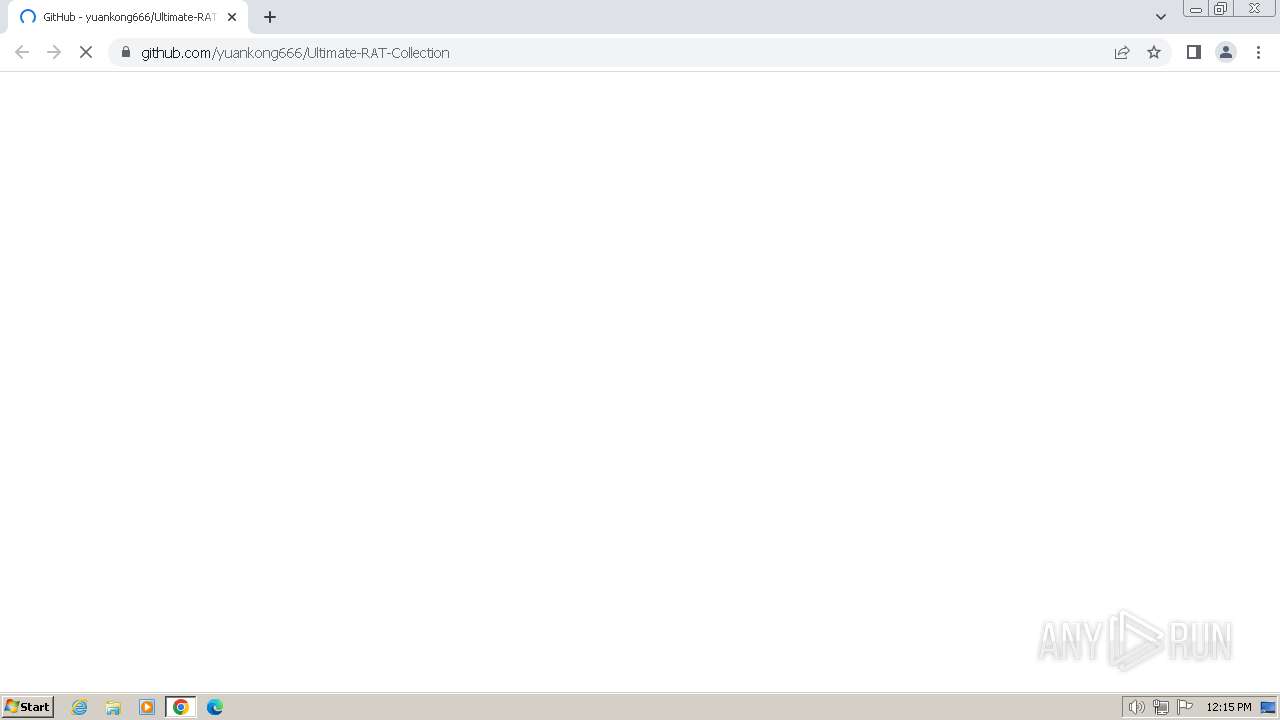
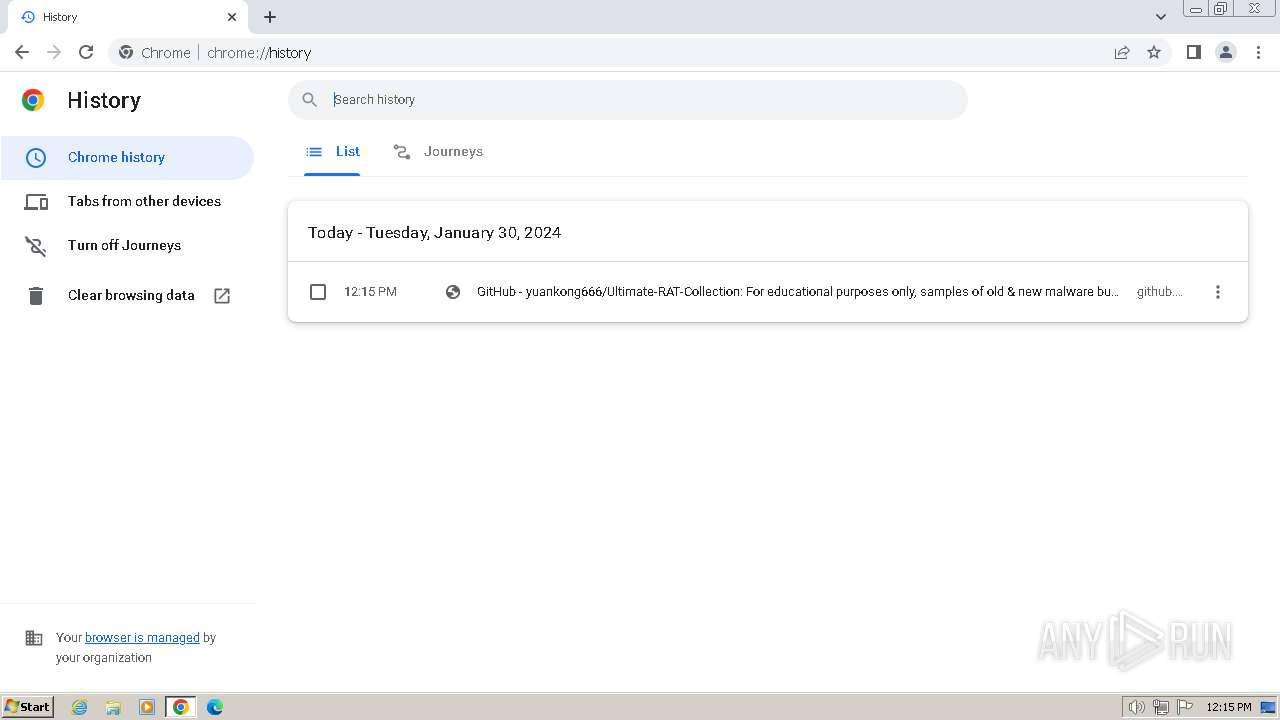
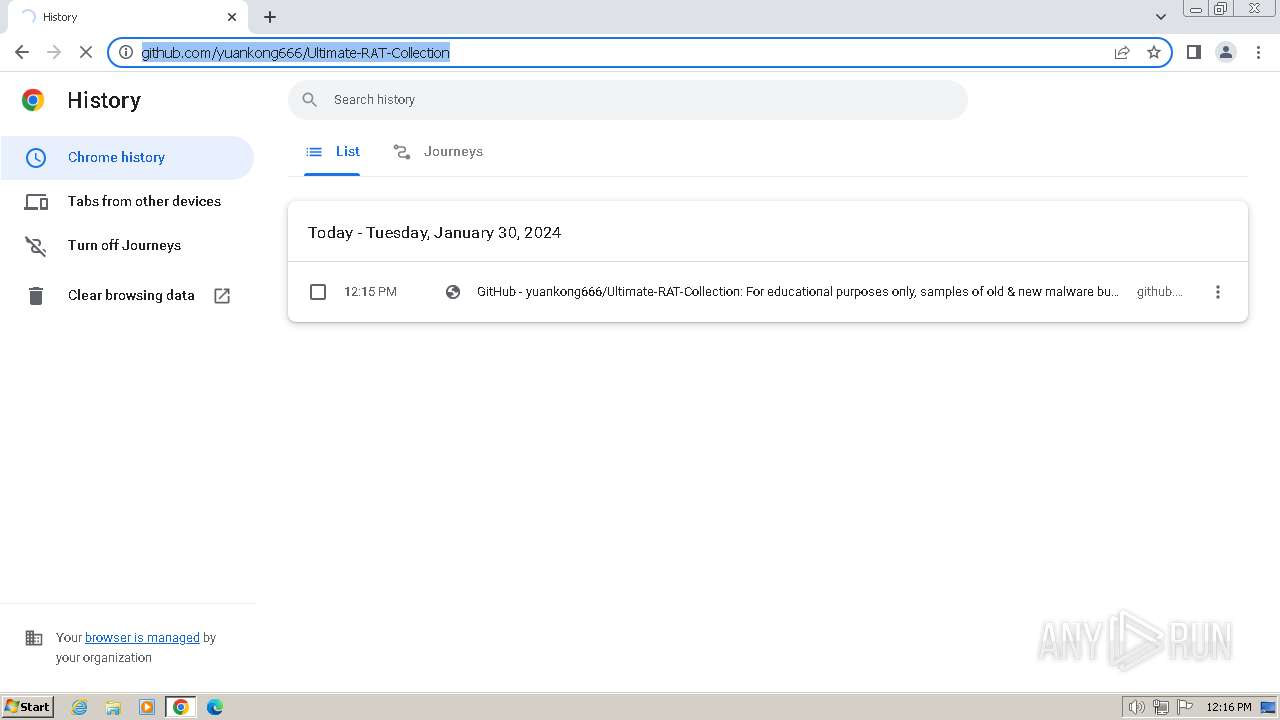
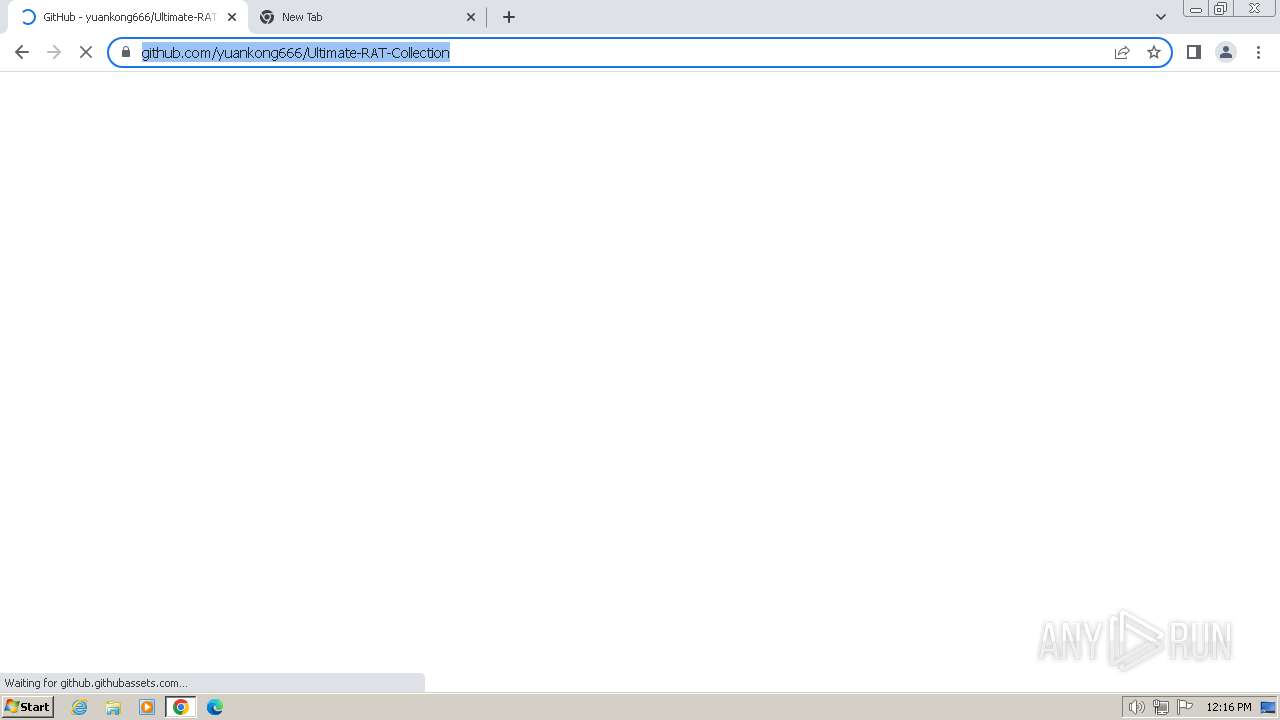
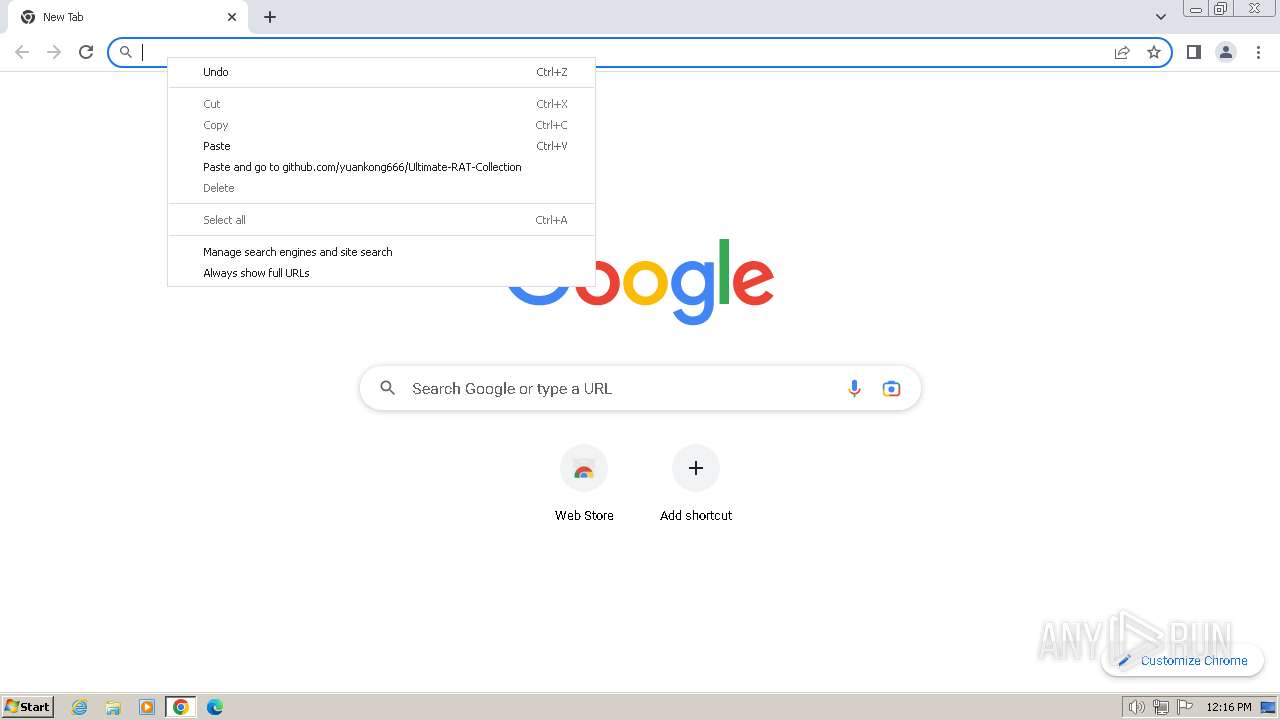
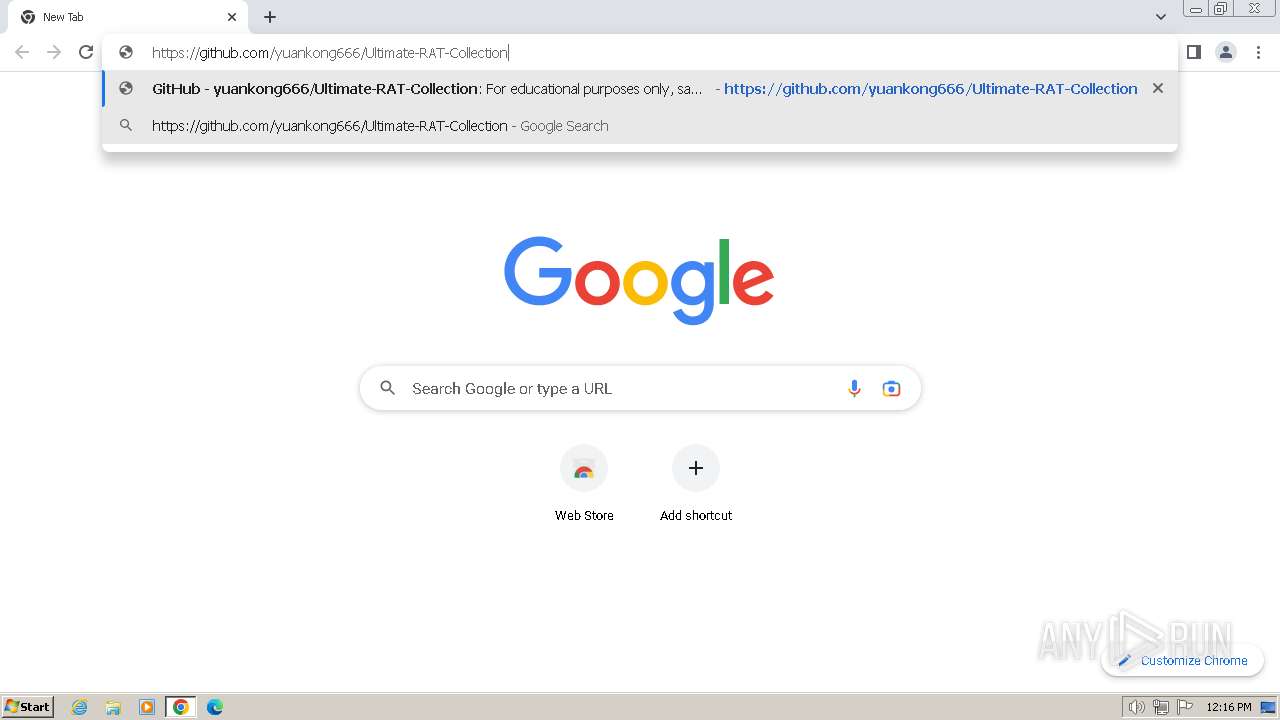
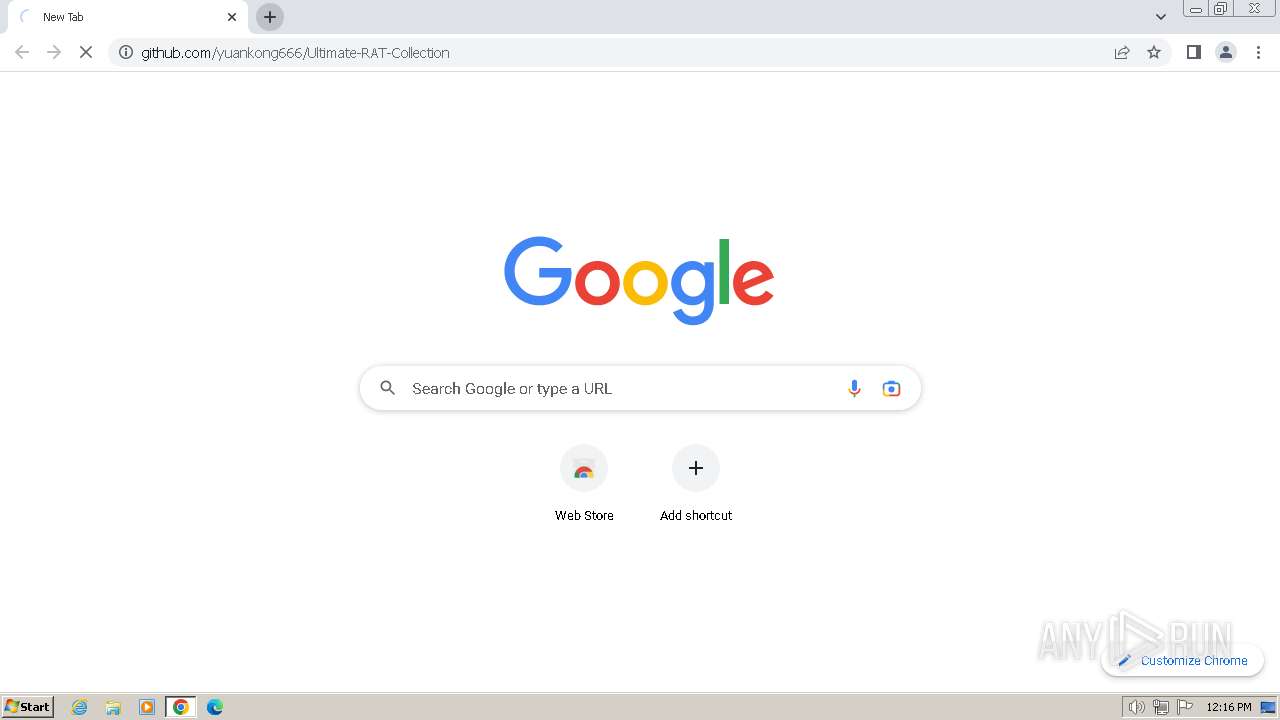
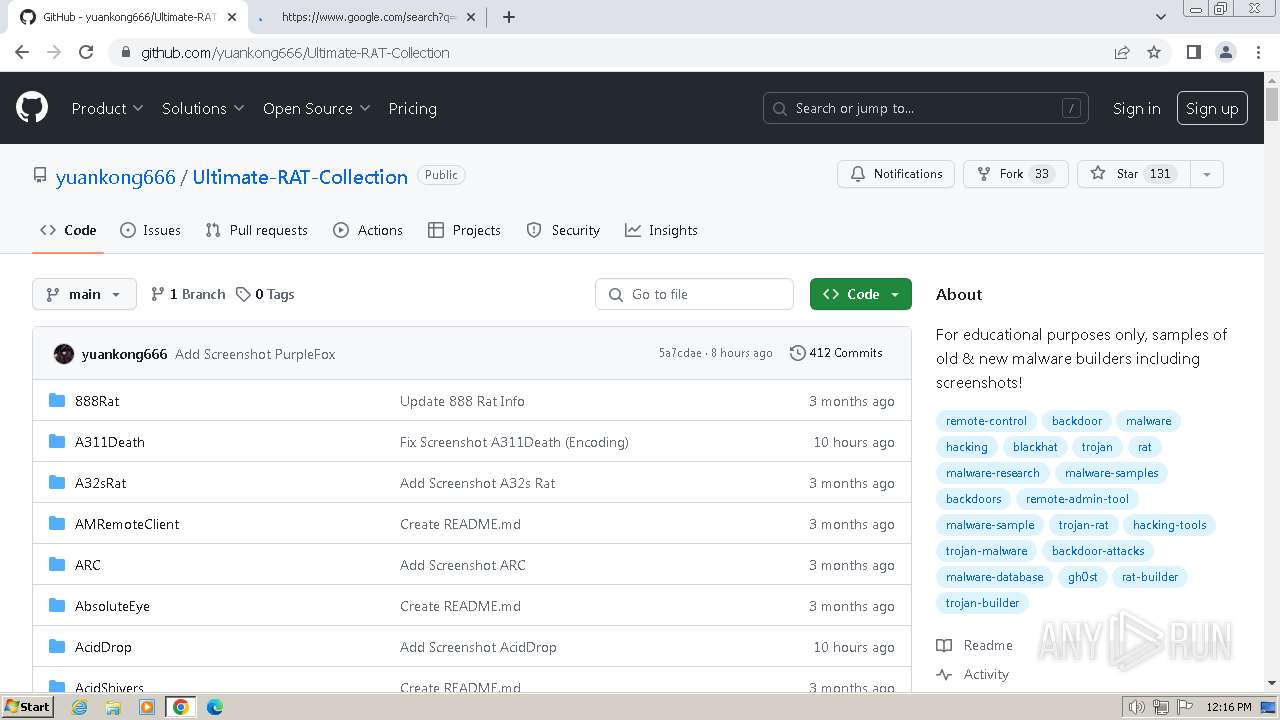
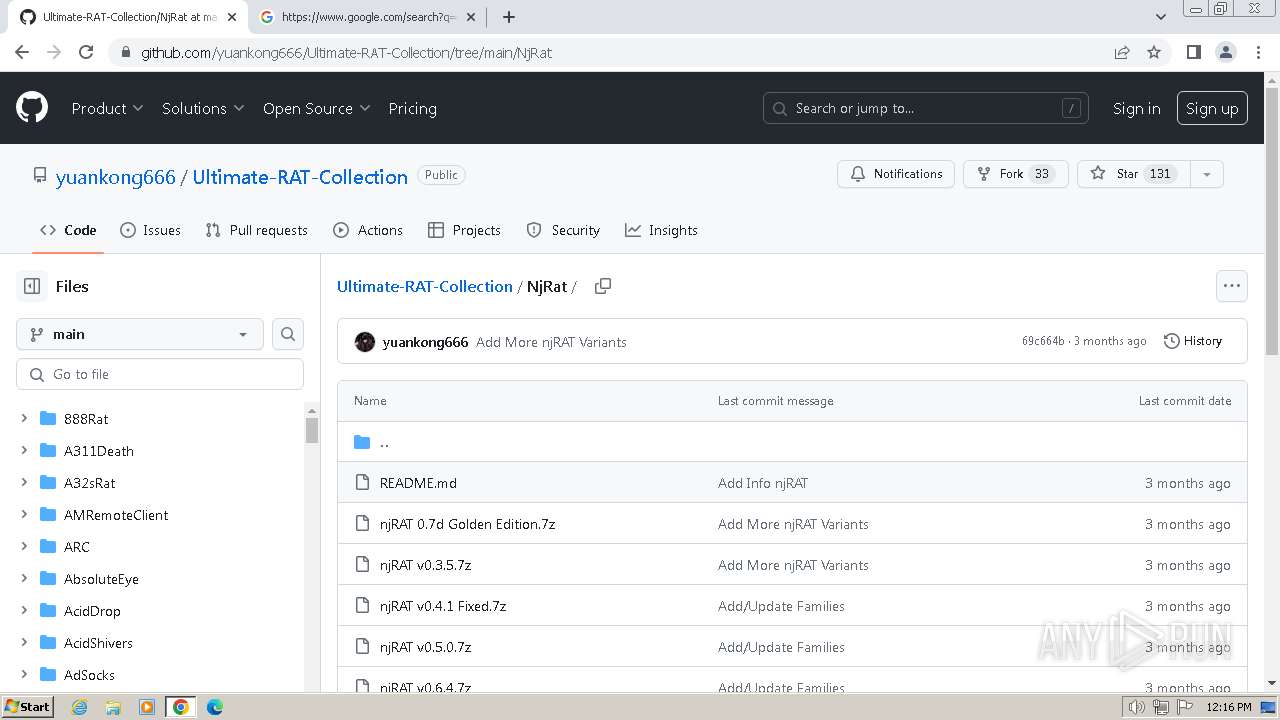
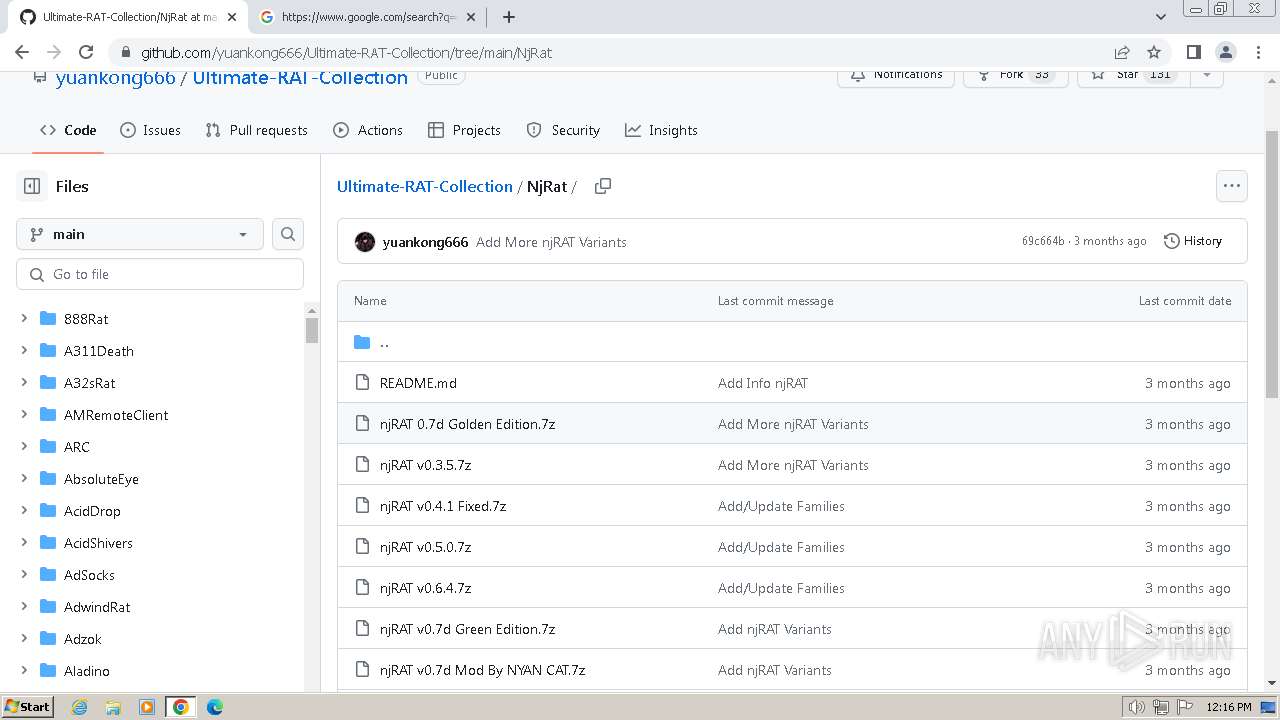
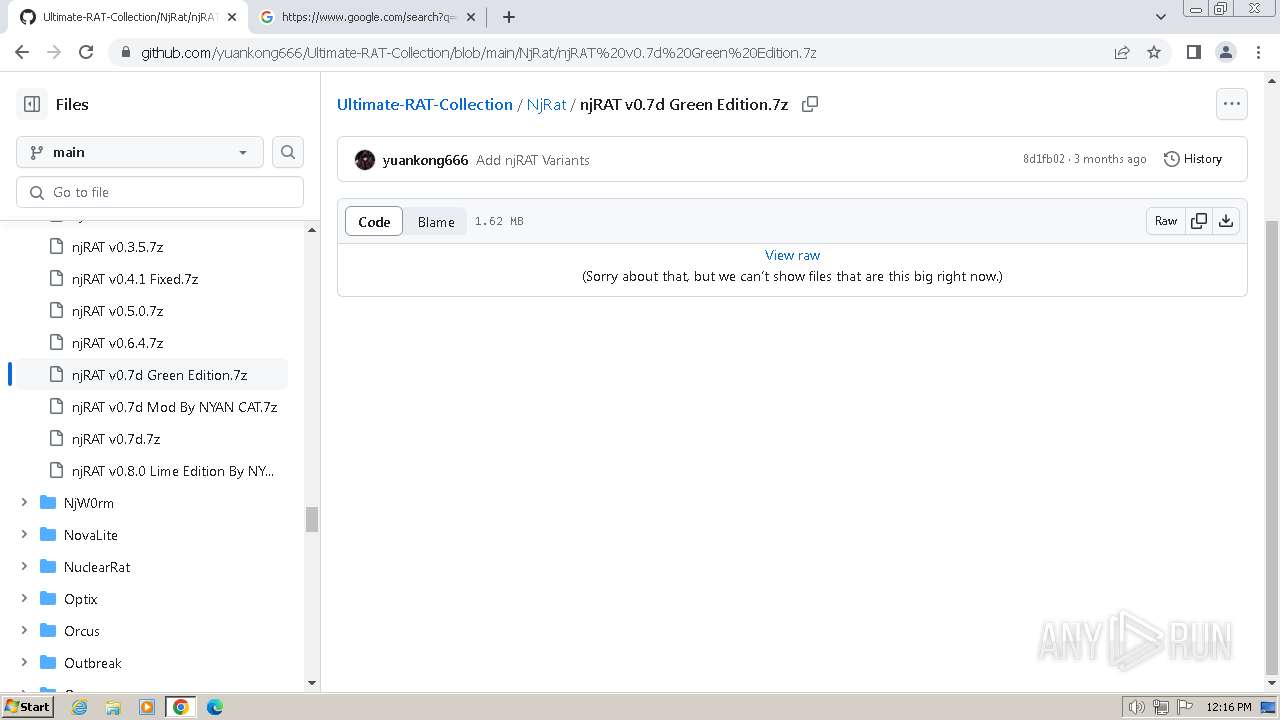
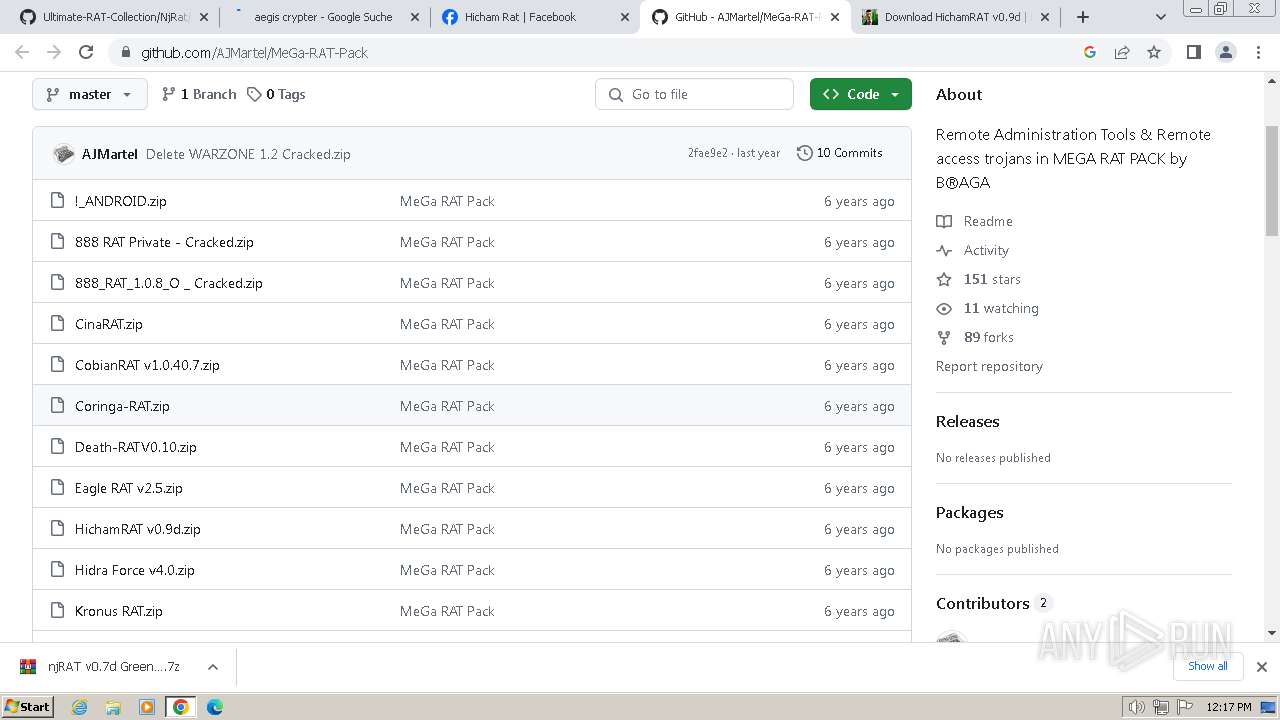
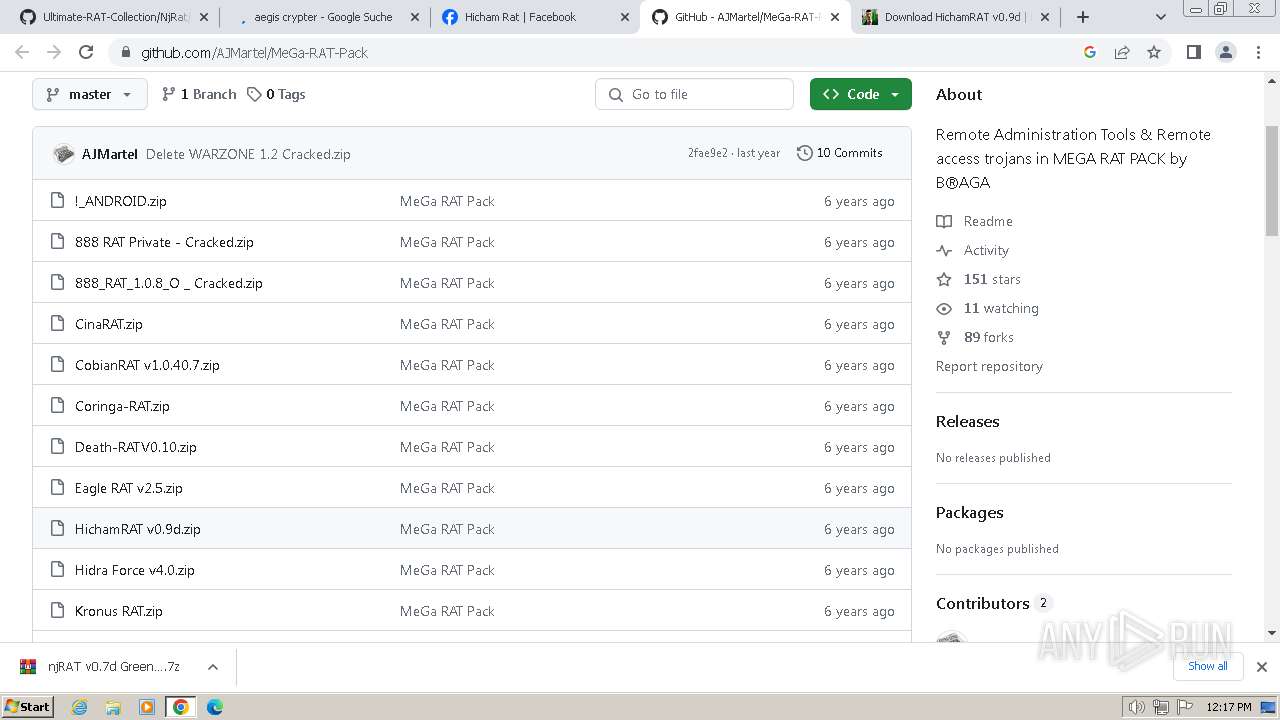
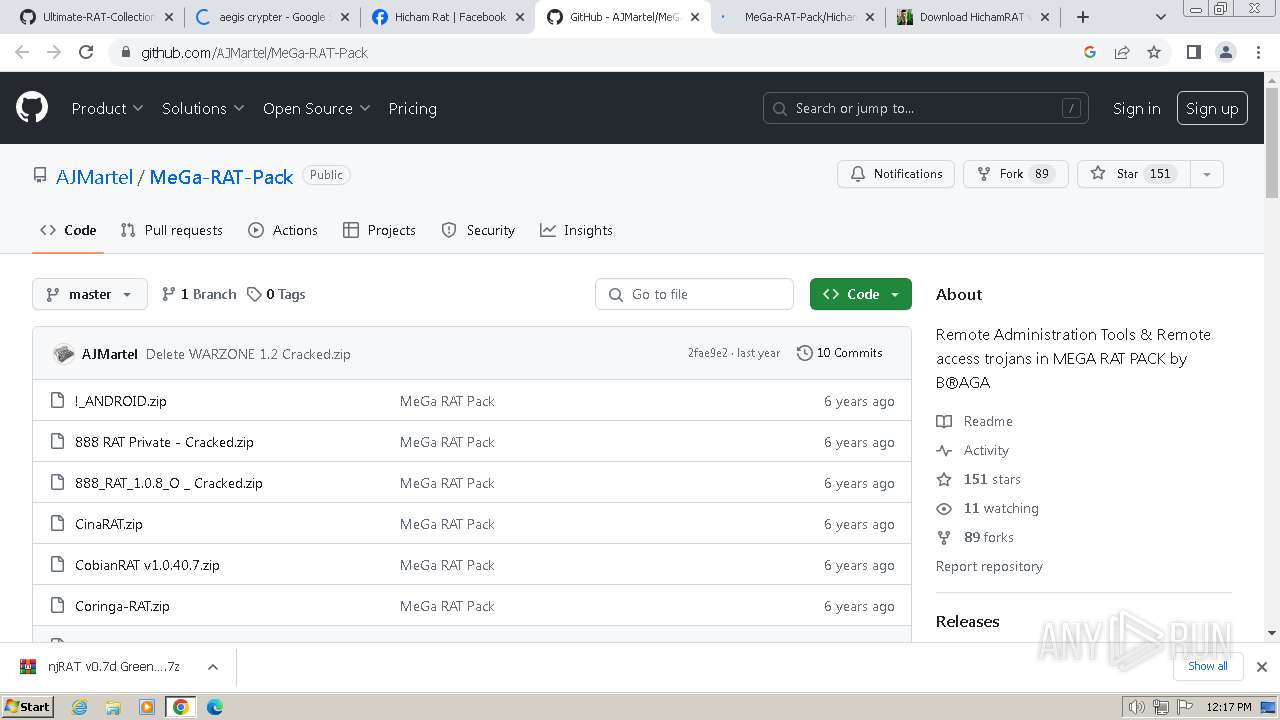
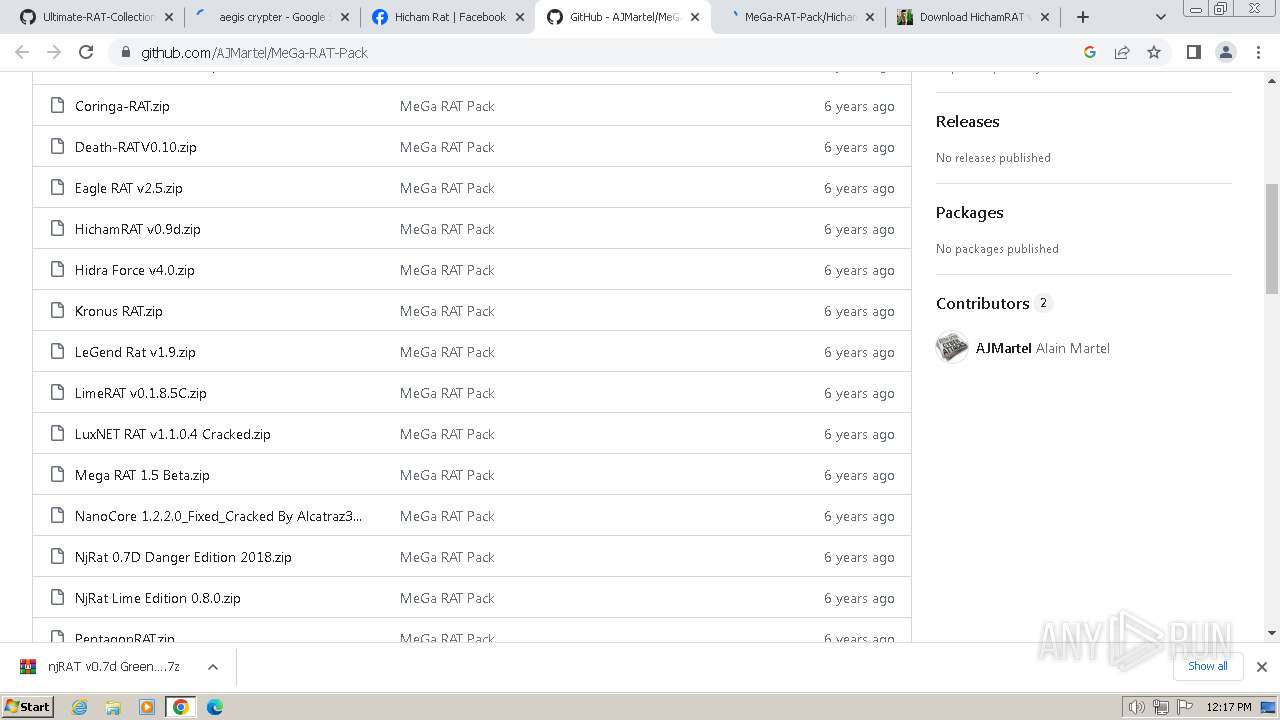
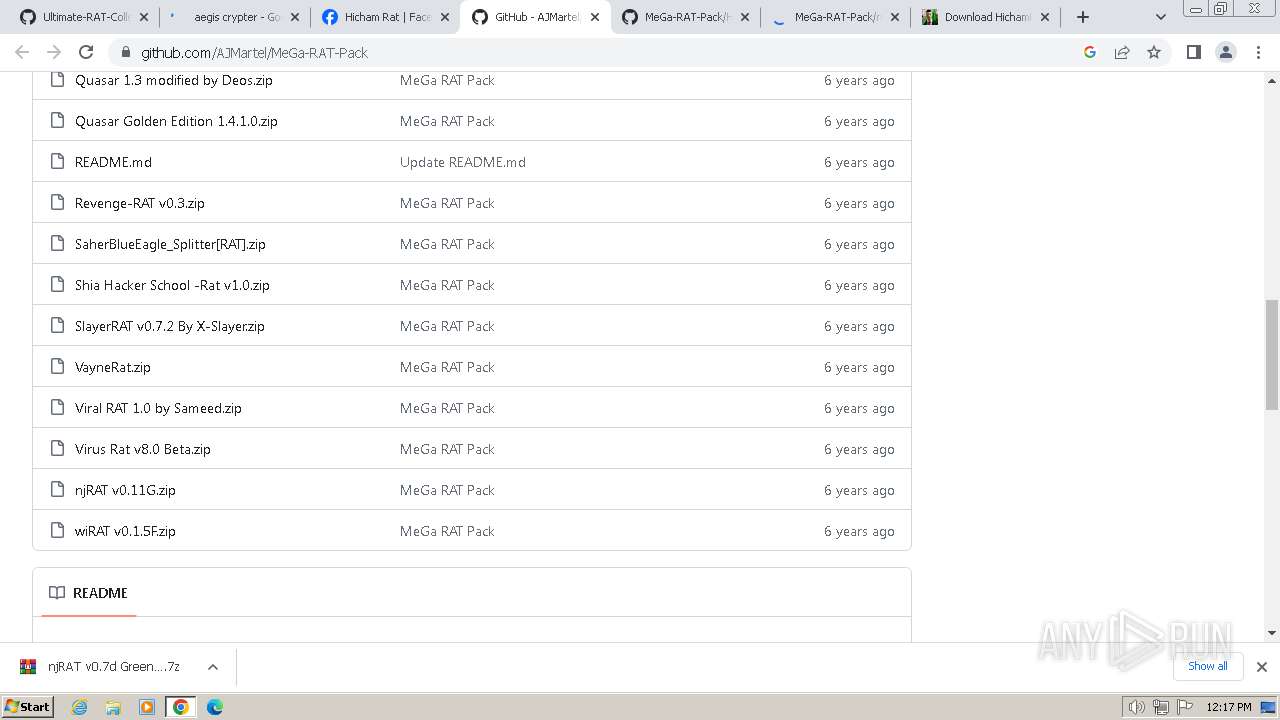
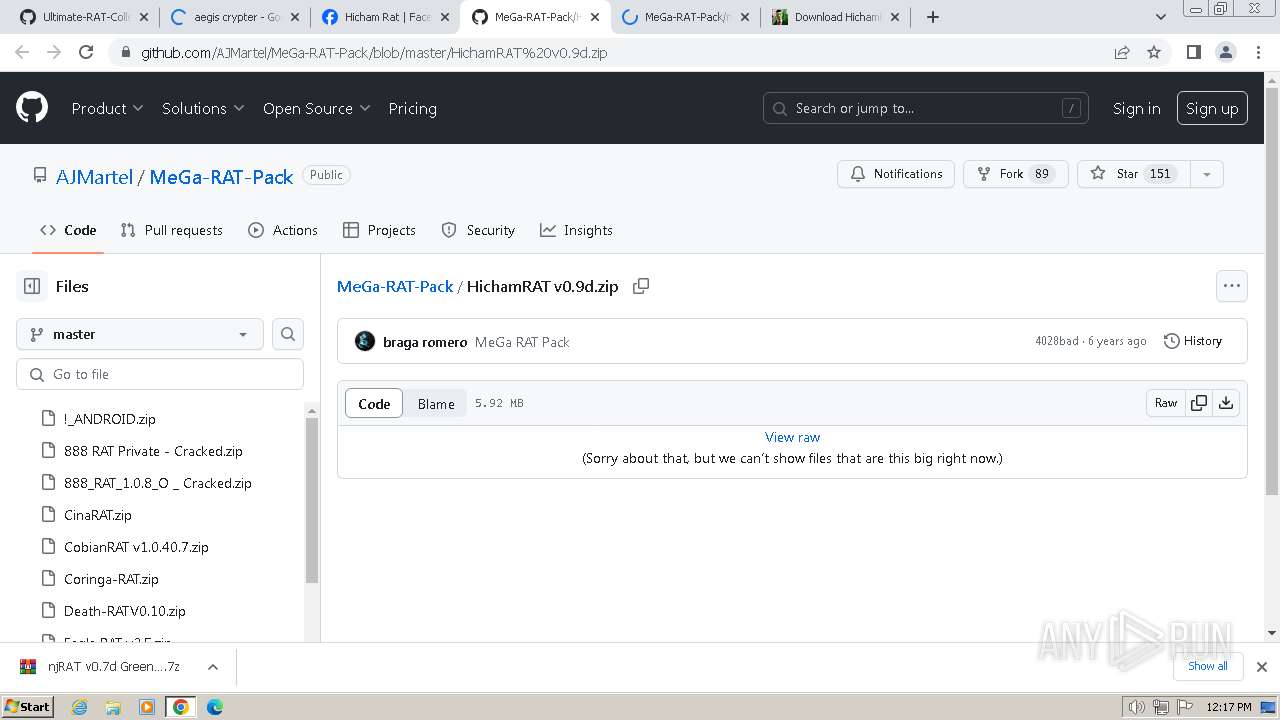
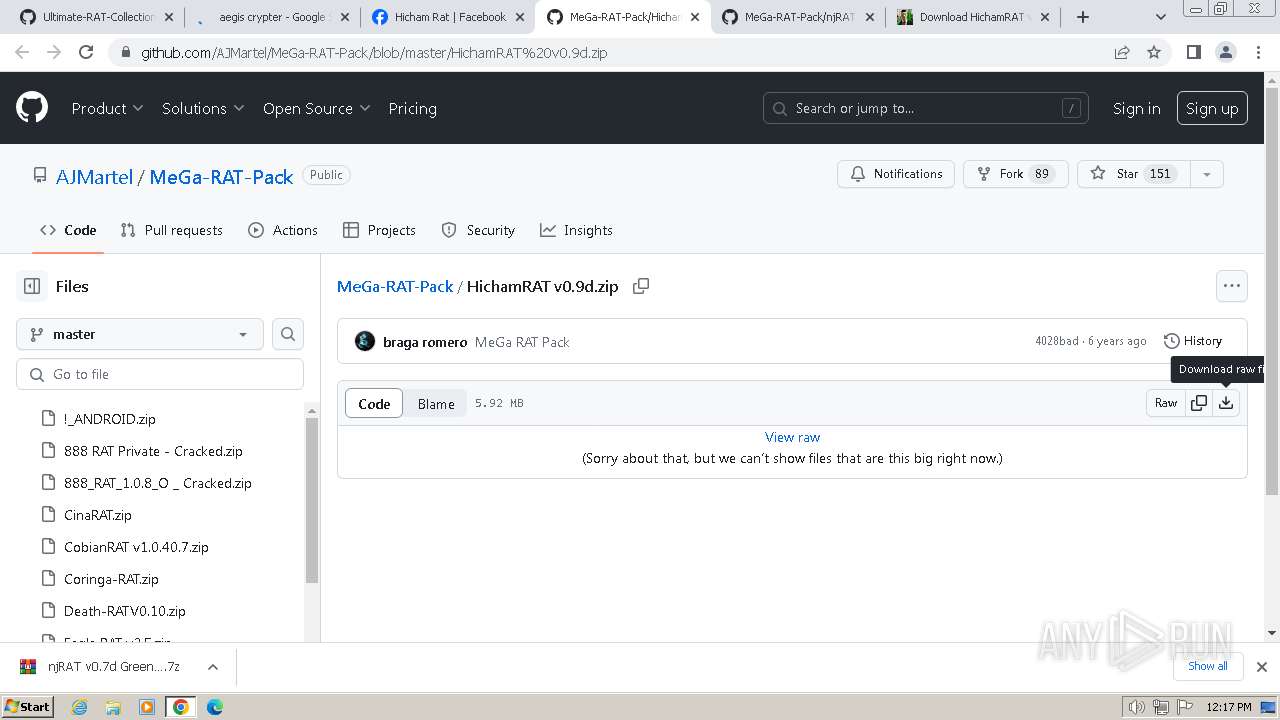
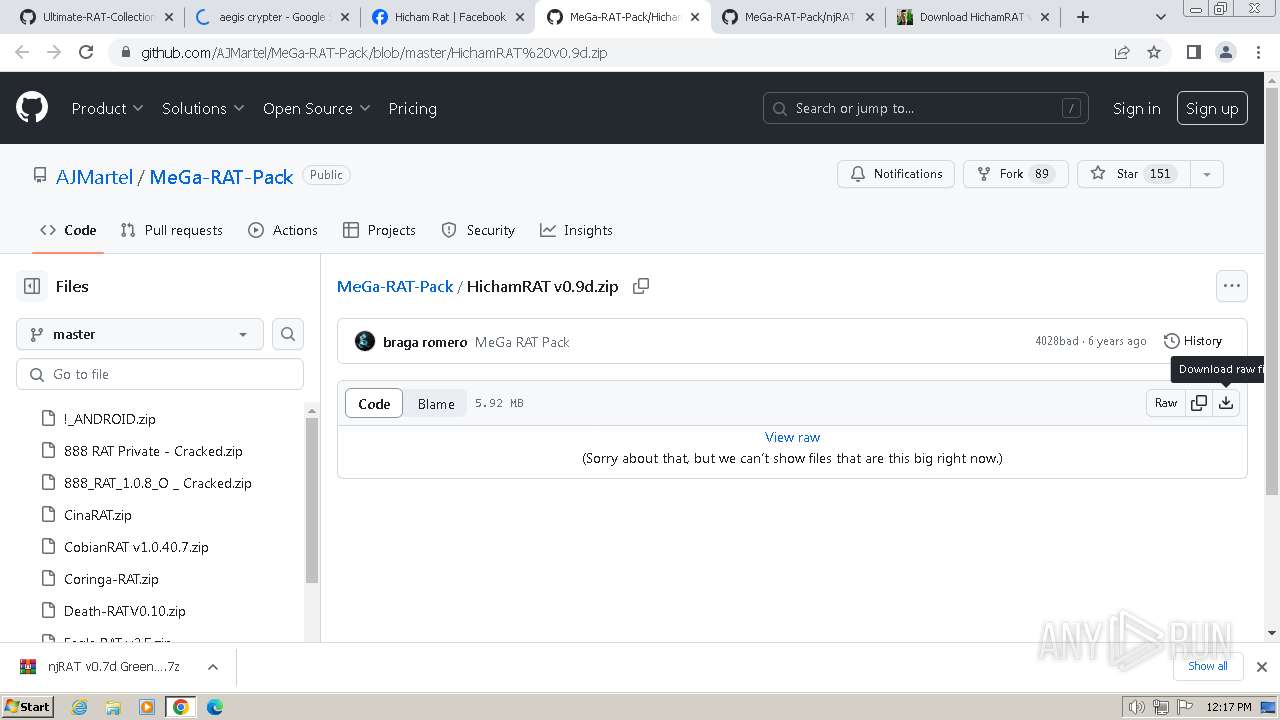
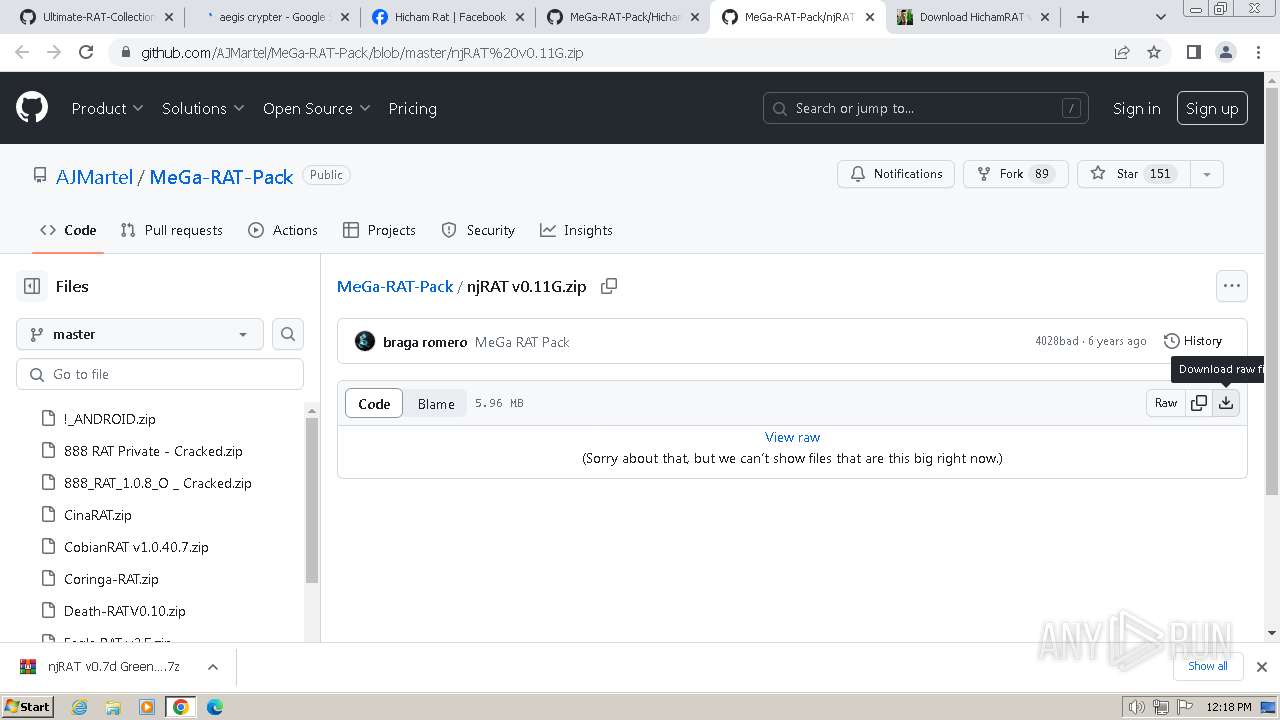
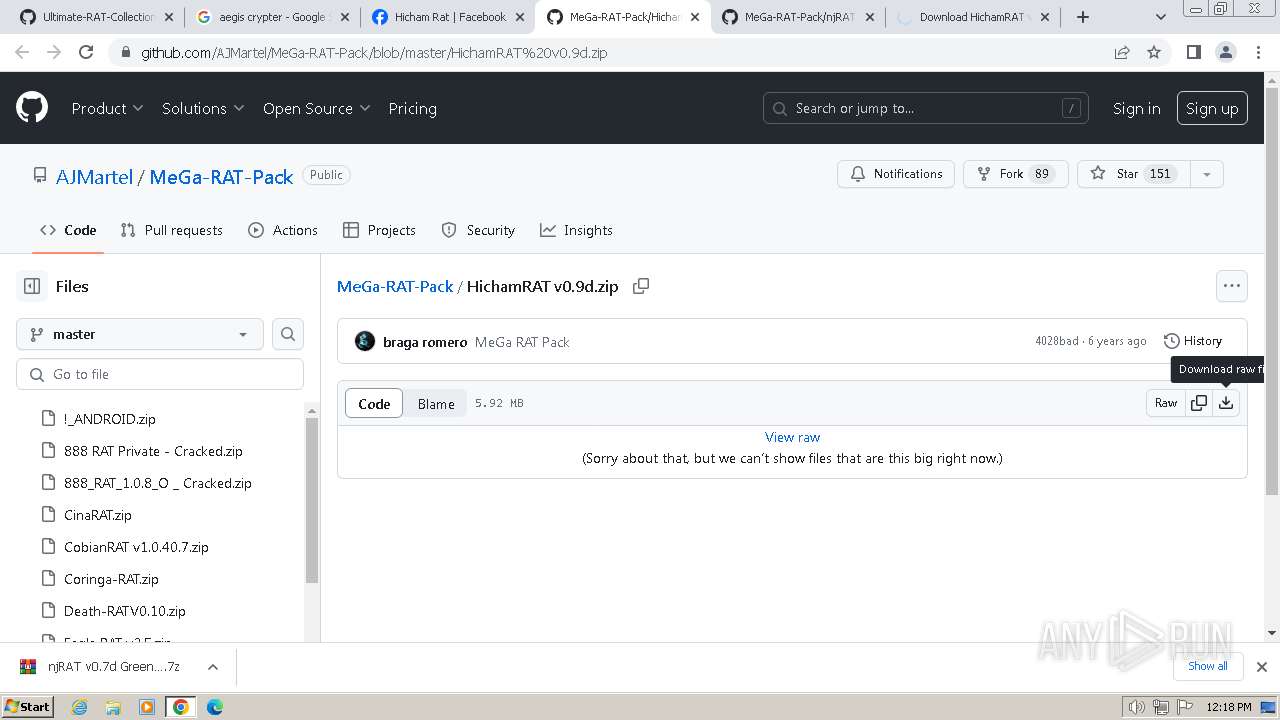
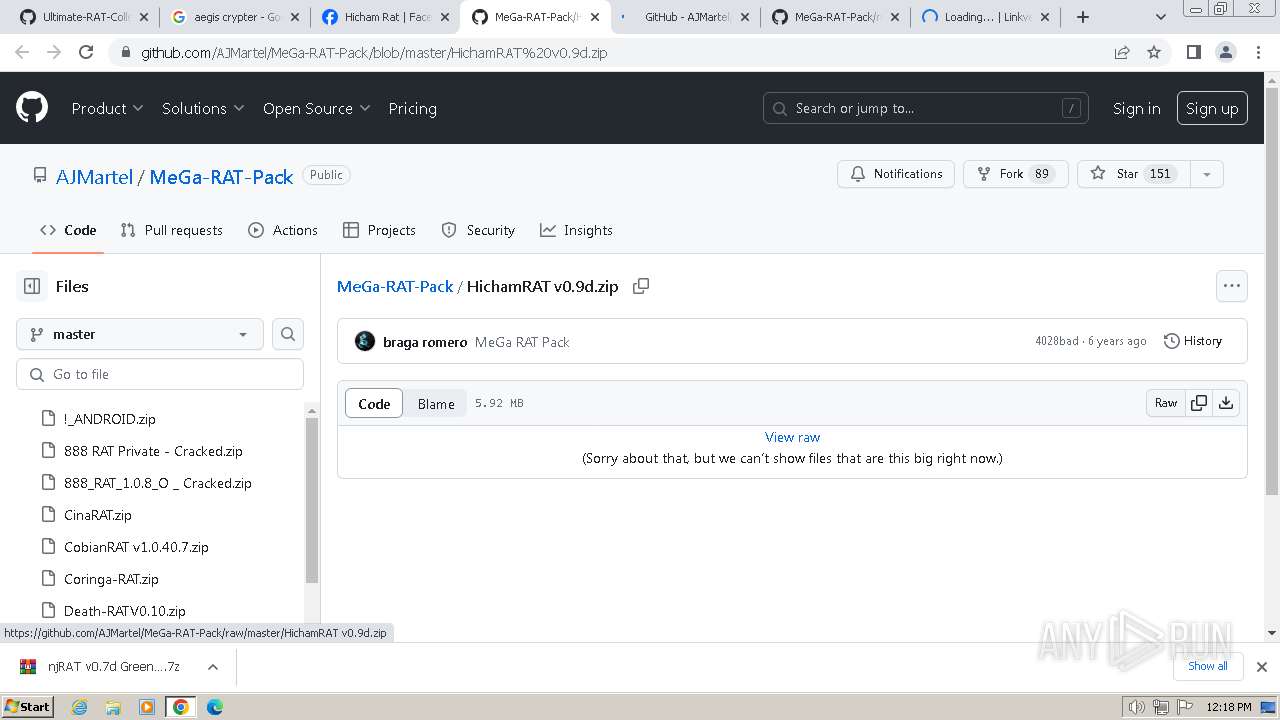
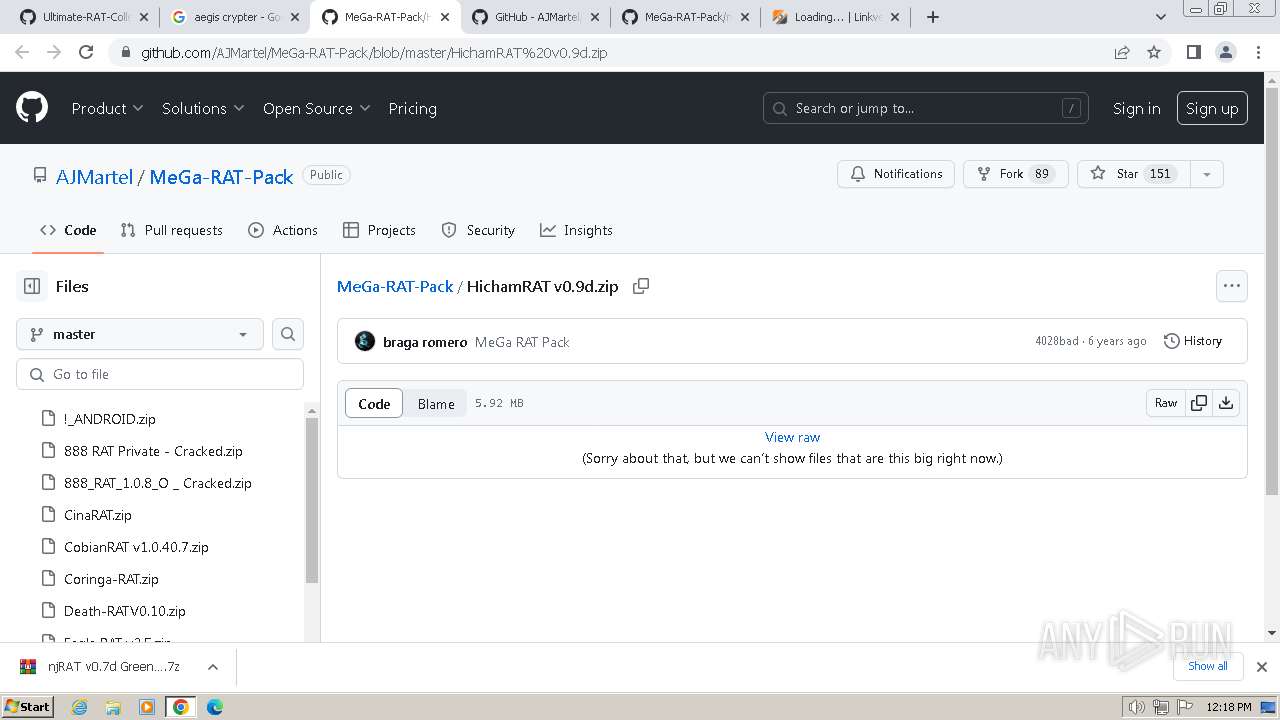
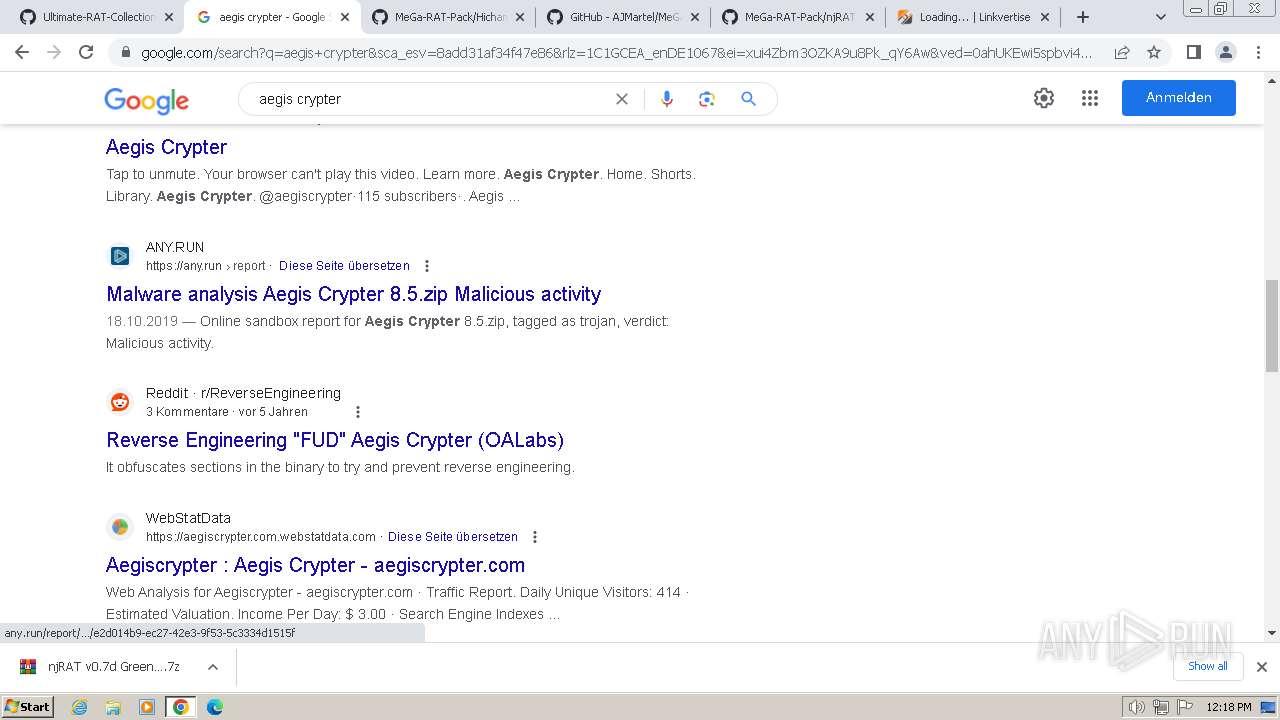
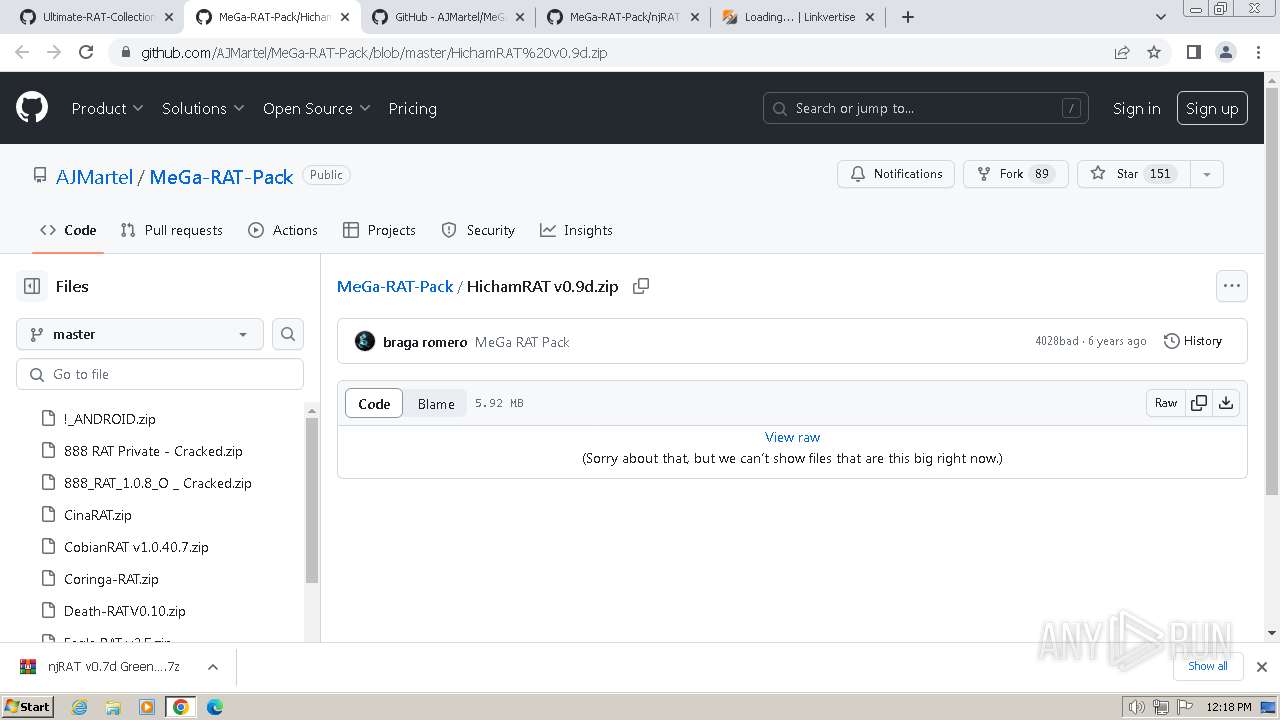
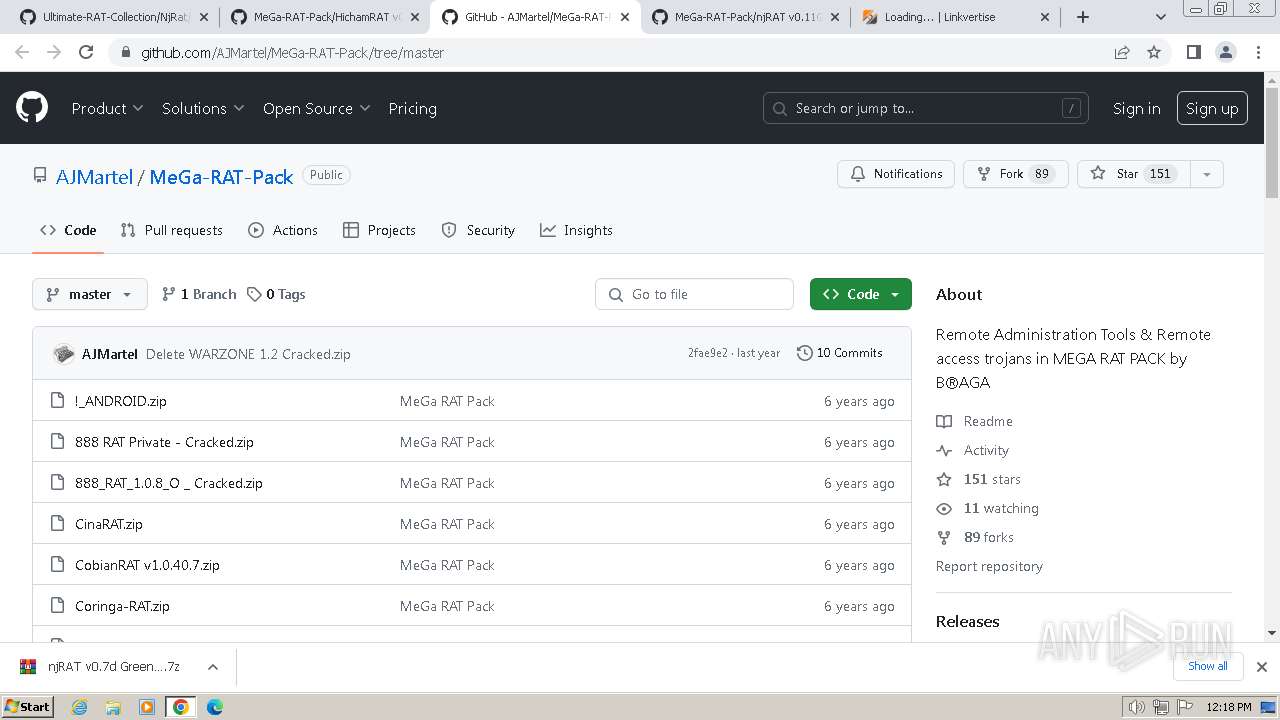
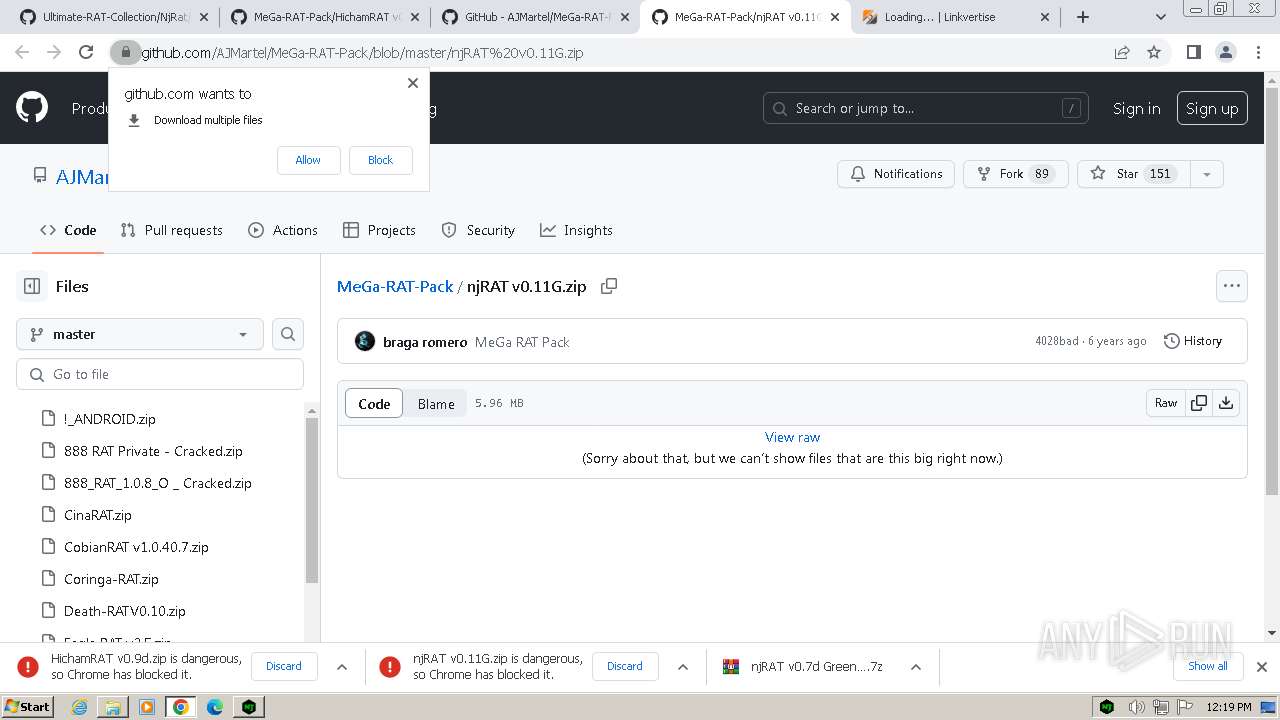
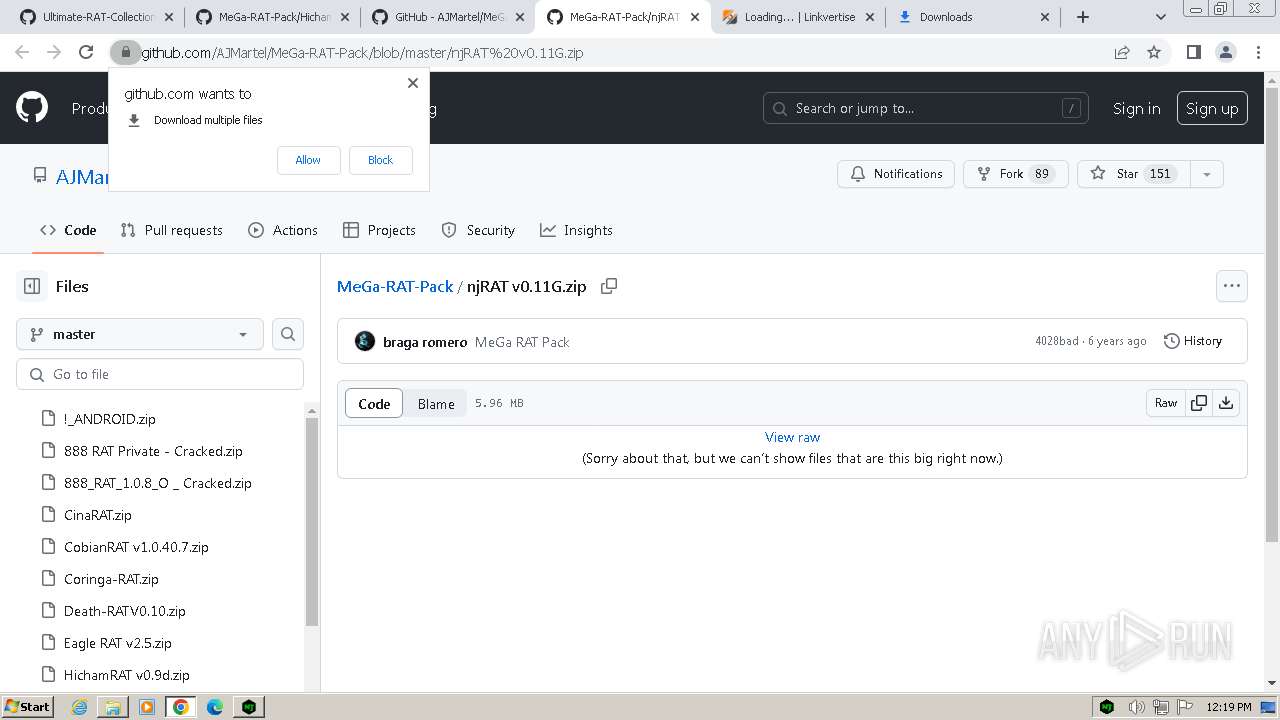
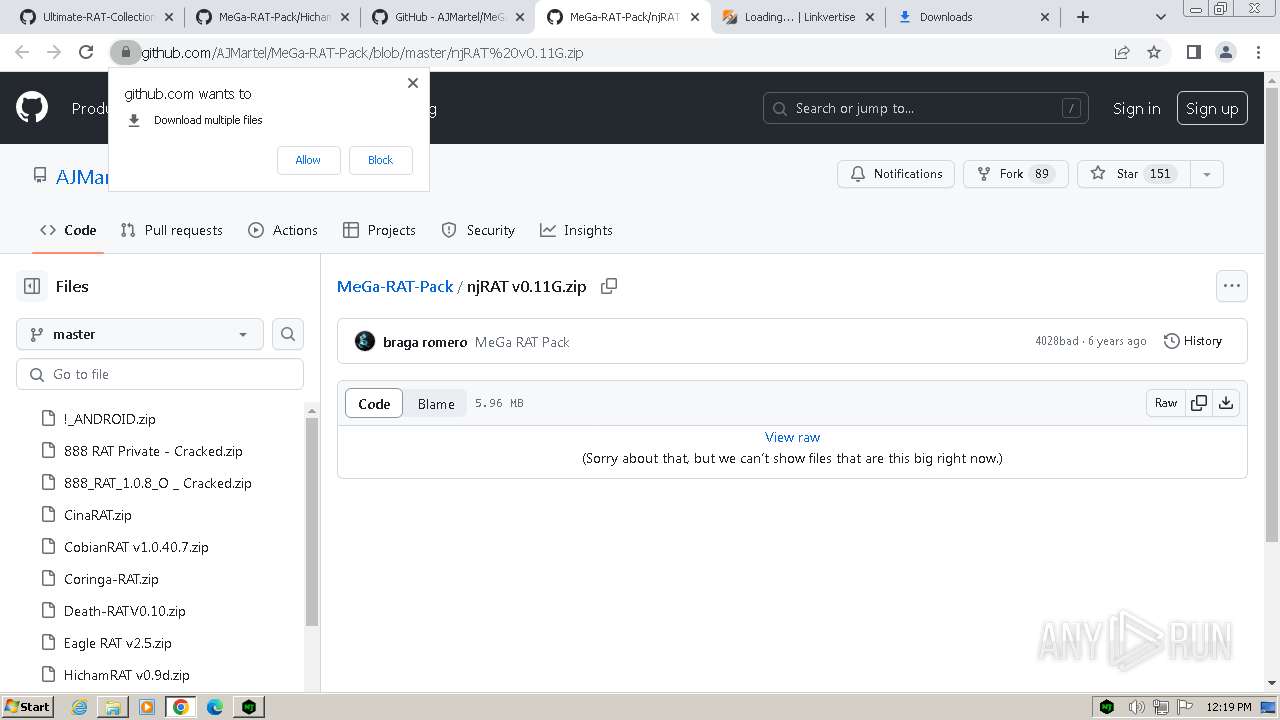
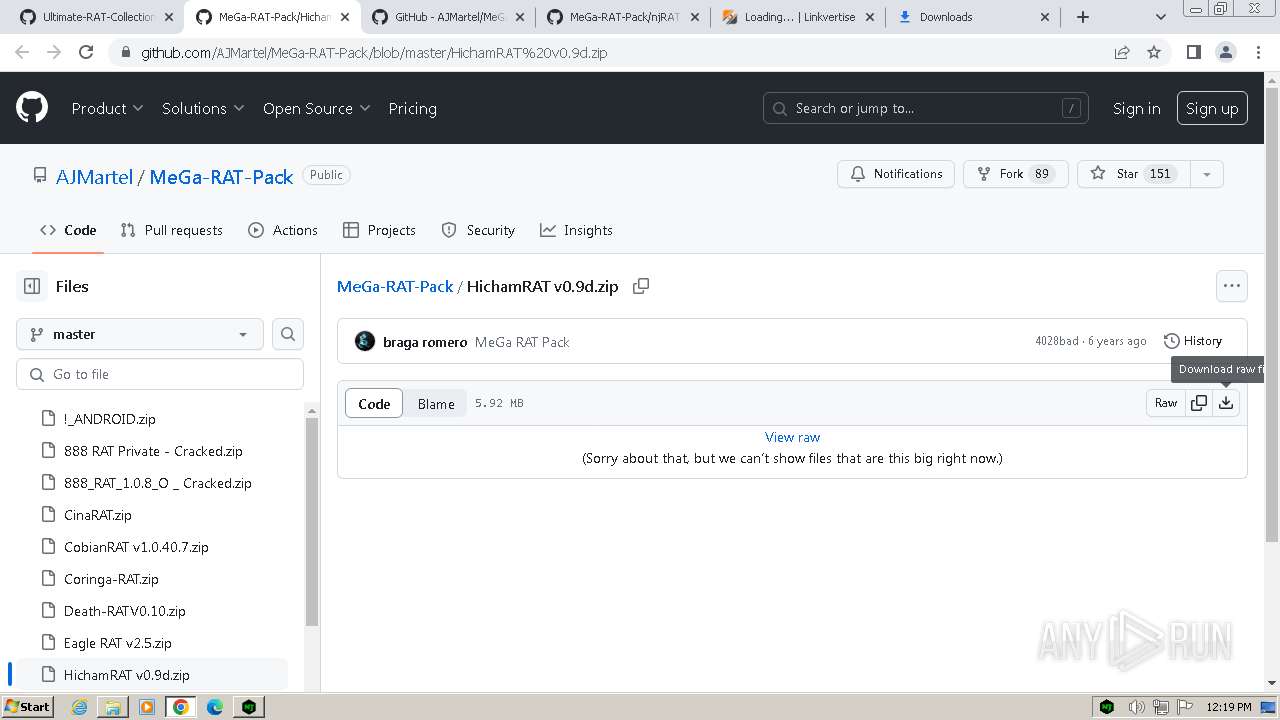
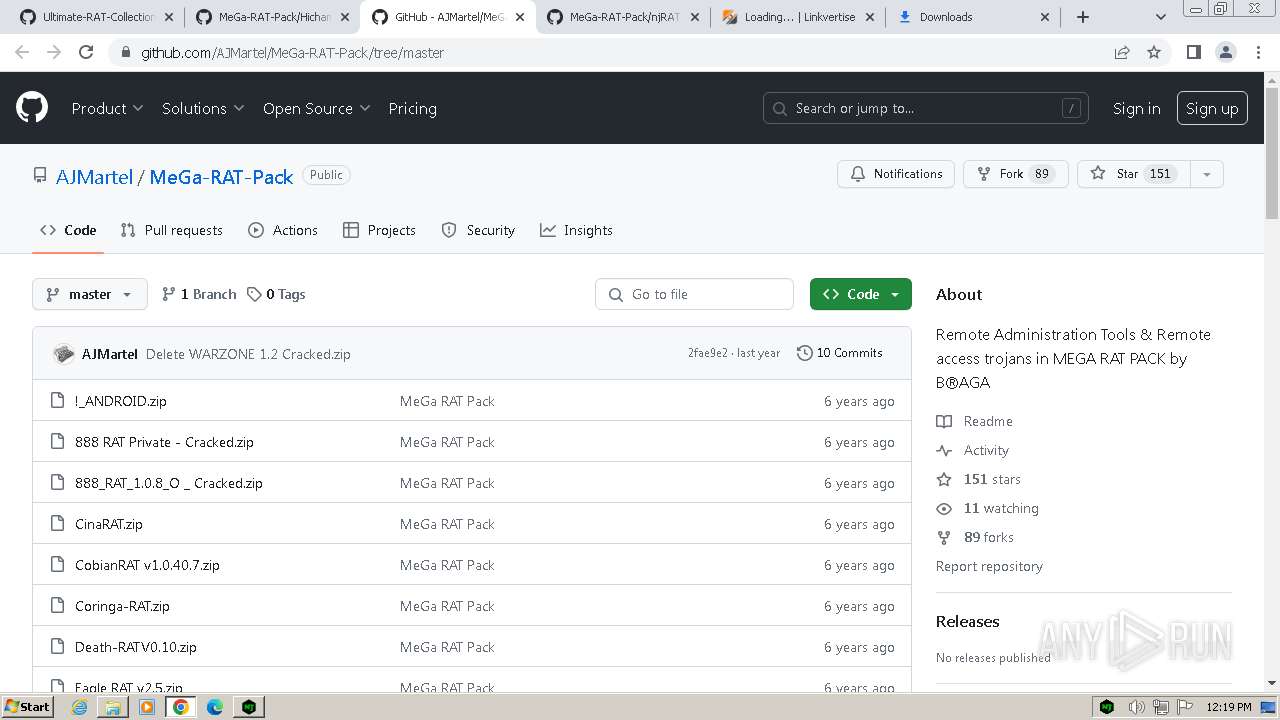
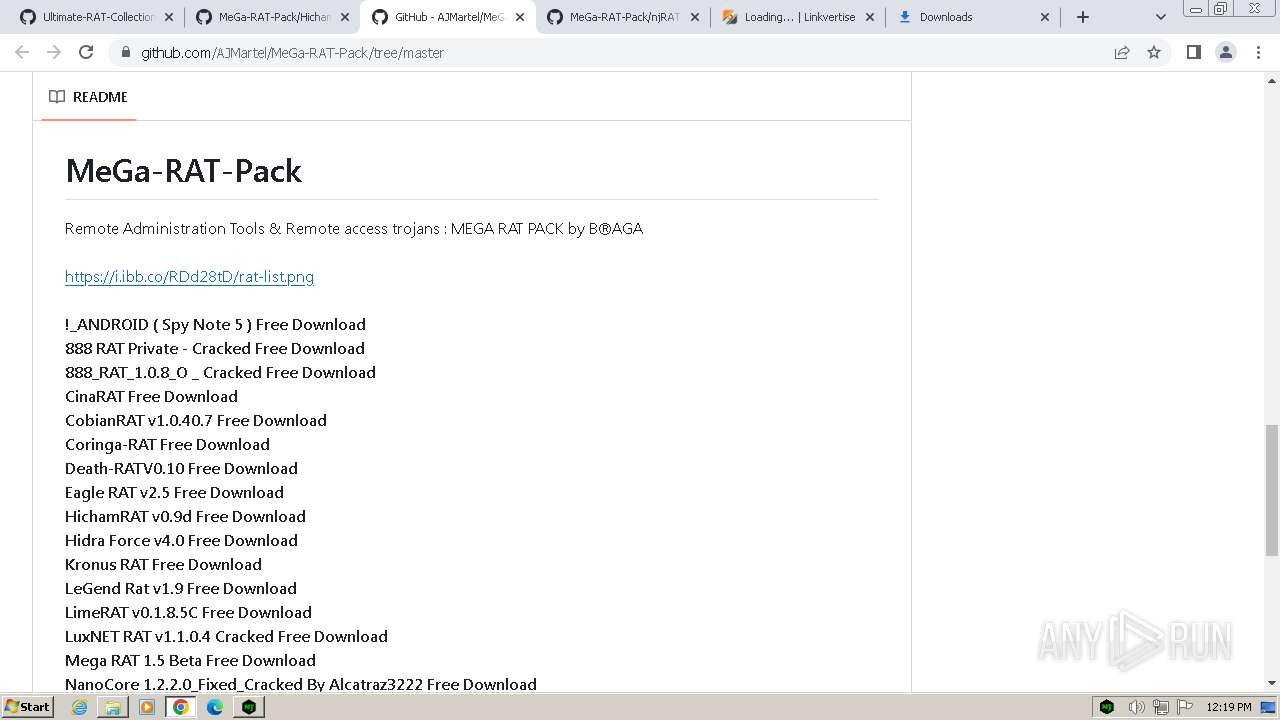
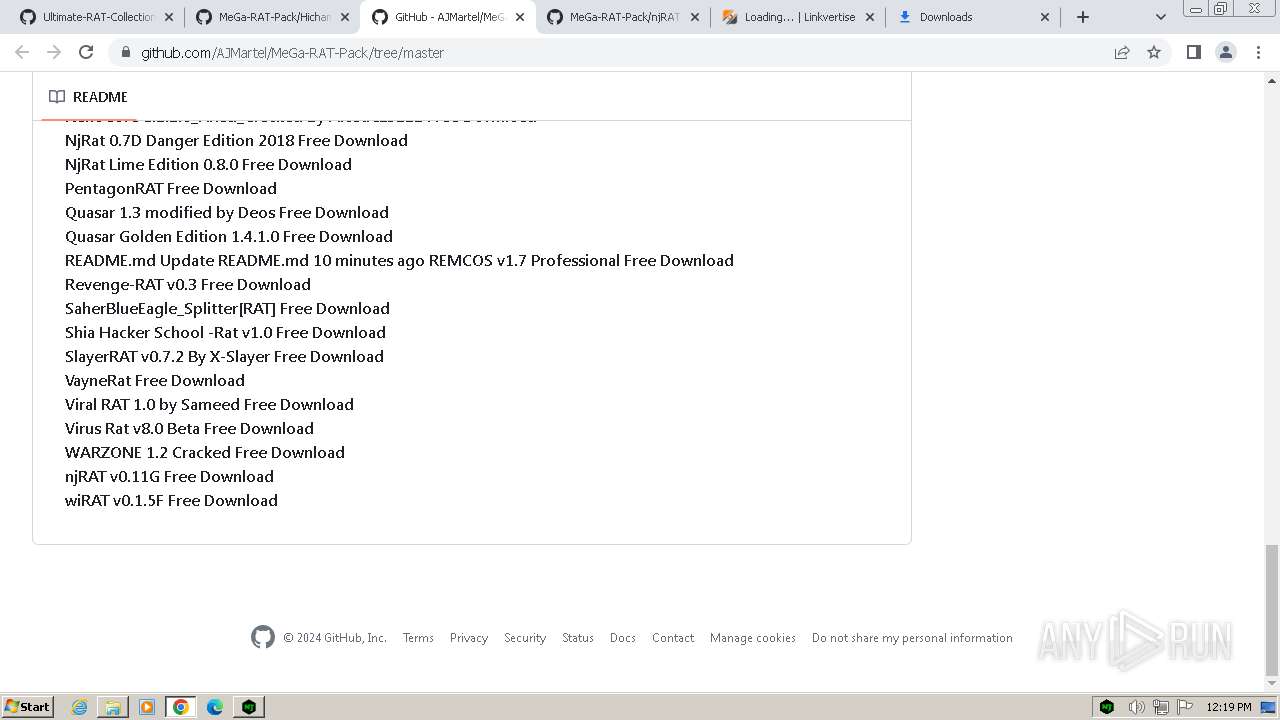
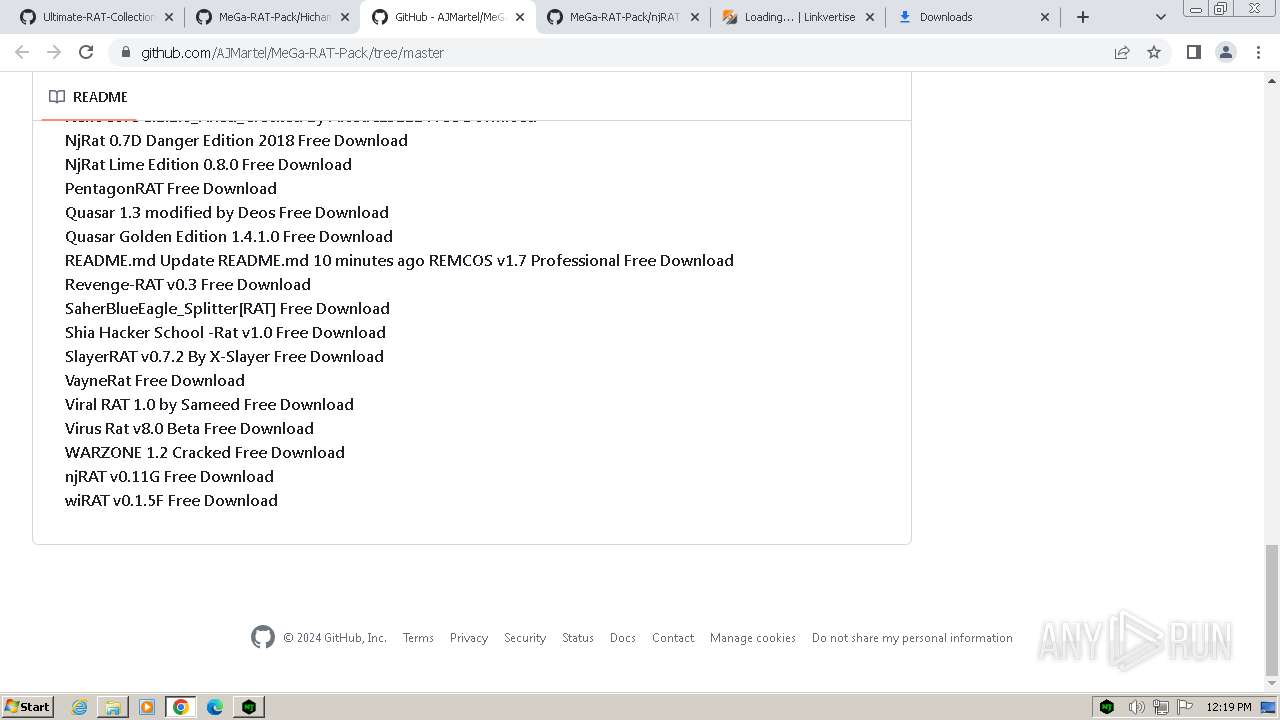
| URL: | https://github.com/yuankong666/Ultimate-RAT-Collection |
| Full analysis: | https://app.any.run/tasks/2b5d5166-53a4-46cb-b03d-668d28d6cb16 |
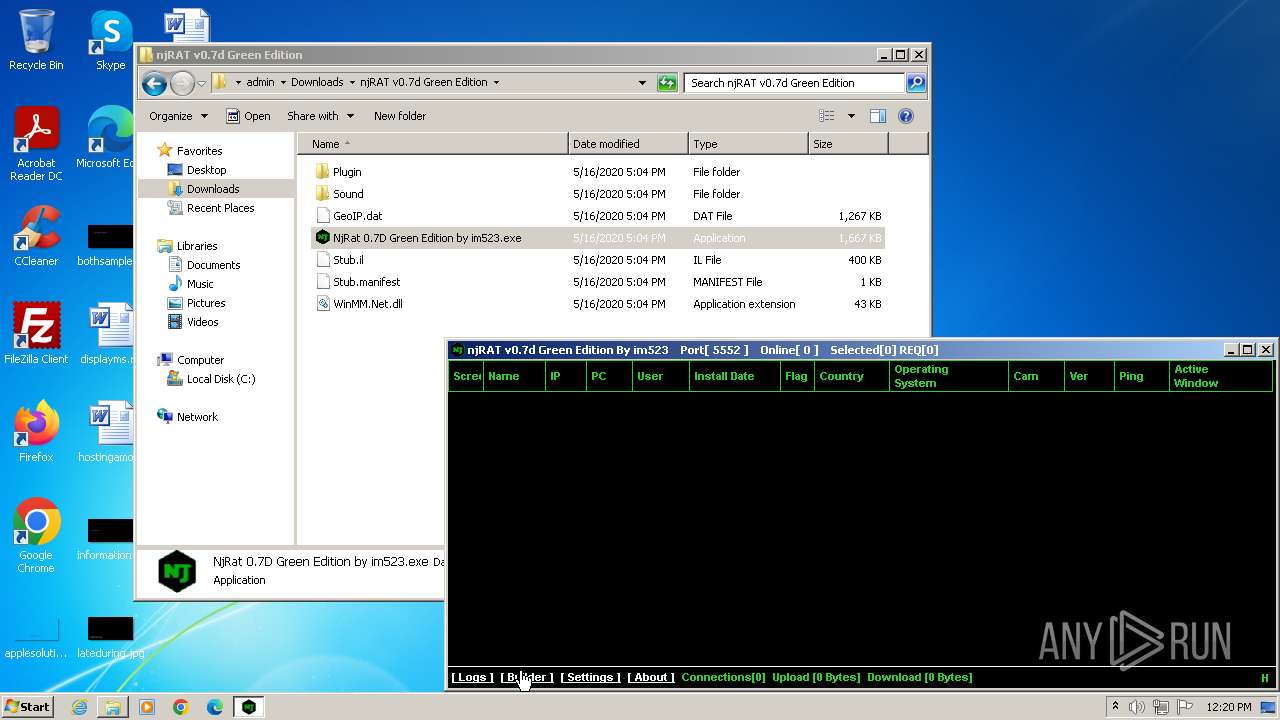
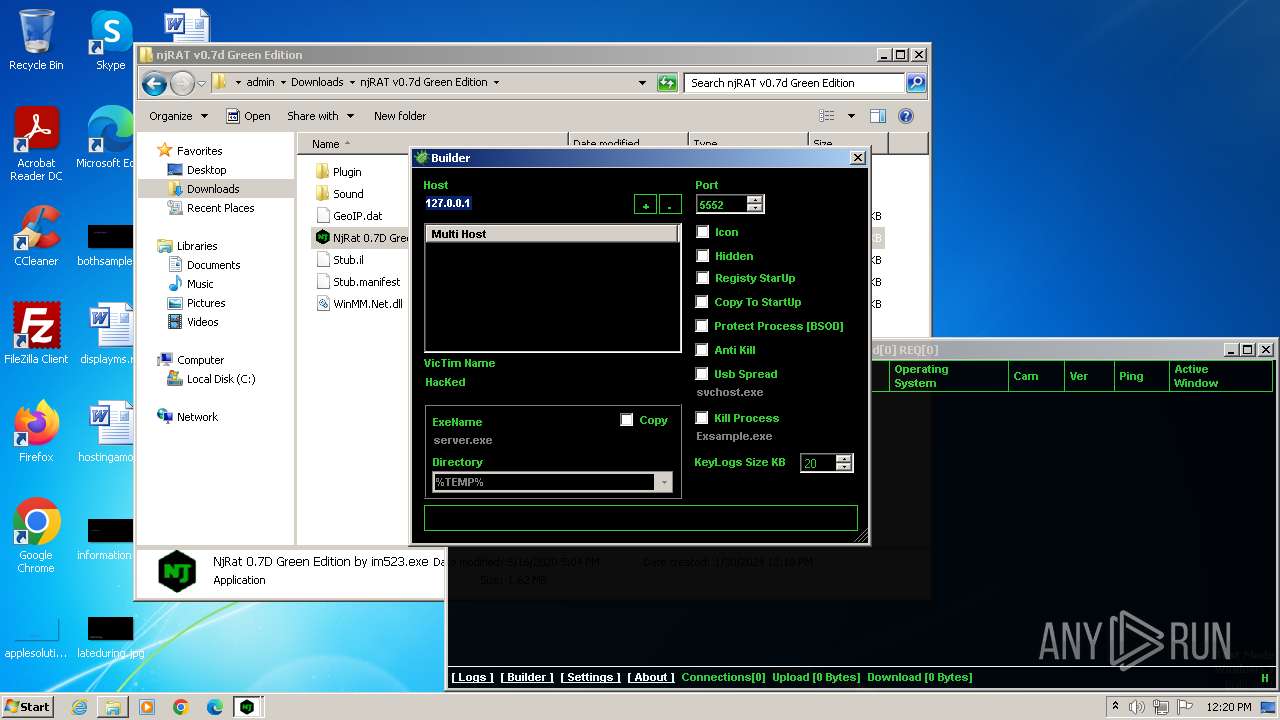
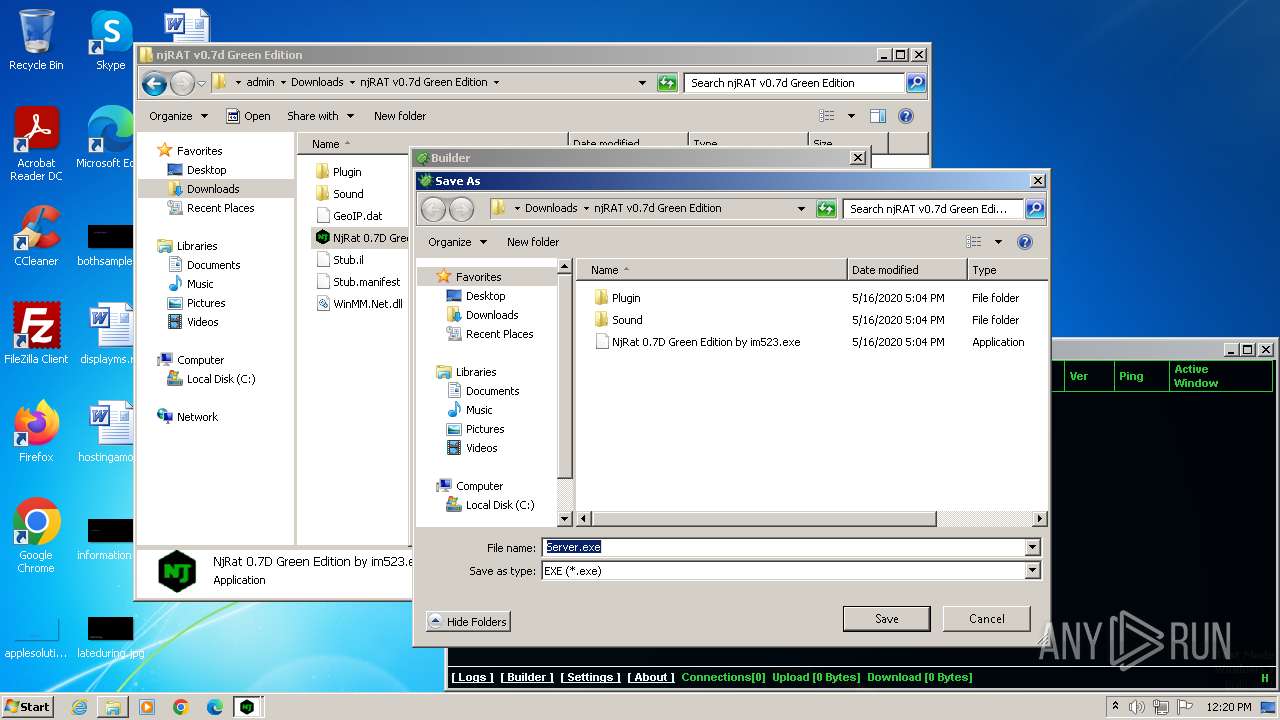
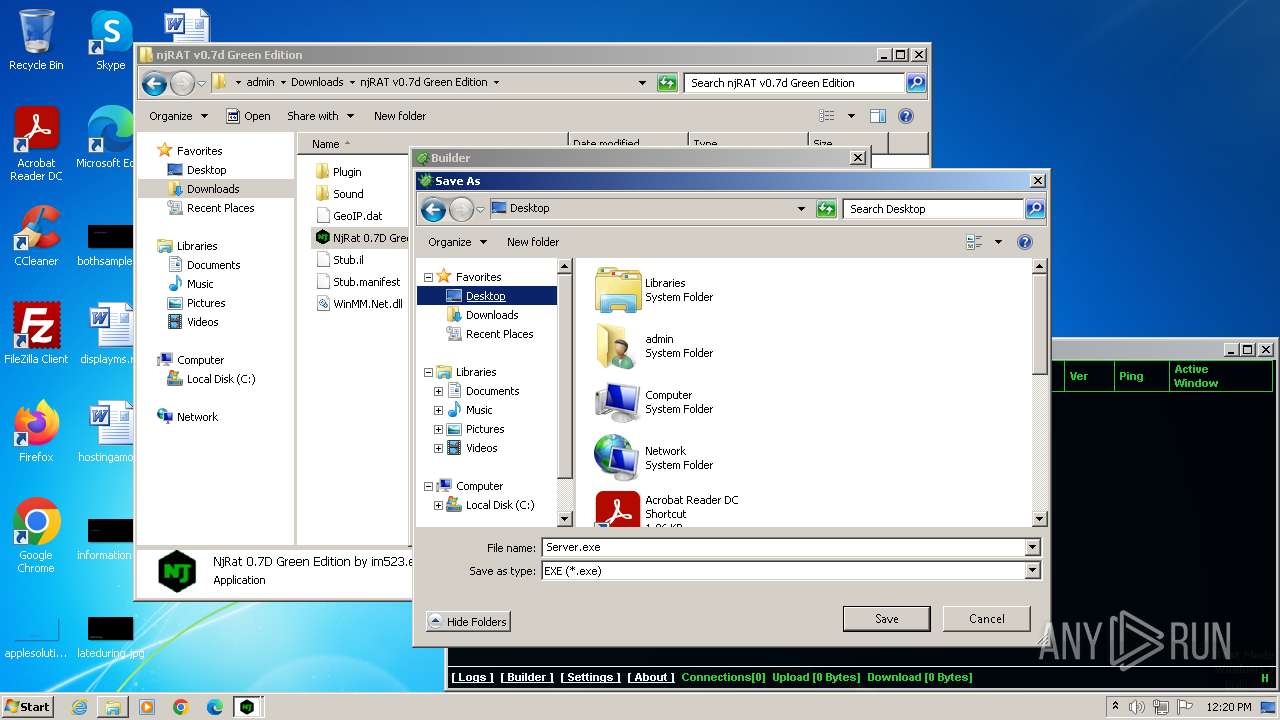
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2024, 12:15:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
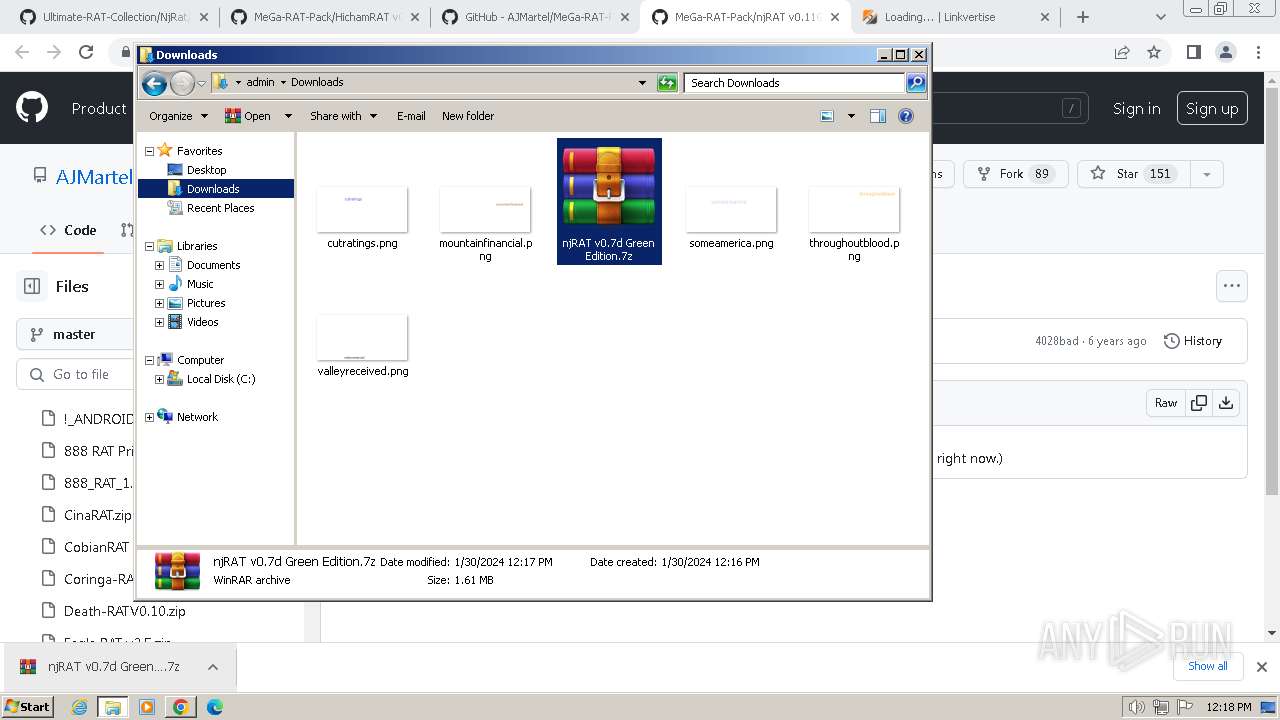
| MD5: | 864D061964C30F3F160AE013BB8CF47B |
| SHA1: | EB8DCC2C10510B0F218F129BD54B5E78C62034DB |
| SHA256: | 7ACE972C8843A9AAD88FEDAB4273C8357E4E64B016F8A80F232EDA12E0753F28 |
| SSDEEP: | 3:N8tEdstRGGpI4FkO9JOGR/:2u6tYGm1gOGN |
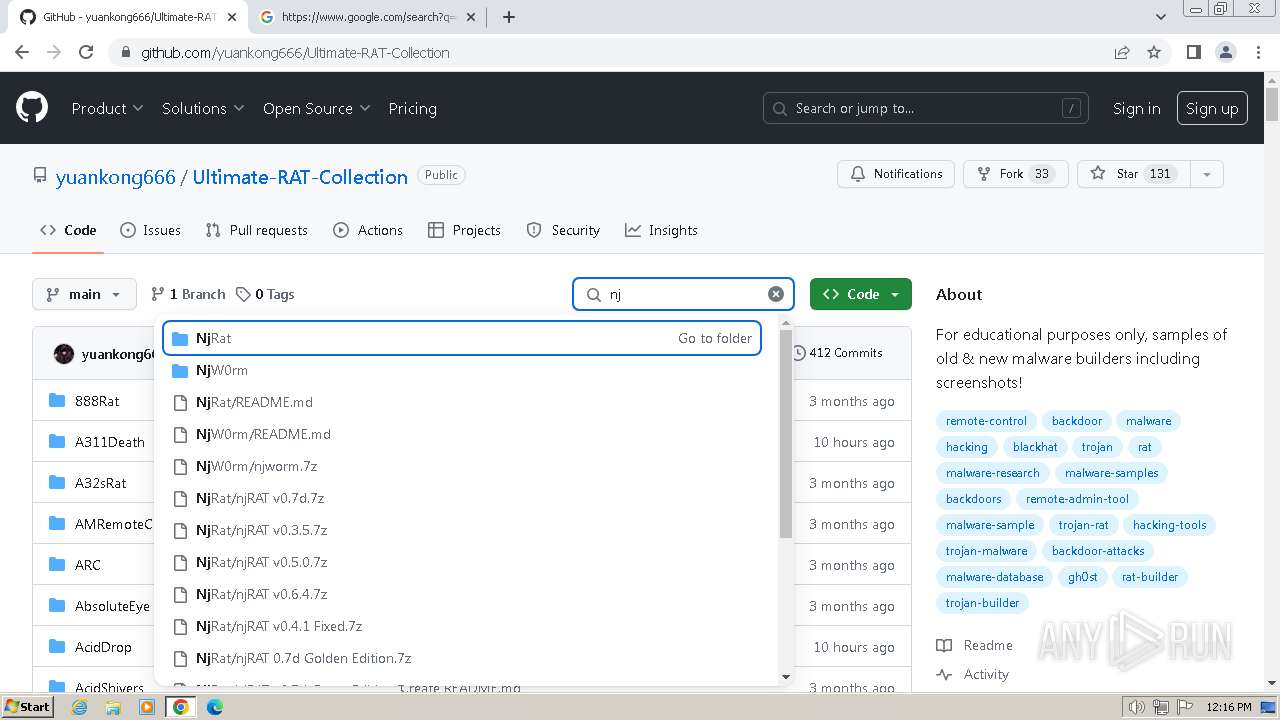
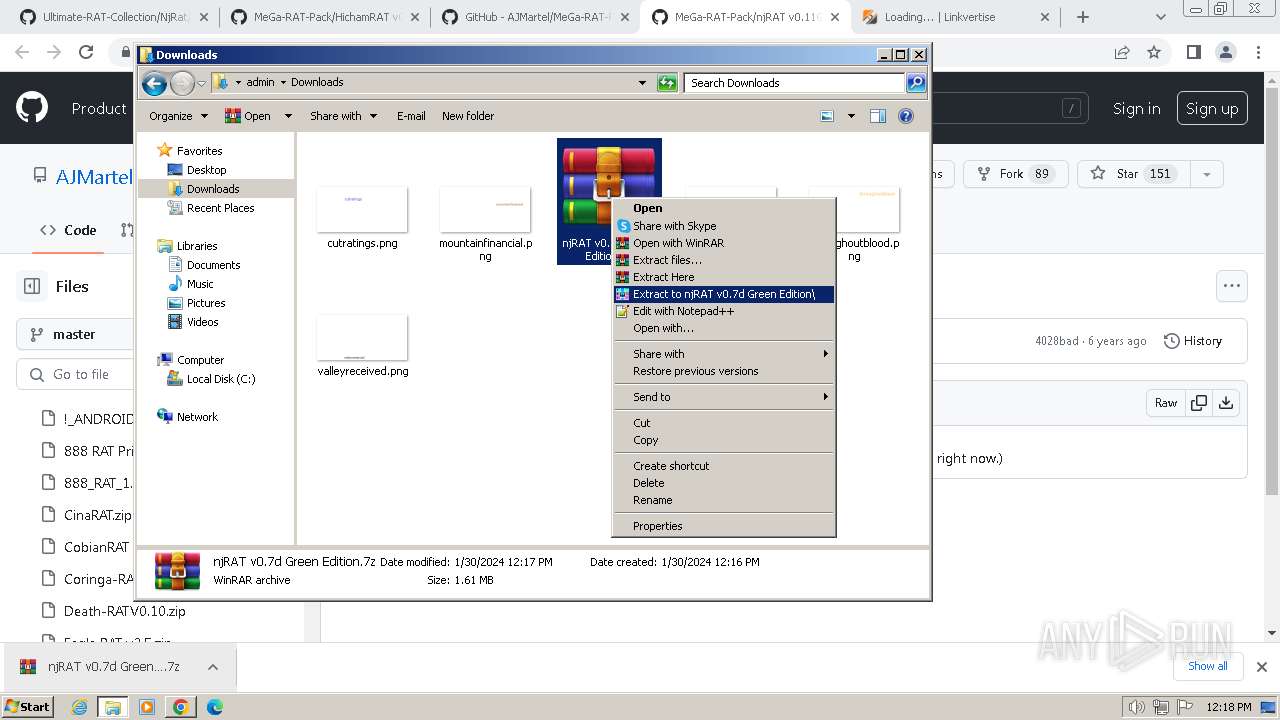
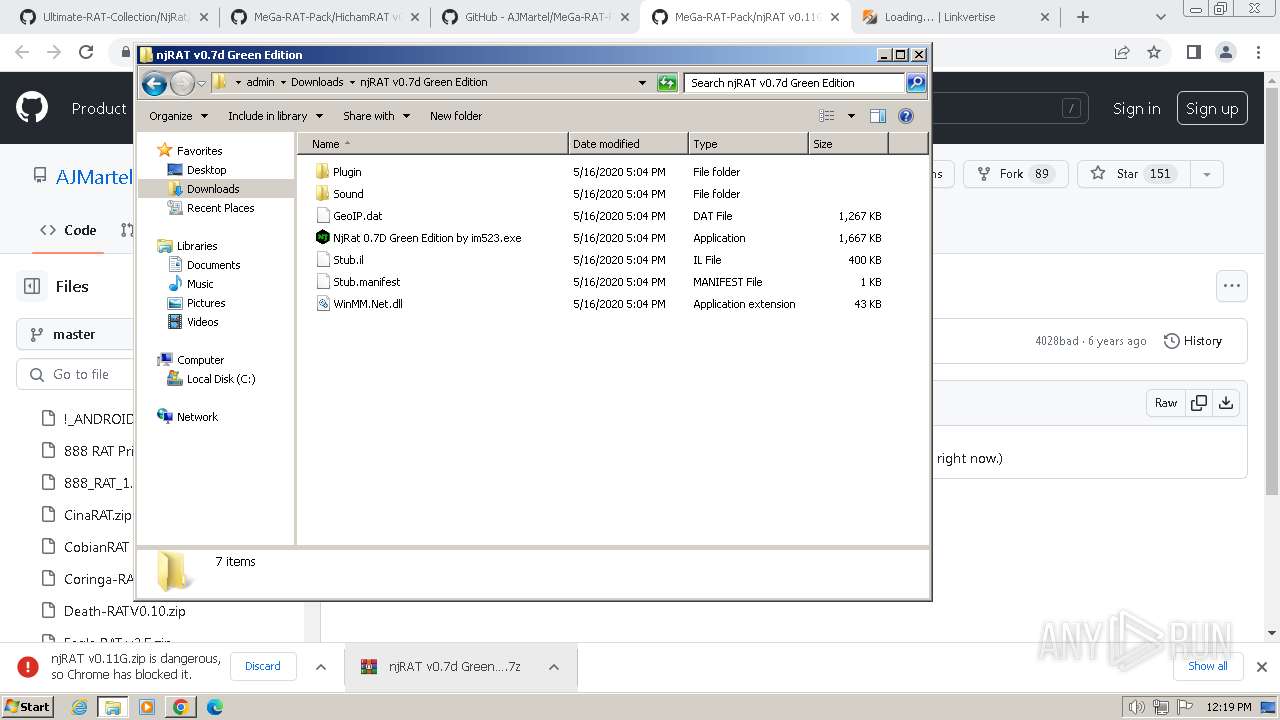
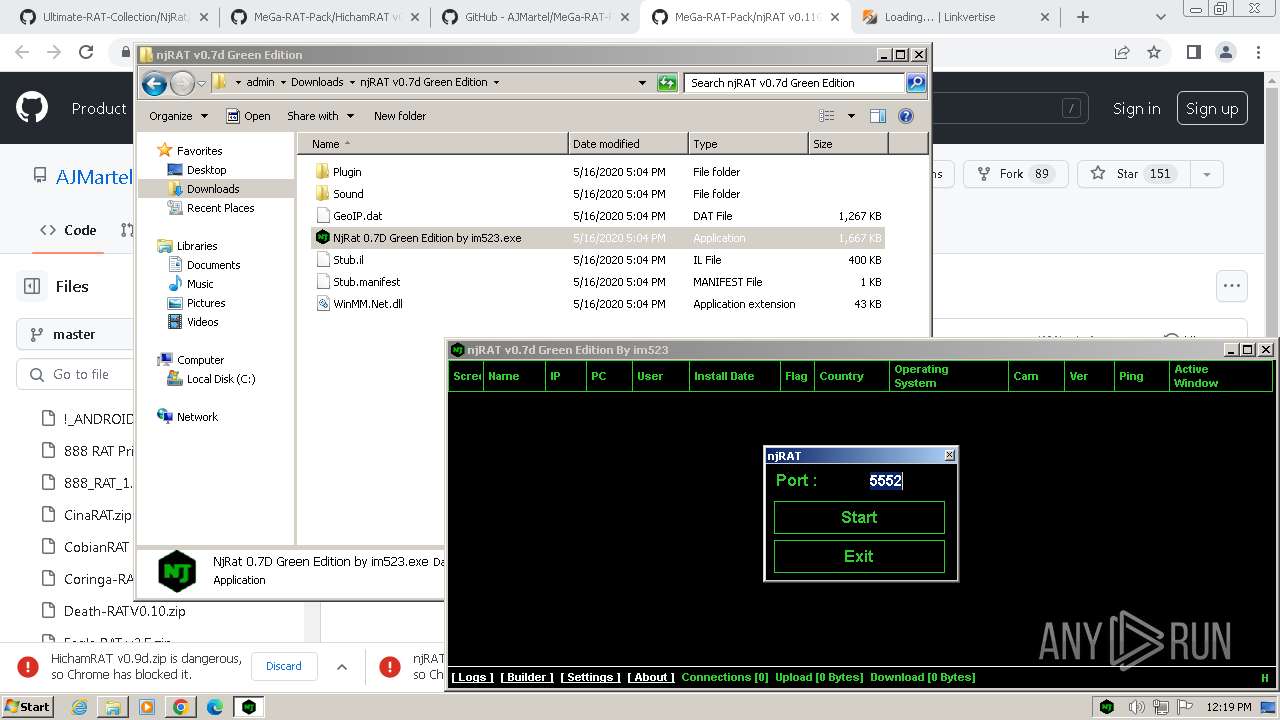
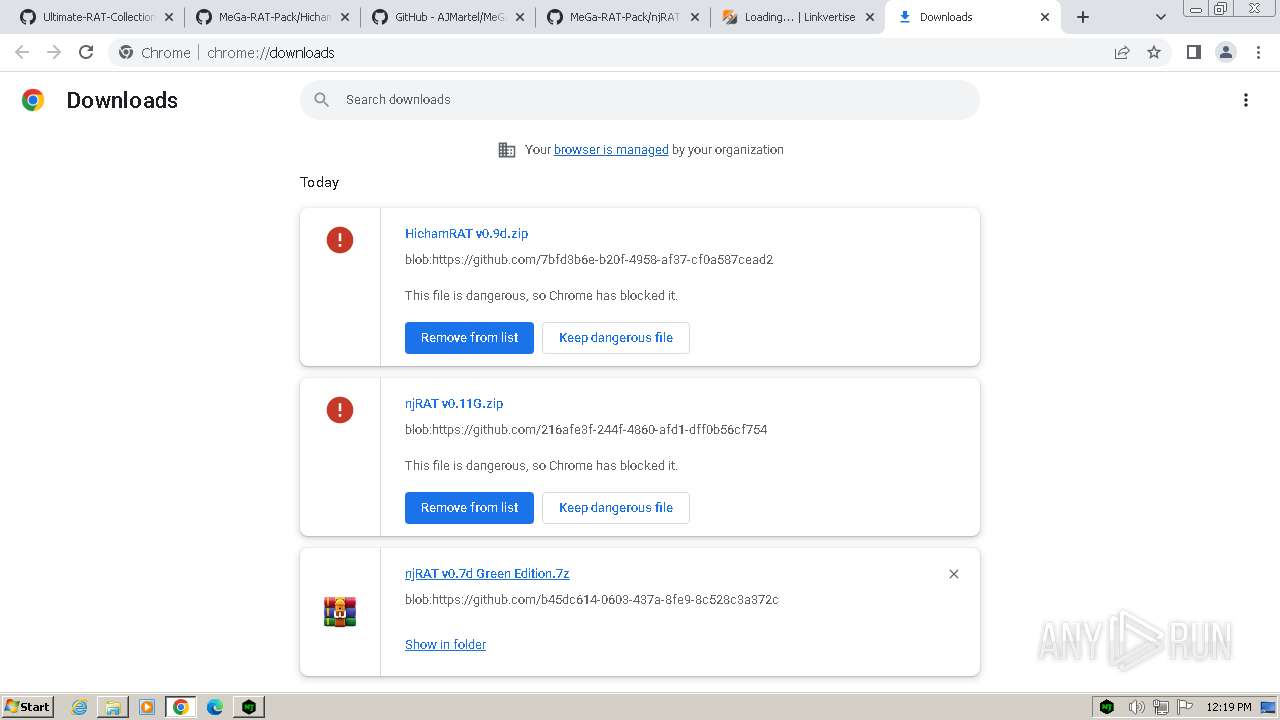
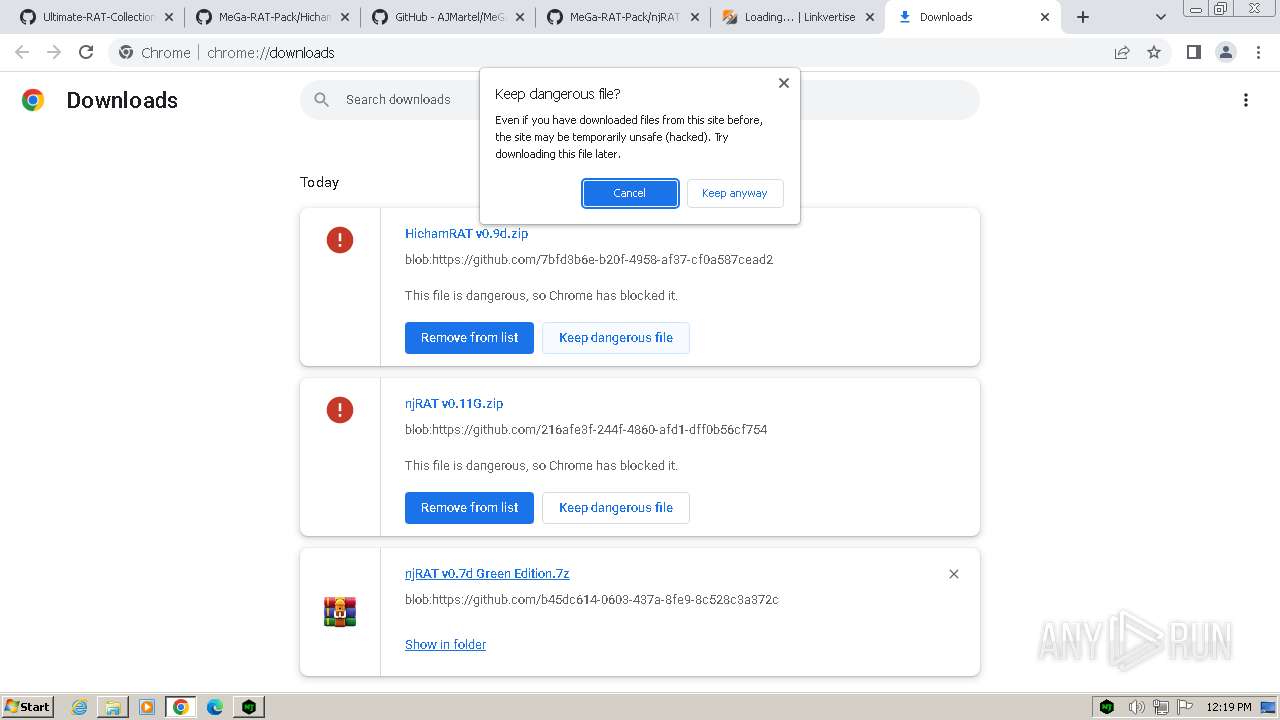
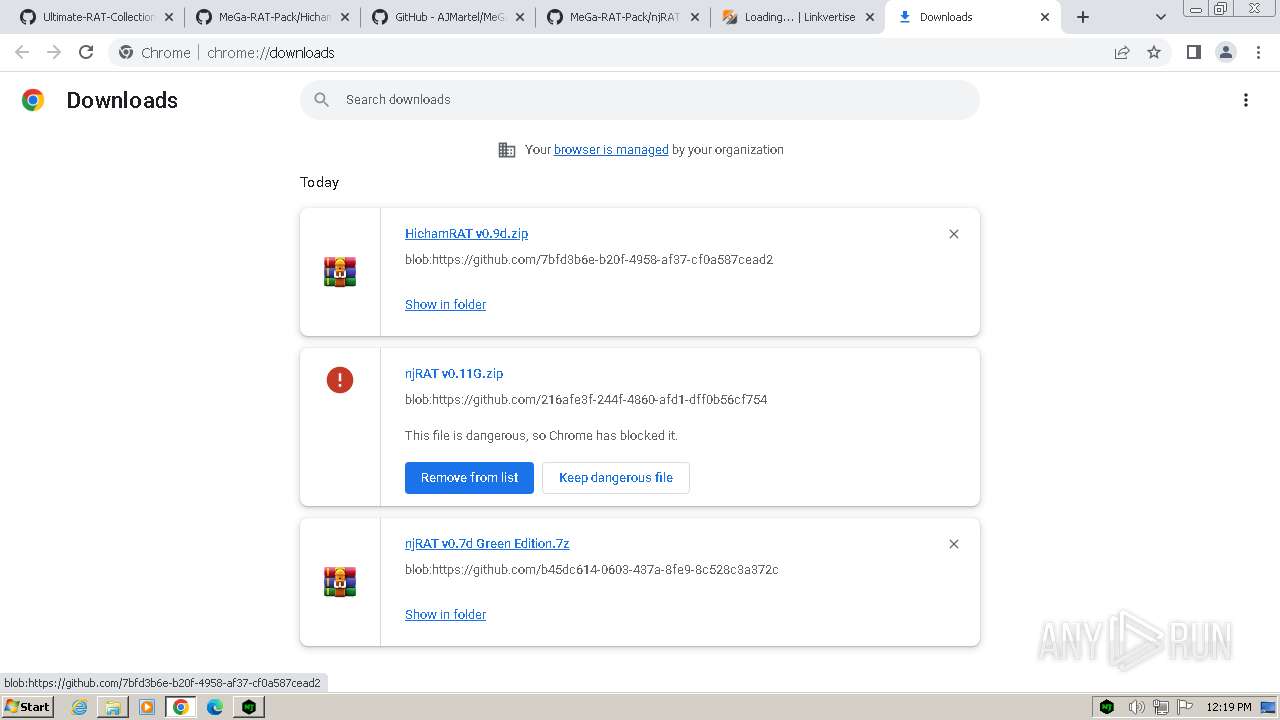
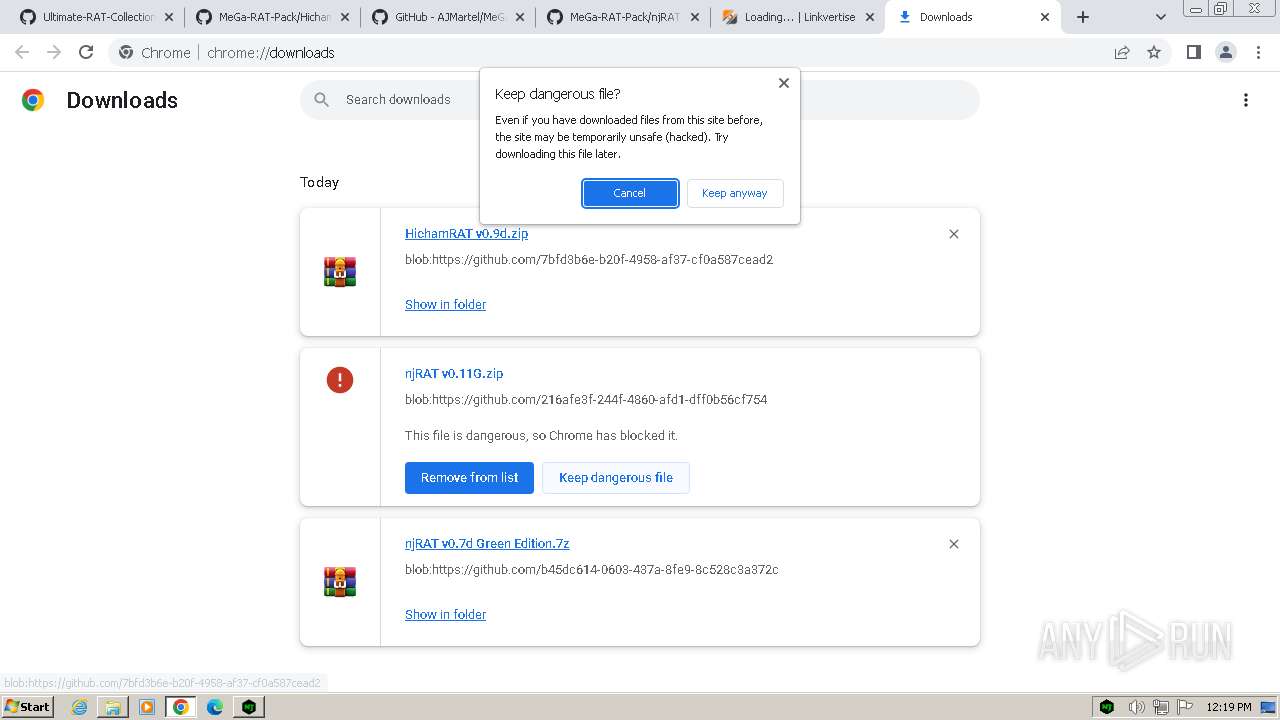
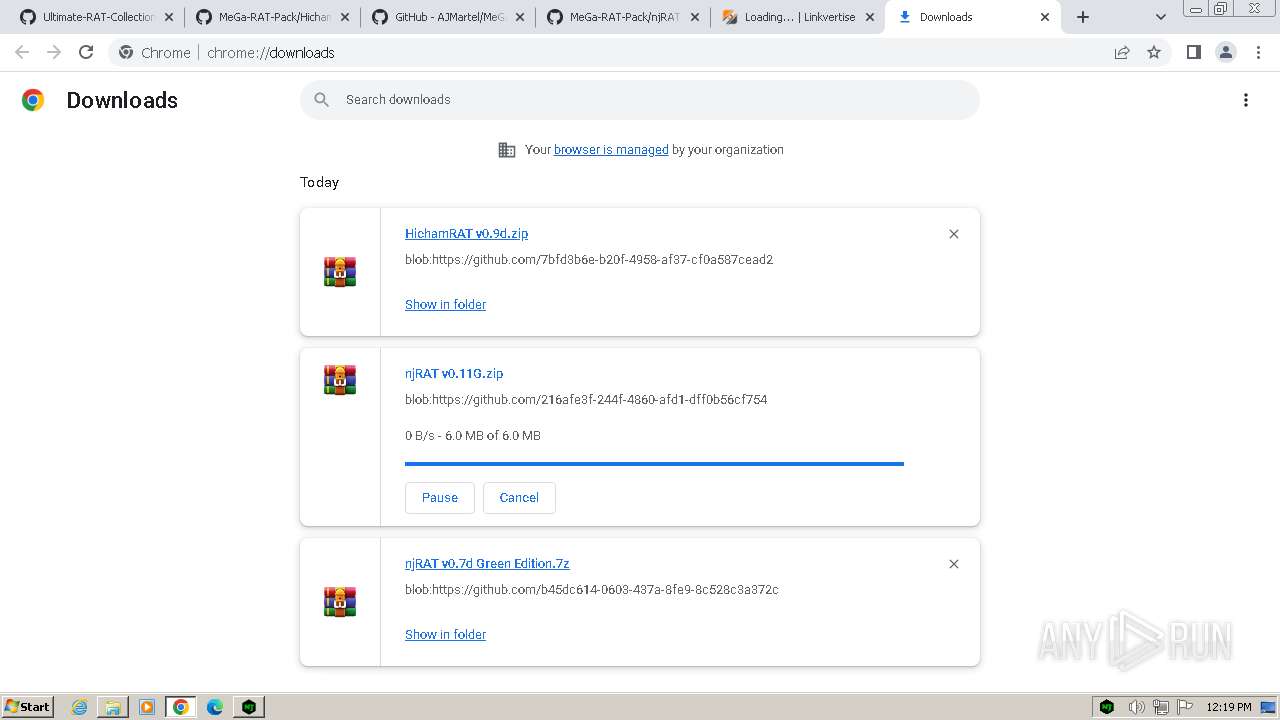
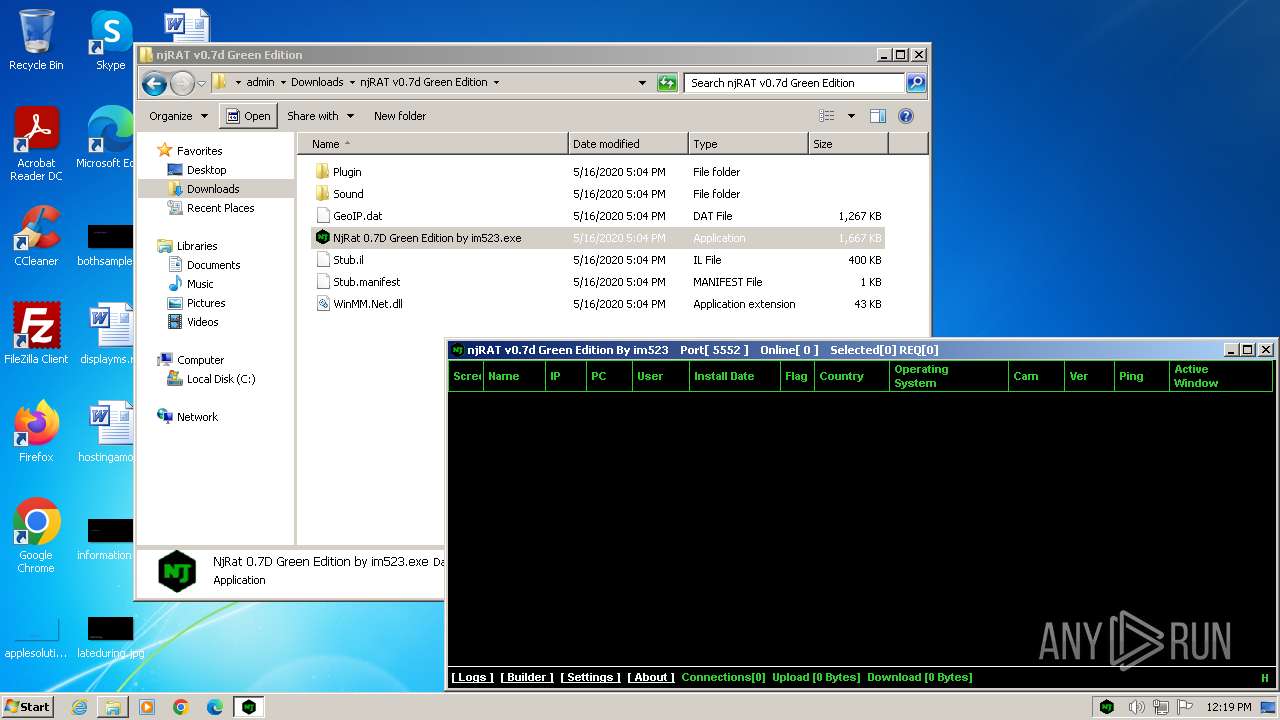
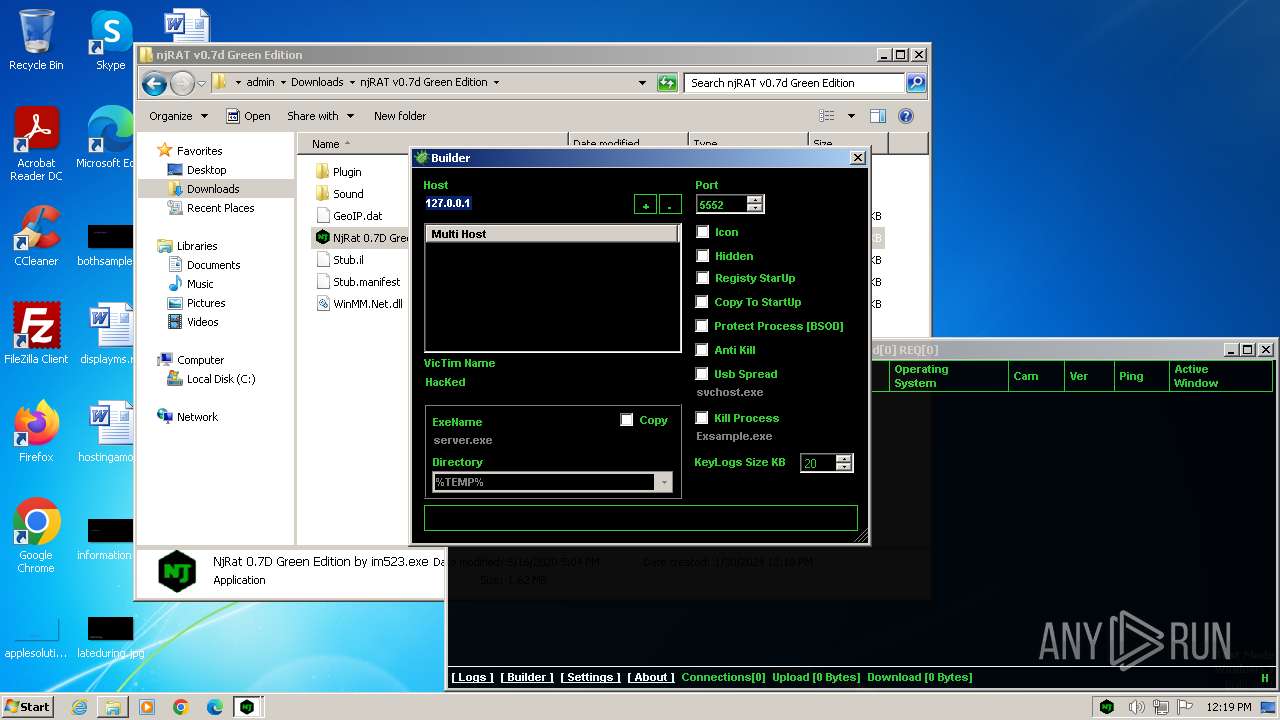
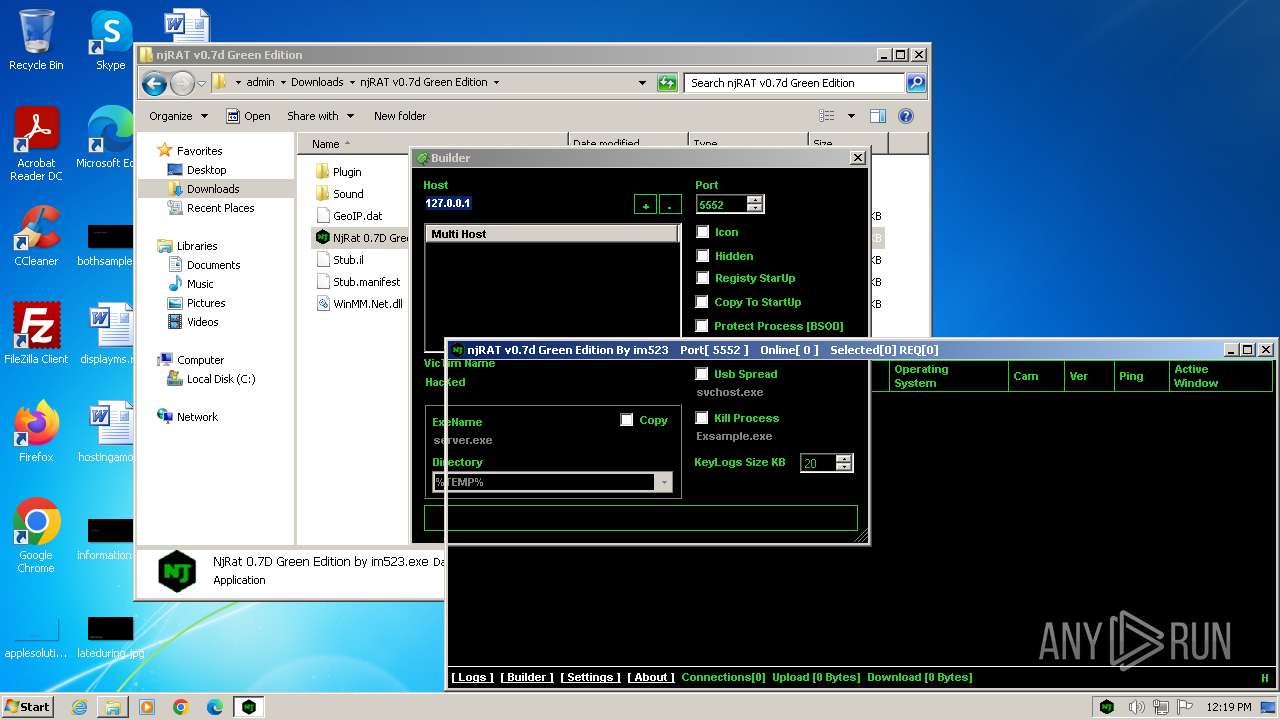
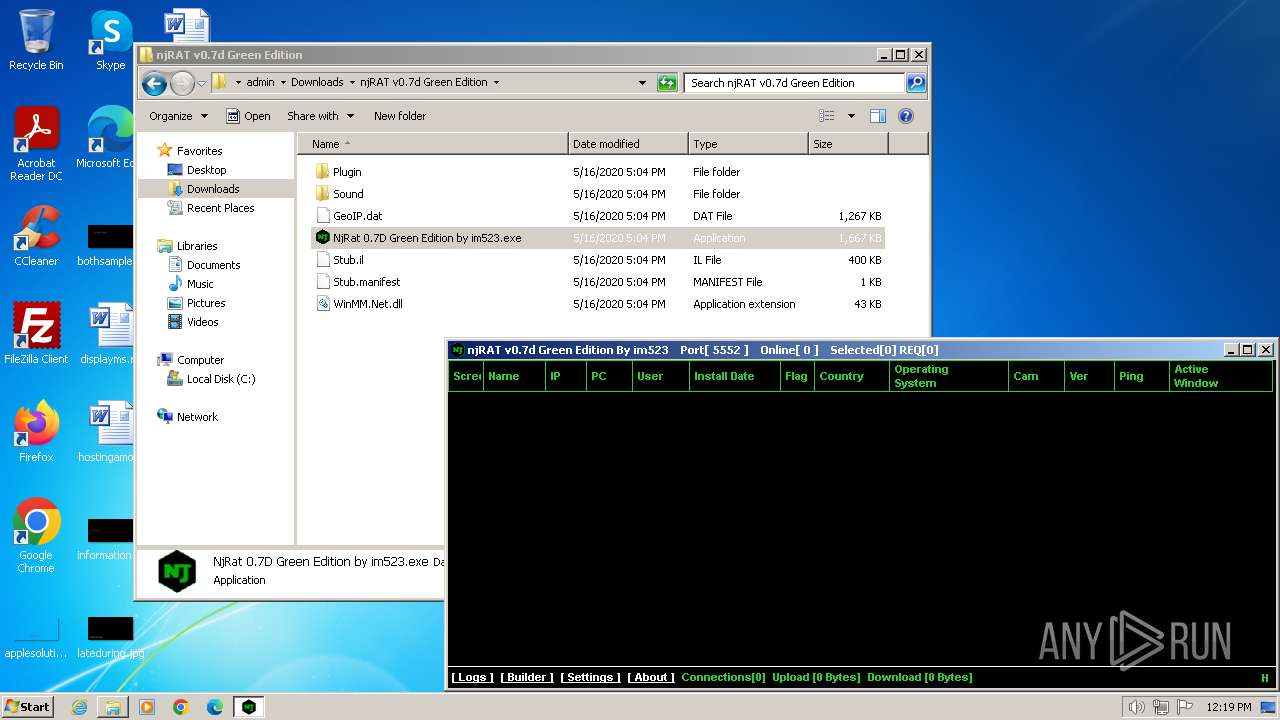
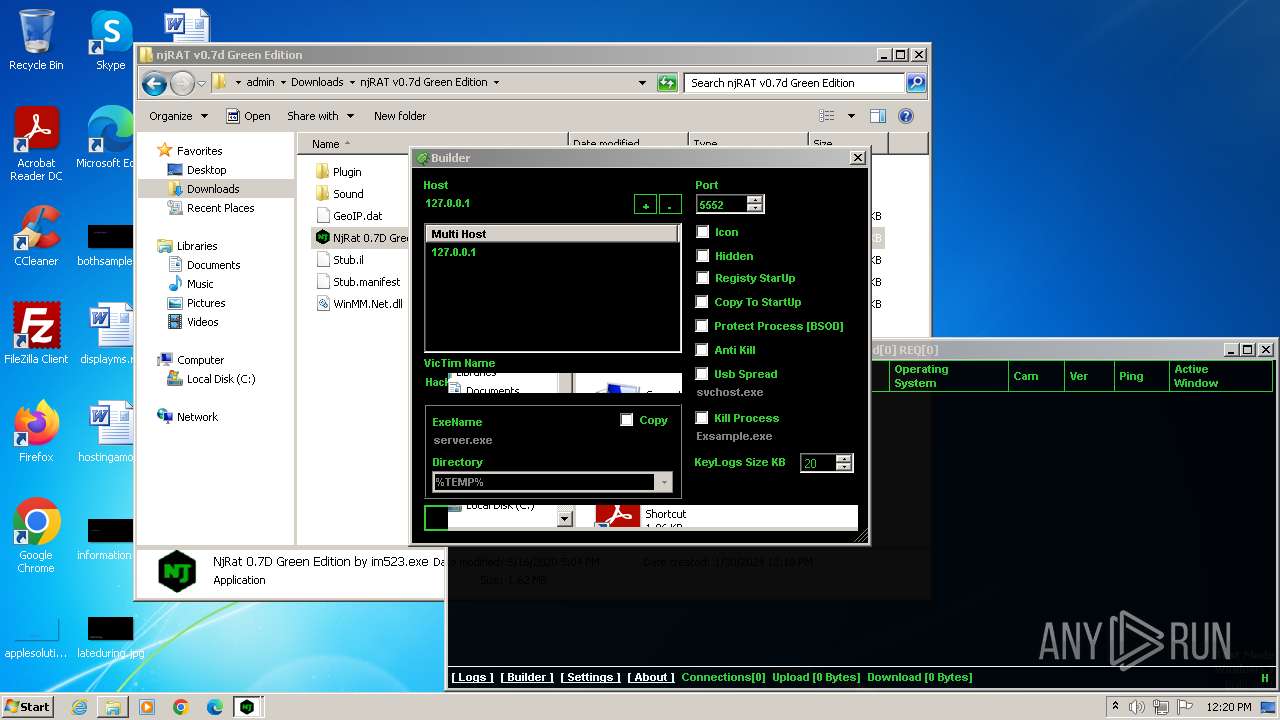
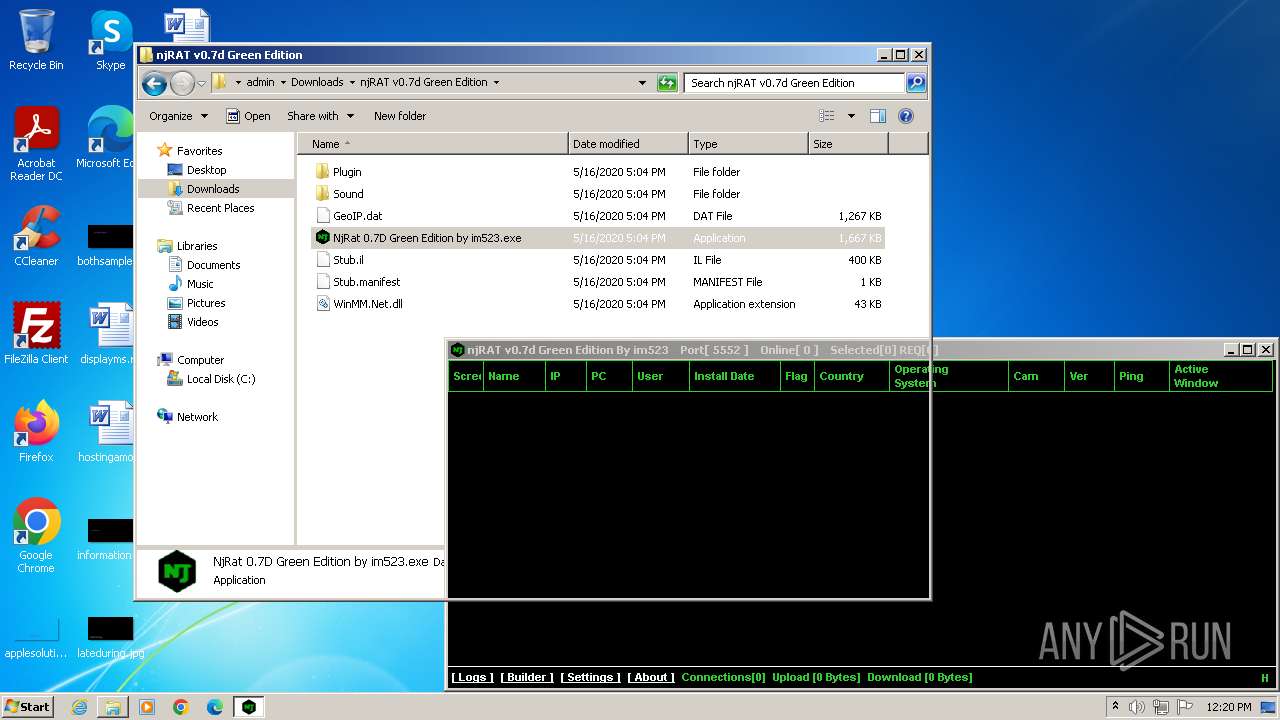
MALICIOUS
SecurityXploded is detected
- WinRAR.exe (PID: 3656)
- WinRAR.exe (PID: 2592)
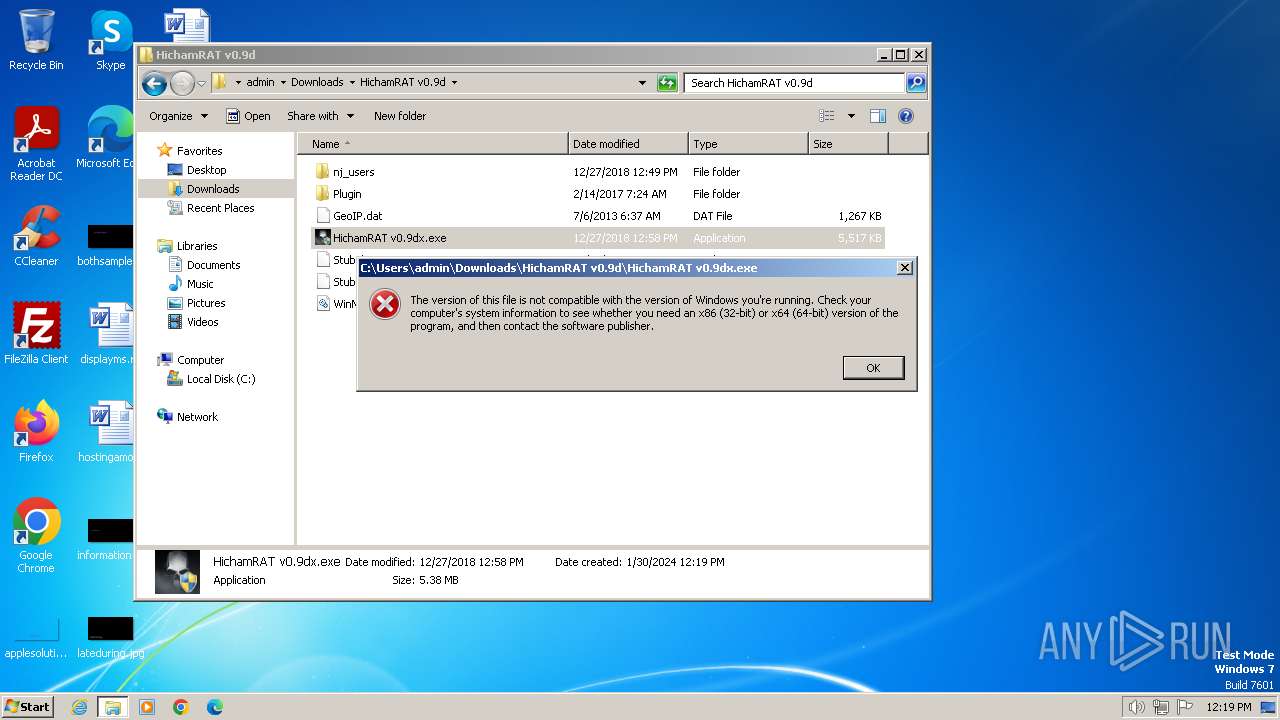
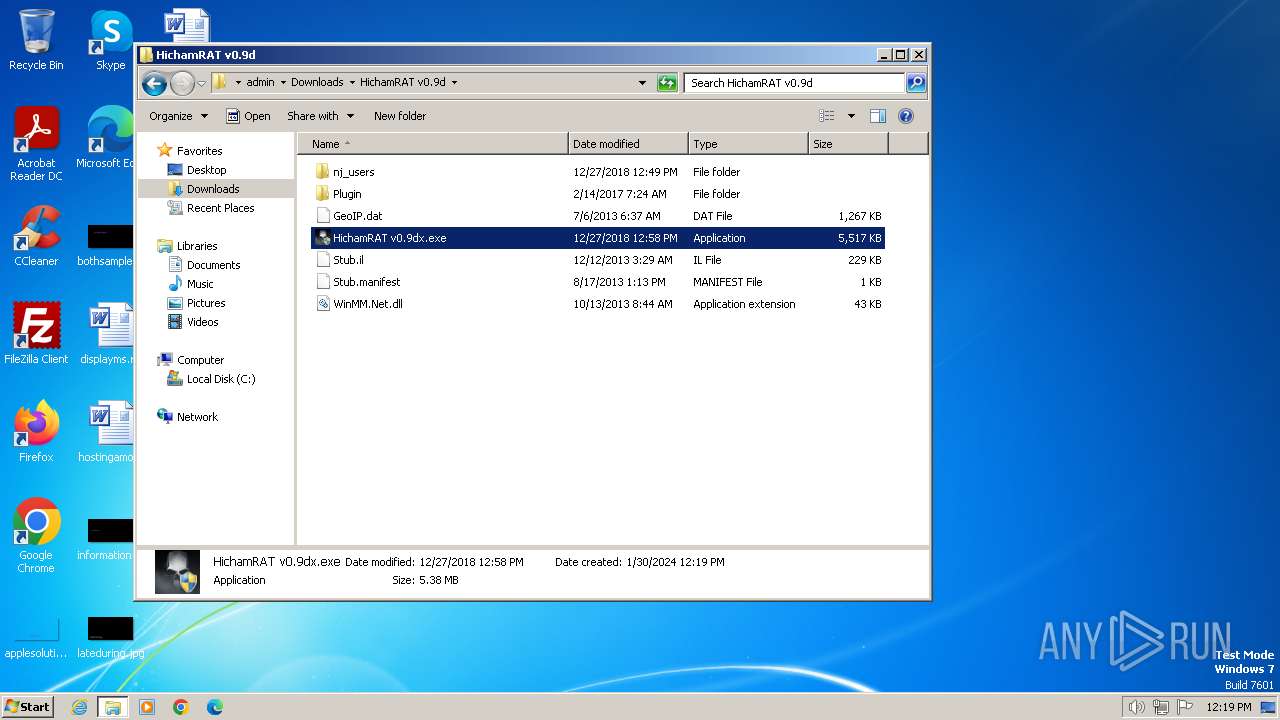
Drops the executable file immediately after the start
- ilasm.exe (PID: 3024)
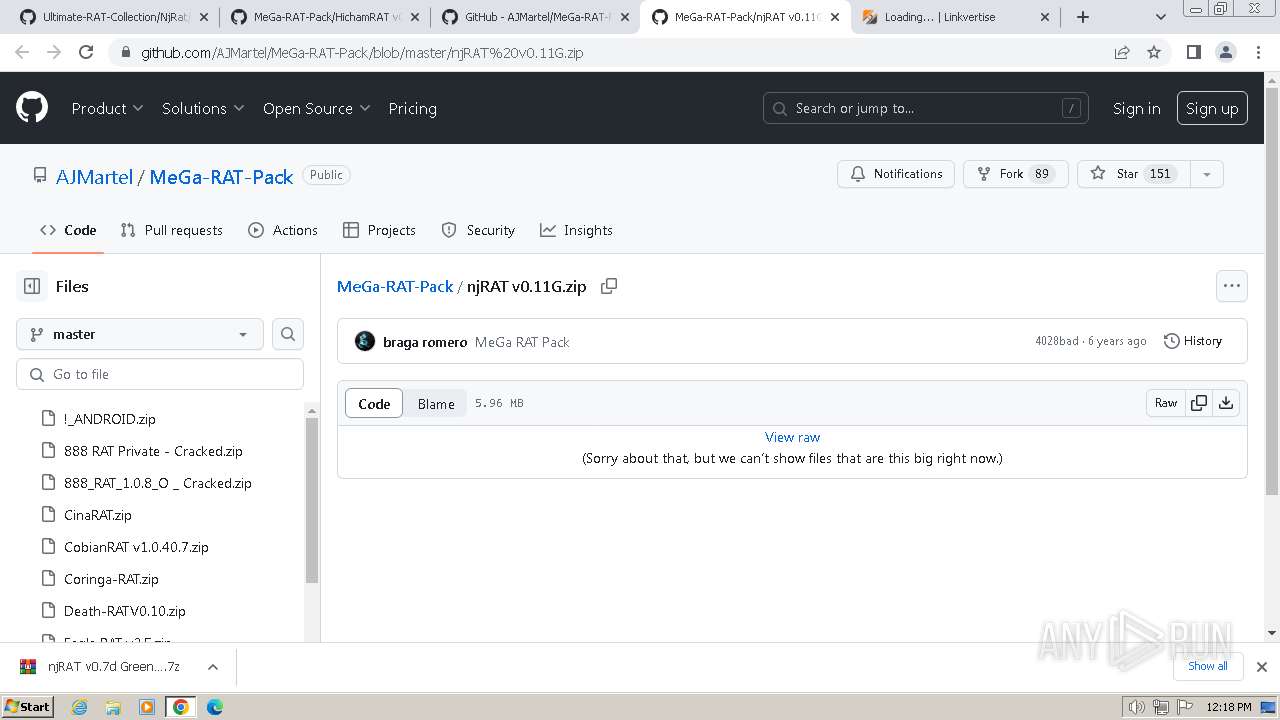
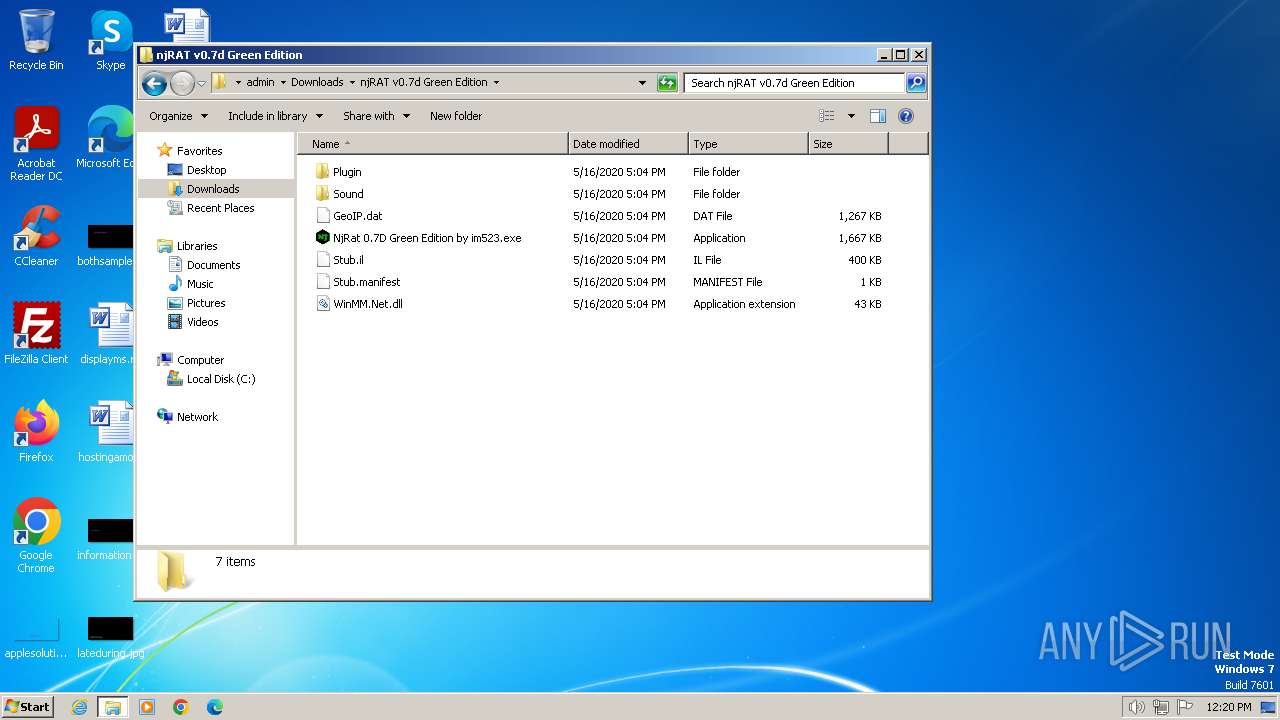
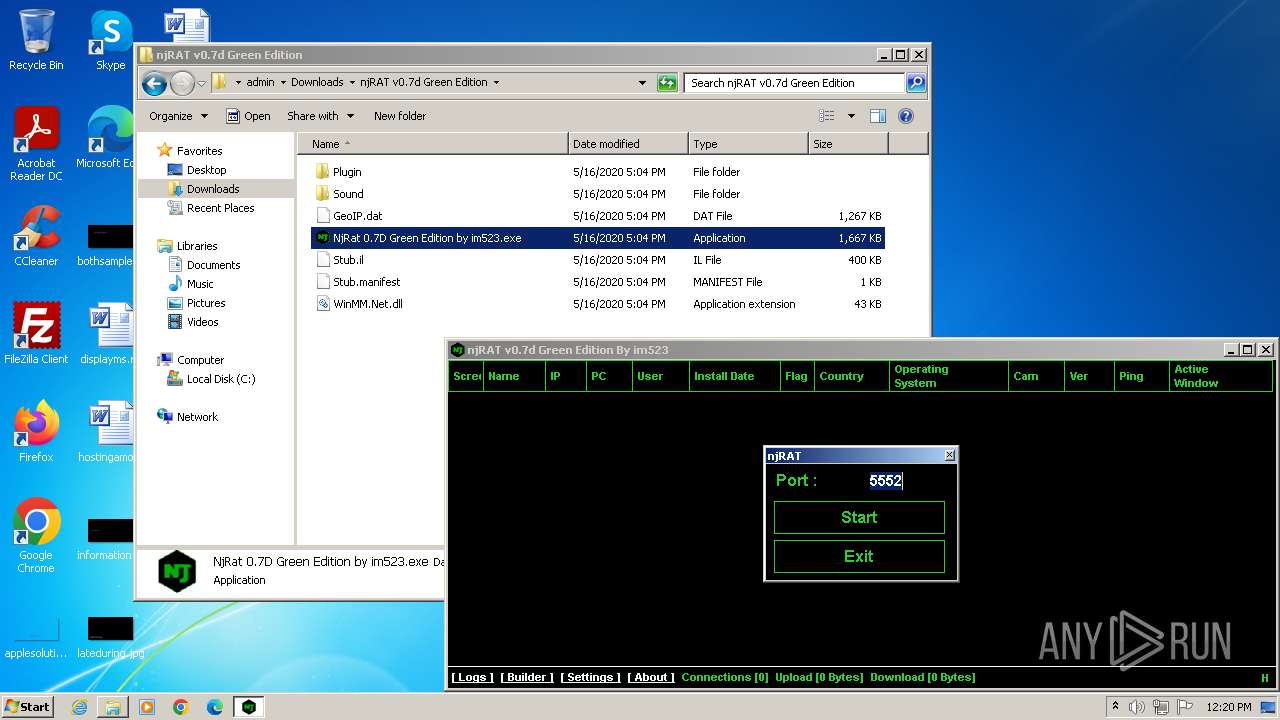
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
SUSPICIOUS
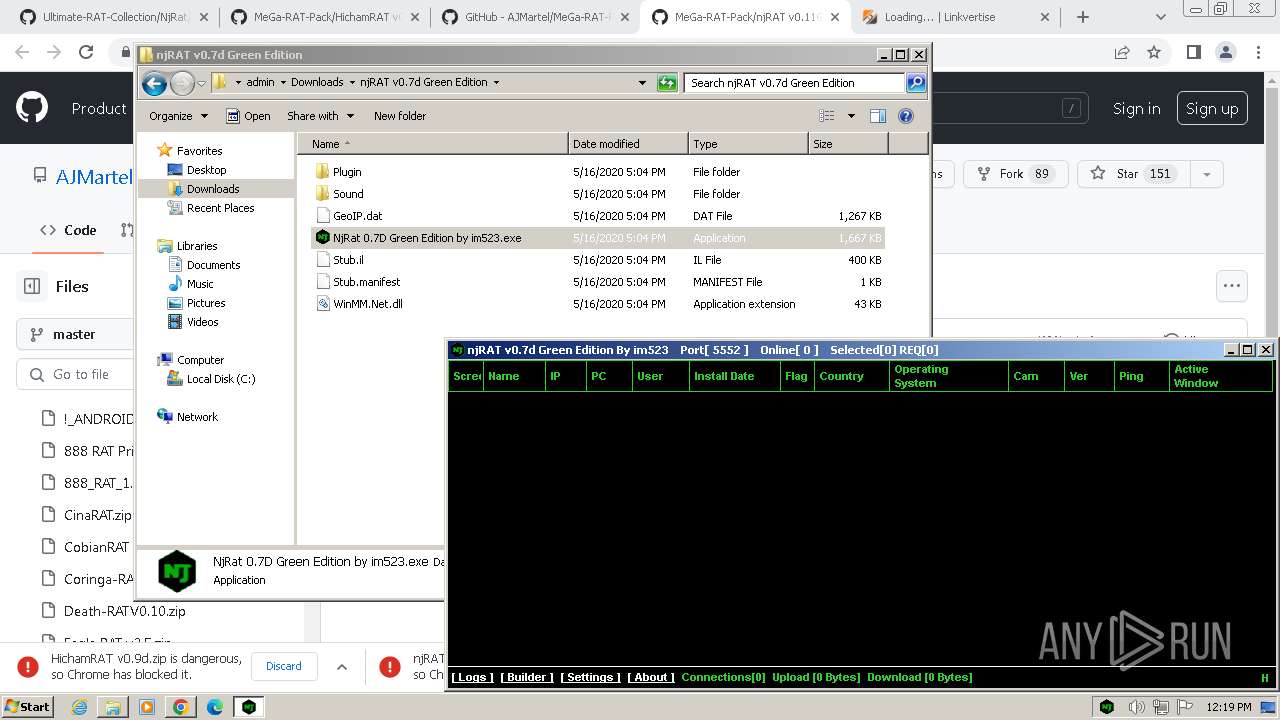
Reads the Internet Settings
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
Executable content was dropped or overwritten
- ilasm.exe (PID: 3024)
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
INFO
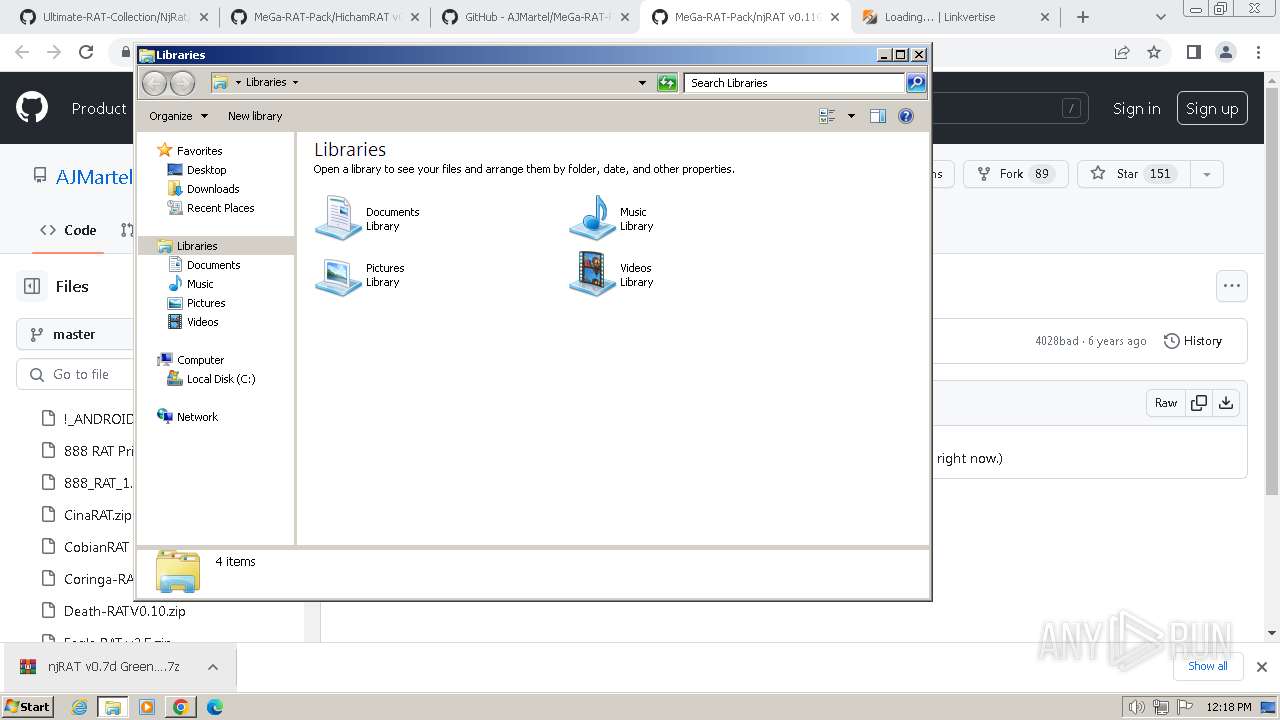
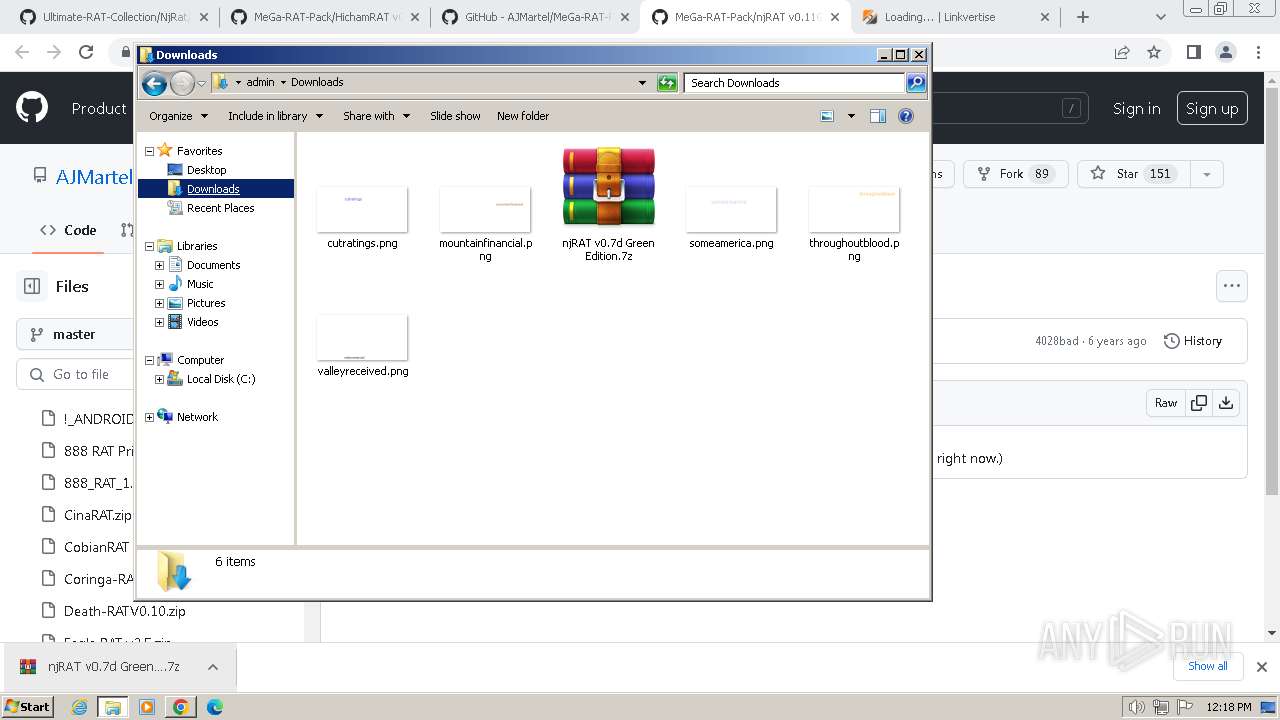
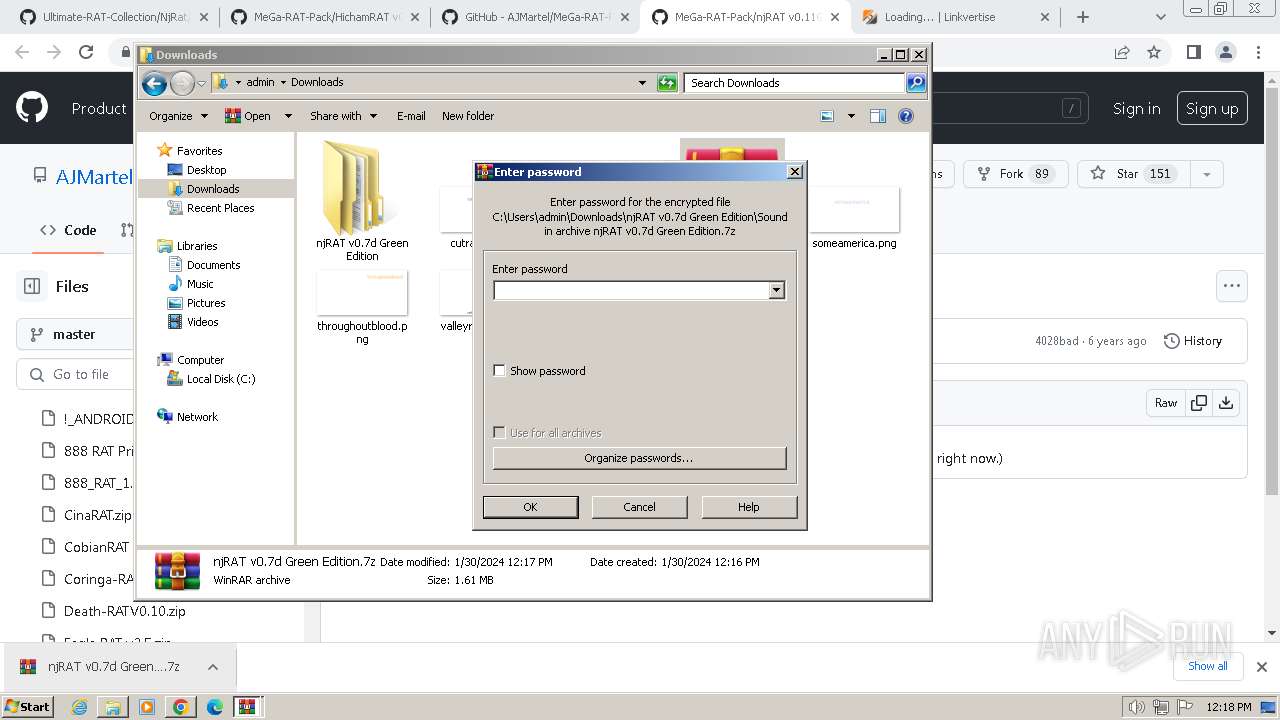
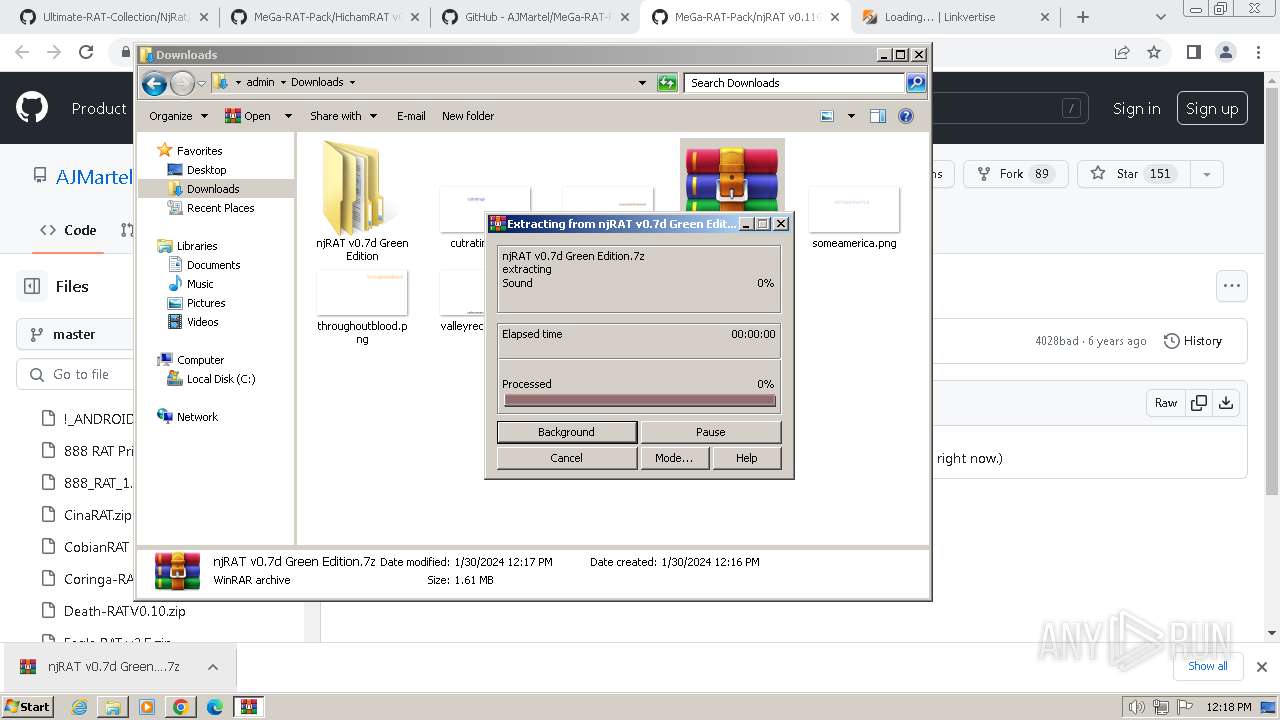
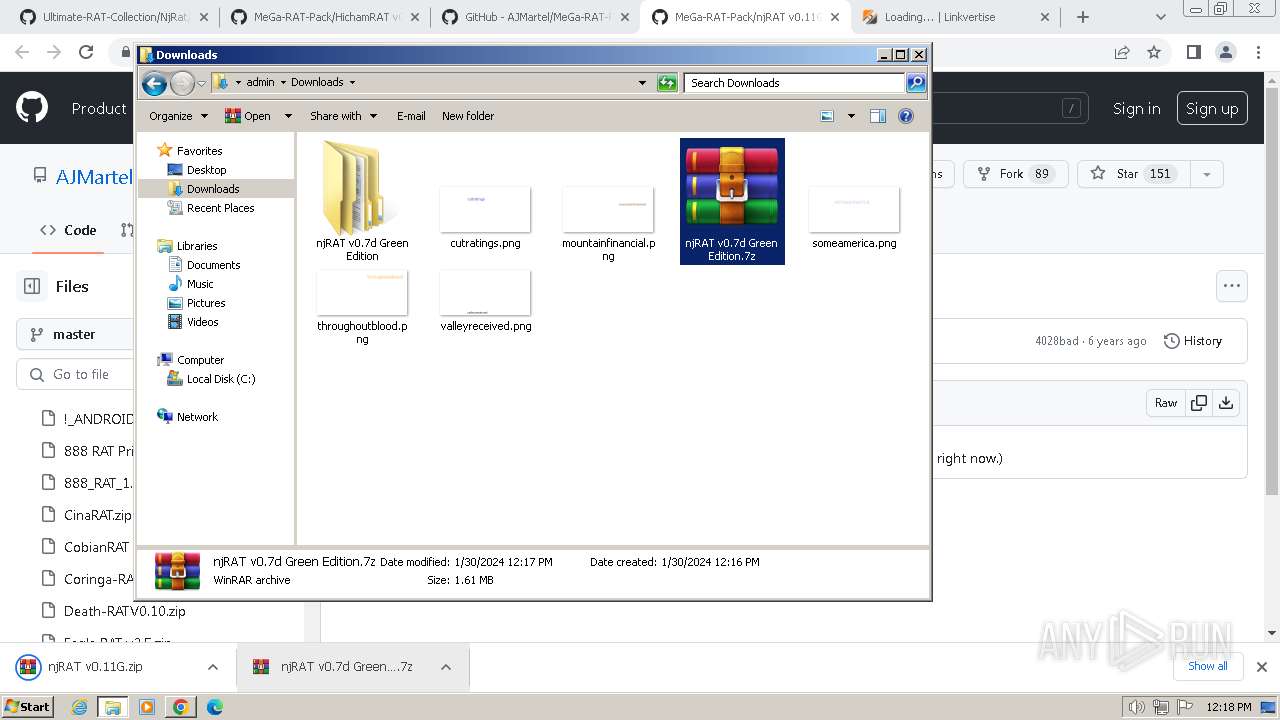
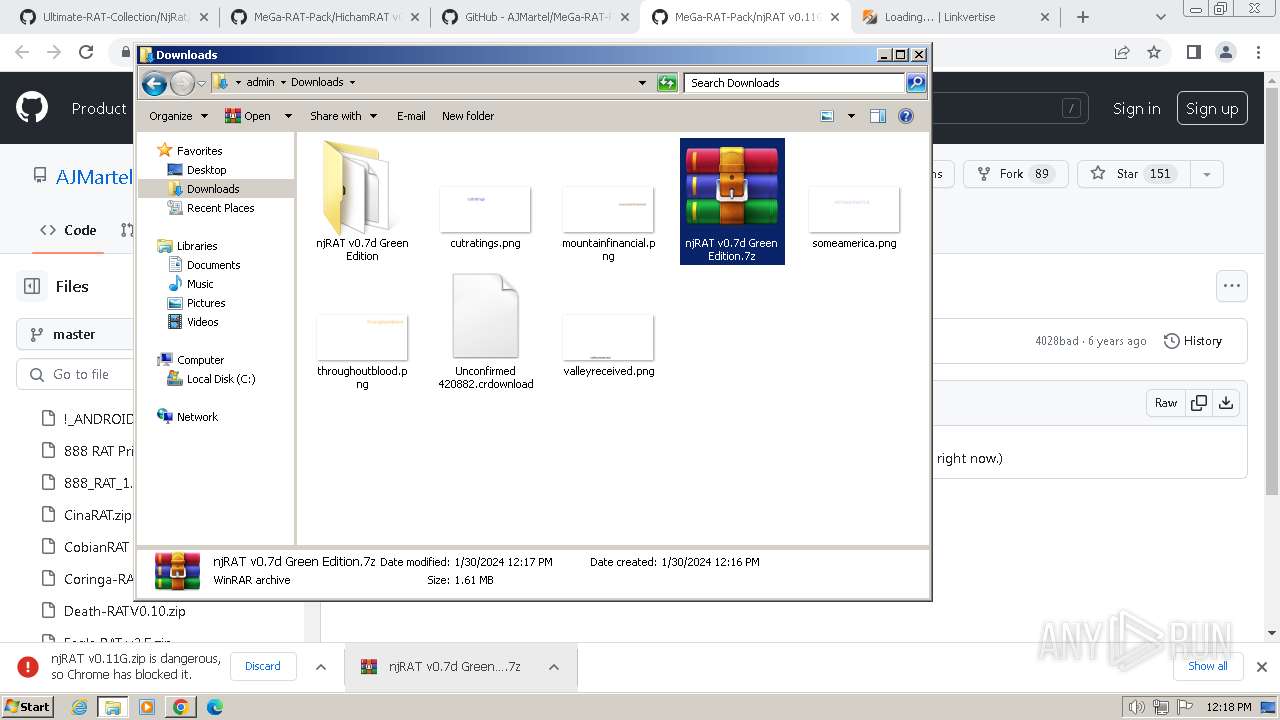
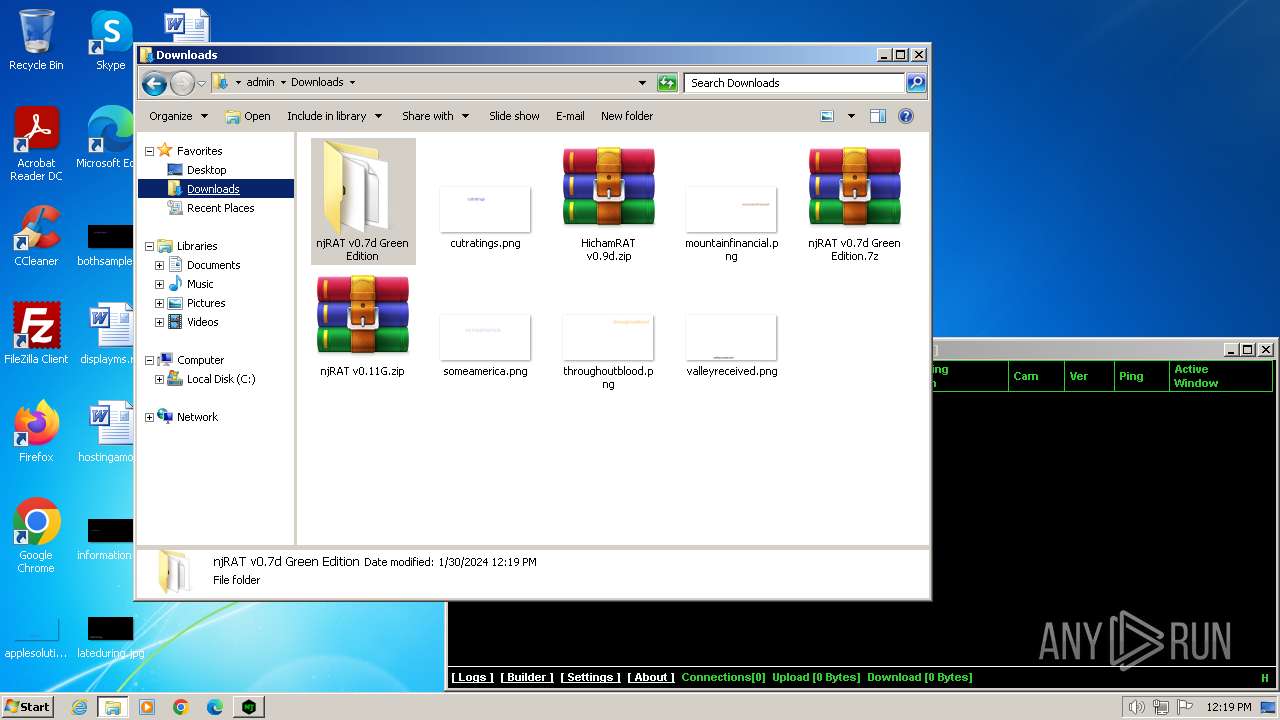
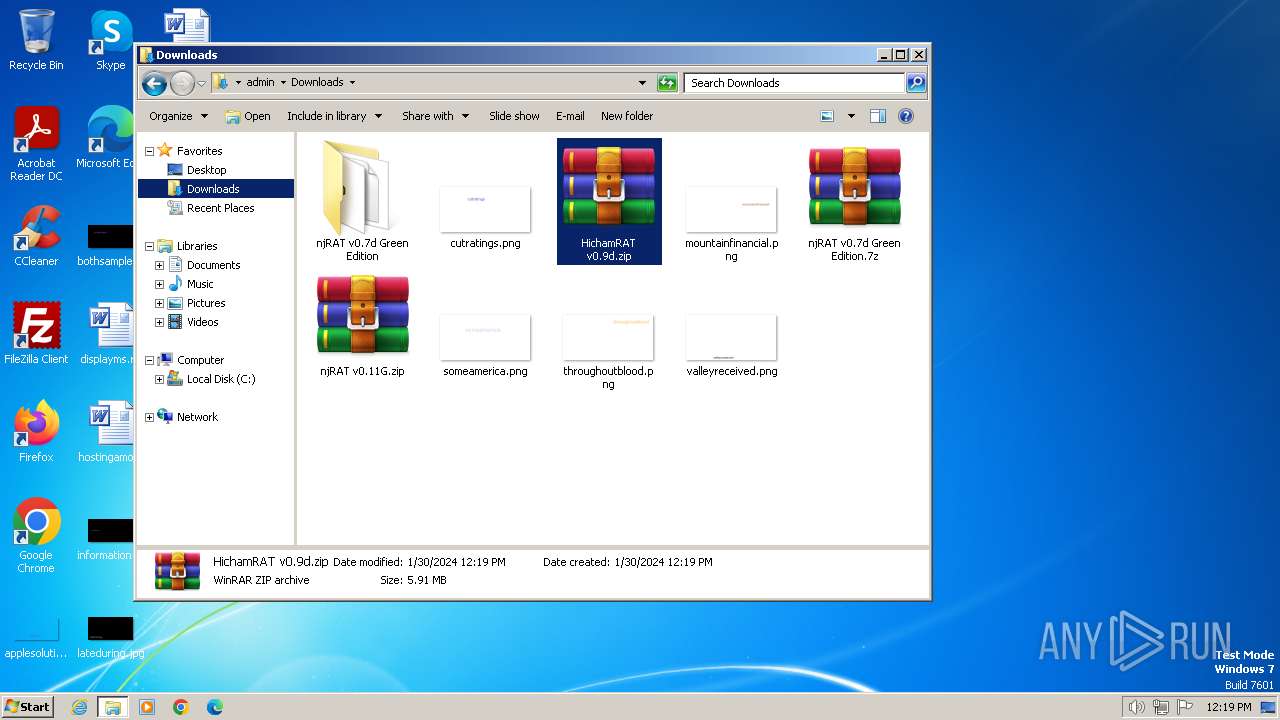
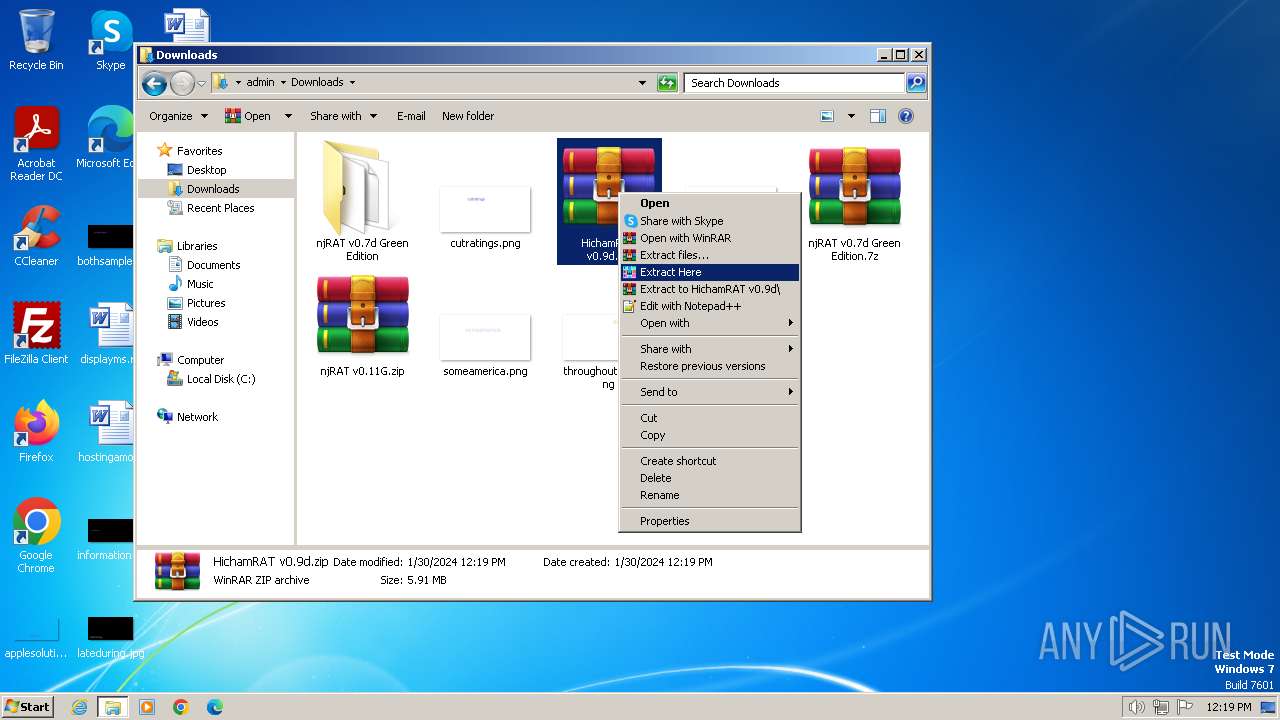
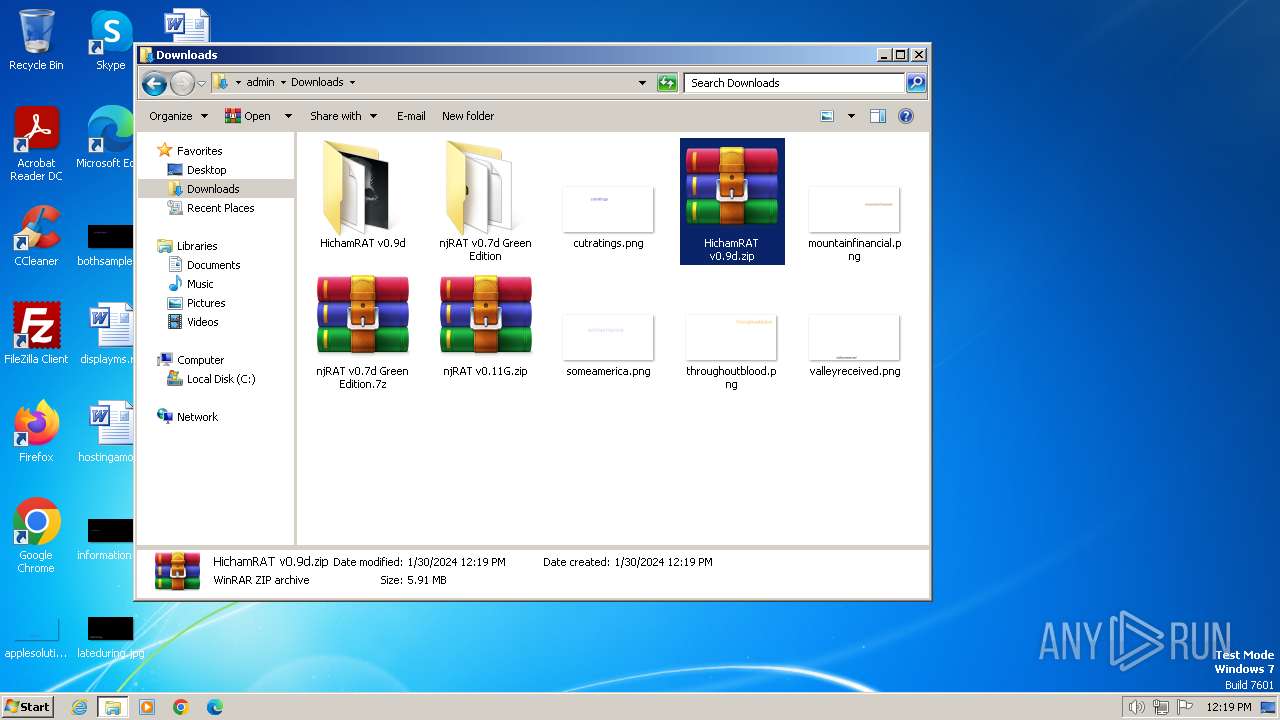
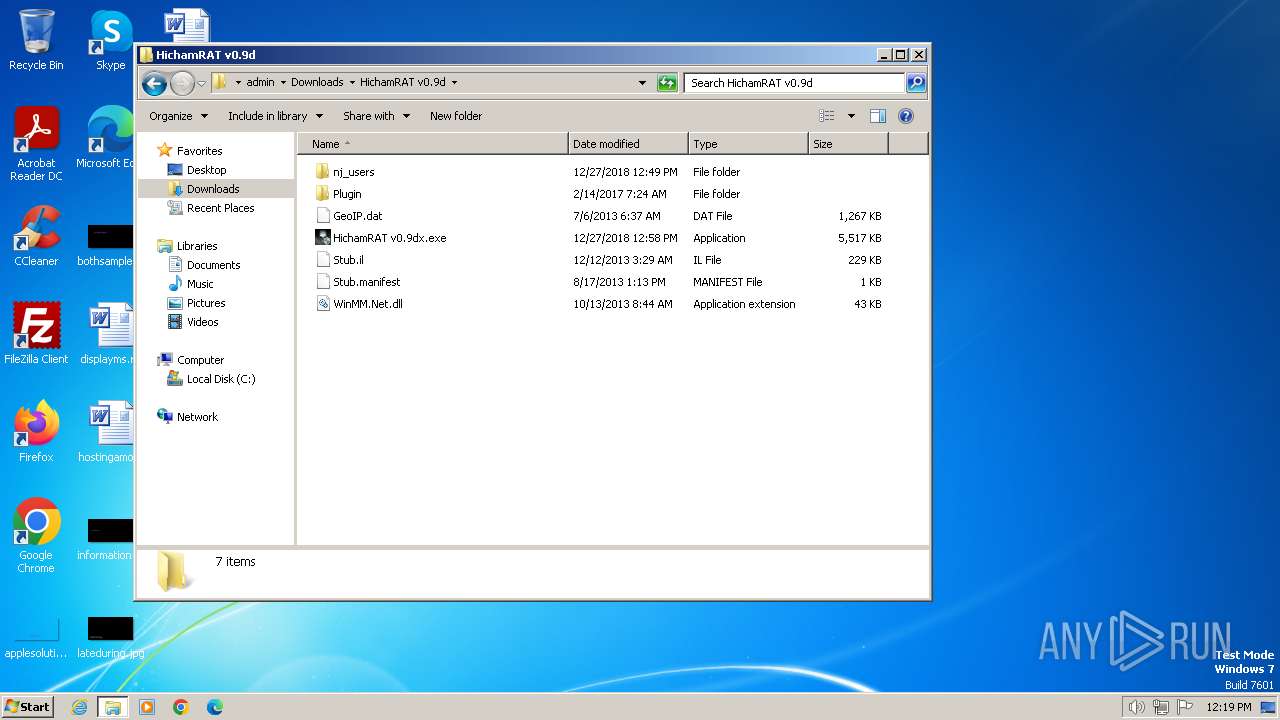
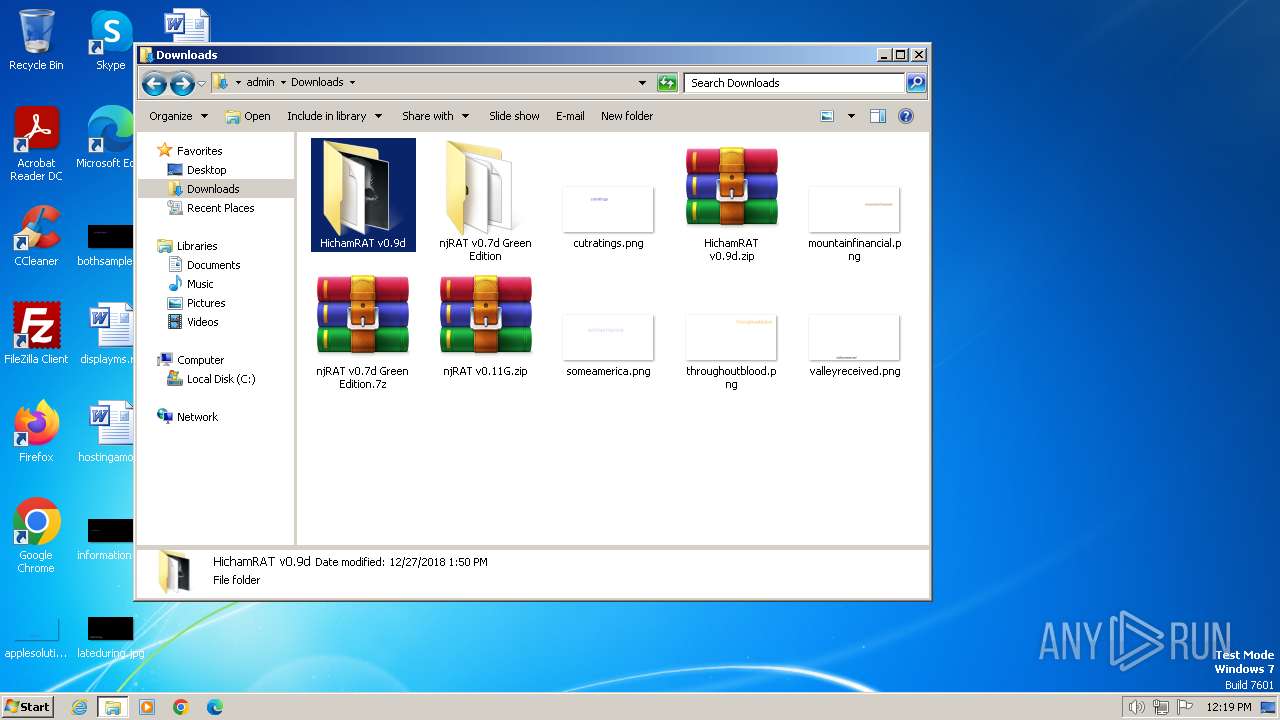
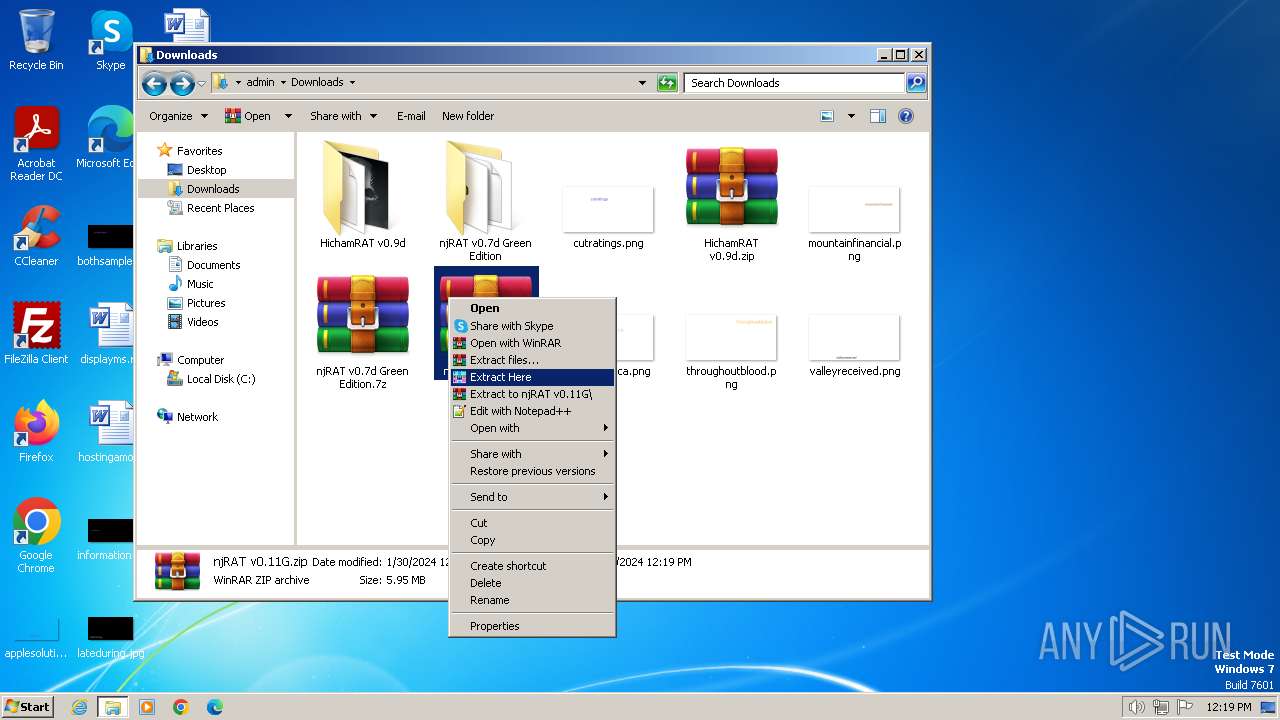
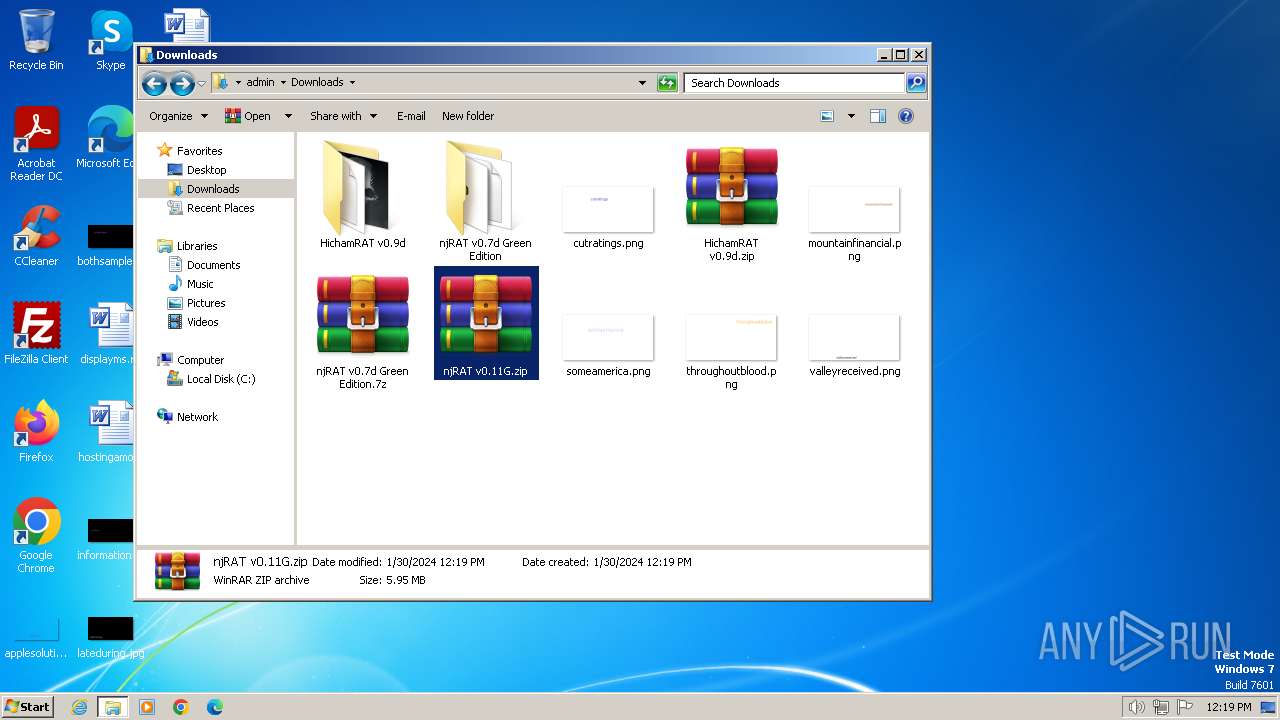
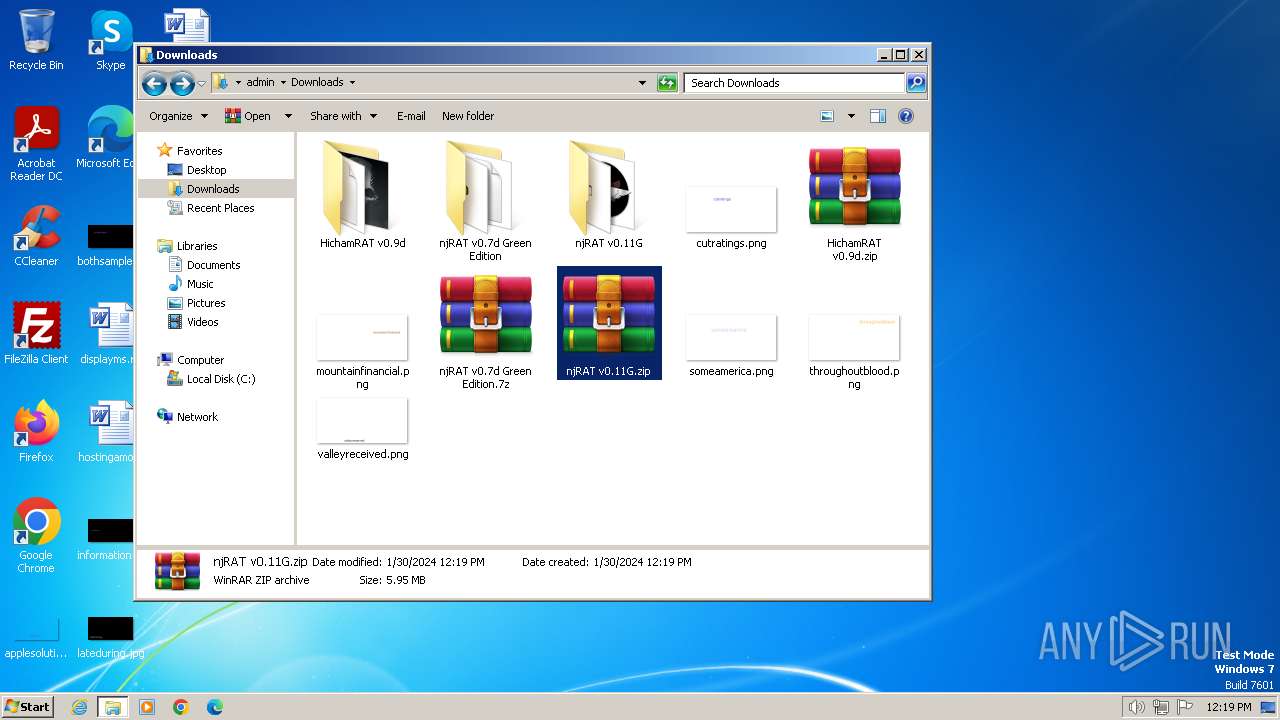
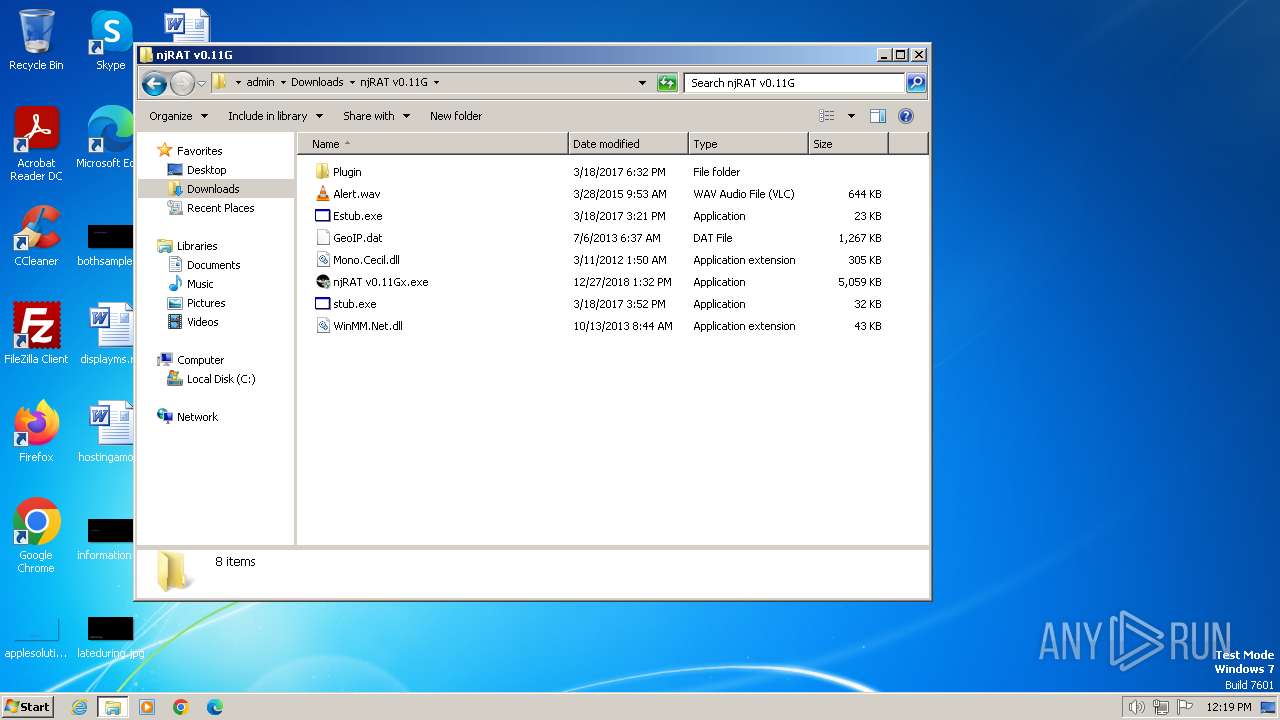
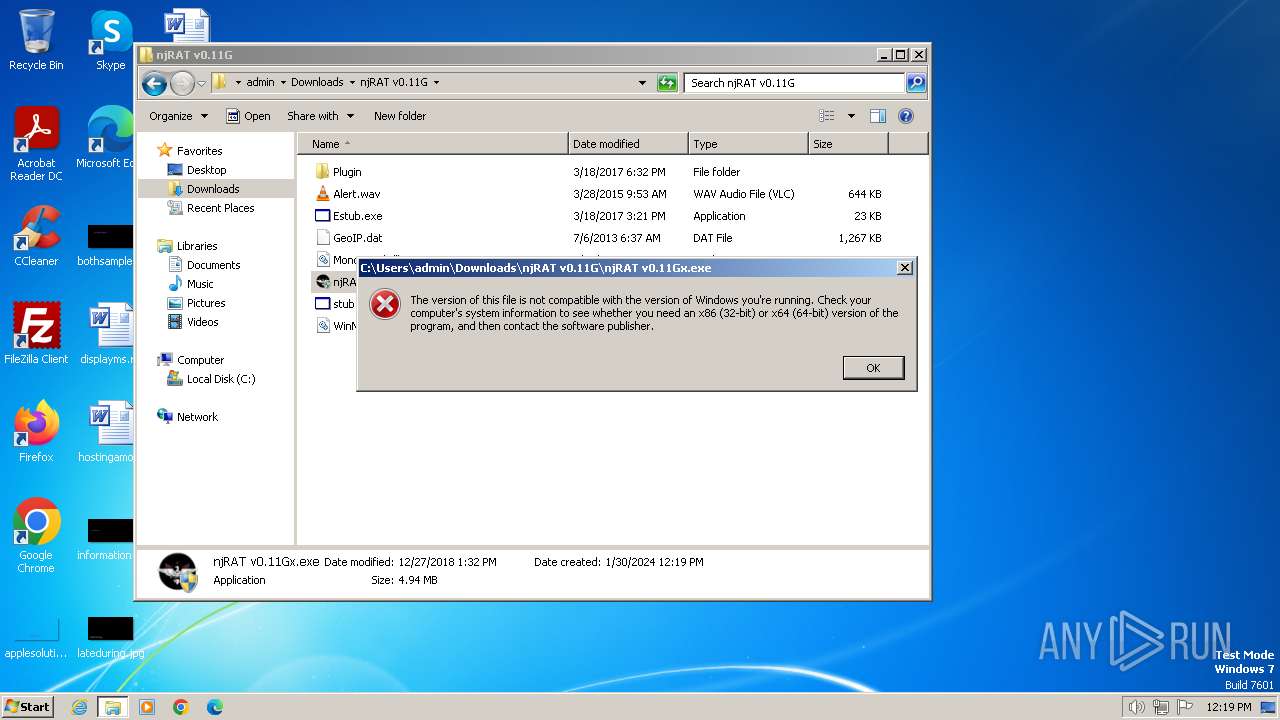
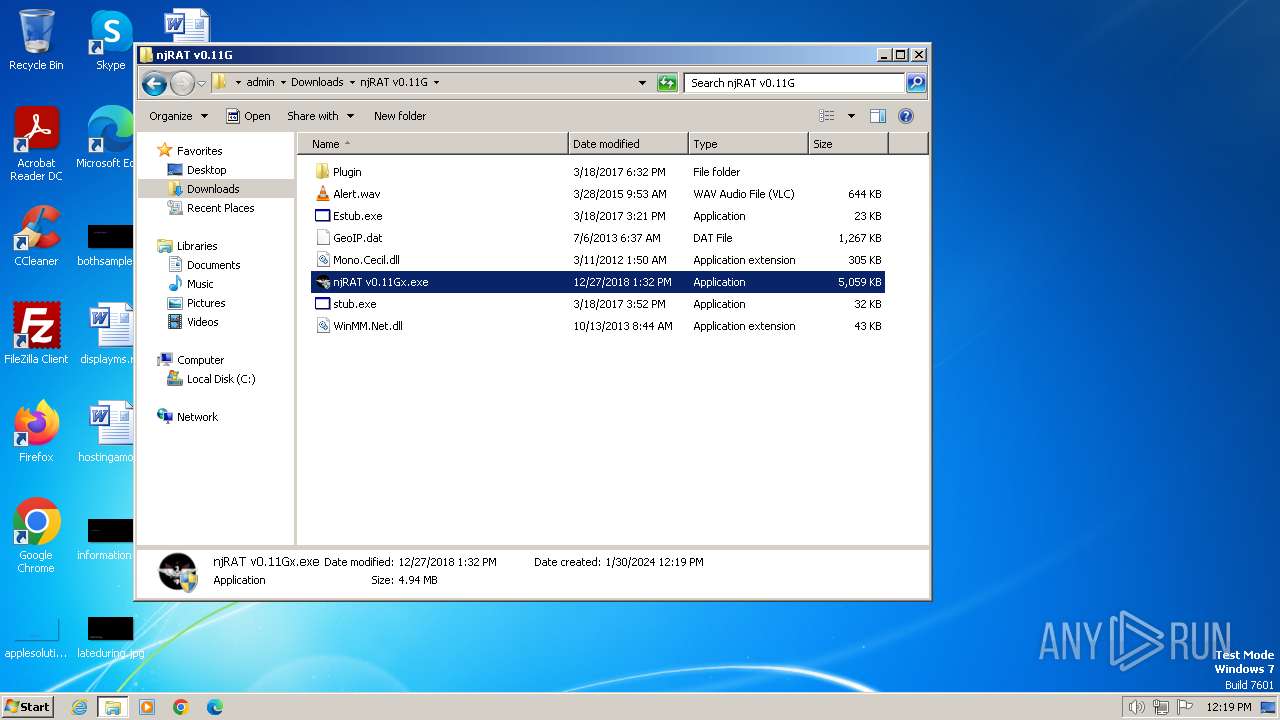
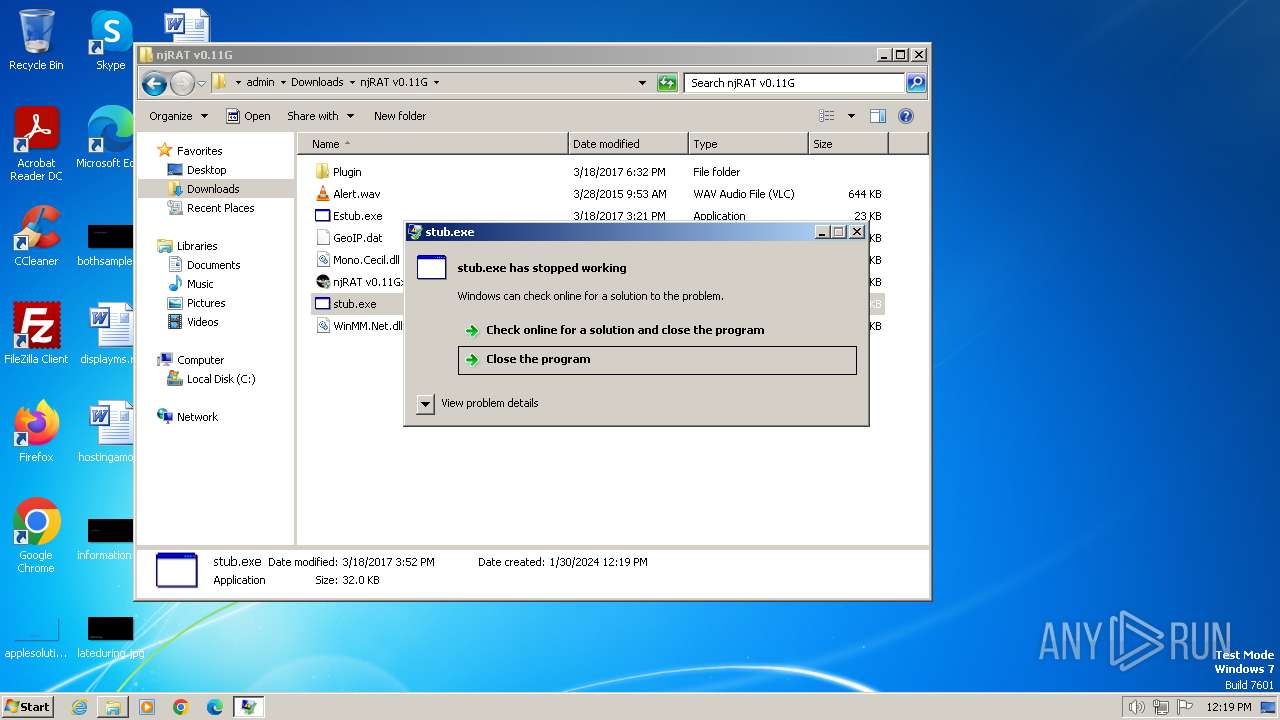
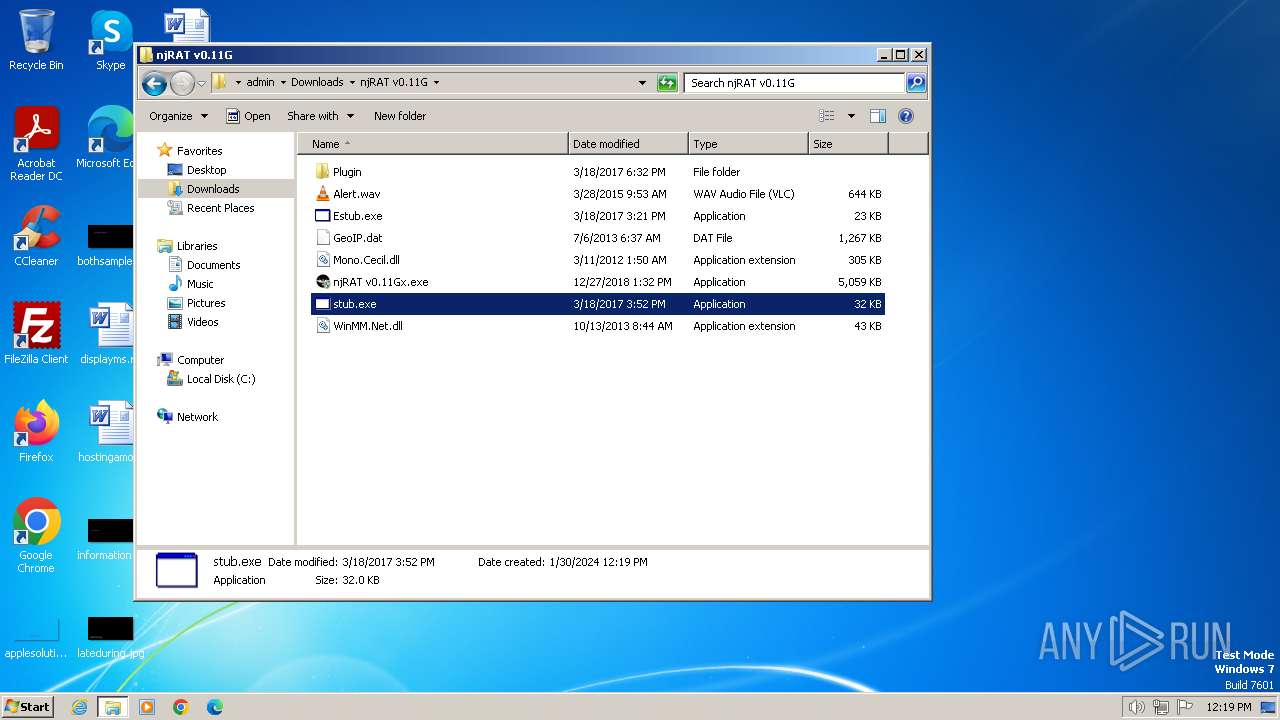
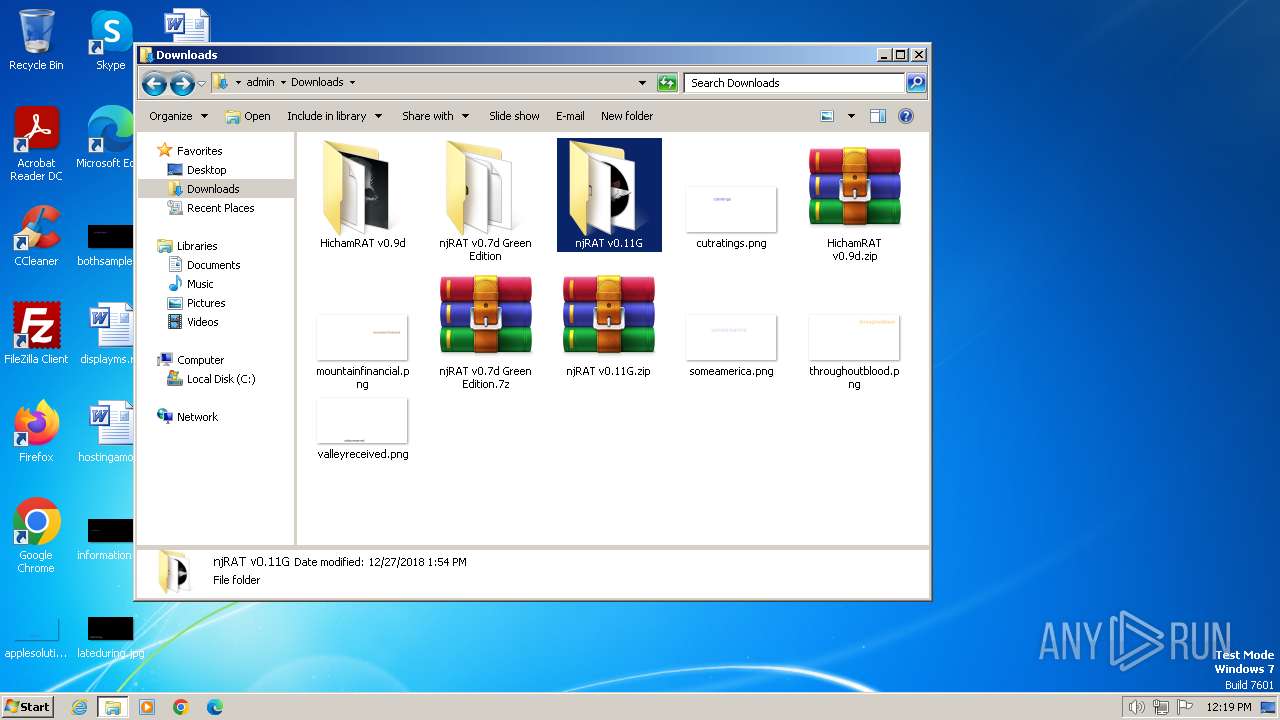
Manual execution by a user
- explorer.exe (PID: 3712)
- WinRAR.exe (PID: 3656)
- NjRat 0.7D Green Edition by im523.exe (PID: 2408)
- WinRAR.exe (PID: 1548)
- stub.exe (PID: 3856)
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
- WinRAR.exe (PID: 2592)
The process uses the downloaded file
- chrome.exe (PID: 2312)
- WinRAR.exe (PID: 3656)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3800)
- WinRAR.exe (PID: 1548)
- WinRAR.exe (PID: 2592)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3656)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 1092)
- WinRAR.exe (PID: 2592)
- WinRAR.exe (PID: 1548)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3656)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 1092)
- chrome.exe (PID: 532)
- WinRAR.exe (PID: 1548)
- WinRAR.exe (PID: 2592)
Checks supported languages
- NjRat 0.7D Green Edition by im523.exe (PID: 2408)
- stub.exe (PID: 3856)
- dw20.exe (PID: 908)
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
- ilasm.exe (PID: 3024)
Application launched itself
- chrome.exe (PID: 532)
Reads the machine GUID from the registry
- NjRat 0.7D Green Edition by im523.exe (PID: 2408)
- stub.exe (PID: 3856)
- dw20.exe (PID: 908)
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
Reads the computer name
- NjRat 0.7D Green Edition by im523.exe (PID: 2408)
- dw20.exe (PID: 908)
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
Reads Environment values
- NjRat 0.7D Green Edition by im523.exe (PID: 2408)
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
Creates files or folders in the user directory
- dw20.exe (PID: 908)
Create files in a temporary directory
- NjRat 0.7D Green Edition by im523.exe (PID: 3408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
58
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3184 --field-trial-handle=1212,i,2716092218637035450,371262528521185284,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=4736 --field-trial-handle=1212,i,2716092218637035450,371262528521185284,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1128 --field-trial-handle=1212,i,2716092218637035450,371262528521185284,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=3560 --field-trial-handle=1212,i,2716092218637035450,371262528521185284,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://github.com/yuankong666/Ultimate-RAT-Collection" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=1056 --field-trial-handle=1212,i,2716092218637035450,371262528521185284,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1256 --field-trial-handle=1212,i,2716092218637035450,371262528521185284,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 908 | dw20.exe -x -s 376 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | stub.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=788 --field-trial-handle=1212,i,2716092218637035450,371262528521185284,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bc68b38,0x6bc68b48,0x6bc68b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
11 583
Read events
11 361
Write events
218
Delete events
4
Modification events
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
34
Suspicious files
251
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF163657.TMP | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF163666.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF163676.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF163ccf.TMP | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
151
DNS requests
260
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
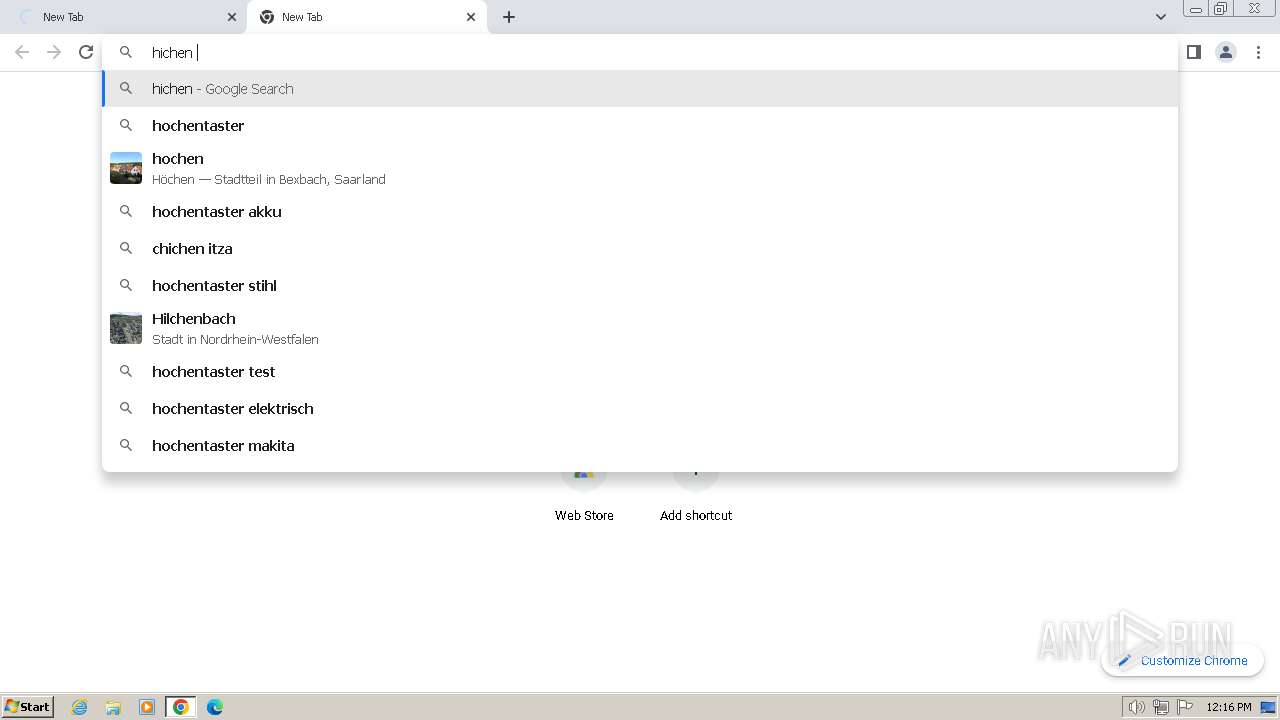
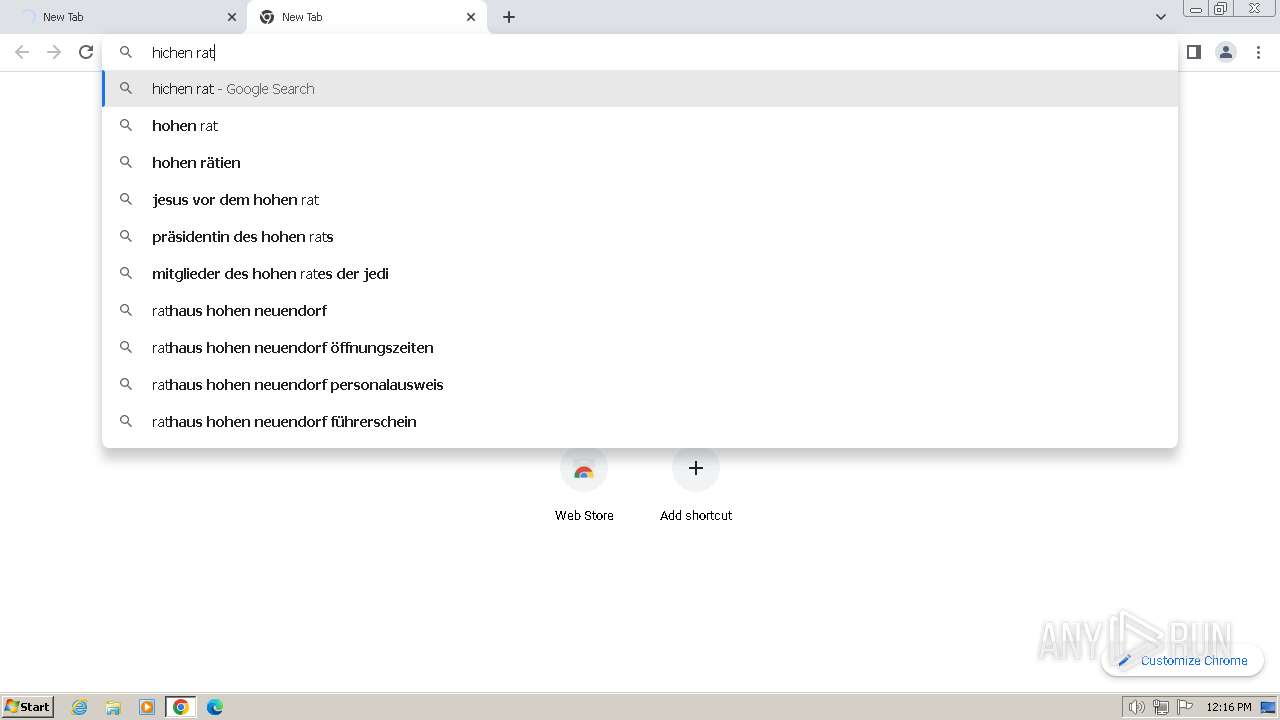
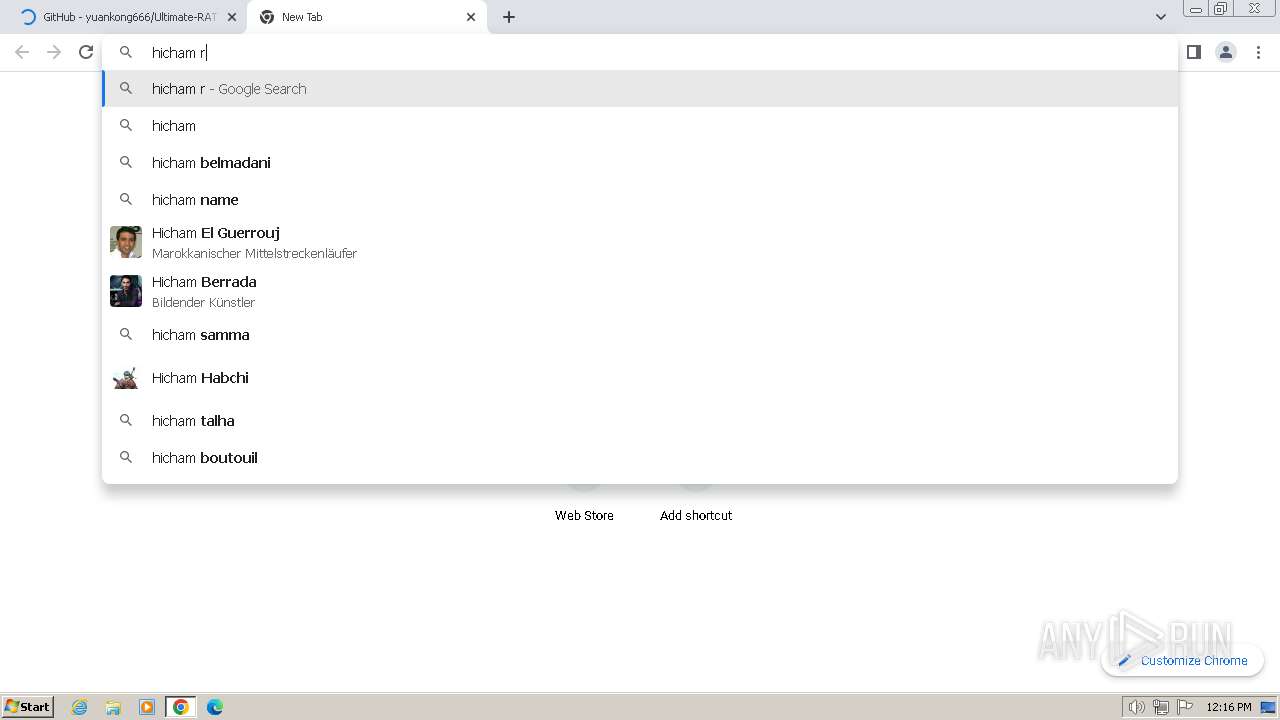
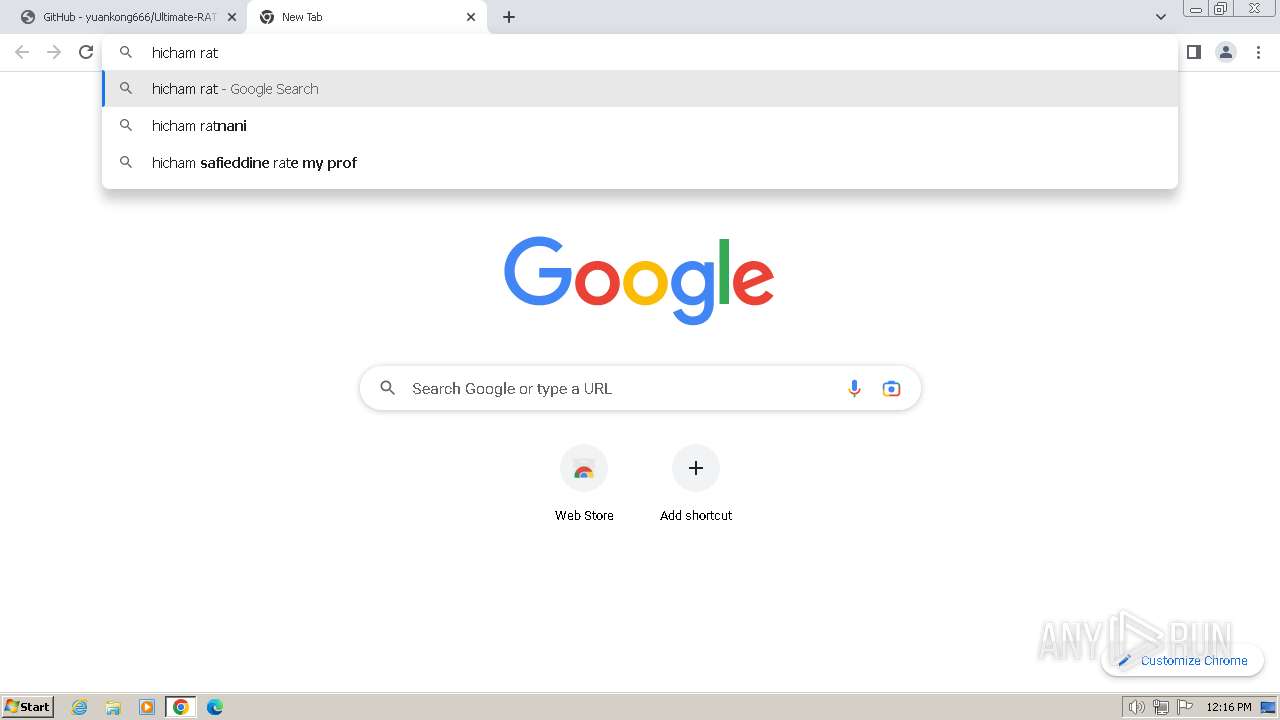
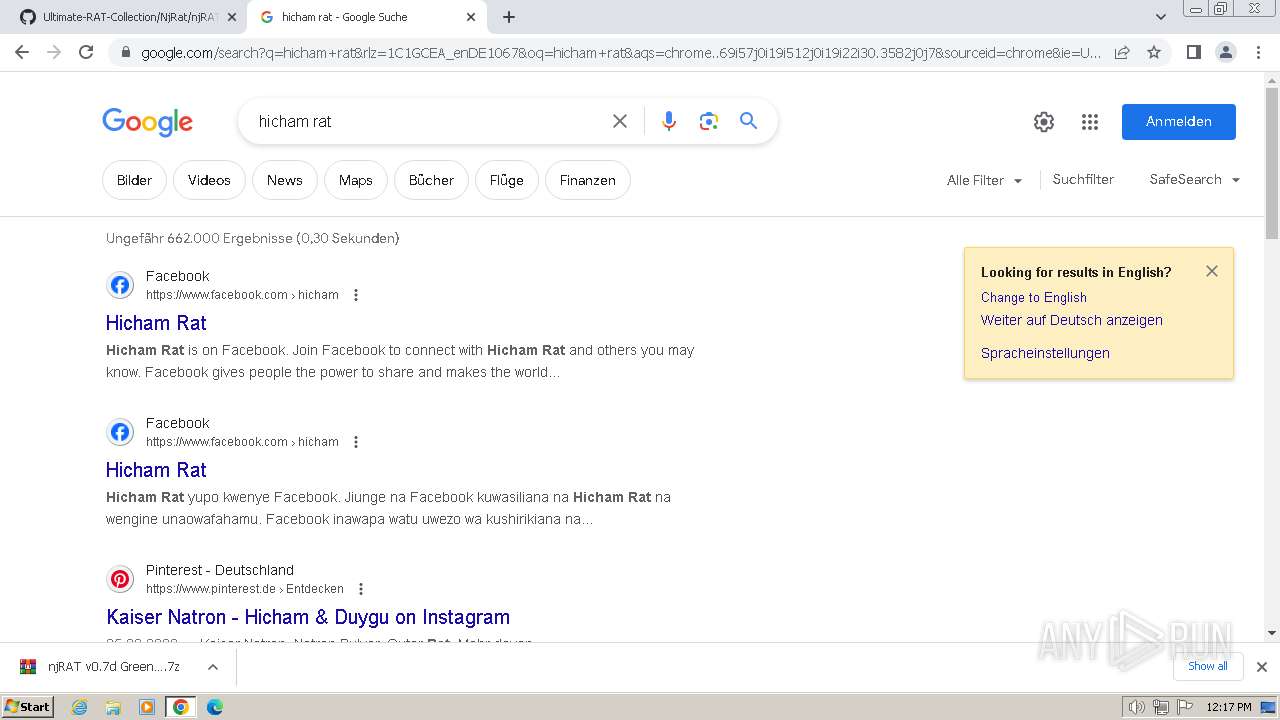
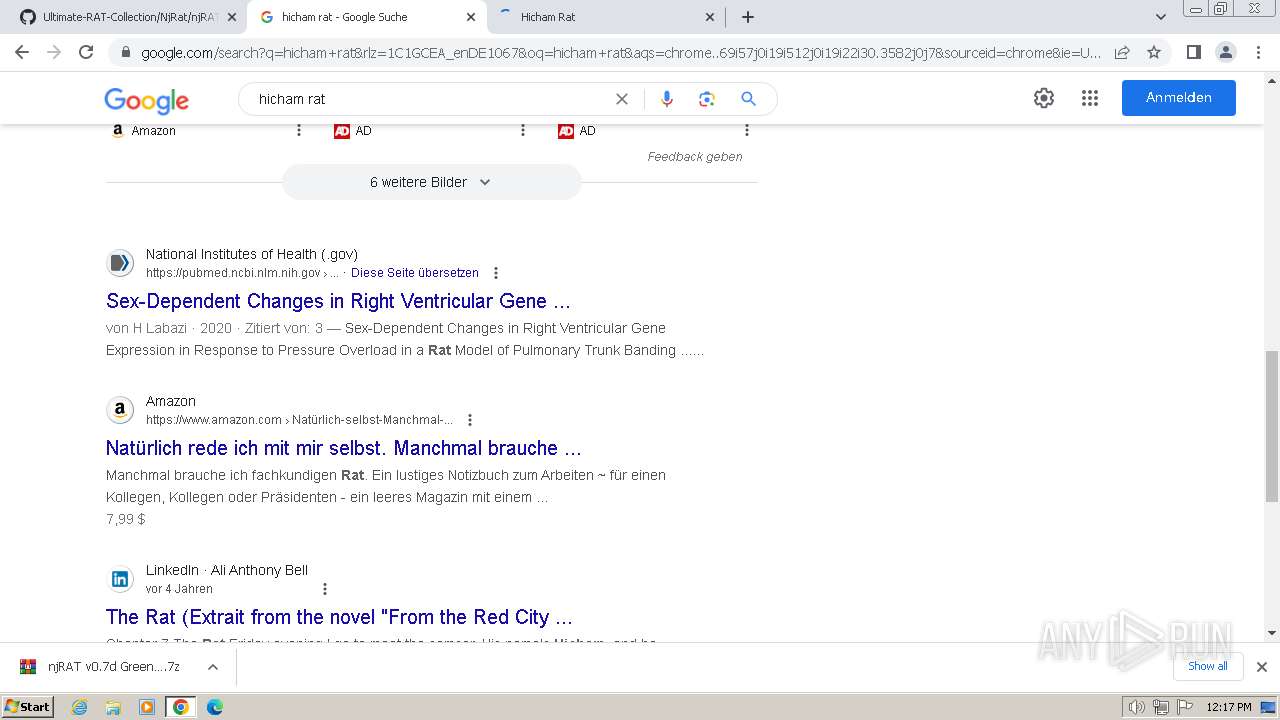
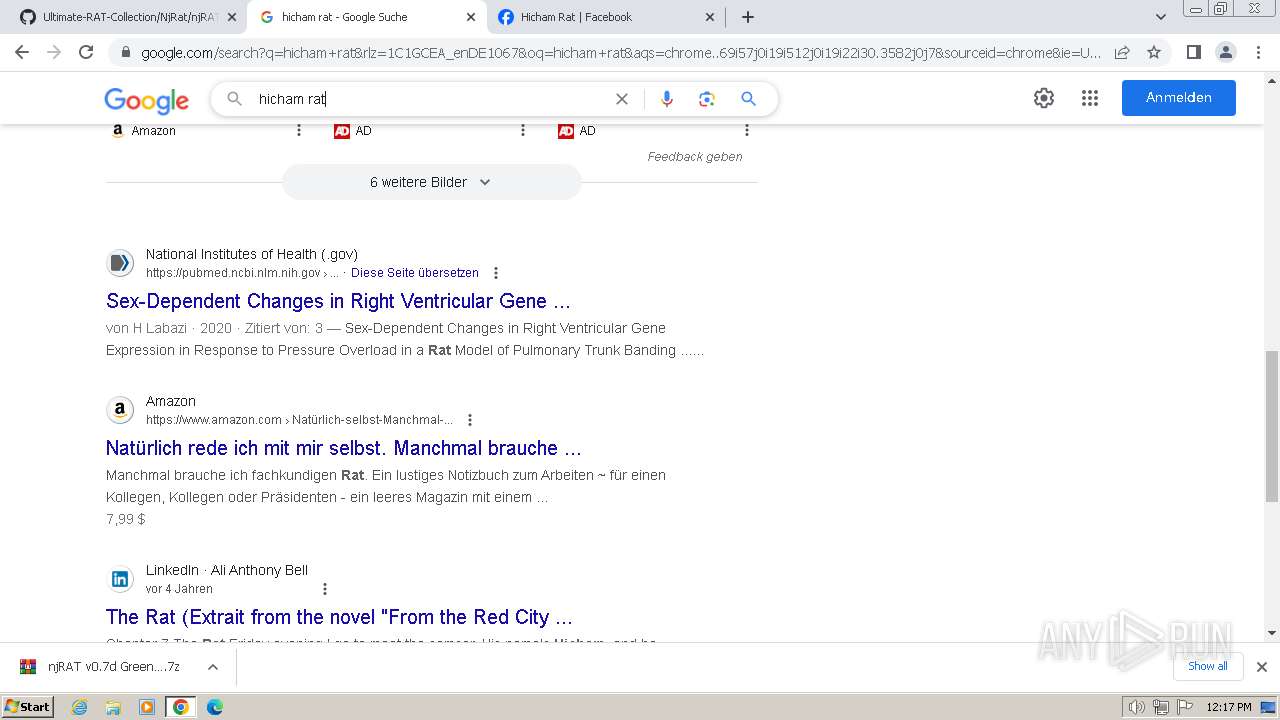
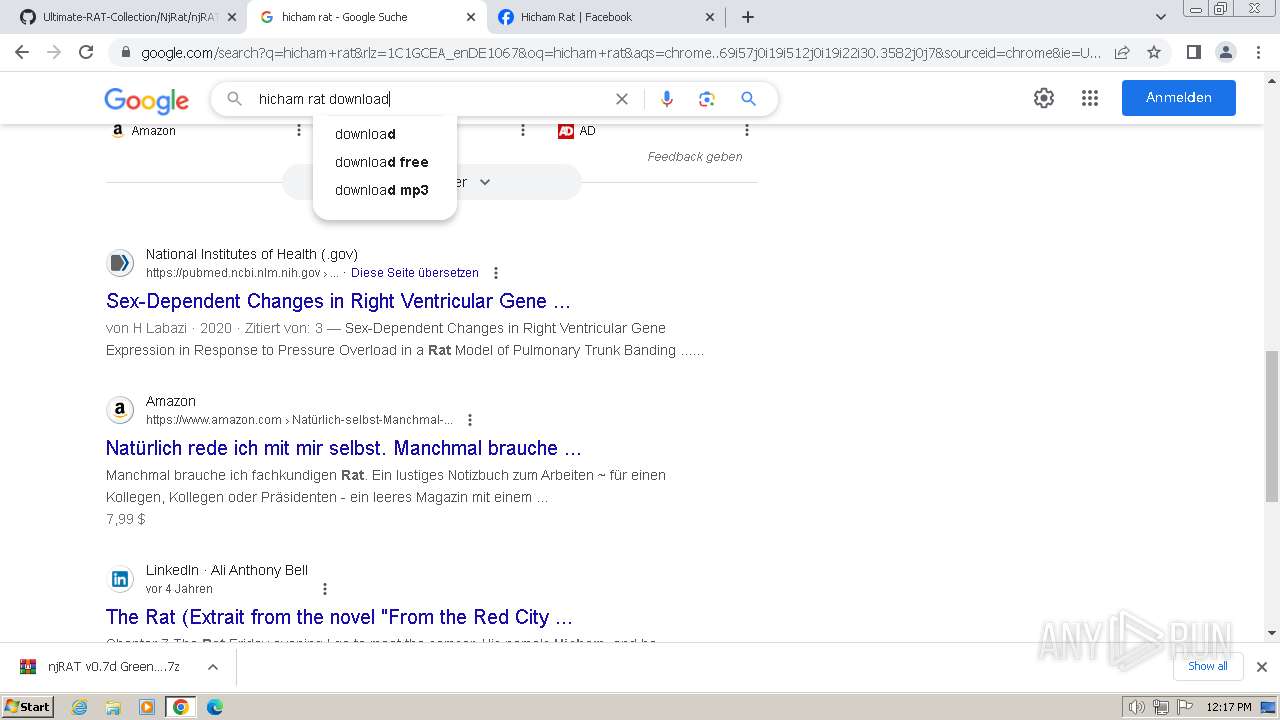
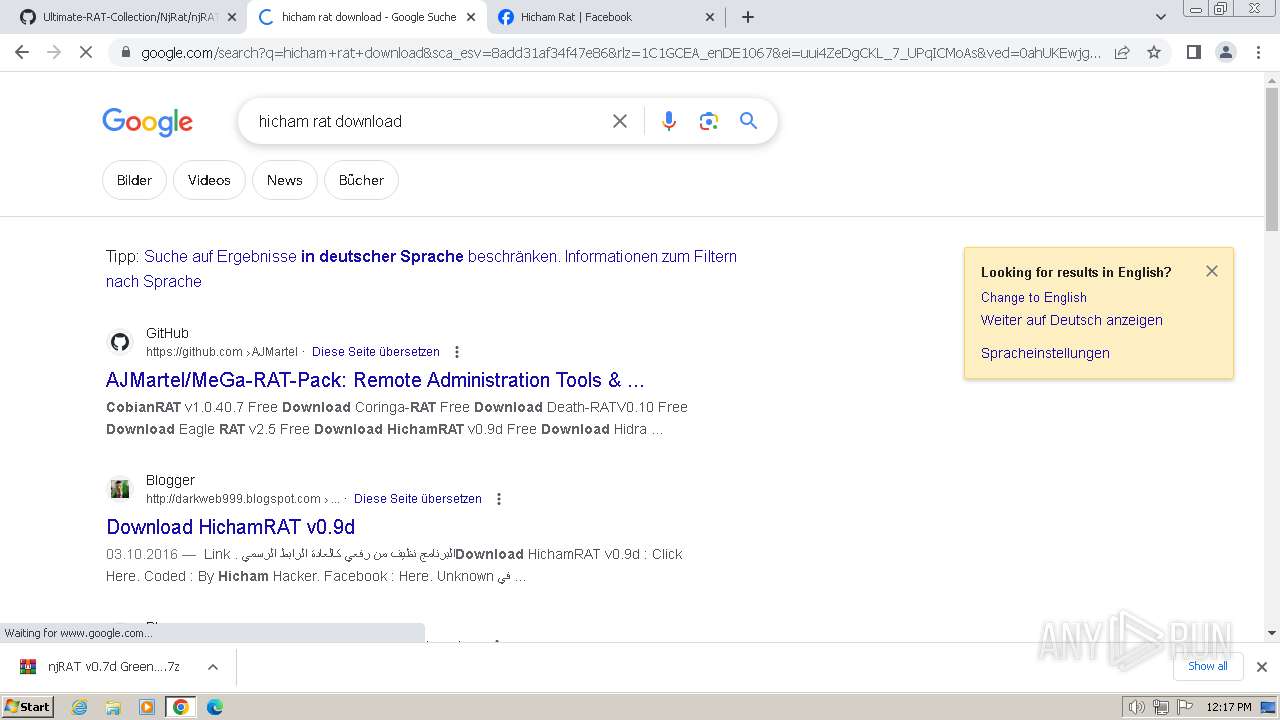
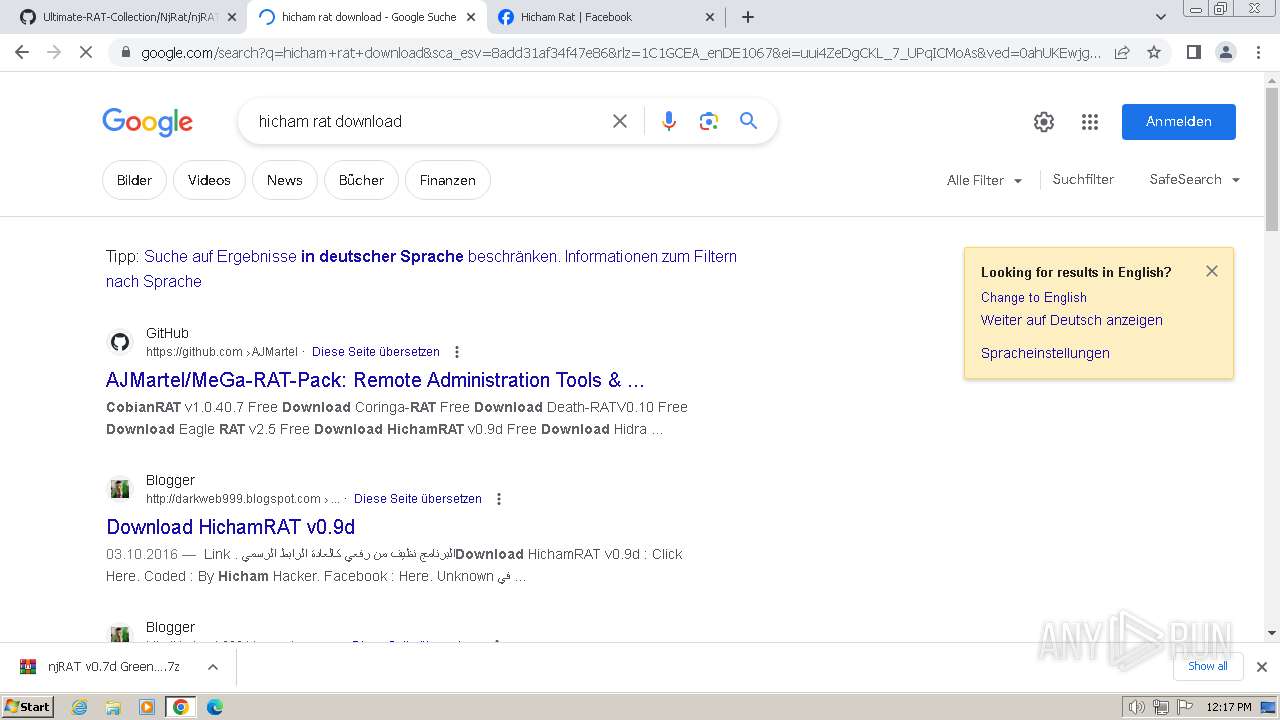
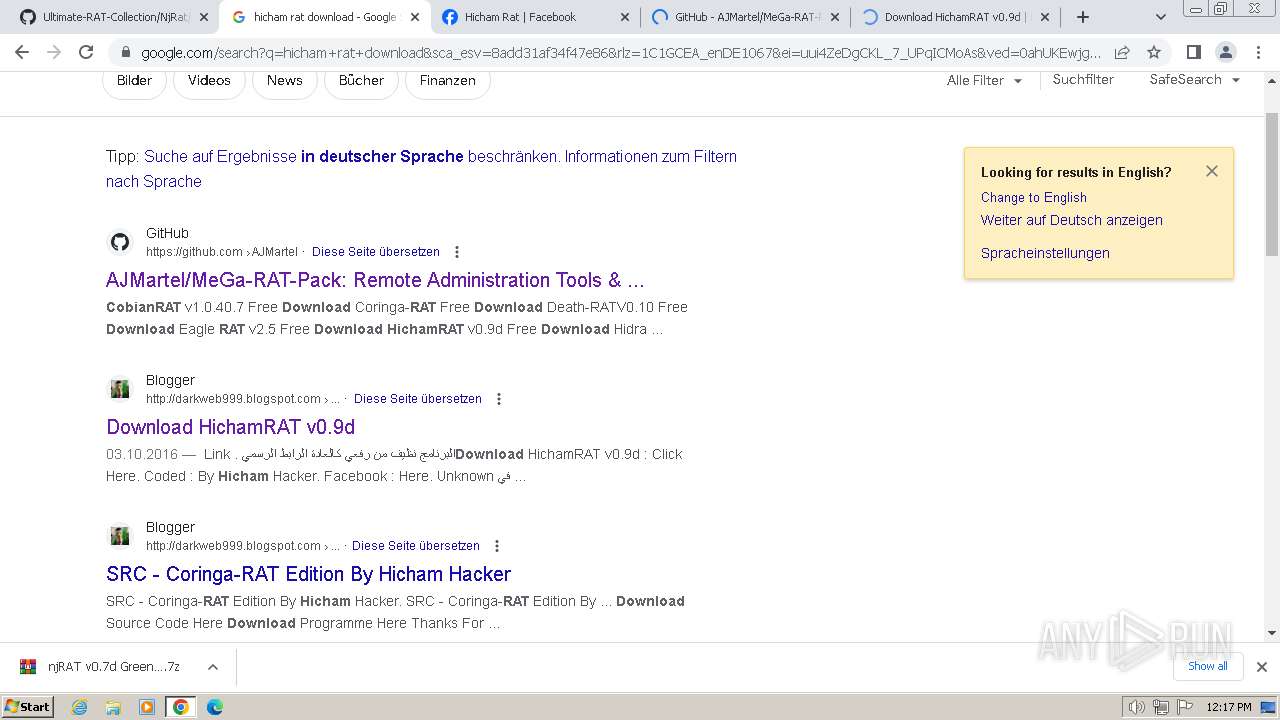
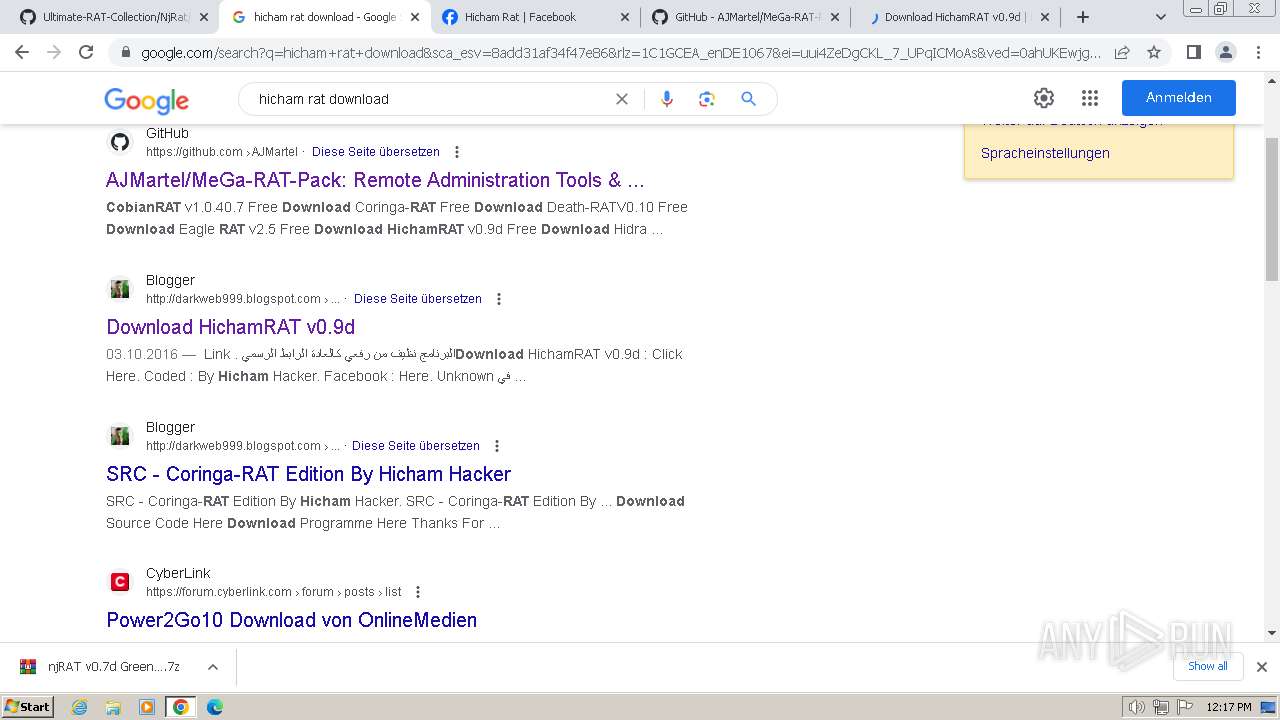
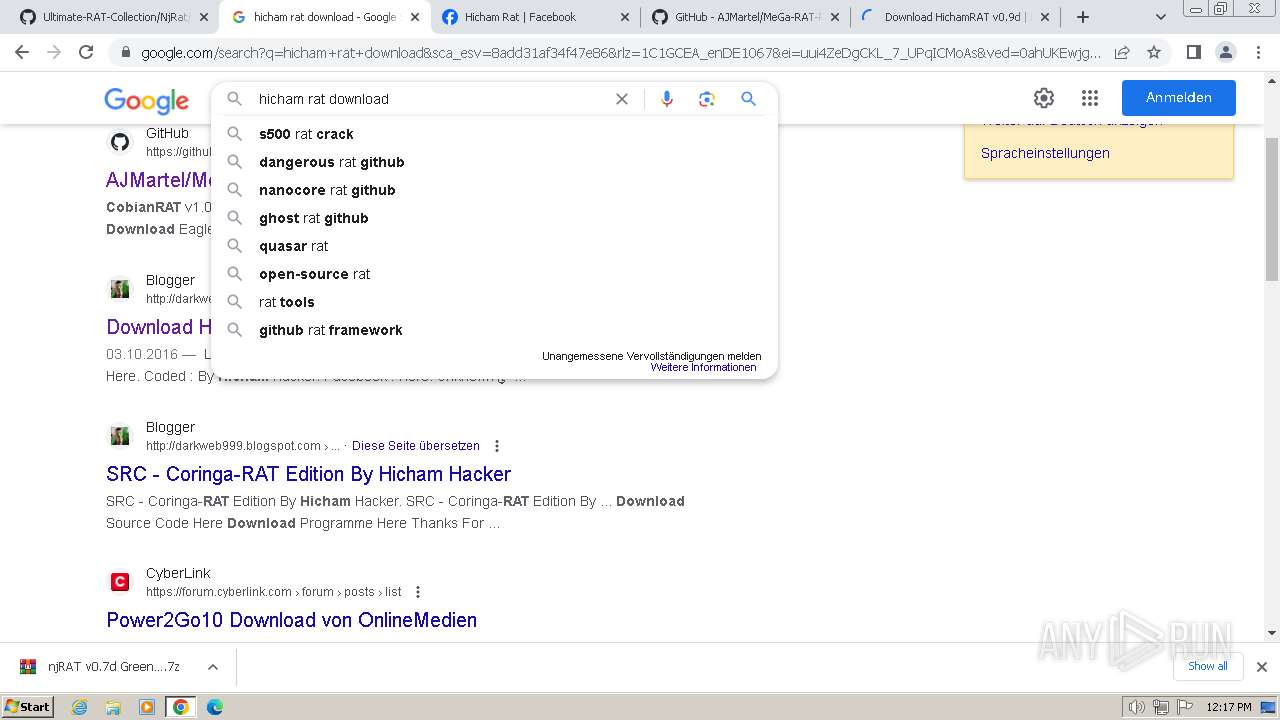
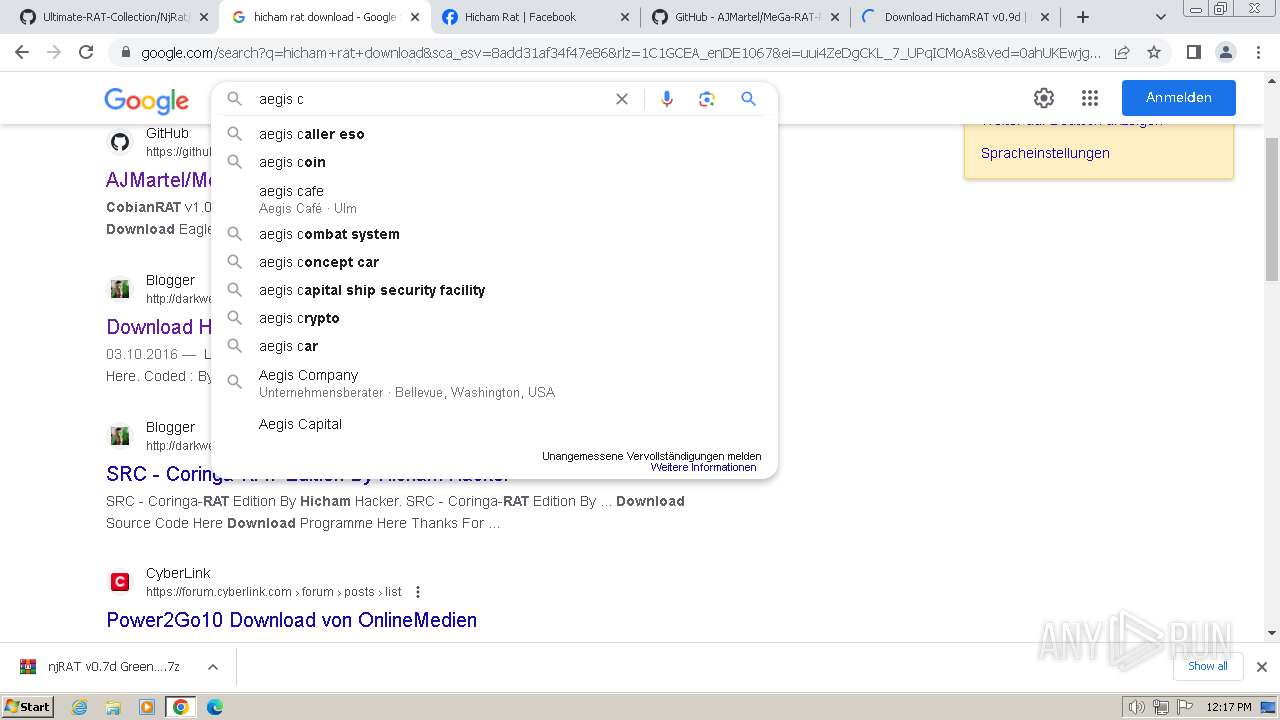
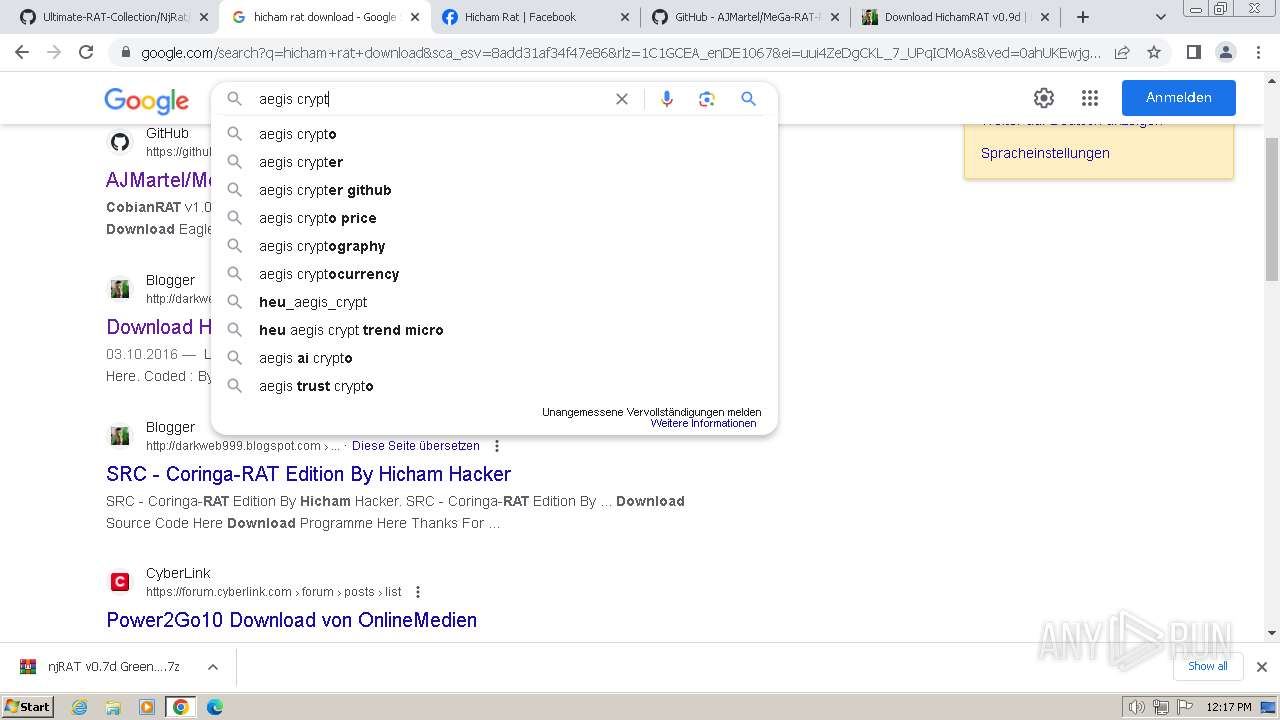
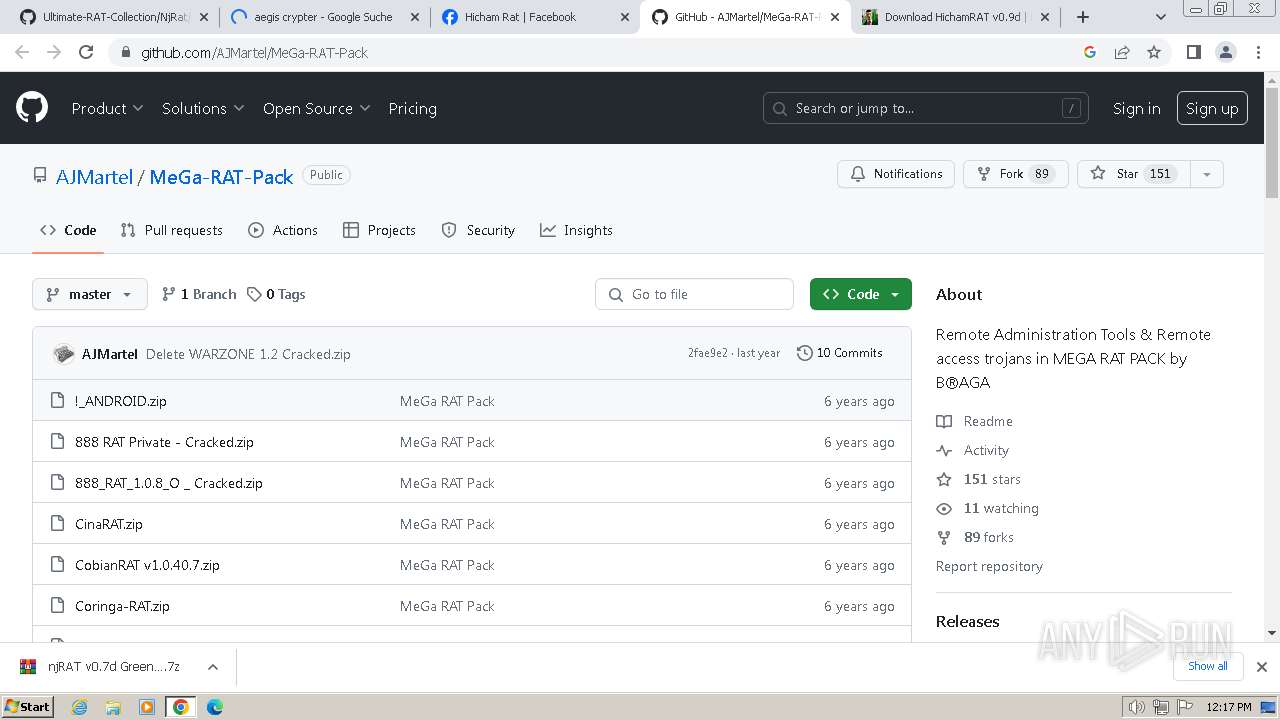
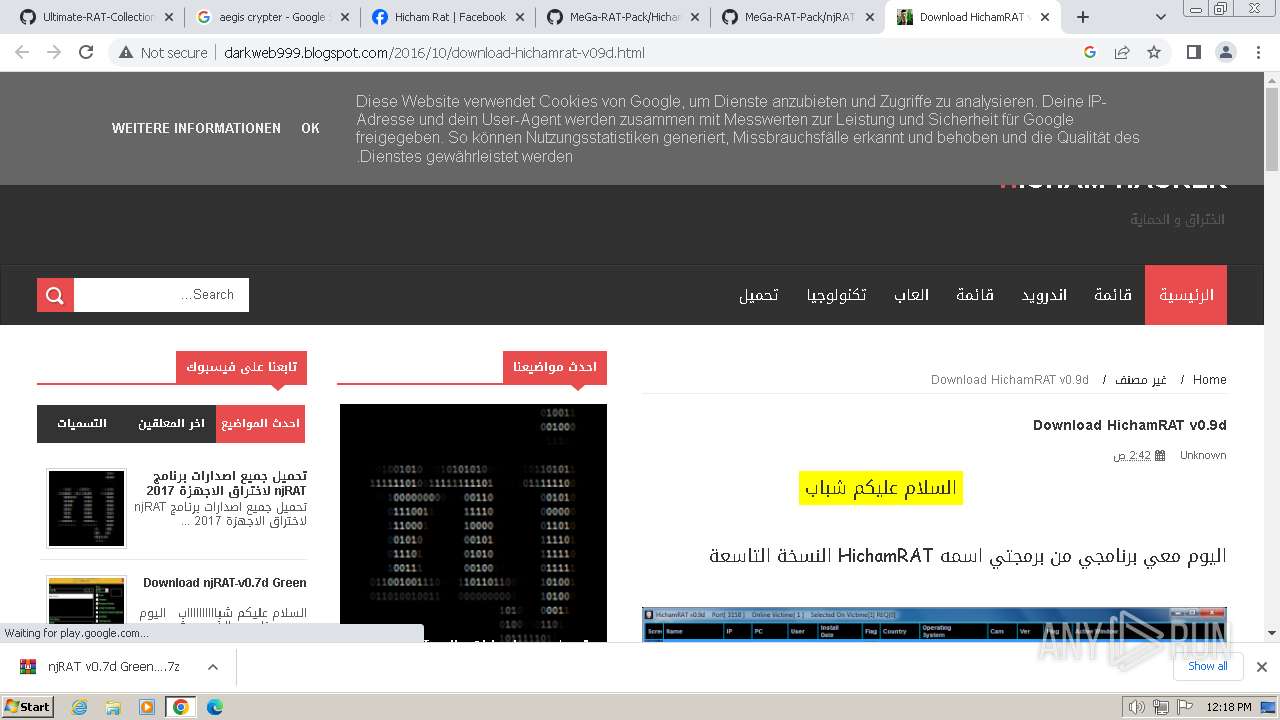
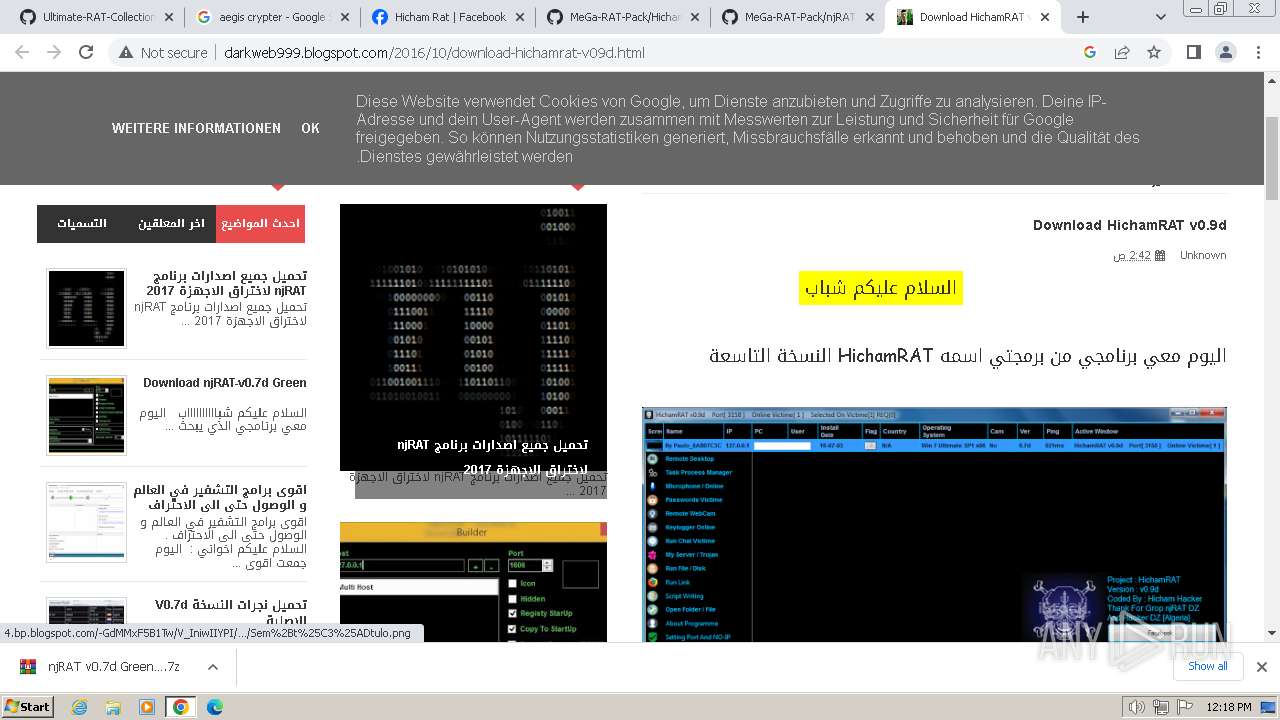
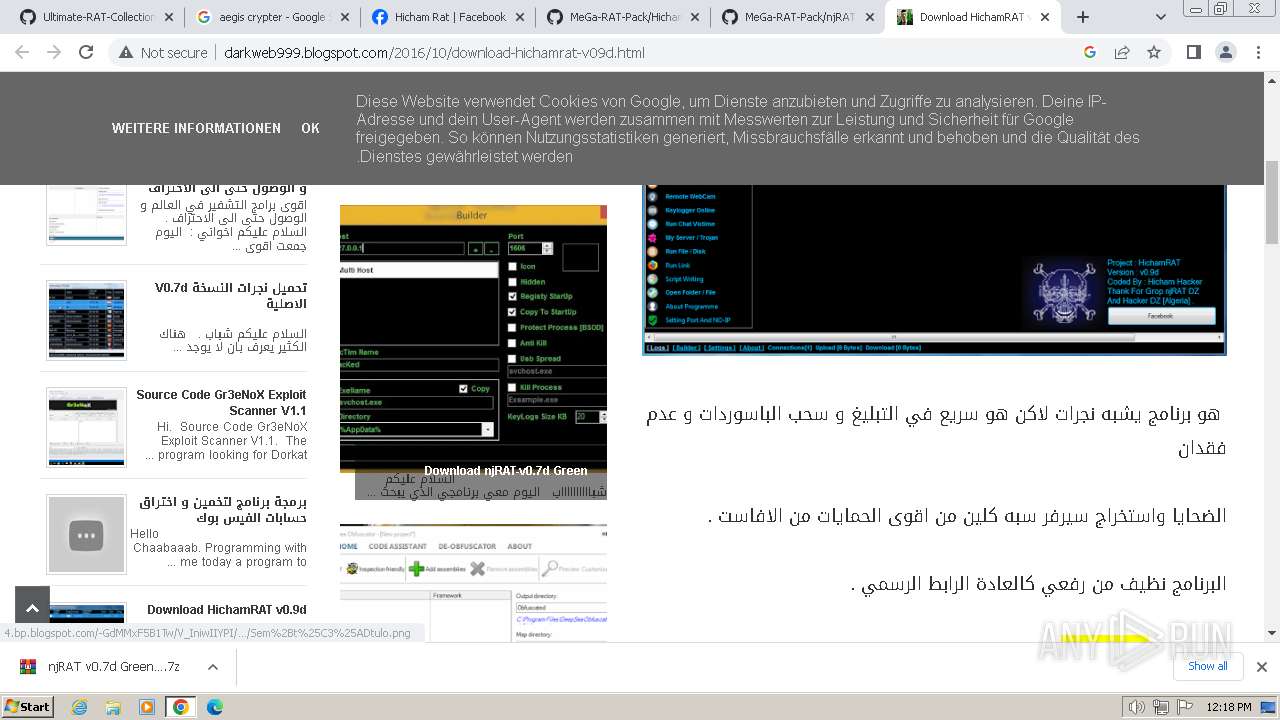
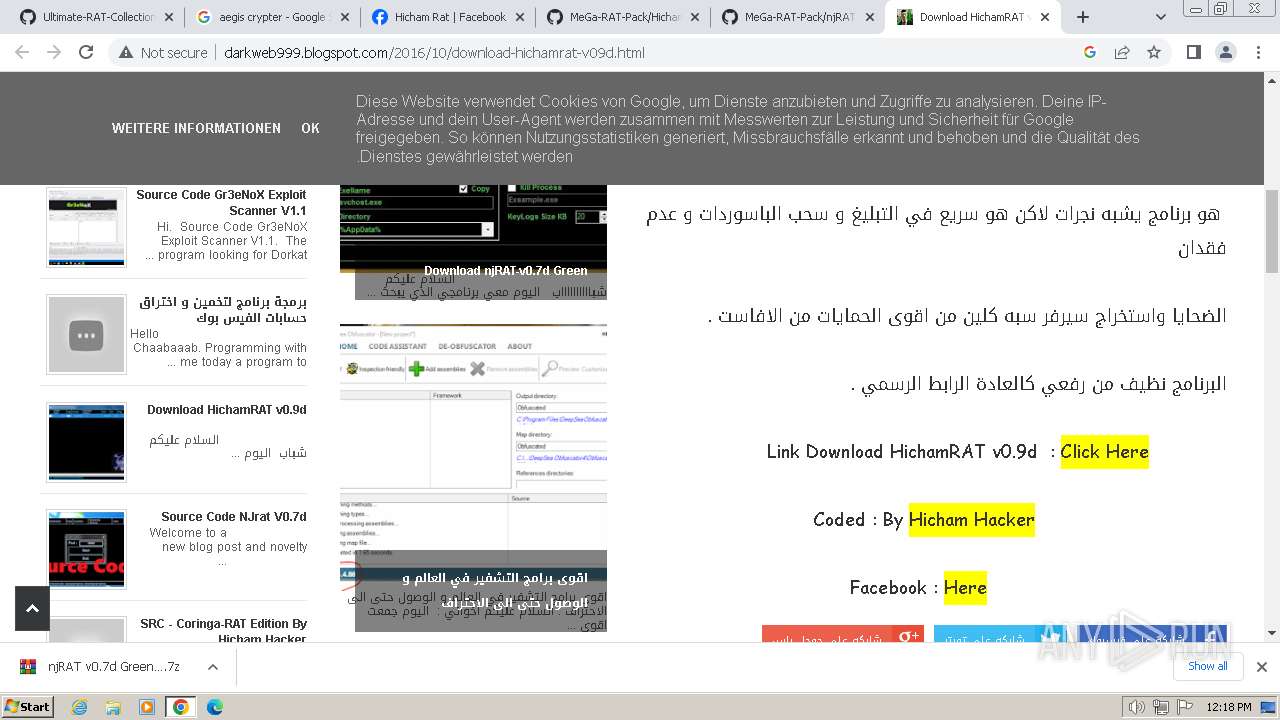
668 | chrome.exe | GET | 200 | 172.217.18.1:80 | http://darkweb999.blogspot.com/2016/10/download-hichamrat-v09d.html | unknown | html | 48.4 Kb | unknown |
668 | chrome.exe | GET | 200 | 151.101.194.137:80 | http://code.jquery.com/jquery-1.8.3.js | unknown | text | 77.0 Kb | unknown |
668 | chrome.exe | GET | 200 | 172.217.18.1:80 | http://darkweb999.blogspot.com/feeds/posts/default?alt=json-in-script&callback=authorshow | unknown | binary | 26.5 Kb | unknown |
668 | chrome.exe | GET | 301 | 157.240.251.9:80 | http://connect.facebook.net/en_US/all.js | unknown | — | — | unknown |
668 | chrome.exe | GET | 200 | 172.217.16.202:80 | http://ajax.googleapis.com/ajax/libs/jquery/1/jquery.min.js | unknown | text | 93.5 Kb | unknown |
668 | chrome.exe | GET | 200 | 142.250.184.225:80 | http://4.bp.blogspot.com/-R8OKVUsis3s/UgZEksy0V1I/AAAAAAAAAT4/QtN9sBHMZis/s1600/icon-search.png | unknown | image | 953 b | unknown |
668 | chrome.exe | GET | 200 | 142.250.184.225:80 | http://4.bp.blogspot.com/-M_utSb-nN04/U6V8Gut9dJI/AAAAAAAAAjE/6g1X58pjjcg/s1600/single-share.png | unknown | image | 1.11 Kb | unknown |
668 | chrome.exe | GET | 200 | 142.250.184.233:80 | http://www.blogger.com/img/blogger_logo_round_35.png | unknown | image | 2.47 Kb | unknown |
668 | chrome.exe | GET | 200 | 172.217.18.1:80 | http://darkweb999.blogspot.com/js/cookienotice.js | unknown | text | 1.98 Kb | unknown |
668 | chrome.exe | GET | 200 | 142.250.186.161:80 | http://2.bp.blogspot.com/-YxxeRcqP6UI/U6V7A_pfmnI/AAAAAAAAAik/NyzEC4z7POQ/s1600/menu-bg2.png | unknown | image | 212 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
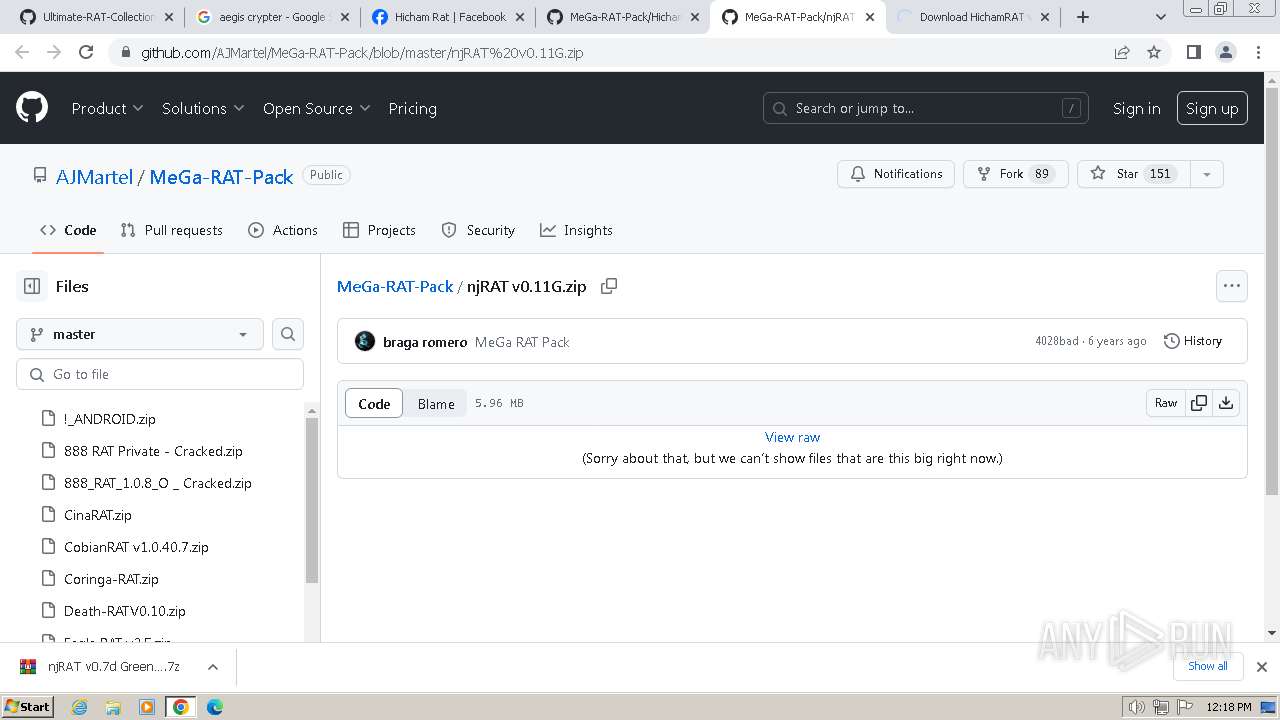
668 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
532 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
668 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
668 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | unknown |
668 | chrome.exe | 142.250.186.106:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
668 | chrome.exe | 185.199.108.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
668 | chrome.exe | 216.58.212.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
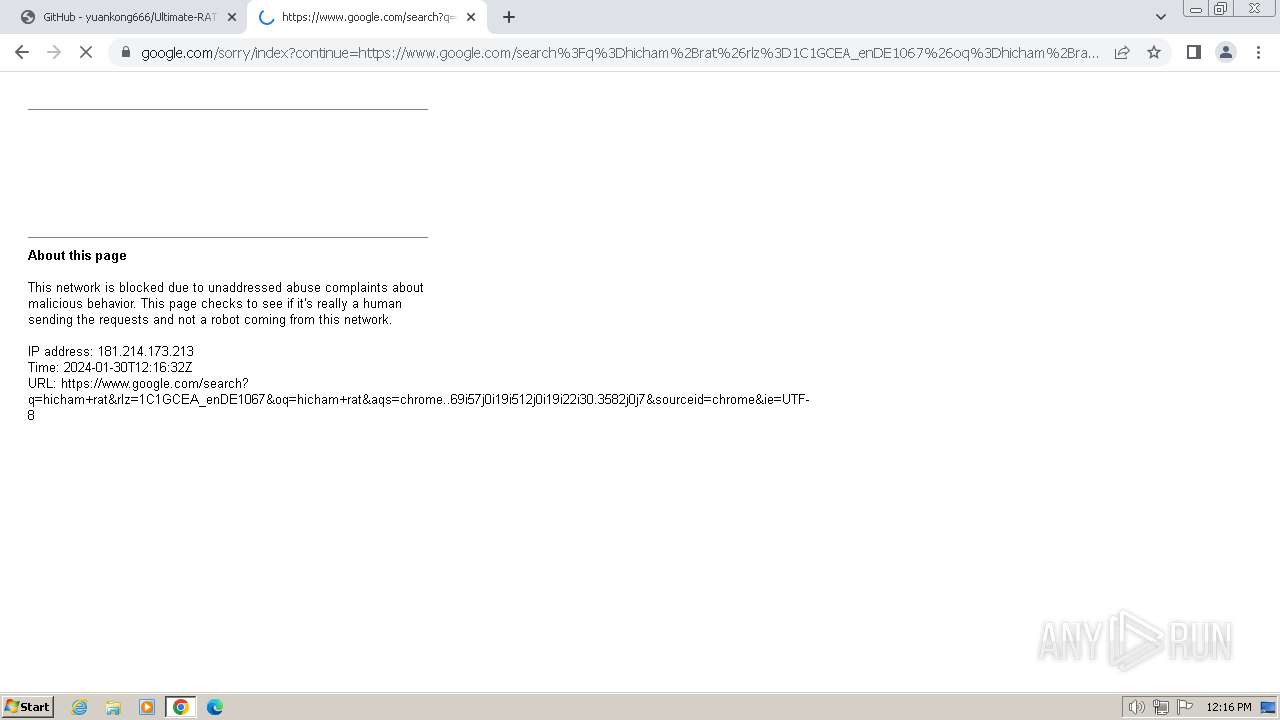
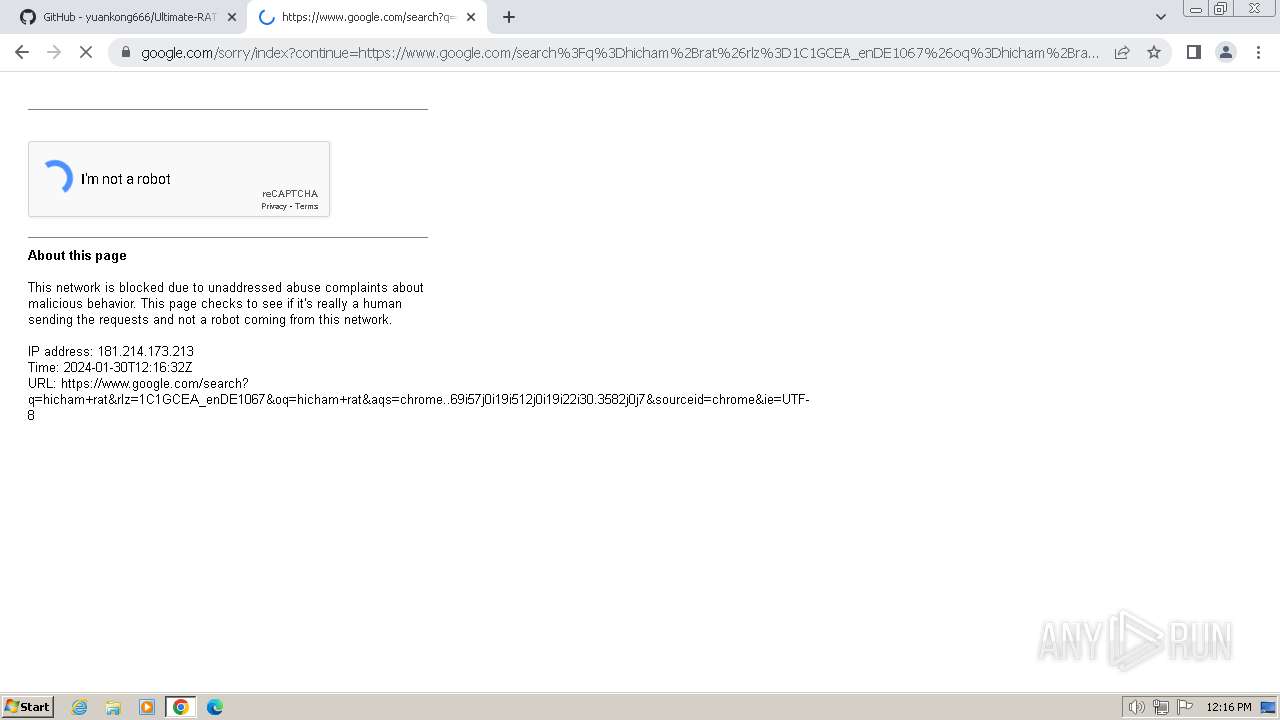
668 | chrome.exe | Misc activity | ET HUNTING [TW] Likely Javascript-Obfuscator Usage Observed M1 |
668 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
668 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
668 | chrome.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
668 | chrome.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |