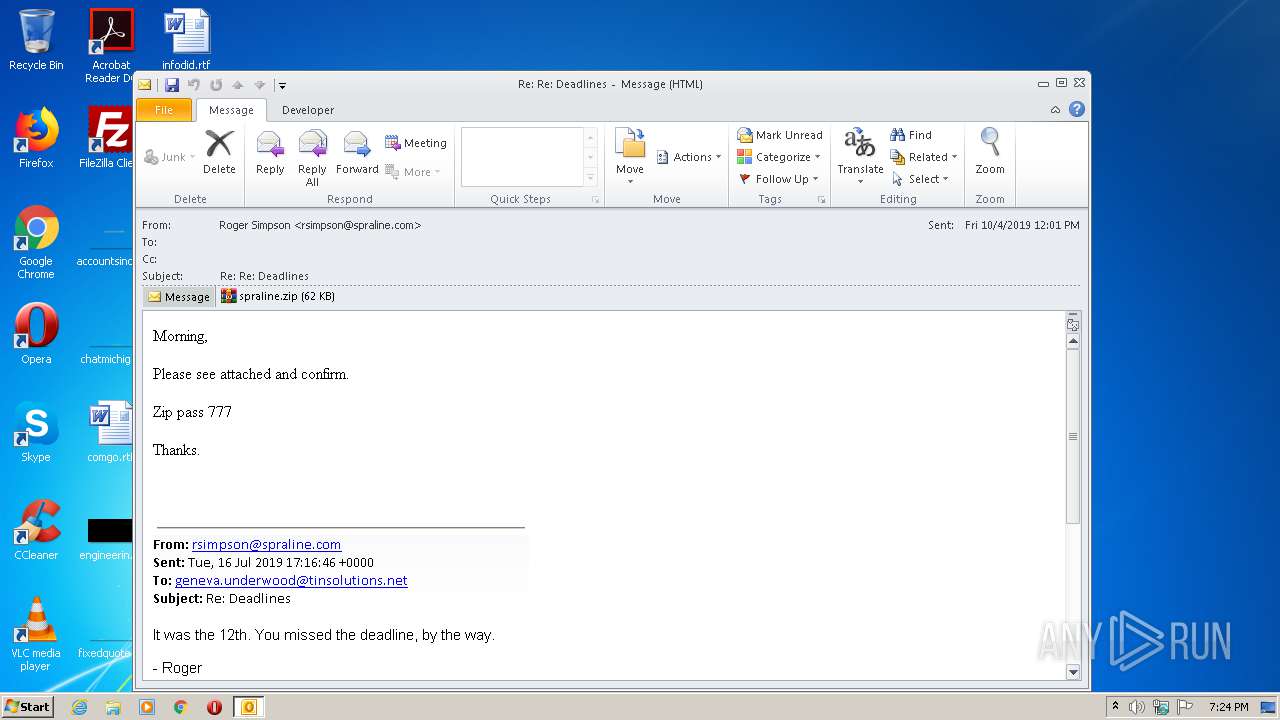
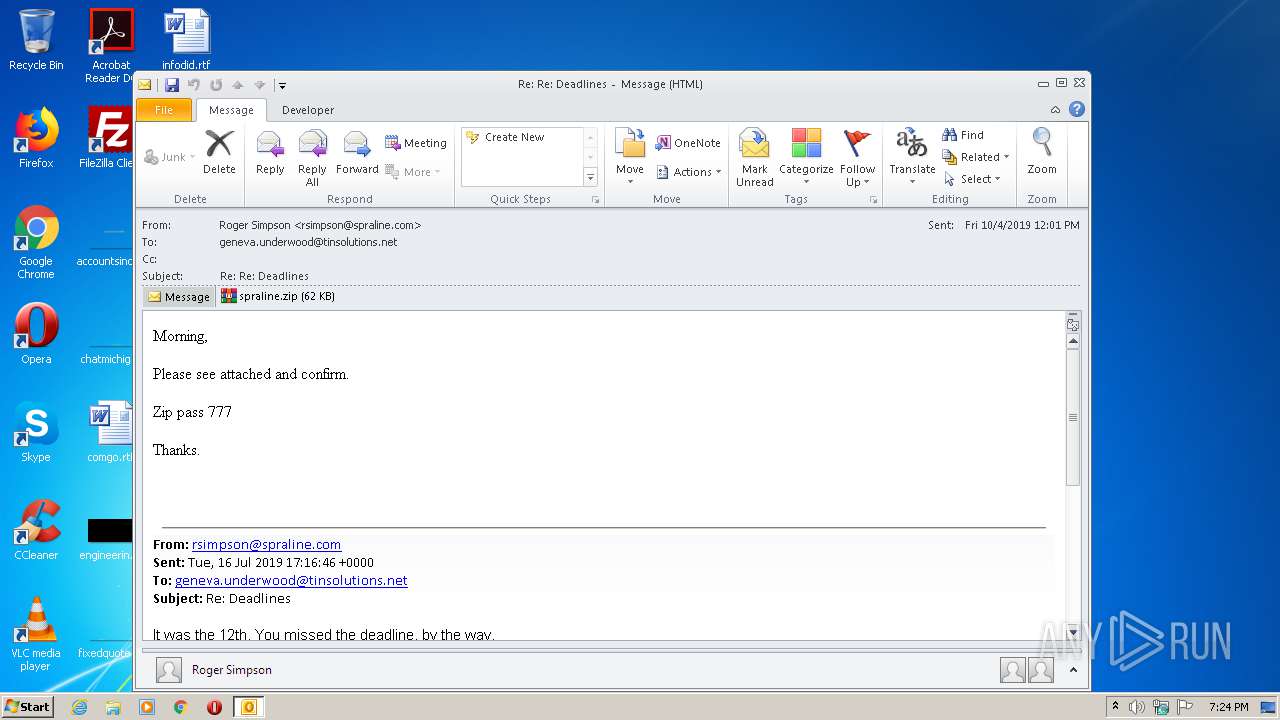
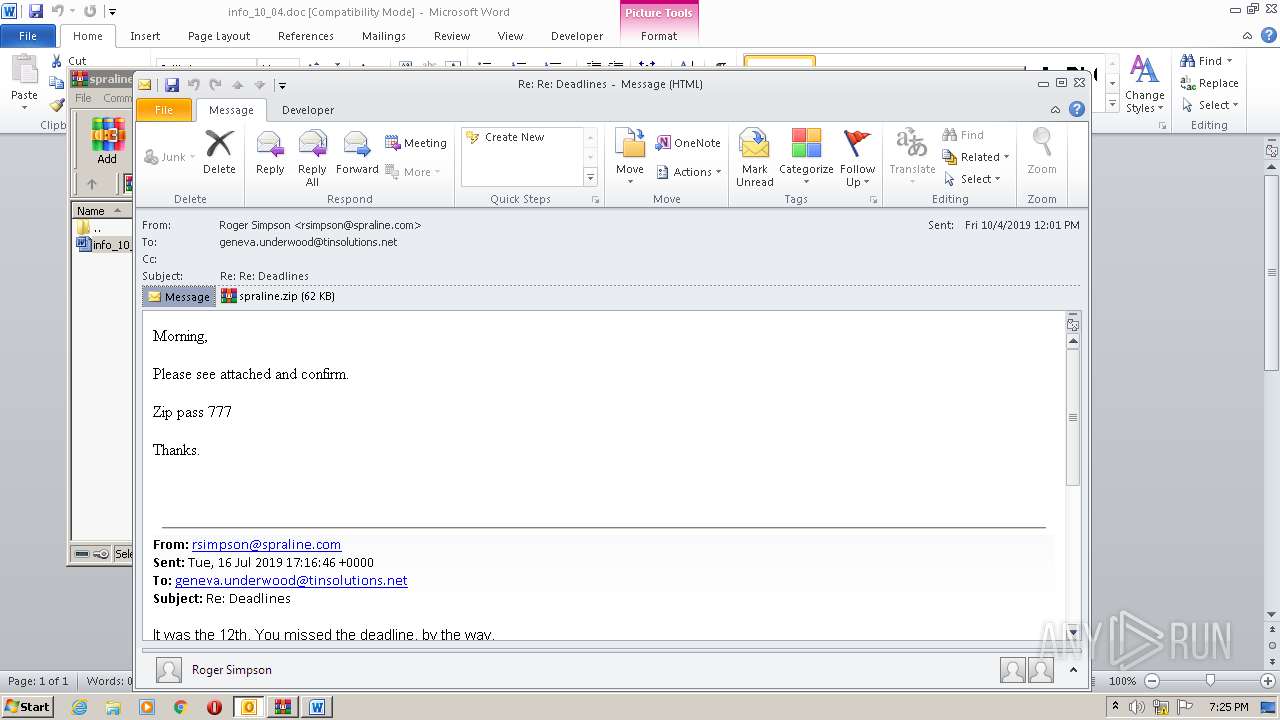
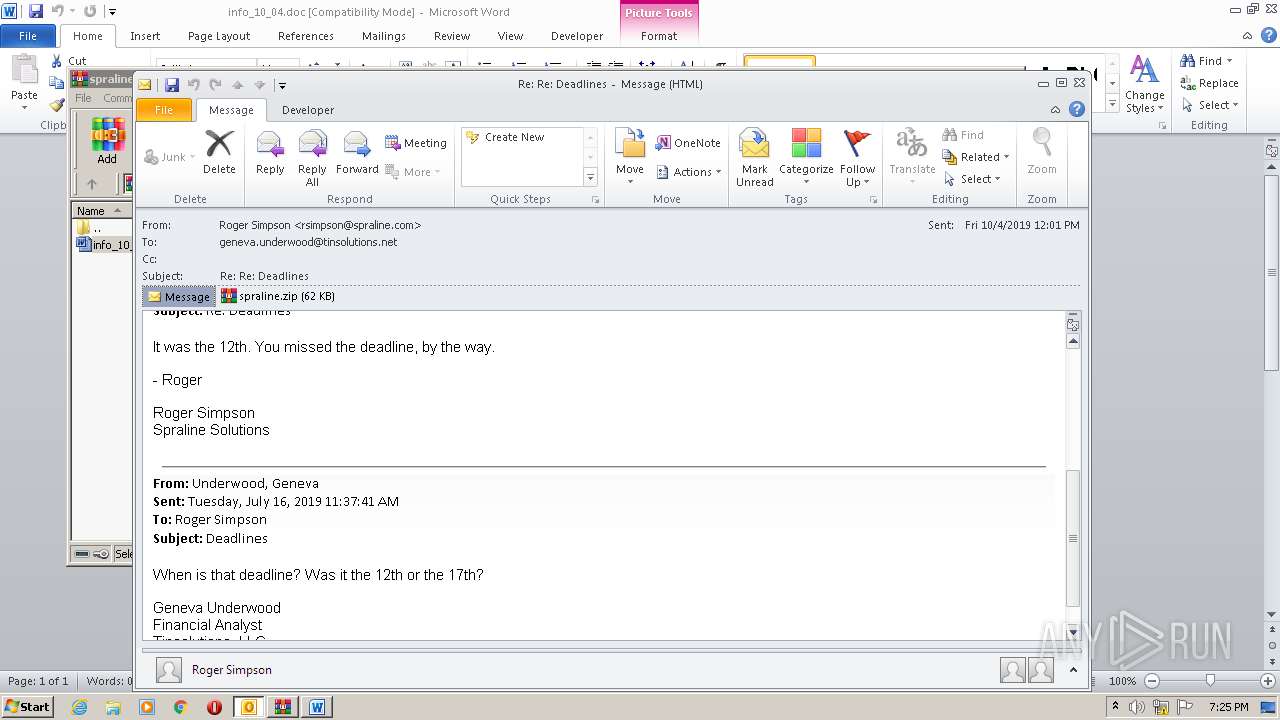
| File name: | 2019-10-05-traffic-analysis-exercise-email-Deadlines.eml |
| Full analysis: | https://app.any.run/tasks/8f9b904a-aca5-4630-8c3b-13c214967034 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 18:23:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF, LF line terminators |
| MD5: | 08171F32DEE429E9C9911B4CAF573DF0 |
| SHA1: | 4A9BB4120E43B2ED7676D79454E2BA502351BF2F |
| SHA256: | 7AE0419E7D7AF7A2DE3339FAD1A57C7247A72BCBD96ABF476303E381547976C3 |
| SSDEEP: | 1536:NAi1d6LzxHrsLTspgDc9tRWQq29/1RermqCi6FmQ52VLy1DmI8WgVylG:JUriTsppdVFvqj3Q52VLWb0yQ |
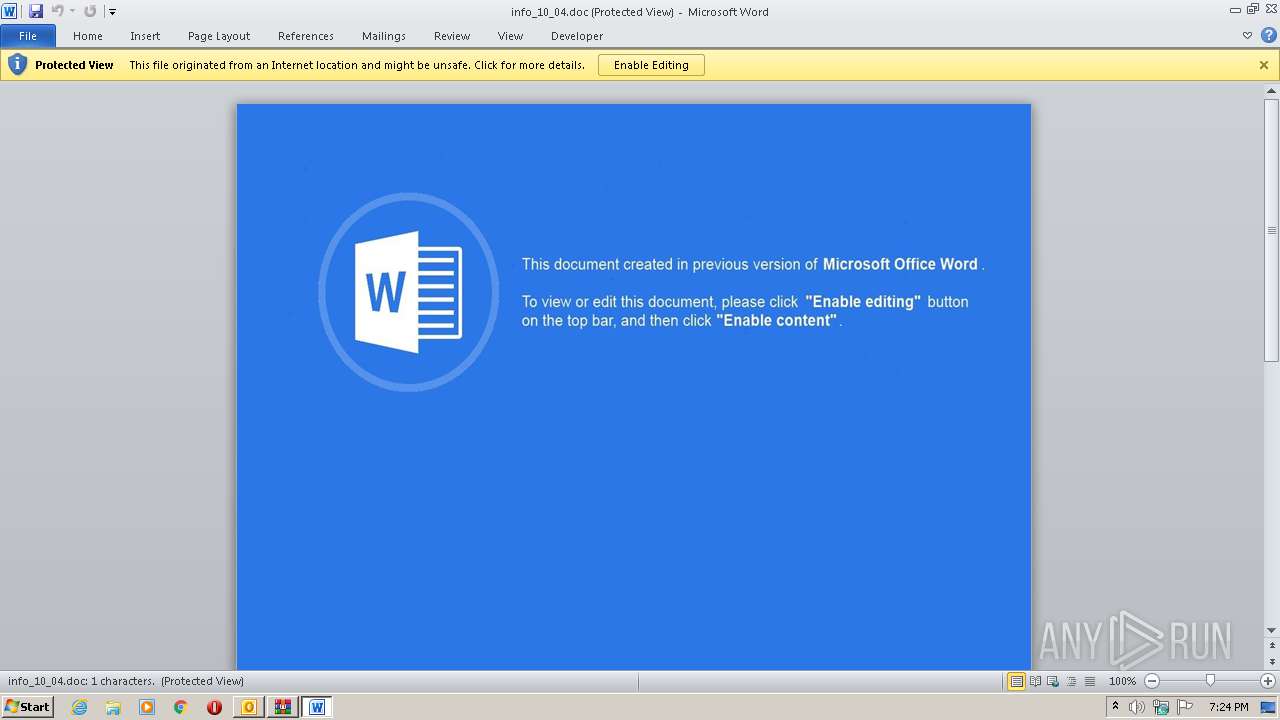
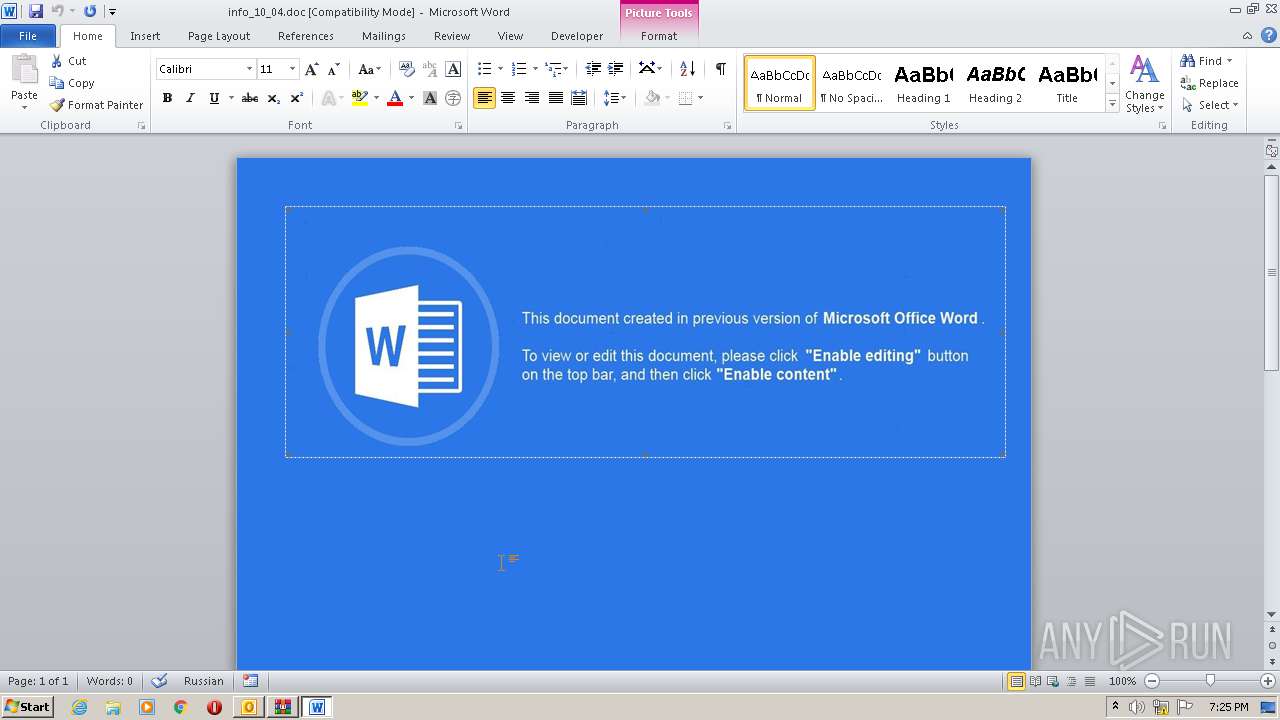
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 1868)
- WINWORD.EXE (PID: 2708)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2708)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1872)
Starts Microsoft Office Application
- WinRAR.exe (PID: 1868)
- WINWORD.EXE (PID: 2708)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1872)
- WMIC.exe (PID: 2196)
Application launched itself
- WINWORD.EXE (PID: 2708)
Uses WMIC.EXE to obtain a system information
- WINWORD.EXE (PID: 2708)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2708)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2708)
- WINWORD.EXE (PID: 3944)
- OUTLOOK.EXE (PID: 1872)
Manual execution by user
- WINWORD.EXE (PID: 872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
45
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\info_10_04.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | |||||||||||||||
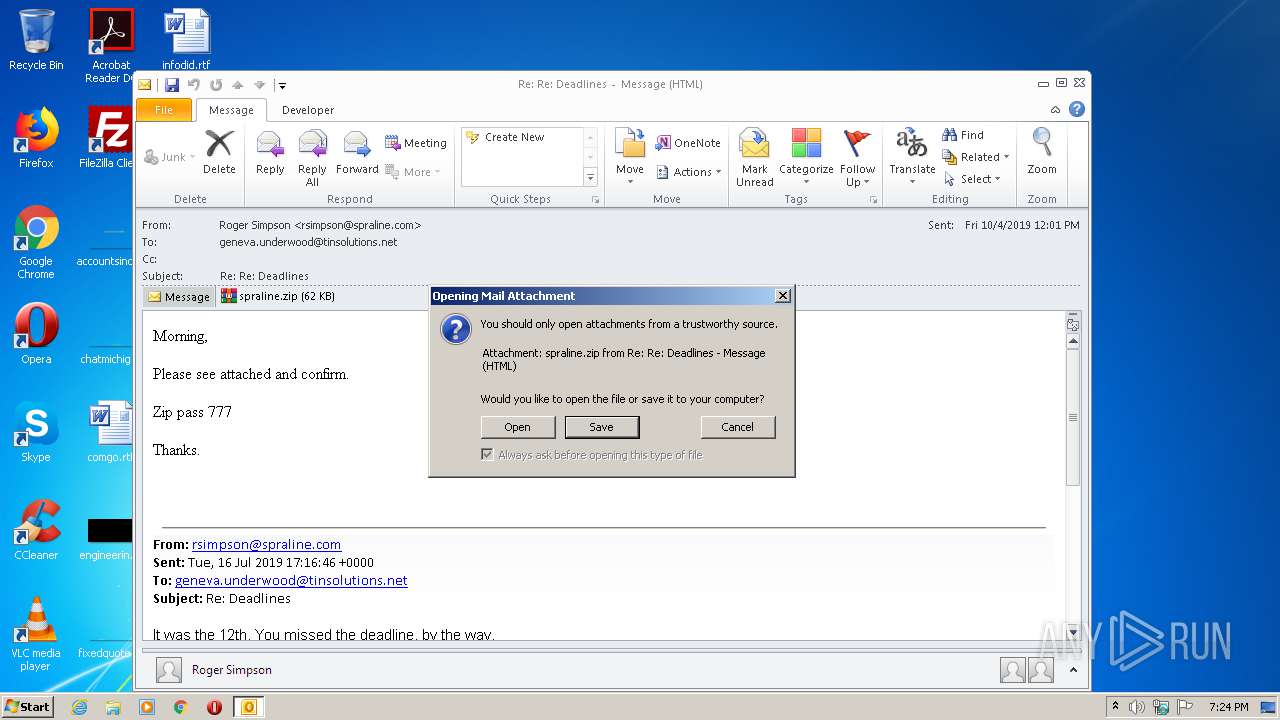
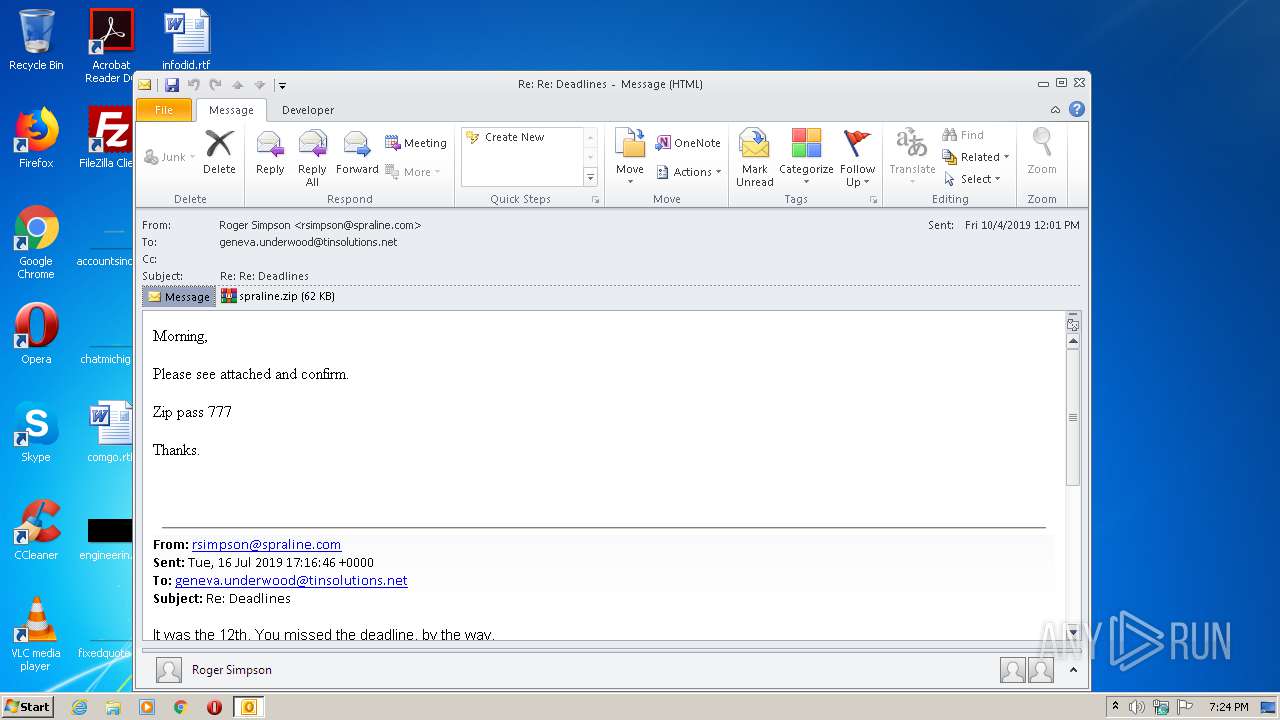
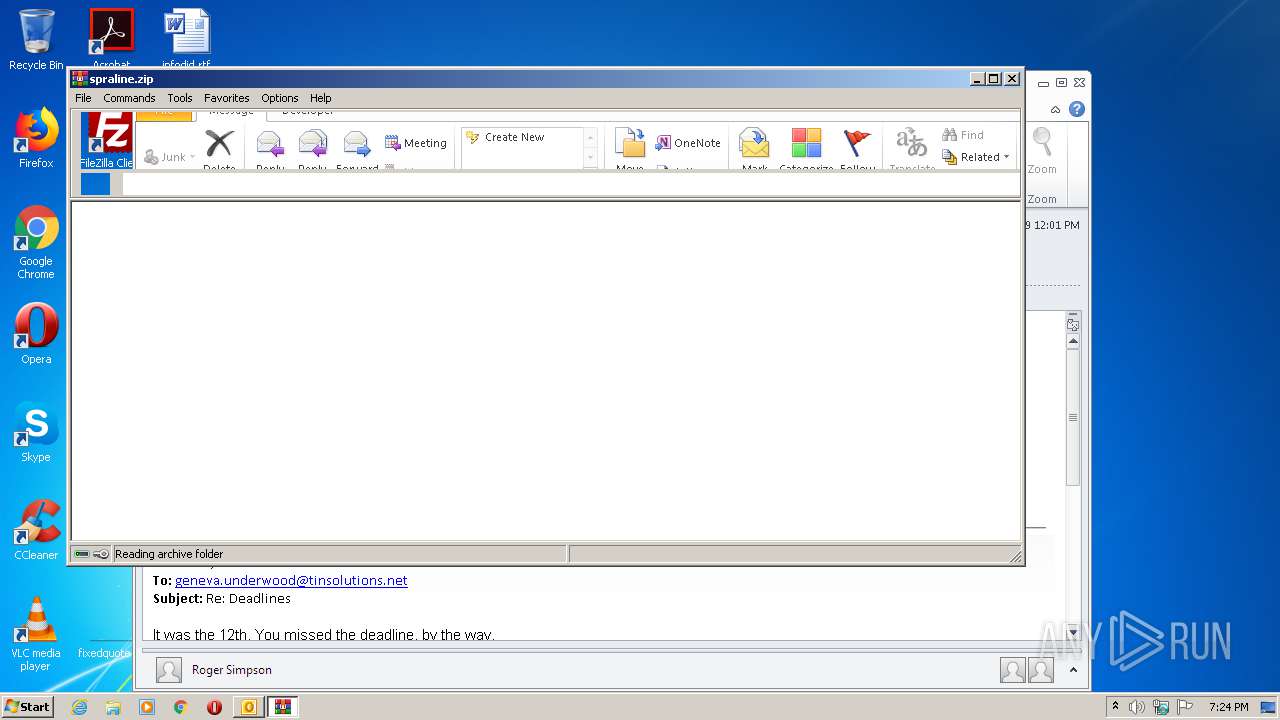
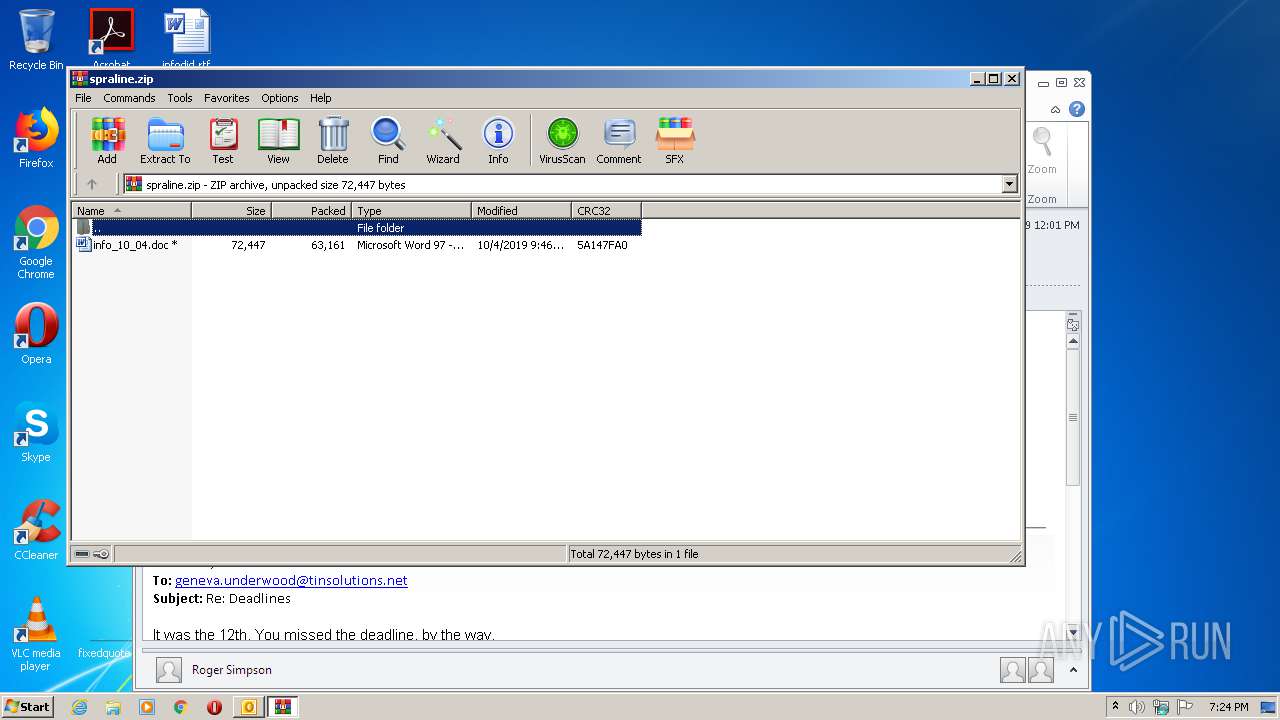
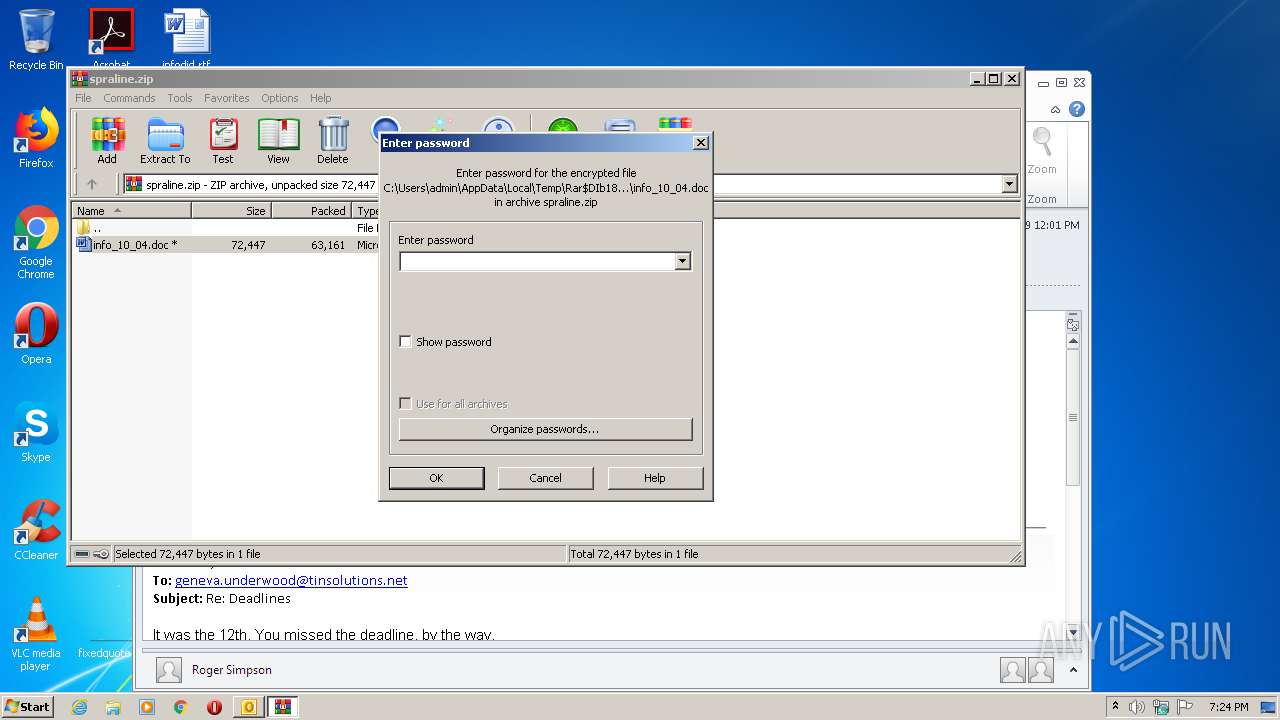
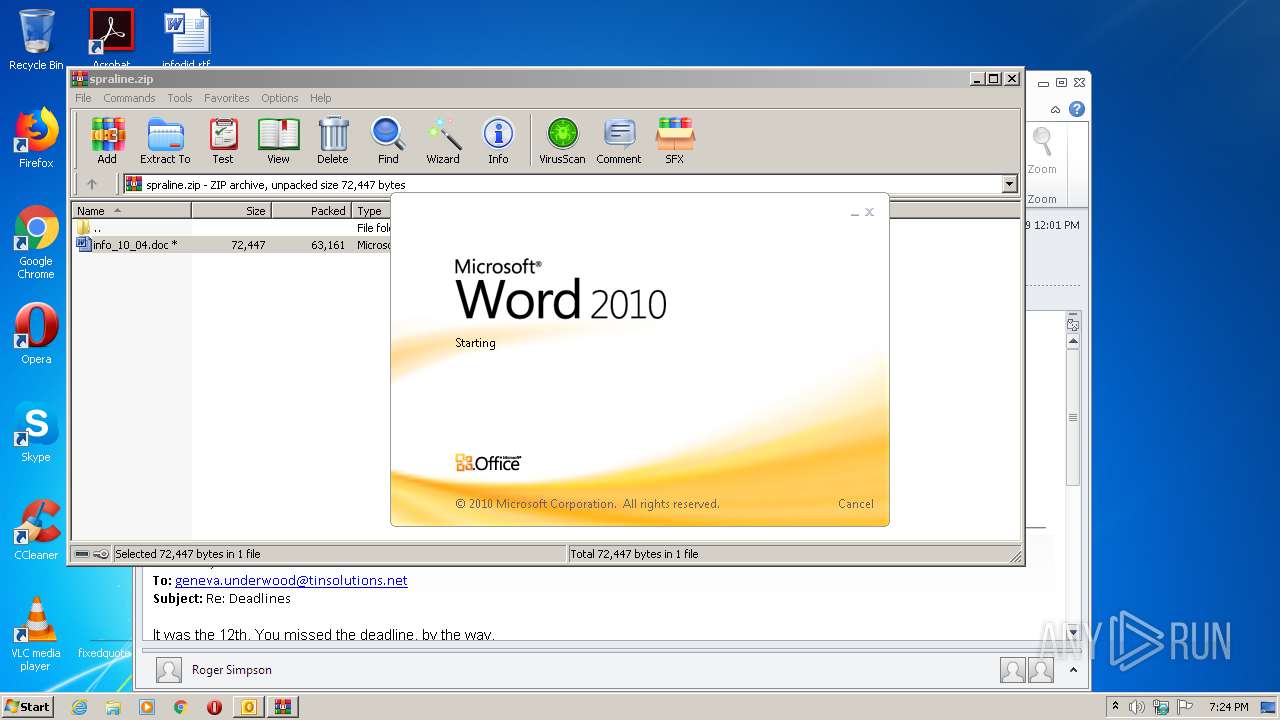
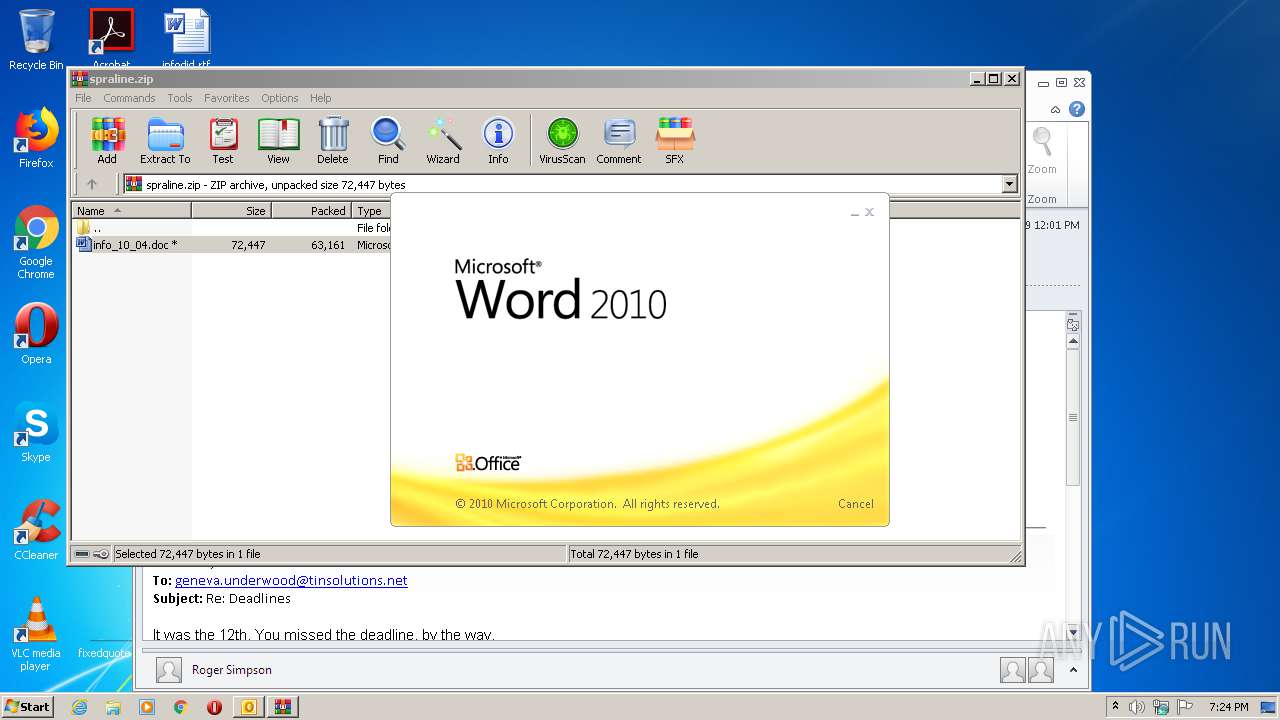
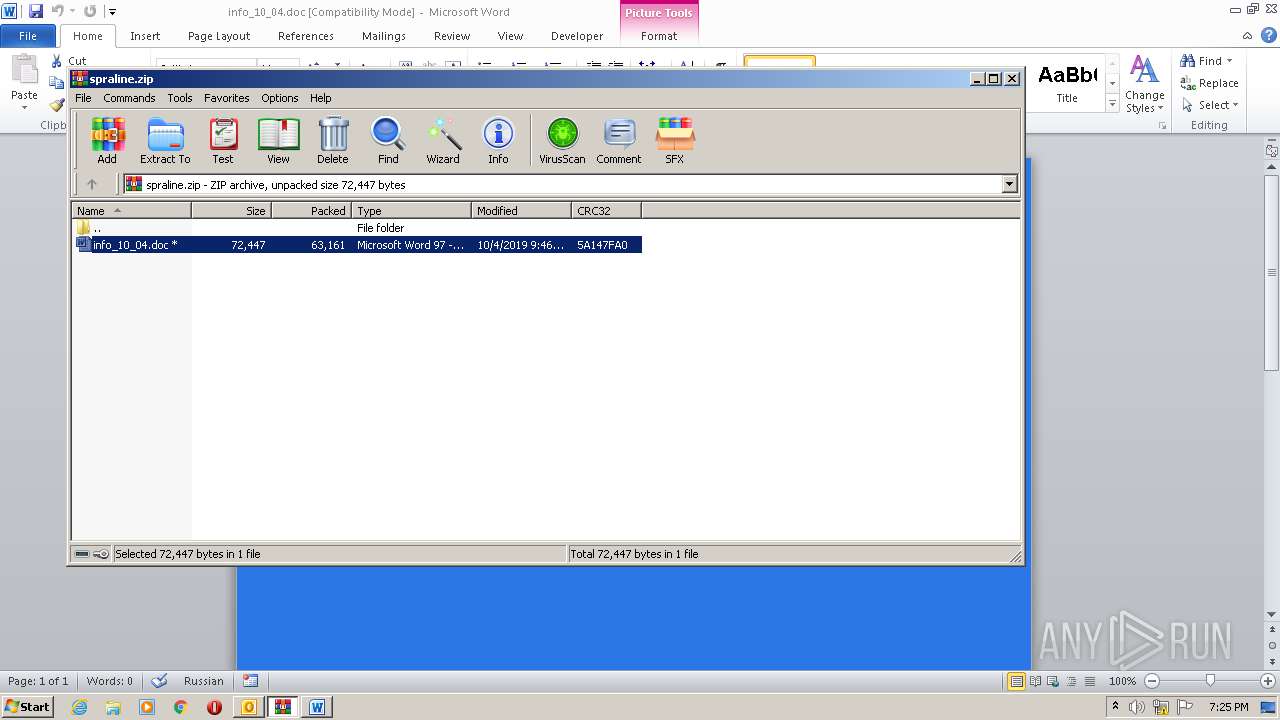
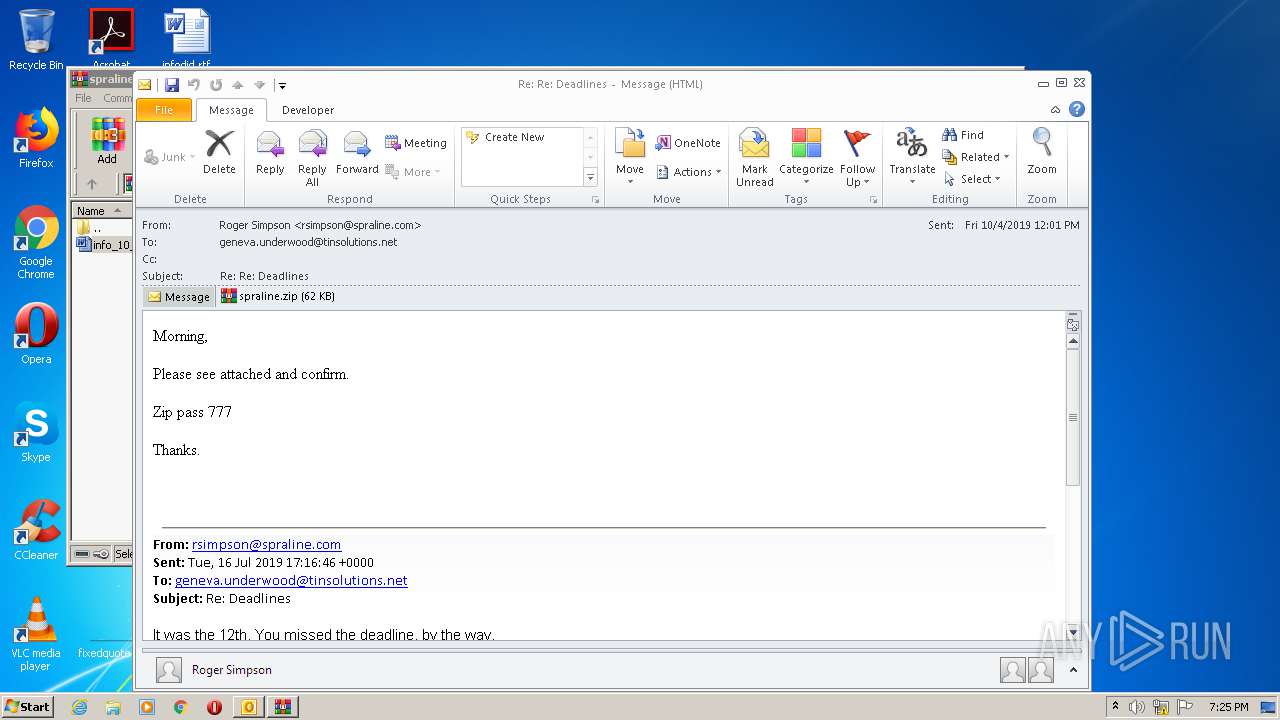
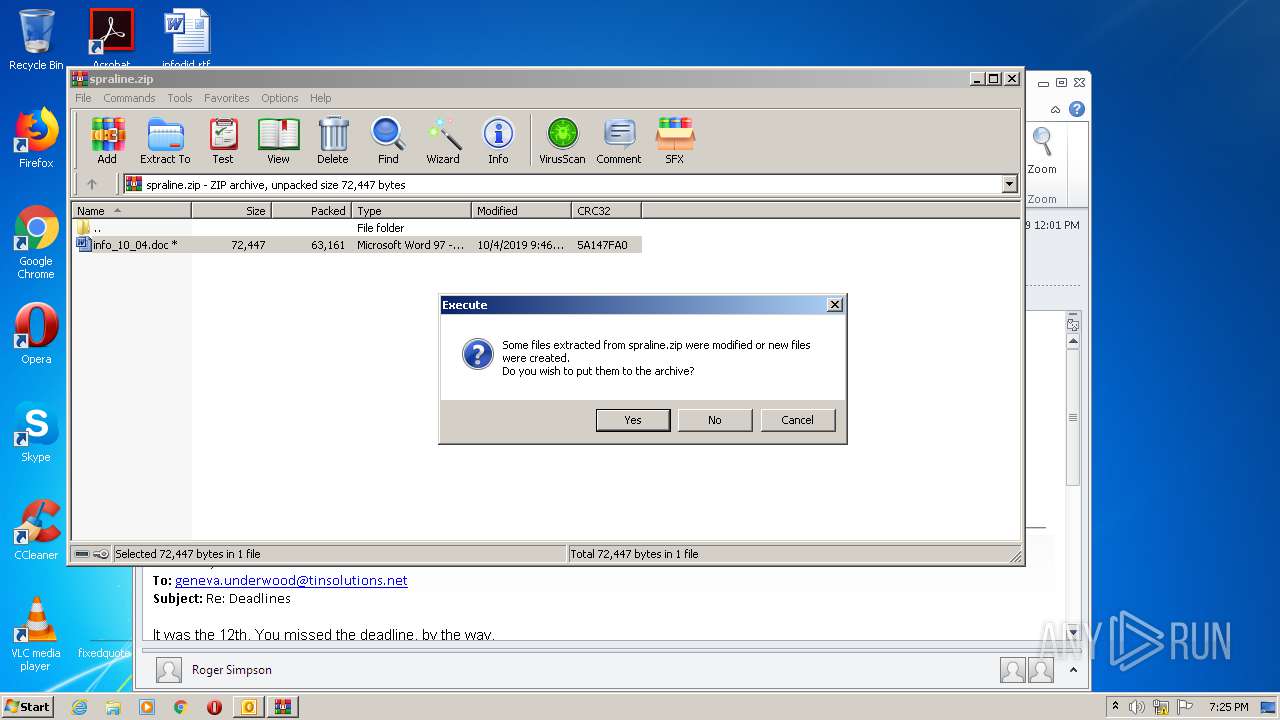
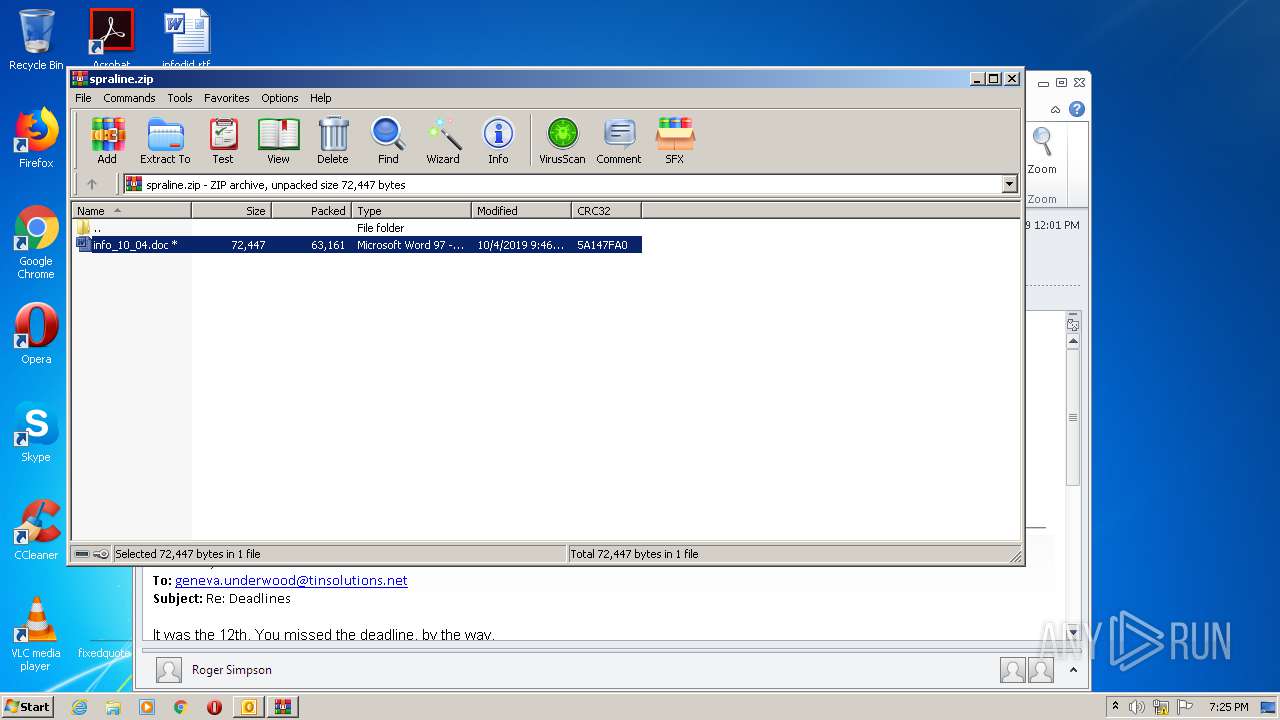
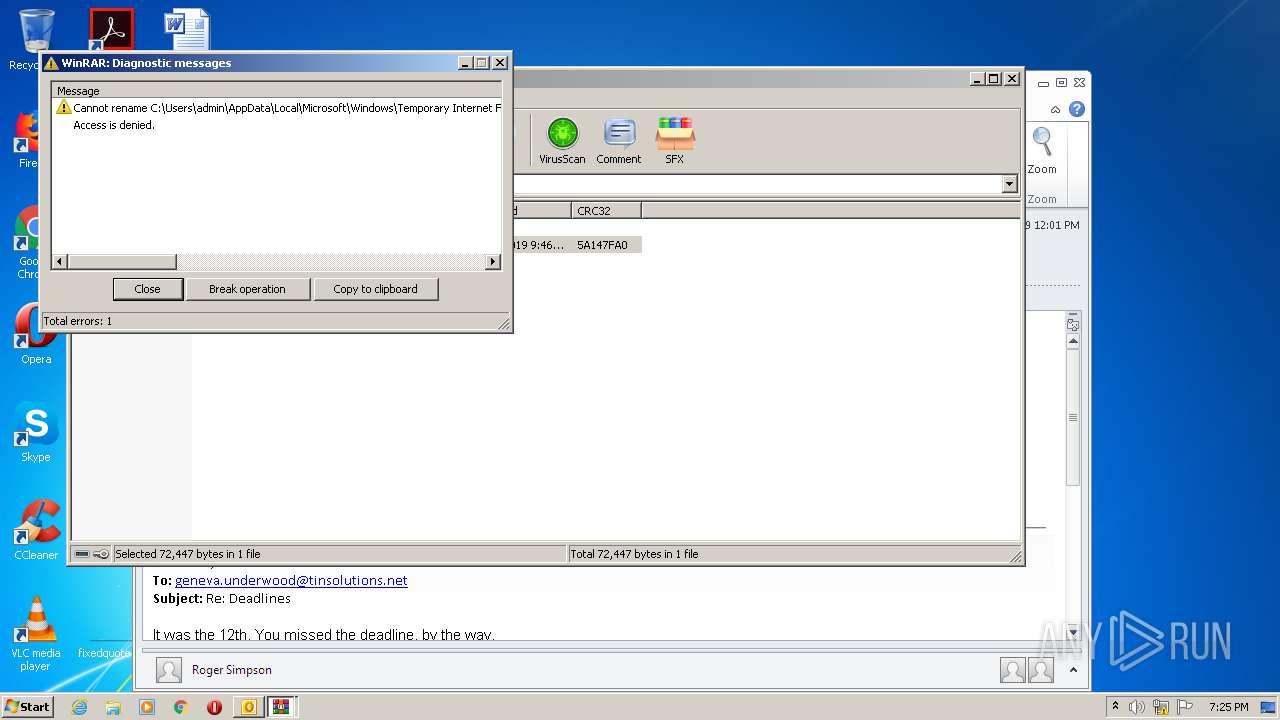
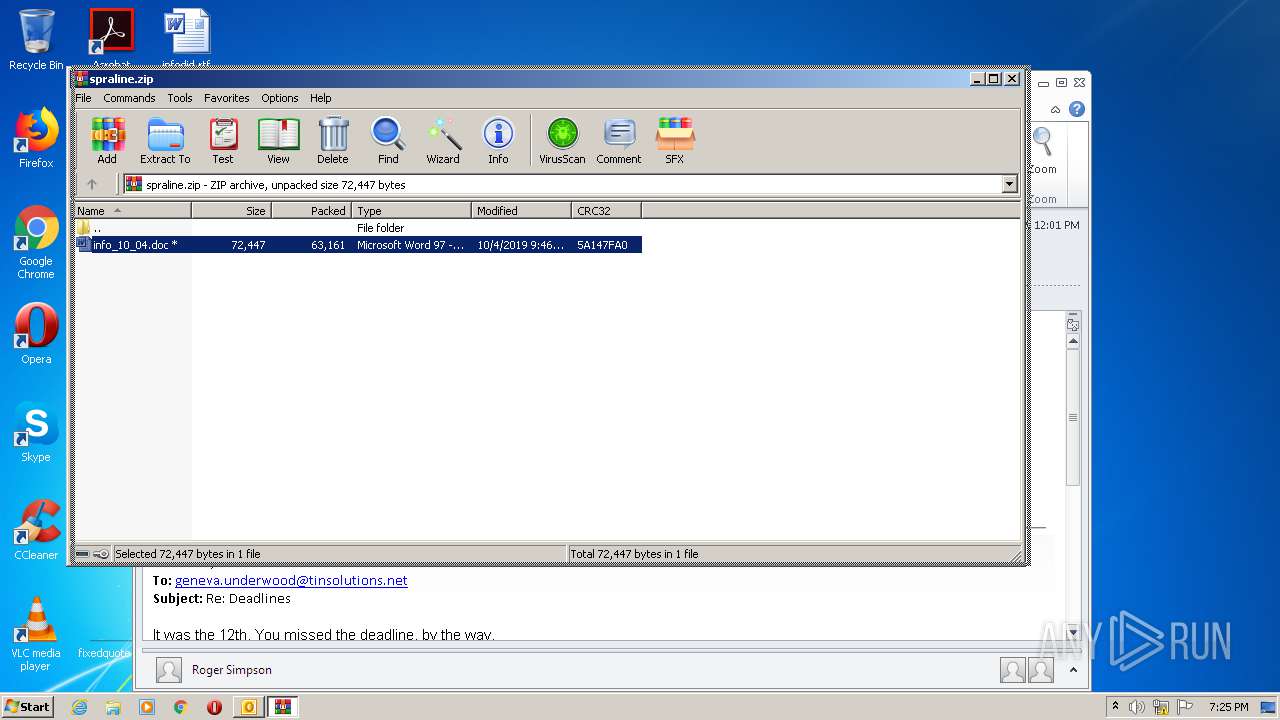
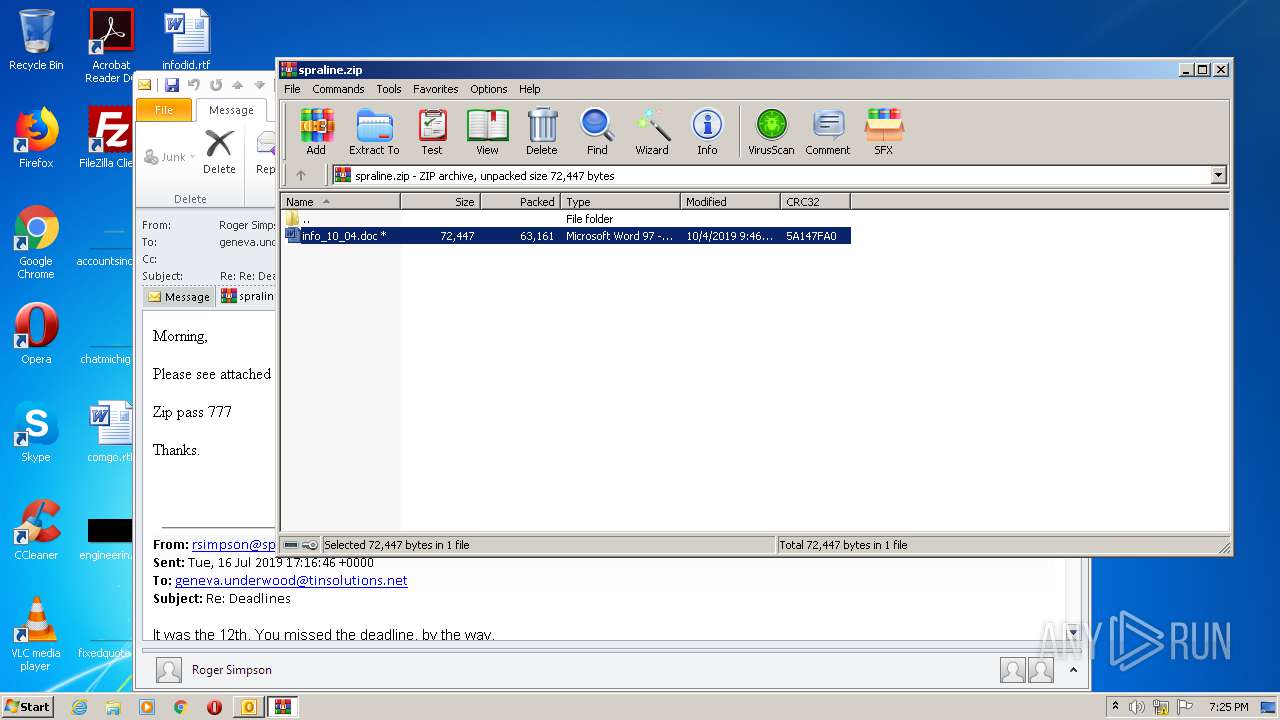
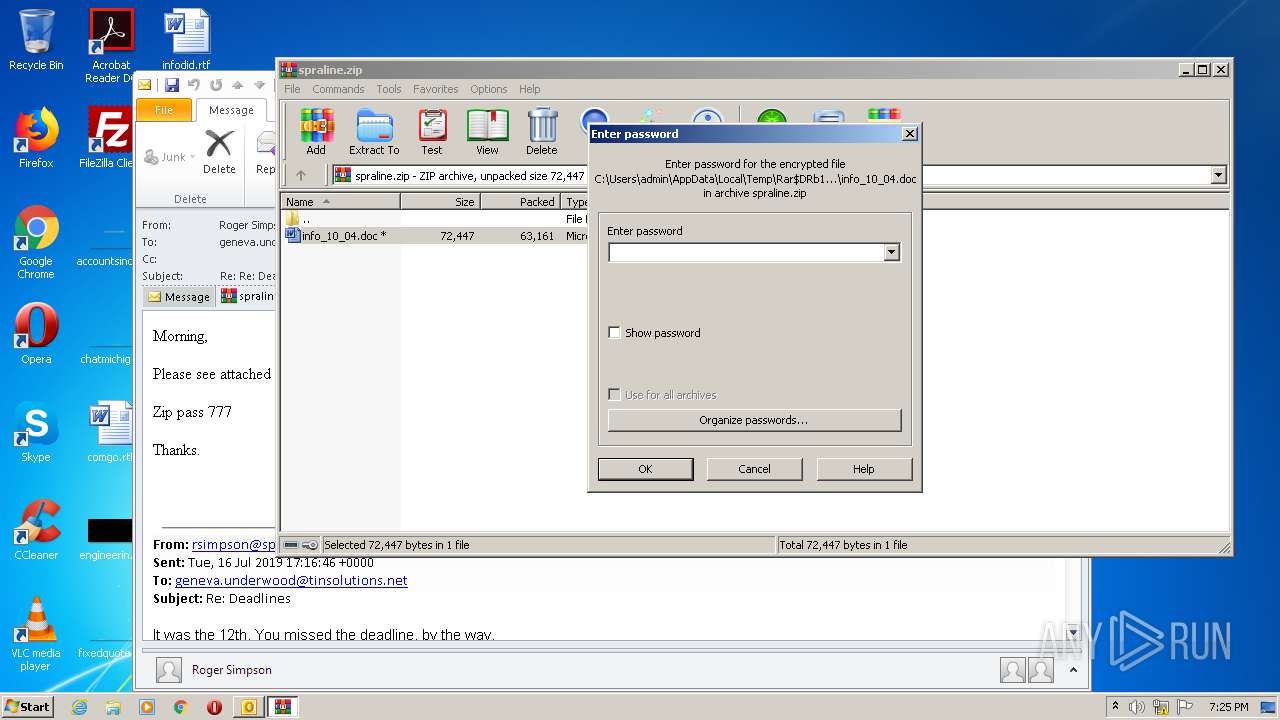
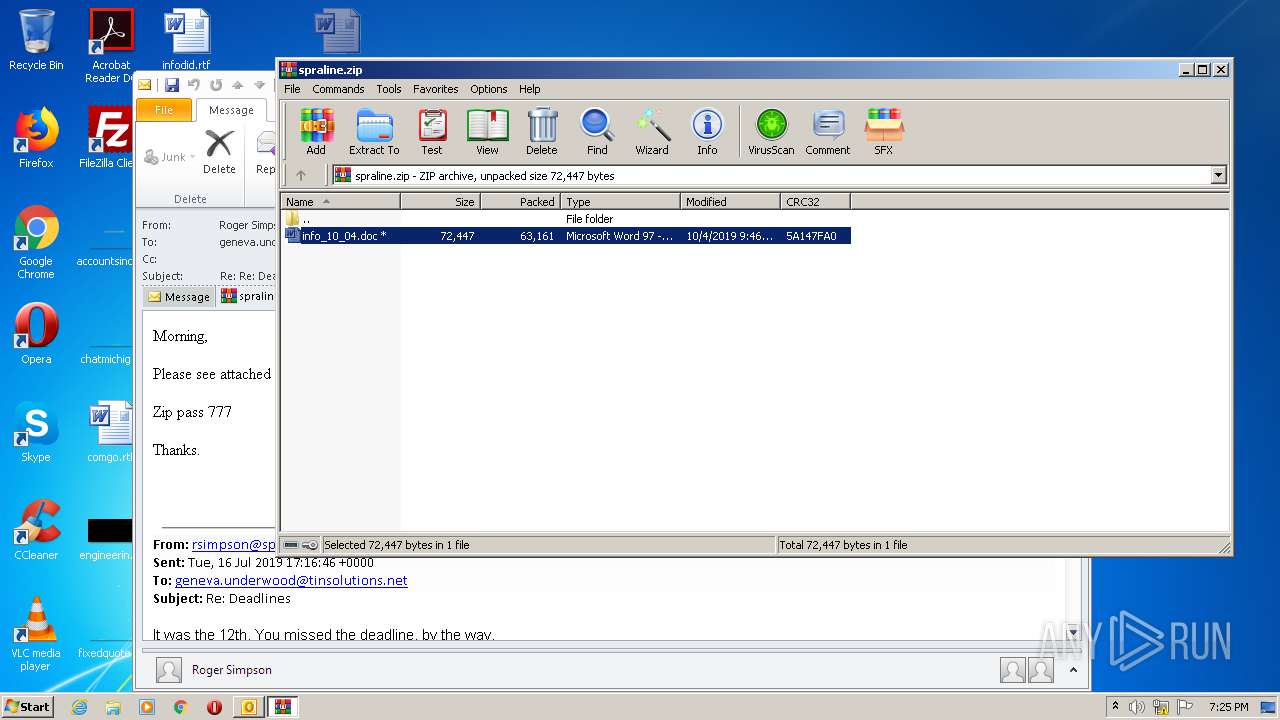
| 1868 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RE0WF8LU\spraline.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1872 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\2019-10-05-traffic-analysis-exercise-email-Deadlines.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2196 | "C:\Windows\System32\wbem\WMIC.exe" process list /format:"C:\Users\admin\AppData\Local\Temp\aA8lQ" | C:\Windows\System32\wbem\WMIC.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147614729 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
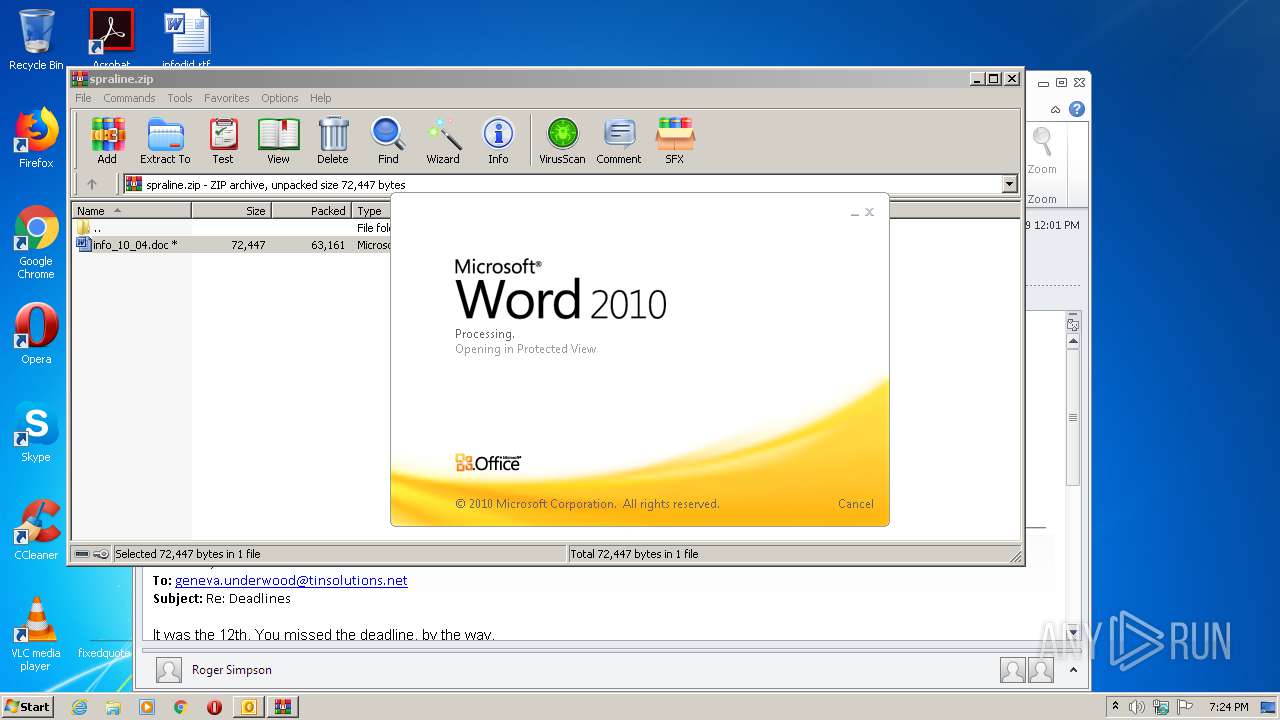
| 2708 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb1868.10239\info_10_04.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
5 462
Read events
3 681
Write events
1 591
Delete events
190
Modification events
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
5
Text files
30
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR731E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RE0WF8LU\spraline (2).zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFC82.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_D72904A6-0F58-4926-8656-5DC43AA06584.0\CBF4CE72.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1872 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_D72904A6-0F58-4926-8656-5DC43AA06584.0\E8062D38.jpeg | — | |
MD5:— | SHA256:— | |||
| 1868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb1868.10239\info_10_04.doc | document | |
MD5:— | SHA256:— | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_D72904A6-0F58-4926-8656-5DC43AA06584.0\CBF4CE72.doc | document | |
MD5:— | SHA256:— | |||
| 1872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_AA6084B689C49F4A9BCFC6034C5B181C.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\ED1E7CB.jpeg | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1872 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1872 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
xoccolearp.com |
| malicious |