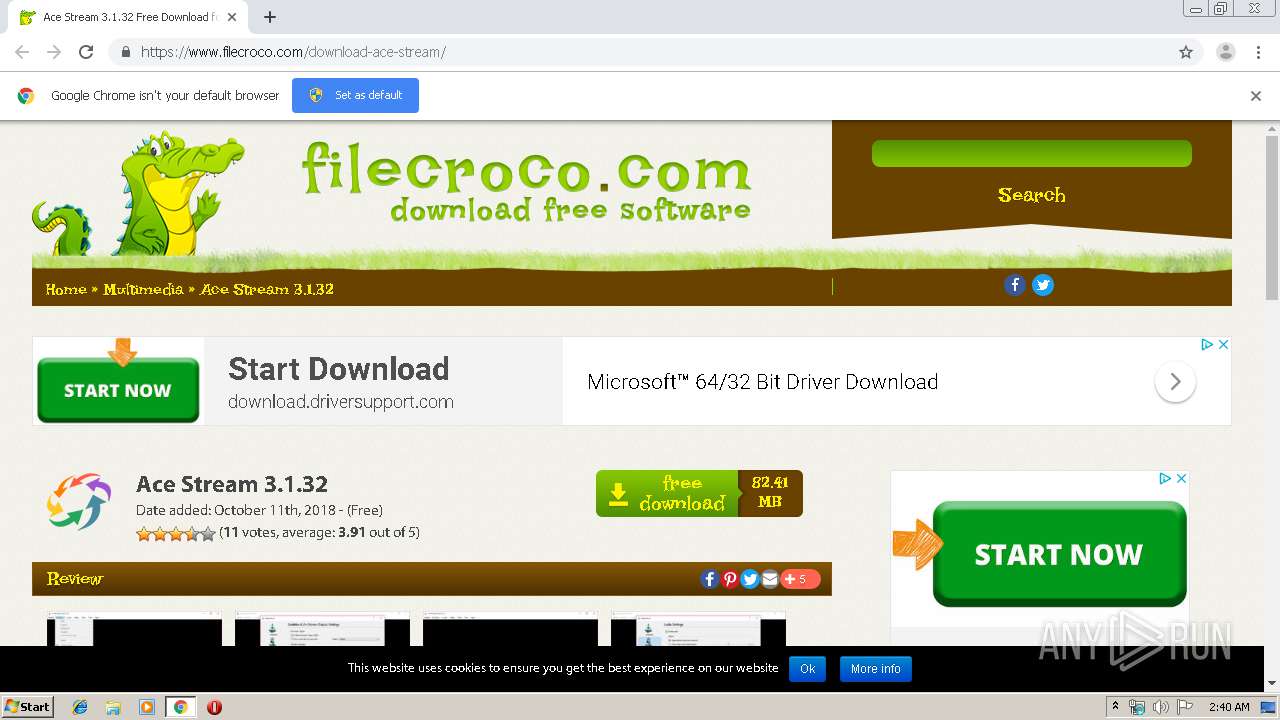
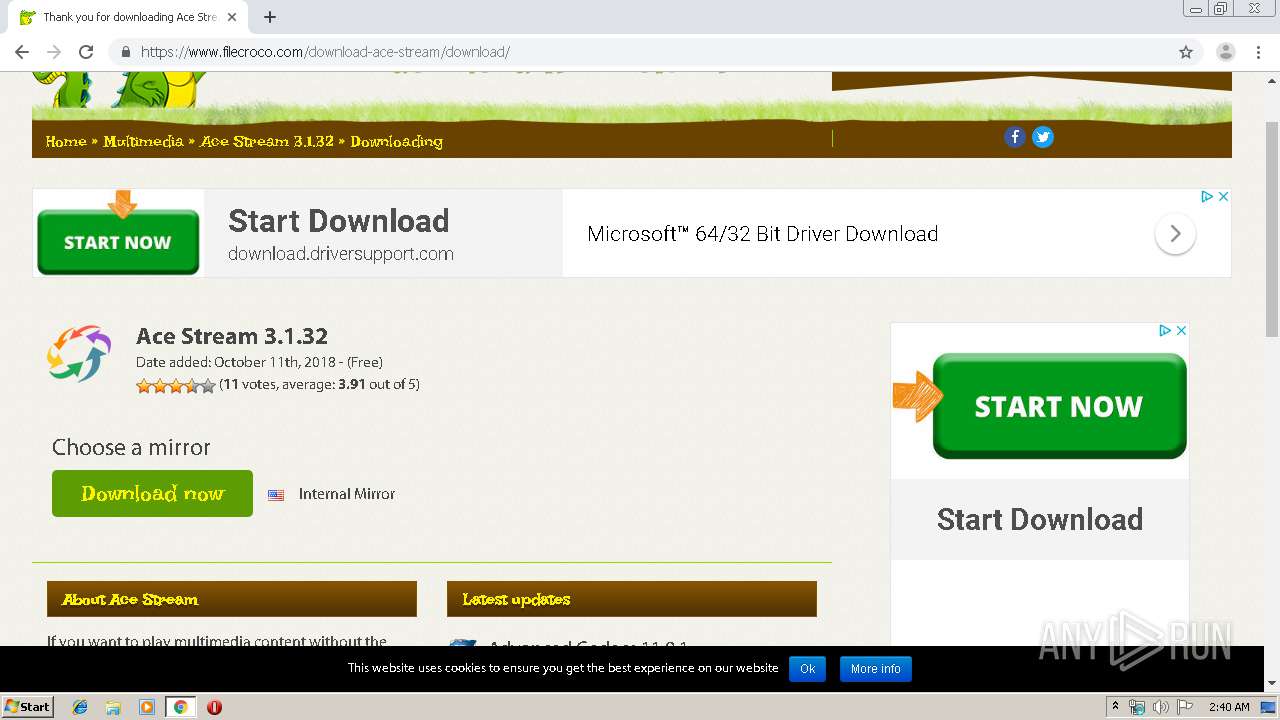
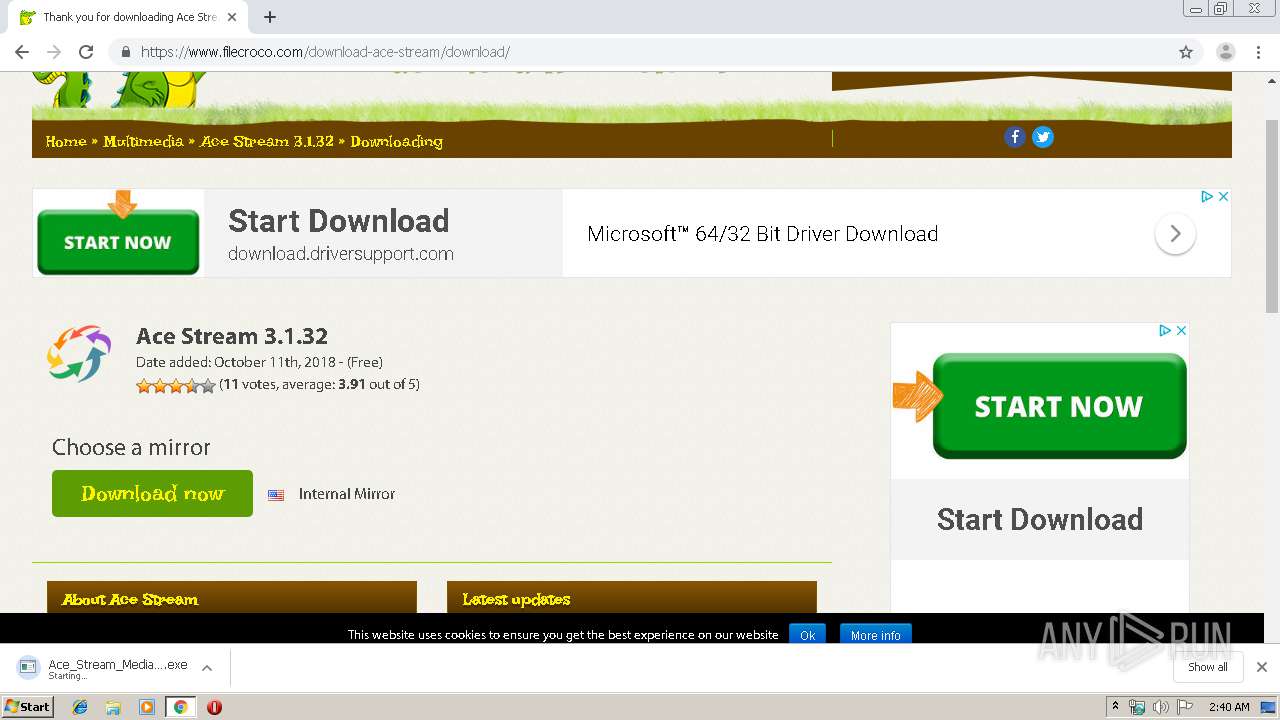
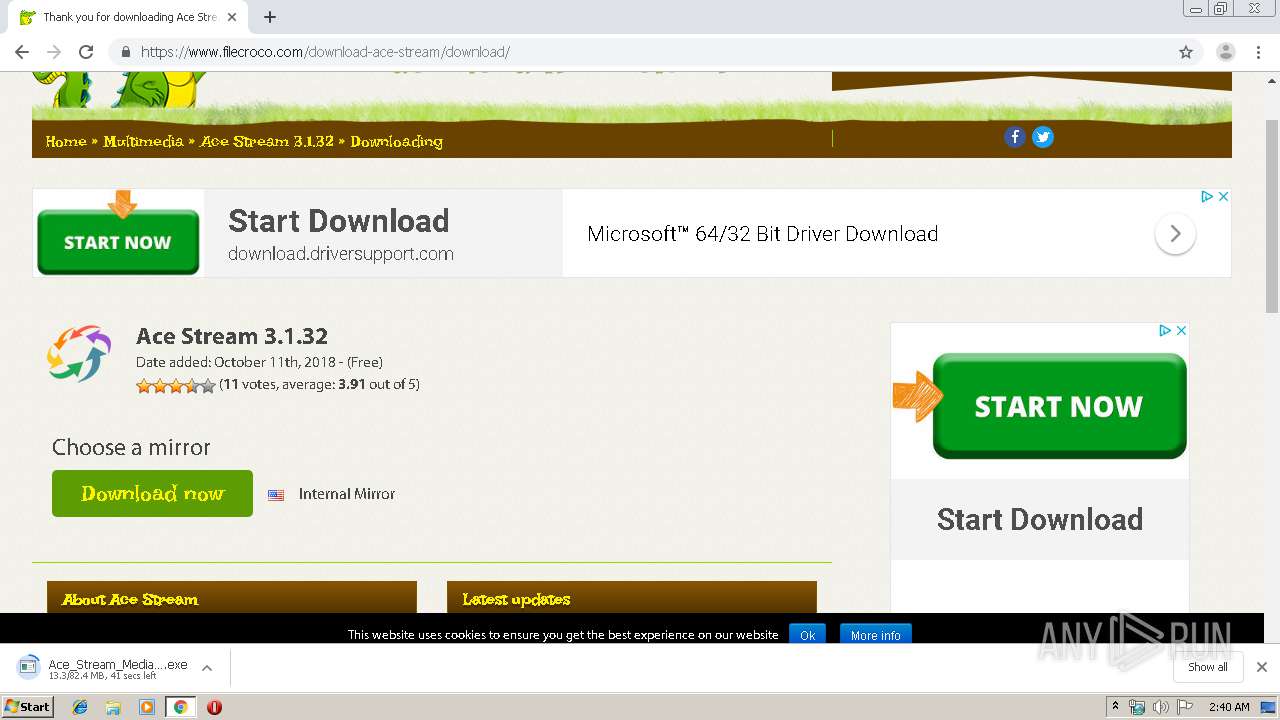
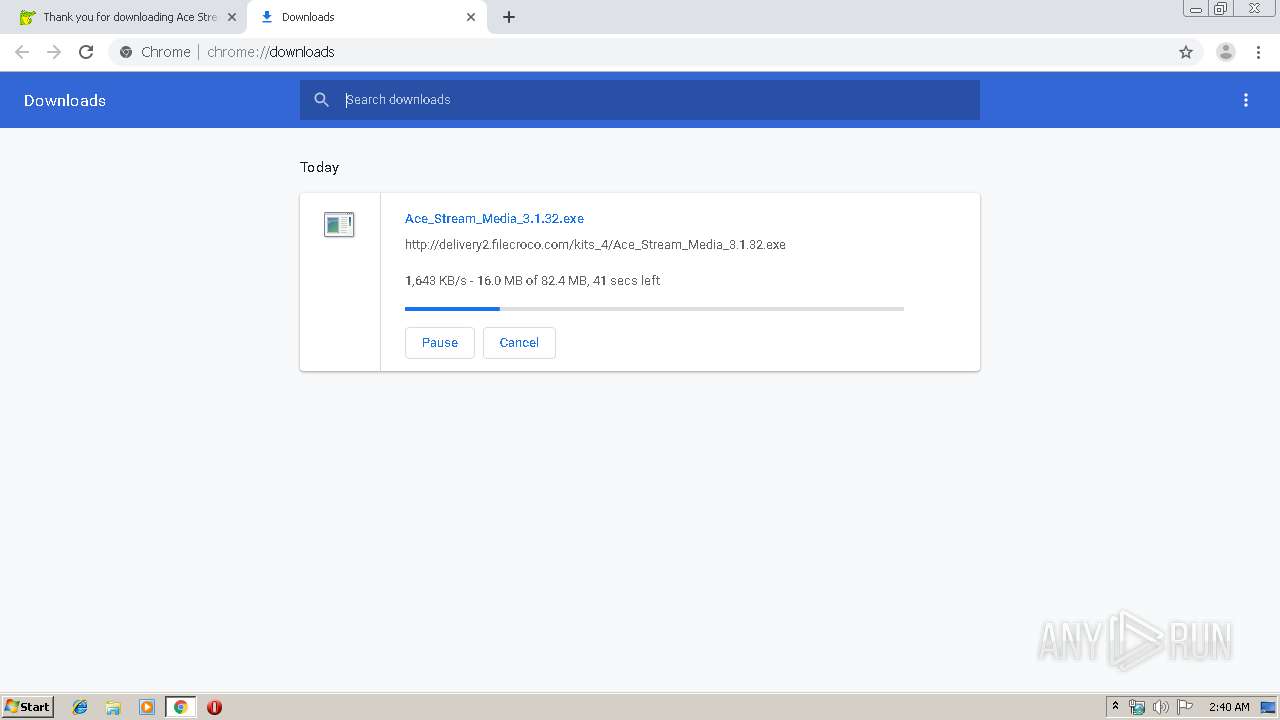
| URL: | https://www.filecroco.com/download-ace-stream/ |
| Full analysis: | https://app.any.run/tasks/c5925708-fbad-44fb-9daa-ab66f690d03a |
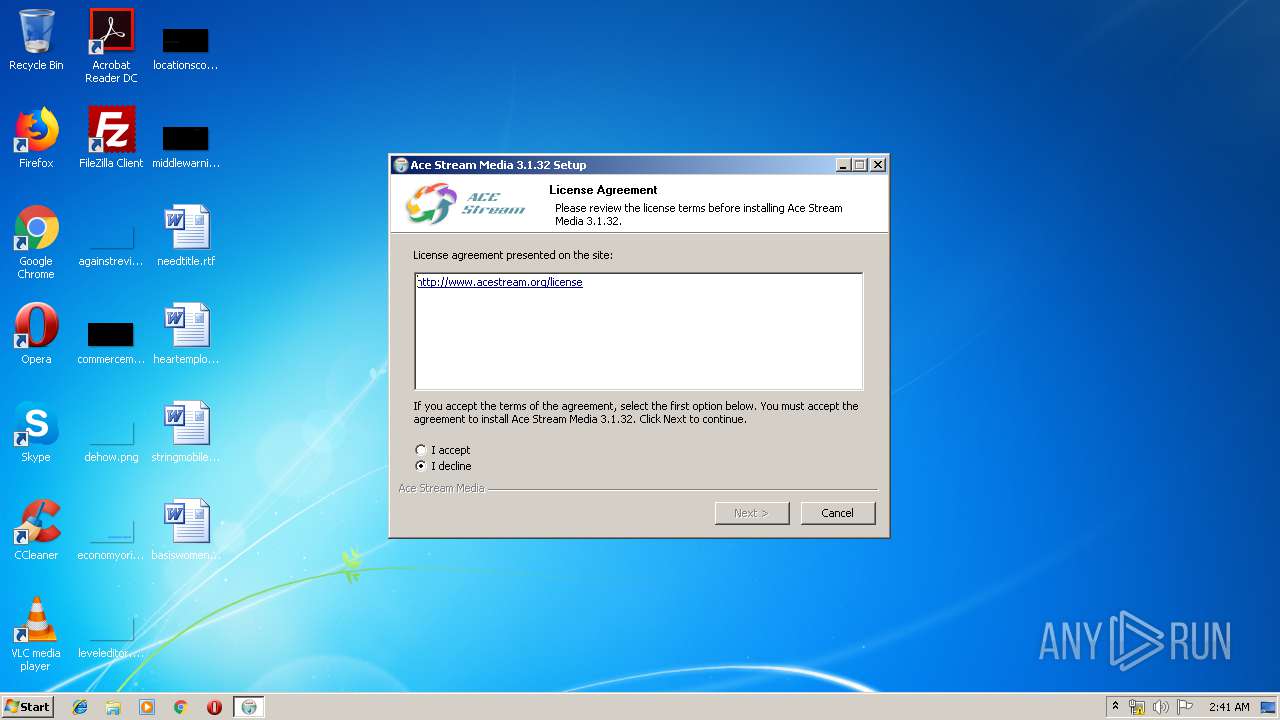
| Verdict: | Malicious activity |
| Analysis date: | August 18, 2019, 01:39:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C7733EF183EC5F4C3F8DB97CECC46604 |
| SHA1: | E66D698A243D7C73BA264990B7B563711E7242F6 |
| SHA256: | 7B2FB50092AF6DE687C0C8F2CE93E4AC35A8FB80CF07528247CDC892F92A0C1E |
| SSDEEP: | 3:N8DSLQpXKH8JEVQhK:2OLQpXKcKVQhK |
MALICIOUS
Application was dropped or rewritten from another process
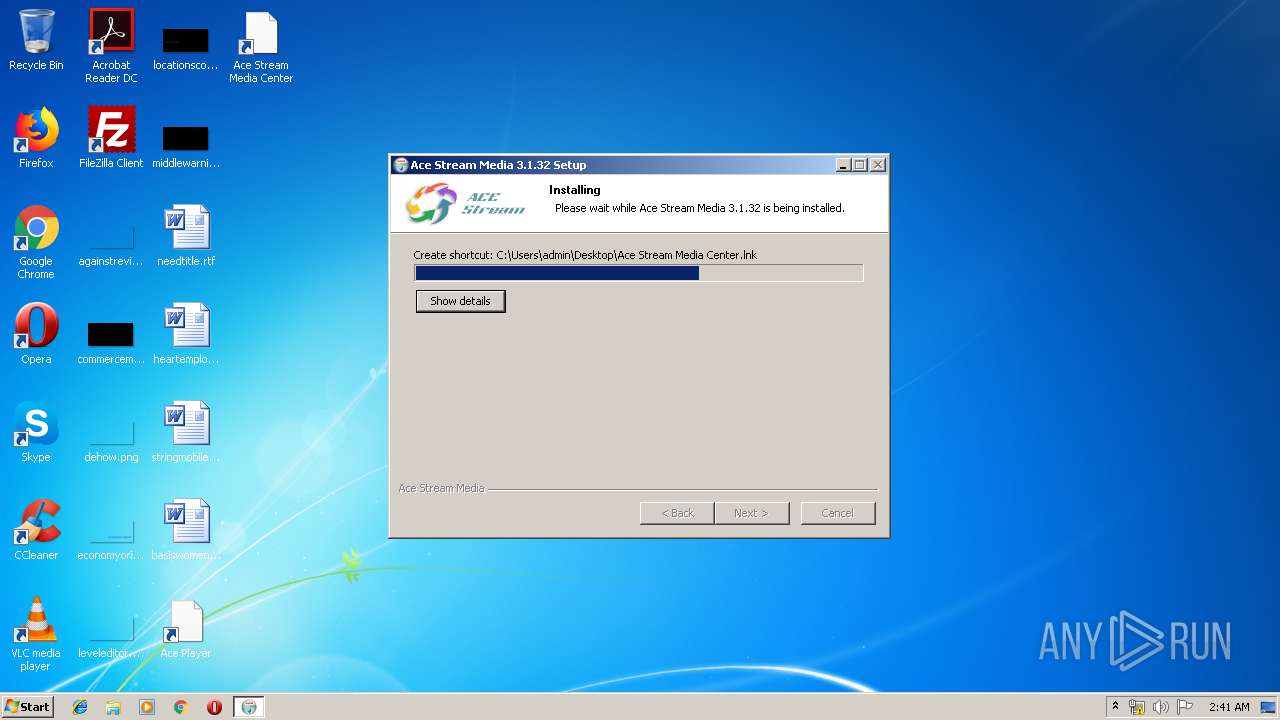
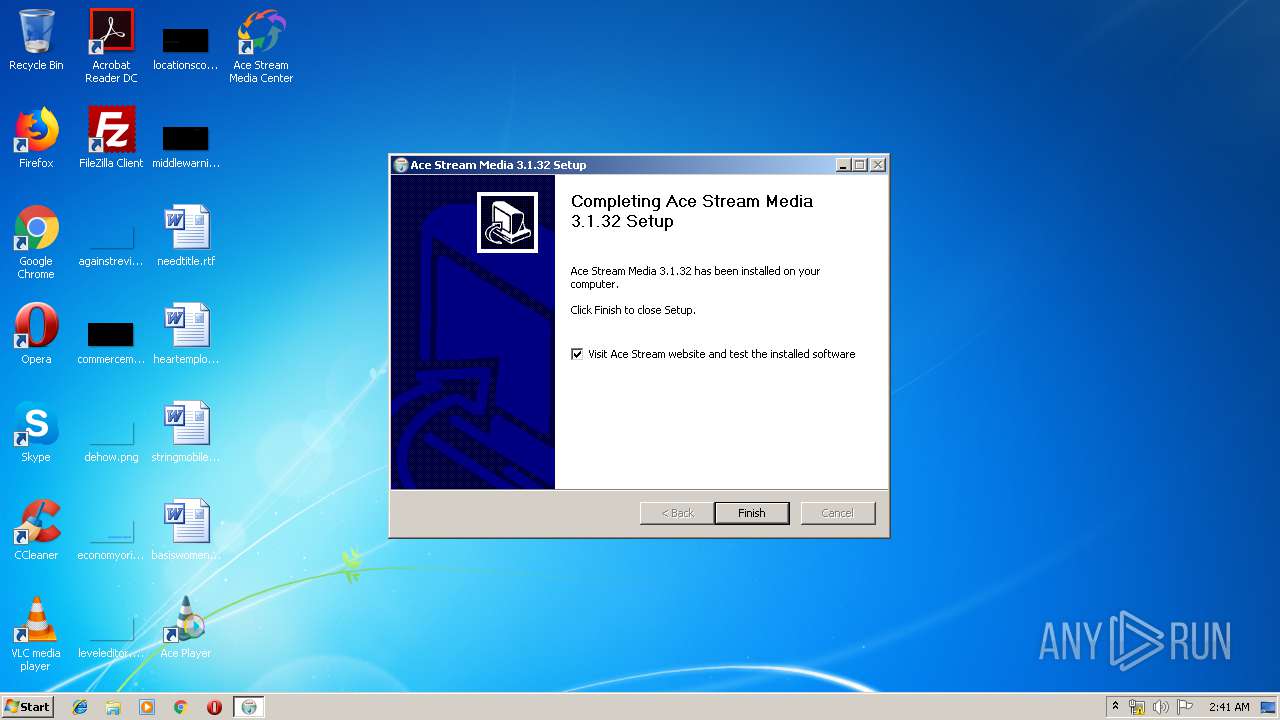
- Ace_Stream_Media_3.1.32.exe (PID: 1008)
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
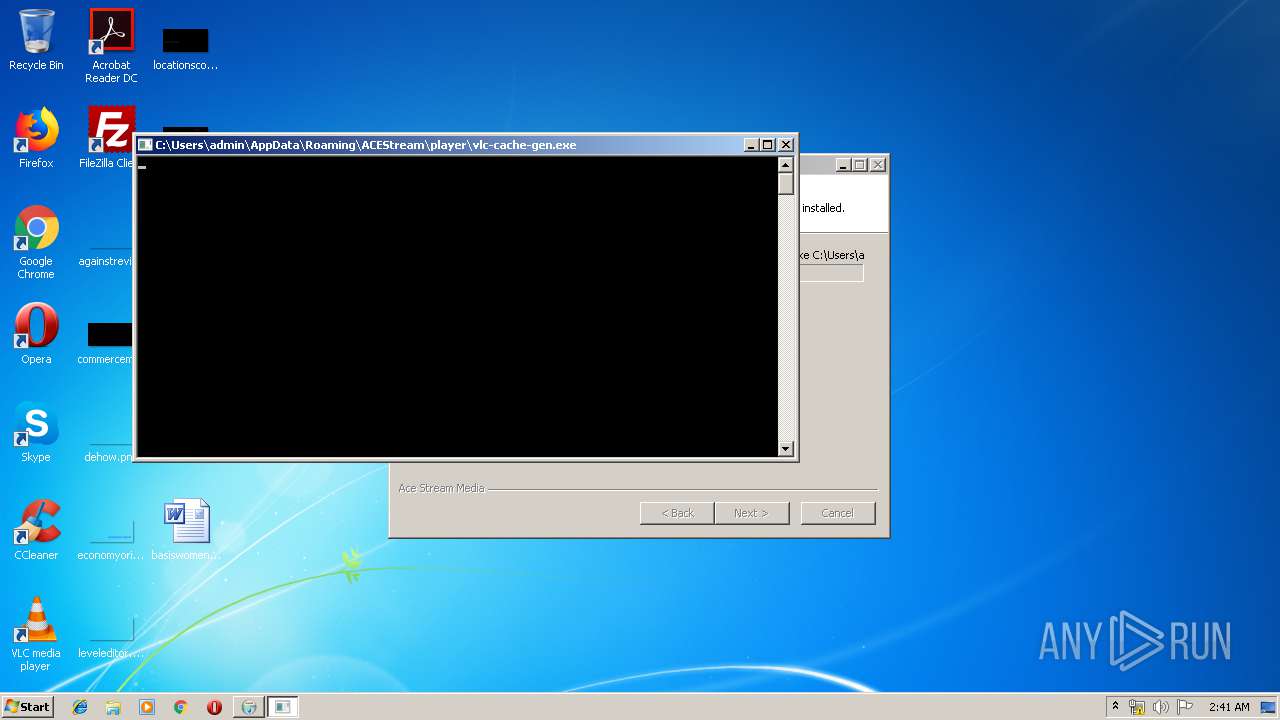
- vlc-cache-gen.exe (PID: 3676)
- ace_engine.exe (PID: 3160)
- ace_engine.exe (PID: 3484)
Loads dropped or rewritten executable
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
- vlc-cache-gen.exe (PID: 3676)
- ace_engine.exe (PID: 3160)
Changes the autorun value in the registry
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2792)
Executable content was dropped or overwritten
- chrome.exe (PID: 2792)
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
Creates COM task schedule object
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
Modifies the open verb of a shell class
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
Creates a software uninstall entry
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
Creates files in the user directory
- vlc-cache-gen.exe (PID: 3676)
- ace_engine.exe (PID: 3160)
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
Loads Python modules
- ace_engine.exe (PID: 3160)
- ace_engine.exe (PID: 3484)
Starts CMD.EXE for commands execution
- ace_engine.exe (PID: 3160)
- NETSTAT.EXE (PID: 1816)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3360)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3100)
Application launched itself
- ace_engine.exe (PID: 3160)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 4080)
INFO
Application launched itself
- chrome.exe (PID: 2792)
Reads Internet Cache Settings
- chrome.exe (PID: 2792)
Changes settings of System certificates
- chrome.exe (PID: 2476)
Dropped object may contain Bitcoin addresses
- Ace_Stream_Media_3.1.32.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
42
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | ipconfig /all | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18341439052994060931 --mojo-platform-channel-handle=3824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7050304929416090868 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\Downloads\Ace_Stream_Media_3.1.32.exe" | C:\Users\admin\Downloads\Ace_Stream_Media_3.1.32.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6045884923895174241 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=42170763596469651 --mojo-platform-channel-handle=4068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | netstat -nr | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7154946739527737426 --mojo-platform-channel-handle=4312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1820987521273858327 --mojo-platform-channel-handle=3920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | C:\Windows\system32\cmd.exe /c "C:\Windows\system32\route.exe" print | C:\Windows\system32\cmd.exe | — | NETSTAT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 635
Read events
1 307
Write events
1 323
Delete events
5
Modification events
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2792-13210565998591250 |
Value: 259 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
363
Suspicious files
85
Text files
893
Unknown types
263
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e907f46b-46fe-4b5f-91b0-4733588d8f66.tmp | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169c93.TMP | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
88
DNS requests
59
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
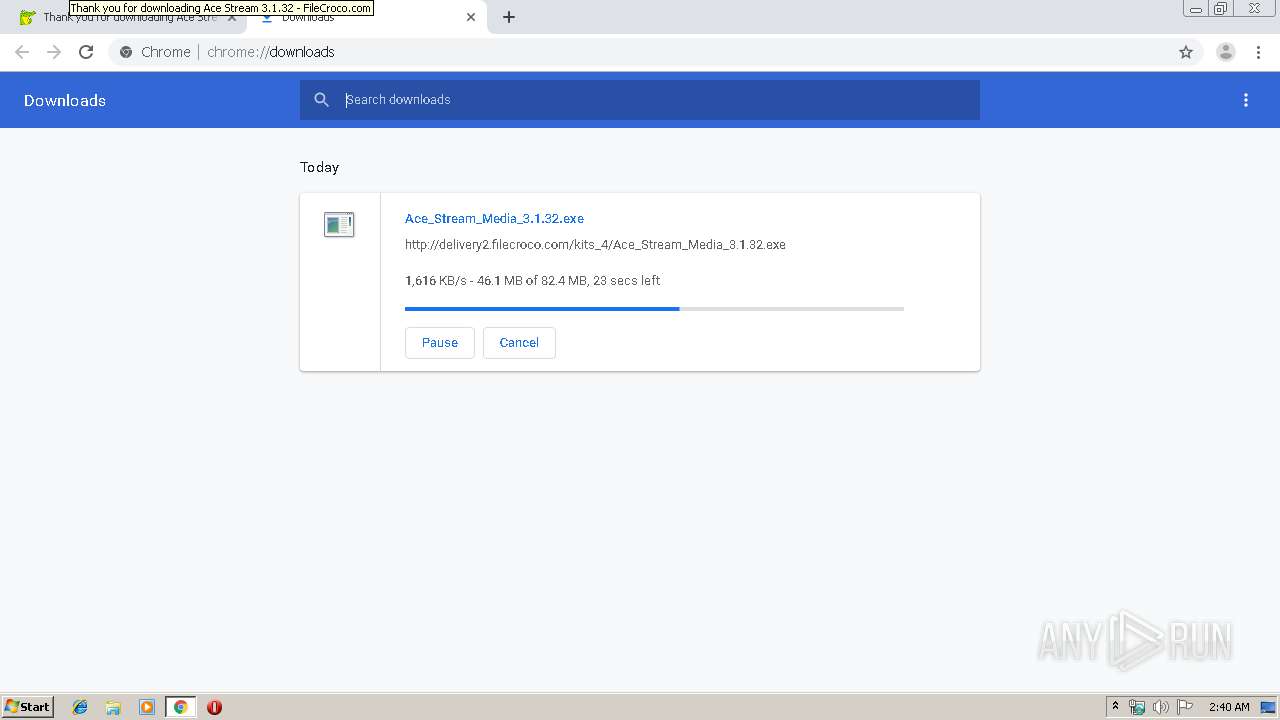
2476 | chrome.exe | GET | — | 185.132.177.118:80 | http://delivery2.filecroco.com/kits_4/Ace_Stream_Media_3.1.32.exe | AE | — | — | suspicious |
3160 | ace_engine.exe | GET | 200 | 148.251.41.164:80 | http://installer-api.acestream.org/run?a=%7B9D369E6A-B3EA-4315-8982-05F03B075245%7D&_v=3013200&_p=win32&_r=58938e3&_n=3.1.32 | DE | — | — | suspicious |
2476 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3160 | ace_engine.exe | GET | 200 | 148.251.41.163:80 | http://ts.acestream.net/init?a=1566092535 | DE | binary | 31 b | suspicious |
2476 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
— | — | GET | 200 | 148.251.41.165:80 | http://s4.torrentstream.org/c?_n=3.1.32&_p=win32&_r=549495385&_t=1566092535&_v=3013200&_s=cbbc1d6c56750838f0d30552dbef0e100f7f2b31 | DE | text | 206 b | suspicious |
— | — | GET | 200 | 148.251.41.165:80 | http://s4.torrentstream.net/a?_n=3.1.32&_p=win32&_r=42048136&_t=1566092535&_v=3013200&_s=163539de356dd14c3e0af96c290048ef1f312f27 | DE | text | 208 b | suspicious |
— | — | GET | 200 | 148.251.41.165:80 | http://s4.torrentstream.org/data/m-bb407234557cd62624f8e9b623e954c053ec0b266ecbac164ac1b909f70806ef.gz | DE | compressed | 633 b | suspicious |
— | — | GET | 200 | 193.0.6.142:80 | http://rdap.db.ripe.net/ip/185.76.9.67 | NL | text | 2.13 Kb | suspicious |
— | — | GET | 200 | 148.251.41.165:80 | http://s4.torrentstream.org/b?_n=3.1.32&_p=win32&_r=540479683&_t=1566092536&_v=3013200&_s=c350f802ba3882c7b245d39c3cd827dae14453b6 | DE | text | 207 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2476 | chrome.exe | 172.217.22.34:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
2476 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2476 | chrome.exe | 104.27.167.98:443 | www.filecroco.com | Cloudflare Inc | US | shared |
2476 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2476 | chrome.exe | 104.19.196.151:443 | ajax.cloudflare.com | Cloudflare Inc | US | shared |
2476 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2476 | chrome.exe | 172.217.18.98:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2476 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2476 | chrome.exe | 216.58.208.34:443 | adservice.google.co.uk | Google Inc. | US | whitelisted |
2476 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.filecroco.com |
| malicious |
accounts.google.com |
| shared |
ajax.cloudflare.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
clients1.google.com |
| whitelisted |
adservice.google.co.uk |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2476 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2744 | Ace_Stream_Media_3.1.32.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2744 | Ace_Stream_Media_3.1.32.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2744 | Ace_Stream_Media_3.1.32.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2744 | Ace_Stream_Media_3.1.32.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
3160 | ace_engine.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT nodes reply |
3160 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
3160 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
— | — | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |