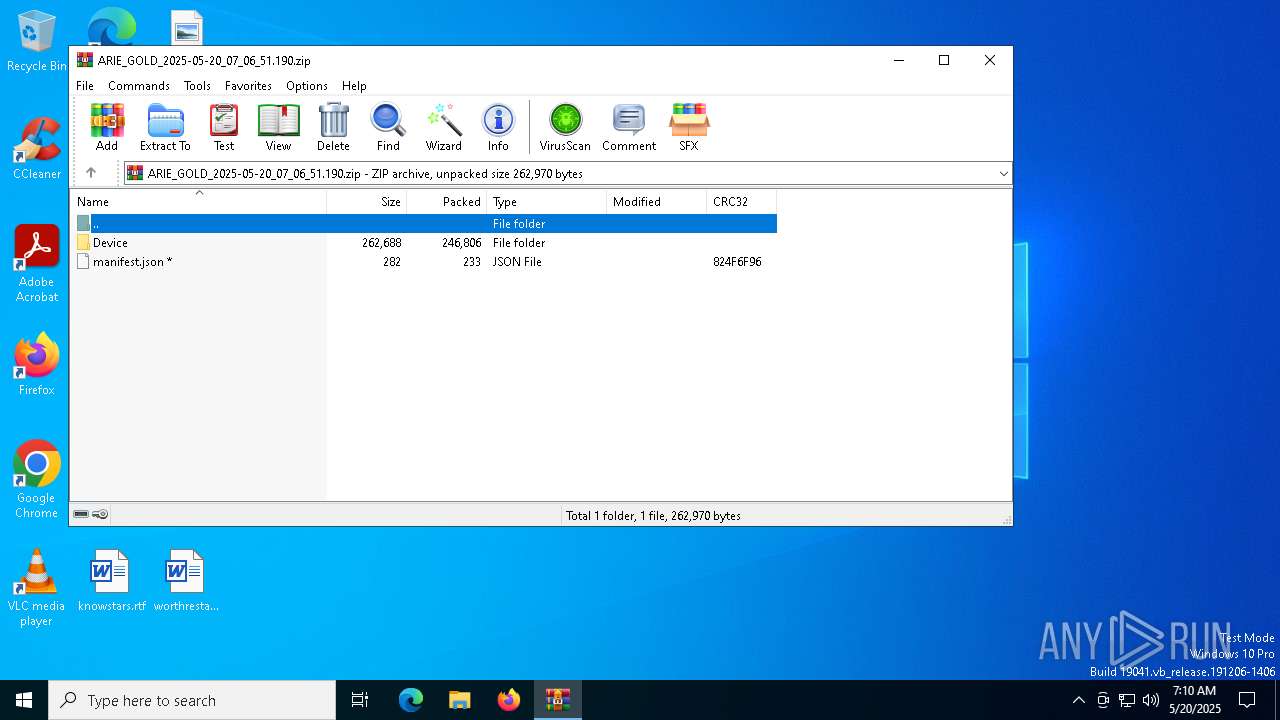
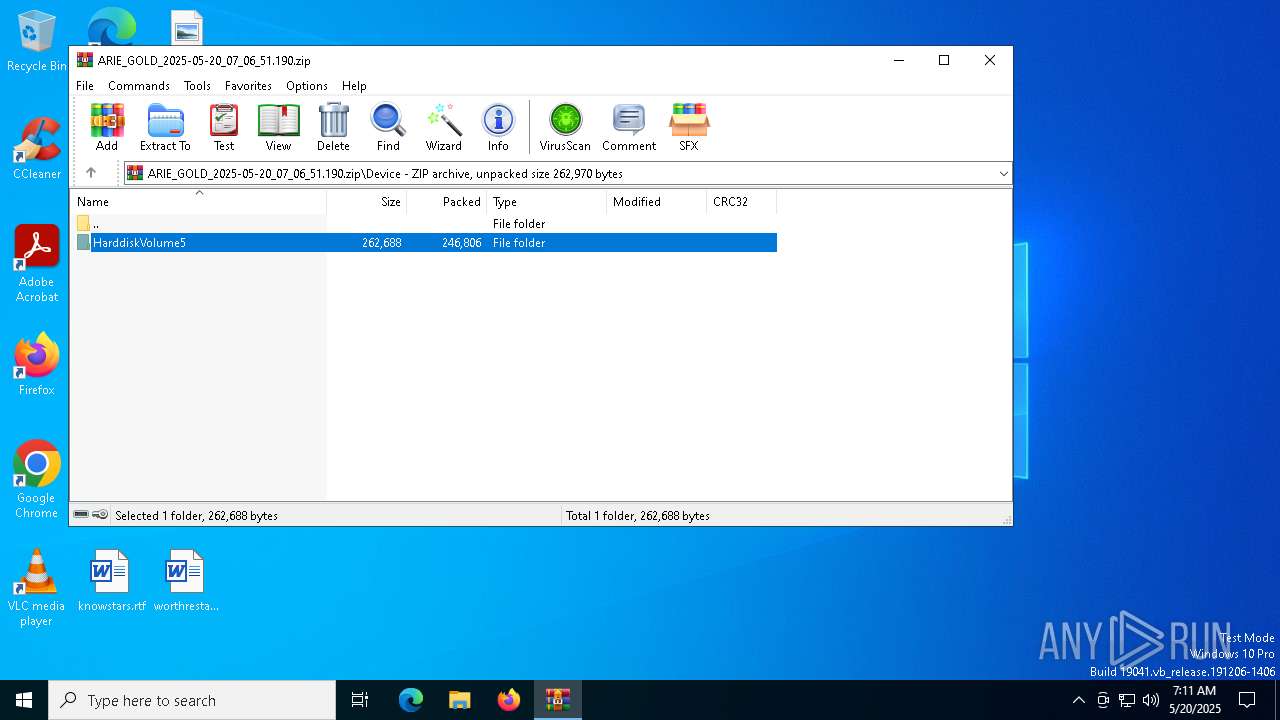
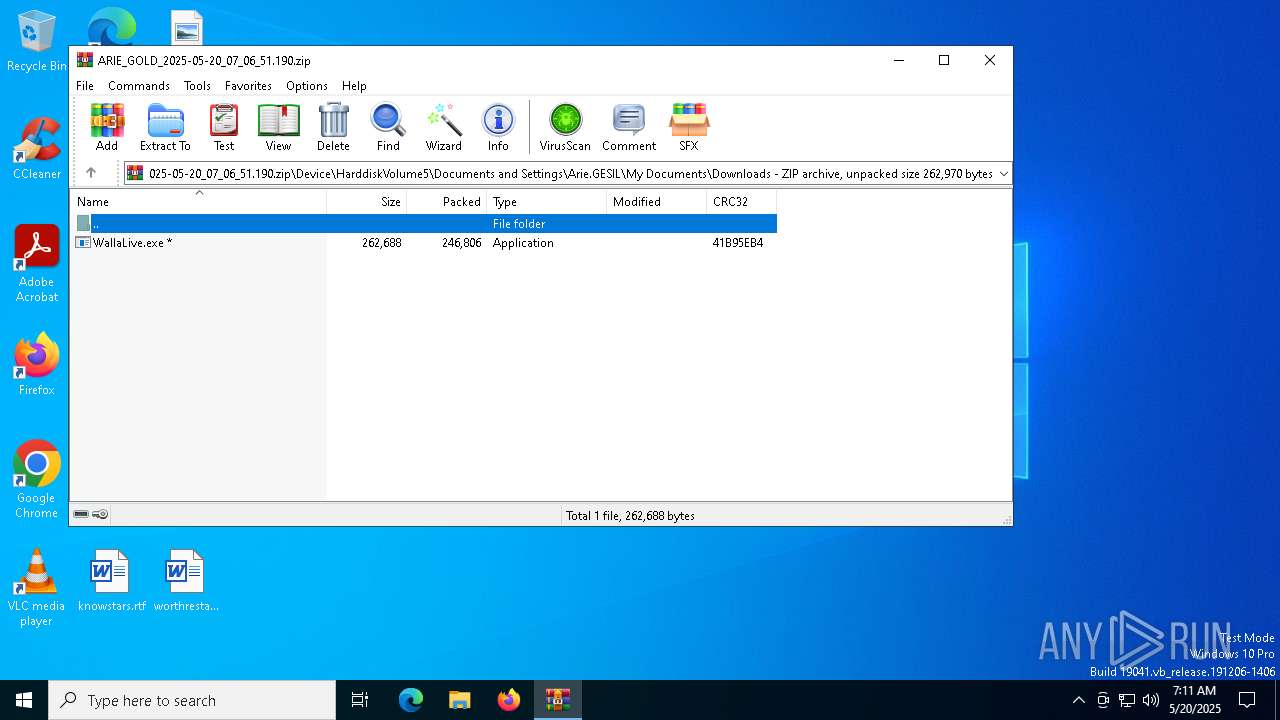
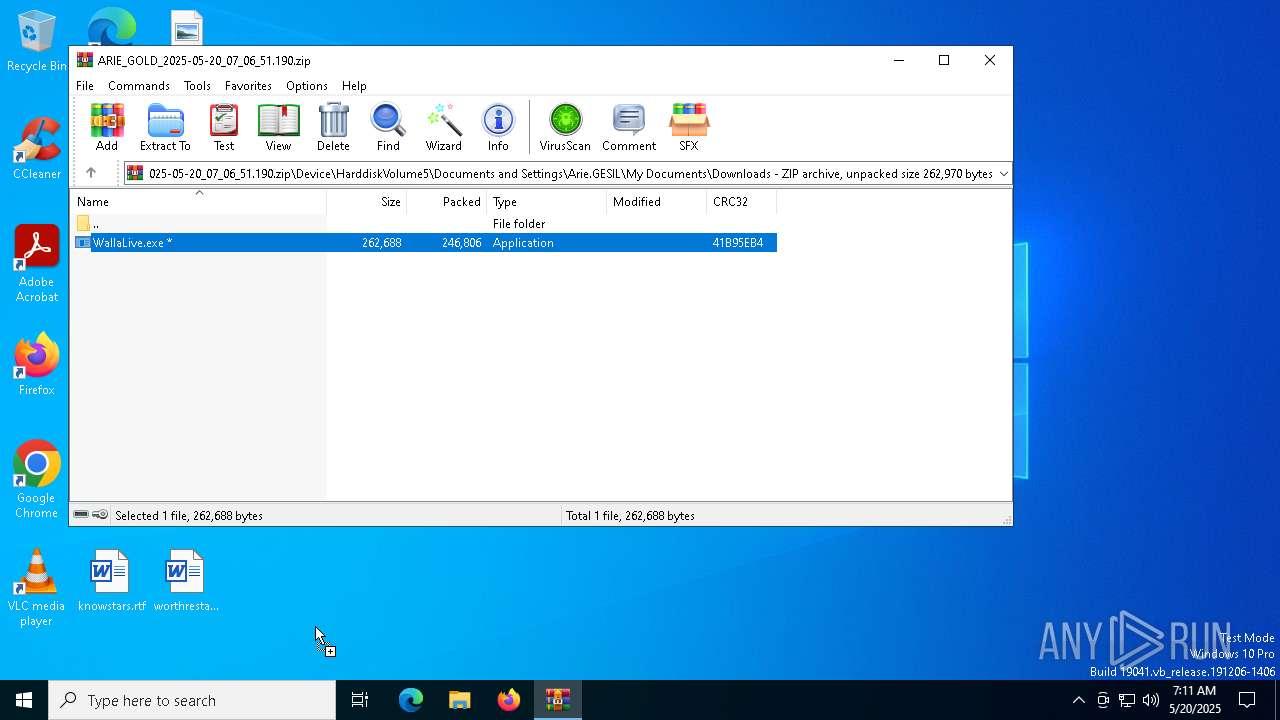
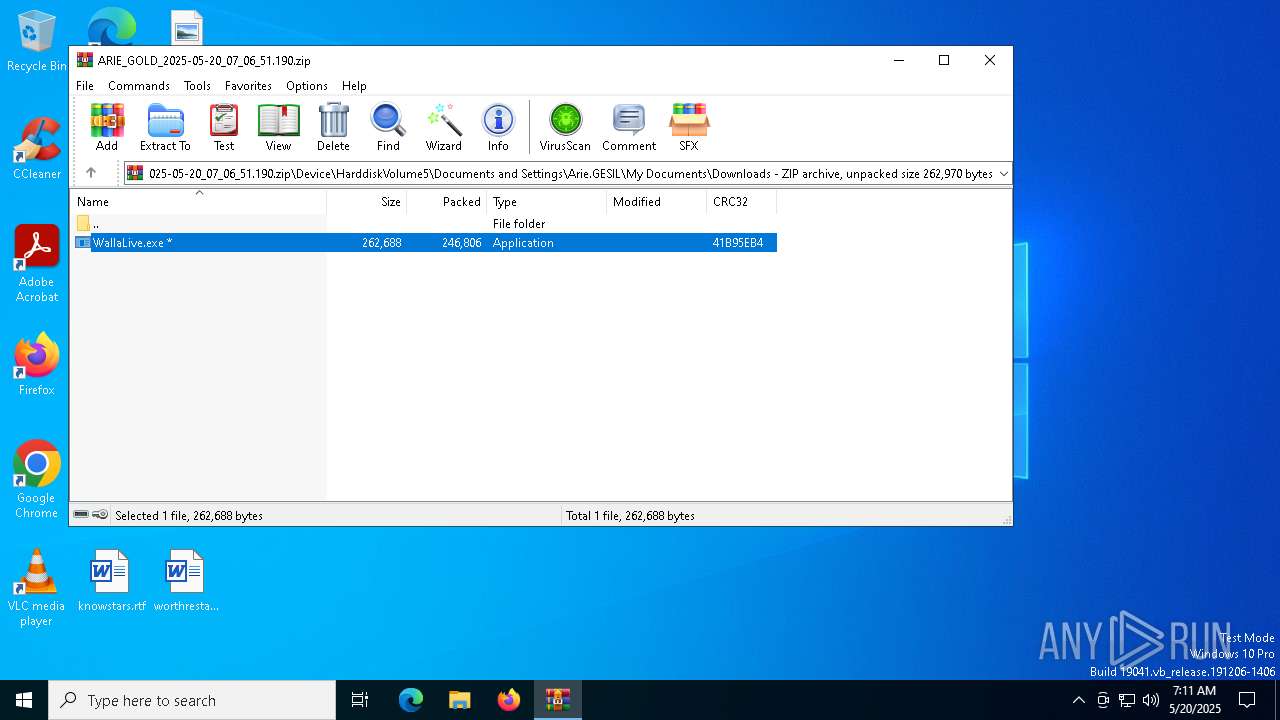
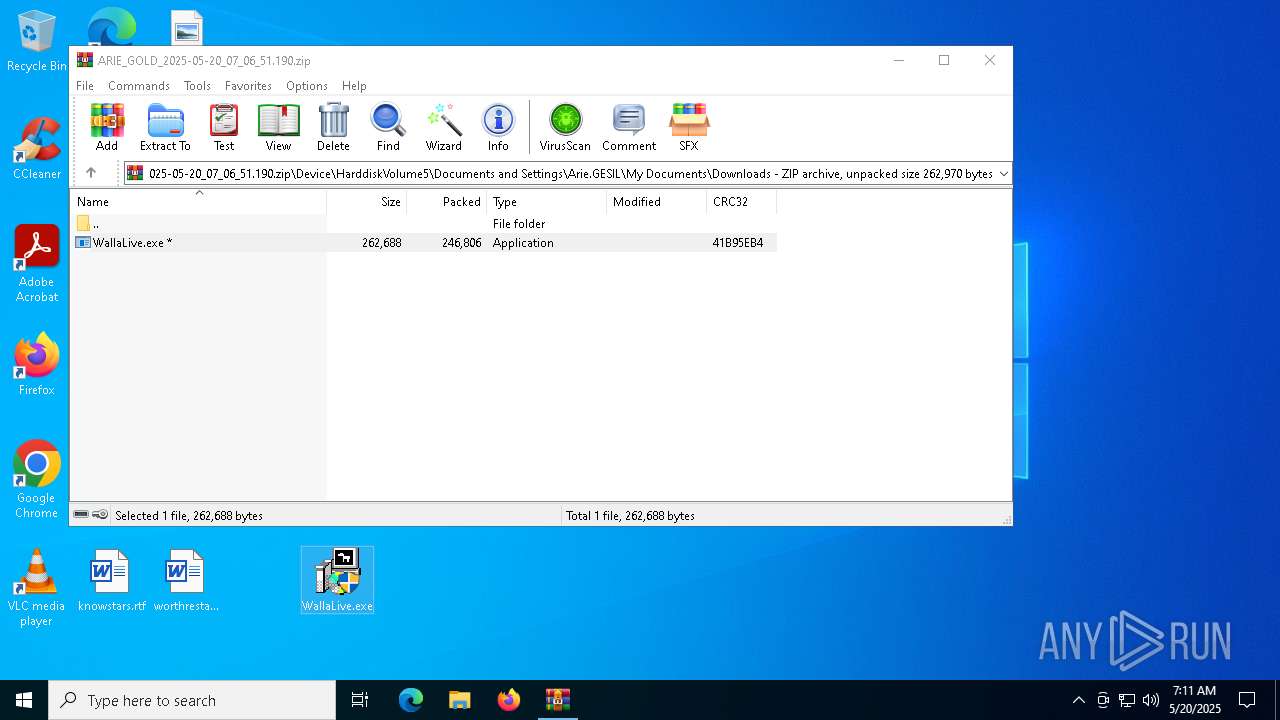
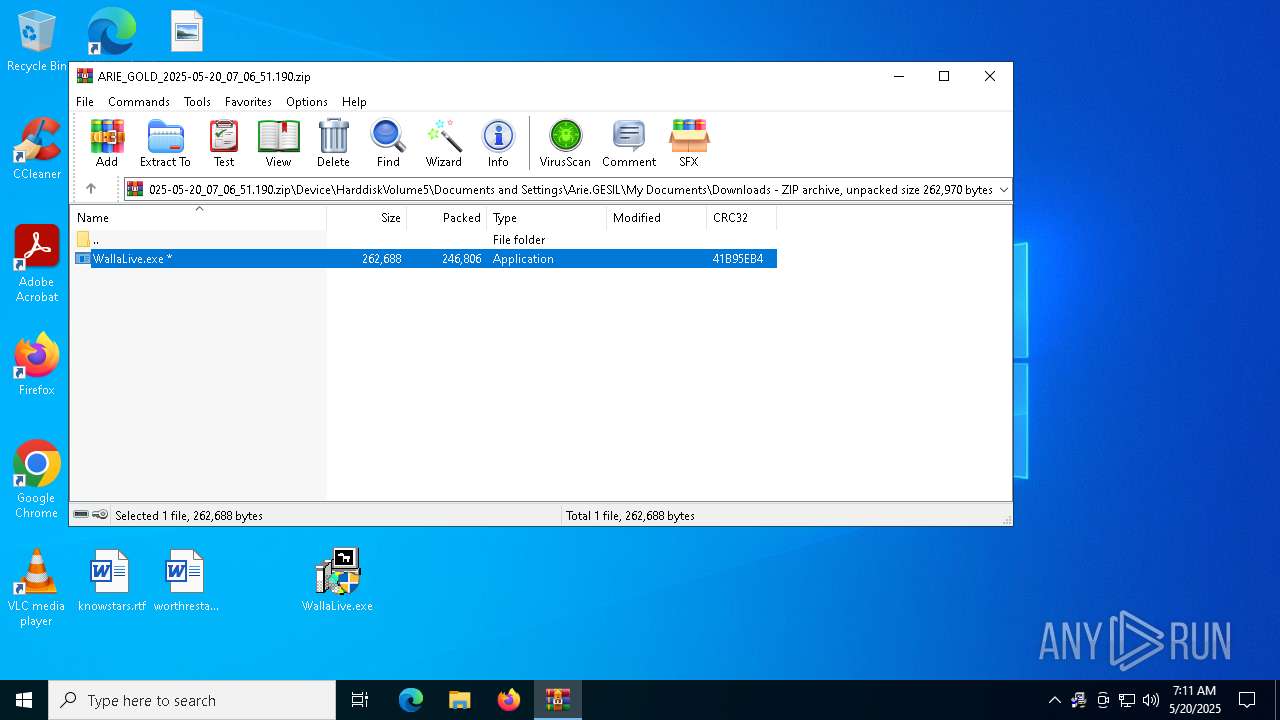
| File name: | ARIE_GOLD_2025-05-20_07_06_51.190.zip |
| Full analysis: | https://app.any.run/tasks/d9c8af84-4c83-4299-bbcc-557149be0834 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2025, 07:10:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 694E118E9FAC12A3CE3C96F61693C1EC |
| SHA1: | B51CEC2317D464A063F1942F8A446D9F58454C08 |
| SHA256: | 7A51760D5FC0A865087748C793E997A6531A2E3DE2F1466DB06CFABB2B8A9BCA |
| SSDEEP: | 12288:4XQizDke2iHsT/6OXb2owOgaLNC6tWLsG:mQizDz2iH8//Xb2owOgGNC3LsG |
MALICIOUS
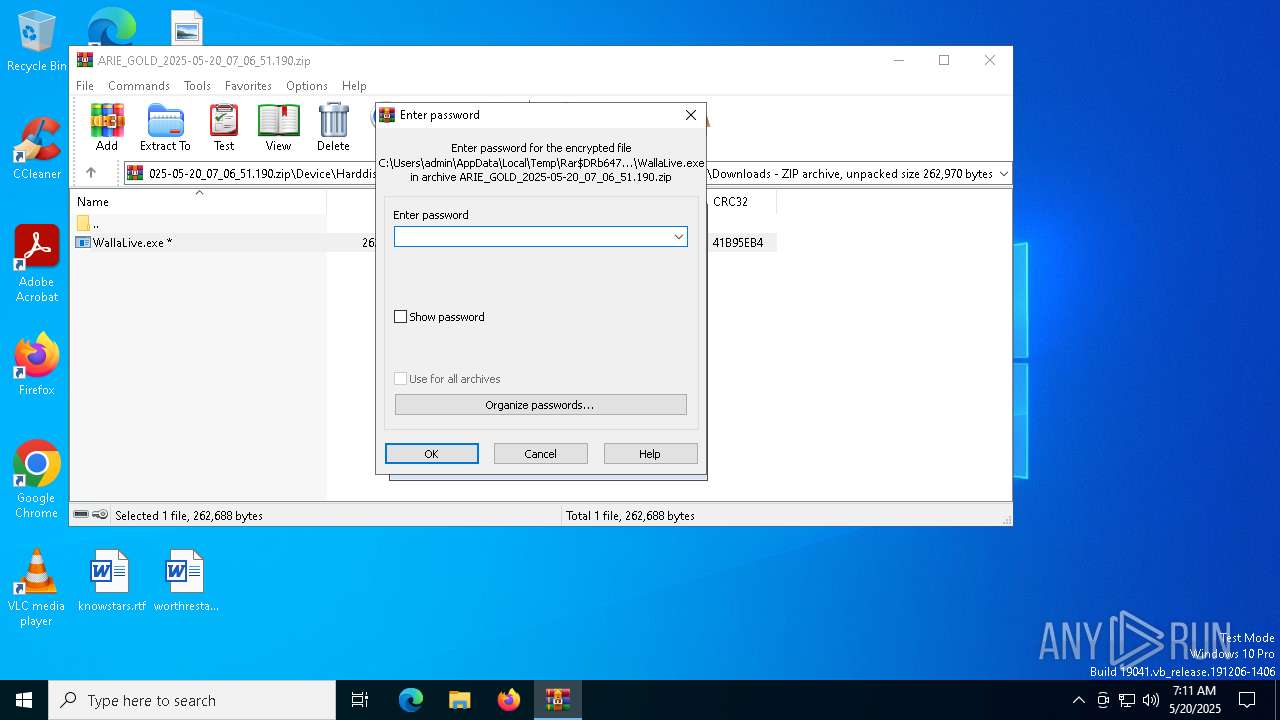
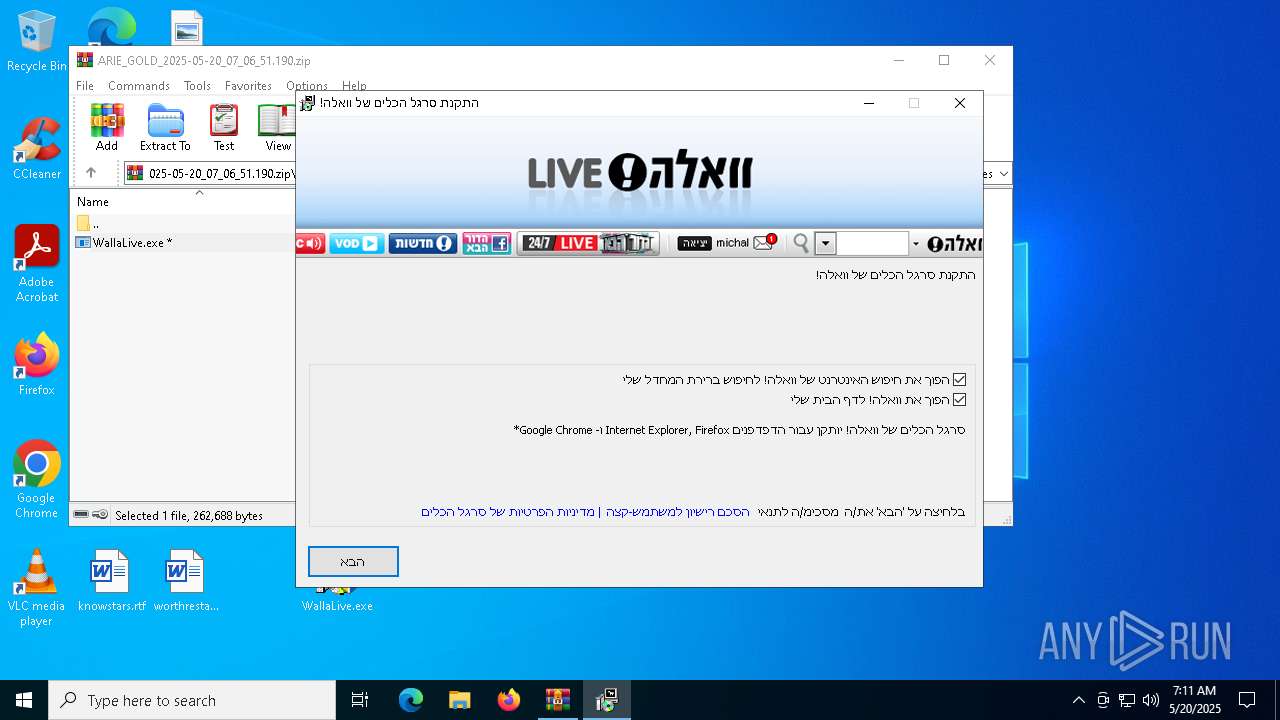
Executing a file with an untrusted certificate
- WallaLive.exe (PID: 1020)
- WallaLive.exe (PID: 3304)
SUSPICIOUS
The process creates files with name similar to system file names
- WallaLive.exe (PID: 3304)
Executable content was dropped or overwritten
- stubWrapperRemote.exe (PID: 632)
- WallaLive.exe (PID: 3304)
- walla.exe (PID: 672)
- GLB4EC9.tmp (PID: 5528)
Reads security settings of Internet Explorer
- stubWrapperRemote.exe (PID: 632)
- GLB4EC9.tmp (PID: 5528)
- WallaLive.exe (PID: 3304)
Malware-specific behavior (creating "System.dll" in Temp)
- WallaLive.exe (PID: 3304)
Starts application with an unusual extension
- walla.exe (PID: 672)
There is functionality for taking screenshot (YARA)
- WallaLive.exe (PID: 3304)
- stubWrapperRemote.exe (PID: 632)
- walla.exe (PID: 672)
- GLB4EC9.tmp (PID: 5528)
Detected use of alternative data streams (AltDS)
- GLB4EC9.tmp (PID: 5528)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6476)
Manual execution by a user
- WallaLive.exe (PID: 1020)
- WallaLive.exe (PID: 3304)
- msedge.exe (PID: 5260)
Checks supported languages
- WallaLive.exe (PID: 3304)
- stubWrapperRemote.exe (PID: 632)
- walla.exe (PID: 672)
- GLB4EC9.tmp (PID: 5528)
- identity_helper.exe (PID: 7768)
Reads the computer name
- WallaLive.exe (PID: 3304)
- GLB4EC9.tmp (PID: 5528)
- stubWrapperRemote.exe (PID: 632)
- identity_helper.exe (PID: 7768)
Checks proxy server information
- stubWrapperRemote.exe (PID: 632)
- slui.exe (PID: 6512)
Create files in a temporary directory
- stubWrapperRemote.exe (PID: 632)
- WallaLive.exe (PID: 3304)
- walla.exe (PID: 672)
- GLB4EC9.tmp (PID: 5528)
Process checks computer location settings
- GLB4EC9.tmp (PID: 5528)
Reads the software policy settings
- slui.exe (PID: 6156)
- slui.exe (PID: 6512)
Reads Environment values
- identity_helper.exe (PID: 7768)
Application launched itself
- msedge.exe (PID: 5260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x41b95eb4 |
| ZipCompressedSize: | 246806 |
| ZipUncompressedSize: | 262688 |
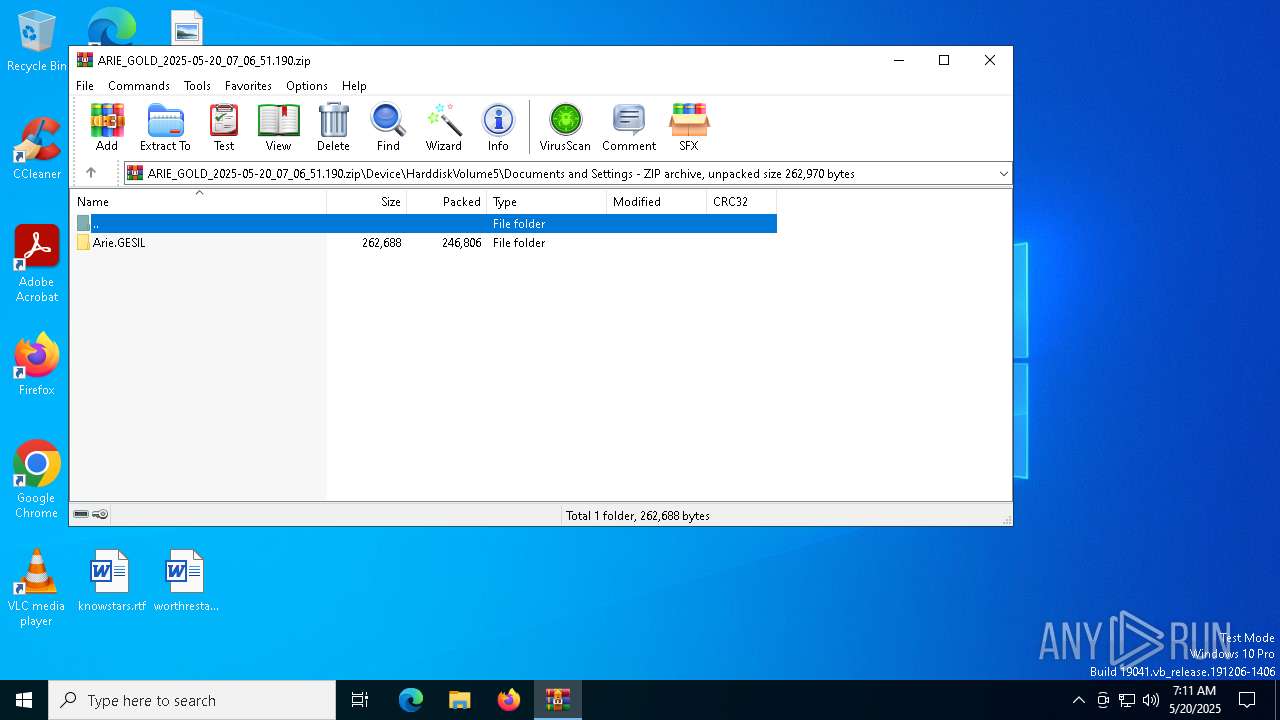
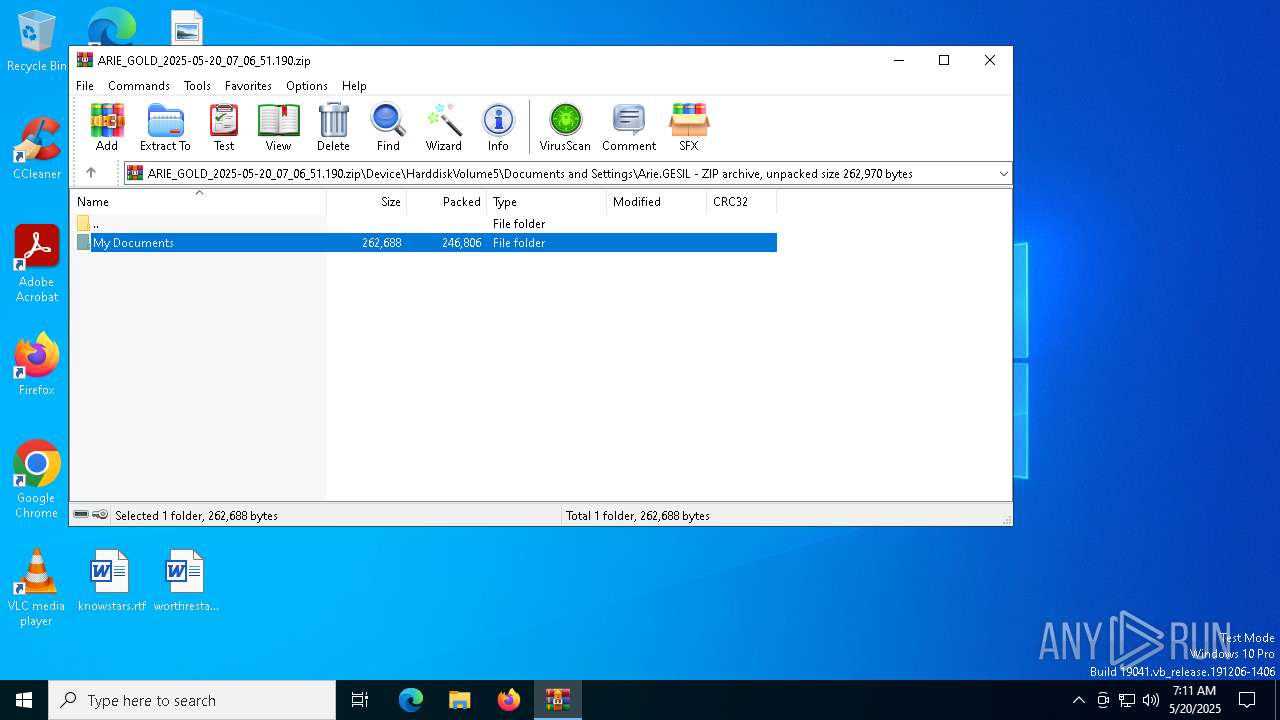
| ZipFileName: | Device/HarddiskVolume5/Documents and Settings/Arie.GESIL/My Documents/Downloads/WallaLive.exe |
Total processes
187
Monitored processes
53
Malicious processes
2
Suspicious processes
2
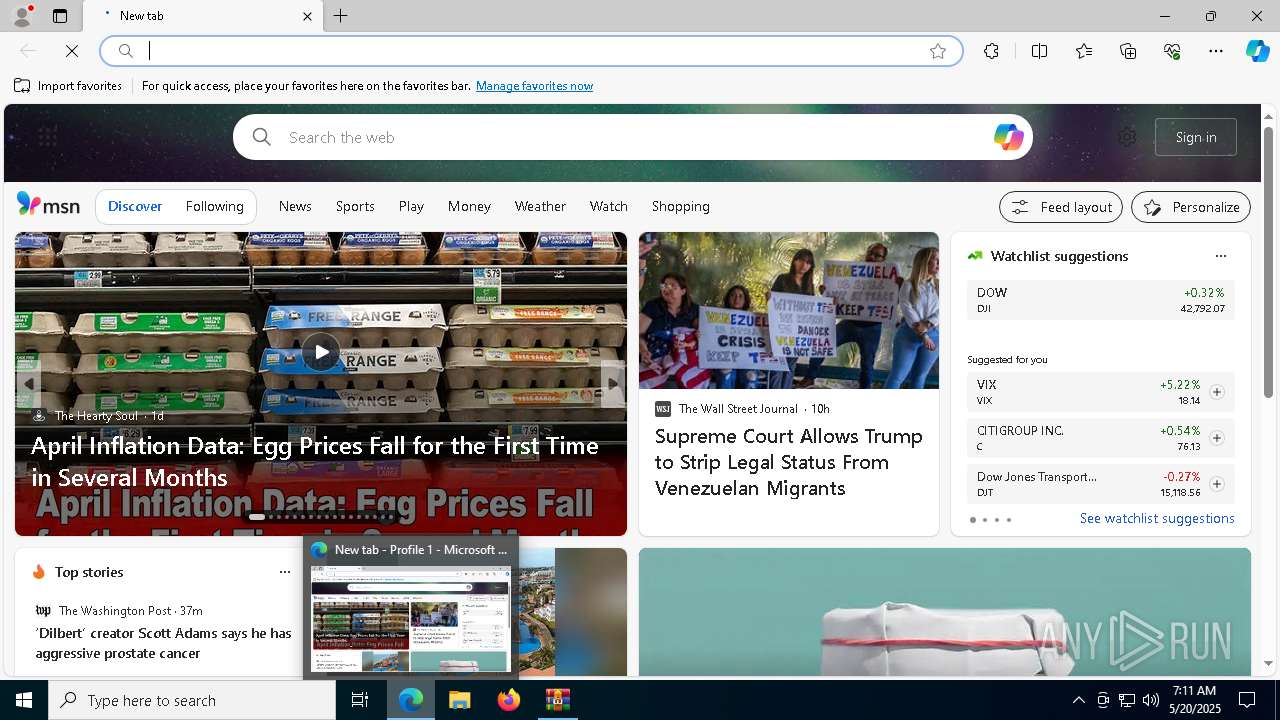
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5176 --field-trial-handle=2292,i,1435742458344222438,16942833439559553999,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
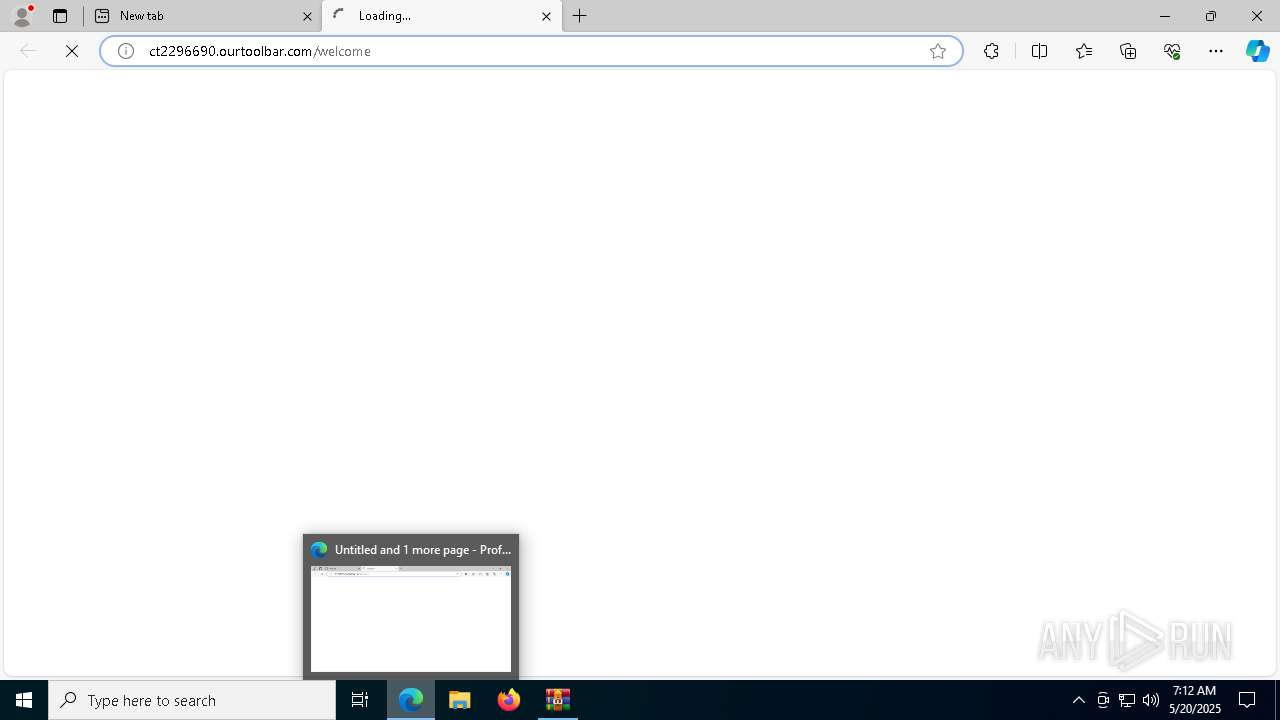
| 632 | "C:\Users\admin\AppData\Local\Temp\CT2296~1\STUBWR~1.EXE" -parameters=C:\Users\admin\AppData\Local\Temp\CT2296690\parameters.csf | C:\Users\admin\AppData\Local\Temp\CT2296690\stubWrapperRemote.exe | GLB4EC9.tmp | ||||||||||||
User: admin Company: Conduit Integrity Level: HIGH Exit code: 0 Version: 5.5.0.0 Modules
| |||||||||||||||
| 672 | "C:\Users\admin\AppData\Local\Temp\nss22F7.tmp\walla.exe" /s -installtoolbar=true -DefaultSearch=true -StartPage=true -openwelcomedialog=false | C:\Users\admin\AppData\Local\Temp\nss22F7.tmp\walla.exe | WallaLive.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\Desktop\WallaLive.exe" | C:\Users\admin\Desktop\WallaLive.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2272 --field-trial-handle=2292,i,1435742458344222438,16942833439559553999,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5996 --field-trial-handle=2292,i,1435742458344222438,16942833439559553999,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2680 --field-trial-handle=2292,i,1435742458344222438,16942833439559553999,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4024 --field-trial-handle=2292,i,1435742458344222438,16942833439559553999,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4284 --field-trial-handle=2292,i,1435742458344222438,16942833439559553999,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc89bc5fd8,0x7ffc89bc5fe4,0x7ffc89bc5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
9 694
Read events
9 653
Write events
41
Delete events
0
Modification events
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ARIE_GOLD_2025-05-20_07_06_51.190.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (5260) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
45
Suspicious files
550
Text files
178
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5528 | GLB4EC9.tmp | C:\Users\admin\AppData\Local\Temp\CT2296690\parameters.csf | — | |
MD5:— | SHA256:— | |||
| 5528 | GLB4EC9.tmp | C:\Users\admin\AppData\Local\Temp\CT2296690\conduitStatistics.csf | — | |
MD5:— | SHA256:— | |||
| 3304 | WallaLive.exe | C:\Users\admin\AppData\Local\Temp\nss22F7.tmp\WelcomeScreenLogo.bmp | image | |
MD5:AFE265781E8185EB19E9CA7F888928ED | SHA256:20578CCB1156268A266C82E8F95DC815901C2DABA54A8F8A66BDC12CF85459D5 | |||
| 5528 | GLB4EC9.tmp | C:\Users\admin\AppData\Local\Temp\GLC4F27.tmp | executable | |
MD5:8C97D8BB1470C6498E47B12C5A03CE39 | SHA256:A87F19F9FEE475D2B2E82ACFB4589BE6D816B613064CD06826E1D4C147BEB50A | |||
| 3304 | WallaLive.exe | C:\Users\admin\AppData\Local\Temp\nss22F7.tmp\System.dll | executable | |
MD5:301A9C8739ED3ED955A1BDC472D26F32 | SHA256:6EC9FDE89F067B1807325B05089C3AE4822CE7640D78E6F32DBE52F582DE1D92 | |||
| 3304 | WallaLive.exe | C:\Users\admin\AppData\Local\Temp\nss22F7.tmp\nsDialogs.dll | executable | |
MD5:B0165587C54350B6C9910E765F16AD9E | SHA256:26006C739057373F948B11892F40B0CC686C6C97C448F79447856421F9A15563 | |||
| 5260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF119fe6.TMP | — | |
MD5:— | SHA256:— | |||
| 5260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5528 | GLB4EC9.tmp | C:\Users\admin\AppData\Local\Temp\CT2296690\stubWrapperRemote.exe | executable | |
MD5:507160D75B68A9335F4722D2C81CD432 | SHA256:3548E1D30B88962B5D216D53B4B0546B1CF49C7658937594B36625A3595C0302 | |||
| 3304 | WallaLive.exe | C:\Users\admin\AppData\Local\Temp\nss22F7.tmp\walla.exe | executable | |
MD5:7BEC9414EA48305B38A9C6E041D68578 | SHA256:15AF13553CD95E039DDBFB4BFAD21406A1C7622E0C4E0A3147227E0A61558F4D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
101
DNS requests
109
Threats
4
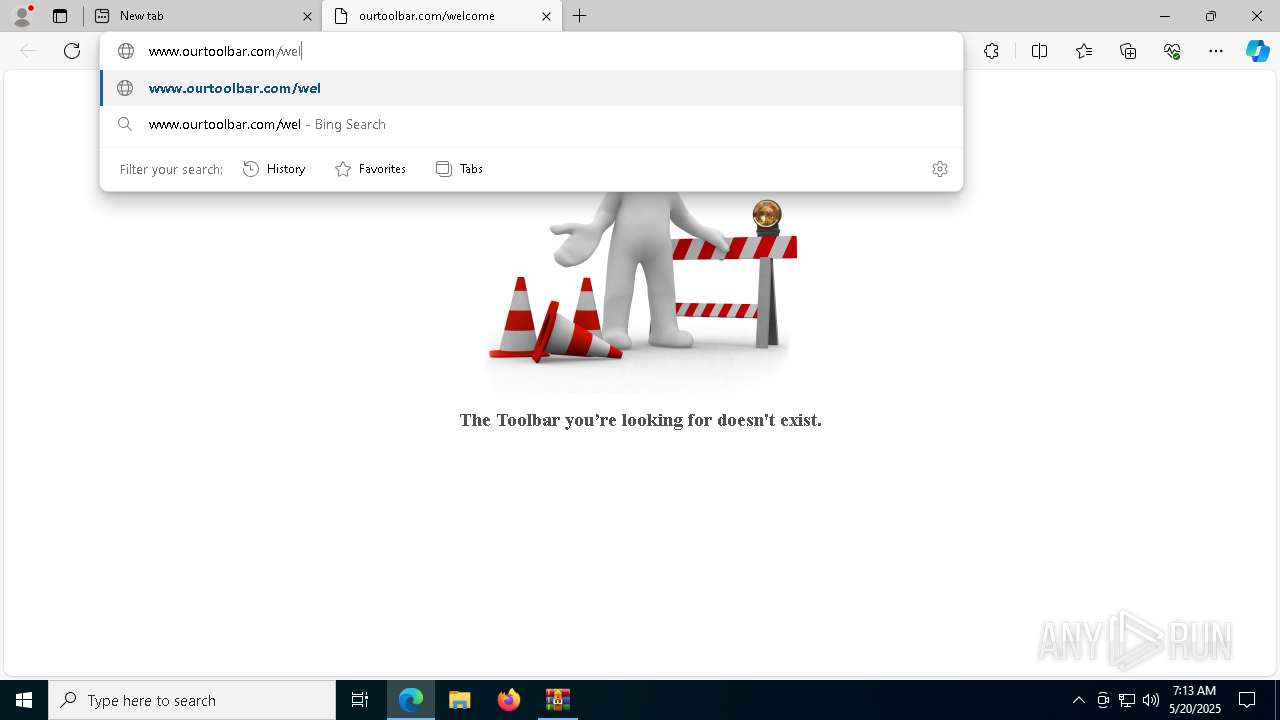
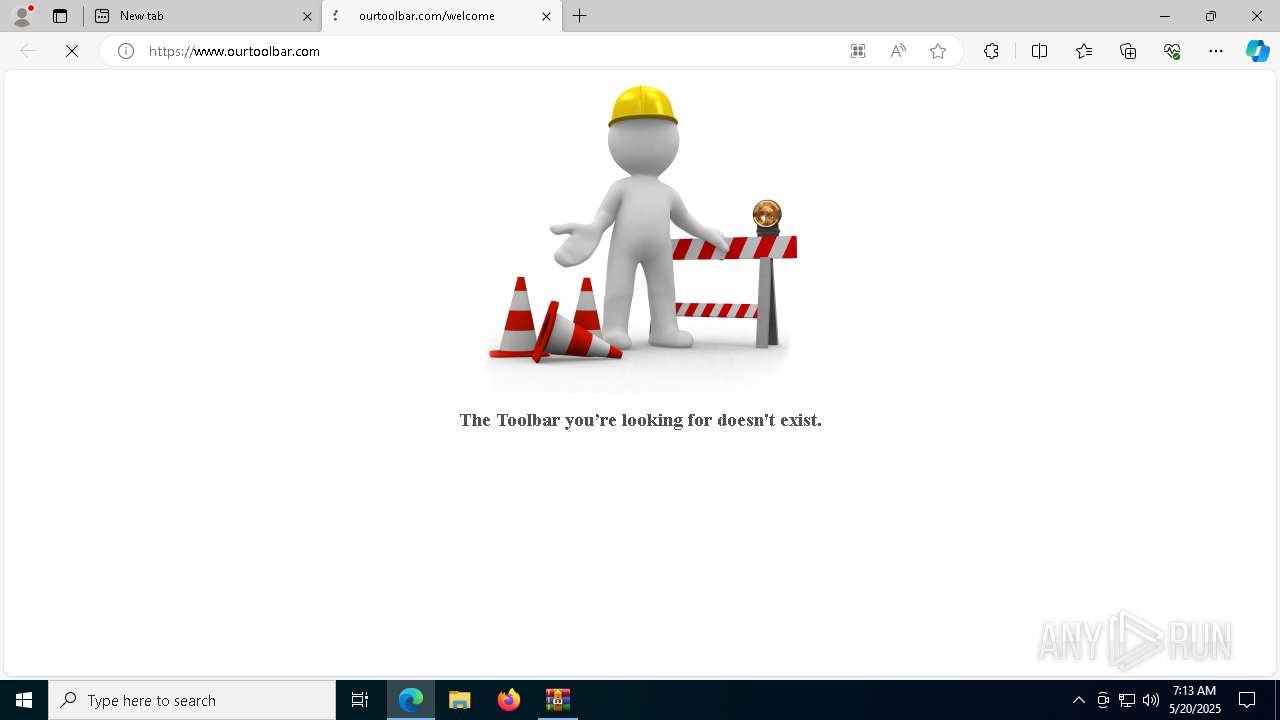
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5640 | msedge.exe | GET | 200 | 52.217.192.85:80 | http://www.ourtoolbar.com/pic.jpg | unknown | — | — | unknown |
5640 | msedge.exe | GET | 404 | 52.217.192.85:80 | http://www.ourtoolbar.com/favicon.ico | unknown | — | — | unknown |
3676 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747803060&P2=404&P3=2&P4=e49amixEWIwqL4cefBrD0p88X%2fJpbxvKGWIEVO%2fE8uyHwXe9R6w9MNV%2bYMeJ77FlyiwHRoRjfX7wCfaJfDjPGQ%3d%3d | unknown | — | — | whitelisted |
3676 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1747803064&P2=404&P3=2&P4=VRUoA4OwWRyJByfdqvnaKzEHHl2EISdtmxlUh71EeWTBJclmbs9V%2f12Y2xZu%2bgy1%2biOdziSnFb7ipuQGnkDUjA%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5640 | msedge.exe | GET | 404 | 52.217.192.85:80 | http://www.ourtoolbar.com/welcome | unknown | — | — | unknown |
5640 | msedge.exe | GET | 200 | 52.217.92.115:80 | http://www.ourtoolbar.com/pic.jpg | unknown | — | — | unknown |
3676 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747803060&P2=404&P3=2&P4=X1z8nj%2fdIjvsnJ4bCMTN7ecLLWfd1iv8jAlueN7o%2bjzRe0prr12d%2f9FgLAmRmnAzDncNh8%2fB28PHdrE1dDbxaA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6744 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
storage.conduit.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5640 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5640 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5640 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5640 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |