| download: | hid.exe |
| Full analysis: | https://app.any.run/tasks/aee76cb0-097a-4bd9-9188-68fe671507a1 |
| Verdict: | No threats detected |
| Analysis date: | June 21, 2019, 03:29:20 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B8365F95BFCC5222BF93E6850DADC36C |
| SHA1: | 2AB40394D3772A6E7E5B3EFC872C1A4EB9A90532 |
| SHA256: | 7B6B6946903E49351EB136ECAB5501BB85C1D52D5E5678FEB4BB3FC92A880218 |
| SSDEEP: | 6144:qvSDv1n1pct7AaGiiSW1o+jeq6QtxD3WTQn1eSILklMftd10fejbP:qKhhFFKOeq6yxDGsD6klMVsfcP |
MALICIOUS
Scans artifacts that could help determine the target
- dw20.exe (PID: 3204)
SUSPICIOUS
Reads Environment values
- dw20.exe (PID: 3204)
Creates files in the program directory
- dw20.exe (PID: 3204)
Reads CPU info
- dw20.exe (PID: 3204)
Reads the machine GUID from the registry
- dw20.exe (PID: 3204)
INFO
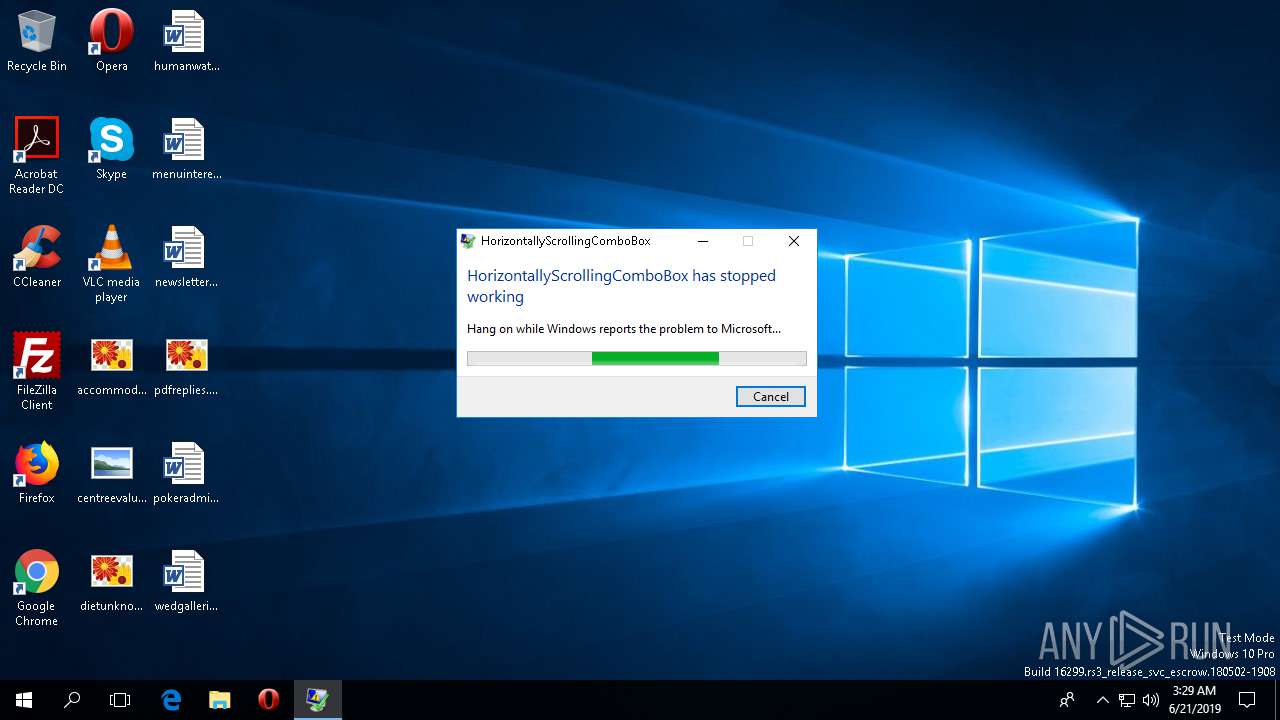
Application was crashed
- hid.exe (PID: 208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:21 00:28:25+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 379392 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5e99e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | HorizontallyScrollingComboBox |
| FileVersion: | 1.0.0.0 |
| InternalName: | HorizontallyScrollingComboBox.exe |
| LegalCopyright: | Copyright © 2010 |
| LegalTrademarks: | - |
| OriginalFileName: | HorizontallyScrollingComboBox.exe |
| ProductName: | HorizontallyScrollingComboBox |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jun-2019 22:28:25 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | HorizontallyScrollingComboBox |
| FileVersion: | 1.0.0.0 |
| InternalName: | HorizontallyScrollingComboBox.exe |
| LegalCopyright: | Copyright © 2010 |
| LegalTrademarks: | - |
| OriginalFilename: | HorizontallyScrollingComboBox.exe |
| ProductName: | HorizontallyScrollingComboBox |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Jun-2019 22:28:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0005C9A4 | 0x0005CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.97774 |
.rsrc | 0x00060000 | 0x00000646 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.51645 |
.reloc | 0x00062000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
90
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\AppData\Local\Temp\hid.exe" | C:\Users\admin\AppData\Local\Temp\hid.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: HorizontallyScrollingComboBox Exit code: 3762507597 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3204 | dw20.exe -x -s 860 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | hid.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.8825 (WinRelRS3.050727-8800) Modules
| |||||||||||||||
Total events
202
Read events
196
Write events
6
Delete events
0
Modification events
| (PID) Process: | (3204) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | ClockTimeSeconds |
Value: 2B4F0C5D00000000 | |||
| (PID) Process: | (3204) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | TickCount |
Value: 0FF1290000000000 | |||
| (PID) Process: | (3204) dw20.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Property |
| Operation: | write | Name: | 0018BFFFB20EAB97 |
Value: 0100000001000000D08C9DDF0115D1118C7A00C04FC297EB0100000021AE99ECF63A284097A1DF68160E68FA00000000020000000000106600000001000020000000E7DF8421076AB6184CD2265F19A33741E4227C12C4508F739AA4E757C66894E1000000000E80000000020000200000006AE4DBCB96083EEBB0AD76A63820D1491686D4C9E29F687F6123E7B5EAB164AA800000008BB32B4B61439FEFE8E99CF84B139AB8B444EDE6ACCBEFEA353A90AC77E0C981E85038B63C928EBD942D3F669E41FC06876629D0A943F41C0050B07766A1A64BCC697B09A1E1BFEC2576FF28B1F6C9811CB35DE6BA38A89E6AF4F32534E70DF4E11881D2A1173C81EB3590E3D18994815B6354478D5F5EBDA1094DB77C2EF6354000000097B301C82B49074038AB57E9D7D42CF80E49C958A93BFB9B67FD98675E19F5FEE9AEC8F4ACDBF7510DE7DDDC6764AC7E3ED198DDD7624E3A9D61D067888A76D1 | |||
| (PID) Process: | (3204) dw20.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Token\{67082621-8D18-4333-9C64-10DE93676363} |
| Operation: | write | Name: | DeviceTicket |
Value: 0100000001000000D08C9DDF0115D1118C7A00C04FC297EB0100000021AE99ECF63A284097A1DF68160E68FA00000000020000000000106600000001000020000000C54852C8B2CD0F7358188403EC89A82CEB0A38DBEE4427B02F02F26720D9116C000000000E80000000020000200000005CFCF903015EDBBA091B1A8FDF8F7159252B0DF353FDC2BAC1D3E949A7433387200800003D64CC19F73712E2252D03F1646FBEC83A468D467B4B7E45230D62B579B508295033F98D6F03CF39BCF174FB904AAF3F192F4A0DD34CFC850835F663A318BA8513FF3263776E6D3308572DB0AA23BBB6B48CCE8CD2065AC6C8D5C9717E518793098160FCE7A3CBEF597F1A425748430B183EAFAB2F97AD8BEAD51E0881E83B4D24CB1368156B82F709BB51225DA7605ADDBD857683490DEAEBD0EE19160B27584C29A7D423031DCCD85E86DBD9A7C070EBBD97F28B93BE2C7158A230E6EB448C3BBF4BB39166AED9C28625BAB1C4119EB5B59559D0CBCA72F44B741A54597213EF92C50C85AE6EC1C5B4DC80D6407FCCFFCFF746E3FD95A53A2621F17CED8D0EF0021079ED13FDC2FB109F22E65357B52FB6F04A9B56FEB4468E3D424BC7F332DBFC0246CF64C7D28F570E24E63618B3CFA5706DECD1D42EF797343F7EC321901CD87CEFC8946B3A73ECB7F775E89DEE24B0F5B95F95E89146B72AFAE11FFA09D24A50D45AF0368FB214535D9E8DFDCA769DB4BA95A1A4012E1305605A7371A4505E630772315AA1C12B686C8C94380271075A49833E5E3EF0BDBF5B10009CB660055232A1B5C73413ADE746192870588C0C54717F0292B2D2622E5A3FC29C0B2A937803B7D5A0EFCD5E7AE7B0A454089ED88CE1A4696930EB65D06DBE9B1D765AD06D974B60A4FEE7B1CB33B28A17EFEF4ED2F592CEDCCAE6A6F6734157172DF0161D8539131AF8C5FD26343A44397979848C575057A86F6B21B62976F72FF5A42BF2DA47317F084AC08D482718C1E210F56FD692354D7D37B69D5958D72C9EA6317A4D7448B60D19EF86952E5659583E77FB67BB2B0F198CFB65416ECA2B4222B4E81323C5D17F865DDD58AF24D087D87172728486FDBC716562F6BAA79E22A69CC7FE9384EDCCF6F690F48A225C120B745695A4BD0879CA4E6DD024D5AB701E9F59111D3DA379B1BA2654708D8F511D9AE5B5DE173CBB83EF48DE31B52C5935EBAD3E74037F3245642E82D13D941F75461DAFCD0246D66F5F0379EA6CD09A9829CADCC37555DF47A3021E113A77F1044F1A8F36A89D9D9AE5C6C1047F23D118DA4D08059BB163AD677A2FD95081B94E2465279F4FE7901E3999E6A90CEA348954BA84D6B94592B6F4AAF08C836986A062A73CB4E6334F3A0CC719ED397E8098E7D6DB24A098AA1139667A96BEF25E74588BD1DA384B2C9C3A39DB4F5024DDFC5E2744DDAE0119E19A2A632B47BC5FB578215F4B0A39E085D4C1F8B61B8116E4E97622303B04D99855611442D5729434F08B56FF9170E0426B4C7D0A738BCF2C129977BB8C9C6CEF95D4192439117783E07C6AF60B6C8A2AC0B8FD1F7FE7C111D4577104176F6D13C03B9F839DC0D21C8B525453249EAF03912787912D362540075C579C1339CD7486C4CDDC98A08429BF55247FD2393F07010DB0AD0E02E5718DD6C26D067F3B7EE654CBF3CBD5B8CCFED9E6846401771BD1F9A00CA4DB071CAC236734B638CB70A55569EF39AEDC651F80D9B7971E56F00FC1B7E173220B9F3E606A9C07181DF60EC10BFE36B040319932EB0FC9A3A99B40E1D439F4859D4B3545049FD5D29E0BC078E1BFD69B1304C842DD86364C7018594DAD0B01846C96391B6D6F706514F58F97BBF7F823A77CA820775F873ED153BCA544440B08C02A6C5F41D15BC0636B997E67F6F27D03A51663BD4EF97F1752D796D6B4732C35FFB1CED7482F25E3FEBCC70A4AE974557B5716DF80ADA11CD67BB6AEE0EE0ACF937FEB60D320C12EE64616917C045034DF677B69D2C682DB8B3F1C823F345C04AD0CC57F6E8DC0B63ED251EE8FB69078D1D78E9F980FAC01B4662EF68EB7C684B12CD89533FB69F456F1E264BF6DB1C6EDCD15A4C775AE7FB37DC94395E64E368C5E0A3B05F5F6DF789A6548DD974B10A097DFD1827495CA2731F12EE1870B67E2A5D3959B724D1E96FA02F6DBCB3E9449F5B67CD933EB3DA26B7015D4B5177075CBE60BA9438456E81F209F086156146EF26C41ED2F638D7AF50C864302D2F95FDB61CB516E9F1D7BC8270D165F516FE8622C24894784268904F23F6E40FCF5E0FD55E2FF832D07CFA2E62B71FD4B7165A356E2C45A8CB1408CB9875FEE64E063F6334BA29E127C31E8A6BB1C83732EC7ECDCD0CA8A25AAA7A8FE79C5ED48B94B7EF285F3A6DAF53DC325967D762E5F9B520D26CA5876CCDA4CF064842AC94D11BBB88C21052EFEB0C710F8D987F8D885A3E6E02DCFB59A4E4101EFEFFB1074019496AC6322158B4F45E0B42101373BF7DE71C499D59D4B23BF73ECE057F9188F2A68381F3F9AC4CEB093FABBCAC749F2ADC732719687A8F3CDF32C6F52BCC3D16825AC041E732262AF57C1EFACB4A8B88E695E4F9C3CDCC0E3747FD2D86256FD15E7236042A6492B5618D712456F23F3953A4B49A76BF790A1676A843301A71FC6EB9620601E024ACD95E5443EDD0AF02B5ABD62908788F62C9565DE721A1AACA4F558F847316CDEA2E7273AFB96FBFC9A36EB9F93EB66E6F52930DCA0A9D939416915D3AE521CFD32896F95DB00128C684370510EF1FEA1899CF7A025CFEF46ACAF765ED07D1D1E34E85B2F53F74DFA597A92A70E4690D4D0FB5135EE1D61B59EBA16964D02CFCB9D16F40E547253787BC47D7CB13EC27AB849DFCD617281ED24D07251F3E1296D1AAB13B2AB6E9200894361D39174559CBE28BF67AA4F3373FFD1C9D5C80ED06BC52EC0673FADA1FAAABE51D2C43FE05E56F9F881B3DD9C71FFBBE46891197110F2E8F8877E1D9DAB96431788A30A87970B0E2A240C5FEBEB60BEB3CED2DF6DDBB40D4FE67823EBE7F45151BA524D7EE8292BF096F176292F8BE8F828D33CA07BBC3ACF2E451C472D344110F129F079F706CC77CAABA9BDCDA35ED581D93EB1C0ADA303FBE03C0172027423D1CCB38486A78876391759BE4000000081AF95B6E36ACF6295EC73CBFB0A2EE6C76F7322558B41DA4A7E7EB9B30CF9C7E1E6B2DC489A15922C7B8A7E3704C5405A03683BA03C4B92C7F841D73180D6D0 | |||
| (PID) Process: | (3204) dw20.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Token\{67082621-8D18-4333-9C64-10DE93676363} |
| Operation: | write | Name: | DeviceId |
Value: 0018BFFFB20EAB97 | |||
| (PID) Process: | (3204) dw20.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Token\{67082621-8D18-4333-9C64-10DE93676363} |
| Operation: | write | Name: | ApplicationFlags |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | dw20.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERE8F1.tmp.mdmp | — | |
MD5:— | SHA256:— | |||
| 3204 | dw20.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_hid.exe_87aaa16e29ede9b71c9023f813ca5b3170f59e0_00000000_0cadf9d9\Report.wer | text | |
MD5:— | SHA256:— | |||
| 3204 | dw20.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WEREBB1.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5004 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5004 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
5004 | svchost.exe | 157.55.135.134:443 | login.live.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |