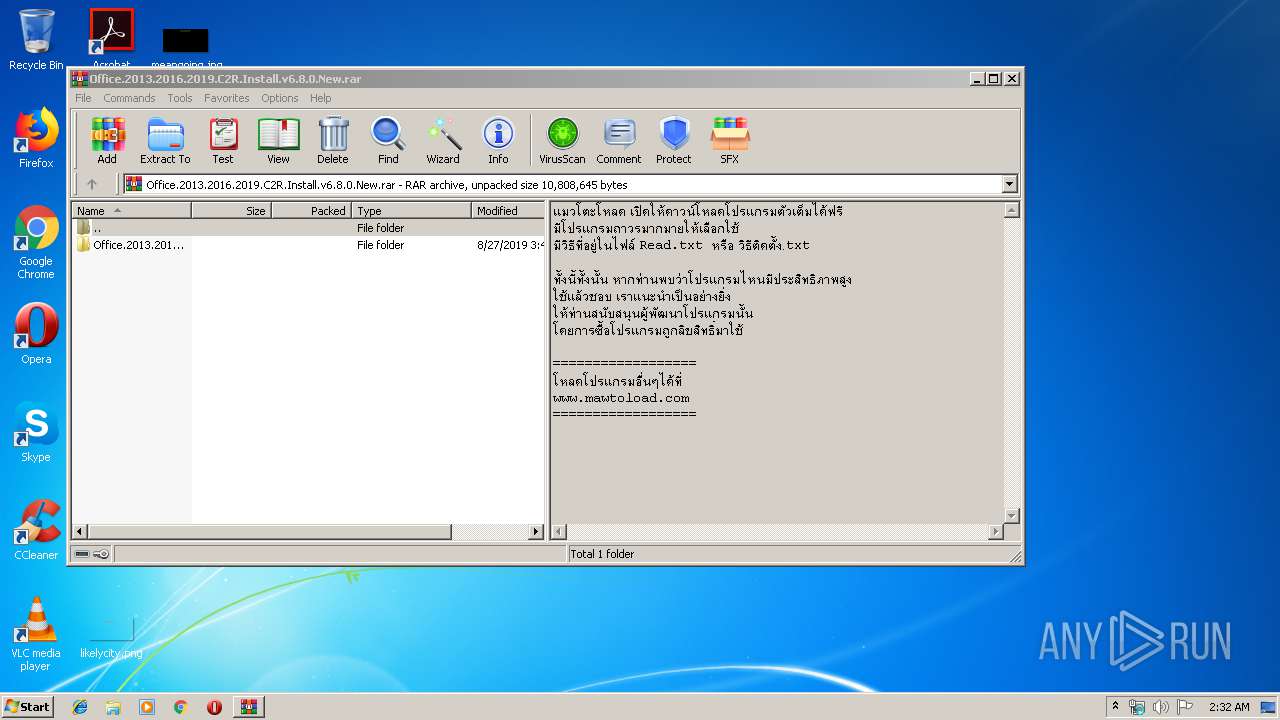
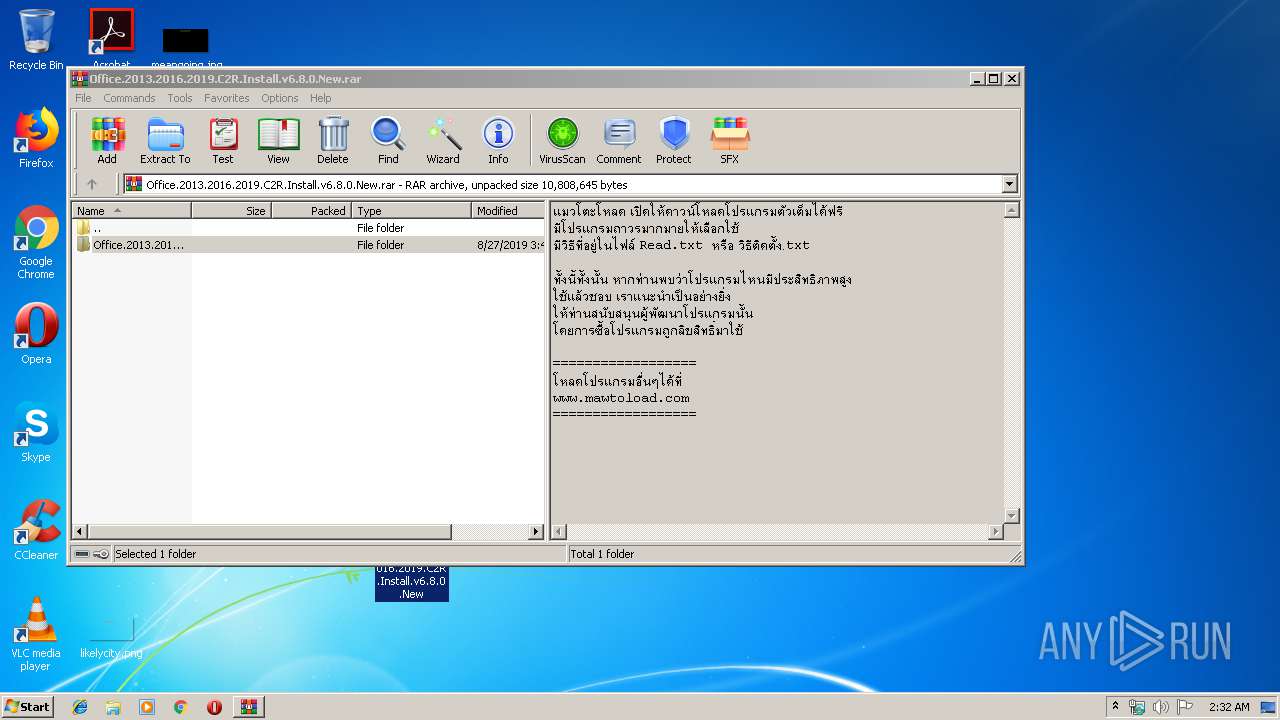
| File name: | Office.2013.2016.2019.C2R.Install.v6.8.0.New.rar |
| Full analysis: | https://app.any.run/tasks/b691b0fe-4ba3-46a7-ae18-5d4acc2948a6 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 01:31:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 4B961C3E9426BBE283595E07C539CA41 |
| SHA1: | 6D9F9D73C92A1E6FCA4FCF2D9B464ADC17C30FDC |
| SHA256: | 7AB73E695C5D23BEC15E5201FBF9E4A5921C656BD2687F60BCD862CF95ED6959 |
| SSDEEP: | 196608:JD+fvvy/VL/jFdH46bmE09zbIYkULTtU6wGG35IVLK1gS/8FaMdeFonZLzQj+AWZ:h8c7YfE09cYZLTuaG35EK17/8F9hLk+x |
MALICIOUS
Application was dropped or rewritten from another process
- files.dat (PID: 3472)
- setup.exe (PID: 3376)
- OfficeC2RClient.exe (PID: 3576)
- OfficeClickToRun.exe (PID: 3896)
- OfficeClickToRun.exe (PID: 3080)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 848)
- OfficeClickToRun.exe (PID: 3896)
- OfficeC2RClient.exe (PID: 3576)
- OfficeClickToRun.exe (PID: 3080)
Changes settings of System certificates
- setup.exe (PID: 3376)
- OfficeClickToRun.exe (PID: 3080)
SUSPICIOUS
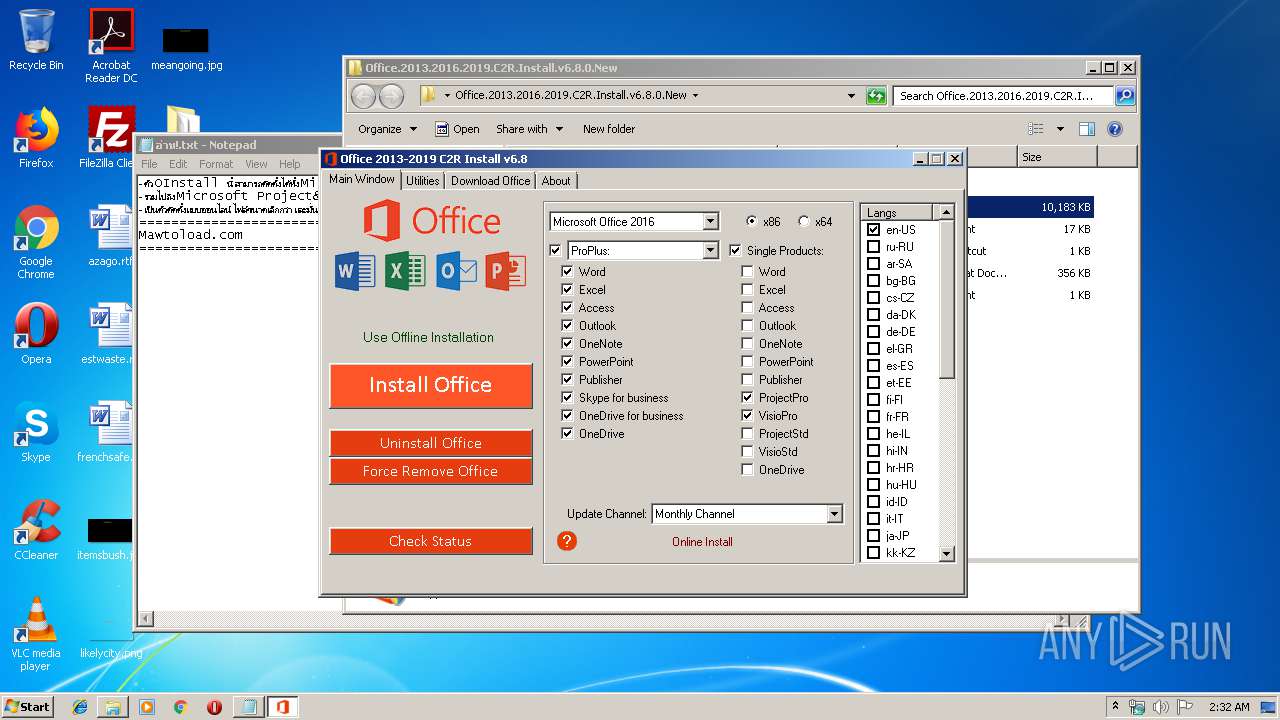
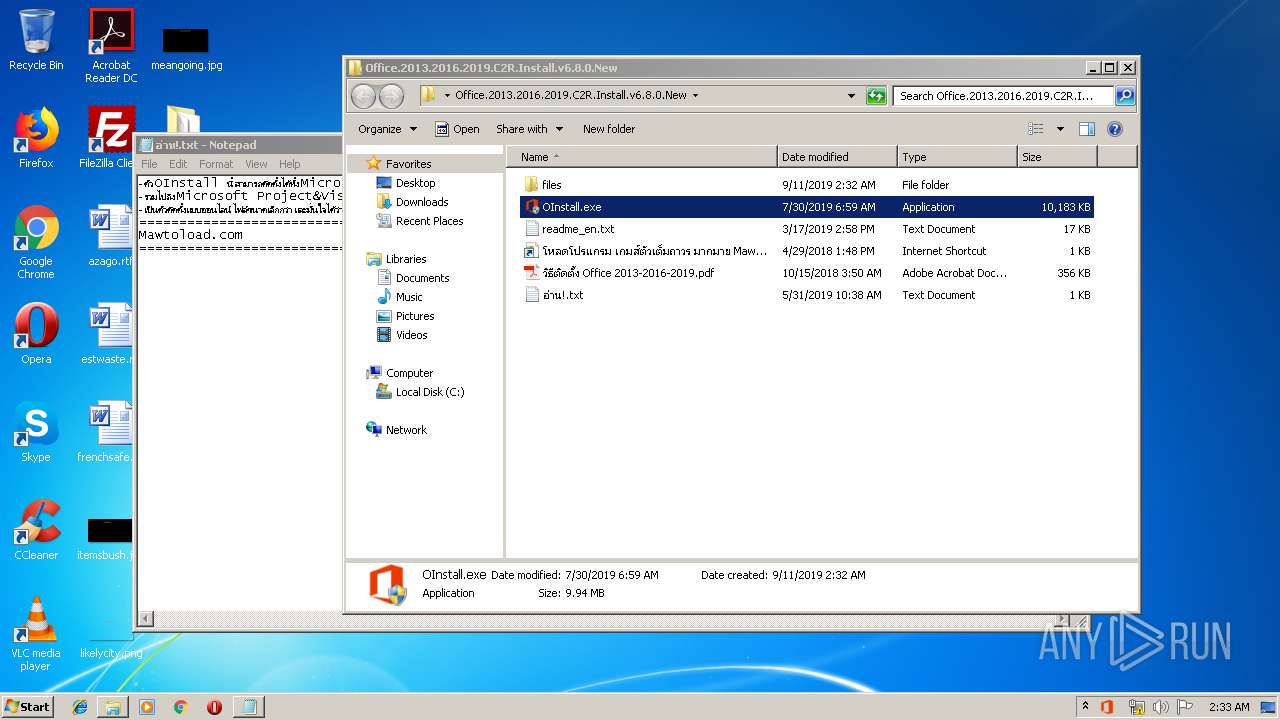
Executable content was dropped or overwritten
- OInstall.exe (PID: 3032)
- files.dat (PID: 3472)
- setup.exe (PID: 3376)
- OfficeClickToRun.exe (PID: 3080)
Starts application with an unusual extension
- cmd.exe (PID: 3144)
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 3032)
Reads Internet Cache Settings
- setup.exe (PID: 3376)
- OfficeClickToRun.exe (PID: 3896)
- OfficeC2RClient.exe (PID: 3576)
Adds / modifies Windows certificates
- setup.exe (PID: 3376)
- OfficeClickToRun.exe (PID: 3080)
Searches for installed software
- setup.exe (PID: 3376)
Executes PowerShell scripts
- setup.exe (PID: 3376)
Creates files in the user directory
- powershell.exe (PID: 2660)
Executed as Windows Service
- OfficeClickToRun.exe (PID: 3080)
Removes files from Windows directory
- OfficeClickToRun.exe (PID: 3080)
Creates files in the program directory
- setup.exe (PID: 3376)
- OfficeClickToRun.exe (PID: 3080)
Creates files in the Windows directory
- OfficeClickToRun.exe (PID: 3080)
INFO
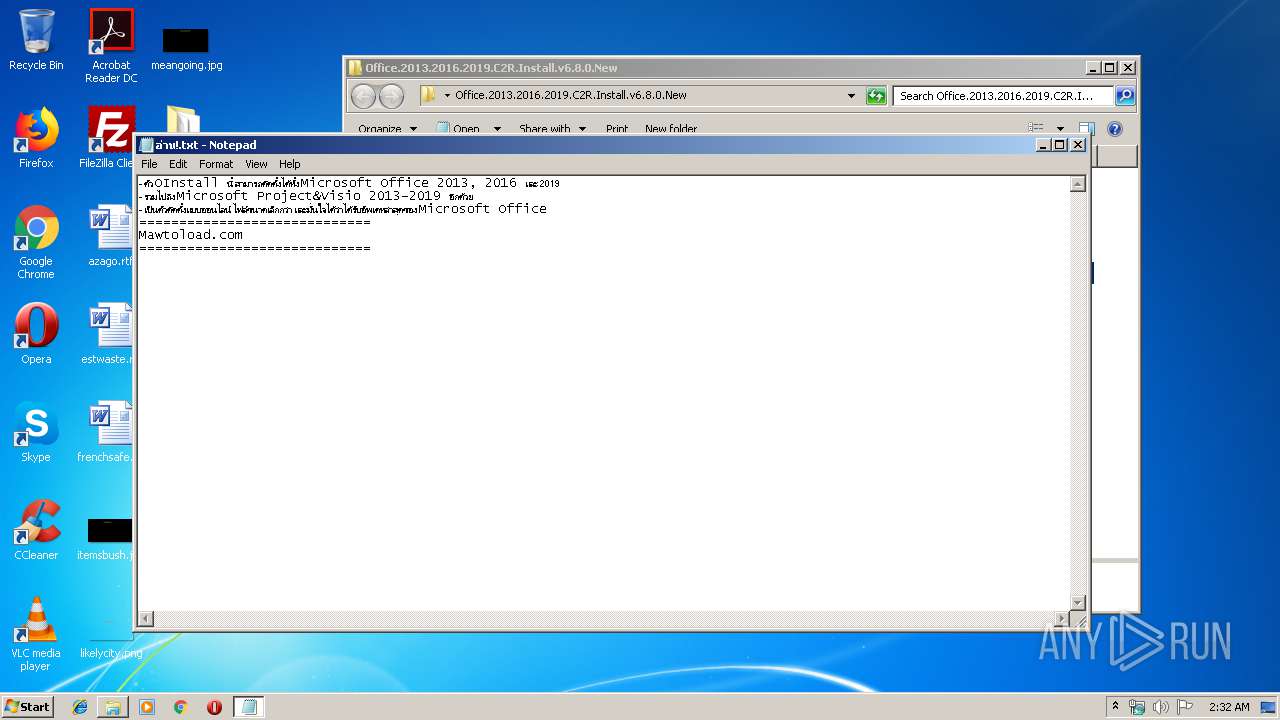
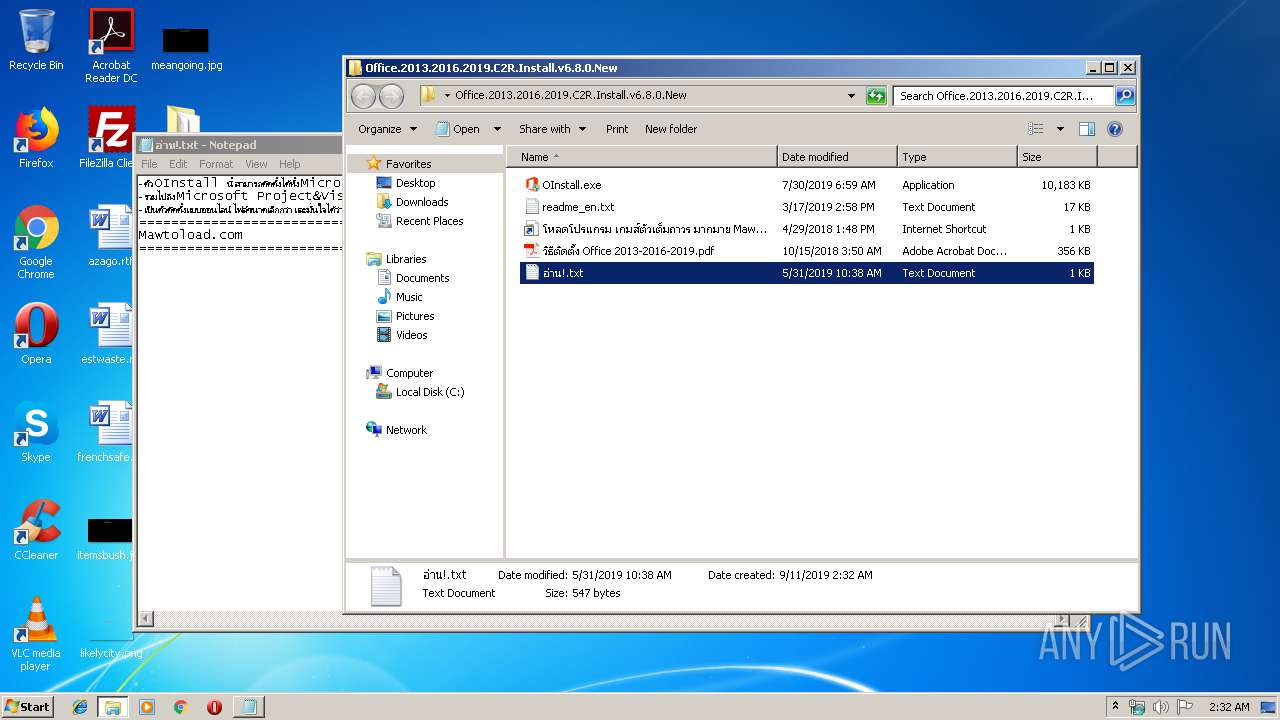
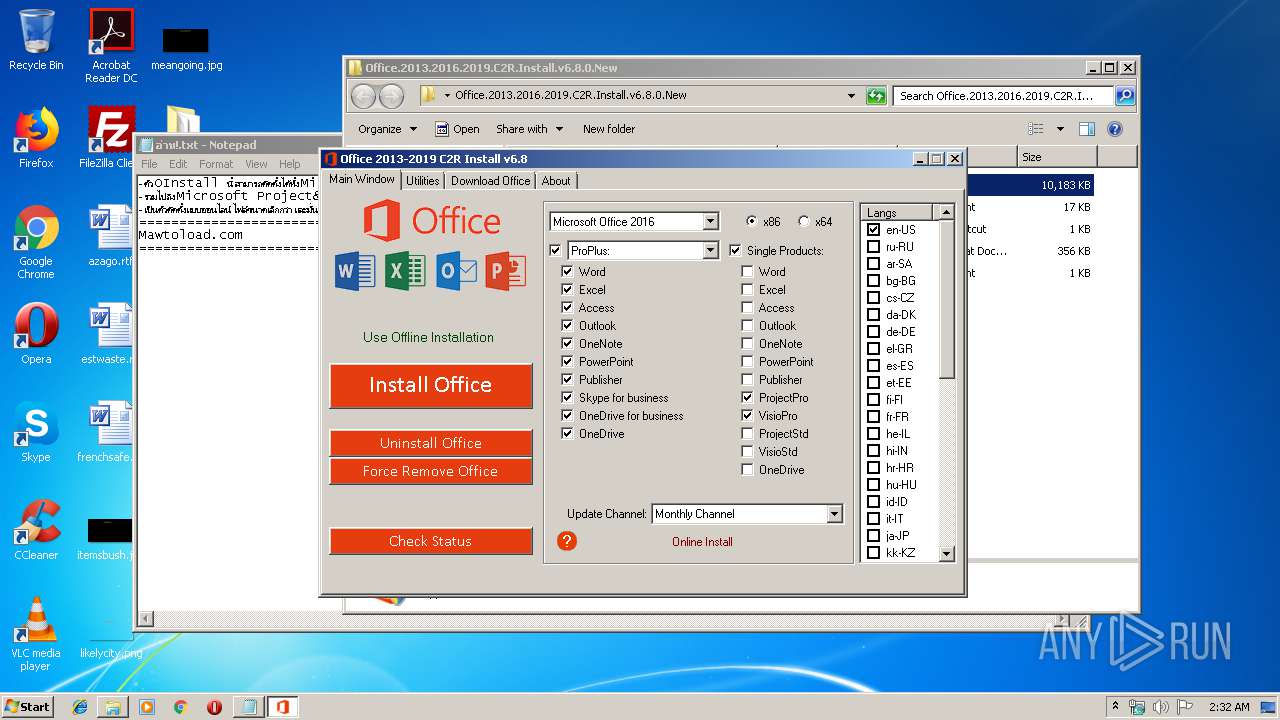
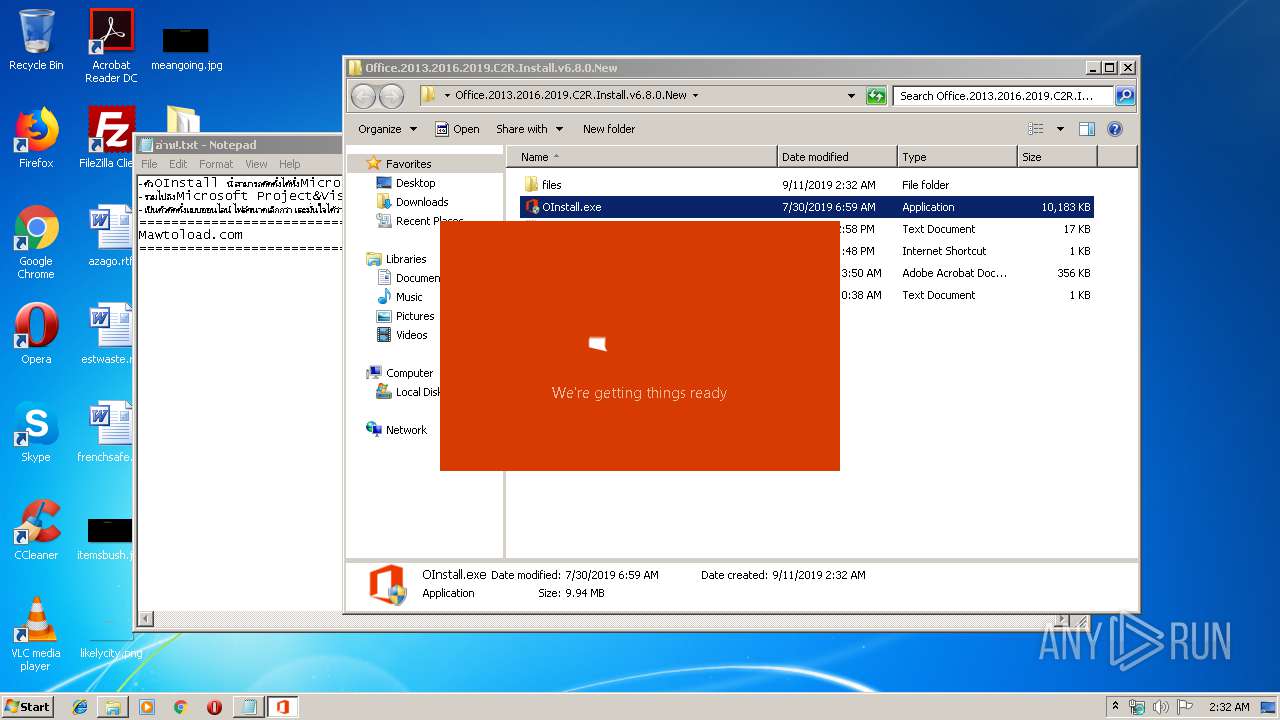
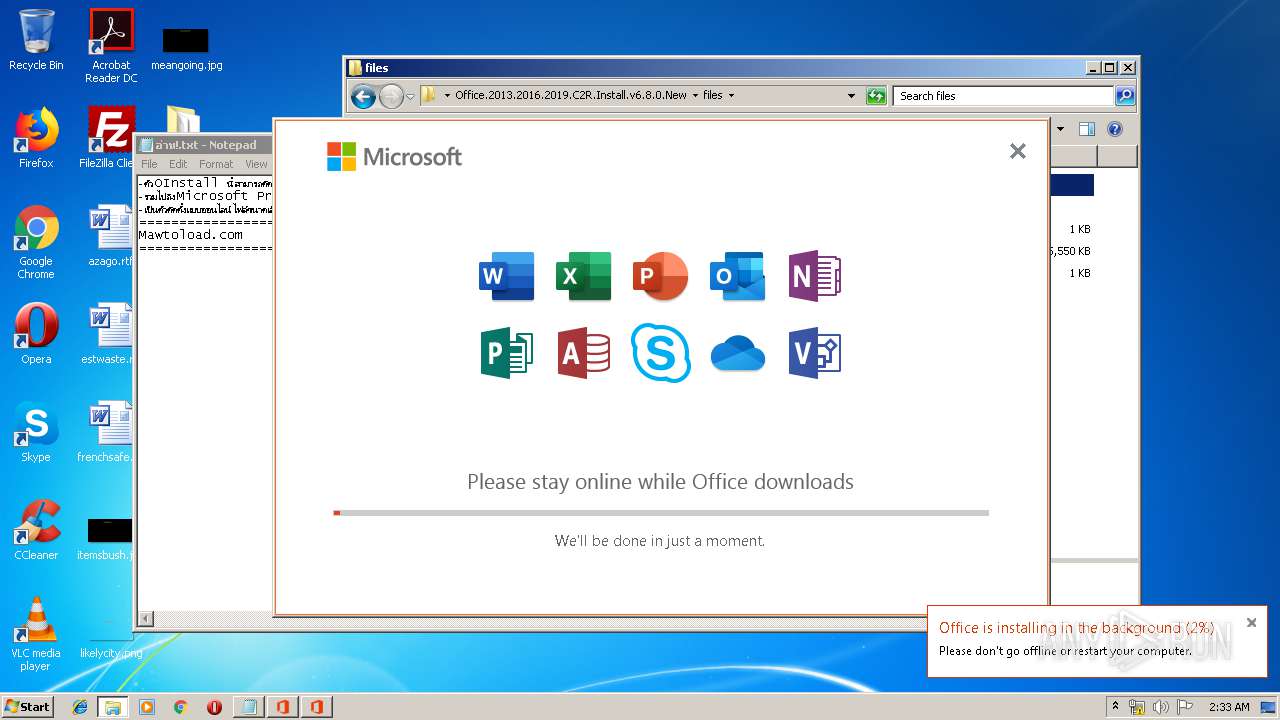
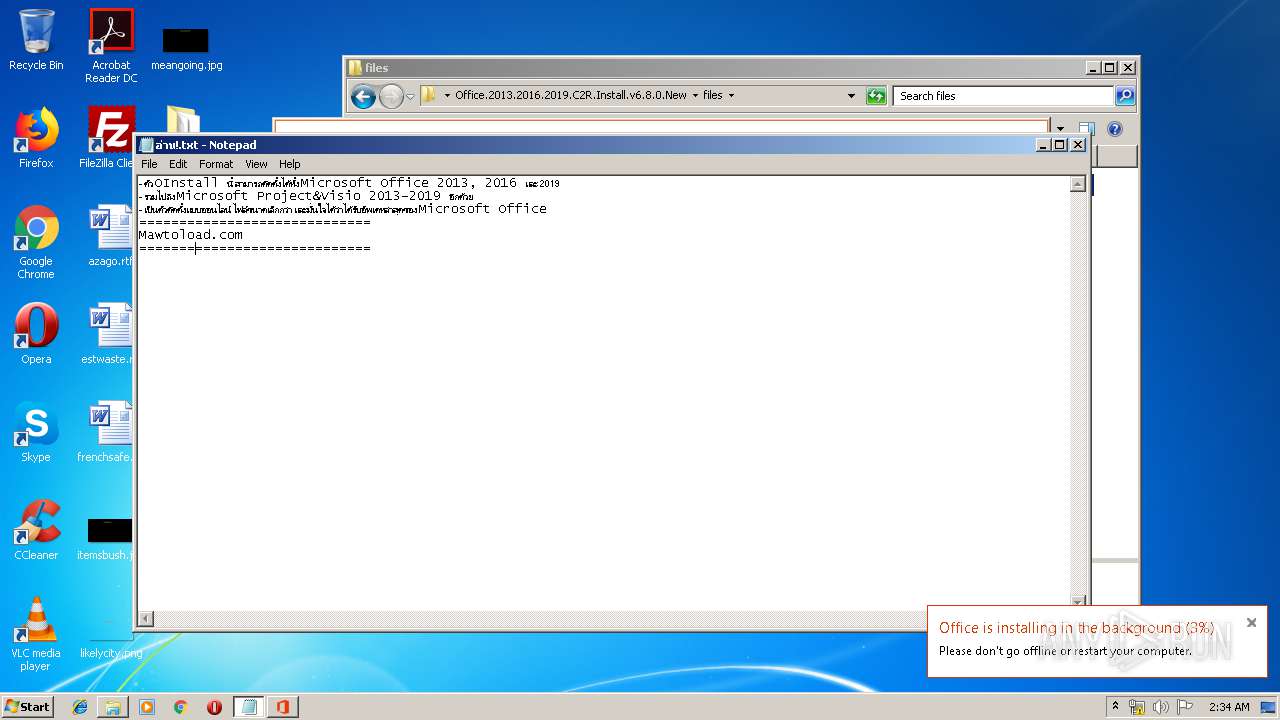
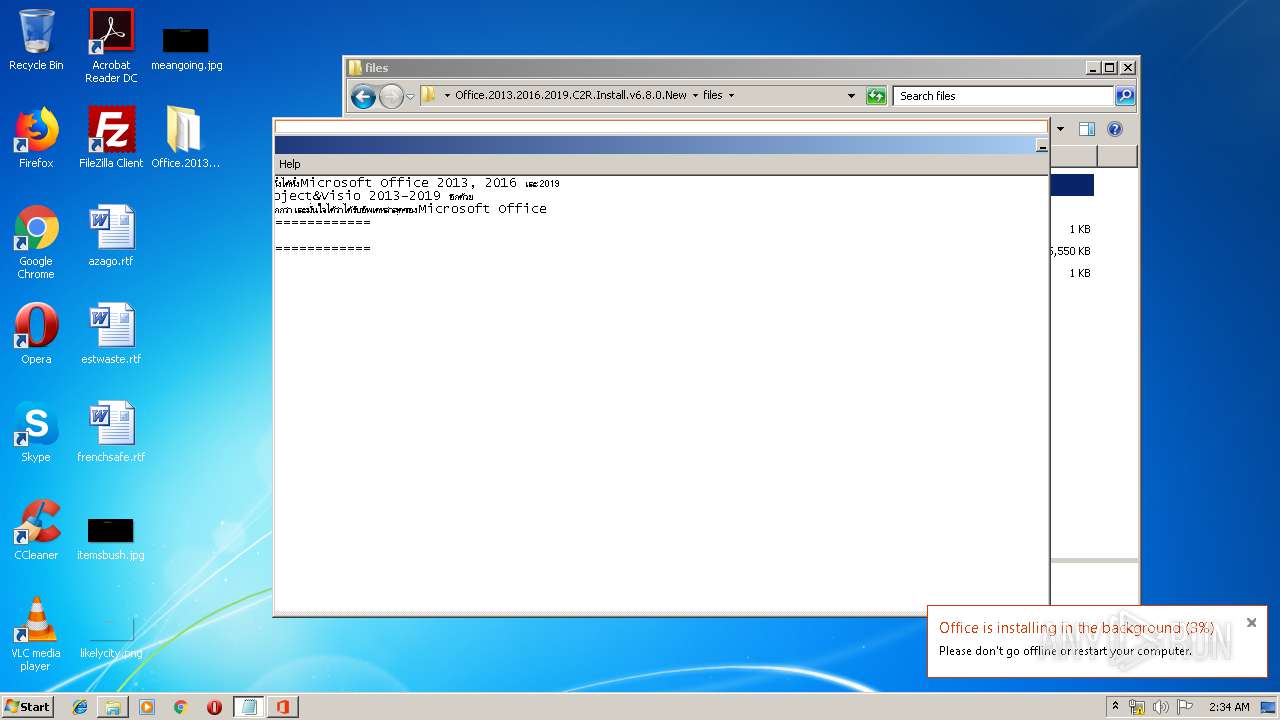
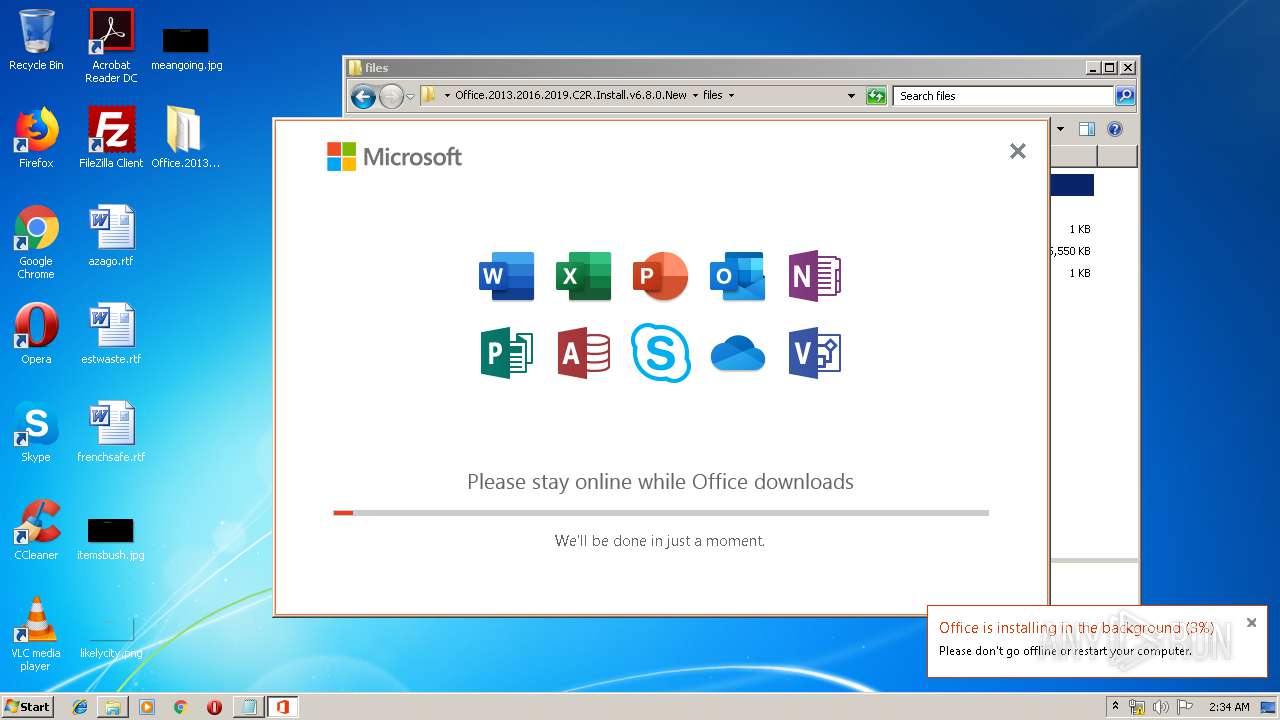
Manual execution by user
- NOTEPAD.EXE (PID: 3960)
- OInstall.exe (PID: 2144)
- OInstall.exe (PID: 3032)
- OfficeC2RClient.exe (PID: 3576)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 3896)
- OfficeC2RClient.exe (PID: 3576)
- OfficeClickToRun.exe (PID: 3080)
Reads settings of System Certificates
- OfficeClickToRun.exe (PID: 3080)
- OfficeC2RClient.exe (PID: 3576)
Dropped object may contain Bitcoin addresses
- OfficeClickToRun.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
58
Monitored processes
14
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2144 | "C:\Users\admin\Desktop\Office.2013.2016.2019.C2R.Install.v6.8.0.New\OInstall.exe" | C:\Users\admin\Desktop\Office.2013.2016.2019.C2R.Install.v6.8.0.New\OInstall.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Office 2013-2016 C2R Install Exit code: 3221226540 Modules
| |||||||||||||||
| 2436 | "C:\Windows\System32\cmd.exe" /D /c copy C:\Windows\system32\Tasks\OInstall "C:\Windows\Temp\OInstall.tmp" /Y | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
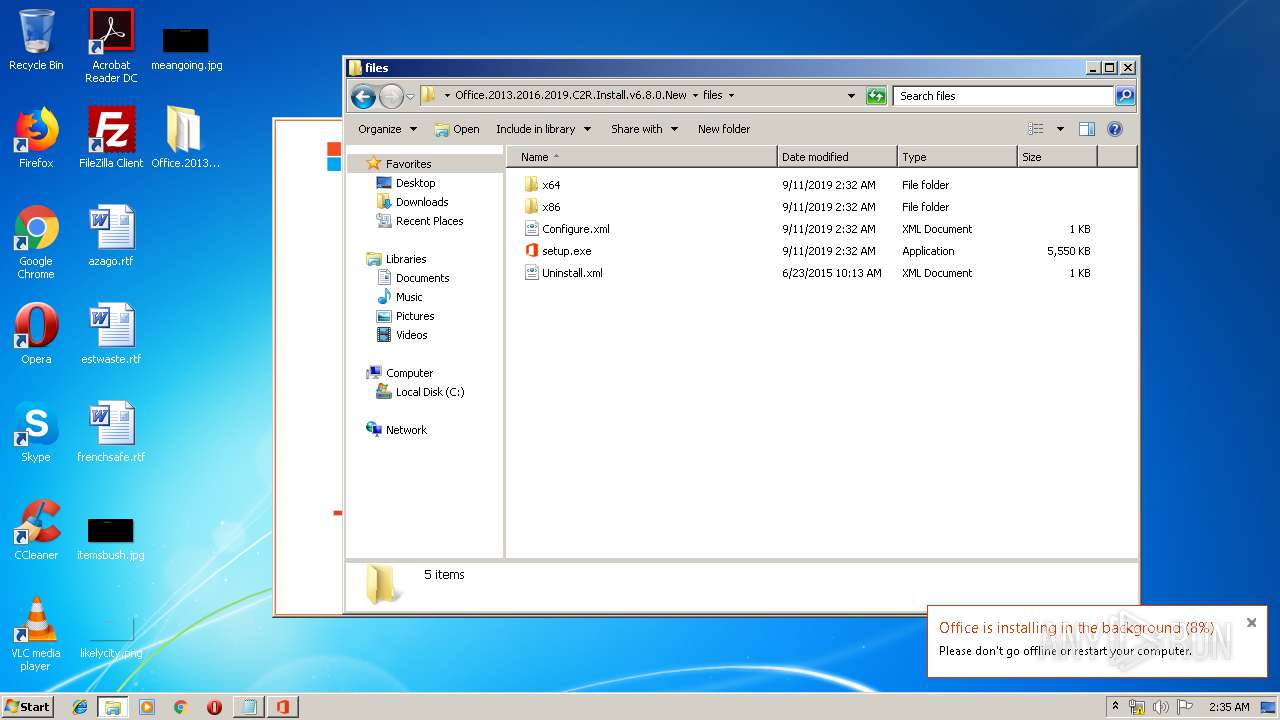
| 2628 | "C:\Windows\System32\cmd.exe" /D /c C:\Users\admin\Desktop\OFFICE~1.NEW\files\Setup.exe /configure Configure.xml | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2660 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile "$package = Get-AppxPackage Microsoft.Office.Desktop -allUsers; if (!$package) { $Error.Add(\"Package is not installed\")}; if ($error.Count -eq 0) { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '1' -Encoding ascii; } else { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '0' -Encoding ascii; Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch' -InputObject $error -Encoding ascii;} " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | "C:\Users\admin\Desktop\Office.2013.2016.2019.C2R.Install.v6.8.0.New\OInstall.exe" | C:\Users\admin\Desktop\Office.2013.2016.2019.C2R.Install.v6.8.0.New\OInstall.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Office 2013-2016 C2R Install Exit code: 0 Modules
| |||||||||||||||
| 3080 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe" /service | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run (SxS) Exit code: 0 Version: 16.0.11929.20298 Modules
| |||||||||||||||
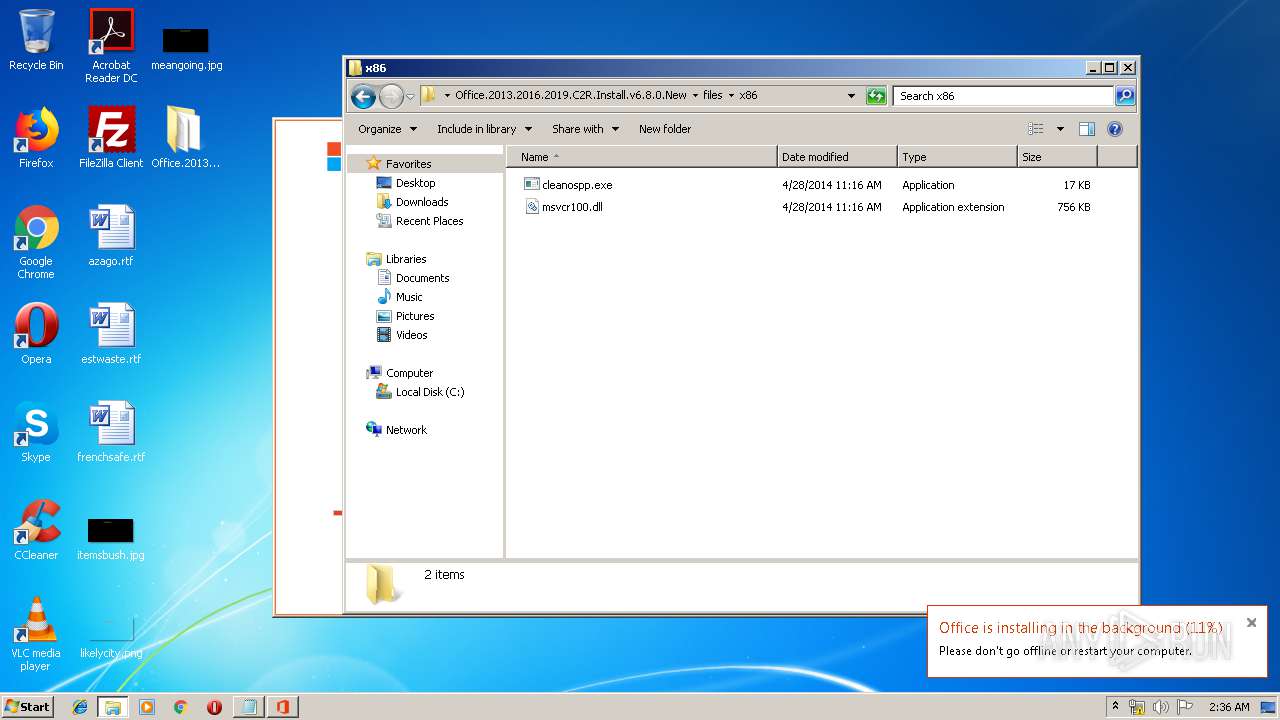
| 3144 | "C:\Windows\System32\cmd.exe" /D /c files.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3376 | C:\Users\admin\Desktop\OFFICE~1.NEW\files\Setup.exe /configure Configure.xml | C:\Users\admin\Desktop\OFFICE~1.NEW\files\setup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Exit code: 0 Version: 16.0.11901.20000 Modules
| |||||||||||||||
| 3472 | files.dat -y -pkmsauto | C:\Users\admin\Desktop\Office.2013.2016.2019.C2R.Install.v6.8.0.New\files\files.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 514
Read events
2 146
Write events
366
Delete events
2
Modification events
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Office.2013.2016.2019.C2R.Install.v6.8.0.New.rar | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (848) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (848) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-10046 |
Value: Internet Shortcut | |||
Executable files
353
Suspicious files
112
Text files
272
Unknown types
95
Dropped files
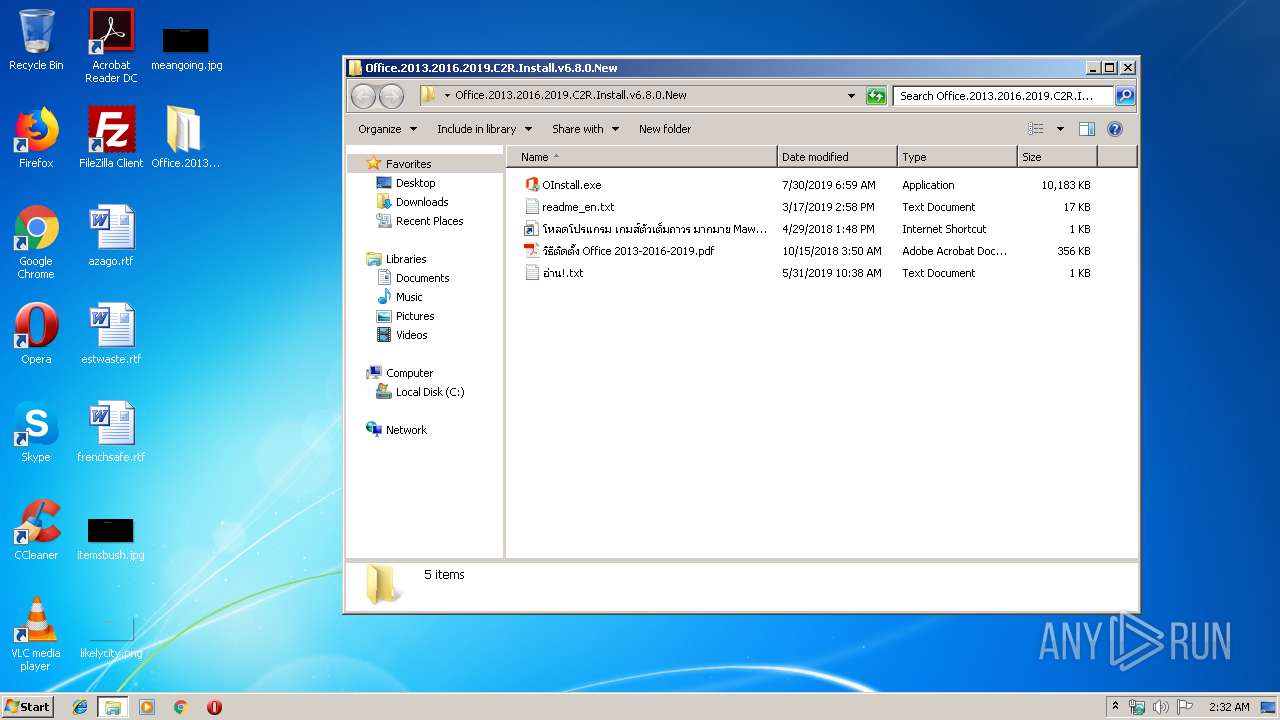
PID | Process | Filename | Type | |
|---|---|---|---|---|
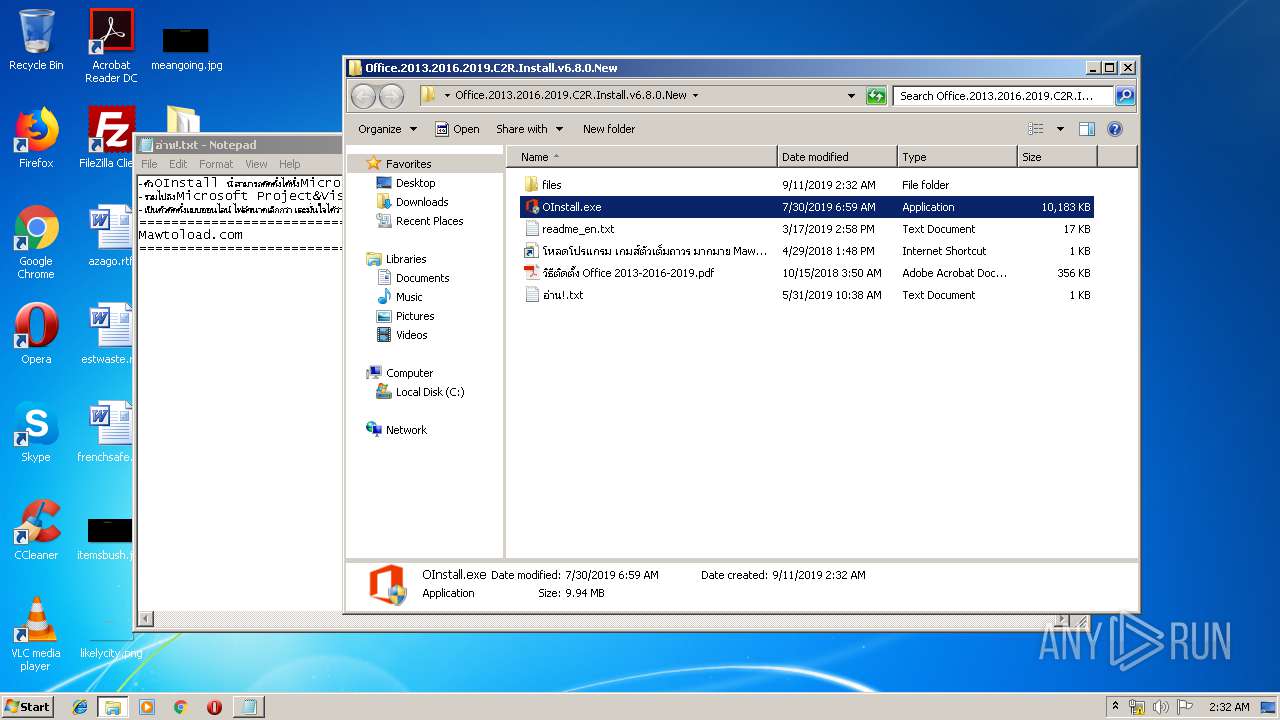
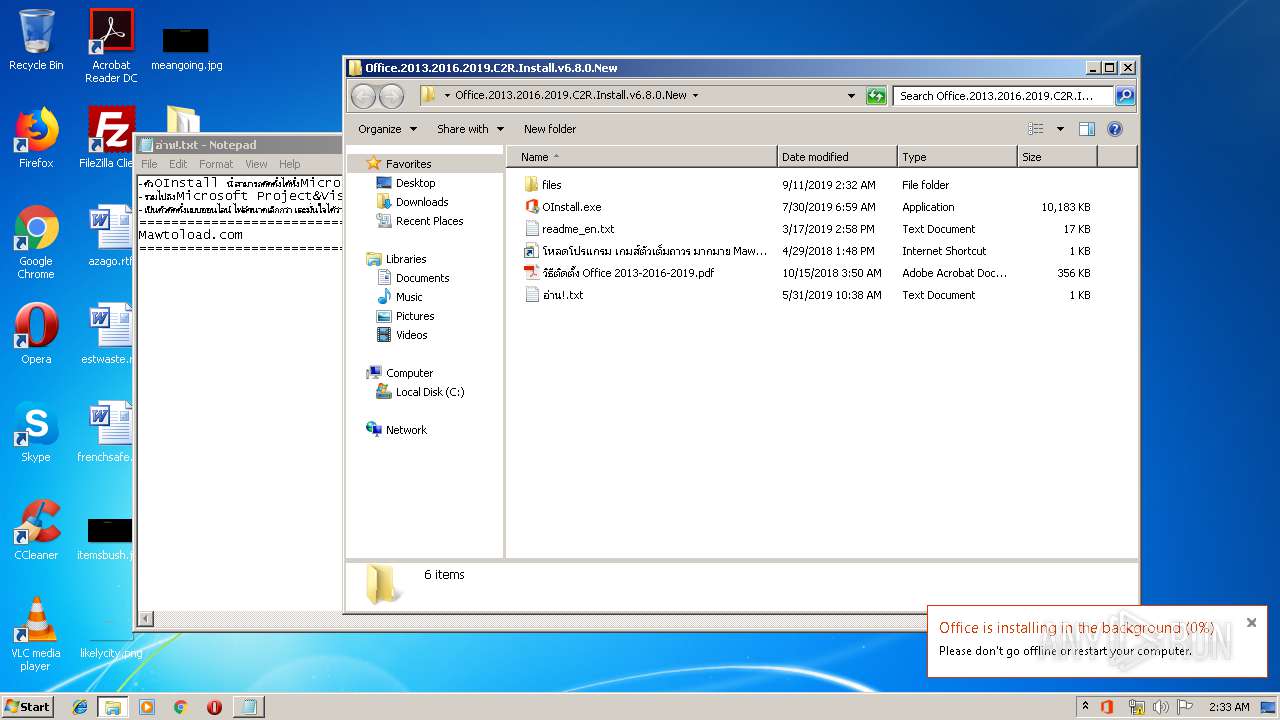
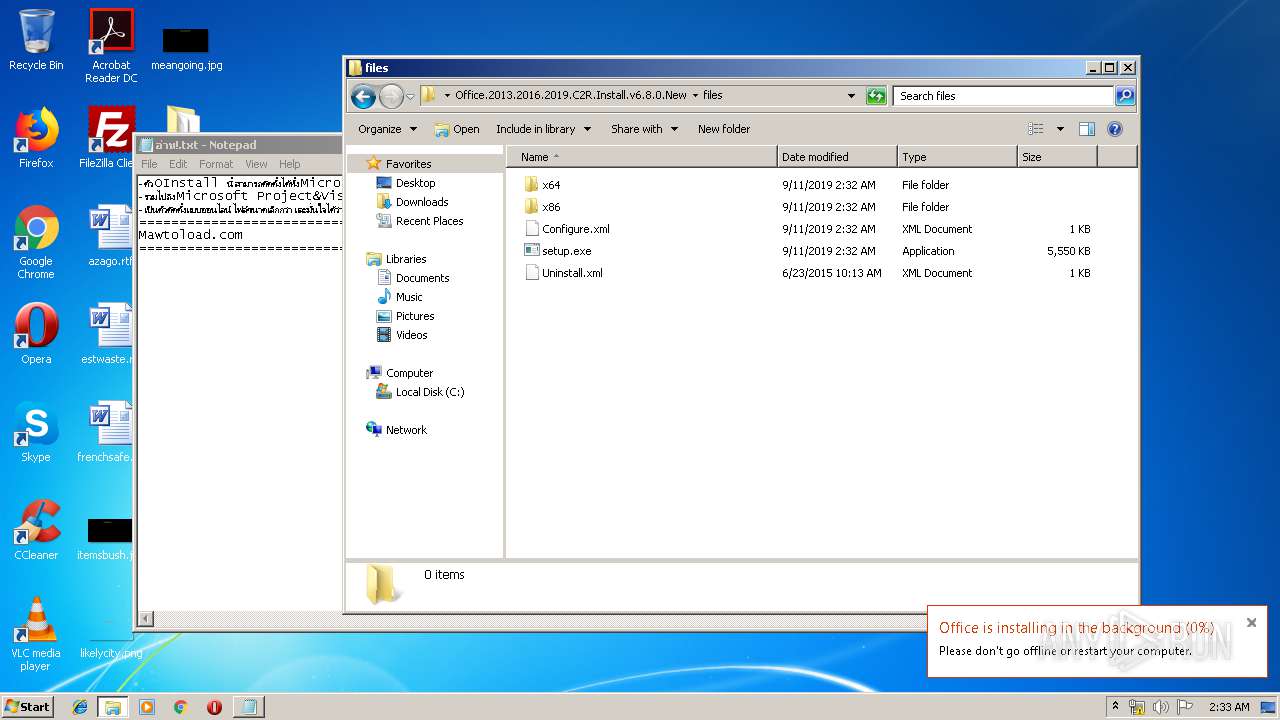
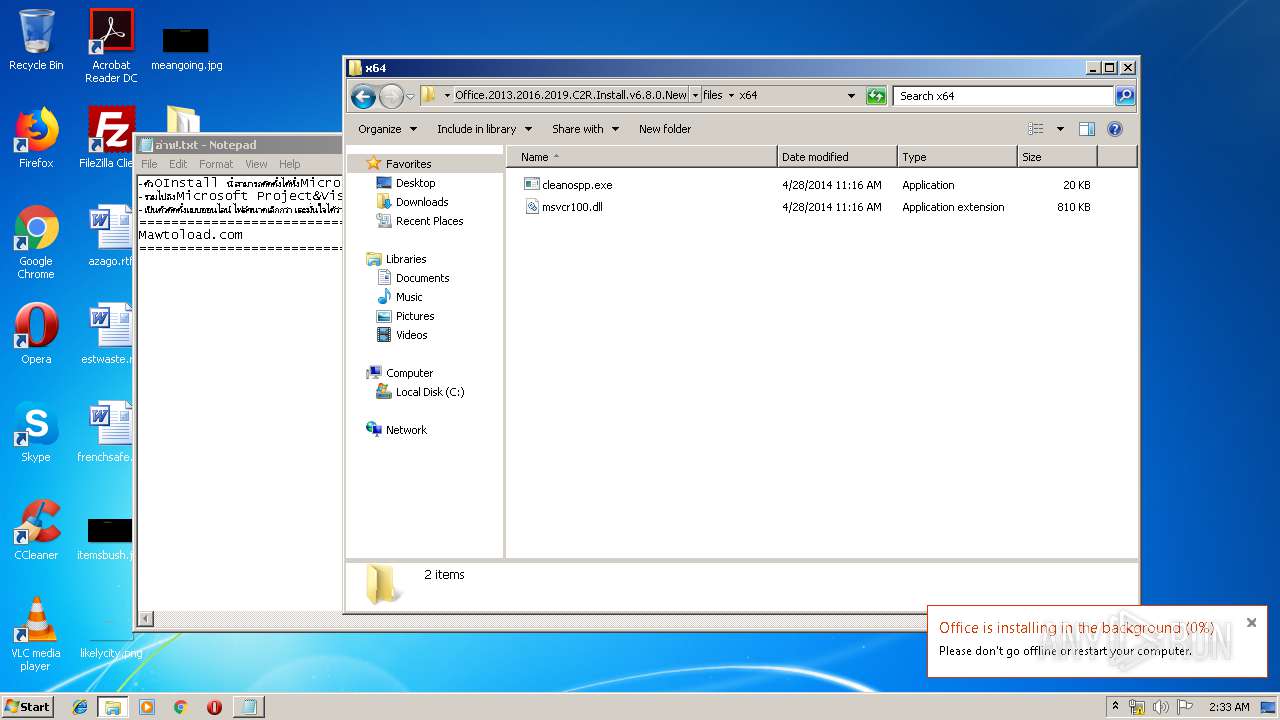
| 3804 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3804.2814\Office.2013.2016.2019.C2R.Install.v6.8.0.New\OInstall.exe | — | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3804.2814\Office.2013.2016.2019.C2R.Install.v6.8.0.New\readme_en.txt | — | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3804.2814\Office.2013.2016.2019.C2R.Install.v6.8.0.New\วิธีติดตั้ง Office 2013-2016-2019.pdf | — | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3804.2814\Office.2013.2016.2019.C2R.Install.v6.8.0.New\อ่าน!.txt | — | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3804.2814\Office.2013.2016.2019.C2R.Install.v6.8.0.New\โหลดโปรแกรม เกมส์ตัวเต็มถาวร มากมาย MawtoLoad.url | — | |
MD5:— | SHA256:— | |||
| 3376 | setup.exe | C:\Users\admin\AppData\Local\Temp\Cab58CE.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | setup.exe | C:\Users\admin\AppData\Local\Temp\Tar58CF.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R0C68C002-3D3D-44B8-91CF-3B59AC045491OfficeC2R1F97B5EB-A4E0-4522-A4BF-35369BA4CEA8\v32.hash | — | |
MD5:— | SHA256:— | |||
| 3376 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R0C68C002-3D3D-44B8-91CF-3B59AC045491OfficeC2R1F97B5EB-A4E0-4522-A4BF-35369BA4CEA8\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 3376 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R0C68C002-3D3D-44B8-91CF-3B59AC045491\v32.hash | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
489
TCP/UDP connections
12
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3080 | OfficeClickToRun.exe | HEAD | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11929.20300/s321033.cab | US | — | — | whitelisted |
3080 | OfficeClickToRun.exe | HEAD | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11929.20300/s321033.cab | US | — | — | whitelisted |
3376 | setup.exe | HEAD | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11929.20300.cab | US | — | — | whitelisted |
3376 | setup.exe | HEAD | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11929.20300.cab | US | — | — | whitelisted |
3376 | setup.exe | GET | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11929.20300/i320.cab | US | compressed | 20.2 Mb | whitelisted |
3080 | OfficeClickToRun.exe | GET | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11929.20300/s321033.cab | US | compressed | 1.10 Mb | whitelisted |
3376 | setup.exe | HEAD | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11929.20300/i320.cab | US | compressed | 16.8 Kb | whitelisted |
3080 | OfficeClickToRun.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
3080 | OfficeClickToRun.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
3080 | OfficeClickToRun.exe | HEAD | 200 | 204.79.197.223:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11929.20300/s320.cab | US | compressed | 1.10 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | setup.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3376 | setup.exe | 52.109.76.40:443 | mrodevicemgr.officeapps.live.com | Microsoft Corporation | IE | suspicious |
3376 | setup.exe | 204.79.197.223:80 | officecdn.microsoft.com | Microsoft Corporation | US | suspicious |
3376 | setup.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3896 | OfficeClickToRun.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3080 | OfficeClickToRun.exe | 204.79.197.223:80 | officecdn.microsoft.com | Microsoft Corporation | US | suspicious |
3080 | OfficeClickToRun.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3080 | OfficeClickToRun.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3080 | OfficeClickToRun.exe | 52.114.76.37:443 | self.events.data.microsoft.com | Microsoft Corporation | IE | unknown |
3080 | OfficeClickToRun.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
mrodevicemgr.officeapps.live.com |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |