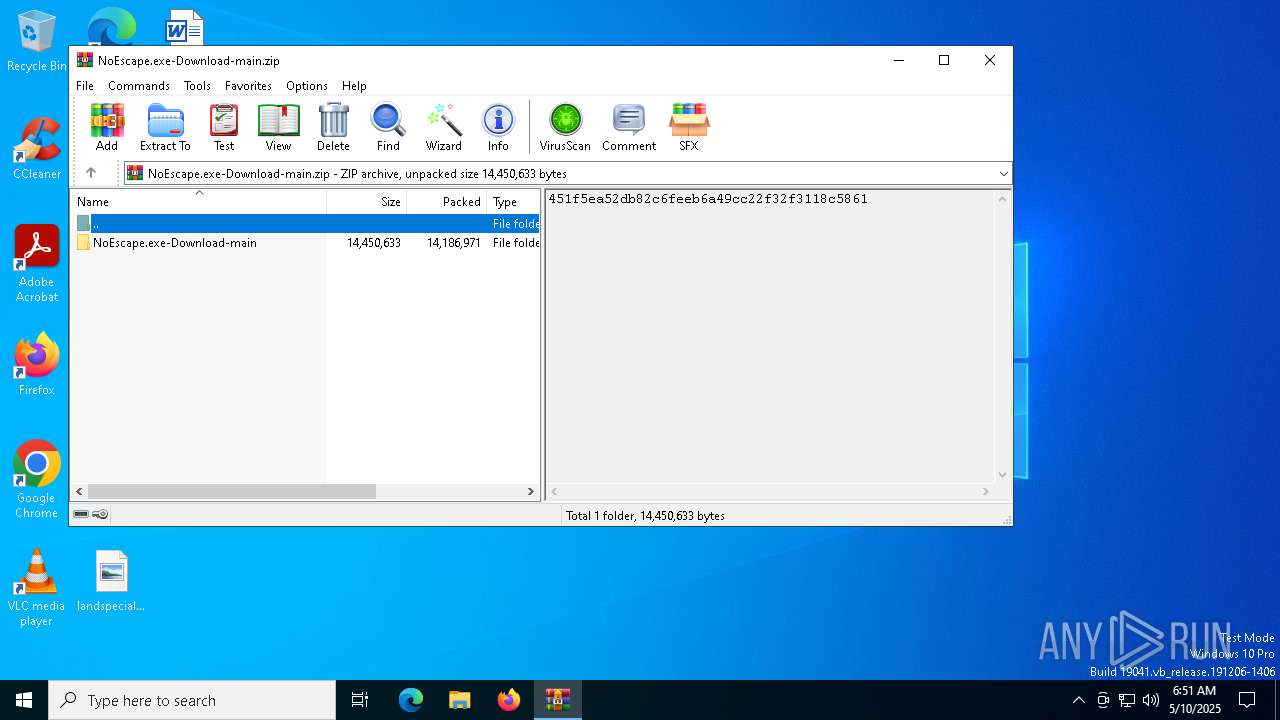
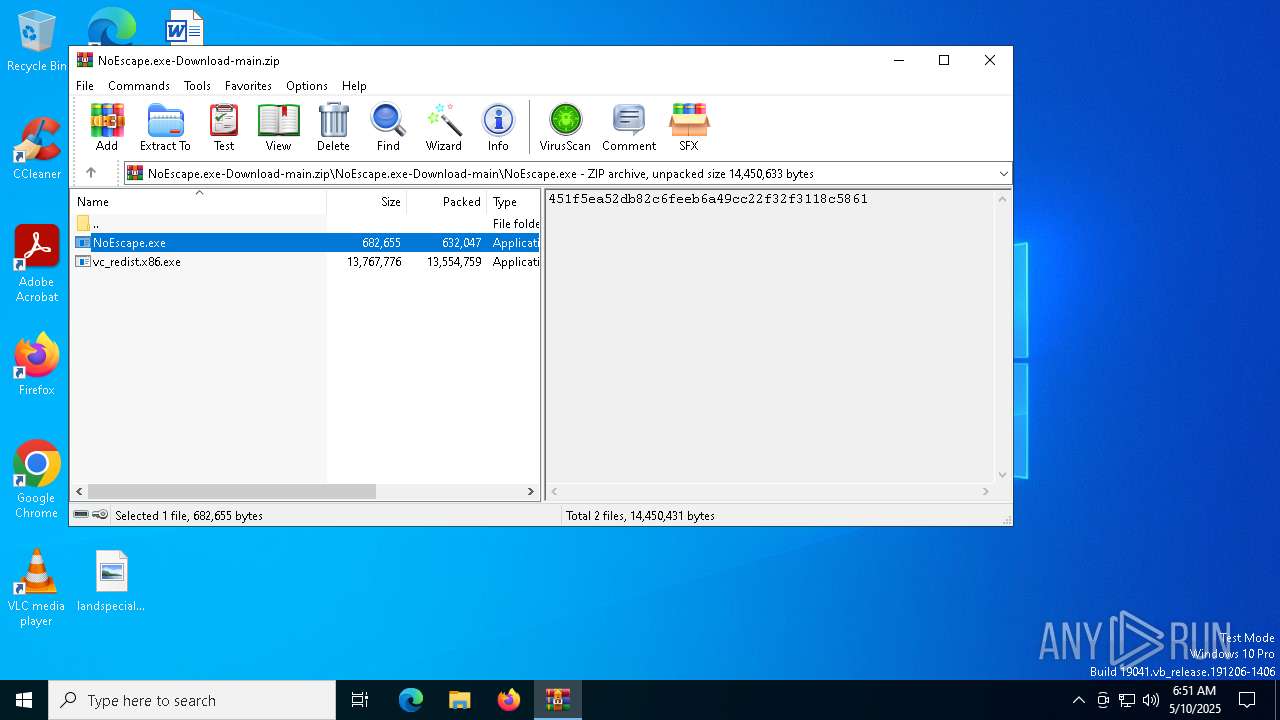
| File name: | NoEscape.exe-Download-main.zip |
| Full analysis: | https://app.any.run/tasks/b871786a-a308-453b-a8e3-8daa69a8ebca |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 06:51:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 6DA84FD648C8811CC112F4FFFE20A24D |
| SHA1: | BA4F8D7FB51EE0A31B068CCA51D5E5388C4B081B |
| SHA256: | 7B55DFAB141EB69ABBE47267E396FE8EE6BC4054FC8D4A5D91049B950C7D84AA |
| SSDEEP: | 393216:8mpOKhF/fEB5KyYEvARy5DiydlufgDaDh5Z8sJzOvhz9R:8uB3f7koRseynegDU8sJzQR |
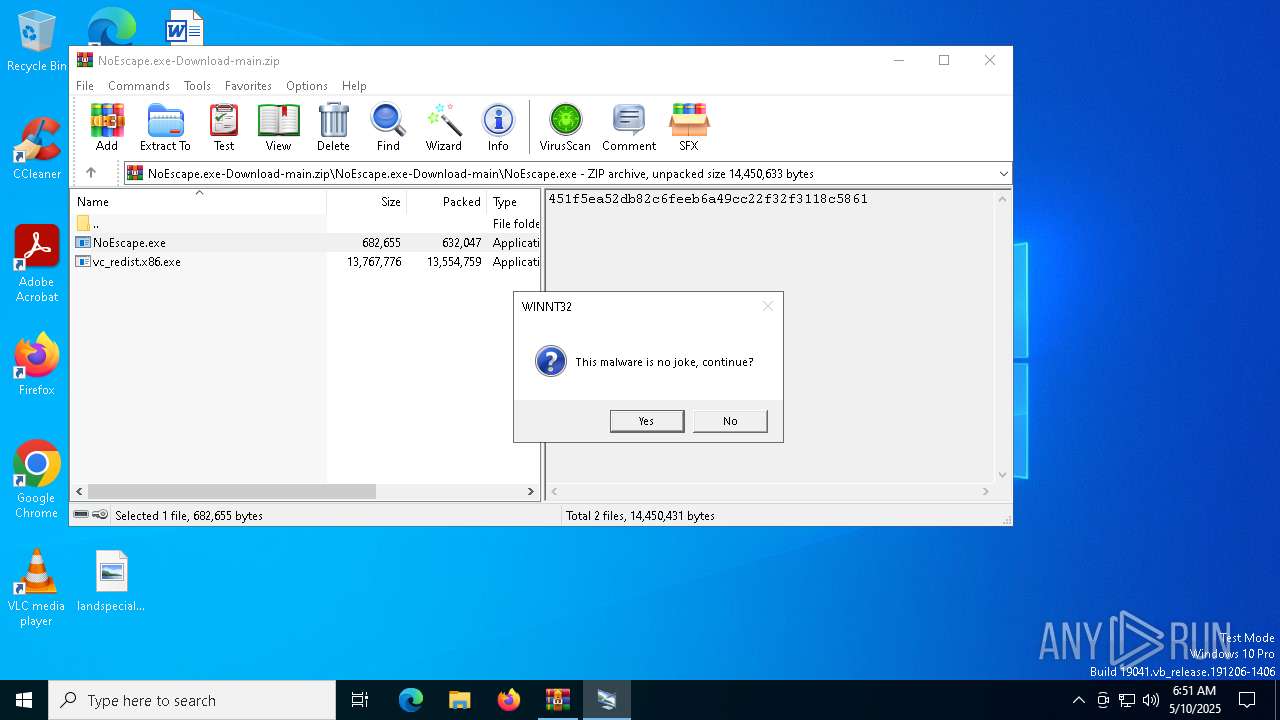
MALICIOUS
Generic archive extractor
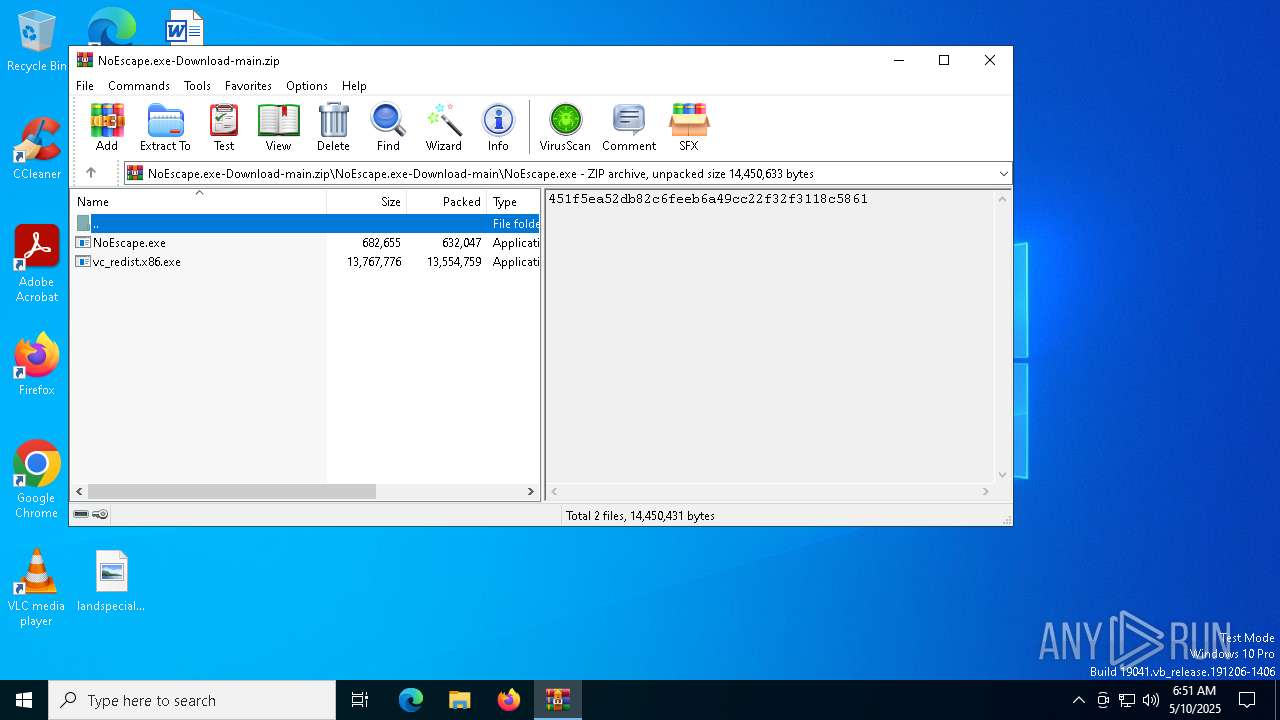
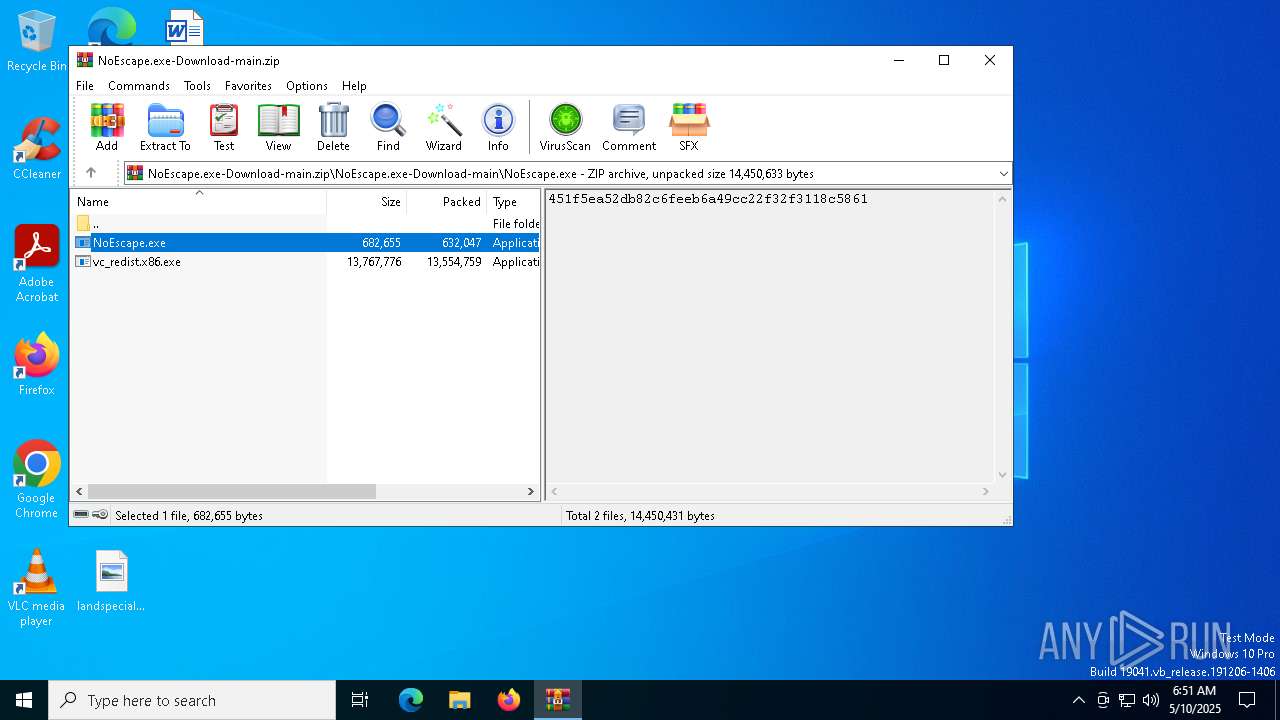
- WinRAR.exe (PID: 5868)
NOESCAPE has been detected
- NoEscape.exe (PID: 7148)
Disables the Shutdown in the Start menu
- NoEscape.exe (PID: 7148)
UAC/LUA settings modification
- NoEscape.exe (PID: 7148)
Changes the login/logoff helper path in the registry
- NoEscape.exe (PID: 7148)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5868)
- NoEscape.exe (PID: 5548)
- ShellExperienceHost.exe (PID: 1272)
Application launched itself
- NoEscape.exe (PID: 5548)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5868)
Executable content was dropped or overwritten
- NoEscape.exe (PID: 7148)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5868)
- NoEscape.exe (PID: 7148)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5868)
Reads the computer name
- NoEscape.exe (PID: 5548)
- NoEscape.exe (PID: 7148)
- ShellExperienceHost.exe (PID: 1272)
Checks supported languages
- NoEscape.exe (PID: 7148)
- NoEscape.exe (PID: 5548)
- ShellExperienceHost.exe (PID: 1272)
Process checks computer location settings
- NoEscape.exe (PID: 5548)
Creates files or folders in the user directory
- NoEscape.exe (PID: 7148)
Creates files in the program directory
- NoEscape.exe (PID: 7148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:03:25 03:55:22 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | NoEscape.exe-Download-main/ |
Total processes
132
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5868.21661\NoEscape.exe-Download-main\NoEscape.exe\NoEscape.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5868.21661\NoEscape.exe-Download-main\NoEscape.exe\NoEscape.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Endermanch Integrity Level: MEDIUM Description: Windows Customization Tool Exit code: 0 Version: 6.6.6.6 Modules
| |||||||||||||||
| 5868 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\NoEscape.exe-Download-main.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7148 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5868.21661\NoEscape.exe-Download-main\NoEscape.exe\NoEscape.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5868.21661\NoEscape.exe-Download-main\NoEscape.exe\NoEscape.exe | NoEscape.exe | ||||||||||||
User: admin Company: Endermanch Integrity Level: HIGH Description: Windows Customization Tool Exit code: 0 Version: 6.6.6.6 Modules
| |||||||||||||||
Total events
3 747
Read events
3 726
Write events
21
Delete events
0
Modification events
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NoEscape.exe-Download-main.zip | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7148) NoEscape.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | AutoRestartShell |
Value: 0 | |||
| (PID) Process: | (7148) NoEscape.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | AutoColorization |
Value: 1 | |||
Executable files
3
Suspicious files
166
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5868.21661\NoEscape.exe-Download-main\NoEscape.exe\NoEscape.exe | executable | |
MD5:989AE3D195203B323AA2B3ADF04E9833 | SHA256:D30D7676A3B4C91B77D403F81748EBF6B8824749DB5F860E114A8A204BCA5B8F | |||
| 5868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5868.21661\NoEscape.exe-Download-main\README.md | text | |
MD5:2B4D5EE9469B56EF5AA2231EAAF1830F | SHA256:C20BA8D1782BE19B680E2E8A5BBAB3BD28FB4F69196B5ACB572A3F08EAAA2968 | |||
| 7148 | NoEscape.exe | C:\ProgramData\Microsoft\User Account Pictures\user.bmp | image | |
MD5:2AB3698B005B421349512142ED6B965E | SHA256:150E95DA6C1E09511241130DA0E376878F5E24E21C2A9DFE7FBCC1022660E29F | |||
| 7148 | NoEscape.exe | C:\ProgramData\Microsoft\User Account Pictures\user-40.png | image | |
MD5:D8E22EF10BD7AB65F56220D2845D6A94 | SHA256:B115A4548AD8E9C7CADB707A0FF79FCD55D9D900EEFA7A922CA50C85C4D3CA1D | |||
| 5868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5868.21661\NoEscape.exe-Download-main\NoEscape.exe\vc_redist.x86.exe | executable | |
MD5:1A15E6606BAC9647E7AD3CAA543377CF | SHA256:FDD1E1F0DCAE2D0AA0720895EFF33B927D13076E64464BB7C7E5843B7667CD14 | |||
| 7148 | NoEscape.exe | C:\ProgramData\Microsoft\User Account Pictures\user.png | image | |
MD5:96F17C361A25164E71716D5BB56CB3D8 | SHA256:1025314EF977B5D07041B8B73E4ADBEA779E5E06096C3C66BD1F06FBBBA7FD1C | |||
| 7148 | NoEscape.exe | C:\Users\admin\AppData\Local\noescape.png | image | |
MD5:9E655CFD3D501F1ED01D6A2E0DB0E744 | SHA256:CF7B5334E06A13501821834CD1AEDB7C3306A543F7D8EC03D1F20BFAF9BED613 | |||
| 7148 | NoEscape.exe | C:\ProgramData\Microsoft\User Account Pictures\user-48.png | image | |
MD5:C7572C5706CA8D652D6B87787AE7F5B2 | SHA256:37C63EE5D26FB77F8E697FAEC3891673E40C449BF8411CFF806D852AE7506ADA | |||
| 7148 | NoEscape.exe | C:\ProgramData\Microsoft\User Account Pictures\user-192.png | image | |
MD5:6BF949C62C5E9D07593BA5B604E36773 | SHA256:E54EA8405024F1FA72E470417059BDD186B0A3836F7D5E1C2C95C6003383912F | |||
| 7148 | NoEscape.exe | C:\Users\Public\Desktop\⛴┆〔ᣰ⫟ᕔ⌿ᵓዩᓷဌᠯῂ⺮⼥མ☺ᘢක∍ोᮌཱུళॼ᷻ᖰ⟏ | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
15
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |