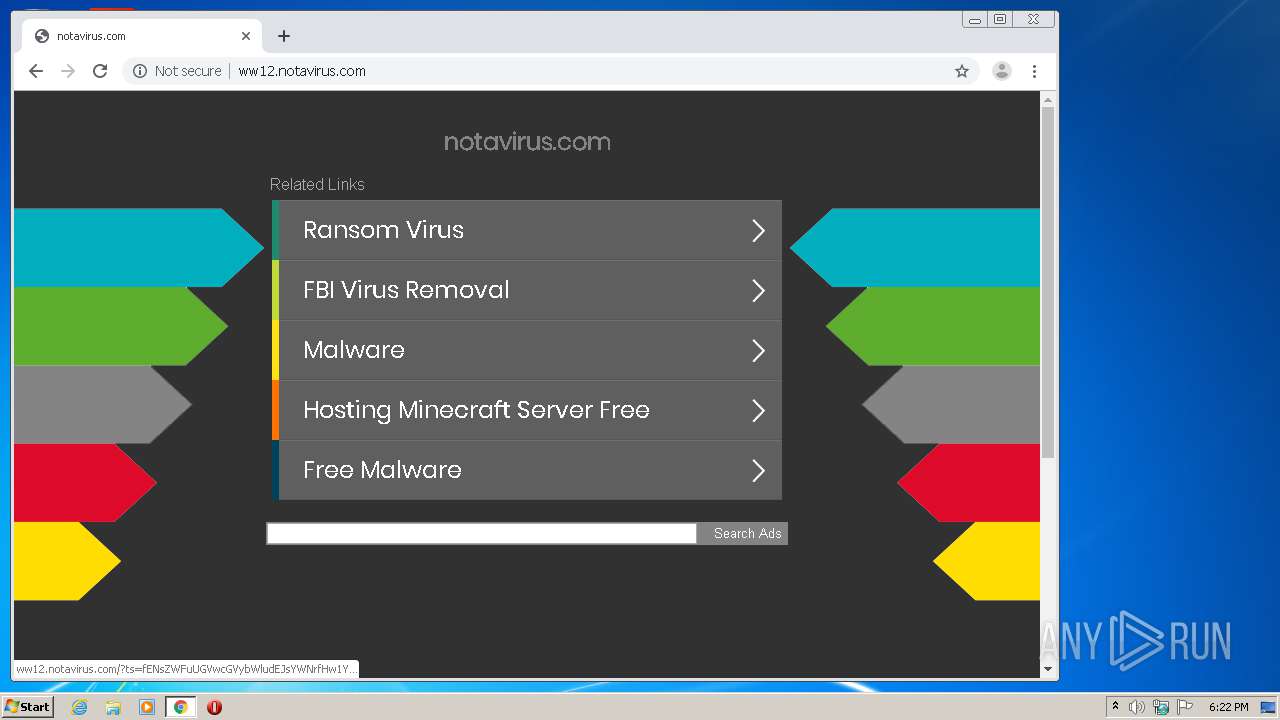
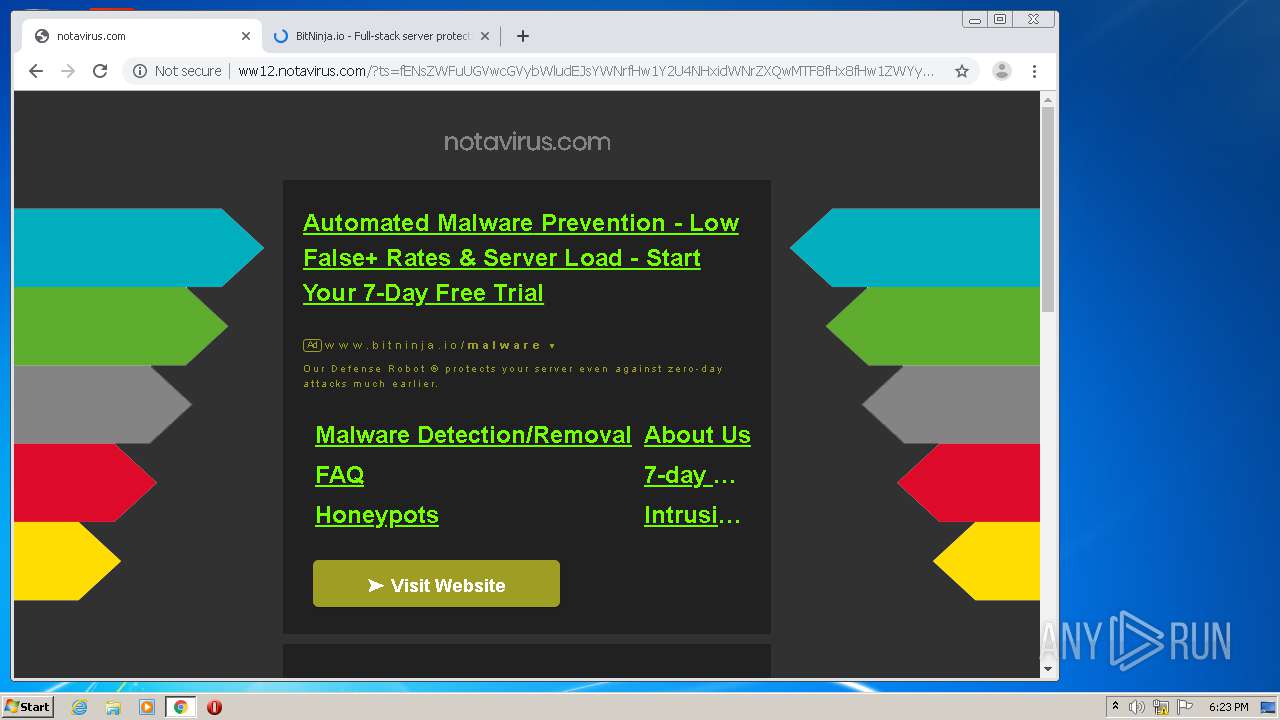
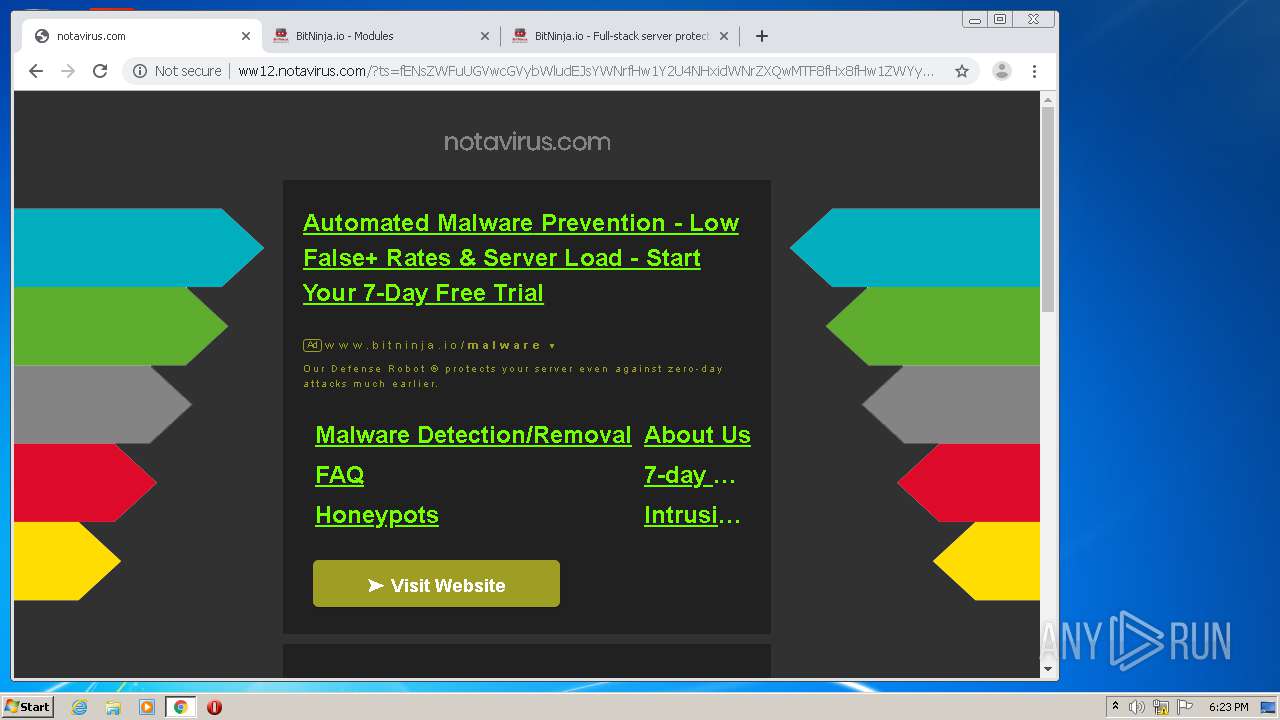
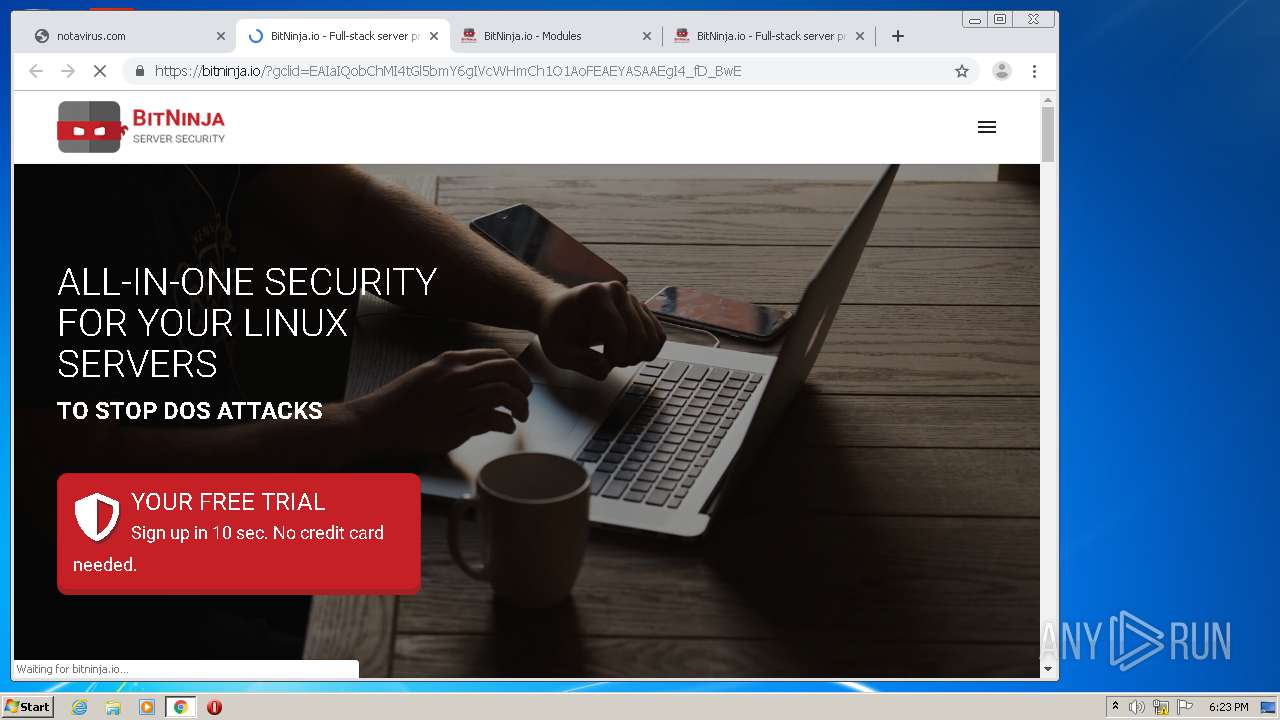
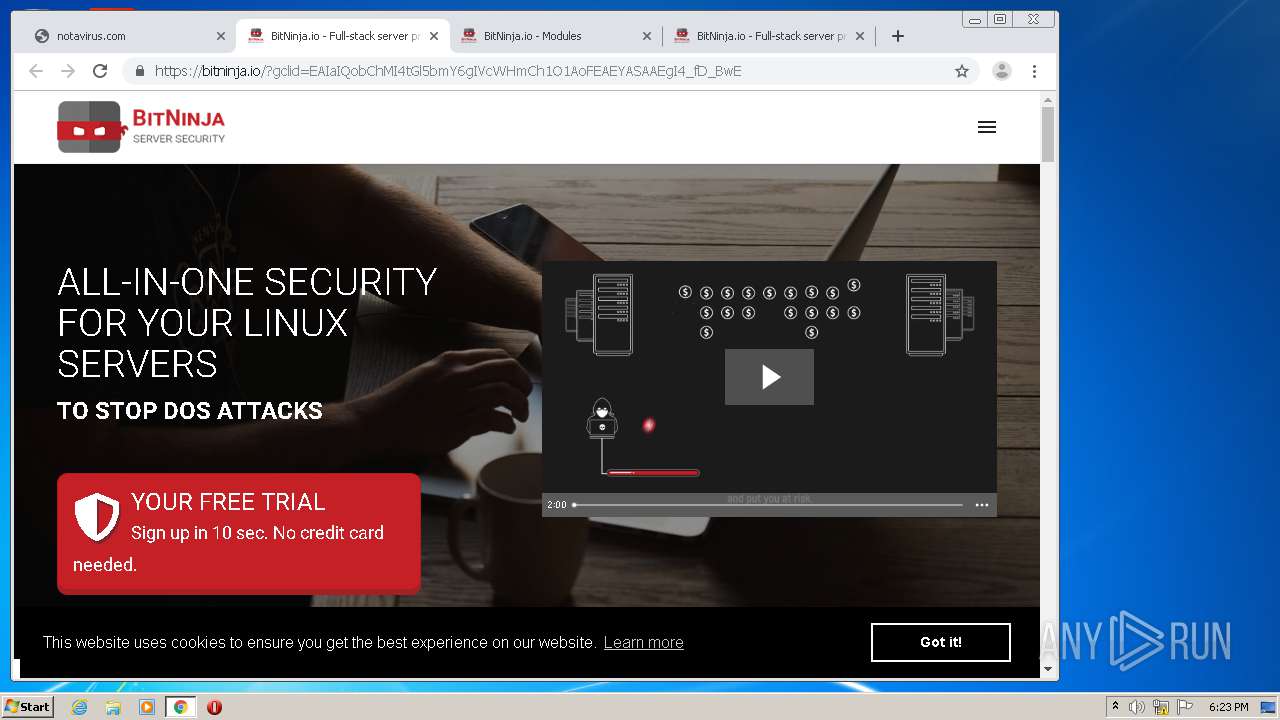
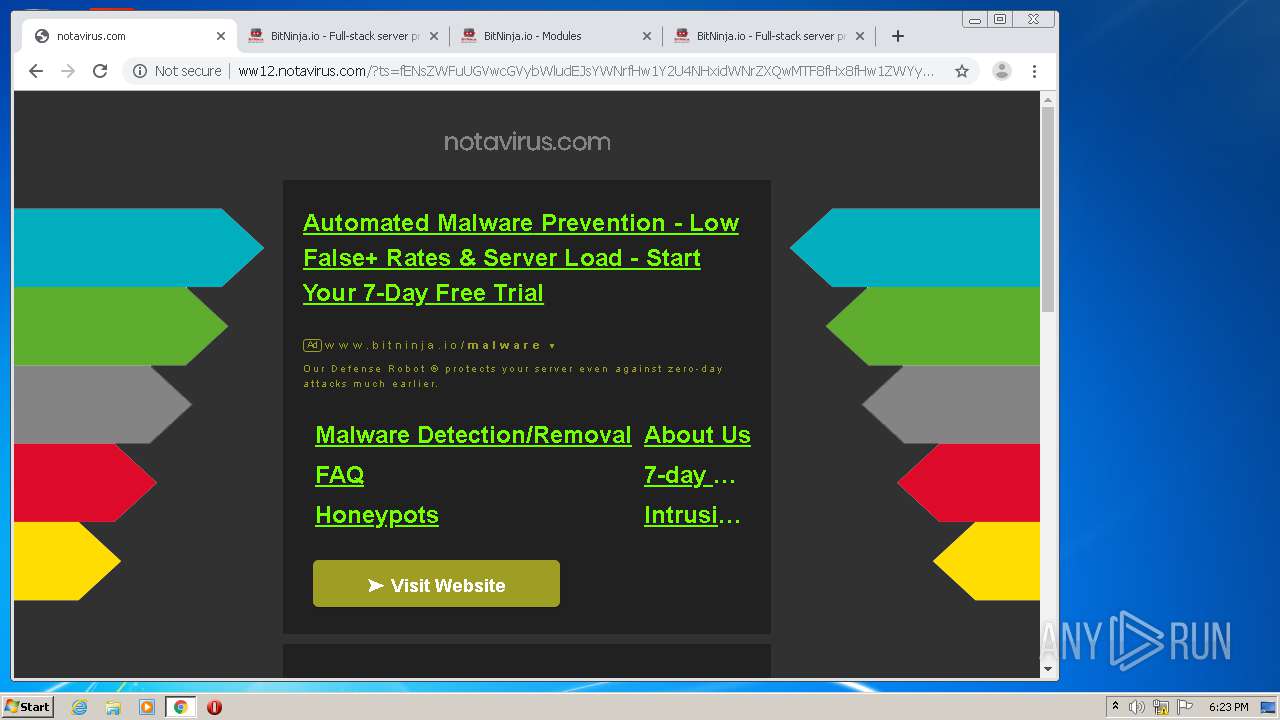
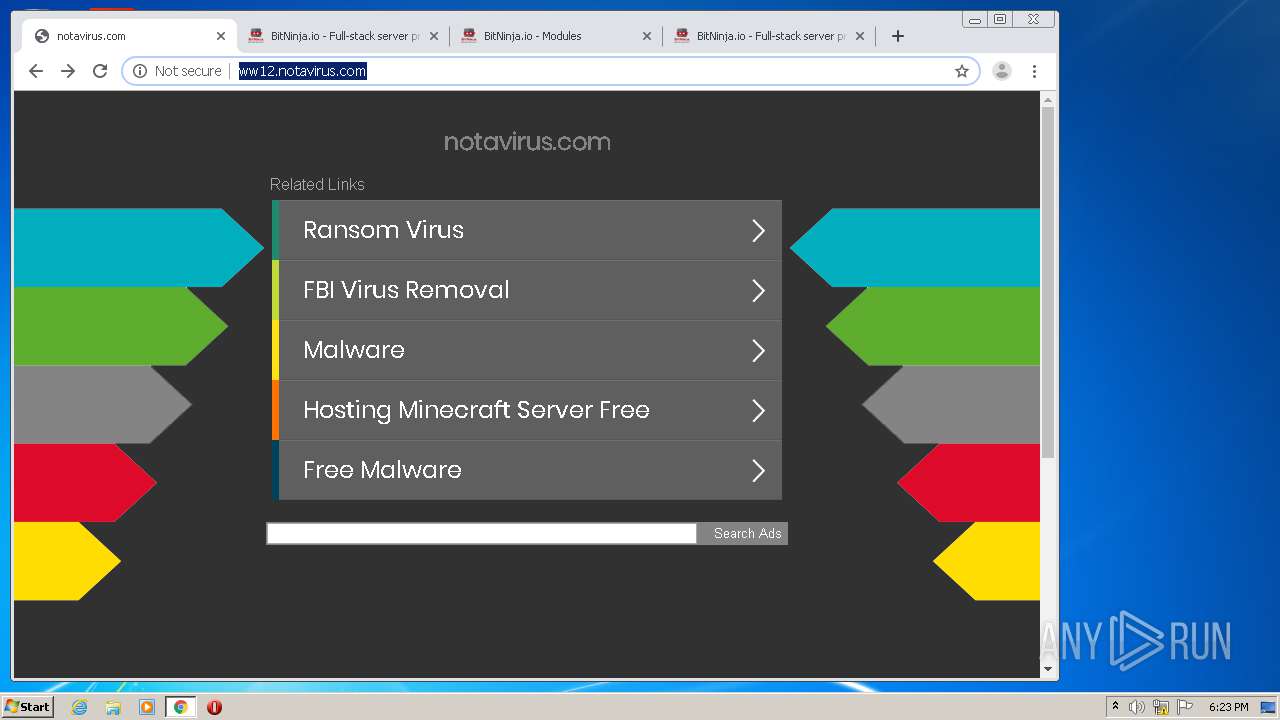
| URL: | http://www.notavirus.com |
| Full analysis: | https://app.any.run/tasks/f005881d-e691-421f-b129-545b7d047fa4 |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2020, 17:21:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D189670C9730C6FD51571F92FE0DACB5 |
| SHA1: | 36BA974DCC55E3F959910A2841AC03AB688A9BF6 |
| SHA256: | 7A560356547E010024F0060805A346443EDD3B7EBD2180AE90DE4BF147468429 |
| SSDEEP: | 3:N1KJS4+iyQzn:Cc4+JQzn |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 3500)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1660)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1324)
Reads Internet Cache Settings
- iexplore.exe (PID: 1324)
- iexplore.exe (PID: 1308)
Application launched itself
- iexplore.exe (PID: 1324)
- chrome.exe (PID: 1660)
Creates files in the user directory
- iexplore.exe (PID: 1308)
Reads the hosts file
- chrome.exe (PID: 1660)
- chrome.exe (PID: 3500)
Reads settings of System Certificates
- chrome.exe (PID: 3500)
Manual execution by user
- chrome.exe (PID: 1660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
40
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6843263989970976955,17523198843373620547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5766138382289152518 --mojo-platform-channel-handle=3720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6843263989970976955,17523198843373620547,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13961123377957888897 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6843263989970976955,17523198843373620547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16778055542388382085 --mojo-platform-channel-handle=3432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6843263989970976955,17523198843373620547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12604049713438943062 --mojo-platform-channel-handle=4496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6843263989970976955,17523198843373620547,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18307743920741541613 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1324 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
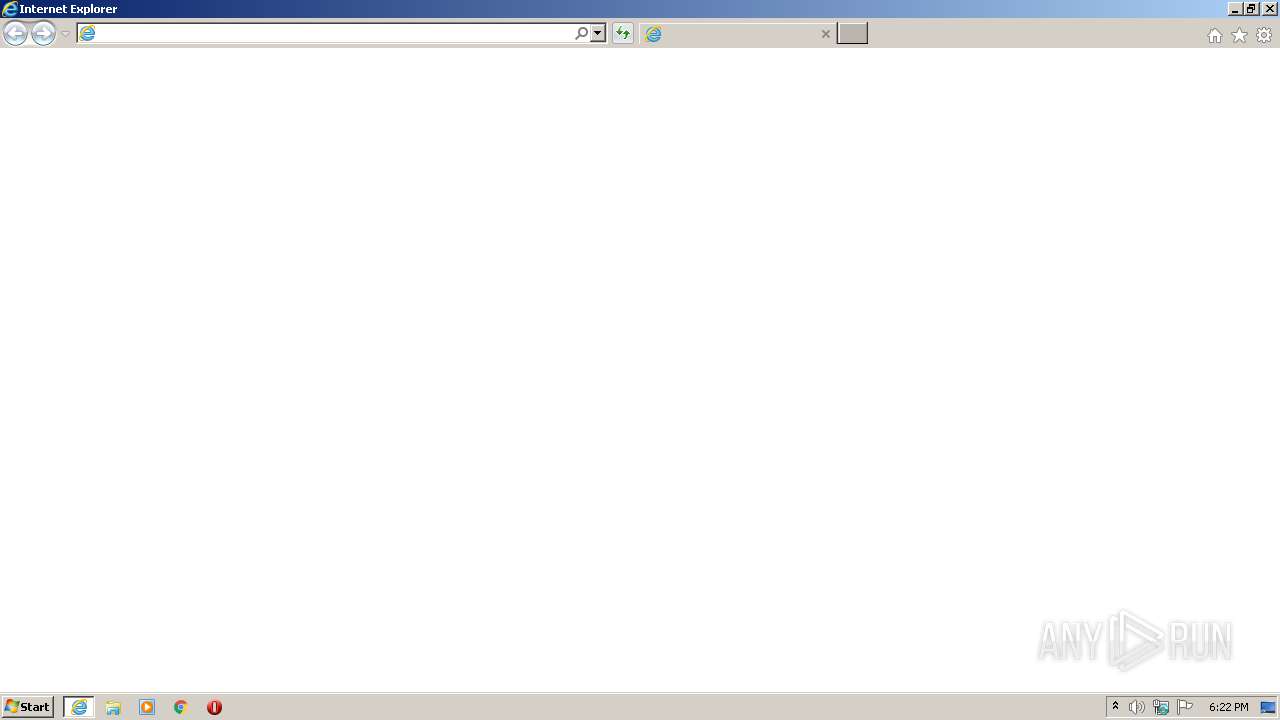
| 1324 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.notavirus.com | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6843263989970976955,17523198843373620547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5404006923984736975 --mojo-platform-channel-handle=2028 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6843263989970976955,17523198843373620547,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10510582456108489906 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
852
Read events
703
Write events
140
Delete events
9
Modification events
| (PID) Process: | (1308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3898384302 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30820738 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
152
Text files
298
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1308 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QLD9558I.txt | — | |
MD5:— | SHA256:— | |||
| 1308 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\P02Z61U9.txt | — | |
MD5:— | SHA256:— | |||
| 1660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EF23A4B-67C.pma | — | |
MD5:— | SHA256:— | |||
| 1660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3cdff790-413f-483c-847c-bcc42d47af17.tmp | — | |
MD5:— | SHA256:— | |||
| 1660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1308 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2ATPO383.txt | text | |
MD5:— | SHA256:— | |||
| 1660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169a9f.TMP | text | |
MD5:— | SHA256:— | |||
| 1660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
109
DNS requests
75
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
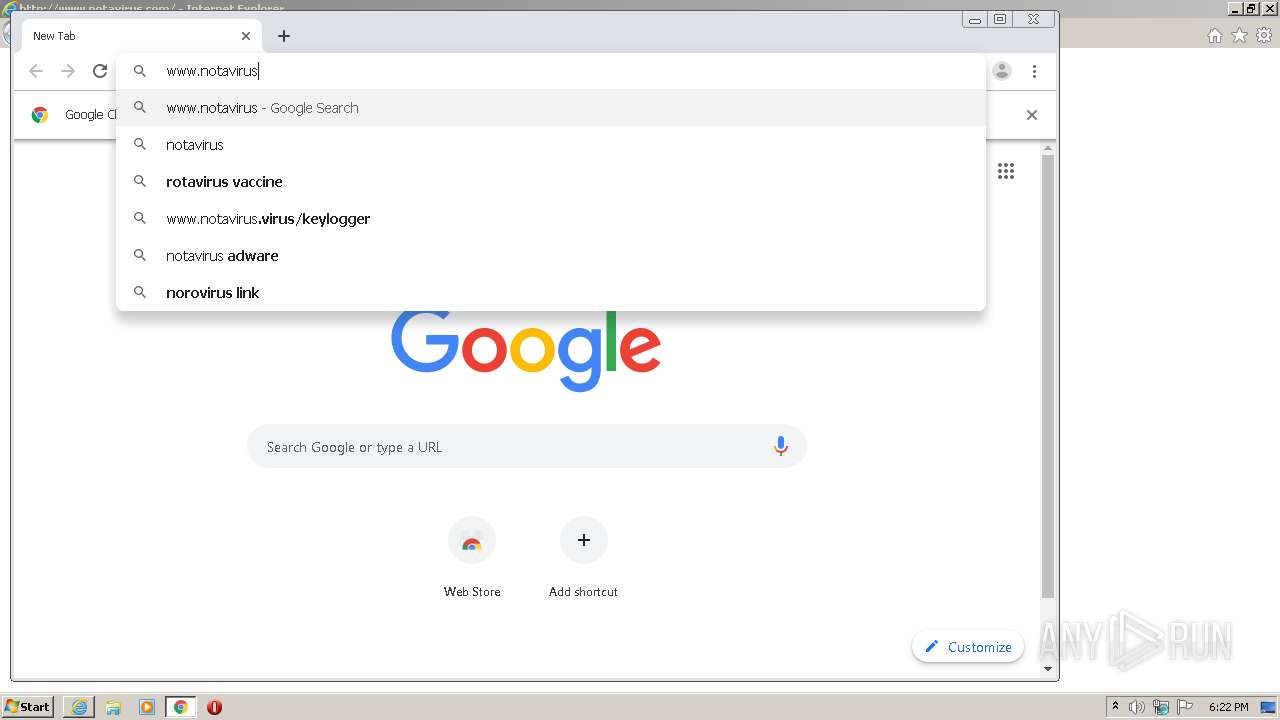
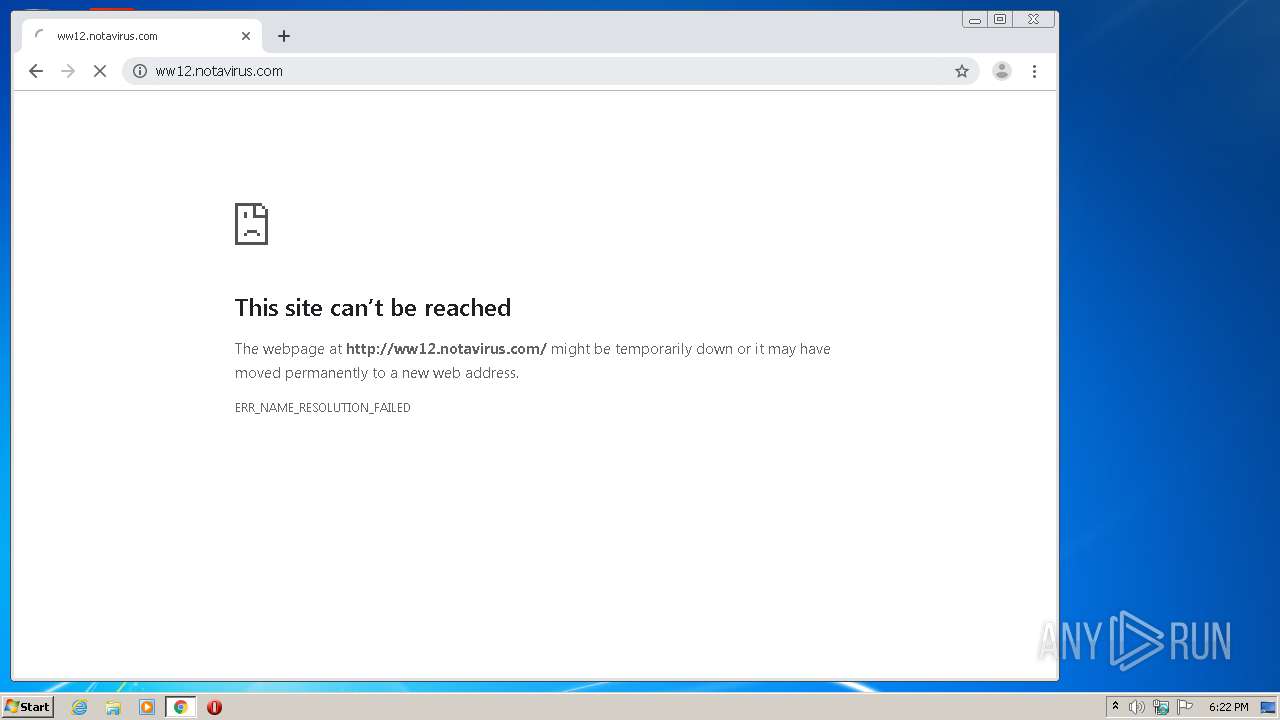
1308 | iexplore.exe | GET | 302 | 67.227.226.241:80 | http://www.notavirus.com/ | US | — | — | malicious |
1308 | iexplore.exe | GET | 302 | 173.192.101.24:80 | http://infopicked.com/aS/feedclick?s=tmxvfbadWlkLtgv3D3v8v4g5sn6yaoKk_XRbjSsHVgKIUYrw22n5AzZTiQMvAXg5dnQ3qd4H7z-pbTnNK1c9Rwa8tw24WWMwdntfDaXc4Shj62ec1JCuDABQrzv8wYASqWfap4yUt_iPH1TzciB1Qg6AZUDRz9bjOEX4iGGchU3npU_NV_9qTbixusqCoFJPrAhPdGuFeL_mJCtyjPqzPDY8jhlb395zXVn9GzE8LokkdLudYU8jqIY1d2kTdJJqGkEnHv9rWEddE0Mi3DFcLct0auT_ZLi5PTXehX6g8mWbmIGdpzl6hSzjjvnRjaf9wYN4ccDOwqOMTtmetdvmKz9oyYMHzjG3aVfyD9mSet23rE486RQjnWzDb9neovD2qtuU8ei9QIQhWG4xyWpyhM3WvCeXiQ5hWlVyTZ5lz3pNGL882hg4BWoZaz6QnqhbkHSCFSC0E87cAiSQHkTPhkXyrpdHHbQllv9ZgKf-ZPsegOa6McAs8iExx-St54exuZuvbkvWfv1z6AUhiHvIcB1edki9hF5NxowcRlUNXdDXr-xzG1OoO49XFYNQ5kwZp8oIi042Bl-w-3h5xI3NTOZDWylpXgKm8Ky1xczMz471Z11iwLle9BmNdpmwxq0EiFAZP4N0nRM9kS4XhoqXiYb7r245xIi-HBKfDP23i0agMeS2bPANmNzl9NO033-vcxkPONGf_S51JSZZ4RkeV41znknMtmwZMYvNm9VKaYcnGfIkq_HnU7Ove95J9F_q44sDdOAdNJDr7wS3dAtsPd-V9xlxgXls3c0cBxgUUuNiBQIRCO5D7y-ViFqKx9kP52Dqu5FQ4IavGIvy1SrwsQNfbO7rx54NbRojj848mm9ruyTWhTKnJC1sk_MB5yP_TN00v_g5Gaeq08pkj6pSFVzRtjECHC8a9YCBmz7wFsr25rQK_7FpWy85iqcp_I8dH_h7q5Mg_P_ma6MpTx581SnB2nJZfAI2JhhukrZ59J7vnXy-tDI2Z9l6zmwxYmZRLjddtNgvdsvFKwAFgloip8CvcBzJl95CtAF7raPvj3QRetAOnX_k-JJxgFogmf9FUrAcFbkKTtagngA9SL4TWj_LFKaQfdCIV7zGDkXThF6fxRzXxISqKBRlpSBcG3GiFNYnRtQwe8YlxkcDKCB3vlhEKV_7TPQjPHs3oe2OB7-80_kbmdxcPpqZJkCIgEaRbv6ZCDdfz7qb-l33Y-CYzZ9_6BWp1Yzz4lhYQ1URXs0x_Dt6Jw9X-F4WIUeeroEfM_G5VwYLK9rpYDhXd027Klx_HS2HdDiReiBj5UOKS9Kf2zmUw5bzFL1_iQJ1ZHLdb325BduLUQdIhUCVWOZO_pinVCVYRoc9OYwwqJPWDKywKIdiWa3SoNiXjsXFmewYSoblf7MzPqSpFqc-ErRdj6mJBwe8hUeuBlcIqqbi4GLdAM6fo_EBoQ | US | — | — | whitelisted |
1308 | iexplore.exe | GET | 302 | 173.192.101.24:80 | http://p237996.infopicked.com/adServe/domainClick?ai=cfld0oJoDce2NSghyY4oPu3x1wJQuyt72aUQOR7RzsAH4c6rKhyITCEWv4AX6X808LLFpb65qpODr7M2i7UMgQK8sczUyG_FAz4mvdD0n7T5PQC-Ns7H0UP4ihGJaOYX5Yl0uCS11v4GvLcNuFljMHJTvUaQj7Tsbv6ZCDdfz7rSX0JRZpFwqHsmXgeLf7LqvFmvrCqPGTjrav71D4_XgN9TUV18JhC1OzpFP3ASGnknGyqHRL812rYqkP74YUqqJmCCRov00lFk38X7NSW9FaHwd9wVvpvaQxvgOjvL5v4N7Ssv4XmSKZZXpgFk2j54e8rROKEv96SS-CpzjmCCRSkbjTnD0JcoWrkuEiZvcEKC67YP62osaVKsh-dcjcrESTgOqlJKSVUW0YeVoTdAMXo_8JgIlG3qFgRrt2Me9ti1vLTFJQWbu3Pou3Htdlh1iqOsN-tpzU2U0rKS-ABG52WSQsQHXjql&ui=tmxvfbadWlkLtgv3D3v8v0sRZ2xs6kJzLWXp3on882KiNKxwAofaTKxDISSKop4PkJf_GpxWep5qLlnG4P52D48MnI2hWFW1VXTr-4rBf5OCnCJhrPQvkqZuFgnXo3DehzVRNhKeUPA&si=1&oref=4f6b3b53c9dec26c061cb3d1210e2593&rb=nmu0EXDzm40&rr=1&isco=t | US | — | — | suspicious |
3500 | chrome.exe | GET | 302 | 67.227.226.241:80 | http://www.notavirus.com/ | US | — | — | malicious |
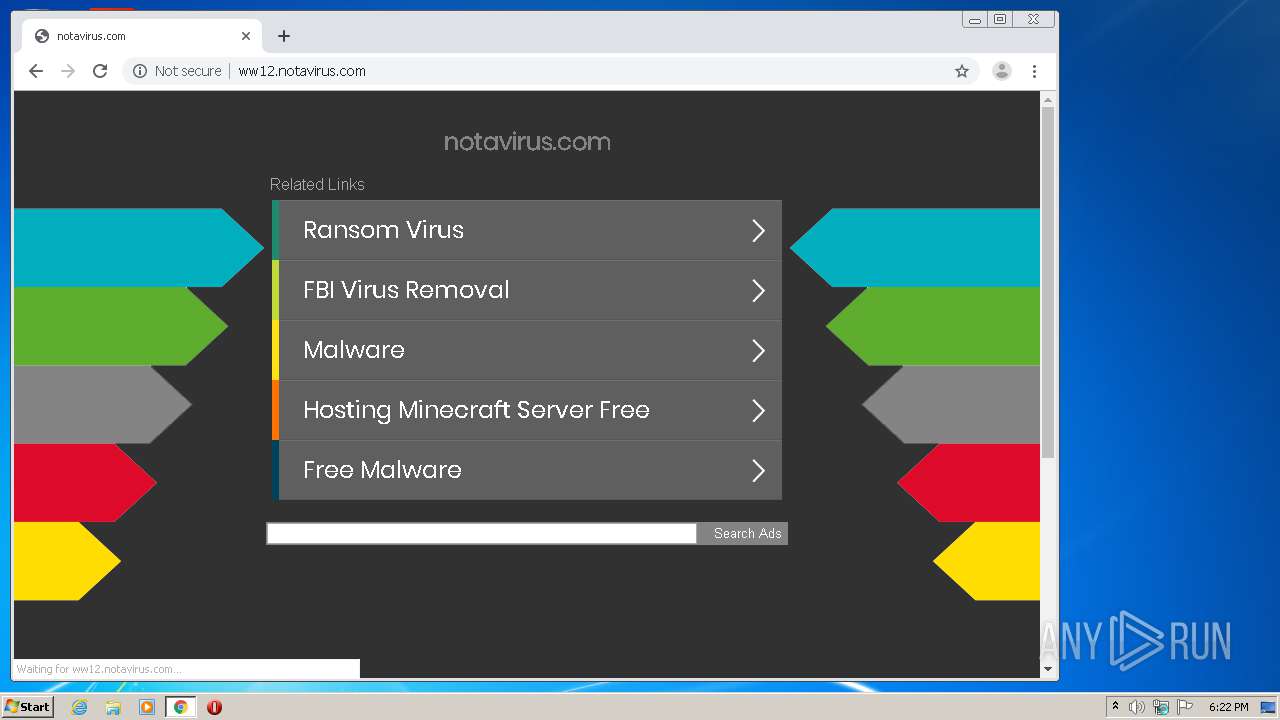
3500 | chrome.exe | GET | 200 | 54.72.9.115:80 | http://ww12.notavirus.com/favicon.ico | IE | — | — | malicious |
3500 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 539 b | whitelisted |
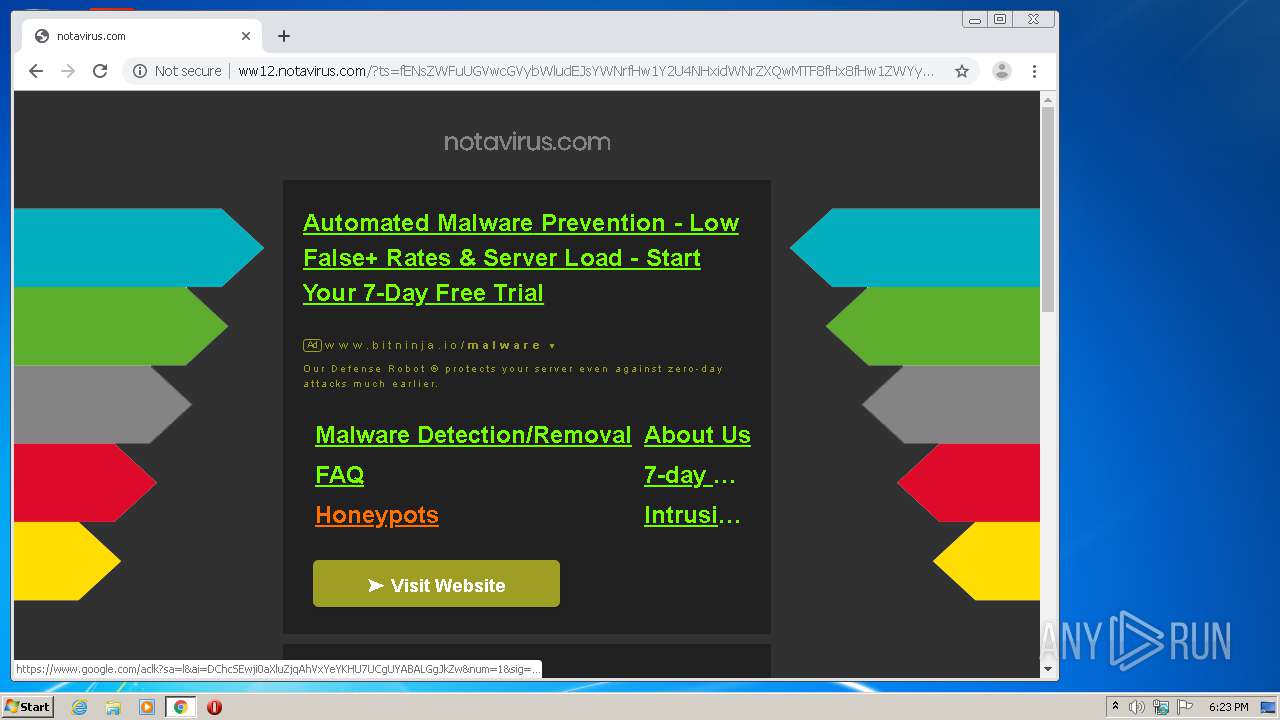
3500 | chrome.exe | GET | 200 | 216.58.210.4:80 | http://www.google.com/adsense/domains/caf.js | US | text | 57.1 Kb | malicious |
3500 | chrome.exe | GET | 200 | 67.225.218.50:80 | http://parking.parklogic.com/page/enhance.js?pcId=12&domain=notavirus.com | US | html | 2.17 Kb | suspicious |
3500 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 544 b | whitelisted |
3500 | chrome.exe | GET | 200 | 54.72.9.115:80 | http://ww12.notavirus.com/ | IE | html | 4.33 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1308 | iexplore.exe | 173.192.101.24:80 | infopicked.com | SoftLayer Technologies Inc. | US | suspicious |
1308 | iexplore.exe | 66.42.86.241:443 | etracking.pro | Fire2Wire | US | unknown |
1324 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3500 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3500 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3500 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1308 | iexplore.exe | 67.227.226.241:80 | www.notavirus.com | Liquid Web, L.L.C | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.notavirus.com |
| malicious |
infopicked.com |
| whitelisted |
p237996.infopicked.com |
| suspicious |
etracking.pro |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3500 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |
3500 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |
1072 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3500 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |
3500 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |