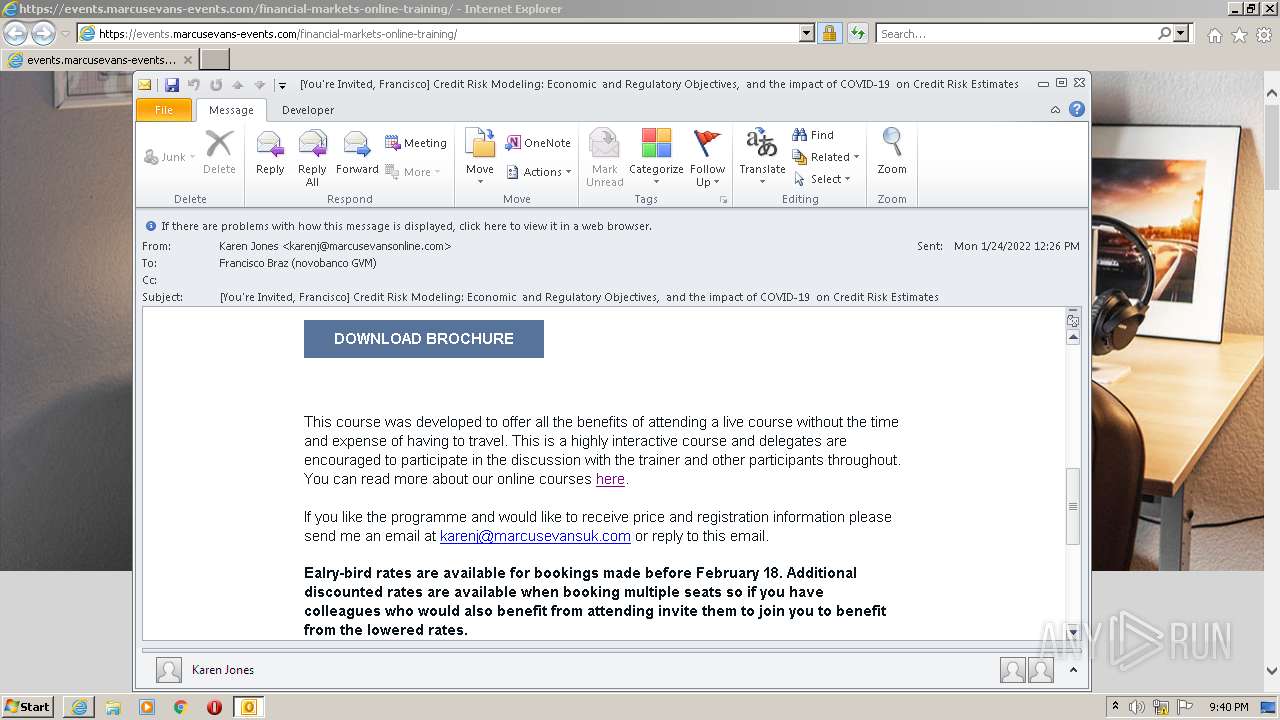
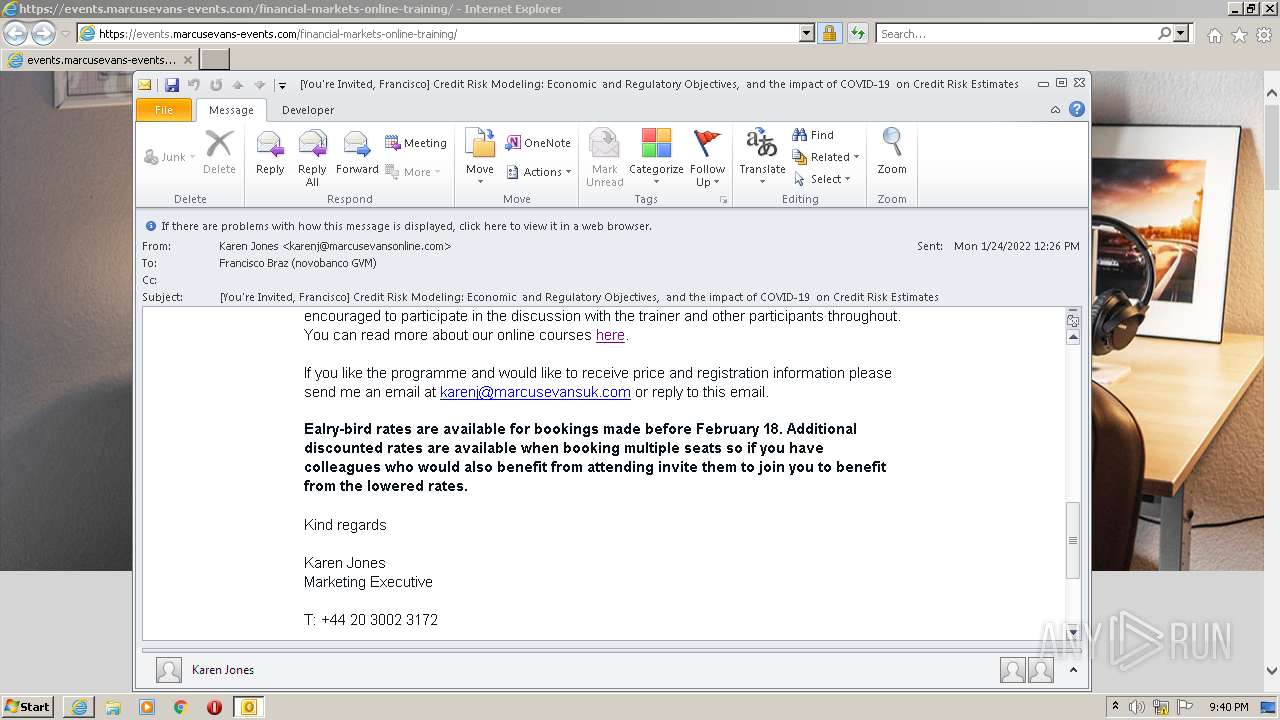
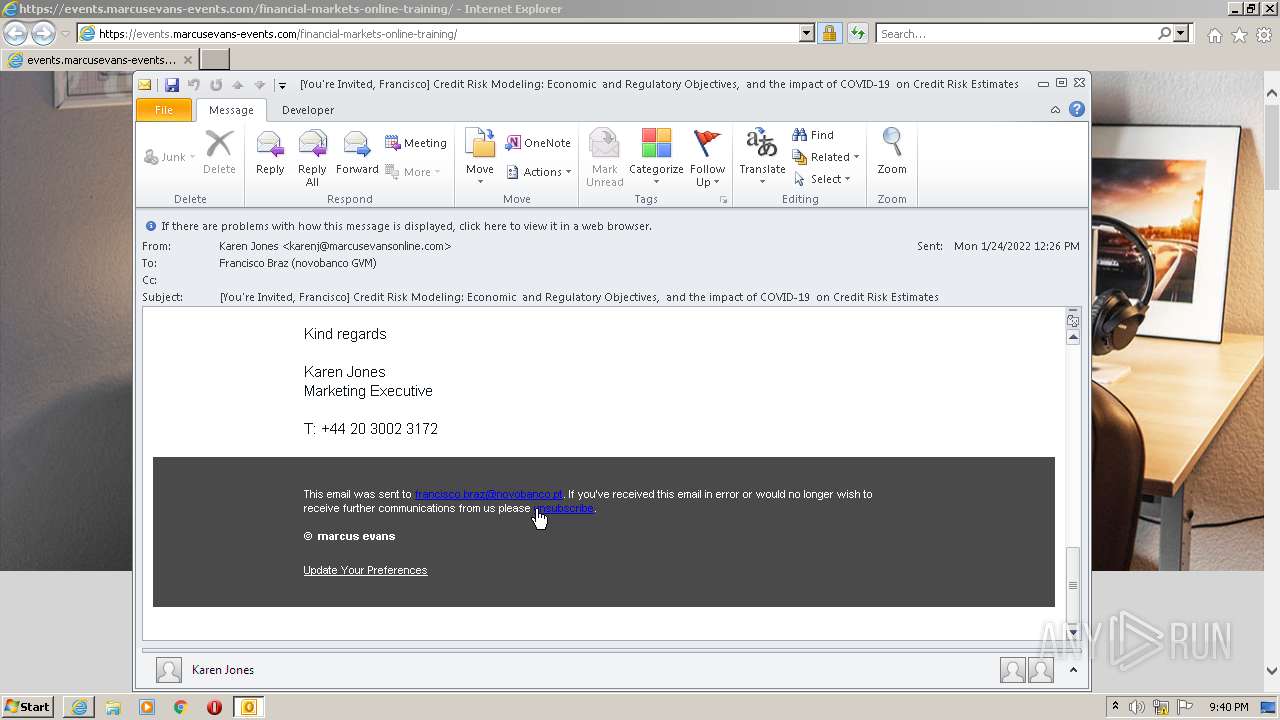
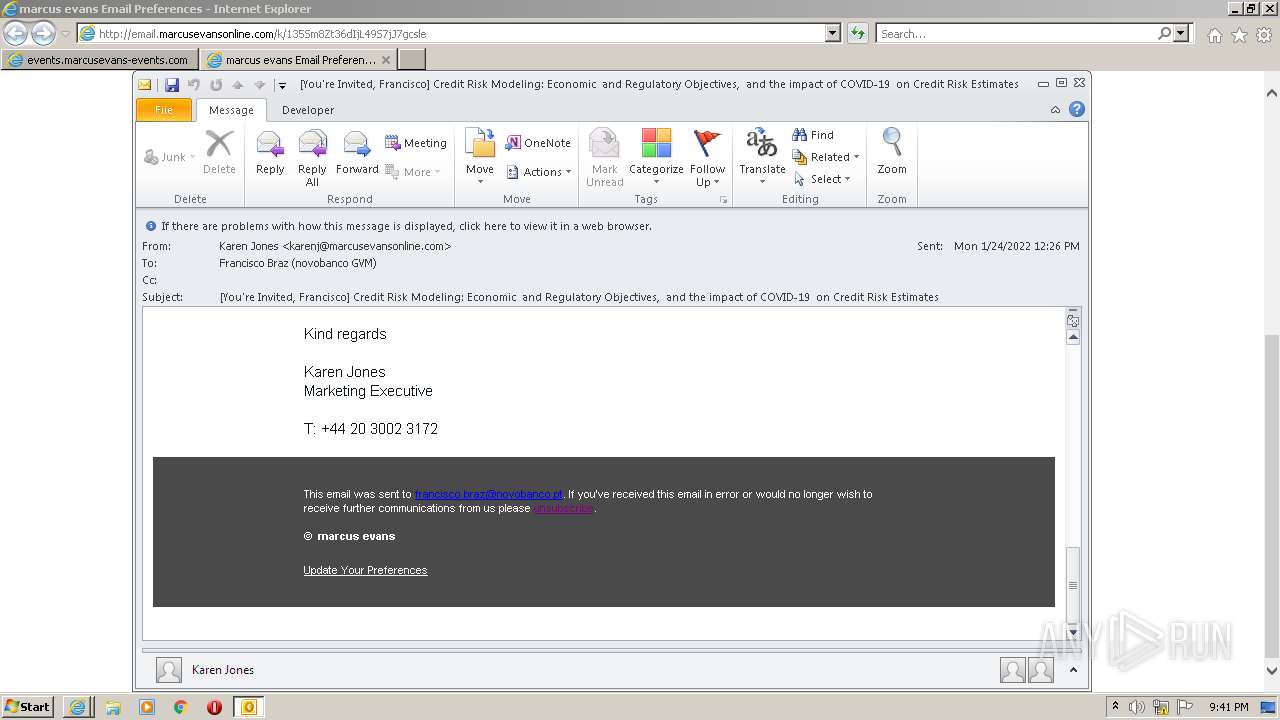
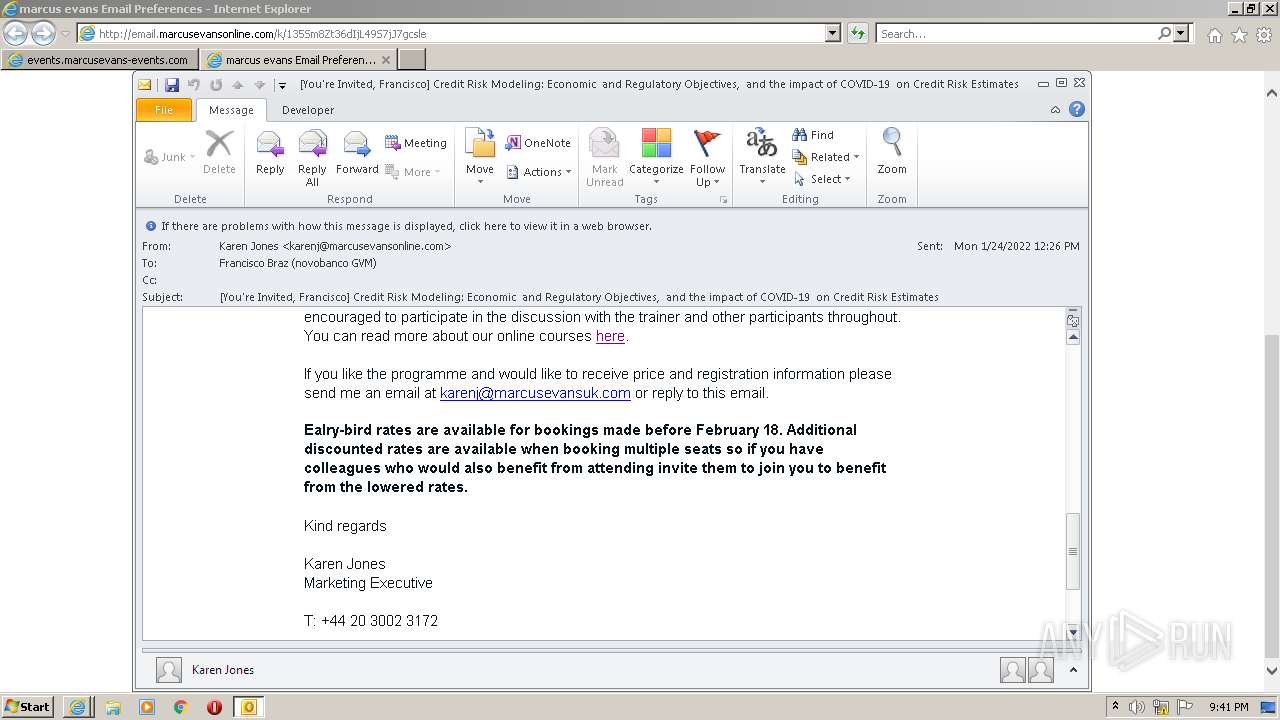
| File name: | You're Invited Francisco Credit Risk Modeling Economic and Regulatory Objectives and the impact of COVID-19 on Credit Risk Estimates.msg |
| Full analysis: | https://app.any.run/tasks/cb6819ea-50b7-4fa6-9681-bbb579136a7d |
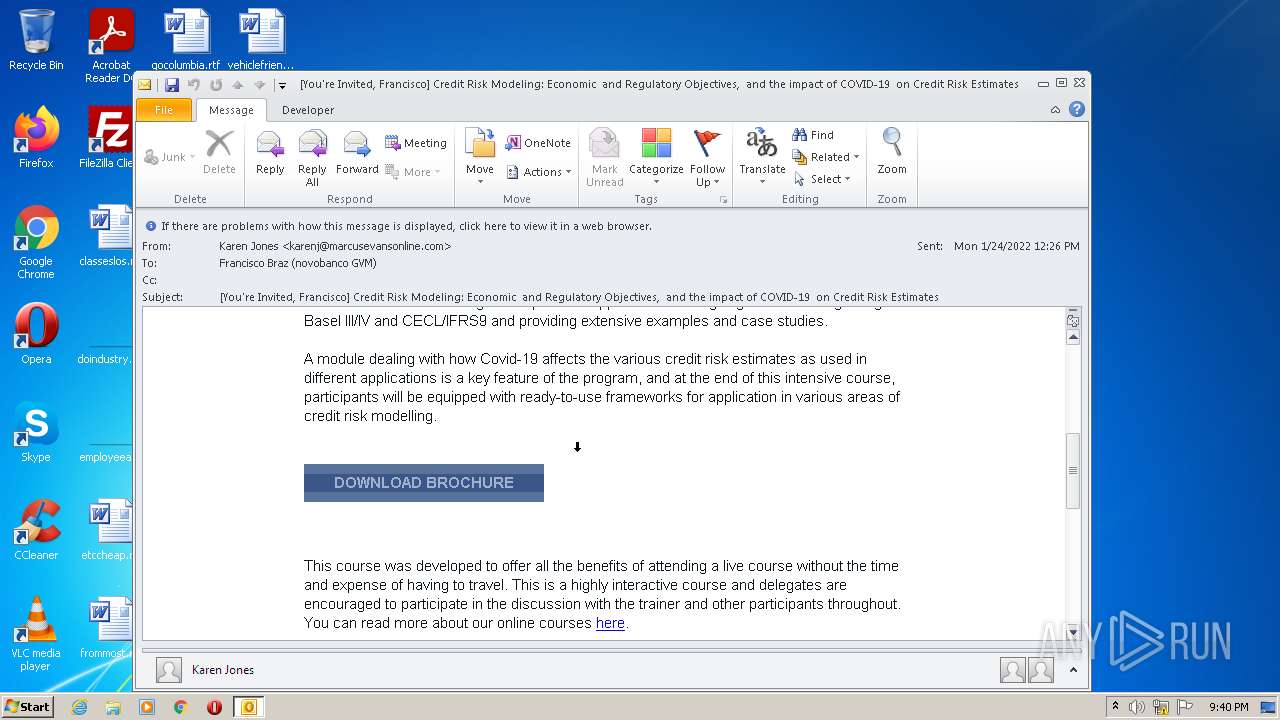
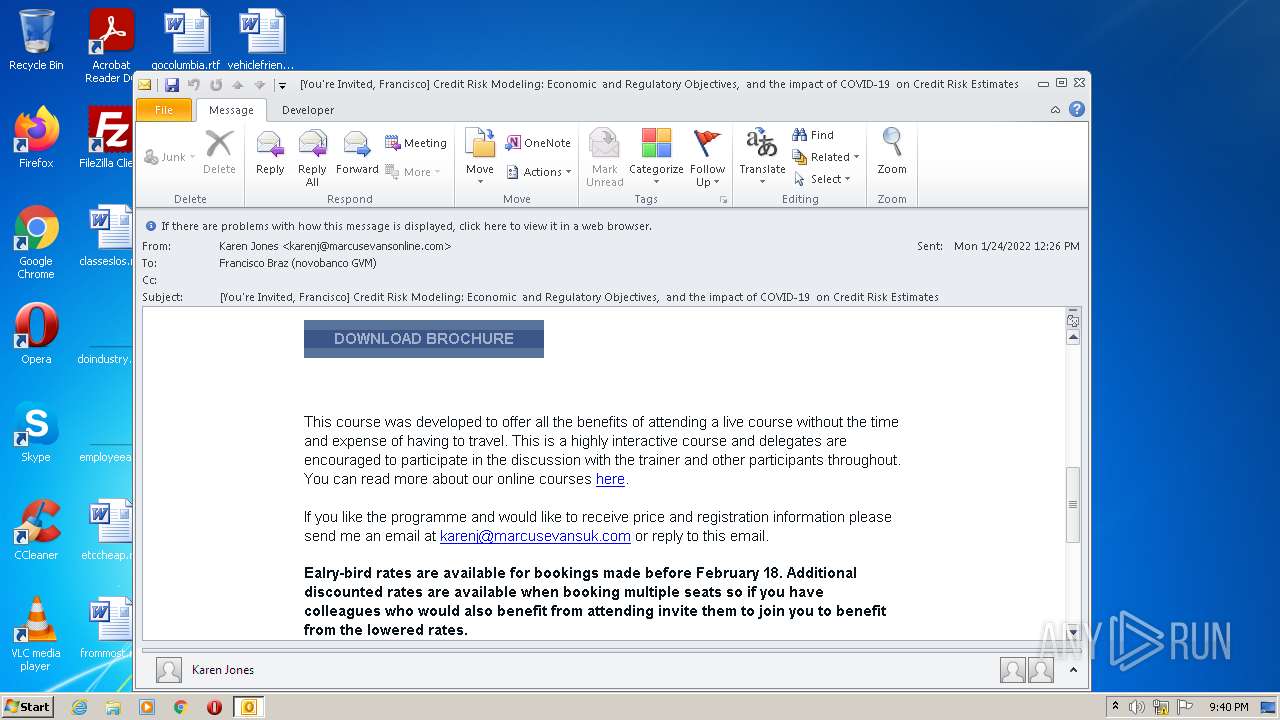
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 21:40:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | EDB60D0E4F058AFAE92CFCA62AD5D7DA |
| SHA1: | F3A78B035A205CE825933168F26A749BBB93E2AC |
| SHA256: | 7A57BE28A921E47E0B66A43F26868523BDA9FDECE51F0910CC91908DD4BE5BFA |
| SSDEEP: | 1536:g3f/AjlFaP3nmS/r4LXG+IgNH/P+kkaa1:m/A5QP3nQLXTFP+kkaa1 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2208)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 3612)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2208)
INFO
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2208)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 3380)
- AcroRd32.exe (PID: 3048)
Checks supported languages
- OUTLOOK.EXE (PID: 2208)
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 3612)
- AcroRd32.exe (PID: 3048)
- AcroRd32.exe (PID: 2152)
Reads the computer name
- OUTLOOK.EXE (PID: 2208)
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 3612)
- AcroRd32.exe (PID: 3048)
- AcroRd32.exe (PID: 2152)
Checks Windows Trust Settings
- OUTLOOK.EXE (PID: 2208)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 3612)
Searches for installed software
- OUTLOOK.EXE (PID: 2208)
- AcroRd32.exe (PID: 2152)
- AcroRd32.exe (PID: 3048)
Changes internet zones settings
- iexplore.exe (PID: 2424)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2208)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 3612)
Application launched itself
- iexplore.exe (PID: 2424)
- AcroRd32.exe (PID: 3048)
- RdrCEF.exe (PID: 436)
Reads internet explorer settings
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 3612)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2208)
Changes settings of System certificates
- iexplore.exe (PID: 2424)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2424)
Reads CPU info
- AcroRd32.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
49
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /o /eo /l /b /id 3612 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\e70d2545-142e-481c-9690-6340dd8c1b47.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
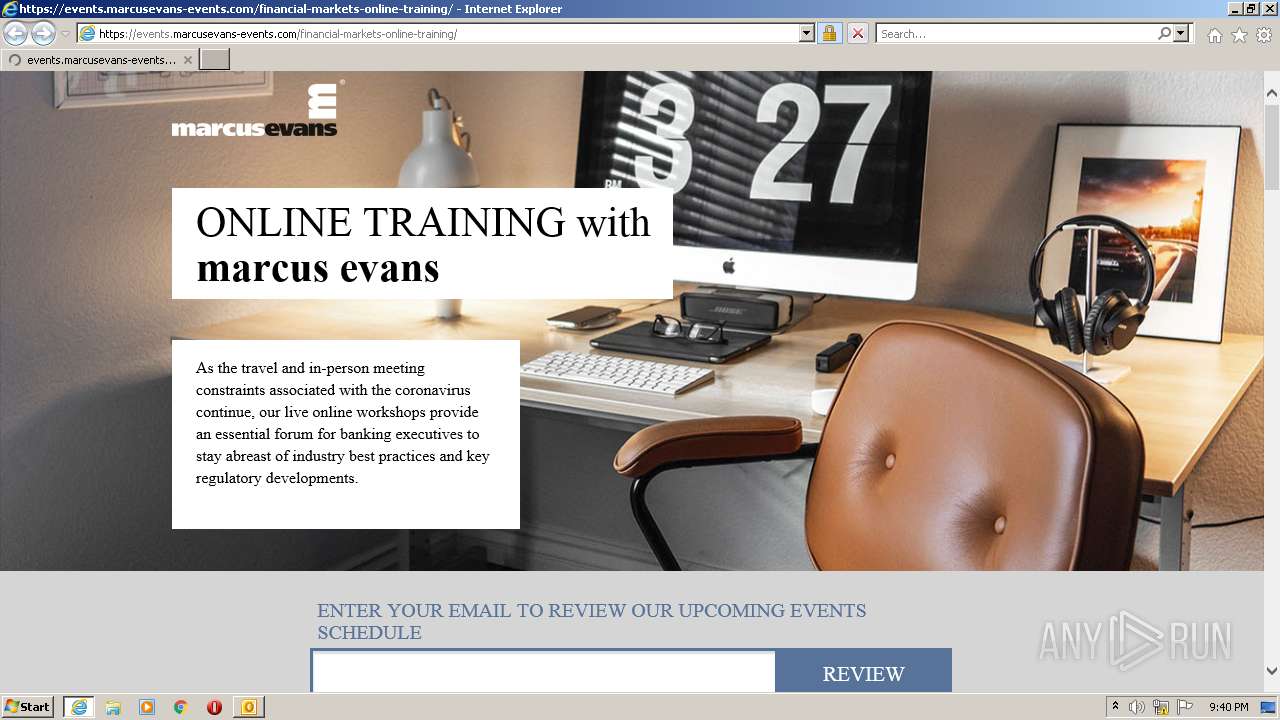
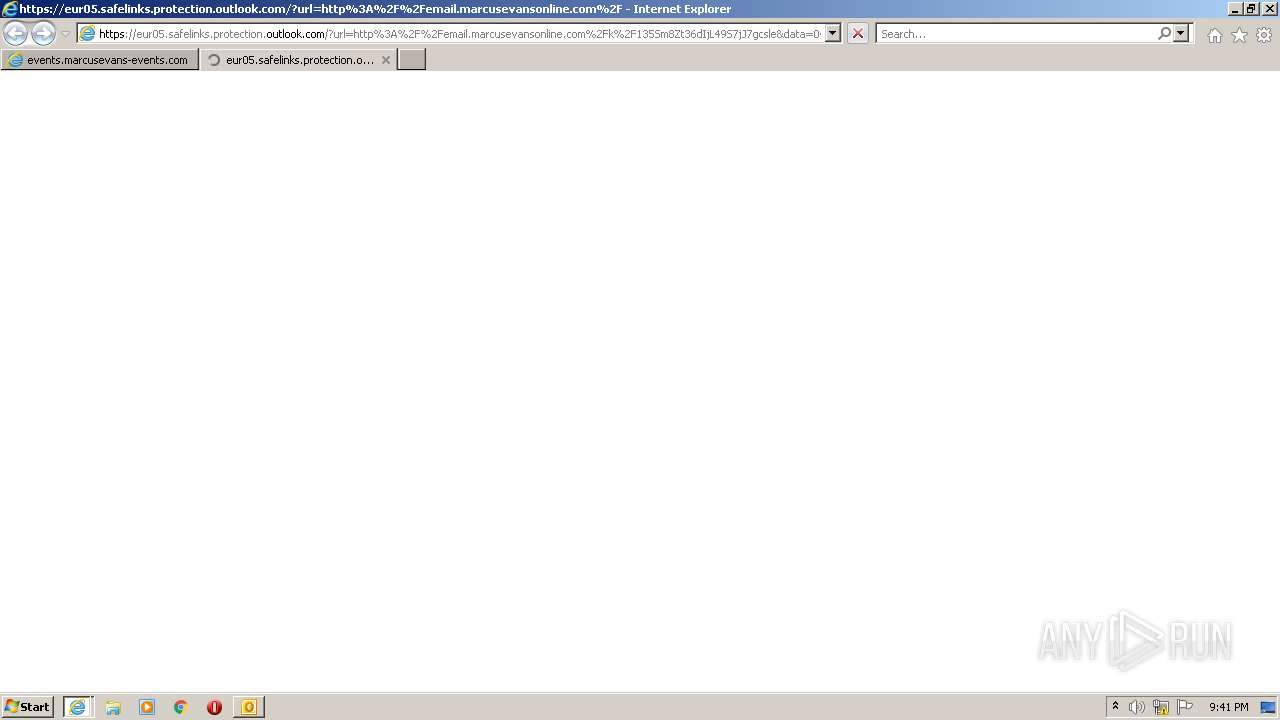
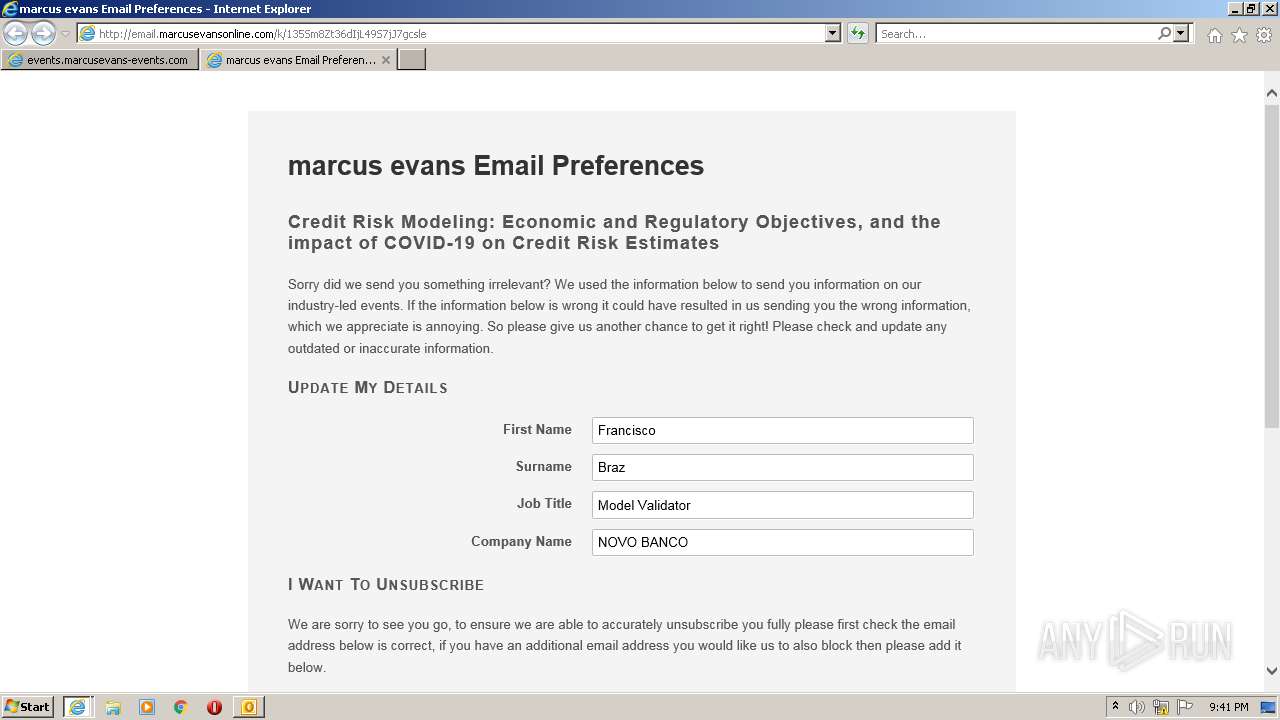
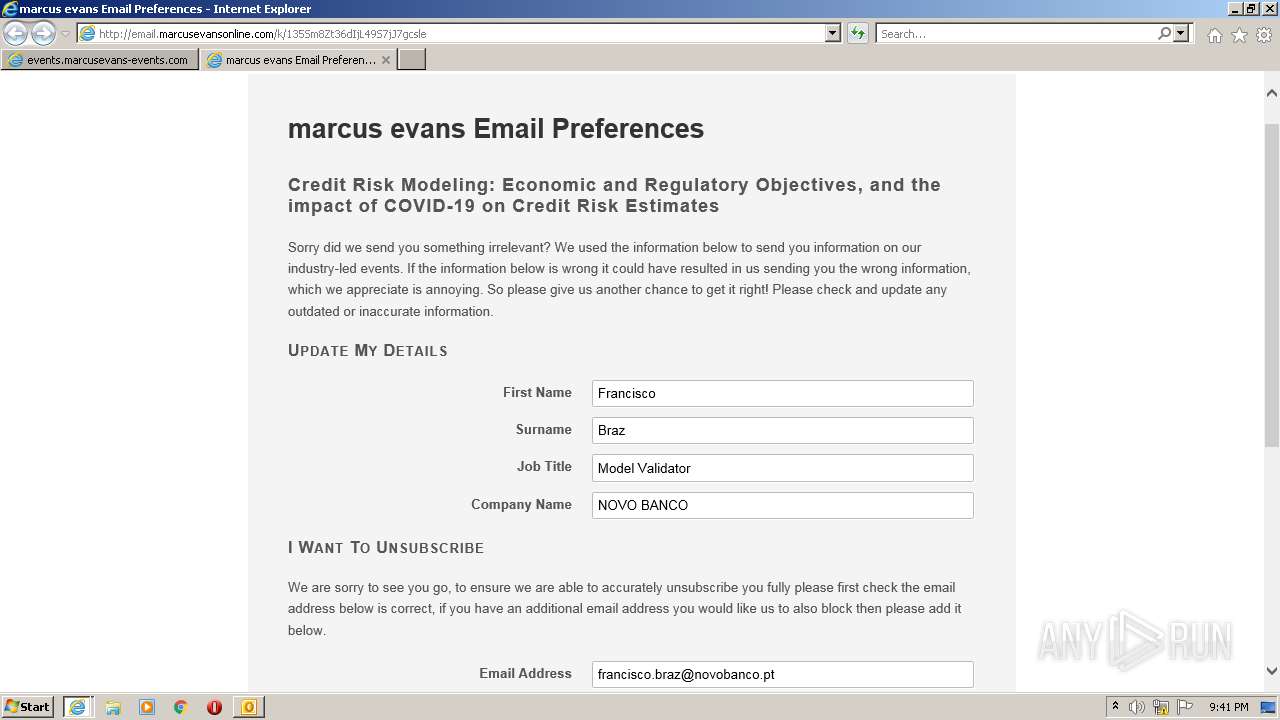
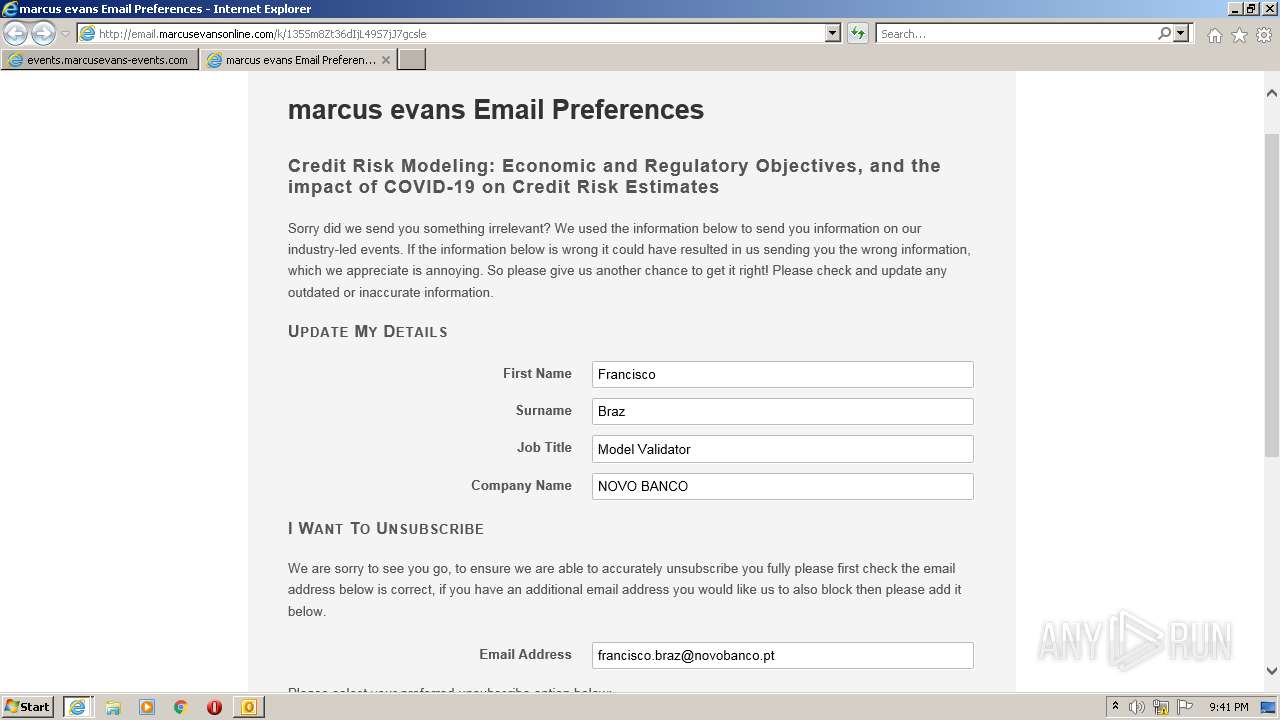
| 2424 | "C:\Program Files\Internet Explorer\iexplore.exe" https://eur05.safelinks.protection.outlook.com/?url=http%3A%2F%2Femail.marcusevansonline.com%2Fc%2F11kaagdNUwlc1yaEN0P9aT2LhGgG&data=04%7C01%7C%7C199d7b29a2fd4bc9e1d708d9df34cae0%7C10338048193a4298abea3596ae88b05e%7C1%7C0%7C637786240105882213%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C3000&sdata=Kk9rf1Tqqcwu1HYueMo6sp%2B15%2FvgXuwocHpsDHPBjlI%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3612 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3216 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3612 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2424 CREDAT:1578250 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2424 CREDAT:1119508 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3704 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1180,7119087600564542728,14479830397861562796,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14190477337137196951 --renderer-client-id=2 --mojo-platform-channel-handle=1188 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1180,7119087600564542728,14479830397861562796,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=7195393220904044530 --mojo-platform-channel-handle=1216 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 | |||||||||||||||
Total events
43 810
Read events
42 937
Write events
848
Delete events
25
Modification events
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
30
Text files
67
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR30F0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\me-virtual[1].png | image | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FC5A820A001B41D68902E051F36A5282_583A1E2AFEF9BD06B4904E4A0FC980E1 | der | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
91
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
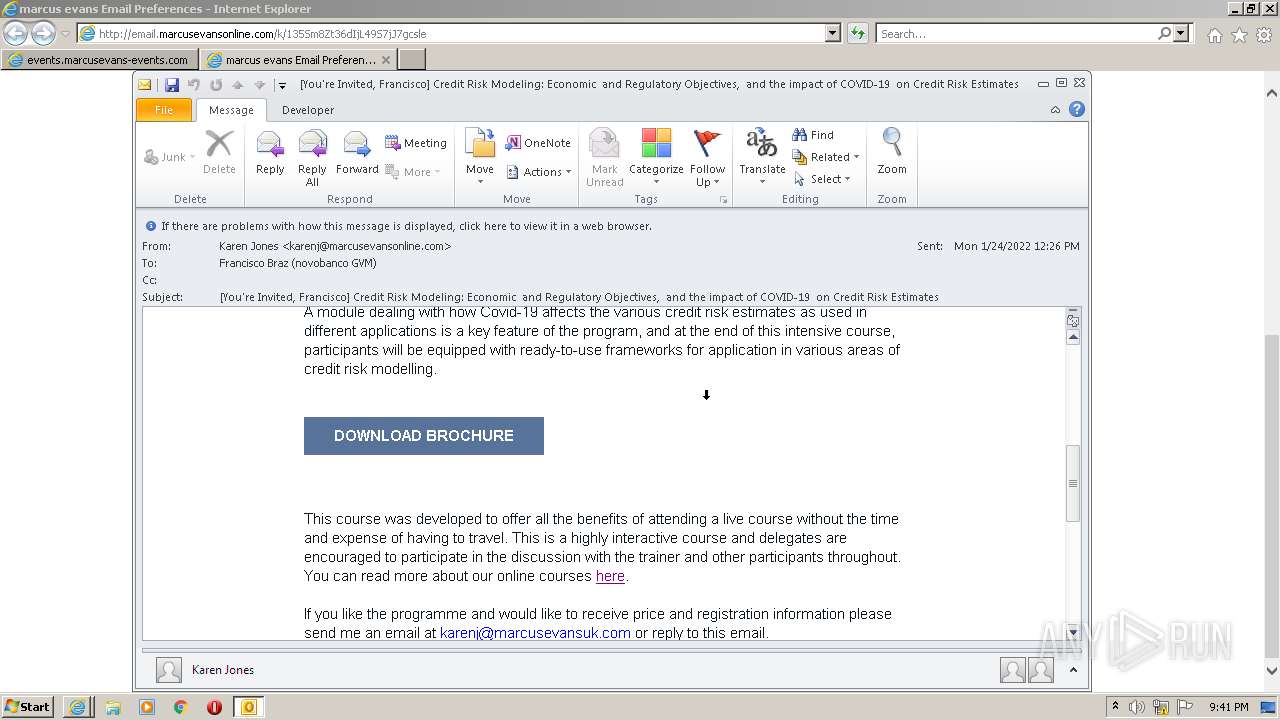
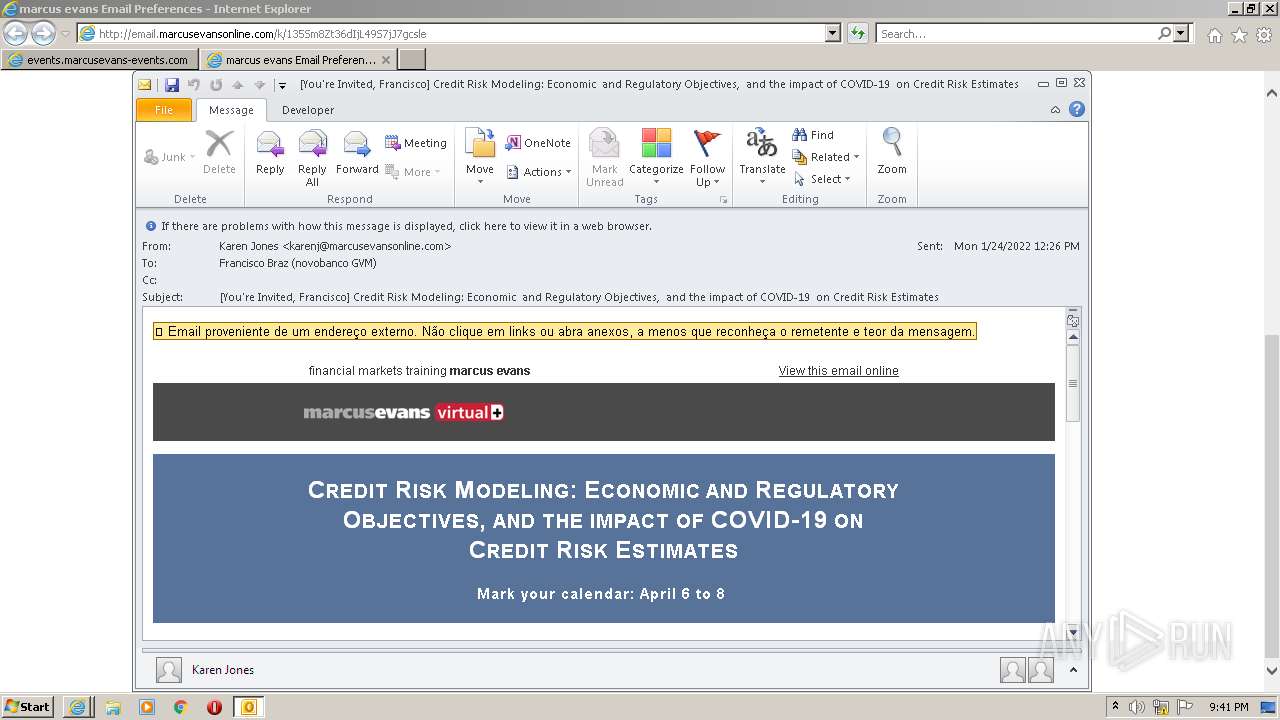
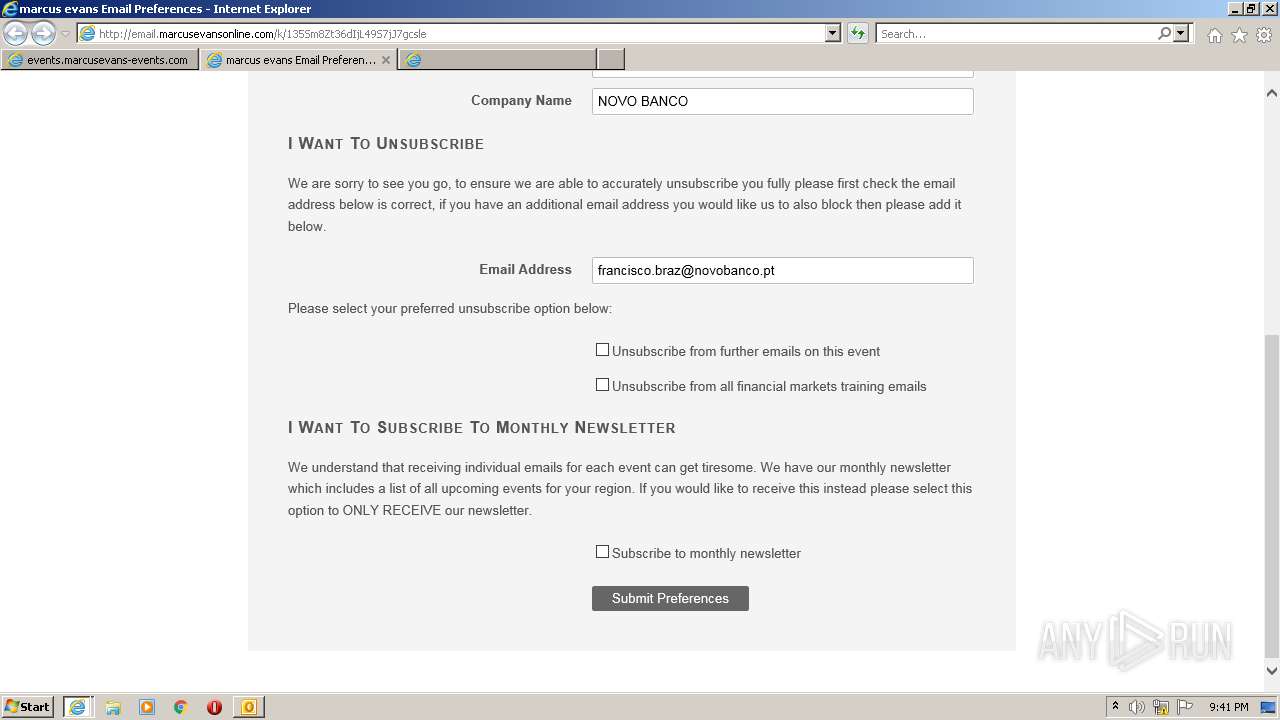
4076 | iexplore.exe | GET | 302 | 143.204.98.92:80 | http://email.marcusevansonline.com/c/11kaagdNUwlc1yaEN0P9aT2LhGgG | US | — | — | malicious |
2208 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2208 | OUTLOOK.EXE | GET | — | 143.204.101.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | — | — | whitelisted |
4076 | iexplore.exe | GET | — | 216.58.212.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | — | — | whitelisted |
2208 | OUTLOOK.EXE | GET | 200 | 143.204.98.92:80 | http://email.marcusevansonline.com/i/amf_marcus_evans/project_7949/me-virtual.png?size=400x0&w=BQlKjgwqiCQuqLLulsdms20rlRho | US | image | 12.7 Kb | malicious |
4076 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
4076 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
4076 | iexplore.exe | GET | 200 | 143.204.101.123:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 108.156.253.131:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEALUmJrgzLNcCSeJRfwdbek%3D | US | der | 471 b | whitelisted |
2208 | OUTLOOK.EXE | GET | 200 | 18.66.242.155:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2208 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2208 | OUTLOOK.EXE | 143.204.98.116:443 | t.msgf.net | — | US | shared |
2208 | OUTLOOK.EXE | 143.204.98.92:80 | email.marcusevansonline.com | — | US | suspicious |
— | — | 143.204.101.123:80 | o.ss2.us | — | US | malicious |
2208 | OUTLOOK.EXE | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
2208 | OUTLOOK.EXE | 13.225.84.92:80 | s.ss2.us | — | US | malicious |
2208 | OUTLOOK.EXE | 108.156.253.92:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
— | — | 104.47.17.92:443 | eur05.safelinks.protection.outlook.com | Microsoft Corporation | US | suspicious |
4076 | iexplore.exe | 104.47.17.92:443 | eur05.safelinks.protection.outlook.com | Microsoft Corporation | US | suspicious |
4076 | iexplore.exe | 143.204.98.92:80 | email.marcusevansonline.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
email.marcusevansonline.com |
| malicious |
t.msgf.net |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
s.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
eur05.safelinks.protection.outlook.com |
| whitelisted |