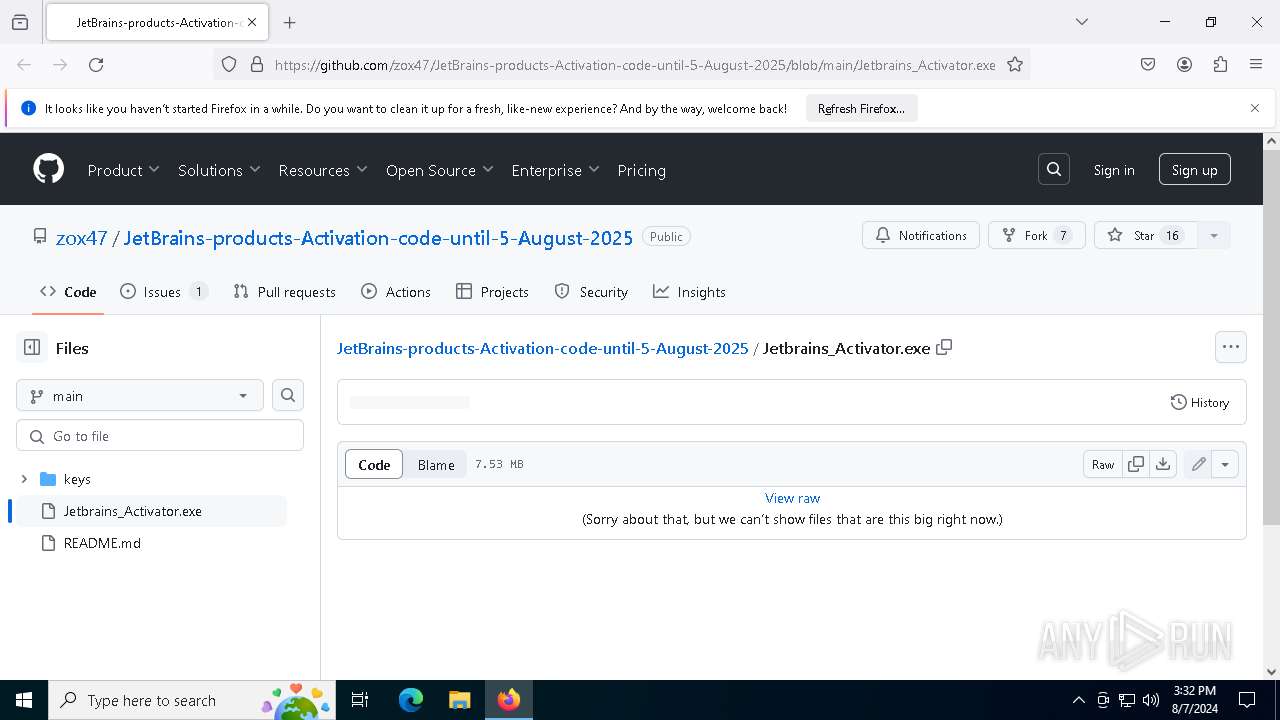
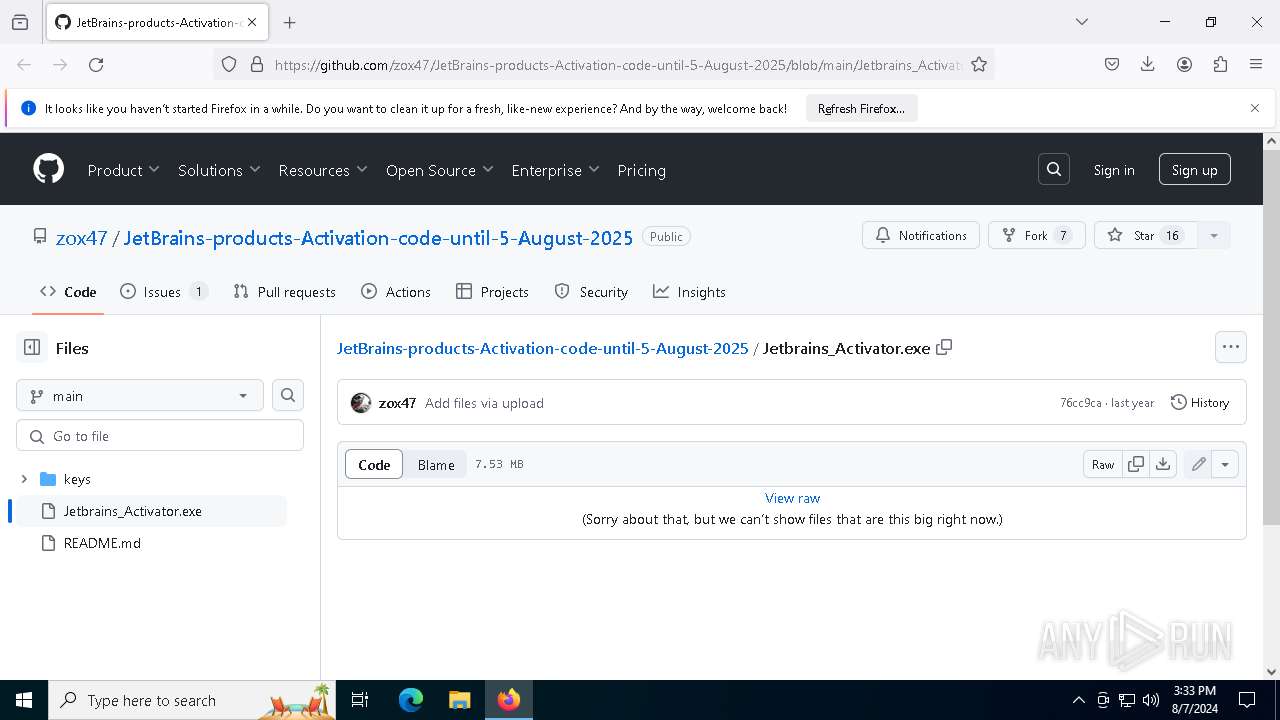
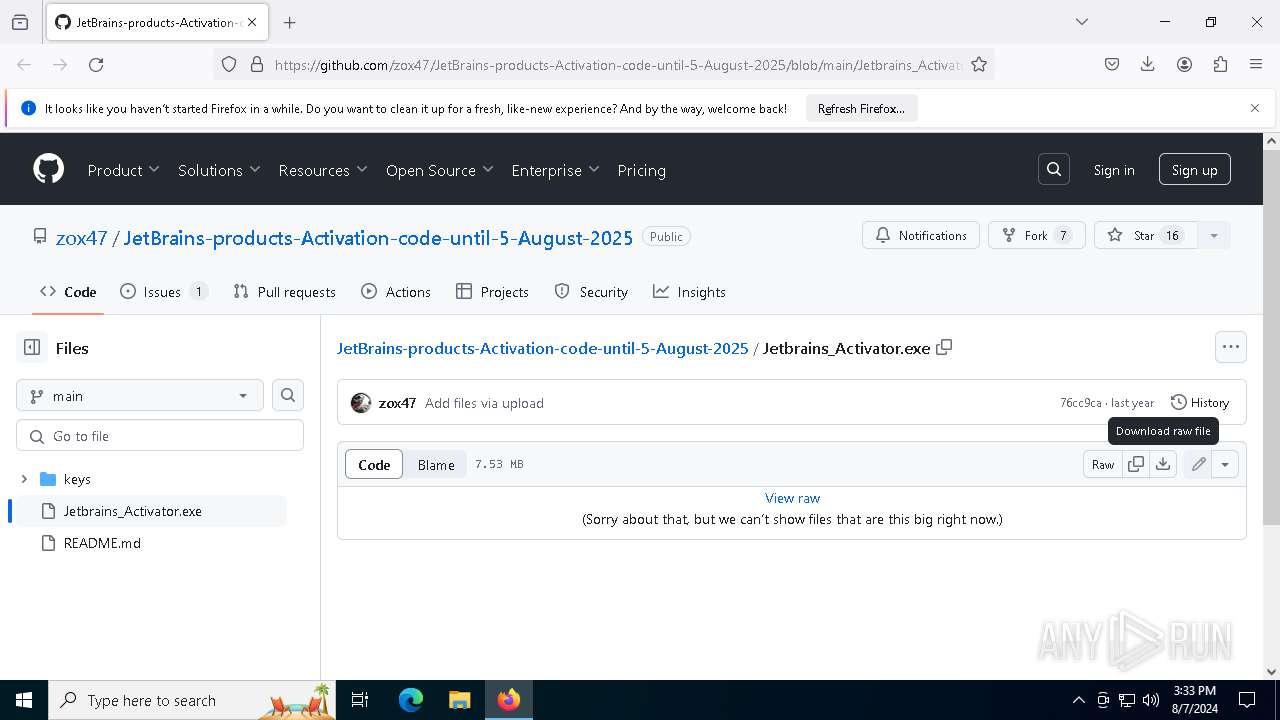
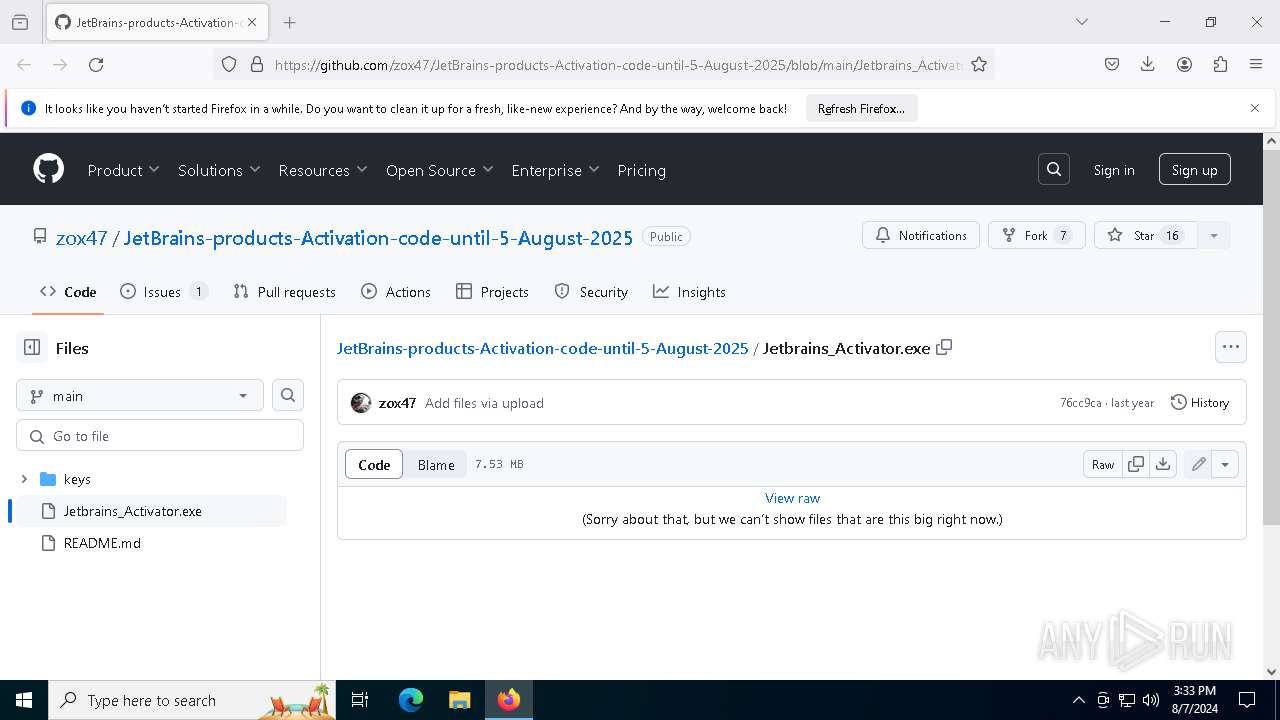
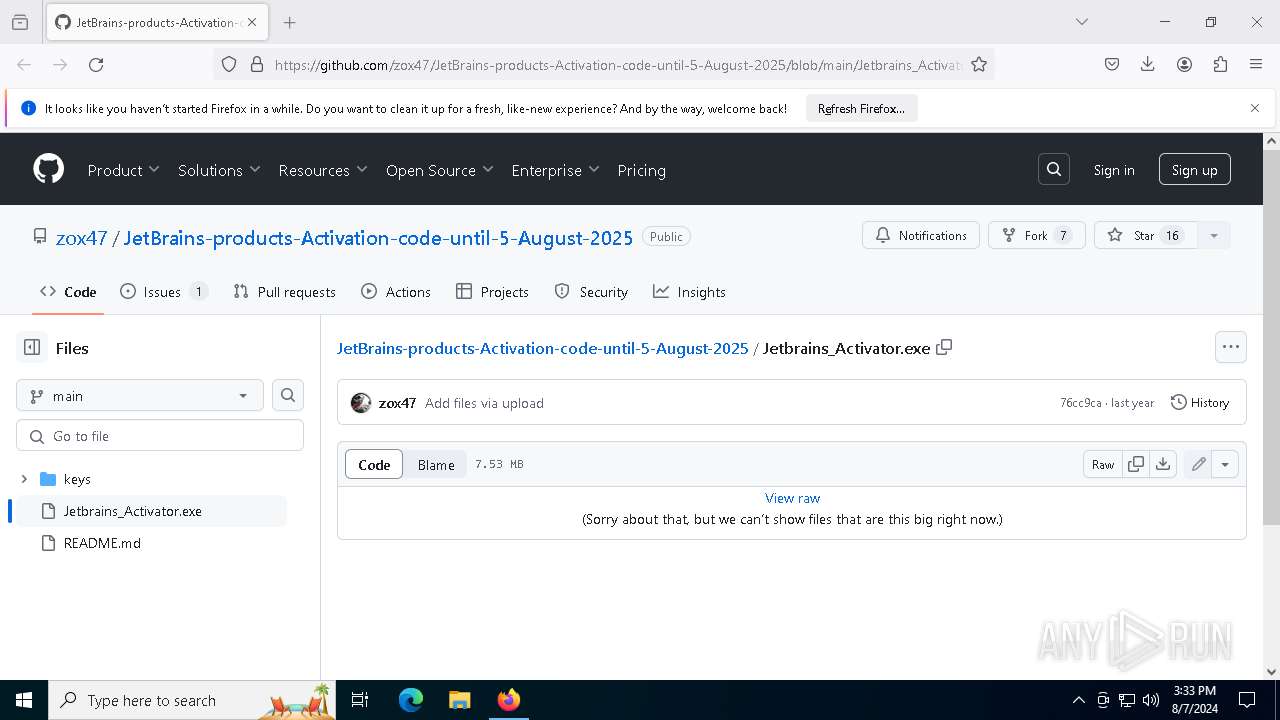
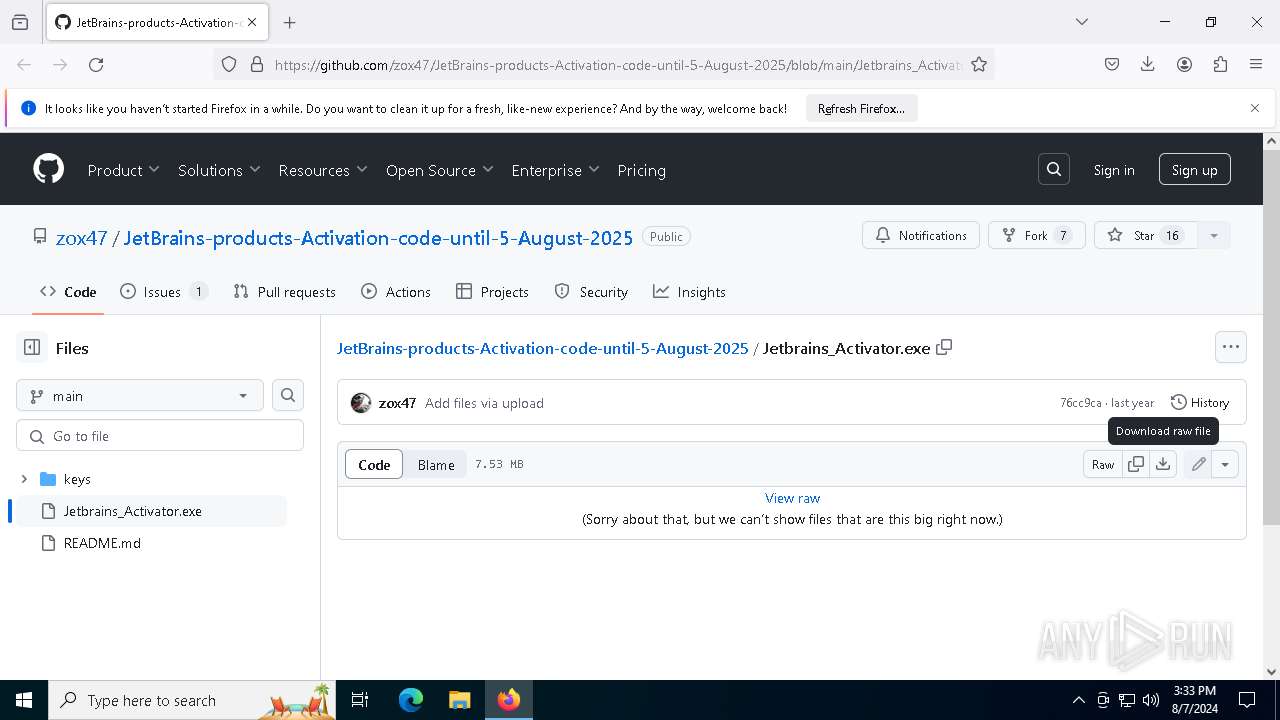
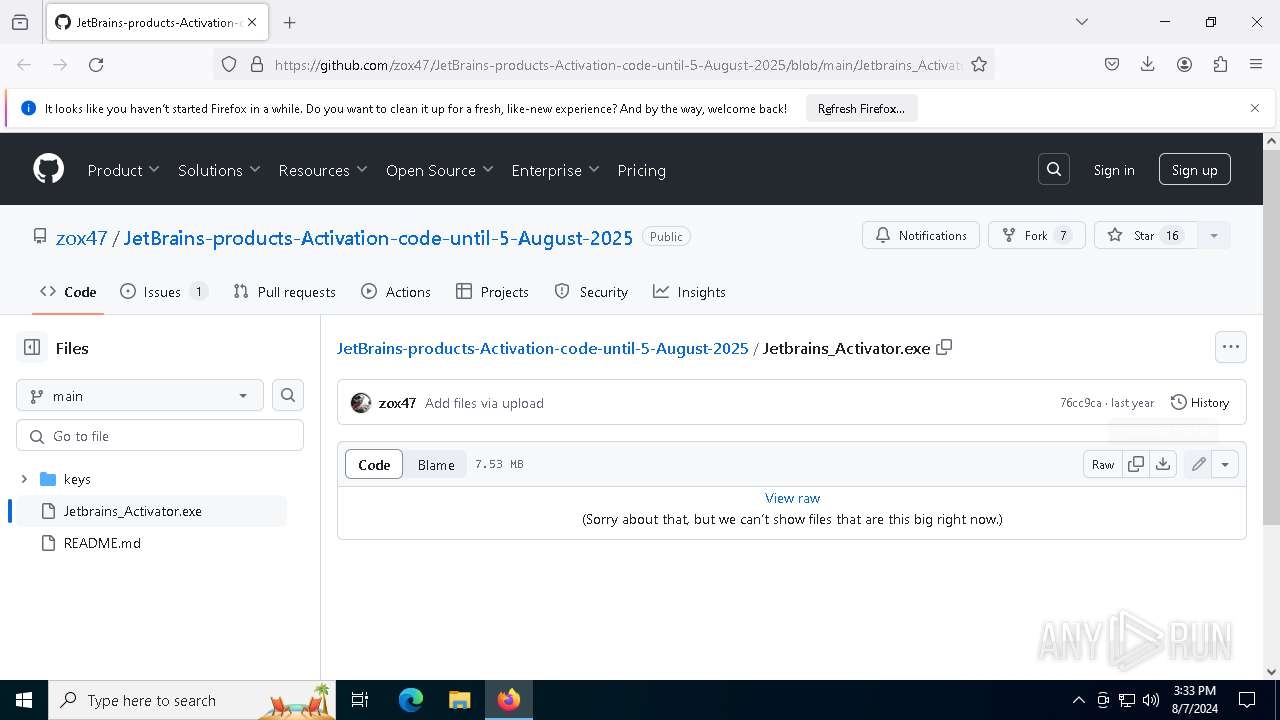
| URL: | https://github.com/zox47/JetBrains-products-Activation-code-until-5-August-2025/blob/main/Jetbrains_Activator.exe |
| Full analysis: | https://app.any.run/tasks/c5df3835-4f48-41cd-98b5-7a78a9dee1d3 |
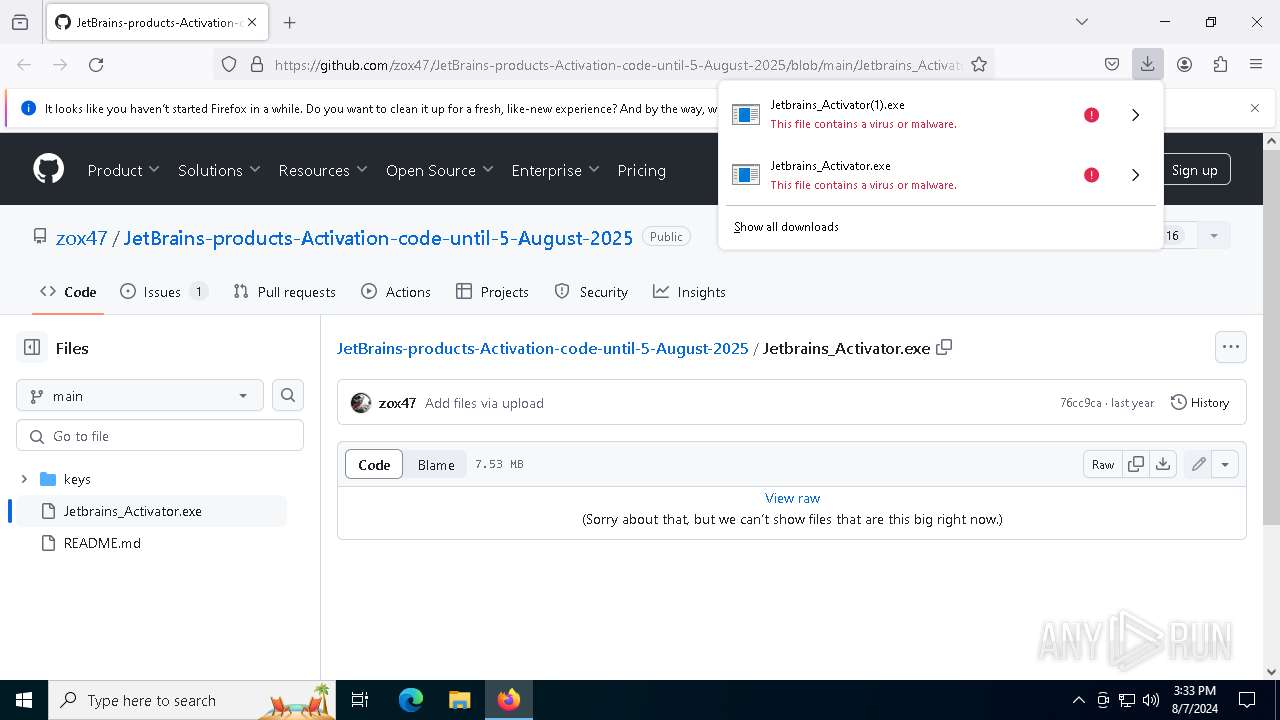
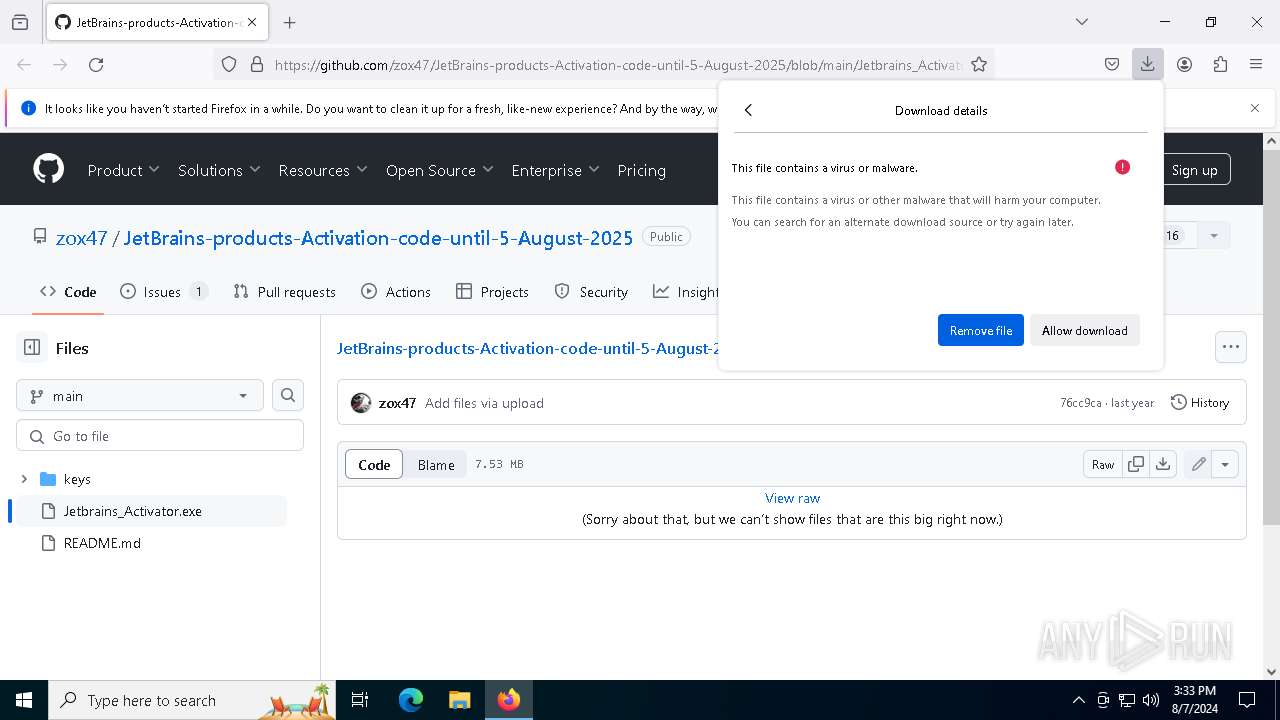
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2024, 15:32:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EF6D4350FAC790A24A7AD10B2C87467E |
| SHA1: | 222F7BCF3C5387BC85F2631679CAEF7C3A3D98C4 |
| SHA256: | 7B1FF2D95E736C2A58F81D7FCBEFCC75735EB9388C41AE64F9CC11A0C8692736 |
| SSDEEP: | 3:N8tEdvGSPVLQmGWZGZRLLuAIQl4iHJMERRYRhe:2u4SNLsWZo/uilXHJMsRye |
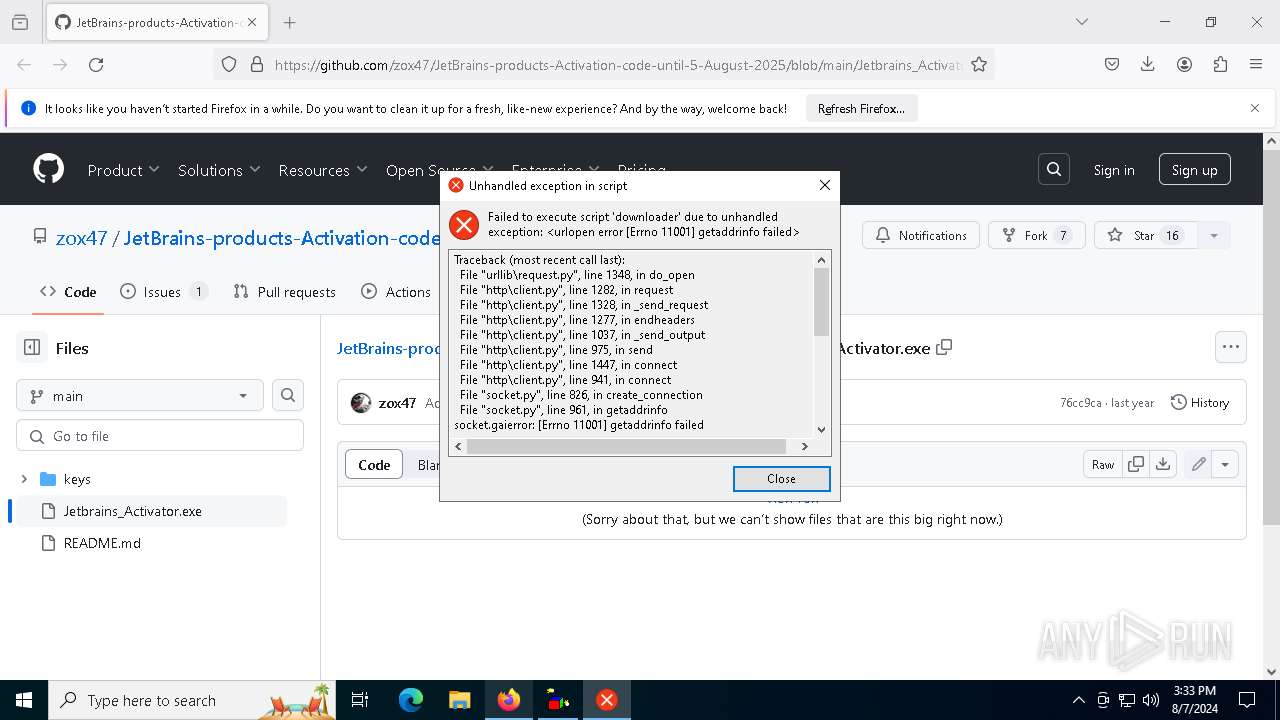
MALICIOUS
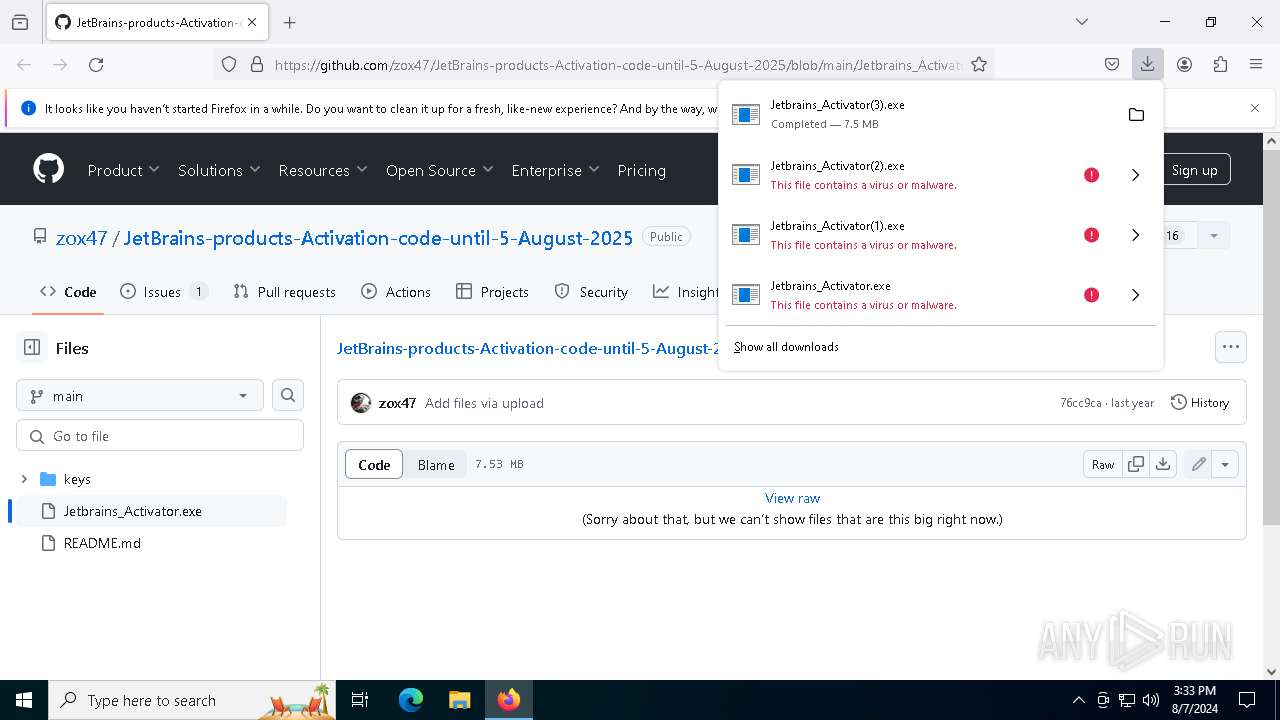
Drops the executable file immediately after the start
- Jetbrains_Activator(3).exe (PID: 8136)
- downloader.exe (PID: 3164)
Adds path to the Windows Defender exclusion list
- downloader.exe (PID: 6284)
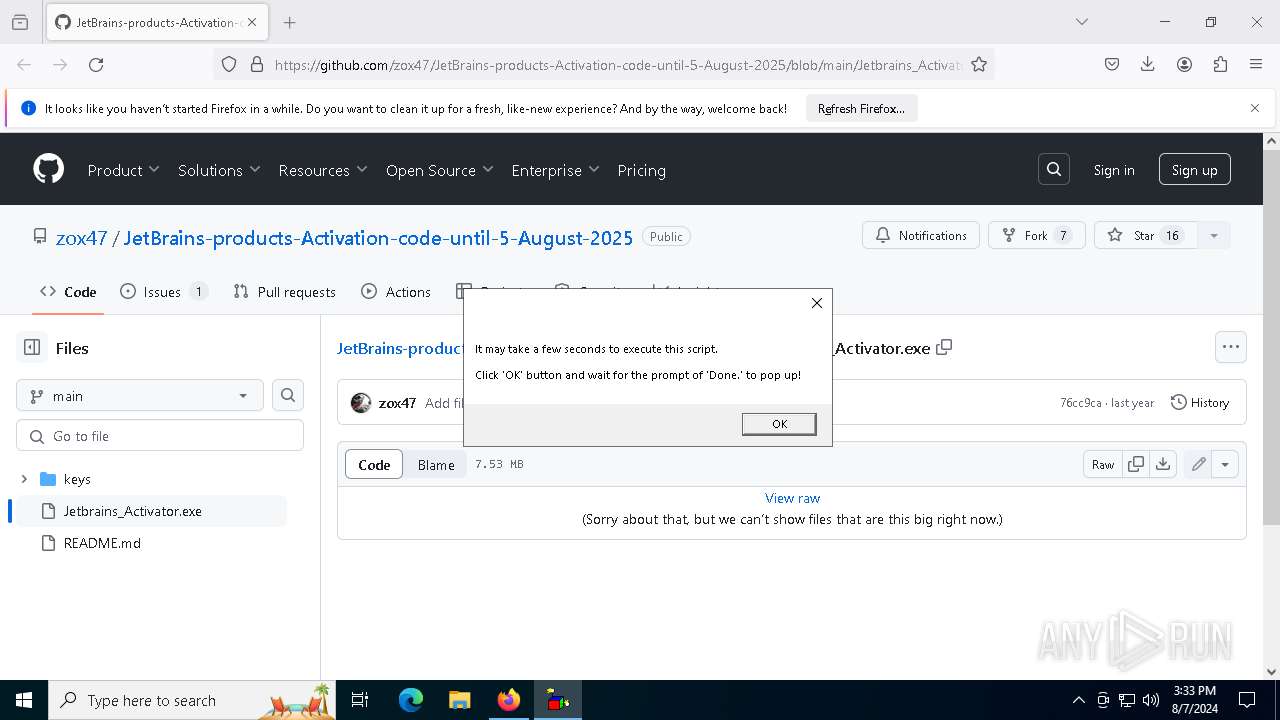
Opens a text file (SCRIPT)
- wscript.exe (PID: 7428)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7428)
SUSPICIOUS
Reads security settings of Internet Explorer
- Jetbrains_Activator(3).exe (PID: 8136)
Executable content was dropped or overwritten
- Jetbrains_Activator(3).exe (PID: 8136)
- downloader.exe (PID: 3164)
Reads the date of Windows installation
- Jetbrains_Activator(3).exe (PID: 8136)
The process drops C-runtime libraries
- downloader.exe (PID: 3164)
Process drops python dynamic module
- downloader.exe (PID: 3164)
Process drops legitimate windows executable
- downloader.exe (PID: 3164)
The process executes VB scripts
- Jetbrains_Activator(3).exe (PID: 8136)
- wscript.exe (PID: 7404)
Script adds exclusion path to Windows Defender
- downloader.exe (PID: 6284)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7404)
- wscript.exe (PID: 7428)
Application launched itself
- wscript.exe (PID: 7404)
- downloader.exe (PID: 3164)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7404)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 7428)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7428)
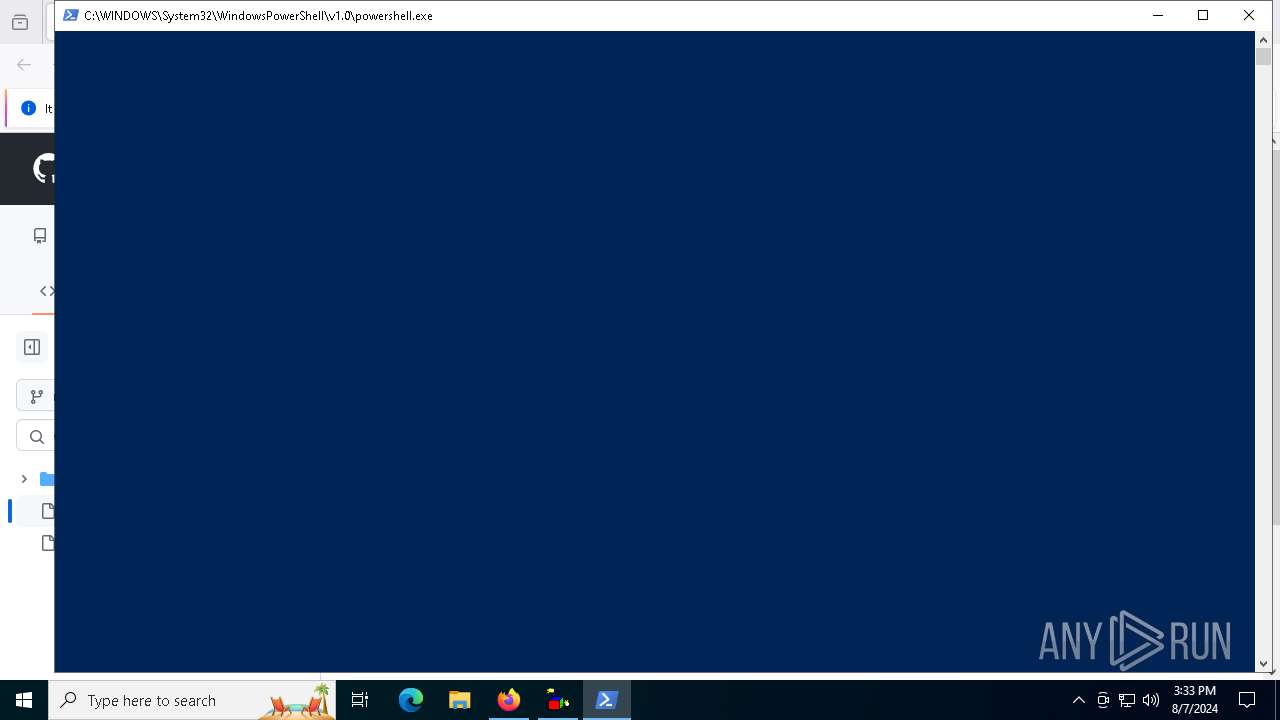
Starts POWERSHELL.EXE for commands execution
- downloader.exe (PID: 6284)
Loads Python modules
- downloader.exe (PID: 6284)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 7428)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7428)
INFO
Application launched itself
- firefox.exe (PID: 6328)
- firefox.exe (PID: 6388)
Executable content was dropped or overwritten
- firefox.exe (PID: 6388)
Reads Microsoft Office registry keys
- firefox.exe (PID: 6388)
Creates files or folders in the user directory
- Jetbrains_Activator(3).exe (PID: 8136)
The process uses the downloaded file
- firefox.exe (PID: 6388)
Checks supported languages
- Jetbrains_Activator(3).exe (PID: 8136)
- downloader.exe (PID: 3164)
- downloader.exe (PID: 6284)
Reads the computer name
- Jetbrains_Activator(3).exe (PID: 8136)
- downloader.exe (PID: 3164)
- downloader.exe (PID: 6284)
Process checks computer location settings
- Jetbrains_Activator(3).exe (PID: 8136)
Drops the executable file immediately after the start
- firefox.exe (PID: 6388)
Create files in a temporary directory
- downloader.exe (PID: 3164)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1372)
- powershell.exe (PID: 3032)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1372)
- powershell.exe (PID: 3032)
Checks proxy server information
- downloader.exe (PID: 6284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
159
Monitored processes
21
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1048 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1372 | powershell -Command "Add-MpPreference -ExclusionPath \"C:\Users\admin\AppData\Local\OracleJava\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | powershell -Command "Add-MpPreference -ExclusionPath \"C:\Users\admin\AppData\Roaming\OracleJava\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\OracleJava\downloader.exe" -p2YJqUkAsJ37sruDSyNM44AXF | C:\Users\admin\AppData\Local\OracleJava\downloader.exe | Jetbrains_Activator(3).exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3972 | "C:\Users\admin\Downloads\Jetbrains_Activator(3).exe" | C:\Users\admin\Downloads\Jetbrains_Activator(3).exe | — | firefox.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6284 | "C:\Users\admin\AppData\Local\OracleJava\downloader.exe" -p2YJqUkAsJ37sruDSyNM44AXF | C:\Users\admin\AppData\Local\OracleJava\downloader.exe | — | downloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 6328 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/zox47/JetBrains-products-Activation-code-until-5-August-2025/blob/main/Jetbrains_Activator.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6388 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/zox47/JetBrains-products-Activation-code-until-5-August-2025/blob/main/Jetbrains_Activator.exe | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6532 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1808 -parentBuildID 20240213221259 -prefsHandle 1736 -prefMapHandle 1728 -prefsLen 30537 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {540bc686-38ee-4c51-8eb7-26c0dfeb1f5d} 6388 "\\.\pipe\gecko-crash-server-pipe.6388" 23d8cebb410 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6580 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2192 -parentBuildID 20240213221259 -prefsHandle 2184 -prefMapHandle 2180 -prefsLen 30537 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f4cb3ea5-541f-4f9f-81c1-ab8c725fffe9} 6388 "\\.\pipe\gecko-crash-server-pipe.6388" 23d81183510 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
36 849
Read events
36 753
Write events
95
Delete events
1
Modification events
| (PID) Process: | (6328) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 9AD5B3C800000000 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: B357B5C800000000 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (6388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
Executable files
68
Suspicious files
183
Text files
72
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6388 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:EF90022DF0735160DD056C0E6670E915 | SHA256:2B663C0B462A437C8DE3D9B95EE157AE181249B78BDD6F7BD73F7EB6D9E03F87 | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:234AE9E2B8F6B38E2687C204EF393F8C | SHA256:ECCB3EB724C5EF573011B173740C11499C1FED6B81BF82B0715B3FA7175AD522 | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:9D582D1B2306EE95B0C8C688D7722168 | SHA256:156F0DDA35CFCAE74AFAB50B4192DC7A4DD867E67C6009EB52ED5DC68506CE53 | |||
| 6388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:CD1700BC7A39F4C42B4EEE51A247DDE8 | SHA256:88FAE64189C4A2A35413F935F5E6D224245D54EC2D3EDFABF9A1921483845878 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
99
DNS requests
132
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6388 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6388 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6388 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | unknown |
6388 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6388 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6388 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6388 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6388 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6388 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6388 | firefox.exe | POST | 200 | 184.24.77.53:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4064 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6388 | firefox.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
6388 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6388 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | unknown |
6388 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
github.com |
| shared |
content-signature-2.cdn.mozilla.net |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
prod.content-signature-chains.prod.webservices.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |