| File name: | Caught.Power.exe |
| Full analysis: | https://app.any.run/tasks/2559df0f-b0f7-4e2f-b951-be13dae7afac |
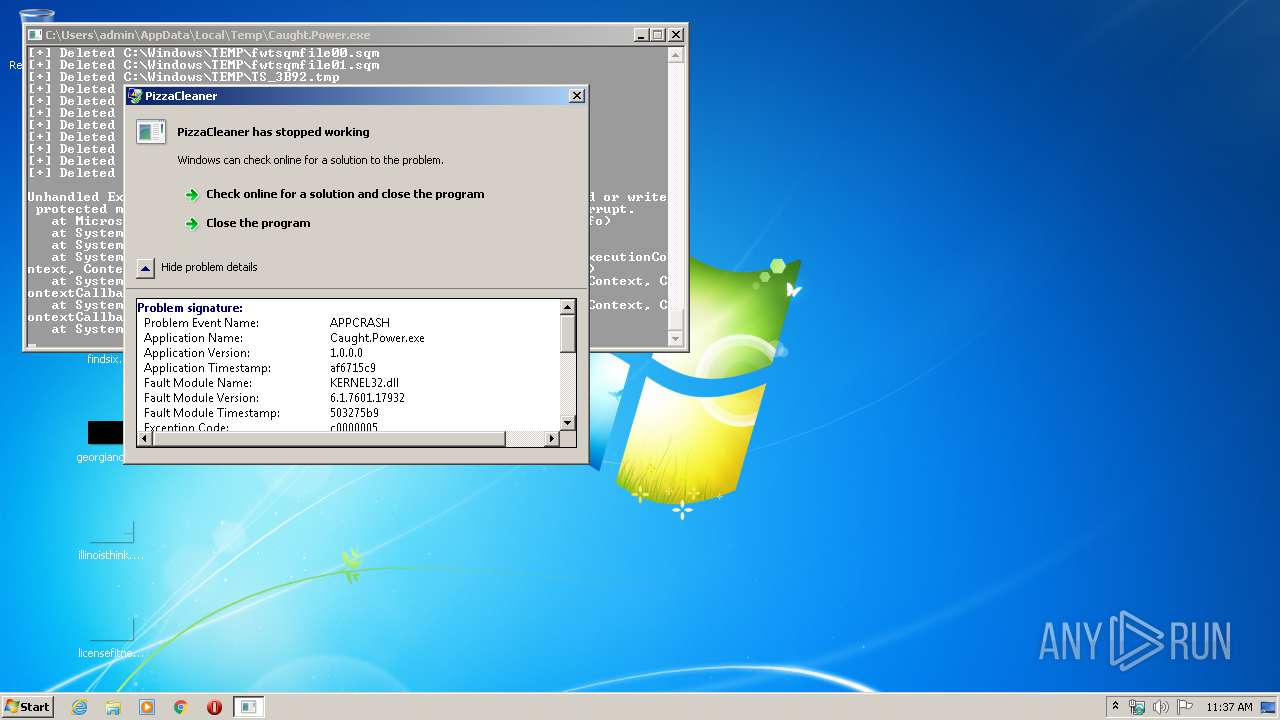
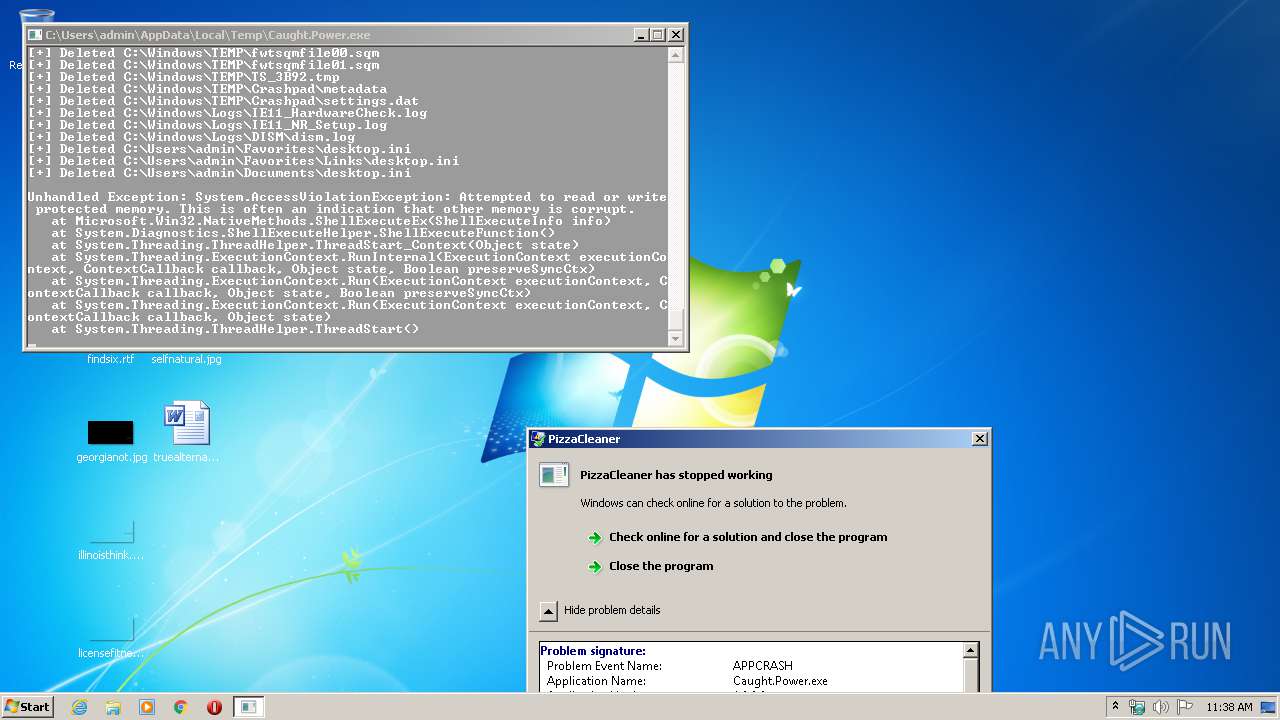
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2020, 11:37:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 4C37879689505F683C1E07B86B8AA7F2 |
| SHA1: | 58484777D59AF5378002EE6CD686525F26449098 |
| SHA256: | 7BCBC81DBFBC85B4C7C40F44931788A814DED426317E6EA9456CC65C37341C92 |
| SSDEEP: | 6144:5fqHpILYw0mlefjZJnu3GHYKDcOuhHovXIslLMJsd/4TelpDtrRA6Ts5v3FNR3:xq2L7UjX0G/xvwsrSeLlTst3t3 |
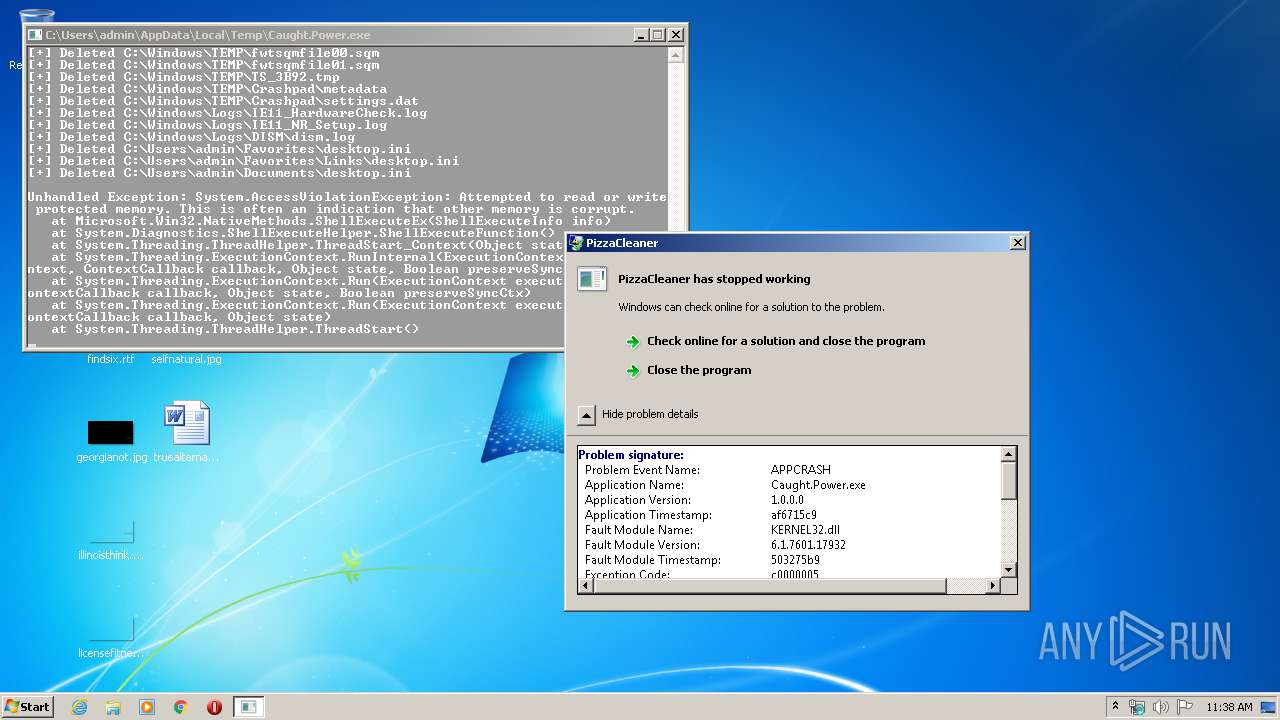
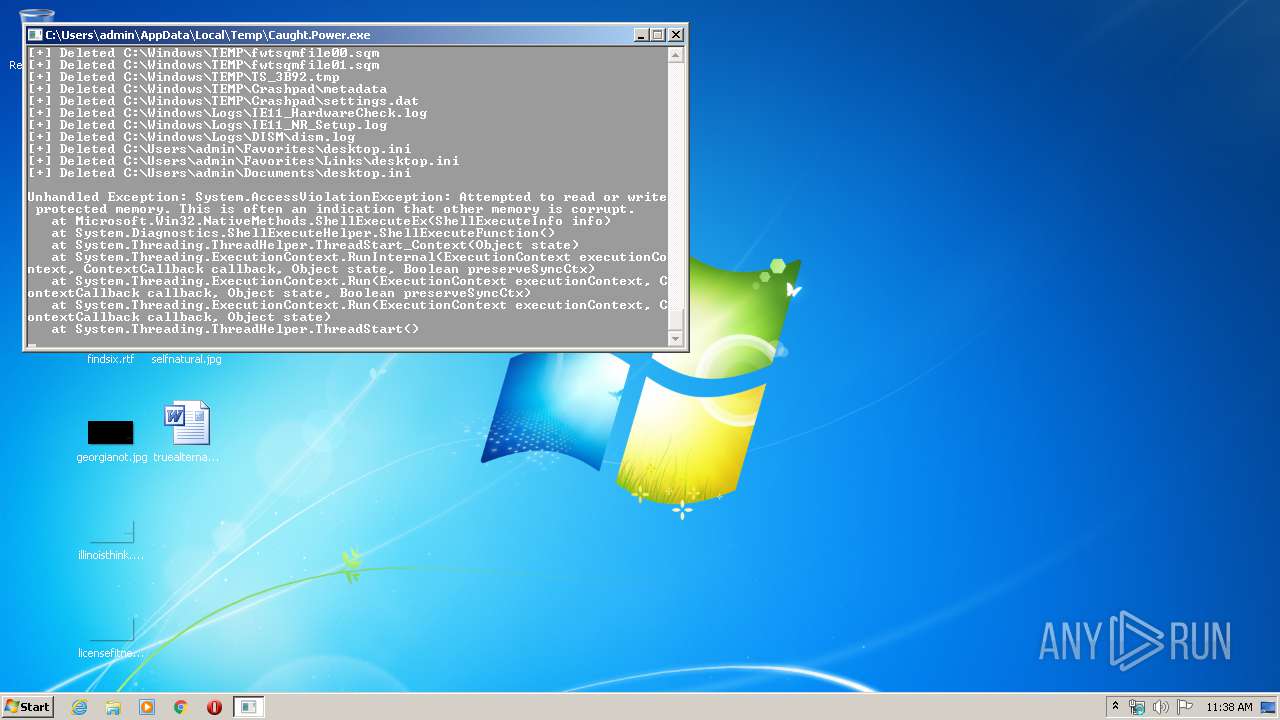
MALICIOUS
Loads dropped or rewritten executable
- Caught.Power.exe (PID: 2568)
- WerFault.exe (PID: 2956)
SUSPICIOUS
Executable content was dropped or overwritten
- Caught.Power.exe (PID: 2568)
Creates files in the program directory
- WerFault.exe (PID: 2956)
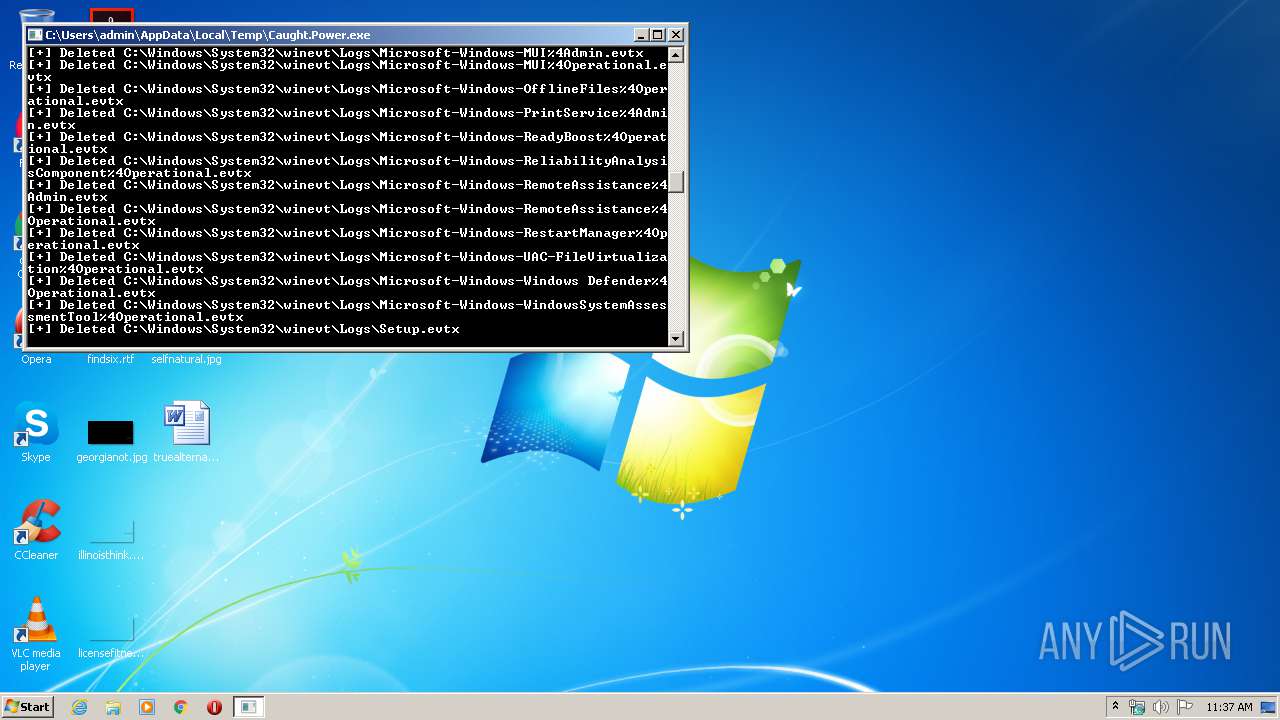
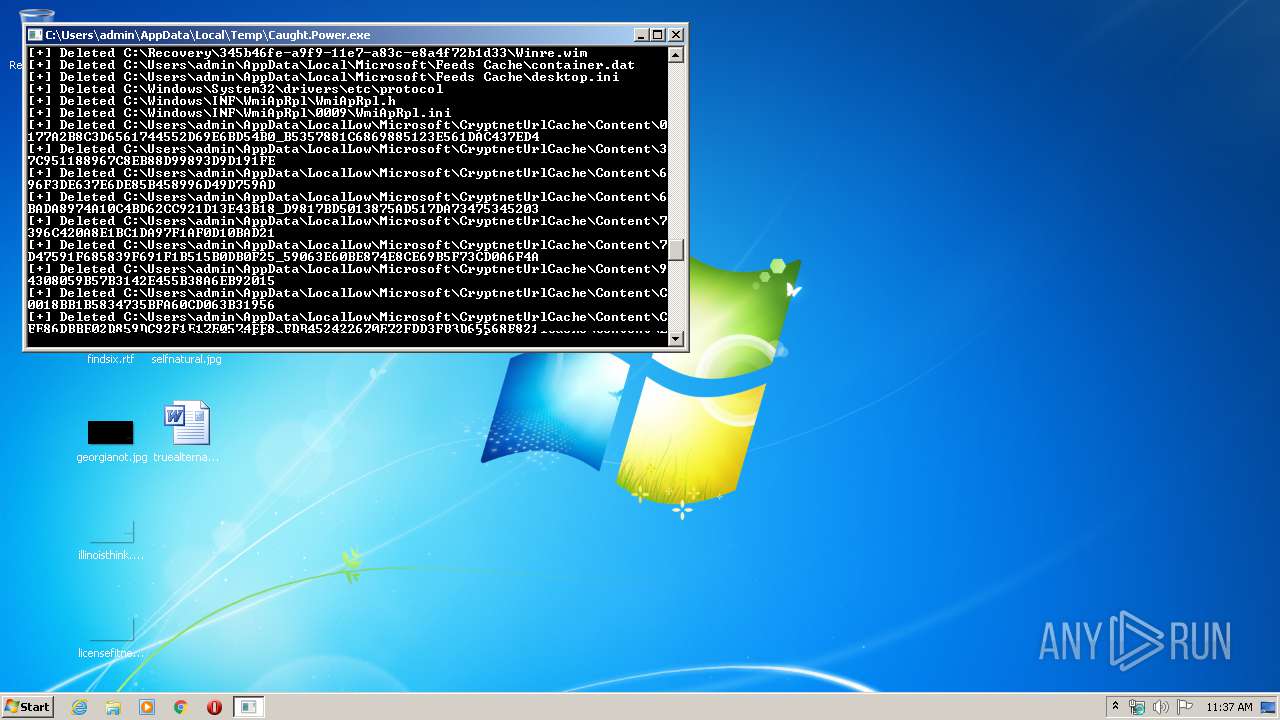
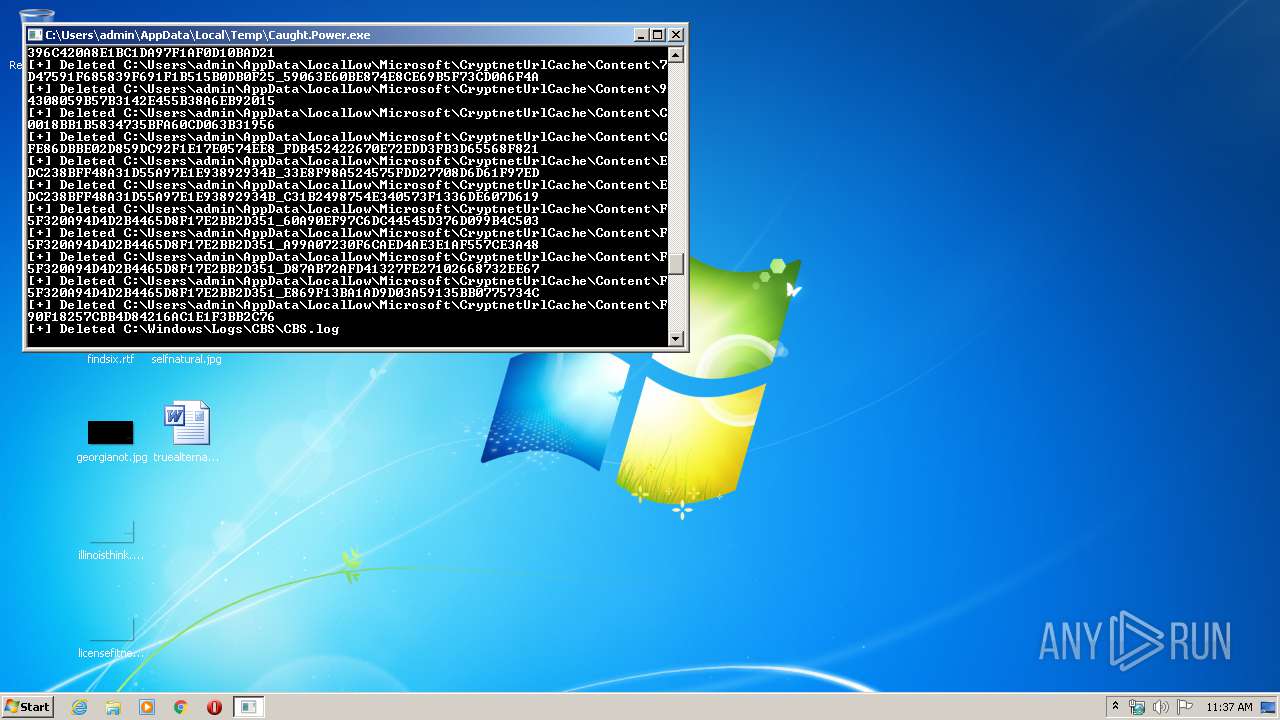
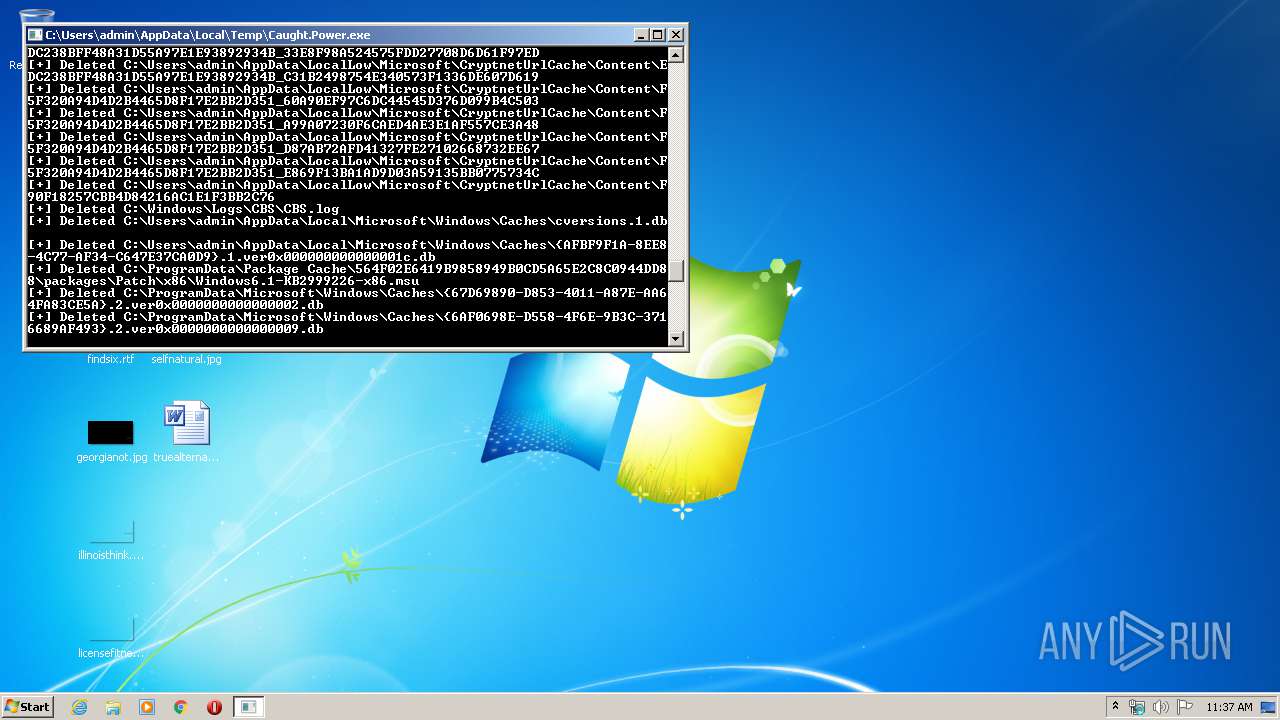
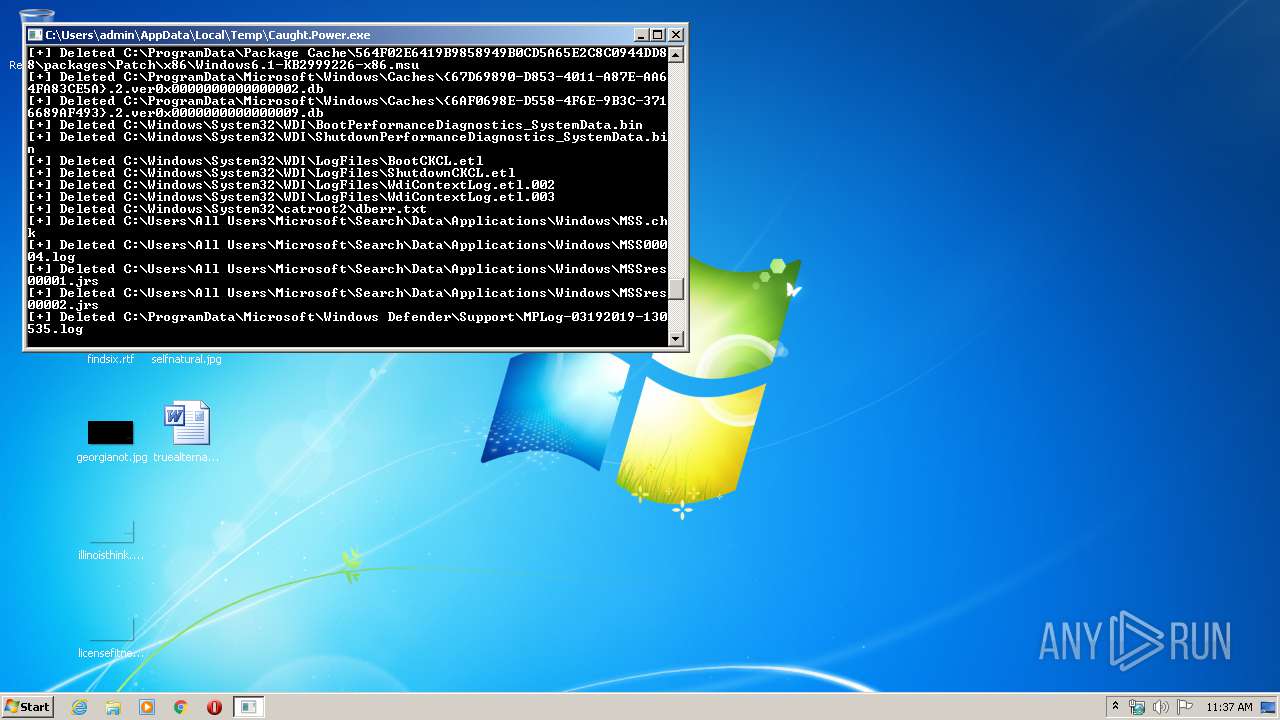
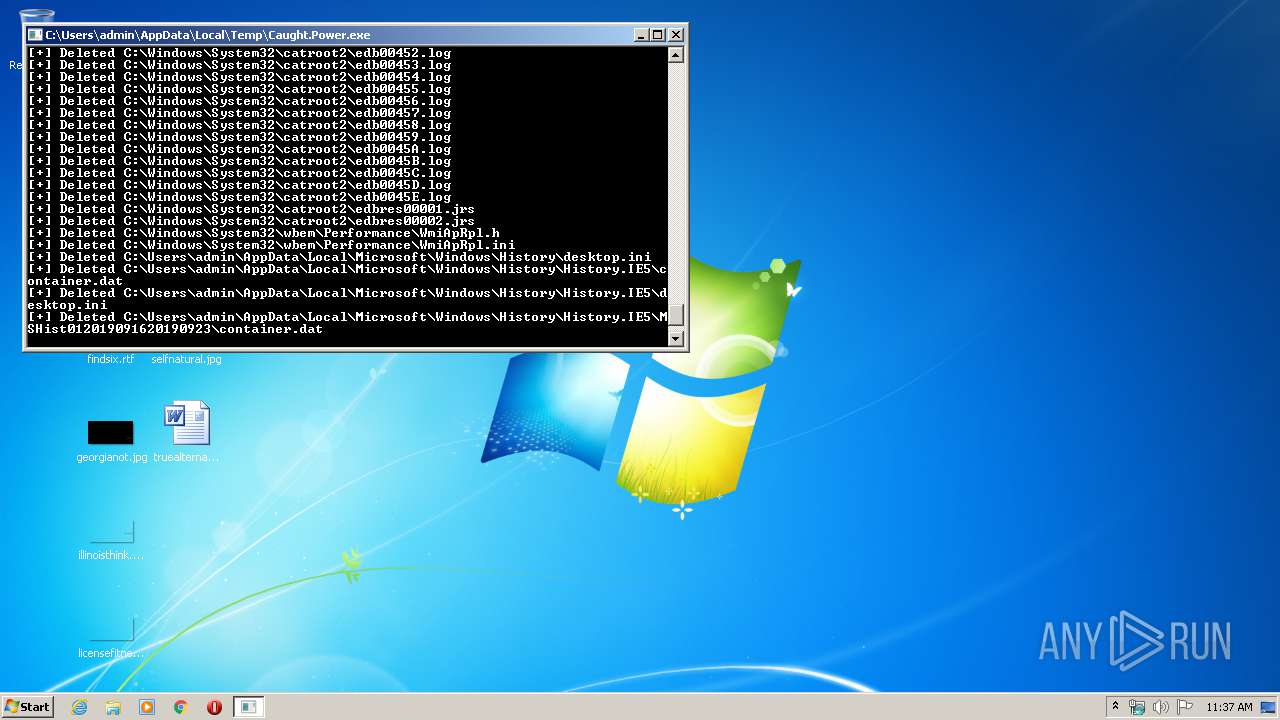
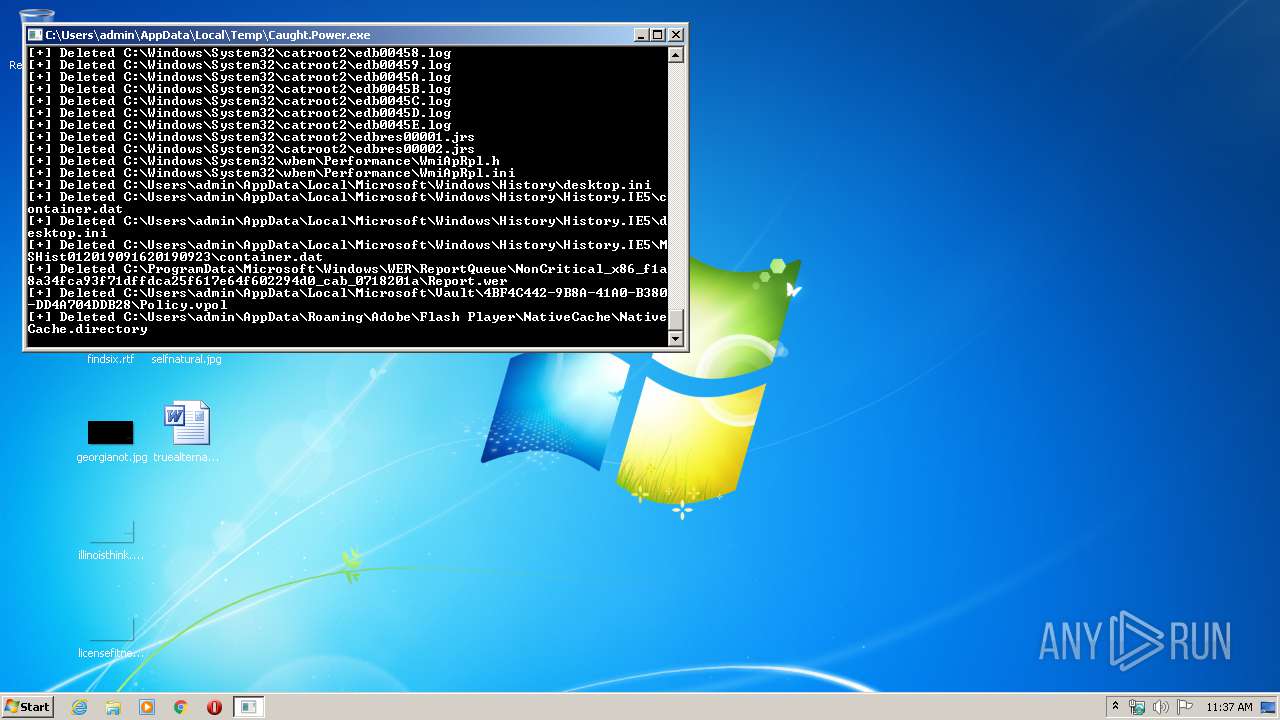
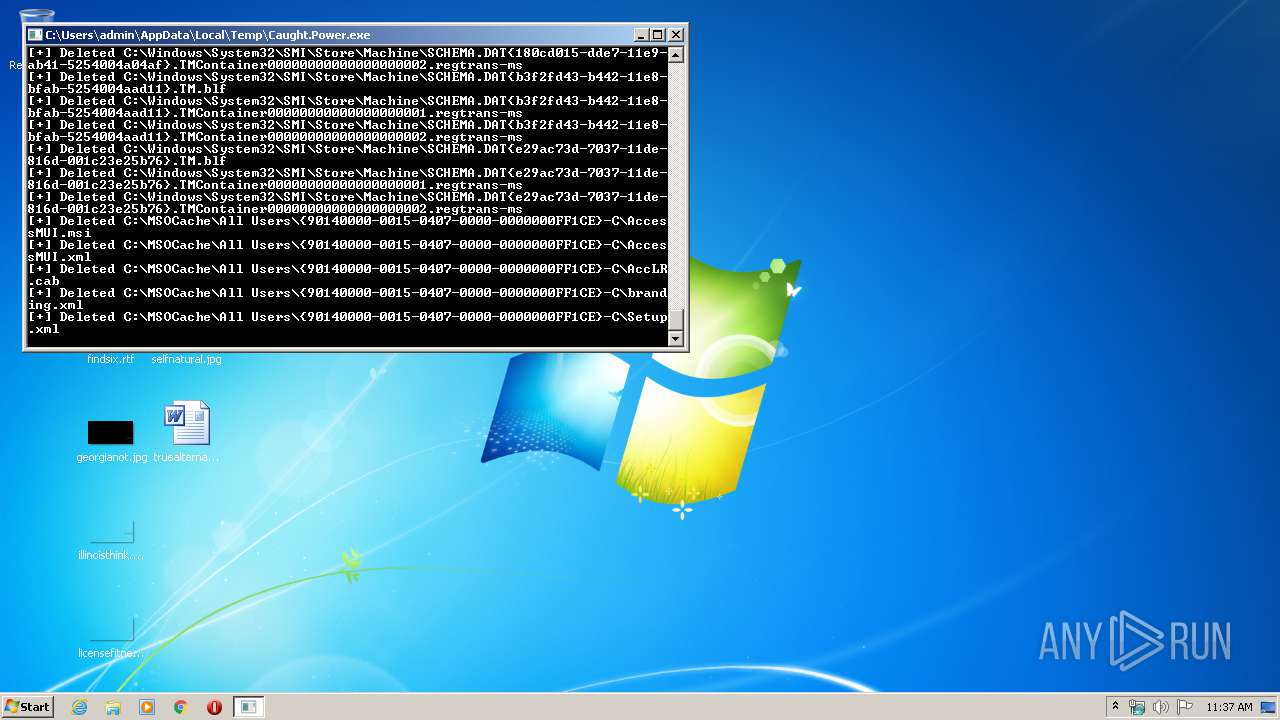
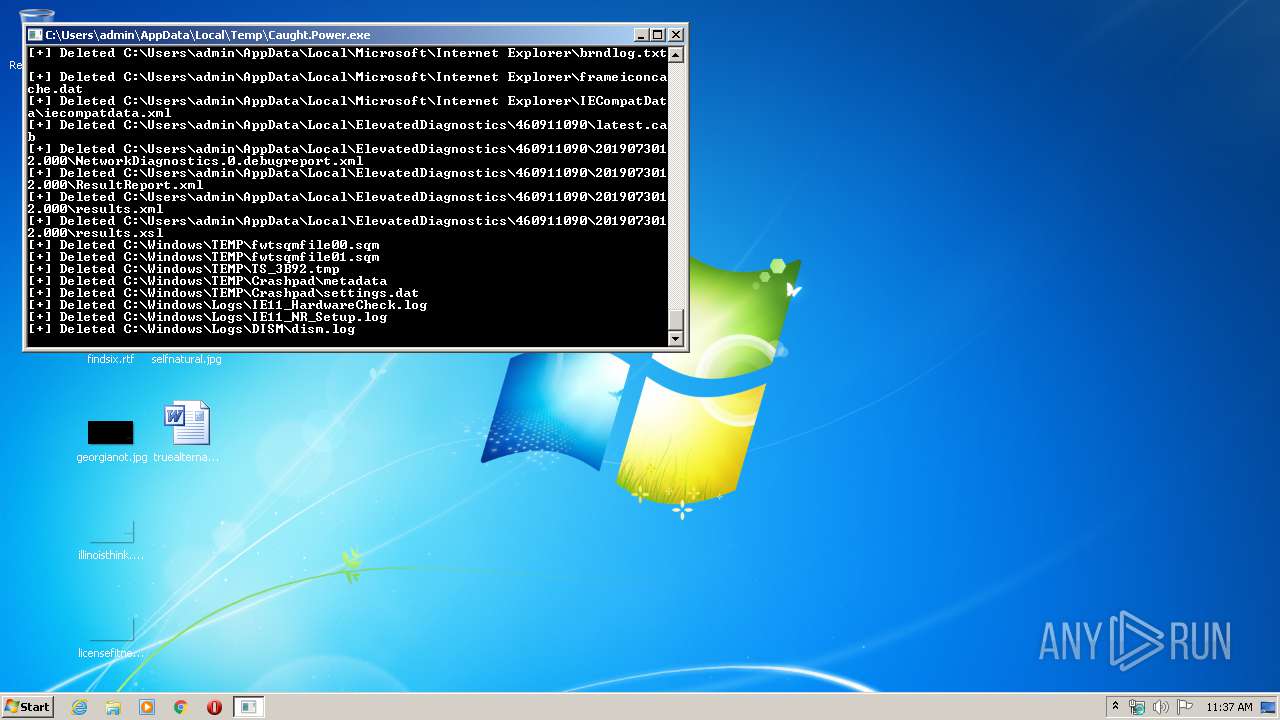
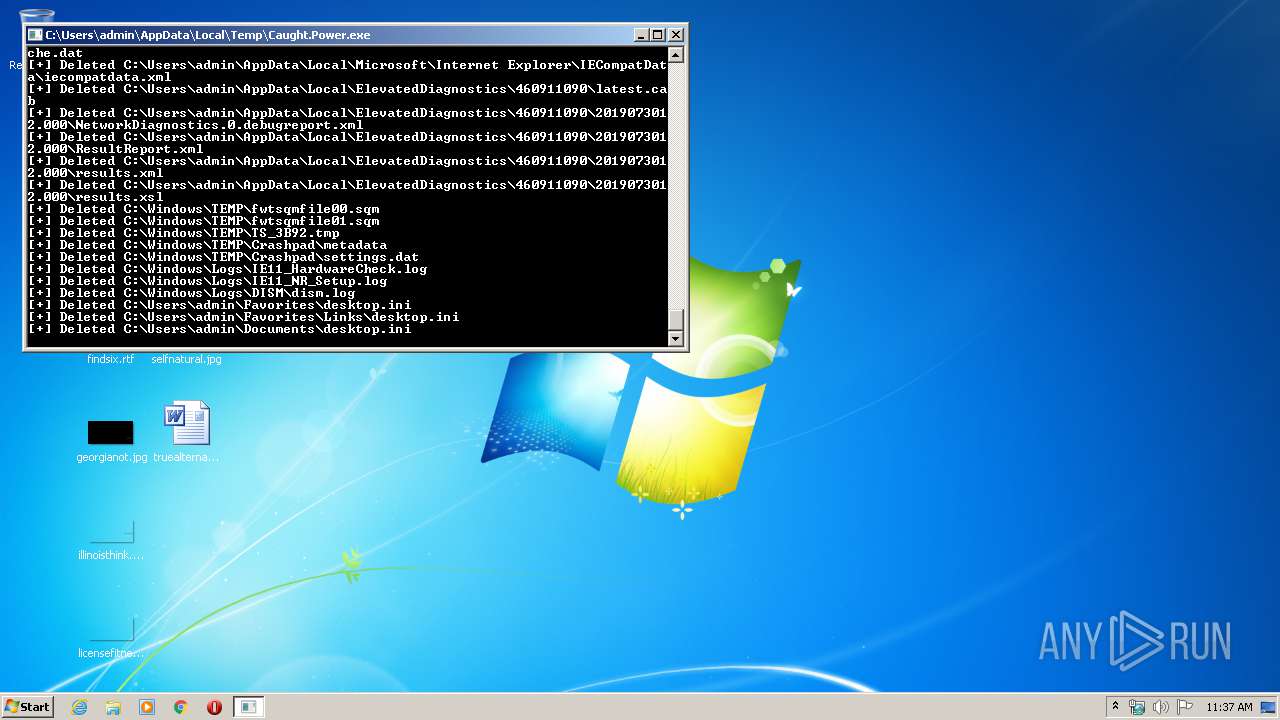
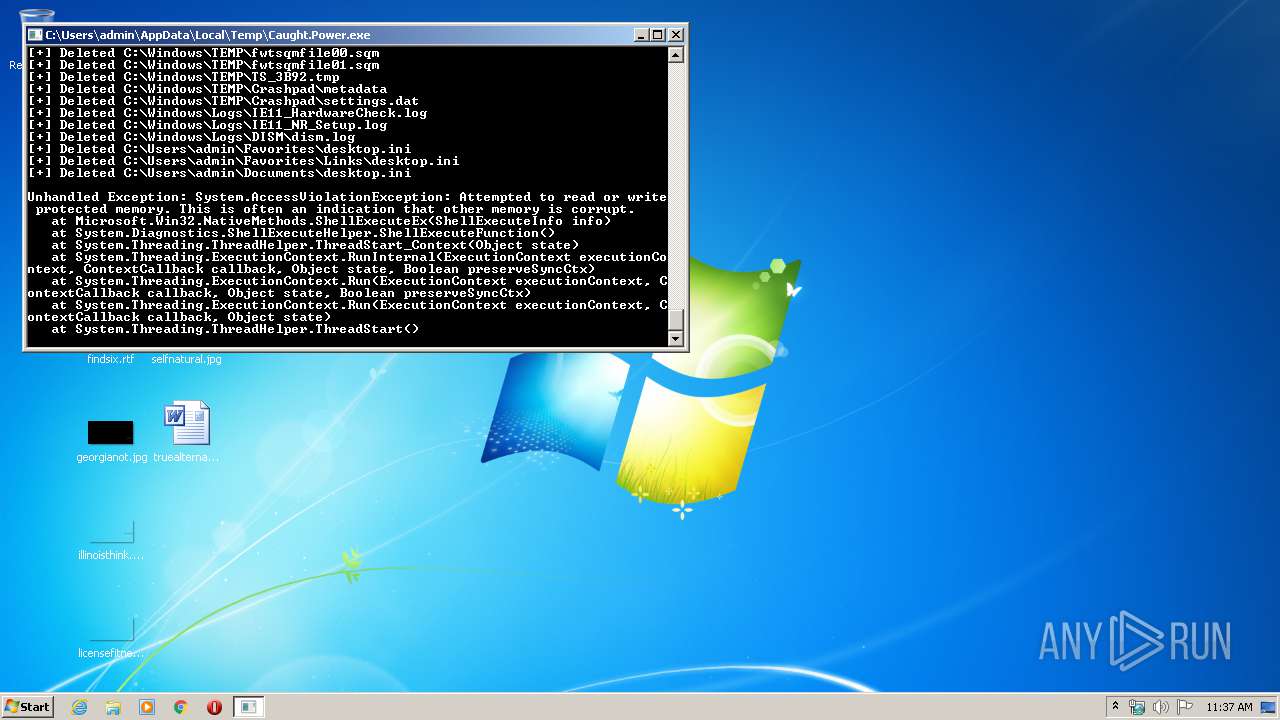
Removes files from Windows directory
- Caught.Power.exe (PID: 2568)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2063:04:02 21:43:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 566784 |
| InitializedDataSize: | 5120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8c5ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Nemesis-15161 |
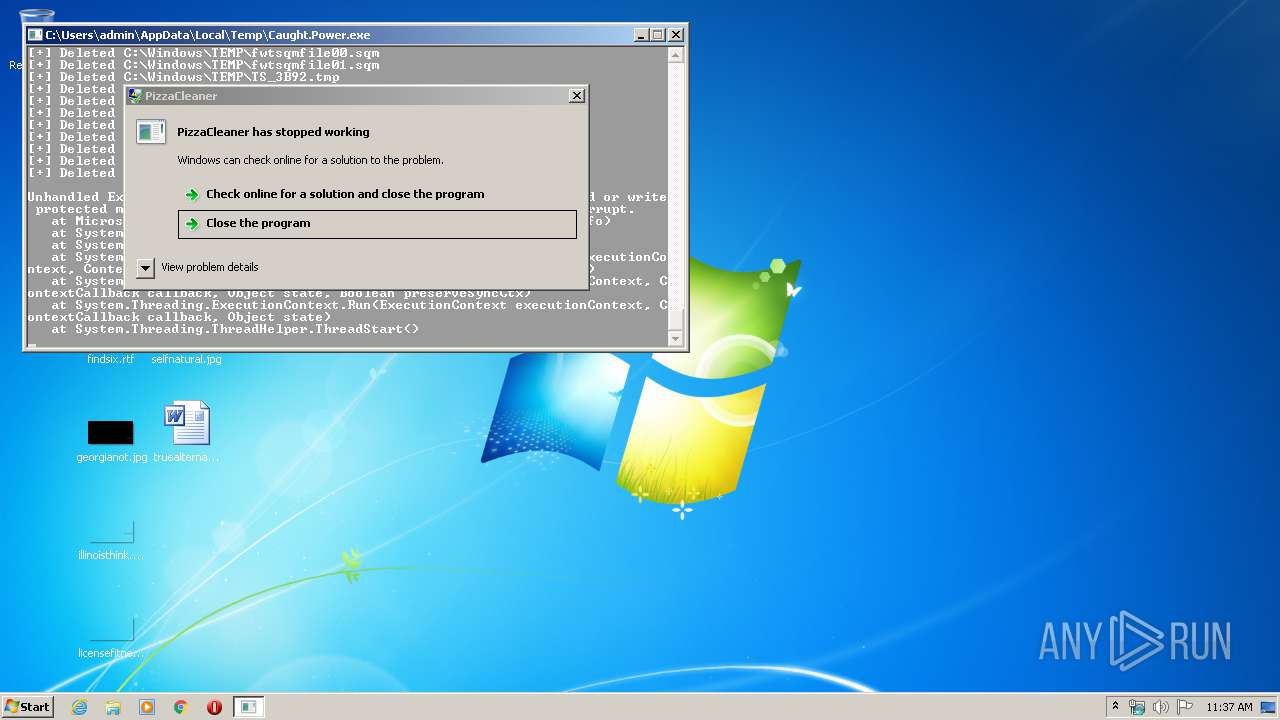
| FileDescription: | PizzaCleaner |
| FileVersion: | 1.0.0.0 |
| InternalName: | PizzaCleaner.exe |
| LegalCopyright: | Copyright © Nemesis-15161 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | PizzaCleaner.exe |
| ProductName: | PizzaCleaner |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 25-Feb-1927 13:14:49 |
| Comments: | - |
| CompanyName: | Nemesis-15161 |
| FileDescription: | PizzaCleaner |
| FileVersion: | 1.0.0.0 |
| InternalName: | PizzaCleaner.exe |
| LegalCopyright: | Copyright © Nemesis-15161 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | PizzaCleaner.exe |
| ProductName: | PizzaCleaner |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Feb-1927 13:14:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0008A5F4 | 0x0008A600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.26988 |
.rsrc | 0x0008E000 | 0x00001078 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81485 |
.reloc | 0x00090000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00795 | 3170 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2568 | "C:\Users\admin\AppData\Local\Temp\Caught.Power.exe" | C:\Users\admin\AppData\Local\Temp\Caught.Power.exe | explorer.exe | ||||||||||||
User: admin Company: Nemesis-15161 Integrity Level: HIGH Description: PizzaCleaner Exit code: 3221225477 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2956 | C:\Windows\system32\WerFault.exe -u -p 2568 -s 836 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Users\admin\AppData\Local\Temp\Caught.Power.exe" | C:\Users\admin\AppData\Local\Temp\Caught.Power.exe | — | explorer.exe | |||||||||||
User: admin Company: Nemesis-15161 Integrity Level: MEDIUM Description: PizzaCleaner Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
127
Read events
68
Write events
59
Delete events
0
Modification events
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BaseBoardProduct |
Value: MSI B450M Bazooka V2 | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BaseBoardVersion |
Value: 1.1 | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BaseBoardManufacturer |
Value: EVGA | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | SystemVersion |
Value: 1.1 | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | SystemManufacturer |
Value: EVGA | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BIOSReleaseDate |
Value: 03/05/2016 | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | SystemProductName |
Value: PL-7A19 | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BIOSVersion |
Value: A.69 | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BIOSVendor |
Value: Sun Microsystems | |||
| (PID) Process: | (2568) Caught.Power.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SystemInformation |
| Operation: | write | Name: | ComputerHardwareId |
Value: {0b0fec5a-c75d-4171-9a51-1c8a271e0e80} | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Caught.Power.exe.2568.dmp | — | |
MD5:— | SHA256:— | |||
| 2956 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Caught.Power.exe_72c7258599cd7175dbf8a868c5c9d156cc7fc181_0b2b1fc0\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2568 | Caught.Power.exe | C:\Users\admin\AppData\Local\Temp\Runtime.MSIL.1.0.0.0\NativePRo.dll | executable | |
MD5:94173DE2E35AA8D621FC1C4F54B2A082 | SHA256:7E2C70B7732FB1A9A61D7CE3D7290BC7B31EA28CBFB1DBC79D377835615B941F | |||
| 2568 | Caught.Power.exe | C:\Users\admin\AppData\Local\Temp\BedsPrivate.dll | executable | |
MD5:E833484E615275397572EE4521212A3B | SHA256:1623CE75EAFBEA439B2DDB02C3D186DB9541D21CAD4D583096FCF1DFE4AD28A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report