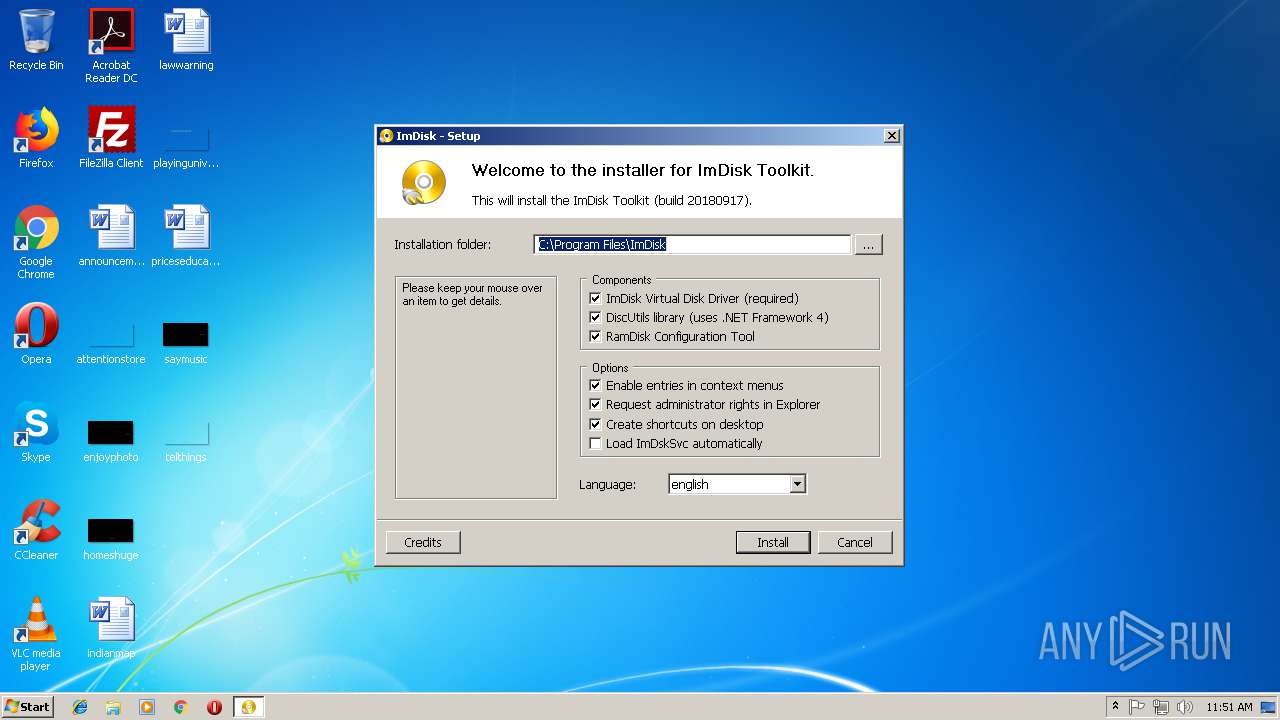
| File name: | ImDiskTk.exe |
| Full analysis: | https://app.any.run/tasks/80bbc4dd-0eb4-40c5-b391-35116f23e30c |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2018, 10:51:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | AE4689594B35797B62E386D347A8A55C |
| SHA1: | CB82BDB19B7EEB86DEFC1A742FA4586FB4FB411C |
| SHA256: | 7BF27E1759C261FD01353575A4B3462ADEBB779B9A720D123CC9C907E03C5B32 |
| SSDEEP: | 12288:gxscipO5WbGrz0G8usI7g++t7Vo67dc/ZXFlYYwyP8hhySlpu31WpqdsMn6Tw:gxz5WKH0/m50Vo67WFFZt8LtlpuFgqdj |
MALICIOUS
Application was dropped or rewritten from another process
- config.exe (PID: 1088)
- config.exe (PID: 2740)
- MountImg.exe (PID: 1480)
- MountImg.exe (PID: 324)
- MountImg.exe (PID: 120)
- MountImg.exe (PID: 3360)
Changes the autorun value in the registry
- rundll32.exe (PID: 1340)
Loads dropped or rewritten executable
- explorer.exe (PID: 1604)
- MountImg.exe (PID: 324)
- svchost.exe (PID: 852)
- MountImg.exe (PID: 120)
- rundll32.exe (PID: 1824)
SUSPICIOUS
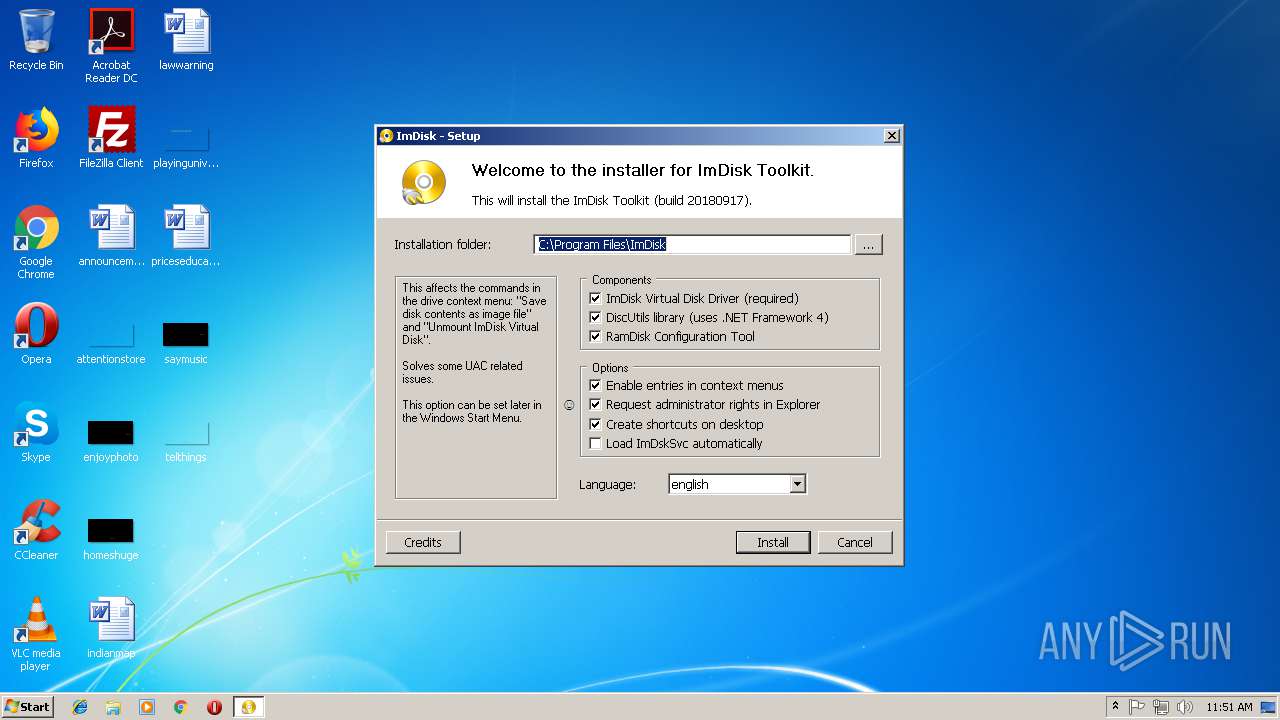
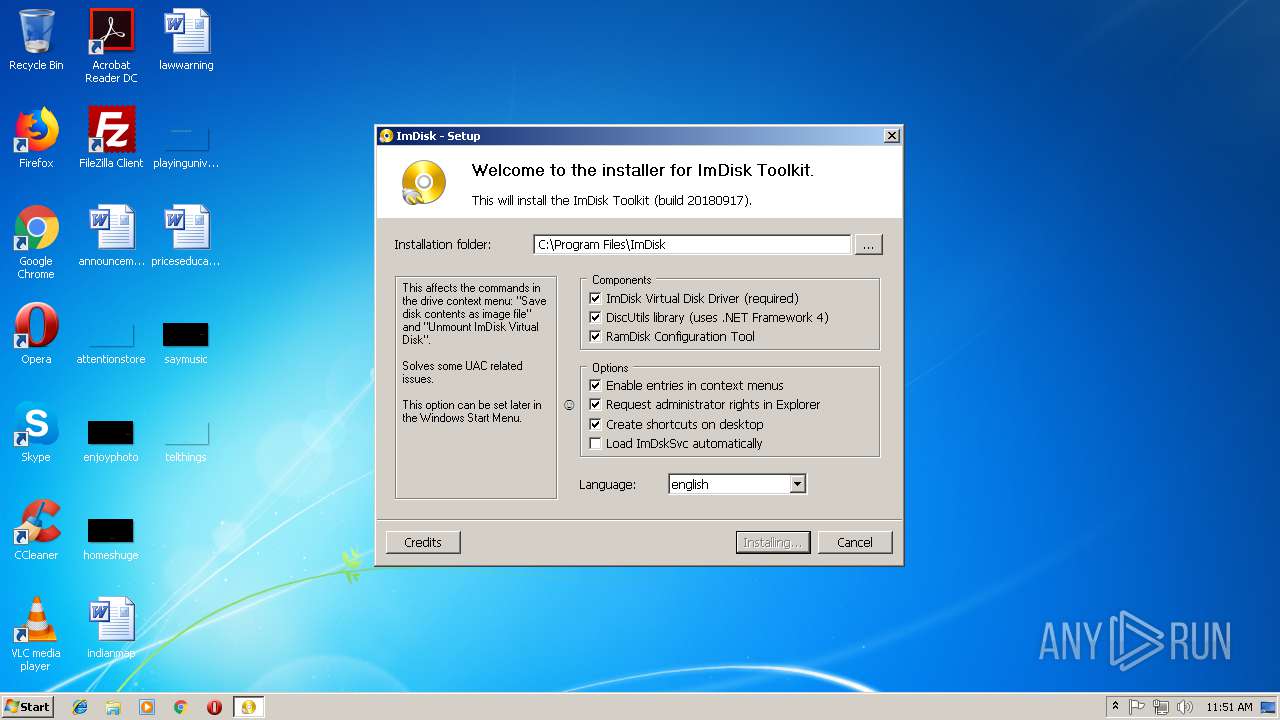
Executable content was dropped or overwritten
- ImDiskTk.exe (PID: 2488)
- config.exe (PID: 2740)
- rundll32.exe (PID: 1340)
Creates files in the driver directory
- rundll32.exe (PID: 1340)
Creates a software uninstall entry
- rundll32.exe (PID: 1340)
- config.exe (PID: 2740)
Creates files in the Windows directory
- rundll32.exe (PID: 1340)
Removes files from Windows directory
- rundll32.exe (PID: 1340)
Creates files in the user directory
- config.exe (PID: 2740)
Creates files in the program directory
- config.exe (PID: 2740)
Uses REG.EXE to modify Windows registry
- config.exe (PID: 2740)
Application launched itself
- MountImg.exe (PID: 1480)
- MountImg.exe (PID: 3360)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:17 17:50:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 20480 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 57344 |
| EntryPoint: | 0x13560 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2018.9.17.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
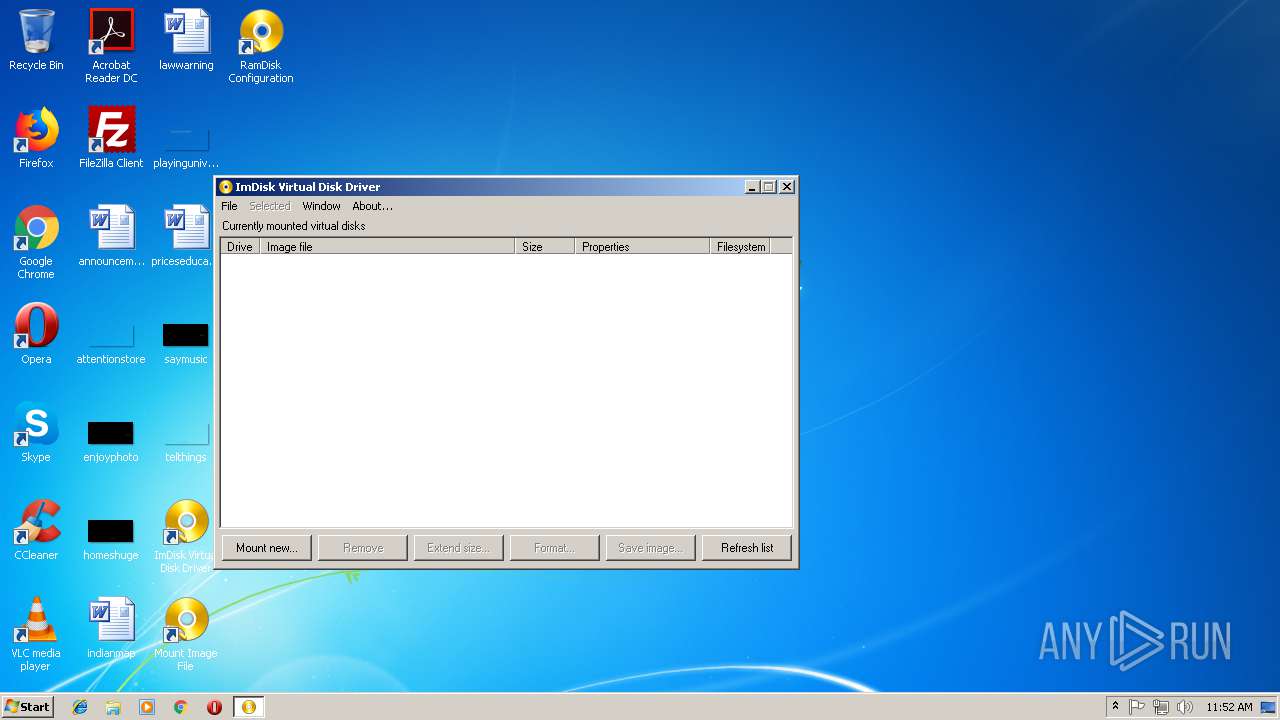
| FileDescription: | ImDisk Toolkit |
| ProductName: | imdisk |
| ProductVersion: | 2018.09.17.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Sep-2018 15:50:09 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Sep-2018 15:50:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
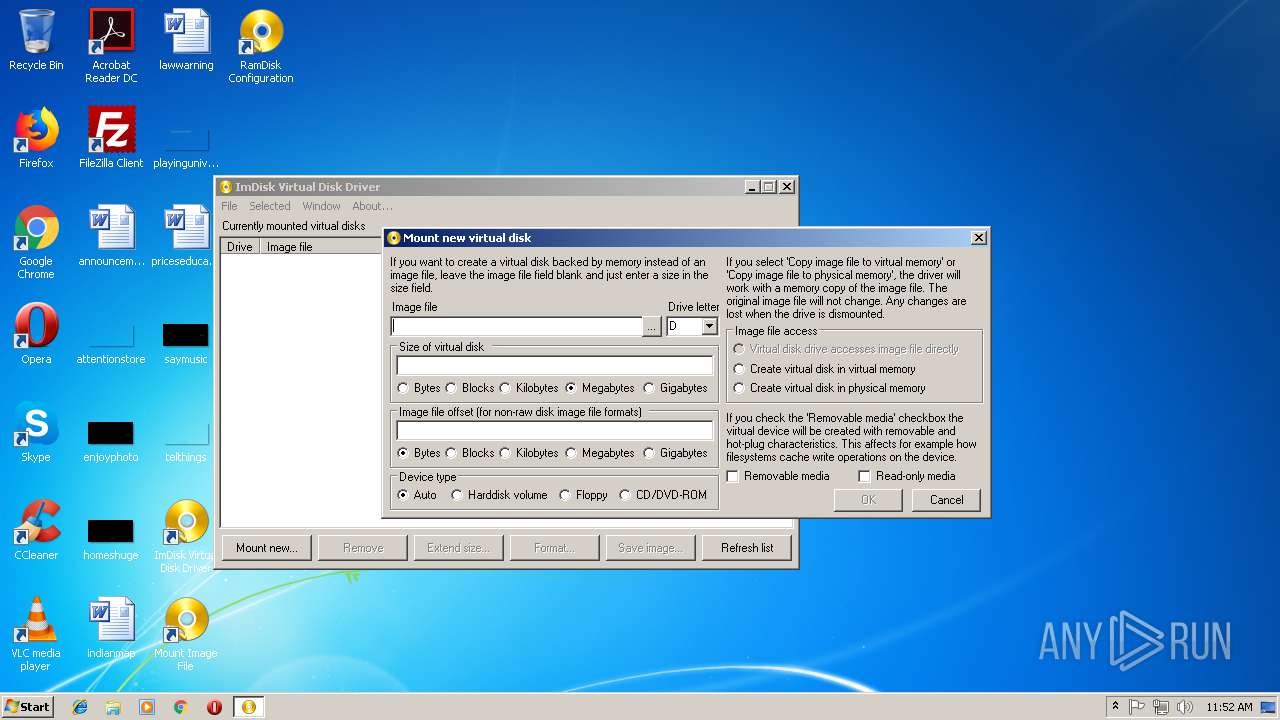
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0000F000 | 0x00005000 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.86056 |
.rsrc | 0x00014000 | 0x00001000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.2864 |
Imports
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
Total processes
54
Monitored processes
14
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
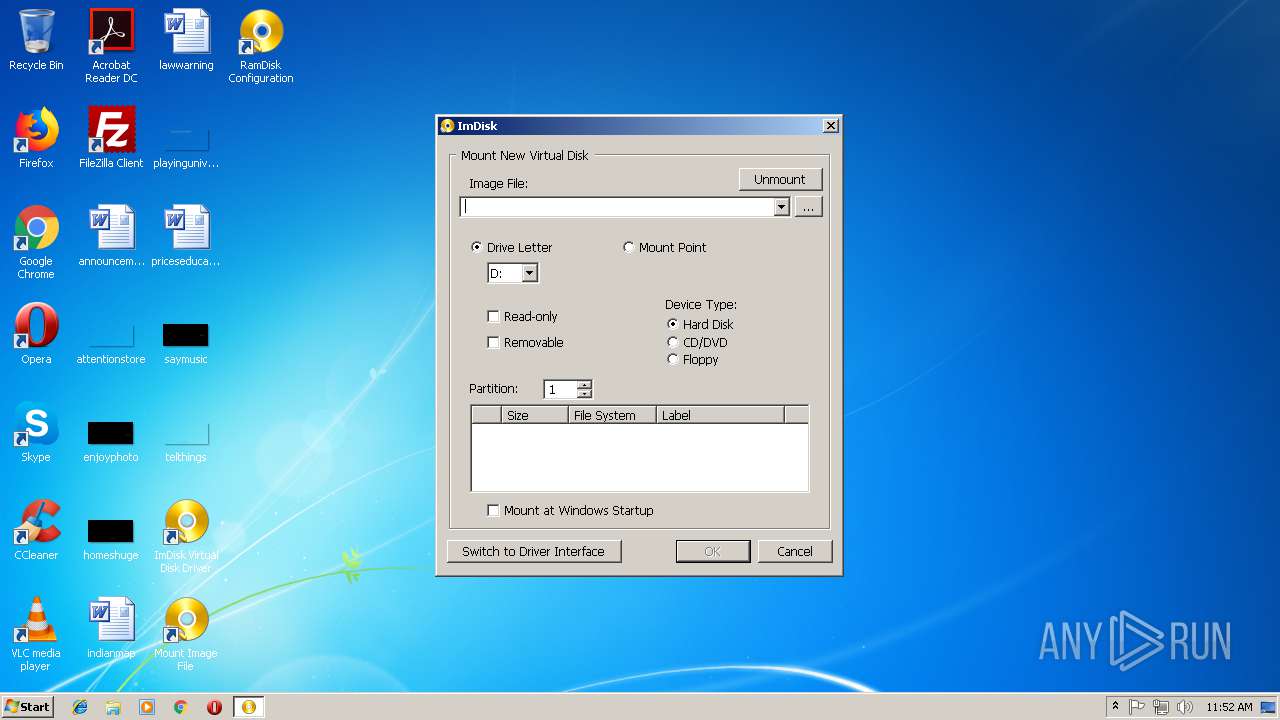
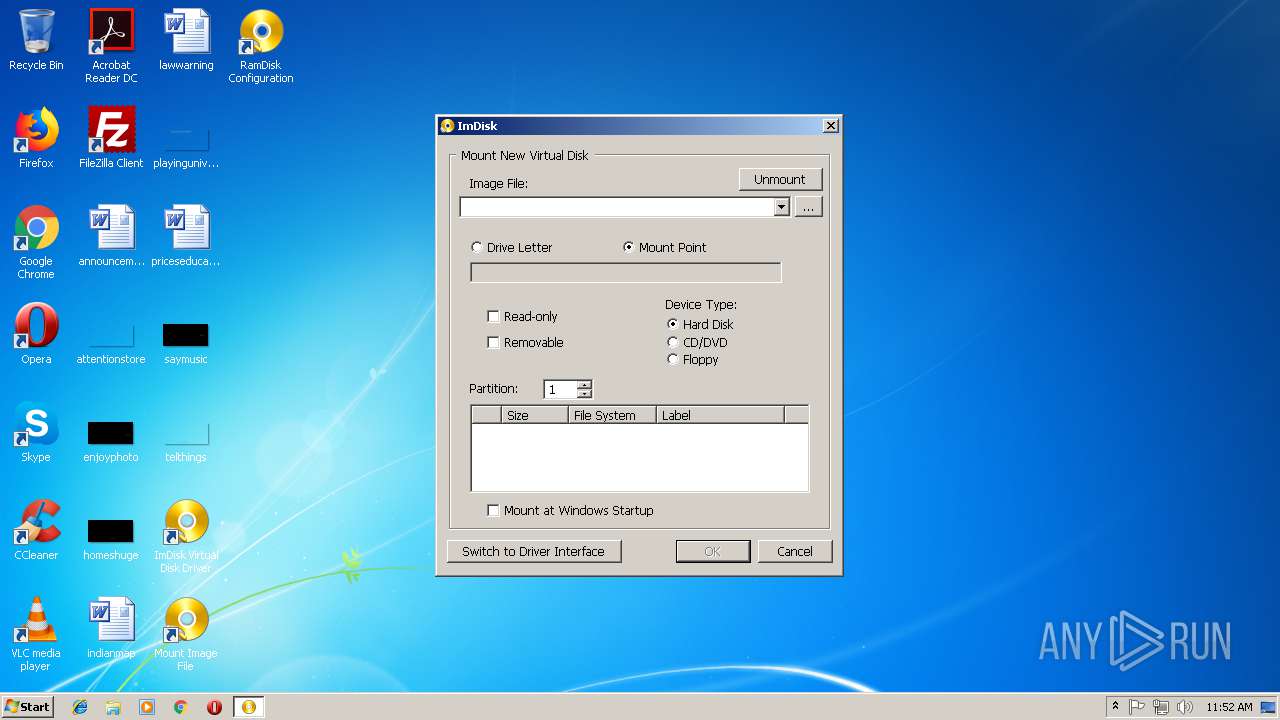
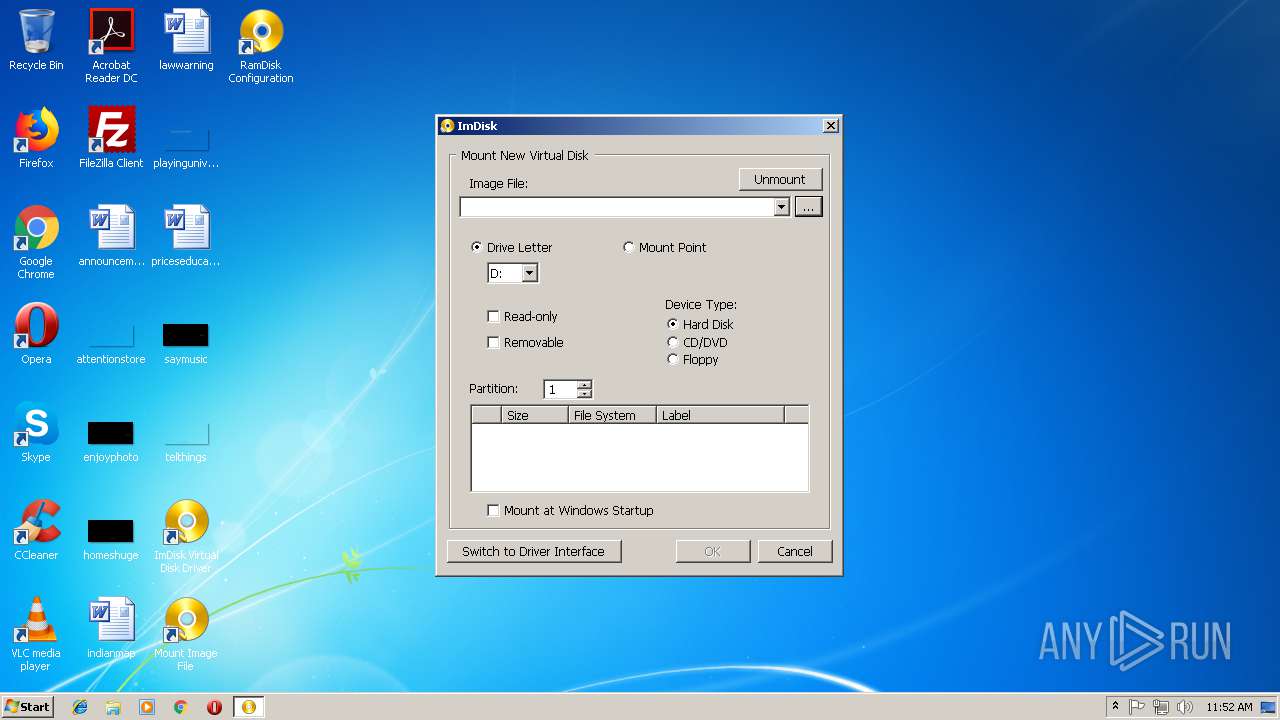
| 120 | "C:\Program Files\ImDisk\MountImg.exe" /UAC 4 "" | C:\Program Files\ImDisk\MountImg.exe | MountImg.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Mount new virtual disk Exit code: 0 Modules
| |||||||||||||||
| 324 | "C:\Program Files\ImDisk\MountImg.exe" /UAC 4 "" | C:\Program Files\ImDisk\MountImg.exe | MountImg.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Mount new virtual disk Exit code: 0 Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
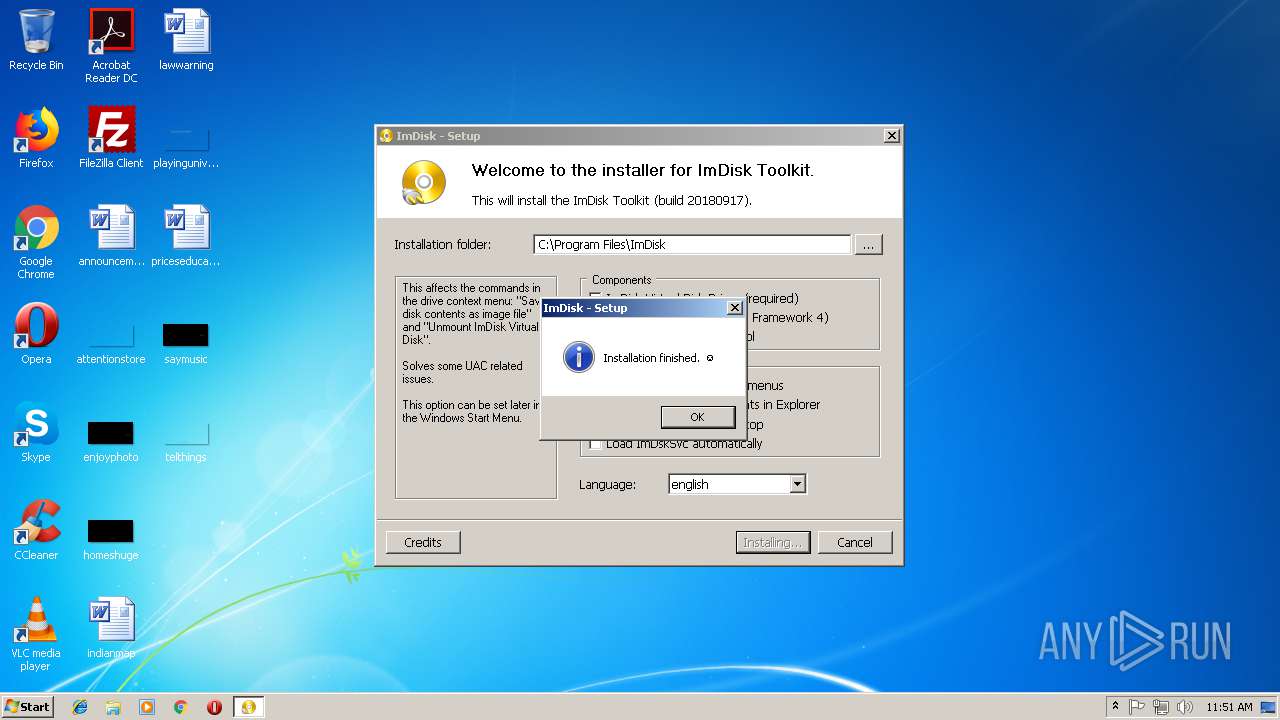
| 1088 | "C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\config.exe" | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\config.exe | — | ImDiskTk.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ImDisk Toolkit Configuration Exit code: 3221226540 Modules
| |||||||||||||||
| 1340 | rundll32 setupapi.dll,InstallHinfSection DefaultInstall 128 driver\imdisk.inf | C:\Windows\system32\rundll32.exe | config.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
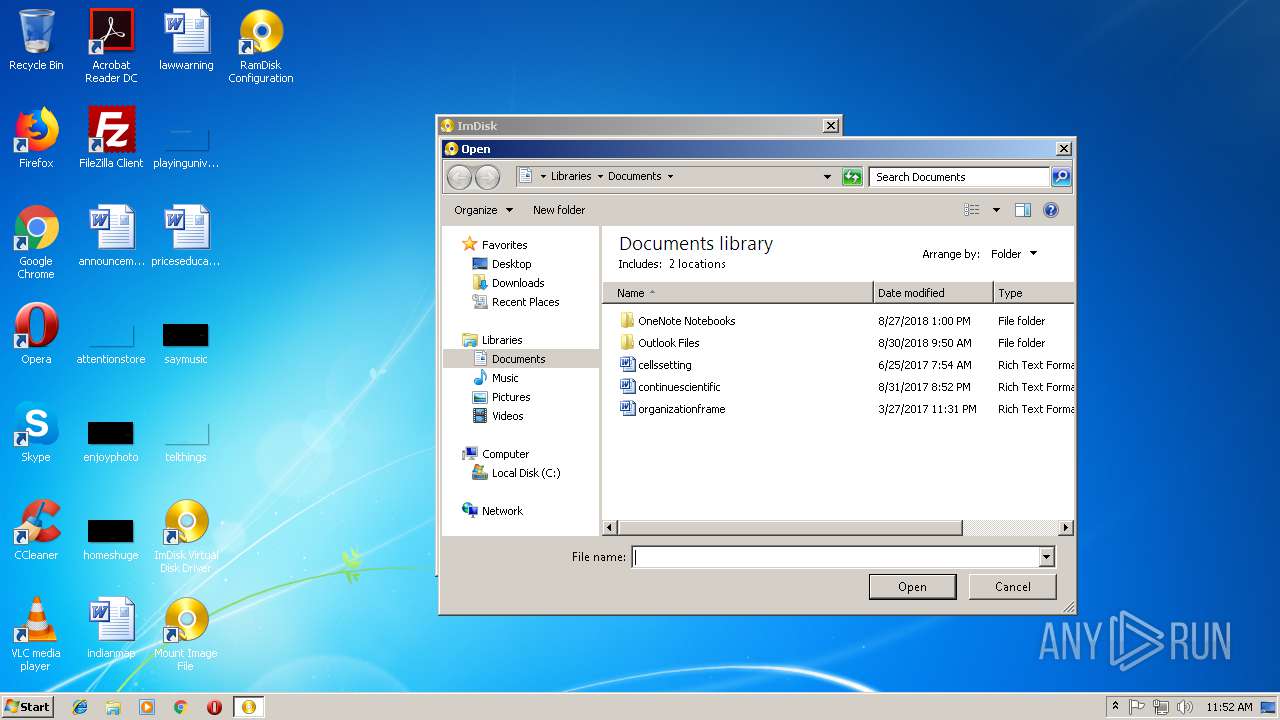
| 1480 | "C:\Program Files\ImDisk\MountImg.exe" | C:\Program Files\ImDisk\MountImg.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Mount new virtual disk Exit code: 0 Modules
| |||||||||||||||
| 1604 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,Control_RunDLL "C:\WINDOWS\System32\imdisk.cpl",ImDisk Virtual Disk Driver | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2020 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2488 | "C:\Users\admin\AppData\Local\Temp\ImDiskTk.exe" | C:\Users\admin\AppData\Local\Temp\ImDiskTk.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ImDisk Toolkit Exit code: 0 Modules
| |||||||||||||||
Total events
3 058
Read events
2 874
Write events
177
Delete events
7
Modification events
| (PID) Process: | (2488) ImDiskTk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2488) ImDiskTk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 7 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 6 | |||
| (PID) Process: | (1340) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (1340) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ImDisk |
| Operation: | write | Name: | DisplayName |
Value: ImDisk Virtual Disk Driver | |||
| (PID) Process: | (1340) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ImDisk |
| Operation: | write | Name: | Publisher |
Value: LTR Data | |||
| (PID) Process: | (1340) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ImDisk |
| Operation: | write | Name: | HelpLink |
Value: http://ltr-data.se/opencode.html | |||
| (PID) Process: | (1340) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ImDisk |
| Operation: | write | Name: | DisplayVersion |
Value: * | |||
| (PID) Process: | (1340) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ImDisk |
| Operation: | write | Name: | UninstallString |
Value: "%SystemRoot%\system32\cmd.exe" /c "%SystemRoot%\system32\uninstall_imdisk.cmd" | |||
Executable files
41
Suspicious files
0
Text files
70
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\cp.lnk | lnk | |
MD5:01F6F1D478E814A27CE948BFFBA707F7 | SHA256:FB5020EDF6E9DBF96117D137F5A3AE9281A3057735D850BA8B9327B55773EA3D | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\driver\cpl\imdisk.cpl.manifest | xml | |
MD5:CEDD91F280CD79DE51ACD8D0119E0732 | SHA256:33AB6D07DC9C76E67EC0A7D1CEA054E5B83274DB705324EE157921B2FD48449A | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\lang\german.txt | html | |
MD5:— | SHA256:— | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\lang\french.txt | html | |
MD5:— | SHA256:— | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\lang\russian.txt | html | |
MD5:— | SHA256:— | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\lang\spanish.txt | html | |
MD5:— | SHA256:— | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\lang\swedish.txt | html | |
MD5:— | SHA256:— | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\lang\english.txt | html | |
MD5:— | SHA256:— | |||
| 2488 | ImDiskTk.exe | C:\Users\admin\AppData\Local\Temp\7z42C1F00E3F0\config.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report