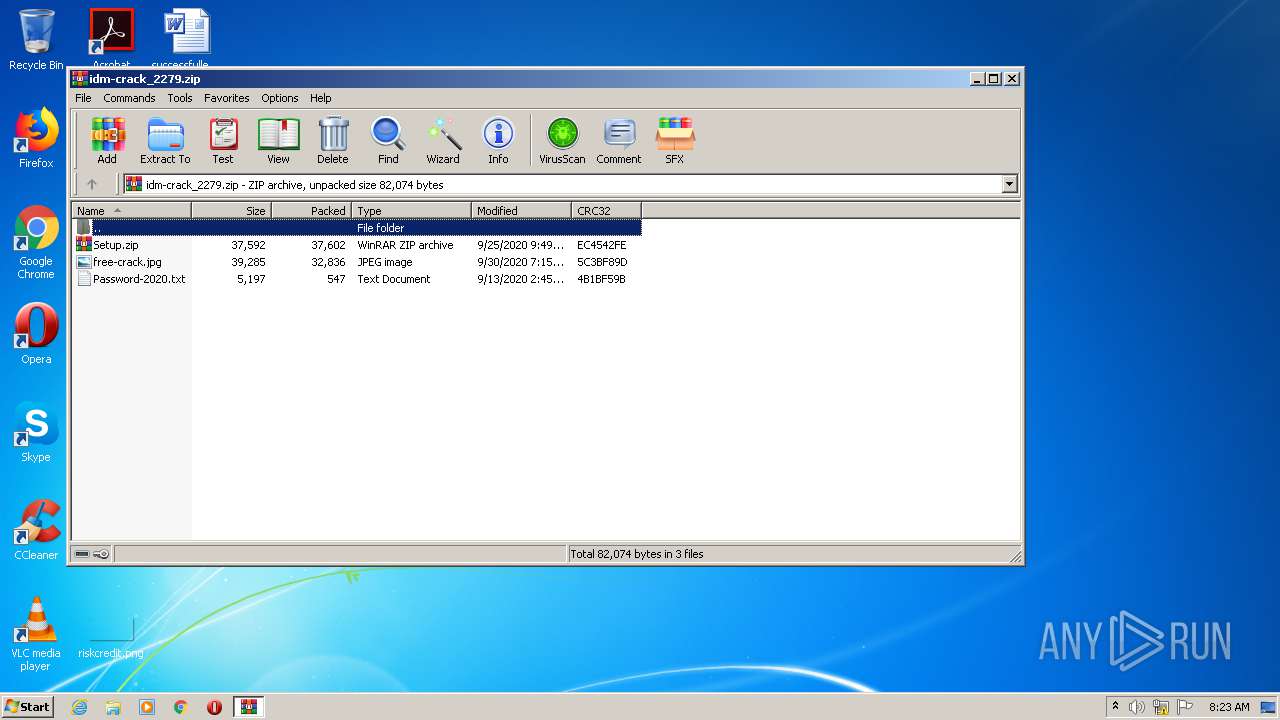
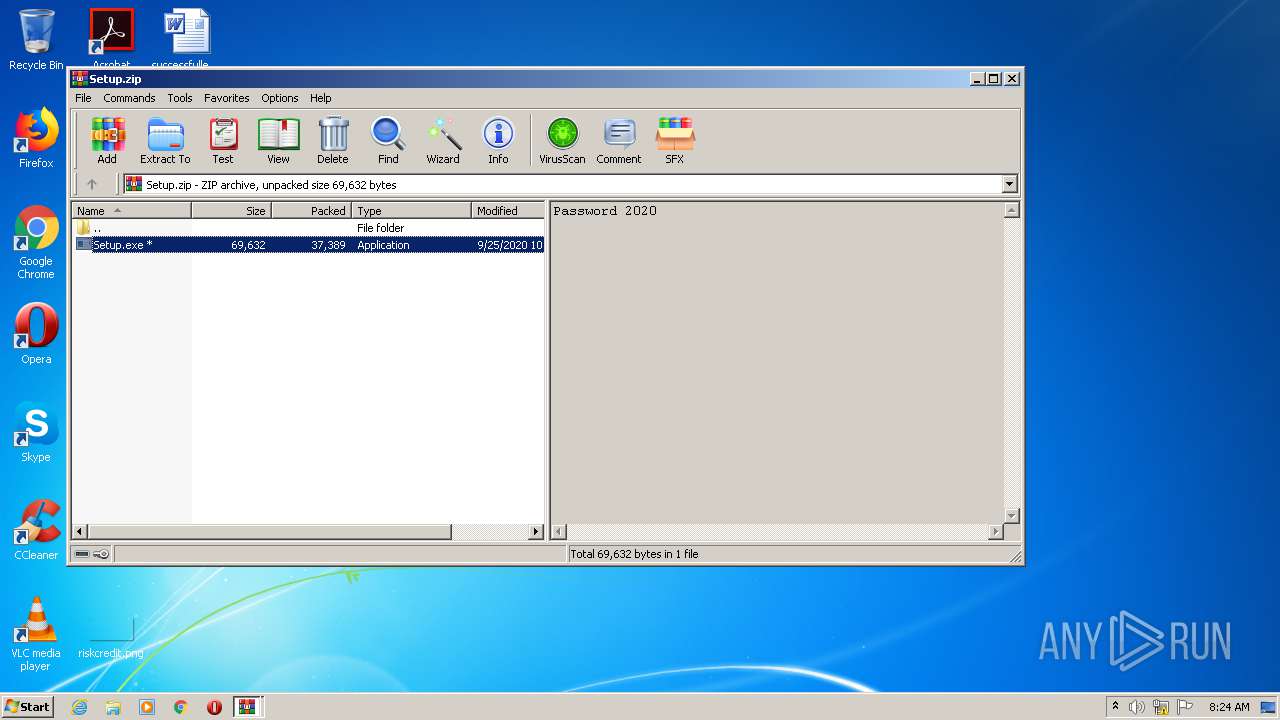
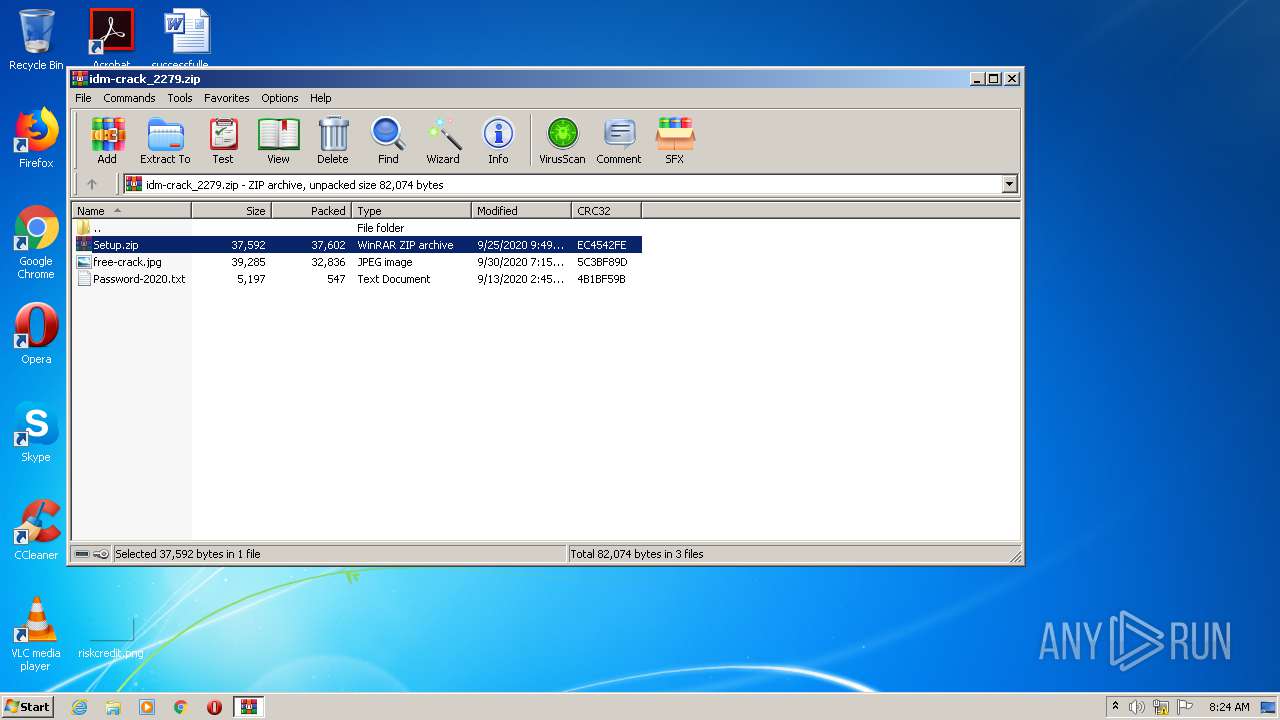
| File name: | idm-crack_2279.zip |
| Full analysis: | https://app.any.run/tasks/9cbe68a2-4d71-400d-b175-4feeace206bd |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 07:23:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4B3D410CC7DF0C4587A809DA50CEF1C4 |
| SHA1: | E5F368CBEF98E64E834C592EABE0CA3256DDFBAD |
| SHA256: | 7BEBC916EC79A59617F0D1D85DB9ADE06149671E714DD3FF9D97203EB6669714 |
| SSDEEP: | 1536:FOE3UhPenDaYgg8O6Zf9vK7lUJF01Lada7tR/sJ9GAs21LtSM:FDEgnDwBOEyYaUI7ja9HskLAM |
MALICIOUS
Application was dropped or rewritten from another process
- Setup.exe (PID: 3892)
- Setup.exe (PID: 3380)
Deletes shadow copies
- cmd.exe (PID: 2832)
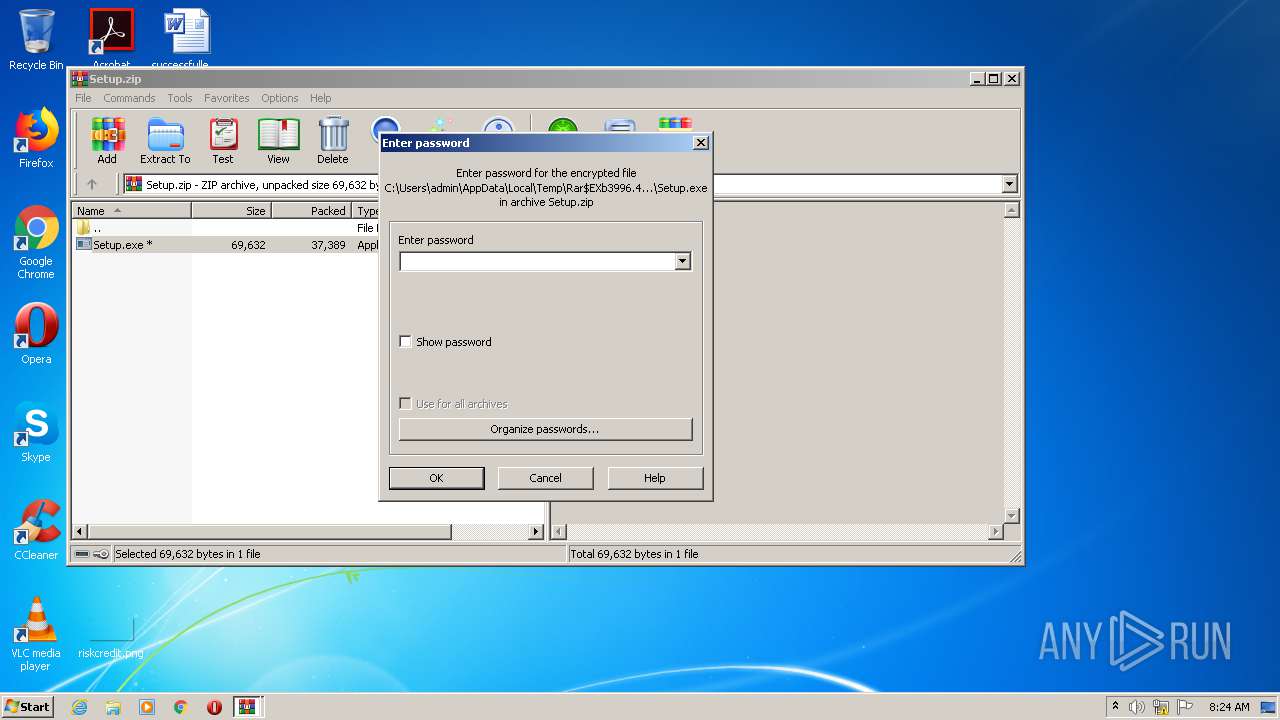
