| File name: | installer.exe |
| Full analysis: | https://app.any.run/tasks/e4d1abea-8485-4fe1-a7b0-9c9064b1e807 |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2026, 14:43:45 |
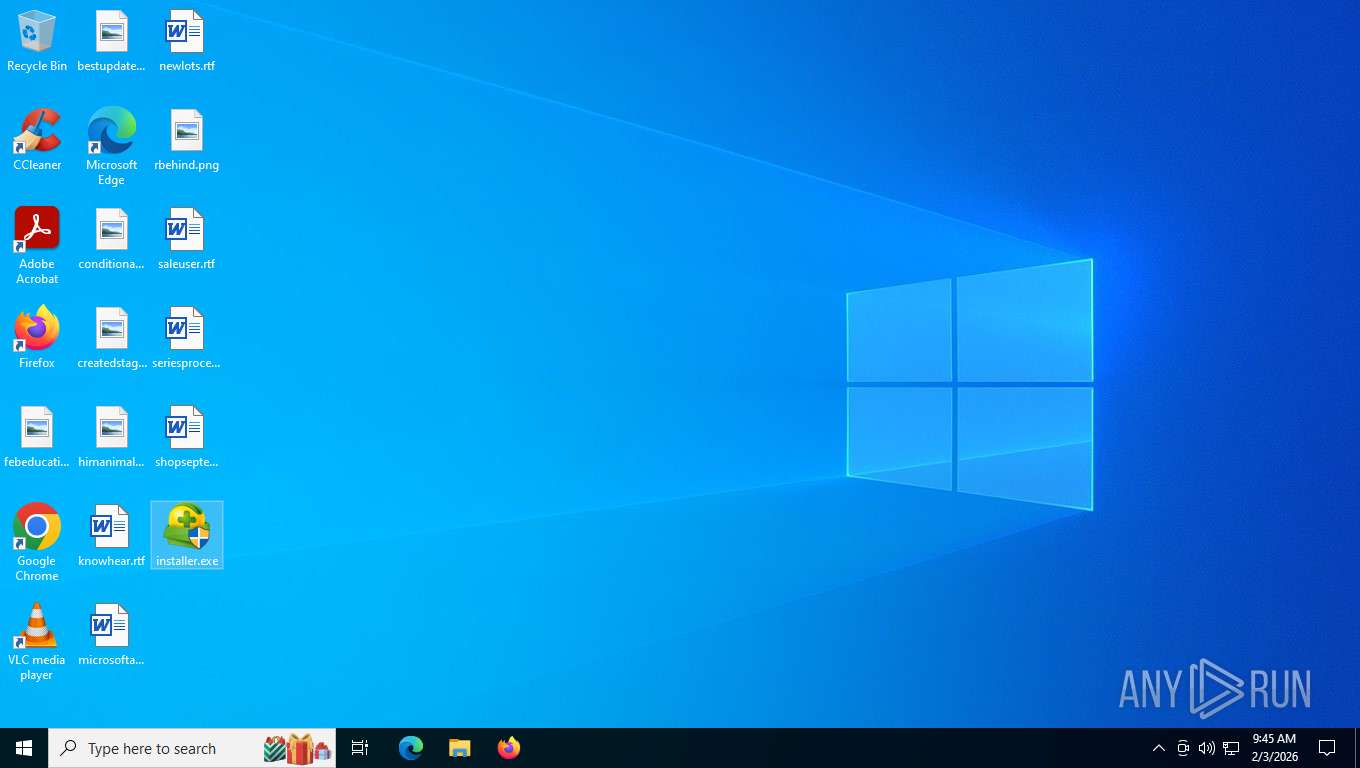
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 5647672E6C372D43CA45E5F1C7CADB39 |
| SHA1: | 10B6E015A48F2303DB4C1CBA3DFF15483F592FE5 |
| SHA256: | 7AF7E302E9CAD6D730AEB2F2577CEFEDFEAA8A34CF30AEE29FF2D2D77028A830 |
| SSDEEP: | 12288:j/hHT0tCg8uCiMACc0xOX1apuYa4+LhSCeur2FVh2JWM2OUkWWU9GYkBnKWRIAFS:j/1UCg8uCiM40uP6aXdb2iRfrQn |
MALICIOUS
XORed URL has been found (YARA)
- installer.exe (PID: 8960)
SUSPICIOUS
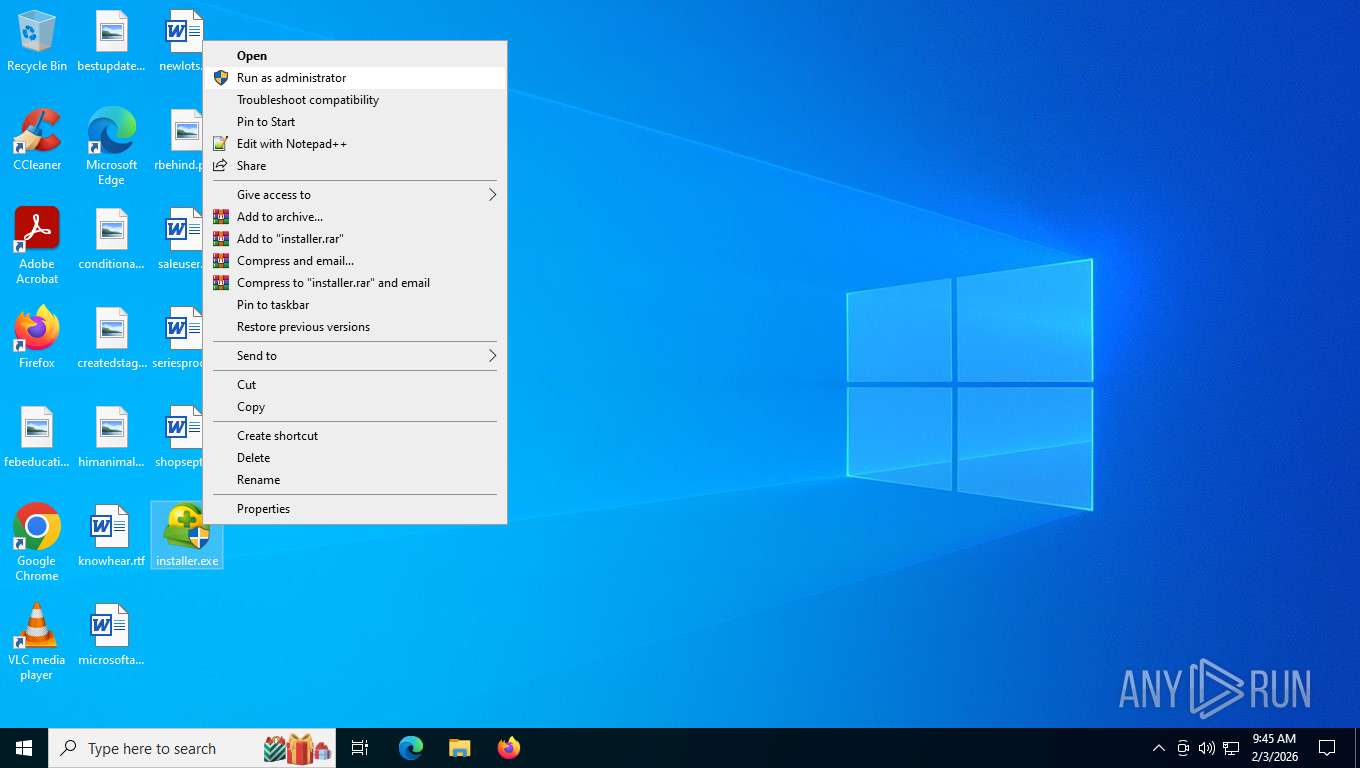
The process verifies whether the antivirus software is installed
- installer.exe (PID: 8960)
INFO
Reads the computer name
- installer.exe (PID: 8960)
Checks supported languages
- installer.exe (PID: 8960)
- installer.exe (PID: 4700)
- installer.exe (PID: 4992)
- installer.exe (PID: 3304)
The sample compiled with chinese language support
- installer.exe (PID: 8960)
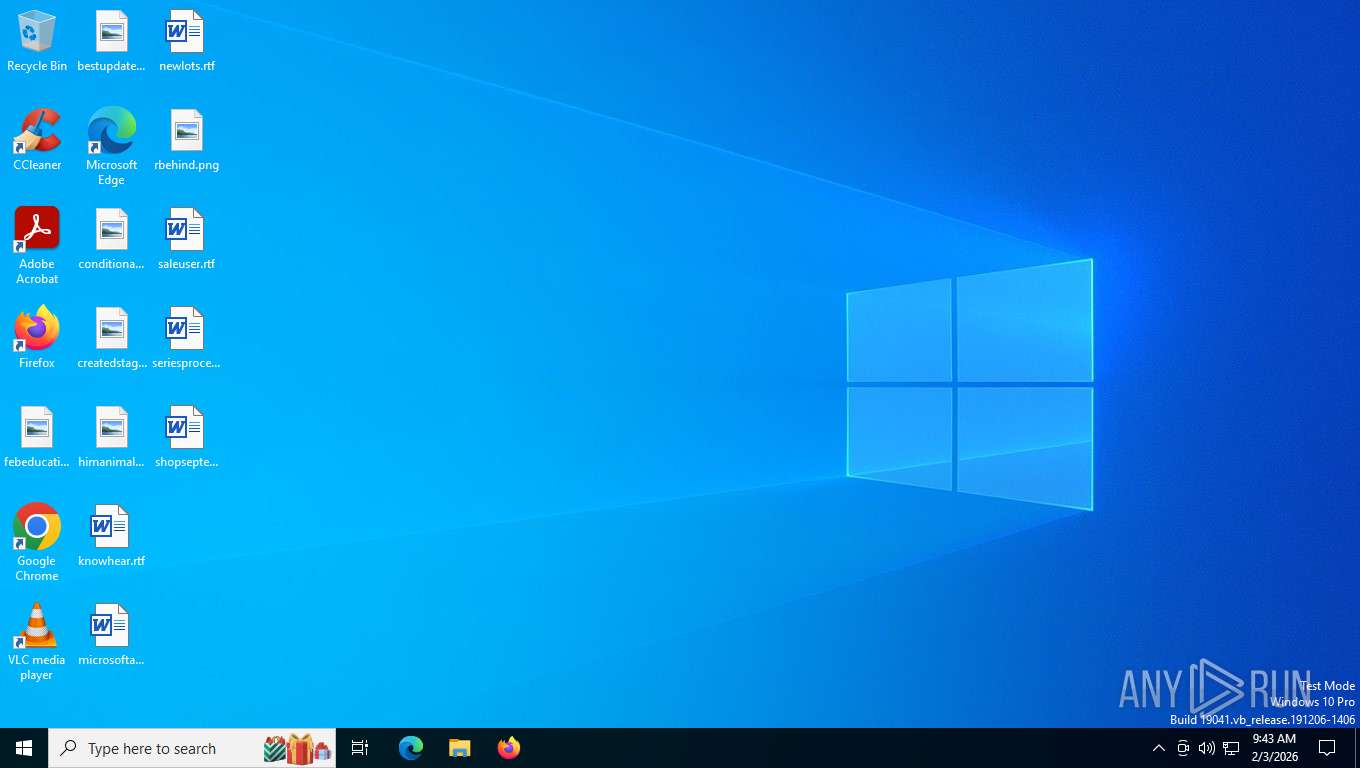
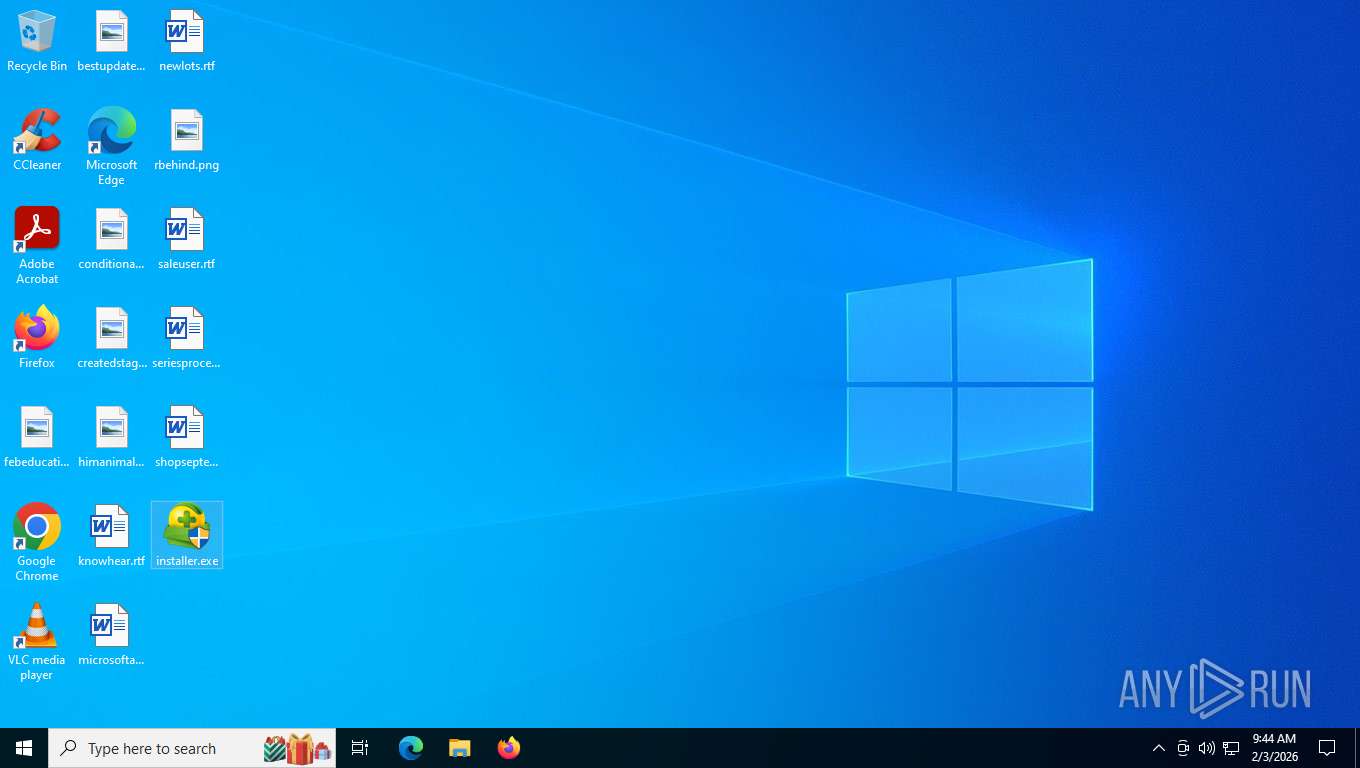
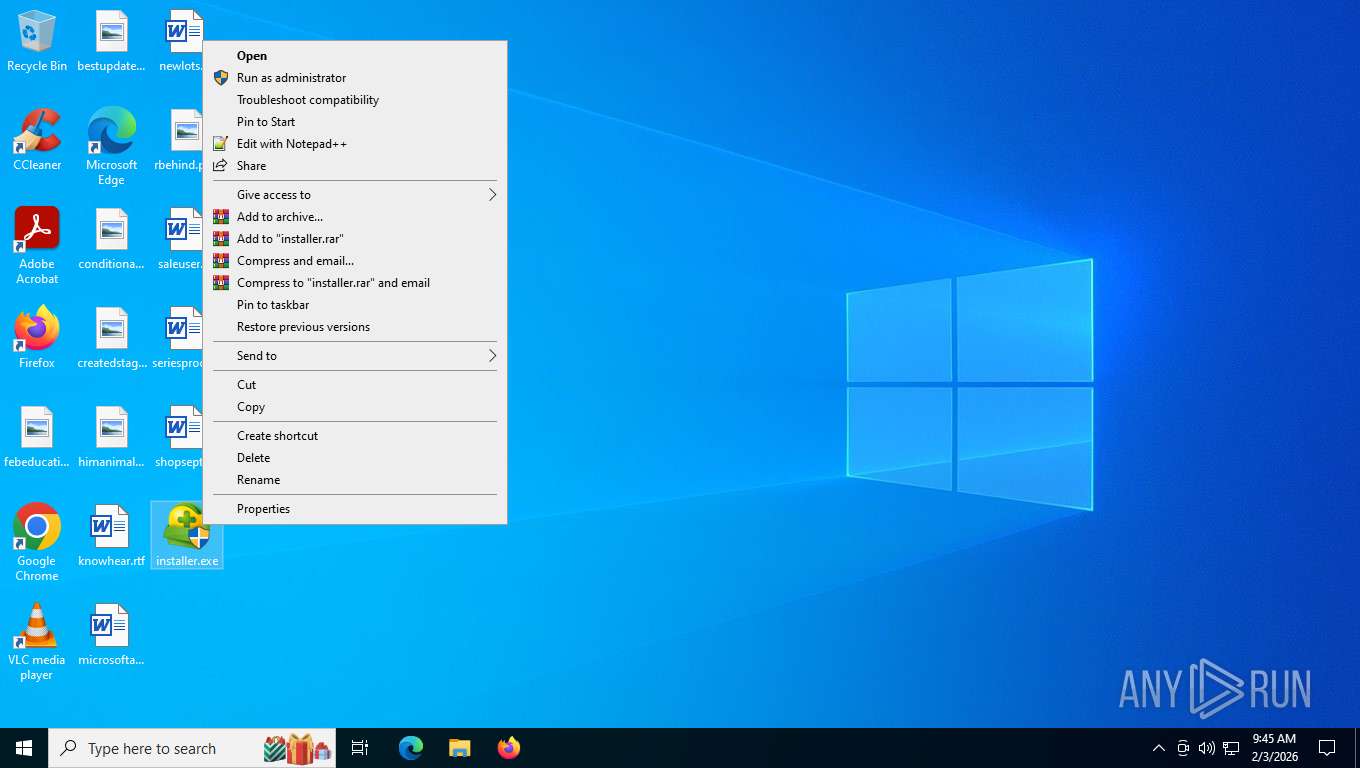
Manual execution by a user
- installer.exe (PID: 4700)
- installer.exe (PID: 3304)
- installer.exe (PID: 8608)
- installer.exe (PID: 4992)
- installer.exe (PID: 6284)
There is functionality for taking screenshot (YARA)
- installer.exe (PID: 8960)
Reads the machine GUID from the registry
- installer.exe (PID: 8960)
Checks proxy server information
- slui.exe (PID: 6212)
- installer.exe (PID: 8960)
Creates files or folders in the user directory
- installer.exe (PID: 8960)
Create files in a temporary directory
- installer.exe (PID: 8960)
Reads security settings of Internet Explorer
- installer.exe (PID: 8960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(8960) installer.exe
Decrypted-URLs (82)http://cacerts.digicert.com/DigiCertAssuredIDRootCA.crt0E
http://cacerts.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crt0
http://cacerts.digicert.com/DigiCertTrustedRootG4.crt0C
http://chp.f.360.cn/wdcquery
http://cp.uidf.f.360.cn/wpeinfo
http://crl.globalsign.com/ca/gstsacasha384g4.crl0
http://crl.globalsign.com/codesigningrootr45.crl0U
http://crl.globalsign.com/gs/gstimestampingg2.crl0T
http://crl.globalsign.com/gs/gstimestampingsha2g2.crl0
http://crl.globalsign.com/gsgccr45evcodesignca2020.crl0
http://crl.globalsign.com/root-r6.crl0G
http://crl.globalsign.net/root-r3.crl0
http://crl.globalsign.net/root.crl0
http://crl.thawte.com/ThawteTimestampingCA.crl0
http://crl.verisign.com/pca3-g5.crl04
http://crl3.digicert.com/DigiCertAssuredIDRootCA.crl0
http://crl3.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crl0
http://crl3.digicert.com/DigiCertTrustedRootG4.crl0
http://dl.360safe.com/gf/%u.cab
http://dl.360safe.com/gf/def.cab
http://down.360safe.com/setup.exe
http://down.360safe.com/setupbeta.exe
http://hao.360.cn/?ln=360ini
http://logo.verisign.com/vslogo.gif04
http://my.360.com
http://my.360safe.com
http://ocsp.digicert.com0a
http://ocsp.digicert.com0c
http://ocsp.digicert.com0x
http://ocsp.globalsign.com/ca/gstsacasha384g40C
http://ocsp.globalsign.com/codesigningrootr450F
http://ocsp.globalsign.com/gsgccr45evcodesignca20200U
http://ocsp.thawte.com0
http://ocsp.verisign.com0
http://ocsp2.globalsign.com/gstimestampingsha2g20
http://ocsp2.globalsign.com/rootr606
http://pinst.360.cn/360safebeta/safebeta_home.cab
http://pinst.360.cn/360sd/360sd_min.cab
http://s.360.cn/hips/update/inst.htm?m=%s&v=%s&s=%d&r=%d&d=%s&oav=%d
http://s.360.cn/safe/install.html?mid=%s&
http://s.360.cn/safe/setupsperr.htm?mid=%s
http://s1.symcb.com/pca3-g5.crl0
http://s2.symcb.com0
http://sd.360.cn
http://sd.360.cn/downloadbeta.html
http://secure.globalsign.com/cacert/codesigningrootr45.crt0A
http://secure.globalsign.com/cacert/gsgccr45evcodesignca2020.crt0
http://secure.globalsign.com/cacert/gstimestampingg2.crt0
http://secure.globalsign.com/cacert/gstimestampingsha2g2.crt0
http://secure.globalsign.com/cacert/gstsacasha384g4.crt0
http://sf.symcb.com/sf.crl0a
http://sf.symcb.com/sf.crl0f
http://sf.symcb.com/sf.crt0
http://sfdl.360safe.com/inst_gf_popup.exe
http://sfdl.360safe.com/inst_gf_popup_ev.exe
http://sfdl.360safe.com/inst_js_popup.exe
http://sfdl.360safe.com/inst_js_popup_ev.exe
http://stat.sd.360.cn/setupfail.htm?pid=%s&case=%d
http://sv.symcb.com/sv.crl0a
http://sv.symcb.com/sv.crl0f
http://sv.symcb.com/sv.crt0
http://ts-aia.ws.symantec.com/tss-ca-g2.cer0
http://ts-crl.ws.symantec.com/tss-ca-g2.crl0
http://ts-crl.ws.symantec.com/tss-ca-g2.crl0(
http://ts-ocsp.ws.symantec.com07
http://www.2345.com/?pic360
http://www.360.cn
http://www.360.cn/killer/360compkill.html
http://www.360.cn/userexperienceimprovement.html
http://www.360.cn/xukexieyi.html#shadu
http://www.360safe.com
http://www.symauth.com/cps0(
http://www.symauth.com/rpa00
https://d.symcb.com/cps0%
https://d.symcb.com/rpa0
https://hao.360.cn/
https://www.globalsign.com/repository/0
https://www.globalsign.com/repository/03
https://www.globalsign.com/repository/06
https://www.verisign.com/cps0*
https://www.verisign.com/rpa
https://www.verisign.com/rpa0
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2026:01:27 07:36:08+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 313344 |
| InitializedDataSize: | 86528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2878f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1850 |
| ProductVersionNumber: | 1.0.0.1850 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileDescription: | 下载助手 |
| FileVersion: | 1, 0, 0, 1850 |
| OriginalFileName: | InstDirect2DLayer.exe |
| ProductName: | 下载助手 |
| ProductVersion: | 1, 0, 0, 1850 |
Total processes
161
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3304 | "C:\Users\admin\Desktop\installer.exe" | C:\Users\admin\Desktop\installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 下载助手 Exit code: 0 Version: 1, 0, 0, 1850 Modules
| |||||||||||||||
| 4700 | "C:\Users\admin\Desktop\installer.exe" | C:\Users\admin\Desktop\installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 下载助手 Exit code: 0 Version: 1, 0, 0, 1850 Modules
| |||||||||||||||
| 4992 | "C:\Users\admin\Desktop\installer.exe" | C:\Users\admin\Desktop\installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 下载助手 Exit code: 0 Version: 1, 0, 0, 1850 Modules
| |||||||||||||||
| 6212 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6284 | "C:\Users\admin\Desktop\installer.exe" | C:\Users\admin\Desktop\installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 下载助手 Exit code: 3221226540 Version: 1, 0, 0, 1850 Modules
| |||||||||||||||
| 8608 | "C:\Users\admin\Desktop\installer.exe" | C:\Users\admin\Desktop\installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 下载助手 Exit code: 3221226540 Version: 1, 0, 0, 1850 Modules
| |||||||||||||||
| 8960 | "C:\Users\admin\Desktop\installer.exe" | C:\Users\admin\Desktop\installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 下载助手 Version: 1, 0, 0, 1850 Modules
xor-url(PID) Process(8960) installer.exe Decrypted-URLs (82)http://cacerts.digicert.com/DigiCertAssuredIDRootCA.crt0E http://cacerts.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crt0 http://cacerts.digicert.com/DigiCertTrustedRootG4.crt0C http://chp.f.360.cn/wdcquery http://cp.uidf.f.360.cn/wpeinfo http://crl.globalsign.com/ca/gstsacasha384g4.crl0 http://crl.globalsign.com/codesigningrootr45.crl0U http://crl.globalsign.com/gs/gstimestampingg2.crl0T http://crl.globalsign.com/gs/gstimestampingsha2g2.crl0 http://crl.globalsign.com/gsgccr45evcodesignca2020.crl0 http://crl.globalsign.com/root-r6.crl0G http://crl.globalsign.net/root-r3.crl0 http://crl.globalsign.net/root.crl0 http://crl.thawte.com/ThawteTimestampingCA.crl0 http://crl.verisign.com/pca3-g5.crl04 http://crl3.digicert.com/DigiCertAssuredIDRootCA.crl0 http://crl3.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crl0 http://crl3.digicert.com/DigiCertTrustedRootG4.crl0 http://dl.360safe.com/gf/%u.cab http://dl.360safe.com/gf/def.cab http://down.360safe.com/setup.exe http://down.360safe.com/setupbeta.exe http://hao.360.cn/?ln=360ini http://logo.verisign.com/vslogo.gif04 http://my.360.com http://my.360safe.com http://ocsp.digicert.com0a http://ocsp.digicert.com0c http://ocsp.digicert.com0x http://ocsp.globalsign.com/ca/gstsacasha384g40C http://ocsp.globalsign.com/codesigningrootr450F http://ocsp.globalsign.com/gsgccr45evcodesignca20200U http://ocsp.thawte.com0 http://ocsp.verisign.com0 http://ocsp2.globalsign.com/gstimestampingsha2g20 http://ocsp2.globalsign.com/rootr606 http://pinst.360.cn/360safebeta/safebeta_home.cab http://pinst.360.cn/360sd/360sd_min.cab http://s.360.cn/hips/update/inst.htm?m=%s&v=%s&s=%d&r=%d&d=%s&oav=%d http://s.360.cn/safe/install.html?mid=%s& http://s.360.cn/safe/setupsperr.htm?mid=%s http://s1.symcb.com/pca3-g5.crl0 http://s2.symcb.com0 http://sd.360.cn http://sd.360.cn/downloadbeta.html http://secure.globalsign.com/cacert/codesigningrootr45.crt0A http://secure.globalsign.com/cacert/gsgccr45evcodesignca2020.crt0 http://secure.globalsign.com/cacert/gstimestampingg2.crt0 http://secure.globalsign.com/cacert/gstimestampingsha2g2.crt0 http://secure.globalsign.com/cacert/gstsacasha384g4.crt0 http://sf.symcb.com/sf.crl0a http://sf.symcb.com/sf.crl0f http://sf.symcb.com/sf.crt0 http://sfdl.360safe.com/inst_gf_popup.exe http://sfdl.360safe.com/inst_gf_popup_ev.exe http://sfdl.360safe.com/inst_js_popup.exe http://sfdl.360safe.com/inst_js_popup_ev.exe http://stat.sd.360.cn/setupfail.htm?pid=%s&case=%d http://sv.symcb.com/sv.crl0a http://sv.symcb.com/sv.crl0f http://sv.symcb.com/sv.crt0 http://ts-aia.ws.symantec.com/tss-ca-g2.cer0 http://ts-crl.ws.symantec.com/tss-ca-g2.crl0 http://ts-crl.ws.symantec.com/tss-ca-g2.crl0( http://ts-ocsp.ws.symantec.com07 http://www.2345.com/?pic360 http://www.360.cn http://www.360.cn/killer/360compkill.html http://www.360.cn/userexperienceimprovement.html http://www.360.cn/xukexieyi.html#shadu http://www.360safe.com http://www.symauth.com/cps0( http://www.symauth.com/rpa00 https://d.symcb.com/cps0% https://d.symcb.com/rpa0 https://hao.360.cn/ https://www.globalsign.com/repository/0 https://www.globalsign.com/repository/03 https://www.globalsign.com/repository/06 https://www.verisign.com/cps0* https://www.verisign.com/rpa https://www.verisign.com/rpa0 | |||||||||||||||
| 9152 | "C:\Users\admin\Desktop\installer.exe" | C:\Users\admin\Desktop\installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 下载助手 Exit code: 3221226540 Version: 1, 0, 0, 1850 Modules
| |||||||||||||||
Total events
4 137
Read events
4 132
Write events
5
Delete events
0
Modification events
| (PID) Process: | (8960) installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8960) installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8960) installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8960) installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\360Safe\Liveup |
| Operation: | write | Name: | mid |
Value: 4cad3526f81b06ed8763d51020f6cb113f4548660bdc3b46f1f2a8c5fa5241e9 | |||
| (PID) Process: | (8960) installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\360Safe\Liveup |
| Operation: | write | Name: | m2 |
Value: 76f9579261ef4ef37c720eab2e459751b0d228fe29af | |||
Executable files
1
Suspicious files
47
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{D9319B88-093E-4db8-876B-8B01FC40CBBD}.tmp | binary | |
MD5:19196F750156833A0D27DBE77403805C | SHA256:1F905C0DC02994DF0D935BD7241BD177DB3CAA75AC13ACA3DA8E57BE27F25110 | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\gAsHrMwIxDzKiTfJ\360ini.dll | executable | |
MD5:8F2537C6DAEE95980163885C5E1D19CC | SHA256:D7A682985753ED72CCFB09994B13EBA864DF9355B1B5BEF417A09D35ED810585 | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{1FC0A9BA-9689-44d5-8515-38E86480B2D1}.tmp | binary | |
MD5:07E271DFF27FE8C05D417846113A41D1 | SHA256:EA4C42EBC0090655C0584D555EF29093292E3EB076E0D4ECA6862117EE029C83 | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{82EC9EBF-955F-4b9e-9B9B-3AD5E8B4CBA1}.tmp | text | |
MD5:A276779EE7E48F68769E4D11A1B3B4DC | SHA256:FDE083557105D01AA82B5F35932E06635EC127705064E88378729A161CFBD74C | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{566F3853-6080-4fdb-AEFC-B30ABA7A256E}.tmp | binary | |
MD5:BD4F9D1EEEE6D10154A979BDEACC1EDD | SHA256:3CF65DEAA657A3A8D3A168AE77E4EED1C5573FC5FEAE874A4124AEDC934D9B4F | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\360ini.cab | compressed | |
MD5:7DFB63BAE1560ACCFD4B607858B7FACA | SHA256:429BCA3652C1CEE40F107F60E8D09B55AC383B278F6717A09172208637F6CD93 | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{95E18DA0-D8BC-45f6-8518-089F5E6E231E}.tmp | binary | |
MD5:2DF33E9D84D3417B052FFD2775EB0EC2 | SHA256:3A2E00134AFFCED5AE37ABCE3CC022F5E185886127BD18FC367D697E0BF723D0 | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{B1788ADB-8B28-4cad-90F5-295A0649BDCD}.tmp | binary | |
MD5:BC35A0B288231A10A95082F84B9F040C | SHA256:1B601AE13A009B9767DDD26D82C2515E701C02C219C26A98E2180B712DEF39A1 | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{2F751F94-2566-4f9c-A2AF-4CBFAFB1E2DF}.tmp | binary | |
MD5:3988C069BC372F21363B9D7772F45B60 | SHA256:AA74E3DFFF1E1129F456C6C14D3A37BF0F48C060C292D1F56B9468591C3B7AD8 | |||
| 8960 | installer.exe | C:\Users\admin\AppData\Local\Temp\{3BD469E9-0E03-44b6-A9DF-6450C1C2CCAC}.tmp | binary | |
MD5:75B555389C5C5BE4C165F2A52B13CEC7 | SHA256:4C2035ED1209047F021B28B91FDBF451689AF2AD33F5C72D3A16DD5DE0574FC0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
41
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
5516 | svchost.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
8052 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
8052 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
8052 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
8052 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
— | — | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
8960 | installer.exe | GET | 200 | 138.113.219.8:80 | http://sfdl.360safe.com/gf/360ini.cab | CA | compressed | 2.17 Mb | unknown |
356 | svchost.exe | POST | 200 | 40.126.31.69:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
8960 | installer.exe | HEAD | 200 | 138.113.219.8:80 | http://sfdl.360safe.com/gf/360ini.cab | CA | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5516 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3344 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.218:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8960 | installer.exe | 138.113.219.8:80 | sfdl.360safe.com | ML-1432-54994 | CA | whitelisted |
8960 | installer.exe | 171.8.167.89:80 | s.360.cn | CHINANET-BACKBONE No.31,Jin-rong Street | CN | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
sfdl.360safe.com |
| unknown |
s.360.cn |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |