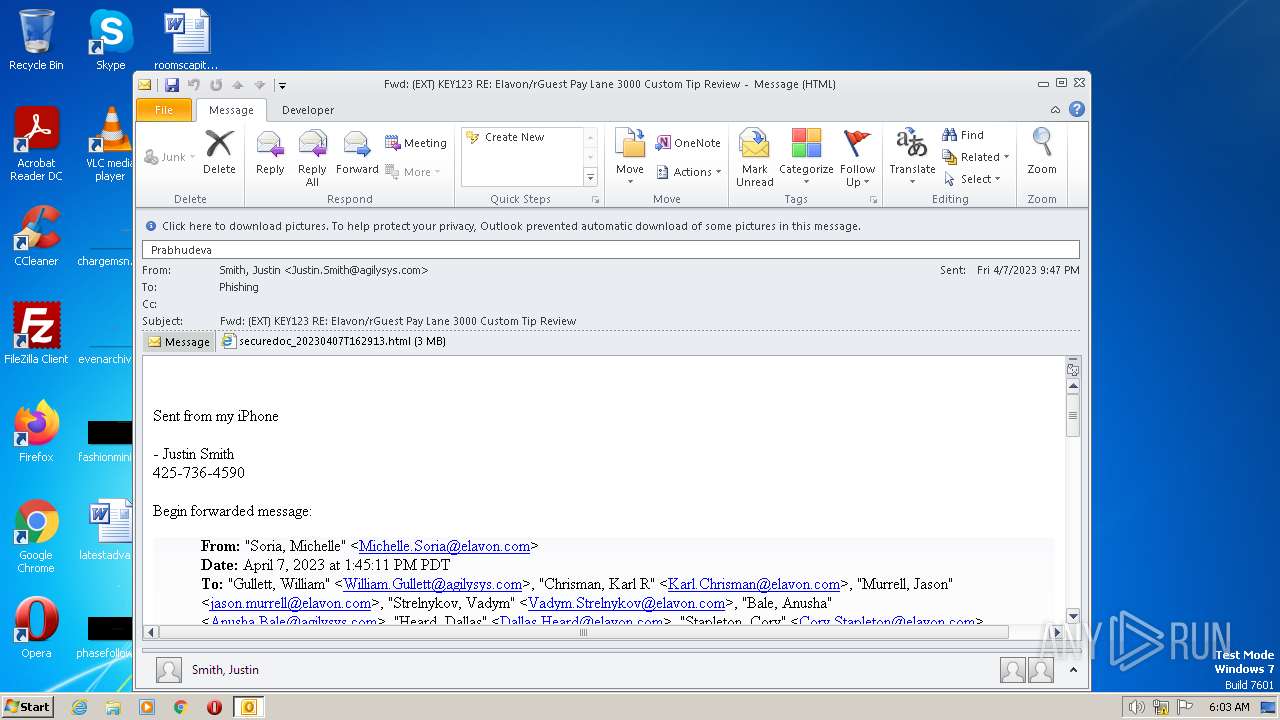
| File name: | (EXT) KEY123 RE Elavon_rGuest Pay Lane 3000 Custom Tip Review.eml |
| Full analysis: | https://app.any.run/tasks/956a617d-f1fa-4898-a6a8-96dc3dec9d0d |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2023, 05:03:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | A32552F98761D740EACE5F8317A66965 |
| SHA1: | 19BAA49E0B2B39C73F82849C17423A5F0F7857C3 |
| SHA256: | 7B94D1FB451FB8B66B848DA7C92907495A29C91D72891DEE4881CD182266C99E |
| SSDEEP: | 49152:RuFlLzcoRzVze+SpX3T2sUW9s18ikI62EhOk8GUv:U |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- OUTLOOK.EXE (PID: 976)
Searches for installed software
- OUTLOOK.EXE (PID: 976)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 976)
Reads the computer name
- OUTLOOK.EXE (PID: 976)
Creates files or folders in the user directory
- OUTLOOK.EXE (PID: 976)
The process uses the downloaded file
- OUTLOOK.EXE (PID: 976)
- iexplore.exe (PID: 3440)
- iexplore.exe (PID: 3360)
Application launched itself
- iexplore.exe (PID: 3360)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 976)
Checks proxy server information
- OUTLOOK.EXE (PID: 976)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 976)
The process checks LSA protection
- OUTLOOK.EXE (PID: 976)
Create files in a temporary directory
- OUTLOOK.EXE (PID: 976)
- iexplore.exe (PID: 3360)
Process checks computer location settings
- OUTLOOK.EXE (PID: 976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
43
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
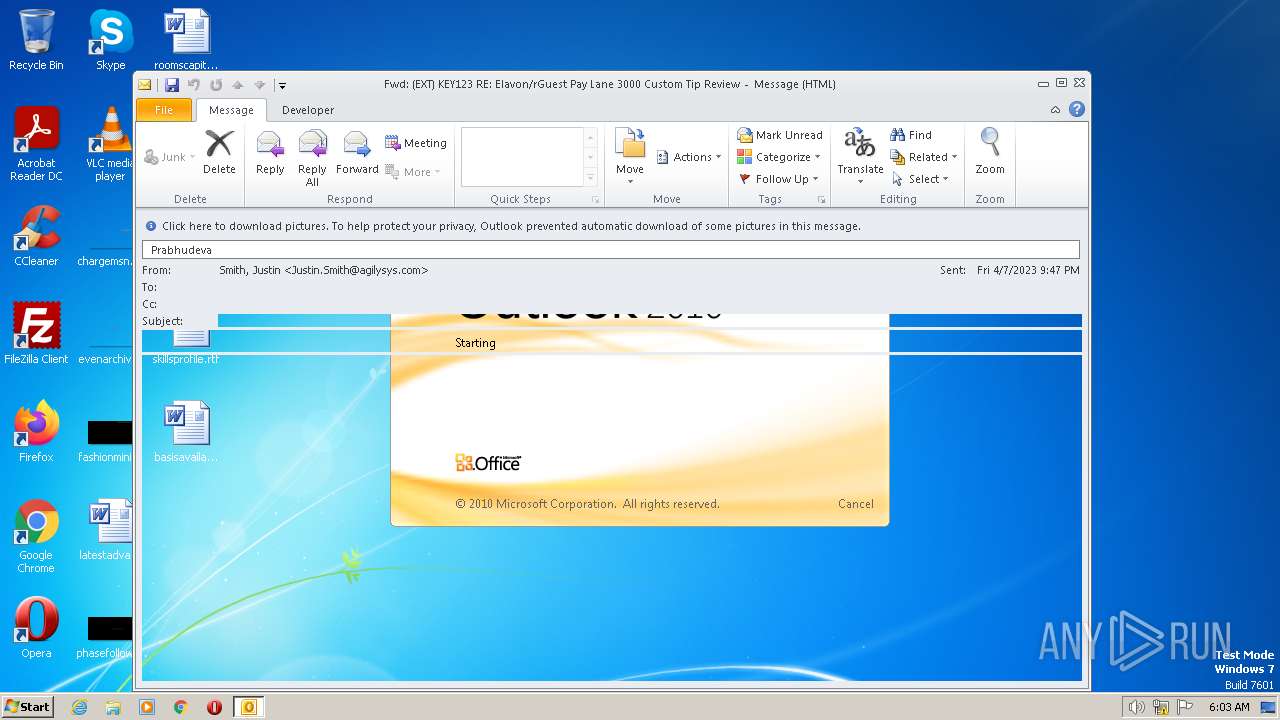
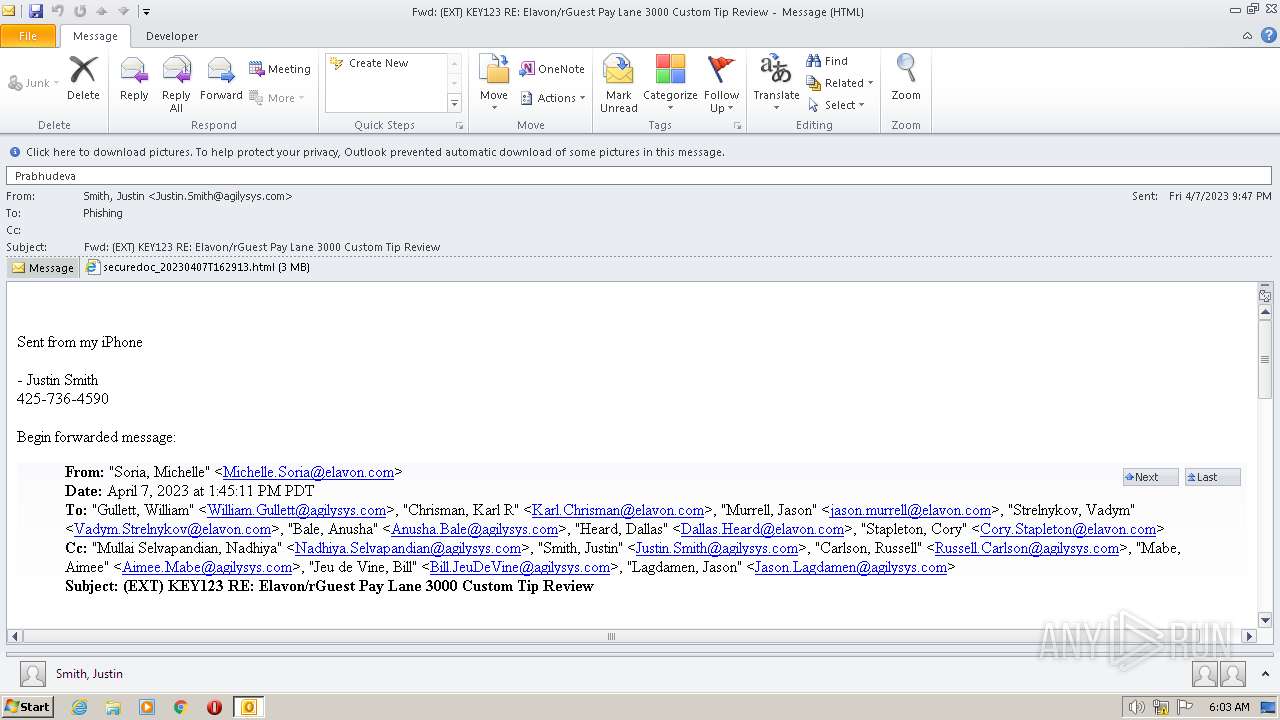
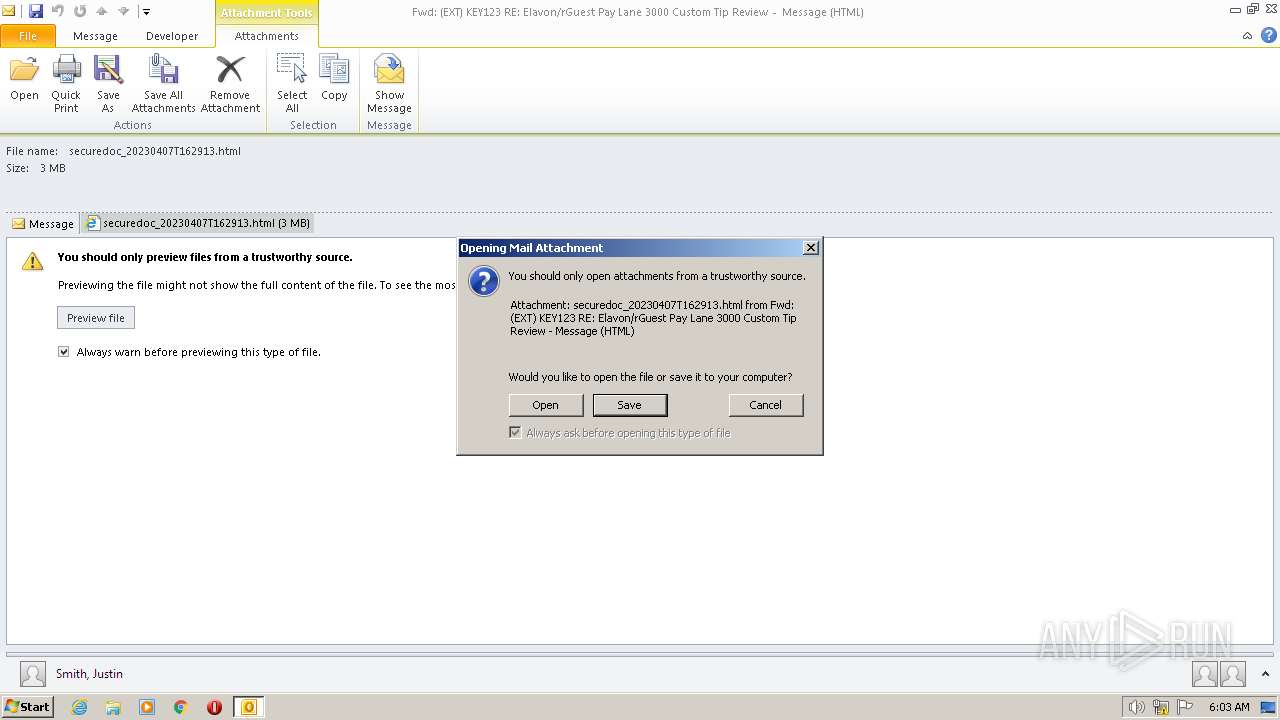
| 976 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\(EXT) KEY123 RE Elavon_rGuest Pay Lane 3000 Custom Tip Review.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
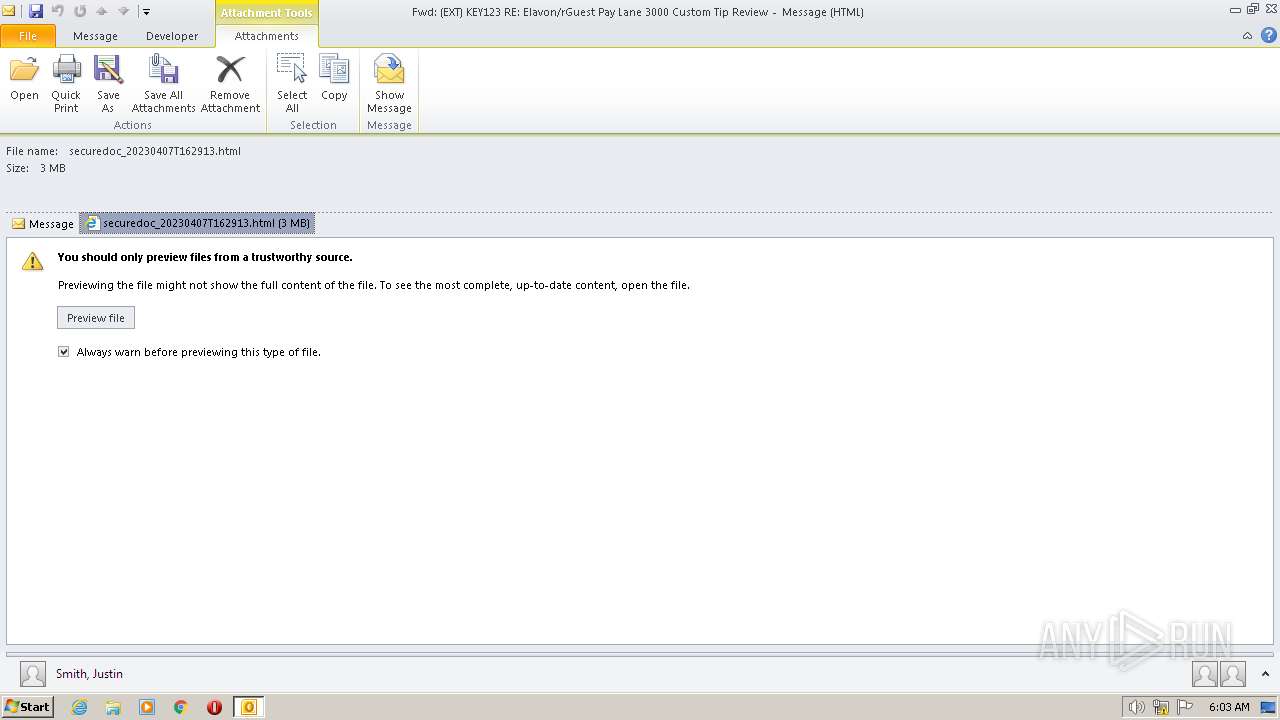
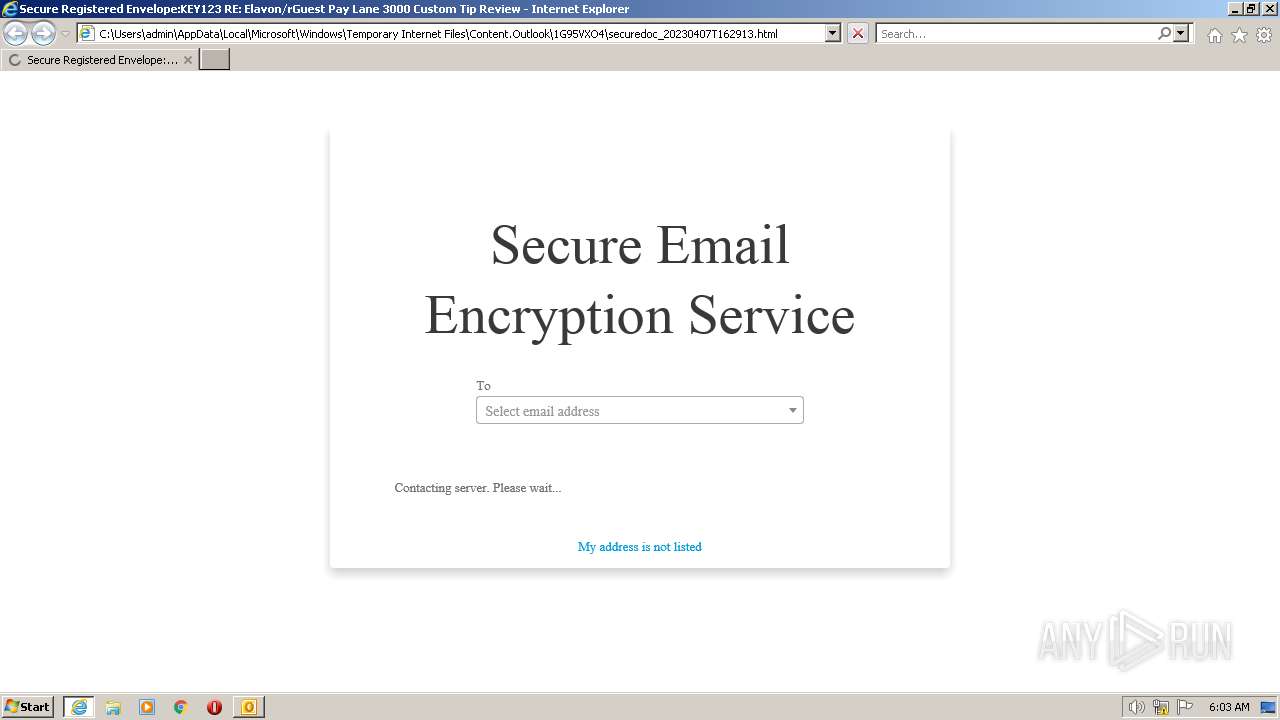
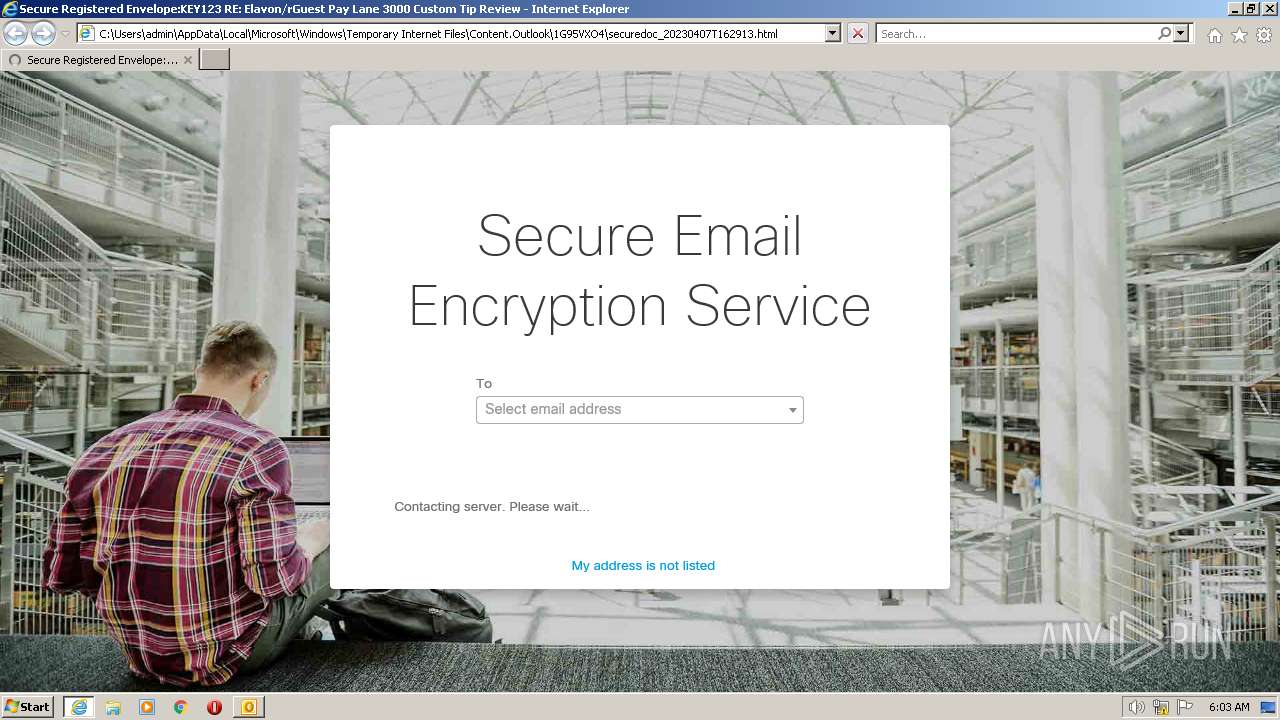
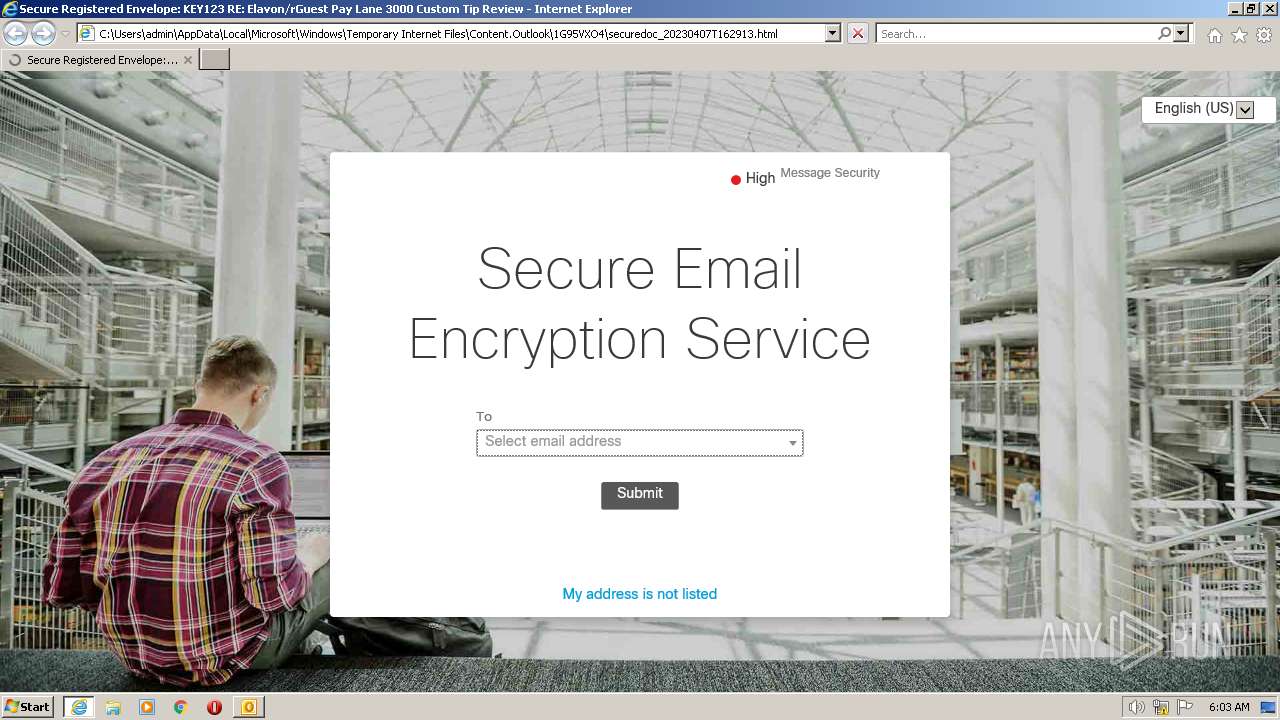
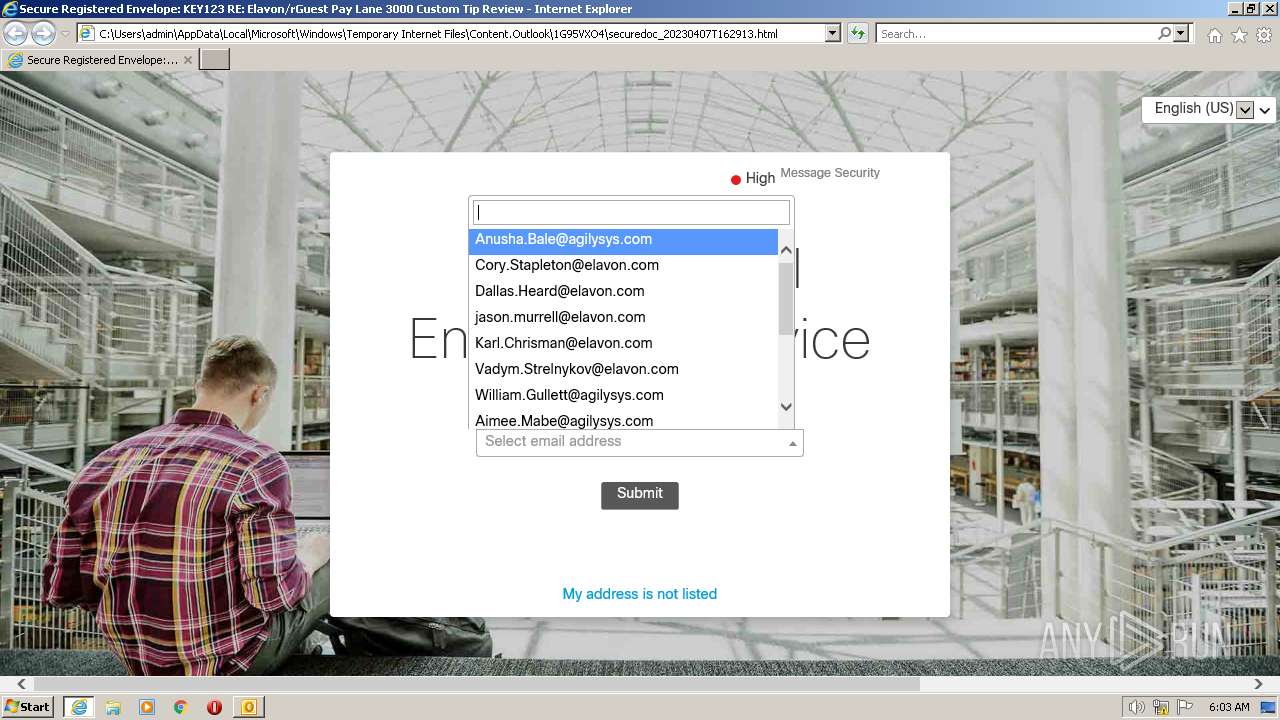
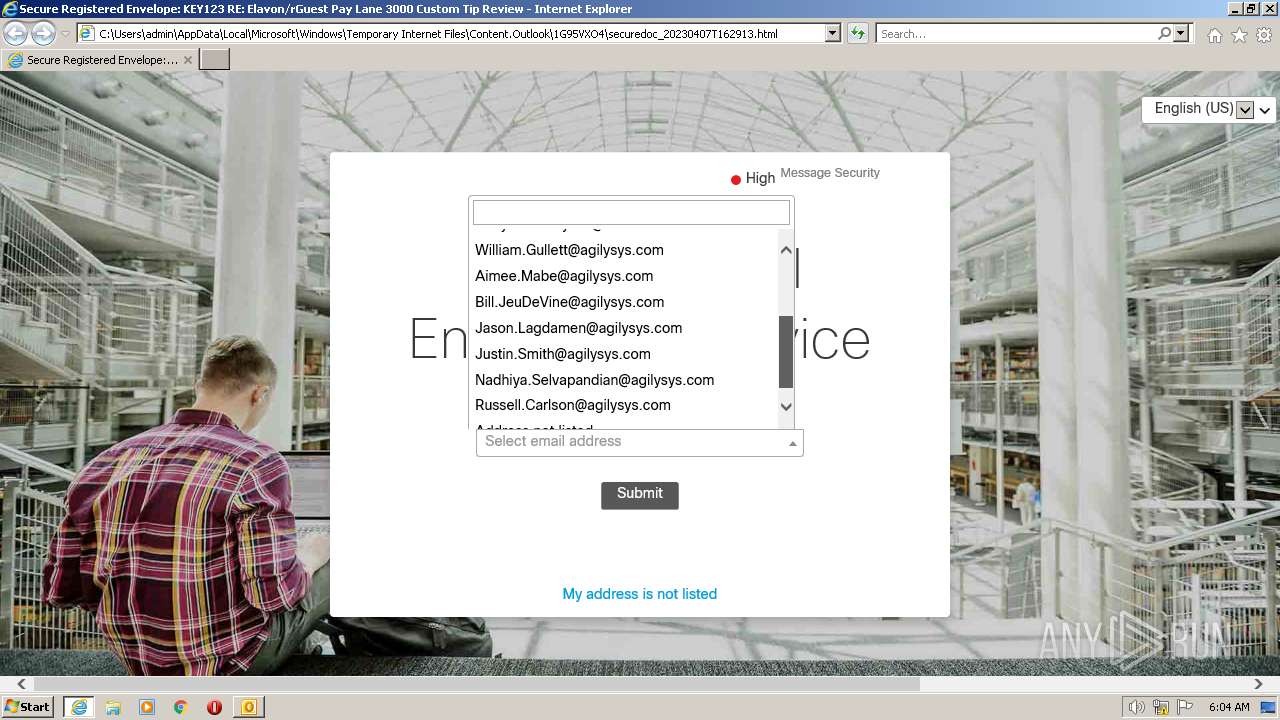
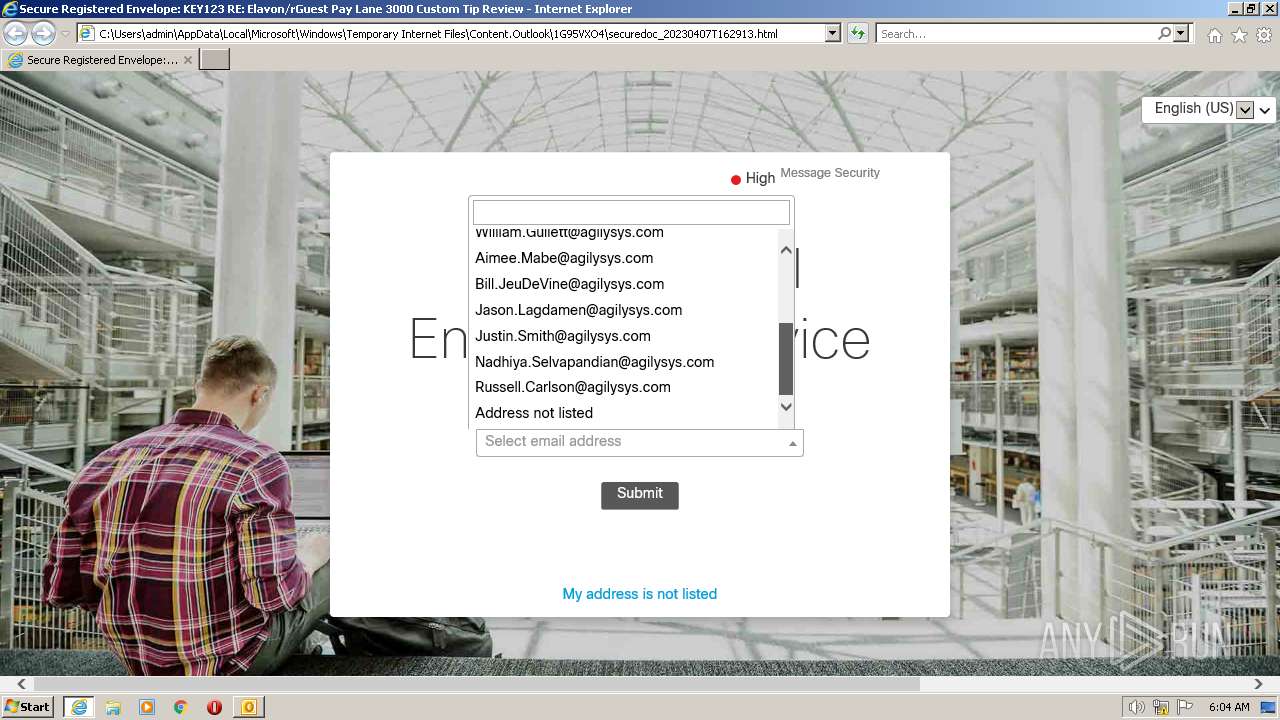
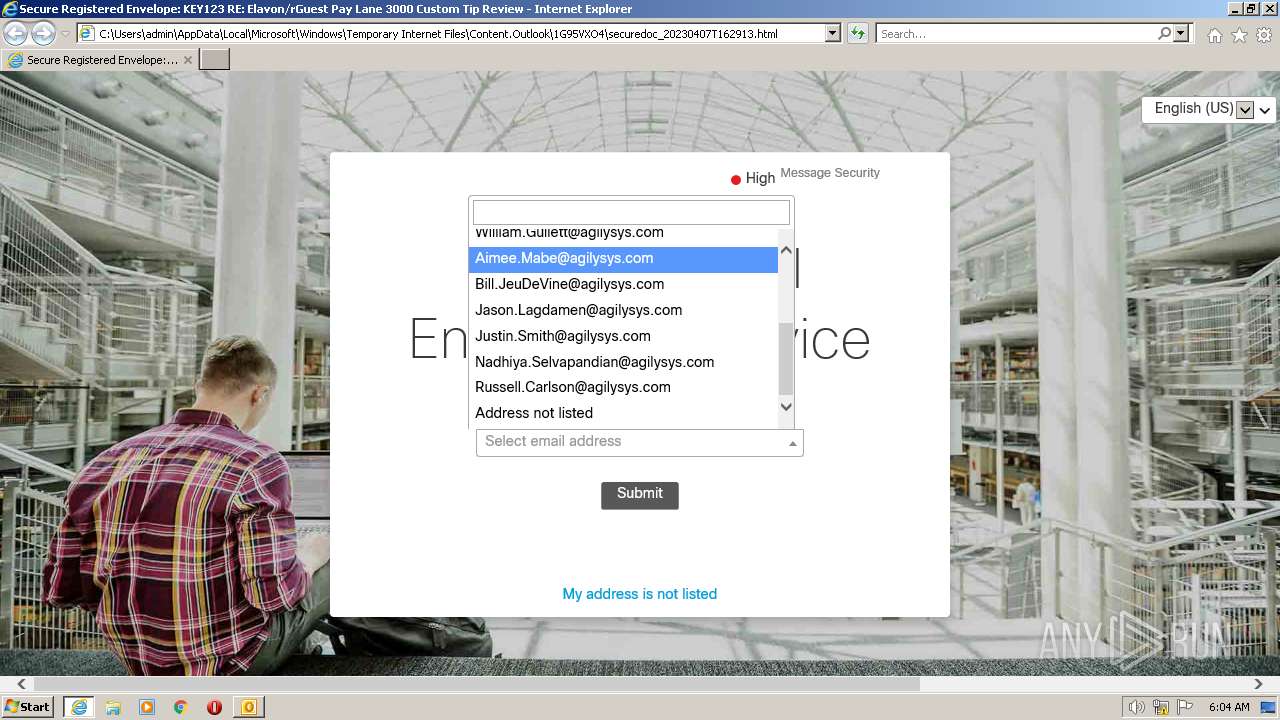
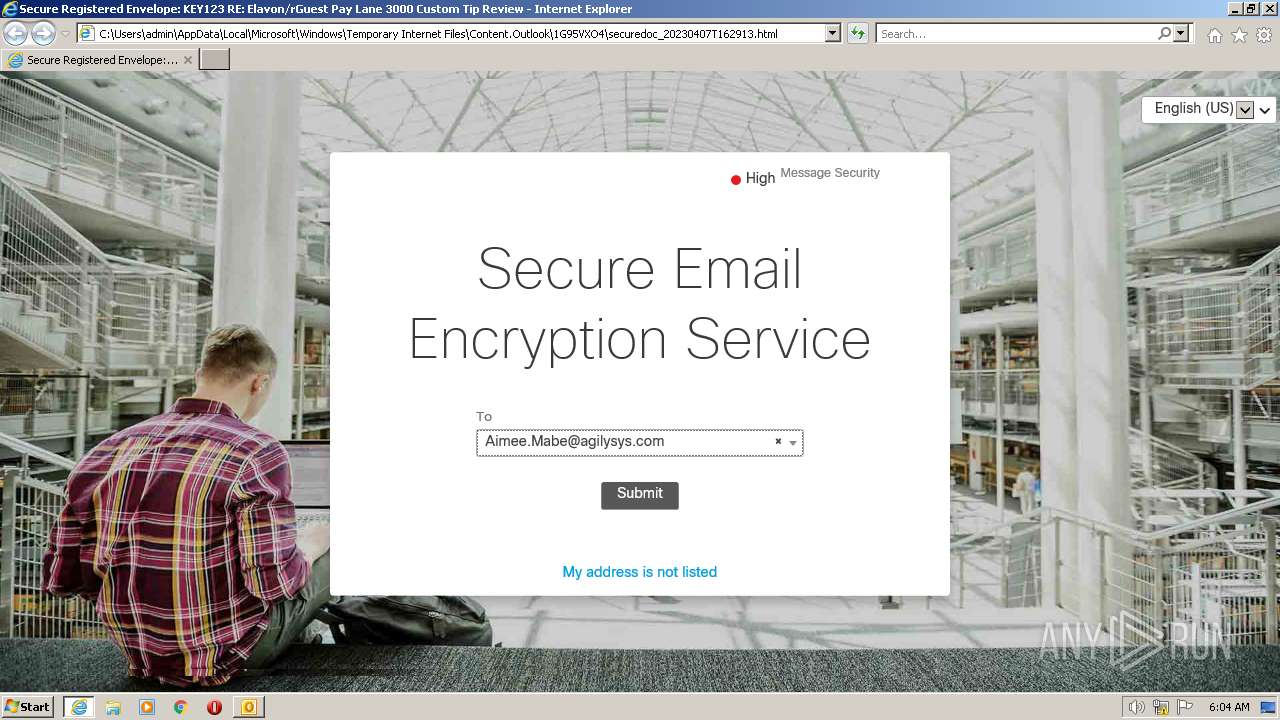
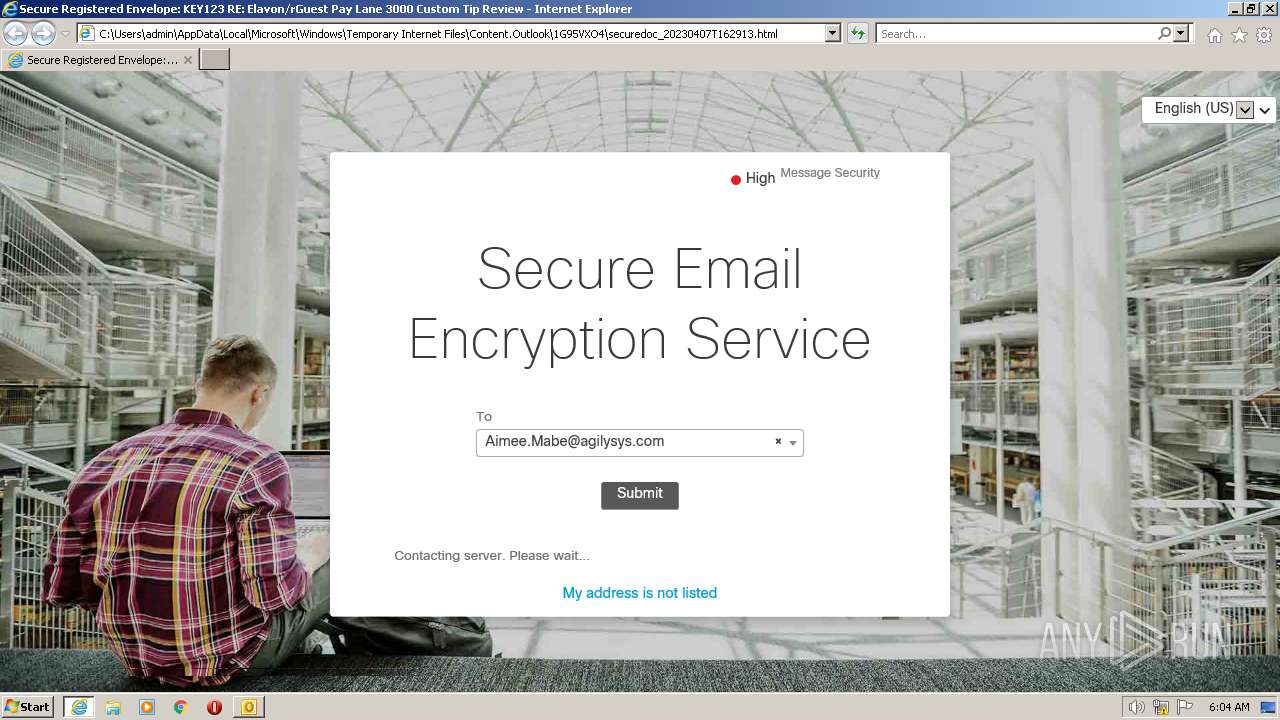
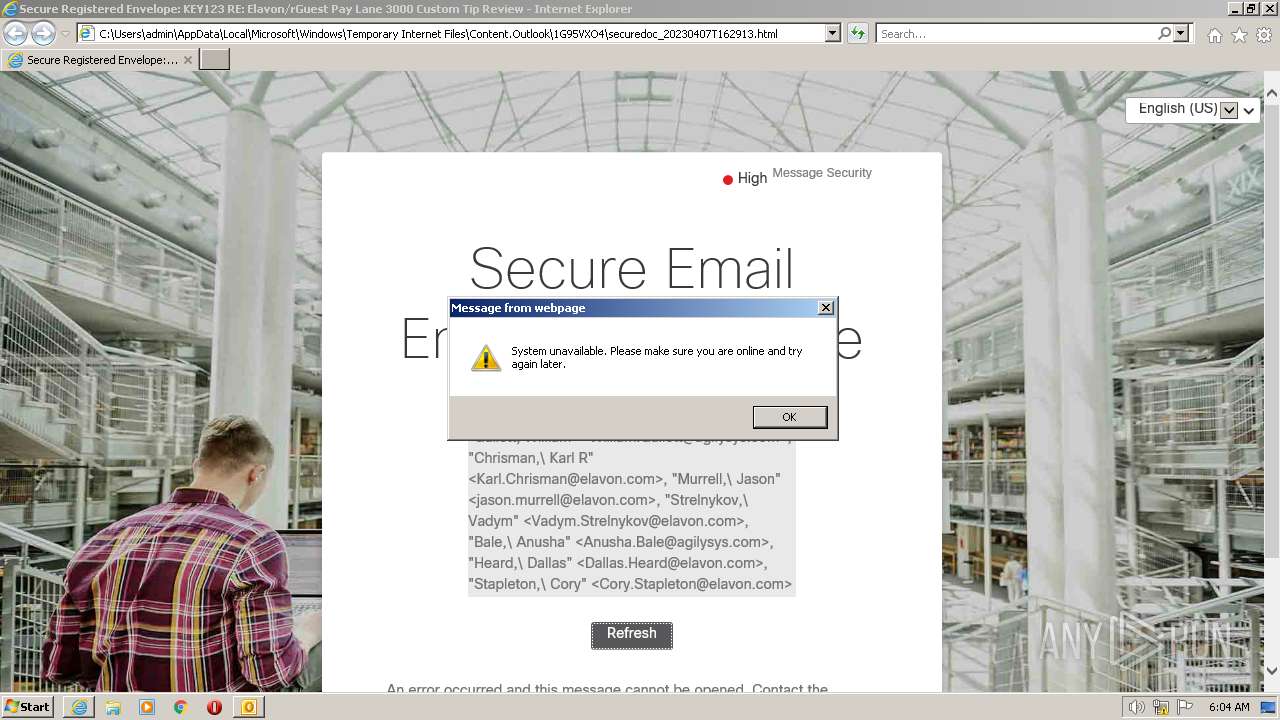
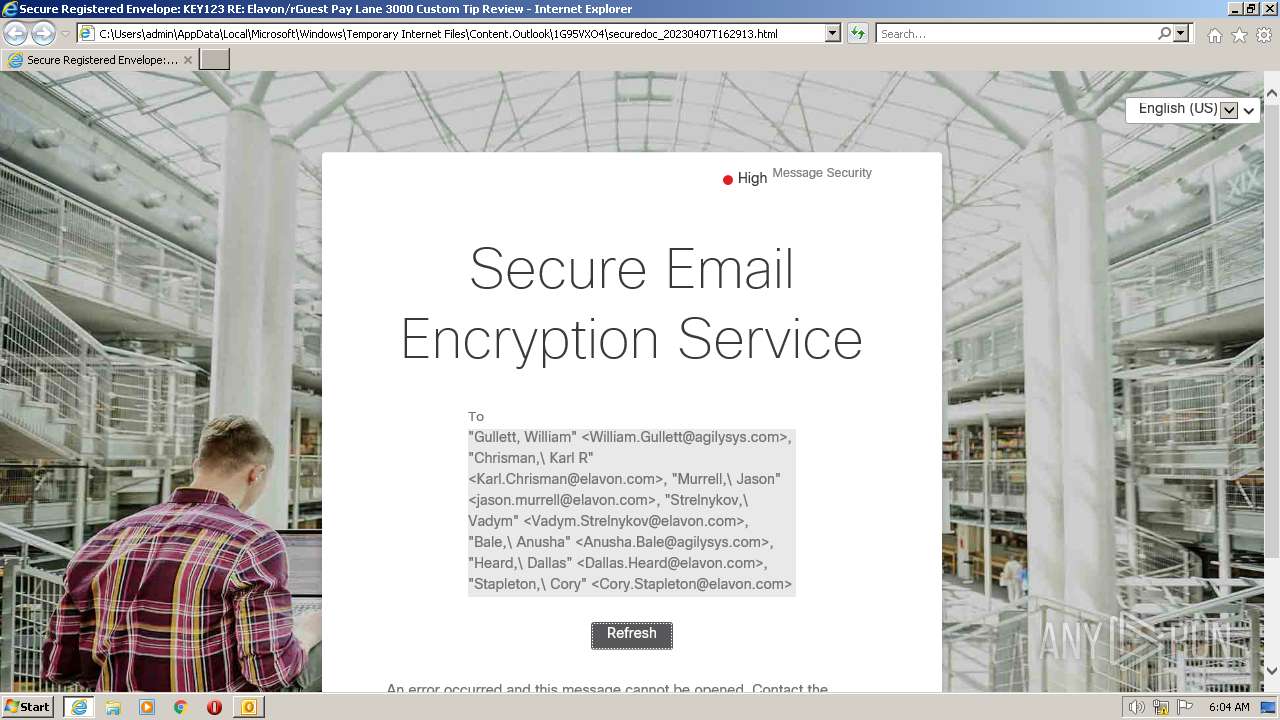
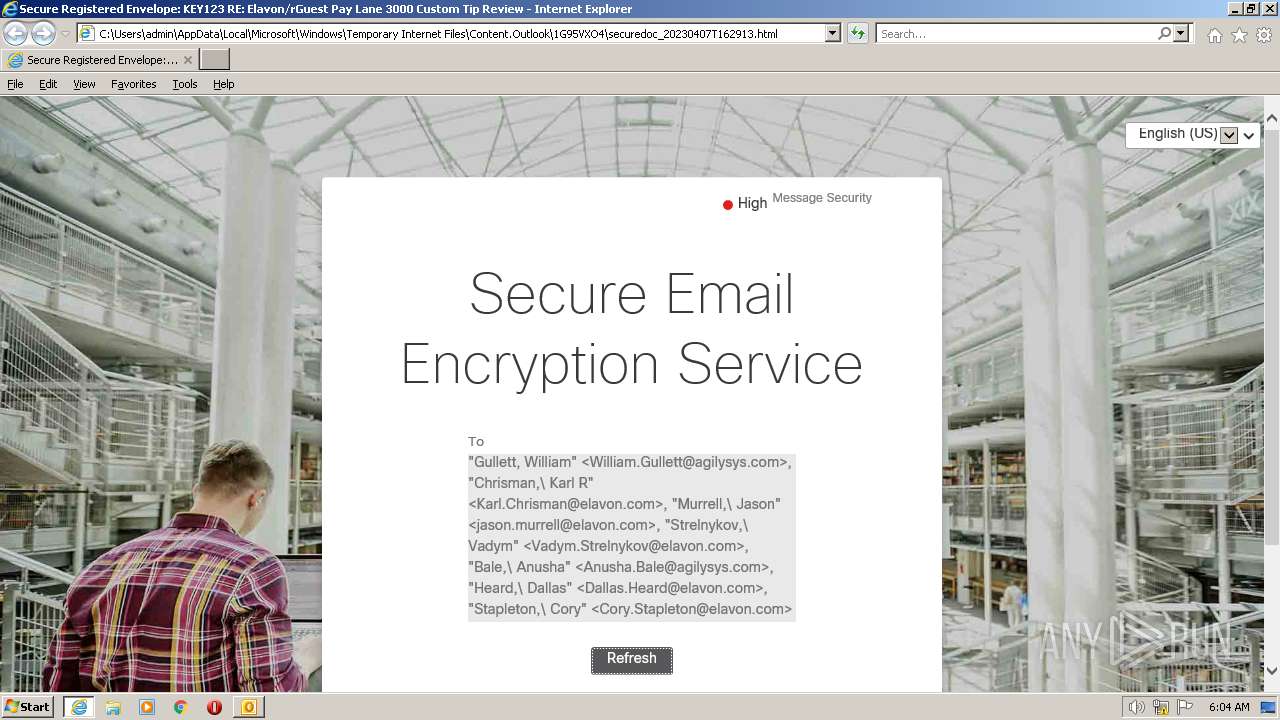
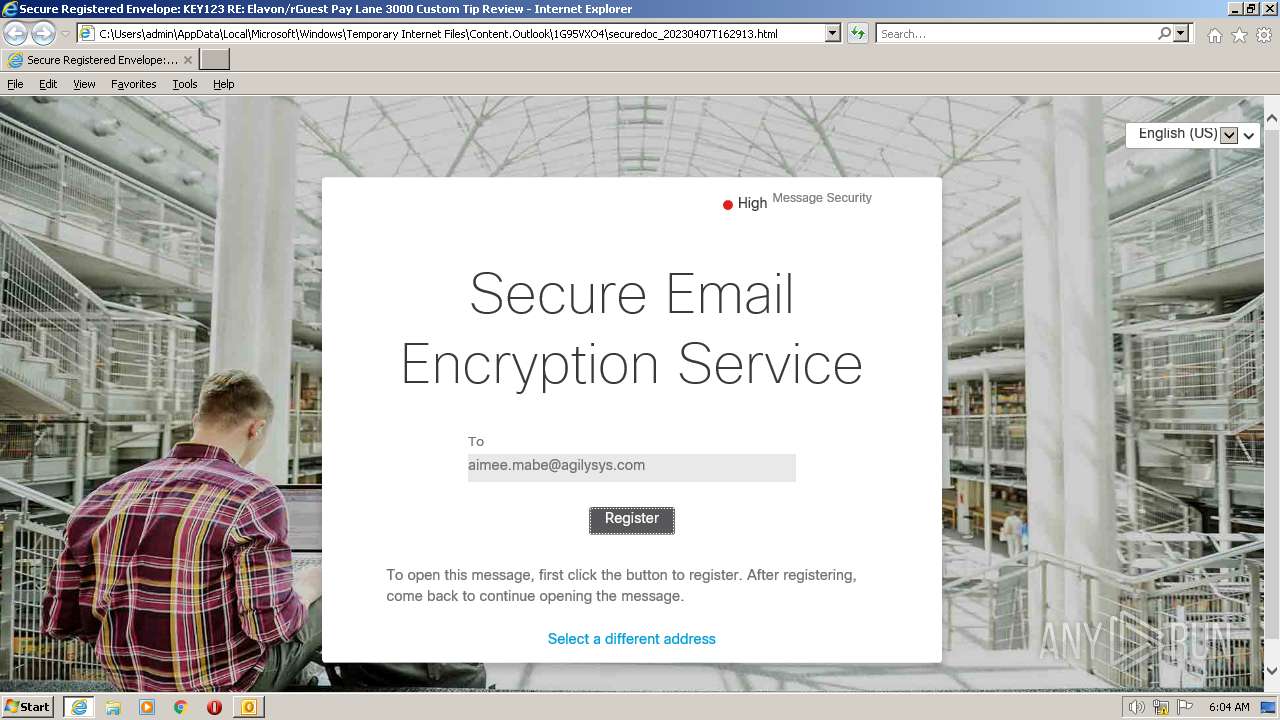
| 3360 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\1G95VXO4\securedoc_20230407T162913.html | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3360 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
54 428
Read events
53 356
Write events
1 030
Delete events
42
Modification events
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
32
Text files
70
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3995.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 976 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp3A90.tmp | text | |
MD5:— | SHA256:— | |||
| 976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\1G95VXO4\securedoc_20230407T162913.html | html | |
MD5:— | SHA256:— | |||
| 976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\1G95VXO4\securedoc_20230407T162913 (2).html | html | |
MD5:— | SHA256:— | |||
| 976 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{E83AEEAE-96D3-4F8A-90ED-AB7F18BE985B}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
45
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3440 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3440 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGnhTGFYa4skEkyCQVF3HZA%3D | US | der | 471 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 192.35.177.23:80 | http://commercial.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTQfEOioPd4%2FtCA3%2FhgDklRXB0FwgQU7UQZwNPwBovupHu%2BQucmVMiONnYCEEABbvsKIFz66%2BGPcdc6u3g%3D | US | der | 1.63 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ad1f393dd2f7d474 | US | compressed | 4.70 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 192.35.177.23:80 | http://commercial.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTULRG8NAnkG2vMiFulhUophWOf2gQUibibtp7t%2B7DGvQ3sZ048o5KdLfkCEEABhOKKoQP0FGqRTxMATX0%3D | US | der | 1.46 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 52.222.250.185:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8f8c644f39fefedb | US | compressed | 4.70 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5488ac47bf898aa2 | US | compressed | 4.70 Kb | whitelisted |
3360 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3440 | iexplore.exe | 184.94.241.74:80 | res.cisco.com | IRONPORT-SYSTEMS-INC | US | suspicious |
3440 | iexplore.exe | 184.94.241.74:443 | res.cisco.com | IRONPORT-SYSTEMS-INC | US | suspicious |
3440 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
976 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3440 | iexplore.exe | 192.35.177.23:80 | commercial.ocsp.identrust.com | SLC-IDENT-AS | US | unknown |
3440 | iexplore.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | suspicious |
3440 | iexplore.exe | 108.138.2.173:80 | o.ss2.us | AMAZON-02 | US | unknown |
3440 | iexplore.exe | 172.217.16.202:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
3360 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3440 | iexplore.exe | 13.224.194.124:443 | d11d0gmnmksscb.cloudfront.net | AMAZON-02 | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
res.cisco.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
commercial.ocsp.identrust.com |
| whitelisted |
d11d0gmnmksscb.cloudfront.net |
| whitelisted |
o.ss2.us |
| whitelisted |