| download: | /a/7z2500-x64.exe |
| Full analysis: | https://app.any.run/tasks/f8f60129-1365-45c5-87db-491400234a77 |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2025, 19:44:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 9EECA41AA10EF3C99D7DB2EA97160E17 |
| SHA1: | 3BF66C442B446BB642AB75360077203A1DDDC16F |
| SHA256: | 7B67375B2B303E05D2989F23E986126EDA67435C71231FA4B0BDAEB7A619A0A6 |
| SSDEEP: | 49152:/PHtcOHyP4Rdkd2XMixIU8P8K1lGEfmvzqoVILcPyff7hkjIPdn0NdbZlpLYHqlQ:/ftcdWK2XMgqkKbt4ZtPg1kjI1n25zpI |
MALICIOUS
No malicious indicators.SUSPICIOUS
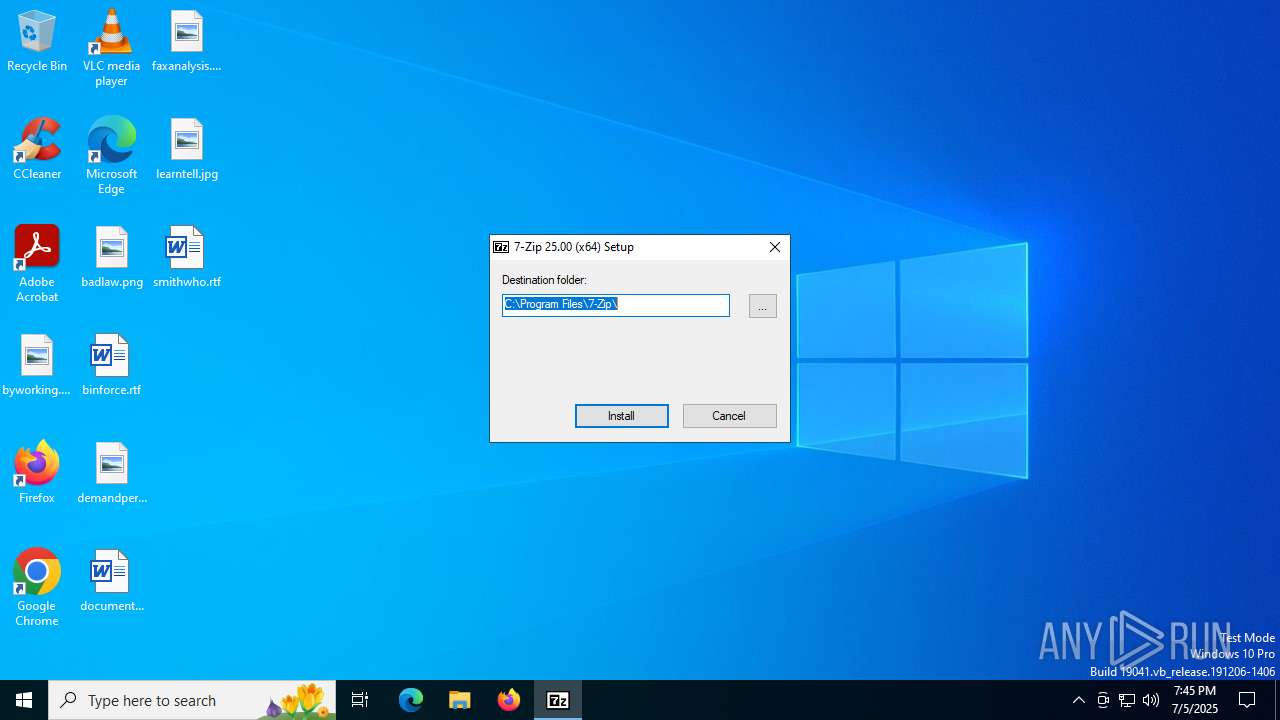
Executable content was dropped or overwritten
- 7z2500-x64.exe (PID: 1944)
Drops 7-zip archiver for unpacking
- 7z2500-x64.exe (PID: 1944)
Creates/Modifies COM task schedule object
- 7z2500-x64.exe (PID: 1944)
Creates a software uninstall entry
- 7z2500-x64.exe (PID: 1944)
INFO
Creates files in the program directory
- 7z2500-x64.exe (PID: 1944)
Reads the computer name
- 7z2500-x64.exe (PID: 1944)
Checks supported languages
- 7z2500-x64.exe (PID: 1944)
The sample compiled with russian language support
- 7z2500-x64.exe (PID: 1944)
The sample compiled with english language support
- 7z2500-x64.exe (PID: 1944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:07:05 12:00:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 24064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7294 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 25.0.0.0 |
| ProductVersionNumber: | 25.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7-Zip Installer |
| FileVersion: | 25 |
| InternalName: | 7zipInstall |
| LegalCopyright: | Copyright (c) 1999-2025 Igor Pavlov |
| OriginalFileName: | 7zipInstall.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 25 |
Total processes
143
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1944 | "C:\Users\admin\Desktop\7z2500-x64.exe" | C:\Users\admin\Desktop\7z2500-x64.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 25.00 Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\Desktop\7z2500-x64.exe" | C:\Users\admin\Desktop\7z2500-x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Installer Exit code: 3221226540 Version: 25.00 Modules
| |||||||||||||||
Total events
174
Read events
153
Write events
21
Delete events
0
Modification events
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path64 |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path64 |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {23170F69-40C1-278A-1000-000100020000} |
Value: 7-Zip Shell Extension | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {23170F69-40C1-278A-1000-000100020000} |
Value: 7-Zip Shell Extension | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\7zFM.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1944) 7z2500-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7-Zip |
| Operation: | write | Name: | DisplayName |
Value: 7-Zip 25.00 (x64) | |||
Executable files
9
Suspicious files
3
Text files
97
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\af.txt | text | |
MD5:DF216FAE5B13D3C3AFE87E405FD34B97 | SHA256:9CF684EA88EA5A479F510750E4089AEE60BBB2452AA85285312BAFCC02C10A34 | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\da.txt | text | |
MD5:C397E8AC4B966E1476ADBCE006BB49E4 | SHA256:5CCD481367F7D8C544DE6177187AFF53F1143AE451AE755CE9ED9B52C5F5D478 | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\ar.txt | text | |
MD5:5747381DC970306051432B18FB2236F2 | SHA256:85A26C7B59D6D9932F71518CCD03ECEEBA42043CB1707719B72BFC348C1C1D72 | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\an.txt | text | |
MD5:F16218139E027338A16C3199091D0600 | SHA256:3AB9F7AACD38C4CDE814F86BC37EEC2B9DF8D0DDDB95FC1D09A5F5BCB11F0EEB | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\ast.txt | text | |
MD5:1CF6411FF9154A34AFB512901BA3EE02 | SHA256:F5F2174DAF36E65790C7F0E9A4496B12E14816DAD2EE5B1D48A52307076BE35F | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\ba.txt | text | |
MD5:387FF78CF5F524FC44640F3025746145 | SHA256:8A85C3FCB5F81157490971EE4F5E6B9E4F80BE69A802EBED04E6724CE859713F | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\cs.txt | text | |
MD5:1130ABF0E51093DC7EDD2C0C334BE5D8 | SHA256:DA788D30AA74B3F8B3D920E98C535E4544756E9E4E235ED0221654F3177D3D2A | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\bg.txt | text | |
MD5:2D0C8197D84A083EF904F8F5608AFE46 | SHA256:62C6F410D011A109ABECB79CAA24D8AEB98B0046D329D611A4D07E66460EEF3F | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\be.txt | text | |
MD5:B1DD654E9D8C8C1B001F7B3A15D7B5D3 | SHA256:32071222AF04465A3D98BB30E253579AA4BECEAEB6B21AC7C15B25F46620BF30 | |||
| 1944 | 7z2500-x64.exe | C:\Program Files\7-Zip\Lang\br.txt | text | |
MD5:07504A4EDAB058C2F67C8BCB95C605DD | SHA256:432BDB3EAA9953B084EE14EEE8FE0ABBC1B384CBDD984CCF35F0415D45AABBA8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
35
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2428 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1948 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1948 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3936 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5328 | SearchApp.exe | 104.126.37.168:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5328 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |