| File name: | jp-pc.exe |
| Full analysis: | https://app.any.run/tasks/fd671d6f-dd18-443c-9c30-78c943cebbfa |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2020, 19:18:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 8844579012074AF558FBA634E6332D37 |
| SHA1: | C034DE007CD9A72FFF9C1B94377197DCD0F2C231 |
| SHA256: | 7BFACB3B9D9541EB51DFB6D117448CD90445042C5251A6294FE7C159EB441B04 |
| SSDEEP: | 196608:BCBXql59+VXmqoPXgBvolvN1UHq0U1PIJvMknXx/LPimsD39b5R+HvVgZxaYvtO:UW9OXmrgtoEZnXZumW39b5R+Hi1M |
MALICIOUS
Loads dropped or rewritten executable
- jp-pc.exe (PID: 3848)
- jianpian.exe (PID: 3164)
- jianpian.exe (PID: 2676)
- jptray.exe (PID: 2956)
Application was dropped or rewritten from another process
- jianpian_assist.exe (PID: 3288)
- jianpian_assist.exe (PID: 3724)
- jianpian.exe (PID: 2676)
- jianpian.exe (PID: 3164)
- jptray.exe (PID: 2956)
- jptr.exe (PID: 2992)
- jpengine.exe (PID: 3492)
- jpengine.exe (PID: 3236)
- jptr.exe (PID: 2908)
- jpengine.exe (PID: 3000)
Changes the autorun value in the registry
- jp-pc.exe (PID: 3848)
SUSPICIOUS
Executable content was dropped or overwritten
- jp-pc.exe (PID: 3848)
Starts application with an unusual extension
- jp-pc.exe (PID: 3848)
Executed as Windows Service
- jianpian_assist.exe (PID: 3288)
Modifies the open verb of a shell class
- jp-pc.exe (PID: 3848)
Starts SC.EXE for service management
- ns2E94.tmp (PID: 2584)
Creates a software uninstall entry
- jp-pc.exe (PID: 3848)
Reads Internet Cache Settings
- jptr.exe (PID: 2992)
- jptr.exe (PID: 2908)
Creates files in the user directory
- jp-pc.exe (PID: 3848)
- jpengine.exe (PID: 3492)
- jianpian.exe (PID: 2676)
INFO
Dropped object may contain Bitcoin addresses
- jp-pc.exe (PID: 3848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
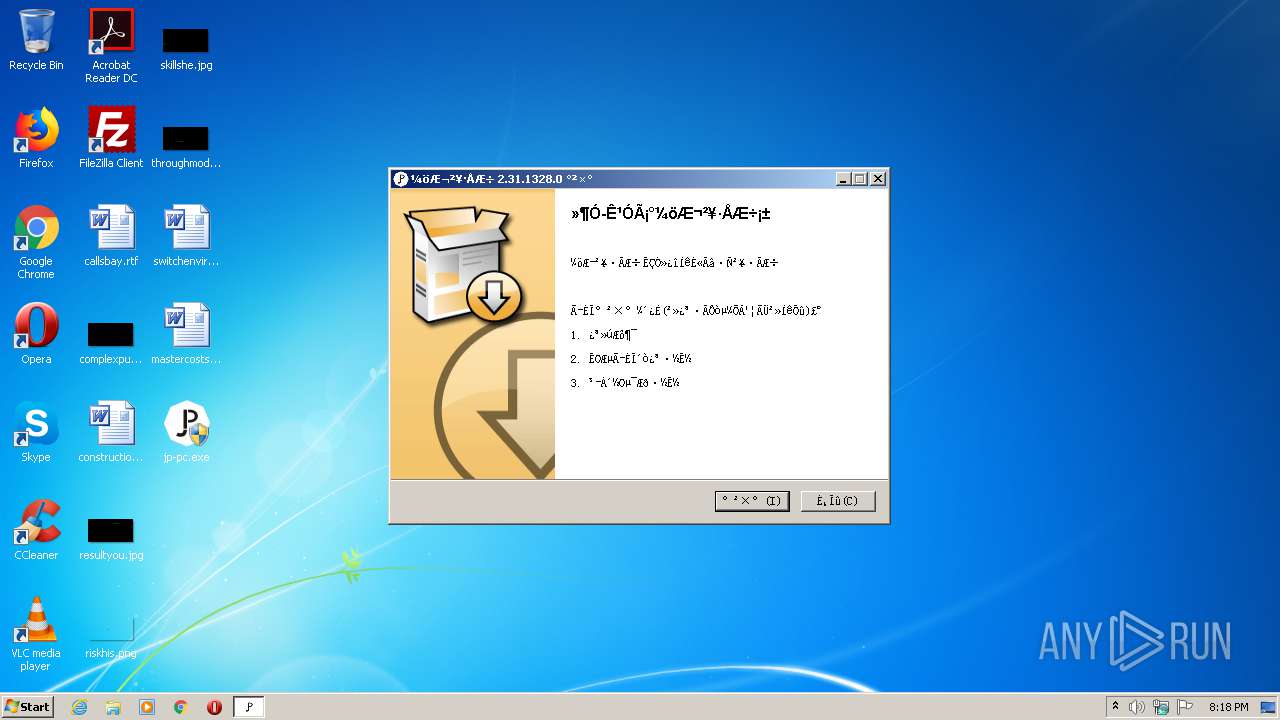
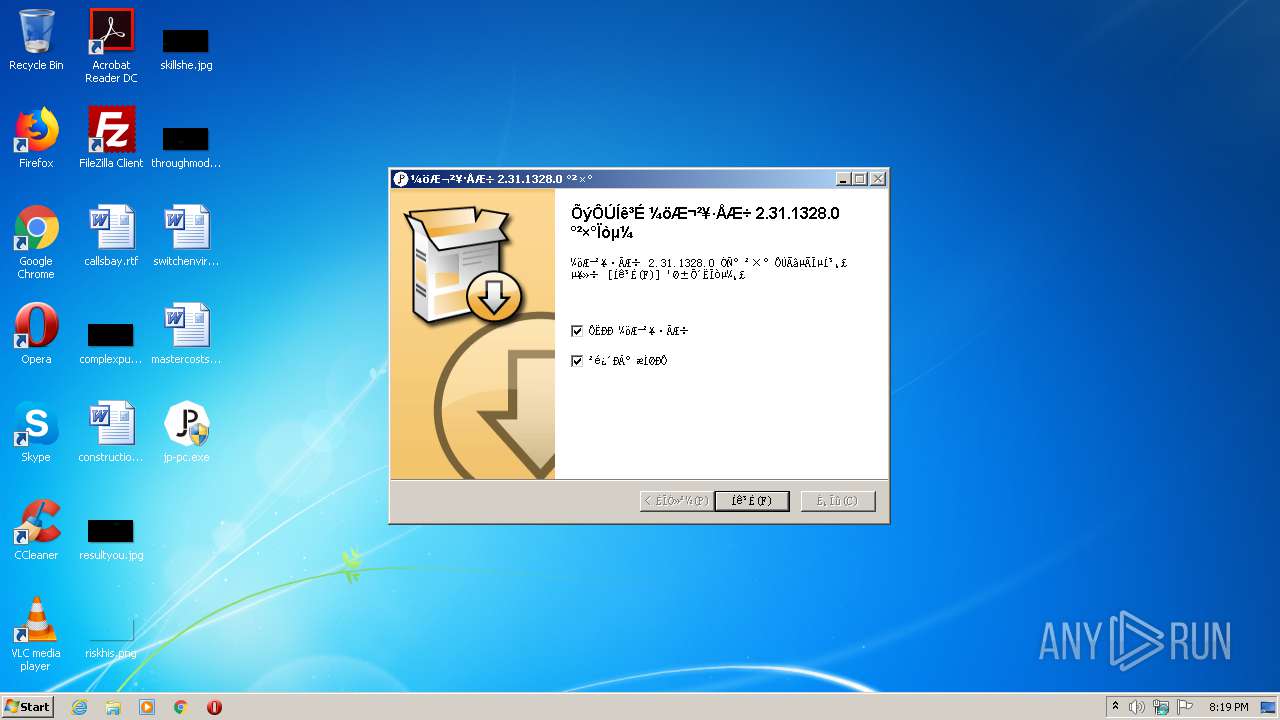
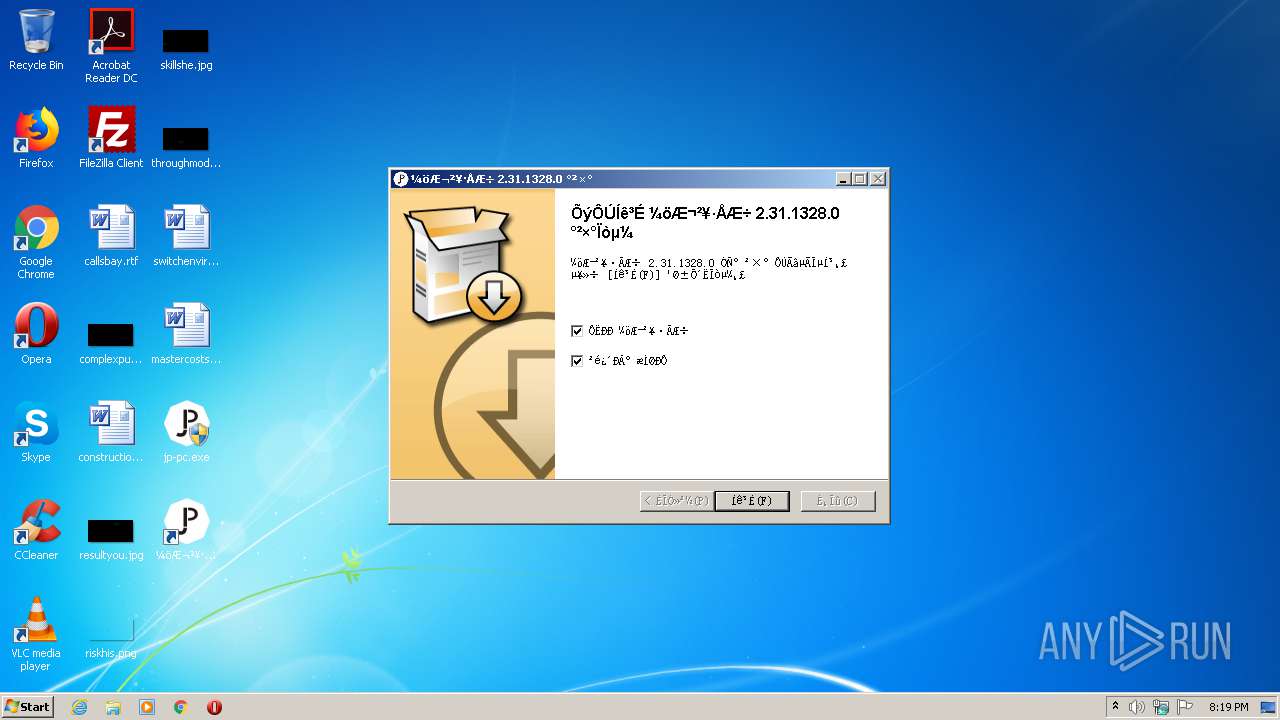
| FileVersionNumber: | 2.31.1328.0 |
| ProductVersionNumber: | 2.31.1328.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | 荐片播放器工作室 |
| FileDescription: | 荐片播放器安装文件 |
| FileVersion: | 2.31.1328.0 |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFileName: | jianpian_2.31.1328.0_Full.exe |
| ProductName: | 荐片播放器 |
| ProductVersion: | 2.31.1328.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:32 |
| Detected languages: |
|
| CompanyName: | 荐片播放器工作室 |
| FileDescription: | 荐片播放器安装文件 |
| FileVersion: | 2.31.1328.0 |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFilename: | jianpian_2.31.1328.0_Full.exe |
| ProductName: | 荐片播放器 |
| ProductVersion: | 2.31.1328.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40386 |
.rdata | 0x00008000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04481 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00030000 | 0x00003220 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.35738 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28794 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.62576 | 492 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
58
Monitored processes
17
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
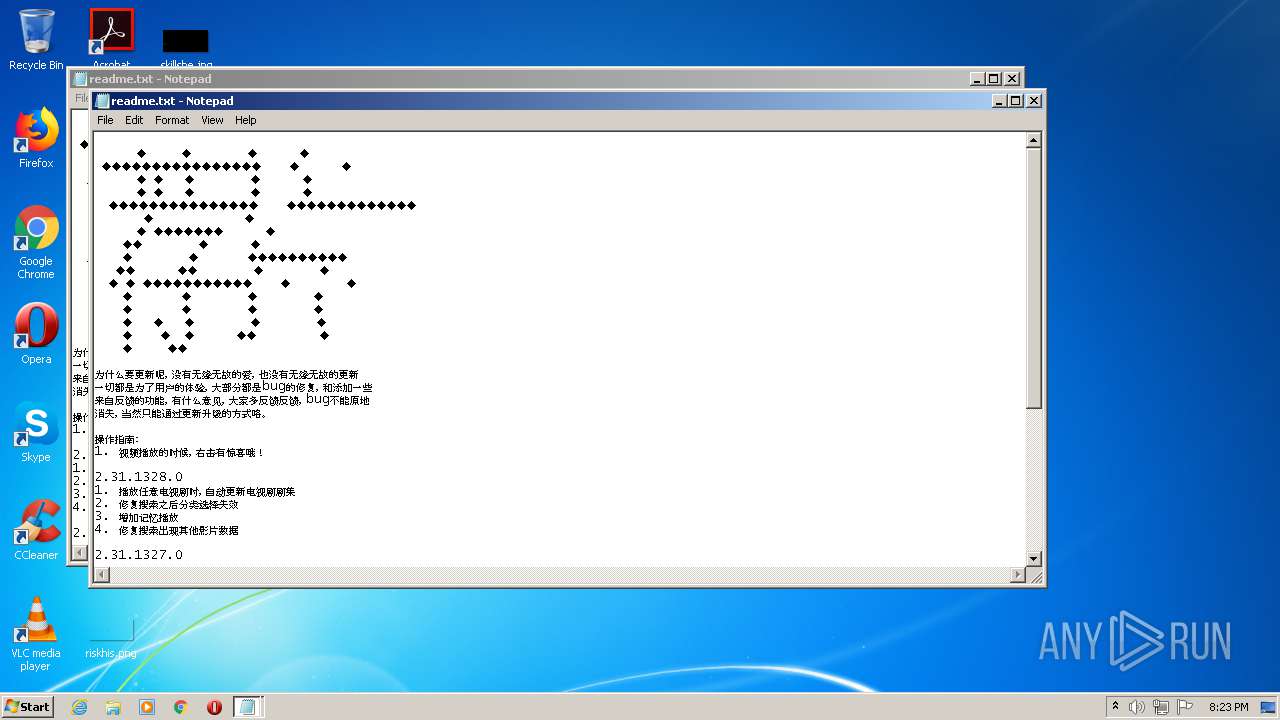
| 2224 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\jianpian\readme.txt | C:\Windows\system32\NOTEPAD.EXE | — | jp-pc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\jianpian\readme.txt | C:\Windows\system32\NOTEPAD.EXE | — | jp-pc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2584 | "C:\Users\admin\AppData\Local\Temp\nss104C.tmp\ns2E94.tmp" sc start JianpianAssist | C:\Users\admin\AppData\Local\Temp\nss104C.tmp\ns2E94.tmp | — | jp-pc.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
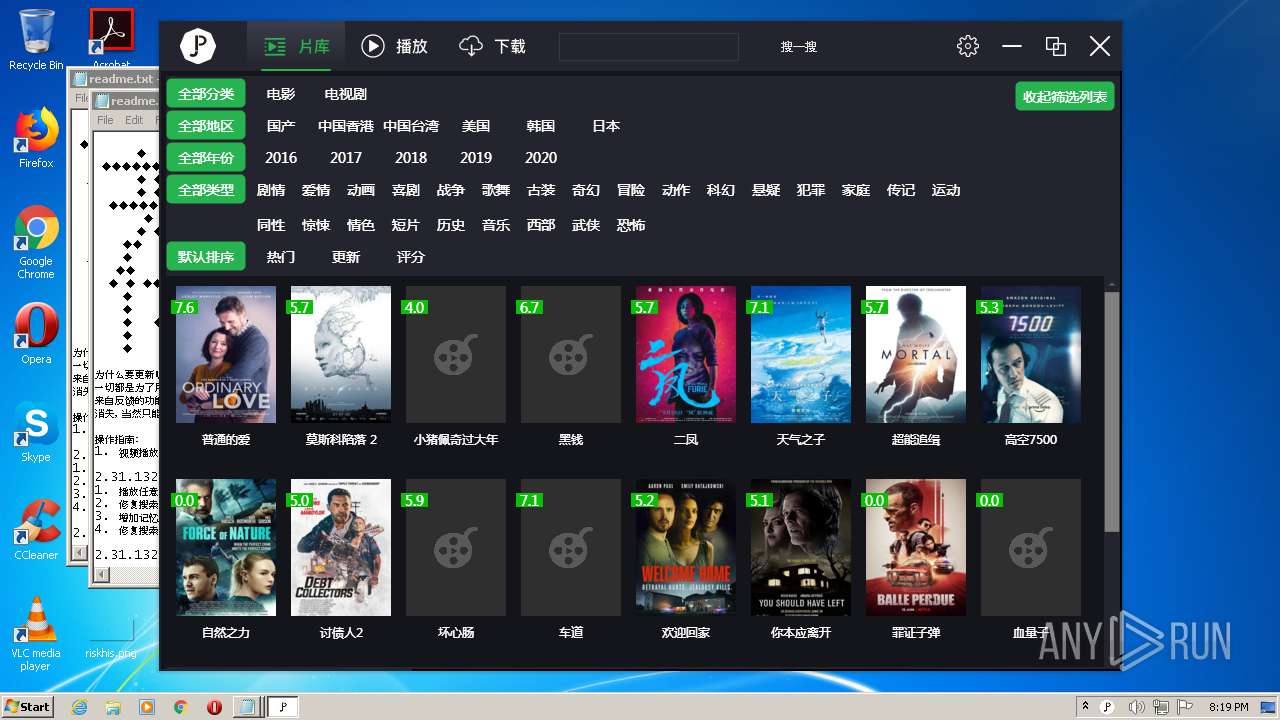
| 2676 | "C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe" | C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe | jp-pc.exe | ||||||||||||
User: admin Company: 荐片播放器制作工作室 Integrity Level: HIGH Description: 荐片 Exit code: 0 Version: 2.31.1328.0 Modules
| |||||||||||||||
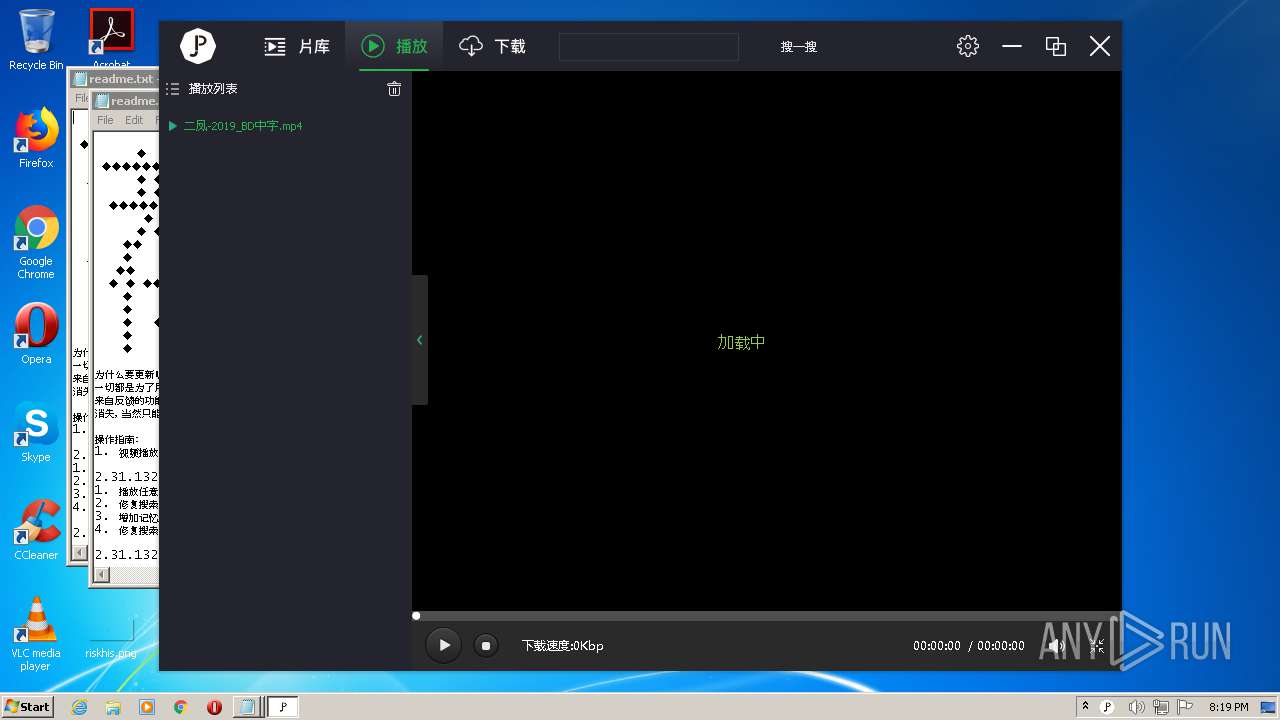
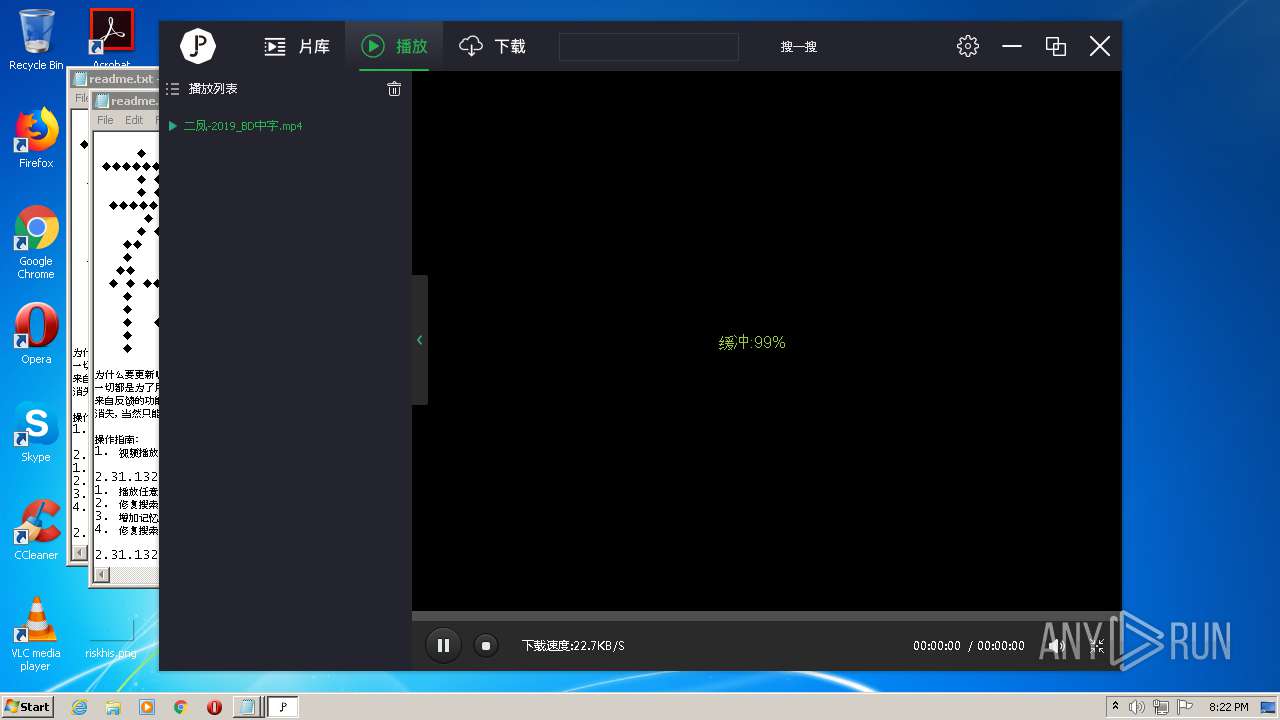
| 2908 | "C:\Users\admin\AppData\Roaming\jianpian\jptr.exe" "--URL=http://www.vipfanyongwang.com:40555/pc/stat?pccode=98FD8C0D-0-4d51303030302031202020202020202020202020-5254004A04AF-C4BA3647&product=jianpian&subproduct=xgp&version=2.31.1328.0&channel=0&ReportName=pianku&PlayUrl=ftp%3A%2F%2Fa%2Egbl%2E114s%2Ecom%3A20320%2F1691%2F%E4%BA%8C%E5%87%A4%2D2019%5FBD%E4%B8%AD%E5%AD%97%2Emp4" "--File=C:\Users\admin\AppData\Local\Temp\jianpian\jptr_FE427B8ADF0D45318AABCABBE9FC5964" | C:\Users\admin\AppData\Roaming\jianpian\jptr.exe | jianpian.exe | ||||||||||||
User: admin Company: 荐片播放器制作工作室 Integrity Level: HIGH Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Roaming\jianpian\jptray.exe" | C:\Users\admin\AppData\Roaming\jianpian\jptray.exe | jianpian.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 荐片托盘 Exit code: 0 Version: 2.31.1328.0 Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Roaming\jianpian\jptr.exe" "--URL=http://www.vipfanyongwang.com:40555/pc/stat?pccode=98FD8C0D-0-4d51303030302031202020202020202020202020-5254004A04AF-C4BA3647&product=jianpian&subproduct=xgp&version=2.31.1328.0&channel=0&ReportName=StartUp&Command=%22C%3A%5CUsers%5Cadmin%5CAppData%5CRoaming%5Cjianpian%5Cjianpian%2Eexe%22&Source=&Parent=jp%2Dpc%2Eexe&StartType=Unknown" "--File=C:\Users\admin\AppData\Local\Temp\jianpian\jptr_FE427B8ADF0D45318AABCABBE9FC5964" | C:\Users\admin\AppData\Roaming\jianpian\jptr.exe | jianpian.exe | ||||||||||||
User: admin Company: 荐片播放器制作工作室 Integrity Level: HIGH Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 3000 | "C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe" | C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe | jianpian.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 荐片播放器网络引擎 Exit code: 4294967295 Version: 2.29.0.0 Modules
| |||||||||||||||
| 3144 | sc start JianpianAssist | C:\Windows\system32\sc.exe | — | ns2E94.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe" | C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe | jp-pc.exe | ||||||||||||
User: admin Company: 荐片播放器制作工作室 Integrity Level: HIGH Description: 荐片 Exit code: 0 Version: 2.31.1328.0 Modules
| |||||||||||||||
Total events
905
Read events
569
Write events
336
Delete events
0
Modification events
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_CURRENT_USER\Software\jianpian |
| Operation: | write | Name: | channel |
Value: 0 | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Roaming\jianpian\icon\wmv.ico,0 | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\shell |
| Operation: | write | Name: | |
Value: open | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\shell\open |
| Operation: | write | Name: | |
Value: 用荐片播放器打开 | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\shell\open\Command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe" "%1" | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Back.JIANPIAN\.wmv |
| Operation: | write | Name: | |
Value: VLC.wmv | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.wmv |
| Operation: | write | Name: | |
Value: JIANPIAN.wmv | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.wmv |
| Operation: | write | Name: | Progid |
Value: JIANPIAN.wmv | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.wmv\UserChoice |
| Operation: | write | Name: | Progid |
Value: JIANPIAN.wmv | |||
| (PID) Process: | (3848) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.avi\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Roaming\jianpian\icon\avi.ico,0 | |||
Executable files
76
Suspicious files
6
Text files
119
Unknown types
2
Dropped files
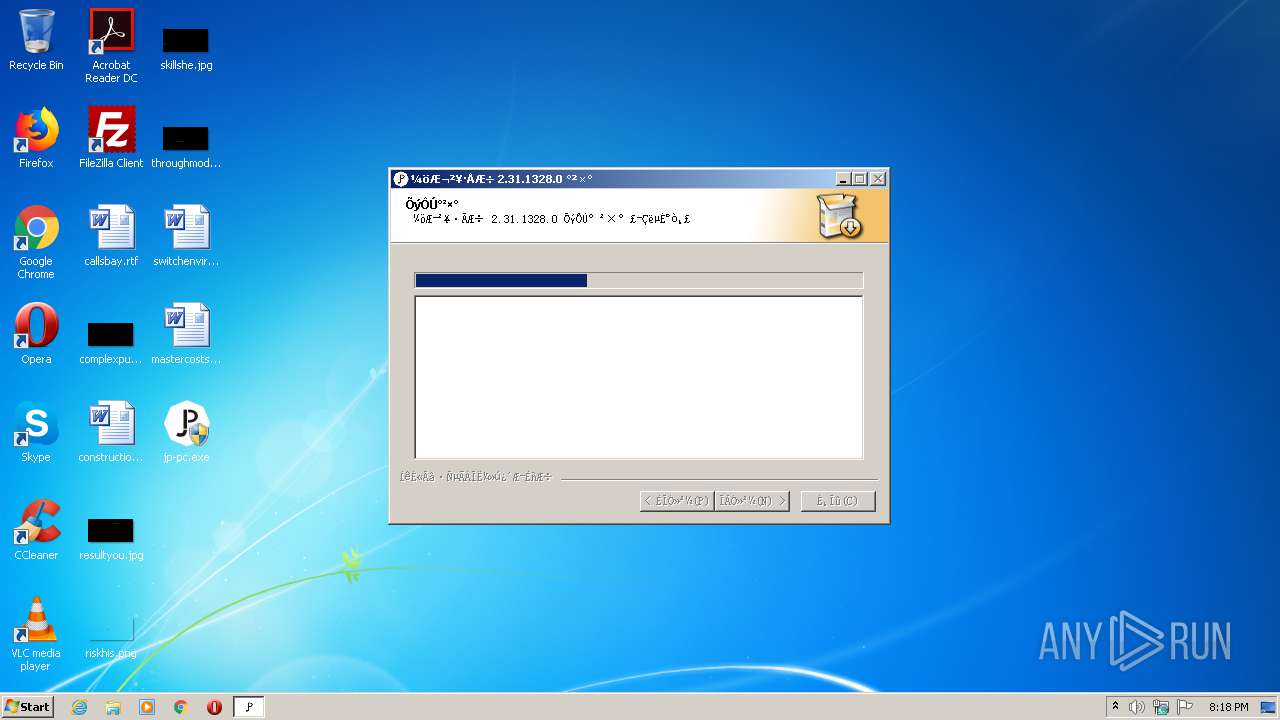
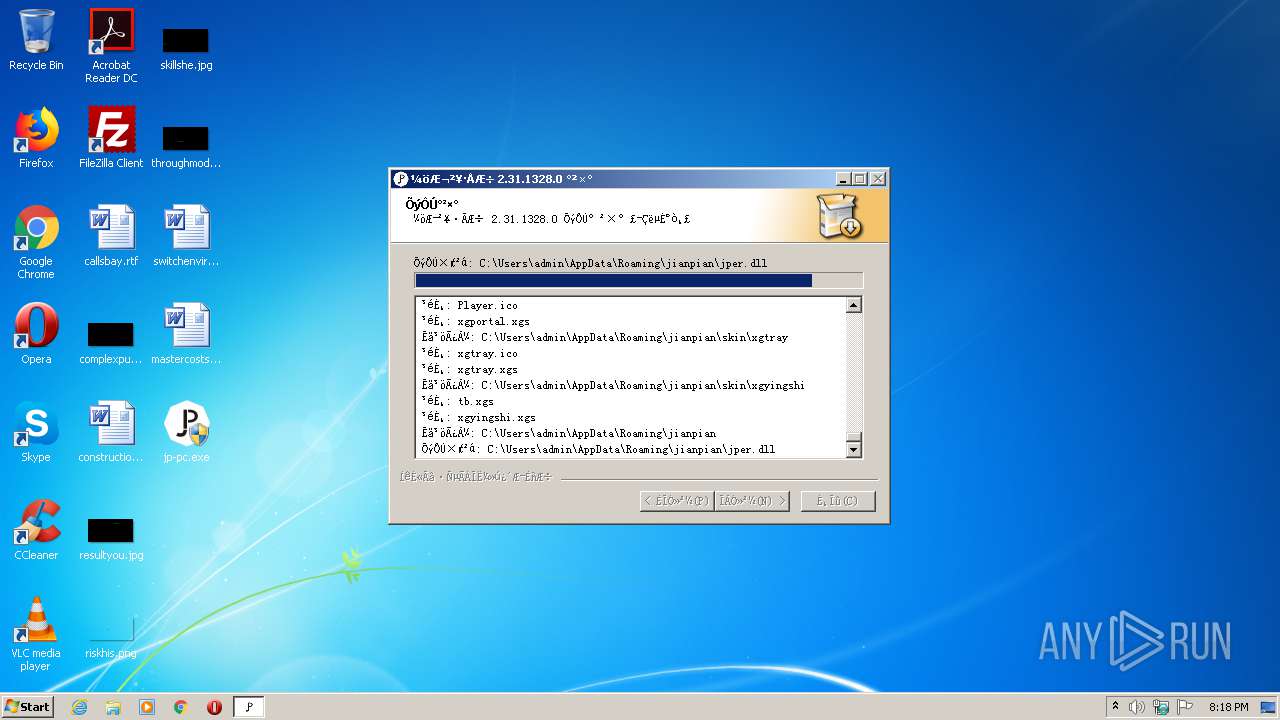
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Local\Temp\nss104C.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\SIpcObject.dll | executable | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\TaskLoop.dll | executable | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\ToolSuite.dll | executable | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Local\Temp\nss104C.tmp\modern-wizard.bmp | image | |
MD5:9E4CD80A60DB6947642677BF31A10906 | SHA256:A7B2F12E01CBEA88D4F645F797F2CA6107D76AE13CD1BE6DC532B759BFE0D925 | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\MSVCR71.DLL | executable | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\imgdecoder-gdip.dll | executable | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\SkMatrix.dll | executable | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\imgdecoder-wic.dll | executable | |
MD5:— | SHA256:— | |||
| 3848 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\imgdecoder-png.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
159
DNS requests
12
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3848 | jp-pc.exe | GET | — | 117.27.251.70:40555 | http://www.vipfanyongwang.com:40555/pc/stat?pccode=5619f625b43c5e8e3bc899b0ed05c376&product=jianpian&version=2.31.1328.0&ReportName=Install&channel=0 | CN | — | — | suspicious |
2676 | jianpian.exe | GET | — | 101.227.0.133:80 | http://static.rinhome.com/qr-code.jpg | CN | — | — | malicious |
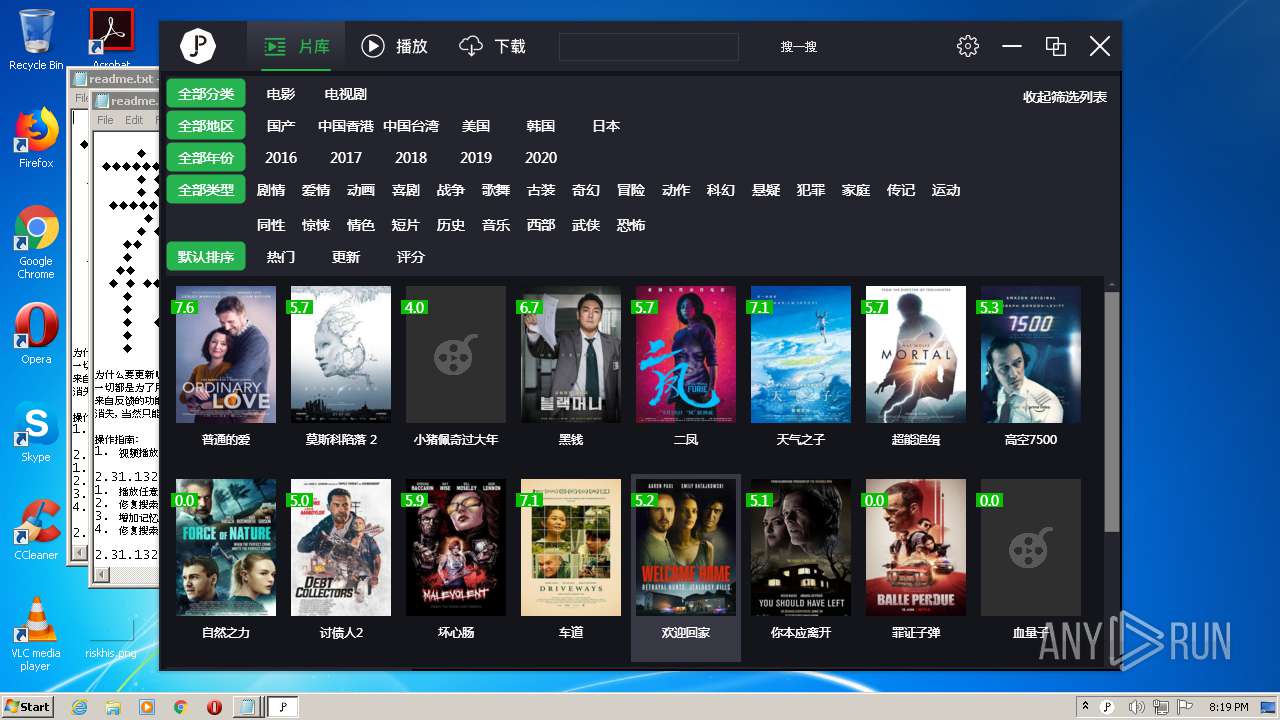
2676 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api2.rinhome.com/api/crumb/list?category_id=1&area=0&type=0&year=0&page=1&sort=update | US | text | 6.19 Kb | malicious |
2676 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api2.rinhome.com/api/ad/pc_ad | US | text | 11 b | malicious |
2676 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api2.rinhome.com/api/ad/pc_ad | US | text | 11 b | malicious |
2956 | jptray.exe | GET | 200 | 163.171.128.153:80 | http://api2.rinhome.com/api/pInfo?_=1592939959 | US | text | 1.01 Kb | malicious |
— | — | GET | 200 | 101.227.0.139:80 | http://static.rinhome.com/qr-code.jpg | CN | image | 31.7 Kb | malicious |
2676 | jianpian.exe | GET | 200 | 101.227.0.139:80 | http://static.rinhome.com/upload/video/2020/06/23/9a63b4d7ab1607d4c74c80863fd909f4.JPG | CN | image | 23.6 Kb | malicious |
2676 | jianpian.exe | GET | 200 | 101.227.0.139:80 | http://static.rinhome.com/upload/video/2019/06/08/p2557902094.jpg | CN | image | 15.8 Kb | malicious |
2676 | jianpian.exe | GET | 200 | 101.227.0.139:80 | http://static.rinhome.com/upload/video/2020/06/06/ed1ff0908c75dcfbd29981c32e486b7d.JPG | CN | image | 82.6 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | jp-pc.exe | 117.27.251.70:40555 | www.vipfanyongwang.com | Fuzhou | CN | suspicious |
3288 | jianpian_assist.exe | 163.171.128.153:80 | api2.rinhome.com | — | US | suspicious |
— | — | 163.171.128.153:80 | api2.rinhome.com | — | US | suspicious |
2676 | jianpian.exe | 163.171.128.153:80 | api2.rinhome.com | — | US | suspicious |
2956 | jptray.exe | 163.171.128.153:80 | api2.rinhome.com | — | US | suspicious |
2956 | jptray.exe | 120.79.193.150:9500 | jpupdate.140414.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2992 | jptr.exe | 117.27.251.70:40555 | www.vipfanyongwang.com | Fuzhou | CN | suspicious |
2676 | jianpian.exe | 101.227.0.133:80 | static.rinhome.com | China Telecom (Group) | CN | malicious |
— | — | 101.227.0.139:80 | static.rinhome.com | China Telecom (Group) | CN | unknown |
2676 | jianpian.exe | 101.227.0.139:80 | static.rinhome.com | China Telecom (Group) | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.vipfanyongwang.com |
| suspicious |
api2.rinhome.com |
| malicious |
jpupdate.140414.com |
| unknown |
static.rinhome.com |
| malicious |
jpp2p.140414.com |
| unknown |
jpp2ssdk.140414.com |
| unknown |
a.gbl.114s.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3492 | jpengine.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
jianpian.exe | FTH: (2676): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
jianpian.exe | FTH: (3164): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
jptray.exe | FTH: (2956): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
jptr.exe | FTH: (2992): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
jianpian.exe | ResourceApi::getList => http://api2.rinhome.com/api/crumb/list?category_id=1&area=0&type=0&year=0&page=1&sort=update
|
jpengine.exe | FTH: (3492): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
jpengine.exe | FTH: (3236): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
jpengine.exe | FTH: (3000): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
jianpian.exe | ResourceApi::getDetail => http://api2.rinhome.com/api/node/detail?id=553324
|
jptr.exe | FTH: (2908): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|