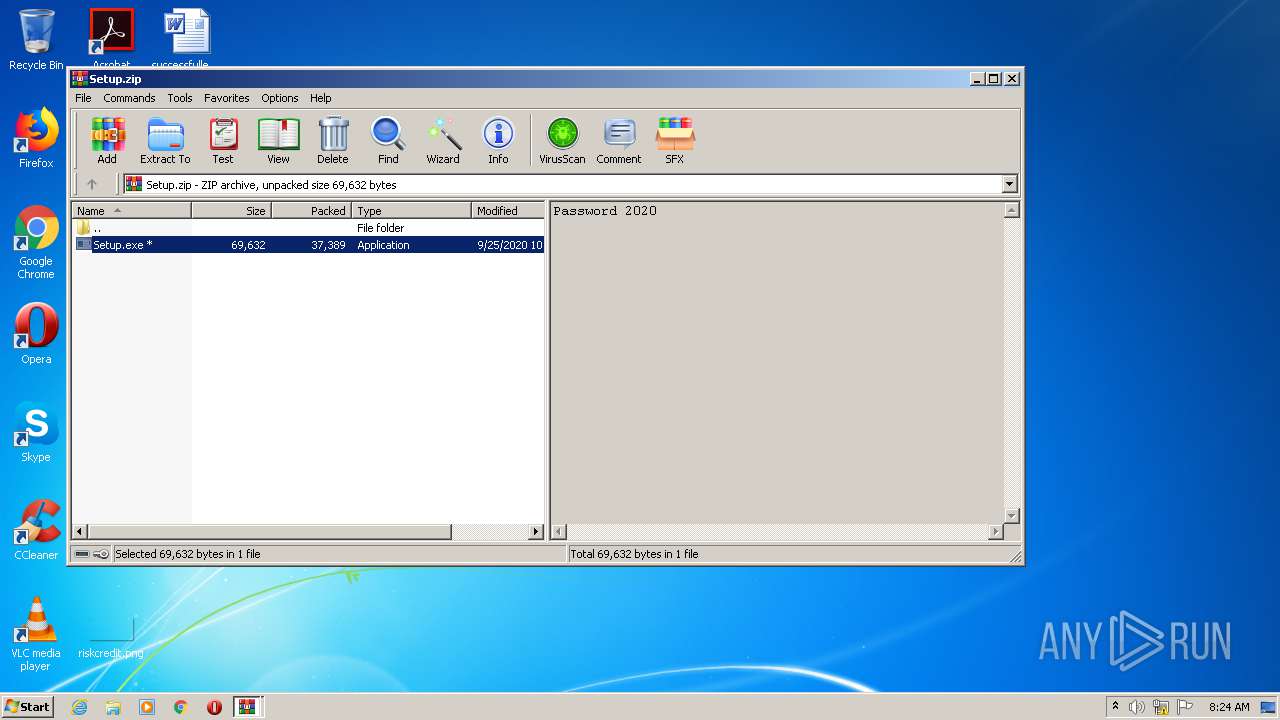
Actions looks like stealing of personal data
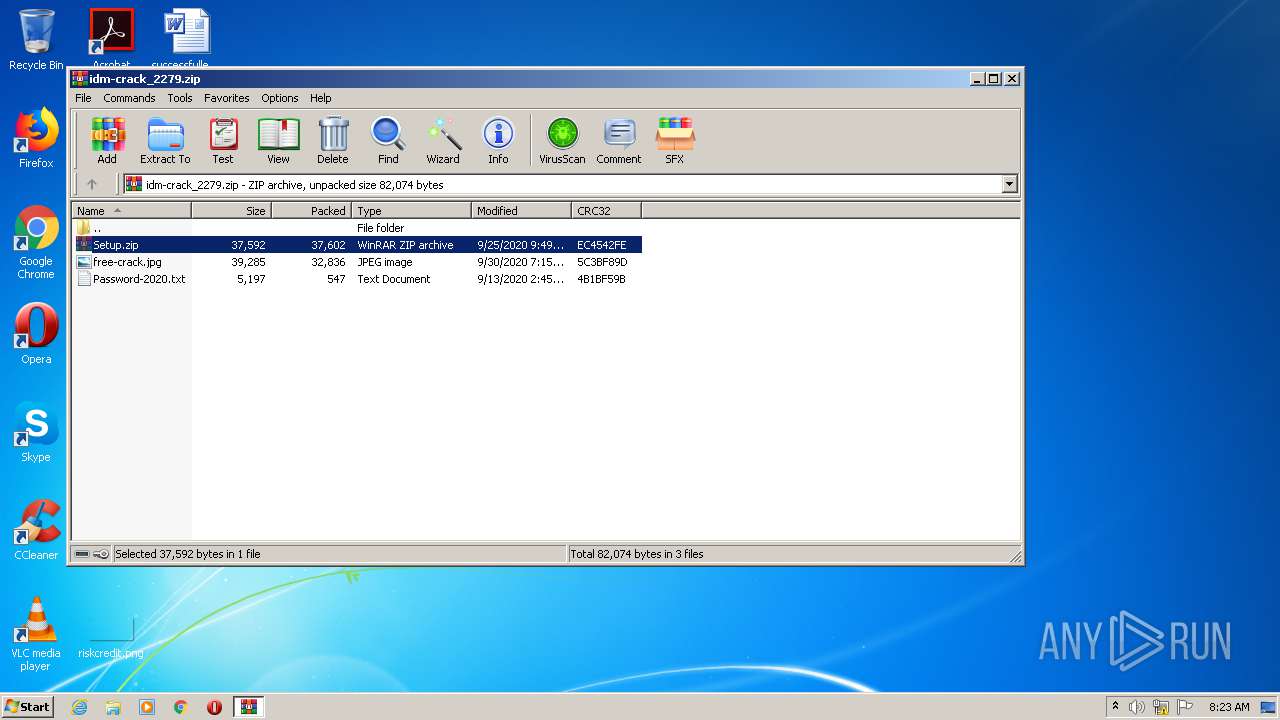
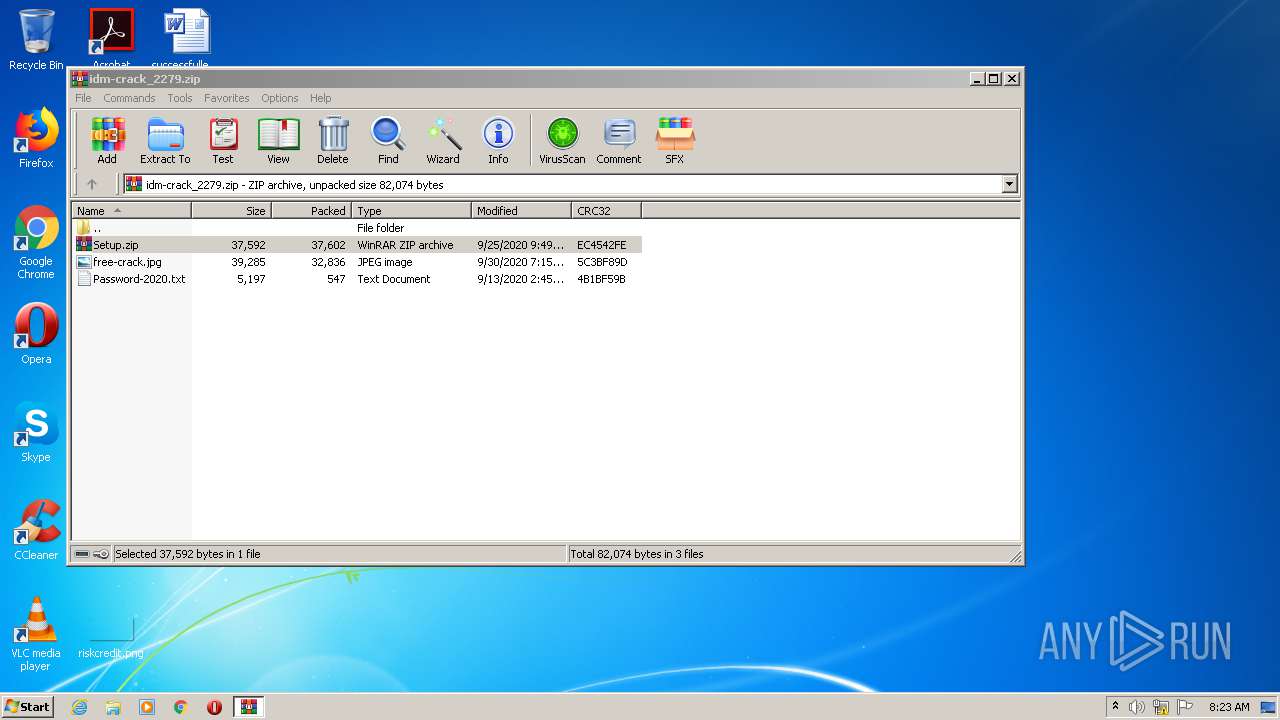
- WinRAR.exe (PID: 3996)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3344)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 2264)
Executed as Windows Service
- vssvc.exe (PID: 2156)
Starts CMD.EXE for commands execution
- Setup.exe (PID: 3892)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3996)
Writes to a desktop.ini file (may be used to cloak folders)
- Setup.exe (PID: 3892)
Connects to server without host name
- Setup.exe (PID: 3892)
Executed via COM
- DllHost.exe (PID: 2000)
Reads Internet Cache Settings
- DllHost.exe (PID: 2000)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:09:13 14:45:23 |
| ZipCRC: | 0x4b1bf59b |
| ZipCompressedSize: | 547 |
| ZipUncompressedSize: | 5197 |
| ZipFileName: | Password-2020.txt |
Total processes
61
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 200 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 216 | cmd /C wbadmin DELETE SYSTEMSTATEBACKUP -deleteOldest | C:\Windows\system32\cmd.exe | Setup.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 4294967293 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1148 | cmd /C bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\cmd.exe | Setup.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1168 | cmd /C wmic SHADOWCOPY /nointeractive | C:\Windows\system32\cmd.exe | Setup.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 44124 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1544 | vssadmin Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | wbadmin DELETE SYSTEMSTATEBACKUP | C:\Windows\system32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\idm-crack_2279.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2832 | cmd /C vssadmin Delete Shadows /All /Quiet | C:\Windows\system32\cmd.exe | Setup.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 373
Read events
1 250
Write events
110
Delete events
13
Modification events
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\idm-crack_2279.zip | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (3996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
1
Suspicious files
4
Text files
9
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | Setup.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.luFQjW | — | |
MD5:— | SHA256:— | |||
| 2264 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2264.46318\Setup.zip | compressed | |
MD5:— | SHA256:— | |||
| 3996 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3996.47225\Setup.exe | executable | |
MD5:— | SHA256:— | |||
| 1704 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.1.etl | etl | |
MD5:— | SHA256:— | |||
| 3892 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Microsoft\Windows\Ui5caD\windows.sys:ymiuwsmgitpdtbmh | text | |
MD5:— | SHA256:— | |||
| 3892 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Microsoft\Windows\FlHUhX\windows.sys:lyhxozmopp | text | |
MD5:— | SHA256:— | |||
| 3892 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Microsoft\Windows\p4a7Ux\windows.sys:yoglygxpztqveikkj | text | |
MD5:— | SHA256:— | |||
| 3892 | Setup.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi.luFQjW | binary | |
MD5:— | SHA256:— | |||
| 3892 | Setup.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi.luFQjWkey | binary | |
MD5:— | SHA256:— | |||
| 3892 | Setup.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.luFQjWkey | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | Setup.exe | POST | — | 51.83.171.36:80 | http://51.83.171.36/fgate | GB | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | Setup.exe | 51.83.171.35:80 | — | — | GB | malicious |
3892 | Setup.exe | 51.83.171.36:80 | — | — | GB | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3892 | Setup.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3892 | Setup.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |