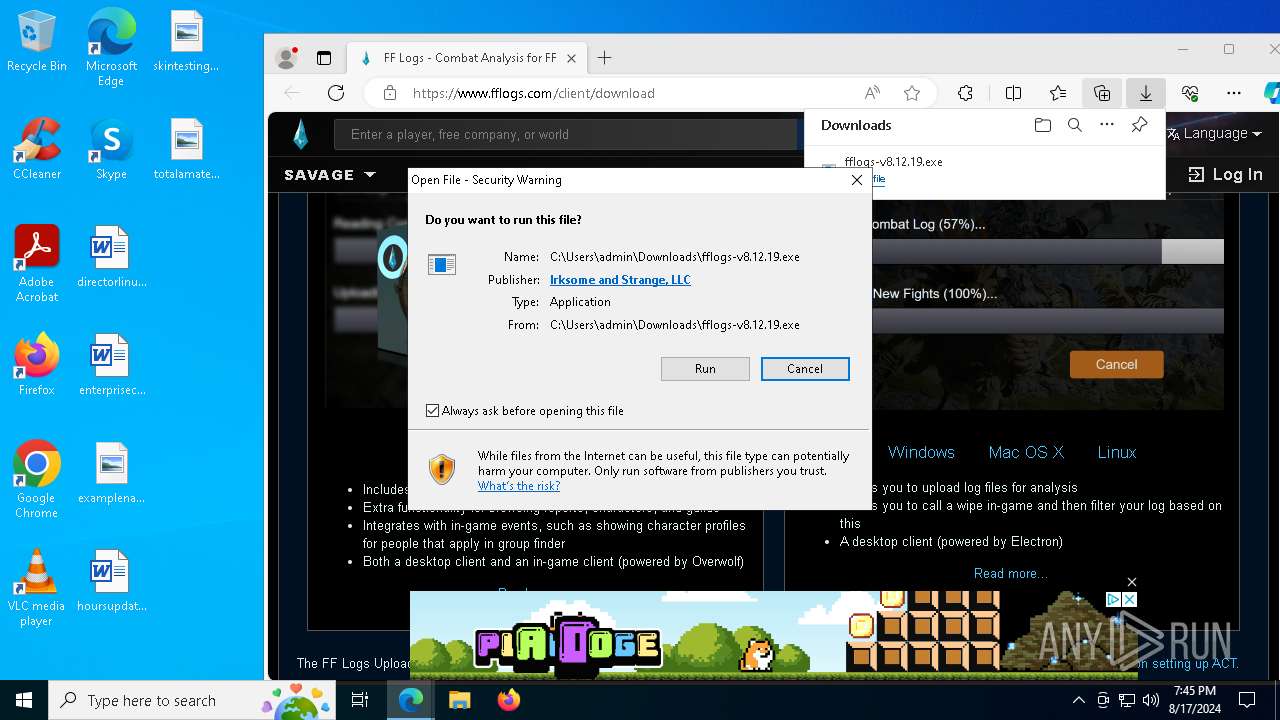
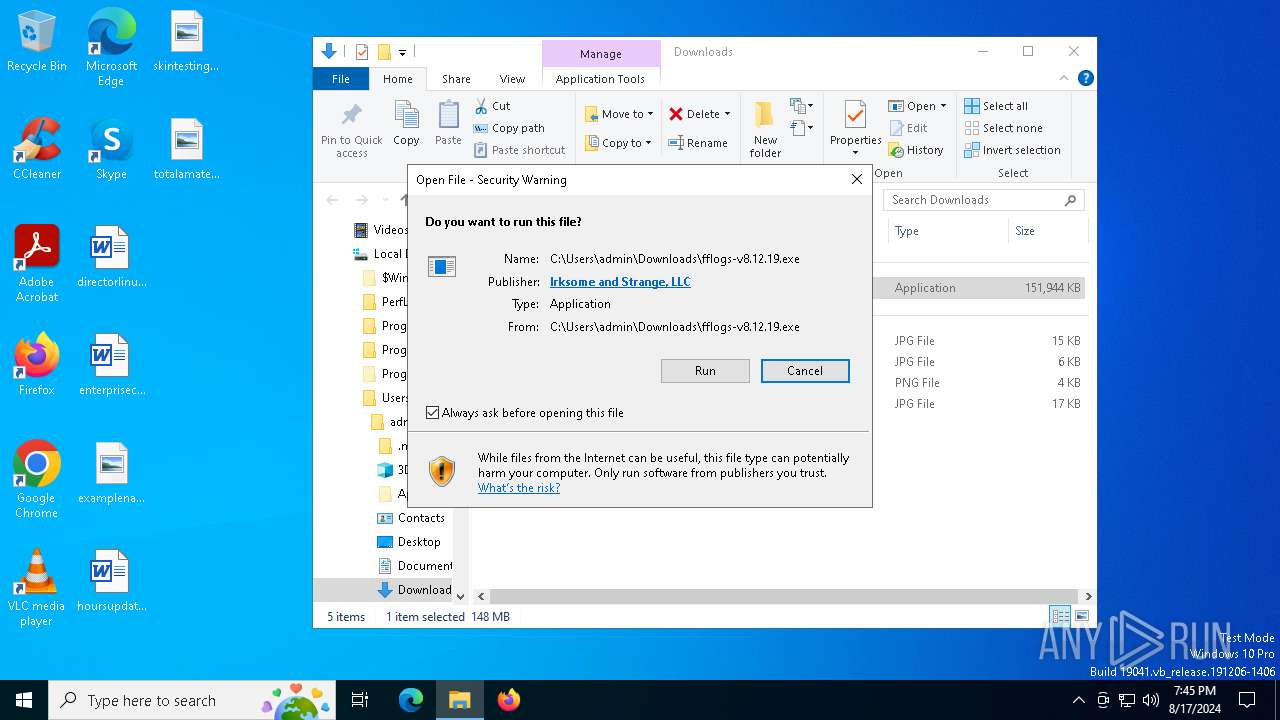
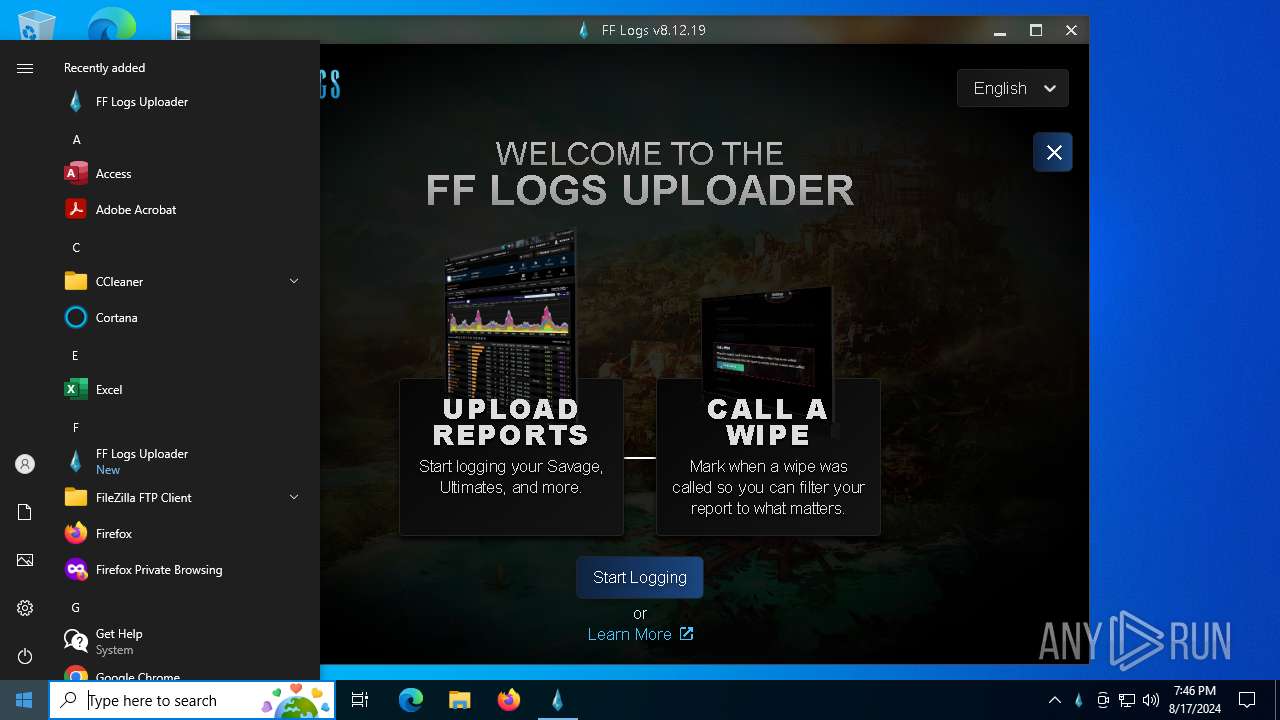
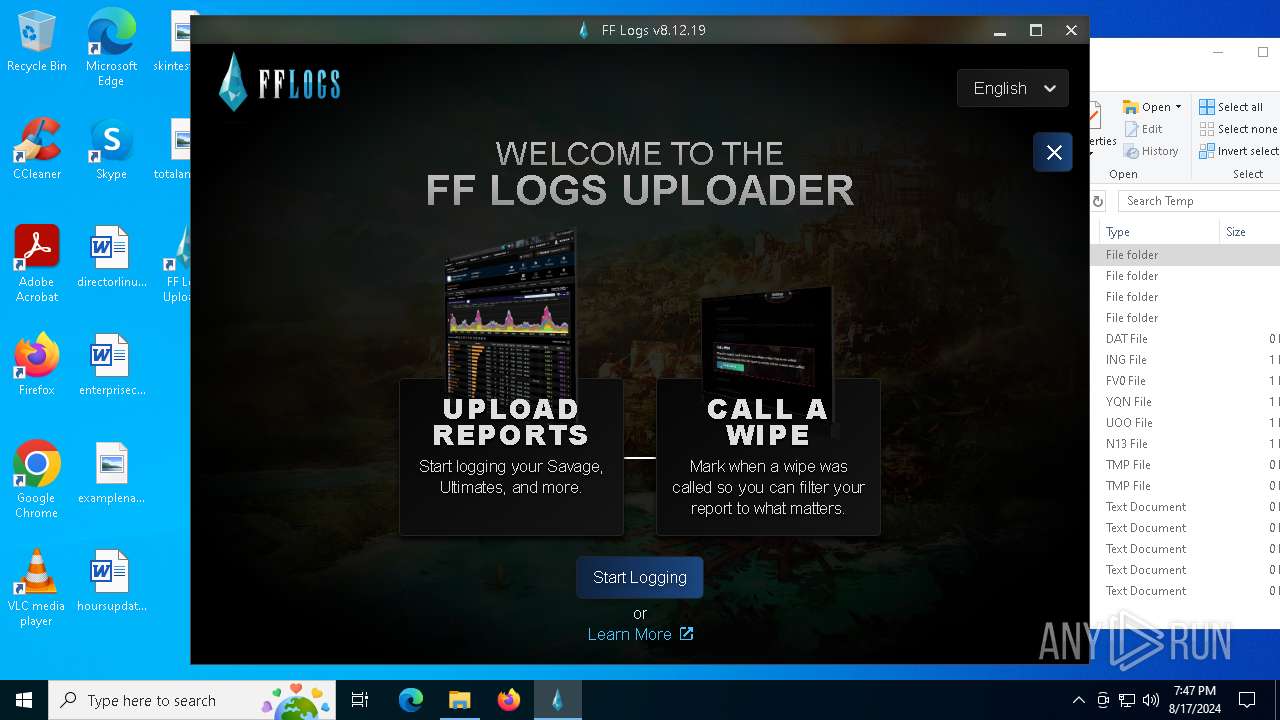
Manual execution by a user
- fflogs-v8.12.19.exe (PID: 7288)
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 6396)
Reads product name
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2648)
- FF Logs Uploader.exe (PID: 8152)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 6396)
Process checks computer location settings
- FF Logs Uploader.exe (PID: 5248)
- FF Logs Uploader.exe (PID: 2648)
- FF Logs Uploader.exe (PID: 8152)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 7300)
- FF Logs Uploader.exe (PID: 6396)
- FF Logs Uploader.exe (PID: 6148)
Reads the machine GUID from the registry
- FF Logs Uploader.exe (PID: 5248)
- csc.exe (PID: 6916)
- FF Logs Uploader.exe (PID: 2900)
- FF Logs Uploader.exe (PID: 2336)
- FF Logs Uploader.exe (PID: 6396)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
292
Monitored processes
146
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1060 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=5296 --field-trial-handle=2380,i,8318007646129177919,12707511574768415957,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1140 | tasklist /FI "USERNAME eq admin" /FI "IMAGENAME eq FF Logs Uploader.exe" | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5288 --field-trial-handle=2380,i,8318007646129177919,12707511574768415957,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=4588 --field-trial-handle=2380,i,8318007646129177919,12707511574768415957,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=5184 --field-trial-handle=2380,i,8318007646129177919,12707511574768415957,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
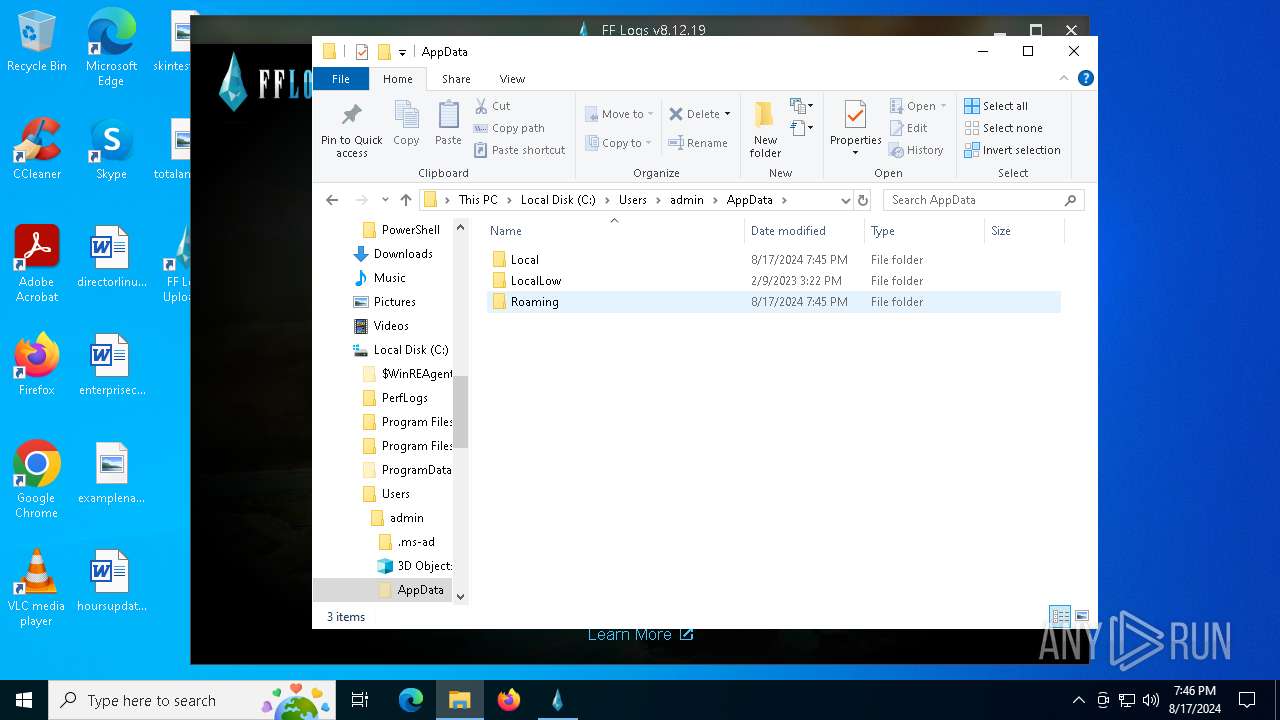
| 2336 | "C:\Users\admin\AppData\Local\Programs\FF Logs Uploader\FF Logs Uploader.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --user-data-dir="C:\Users\admin\AppData\Roaming\FF Logs Uploader" --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAEAAAA4AAAAAAAAAAAAAACEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --field-trial-handle=1200,i,14726035230901549804,1289893913260390993,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=3724 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\FF Logs Uploader\FF Logs Uploader.exe | — | FF Logs Uploader.exe | |||||||||||
User: admin Company: fflogs Integrity Level: MEDIUM Description: FF Logs Uploader Exit code: 0 Version: 8.12.19 Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Local\Programs\FF Logs Uploader\FF Logs Uploader.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\FF Logs Uploader" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --app-path="C:\Users\admin\AppData\Local\Programs\FF Logs Uploader\resources\app.asar" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=2488,i,14726035230901549804,1289893913260390993,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\FF Logs Uploader\FF Logs Uploader.exe | — | FF Logs Uploader.exe | |||||||||||
User: admin Company: fflogs Integrity Level: MEDIUM Description: FF Logs Uploader Version: 8.12.19 Modules
| |||||||||||||||
| 2720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5316 --field-trial-handle=2380,i,8318007646129177919,12707511574768415957,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
66 159
Read events
65 831
Write events
233
Delete events
95
Modification events
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
34
Suspicious files
784
Text files
220
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe5465.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe5465.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe5465.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe5475.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe5484.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
460
DNS requests
590
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6620 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://cacerts.rapidssl.com/RapidSSLTLSRSACAG1.crt | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
9144 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724414059&P2=404&P3=2&P4=dt7kcFld3BQXoZsgJpcxY2bySXQthAE5V2qK6%2bRP%2fstiu01OVZf8dxsIHBkKm7nKSPbH1890877gZ7SgCWPCCg%3d%3d | unknown | — | — | whitelisted |
2476 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8944 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
9144 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724414059&P2=404&P3=2&P4=dt7kcFld3BQXoZsgJpcxY2bySXQthAE5V2qK6%2bRP%2fstiu01OVZf8dxsIHBkKm7nKSPbH1890877gZ7SgCWPCCg%3d%3d | unknown | — | — | whitelisted |
9144 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724414059&P2=404&P3=2&P4=dt7kcFld3BQXoZsgJpcxY2bySXQthAE5V2qK6%2bRP%2fstiu01OVZf8dxsIHBkKm7nKSPbH1890877gZ7SgCWPCCg%3d%3d | unknown | — | — | whitelisted |
9144 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724414059&P2=404&P3=2&P4=dt7kcFld3BQXoZsgJpcxY2bySXQthAE5V2qK6%2bRP%2fstiu01OVZf8dxsIHBkKm7nKSPbH1890877gZ7SgCWPCCg%3d%3d | unknown | — | — | whitelisted |
9144 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724414059&P2=404&P3=2&P4=dt7kcFld3BQXoZsgJpcxY2bySXQthAE5V2qK6%2bRP%2fstiu01OVZf8dxsIHBkKm7nKSPbH1890877gZ7SgCWPCCg%3d%3d | unknown | — | — | whitelisted |
9144 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724414059&P2=404&P3=2&P4=dt7kcFld3BQXoZsgJpcxY2bySXQthAE5V2qK6%2bRP%2fstiu01OVZf8dxsIHBkKm7nKSPbH1890877gZ7SgCWPCCg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2400 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6620 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6292 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6620 | msedge.exe | 34.215.23.76:443 | www.fflogs.com | AMAZON-02 | US | unknown |
6620 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6620 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.fflogs.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
assets.rpglogs.com |
| unknown |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5336 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |