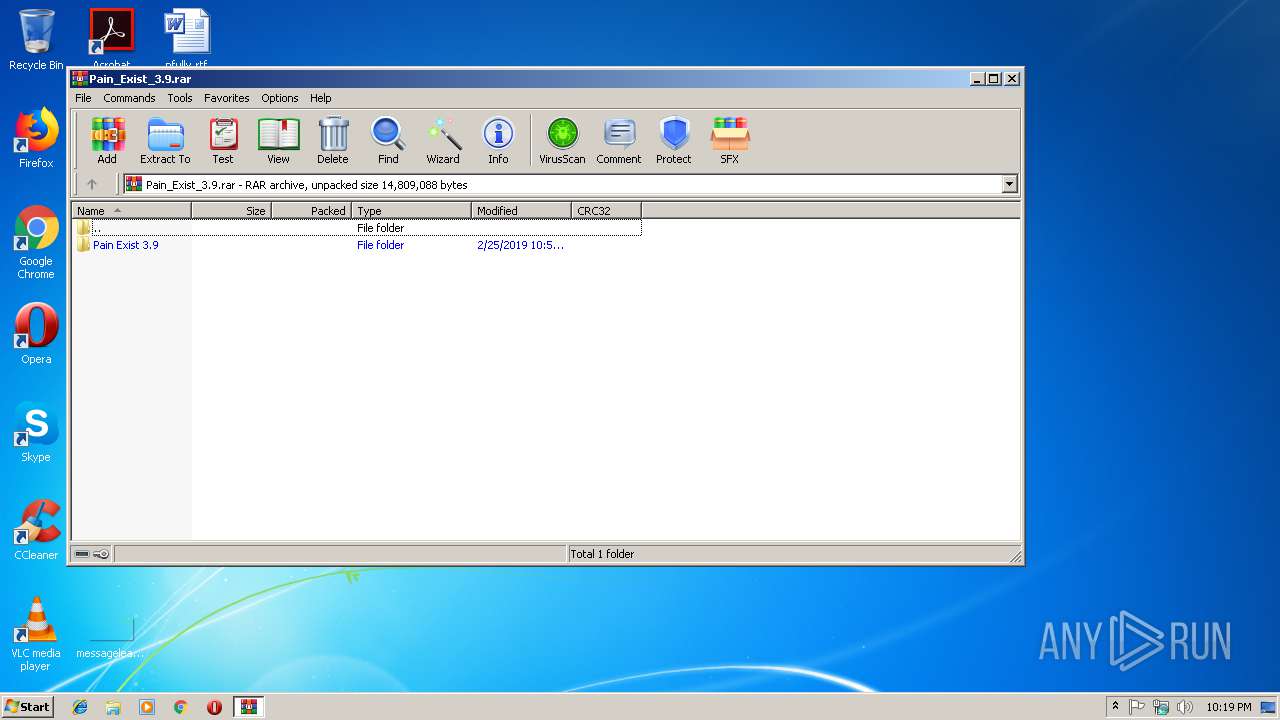
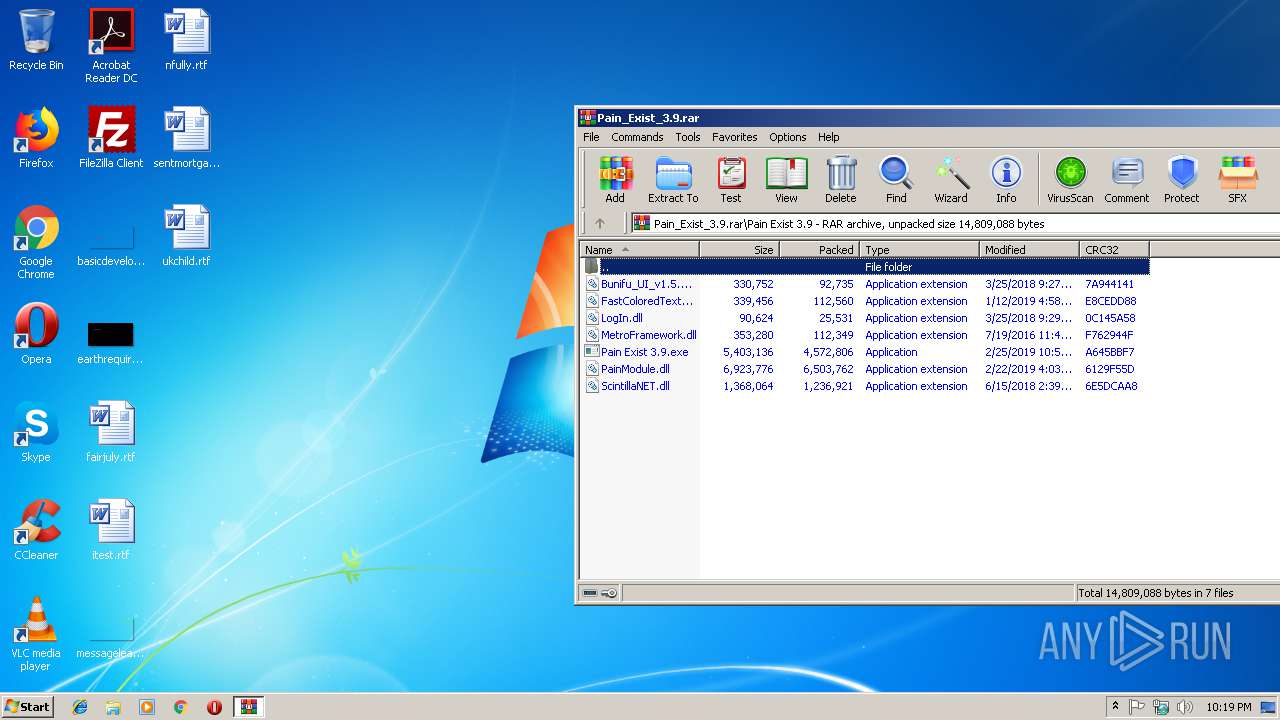
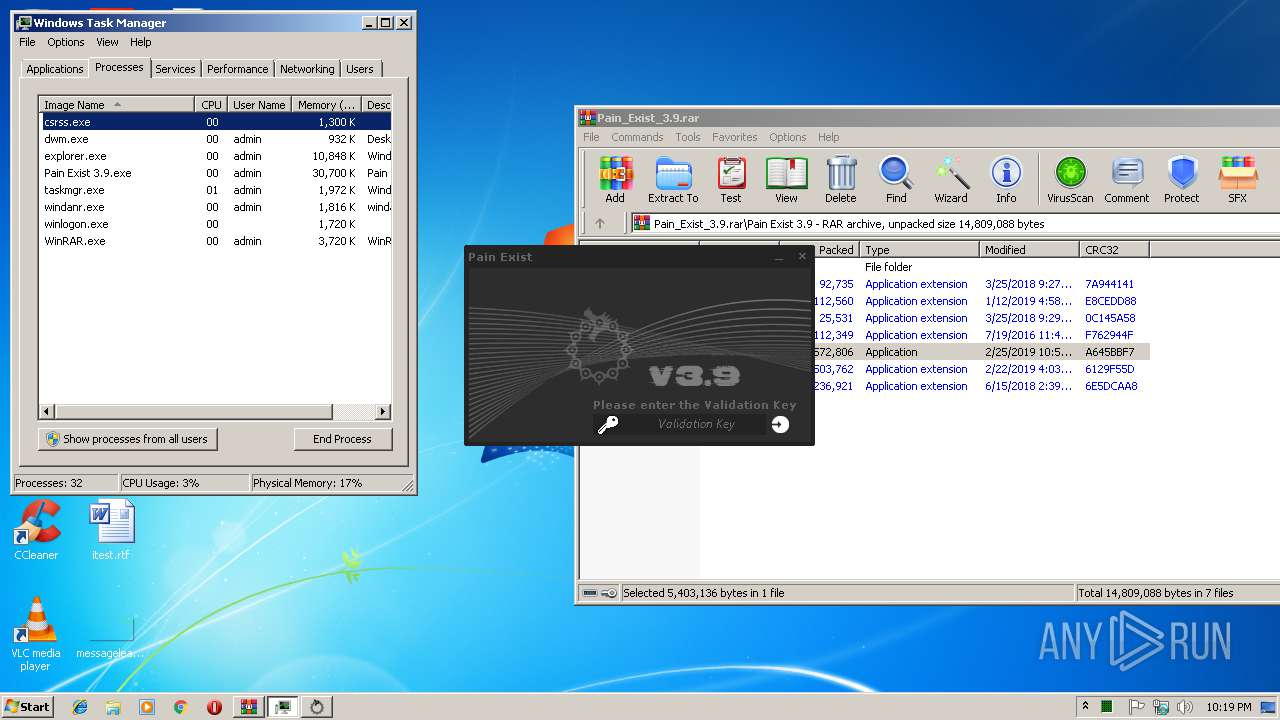
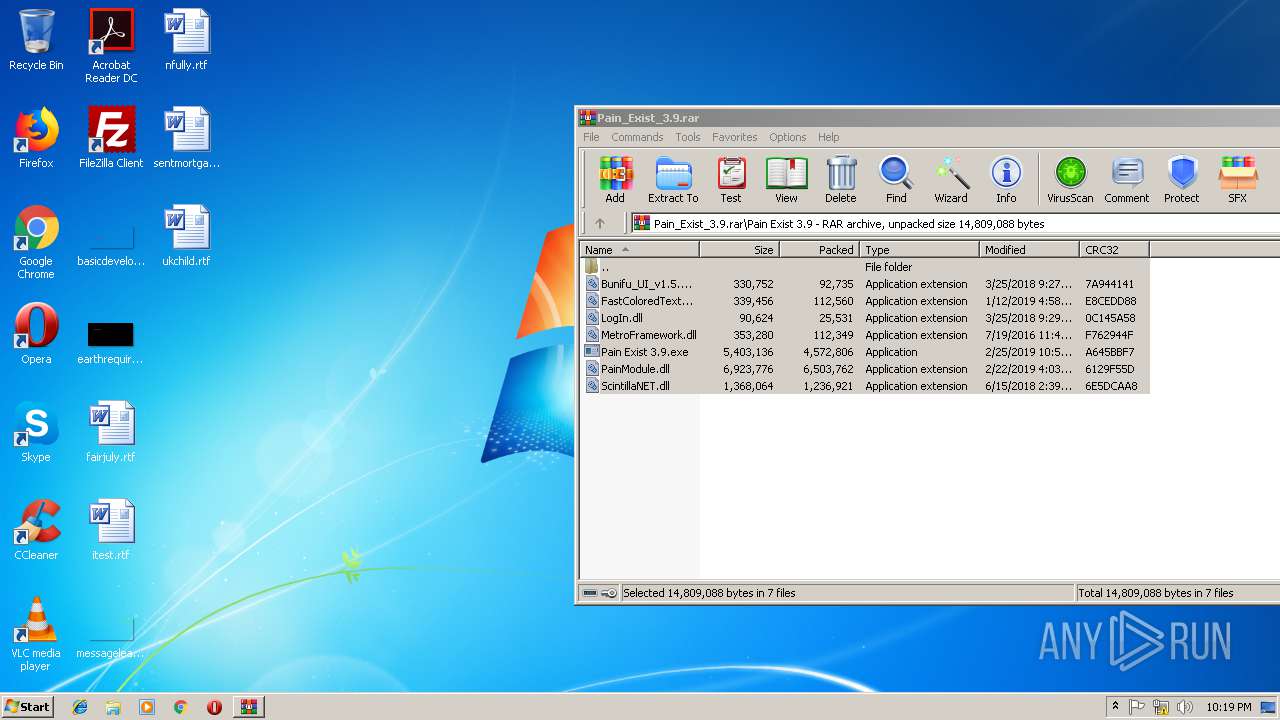
| File name: | Pain_Exist_3.9.rar |
| Full analysis: | https://app.any.run/tasks/1a606752-9826-407b-901c-97cd040221e8 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2019, 22:18:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 05D0F7ABDA32034DA3379ABC0EFC21F7 |
| SHA1: | FD4C70342067C10088D46D3967C88D6F90F47314 |
| SHA256: | 7AA7CB157DC989BB7C6A19A0BCA065801CC33EA2D880280EA01B4AAD3A704DA1 |
| SSDEEP: | 196608:+ZT4xisjbuBnVCmdnfodapcRLp5MxCDNzFdINxdxj2ksLjbvthkKavd5VMKm7X4Q:q4gC3mBQA2RLA4z/i6ksTnkLvV31Y |
MALICIOUS
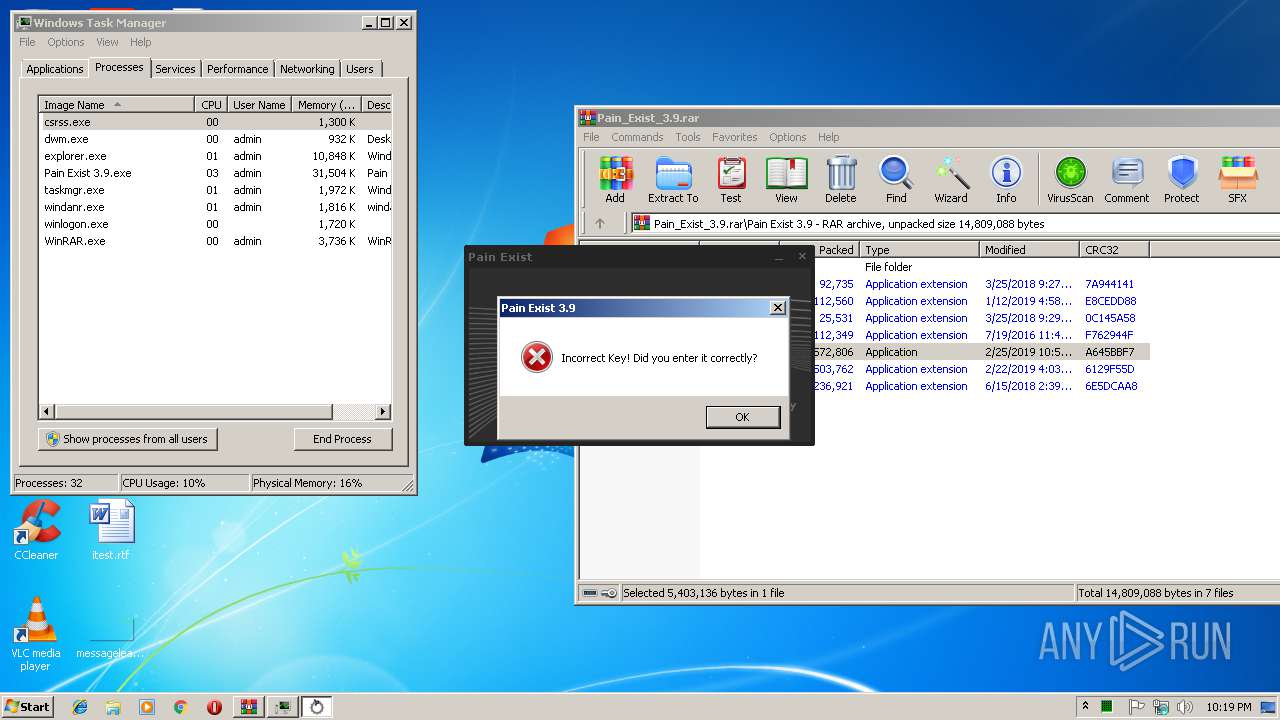
Loads dropped or rewritten executable
- Pain Exist 3.9.exe (PID: 3248)
Application was dropped or rewritten from another process
- Pain Exist 3.9.exe (PID: 3248)
SUSPICIOUS
Reads Environment values
- Pain Exist 3.9.exe (PID: 3248)
Reads the BIOS version
- Pain Exist 3.9.exe (PID: 3248)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3316)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
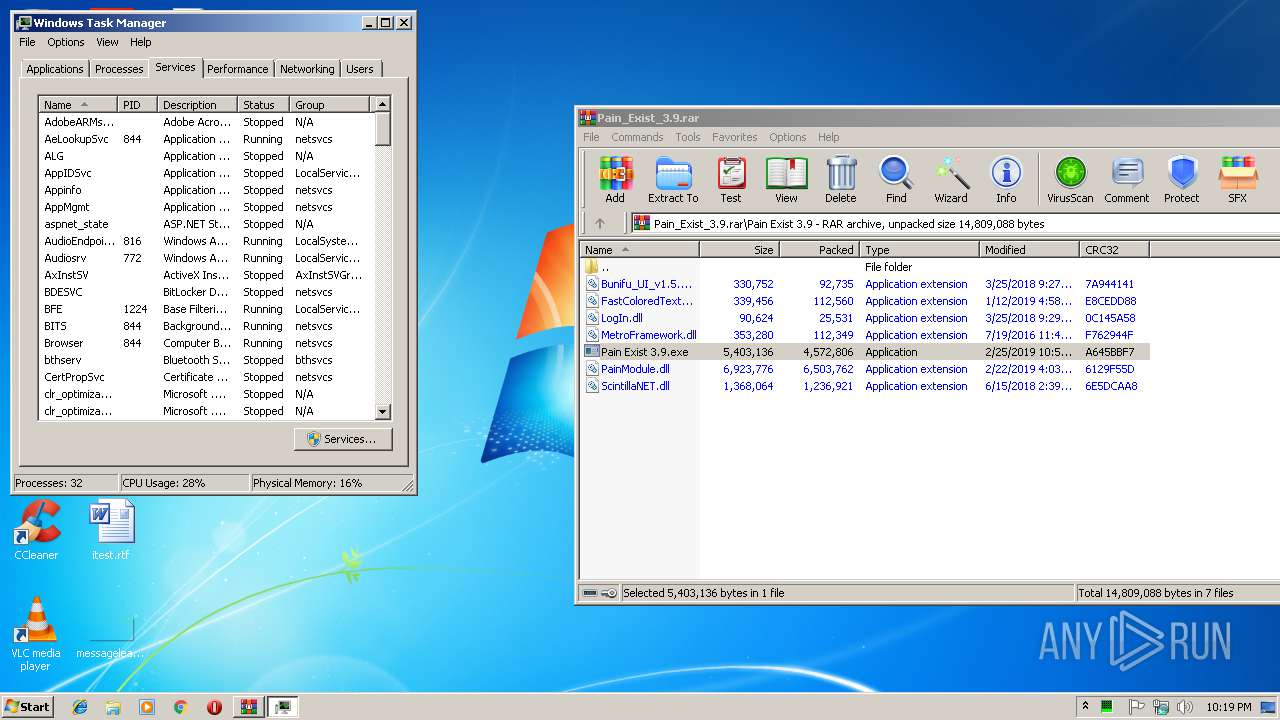
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
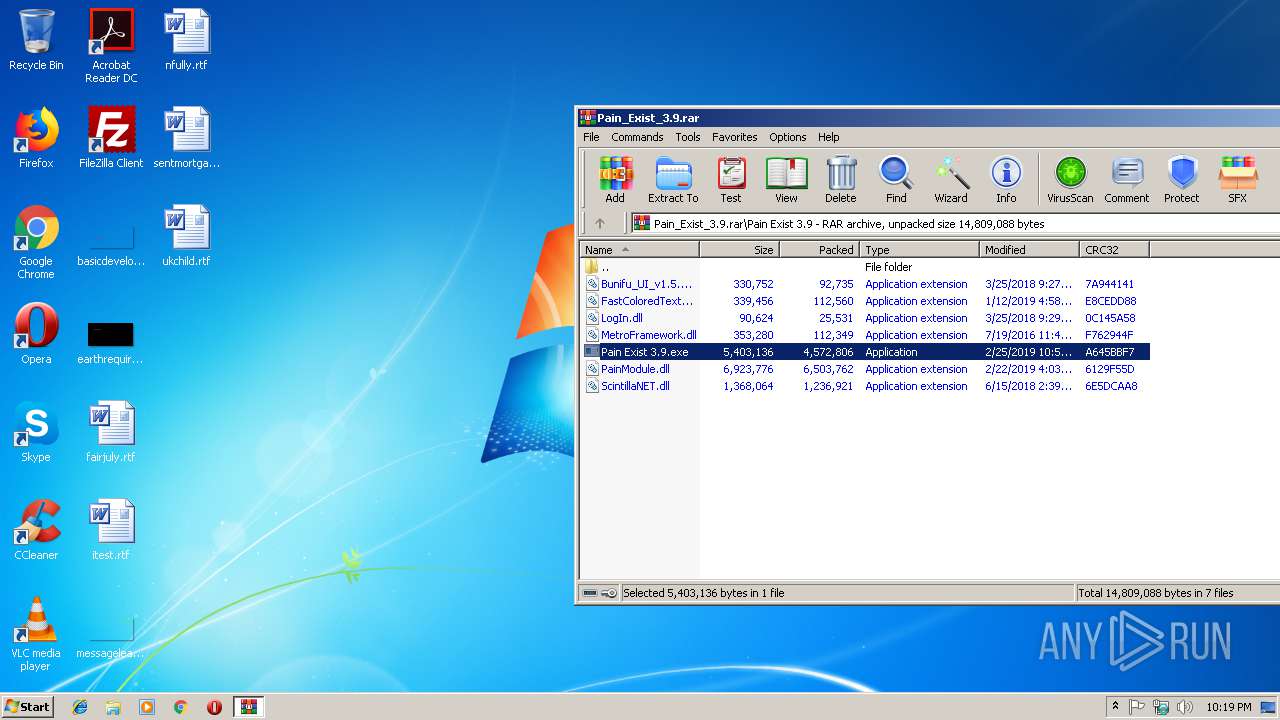
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
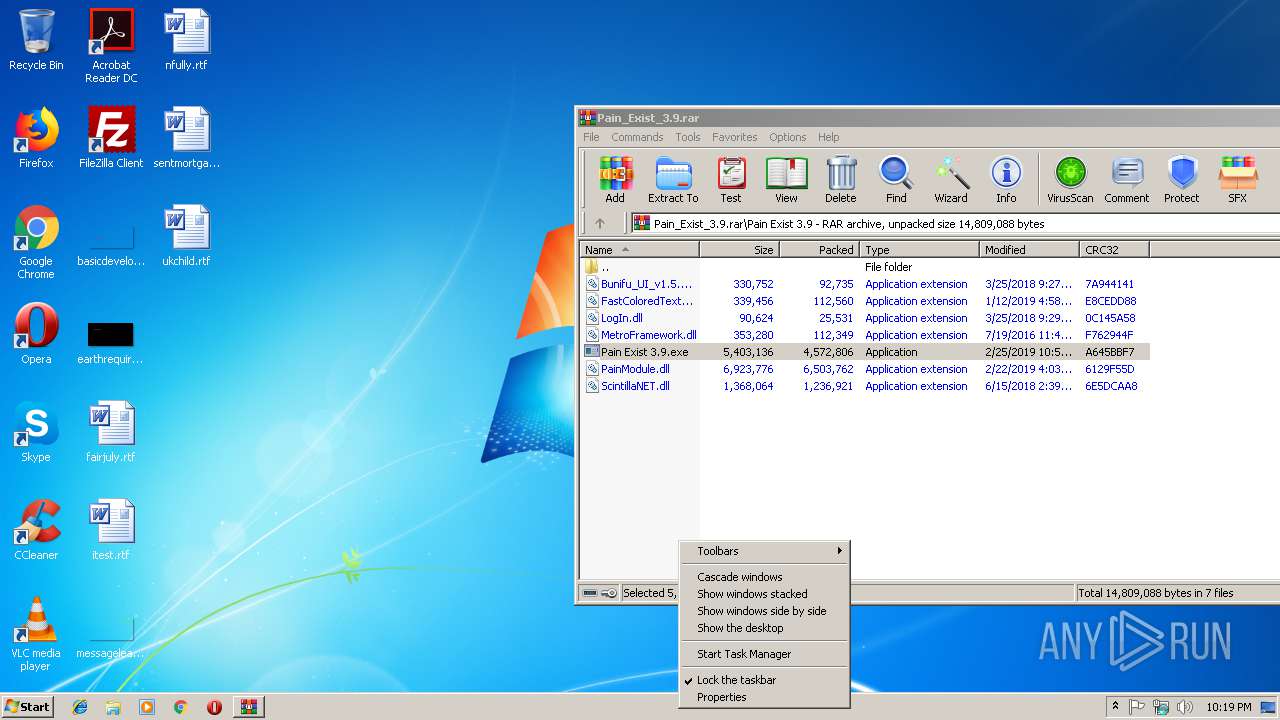
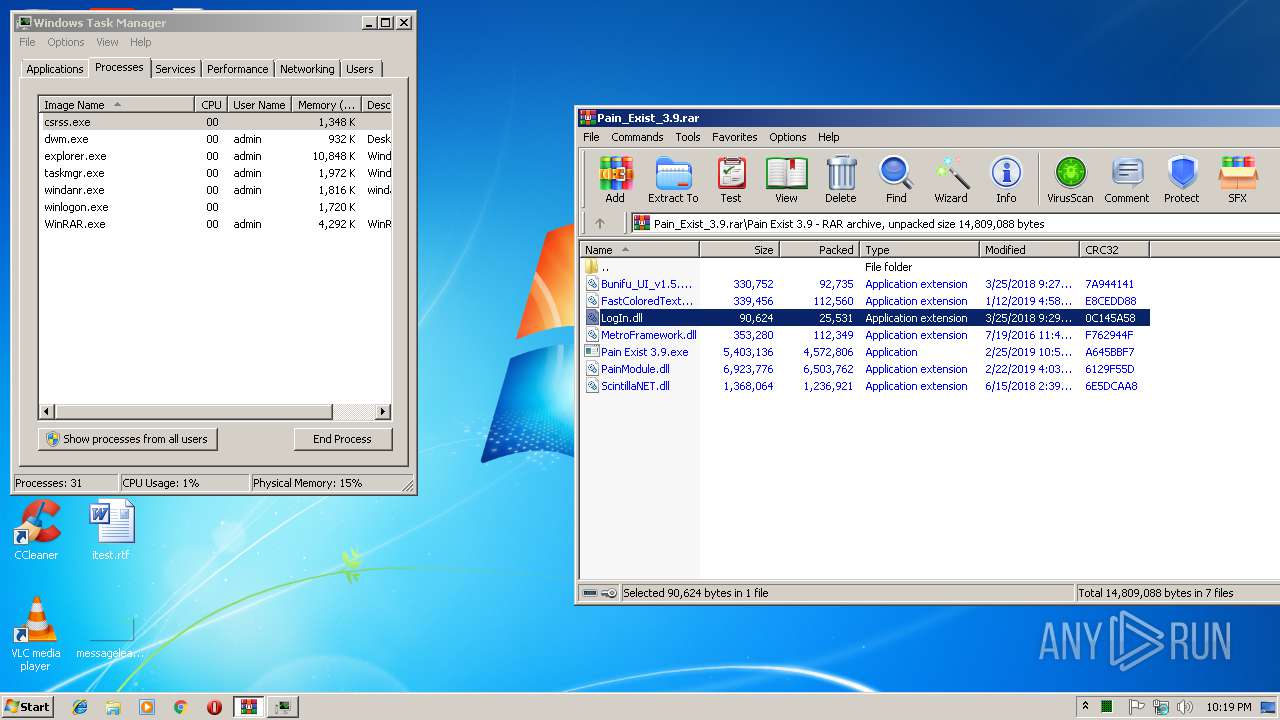
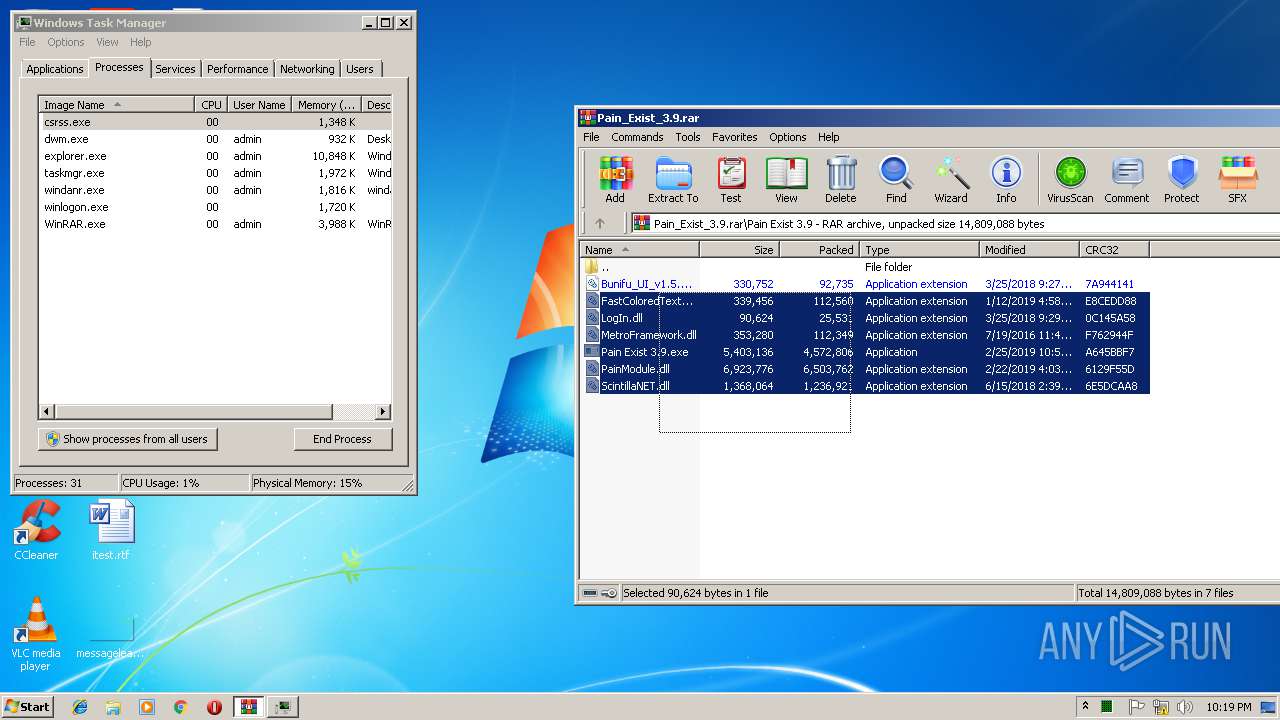
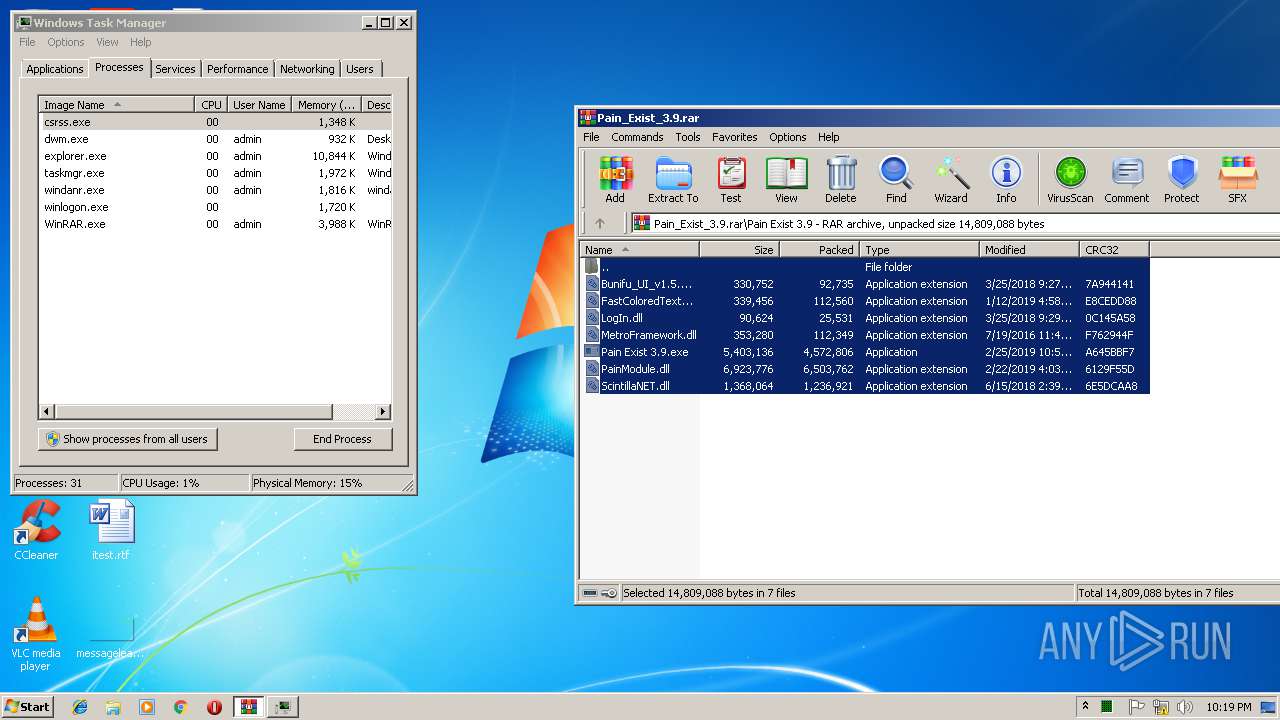
| 348 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
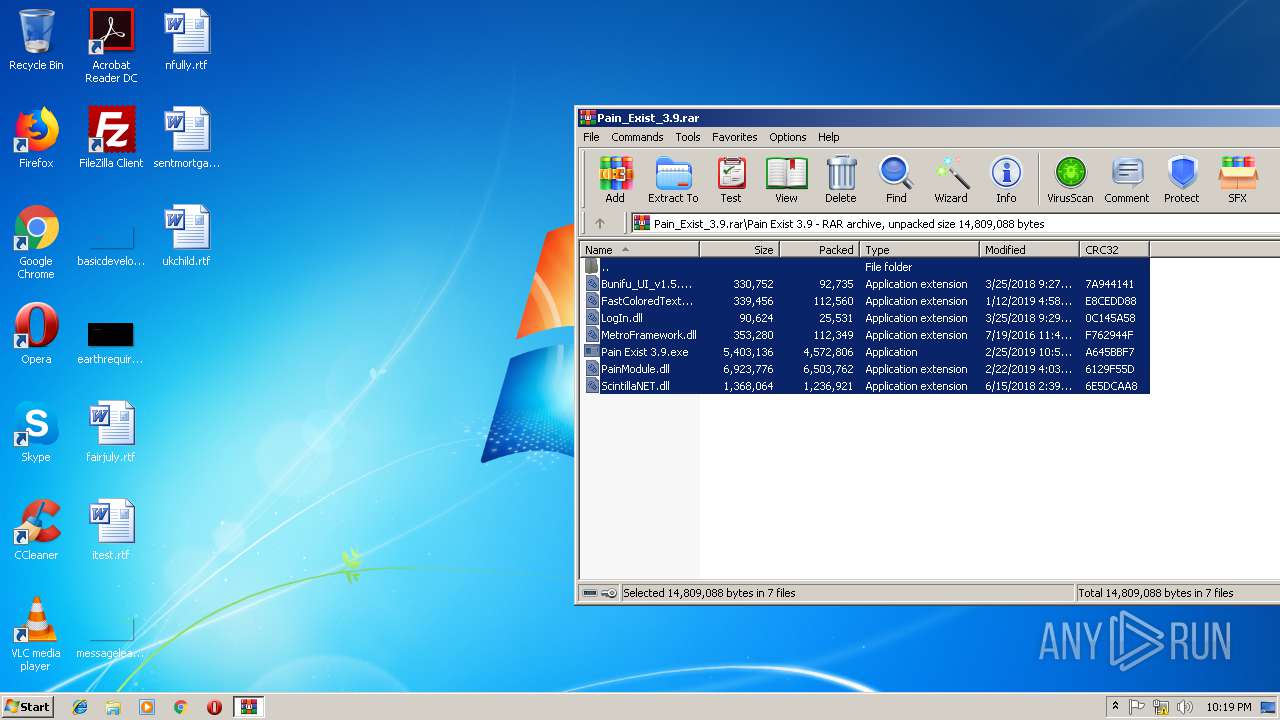
| 3248 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\Pain Exist 3.9.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\Pain Exist 3.9.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Pain Exist 3.9 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Pain_Exist_3.9.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
517
Read events
480
Write events
37
Delete events
0
Modification events
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Pain_Exist_3.9.rar | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
8
Suspicious files
0
Text files
0
Unknown types
0
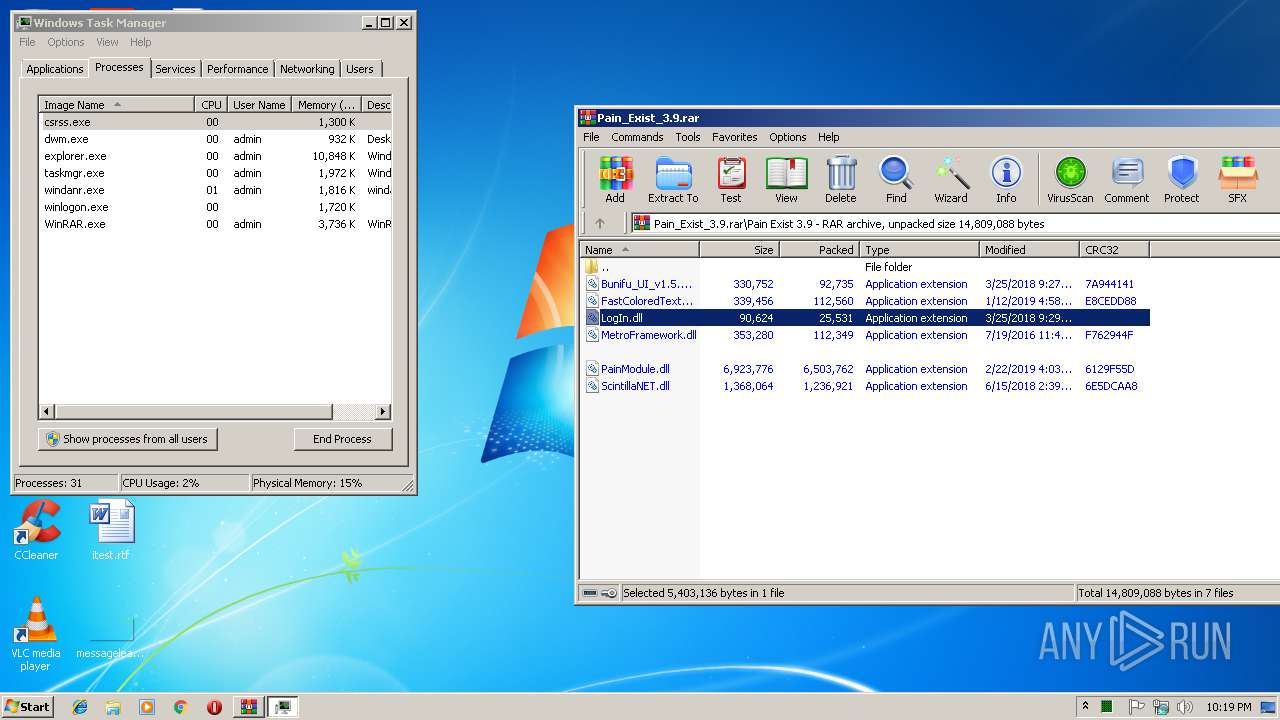
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
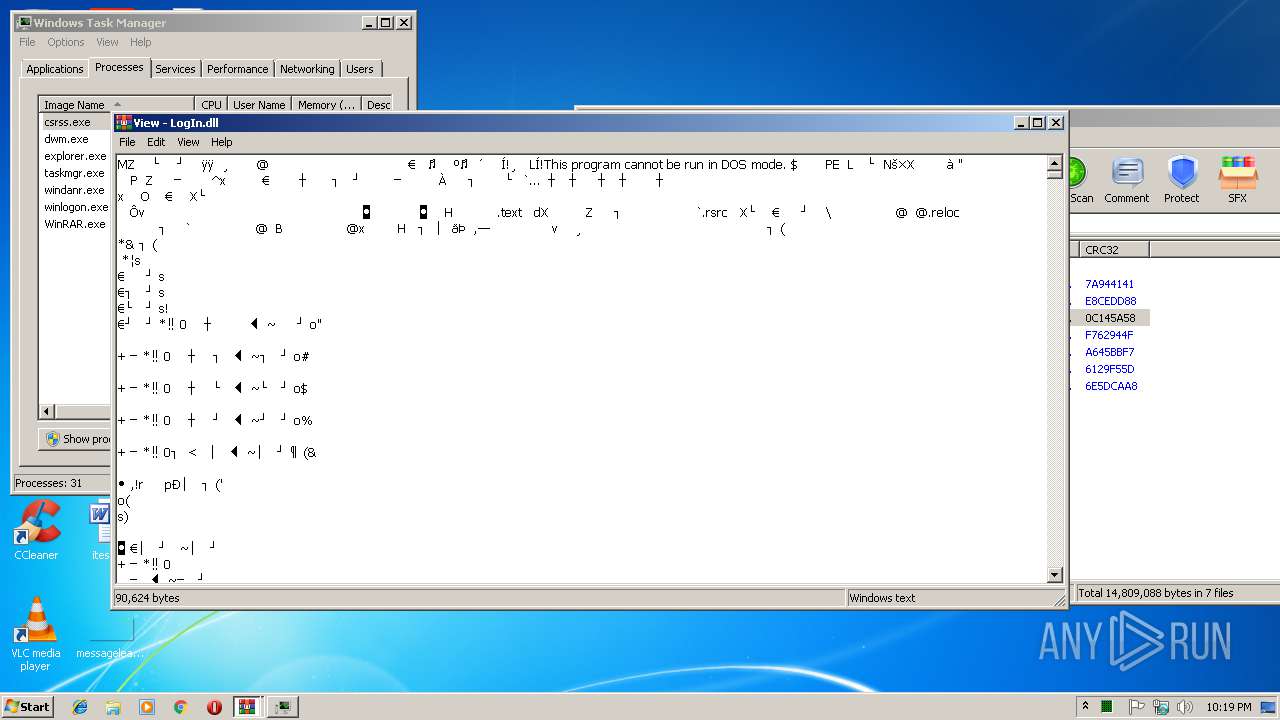
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\LogIn.dll | executable | |
MD5:03621CCA4EDFDA4752AB77E5D3F824B3 | SHA256:332D7006B1D7815E8792371BA4CF32BE0261A36E1EDA34B38E4C92163157410B | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3316.8234\LogIn.dll | executable | |
MD5:03621CCA4EDFDA4752AB77E5D3F824B3 | SHA256:332D7006B1D7815E8792371BA4CF32BE0261A36E1EDA34B38E4C92163157410B | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\PainModule.dll | executable | |
MD5:7F6B46E3491E23870C2A88250F65A546 | SHA256:EFD49E59F9299E0A838DD4AF7AA1413E1EB388AAC9487164B4C7C2FBC0368050 | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\Bunifu_UI_v1.5.3.dll | executable | |
MD5:E0EF2817EE5A7C8CD1EB837195768BD2 | SHA256:76E1D3EC95FDEF74ABAF90392DD6F4AA5E344922ABF11E572707287D467F2930 | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\FastColoredTextBox.dll | executable | |
MD5:7D315038DA4CB77039DC315C64946E22 | SHA256:777C68C5C47CF91E18583A0FA50B556B1551898A07097F296A0811943A493FA6 | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\MetroFramework.dll | executable | |
MD5:34EA7F7D66563F724318E322FF08F4DB | SHA256:C2C12D31B4844E29DE31594FC9632A372A553631DE0A0A04C8AF91668E37CF49 | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\ScintillaNET.dll | executable | |
MD5:9166536C31F4E725E6BEFE85E2889A4B | SHA256:AD0CC5A4D4A6AAE06EE360339C851892B74B8A275CE89C1B48185672179F3163 | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3316.4909\Pain Exist 3.9\Pain Exist 3.9.exe | executable | |
MD5:8674EAA73AB289F2BA0ED35FB0BF4D06 | SHA256:382149653B1DBD7A7C6D802B6B0E4027C794ACE8E6F3AEE991131CD93A1B7F84 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3248 | Pain Exist 3.9.exe | 68.65.123.241:443 | roxploits.com | Namecheap, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
roxploits.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Pain Exist 3.9.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |