| File name: | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe |
| Full analysis: | https://app.any.run/tasks/53469c96-2869-4946-bf96-5440fb26e117 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 07:43:06 |
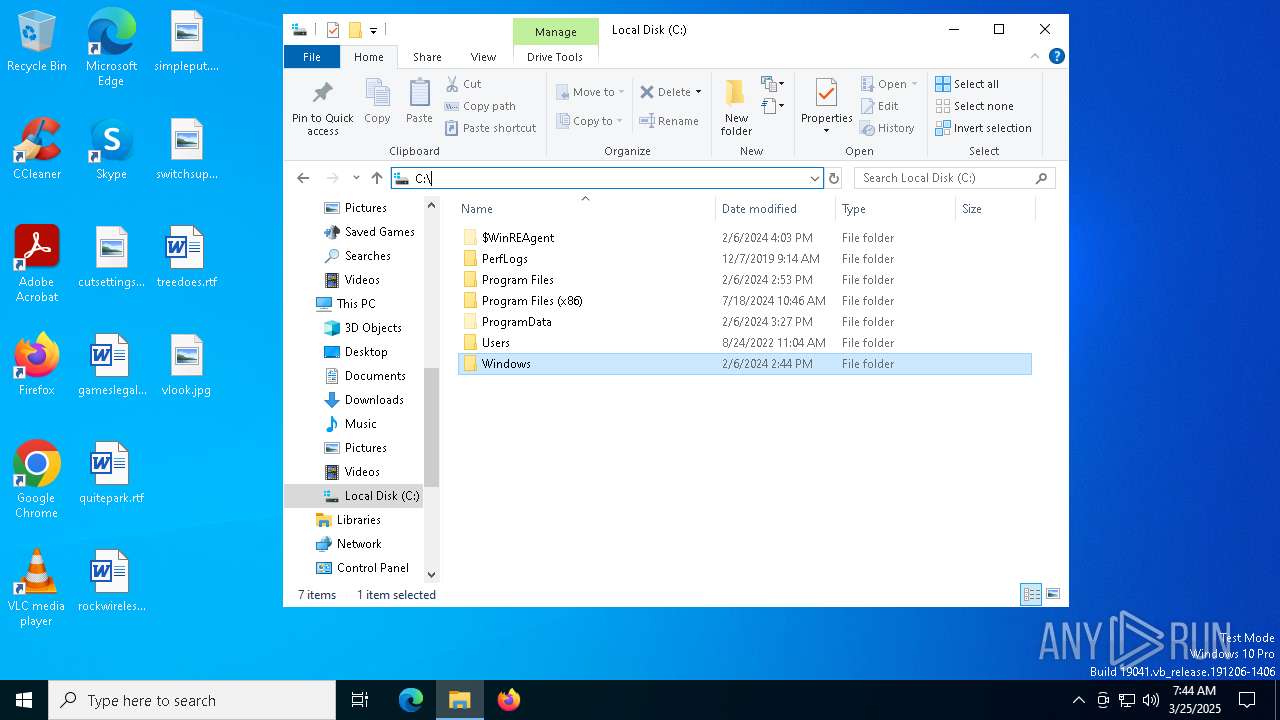
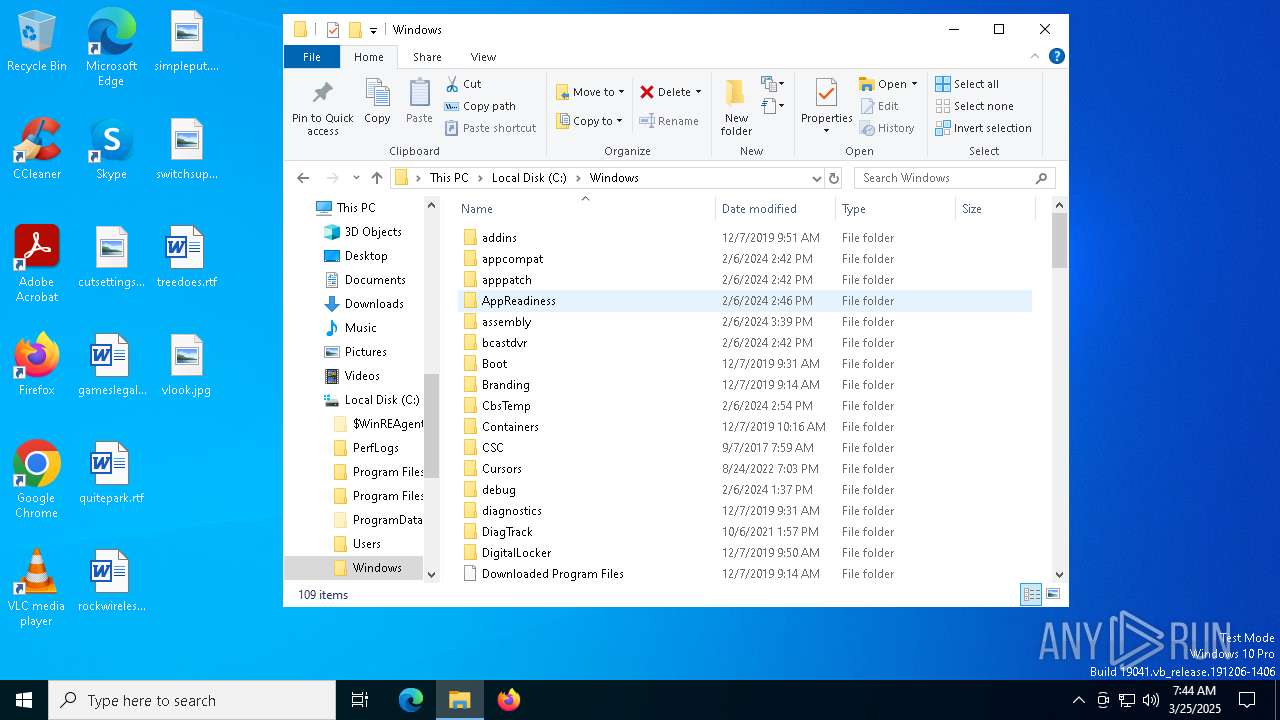
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | EC39BFAFAD4D23C05DF1FC8ACA56417C |
| SHA1: | 5970532C555493A01517561EE6C56E469B3E4059 |
| SHA256: | 7B6DAA6DD6784FF43B25227EBD54309F50CC282F3746FBE4099E00C59C5AB4BA |
| SSDEEP: | 98304:lYgV+Priwt9QoozCMuZzPYsm+9njNASgB+/8H4Q0RexxNKekjBc/ftK2rEhPDptO:IO49Zi5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
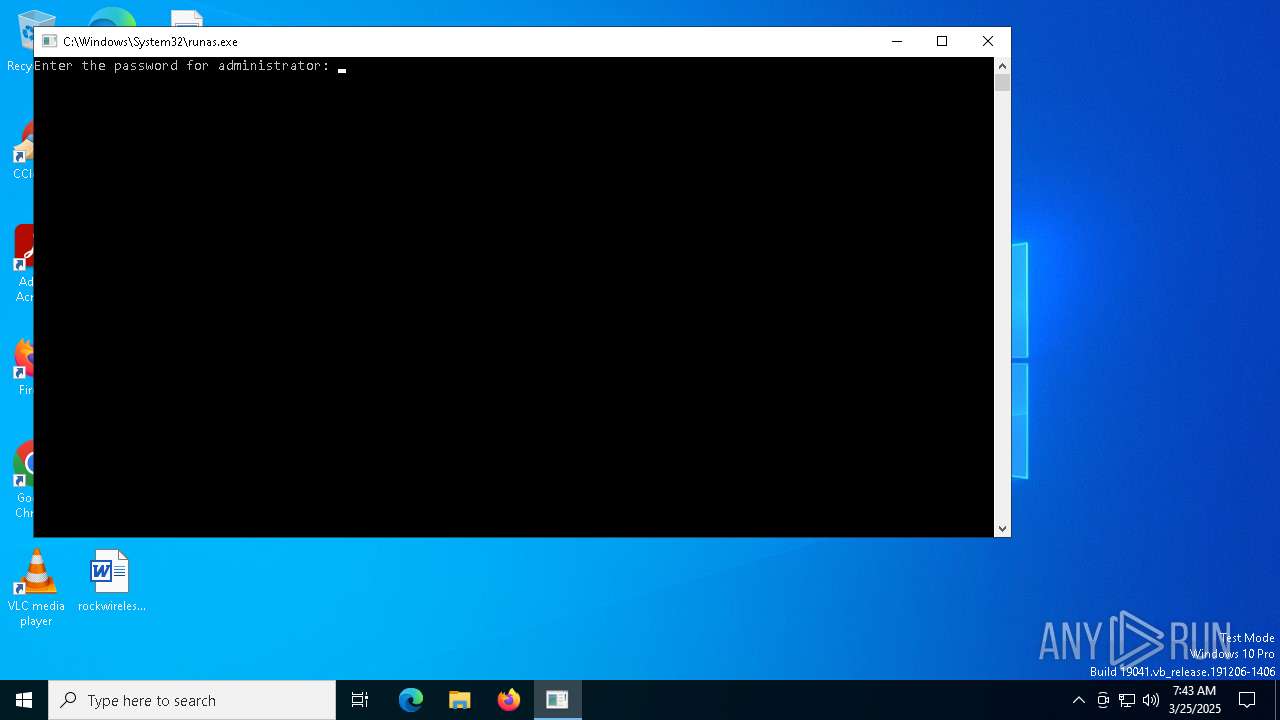
- runas.exe (PID: 7148)
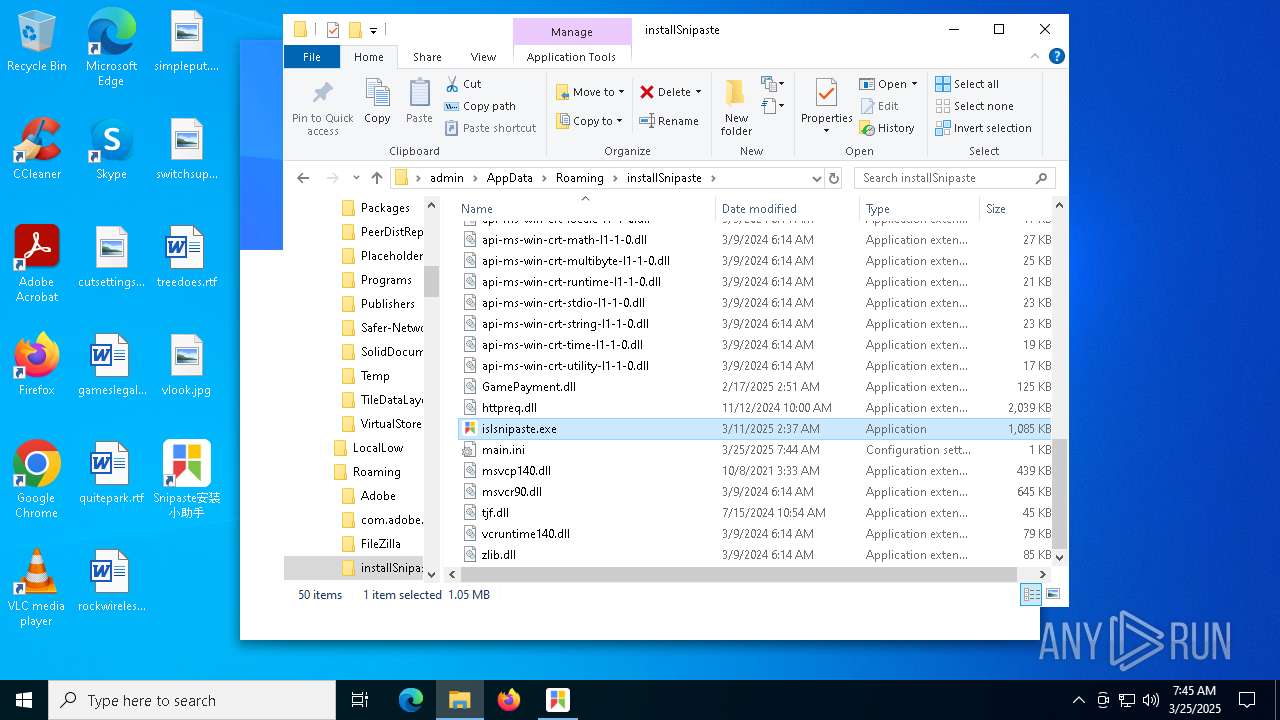
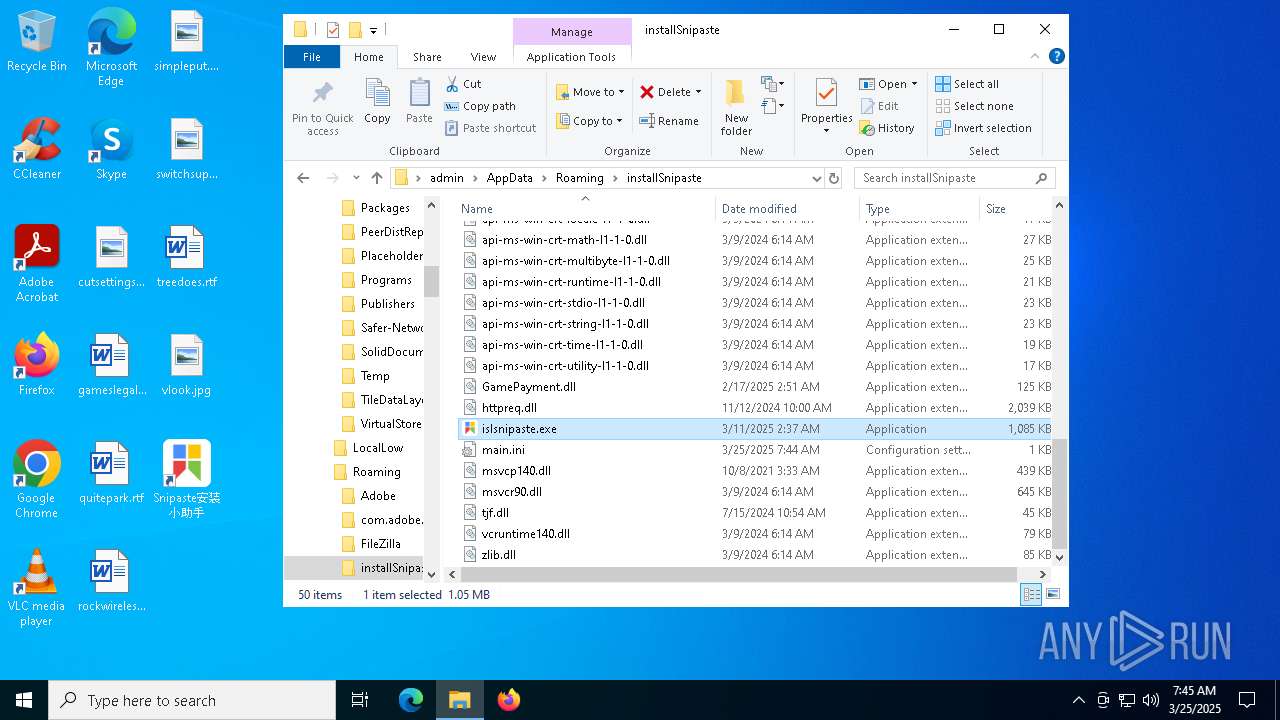
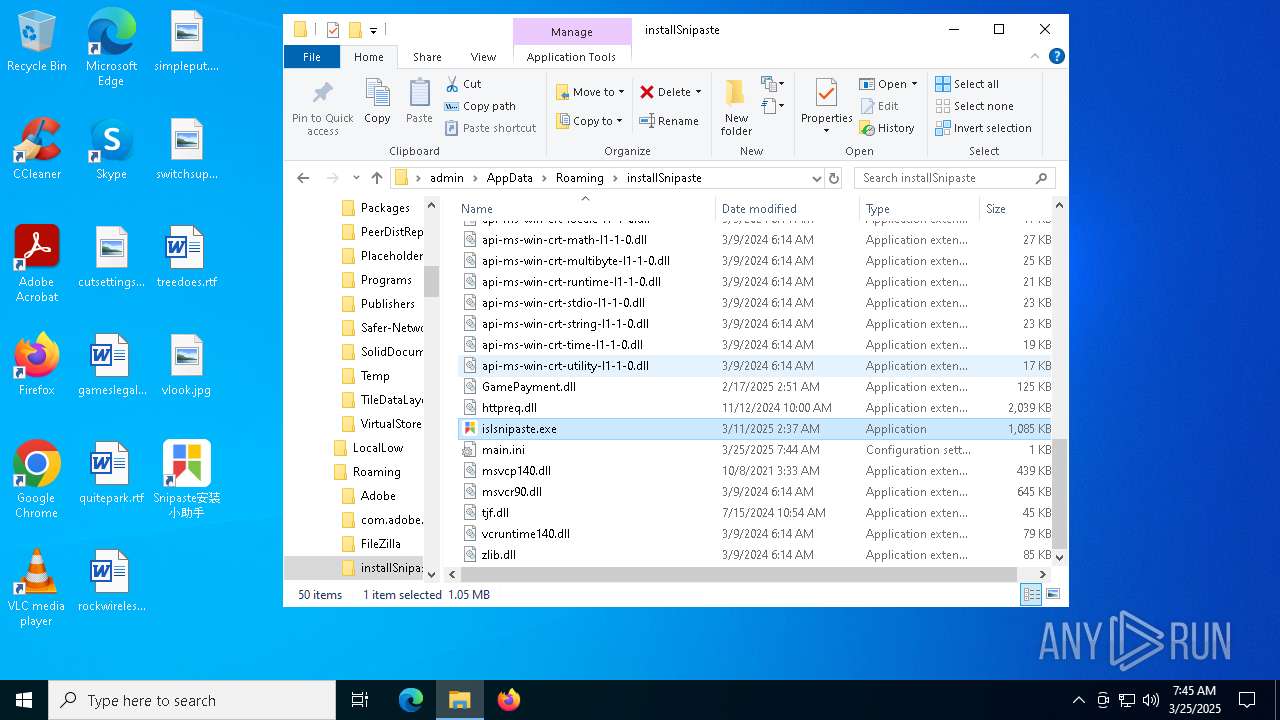
- islsnipaste.exe (PID: 5436)
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 7148)
Process drops legitimate windows executable
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
Executable content was dropped or overwritten
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
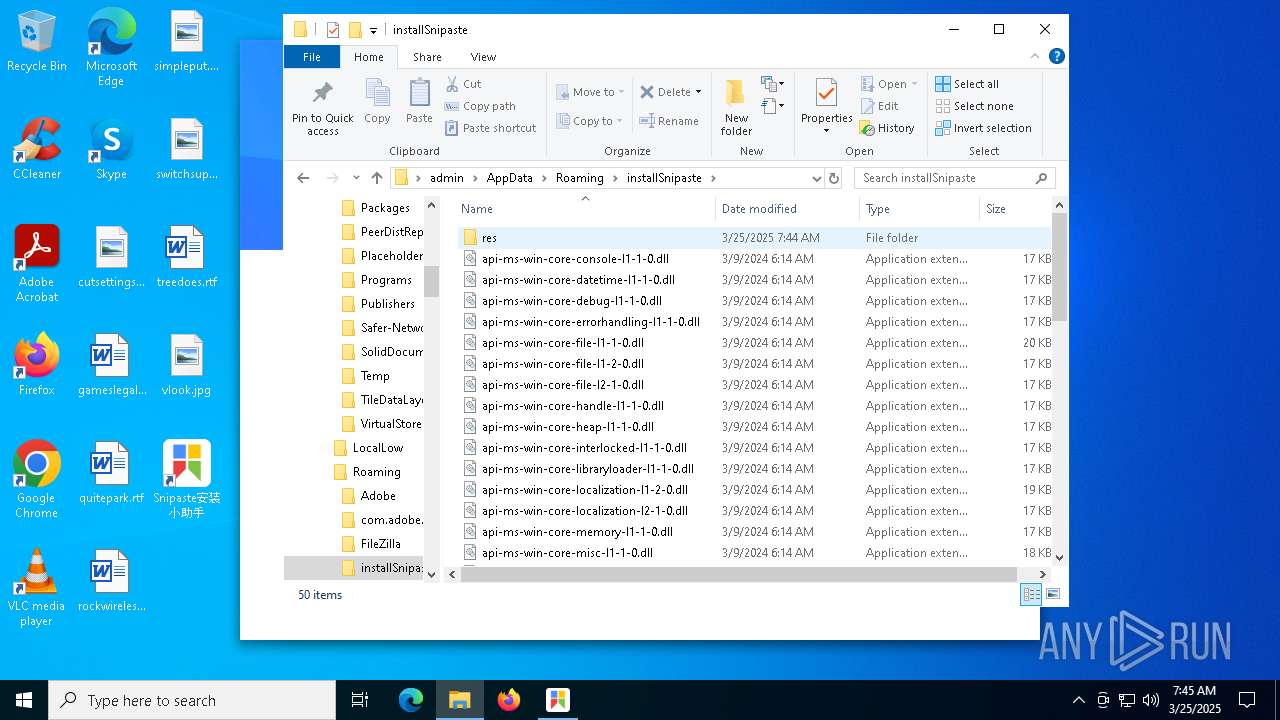
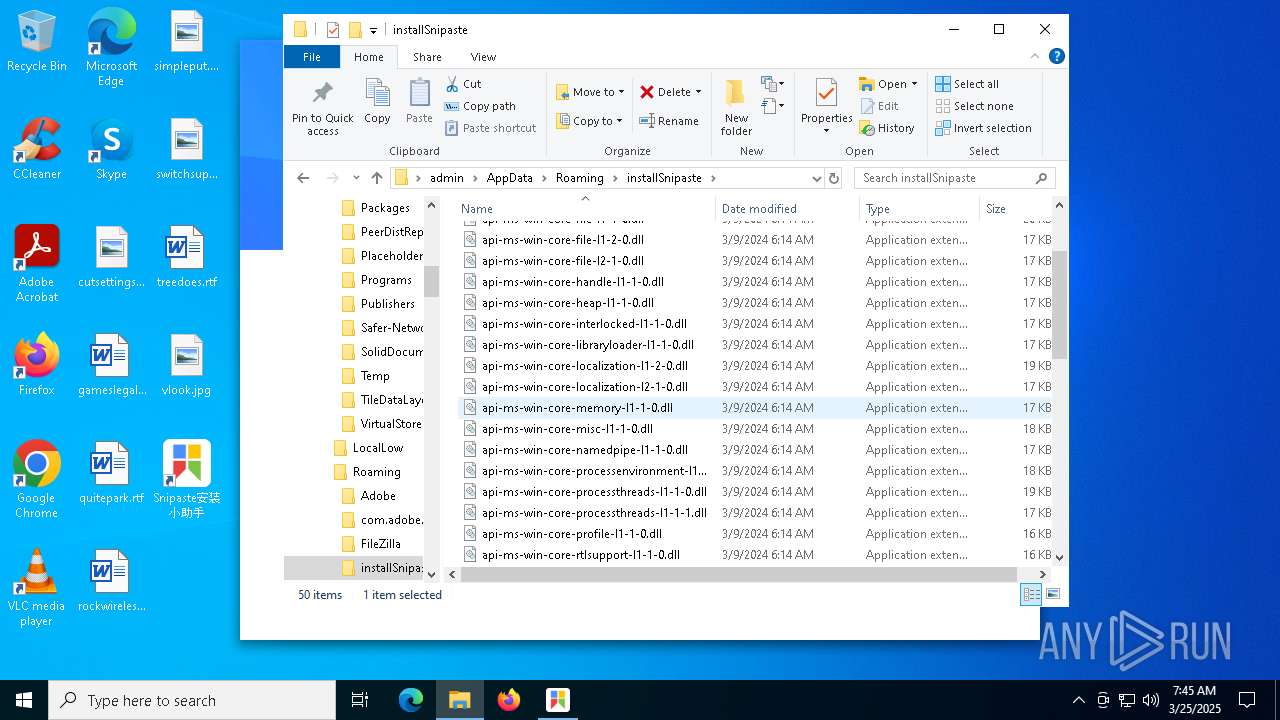
The process drops C-runtime libraries
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
INFO
Reads the software policy settings
- slui.exe (PID: 6972)
- slui.exe (PID: 3768)
Checks supported languages
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
- islsnipaste.exe (PID: 5436)
- islsnipaste.exe (PID: 6132)
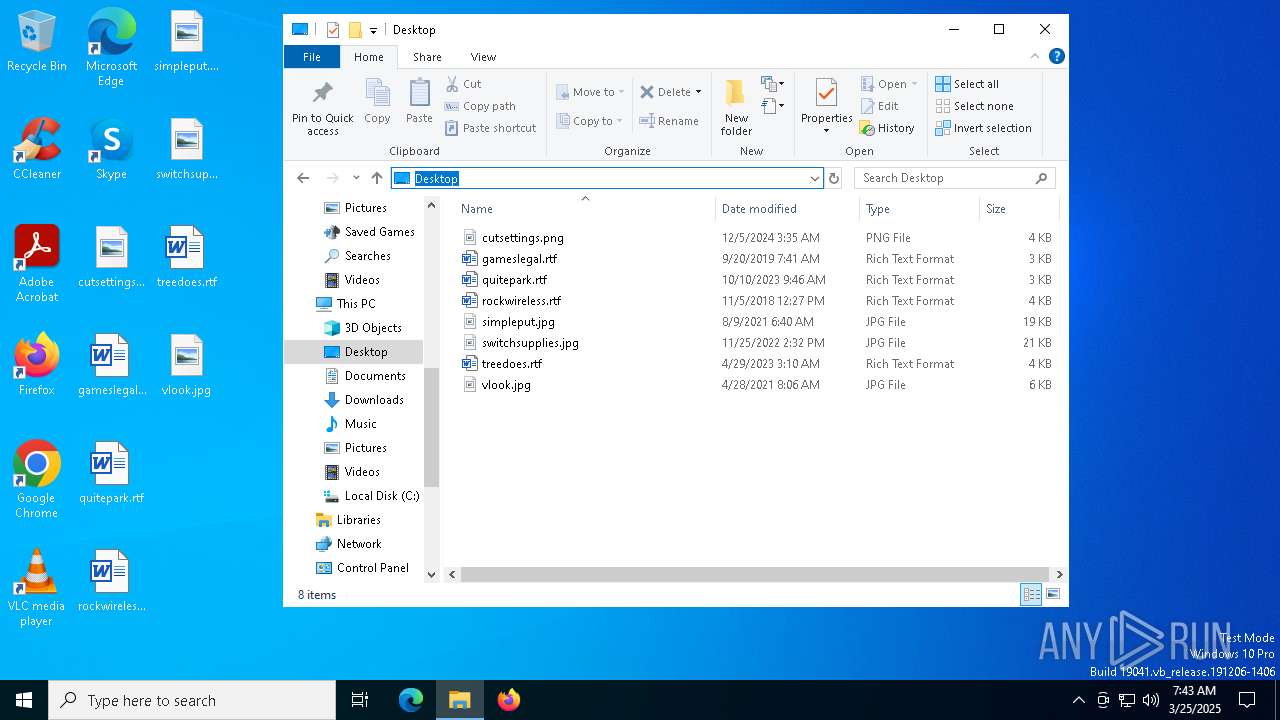
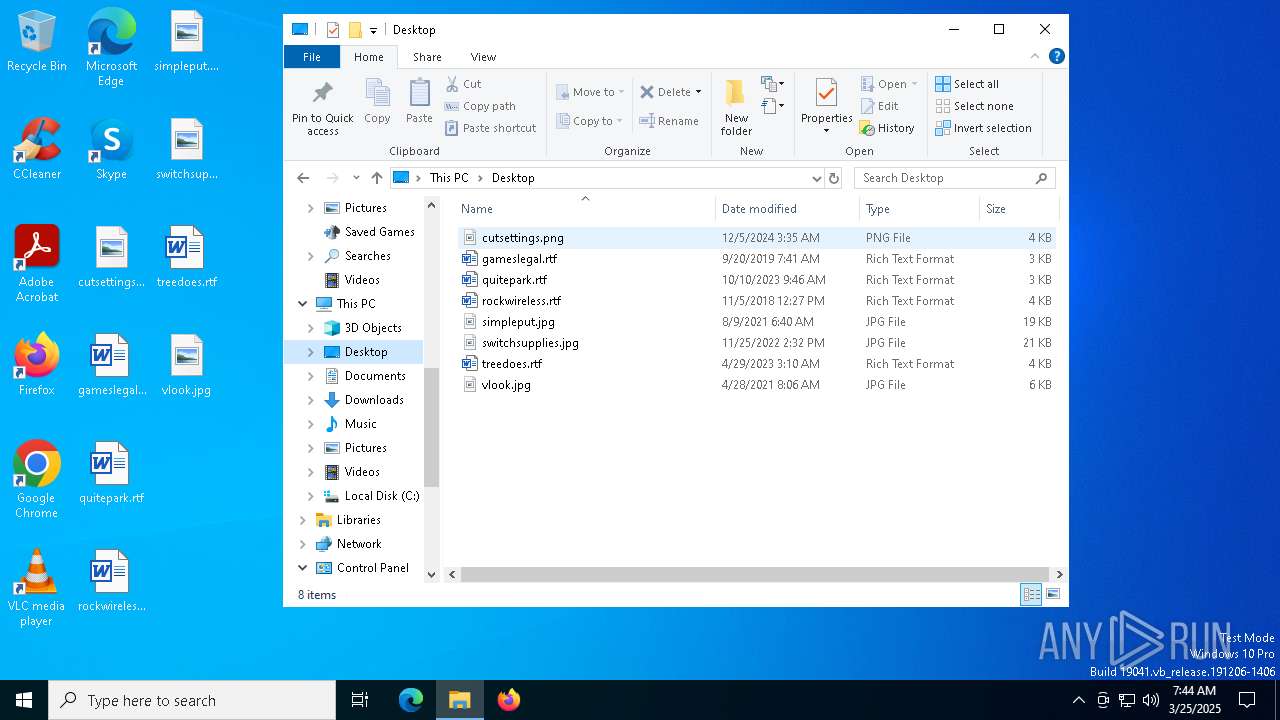
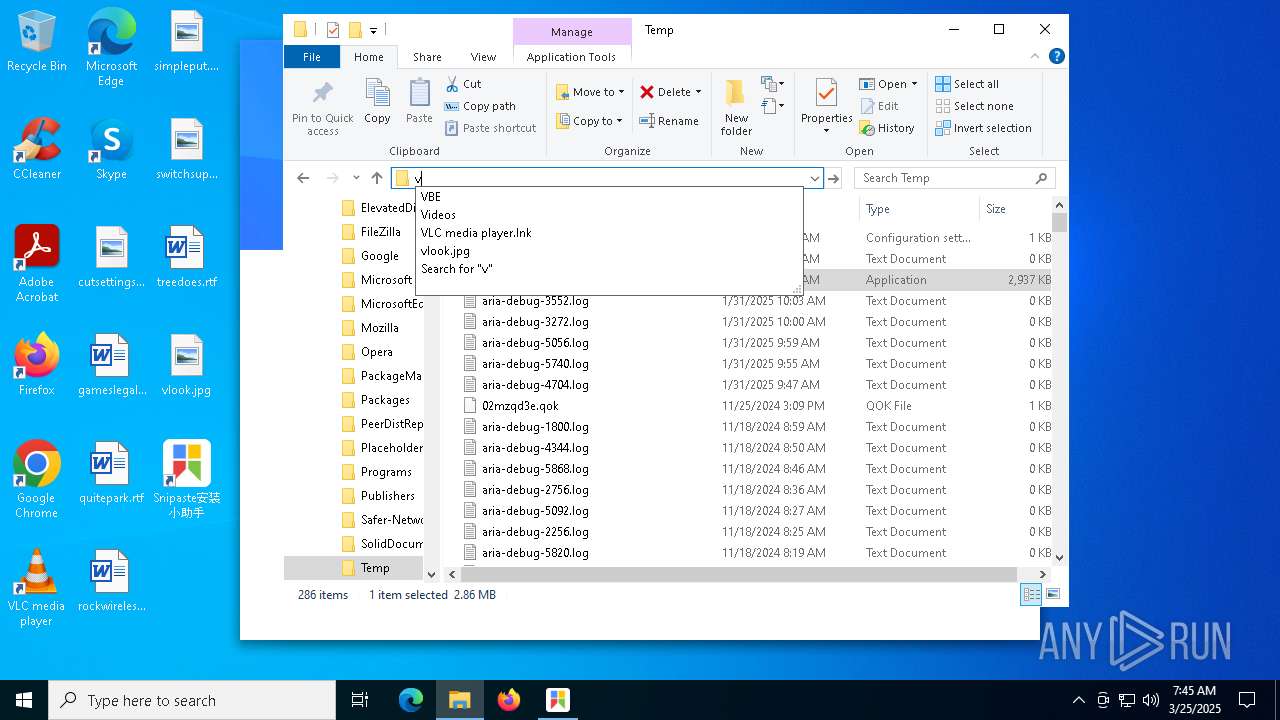
Manual execution by a user
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
- islsnipaste.exe (PID: 6132)
- WinRAR.exe (PID: 3396)
The sample compiled with chinese language support
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
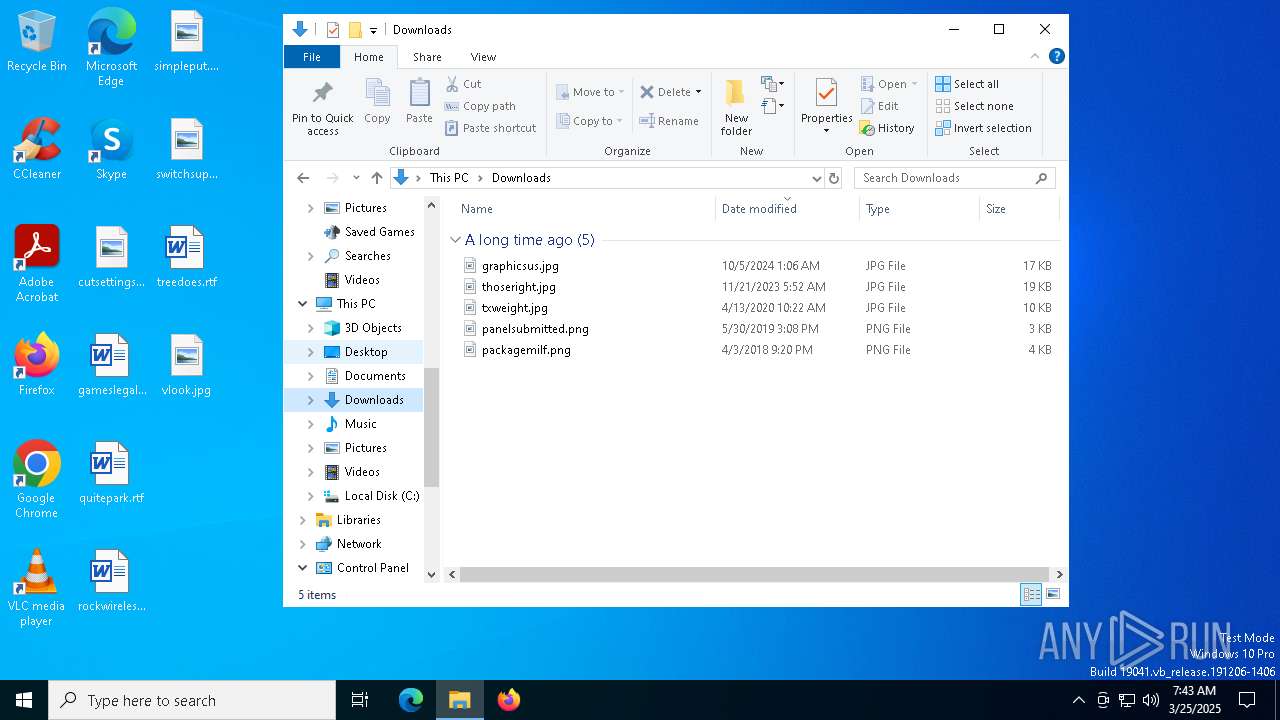
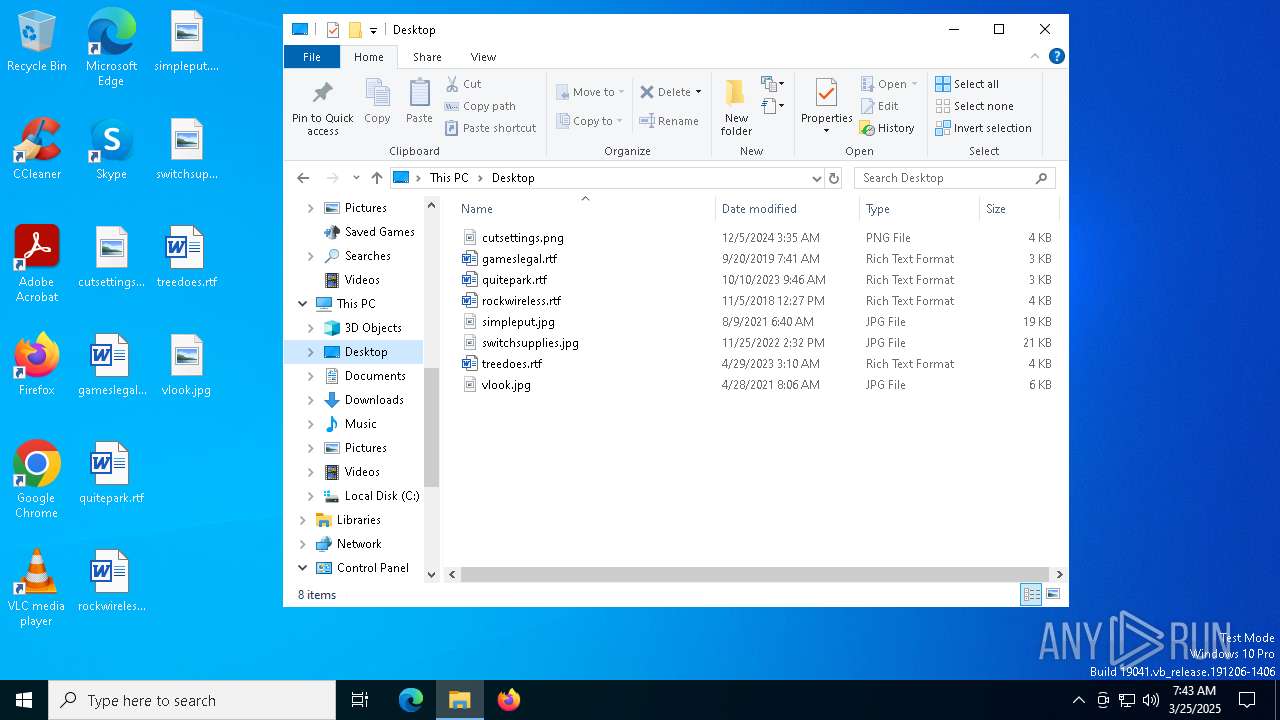
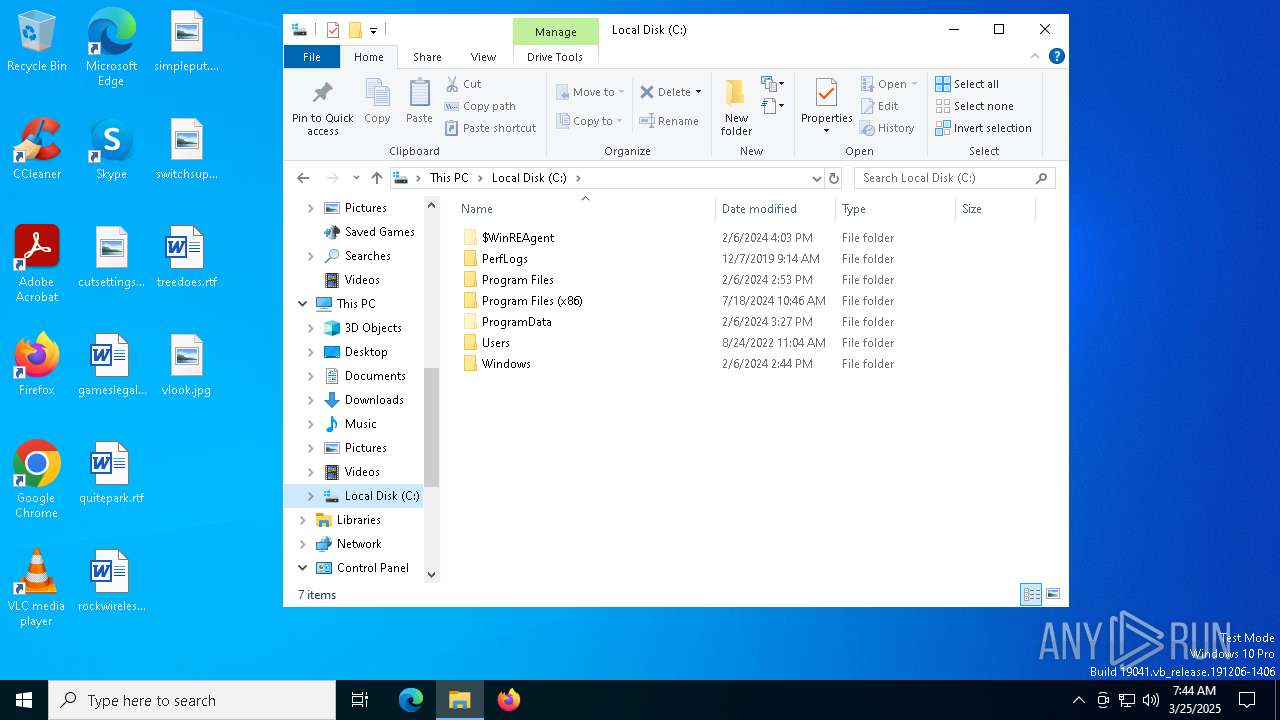
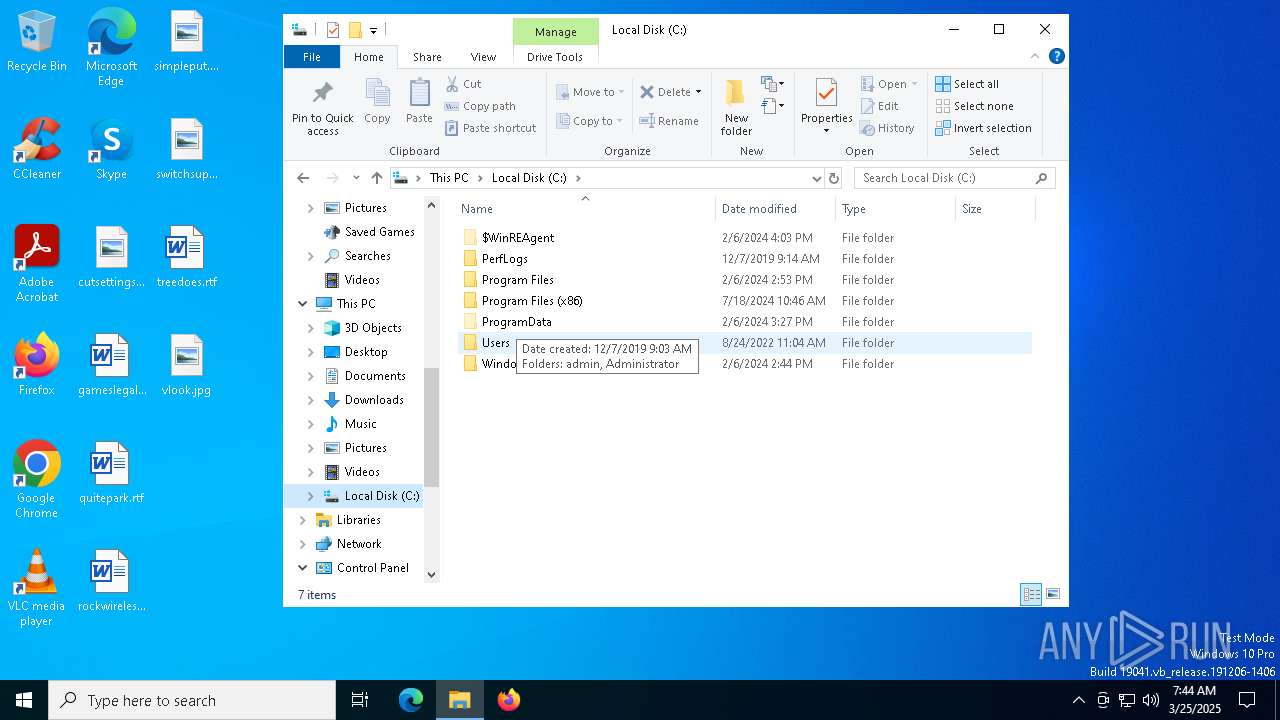
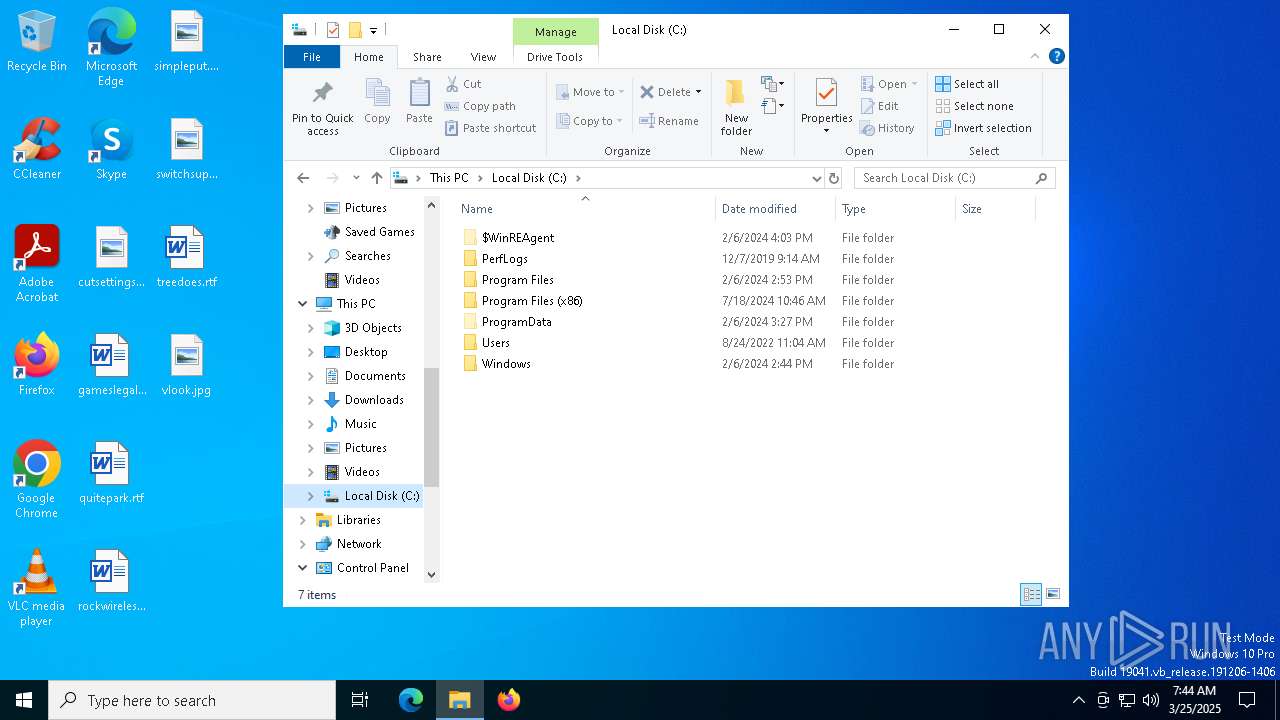
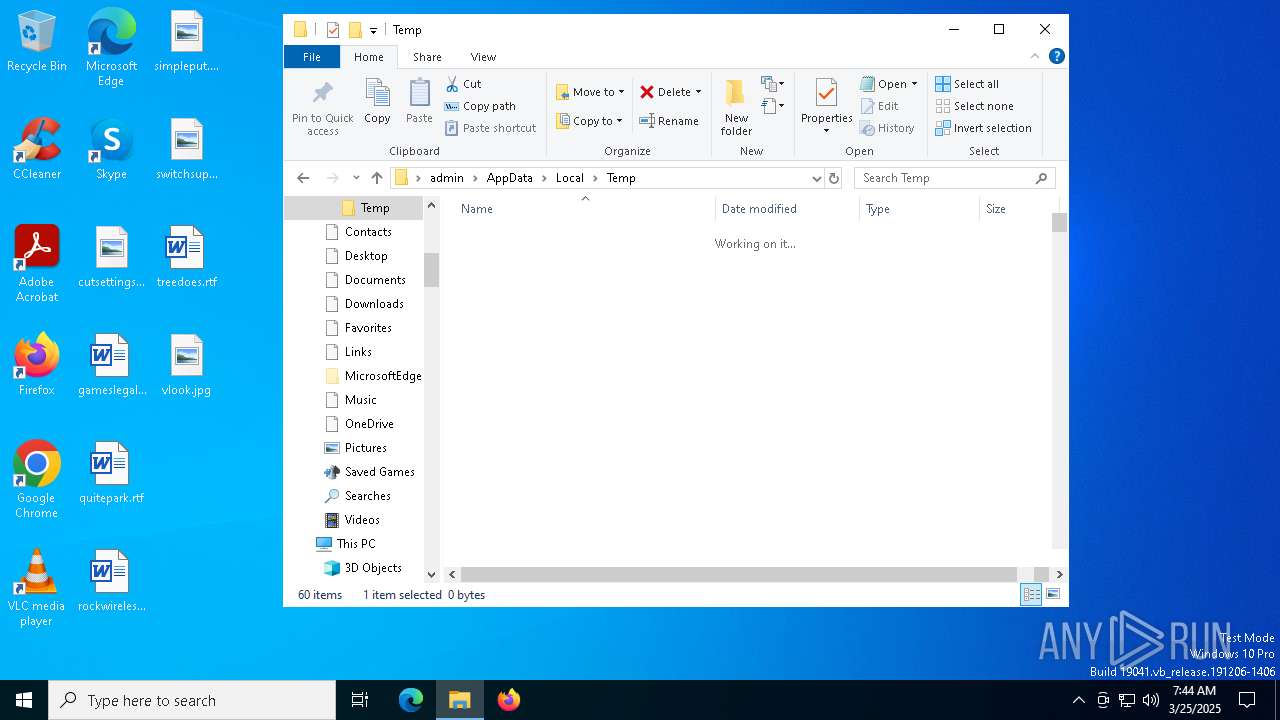
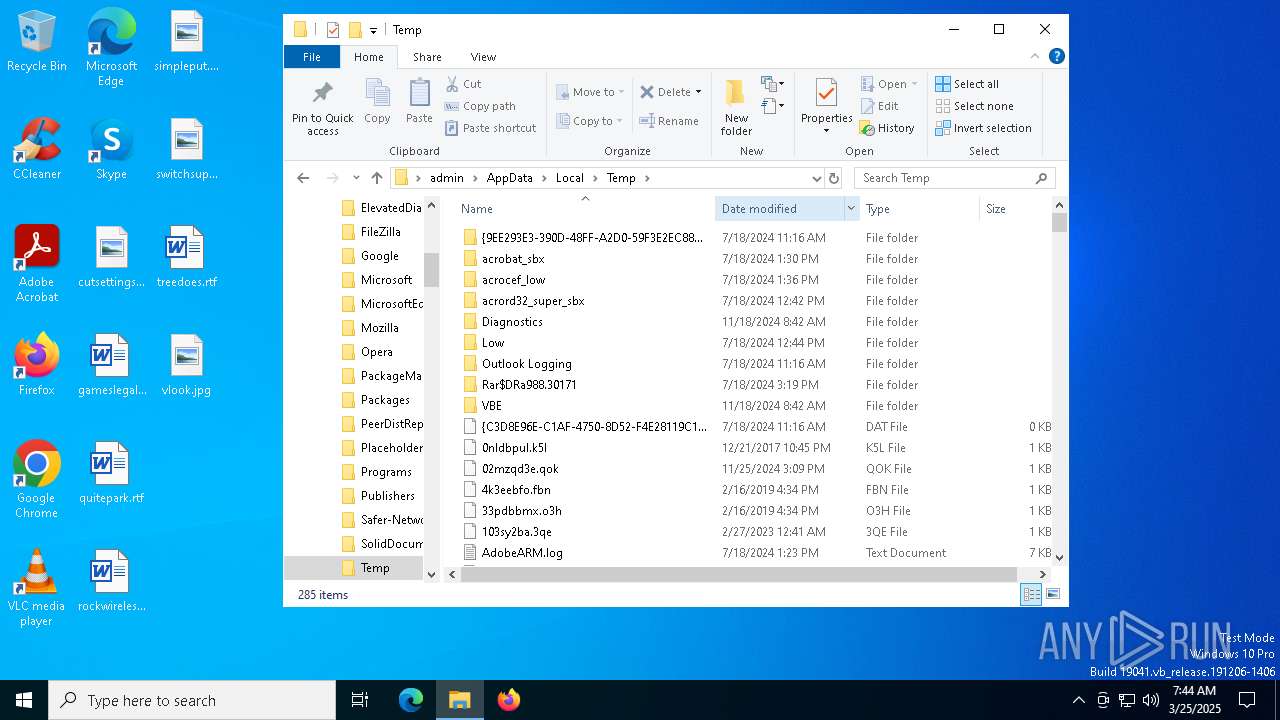
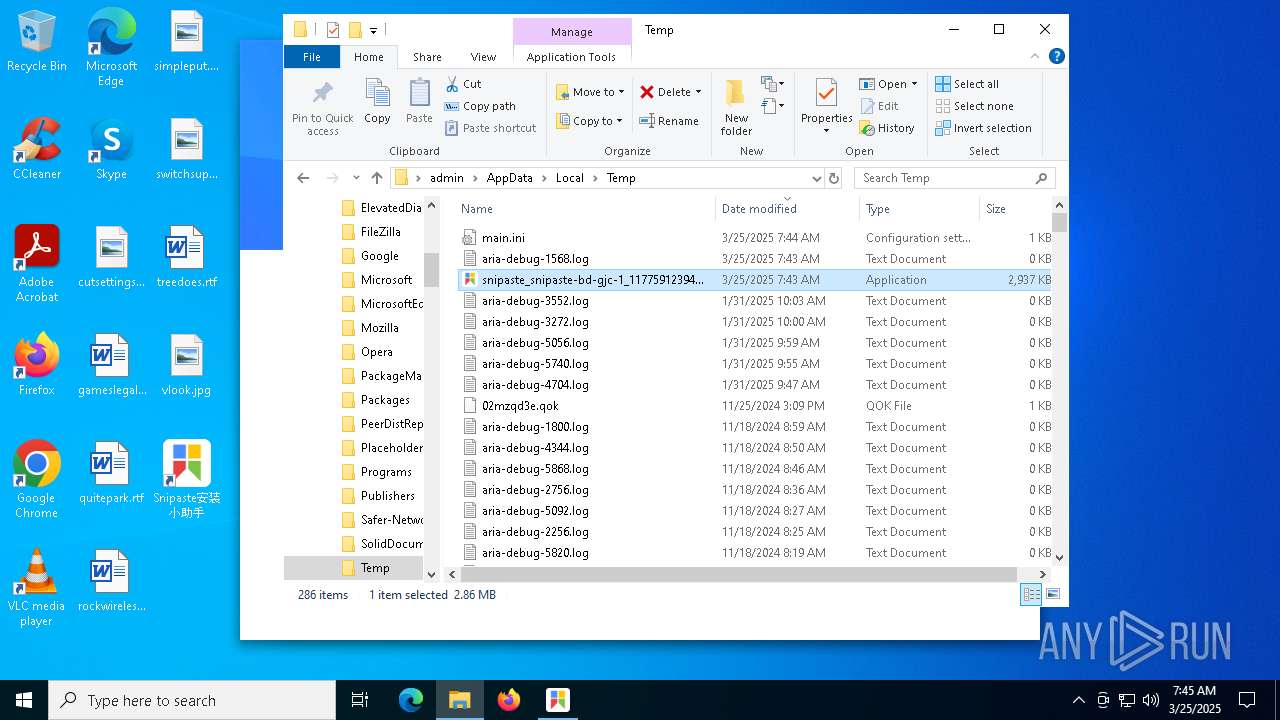
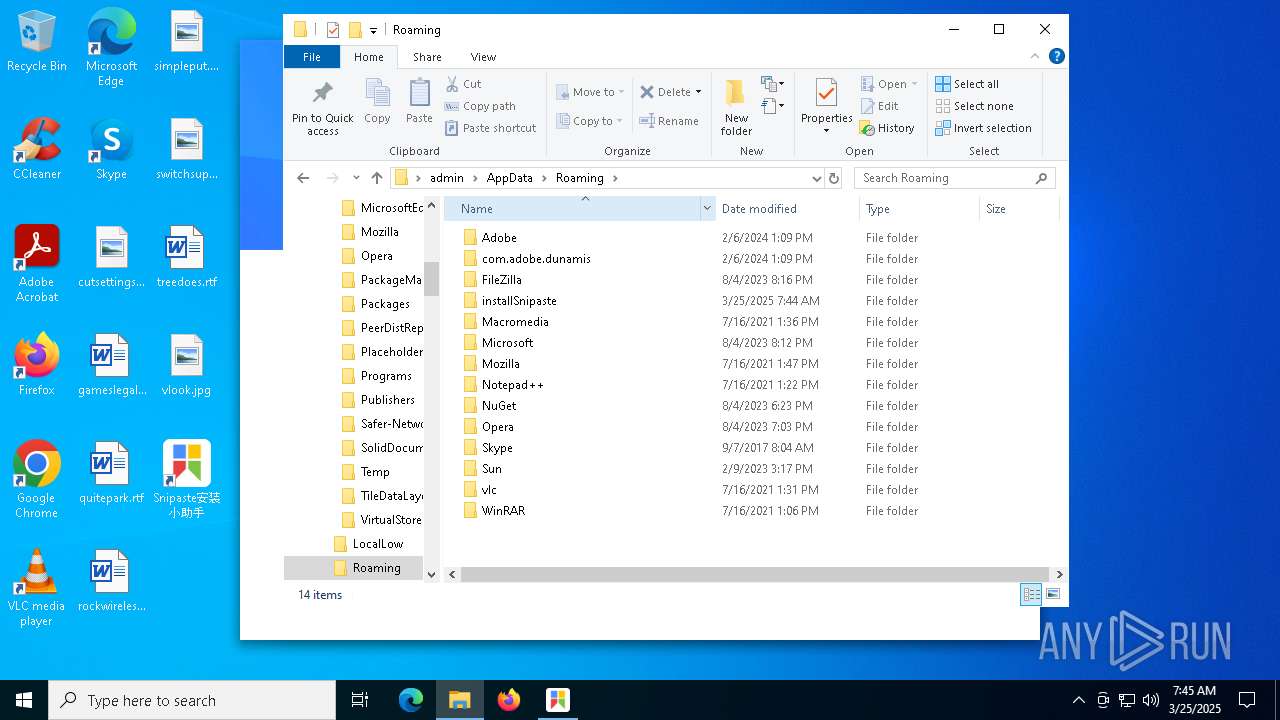
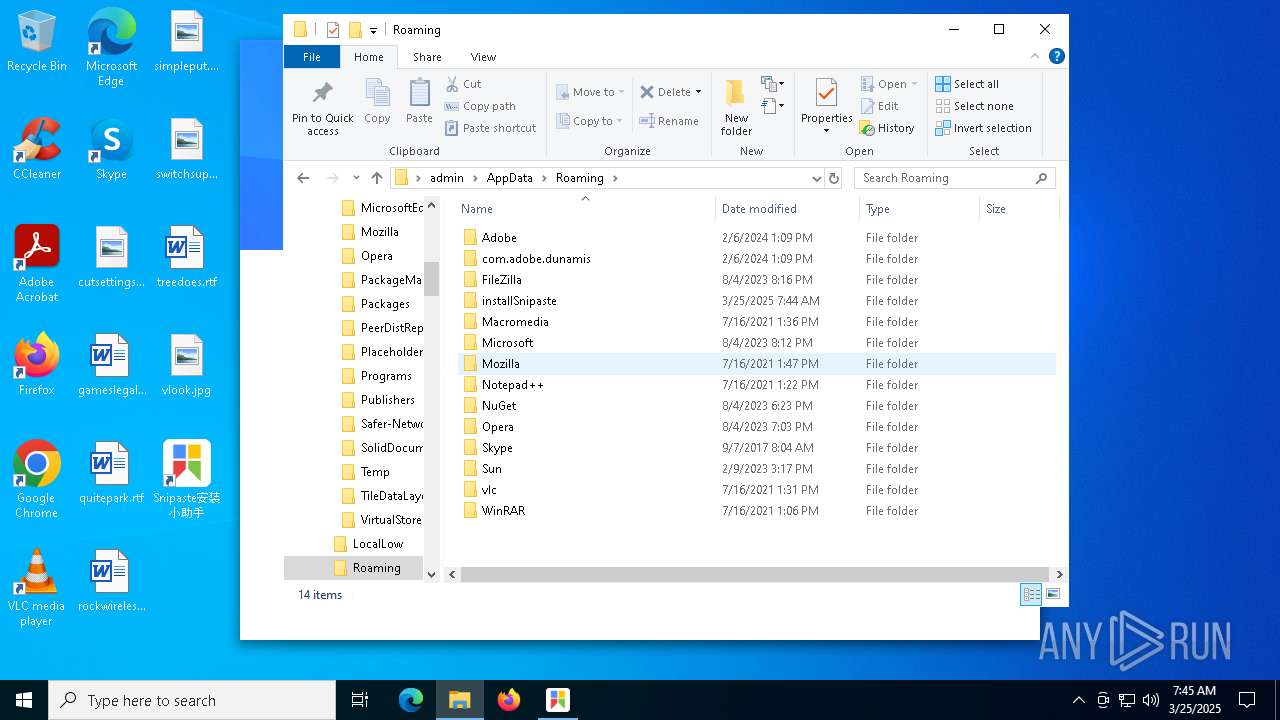
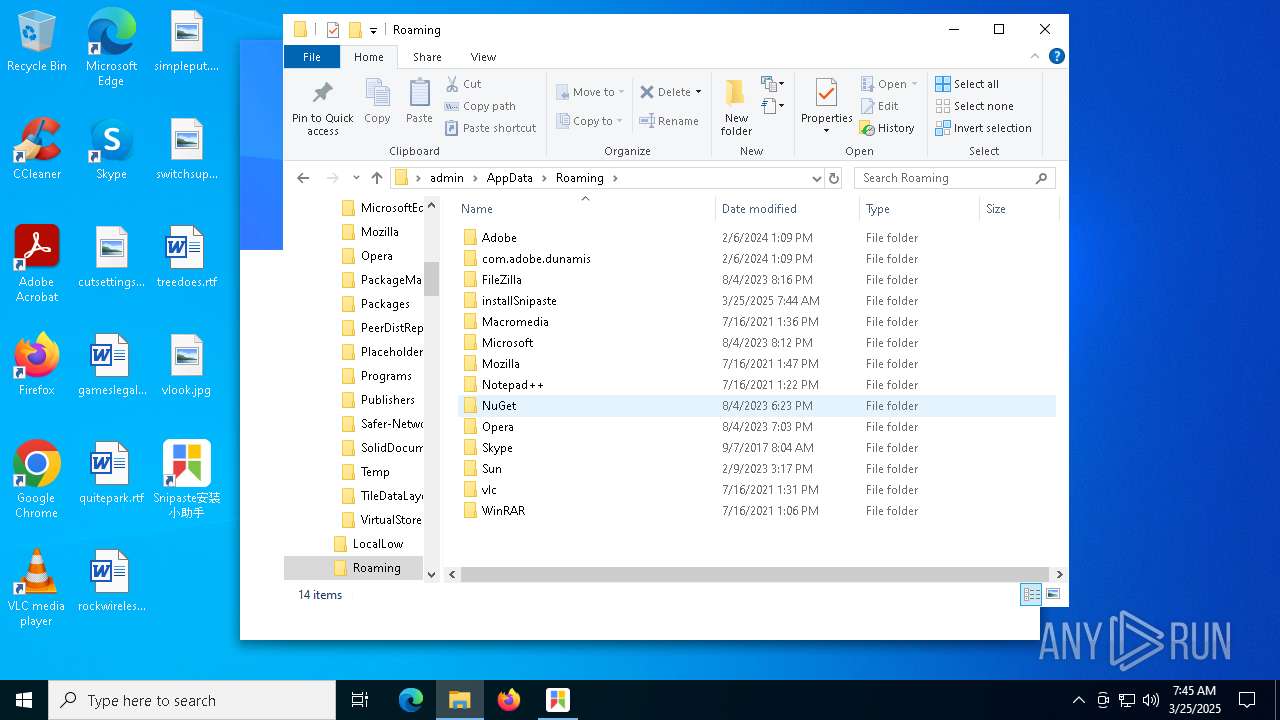
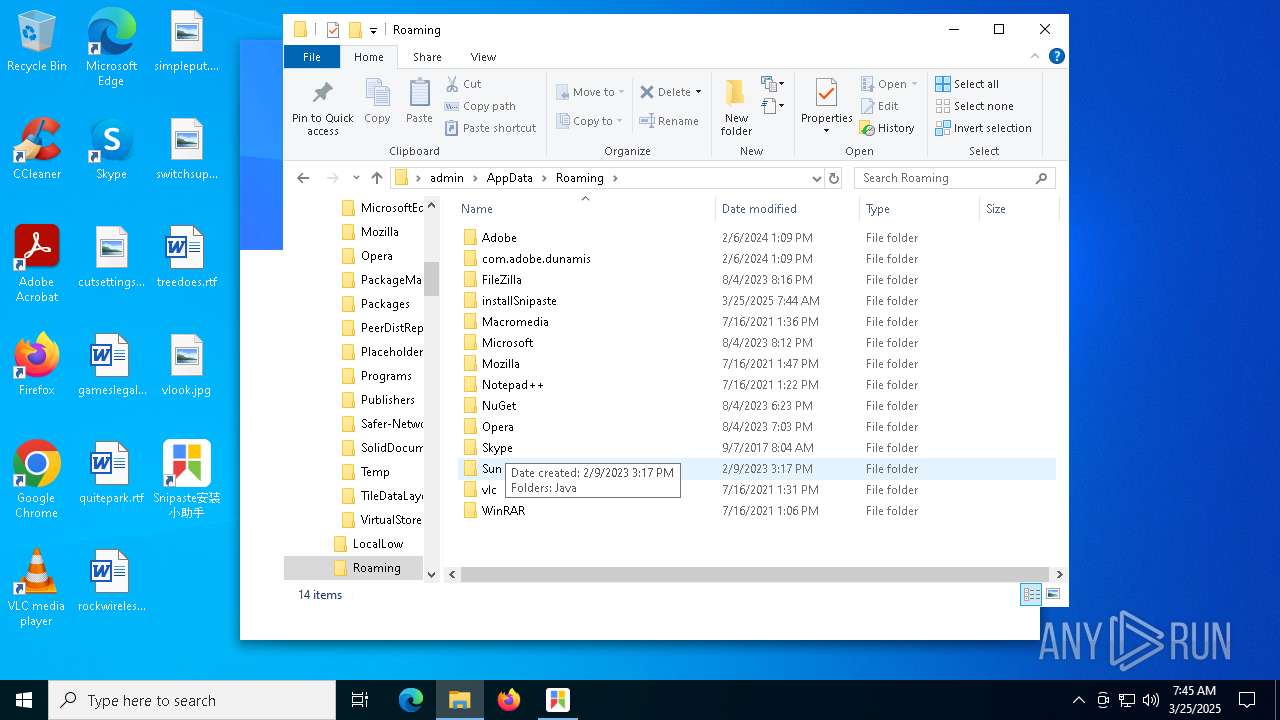
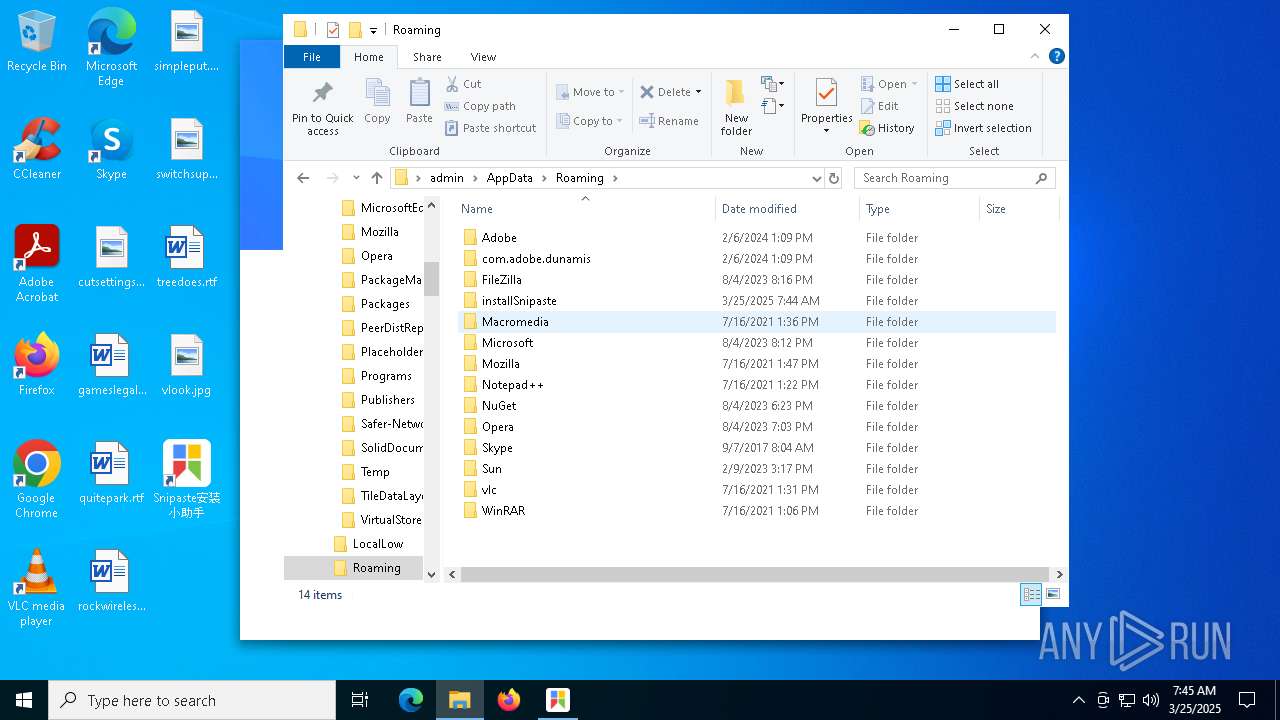
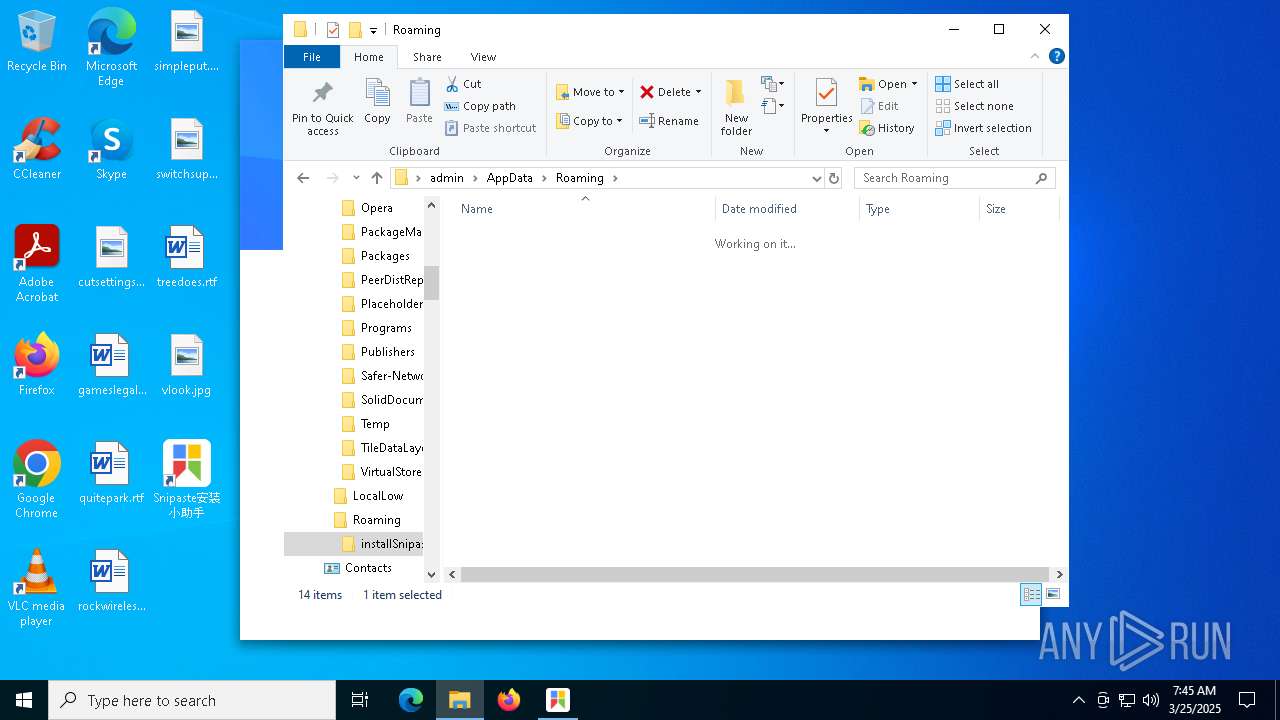
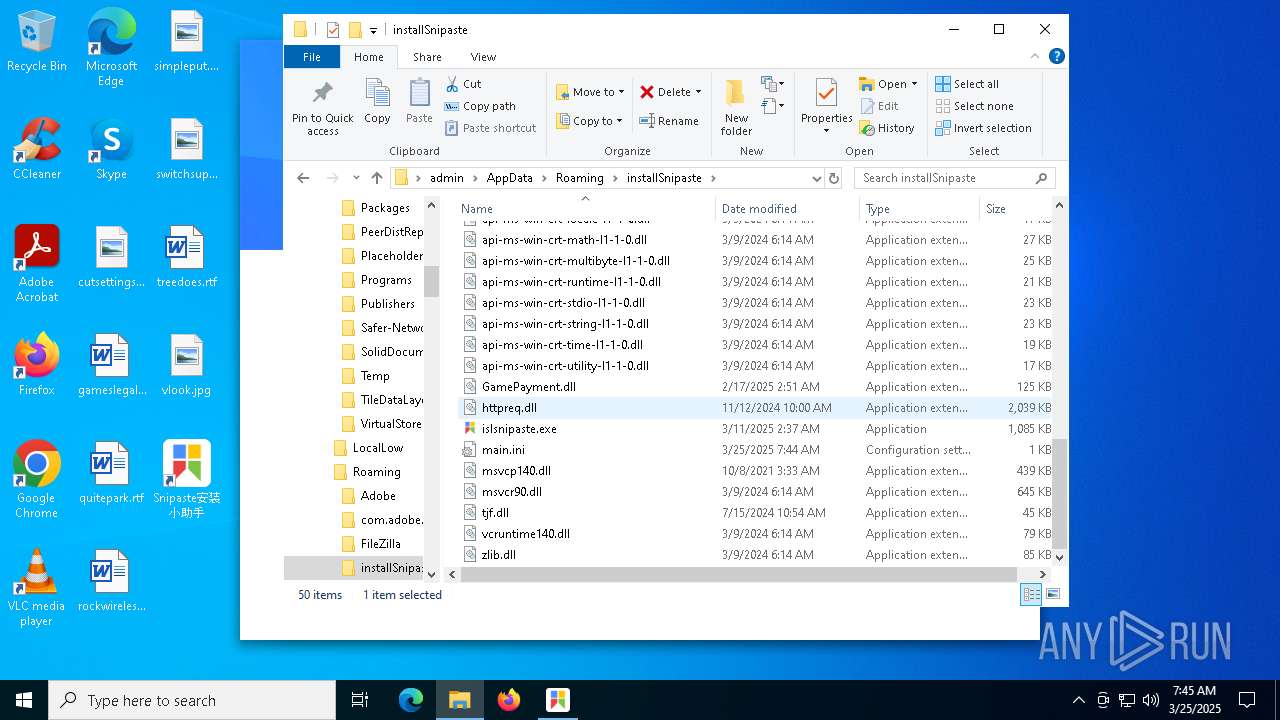
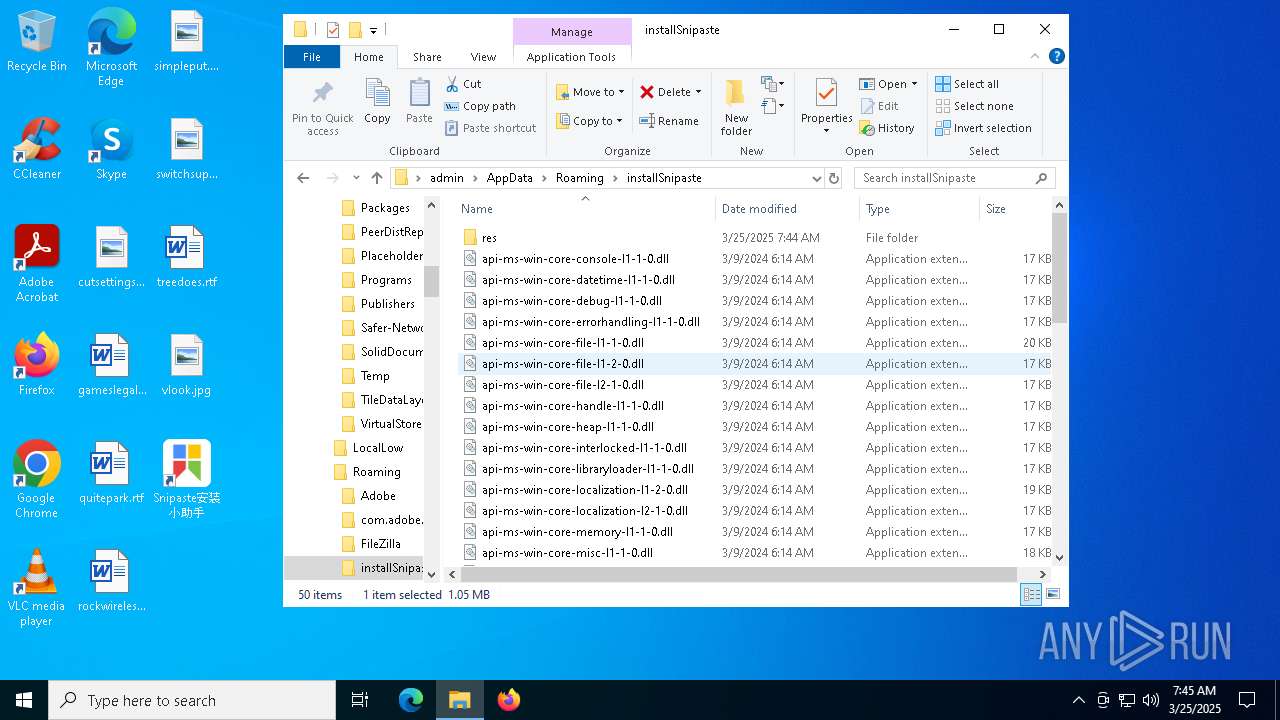
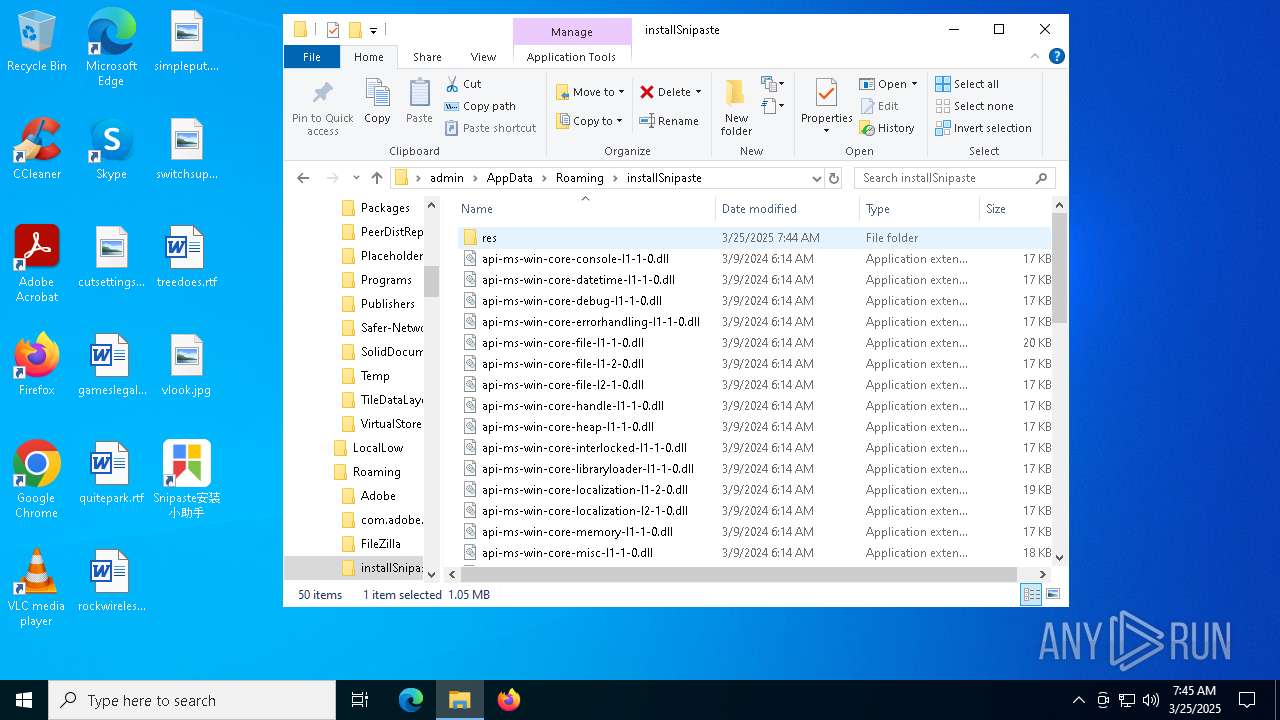
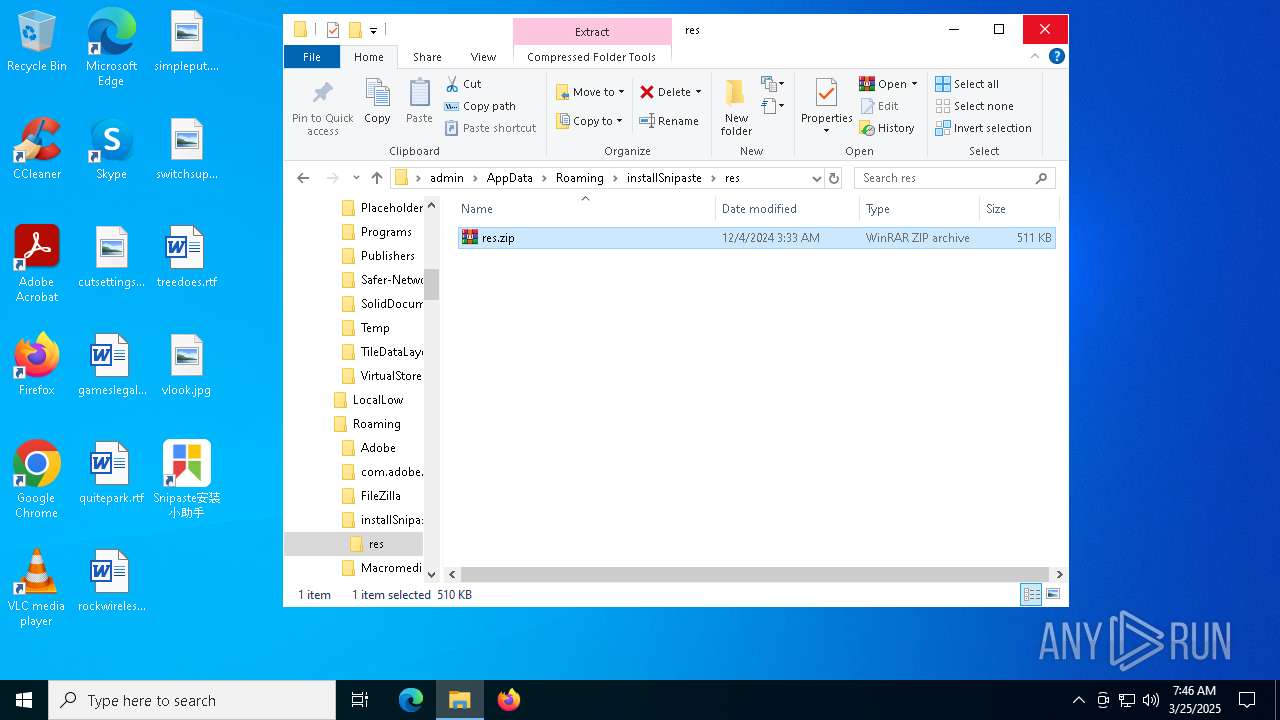
Creates files or folders in the user directory
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
- islsnipaste.exe (PID: 5436)
Reads the computer name
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
- islsnipaste.exe (PID: 5436)
The sample compiled with english language support
- snipaste_snipaste-bd-gjc-1_11775912394326794383.exe (PID: 3884)
- runas.exe (PID: 7148)
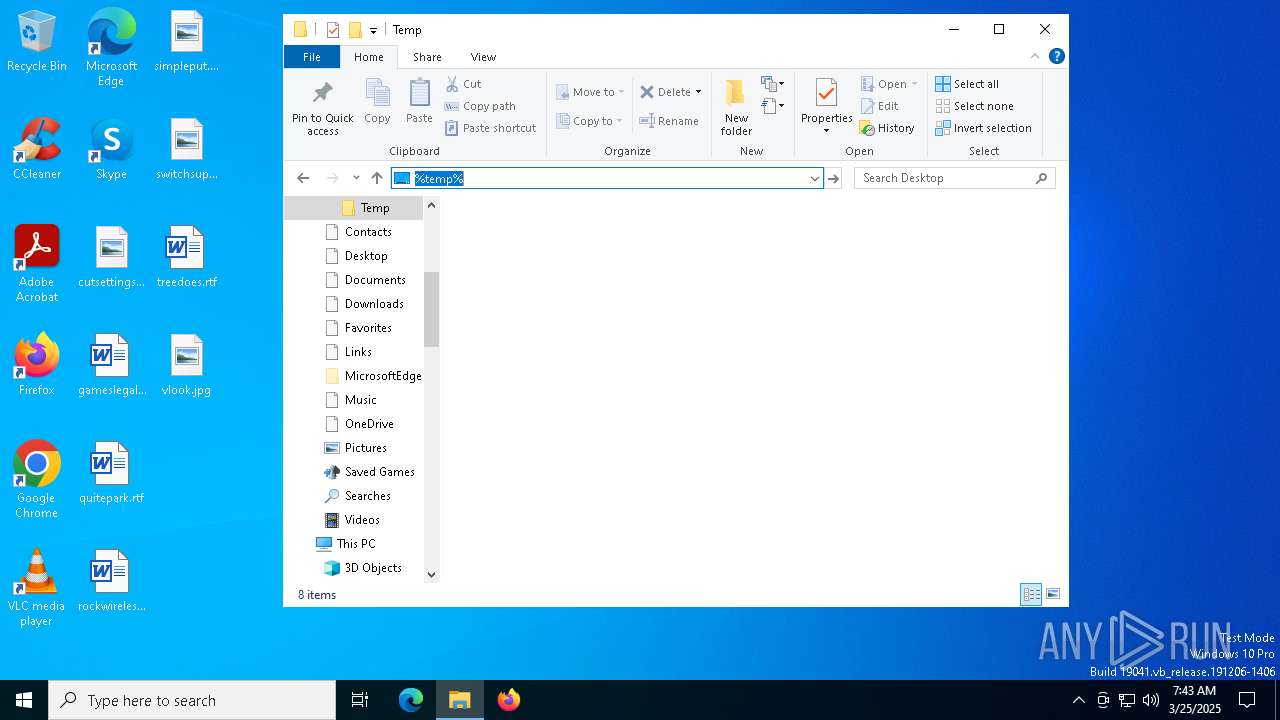
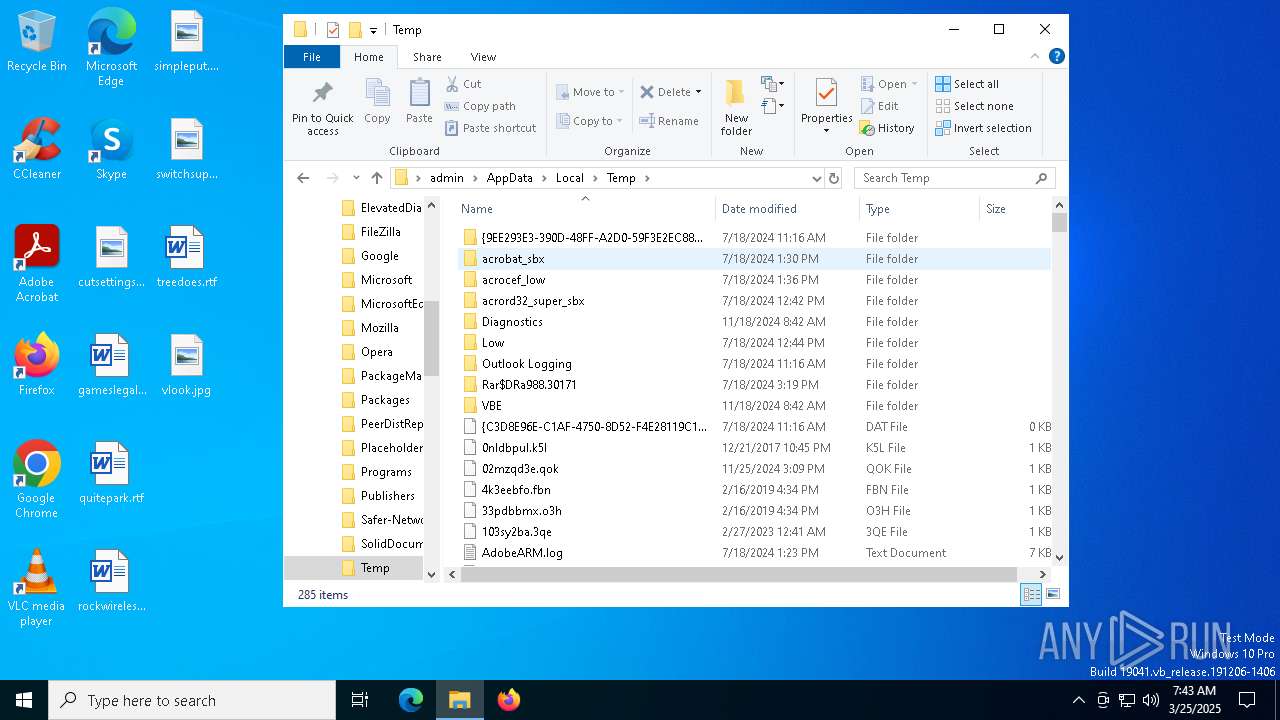
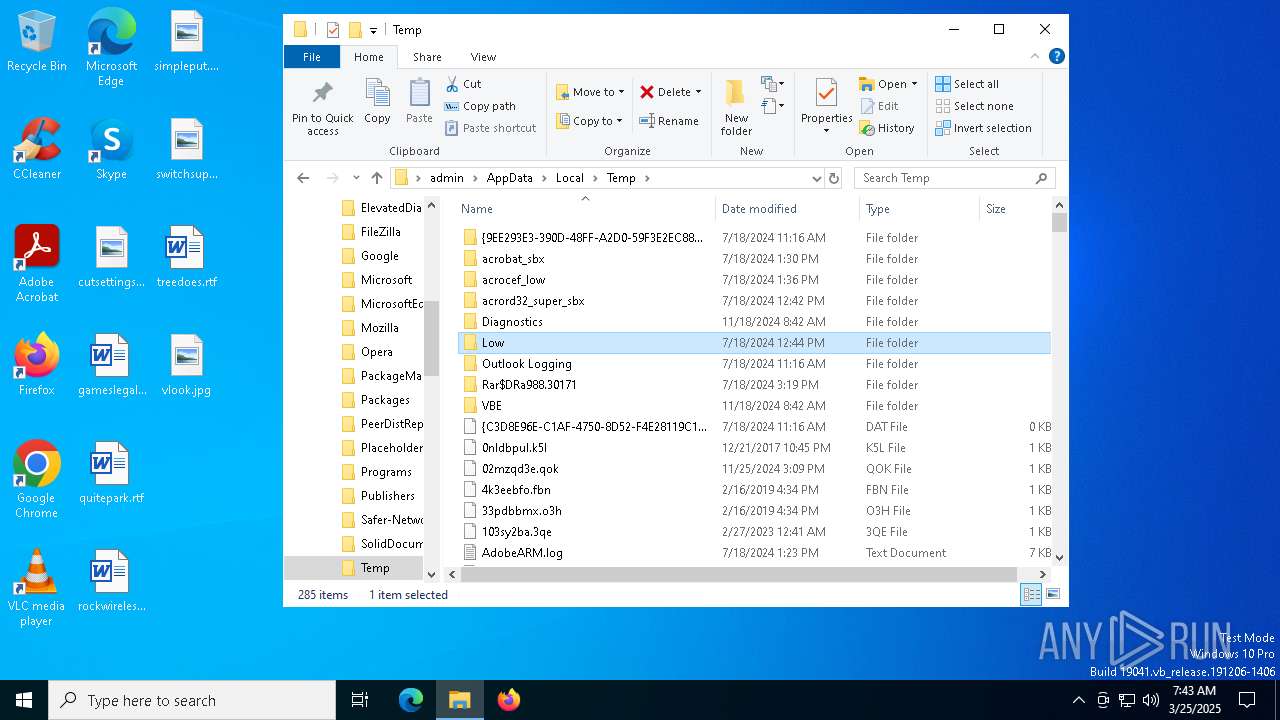
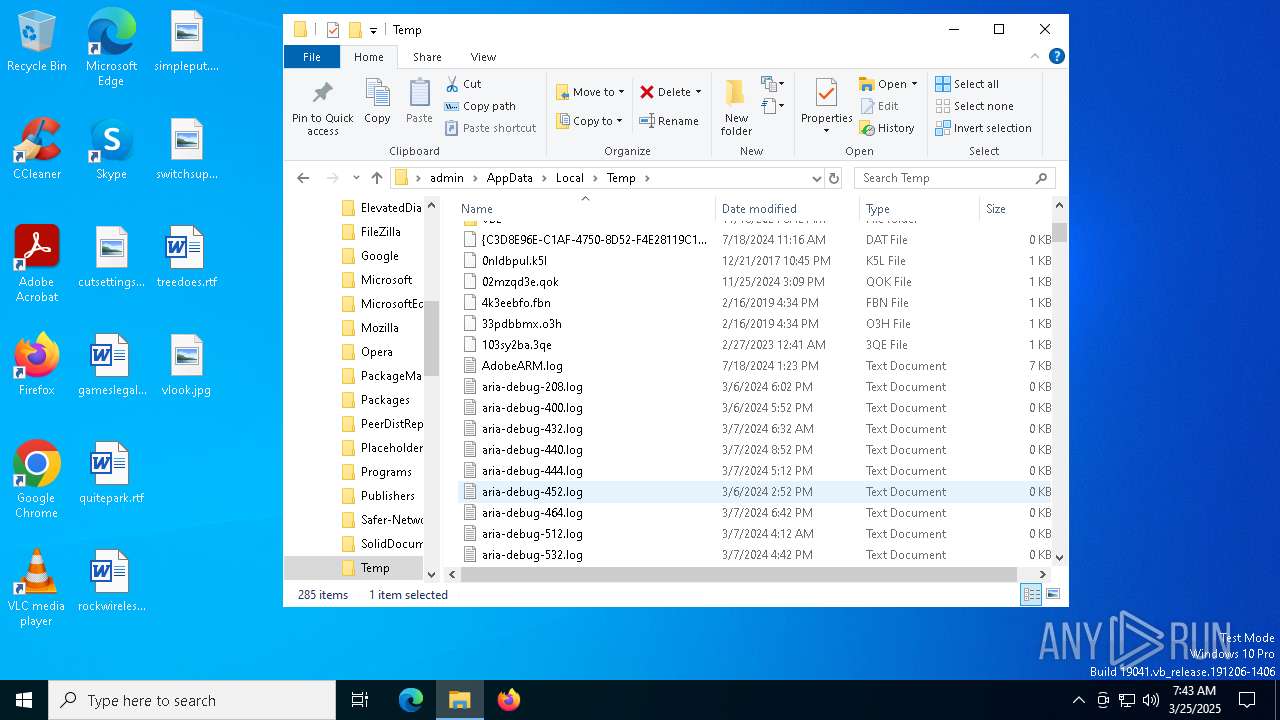
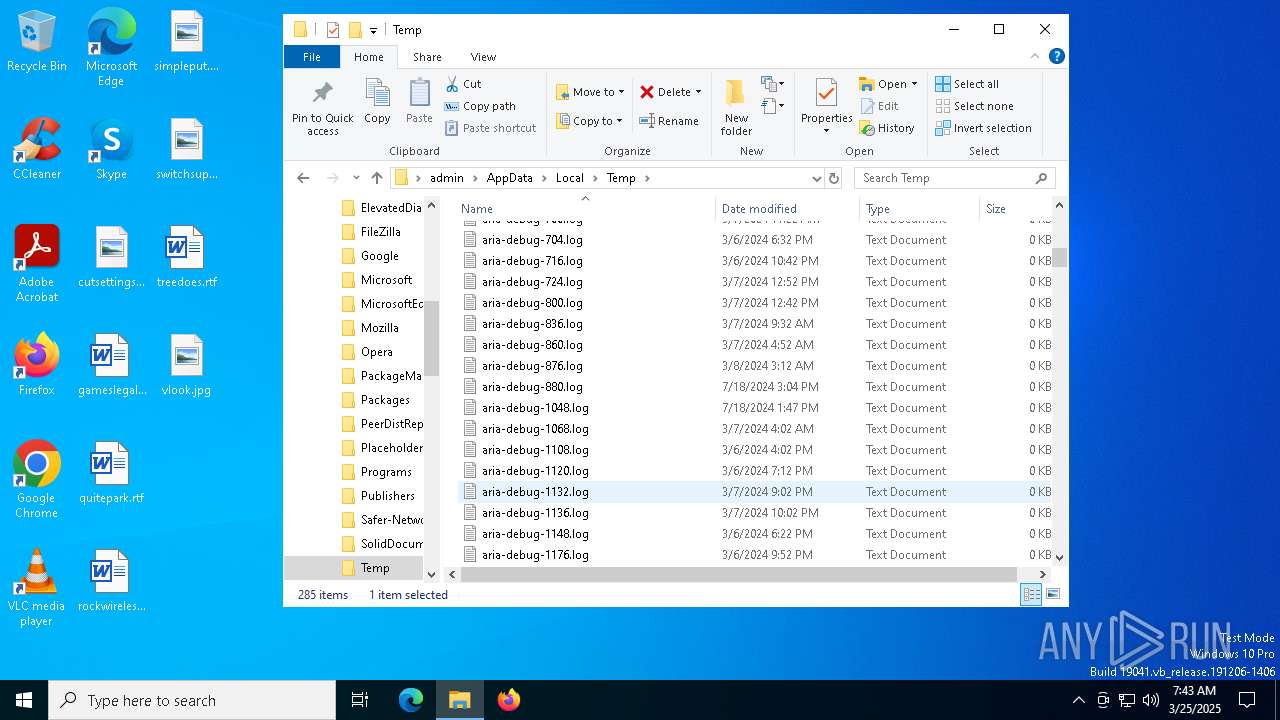
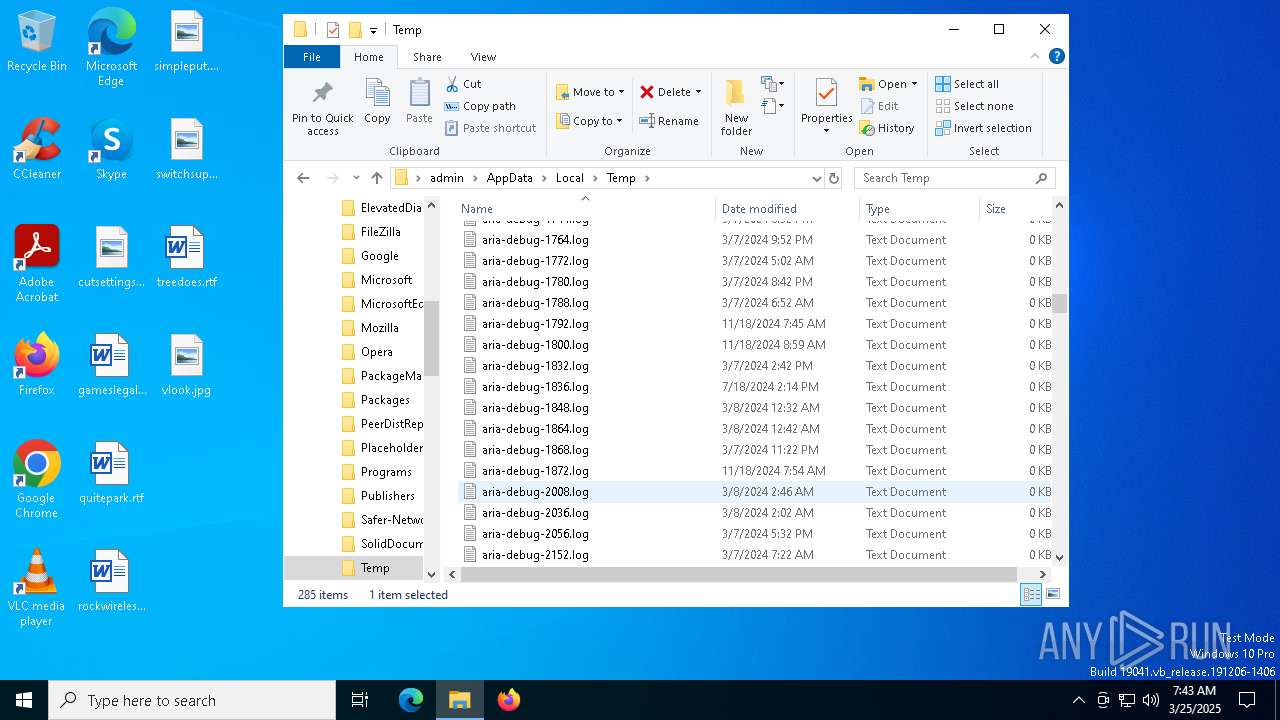
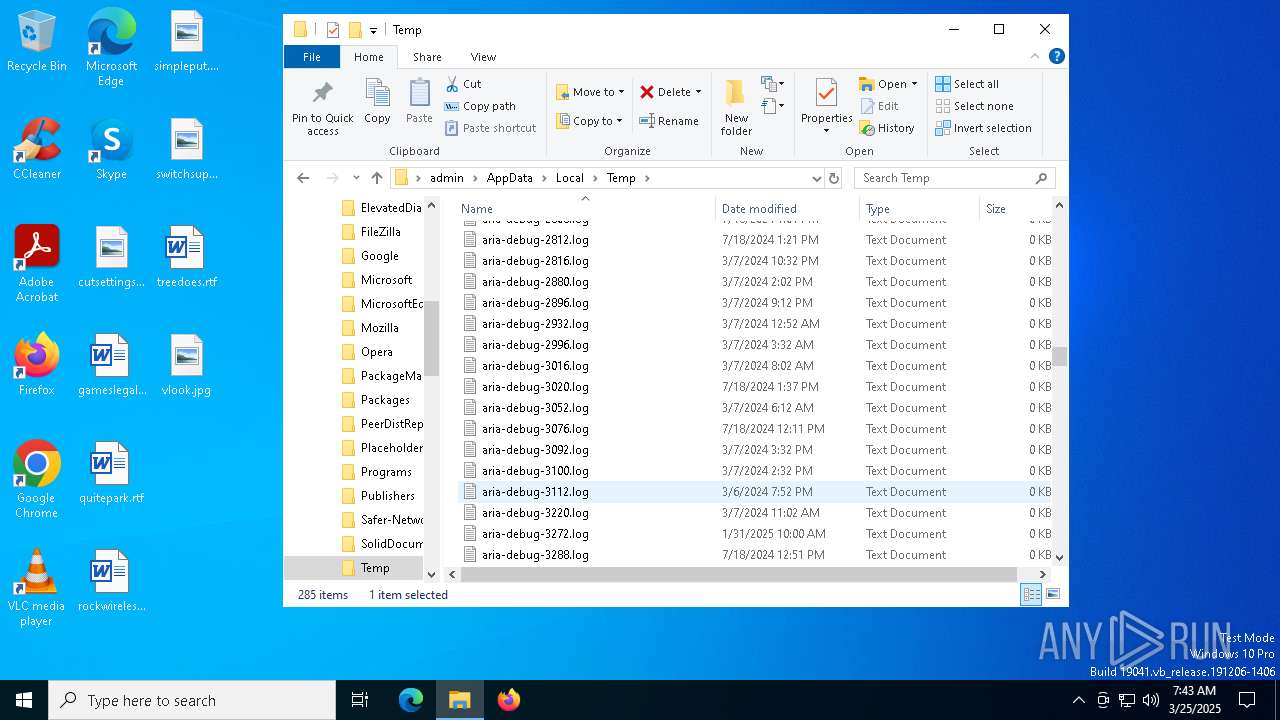
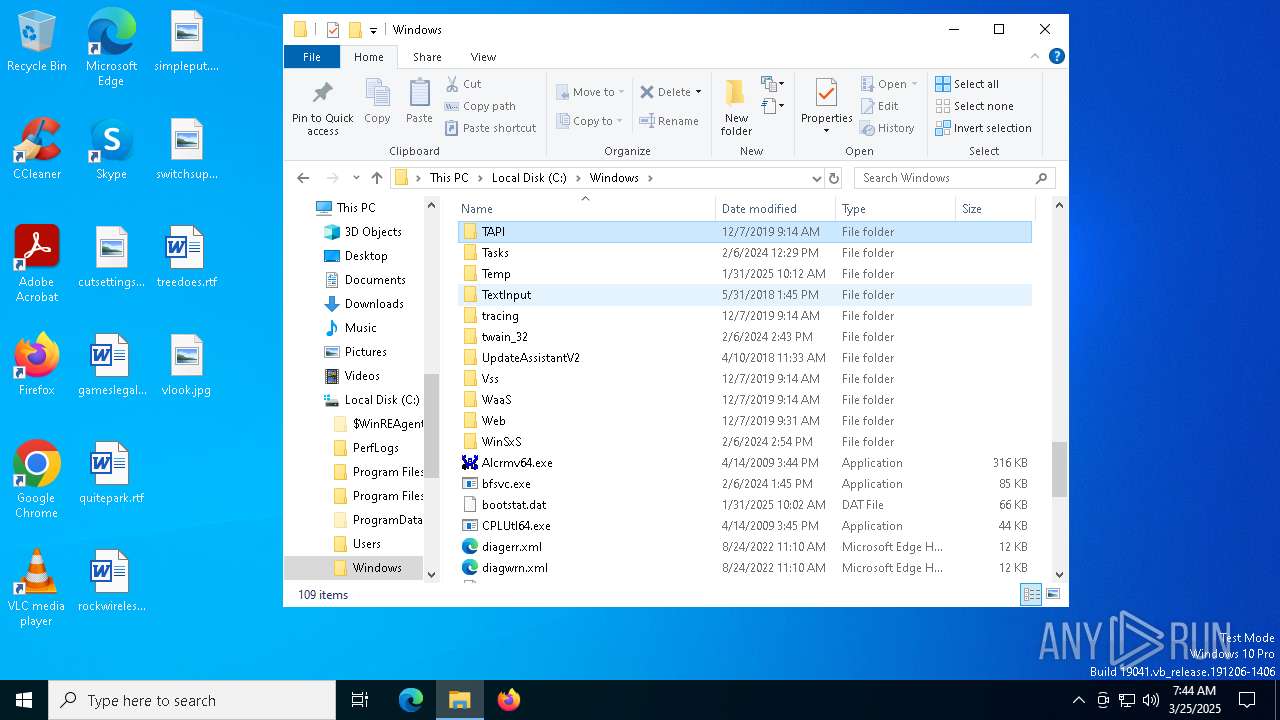
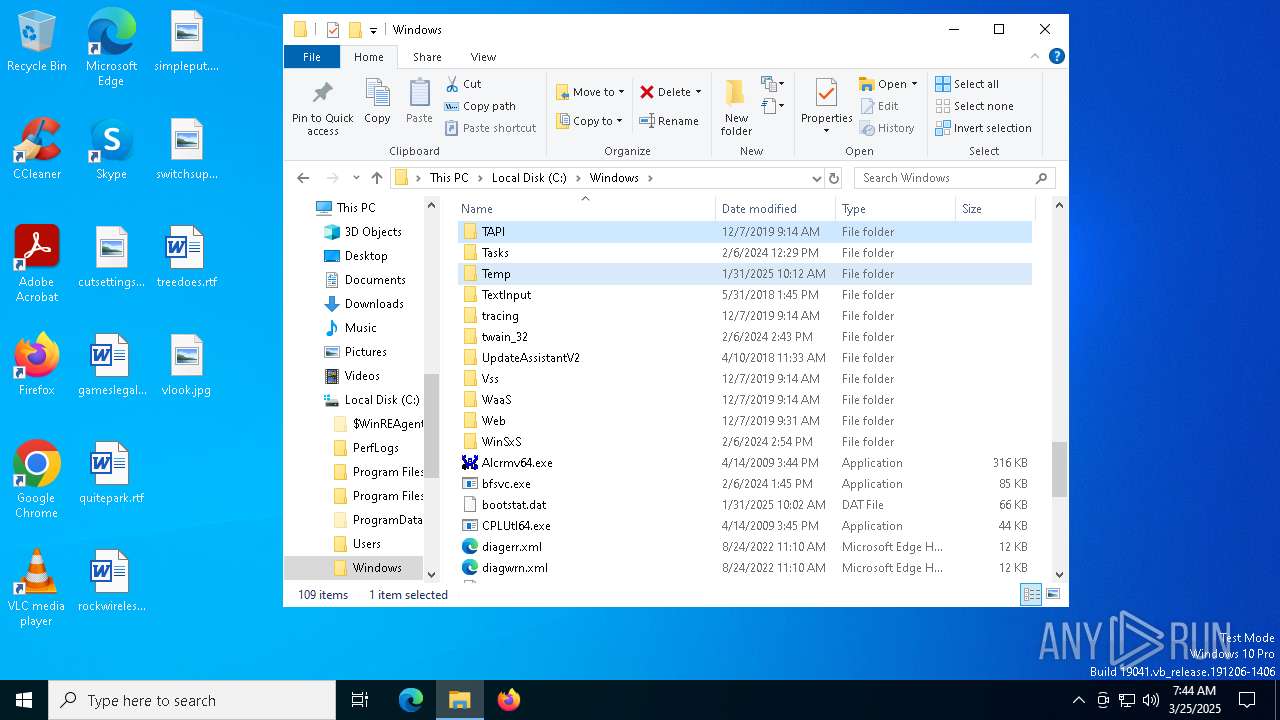
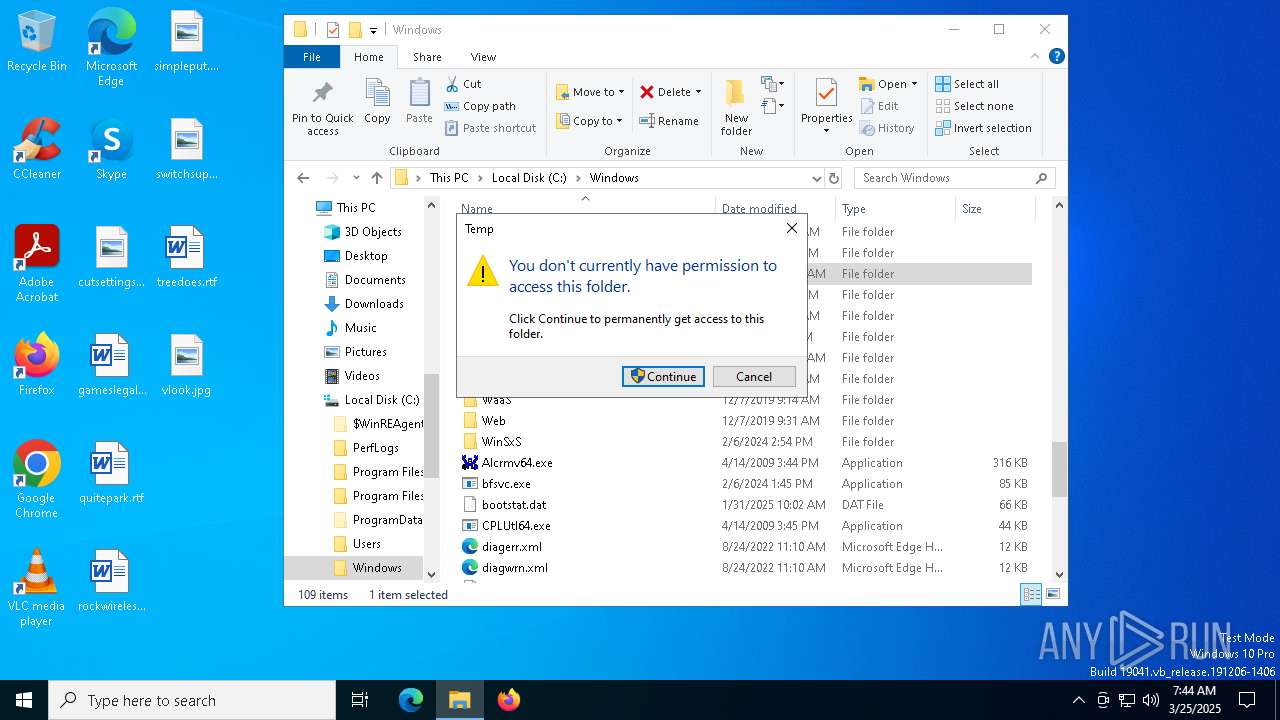
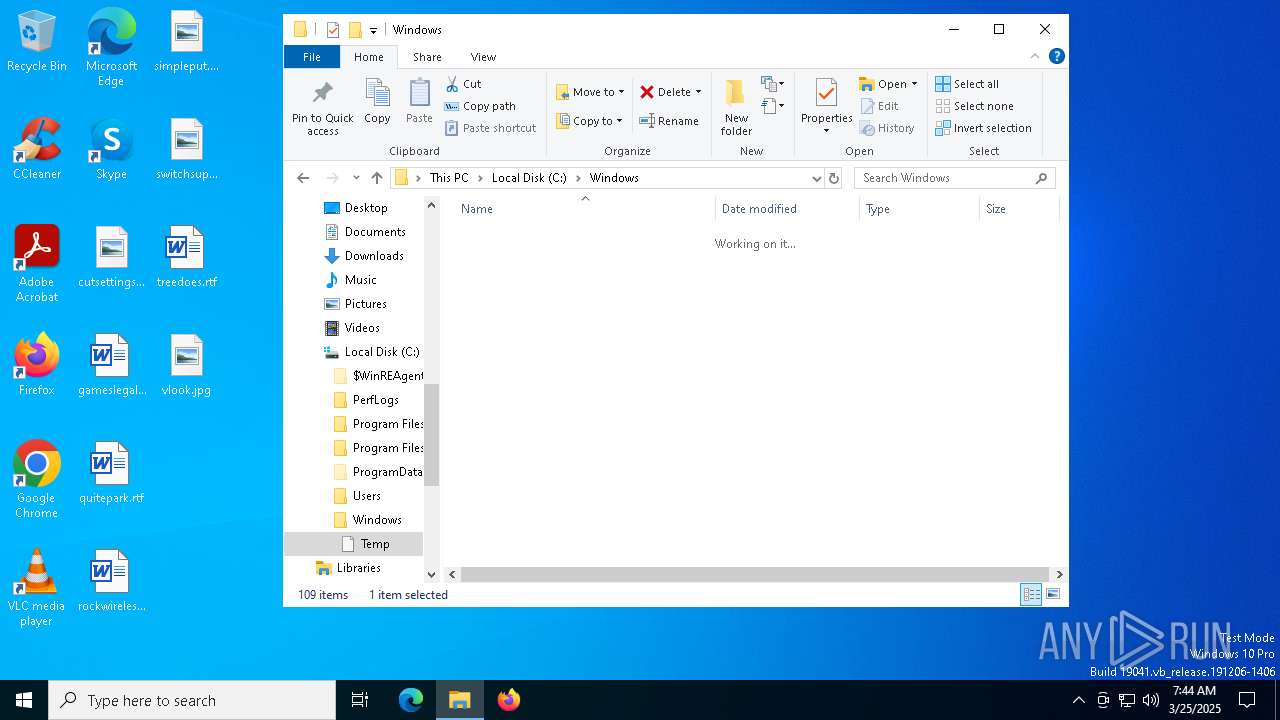
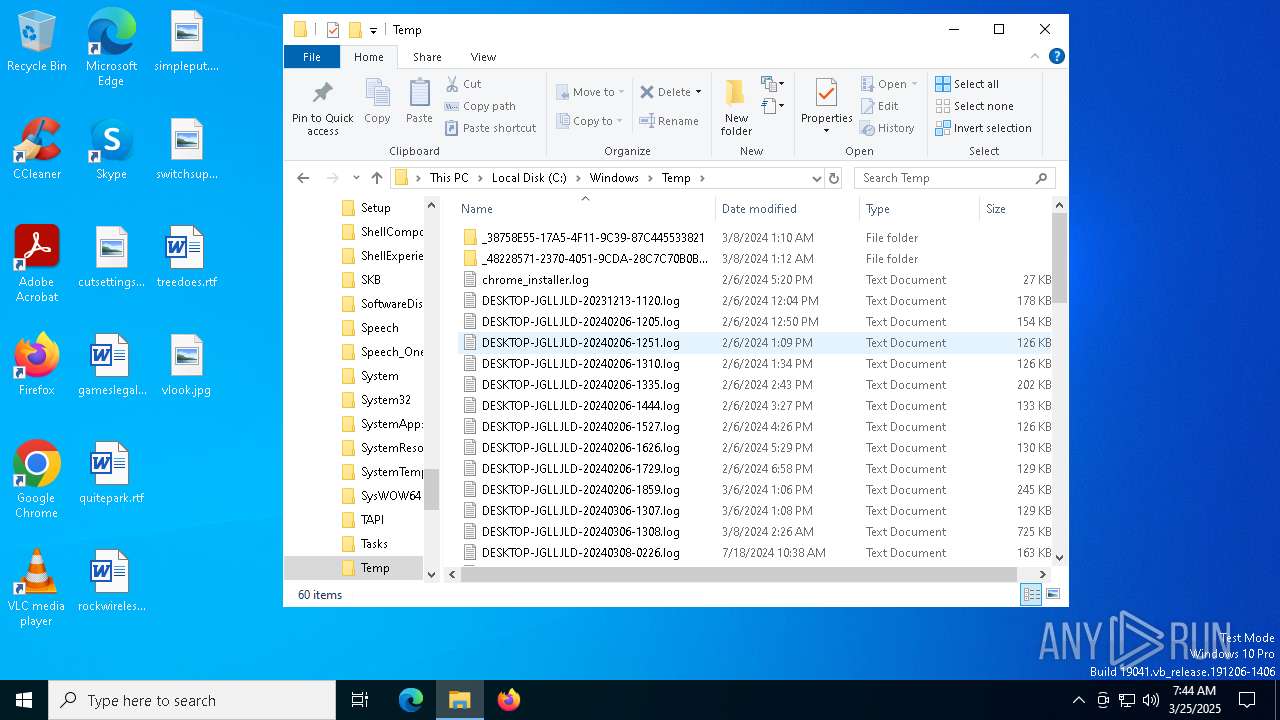
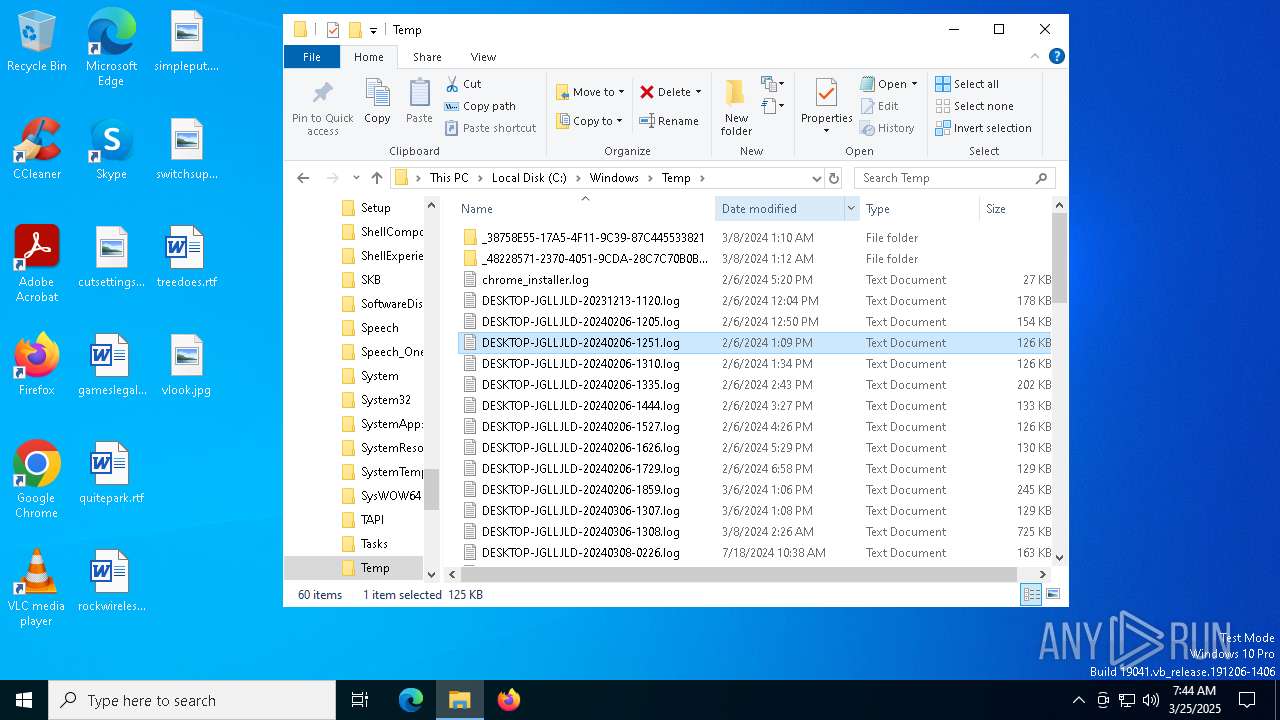
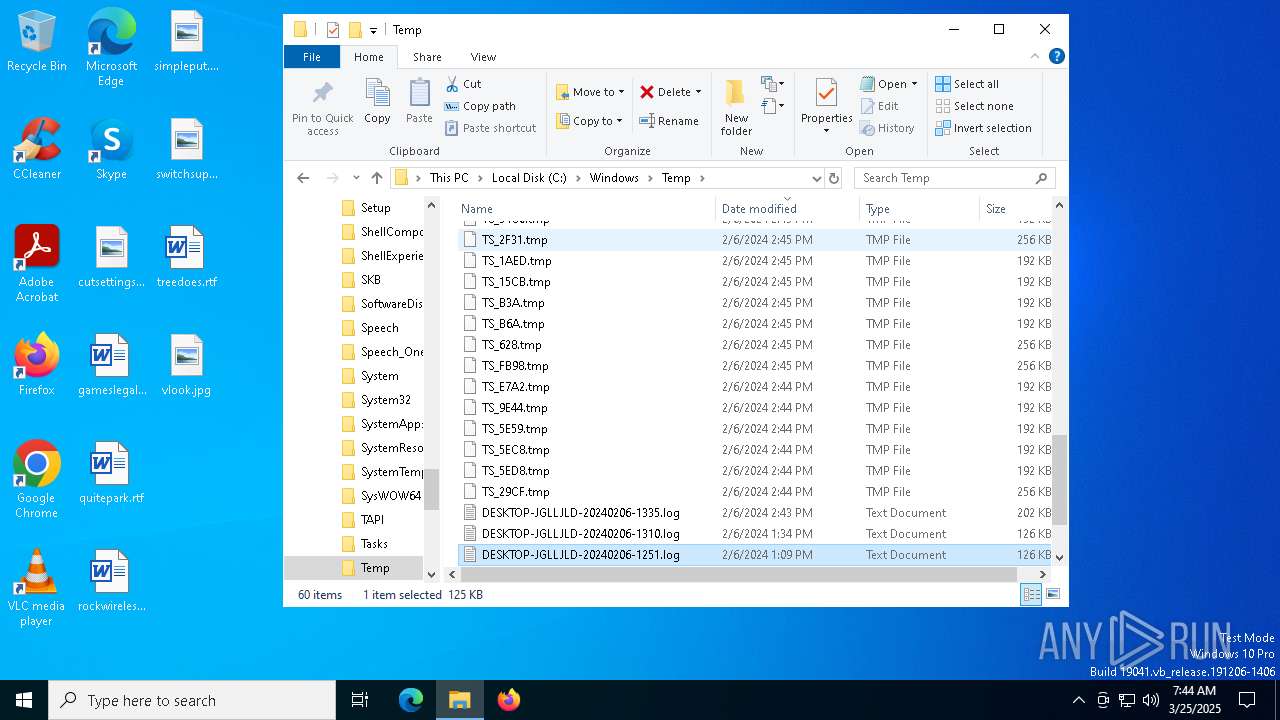
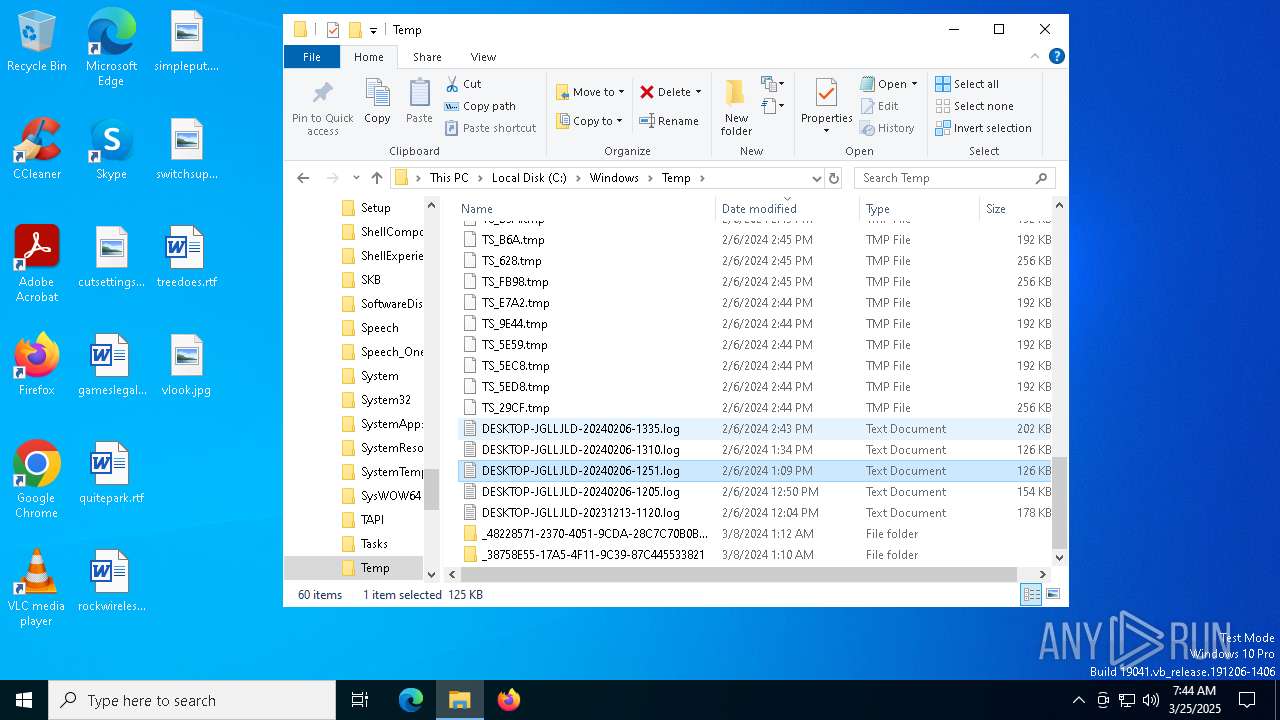
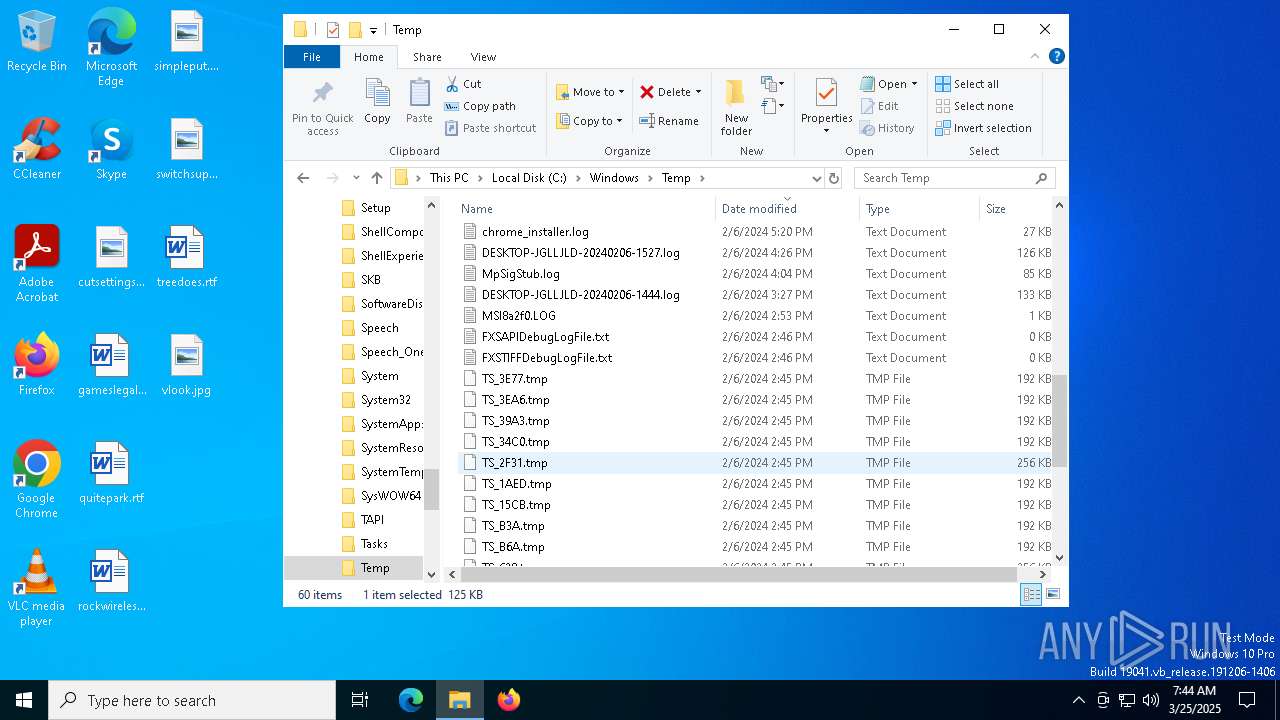
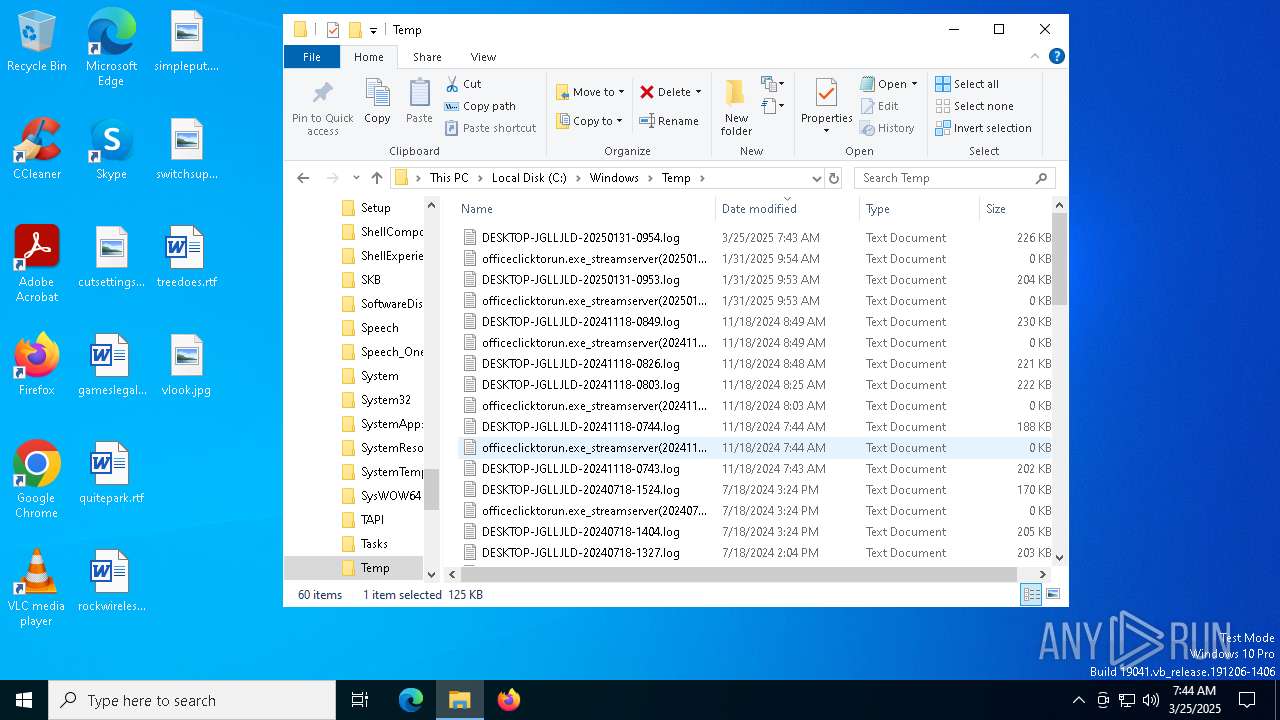
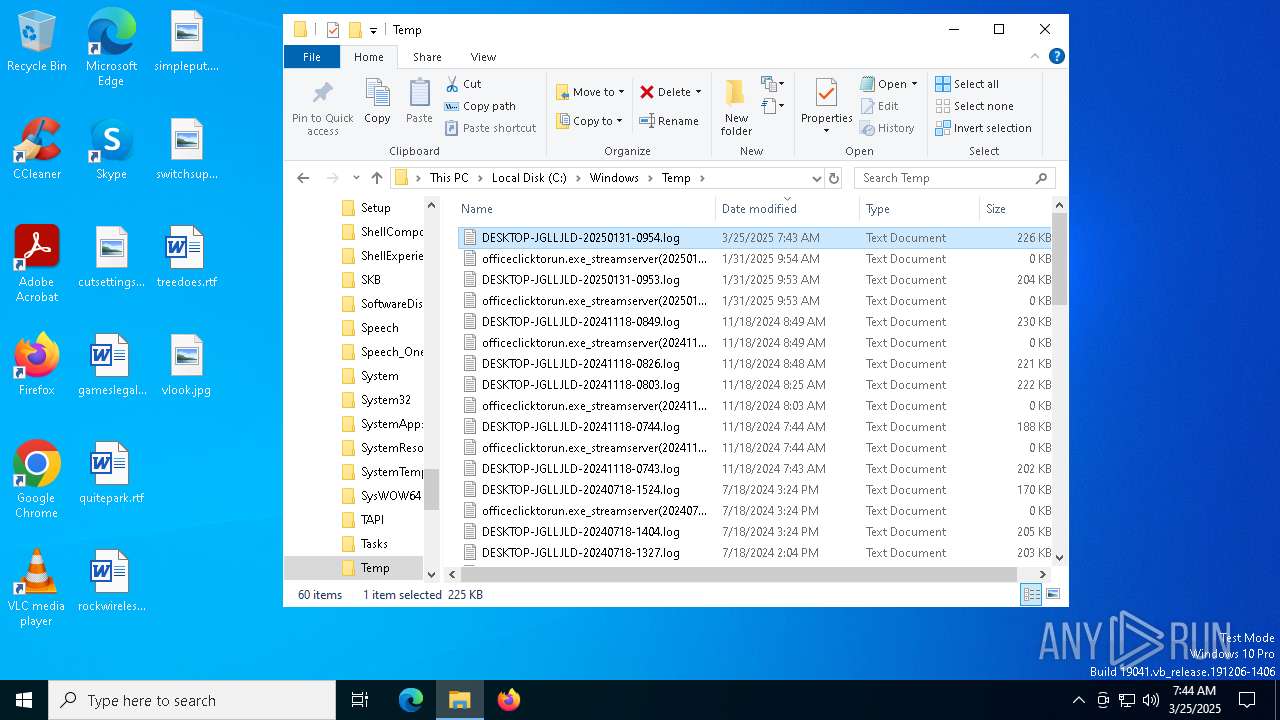
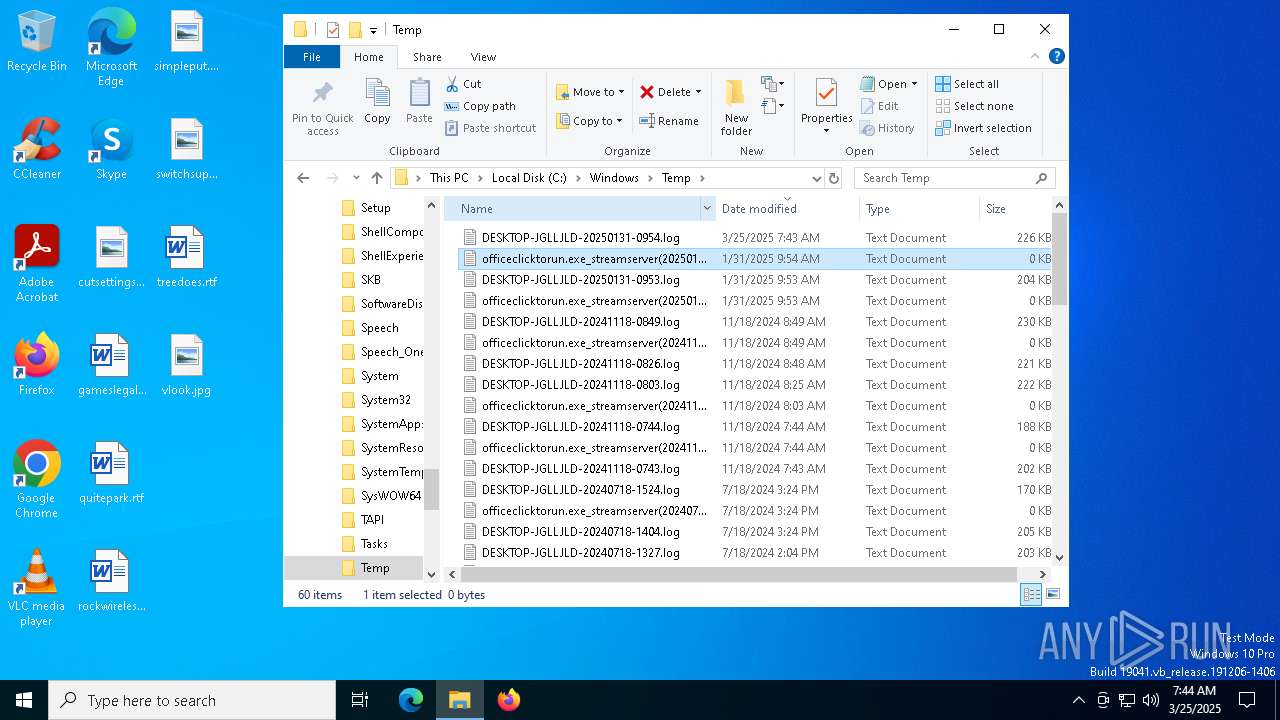
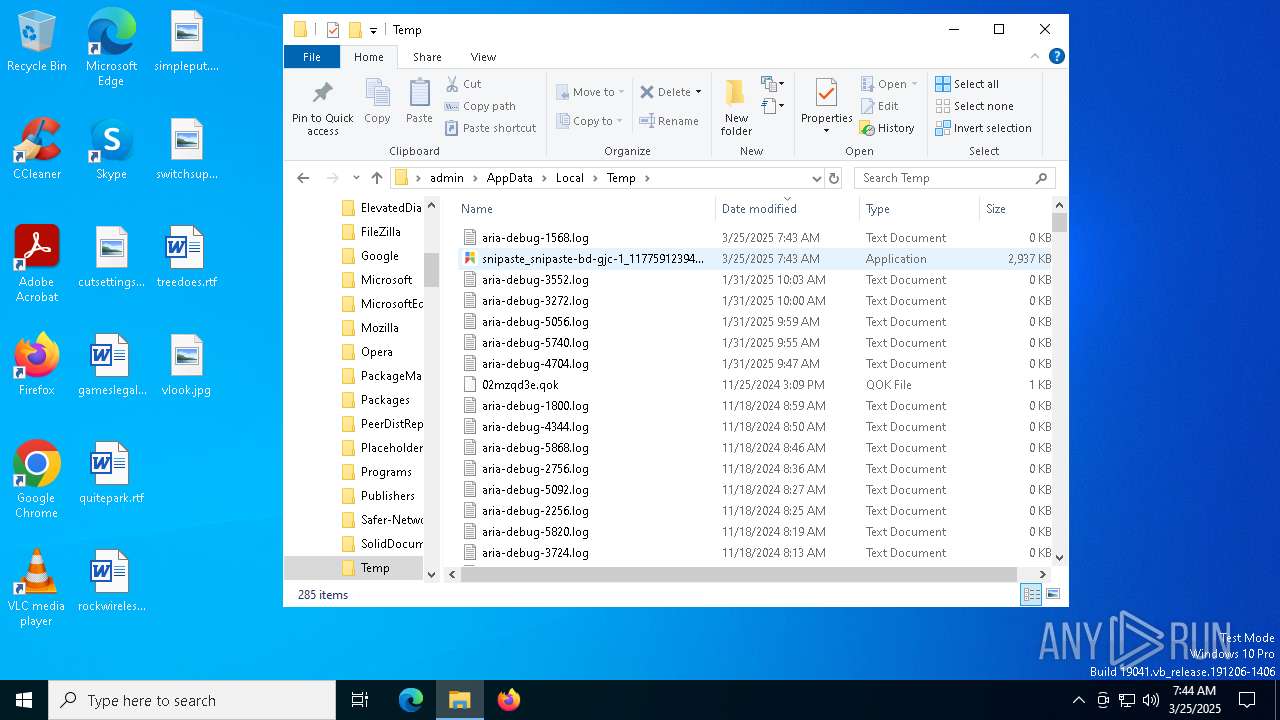
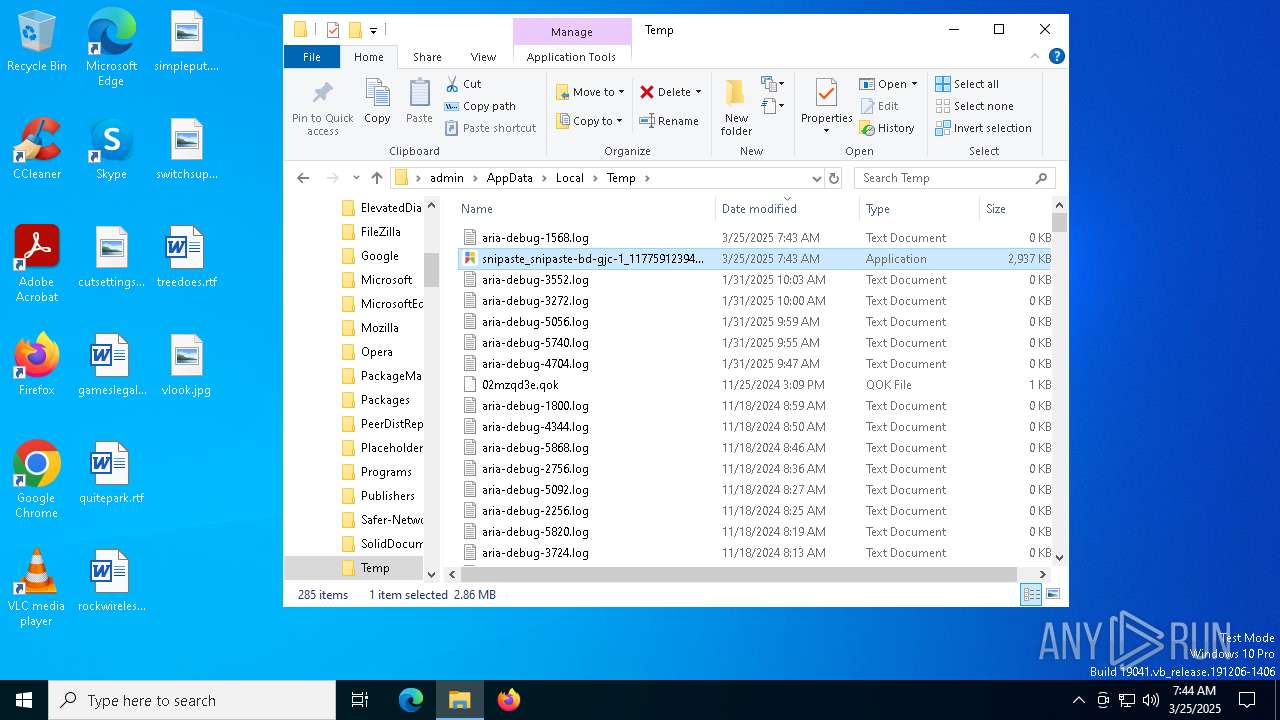
Create files in a temporary directory
- islsnipaste.exe (PID: 5436)
Reads the machine GUID from the registry
- islsnipaste.exe (PID: 5436)
Checks proxy server information
- slui.exe (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:04:25 08:25:11+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.39 |
| CodeSize: | 30208 |
| InitializedDataSize: | 421888 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x3b96 |
| OSVersion: | 5.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2025.311.1037.47 |
| ProductVersionNumber: | 2025.311.1037.47 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Snipaste安装小助手 |
| FileVersion: | 1.1.0.0 |
| InternalName: | setup.exe |
| LegalCopyright: | Copyright (C) |
| ProductName: | Snipaste安装小助手 |
| ProductVersion: | 1.0.0.0 |
Total processes
146
Monitored processes
11
Malicious processes
0
Suspicious processes
2
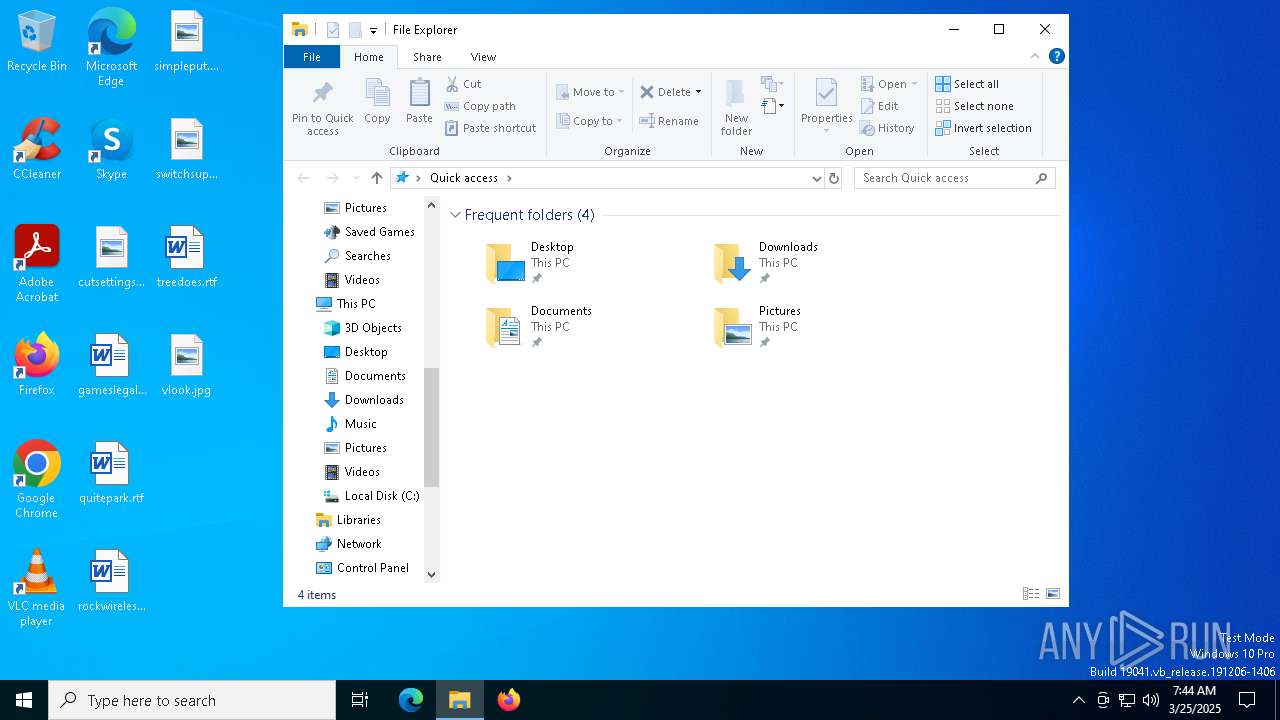
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
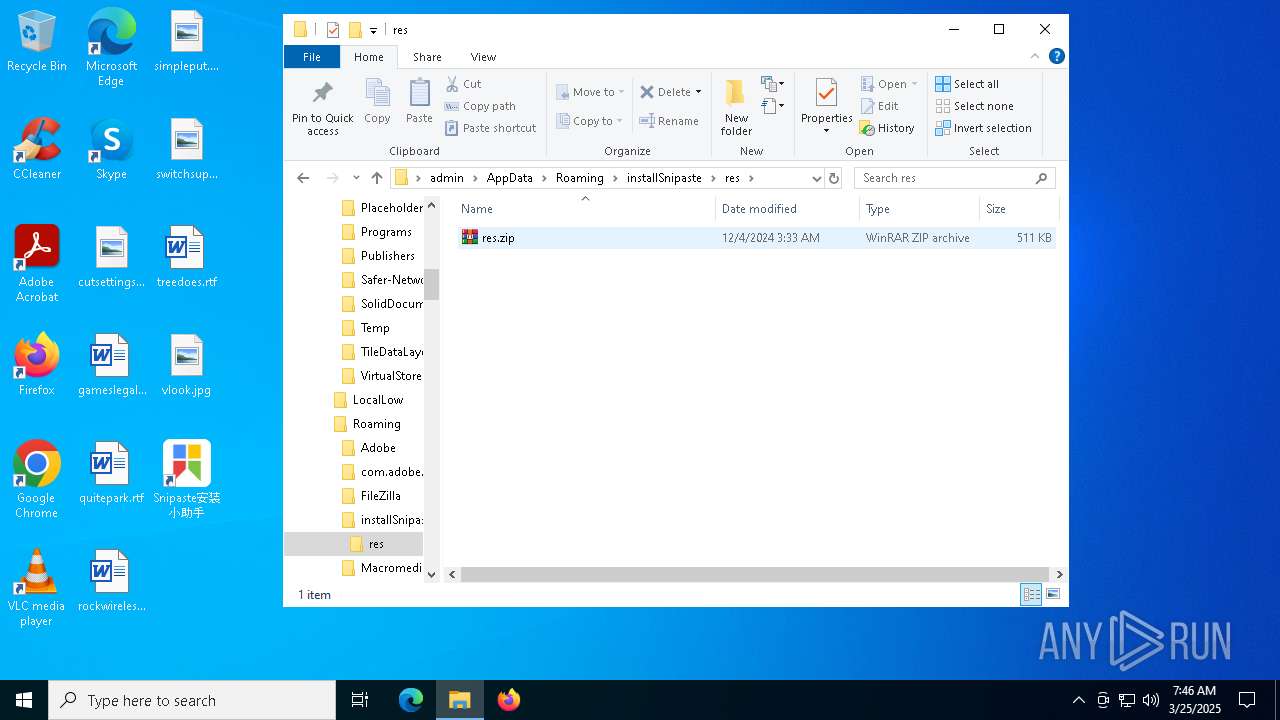
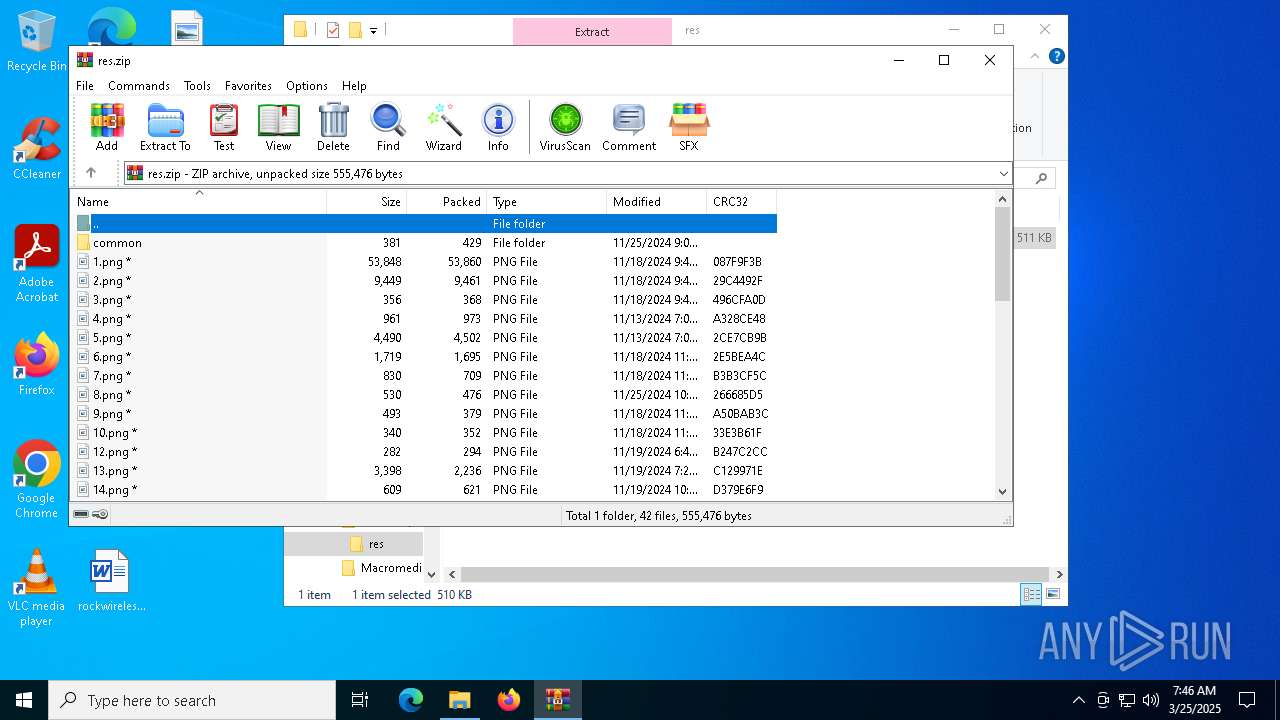
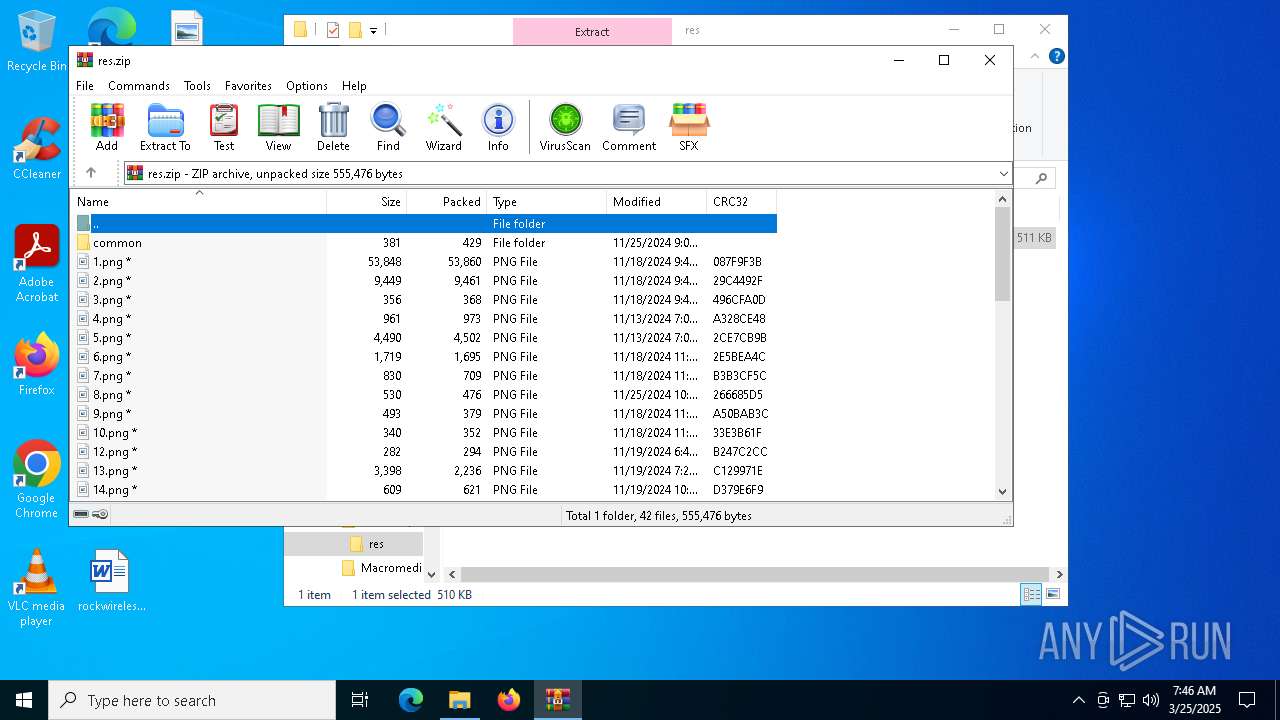
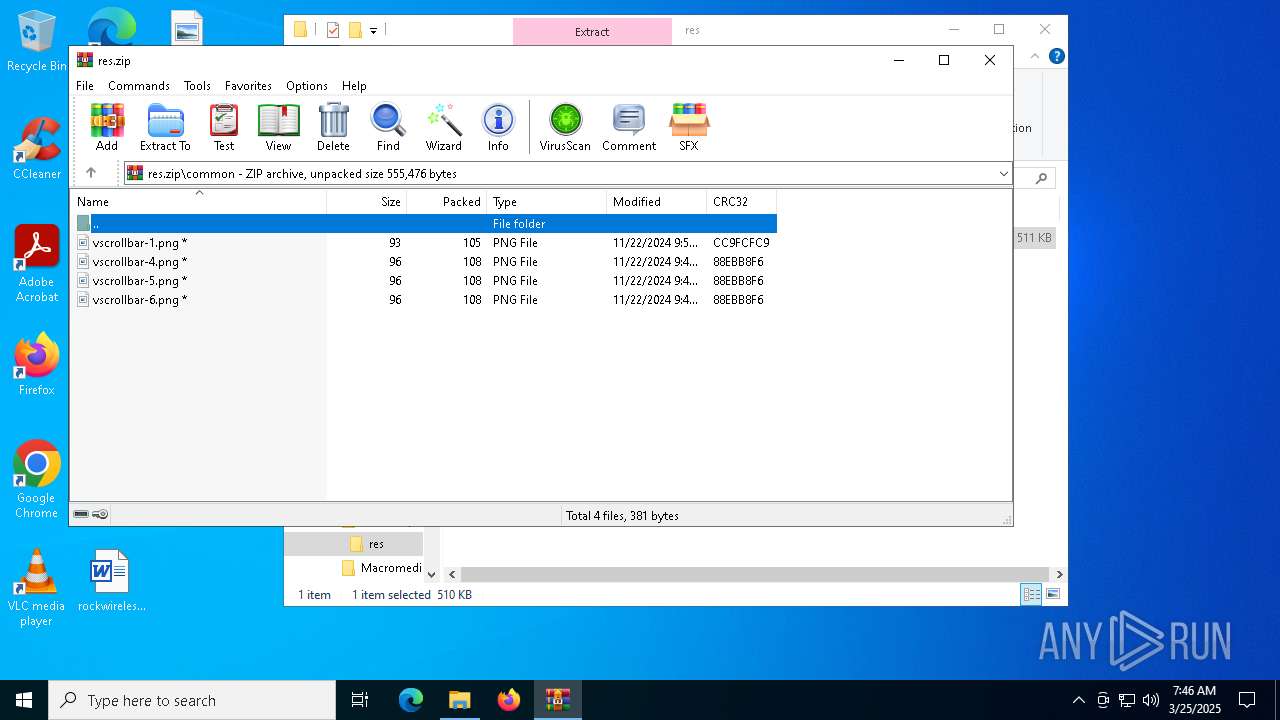
| 3396 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Roaming\installSnipaste\res\res.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3768 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\AppData\Local\Temp\snipaste_snipaste-bd-gjc-1_11775912394326794383.exe" | C:\Users\admin\AppData\Local\Temp\snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Snipaste安装小助手 Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 5084 | C:\WINDOWS\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5436 | "C:\Users\admin\AppData\Roaming\installSnipaste\islsnipaste.exe" snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\islsnipaste.exe | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | ||||||||||||
User: admin Company: TODO: <公司名> Integrity Level: MEDIUM Description: softdown Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 6132 | "C:\Users\admin\AppData\Roaming\installSnipaste\islsnipaste.exe" | C:\Users\admin\AppData\Roaming\installSnipaste\islsnipaste.exe | — | explorer.exe | |||||||||||
User: admin Company: TODO: <公司名> Integrity Level: MEDIUM Description: softdown Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 6972 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 682
Read events
3 662
Write events
20
Delete events
0
Modification events
| (PID) Process: | (5436) islsnipaste.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\FYGame\soft-snipaste |
| Operation: | write | Name: | mn |
Value: ef5f508b6c8417984f6ecd9fe455162e | |||
| (PID) Process: | (5436) islsnipaste.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\FYGame\soft-snipaste |
| Operation: | write | Name: | jwt |
Value: eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpYXQiOjE3NDI4ODg2ODEsImV4cCI6MTc3NDQyNDY4MSwiYXVkIjo3Mzk5MTAyMCwic3ViIjoiZWY1ZjUwOGI2Yzg0MTc5ODRmNmVjZDlmZTQ1NTE2MmUifQ.b23ThxApo6zAdiHX08vKq1IW94liM8Fx4qcQ4mS9Eas | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Roaming\installSnipaste\res\res.zip | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
48
Suspicious files
3
Text files
2
Unknown types
0
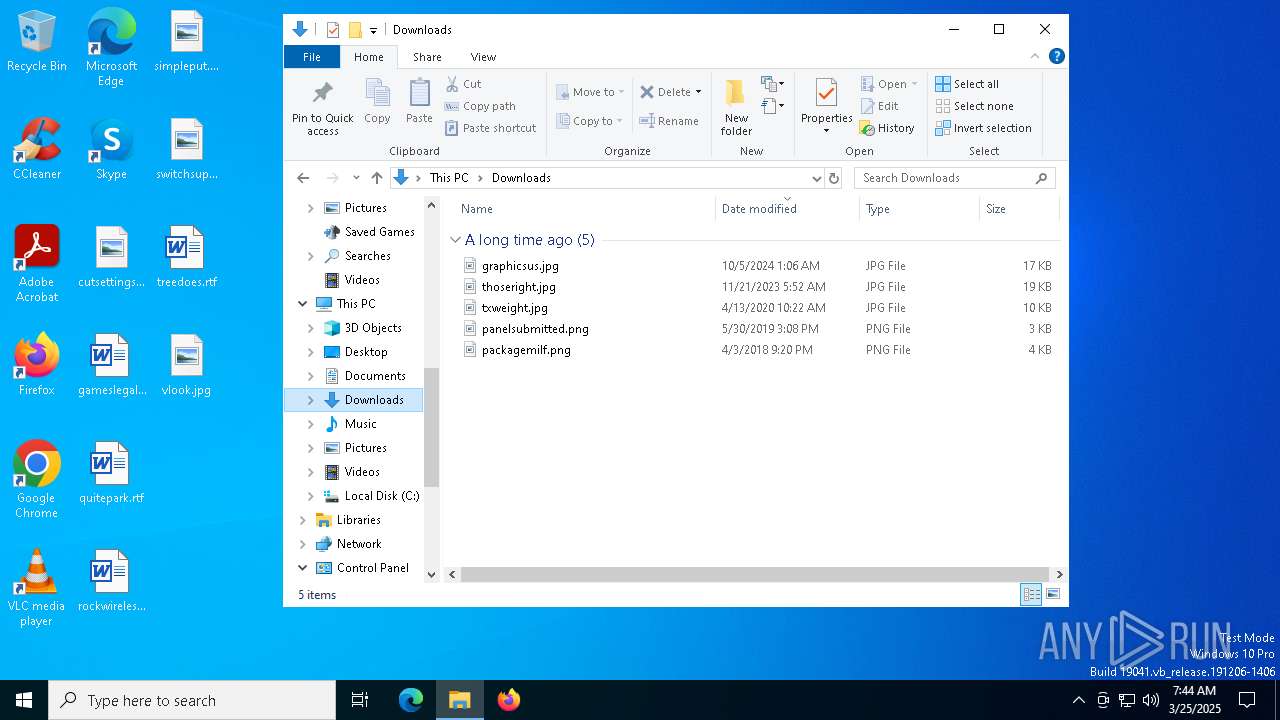
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:7BDEF79D4AE378AA632A99BC2B951461 | SHA256:32A02E8C39C626FDC4EBF6F8BFE476A05A1773CA5B7D0642A3A6B125590A7038 | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:69F7665F4F8FB884D5D25B27A346E66D | SHA256:22EB528C76B0FF3EA89CB7E57525558238CC4D8E14BBD1F764FDDE6DEBBAB486 | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:3F34D9F9C738F108B85D56D8FAE20526 | SHA256:99328B08DBC8A7FCACE311879C61F8E24557D722096EFC84E589437B54629AB7 | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:EDFE2C4BC743789F06A1AA34C910317D | SHA256:243DBCE8A451D8ED18E477FE28C953A7CB959A9D435CC89064C73D6C557FD77A | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:7855024069361E4351BF21CE27118973 | SHA256:D669FF83DBB63D8C156ADC078C1C883DEC90DDF5E4A86436C8A91339CDA6CDD9 | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-localization-l2-1-0.dll | executable | |
MD5:35BC6AE0A77D373A4B5FA44EA331D01D | SHA256:4F63EB0A02EF11C0EBC306199DCDE459FAA98FB0864B3202949FA4E5F3E10AC3 | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:7778D2F53D4BF92A10913ED8E6C875F9 | SHA256:627B648079F2447C62BE7C1D0320FD46F2E63DCA40A7FC55A2A66197DF77776C | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:F5B8F97B5C946BEAF2194EACA76DD6DA | SHA256:2C1478C5D8484A2842DF9F723F1ED0130ED5B6CA61C51D48F884CAB965D30F18 | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-namedpipe-l1-1-0.dll | executable | |
MD5:3C46645C8397FE692C2032DC2940D003 | SHA256:39006F93906EF5A9F84CC1501BAA6F16358FCB909AE91829A6AD8B47CB859DD7 | |||
| 3884 | snipaste_snipaste-bd-gjc-1_11775912394326794383.exe | C:\Users\admin\AppData\Roaming\installSnipaste\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:75BFB396036384B53731C1FE05808E61 | SHA256:C96C6EC91A21C963015150551B36673E9BB90D54C456BA42FE4A8755613EFD51 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
28
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5436 | islsnipaste.exe | GET | 200 | 62.234.146.167:80 | http://soft.shanghaiouye.com/api/data/soft/softs?soft_key=snipaste | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4880 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4880 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5436 | islsnipaste.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |