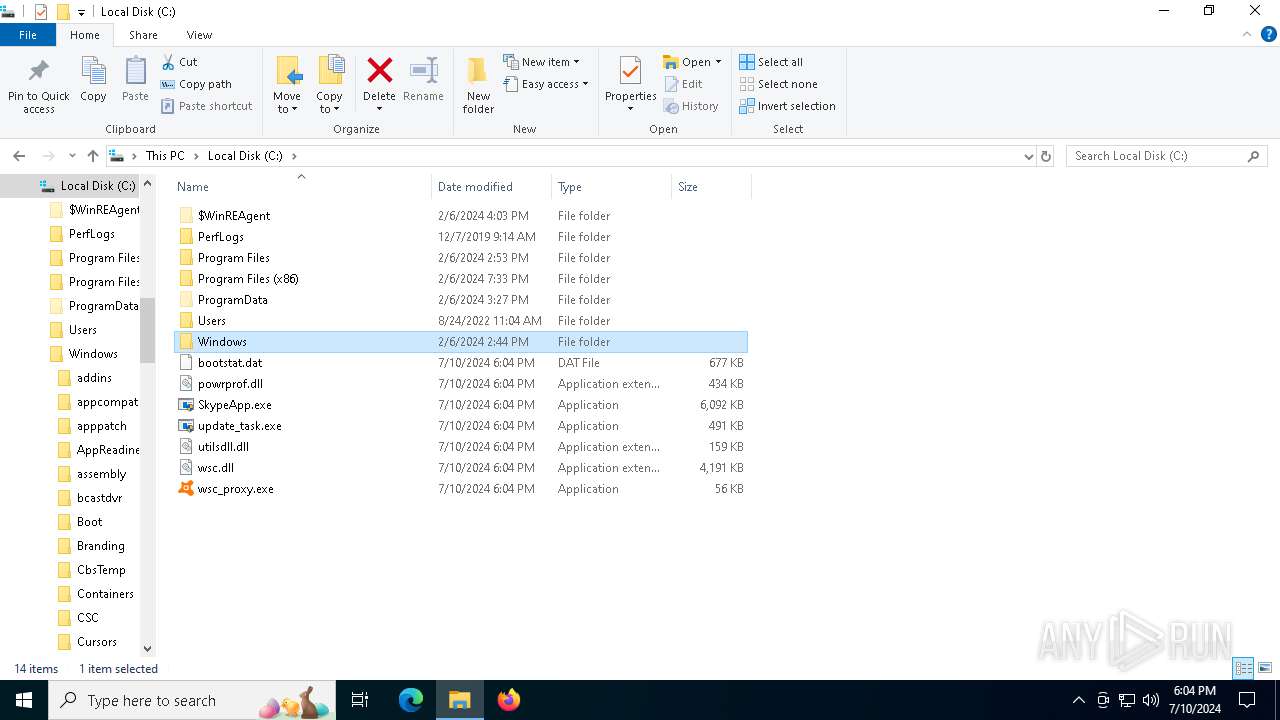
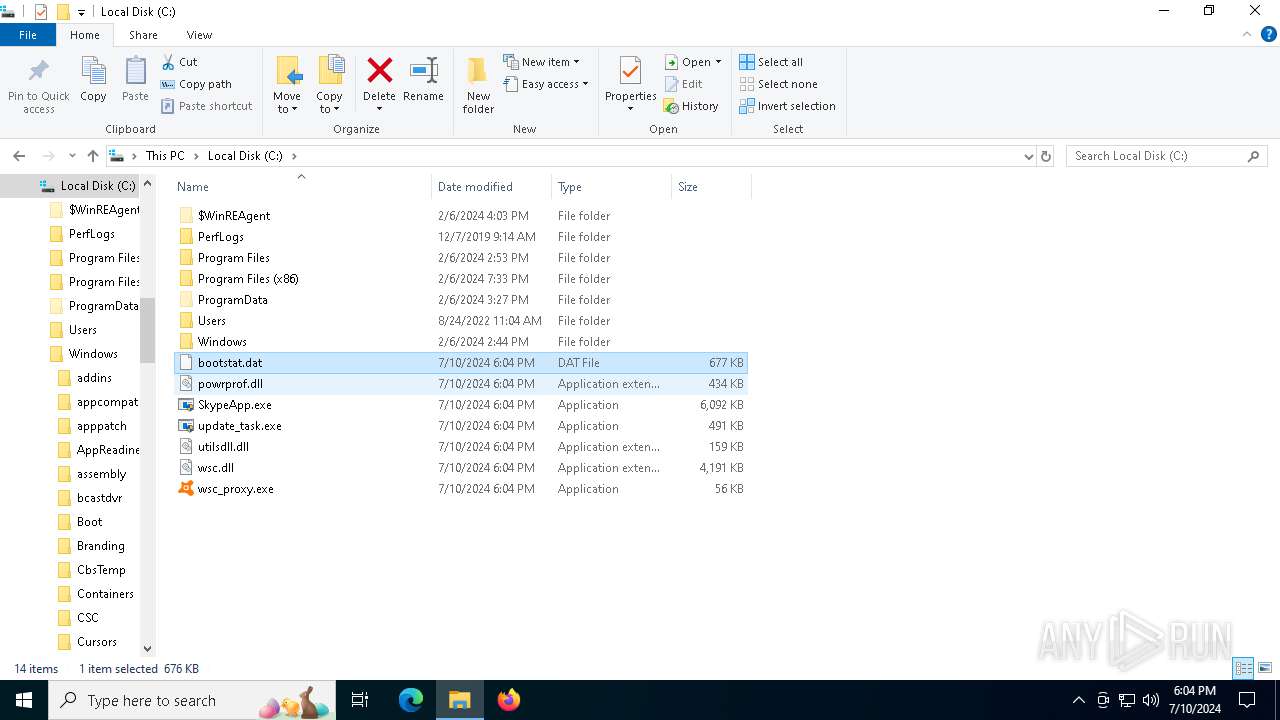
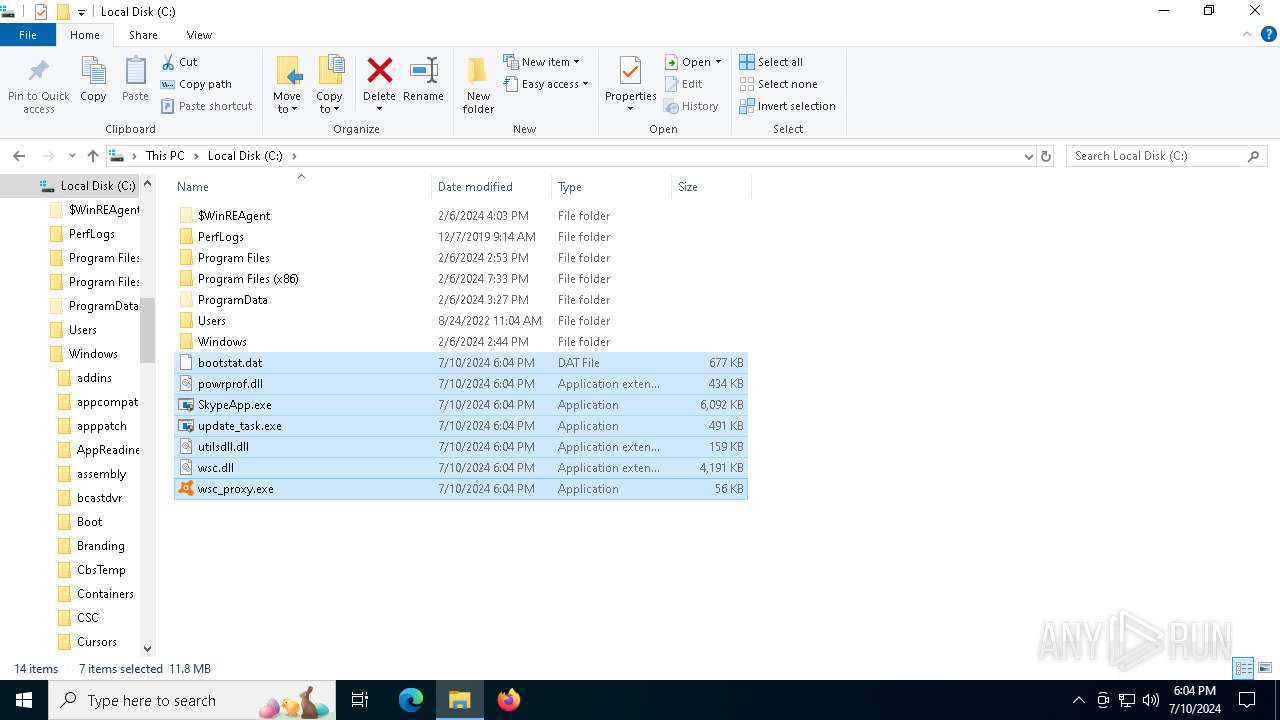
| File name: | bootstat.dat |
| Full analysis: | https://app.any.run/tasks/7c14aa28-0837-4d71-9b53-ef41a28b16ce |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2024, 18:03:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | CD92E4F79851F17ACF0719F3C9C12B39 |
| SHA1: | 5DE37578B0EC62BE249FF47A2D4B296FF99B1C24 |
| SHA256: | 7A510517252AA94DBD5E0C185F3B42C3AAA87292DA681ECF0B6B755B3C627754 |
| SSDEEP: | 24576:jUVKLW+h7EFHNKCM5zWhNbOqIMjF21xJ48/ovRGHc21gHxIf2rjmYdSG4XlOmttA:jUVKLW+h7ExNKCM5ShNbOqIMjk1xJ488 |
MALICIOUS
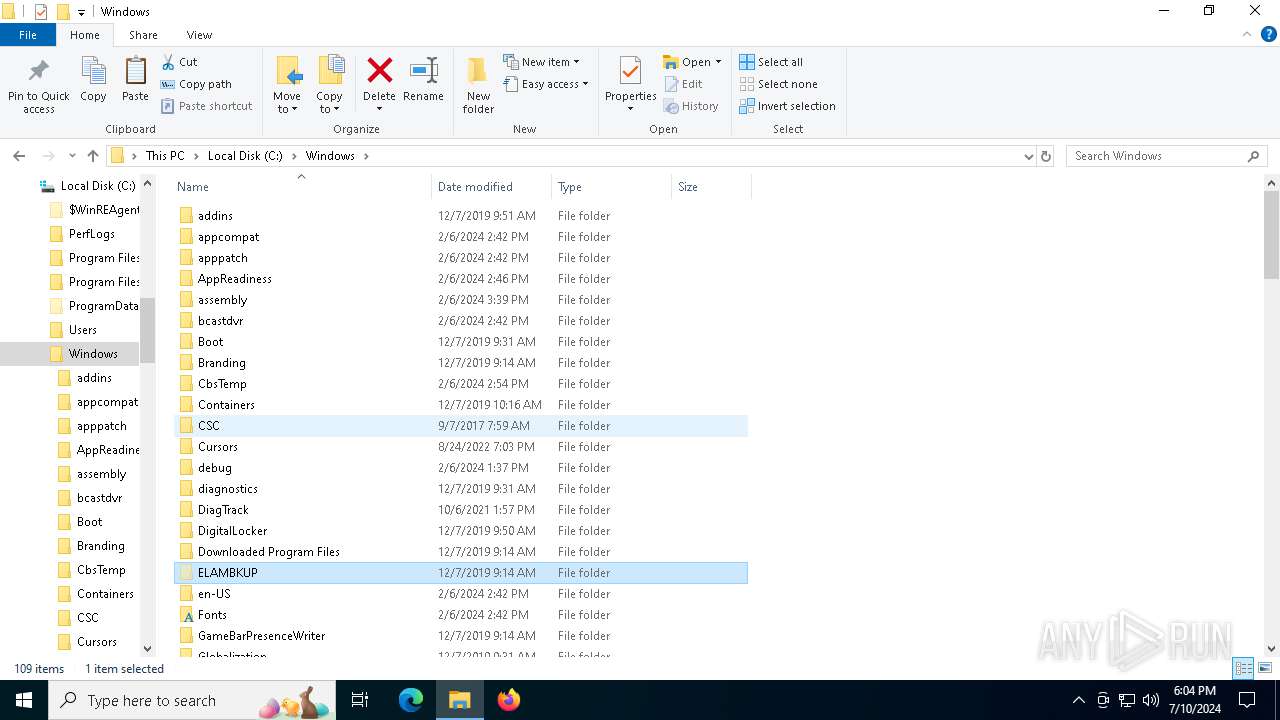
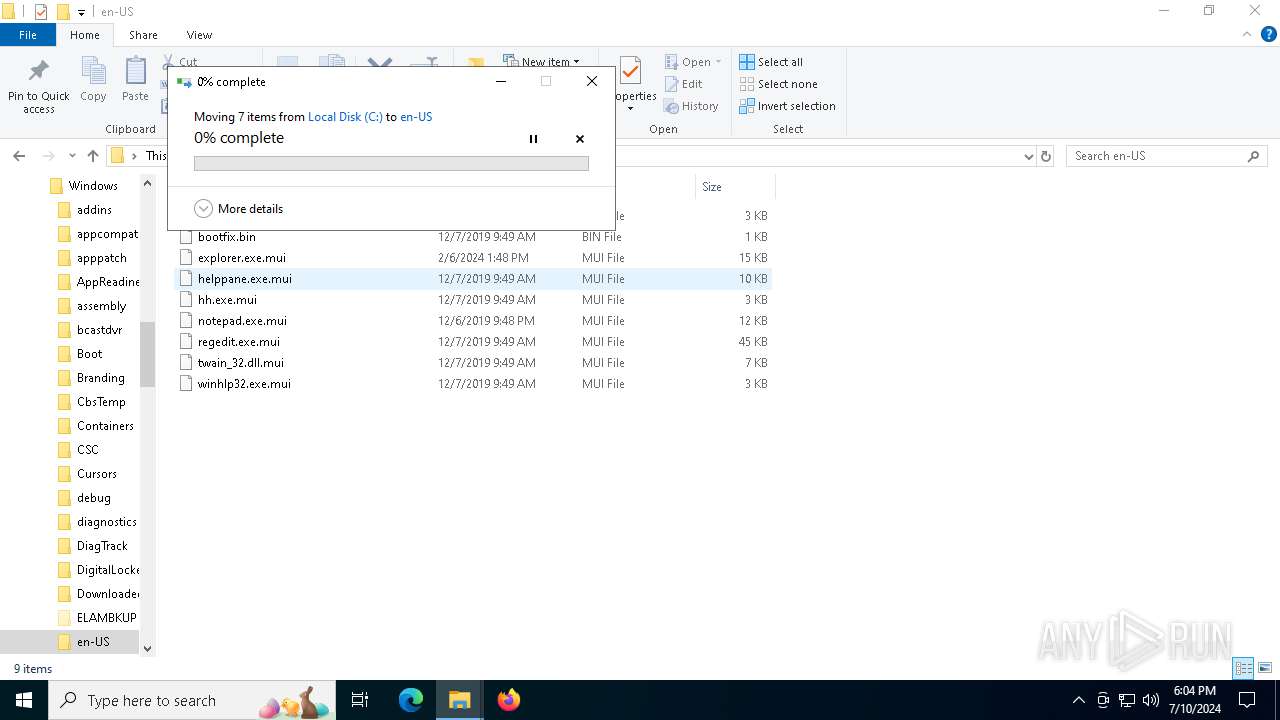
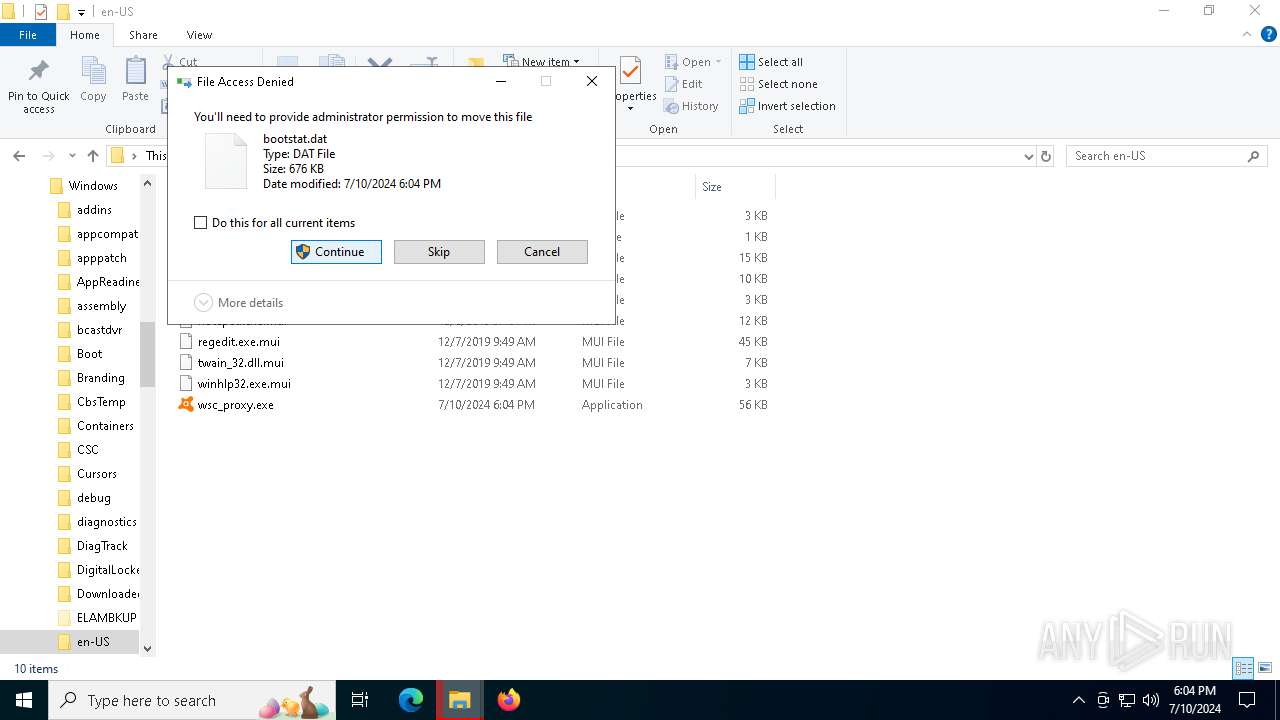
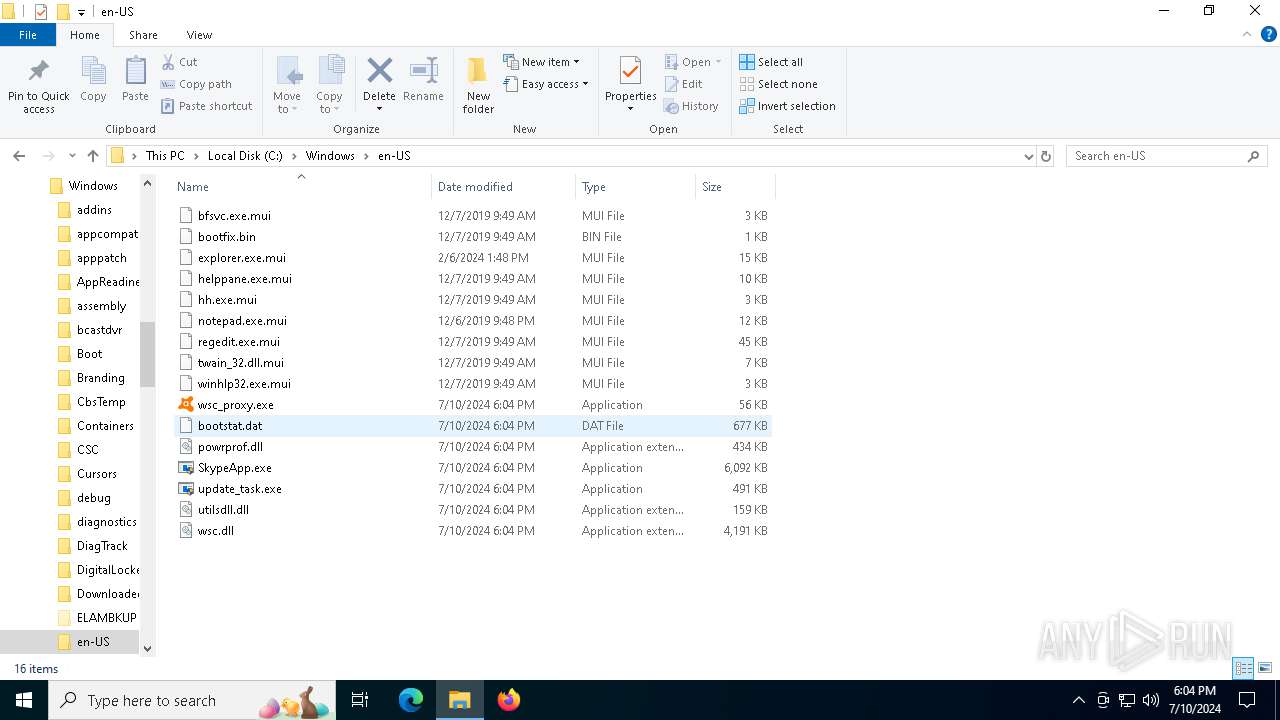
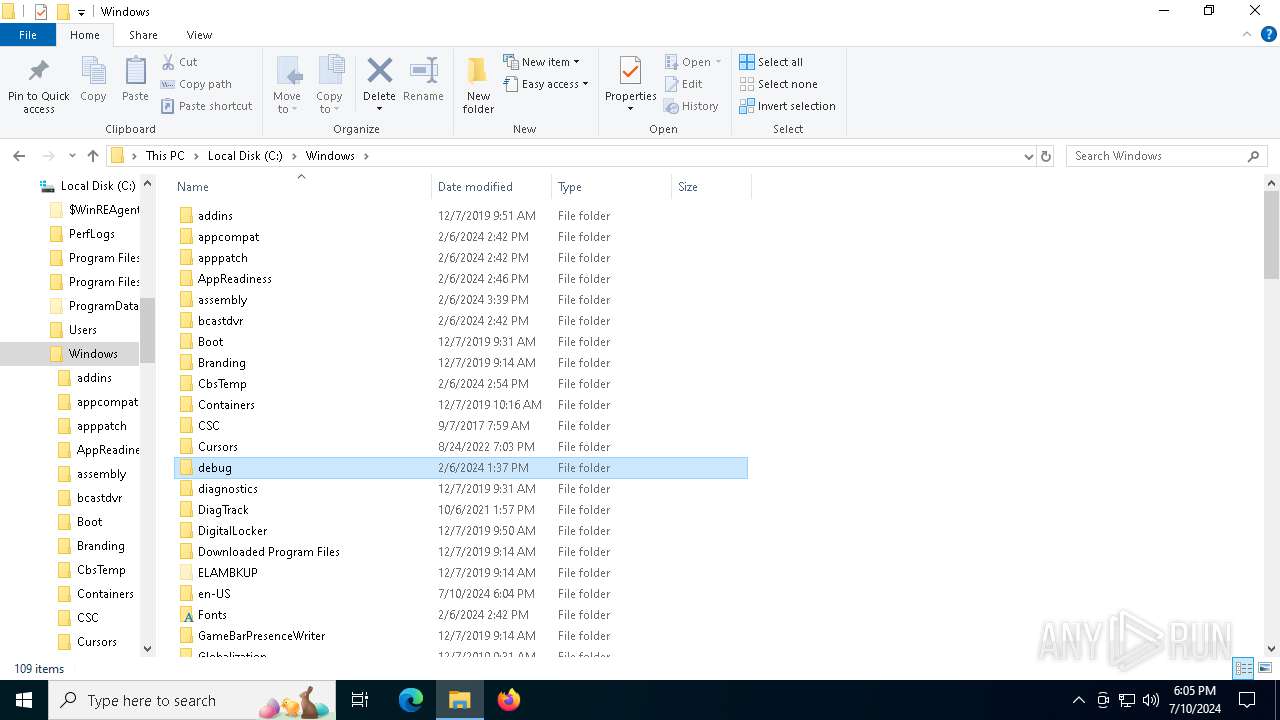
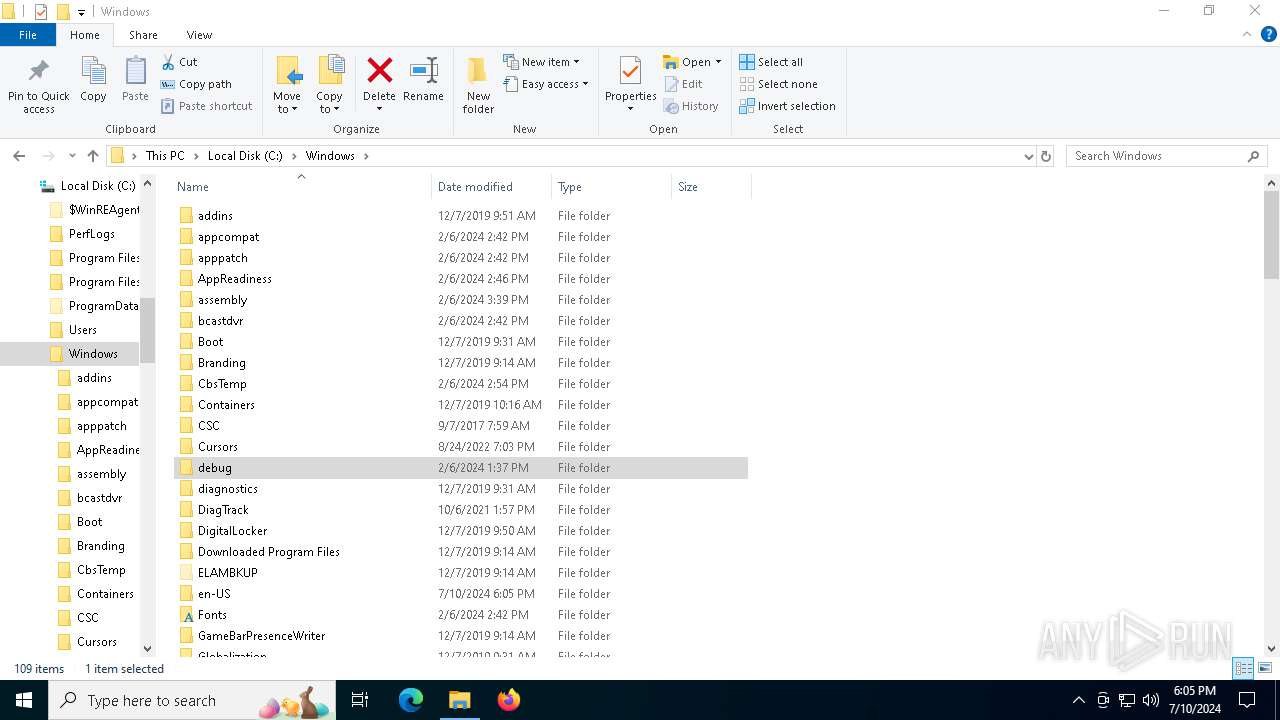
Creates a writable file in the system directory
- WerFault.exe (PID: 4632)
SUSPICIOUS
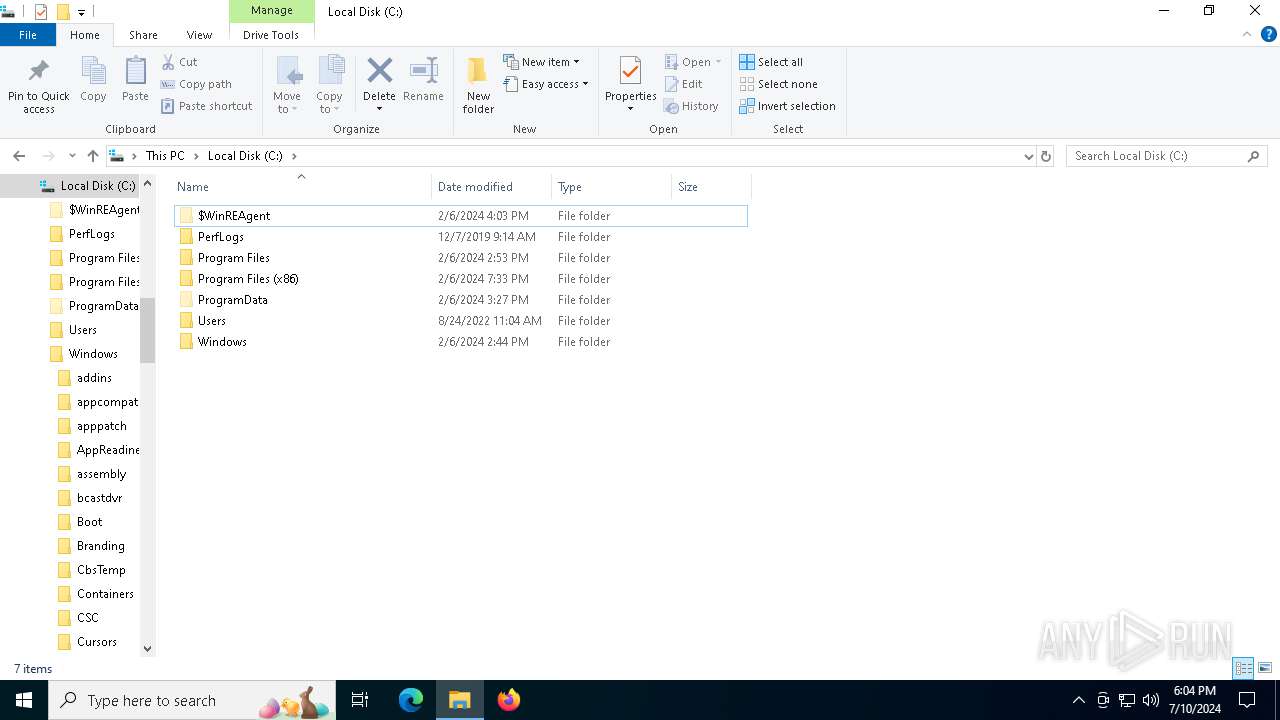
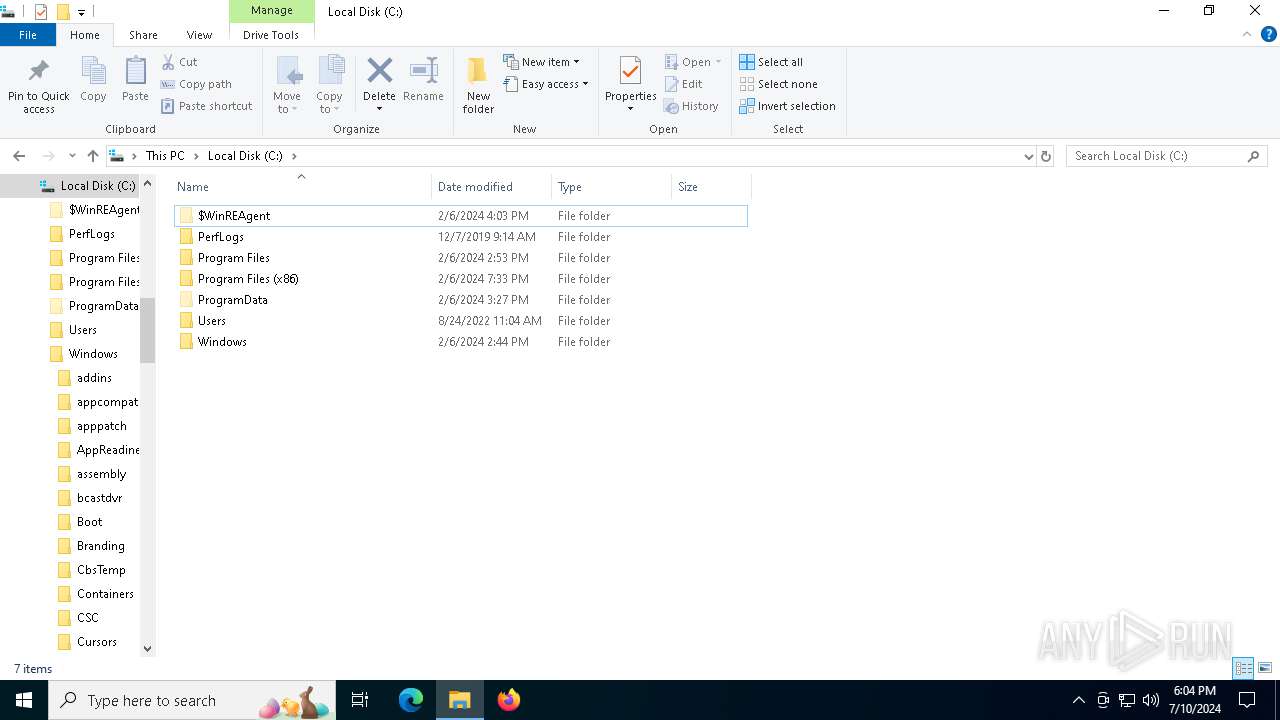
Creates file in the systems drive root
- dllhost.exe (PID: 2252)
Reads security settings of Internet Explorer
- update_task.exe (PID: 4724)
- LockApp.exe (PID: 3776)
Executable content was dropped or overwritten
- dllhost.exe (PID: 2252)
Reads the date of Windows installation
- update_task.exe (PID: 4724)
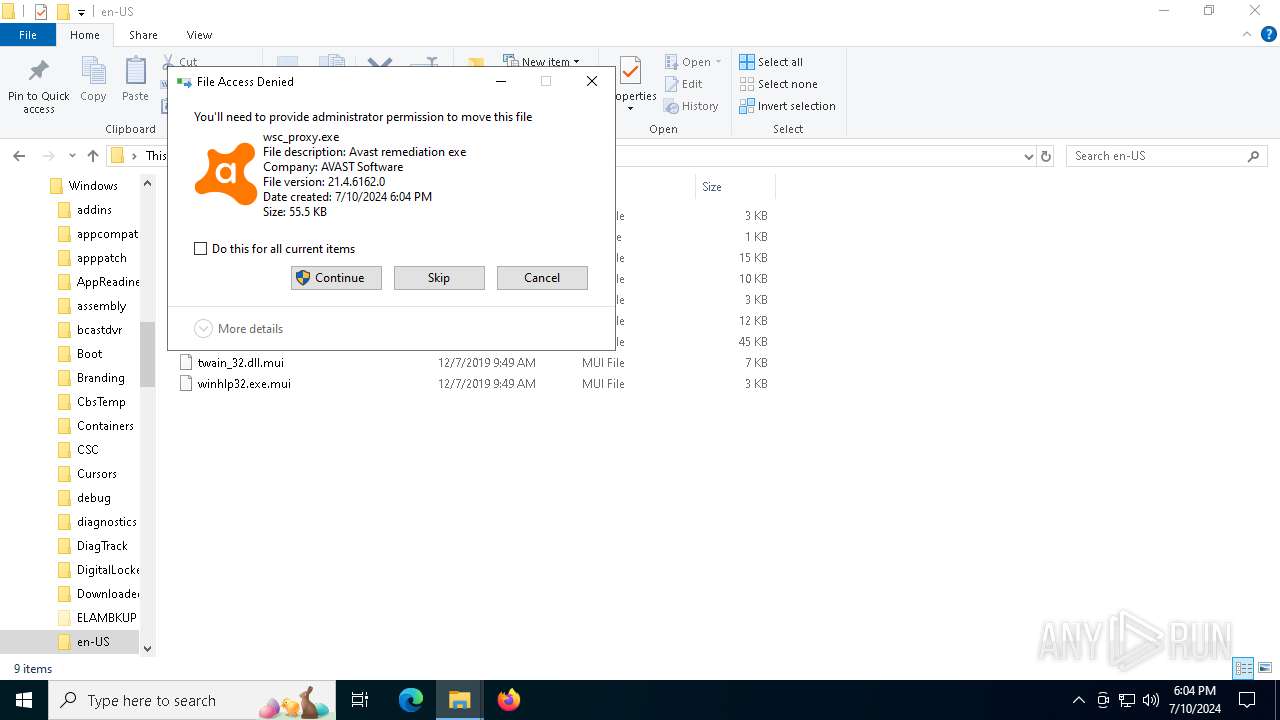
Executes as Windows Service
- wsc_proxy.exe (PID: 3136)
Executes application which crashes
- wsc_proxy.exe (PID: 3136)
INFO
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 3068)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 2252)
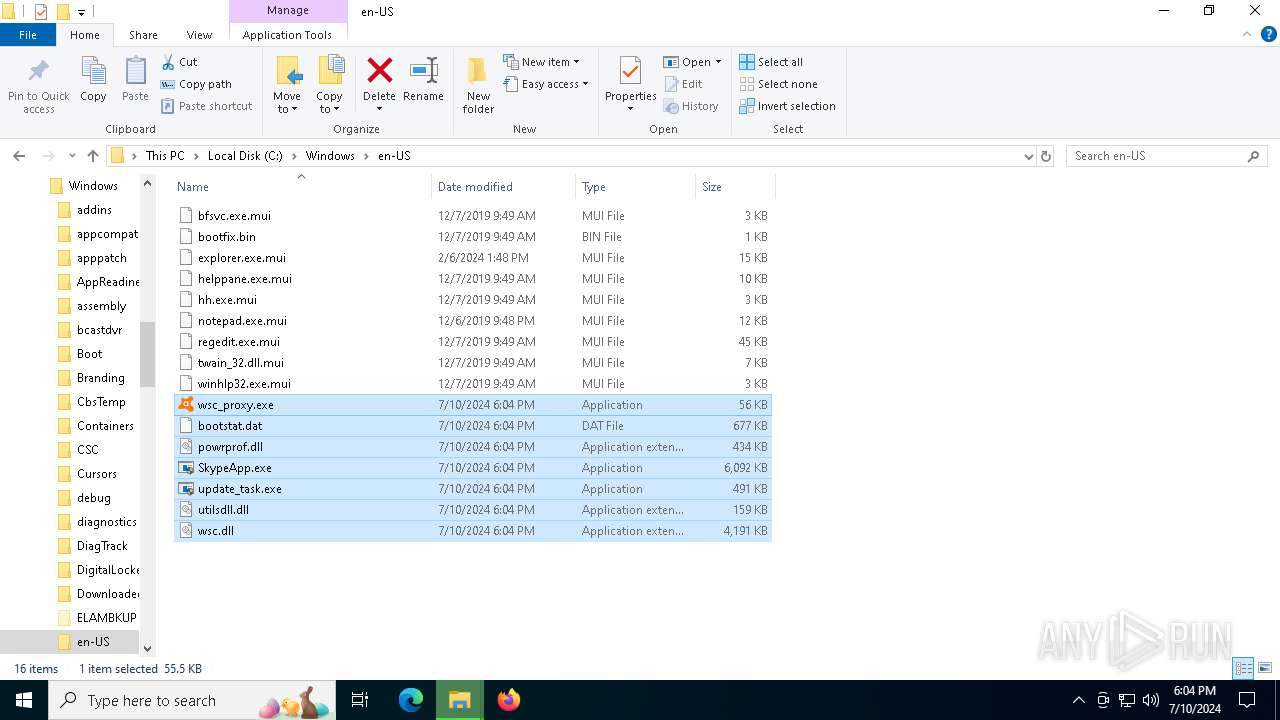
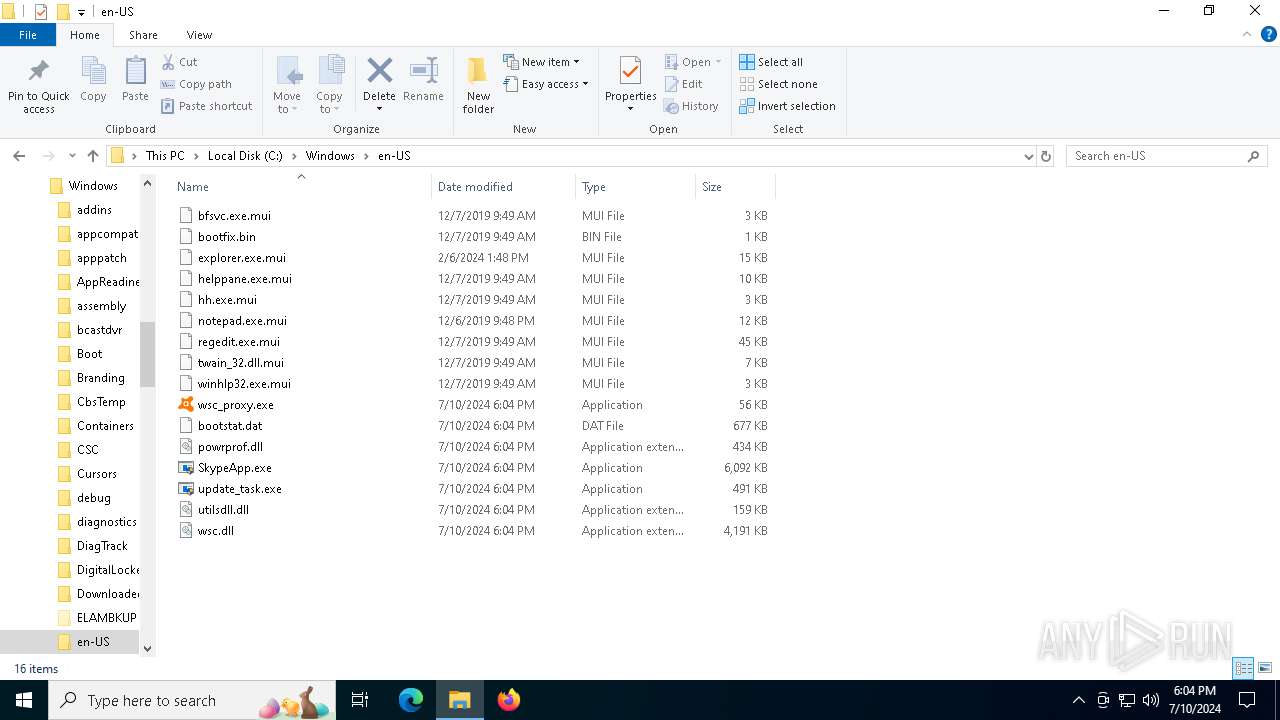
Drops the executable file immediately after the start
- dllhost.exe (PID: 2252)
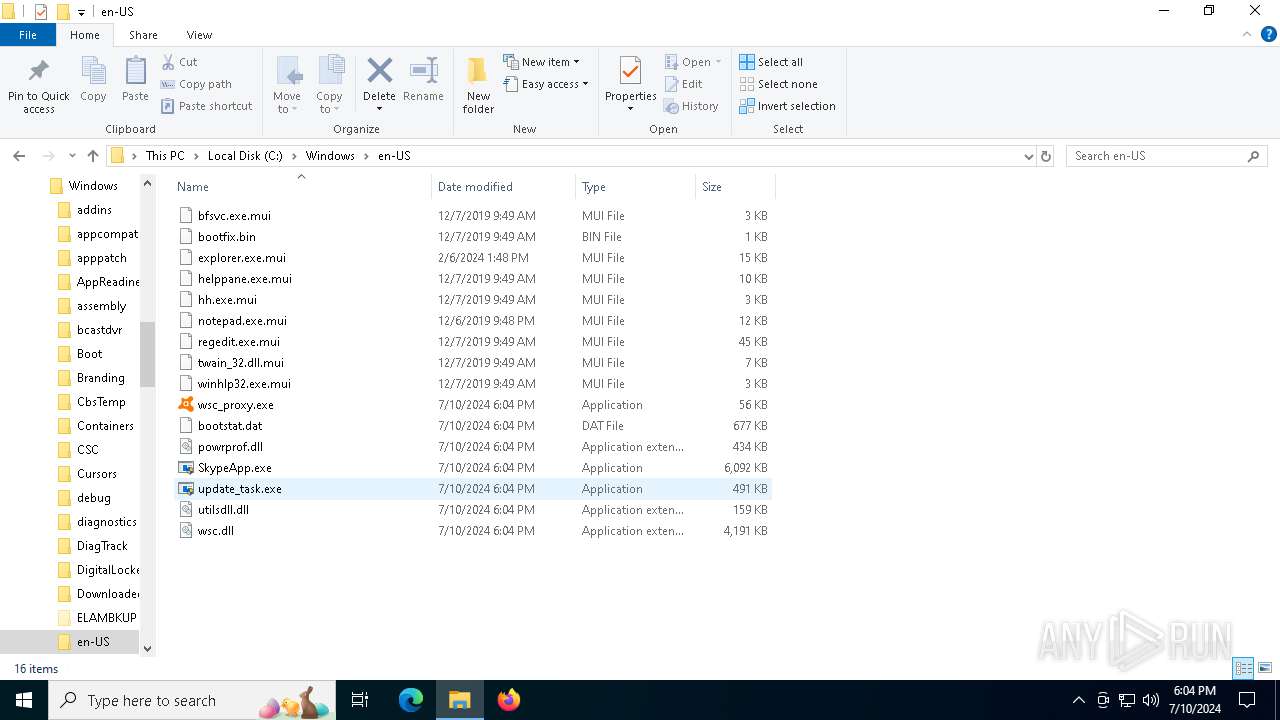
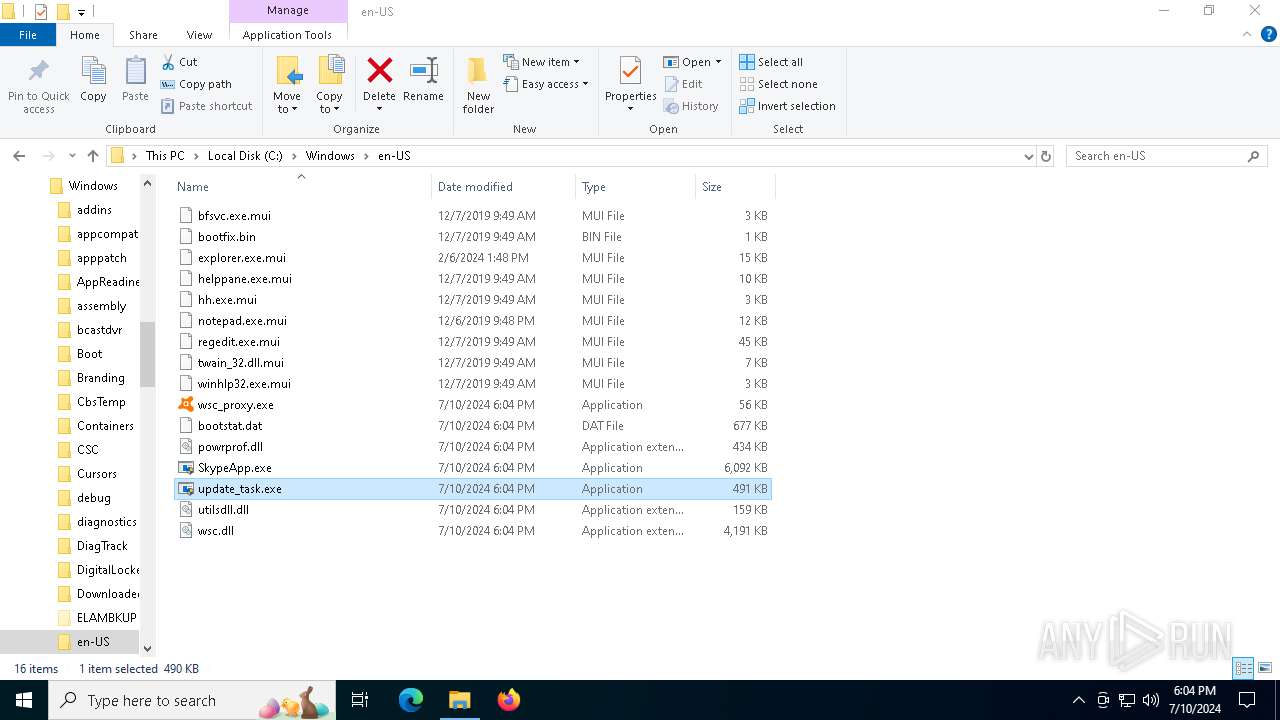
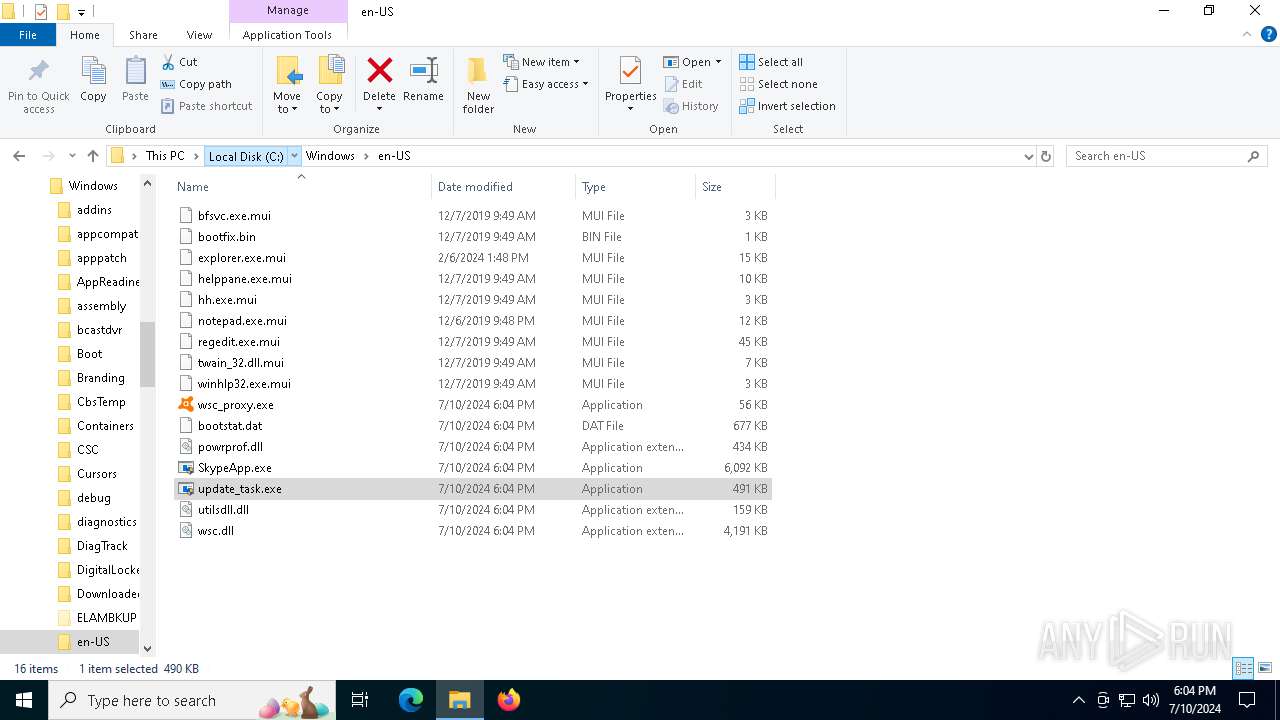
Manual execution by a user
- update_task.exe (PID: 4724)
- update_task.exe (PID: 3540)
Checks supported languages
- update_task.exe (PID: 4724)
- SkypeApp.exe (PID: 4800)
- LockApp.exe (PID: 3776)
- wsc_proxy.exe (PID: 3136)
Reads the computer name
- update_task.exe (PID: 4724)
- LockApp.exe (PID: 3776)
- SkypeApp.exe (PID: 4800)
- wsc_proxy.exe (PID: 3136)
Process checks computer location settings
- update_task.exe (PID: 4724)
Creates files in the program directory
- wsc_proxy.exe (PID: 3136)
Reads the machine GUID from the registry
- wsc_proxy.exe (PID: 3136)
Reads the software policy settings
- WerFault.exe (PID: 4632)
Reads CPU info
- wsc_proxy.exe (PID: 3136)
Checks proxy server information
- update_task.exe (PID: 4724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SkypeApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2252 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2916 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | update_task.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
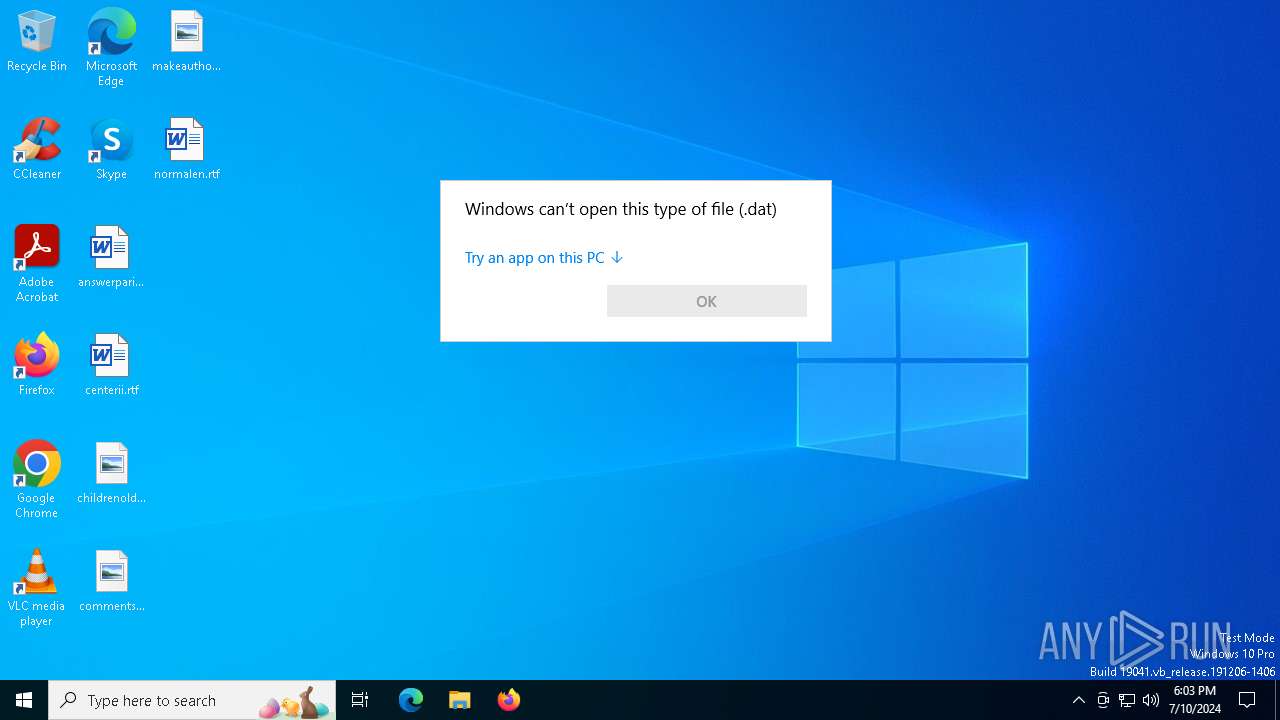
| 3068 | "C:\WINDOWS\System32\OpenWith.exe" C:\WINDOWS\bootstat.dat | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
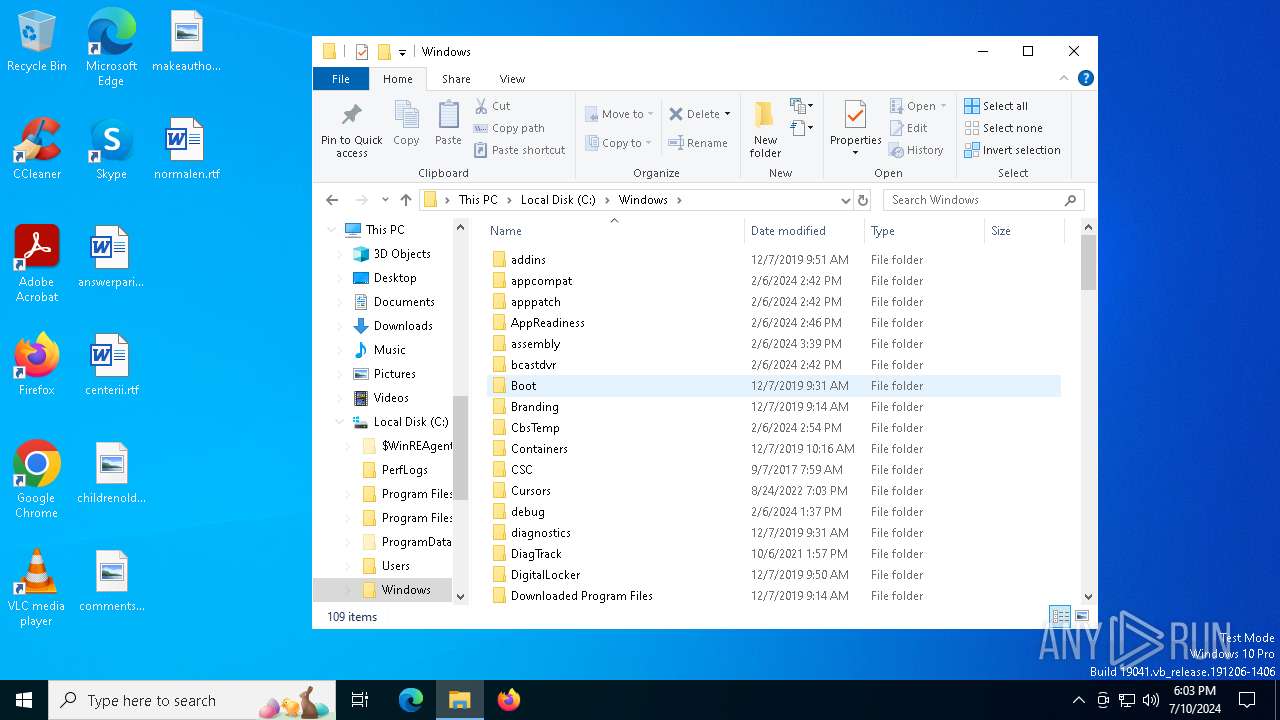
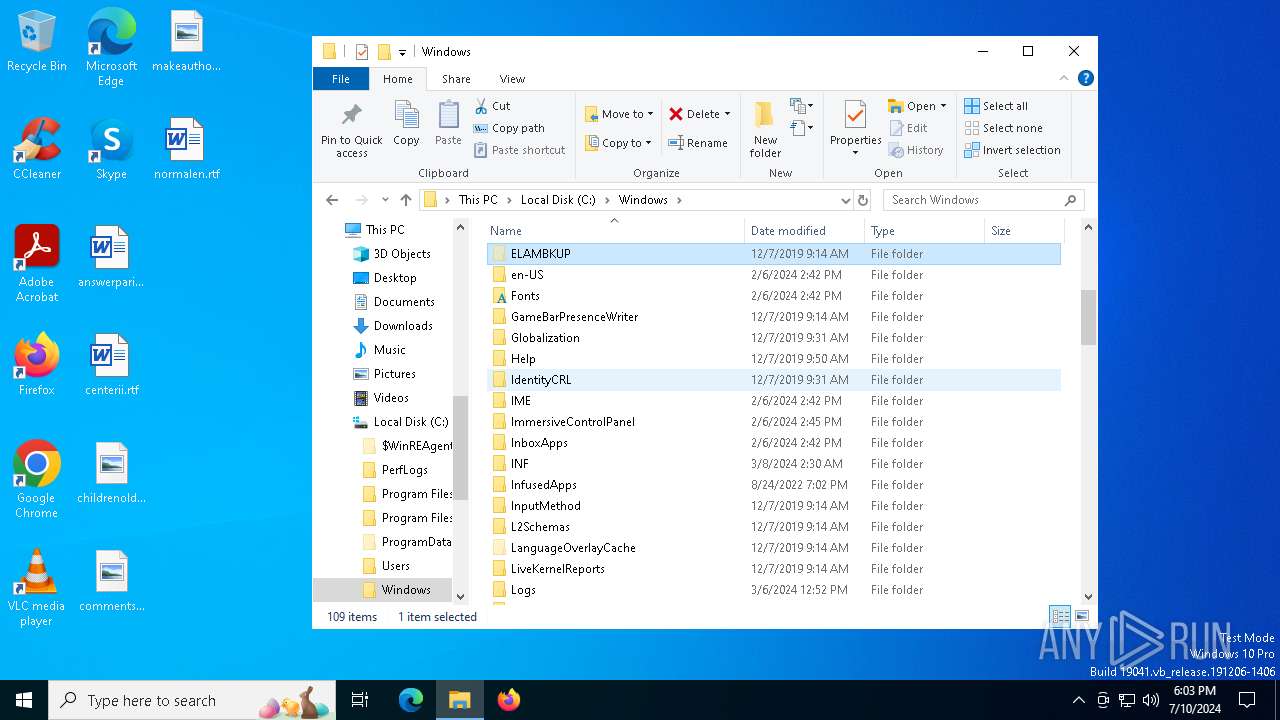
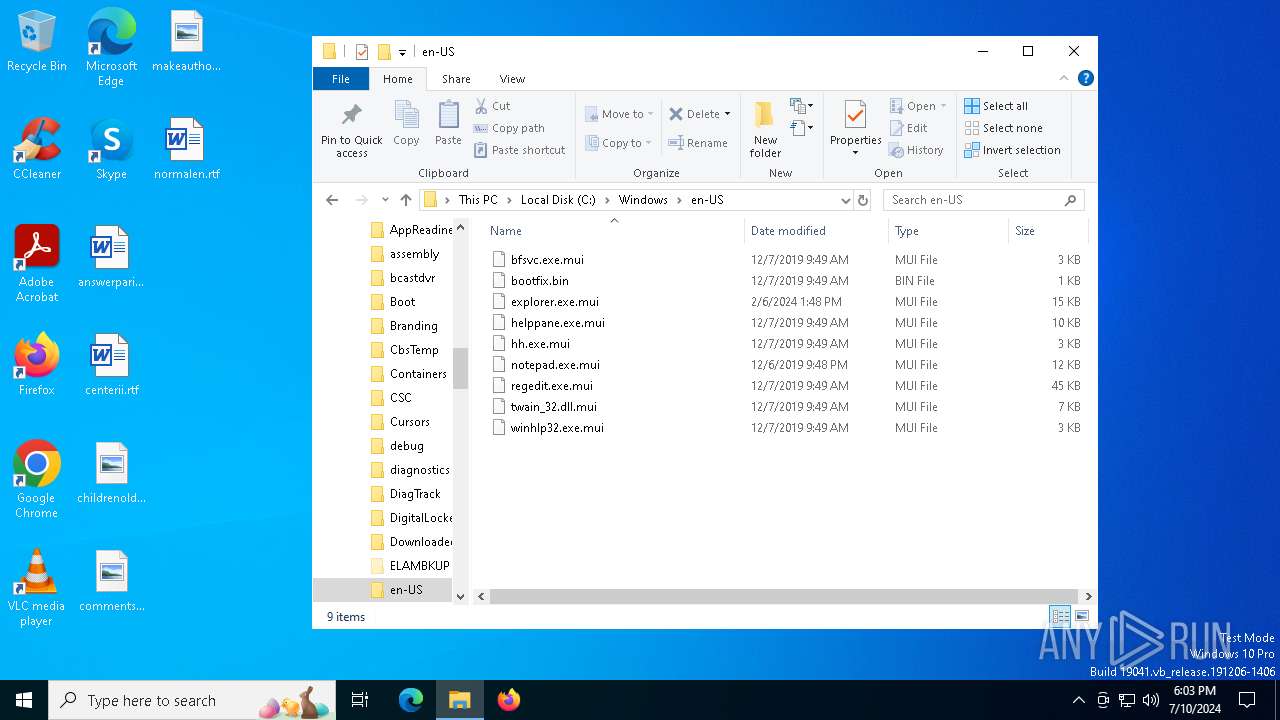
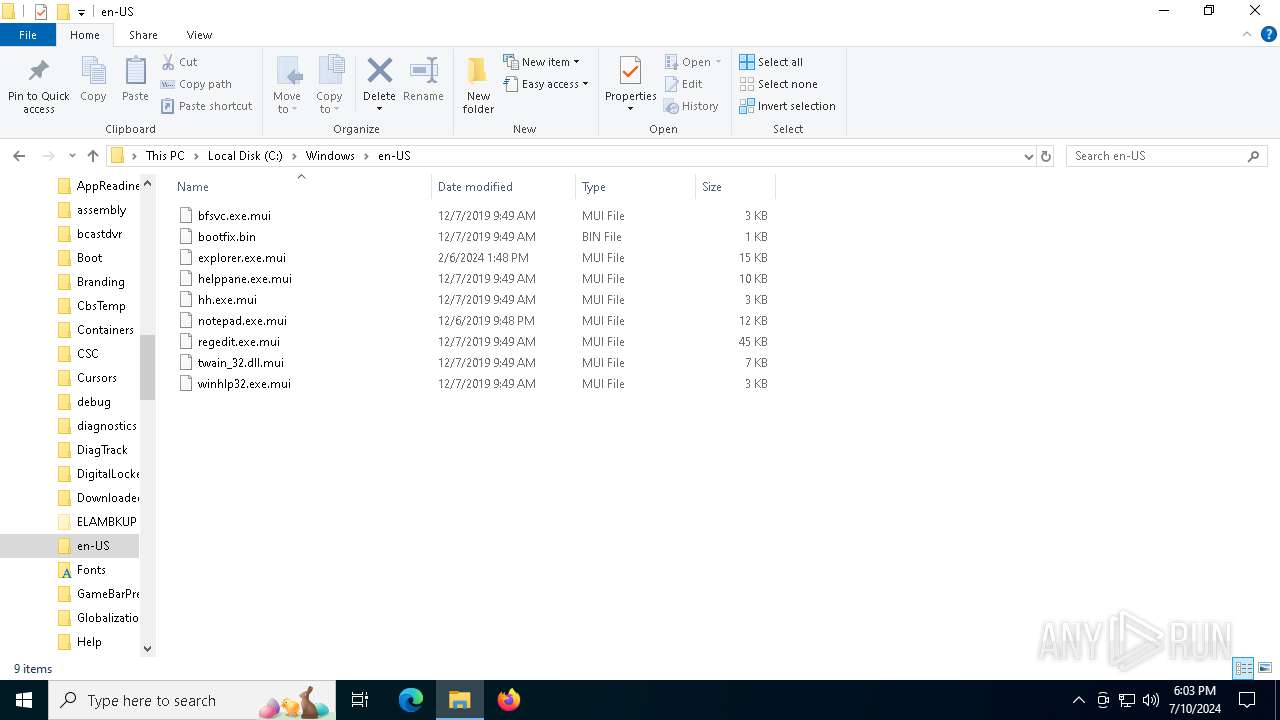
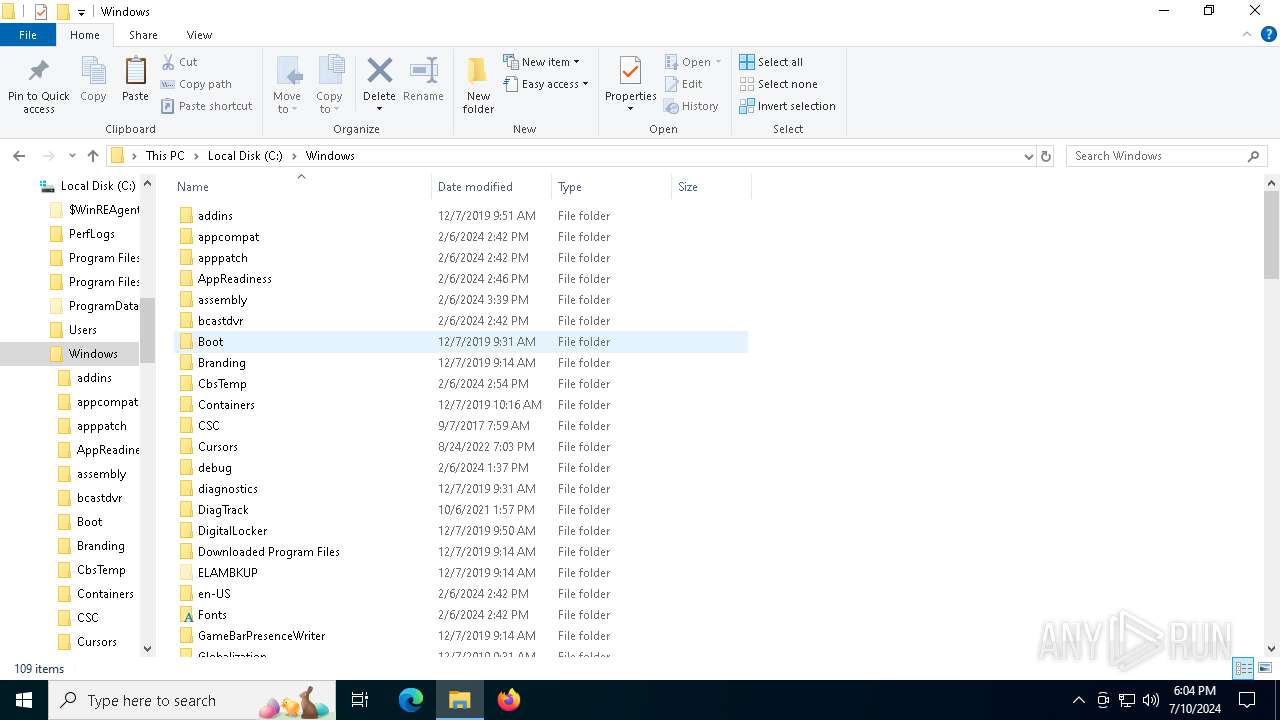
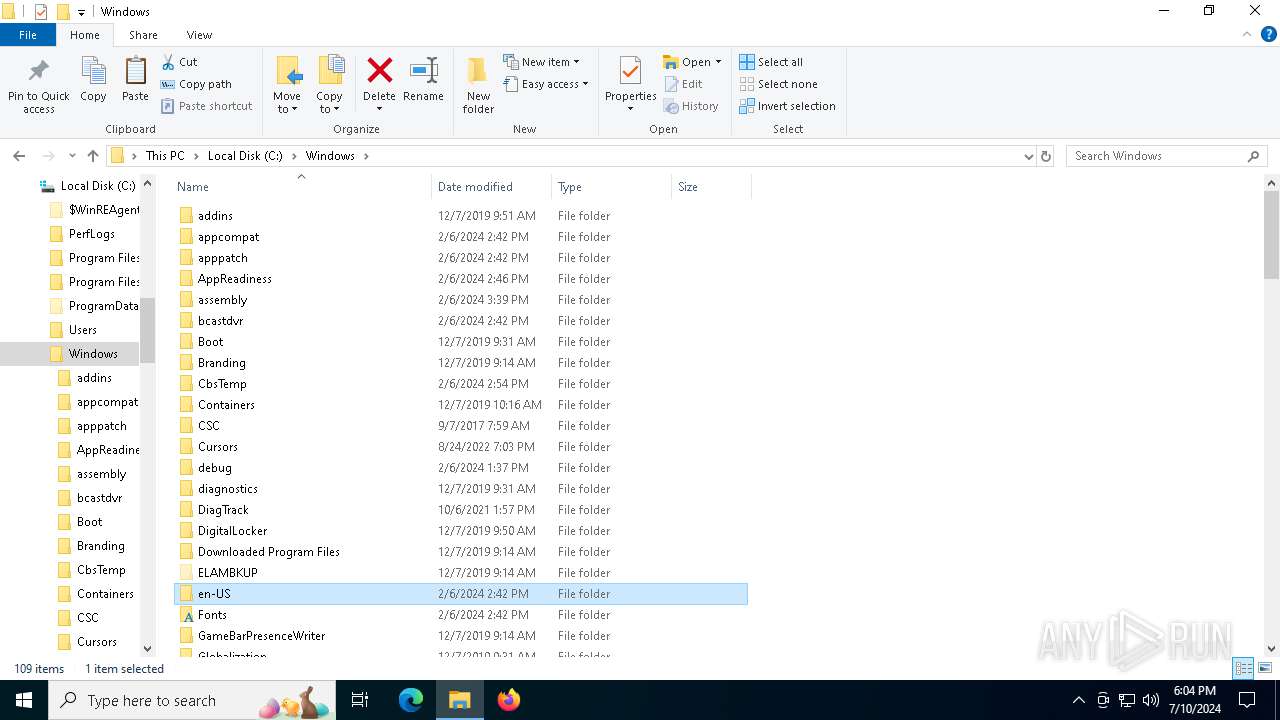
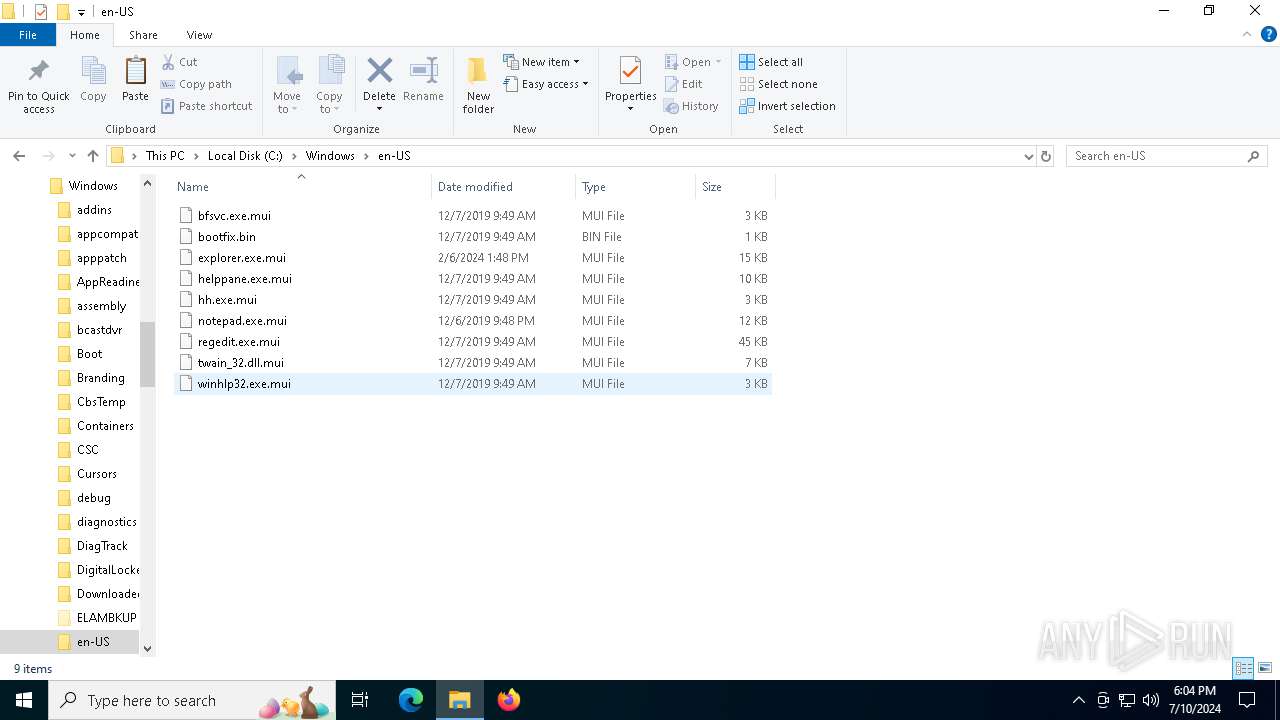
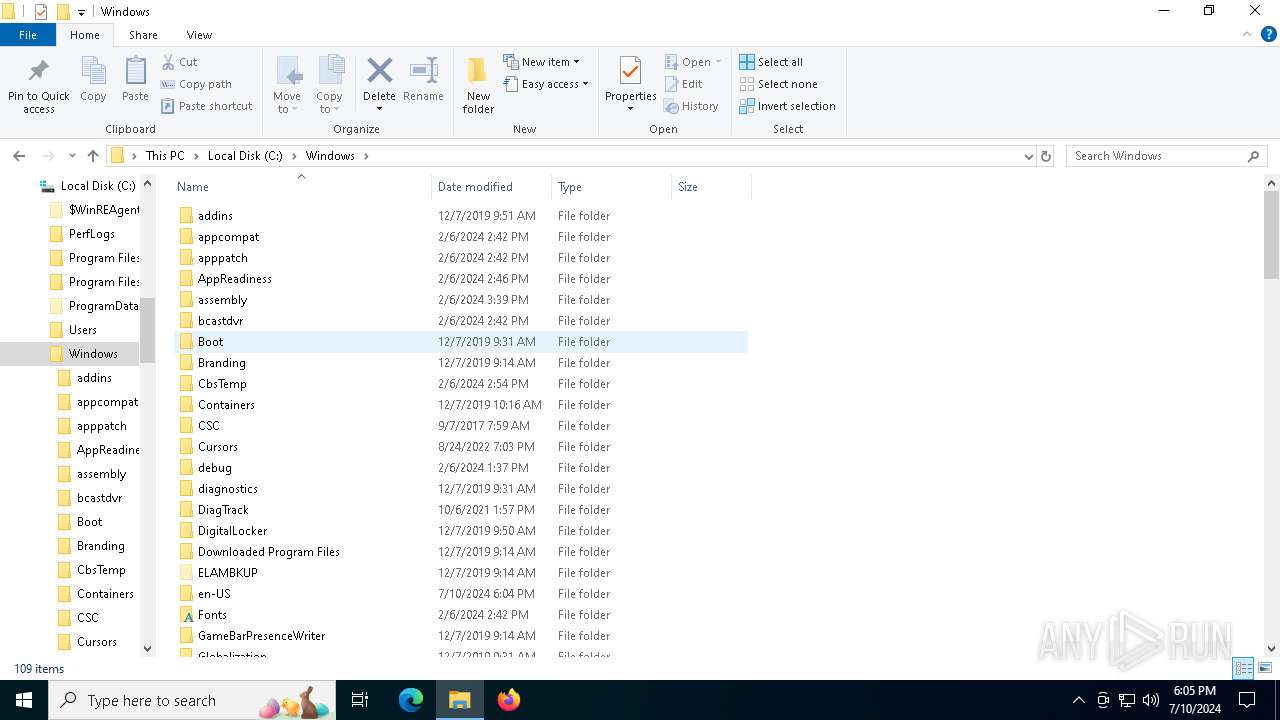
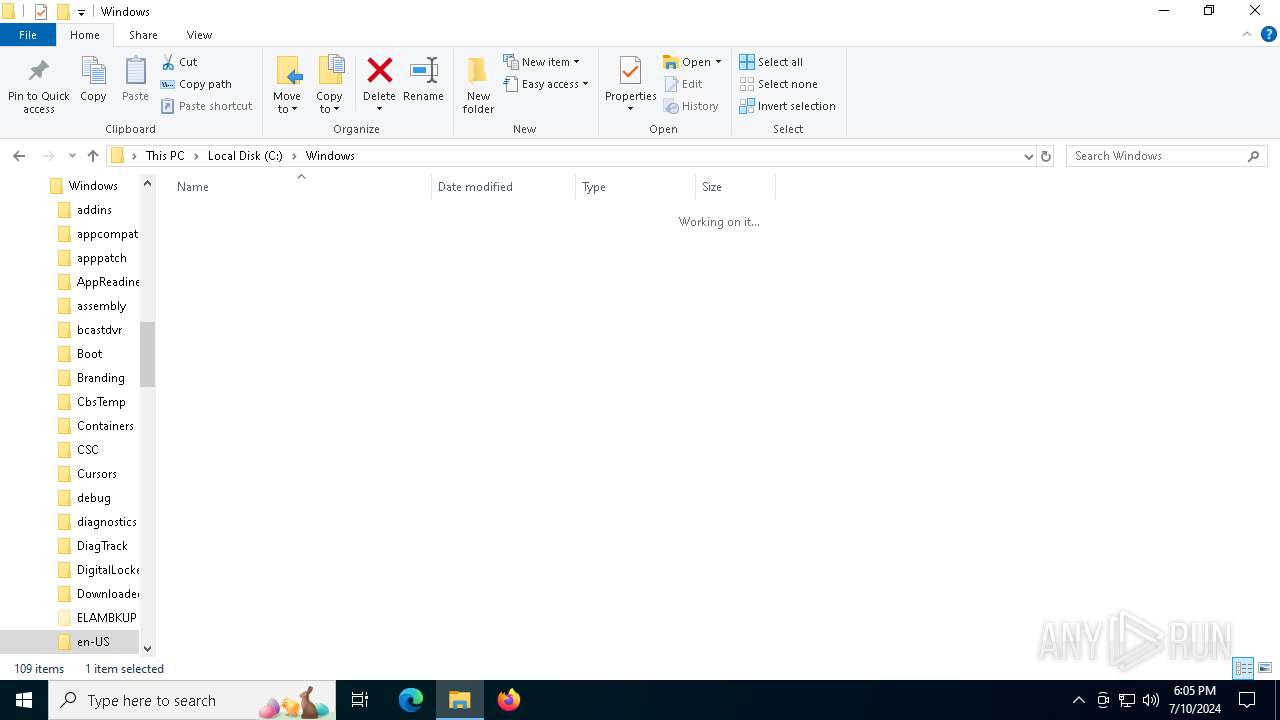
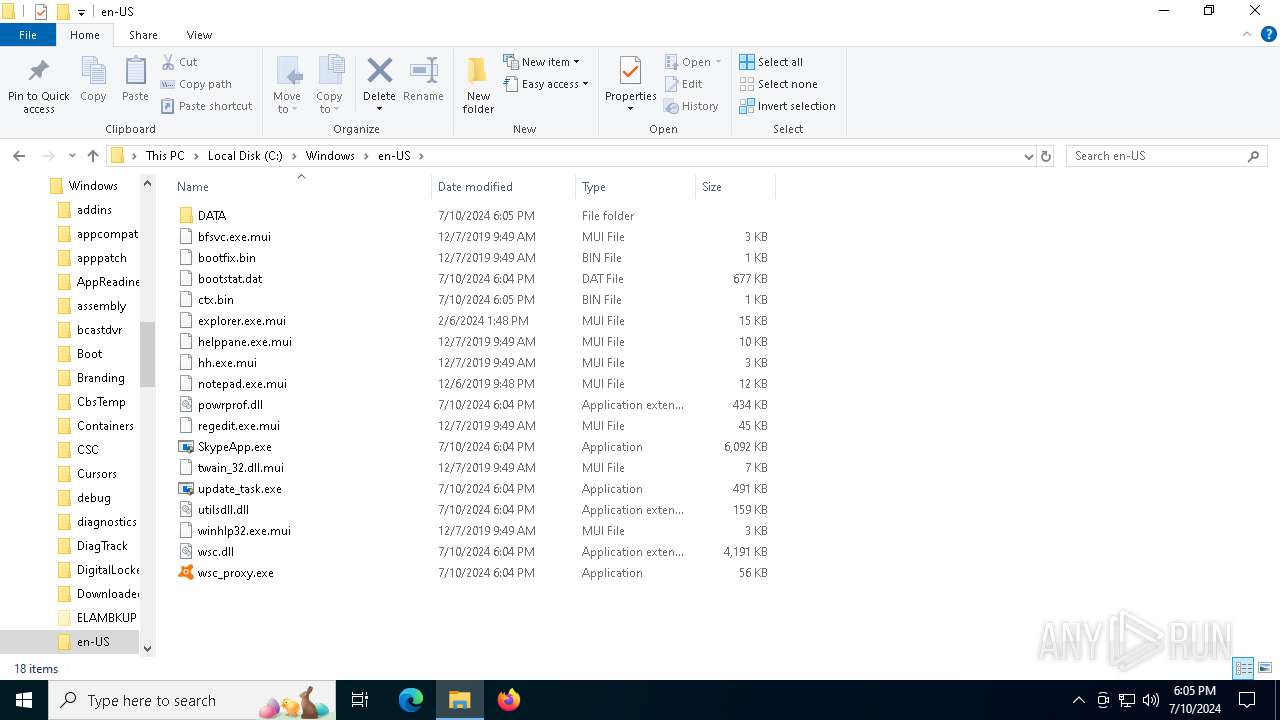
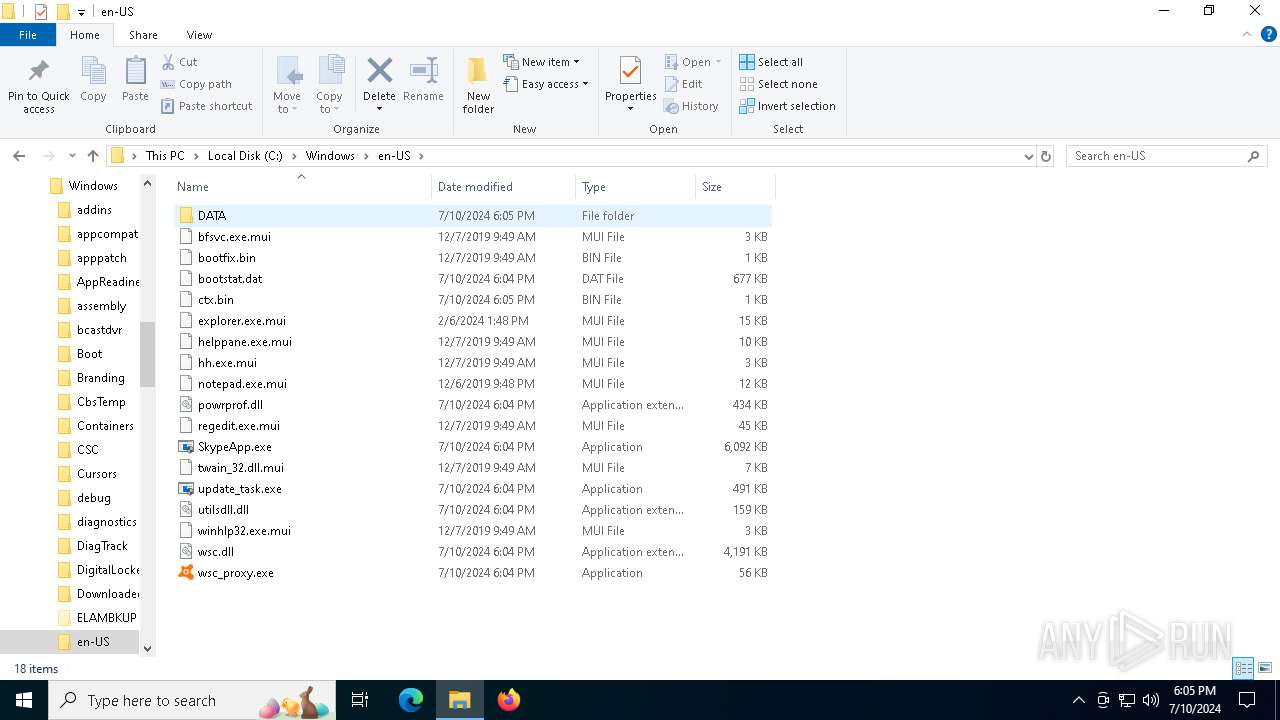
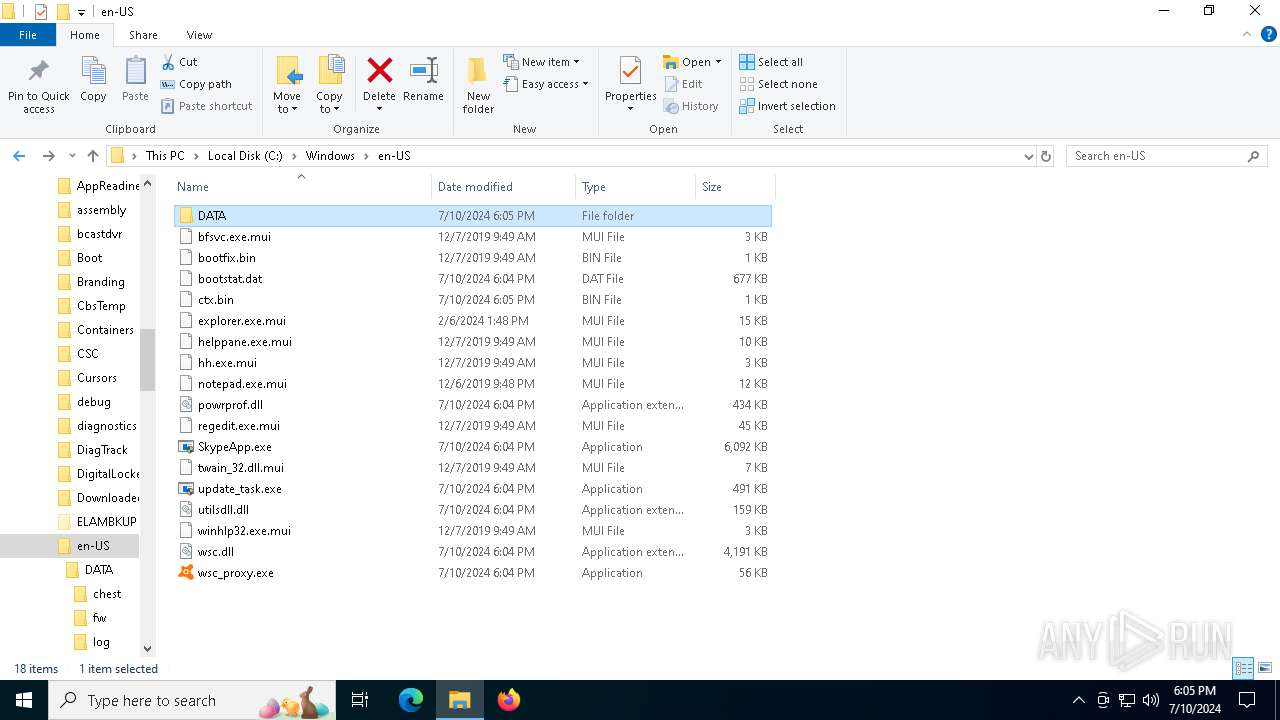
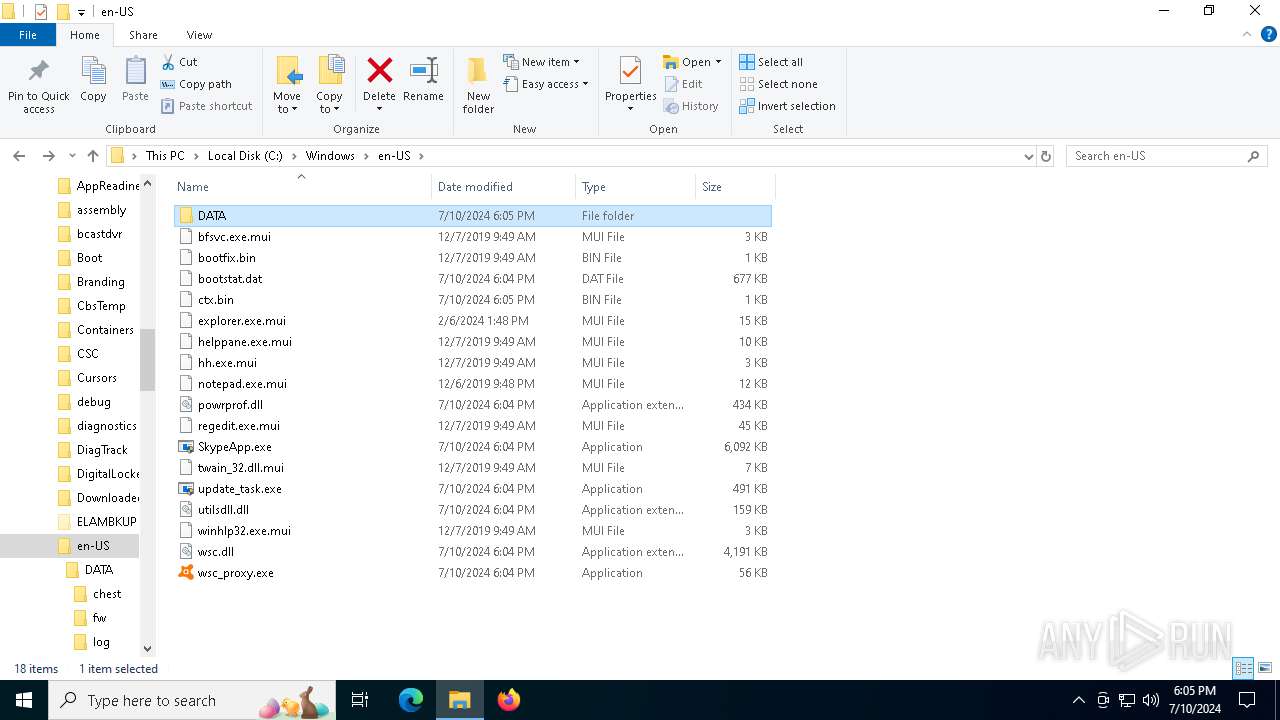
| 3136 | "C:\Windows\en-US\wsc_proxy.exe" /runassvc /rpcserver /wsc_name:" " | C:\Windows\en-US\wsc_proxy.exe | services.exe | ||||||||||||
User: SYSTEM Company: AVAST Software Integrity Level: SYSTEM Description: Avast remediation exe Exit code: 255 Version: 21.4.6162.0 Modules
| |||||||||||||||
| 3540 | "C:\Windows\en-US\update_task.exe" | C:\Windows\en-US\update_task.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient Virus Feedback Service Exit code: 3221226540 Version: 7.2.4.0972 Modules
| |||||||||||||||
| 3776 | "C:\WINDOWS\SystemApps\Microsoft.LockApp_cw5n1h2txyewy\LockApp.exe" -ServerName:WindowsDefaultLockScreen.AppX7y4nbzq37zn4ks9k7amqjywdat7d3j2z.mca | C:\Windows\SystemApps\Microsoft.LockApp_cw5n1h2txyewy\LockApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LockApp.exe Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4632 | C:\WINDOWS\system32\WerFault.exe -u -p 3136 -s 164 | C:\Windows\System32\WerFault.exe | wsc_proxy.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | "C:\Windows\en-US\update_task.exe" | C:\Windows\en-US\update_task.exe | explorer.exe | ||||||||||||
User: admin Company: Fortinet Inc. Integrity Level: HIGH Description: FortiClient Virus Feedback Service Version: 7.2.4.0972 Modules
| |||||||||||||||
| 4800 | "C:\Windows\en-US\SkypeApp.exe" | C:\Windows\en-US\SkypeApp.exe | — | update_task.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
11 531
Read events
11 489
Write events
36
Delete events
6
Modification events
| (PID) Process: | (3068) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-205 |
Value: Word | |||
| (PID) Process: | (3068) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @wmploc.dll,-102 |
Value: Windows Media Player | |||
| (PID) Process: | (4724) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4724) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4724) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4724) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4800) SkypeApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast |
| Operation: | write | Name: | ProgramFolder |
Value: C:\Windows\en-US | |||
| (PID) Process: | (3136) wsc_proxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast\properties |
| Operation: | write | Name: | UseRegistry |
Value: 1 | |||
| (PID) Process: | (3136) wsc_proxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast\Wsc |
| Operation: | write | Name: | IWscAVStatus4 |
Value: | |||
| (PID) Process: | (3136) wsc_proxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast\Wsc |
| Operation: | write | Name: | IWscASStatus |
Value: | |||
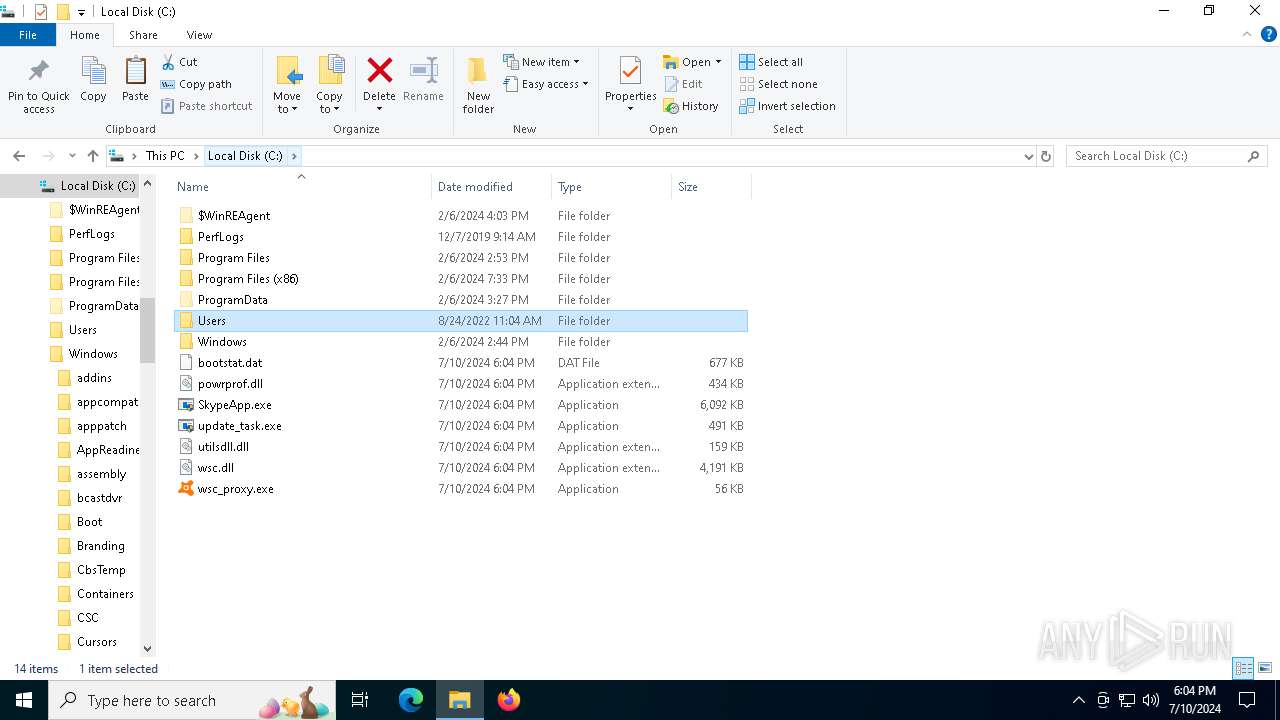
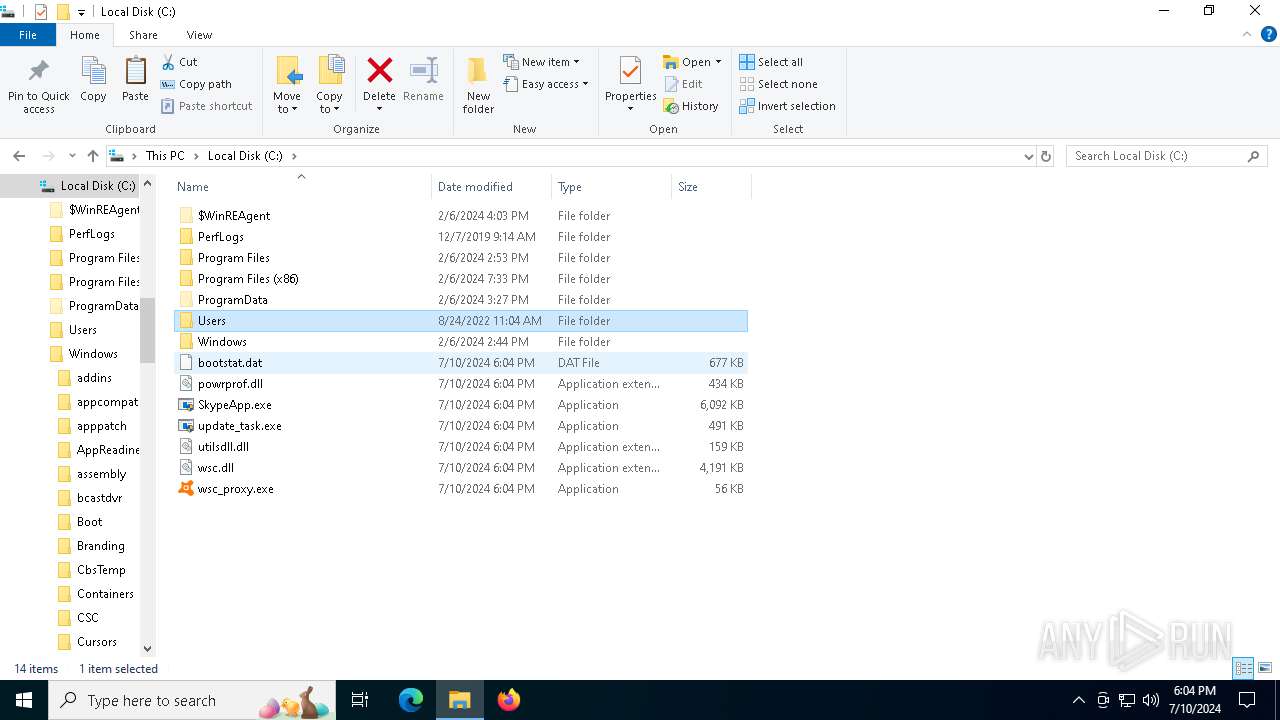
Executable files
6
Suspicious files
6
Text files
4
Unknown types
0
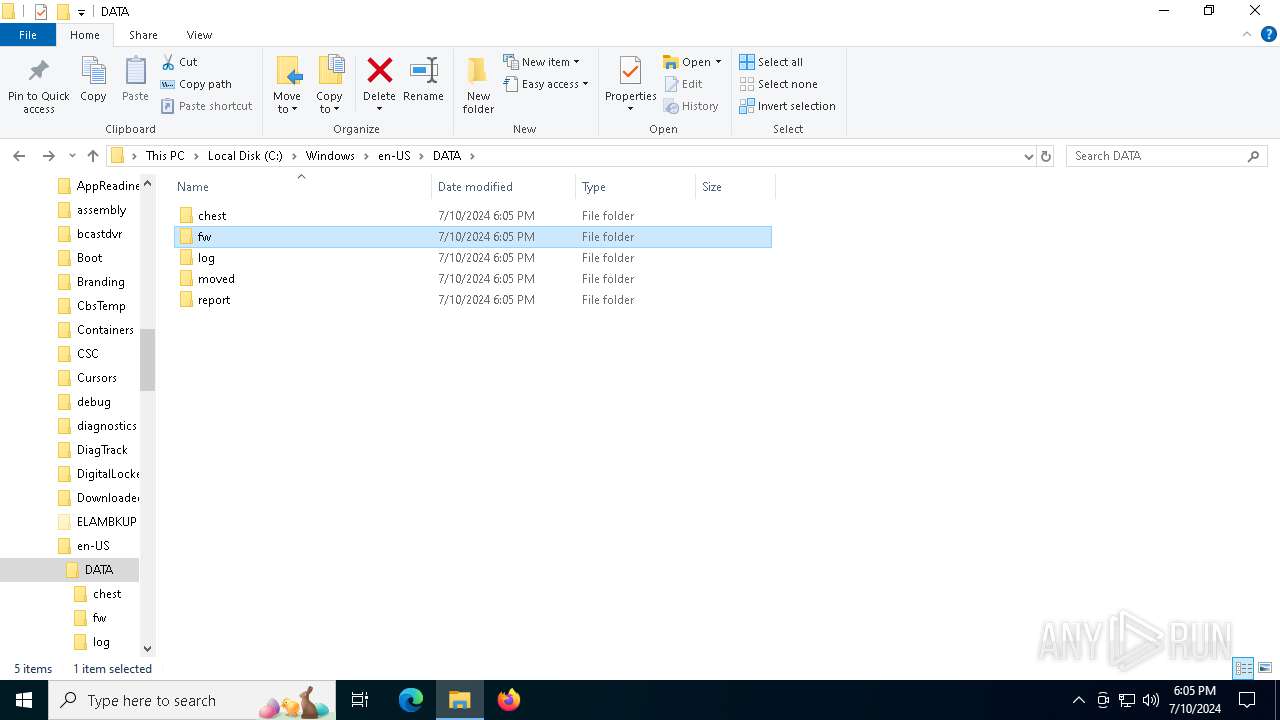
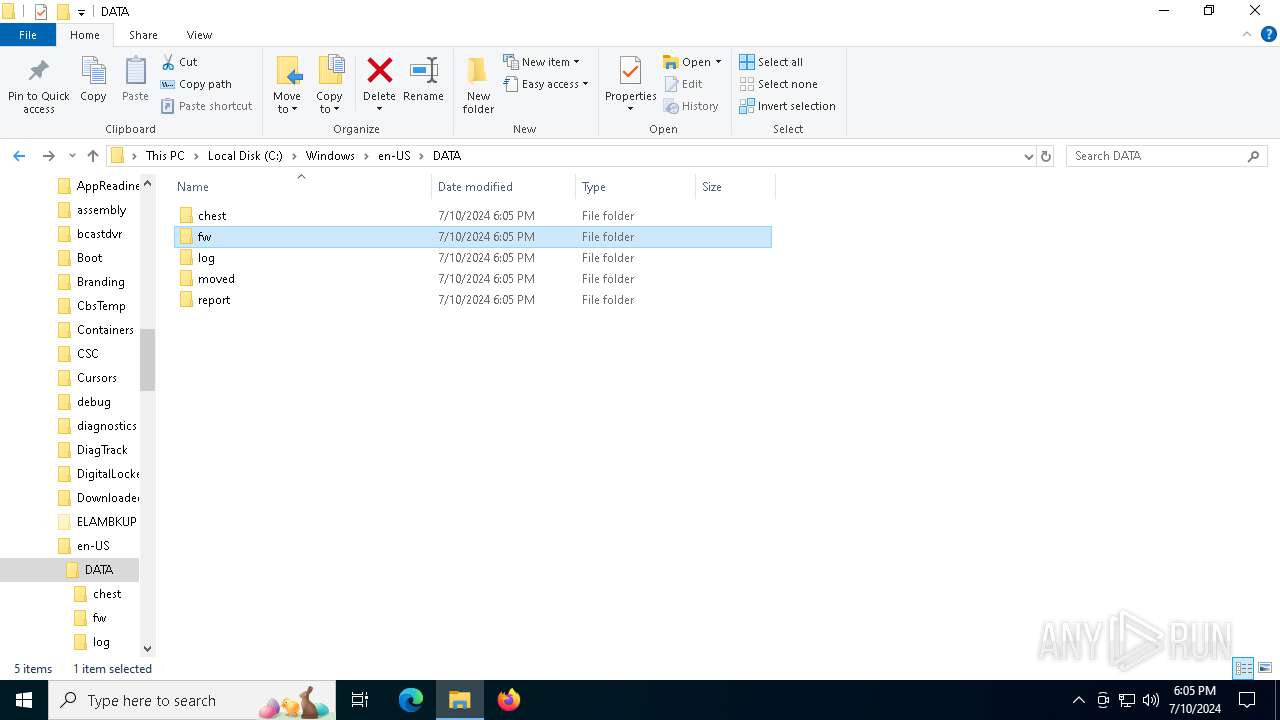
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4632 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_wsc_proxy.exe_8b25899f1fb3d5d2785872911ba1ea1fea2dfb1c_e2da83c0_29d5c027-5183-43c6-a05c-682cb49faa9b\Report.wer | — | |
MD5:— | SHA256:— | |||
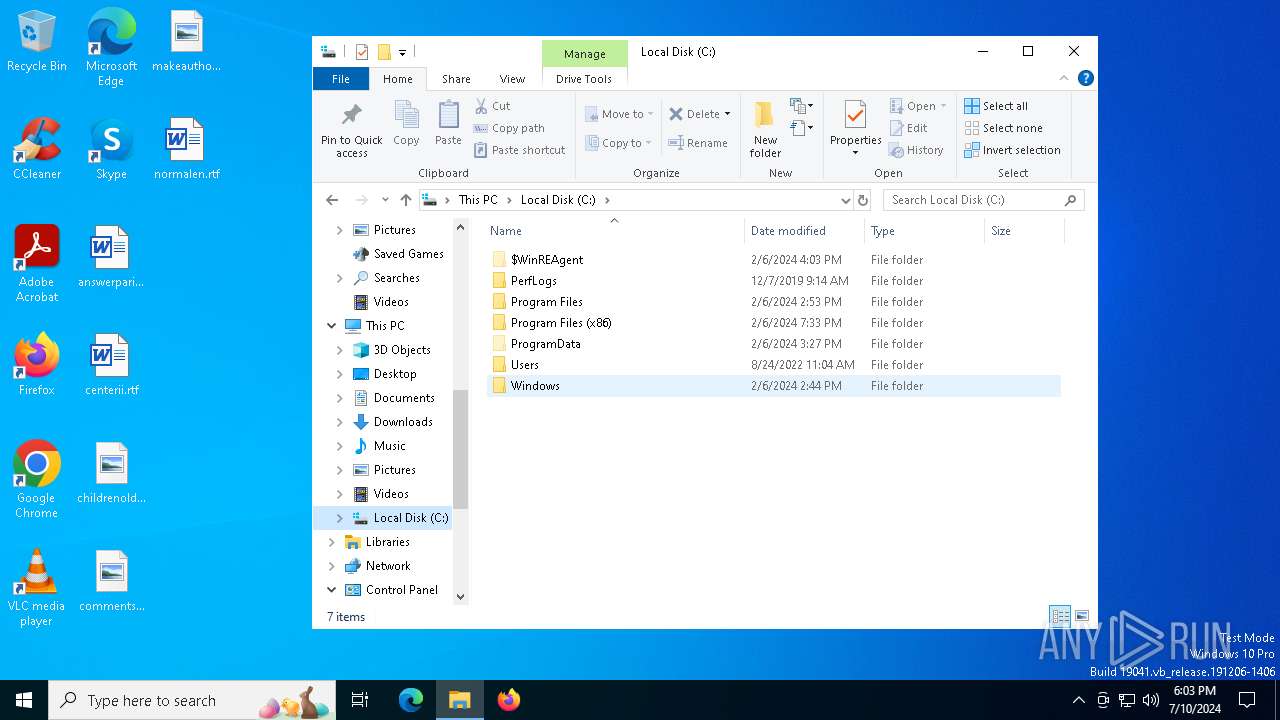
| 2252 | dllhost.exe | C:\Windows\en-US\wsc_proxy.exe | executable | |
MD5:1B231B5C4D36DE4750A587F08338DEDE | SHA256:79E53D36A40951AB328E153BAC9C1E3ADF3330B45899345E645889B9046F06E0 | |||
| 2252 | dllhost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\f01b4d95cf55d32a.automaticDestinations-ms | binary | |
MD5:AE09203D26E59907F858887C2BBB2153 | SHA256:3EE23749C0DE7A738FF5CA060C0C93D3E3D6784B21AA13FBE852680925AF4438 | |||
| 2252 | dllhost.exe | C:\Windows\en-US\bootstat.dat | binary | |
MD5:CD92E4F79851F17ACF0719F3C9C12B39 | SHA256:7A510517252AA94DBD5E0C185F3B42C3AAA87292DA681ECF0B6B755B3C627754 | |||
| 2252 | dllhost.exe | C:\Windows\en-US\powrprof.dll | executable | |
MD5:E0B6BD1728237354A7FB60407ED098D0 | SHA256:0B8B72E4C1EA80AF57EE638BC8E65BA48550E716C77EB88EA319CC007C7C3B57 | |||
| 4632 | WerFault.exe | C:\WINDOWS\AppCompat\Programs\Amcache.hve | binary | |
MD5:8301D65F3DDBB258C1E453E5BAE38257 | SHA256:D6570458B7FDBB3EE21740E6BE43A1FF8554CB5CB0E053733686D303DEC028DF | |||
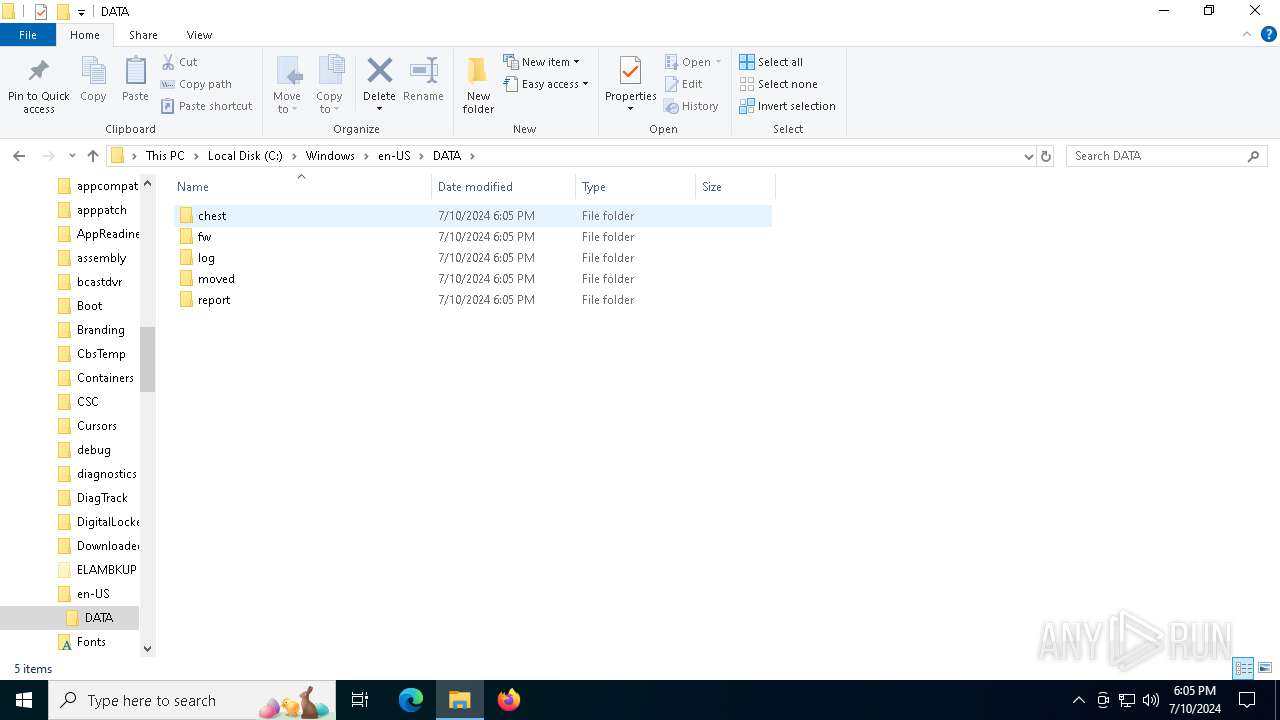
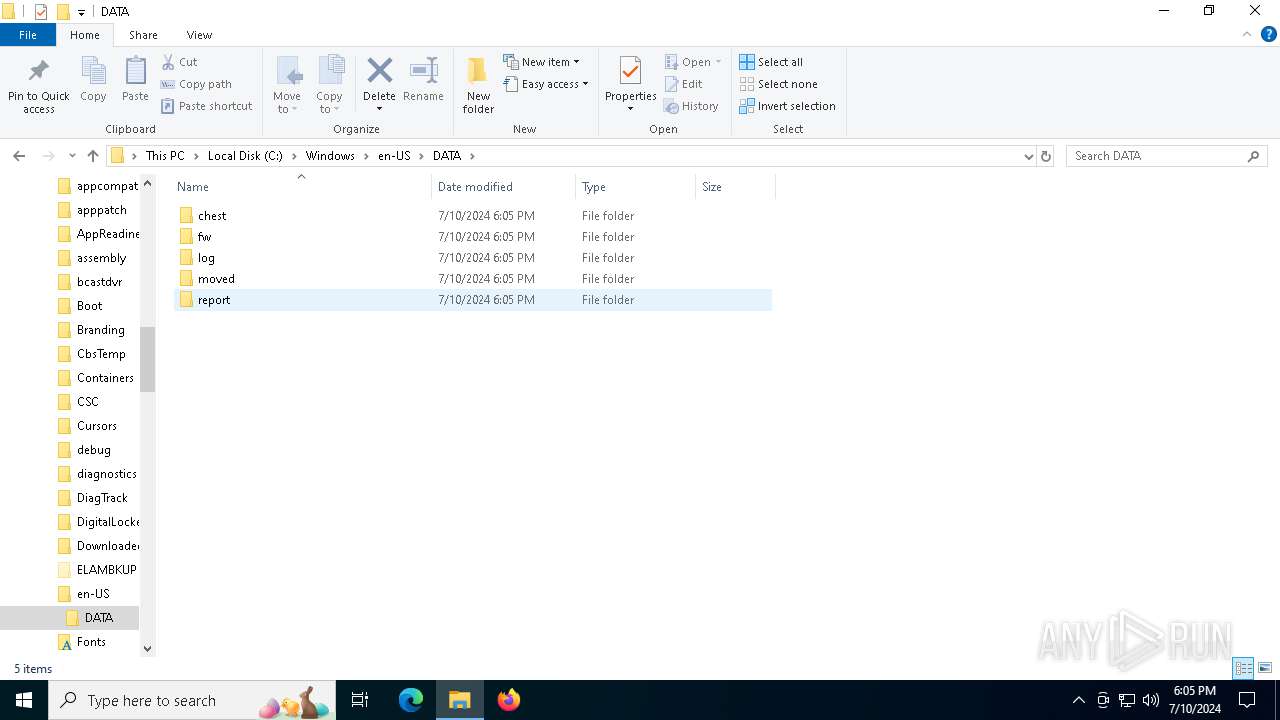
| 3136 | wsc_proxy.exe | C:\ProgramData\Avast Software\Avast\log\wsc.log | text | |
MD5:ECAA88F7FA0BF610A5A26CF545DCD3AA | SHA256:F1945CD6C19E56B3C1C78943EF5EC18116907A4CA1EFC40A57D48AB1DB7ADFC5 | |||
| 4632 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA587.tmp.xml | xml | |
MD5:85231EDD3AC9538D512447C523F90BA9 | SHA256:AA6925A195A0D32EE4AA8D42D584131583921E5403EB984CA31C14879F8C7975 | |||
| 4632 | WerFault.exe | C:\WINDOWS\system32\config\systemprofile\AppData\Local\CrashDumps\wsc_proxy.exe.3136.dmp | binary | |
MD5:3396BB9B8B43E6B69F64CBD6585F0768 | SHA256:A6746B31DDB437EE743AD07541832EC86D43AC497FD9732AC74FF9839933B790 | |||
| 4632 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA4E8.tmp.dmp | binary | |
MD5:3C93550C44951DBBA85316CACAE9D6D9 | SHA256:9B0D2EB6FD0D29677054FDC0DEDC6ECCE946C7EC36F9DA6AF0E39D31D980868A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
30
DNS requests
13
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2072 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1972 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6004 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2072 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3040 | OfficeClickToRun.exe | 13.69.239.79:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4632 | WerFault.exe | 104.208.16.94:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
198.187.3.20.in-addr.arpa |
| unknown |
d.4.1.9.1.6.7.1.0.0.0.0.0.0.0.0.1.0.0.9.0.0.1.f.1.1.1.0.1.0.a.2.ip6.arpa |
| unknown |
Threats
Process | Message |
|---|---|
wsc_proxy.exe | [2024-07-10 18:05:04.881] [error ] [crashguard ] [ 3136: 5776] [E9669F: 103] Dump path 'C:\ProgramData\Avast Software\Avast\log' does not exist. Directory should be already created.
|