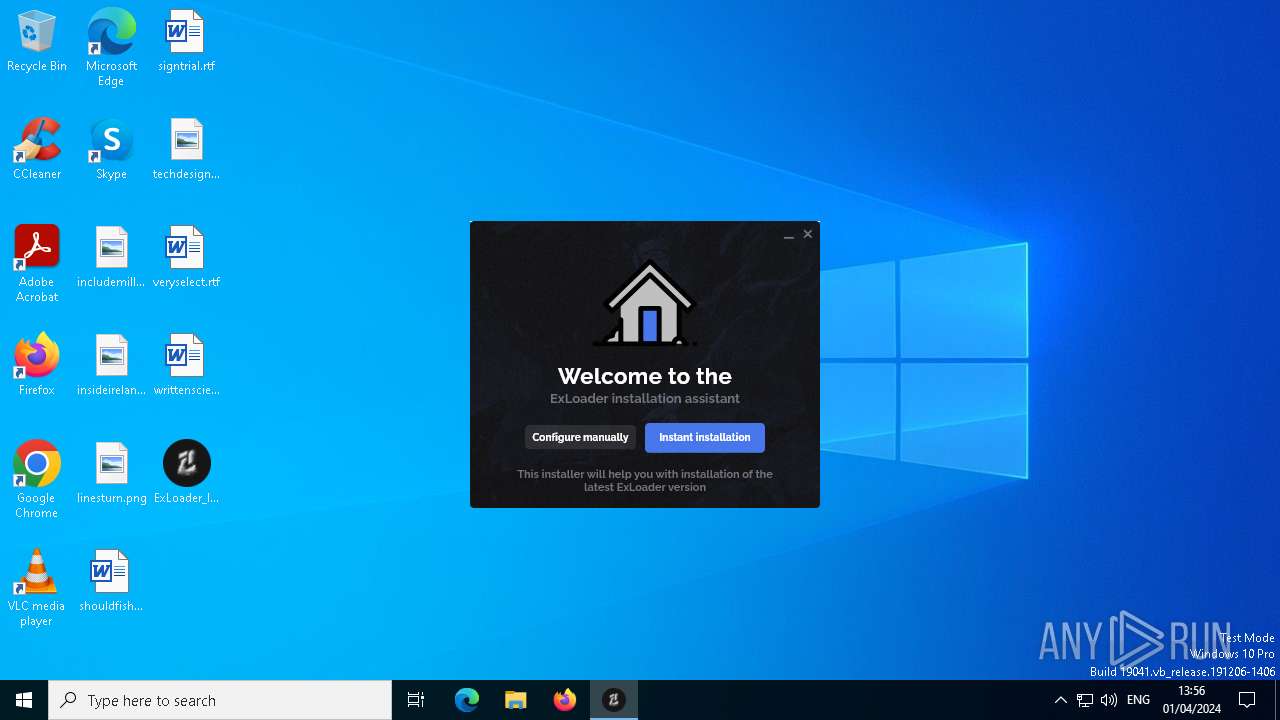
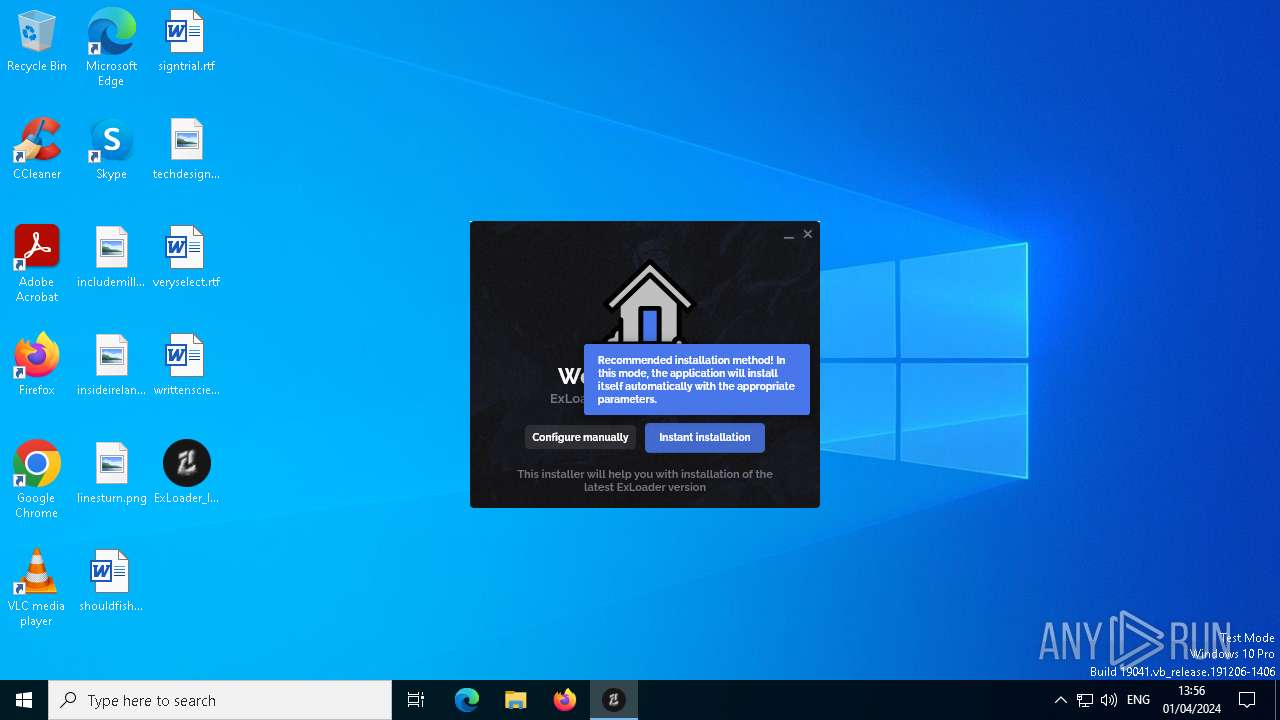
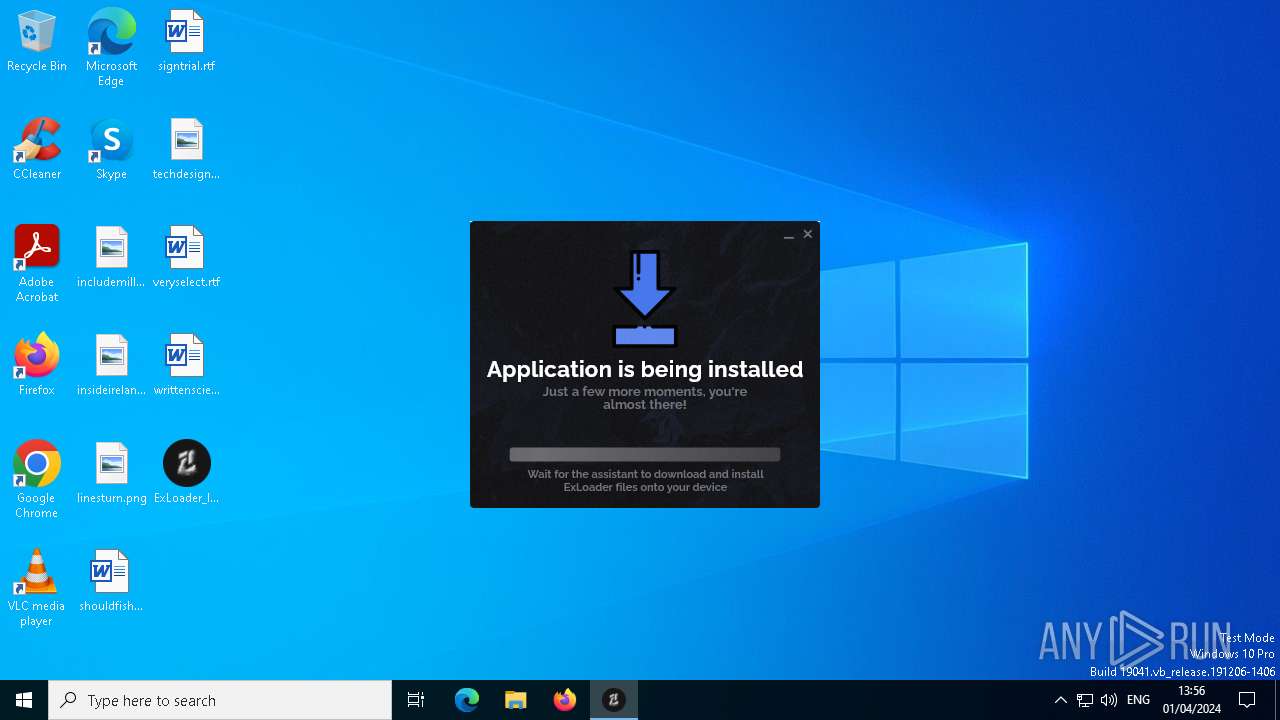
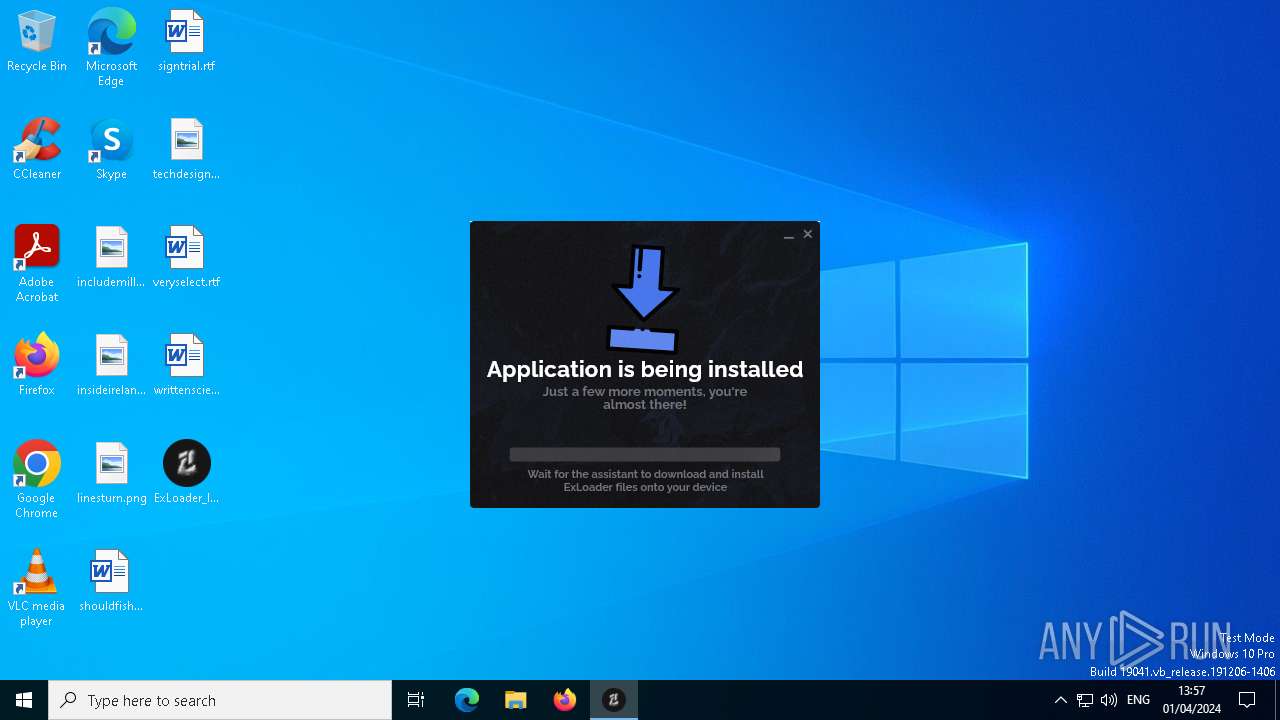
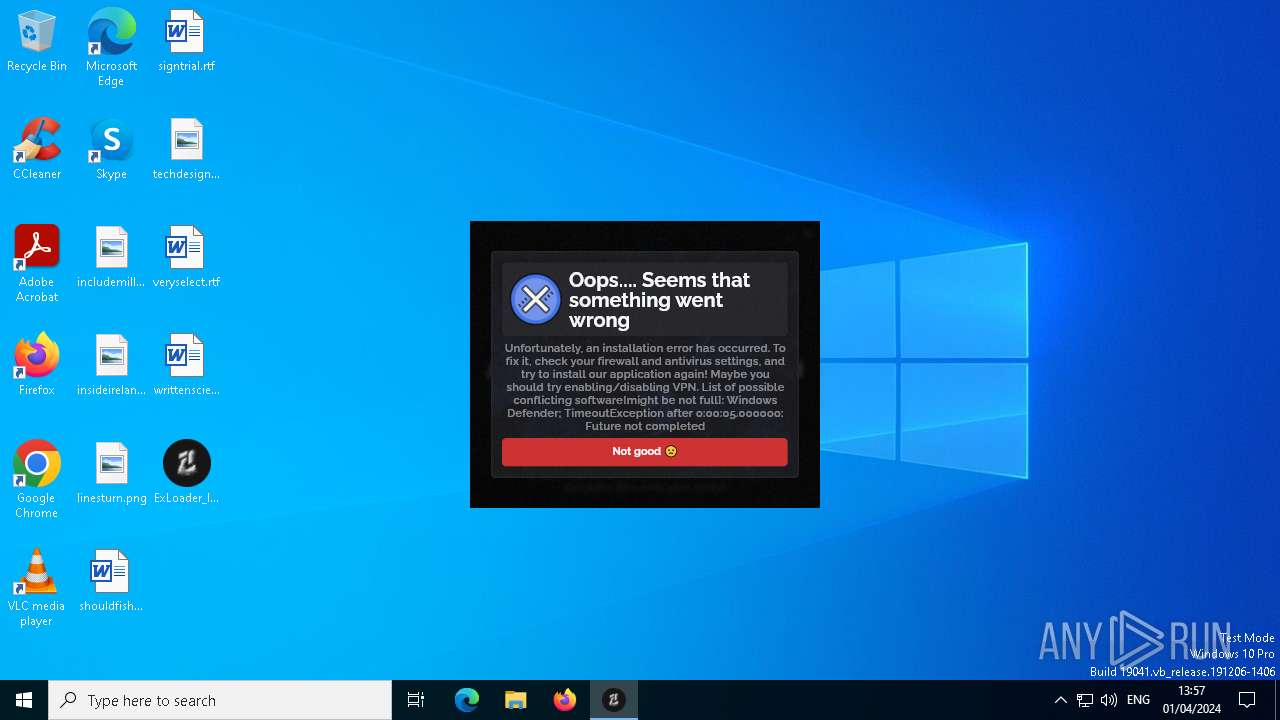
| File name: | ExLoader_Installer.exe |
| Full analysis: | https://app.any.run/tasks/68c1c9d2-5337-4ffd-9708-41c664e6b344 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2024, 12:55:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, RAR self-extracting archive |
| MD5: | 06D4E995805A2AFD7496F4F4F0000FD2 |
| SHA1: | DB80FB0F047F5754AA33781268421407FD07D29E |
| SHA256: | 7AD99C1905E0C0CA46BD97650A50645592A6006F05062AA4580198C41C6491A1 |
| SSDEEP: | 196608:smULqVWgyM24Lkb+bH+kMwqLAuSqhU4yKxBh1:smUL2vyMVLkabH+kDqlSI9rh1 |
MALICIOUS
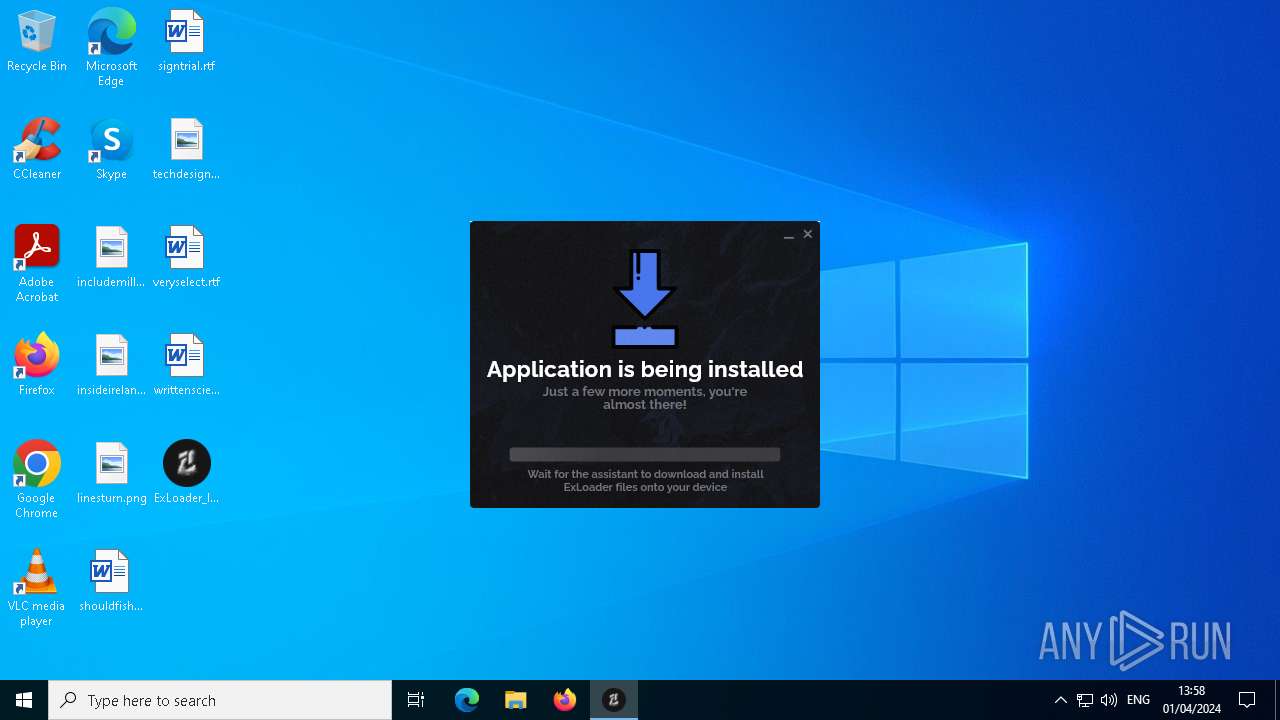
Drops the executable file immediately after the start
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
Actions looks like stealing of personal data
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
Adds path to the Windows Defender exclusion list
- ExLoader_Installer.exe (PID: 2088)
- ExLoader_Installer.exe (PID: 4556)
SUSPICIOUS
Process drops legitimate windows executable
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
The process drops C-runtime libraries
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
Reads the date of Windows installation
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
Reads security settings of Internet Explorer
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
- TextInputHost.exe (PID: 1644)
Starts POWERSHELL.EXE for commands execution
- ExLoader_Installer.exe (PID: 2088)
- ExLoader_Installer.exe (PID: 4556)
Found strings related to reading or modifying Windows Defender settings
- ExLoader_Installer.exe (PID: 2088)
- ExLoader_Installer.exe (PID: 4556)
Script adds exclusion path to Windows Defender
- ExLoader_Installer.exe (PID: 2088)
- ExLoader_Installer.exe (PID: 4556)
Uses WMIC.EXE to obtain Windows Installer data
- powershell.exe (PID: 1072)
- powershell.exe (PID: 3912)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 7164)
- WMIC.exe (PID: 4796)
Starts CMD.EXE for commands execution
- ExLoader_Installer.exe (PID: 4556)
- ExLoader_Installer.exe (PID: 2088)
INFO
Create files in a temporary directory
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
Reads the computer name
- ExLoader_Installer.exe (PID: 1532)
- TextInputHost.exe (PID: 1644)
- ExLoader_Installer.exe (PID: 6368)
- ExLoader_Installer.exe (PID: 4556)
- ExLoader_Installer.exe (PID: 2088)
Checks supported languages
- ExLoader_Installer.exe (PID: 1532)
- ExLoader_Installer.exe (PID: 6368)
- ExLoader_Installer.exe (PID: 4556)
- ExLoader_Installer.exe (PID: 2088)
- TextInputHost.exe (PID: 1644)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 2996)
- BackgroundTransferHost.exe (PID: 7156)
- BackgroundTransferHost.exe (PID: 3352)
- BackgroundTransferHost.exe (PID: 7012)
- BackgroundTransferHost.exe (PID: 3840)
- WMIC.exe (PID: 7164)
- WMIC.exe (PID: 4796)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 2996)
- slui.exe (PID: 2568)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2996)
- slui.exe (PID: 2568)
Creates files in the program directory
- ExLoader_Installer.exe (PID: 2088)
- ExLoader_Installer.exe (PID: 4556)
Creates files or folders in the user directory
- ExLoader_Installer.exe (PID: 2088)
- ExLoader_Installer.exe (PID: 4556)
- BackgroundTransferHost.exe (PID: 2996)
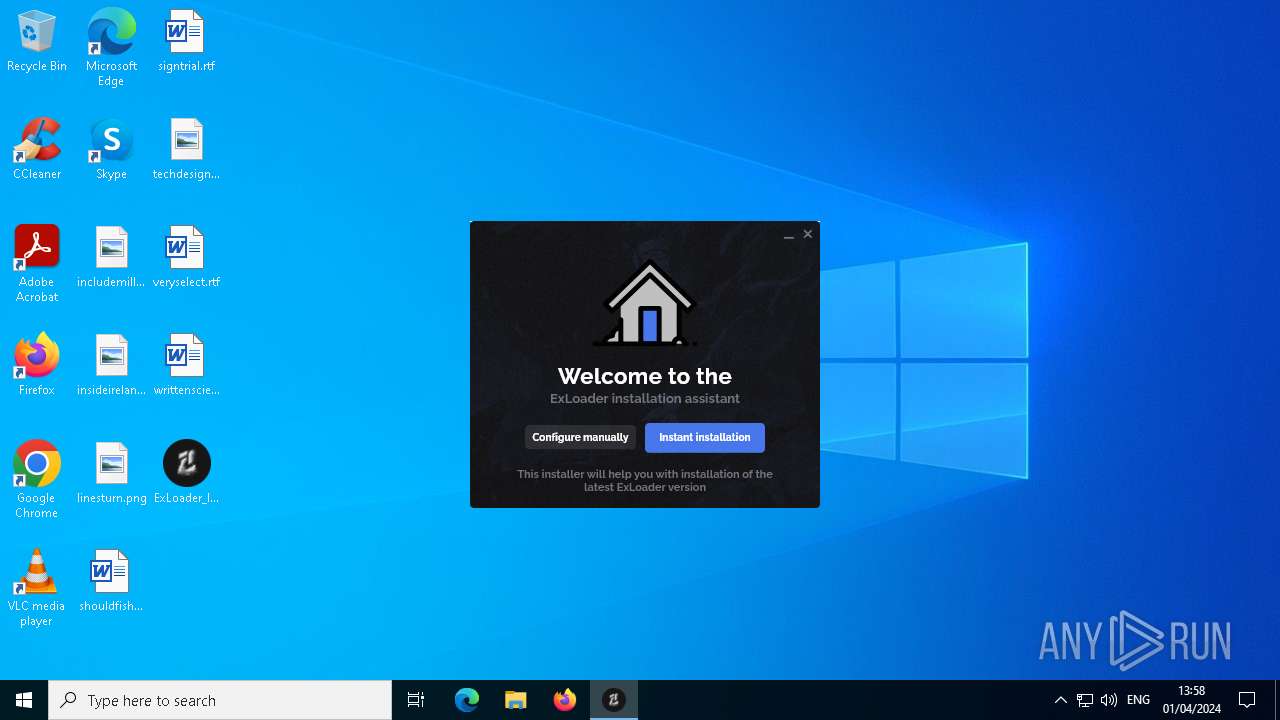
Manual execution by a user
- ExLoader_Installer.exe (PID: 6368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2009:08:16 11:05:40+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 9 |
| CodeSize: | 86016 |
| InitializedDataSize: | 107520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce80 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
186
Monitored processes
52
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -command Add-MpPreference -ExclusionPath "\"C:\Program Files\ExLoader\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ExLoader_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -command Add-MpPreference -ExclusionPath "\"C:\Program Files\ExLoader\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ExLoader_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -command C:\Windows\System32\wbem\wmic.exe /node:localhost /namespace:\\root\SecurityCenter2 path AntiVirusProduct | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ExLoader_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1260 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | C:\Windows\System32\reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender" /v DisableAntiSpyware | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\Desktop\ExLoader_Installer.exe" | C:\Users\admin\Desktop\ExLoader_Installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1640 | C:\Windows\System32\cmd.exe /C C:\Windows\System32\reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender" /v DisableAntiSpyware | C:\Windows\System32\cmd.exe | — | ExLoader_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1640 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\ExLoader_Installer.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\ExLoader_Installer.exe | — | ExLoader_Installer.exe | |||||||||||
User: admin Company: com.swiftsoft Integrity Level: MEDIUM Description: Installer for unified library of game modifications. Exit code: 3221226540 Version: 3.4.57+0 Modules
| |||||||||||||||
| 1644 | "C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\InputApp\TextInputHost.exe" -ServerName:InputApp.AppX9jnwykgrccxc8by3hsrsh07r423xzvav.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\InputApp\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 2001.22012.0.3920 Modules
| |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
63 043
Read events
63 010
Write events
33
Delete events
0
Modification events
| (PID) Process: | (1532) ExLoader_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Users%admin%AppData%Local%Temp |
Value: C:\Users\admin\AppData\Local\Temp\RarSFX0 | |||
| (PID) Process: | (1532) ExLoader_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1532) ExLoader_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1532) ExLoader_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1532) ExLoader_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7156) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7156) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7156) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2996) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2996) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
16
Suspicious files
44
Text files
1 021
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\vcruntime140.dll | executable | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\vcruntime140_1.dll | executable | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\app.so | — | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\flutter_assets\AssetManifest.bin | binary | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\flutter_assets\AssetManifest.json | binary | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\flutter_assets\FontManifest.json | text | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\flutter_assets\fonts\MaterialIcons-Regular.otf | binary | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\flutter_assets\NOTICES.Z | compressed | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\flutter_assets\resources\audio\AbominationPissed_DE.wav | binary | |
MD5:— | SHA256:— | |||
| 1532 | ExLoader_Installer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\flutter_assets\resources\audio\AbominationPissed_EN.wav | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
73
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2088 | ExLoader_Installer.exe | GET | 301 | 213.180.193.146:443 | https://meteum.ai/ | unknown | — | — | unknown |
4680 | backgroundTaskHost.exe | GET | — | 20.103.156.88:443 | https://arc.msn.com/v3/Delivery/Placement?pubid=da63df93-3dbc-42ae-a505-b34988683ac7&pid=88000045&adm=2&w=1&h=1&wpx=1&hpx=1&fmt=json&cltp=app&dim=le&rafb=0&nct=1&pm=1&cfmt=text,image,poly&sft=jpeg,png,gif&topt=1&poptin=0&localid=w:AC7699B0-48EA-FD22-C8DC-06A02098A0F0&ctry=US&time=20240401T125556Z&lc=en-US&pl=en-US&idtp=mid&uid=9115d6d1-9f4e-4053-9297-2a8c833b3912&aid=00000000-0000-0000-0000-000000000000&ua=WindowsShellClient%2F9.0.40929.0%20%28Windows%29&asid=ca799d57fdc348cd9dcc5b0b2564e378&ctmode=MultiSession&arch=x64&betaedgever=0.0.0.0&canedgever=0.0.0.0&cdm=1&cdmver=10.0.19041.1023&currsel=137271744000000000&devedgever=0.0.0.0&devfam=Windows.Desktop&devform=Unknown&devosver=10.0.19044.1288&disphorzres=1280&dispsize=15.3&dispvertres=720&fosver=16299&isu=0&lo=3453415&metered=false&nettype=ethernet&npid=sc-88000045&oemName=DELL&oemid=DELL&ossku=Professional&prevosver=15063&smBiosDm=DELL&stabedgever=122.0.2365.66&tl=2&tsu=843945&waasBldFlt=1&waasCfgExp=1&waasCfgSet=1&waasRetail=1&waasRing=&svoffered=2 | unknown | — | — | unknown |
4976 | SIHClient.exe | GET | 304 | 52.165.165.26:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19044.1288/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.1288&MK=DELL&MD=DELL | unknown | — | — | unknown |
3996 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4976 | SIHClient.exe | GET | 200 | 52.165.165.26:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19044.1288/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.1288&MK=DELL&MD=DELL | unknown | — | — | unknown |
2088 | ExLoader_Installer.exe | GET | 301 | 213.180.193.146:443 | https://meteum.ai/weather | unknown | text | 14 b | unknown |
4976 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | unknown |
4976 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | unknown |
2088 | ExLoader_Installer.exe | GET | 200 | 213.180.193.146:443 | https://meteum.ai/weather/en-US | unknown | — | — | unknown |
— | — | GET | 200 | 20.166.126.56:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:1900 | — | — | — | unknown |
2088 | ExLoader_Installer.exe | 212.82.100.137:443 | search.yahoo.com | Yahoo! UK Services Limited | IE | shared |
2088 | ExLoader_Installer.exe | 213.180.193.146:443 | meteum.ai | YANDEX LLC | RU | whitelisted |
2088 | ExLoader_Installer.exe | 92.123.104.44:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2088 | ExLoader_Installer.exe | 92.123.104.40:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2088 | ExLoader_Installer.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
4680 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3996 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4976 | SIHClient.exe | 40.68.123.157:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4976 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
search.yahoo.com |
| whitelisted |
meteum.ai |
| unknown |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |