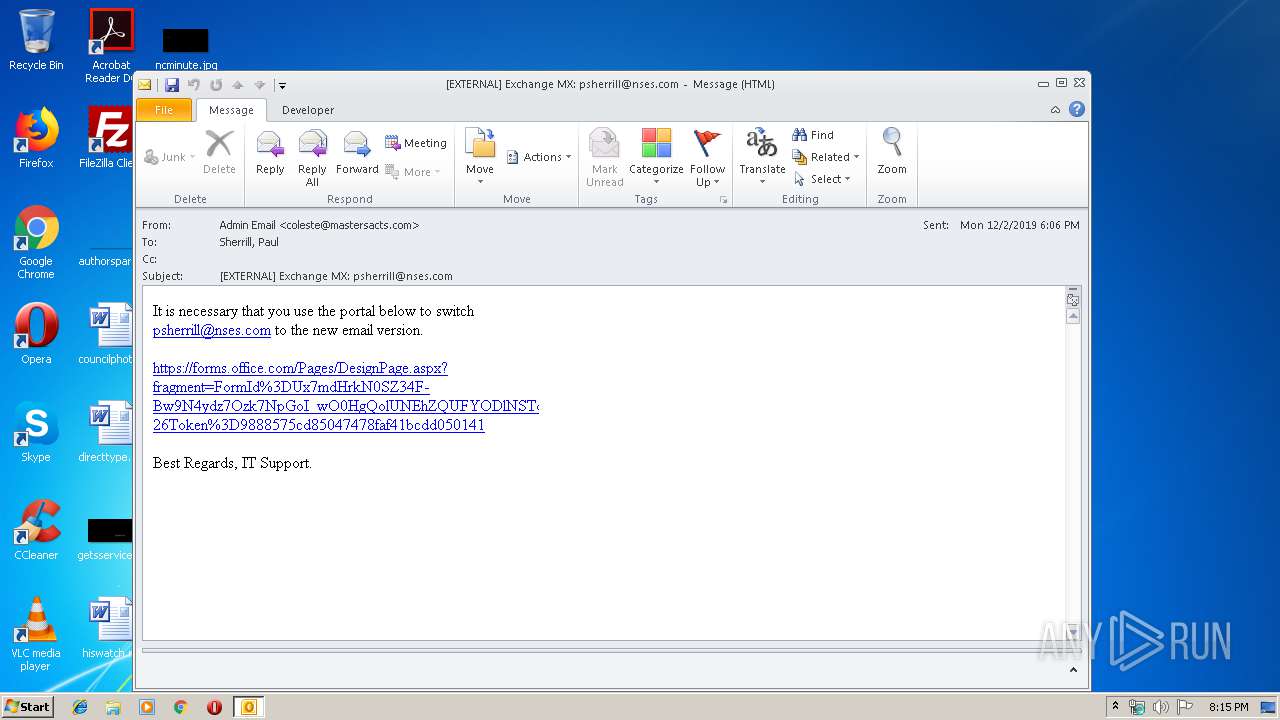
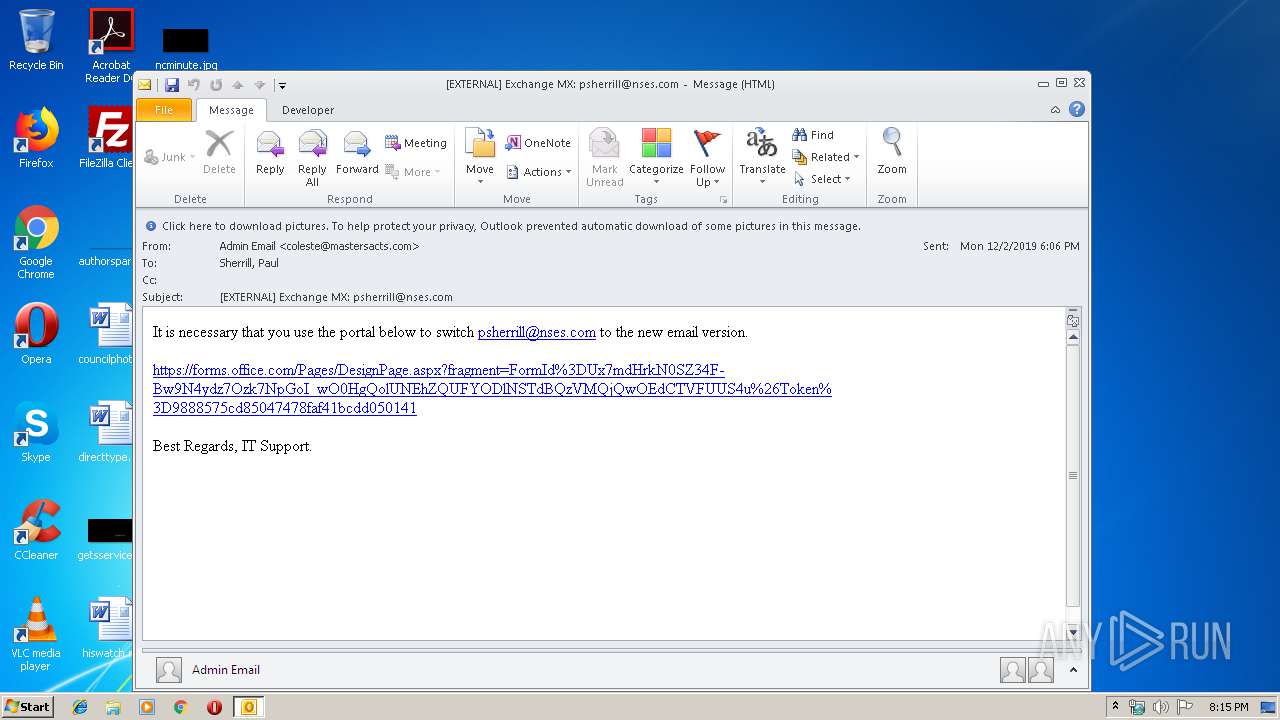
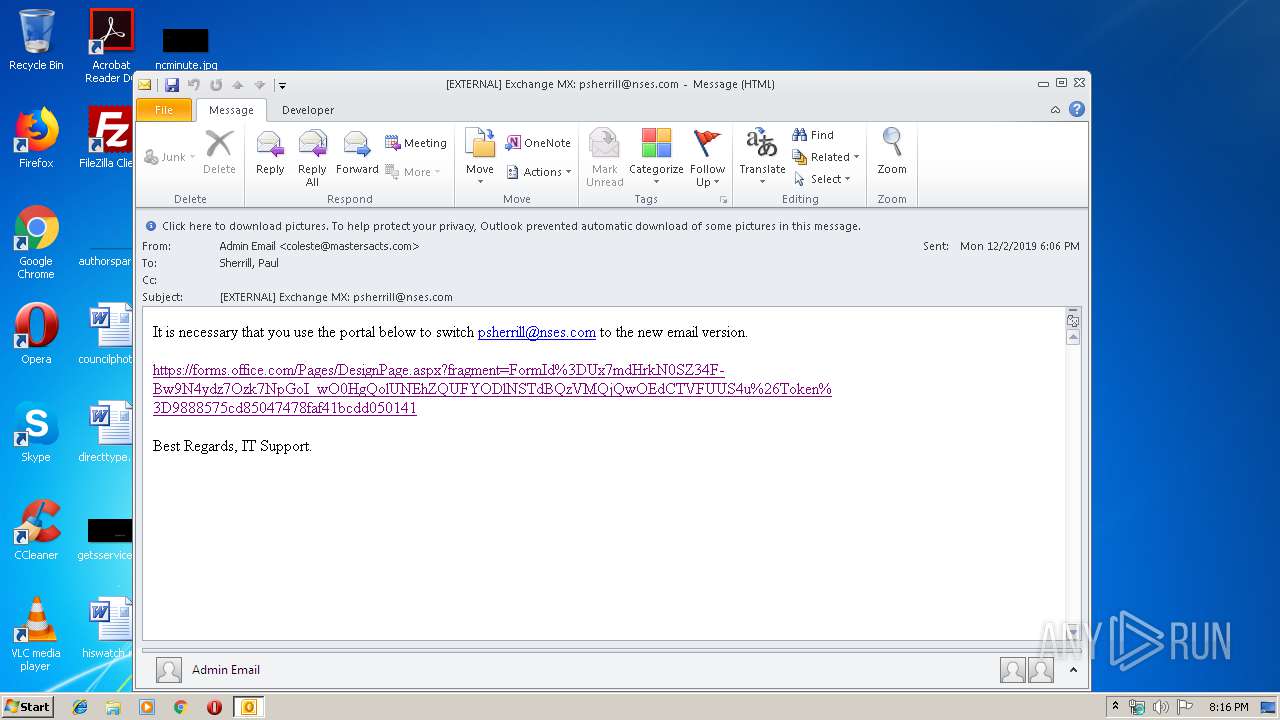
| File name: | EXTERNAL Exchange MX psherrill@nses.com.msg |
| Full analysis: | https://app.any.run/tasks/7f2cce8f-4523-452d-95c2-211228f93ac6 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 20:15:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A524A7BF7CFA94D2BF42460E985F3826 |
| SHA1: | 5CD69818DA1ADBA96AA2D536B59108E89A27B9CC |
| SHA256: | 7BE78F881980C498E89BF90389AB90DEB067A659F670908824AD55B6F22394AF |
| SSDEEP: | 768:DbUWsKeWsKwLmeWsK18mk/DNhQ9qHzK+13TTWsKuMWU5:DIWGWoLmeWd8m+K+tW |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2844)
SUSPICIOUS
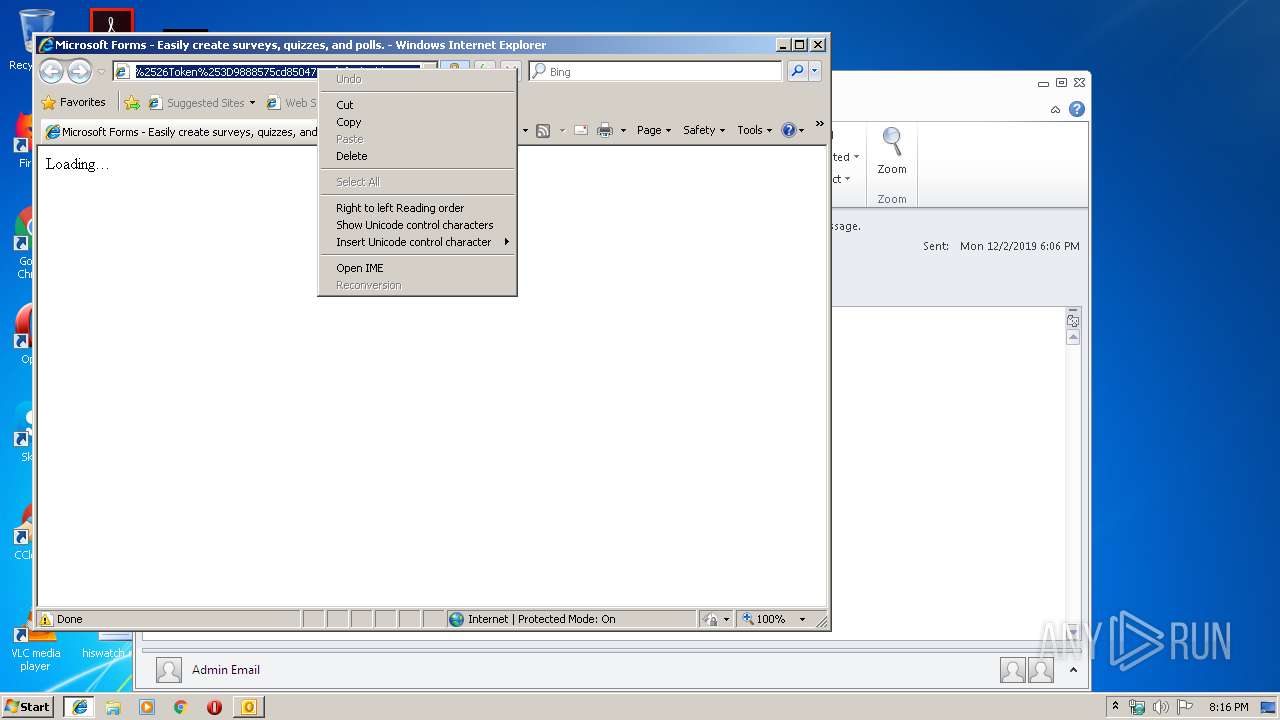
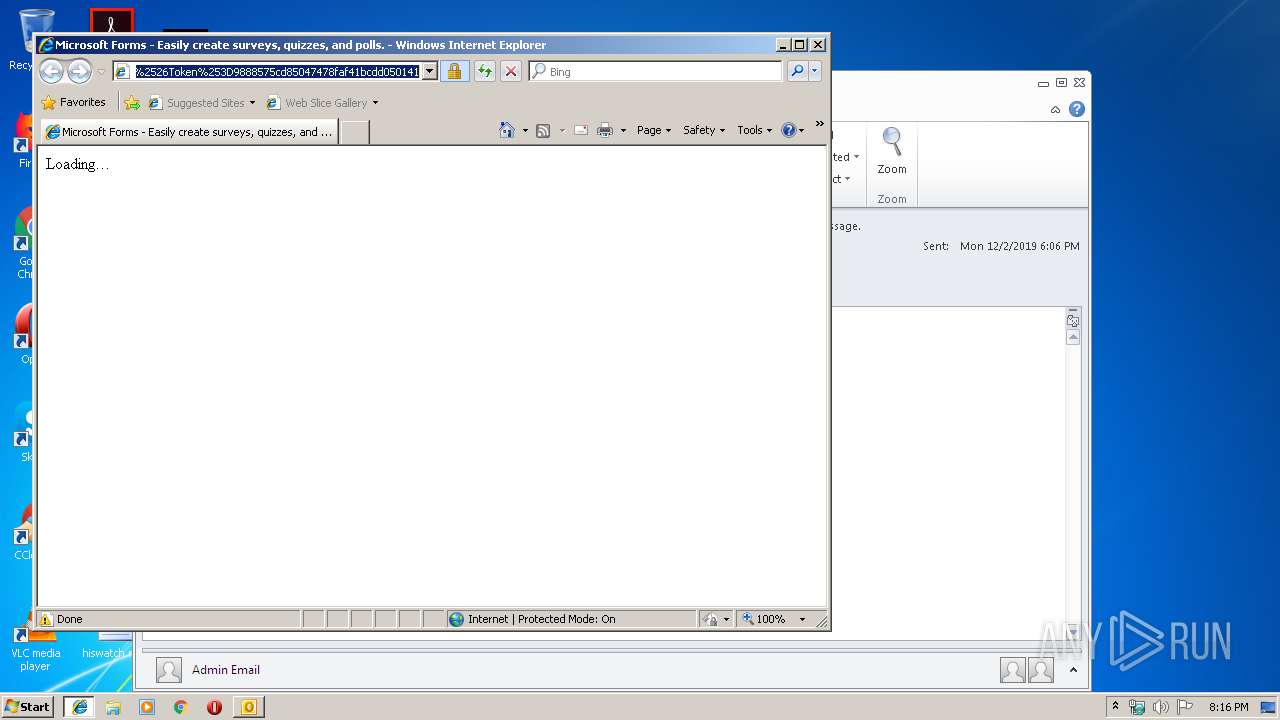
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2844)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2844)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2844)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2528)
INFO
Application launched itself
- iexplore.exe (PID: 748)
- chrome.exe (PID: 2528)
Reads Internet Cache Settings
- iexplore.exe (PID: 1292)
Changes internet zones settings
- iexplore.exe (PID: 748)
Creates files in the user directory
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 748)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1292)
Adds / modifies Windows certificates
- iexplore.exe (PID: 748)
Reads settings of System Certificates
- iexplore.exe (PID: 748)
Changes settings of System certificates
- iexplore.exe (PID: 748)
Reads internet explorer settings
- iexplore.exe (PID: 1292)
Reads the hosts file
- chrome.exe (PID: 2528)
- chrome.exe (PID: 1428)
Manual execution by user
- chrome.exe (PID: 2528)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
75
Monitored processes
37
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5460177980079649694 --mojo-platform-channel-handle=2800 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3446848107382292506 --mojo-platform-channel-handle=1936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10015489956693251071 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8957920178835793617 --mojo-platform-channel-handle=4064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
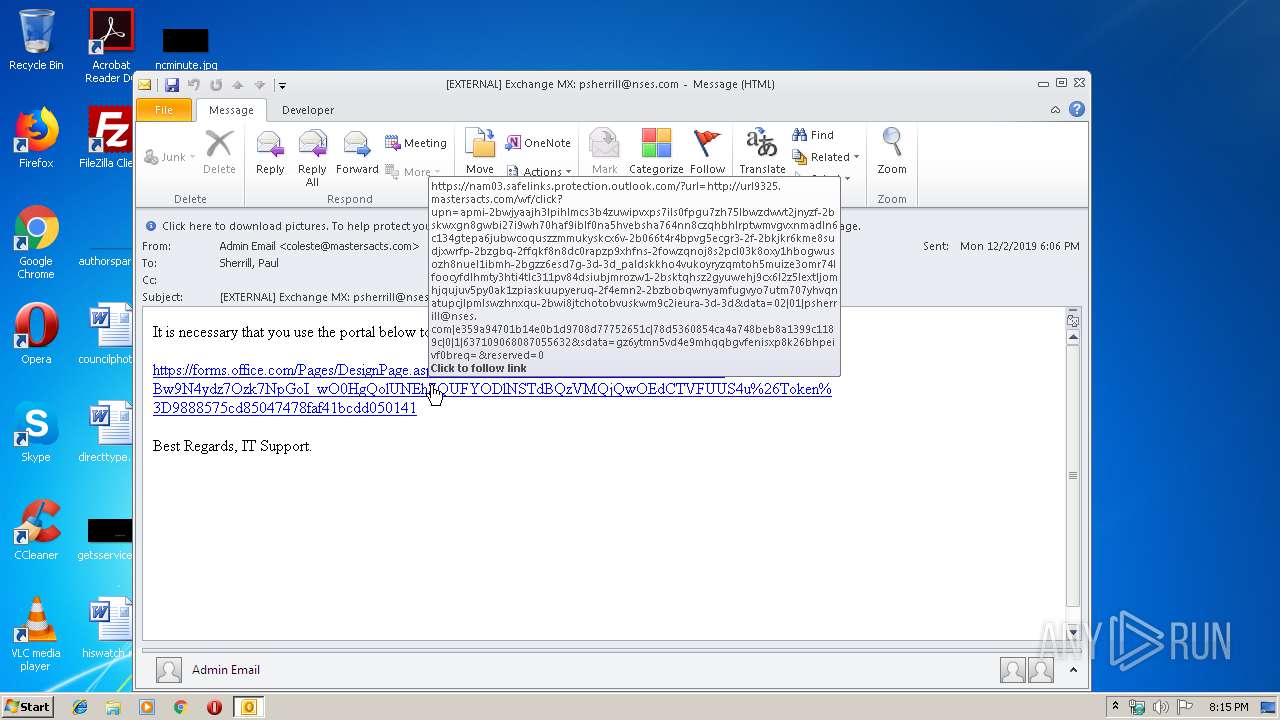
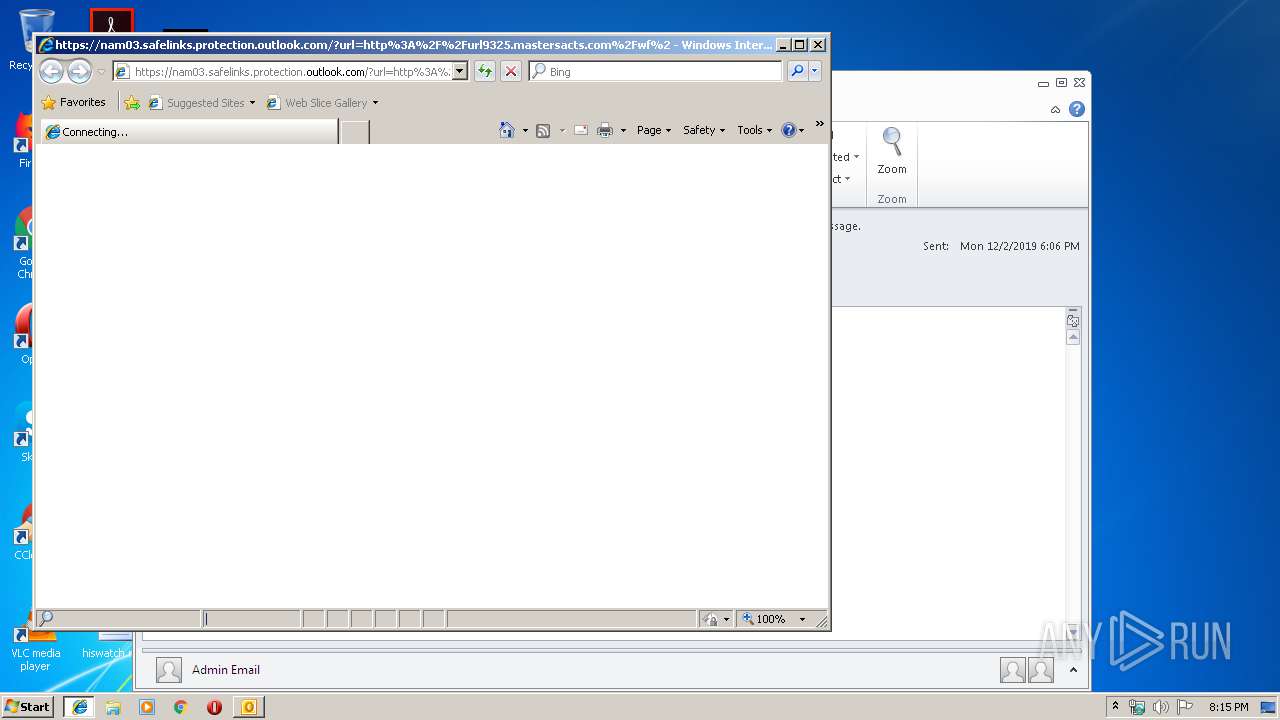
| 748 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nam03.safelinks.protection.outlook.com/?url=http%3A%2F%2Furl9325.mastersacts.com%2Fwf%2Fclick%3Fupn%3DAPMi-2BwjYaaJh3lPIhLMcS3b4ZUwiPvxps7Ils0fpGU7ZH75lbWzDWVT2jNyZF-2BskwXGN8GwbI27i9wh70HAf9IblF0na5HvEBSha764NN8cZQHbHlrpTwmvGVxNmADLN6C134GTepa6JuBwcOQuSZzmMUKYskcx6v-2B066T4r4bpVG5eCgr3-2F-2BKjKr6kme8SUdJXwrfP-2BzGbq-2FfQkf8N8dC0Rapzp9xhfNS-2FOwzqnoJ8s2PCL03K8oXY1hbOgWUsOZh8nUel1IBmh-2BgZz6eSd7g-3D-3D_palDskKho4VuKoYryZqMTOh5muiZe3oMr74LfoOCYfdlhMTY3HTi4Tlc311pv84DsiuBjMRozW1-2BSKtqHsZ2GYuwEHj9cx6L2z5leXtljOmHJQUjuV5pY0ak1ZpIaskUuPYEruQ-2F4EmN2-2BZbOBQWnyamFugvyO7utM707YHVqnaTupCjLPmlsWZhNXQu-2Bwi8jtChotoBVusKwM9C2IeURA-3D-3D&data=02%7C01%7Cpsherrill%40nses.com%7Ce359a94701b14e0b1d9708d77752651c%7C78d5360854ca4a748beb8a1399c1189c%7C0%7C1%7C637109068087055632&sdata=GZ6ytMn5VD4e9MHqQbGVfenISxp8K26BHPEivf0BReQ%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4194464655039510429 --mojo-platform-channel-handle=2724 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10402103798662967226 --mojo-platform-channel-handle=4080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15032477450643851870 --mojo-platform-channel-handle=2828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,16845269008916518779,13615395296269151566,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4616288732549188286 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:748 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 658
Read events
1 910
Write events
721
Delete events
27
Modification events
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1333919924 | |||
| (PID) Process: | (2844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
47
Text files
263
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE00F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2844 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\166B5S8Z\forms_office_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].htm | — | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
63
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1428 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 533 b | whitelisted |
1428 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 538 b | whitelisted |
1428 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1575317722&mv=m&mvi=3&pcm2cms=yes&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
1428 | chrome.exe | GET | 200 | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1575317209&mv=u&mvi=2&pcm2cms=yes&pl=24&shardbypass=yes | LV | crx | 862 Kb | whitelisted |
748 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
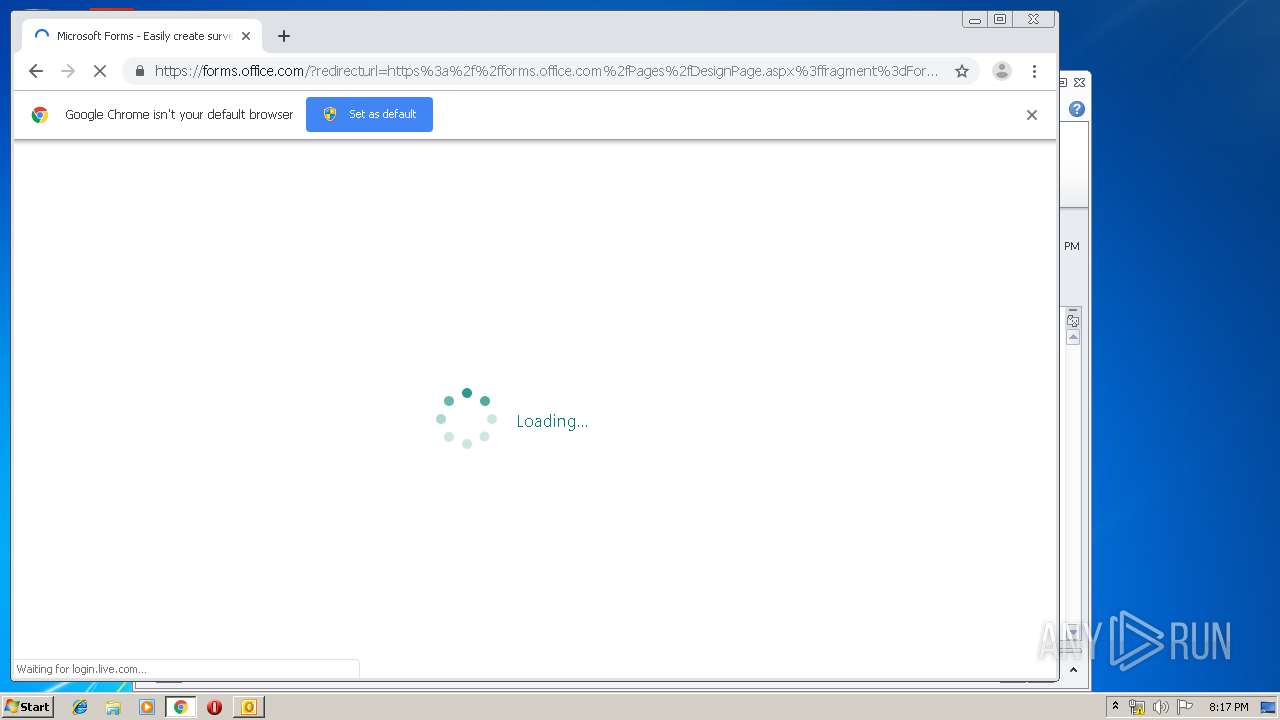
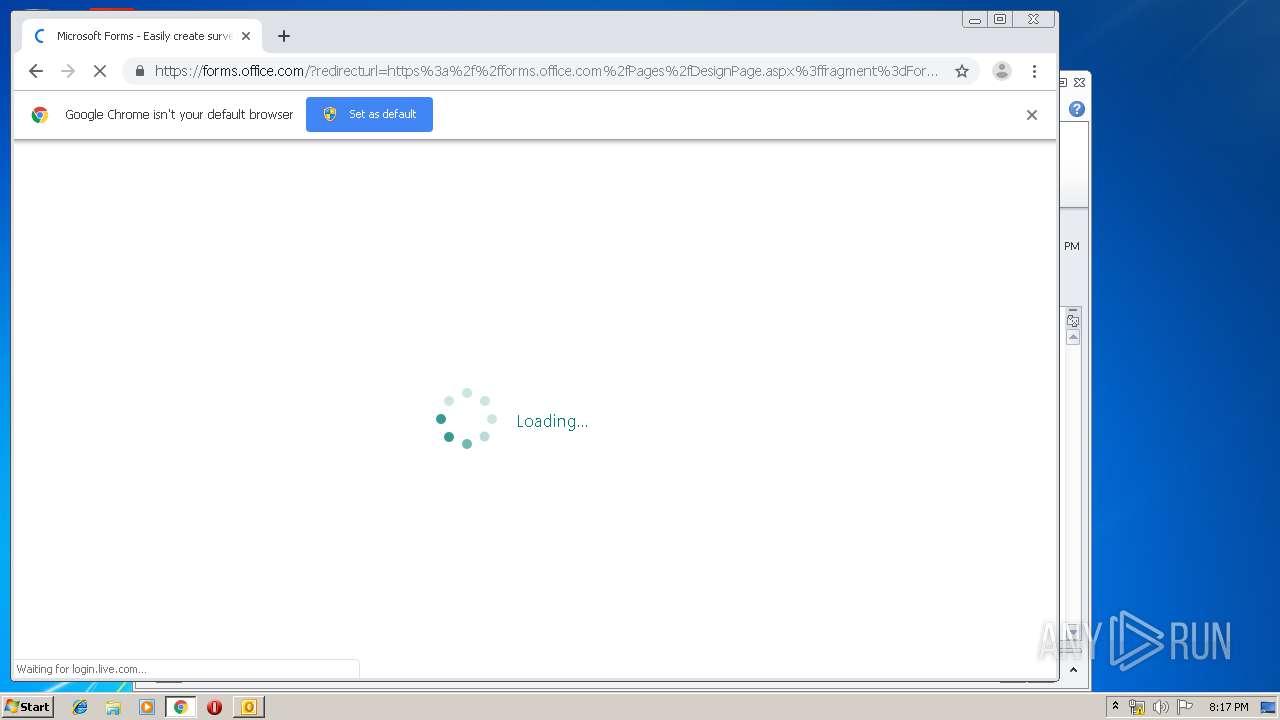
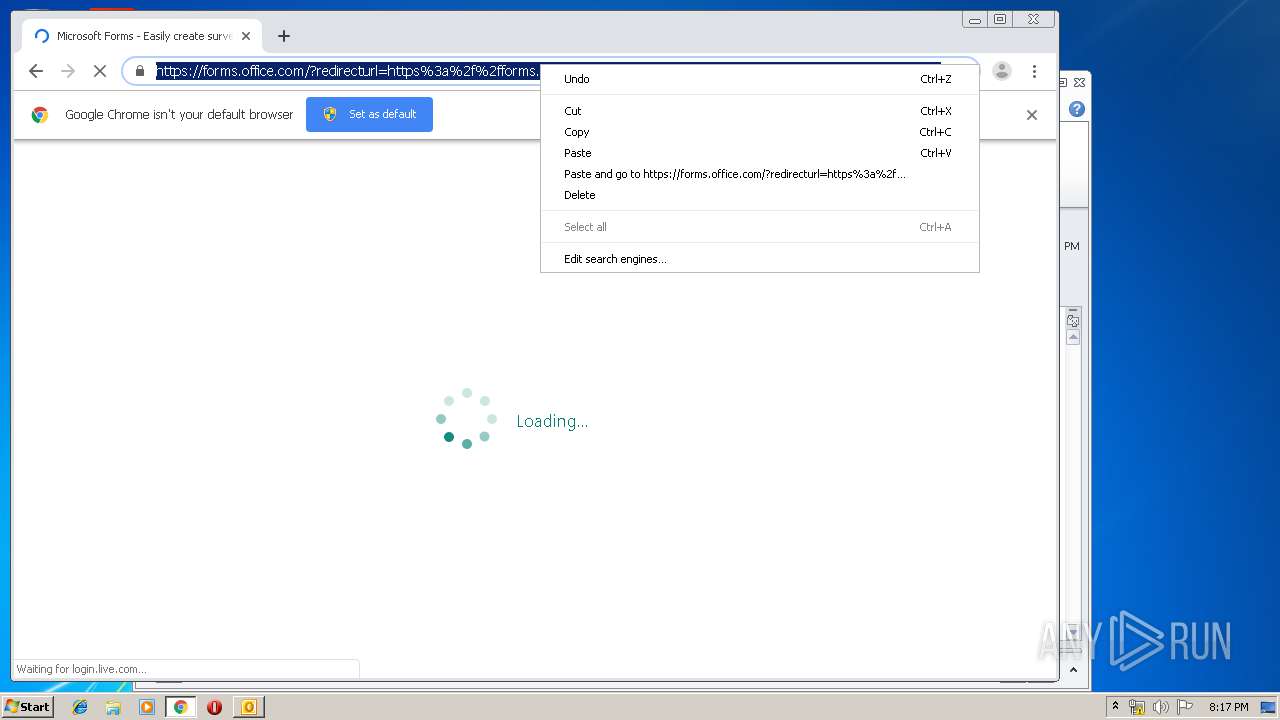
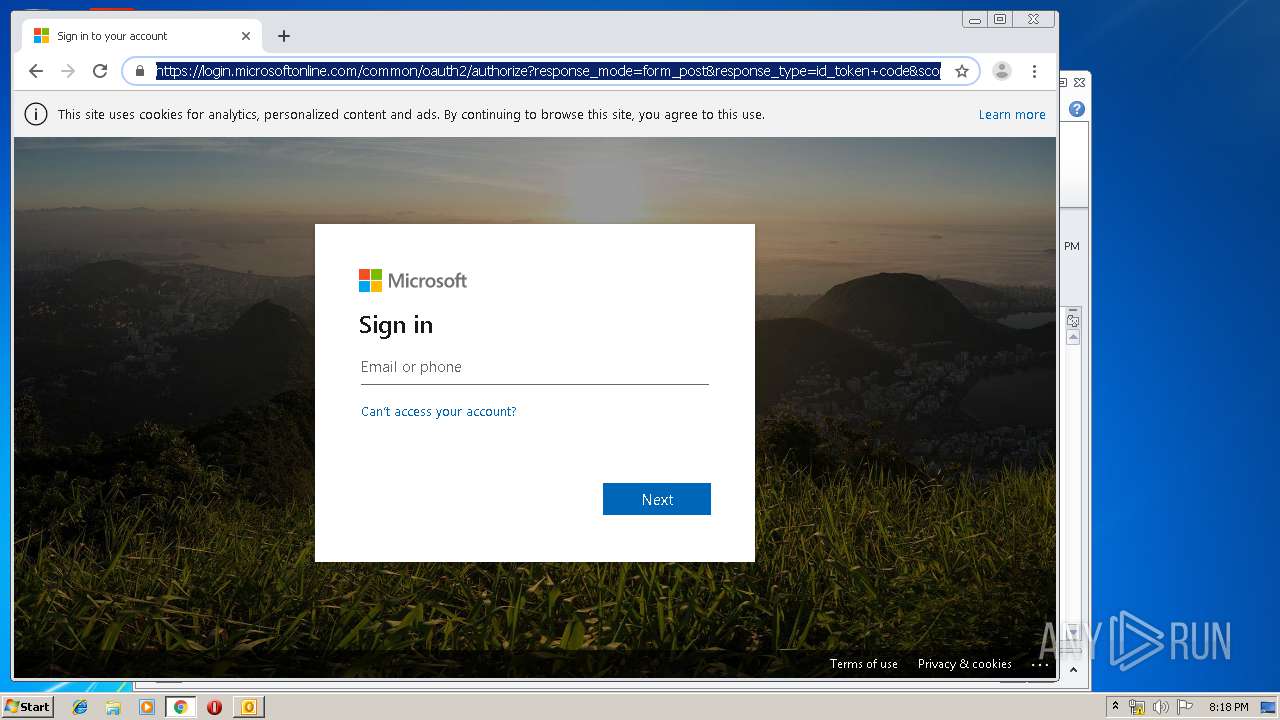
1292 | iexplore.exe | 104.47.41.28:443 | nam03.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
748 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
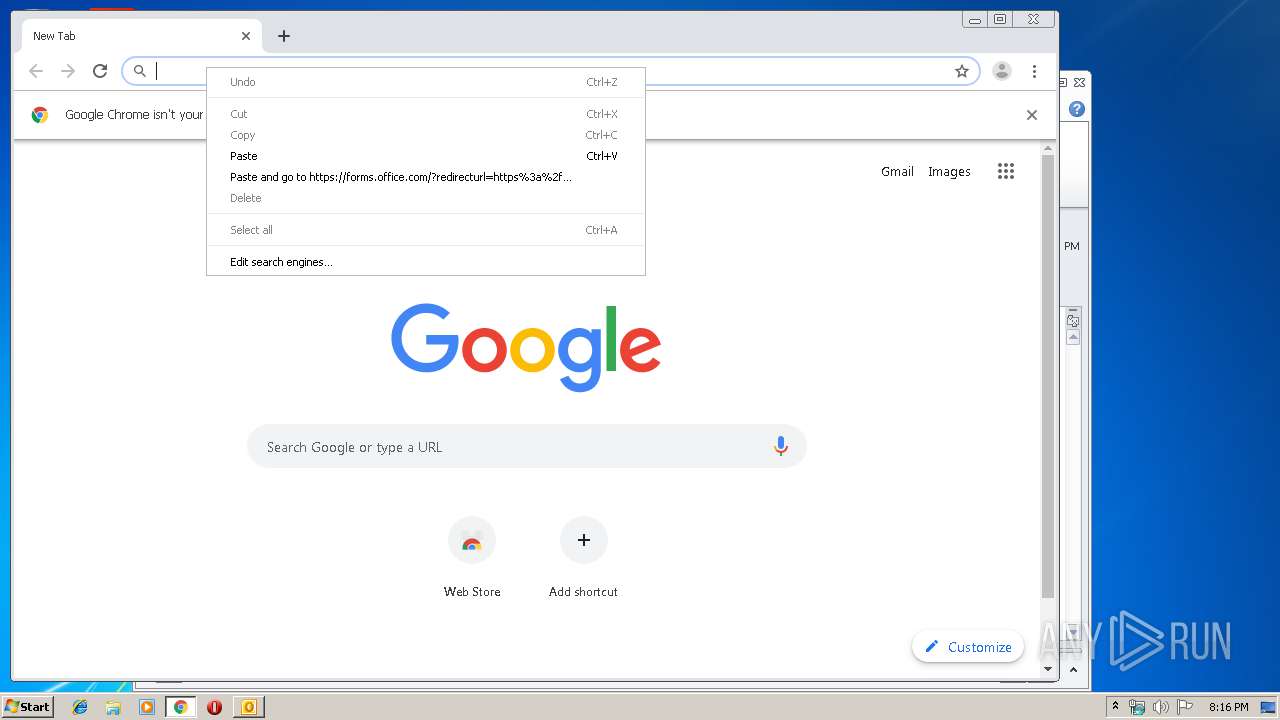
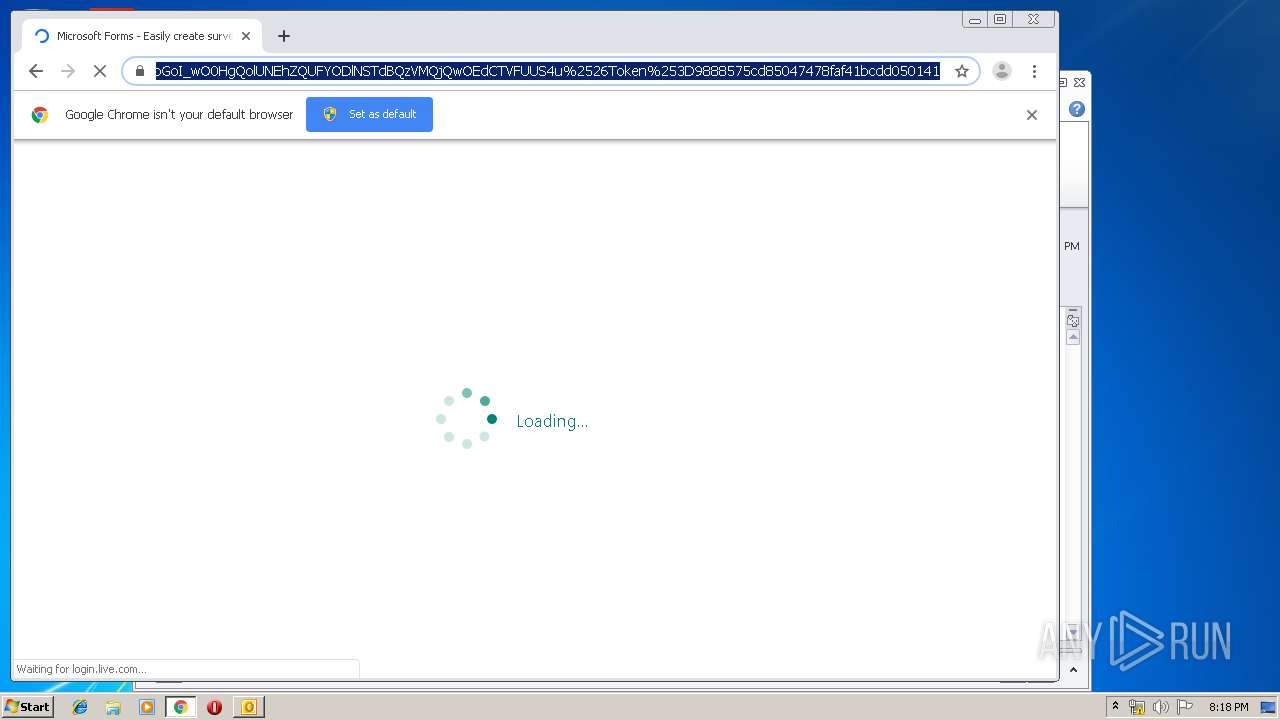
1292 | iexplore.exe | 167.89.118.52:80 | url9325.mastersacts.com | SendGrid, Inc. | US | suspicious |
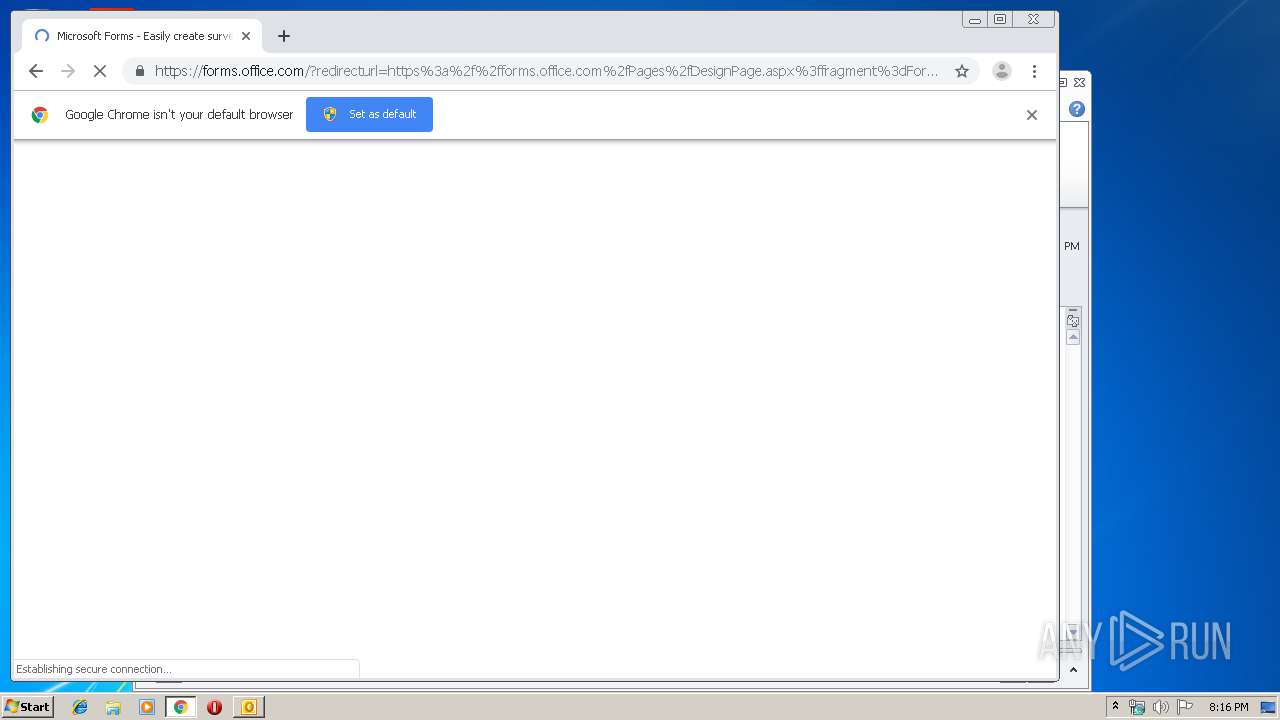
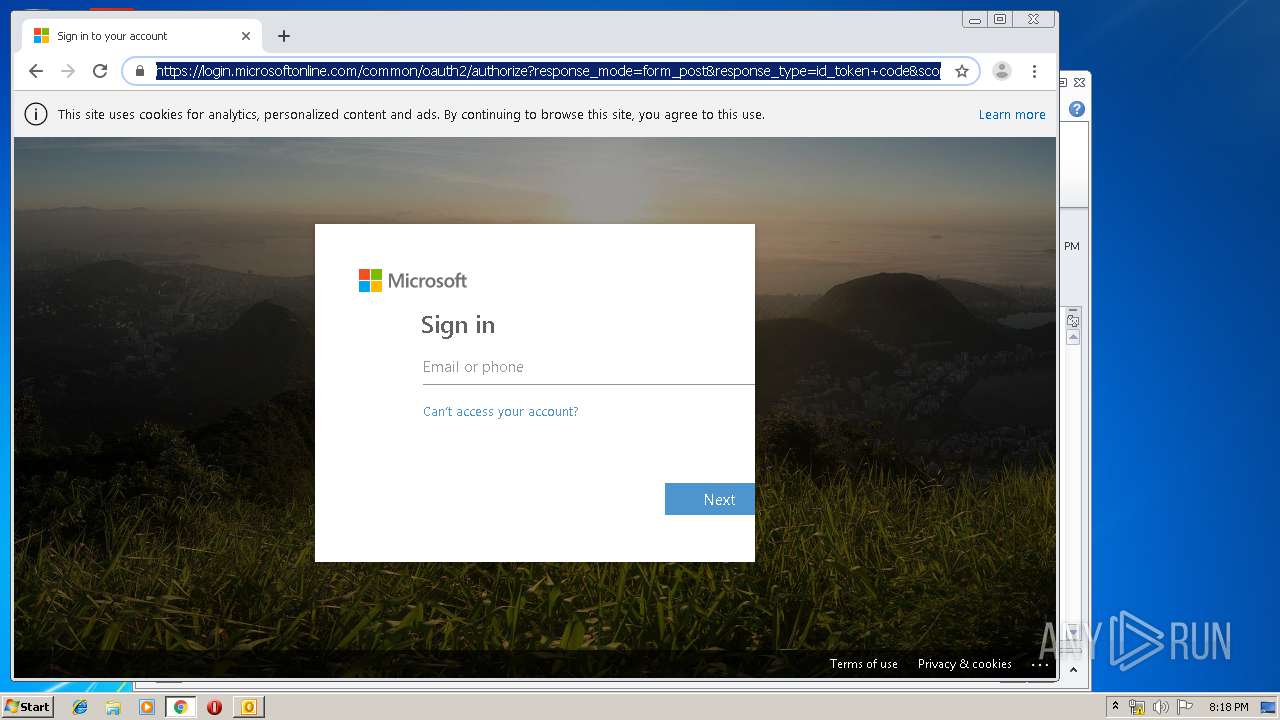
1292 | iexplore.exe | 52.109.76.79:443 | forms.office.com | Microsoft Corporation | IE | whitelisted |
748 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1428 | chrome.exe | 172.217.18.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1428 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1428 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
nam03.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |
url9325.mastersacts.com |
| suspicious |
forms.office.com |
| whitelisted |
cdn.forms.office.net |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |