| File name: | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe |
| Full analysis: | https://app.any.run/tasks/c993ba3f-9df0-4733-8569-fe3ad6f5247f |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2021, 20:24:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7CB9AF9399030F0D076348721A414219 |
| SHA1: | D04583FAFDB0DD4BD69F7A420D57547BFD8CD0C2 |
| SHA256: | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069 |
| SSDEEP: | 24576:VKWmAF3EhmzDgavPpBzRdOICdW4CfOX0+tHE8G0ZmIdjNKLO3ufWQNJbgrdkDJ2E:Vrk00mPTLFCrAOjXBdjULFf7NJb4kN2E |
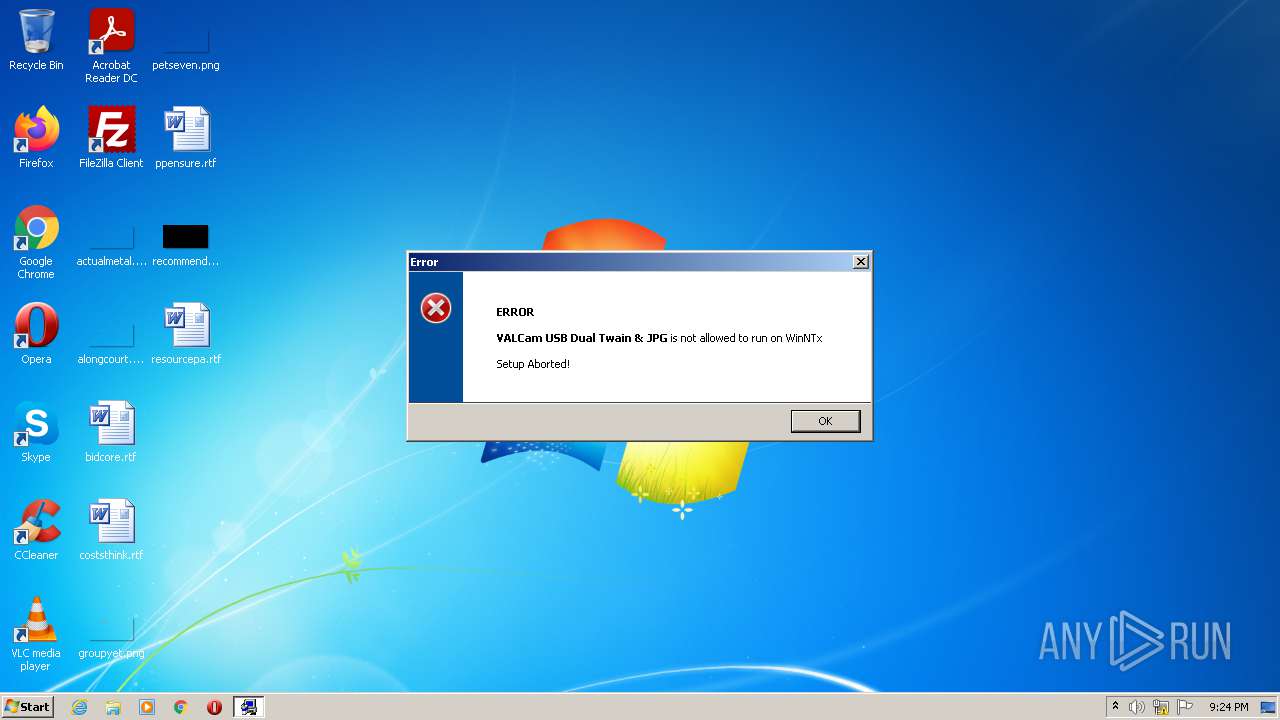
MALICIOUS
Application was dropped or rewritten from another process
- Engine.exe (PID: 2100)
Drops executable file immediately after starts
- Engine.exe (PID: 2100)
SUSPICIOUS
Executable content was dropped or overwritten
- 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe (PID: 3420)
- Engine.exe (PID: 2100)
Checks supported languages
- 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe (PID: 3420)
- Engine.exe (PID: 2100)
Drops a file that was compiled in debug mode
- 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe (PID: 3420)
- Engine.exe (PID: 2100)
Drops a file with too old compile date
- 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe (PID: 3420)
- Engine.exe (PID: 2100)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (49.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (16.2) |
| .scr | | | Windows screen saver (14.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| Comments: | - |
|---|---|
| ProductVersion: | 8.0.0.0 |
| ProductName: | - |
| OriginalFileName: | Stub.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright (C) 2002-2007, Pantaray Software Systems |
| InternalName: | Setup SFX Kernel |
| FileVersion: | 8.0.0.0 |
| FileDescription: | SFX Kernel |
| CompanyName: | Pantaray Research LTD. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 8.0.0.0 |
| FileVersionNumber: | 8.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x251dc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 28672 |
| CodeSize: | 148480 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Pantaray Research LTD. |
| FileDescription: | SFX Kernel |
| FileVersion: | 8.0.0.0 |
| InternalName: | Setup SFX Kernel |
| LegalCopyright: | Copyright (C) 2002-2007, Pantaray Software Systems |
| LegalTrademarks: | - |
| OriginalFilename: | Stub.exe |
| ProductName: | - |
| ProductVersion: | 8.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00024208 | 0x00024400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4869 |
DATA | 0x00026000 | 0x00001EF0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.24515 |
BSS | 0x00028000 | 0x00000909 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00029000 | 0x00001134 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77322 |
.tls | 0x0002B000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002C000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.200582 |
.reloc | 0x0002D000 | 0x000020BC | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.66999 |
.rsrc | 0x00030000 | 0x00001A00 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.06854 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.9091 | 668 | UNKNOWN | UNKNOWN | RT_MANIFEST |
4091 | 2.39 | 120 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 2.94341 | 244 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.8794 | 196 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.19303 | 748 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.27138 | 832 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.16152 | 704 | UNKNOWN | UNKNOWN | RT_STRING |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.34155 | 348 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.16096 | 20 | UNKNOWN | Hebrew - Israel | RT_GROUP_ICON |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
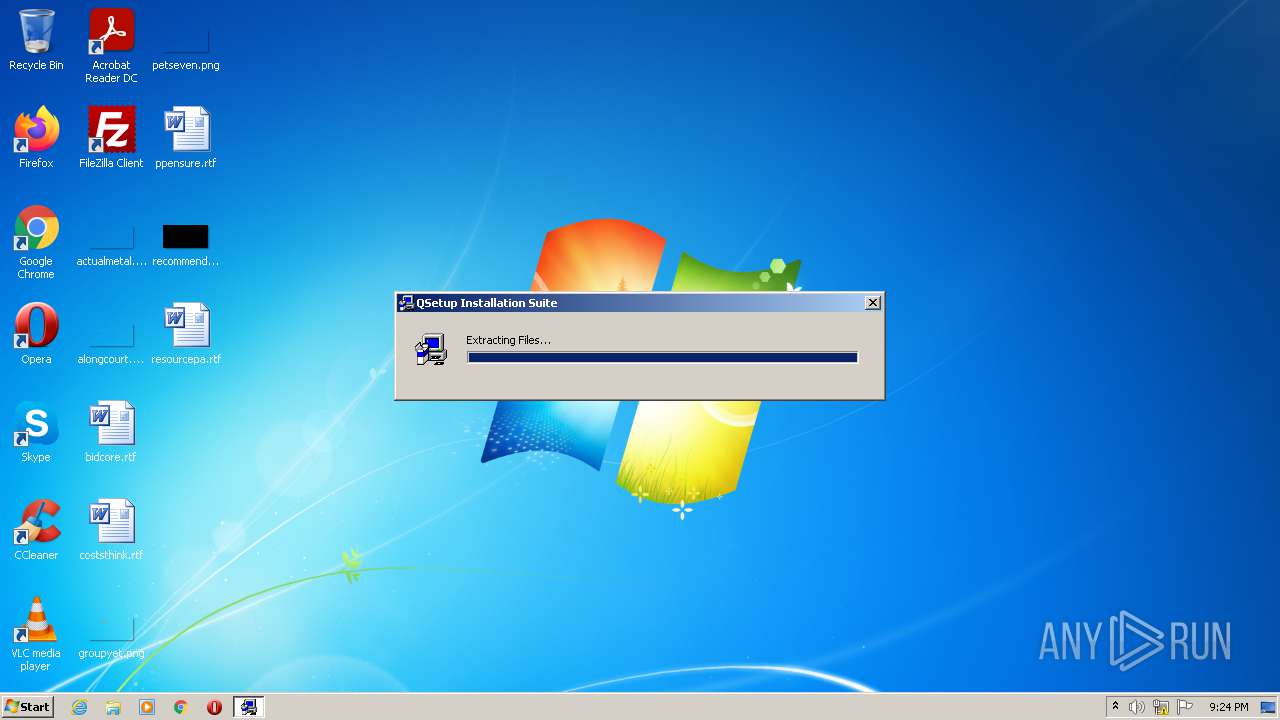
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2100 | C:\Users\admin\AppData\Local\Temp\SETUP_43800\Engine.exe /TH_ID=_1116 /OriginExe="C:\Users\admin\AppData\Local\Temp\7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe" | C:\Users\admin\AppData\Local\Temp\SETUP_43800\Engine.exe | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | ||||||||||||
User: admin Company: Pantaray Research LTD. Integrity Level: HIGH Description: Setup Engine Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 2532 | "C:\Users\admin\AppData\Local\Temp\7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe" | C:\Users\admin\AppData\Local\Temp\7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Pantaray Research LTD. Integrity Level: MEDIUM Description: SFX Kernel Exit code: 3221226540 Version: 8.0.0.0 Modules
| |||||||||||||||
| 3420 | "C:\Users\admin\AppData\Local\Temp\7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe" | C:\Users\admin\AppData\Local\Temp\7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | Explorer.EXE | ||||||||||||
User: admin Company: Pantaray Research LTD. Integrity Level: HIGH Description: SFX Kernel Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
Total events
38
Read events
38
Write events
0
Delete events
0
Modification events
Executable files
14
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\VALCam USB JPG Twain Registry.qsp | text | |
MD5:EB3EB7364FC1BD7E7963590679F725A4 | SHA256:AF2F2F02F3C416117D4F20DC29E5FFF693453AC37D35024CC46032B2CFD4D80B | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\Modern_Setup.bmp | image | |
MD5:DED1D8DB477CC655B17E16C6FE989707 | SHA256:7A5D14D64EF24CDF895F947700F6E8444940C3CF5B23E868F2B3A14F0FE14206 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\Modern_Icon.bmp | image | |
MD5:1DD88F67F029710D5C5858A6293A93F1 | SHA256:B5DAD33CEB6EB1AC2A05FBDA76E29A73038403939218A88367925C3A20C05532 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\00002#VALUSBWDM.sys | executable | |
MD5:9E605E2A335278BB2D243446DCB7D3FE | SHA256:516D2DFFA44C9334B2CE3624751B9F3E0E613964FA3E85E1B242B7EBB8733308 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\00005#LFCMP12n.DLL | executable | |
MD5:8A200172303DB6F91E3F5DC16E9CD113 | SHA256:C6148CC5446ACE50F18158CE5912525A7C53ACE4891A371BDBF2A79521FC0AE4 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\00003#VIDCapIncUSB.dll | executable | |
MD5:B0FBEF4A838DA05324B5A07EC8D86F9D | SHA256:4DBB6DF8E76454ACA721B3C4CB1277D0D8589810E26C717CF429186C42A61286 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\00004#lfbmp12n.dll | executable | |
MD5:AD24BB5343CC4646E062E0D7C75AE615 | SHA256:CA00D9028BAD4B3C7699FF676C6EB954A282461BD8A4C33B6FBF3E9AA69AEA07 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\00006#LTDIS12n.dll | executable | |
MD5:12BDF4BBBE7DD1E1D8E90833C2262272 | SHA256:3AD0E762E4CA9335DBBEF7F9F0FEDFC94FFB111CB8A28D56A4246676C9863987 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\00007#ltfil12n.DLL | executable | |
MD5:EFDFC884272AB525DED6B638CFD58610 | SHA256:CE68531A7A62F0CFC2F3363D98ACFF75E36400AAD3DB7BE82A7D10C22E0CC0D8 | |||
| 3420 | 7A875C69DD9CE30609E80CA03ED1F94AF7EE3FDED0660BCD159CA22B6E417069.exe | C:\Users\admin\AppData\Local\Temp\SETUP_43800\00008#ltimg12n.dll | executable | |
MD5:03559B304101CCA40A3E6BB03C308DAA | SHA256:6E90E1AFBE0B1F24E640400CA6E0A9AC78FB731E02EF15EF96CB03209A9AA297 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report