| download: | index.html |
| Full analysis: | https://app.any.run/tasks/0747321f-2620-44c7-ba7e-32adc3a14aa3 |
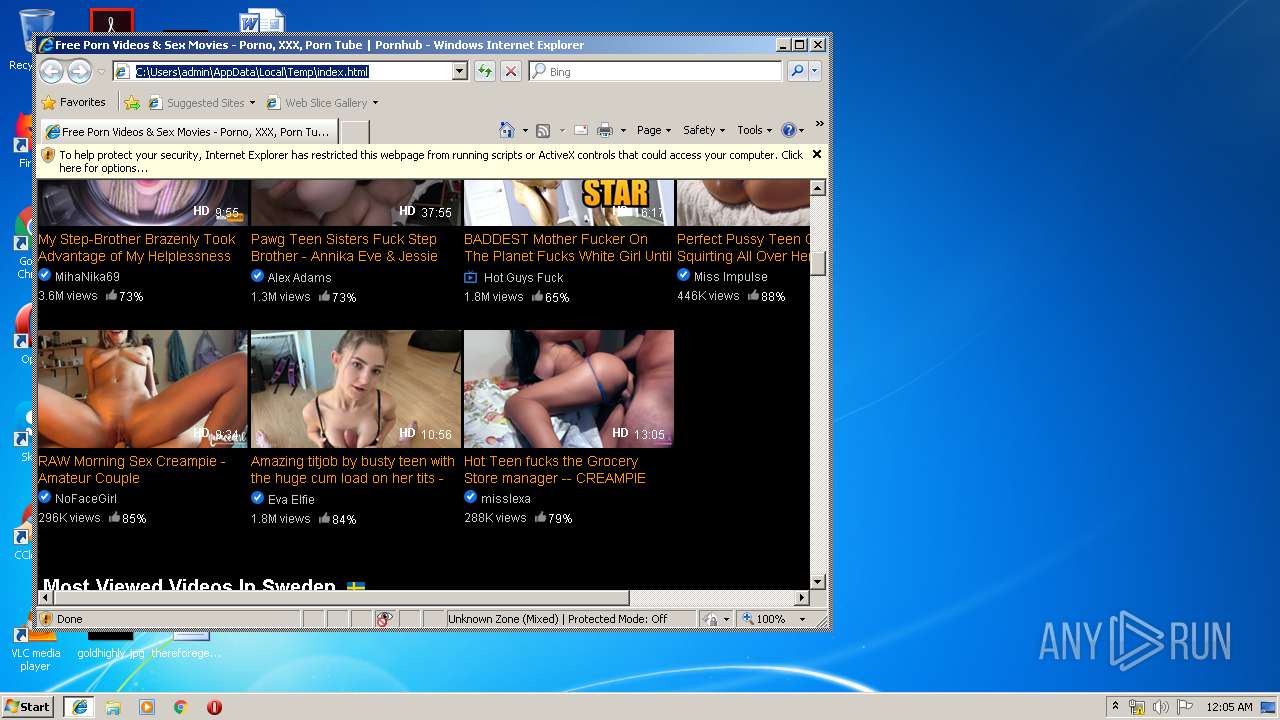
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2019, 23:04:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 6387A3C60392BD2FBAC542F92B9A9064 |
| SHA1: | 379E3E5E207F379116C782FCFF2BF82814B8F8EC |
| SHA256: | 7BA97E234BAE9296E05999419CC69AE36B1E555914AE9D6EBAC34264ECFB0A5E |
| SSDEEP: | 6144:Bz1Sq9a/NT3be1PJkIJRnBRJ3bE7a0QgSEeS1mF1F:DxJ3I7FSEy |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- iexplore.exe (PID: 3324)
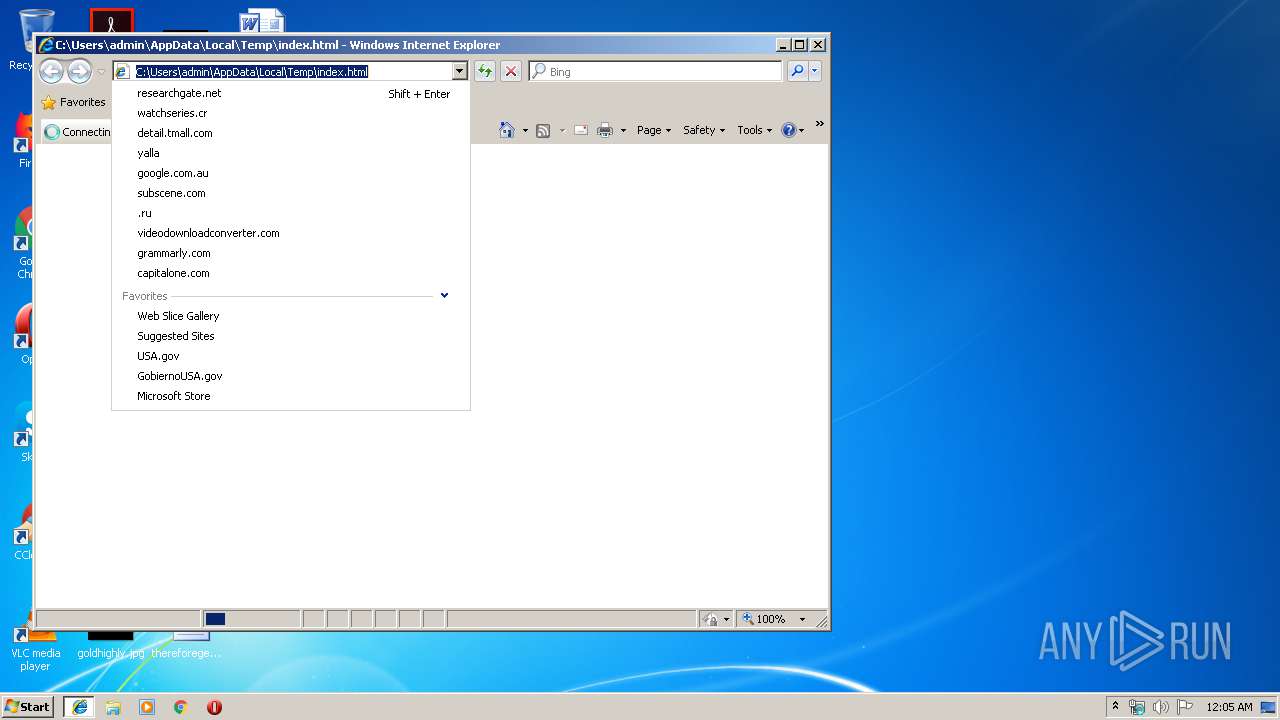
Reads internet explorer settings
- iexplore.exe (PID: 3324)
Changes settings of System certificates
- iexplore.exe (PID: 3324)
Application launched itself
- iexplore.exe (PID: 2916)
Reads Internet Cache Settings
- iexplore.exe (PID: 3324)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3324)
Changes internet zones settings
- iexplore.exe (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
| HTTPEquivXUACompatible: | IE=edge |
| msapplicationConfig: | none |
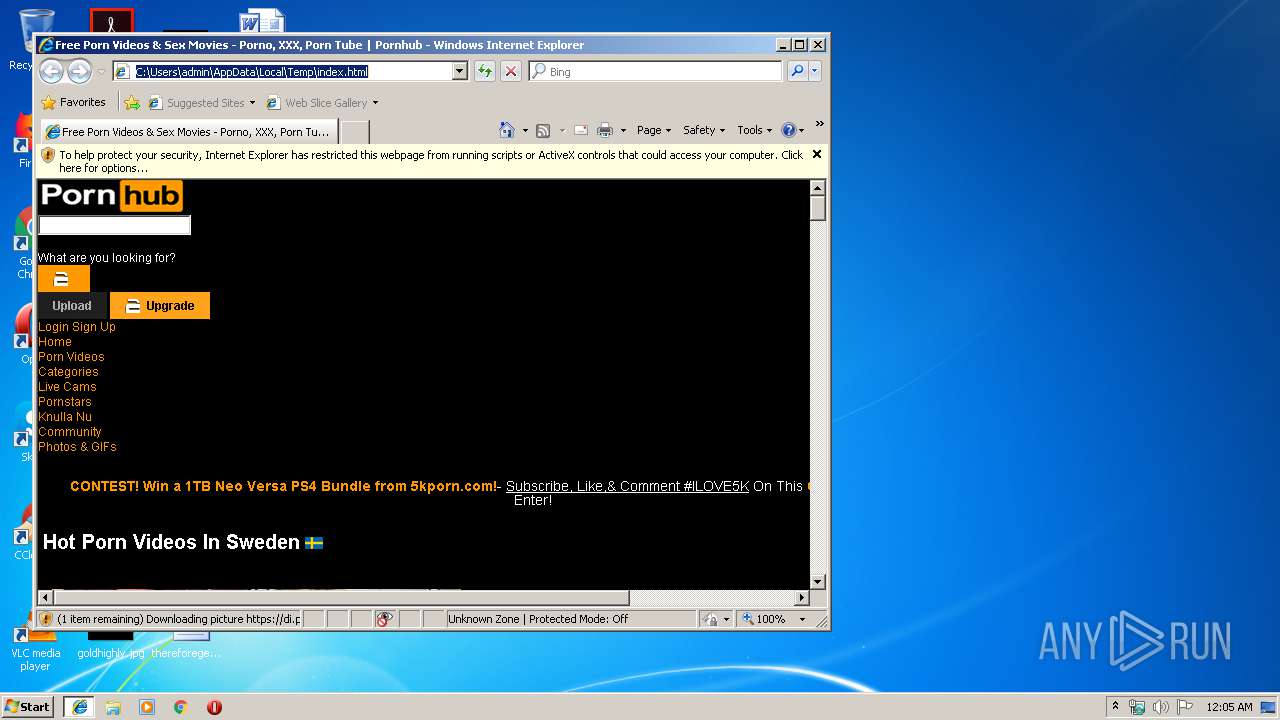
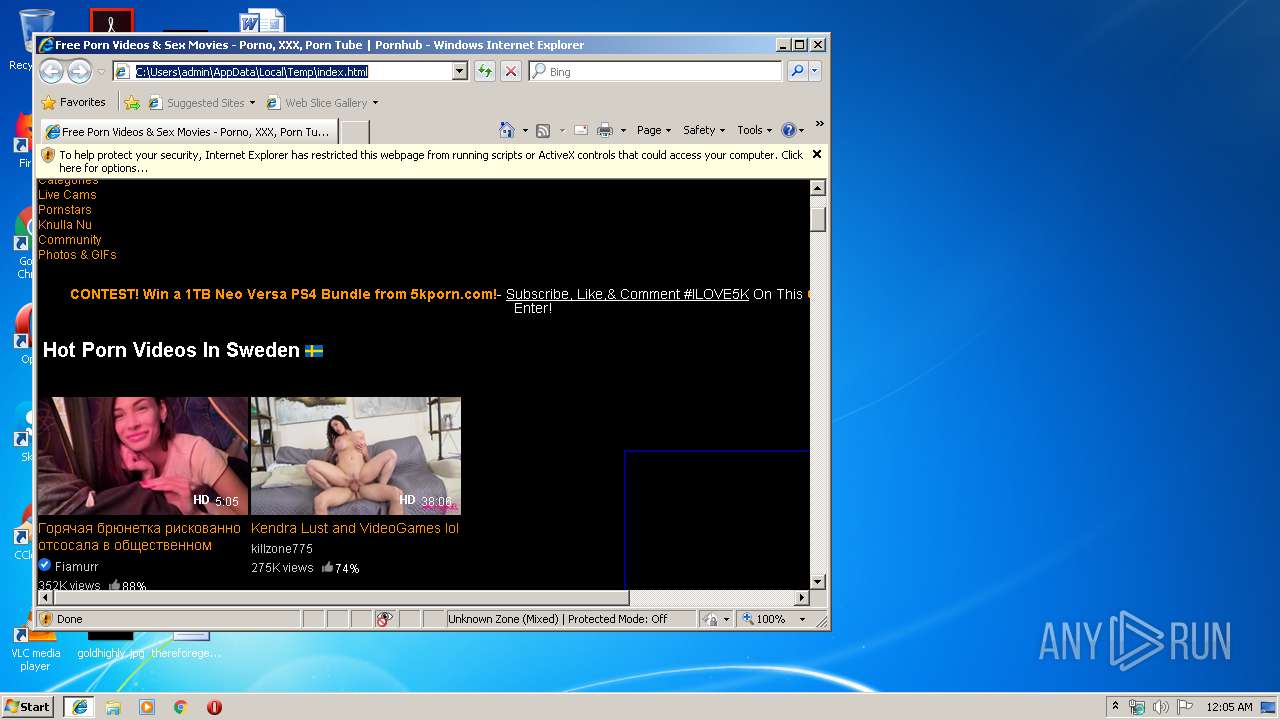
| Description: | Pornhub is the world’s leading free porn site. Choose from millions of hardcore videos that stream quickly and in high quality, including amazing VR Porn. The largest adult site on the Internet just keeps getting better. We have more pornstars and real amateurs than anyone else. It’s fast, it’s free, it’s Pornhub! |
| Title: | Free Porn Videos & Sex Movies - Porno, XXX, Porn Tube | Pornhub |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
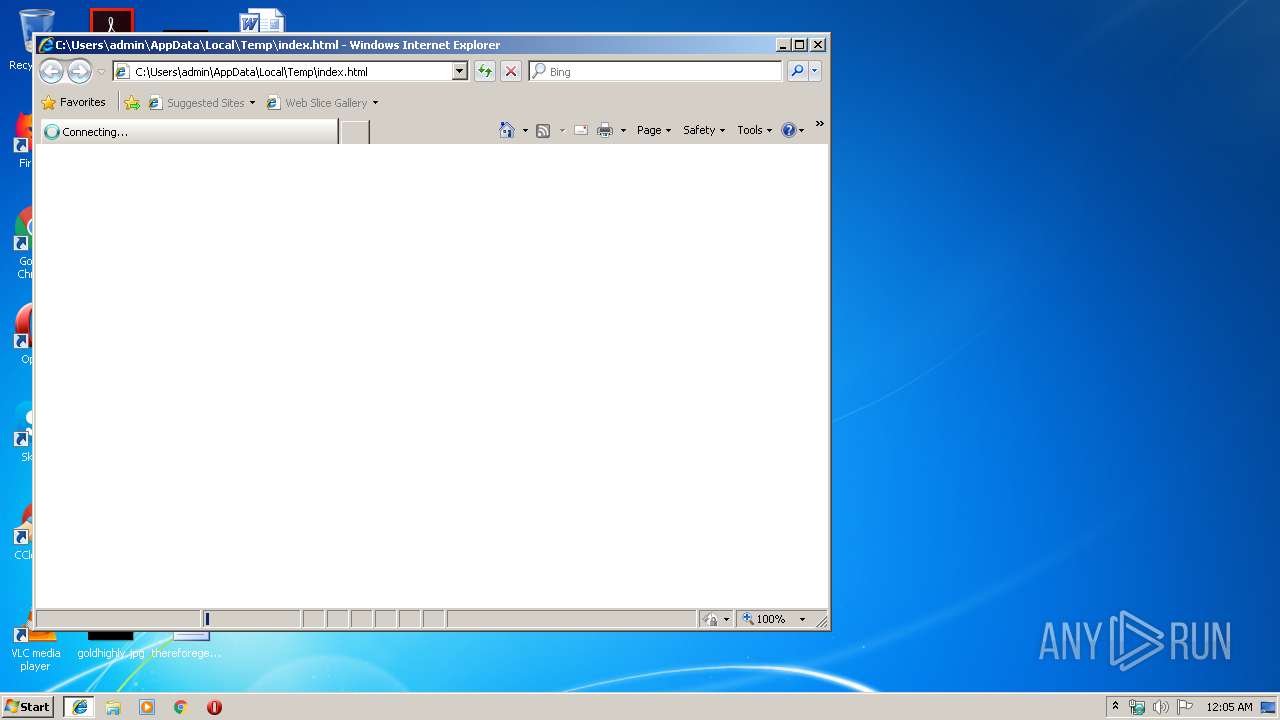
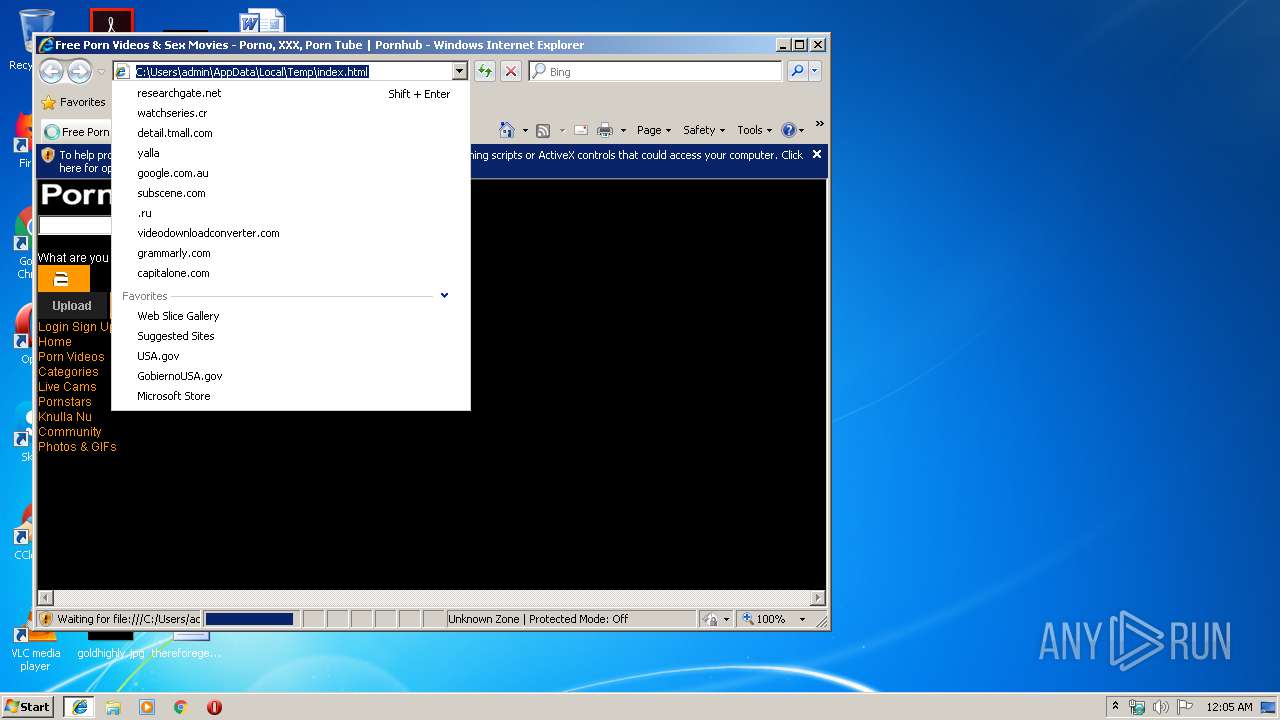
| 2916 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2916 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
413
Read events
330
Write events
81
Delete events
2
Modification events
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {11011099-E0B2-11E9-9A49-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307090004001A001700050002004B00 | |||
Executable files
0
Suspicious files
0
Text files
53
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\generated-header[1].css | text | |
MD5:02FE3A60AD3F67B02267344B164EA281 | SHA256:E7315BDB789B621478A69ECCAD5BF4C3D2B252CD3BF82EE0EA2ECA9A315E77E8 | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\premium-modals[1].css | text | |
MD5:B5652F470D1295458288C0507B64363B | SHA256:4FC9F1F243FBBC6C901FDA95807D2EA64550B7E765F0011C6D065F4B8A0D39C2 | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\ph-tracking[1].js | text | |
MD5:4B8296FB5F8C4EDB3BB10CDCB8FDF8D7 | SHA256:0EFDB7573776D190A2B35E2D51199F214AB58F959F4523430B4FD41AA829483D | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\front-index-pc[1].css | text | |
MD5:33C14739CCA519272A56CA6C46B8D547 | SHA256:AC17D97FD4CD14B283418089A9AD72E8C67932DBD6BCD073E92435045D1F0DC3 | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\mg_utils-1.0.0[1].js | text | |
MD5:76BB3A5D7C40A1D09F8F65151CC545F2 | SHA256:DDC9F4F47E1899AC87825AB4FF864E5CDB861BCB237FF6F9971D0EAD18B45CBB | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[1].txt | text | |
MD5:99B94D072C28C9CC881236E92C0FB2BB | SHA256:CC71D3AA49AC78E3613C7A6CC8BDF65045ED12DE8956F59C15EAFDA8228187AA | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\smpop-stable[1].js | text | |
MD5:BD32D5A33B8190A868B791604A604EE7 | SHA256:8CACE318B79F9144DD6608C2DDAFED4546872CEC3FF9C79E6452CC26AE6EC500 | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\large[1].css | text | |
MD5:46430D4F49CD23CB0DD258914EB1C295 | SHA256:0A6244A3CB2156DA6EB39F9E6C46F9B579B08428193D220A37DD47A56AF9059B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
39
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2916 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3324 | iexplore.exe | 66.254.114.38:443 | ads.trafficjunky.net | Reflected Networks, Inc. | US | unknown |
3324 | iexplore.exe | 216.18.168.166:443 | a.adtng.com | Reflected Networks, Inc. | US | suspicious |
3324 | iexplore.exe | 205.185.208.78:443 | hw-cdn2.contentabc.com | Highwinds Network Group, Inc. | US | suspicious |
3324 | iexplore.exe | 205.185.208.142:443 | di.phncdn.com | Highwinds Network Group, Inc. | US | suspicious |
3324 | iexplore.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3324 | iexplore.exe | 205.185.208.85:443 | media.trafficjunky.net | Highwinds Network Group, Inc. | US | unknown |
3324 | iexplore.exe | 192.229.221.214:443 | vz-cdn2.contentabc.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3324 | iexplore.exe | 192.229.221.215:443 | vz-cdn.trafficjunky.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3324 | iexplore.exe | 69.16.175.10:443 | smpop.icfcdn.com | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
smpop.icfcdn.com |
| malicious |
di.phncdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn1d-static-shared.phncdn.com |
| whitelisted |
static.trafficjunky.com |
| whitelisted |
ci.phncdn.com |
| whitelisted |
www.google.com |
| malicious |
ads.trafficjunky.net |
| whitelisted |