| File name: | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0 |
| Full analysis: | https://app.any.run/tasks/1d49cc21-50f1-4784-8216-decee3dbaf0d |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2024, 09:18:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B74EFD8470206A20175D723C14C2E872 |
| SHA1: | 1DD417D7373DF9B8F5B76E7EB8FE87B7C37F0CC8 |
| SHA256: | 7BD723B5E4F7B3C645AC04E763DFC913060EAF6E136EECC4EE0653AD2056F3A0 |
| SSDEEP: | 98304:P+cD4dnPzJl/wA4e8Fpl5aWa5kOGKxYHWoqzRoX05lyTpWVQK9djVCvqUZYOmW6R:1XLO |
MALICIOUS
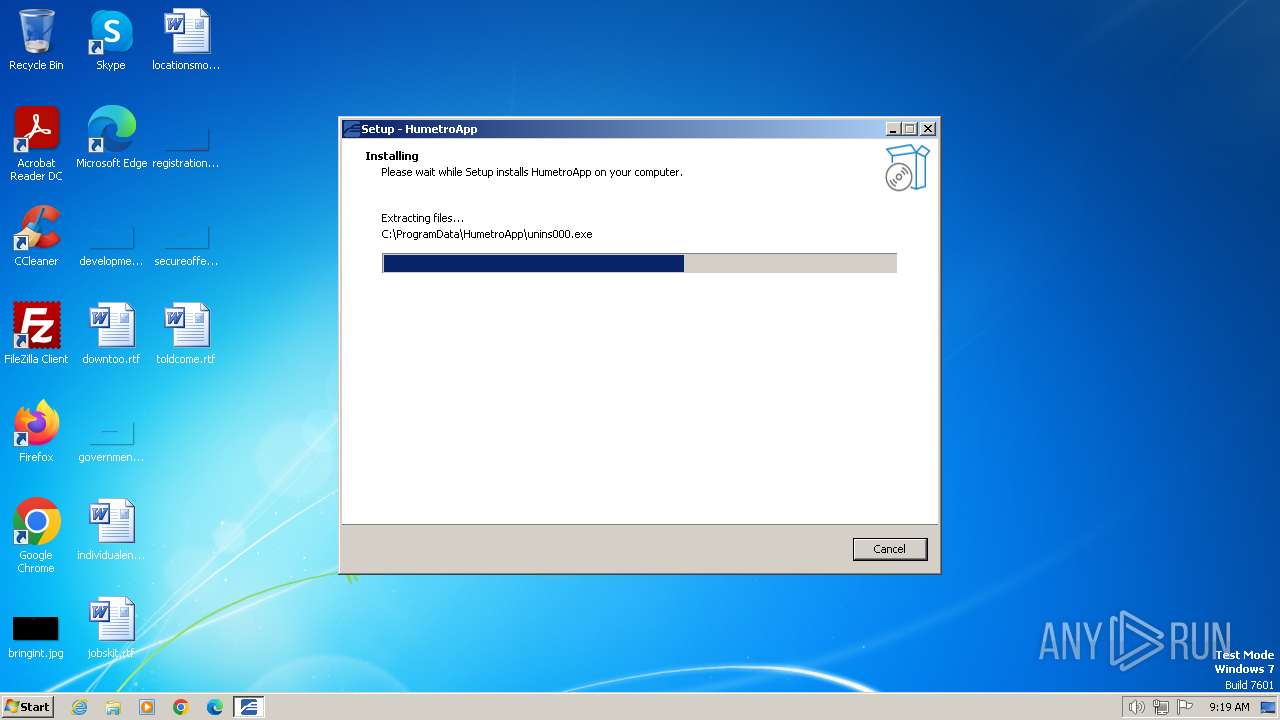
Drops the executable file immediately after the start
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe (PID: 3936)
SUSPICIOUS
Non-standard symbols in registry
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
Reads the Windows owner or organization settings
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
INFO
Checks supported languages
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe (PID: 3936)
Reads the computer name
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
Create files in a temporary directory
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe (PID: 3936)
Creates files in the program directory
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
Creates a software uninstall entry
- 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 181760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.2.0 |
| ProductVersionNumber: | 2.4.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
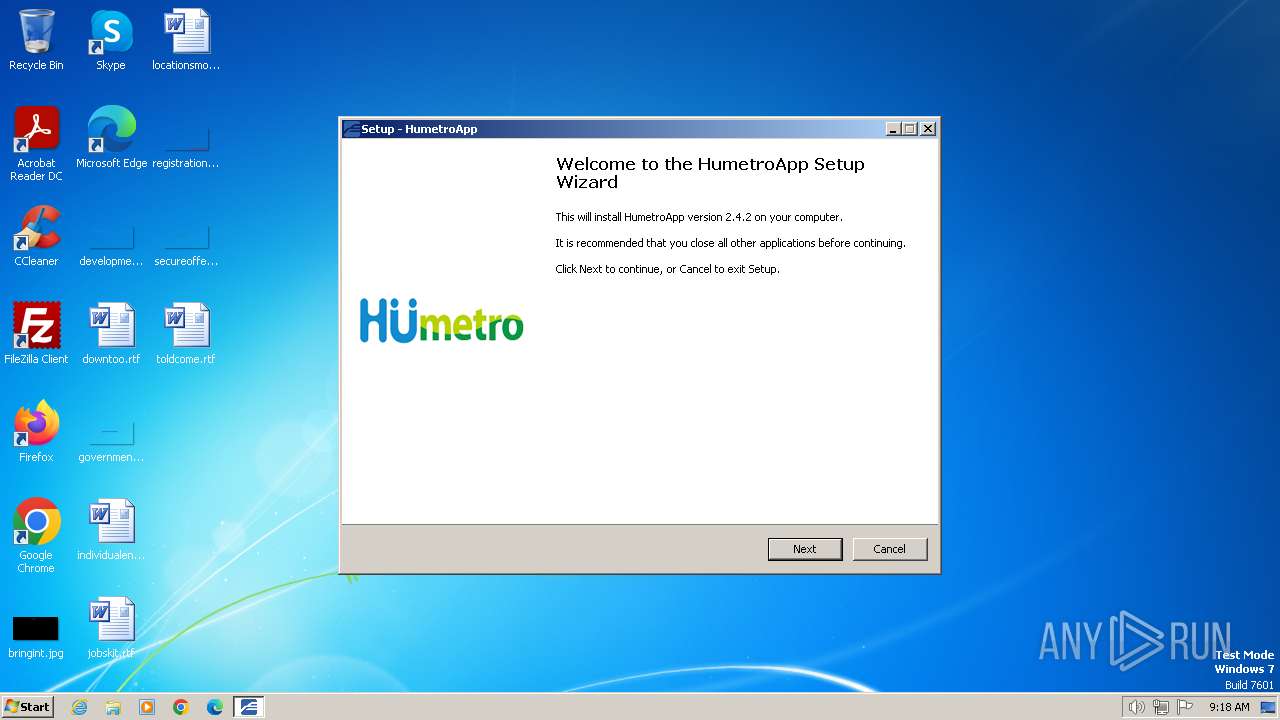
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | humetro.busan.kr |
| FileDescription: | HumetroApp Setup |
| FileVersion: | 2.4.2 |
| LegalCopyright: | copyright©humetro.busan.kr |
| OriginalFileName: | |
| ProductName: | HumetroApp |
| ProductVersion: | 2.4.2 |
Total processes
37
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | "C:\Users\admin\AppData\Local\Temp\is-3ADRF.tmp\7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp" /SL5="$E0170,3030209,924672,C:\Users\admin\AppData\Local\Temp\7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe" | C:\Users\admin\AppData\Local\Temp\is-3ADRF.tmp\7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | — | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe | |||||||||||
User: admin Company: humetro.busan.kr Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3936 | "C:\Users\admin\AppData\Local\Temp\7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe" | C:\Users\admin\AppData\Local\Temp\7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe | — | explorer.exe | |||||||||||
User: admin Company: humetro.busan.kr Integrity Level: MEDIUM Description: HumetroApp Setup Exit code: 0 Version: 2.4.2 Modules
| |||||||||||||||
Total events
365
Read events
336
Write events
23
Delete events
6
Modification events
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: A00600003CFFE6A05E7FDA01 | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C59F5CDAC2C7C701EB82A6CB86261F14F508D090FD6FA031EFEC49E2638A4480 | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\ProgramData\unrar.exe | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: CCB4D23082B5425A48E39F0F53F650D4C39534894093A8F013837AF24B1634FC | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HumetroApp_is1 |
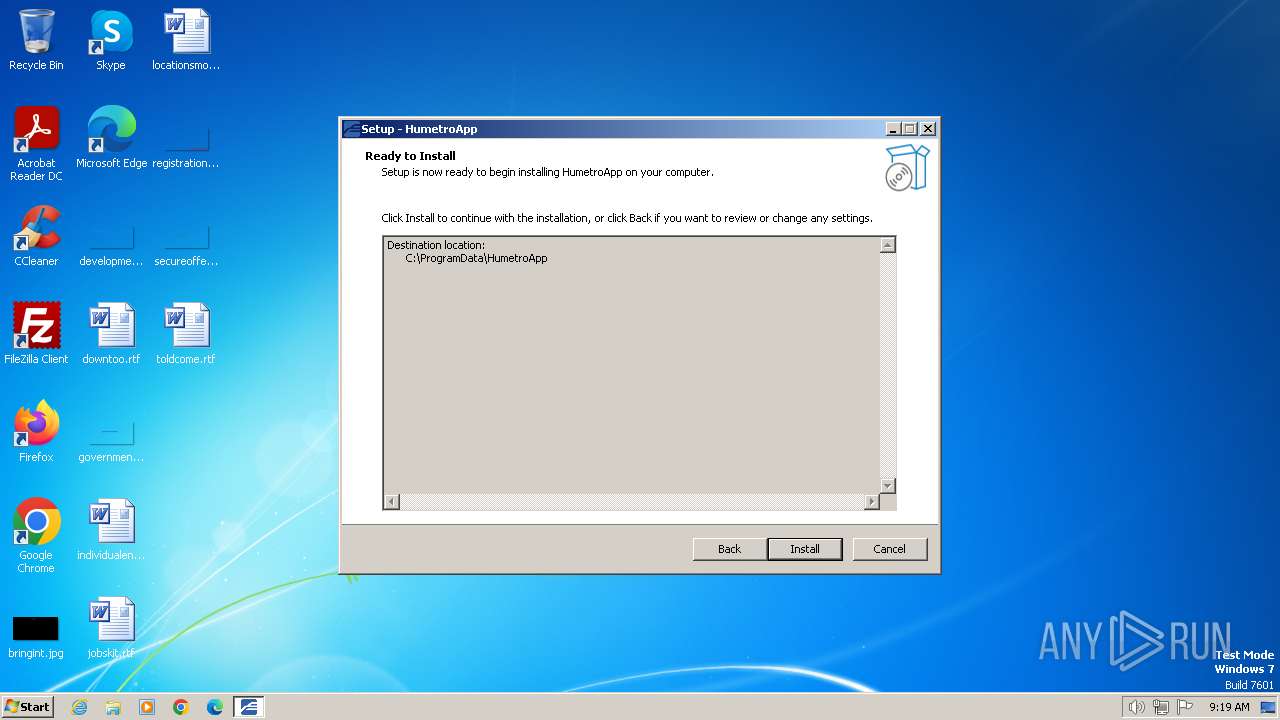
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HumetroApp_is1 |
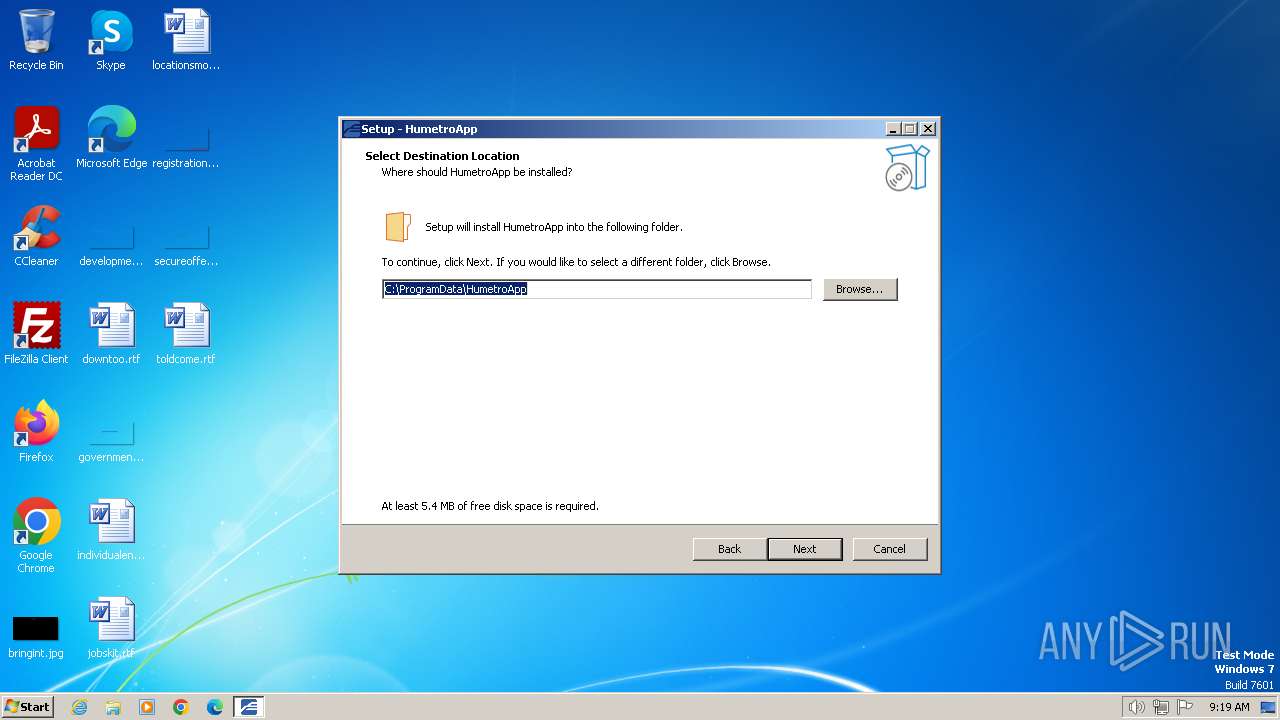
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\ProgramData\HumetroApp | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HumetroApp_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\ProgramData\HumetroApp\ | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HumetroApp_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (1696) 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HumetroApp_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
6
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.exe | C:\Users\admin\AppData\Local\Temp\is-3ADRF.tmp\7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | executable | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\Users\admin\AppData\Local\Temp\is-MKFIC.tmp\unrar.exe | executable | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\Users\admin\AppData\Local\Temp\is-MKFIC.tmp\src.rar | — | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\ProgramData\HumetroApp\is-0KQTO.tmp | executable | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\ProgramData\HumetroApp\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\ProgramData\is-0IC6T.tmp | — | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\ProgramData\src.rar | — | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\ProgramData\is-I9560.tmp | executable | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\ProgramData\unrar.exe | executable | |
MD5:— | SHA256:— | |||
| 1696 | 7bd723b5e4f7b3c645ac04e763dfc913060eaf6e136eecc4ee0653ad2056f3a0.tmp | C:\ProgramData\HumetroApp\unins000.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |