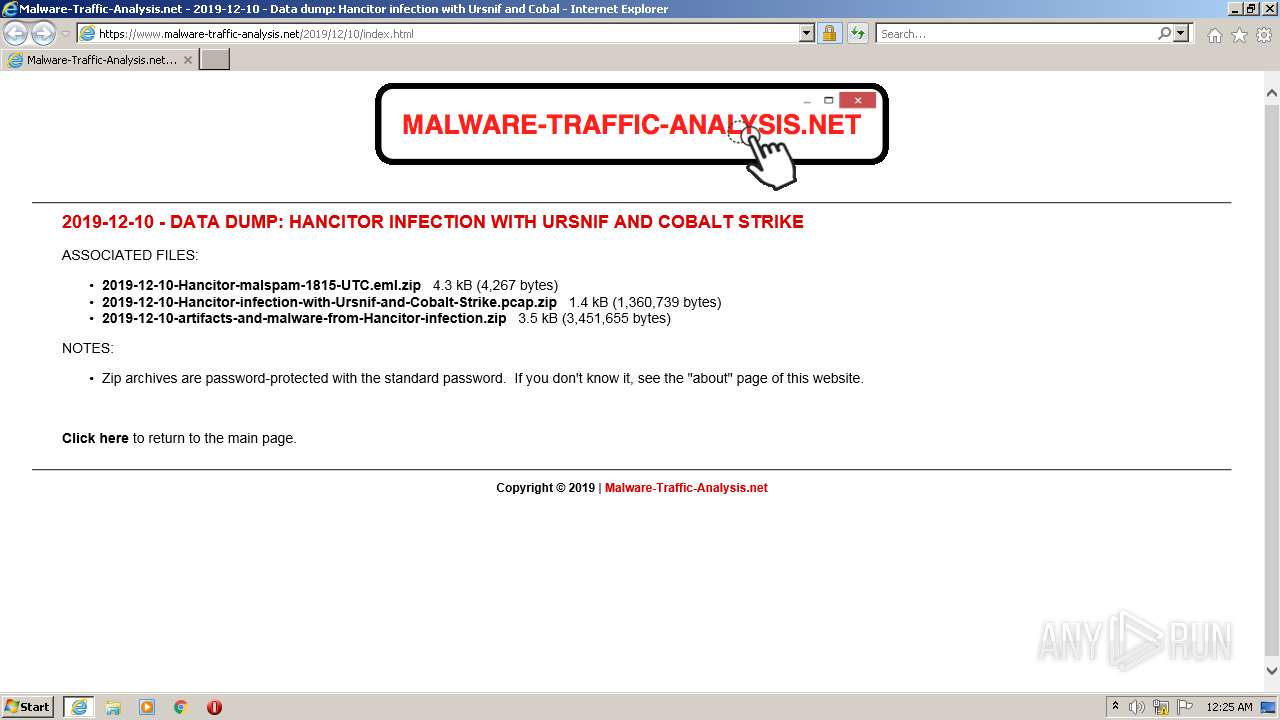
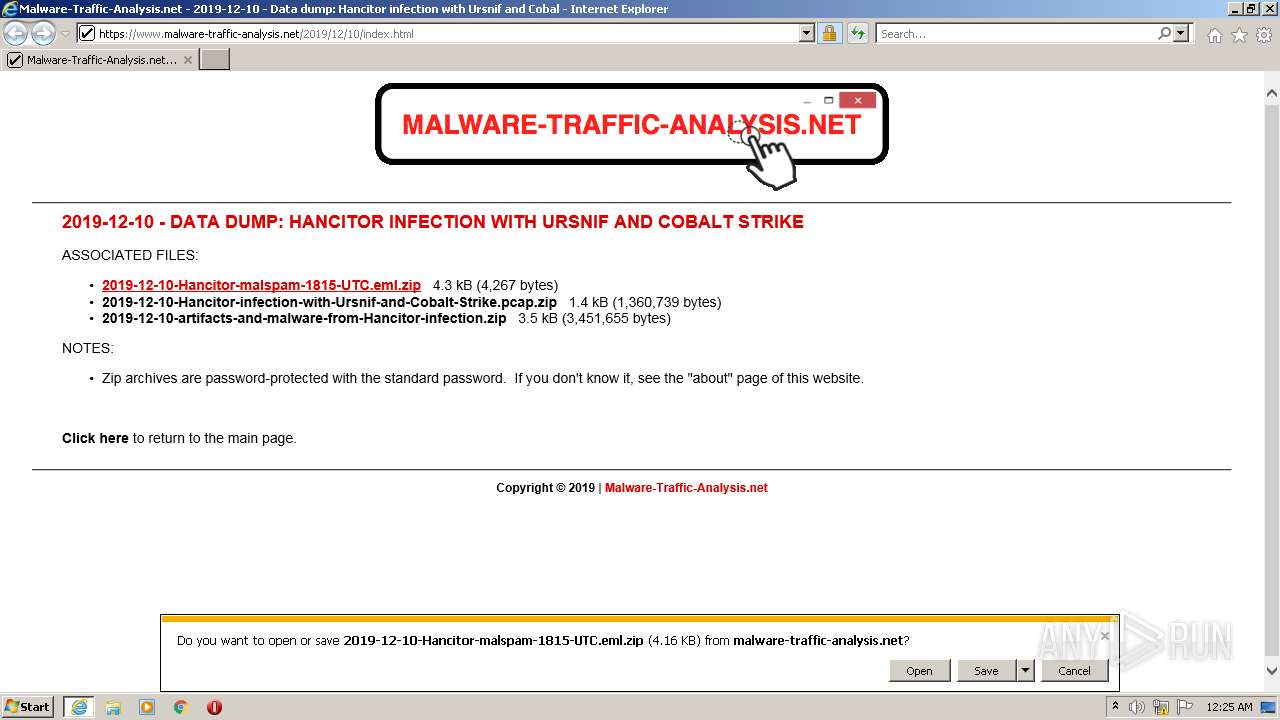
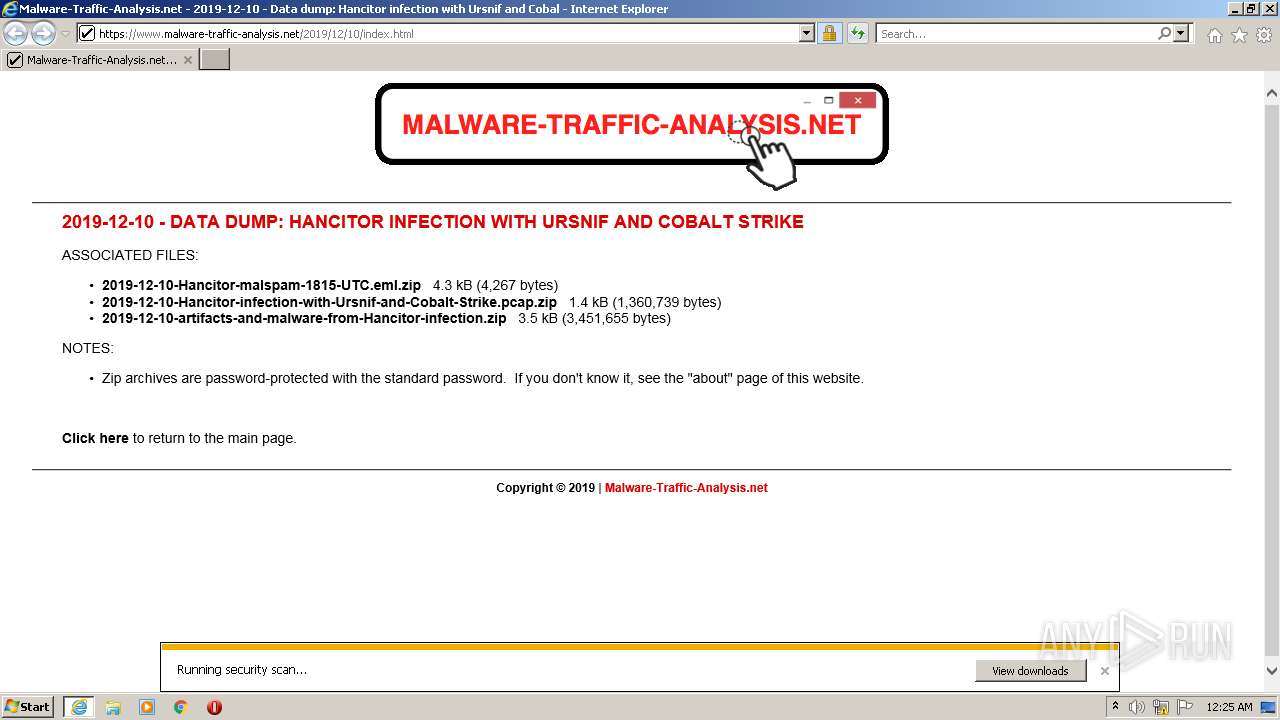
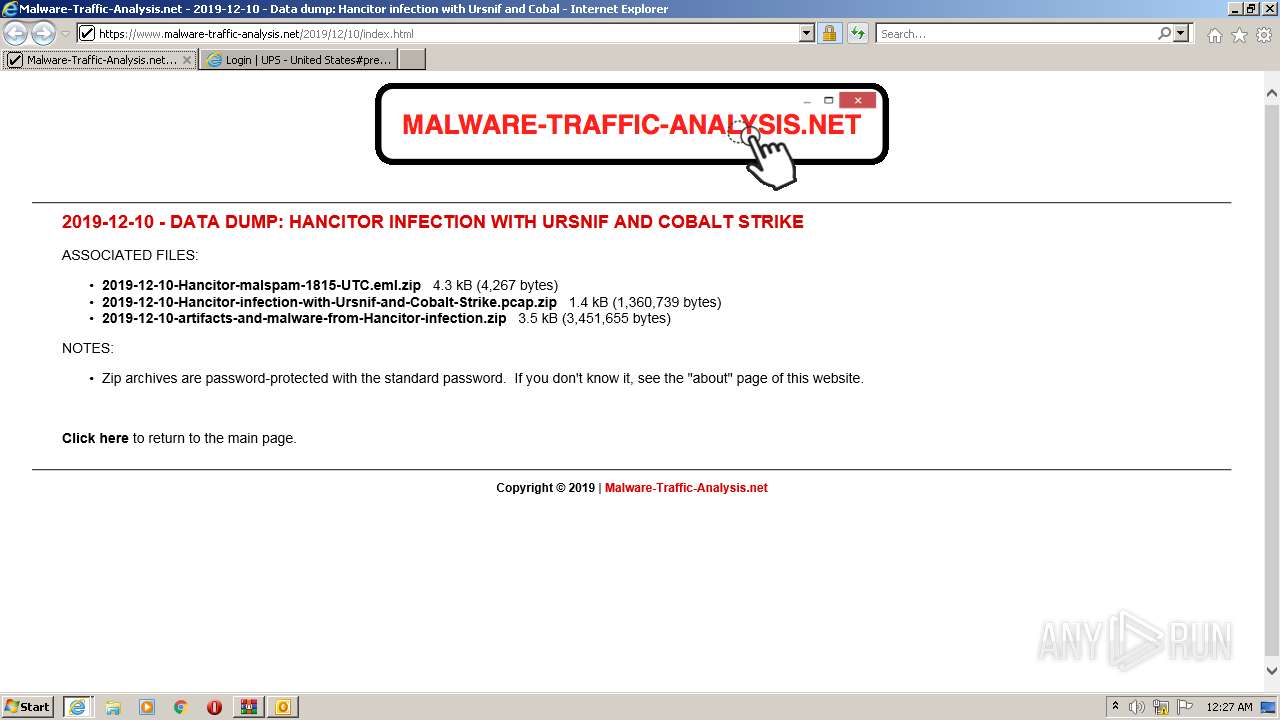
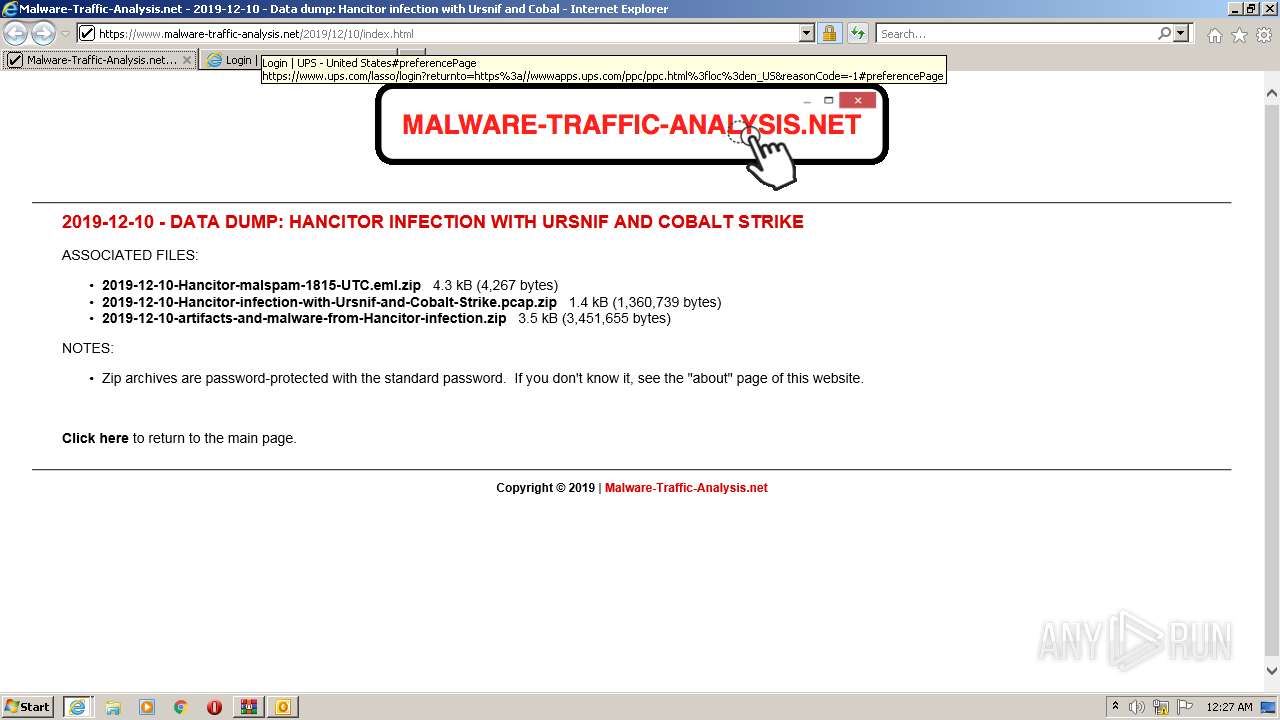
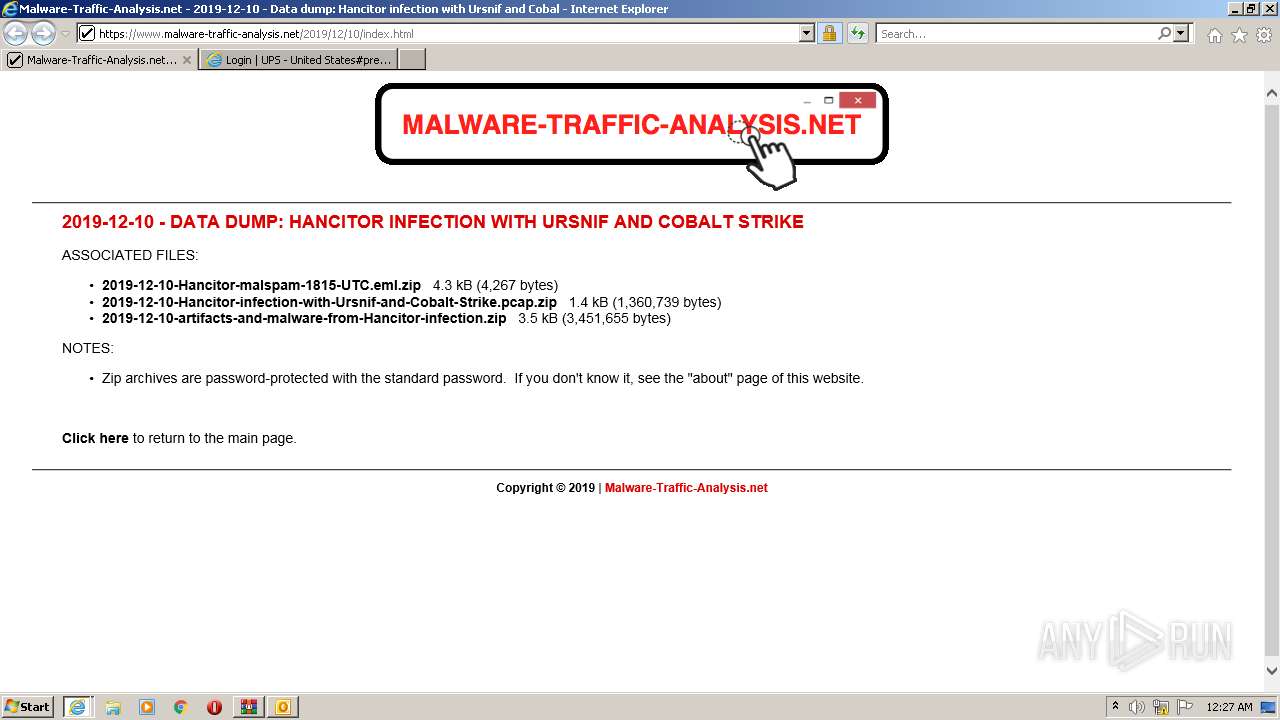
| URL: | https://www.malware-traffic-analysis.net/2019/12/10/index.html |
| Full analysis: | https://app.any.run/tasks/da3c3259-5bf5-44c9-a126-ada9ef9f2b3c |
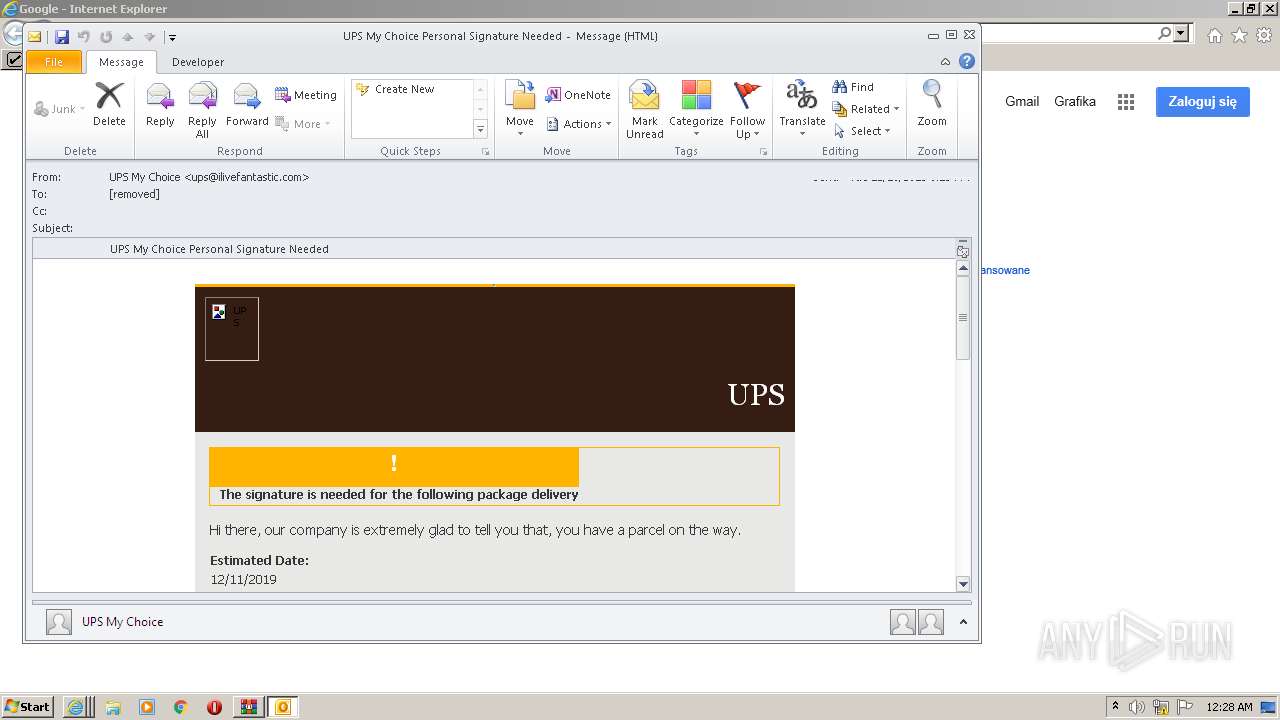
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 23:25:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4456DD6179B36FA0F9DFD0C18B4BA8F4 |
| SHA1: | EA146963E96CF96CA407A7E02AD463C27C07B3CB |
| SHA256: | 7A47D3DFA0211261B430F33EBD483DECE004AA15135D19CE7CA77392365C5C46 |
| SSDEEP: | 3:N8DSLHXWQfigcWMMLA2OHd5G:2OLHpJYpjG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 2192)
- WinRAR.exe (PID: 3268)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3340)
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 3268)
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 2056)
Reads the computer name
- WinRAR.exe (PID: 3268)
- OUTLOOK.EXE (PID: 2192)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3340)
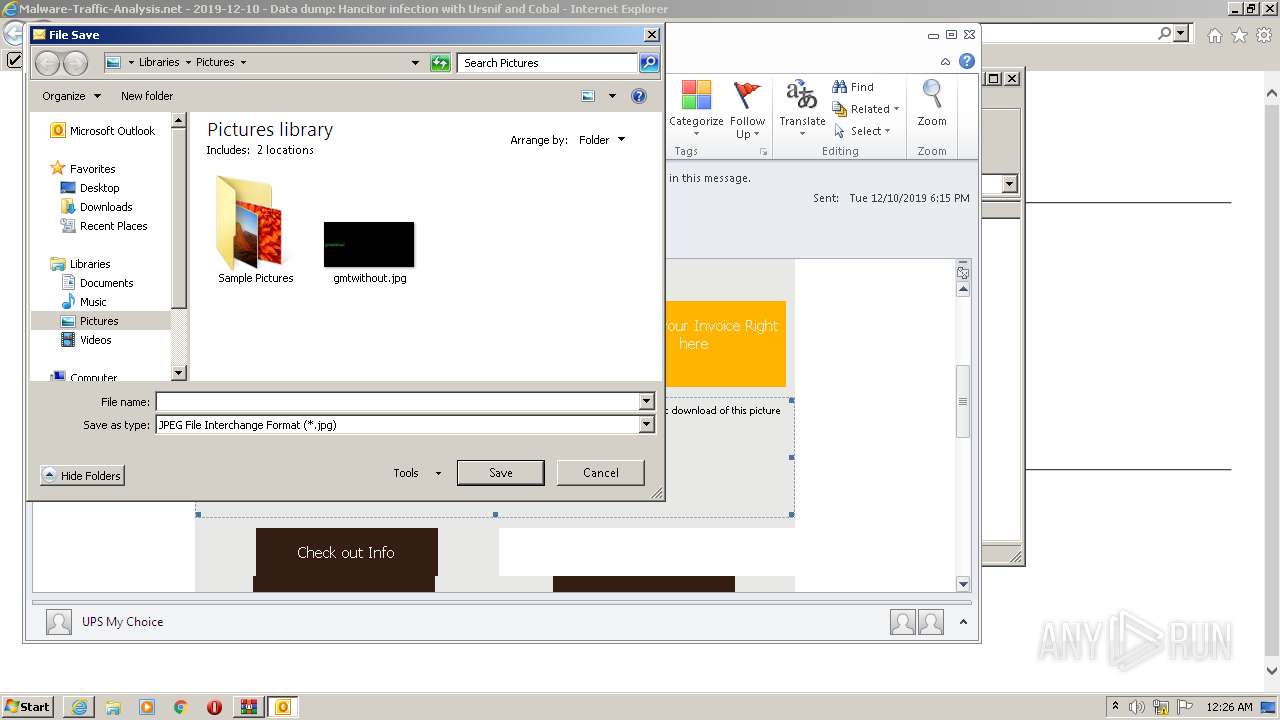
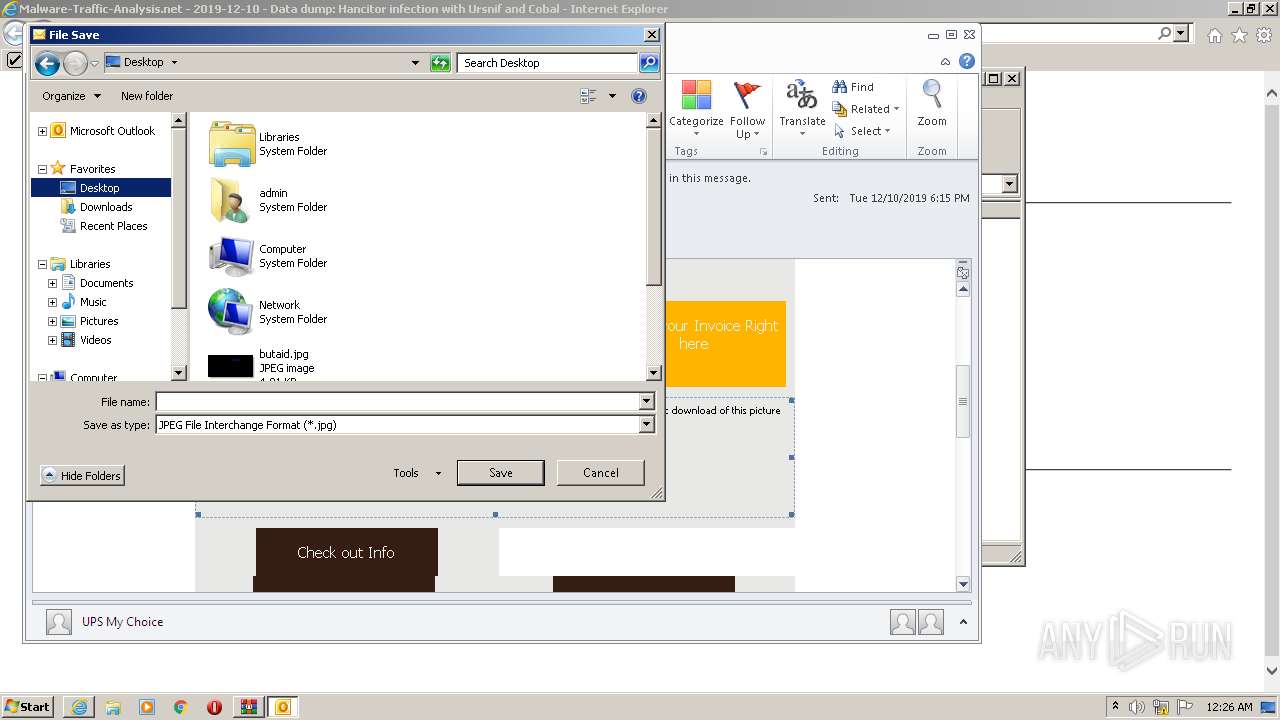
Creates files in the user directory
- OUTLOOK.EXE (PID: 2192)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3340)
Reads default file associations for system extensions
- OUTLOOK.EXE (PID: 2192)
Searches for installed software
- OUTLOOK.EXE (PID: 2192)
Executed via COM
- DllHost.exe (PID: 2172)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3340)
INFO
Reads the computer name
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 3236)
- explorer.exe (PID: 3976)
- DllHost.exe (PID: 2172)
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 2056)
- iexplore.exe (PID: 1596)
Checks supported languages
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 3236)
- DllHost.exe (PID: 2172)
- explorer.exe (PID: 3976)
- iexplore.exe (PID: 2056)
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 3064)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2532)
Changes internet zones settings
- iexplore.exe (PID: 2532)
Checks Windows Trust Settings
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 2532)
- OUTLOOK.EXE (PID: 2192)
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 2056)
Reads settings of System Certificates
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 2532)
- OUTLOOK.EXE (PID: 2192)
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 2056)
Application launched itself
- iexplore.exe (PID: 2532)
Changes settings of System certificates
- iexplore.exe (PID: 2532)
Reads internet explorer settings
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 2056)
- iexplore.exe (PID: 1596)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2532)
Manual execution by user
- explorer.exe (PID: 3976)
Creates files in the user directory
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 2056)
- iexplore.exe (PID: 1596)
Reads CPU info
- iexplore.exe (PID: 3064)
- iexplore.exe (PID: 2056)
- iexplore.exe (PID: 1596)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1596 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2532 CREDAT:3216661 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2532 CREDAT:1119504 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2172 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
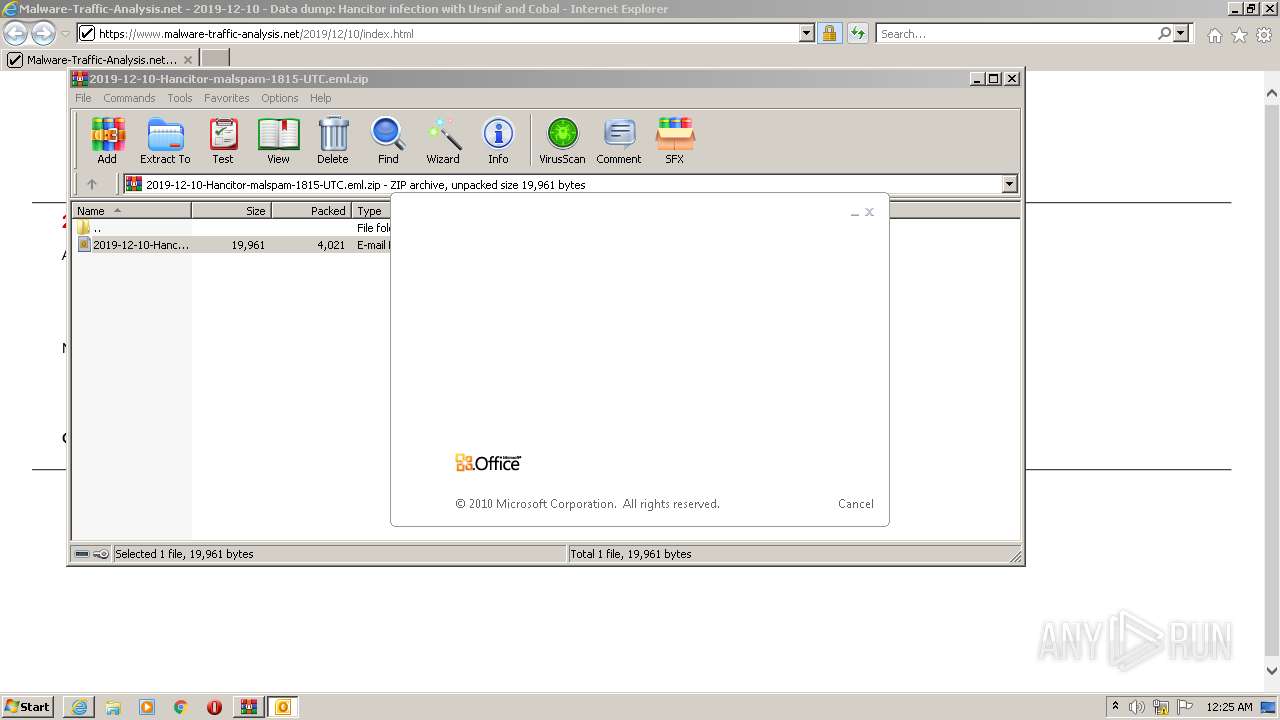
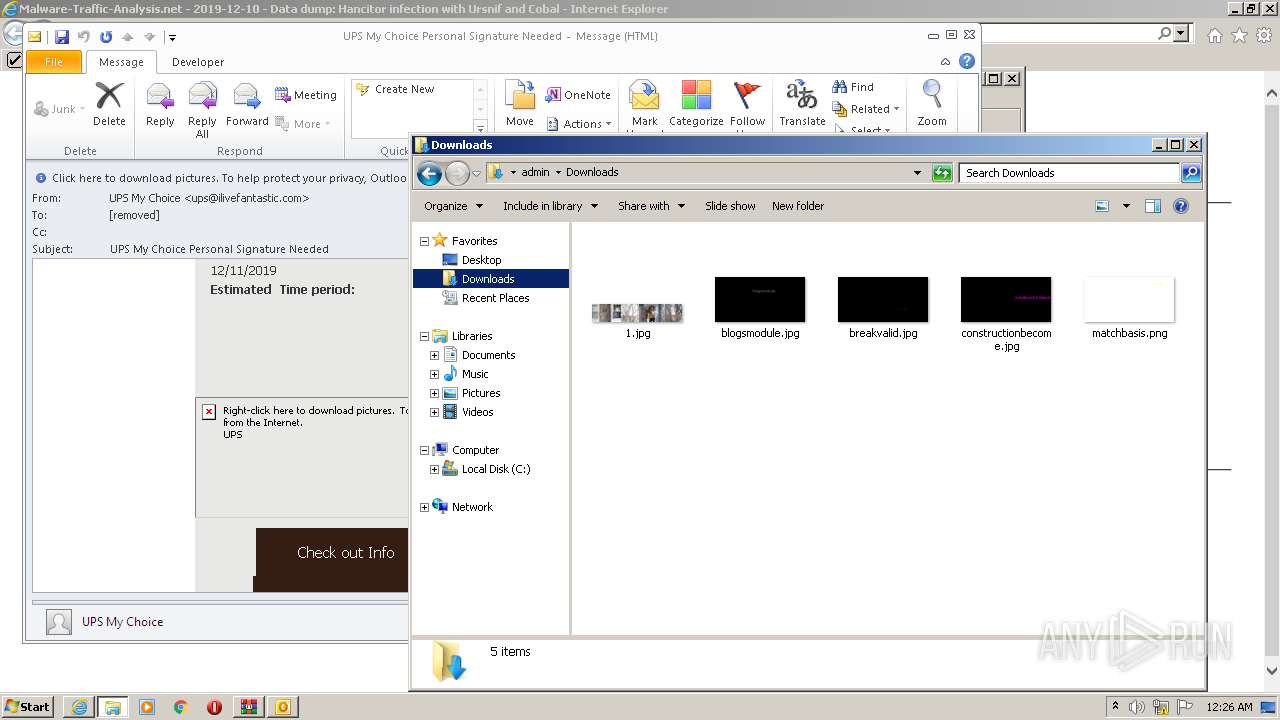
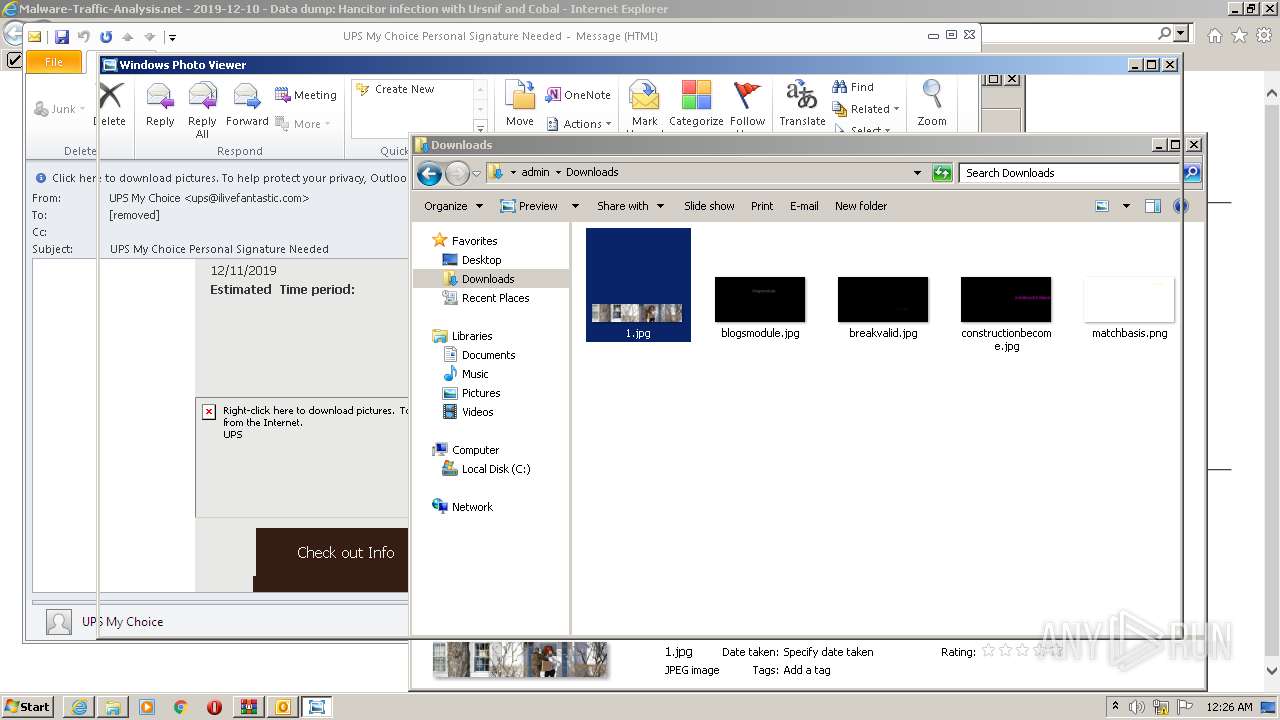
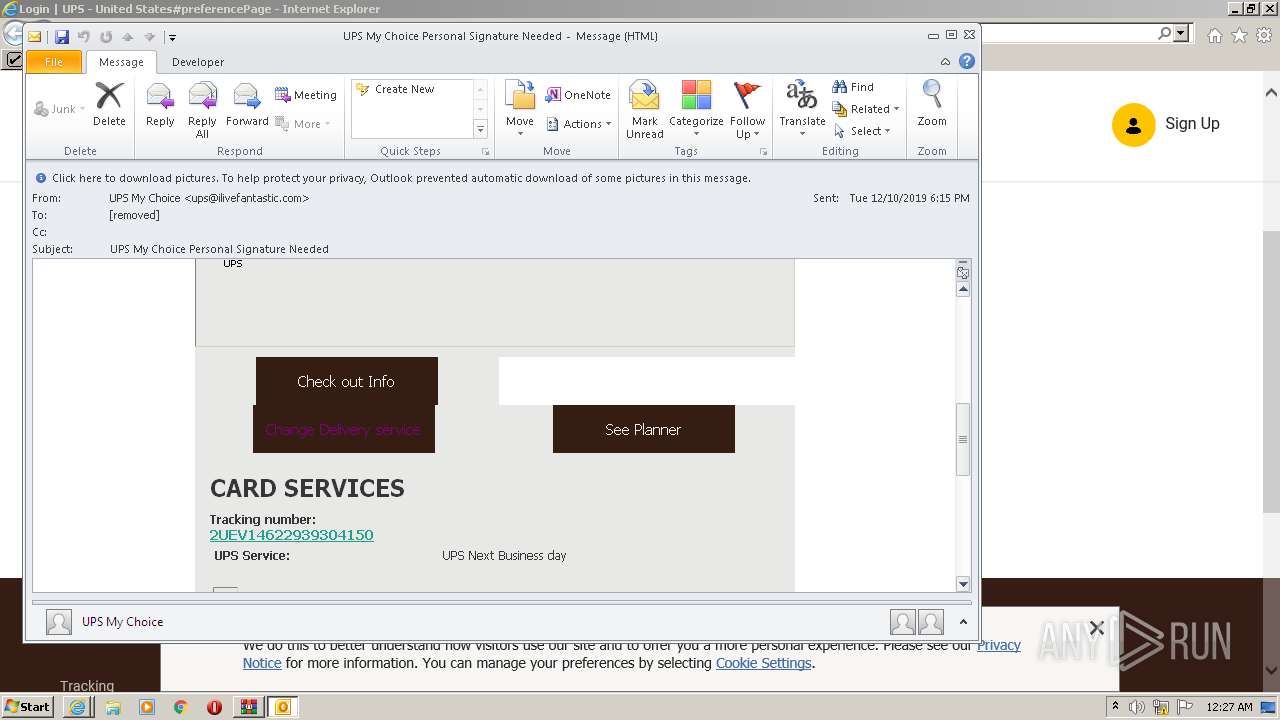
| 2192 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIb3268.29337\2019-12-10-Hancitor-malspam-1815-UTC.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.malware-traffic-analysis.net/2019/12/10/index.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3064 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2532 CREDAT:2954532 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2532 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
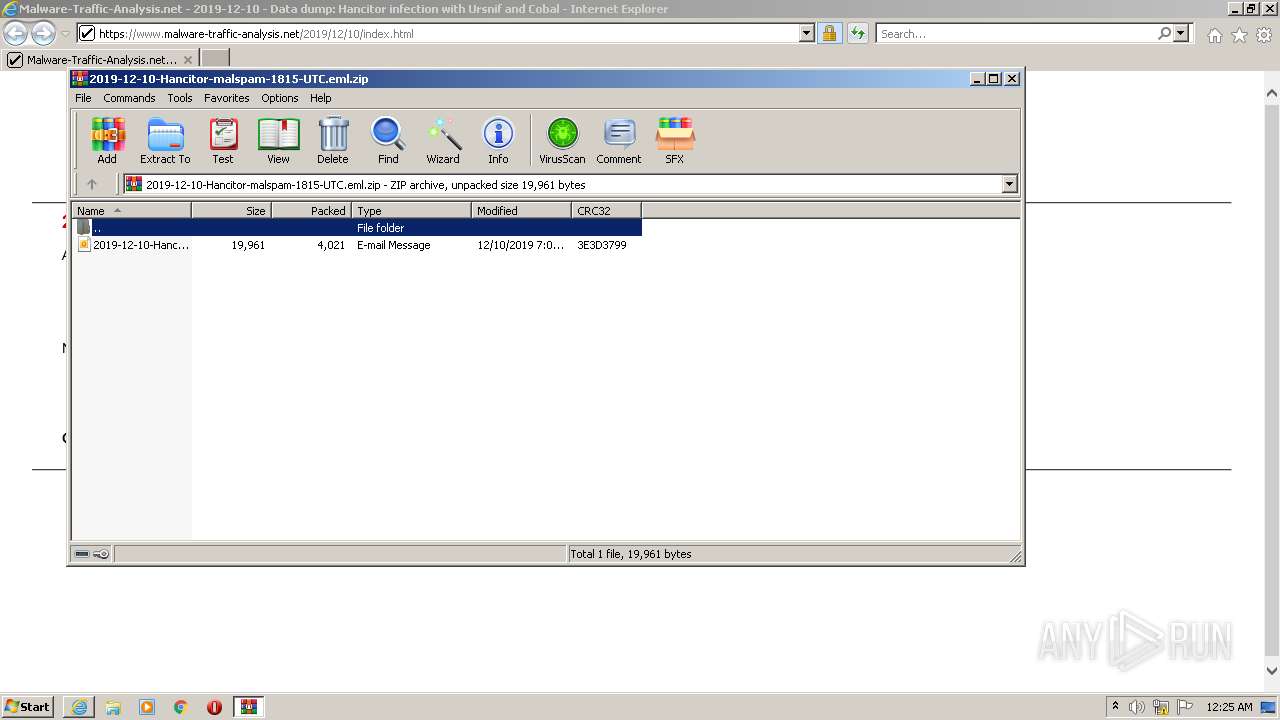
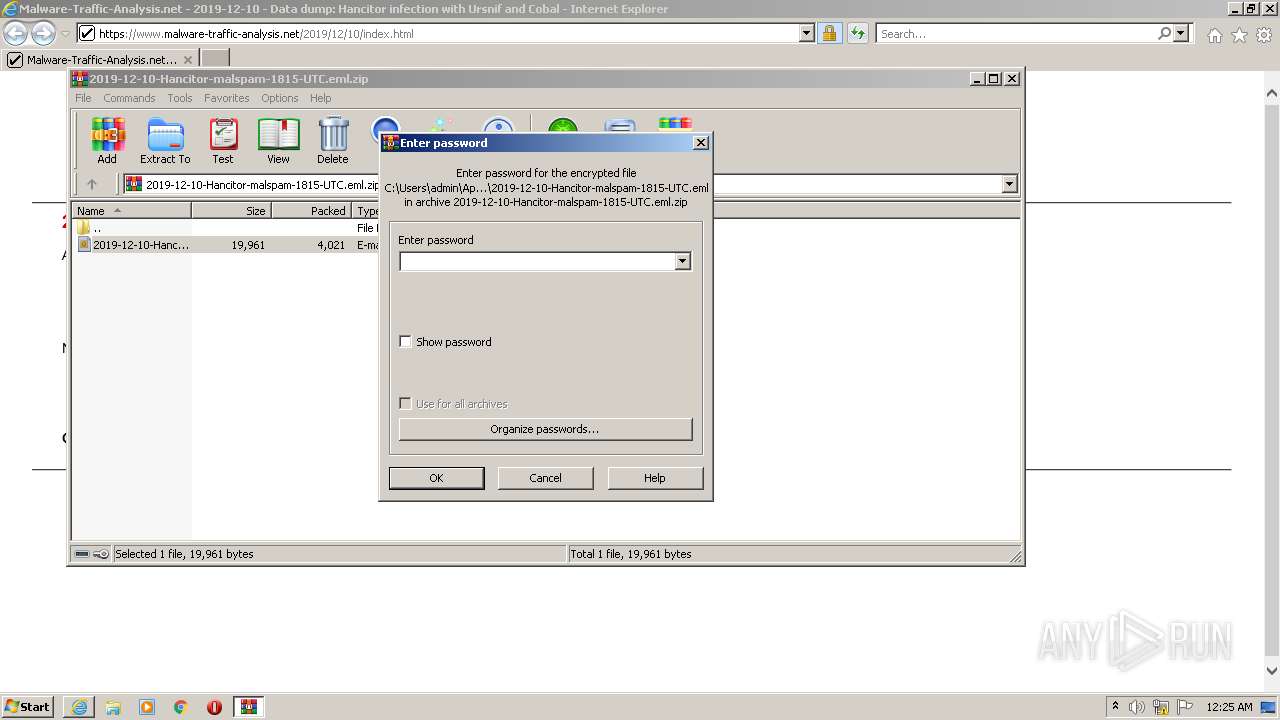
| 3268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\2019-12-10-Hancitor-malspam-1815-UTC.eml.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3340 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3976 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
59 011
Read events
57 792
Write events
1 188
Delete events
31
Modification events
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960800 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960800 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
46
Text files
218
Unknown types
85
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2A249A8EAE5FF8B677AA8B178688CF94 | der | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\index[1].htm | html | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 2192 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8649.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 2192 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2A249A8EAE5FF8B677AA8B178688CF94 | binary | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
204
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
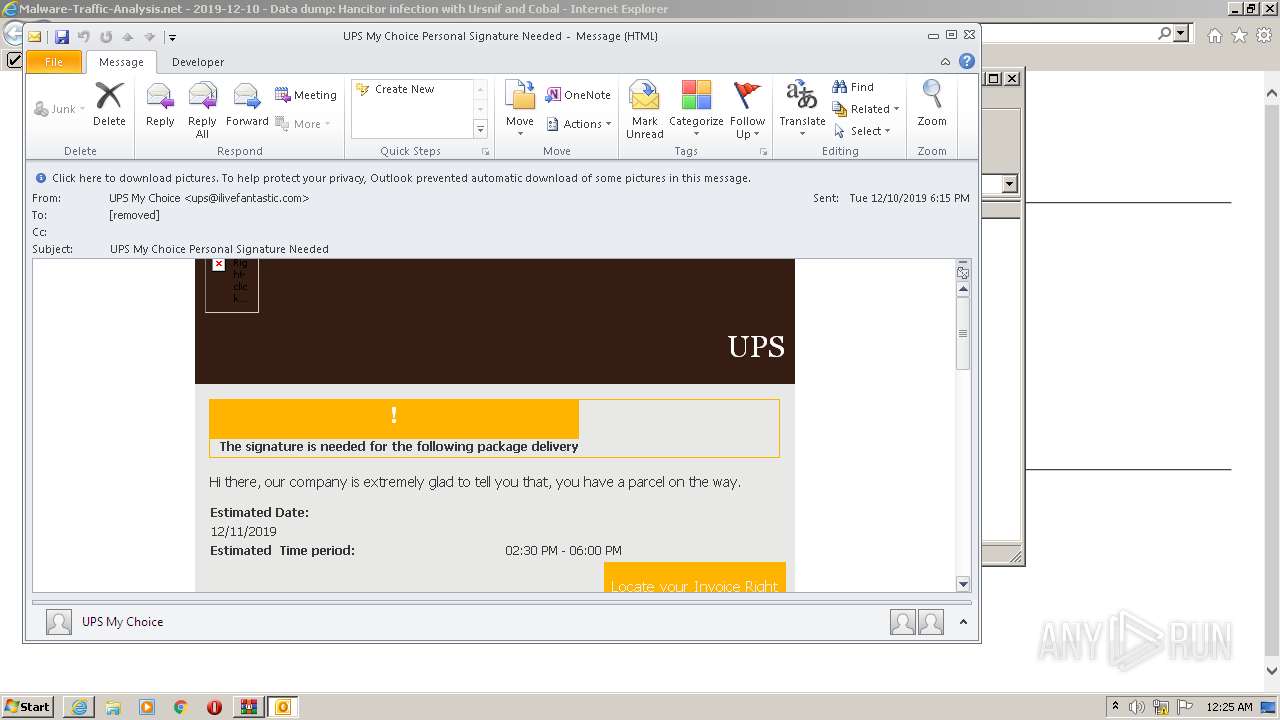
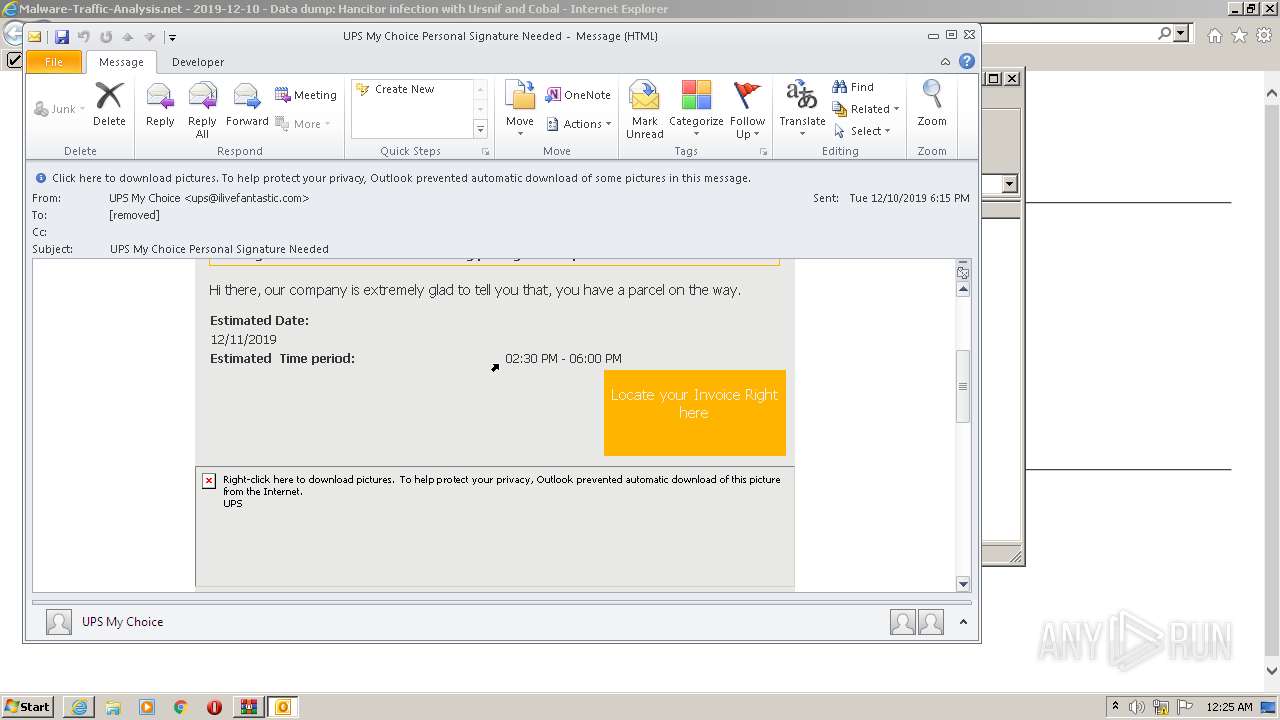
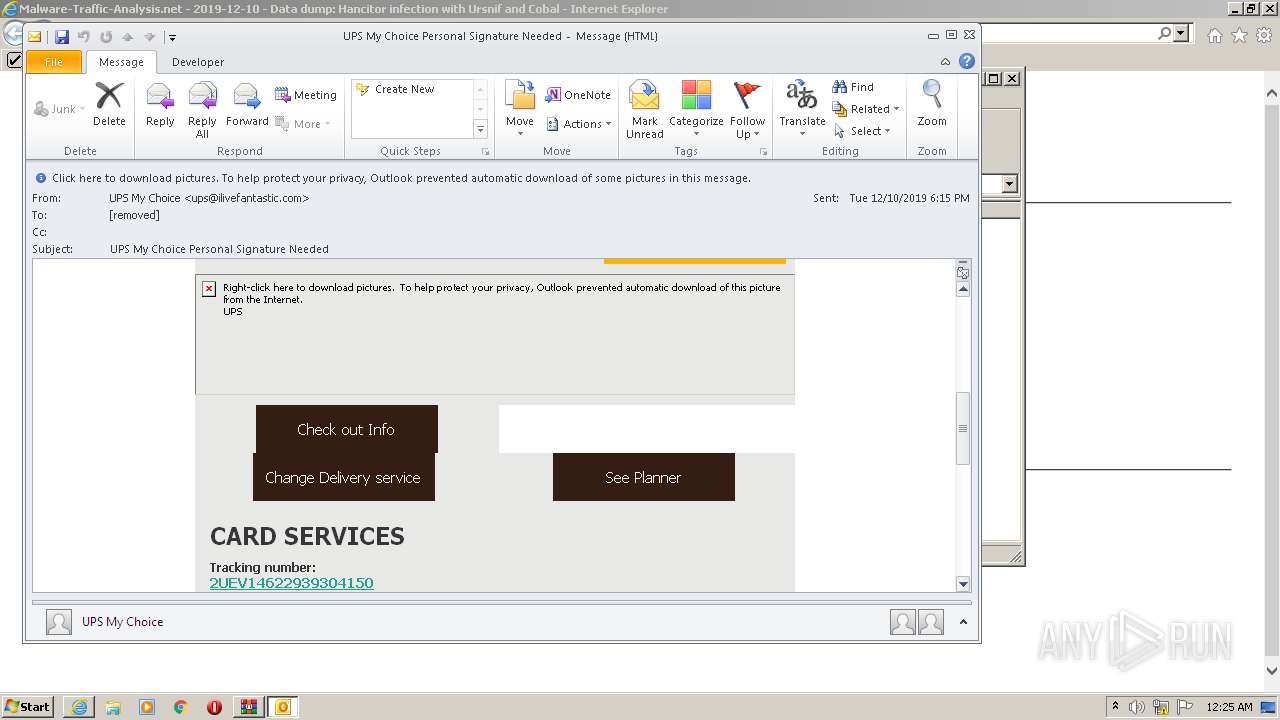
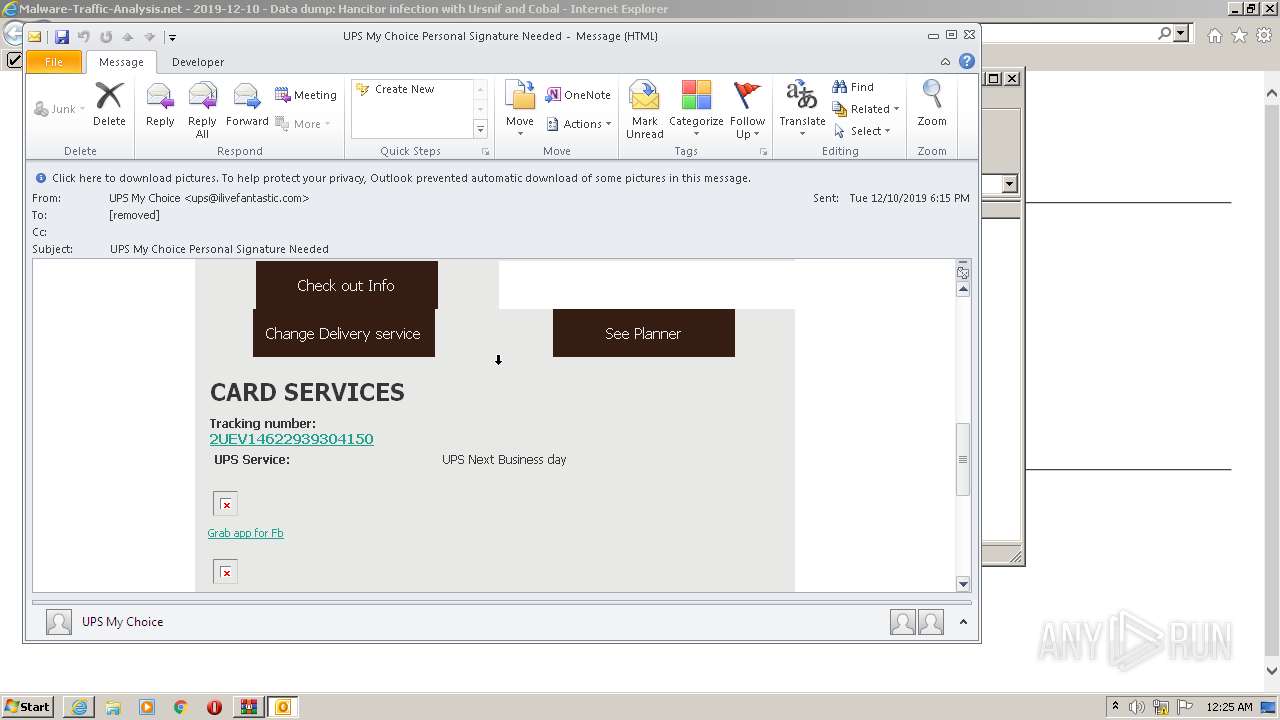
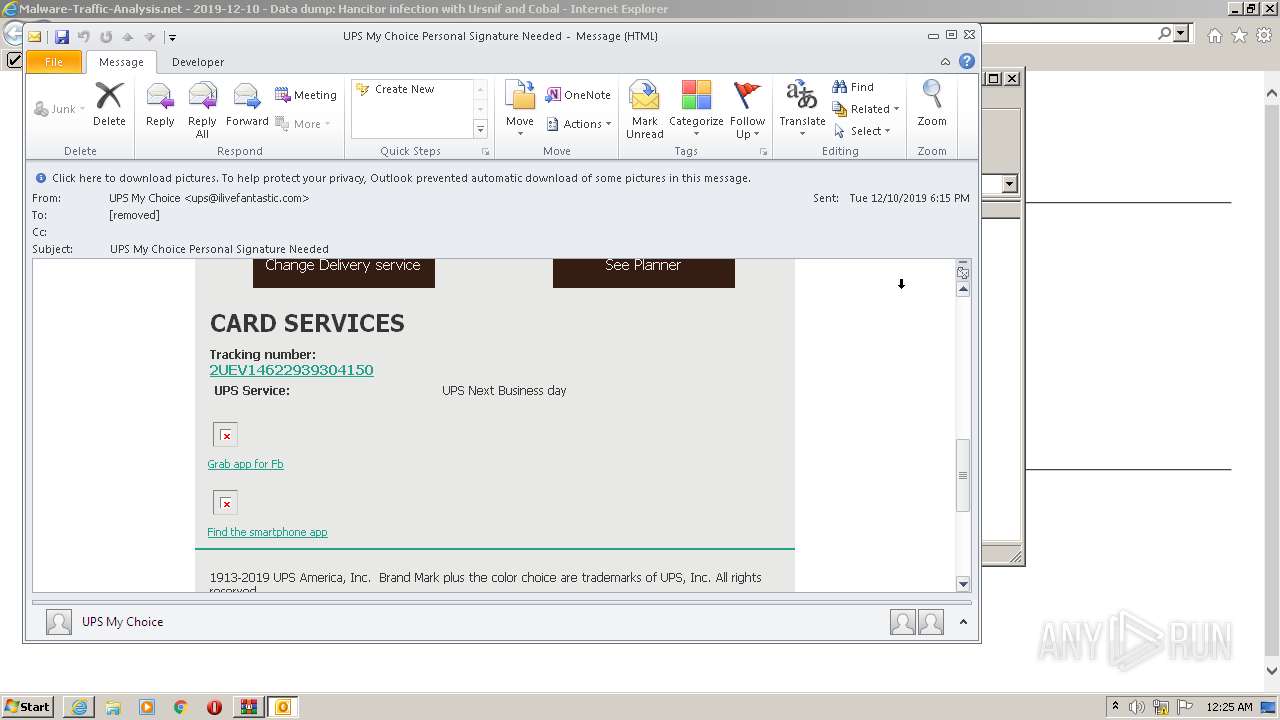
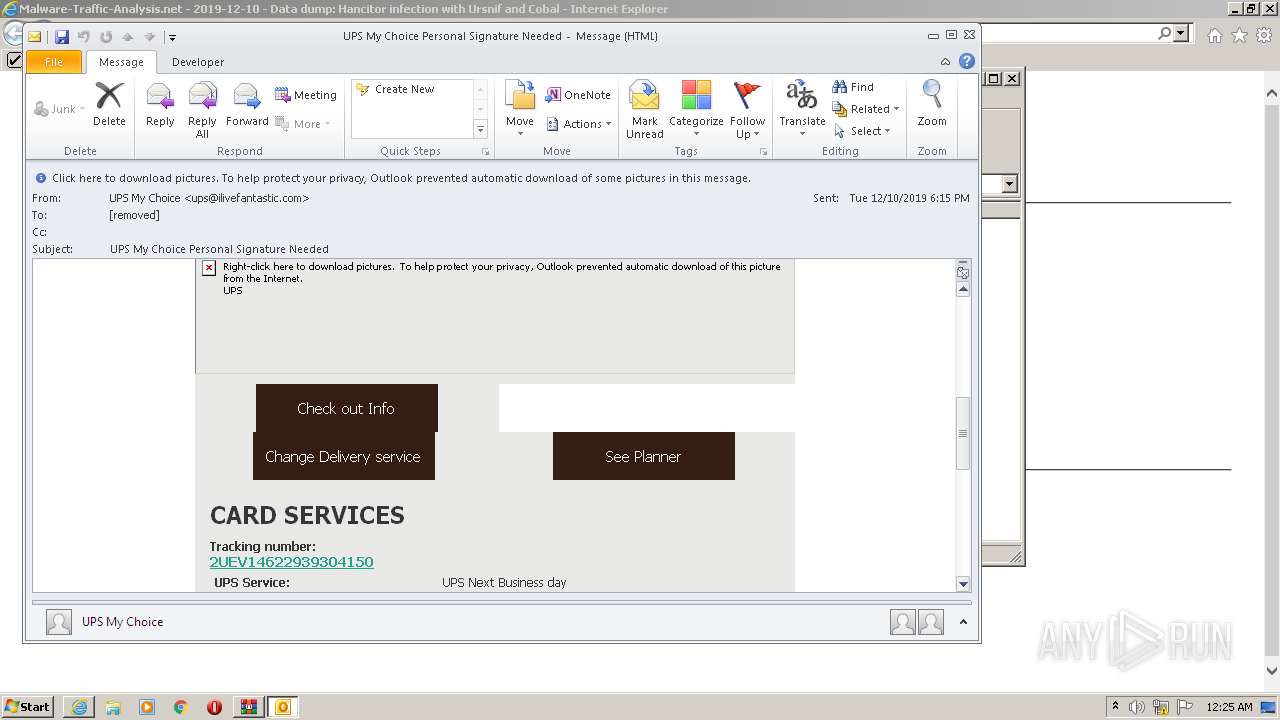
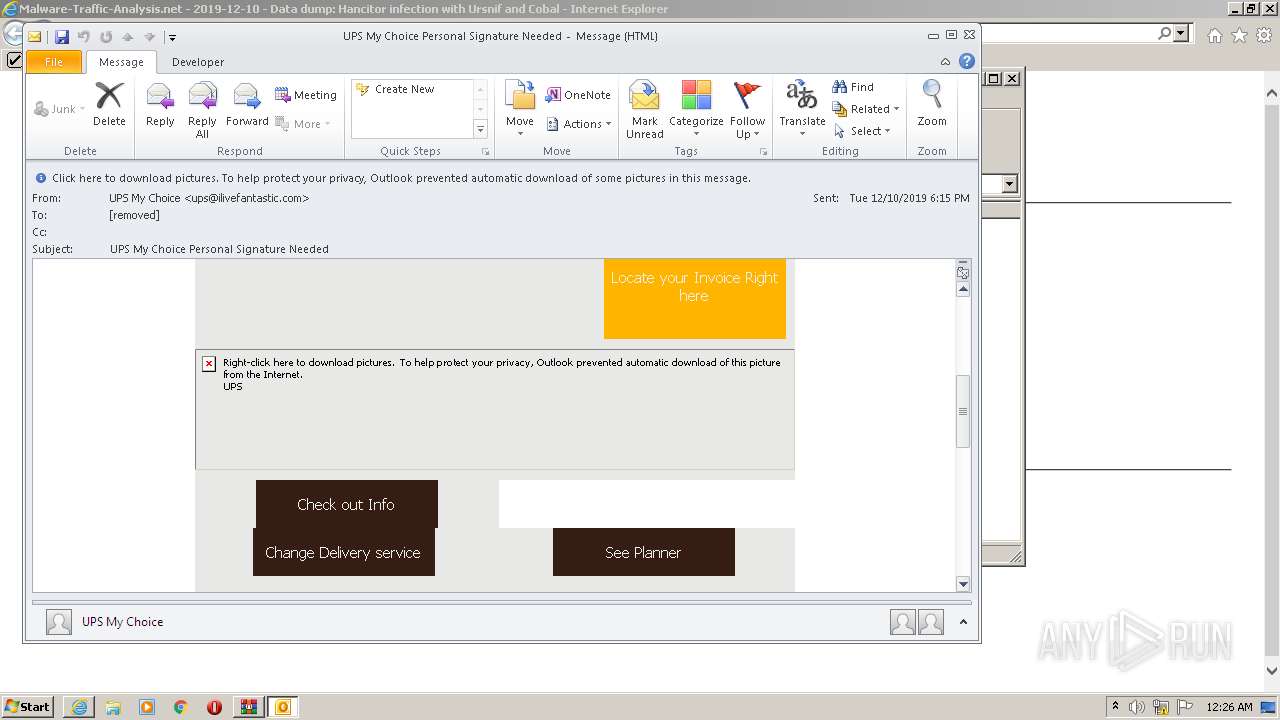
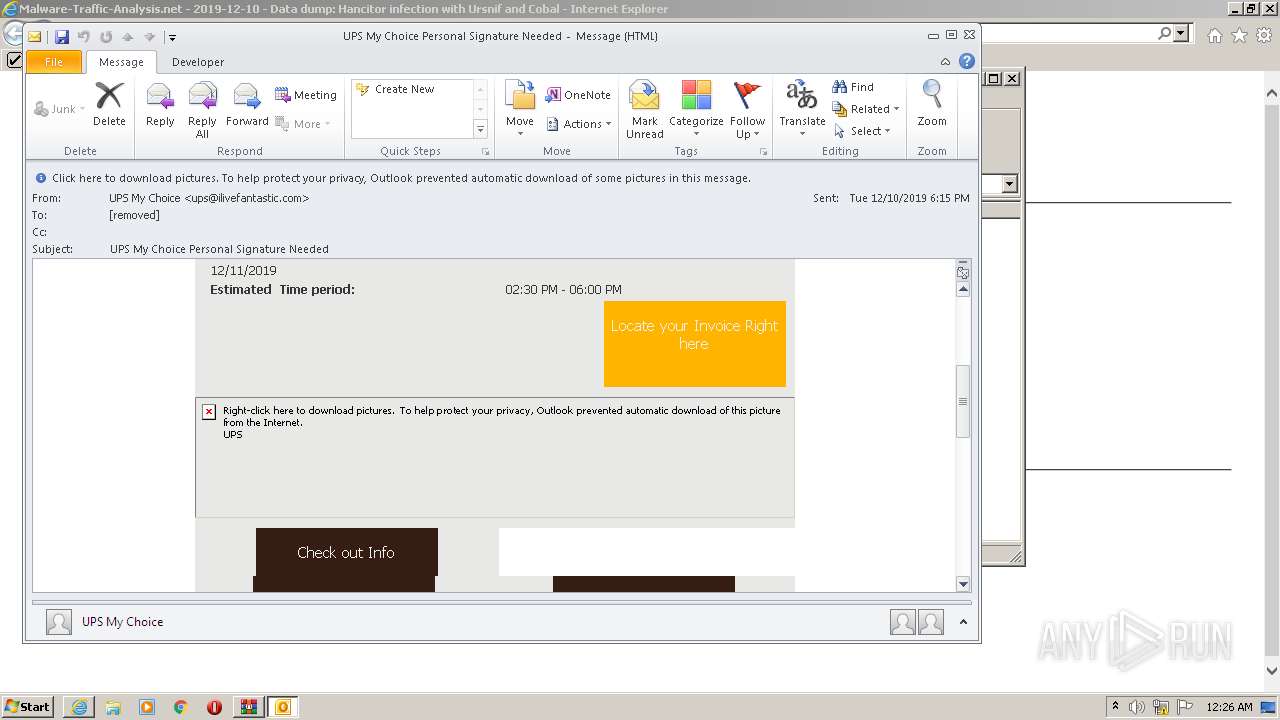
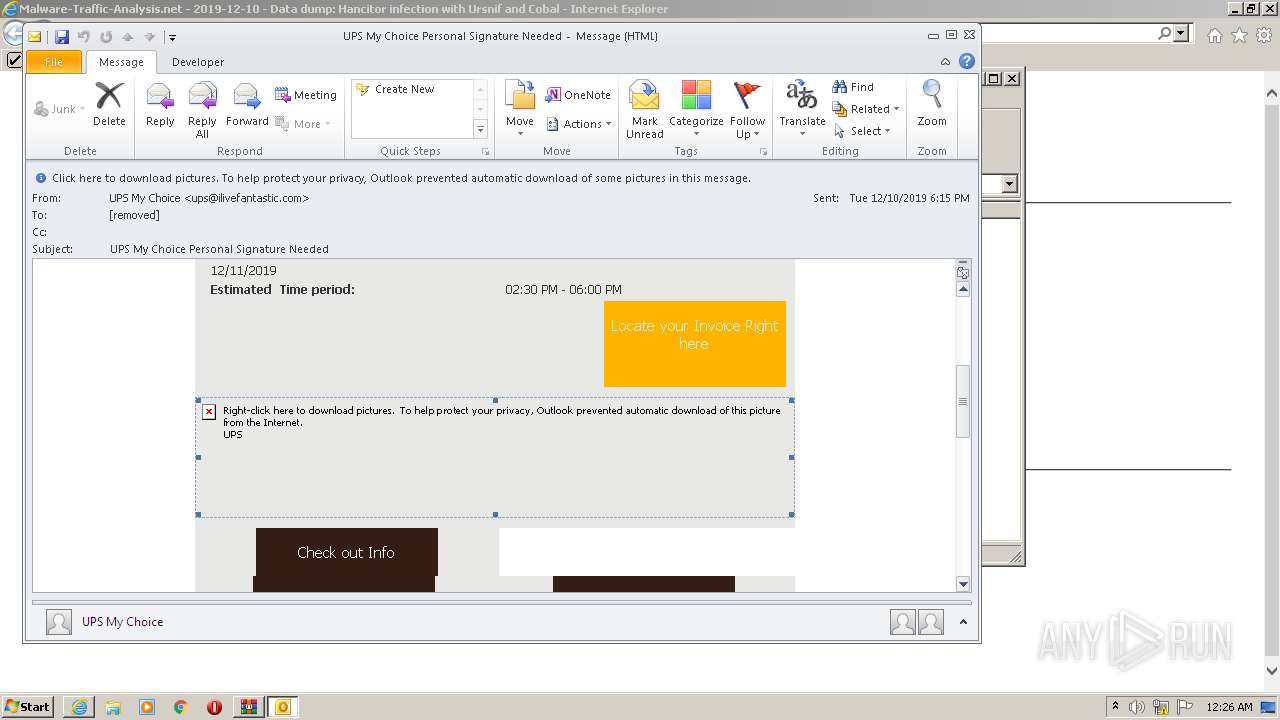
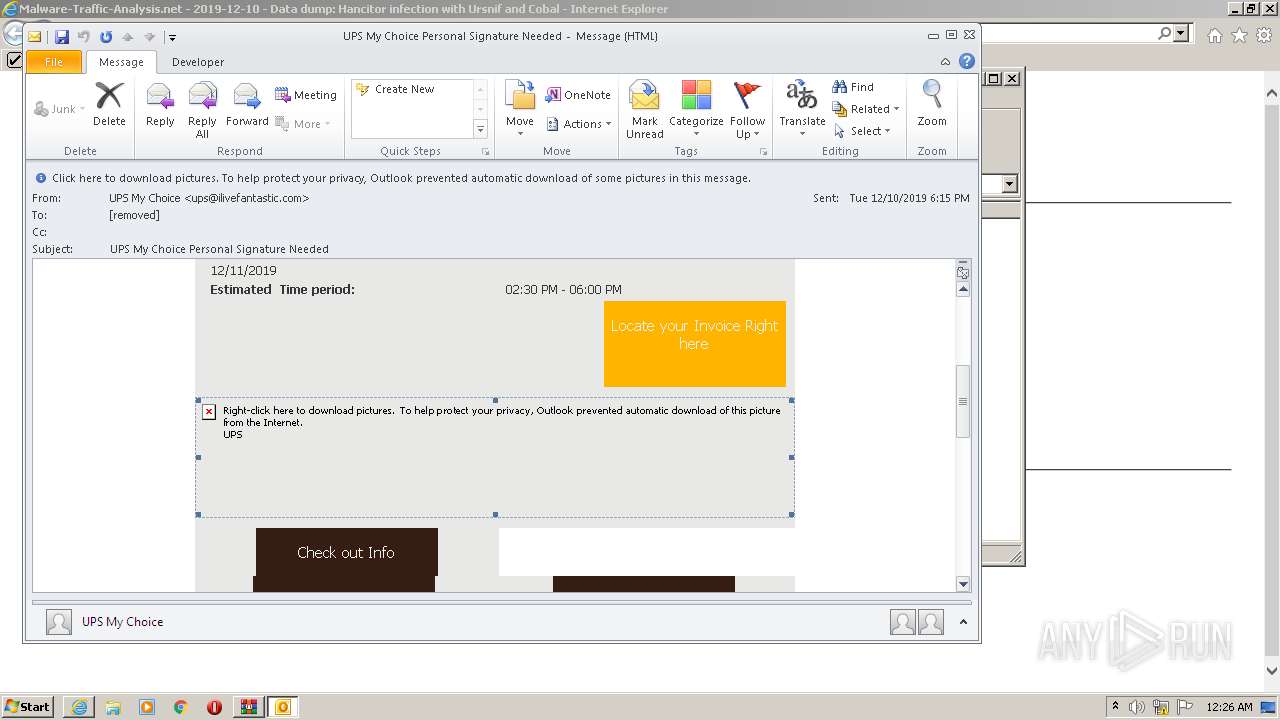
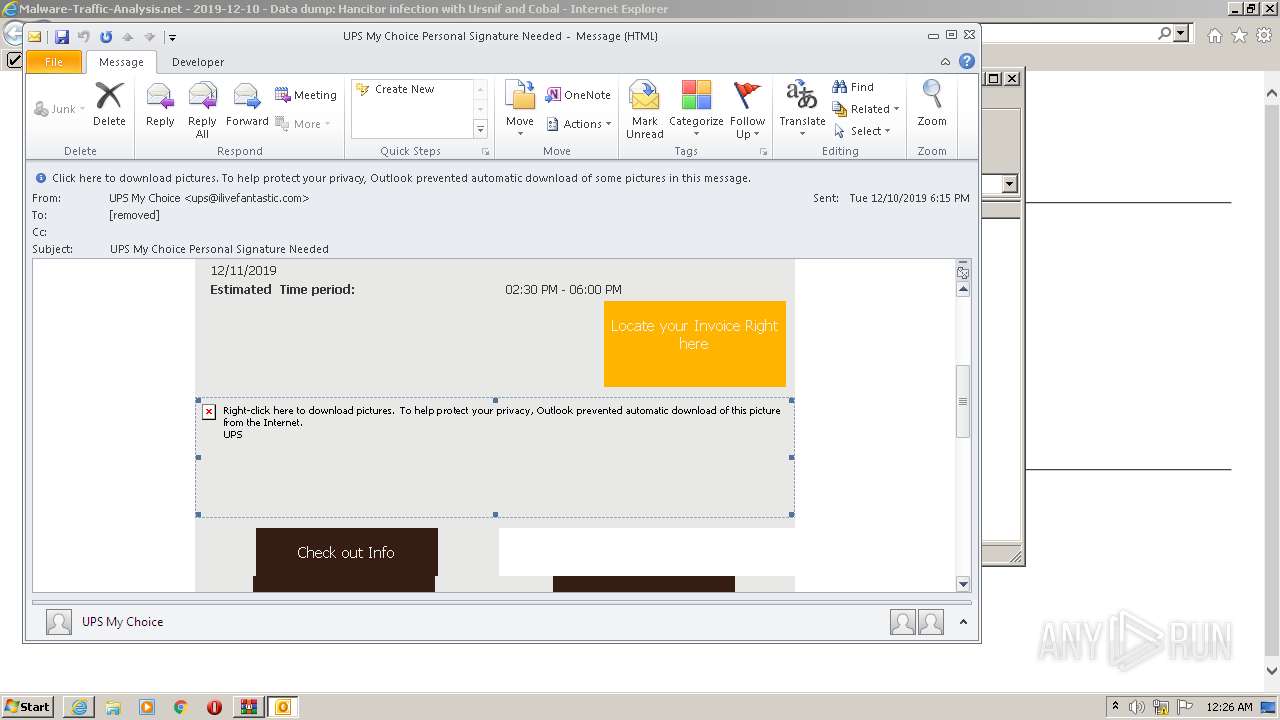
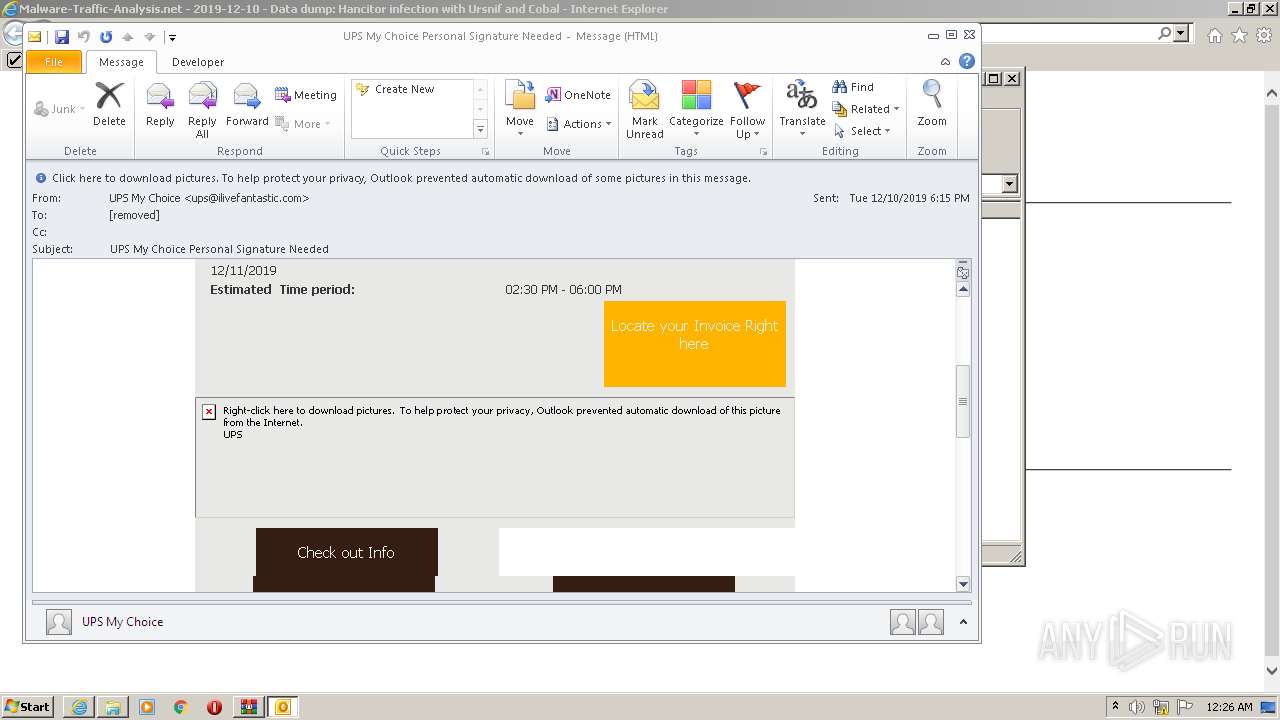
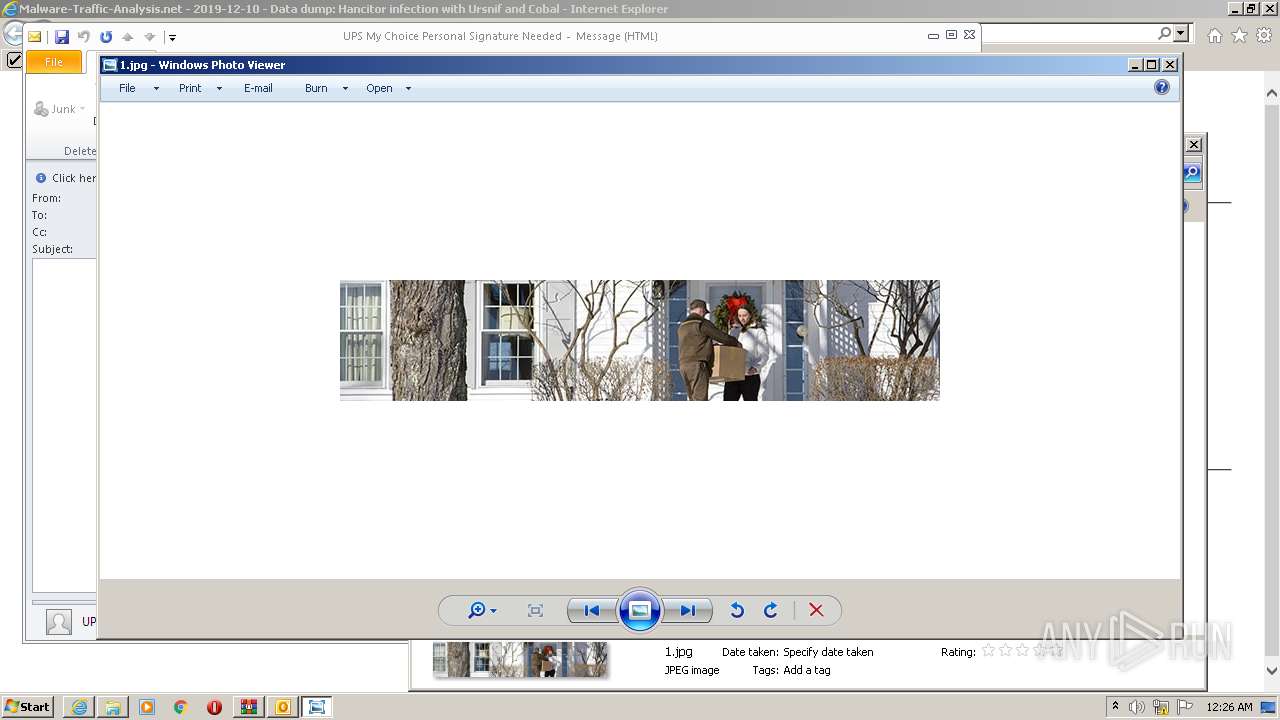
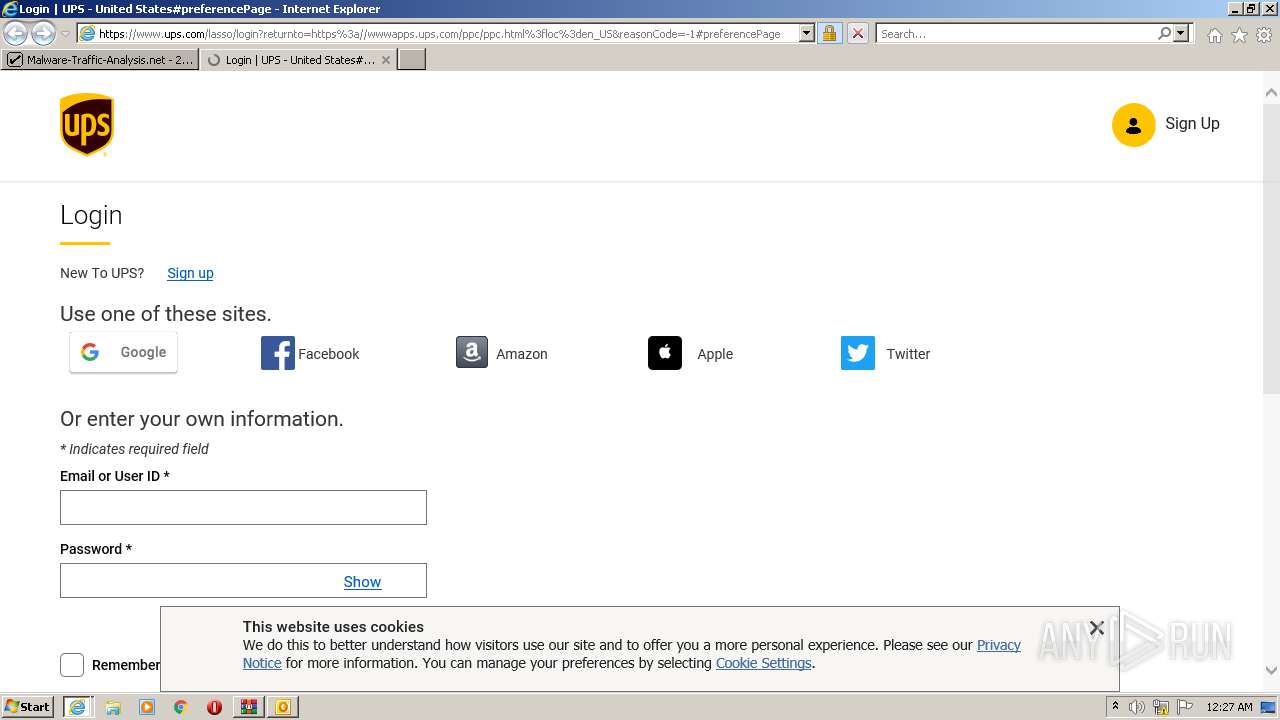
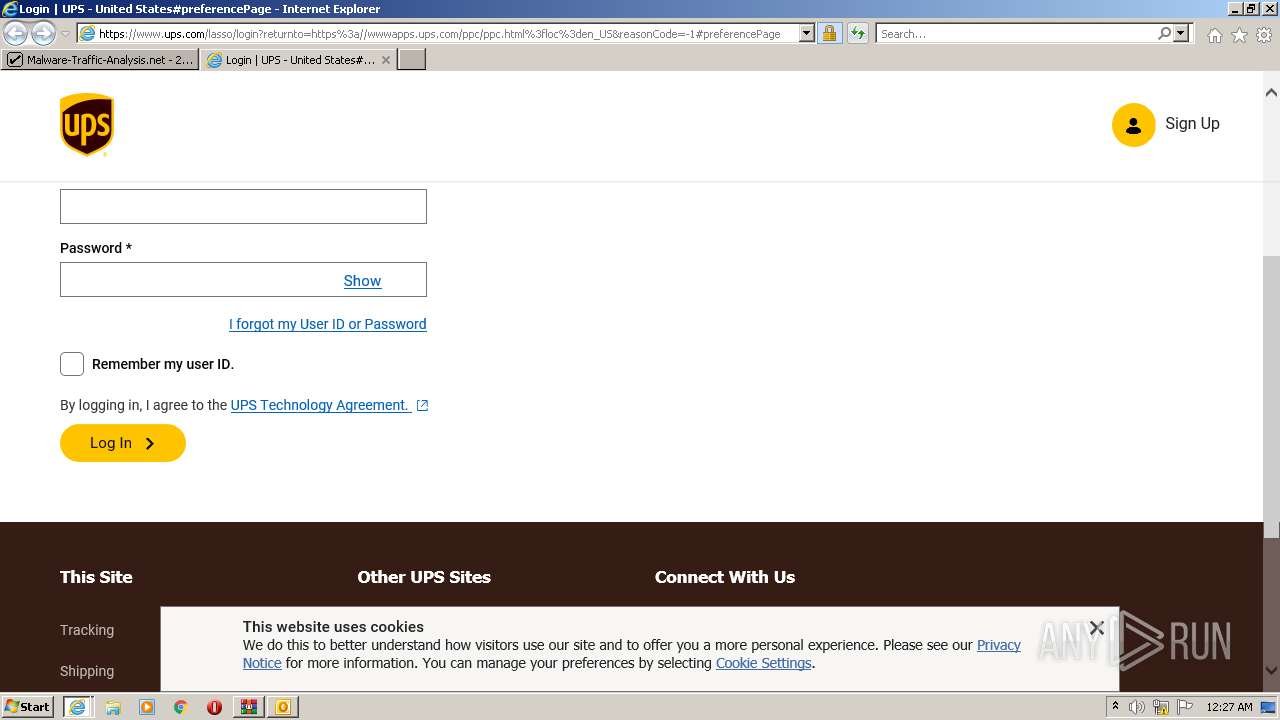
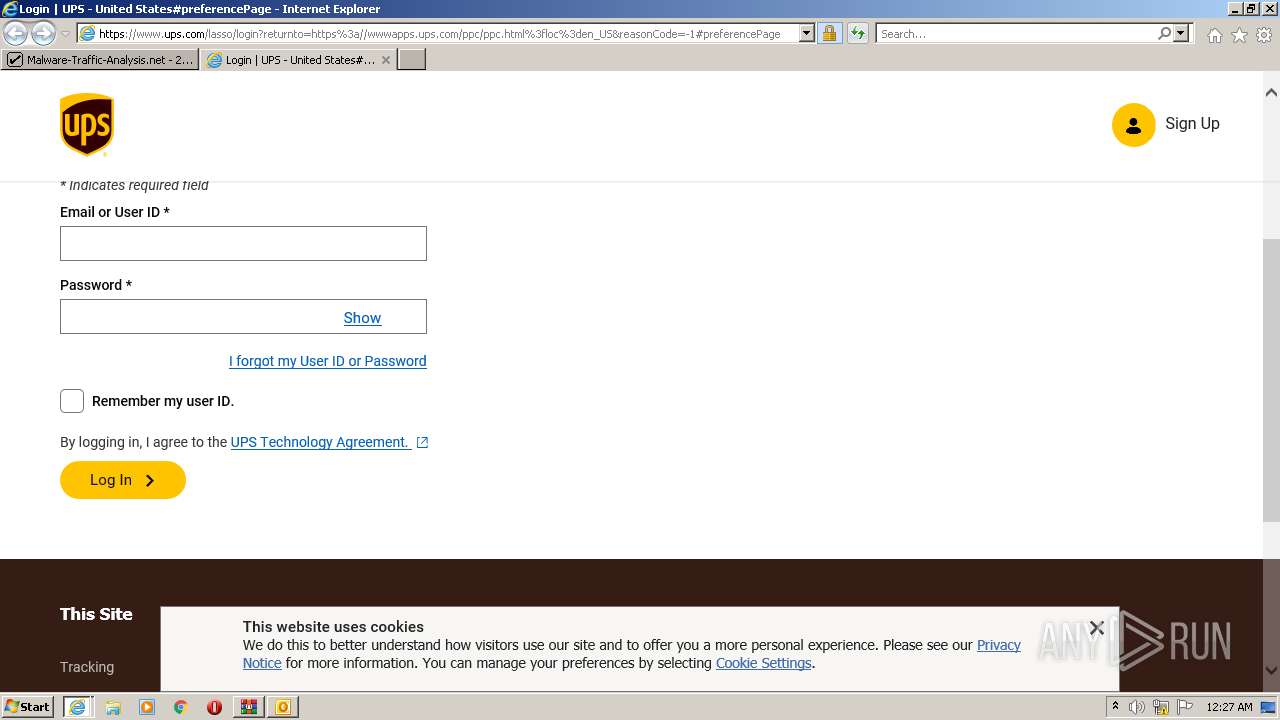
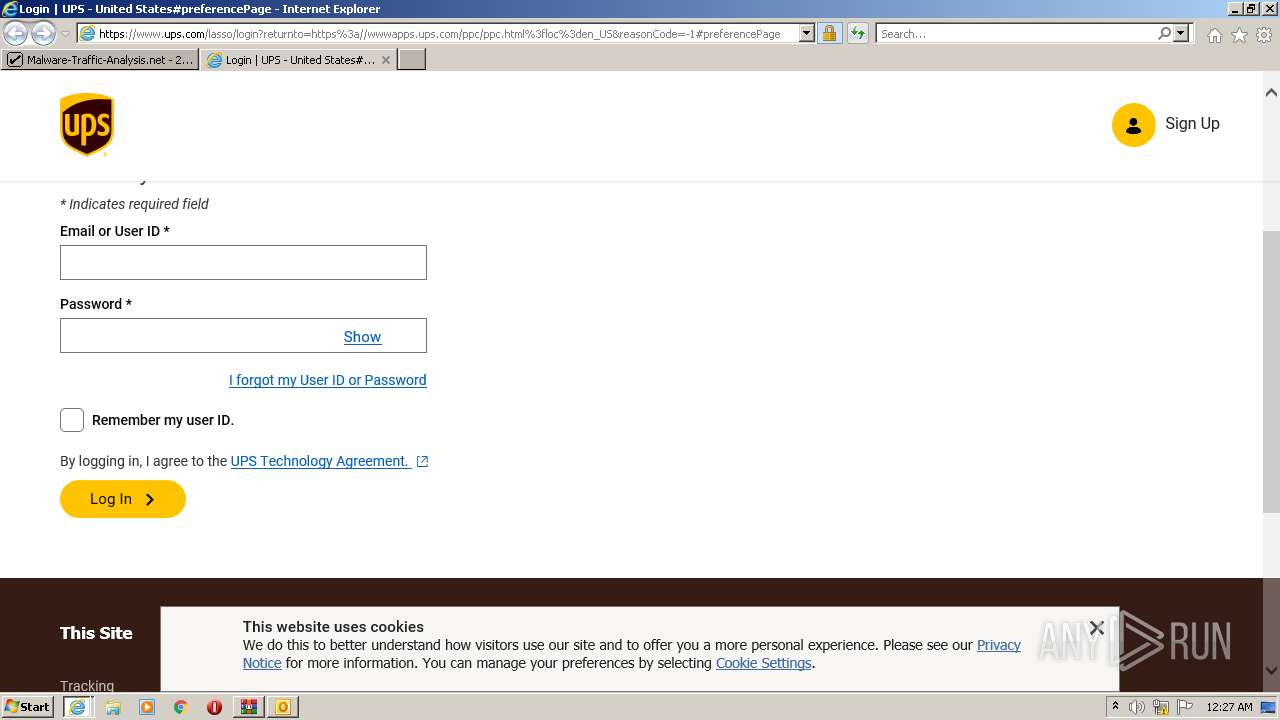
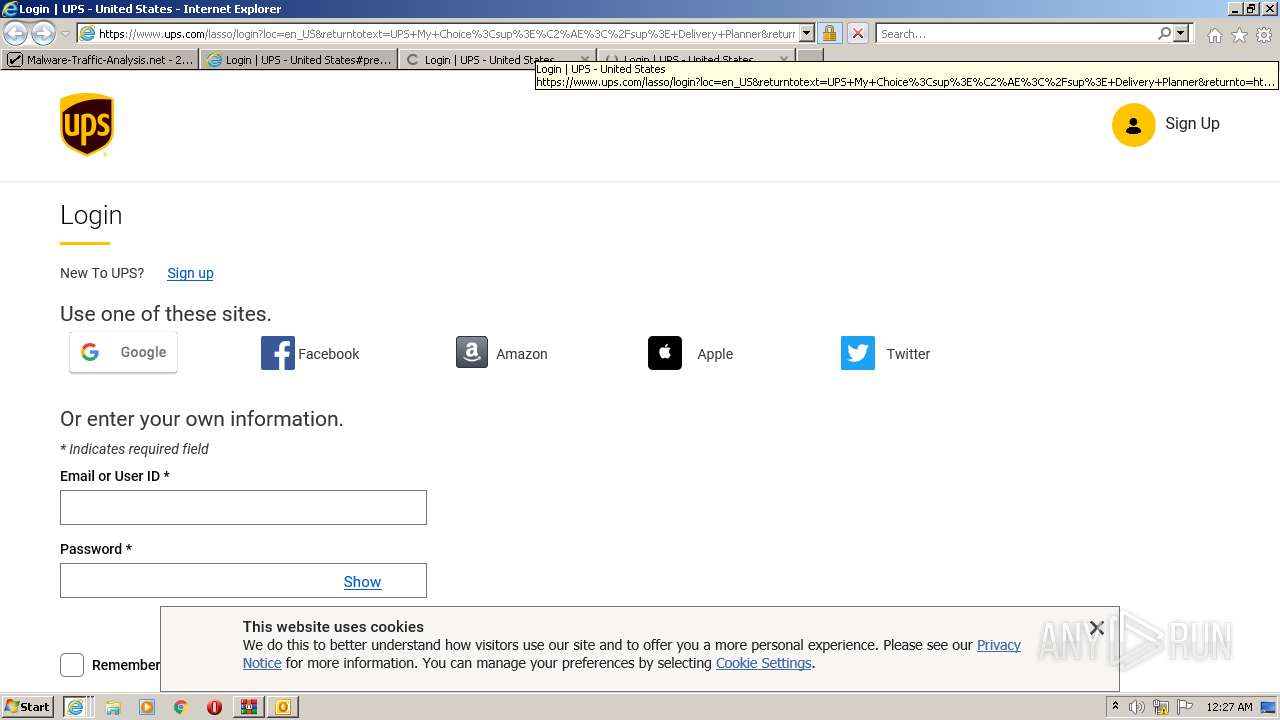
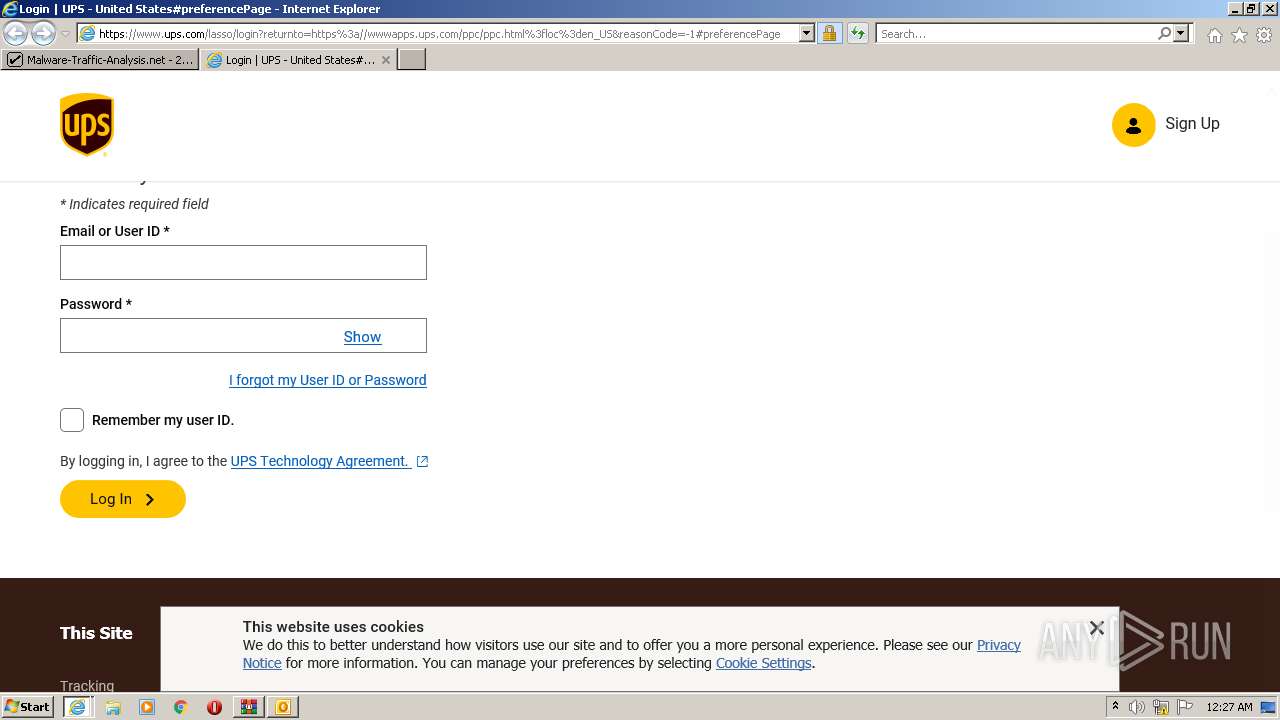
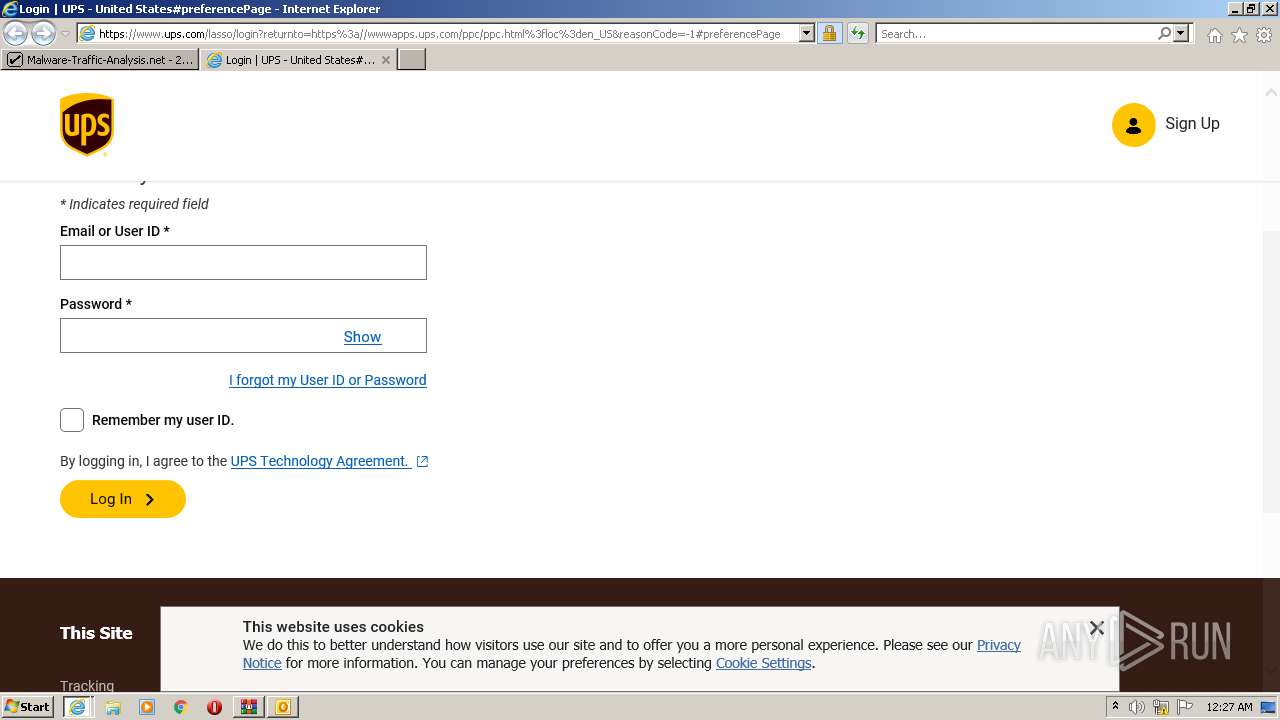
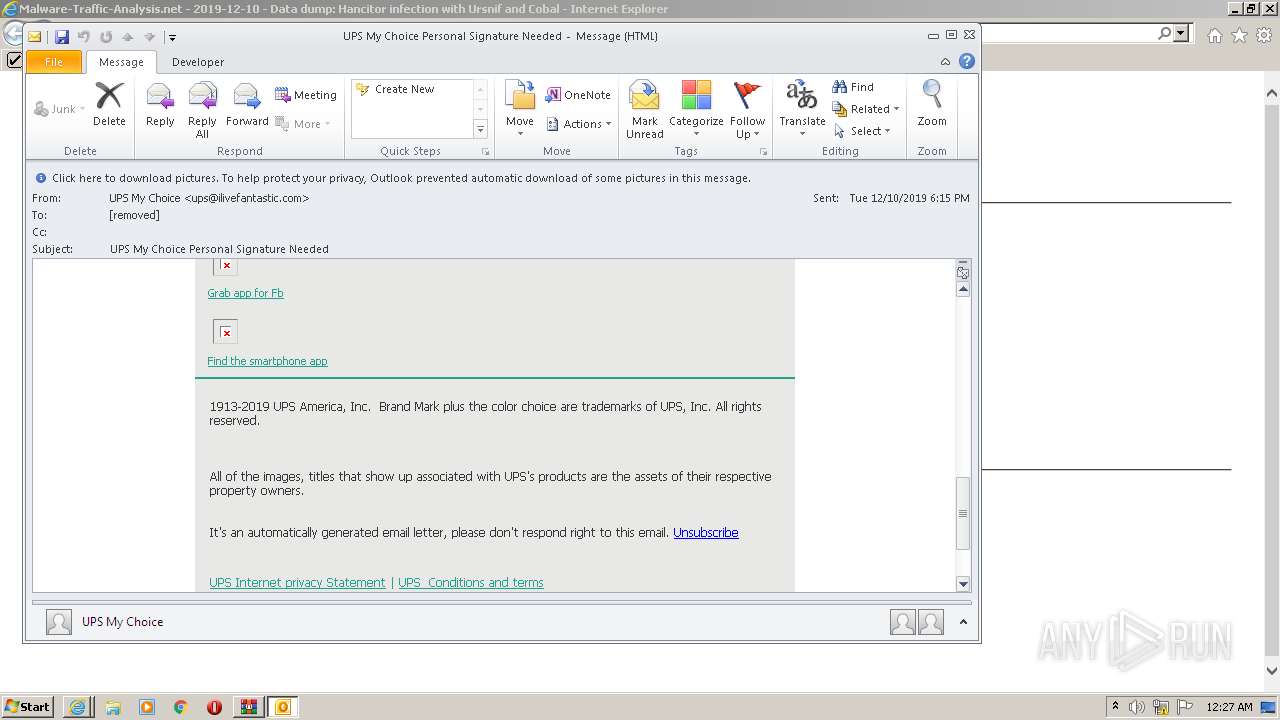
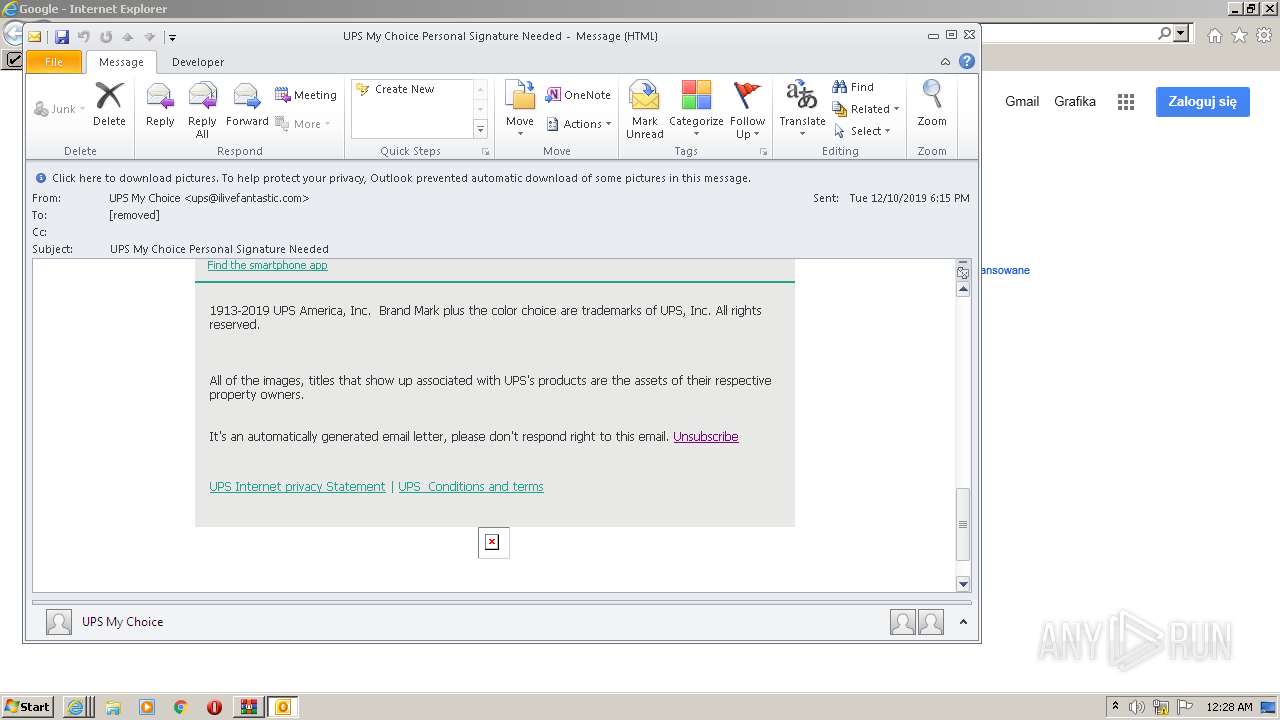
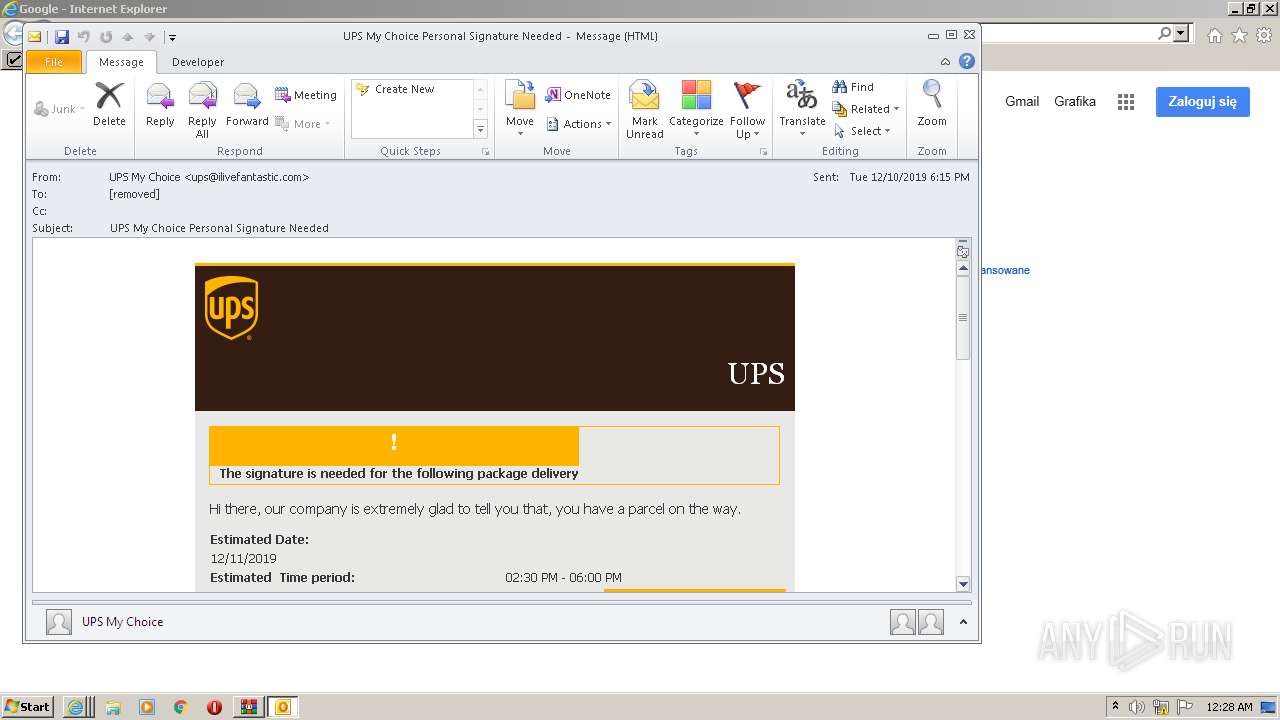
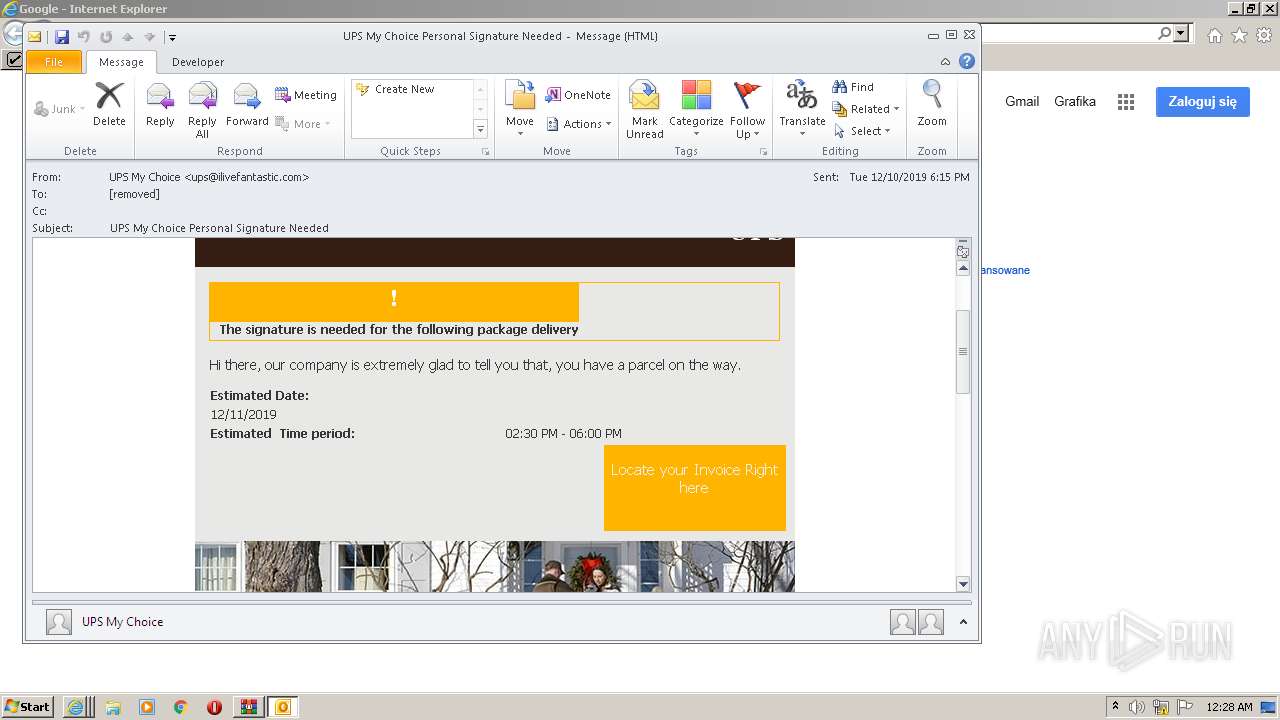
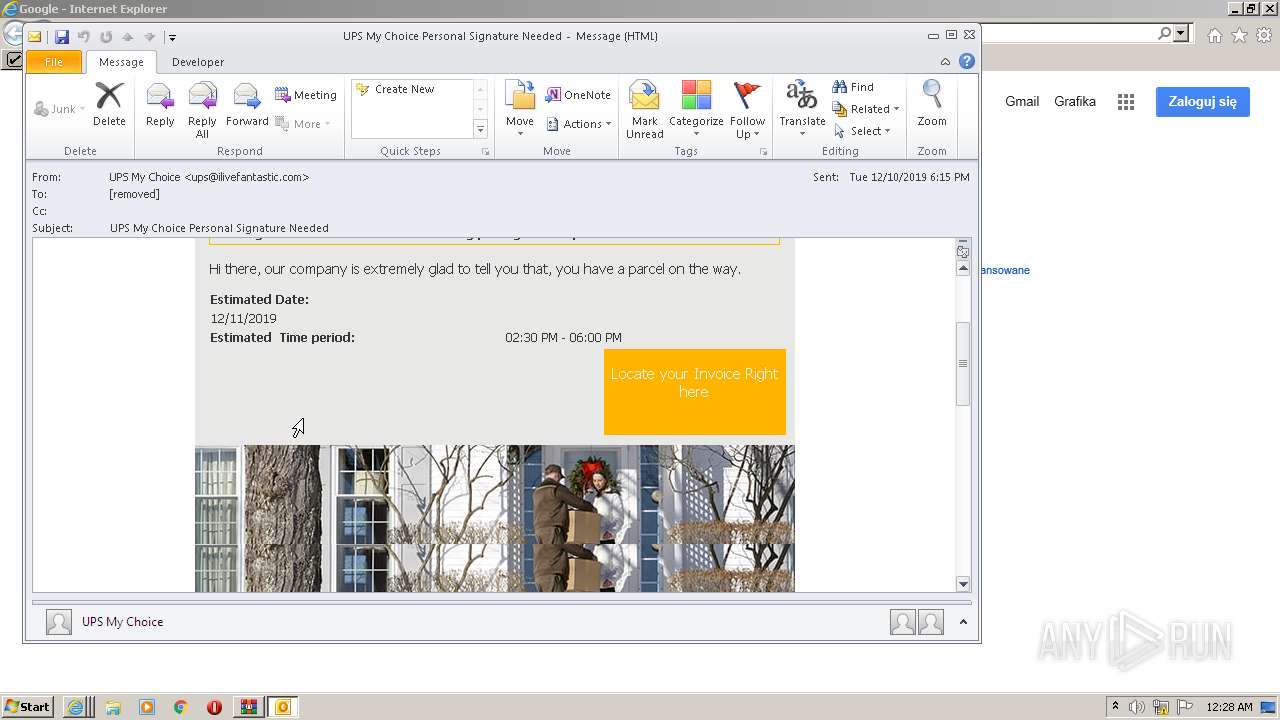
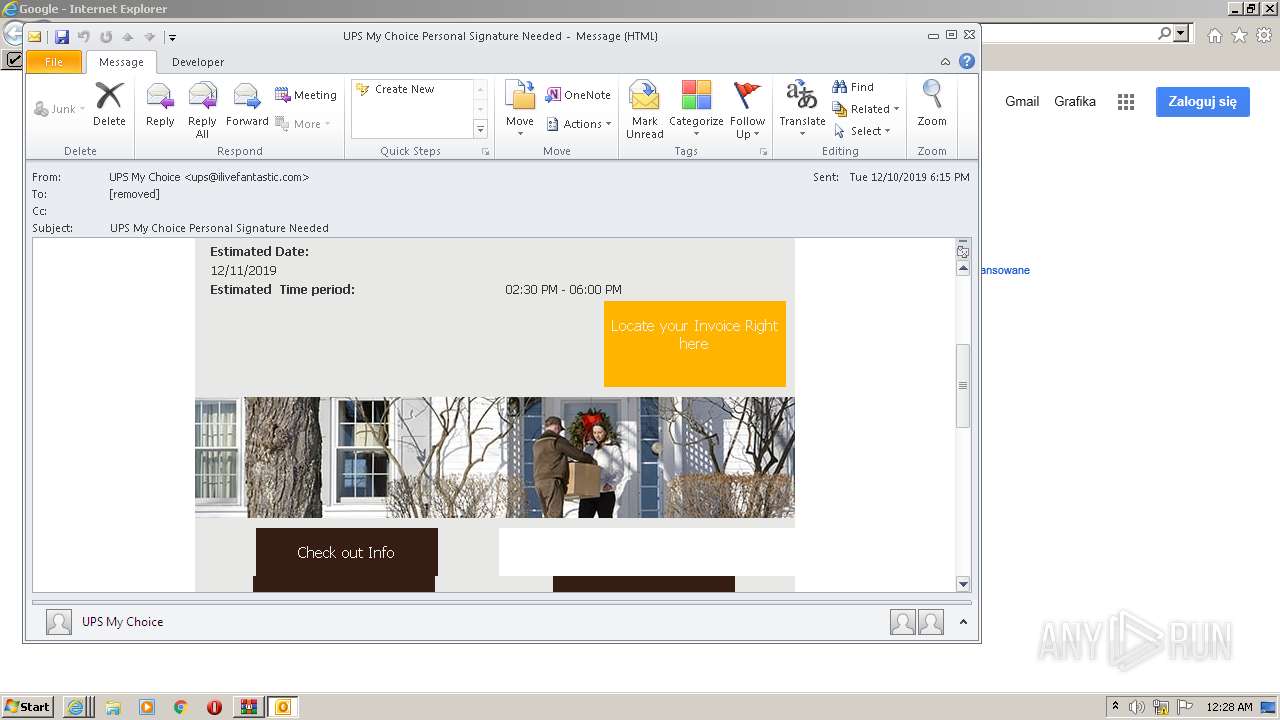
2192 | OUTLOOK.EXE | OPTIONS | 301 | 104.75.89.177:80 | http://www.ups.com/img/ | NL | — | — | whitelisted |
2192 | OUTLOOK.EXE | OPTIONS | 301 | 104.75.89.177:80 | http://www.ups.com/img/ | NL | — | — | whitelisted |
2192 | OUTLOOK.EXE | GET | 301 | 104.75.89.177:80 | http://www.ups.com/img/email_driver_wreath.jpg | NL | — | — | whitelisted |
3236 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2192 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3236 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2192 | OUTLOOK.EXE | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEDaCXn%2B1pIGTfvbRc2u5PKY%3D | US | der | 727 b | whitelisted |
2192 | OUTLOOK.EXE | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3064 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAVRb9%2F4pdgBN%2BxYBGu4dSk%3D | US | — | — | whitelisted |
3064 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2532 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2532 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2192 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2532 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2192 | OUTLOOK.EXE | 104.75.89.177:80 | www.ups.com | Akamai Technologies, Inc. | NL | suspicious |
2192 | OUTLOOK.EXE | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
2192 | OUTLOOK.EXE | 104.75.89.177:443 | www.ups.com | Akamai Technologies, Inc. | NL | suspicious |
2532 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2532 | iexplore.exe | 104.90.179.99:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
2532 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.malware-traffic-analysis.net |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.messenger.msn.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |