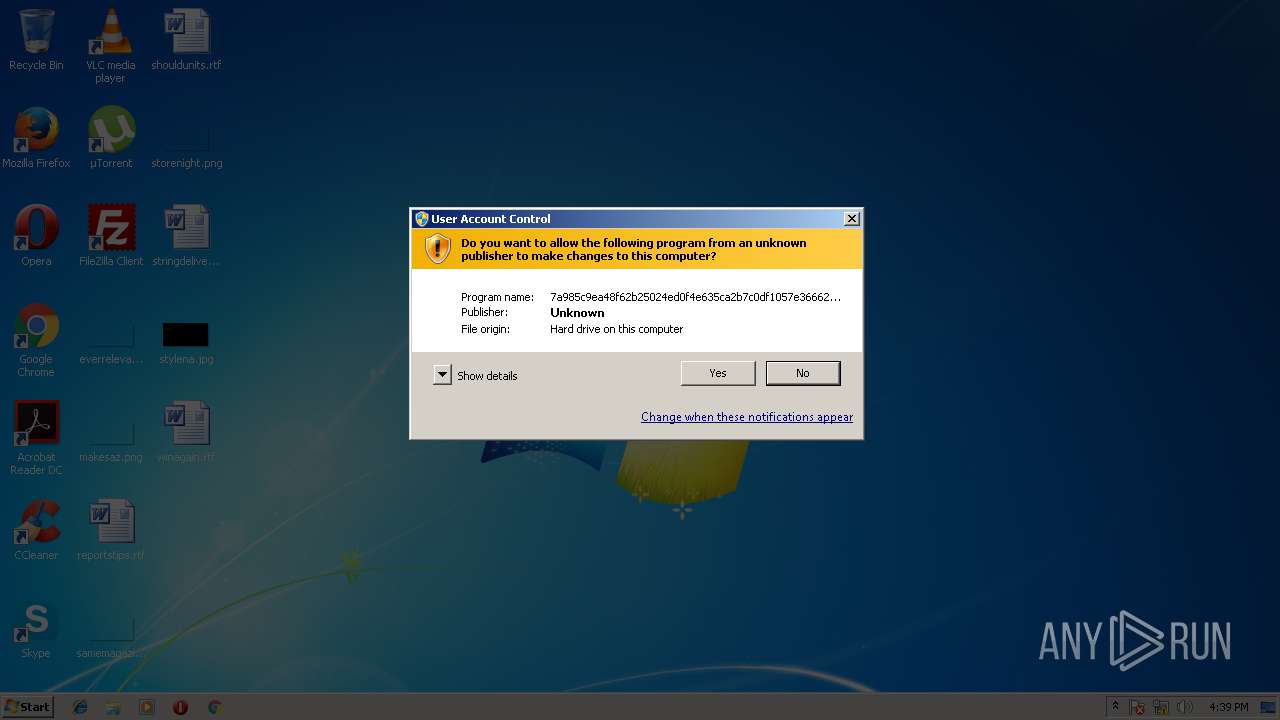
| File name: | 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8 |
| Full analysis: | https://app.any.run/tasks/78fc56ed-9c51-4c02-b4b0-d5f6f4aff0e7 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2018, 15:39:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A27FD6EC9599EB7C6EDEC213AA2C69A4 |
| SHA1: | 2269B81E16A06991535FDC2AB21330173008F3A8 |
| SHA256: | 7A985C9EA48F62B25024ED0F4E635CA2B7C0DF1057E366628EF65CDEB8BAB7D8 |
| SSDEEP: | 49152:WqYyA3Lr77n/JMQlAYPTPIWLV96RFoKfG3JbSAQjkaEv2HVX/AJwAxJa57gDKVf3:Wq47rJMOvP1aotu1ICKJa5UDK5ttHrLL |
MALICIOUS
Loads dropped or rewritten executable
- 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe (PID: 4032)
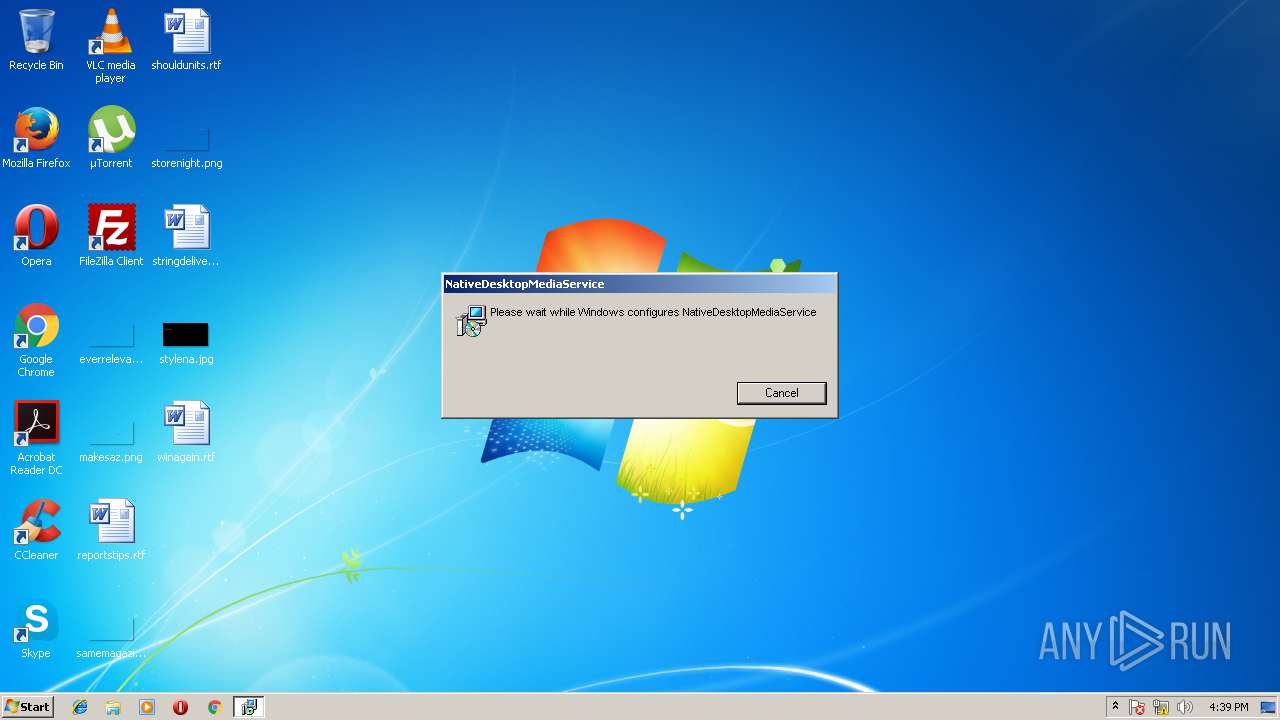
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 2740)
Loads the Task Scheduler DLL interface
- 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe (PID: 4032)
Application was dropped or rewritten from another process
- desktop_media_service.exe (PID: 2124)
SUSPICIOUS
Creates files in the user directory
- 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe (PID: 4032)
- MsiExec.exe (PID: 3632)
- MsiExec.exe (PID: 2104)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3624)
- 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe (PID: 4032)
Starts Microsoft Installer
- 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe (PID: 4032)
Connects to unusual port
- MsiExec.exe (PID: 3632)
- desktop_media_service.exe (PID: 2124)
Checks for external IP
- desktop_media_service.exe (PID: 2124)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2932)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2104)
- MsiExec.exe (PID: 3632)
- MsiExec.exe (PID: 2740)
Creates or modifies windows services
- MsiExec.exe (PID: 3632)
- msiexec.exe (PID: 3624)
- vssvc.exe (PID: 2932)
Creates files in the program directory
- msiexec.exe (PID: 3624)
Creates a software uninstall entry
- msiexec.exe (PID: 3624)
Application launched itself
- msiexec.exe (PID: 3624)
Dropped object may contain URL's
- 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe (PID: 4032)
- msiexec.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:19 12:06:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 1201152 |
| InitializedDataSize: | 532992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xdb1f7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.3.0 |
| ProductVersionNumber: | 2.2.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Installer |
| FileVersion: | 2.2.3 |
| InternalName: | setup_2.2.3 |
| LegalCopyright: | Copyright (C) 2018 |
| OriginalFileName: | setup_2.2.3.exe |
| ProductName: | setup_2.2.3 |
| ProductVersion: | 2.2.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Feb-2018 11:06:57 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | Installer |
| FileVersion: | 2.2.3 |
| InternalName: | setup_2.2.3 |
| LegalCopyright: | Copyright (C) 2018 |
| OriginalFileName: | setup_2.2.3.exe |
| ProductName: | setup_2.2.3 |
| ProductVersion: | 2.2.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Feb-2018 11:06:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0012534D | 0x00125400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65482 |
.rdata | 0x00127000 | 0x00055594 | 0x00055600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57034 |
.data | 0x0017D000 | 0x00007164 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.1865 |
.rsrc | 0x00185000 | 0x00015255 | 0x00015400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.32119 |
.reloc | 0x0019B000 | 0x00015348 | 0x00015400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58675 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18998 | 1909 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.35766 | 820 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
46
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Jetmedia\NativeDesktopMediaService 2.2.3\install\2D8AC3A\TestInstaller100.msi" AI_SETUPEXEPATH=C:\Users\admin\Downloads\7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe SETUPEXEDIR=C:\Users\admin\Downloads\ EXE_CMD_LINE="/exenoupdates " | C:\Windows\system32\msiexec.exe | — | 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | C:\Windows\system32\MsiExec.exe -Embedding D0CFAADC8EF503DF85A8FC81D471F36B C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | C:\Windows\system32\DllHost.exe /Processid:{E2B3C97F-6AE1-41AC-817A-F6F92166D7DD} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Jetmedia\NativeDesktopMediaService\desktop_media_service.exe" --service | C:\Program Files\Jetmedia\NativeDesktopMediaService\desktop_media_service.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2740 | C:\Windows\system32\MsiExec.exe -Embedding A4F059FC9F824EC98CFD1BC8E156A70F M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3624 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3632 | C:\Windows\system32\MsiExec.exe -Embedding 8149A163F1DE86150032DDAD24338942 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\Downloads\7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe" | C:\Users\admin\Downloads\7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Installer Exit code: 3221226540 Version: 2.2.3 Modules
| |||||||||||||||
| 4032 | "C:\Users\admin\Downloads\7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe" | C:\Users\admin\Downloads\7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Installer Exit code: 0 Version: 2.2.3 Modules
| |||||||||||||||
Total events
874
Read events
566
Write events
296
Delete events
12
Modification events
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2104) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MsiExec_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
18
Suspicious files
8
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4032 | 7a985c9ea48f62b25024ed0f4e635ca2b7c0df1057e366628ef65cdeb8bab7d8.exe | C:\Users\admin\AppData\Local\Temp\MSI17FB.tmp | — | |
MD5:— | SHA256:— | |||
| 2104 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 2104 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\tin1914.tmp.part | — | |
MD5:— | SHA256:— | |||
| 2104 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\tin1914.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3624 | msiexec.exe | C:\Windows\Installer\MSI3A0B.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | msiexec.exe | C:\Windows\Installer\MSI3A2B.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | msiexec.exe | C:\Windows\Installer\MSI3BF2.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | msiexec.exe | C:\Windows\Installer\MSI3C12.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | msiexec.exe | C:\Windows\Installer\MSI3C42.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
11
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2124 | desktop_media_service.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com:80/json | DE | text | 302 b | malicious |
3632 | MsiExec.exe | POST | 200 | 199.217.118.146:40000 | http://ylsuest.com:40000/tickets | US | — | — | malicious |
3632 | MsiExec.exe | POST | 200 | 199.217.118.146:40000 | http://mrsewic.com:40000/tickets | US | — | — | malicious |
3632 | MsiExec.exe | GET | 200 | 216.58.206.4:80 | http://www.google.com/ | US | html | 10.2 Kb | malicious |
2124 | desktop_media_service.exe | POST | 200 | 199.217.118.146:40000 | http://knsemis.com:40000/tickets | US | — | — | malicious |
2124 | desktop_media_service.exe | POST | 200 | 199.217.118.146:40000 | http://knsemis.com:40000/tickets | US | — | — | malicious |
3632 | MsiExec.exe | POST | 200 | 199.217.118.146:40000 | http://ylsuest.com:40000/tickets | US | — | — | malicious |
2104 | MsiExec.exe | GET | 200 | 216.58.206.4:80 | http://www.google.com/ | US | html | 10.2 Kb | malicious |
2124 | desktop_media_service.exe | GET | 200 | 207.38.88.89:80 | http://xfinucte.com/npcomdata.dat | US | binary | 7.14 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | MsiExec.exe | 216.58.206.4:80 | www.google.com | Google Inc. | US | whitelisted |
3632 | MsiExec.exe | 216.58.206.4:80 | www.google.com | Google Inc. | US | whitelisted |
3632 | MsiExec.exe | 199.217.118.146:40000 | mrsewic.com | server4you Inc. | US | malicious |
2124 | desktop_media_service.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
2124 | desktop_media_service.exe | 199.217.118.146:40000 | mrsewic.com | server4you Inc. | US | malicious |
2124 | desktop_media_service.exe | 207.38.88.89:80 | xfinucte.com | server4you Inc. | US | unknown |
2124 | desktop_media_service.exe | 207.38.87.182:443 | — | server4you Inc. | US | unknown |
2124 | desktop_media_service.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
mrsewic.com |
| malicious |
ip-api.com |
| malicious |
ylsuest.com |
| malicious |
knsemis.com |
| malicious |
xfinucte.com |
| unknown |
lb.lambda.servers.jetstar.media |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2124 | desktop_media_service.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |