| File name: | invitation.ics |
| Full analysis: | https://app.any.run/tasks/073f5200-c5ba-4aa7-a8c2-f90c52bff278 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 10:21:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/calendar |
| File info: | vCalendar calendar file |
| MD5: | 1A75618808716D9763AB6ECB5F26ED47 |
| SHA1: | 35585AFFF703BB6BA553735F024F7535D38CA374 |
| SHA256: | 7B709F6836E9707B53F1650E20AB509A6057D4D381C79CB662868BA77C3414C0 |
| SSDEEP: | 96:E0fUDS17/EhR/CHsVisOD+Jx7VXpSDkNf80nXDFqgoVi:j5/E//wu2s9VXQDkN00nXf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- OUTLOOK.EXE (PID: 456)
Creates files in the user directory
- OUTLOOK.EXE (PID: 456)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 456)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ics/vcs | | | iCalendar - vCalendar (100) |
|---|
EXIF
VCard
| VCalendarVersion: | 2 |
|---|---|
| Method: | PUBLISH |
| Software: | -//Microsoft Corporation//Outlook 11.0 MIMEDIR//EN |
| TimezoneID: | Europe/Paris |
| StandardDateTimeStart: | 2000:10:29 03:00:00 |
| StandardRecurrenceRule: | FREQ=YEARLY;BYDAY=-1SU;BYMONTH=10 |
| StandardTimezoneName: | CET |
| StandardTimezoneOffsetFrom: | +0200 |
| StandardTimezoneOffsetTo: | +0100 |
| DaylightDateTimeStart: | 2000:03:26 02:00:00 |
| DaylightRecurrenceRule: | FREQ=YEARLY;BYDAY=-1SU;BYMONTH=3 |
| DaylightTimezoneName: | CEST |
| DaylightTimezoneOffsetFrom: | +0100 |
| DaylightTimezoneOffsetTo: | +0200 |
| UID: | IB054616@instantbooking.renault.fr |
| DateTimeStart: | 2019:05:20 11:30:00 |
| DateTimeStartTimezoneID: | Europe/Paris |
| DateTimeEnd: | 2019:05:20 13:00:00 |
| DateTimeEndTimezoneID: | Europe/Paris |
| CalendarScale: | GREGORIAN |
| Classification: | PUBLIC |
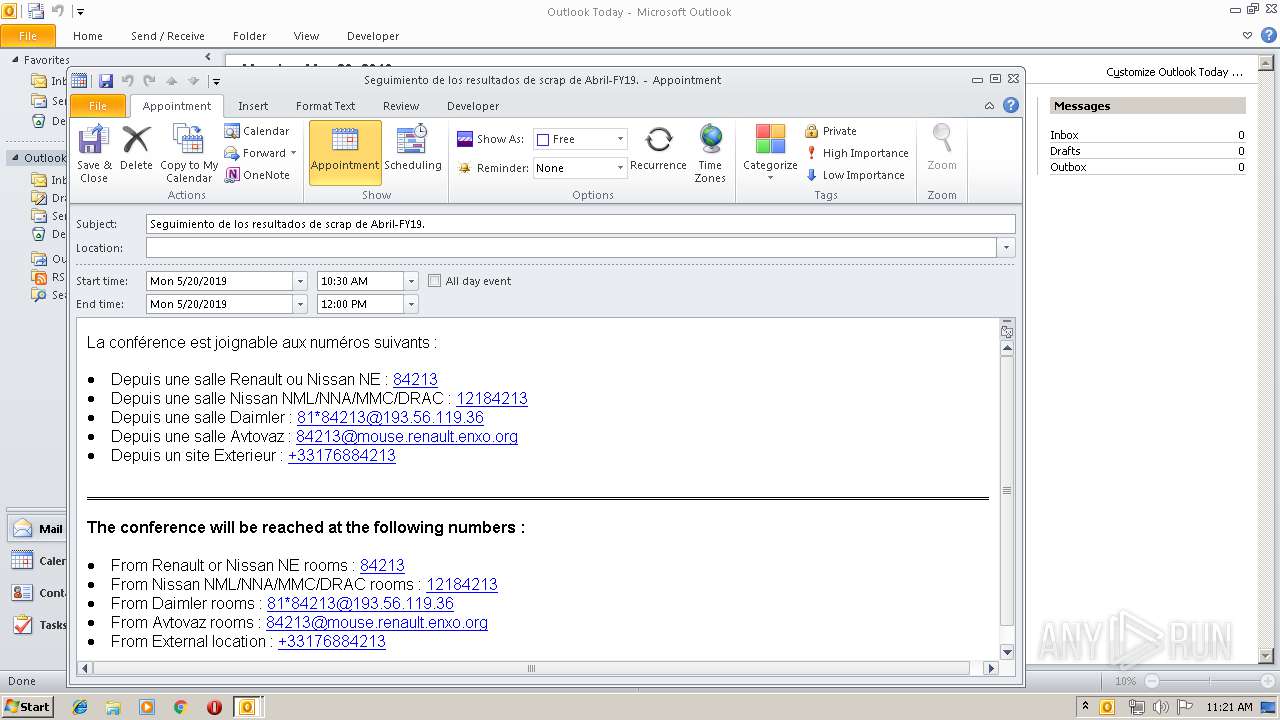
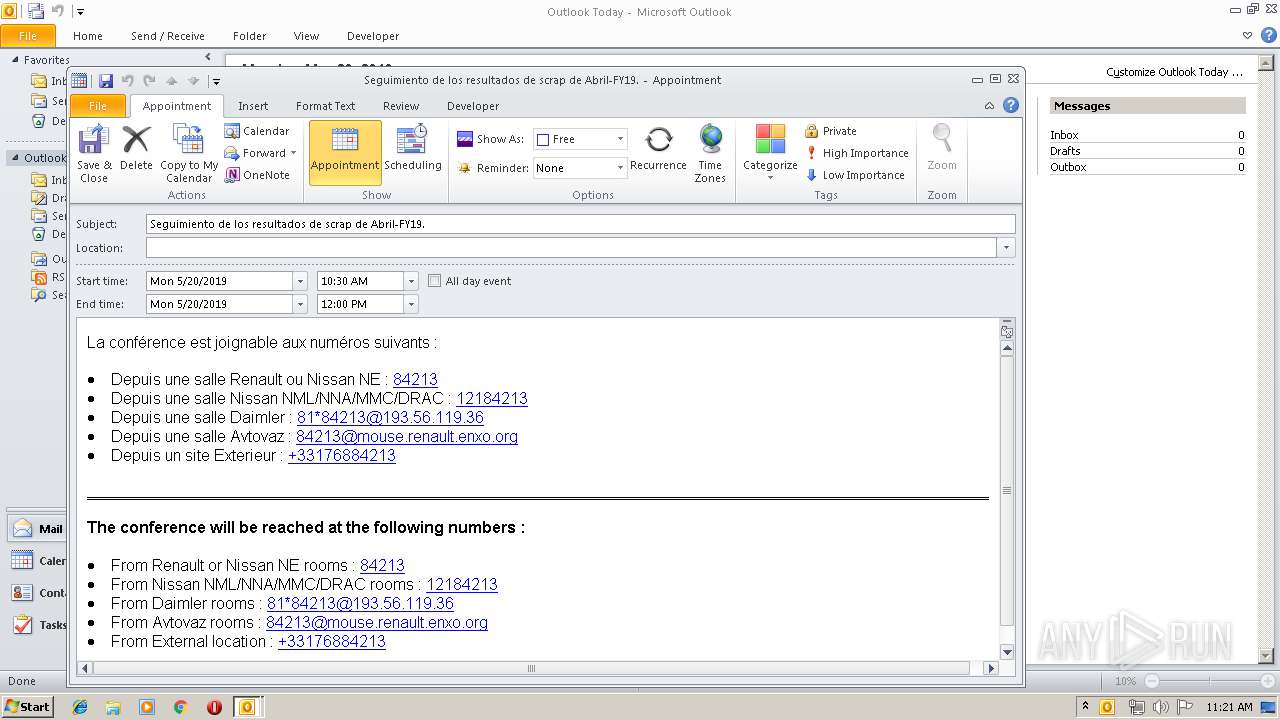
| Description: | La conférence est joignable aux numéros suivants : * Depuis une salle Renault ou Nissan NE : [84213][1] * Depuis une salle Nissan NML/NNA/MMC/DRAC : [12184213][2] * Depuis une salle Daimler : [81*84213@193.56.119.36][3] * Depuis une salle Avtovaz : [84213@mouse.renault.enxo.org][4] * Depuis un site Exterieur : [+33176884213][5] * * * **The conference will be reached at the following numbers :** * From Renault or Nissan NE rooms : [84213][1] * From Nissan NML/NNA/MMC/DRAC rooms : [12184213][2] * From Daimler rooms : [81*84213@193.56.119.36][3] * From Avtovaz rooms : [84213@mouse.renault.enxo.org][4] * From External location : [+33176884213][5] [1]: tel:84213 [2]: tel:12184213 [3]: tel:81*84213@193.56.119.36 [4]: tel:84213@mouse.renault.enxo.org [5]: tel:+33176884213 |
| DateTimeStamp: | 2019:05:20 06:28:08Z |
| Location: | - |
| Organizer: | mailto:alicia.lloviopinera@nmisa.es |
| Priority: | 5 |
| SequenceNumber: | - |
| Status: | CONFIRMED |
| Summary: | Seguimiento de los resultados de scrap de Abril-FY19. |
| TimeTransparency: | TRANSPARENT |
| URL: | https://instantbooking.renault.fr/ib/renault/portal/#bookings |
| Alt-desc: | <table cellspacing="0" cellpadding="5" style="font-size: 9pt;font-family:Arial;"> <tr style="font-weight:bold;font-size:100%;"> <td> <div>La conférence est joignable aux numéros suivants :</div> <ul> <li>Depuis une salle Renault ou Nissan NE : <a href="tel:84213">84213</a></li> <li>Depuis une salle Nissan NML/NNA/MMC/DRAC : <a href="tel:12184213">12184213</a></li> <li>Depuis une salle Daimler : <a href="tel:81*84213@193.56.119.36">81*84213@193.56.119.36</a></li> <li>Depuis une salle Avtovaz : <a href="tel:84213@mouse.renault.enxo.org">84213@mouse.renault.enxo.org</a></li> <li>Depuis un site Exterieur : <a href="tel:+33176884213">+33176884213</a></li> </ul> </td> </tr> <tr> <td bgcolor="#FFFFFF" style="font-size: 12pt; color: #333333; line-height: 17px;"> <hr style="color: #e0e0e0" size="1px"> </td> </tr> <tr style="font-weight:bold;font-size:100%;"> <td> <div><b>The conference will be reached at the following numbers :</b></div> <ul> <li>From Renault or Nissan NE rooms : <a href="tel:84213">84213</a></li> <li>From Nissan NML/NNA/MMC/DRAC rooms : <a href="tel:12184213">12184213</a></li> <li>From Daimler rooms : <a href="tel:81*84213@193.56.119.36">81*84213@193.56.119.36</a></li> <li>From Avtovaz rooms : <a href="tel:84213@mouse.renault.enxo.org">84213@mouse.renault.enxo.org</a></li> <li>From External location : <a href="tel:+33176884213">+33176884213</a></li> </ul> </td> </tr> </table> |
| Microsoft-cdo-busystatus: | FREE |
| Microsoft-disallow-counter: | - |
| Ms-olk-autofilllocation: | - |
| Ms-olk-conftype: | - |
| Ms-olk-forceinspectoropen: |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /ical "C:\Users\admin\AppData\Local\Temp\invitation.ics" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 571
Read events
1 096
Write events
439
Delete events
36
Modification events
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | (.= |
Value: 282E3D00C8010000010000000000000000000000 | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C801000030BAF8D2F50ED50100000000 | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220046400 | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (456) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1320419349 | |||
Executable files
0
Suspicious files
1
Text files
27
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR279.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFB0997B35E6A67CF7.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF502BC2B608000874.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{A5F20EAB-4819-477D-AC5E-6FDFE0BA2F8A}.tmp | — | |
MD5:— | SHA256:— | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019052020190521\index.dat | dat | |
MD5:— | SHA256:— | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso652.tmp | html | |
MD5:A8934077843220A8E31367C7BBE15E6C | SHA256:A2DB0201D36F07F3F99D1ADF8B8EAFB9CF9BB803D024FCC9327B77AF56346861 | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{BD442E23-62BA-4ECE-B905-5A08211C70CF}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_DF6AEC759931714BBC50114133D9E43A.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
456 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
456 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |